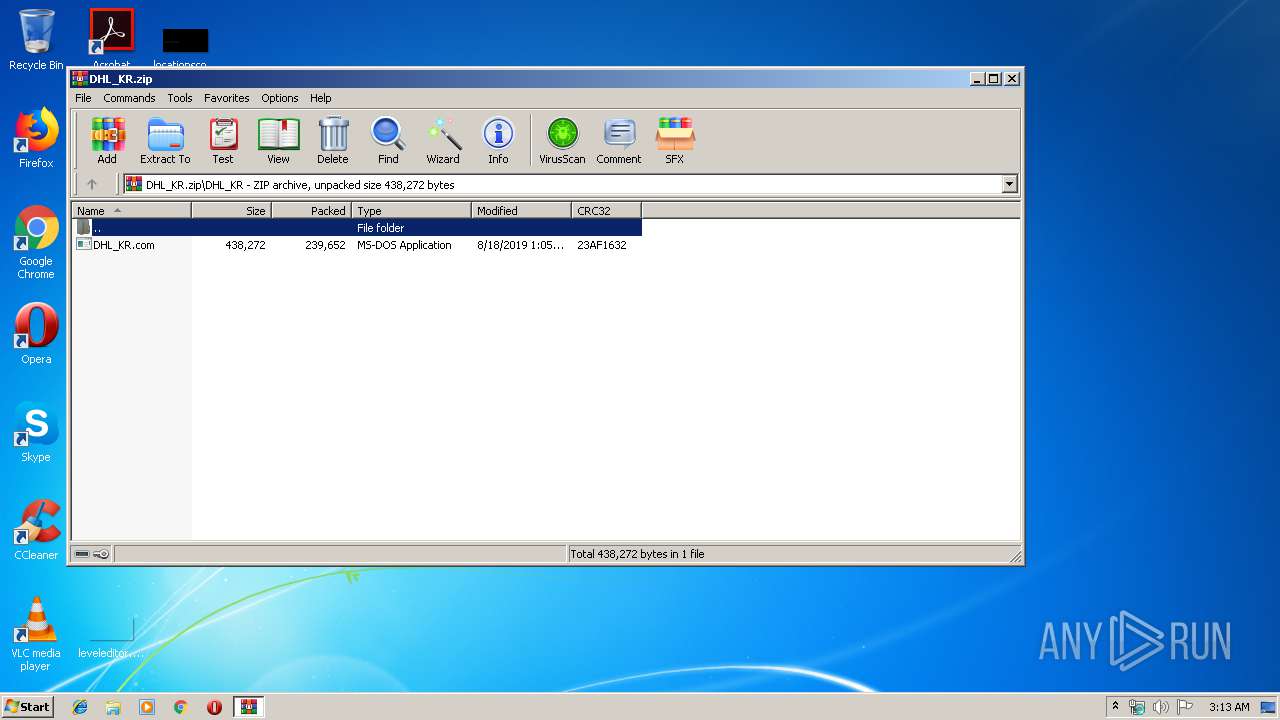
| File name: | DHL_KR.zip |
| Full analysis: | https://app.any.run/tasks/f8673e9d-8c11-4380-8d8c-aa0516186762 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | August 26, 2019, 02:12:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
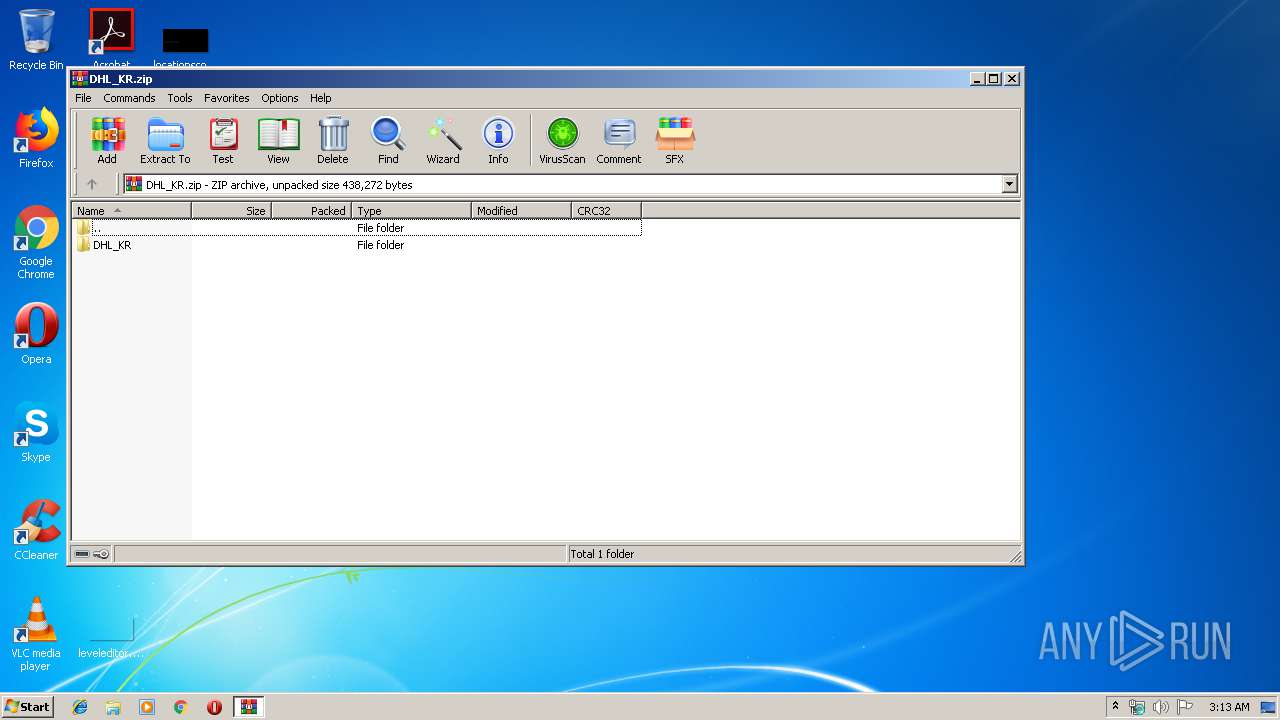
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 38D3DFEBFD261D415CAD88810704F48F |
| SHA1: | 9E5D2B503034394BCA69127533FE7FF486C8EF10 |
| SHA256: | 991477849BAD61381517C361F1E8B0A865C1B06A97D12BBFFF42D6E91E9D2A63 |
| SSDEEP: | 6144:DeHbjND9KBRMs2/0a2Xhg5NrQeF9gTRtQe04fDeMl:K7jNIjMs2/0ayT1TnQ5wqMl |
MALICIOUS
Application was dropped or rewritten from another process
- DHL_KR.com (PID: 4012)
- DHL_KR.com (PID: 3112)
- DHL_KR.com (PID: 3948)
- mfcr6q.exe (PID: 2544)
- mfcr6q.exe (PID: 3216)
- mfcr6q.exe (PID: 4080)
Runs app for hidden code execution
- explorer.exe (PID: 276)
FORMBOOK was detected
- explorer.exe (PID: 276)
Connects to CnC server
- explorer.exe (PID: 276)
Changes the autorun value in the registry
- cmd.exe (PID: 2628)
Actions looks like stealing of personal data
- cmd.exe (PID: 2628)
Formbook was detected
- cmd.exe (PID: 2628)
- Firefox.exe (PID: 3968)
Stealing of credential data
- cmd.exe (PID: 2628)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2860)
- explorer.exe (PID: 276)
- DllHost.exe (PID: 4020)
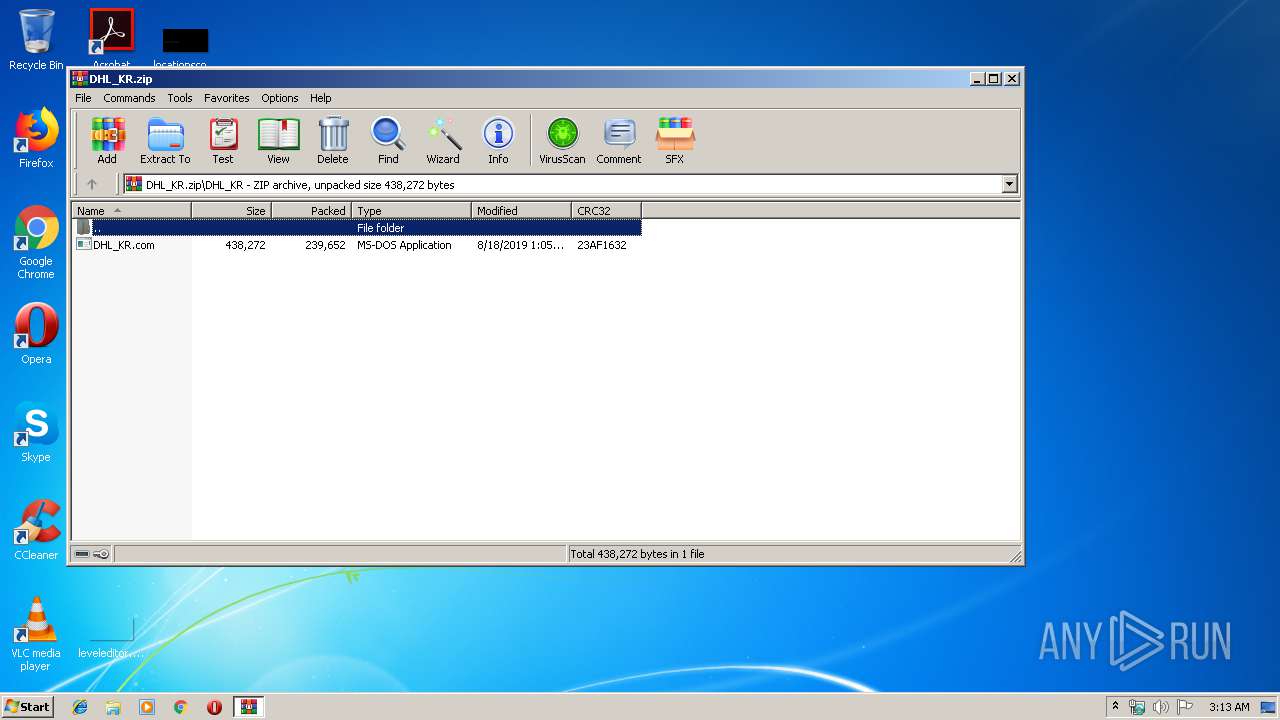
Starts application with an unusual extension
- DHL_KR.com (PID: 4012)
- explorer.exe (PID: 276)
- DHL_KR.com (PID: 3112)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 276)
- cmd.exe (PID: 2628)
Application launched itself
- cmd.exe (PID: 2628)
- mfcr6q.exe (PID: 2544)
Executed via COM
- DllHost.exe (PID: 4020)
Creates files in the program directory
- DllHost.exe (PID: 4020)
Creates files in the user directory
- cmd.exe (PID: 2628)
Loads DLL from Mozilla Firefox
- cmd.exe (PID: 2628)
INFO
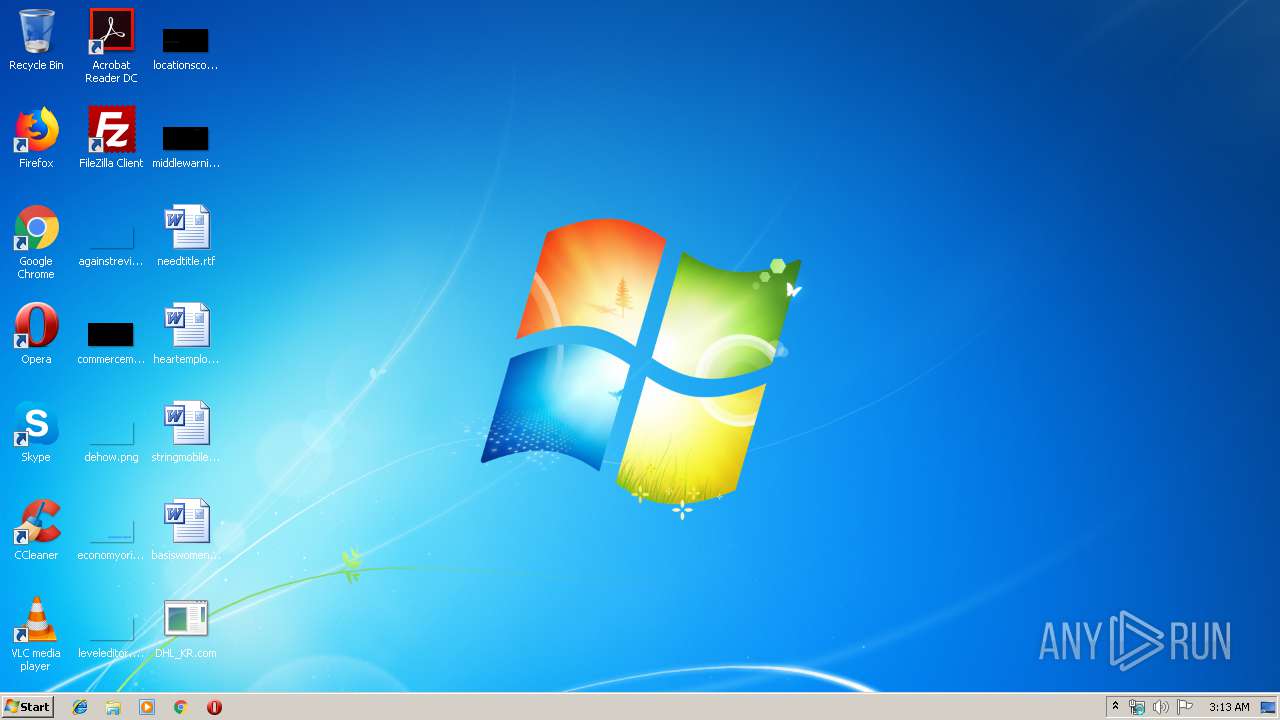
Manual execution by user
- DHL_KR.com (PID: 4012)
- cmd.exe (PID: 2628)
Creates files in the user directory
- Firefox.exe (PID: 3968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:08:18 13:05:29 |
| ZipCRC: | 0x23af1632 |
| ZipCompressedSize: | 239652 |
| ZipUncompressedSize: | 438272 |
| ZipFileName: | DHL_KR/DHL_KR.com |
Total processes
47
Monitored processes
13
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2544 | "C:\Program Files\G-zc\mfcr6q.exe" | C:\Program Files\G-zc\mfcr6q.exe | — | explorer.exe | |||||||||||
User: admin Company: paNDORATV Integrity Level: MEDIUM Exit code: 0 Version: 4.02.0001 Modules
| |||||||||||||||
| 2628 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
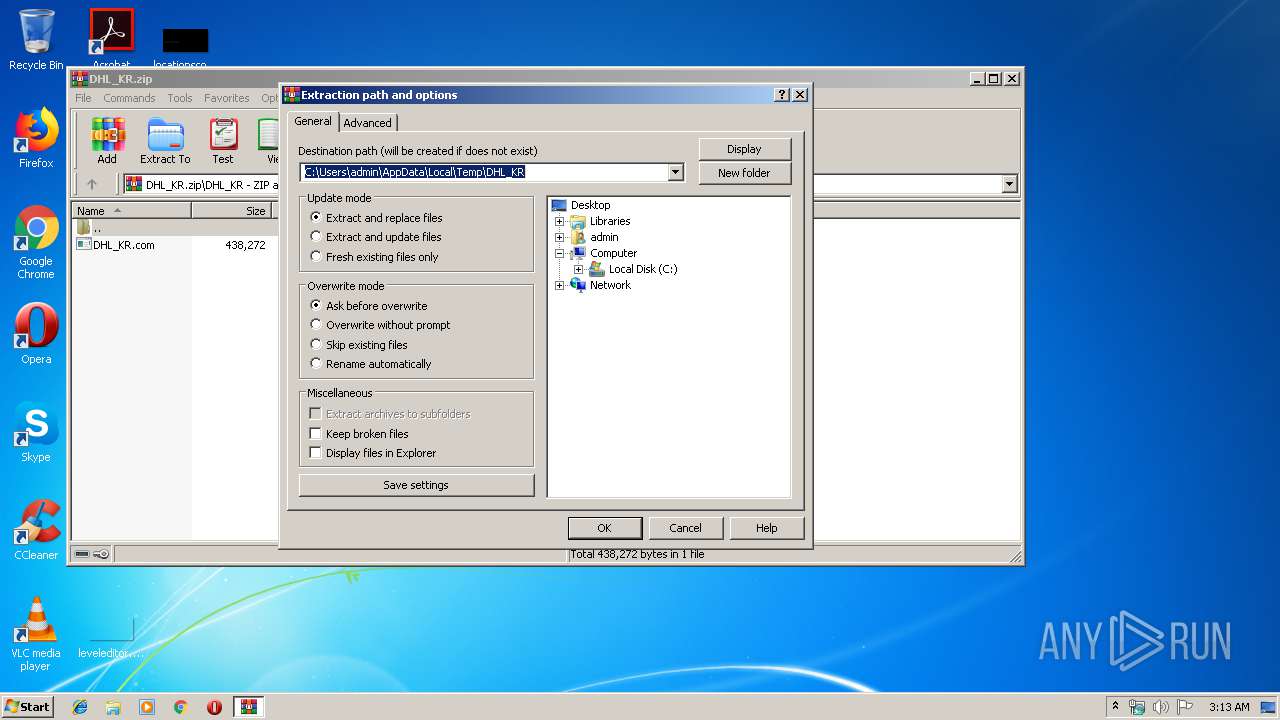
| 2860 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\DHL_KR.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\Desktop\DHL_KR.com" | C:\Users\admin\Desktop\DHL_KR.com | — | DHL_KR.com | |||||||||||
User: admin Company: paNDORATV Integrity Level: MEDIUM Exit code: 0 Version: 4.02.0001 Modules
| |||||||||||||||
| 3216 | "C:\Program Files\G-zc\mfcr6q.exe" | C:\Program Files\G-zc\mfcr6q.exe | — | mfcr6q.exe | |||||||||||
User: admin Company: paNDORATV Integrity Level: MEDIUM Exit code: 0 Version: 4.02.0001 Modules
| |||||||||||||||
| 3276 | /c del "C:\Users\admin\Desktop\DHL_KR.com" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3364 | "C:\Windows\System32\wuauclt.exe" | C:\Windows\System32\wuauclt.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3948 | "C:\Users\admin\Desktop\DHL_KR.com" | C:\Users\admin\Desktop\DHL_KR.com | — | DHL_KR.com | |||||||||||
User: admin Company: paNDORATV Integrity Level: MEDIUM Exit code: 0 Version: 4.02.0001 Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | cmd.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
2 192
Read events
2 162
Write events
30
Delete events
0
Modification events
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DHL_KR.zip | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (276) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
3
Suspicious files
77
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2860 | WinRAR.exe | C:\Users\admin\Desktop\DHL_KR.com | executable | |
MD5:— | SHA256:— | |||
| 276 | explorer.exe | C:\Users\admin\AppData\Local\Temp\G-zc\mfcr6q.exe | executable | |
MD5:— | SHA256:— | |||
| 3112 | DHL_KR.com | C:\Users\admin\AppData\Local\Temp\~DFA11684055DB99B65.TMP | binary | |
MD5:— | SHA256:— | |||
| 4020 | DllHost.exe | C:\Program Files\G-zc\mfcr6q.exe | executable | |
MD5:— | SHA256:— | |||
| 3216 | mfcr6q.exe | C:\Users\admin\AppData\Local\Temp\~DFFD8ACD59997FE83F.TMP | binary | |
MD5:— | SHA256:— | |||
| 2544 | mfcr6q.exe | C:\Users\admin\AppData\Local\Temp\~DF74EA10D8E7FDF2D6.TMP | binary | |
MD5:— | SHA256:— | |||
| 2628 | cmd.exe | C:\Users\admin\AppData\Roaming\7051N28E\705logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 4012 | DHL_KR.com | C:\Users\admin\AppData\Local\Temp\~DFE8E960FFD6E1A9DB.TMP | binary | |
MD5:— | SHA256:— | |||
| 2628 | cmd.exe | C:\Users\admin\AppData\Roaming\7051N28E\705logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 3968 | Firefox.exe | C:\Users\admin\AppData\Roaming\7051N28E\705logrf.ini | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
29
DNS requests
27
Threats
46
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
276 | explorer.exe | GET | — | 104.27.191.13:80 | http://www.pemasarankampoengkurma.com/tt/?w2=5V1MTDzGrEje9A+rurpnqzuoJnugdZjzH0dvo5aFwJnuCpriO1dqdkrTC5vfNMlpzvGKDQ==&s0H=uHlP7BMX | US | — | — | malicious |
276 | explorer.exe | GET | 404 | 47.91.239.71:80 | http://www.wzkns.com/tt/?w2=cf1diMNyh+lRTAYcqTUZMMARPCqzFwxwdvBXmJ7SNzr4Mo5OVi6hssxKU0fglv1auZnkDg==&s0H=uHlP7BMX | HK | html | 2.21 Kb | malicious |
276 | explorer.exe | GET | 404 | 65.254.248.135:80 | http://www.nyamadotbantu.com/tt/?w2=UC3G6cfmHSj3w0xWNTh72guQpoIs+C56Lx0arbCbtvpIVoFAj3Ul+3IomTB4sXgRf3FxHg==&s0H=uHlP7BMX&sql=1 | US | html | 863 b | malicious |
276 | explorer.exe | POST | — | 65.254.248.135:80 | http://www.nyamadotbantu.com/tt/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 65.254.248.135:80 | http://www.nyamadotbantu.com/tt/ | US | — | — | malicious |
276 | explorer.exe | POST | — | 65.254.248.135:80 | http://www.nyamadotbantu.com/tt/ | US | — | — | malicious |
276 | explorer.exe | GET | 404 | 198.54.112.26:80 | http://www.pursemtb.com/tt/?w2=WsRiLUilOF0e3/UDMPL6Kuy27Gh9En8nOqStYRE7TkPPp6FFhj2eWCfSTbf+qV/yotNhpw==&s0H=uHlP7BMX | US | html | 326 b | malicious |
276 | explorer.exe | POST | 404 | 198.54.112.26:80 | http://www.pursemtb.com/tt/ | US | html | 292 b | malicious |
276 | explorer.exe | POST | — | 104.27.191.13:80 | http://www.pemasarankampoengkurma.com/tt/ | US | — | — | malicious |
276 | explorer.exe | POST | 404 | 198.54.112.26:80 | http://www.pursemtb.com/tt/ | US | html | 292 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
276 | explorer.exe | 47.91.239.71:80 | www.wzkns.com | Alibaba (China) Technology Co., Ltd. | HK | malicious |
276 | explorer.exe | 65.254.248.135:80 | www.nyamadotbantu.com | The Endurance International Group, Inc. | US | malicious |
276 | explorer.exe | 198.54.112.26:80 | www.pursemtb.com | Namecheap, Inc. | US | malicious |
276 | explorer.exe | 104.27.191.13:80 | www.pemasarankampoengkurma.com | Cloudflare Inc | US | shared |
276 | explorer.exe | 47.96.113.13:80 | www.wash.ltd | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
276 | explorer.exe | 52.58.78.16:80 | www.bluflo.com | Amazon.com, Inc. | DE | whitelisted |
276 | explorer.exe | 192.0.78.25:80 | www.browndogtrading.com | Automattic, Inc | US | malicious |
— | — | 192.0.78.25:80 | www.browndogtrading.com | Automattic, Inc | US | malicious |
276 | explorer.exe | 50.63.202.43:80 | www.conbrio.life | GoDaddy.com, LLC | US | malicious |
— | — | 50.63.202.43:80 | www.conbrio.life | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.wzkns.com |
| malicious |
www.nyamadotbantu.com |
| malicious |
www.healthywealthyandtravelwise.com |
| unknown |
www.pursemtb.com |
| malicious |
www.ultrastore.site |
| unknown |
www.pemasarankampoengkurma.com |
| malicious |
www.wash.ltd |
| malicious |
www.bluflo.com |
| malicious |
www.wwwjinsha247.com |
| unknown |
www.xn--boq6uq1s7l3a5u0abwl.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
276 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
20 ETPRO signatures available at the full report