| File name: | bomb.exe |
| Full analysis: | https://app.any.run/tasks/43391bba-c010-40e7-a8f4-6b0bc77d4141 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 19, 2025, 04:25:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 0E2AD53C884E25F969B3A575F4BB90BB |
| SHA1: | 81E774FE109DDC9185AD3FB68995A069CE9045E0 |
| SHA256: | 990D1FF1AB883A9BACBBB6ABCF975139D9AB359B74FFBA16F1FA7A66A30E935D |
| SSDEEP: | 192:OJa0tZMoQszhl4AKd+QHzdPbwPz1OLU87glpp/bI6J4YlTtoIw:OLJQjd+qzZ0OLU870NJDoI |
MALICIOUS
HAUSBOMBER has been detected (YARA)
- bomb.exe (PID: 4980)
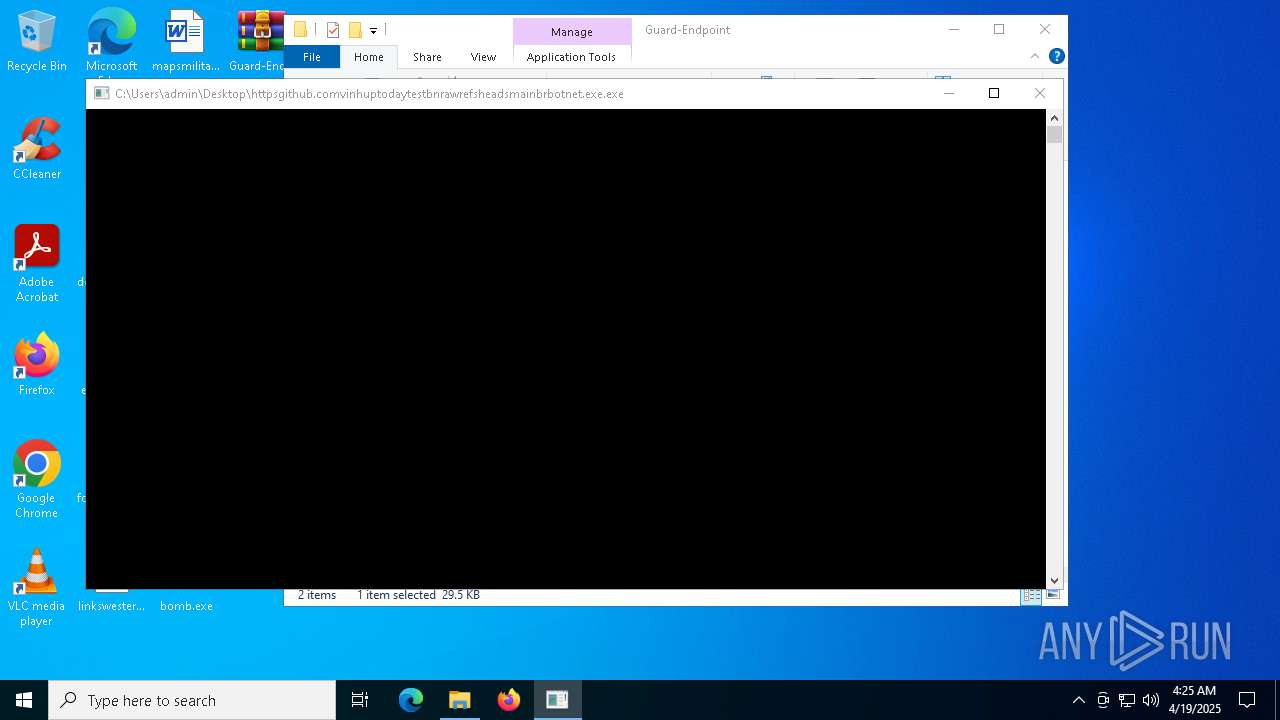
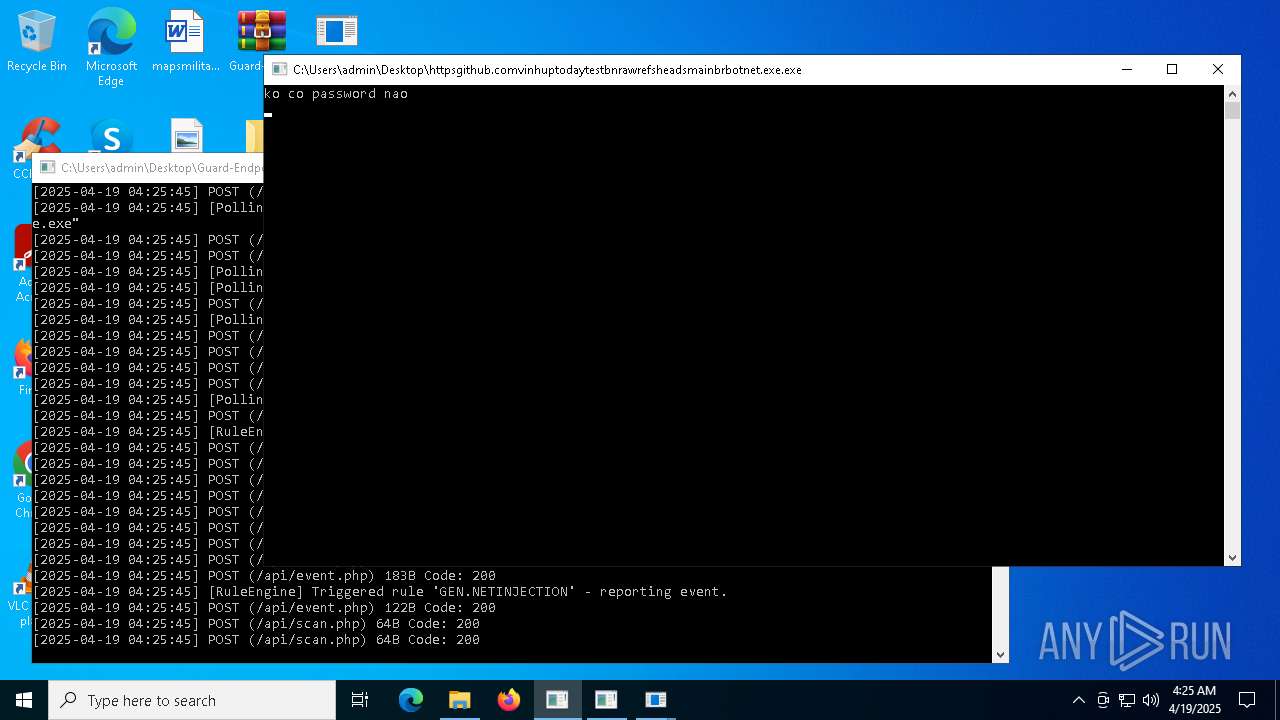
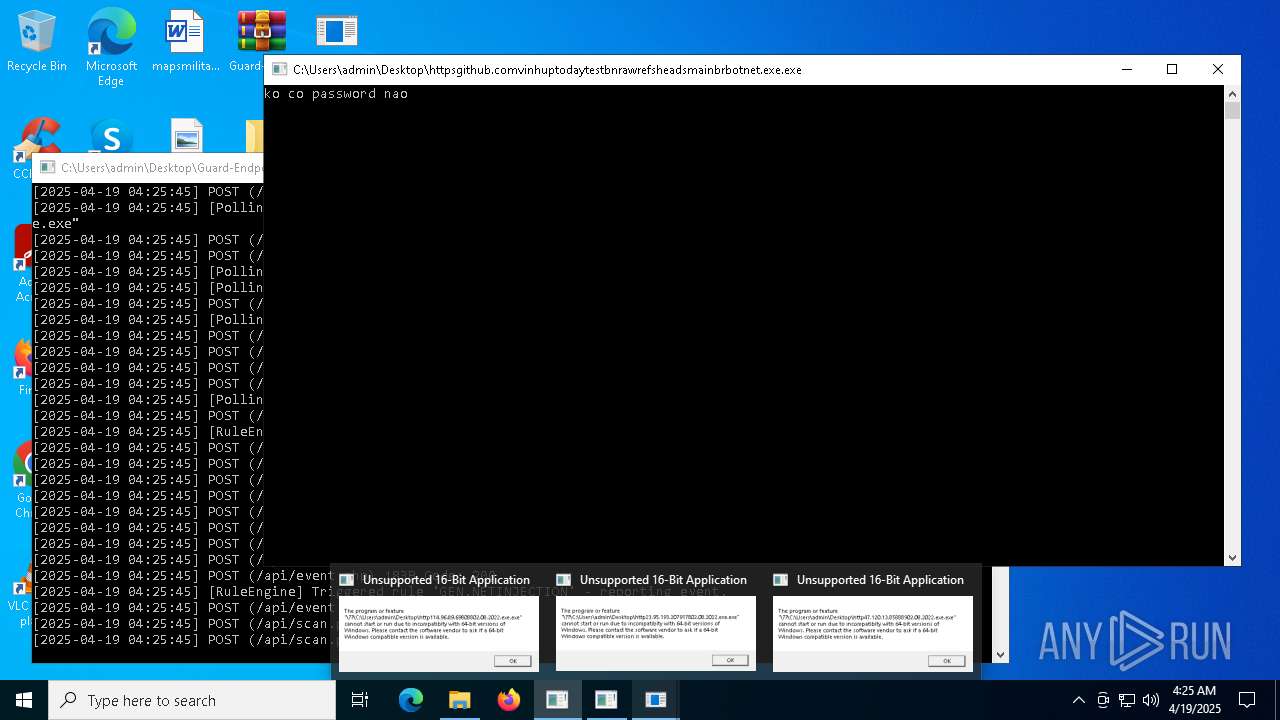
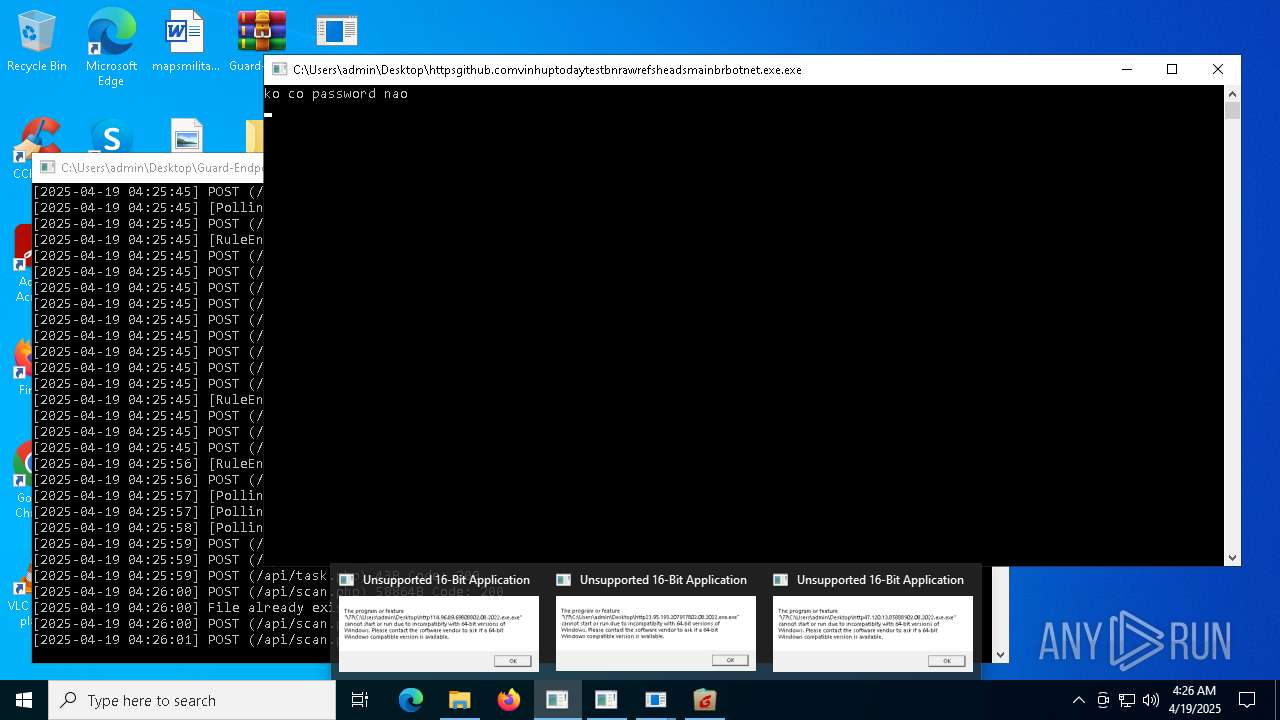
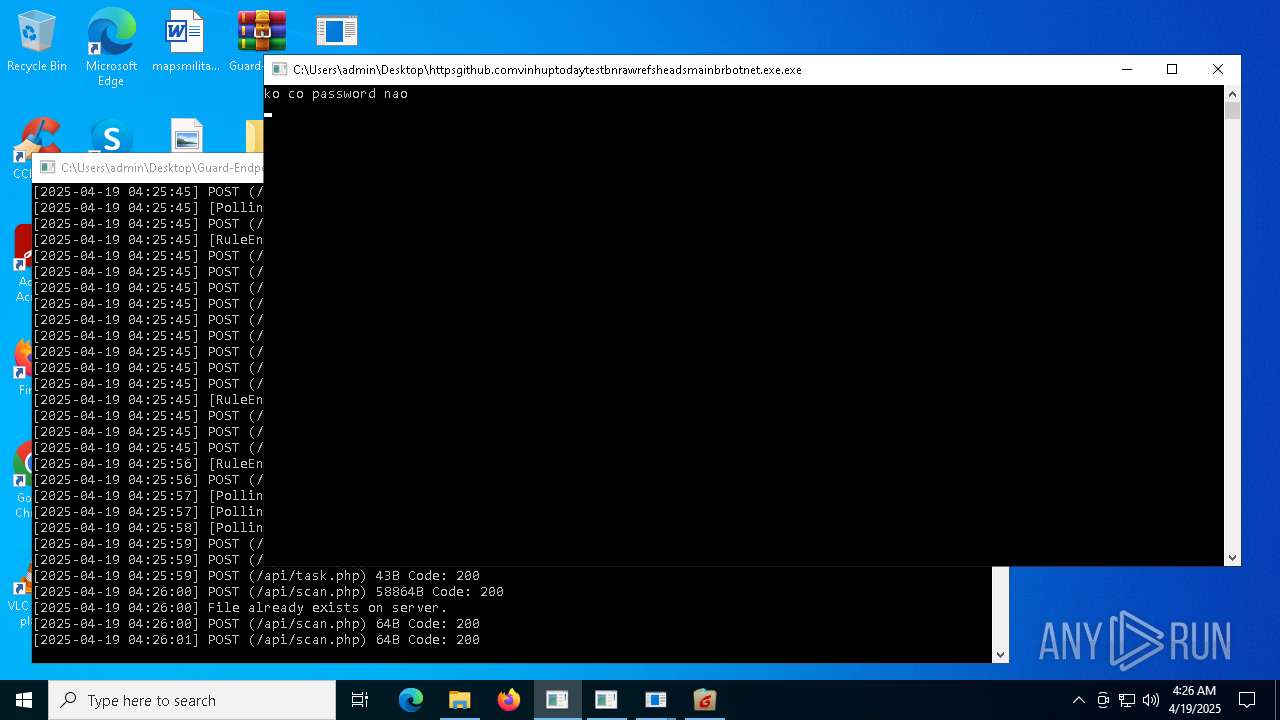
Executing a file with an untrusted certificate
- httpsgithub.comvinhuptodaytestbnrawrefsheadsmainbrbotnet.exe.exe (PID: 1660)
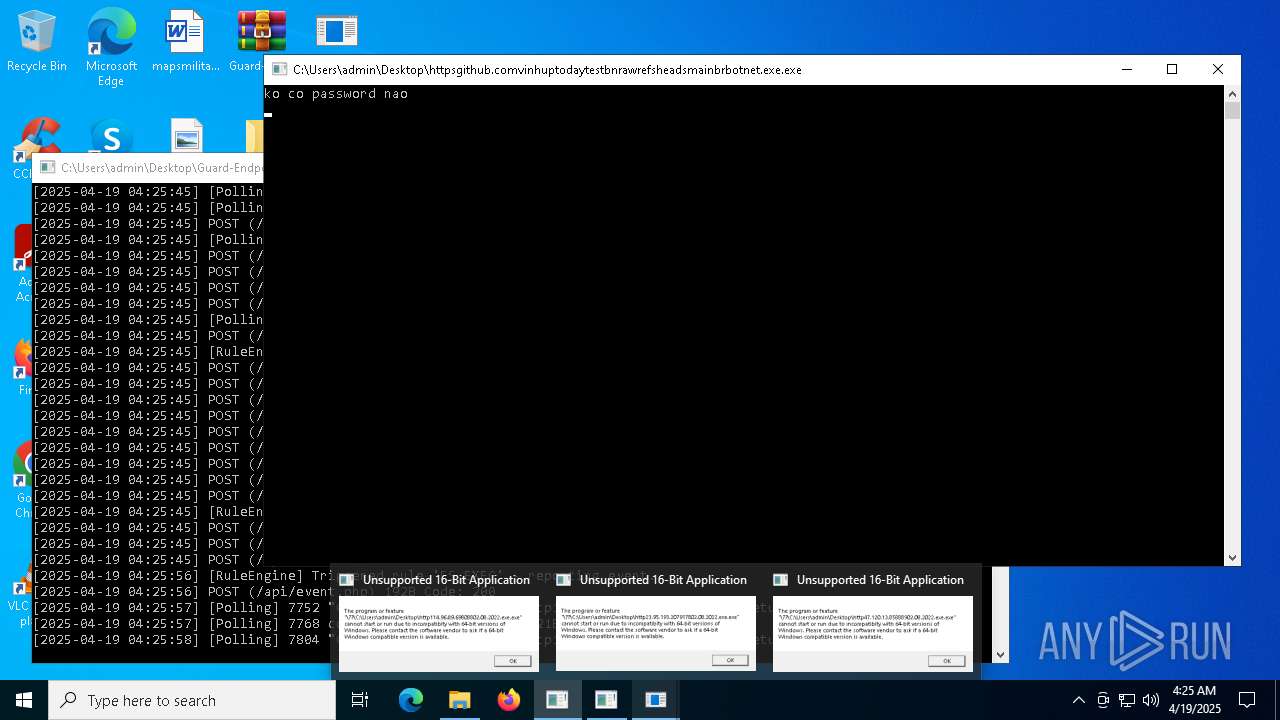
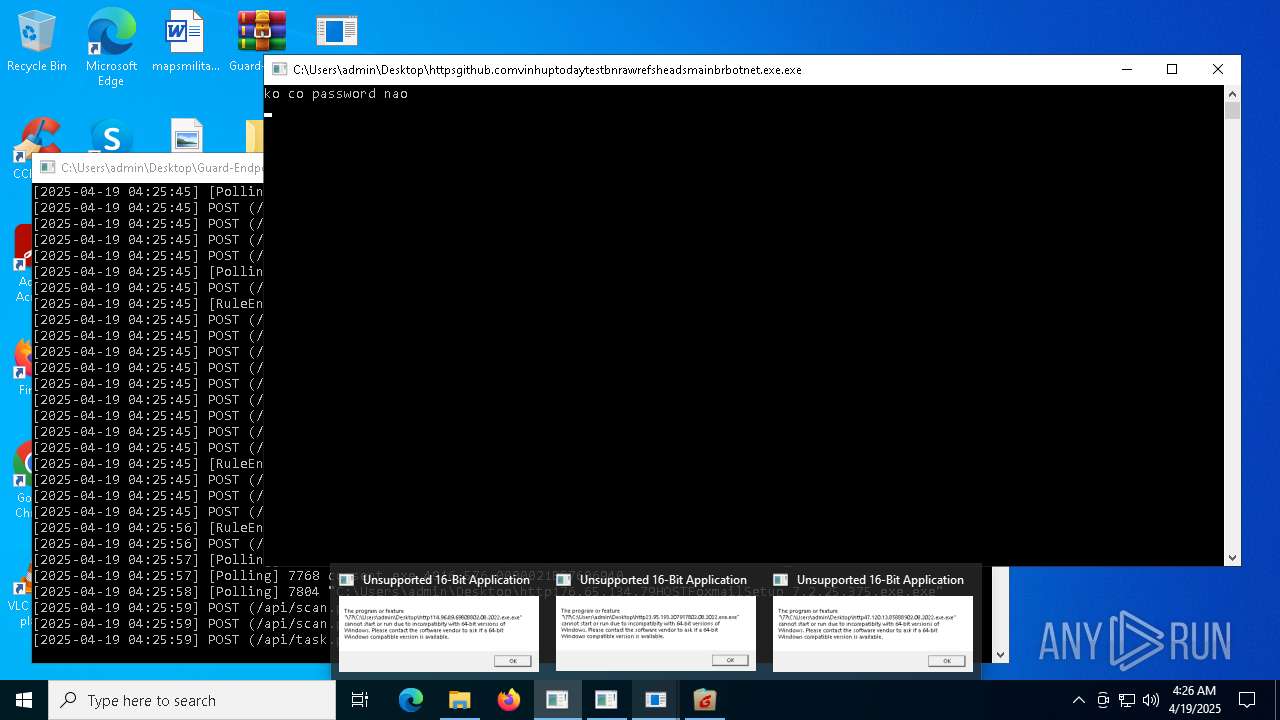
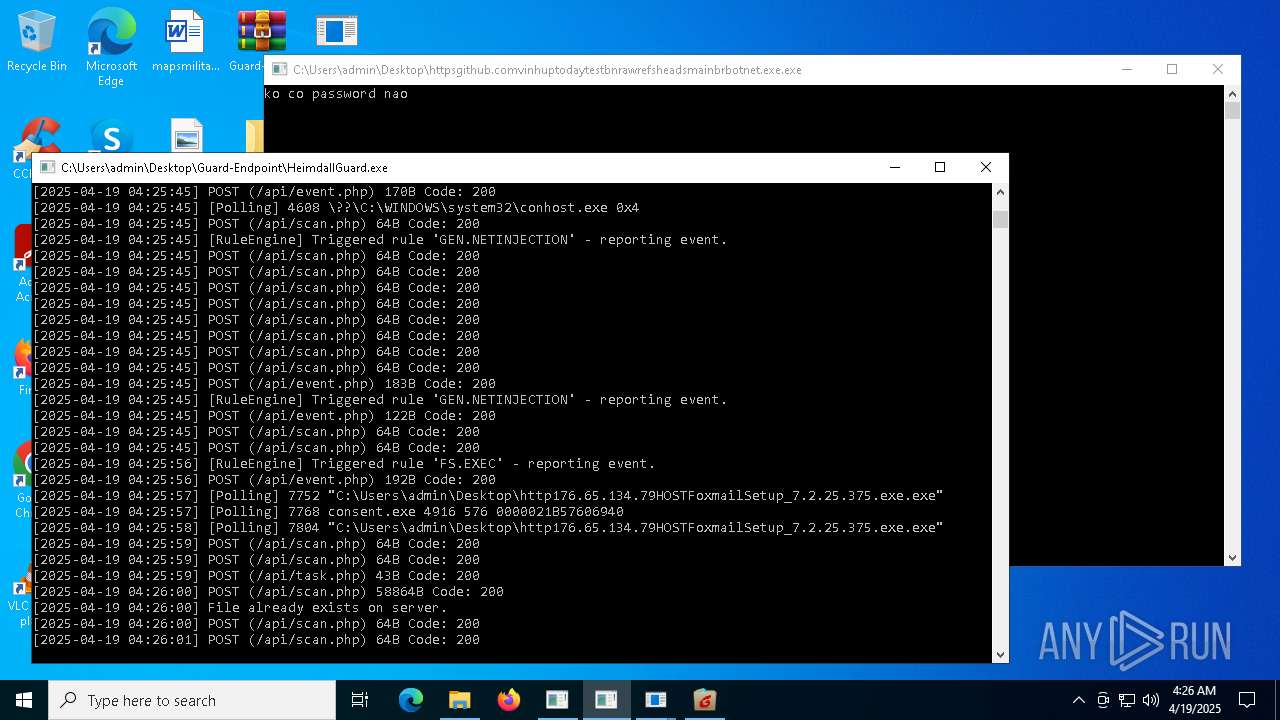
- http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe (PID: 7752)
- http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe (PID: 7804)
METERPRETER has been detected (SURICATA)
- bomb.exe (PID: 4980)
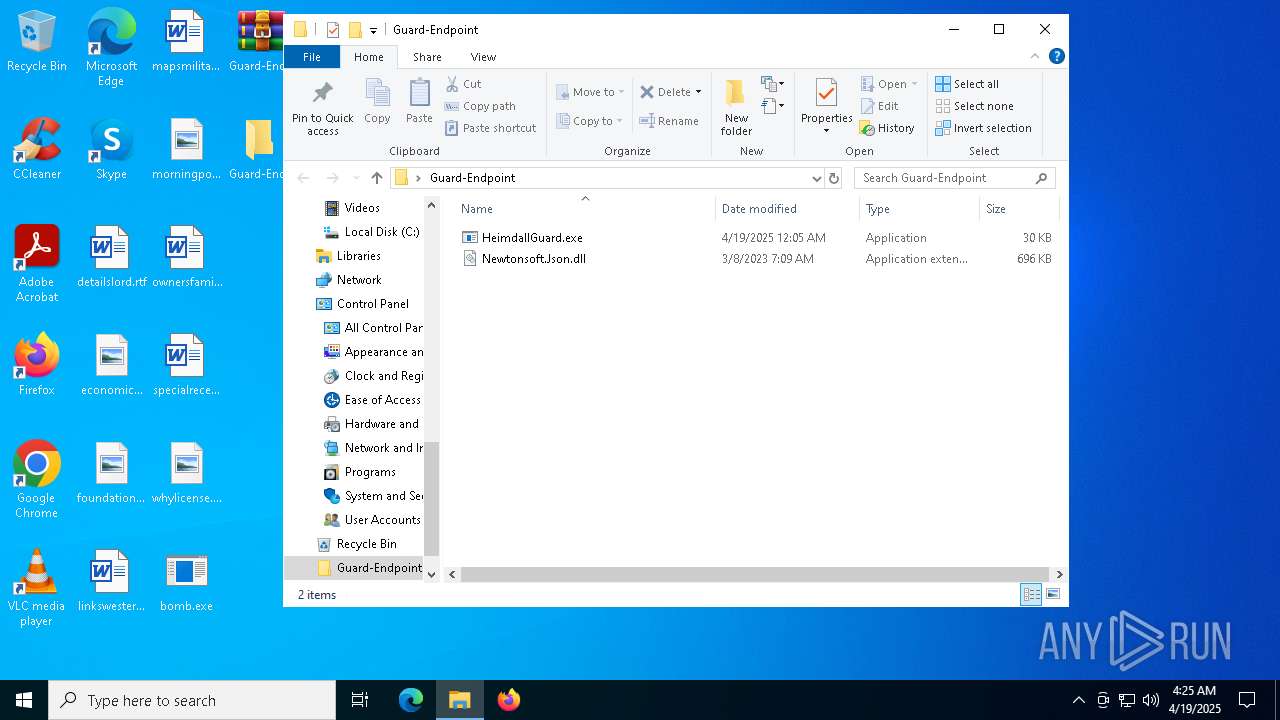
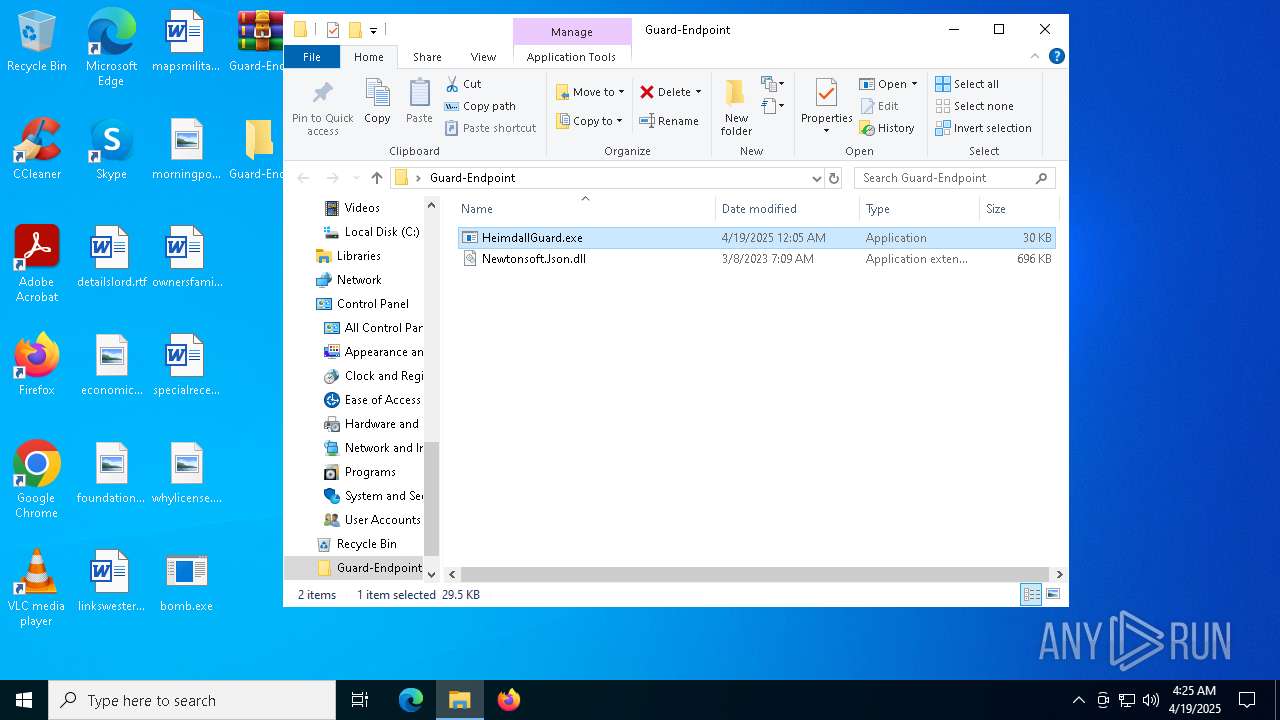
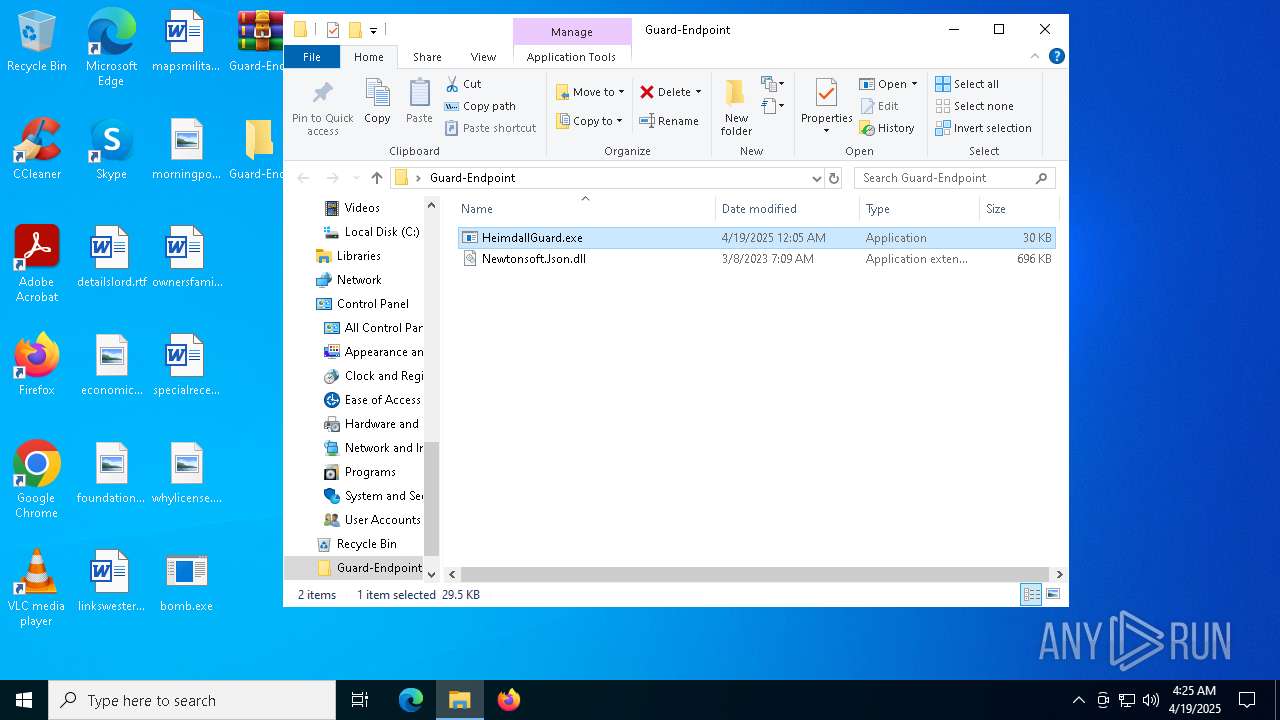
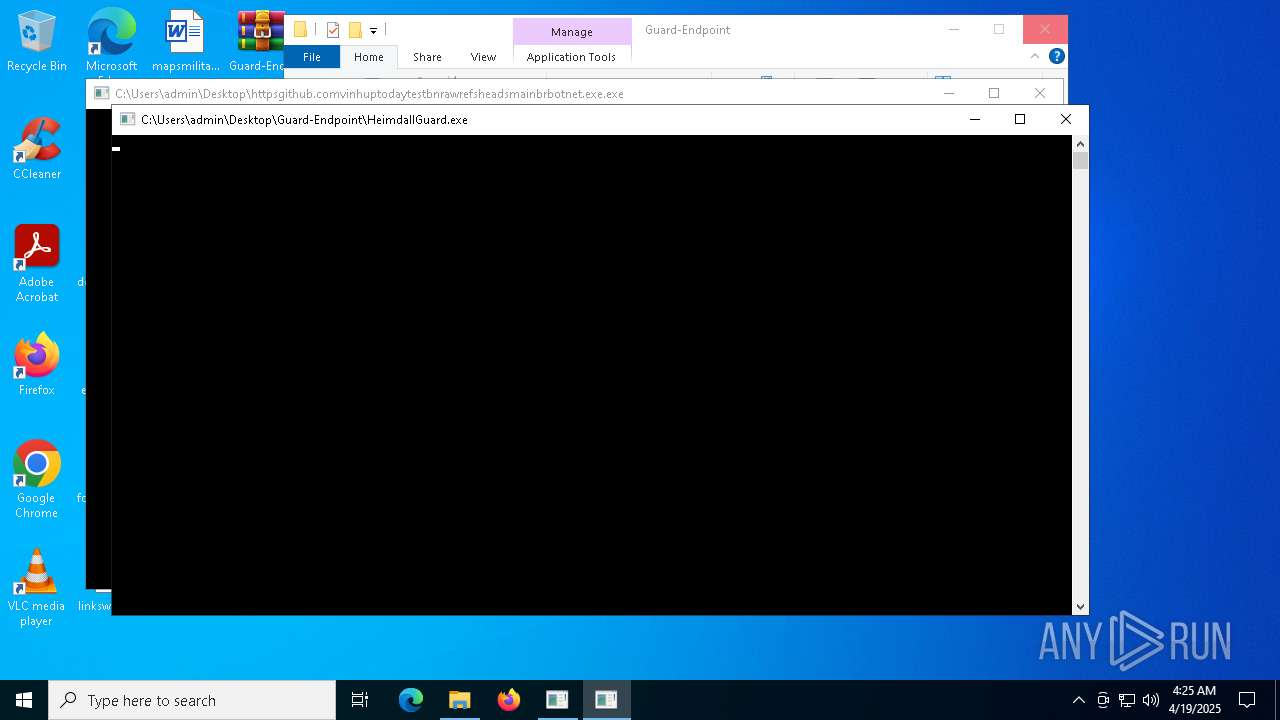
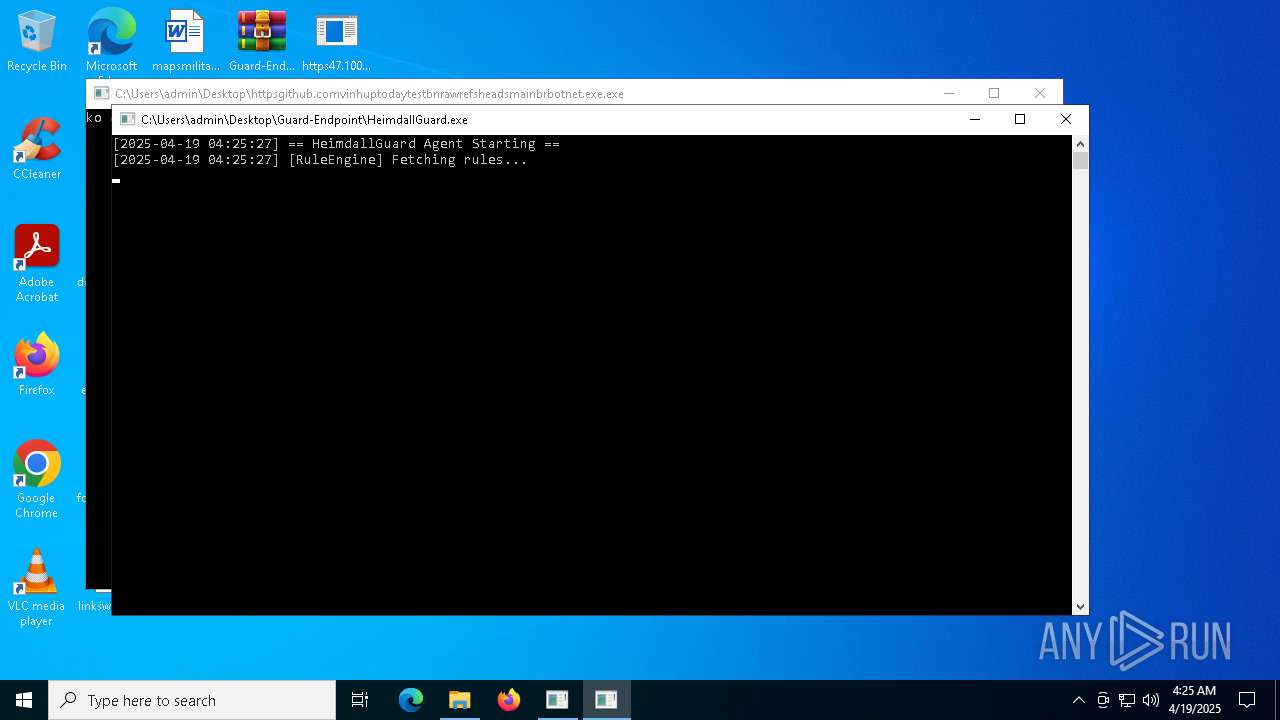
Changes the autorun value in the registry
- HeimdallGuard.exe (PID: 5736)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 616)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 616)
AGENTTESLA has been detected (SURICATA)
- RegAsm.exe (PID: 616)
SUSPICIOUS
Potential Corporate Privacy Violation
- bomb.exe (PID: 4980)
Reads the date of Windows installation
- bomb.exe (PID: 4980)
Executable content was dropped or overwritten
- bomb.exe (PID: 4980)
- http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe (PID: 7804)
Connects to the server without a host name
- bomb.exe (PID: 4980)
- http176.65.134.79HOSTCZXCVTD.exe.exe (PID: 6564)
Process requests binary or script from the Internet
- bomb.exe (PID: 4980)
Connects to unusual port
- bomb.exe (PID: 4980)
- RegAsm.exe (PID: 616)
Application launched itself
- HeimdallGuard.exe (PID: 5736)
Contacting a server suspected of hosting an CnC
- bomb.exe (PID: 4980)
Checks for external IP
- svchost.exe (PID: 2196)
- RegAsm.exe (PID: 616)
Reads security settings of Internet Explorer
- bomb.exe (PID: 4980)
Connects to FTP
- RegAsm.exe (PID: 616)
INFO
Reads the computer name
- bomb.exe (PID: 4980)
- httpsgithub.comvinhuptodaytestbnrawrefsheadsmainbrbotnet.exe.exe (PID: 1660)
- http176.65.134.79HOSTCZXCVTD.exe.exe (PID: 6564)
- HeimdallGuard.exe (PID: 5736)
- RegAsm.exe (PID: 616)
- http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe (PID: 7804)
- HeimdallGuard.exe (PID: 1096)
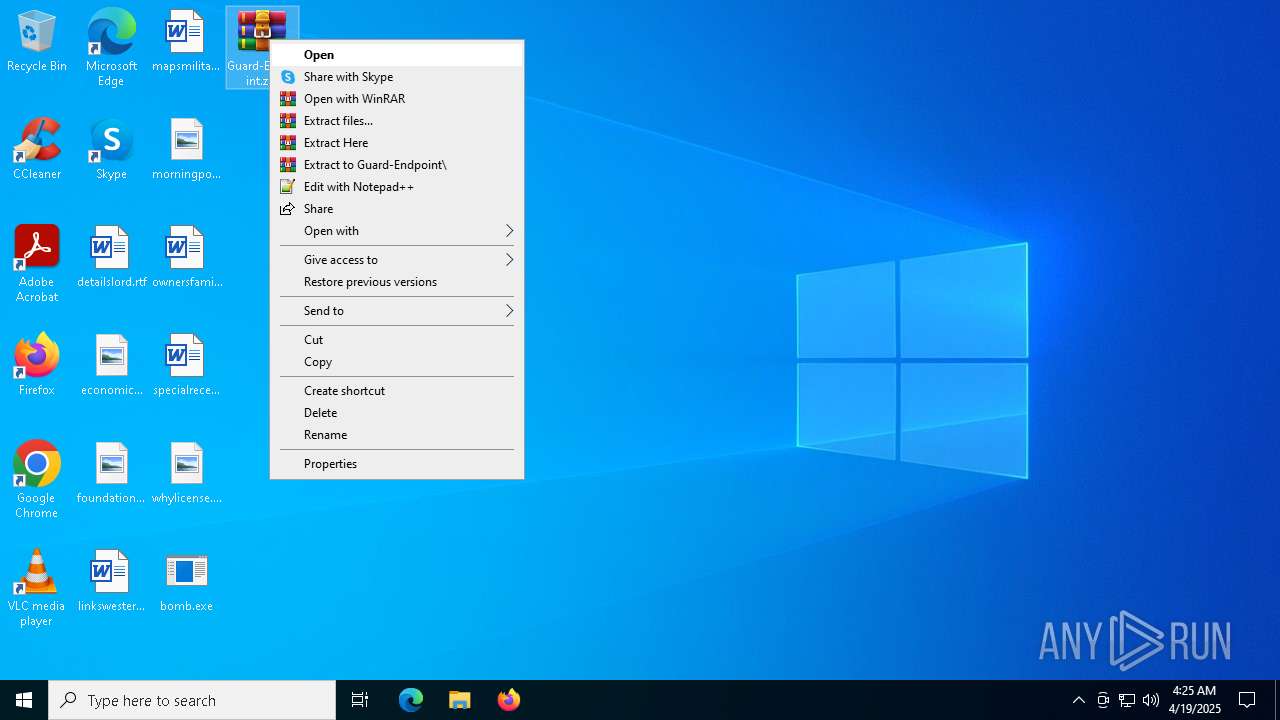
Manual execution by a user
- WinRAR.exe (PID: 5892)
- HeimdallGuard.exe (PID: 5736)
Disables trace logs
- bomb.exe (PID: 4980)
- http176.65.134.79HOSTCZXCVTD.exe.exe (PID: 6564)
- HeimdallGuard.exe (PID: 5736)
- RegAsm.exe (PID: 616)
Process checks computer location settings
- bomb.exe (PID: 4980)
Checks supported languages
- http176.65.134.79HOSTCZXCVTD.exe.exe (PID: 6564)
- httpsgithub.comvinhuptodaytestbnrawrefsheadsmainbrbotnet.exe.exe (PID: 1660)
- HeimdallGuard.exe (PID: 5736)
- RegAsm.exe (PID: 616)
- HeimdallGuard.exe (PID: 1096)
- bomb.exe (PID: 4980)
- http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe (PID: 7804)
Checks proxy server information
- bomb.exe (PID: 4980)
- http176.65.134.79HOSTCZXCVTD.exe.exe (PID: 6564)
- HeimdallGuard.exe (PID: 5736)
- RegAsm.exe (PID: 616)
Reads Environment values
- bomb.exe (PID: 4980)
Reads the software policy settings
- bomb.exe (PID: 4980)
- HeimdallGuard.exe (PID: 5736)
The sample compiled with chinese language support
- bomb.exe (PID: 4980)
- http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe (PID: 7804)
Reads the machine GUID from the registry
- http176.65.134.79HOSTCZXCVTD.exe.exe (PID: 6564)
- httpsgithub.comvinhuptodaytestbnrawrefsheadsmainbrbotnet.exe.exe (PID: 1660)
- HeimdallGuard.exe (PID: 5736)
- RegAsm.exe (PID: 616)
- bomb.exe (PID: 4980)
- HeimdallGuard.exe (PID: 1096)
Create files in a temporary directory
- httpsgithub.comvinhuptodaytestbnrawrefsheadsmainbrbotnet.exe.exe (PID: 1660)
- http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe (PID: 7804)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5892)
Creates files or folders in the user directory
- http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe (PID: 7804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2057:01:07 19:44:57+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 9216 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x43be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | bomb.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | bomb.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
145
Monitored processes
17
Malicious processes
4
Suspicious processes
3
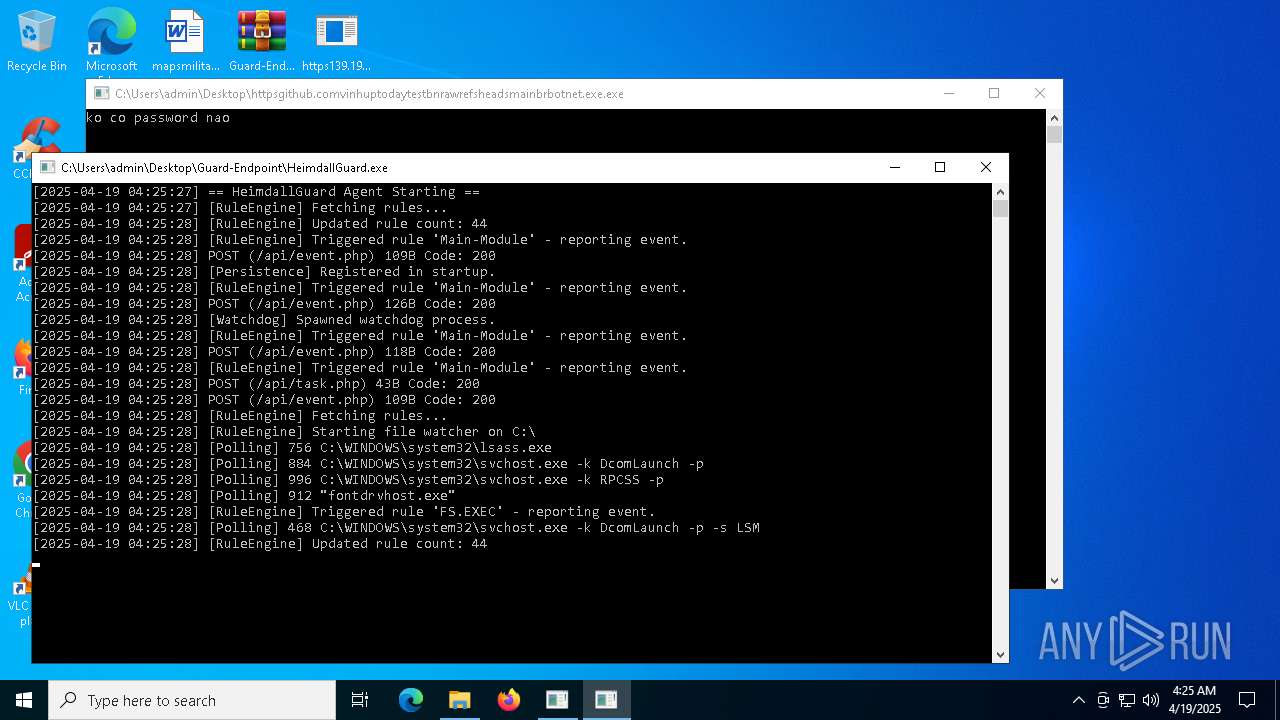
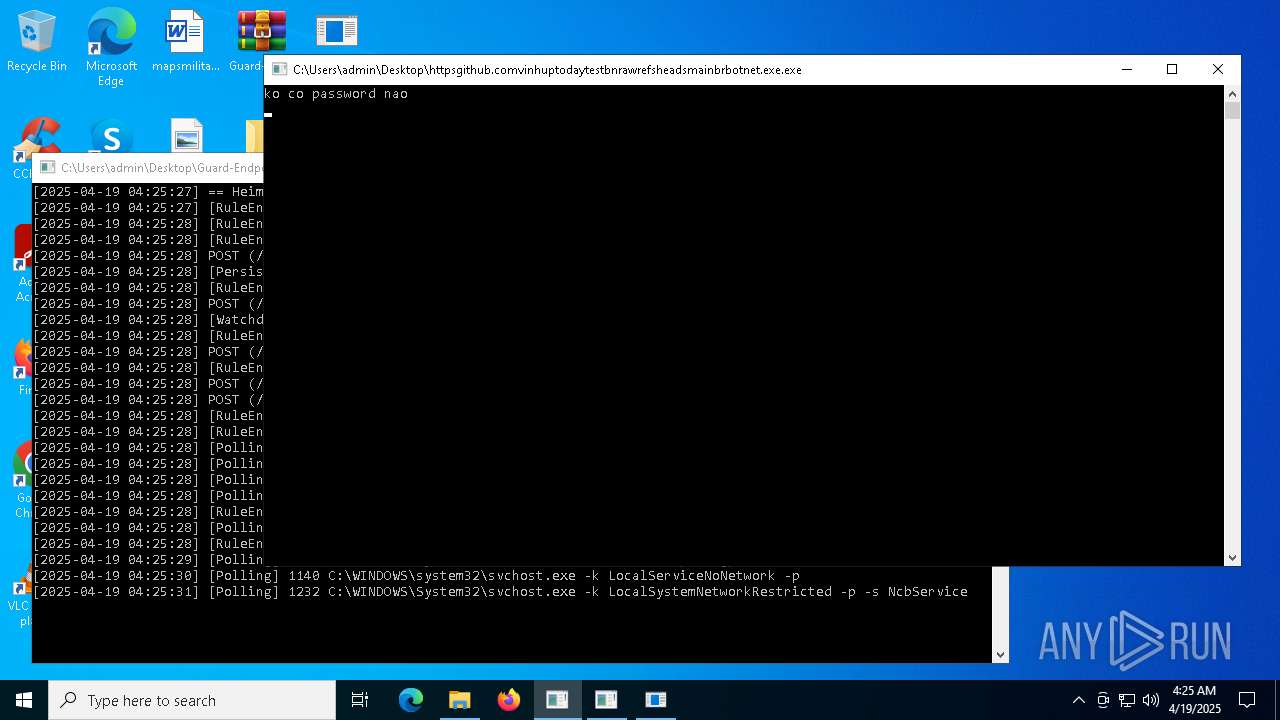
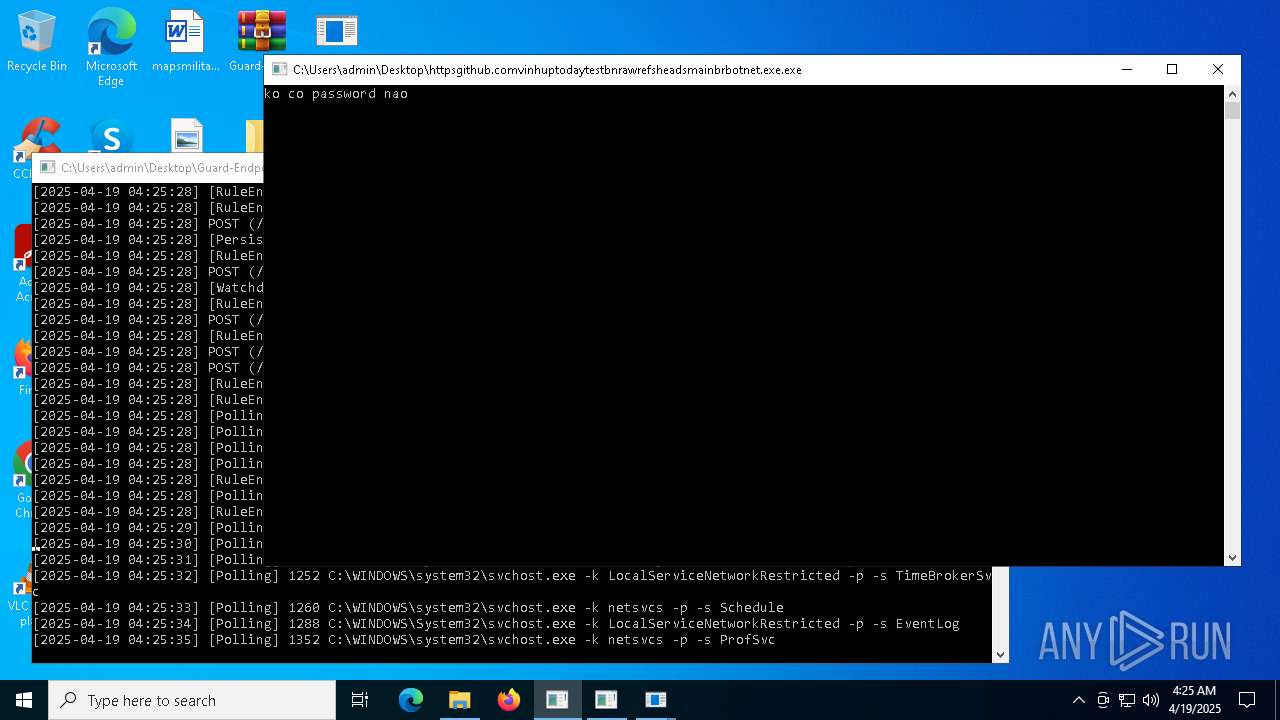
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | http176.65.134.79HOSTCZXCVTD.exe.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 1 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\Desktop\Guard-Endpoint\HeimdallGuard.exe" --watchdog | C:\Users\admin\Desktop\Guard-Endpoint\HeimdallGuard.exe | — | HeimdallGuard.exe | |||||||||||
User: admin Integrity Level: HIGH Description: HeimdallGuard Version: 1.0.0.0 Modules
| |||||||||||||||
| 1184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | HeimdallGuard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
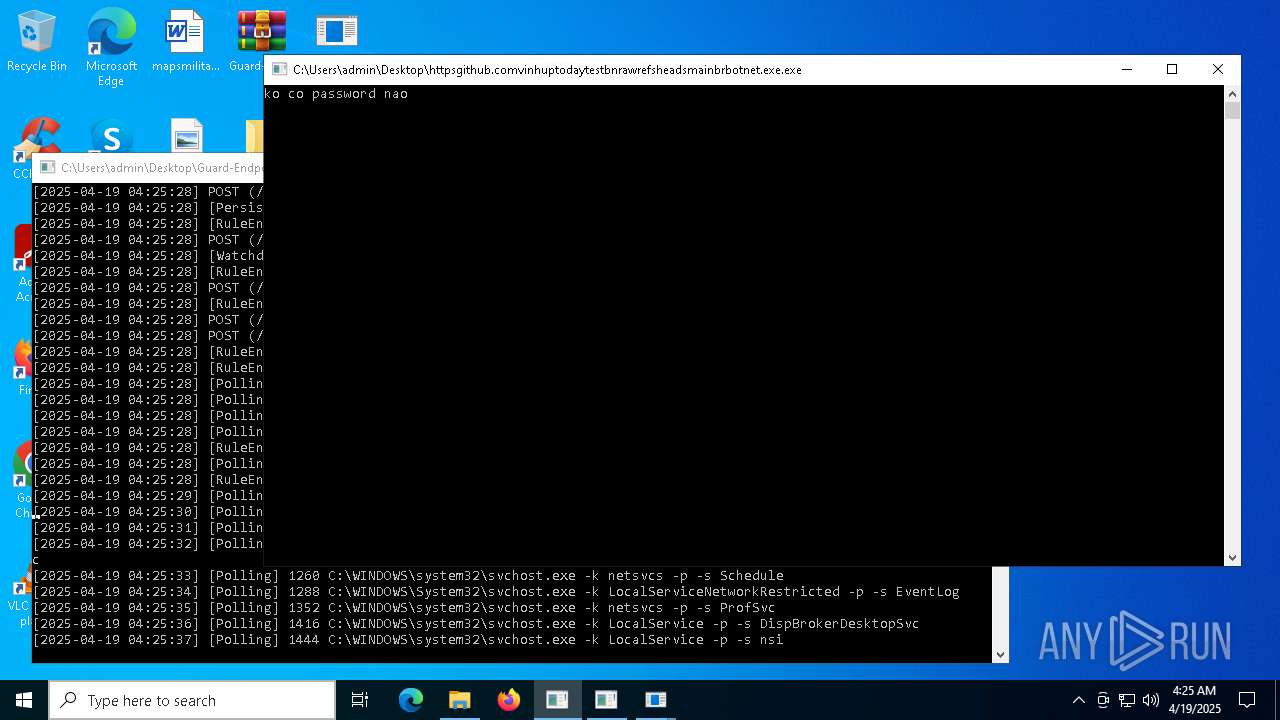
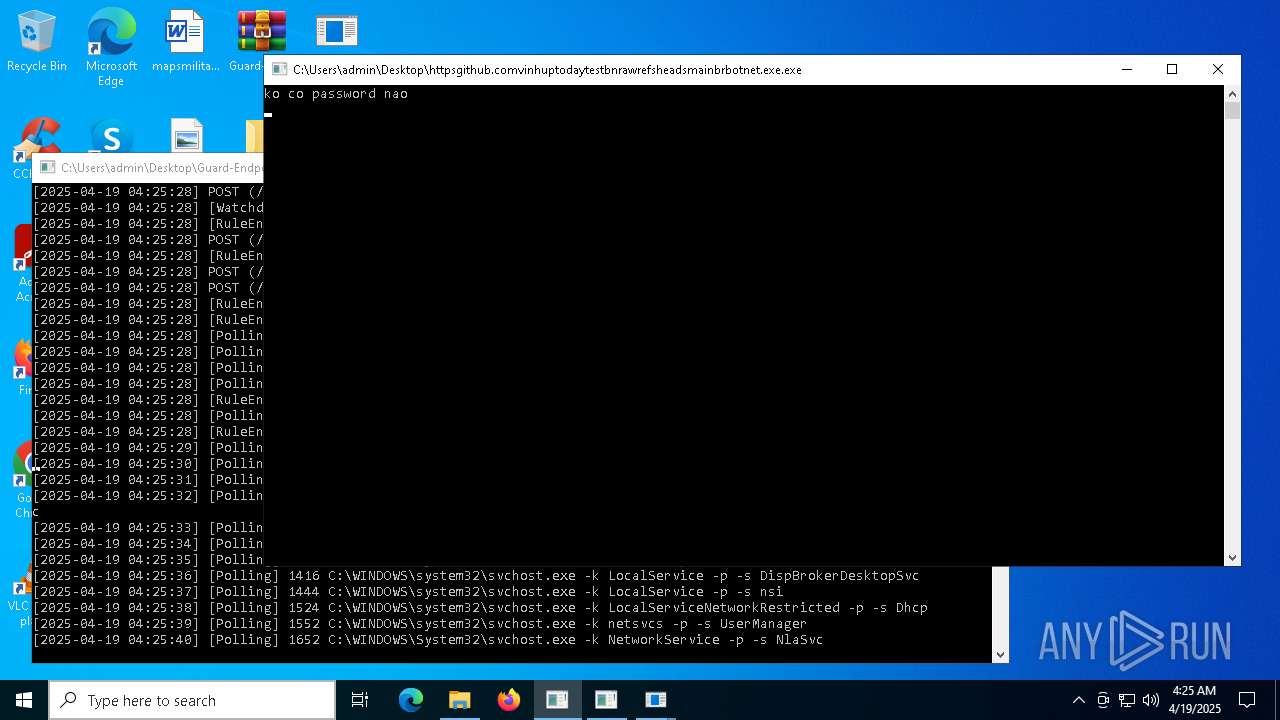
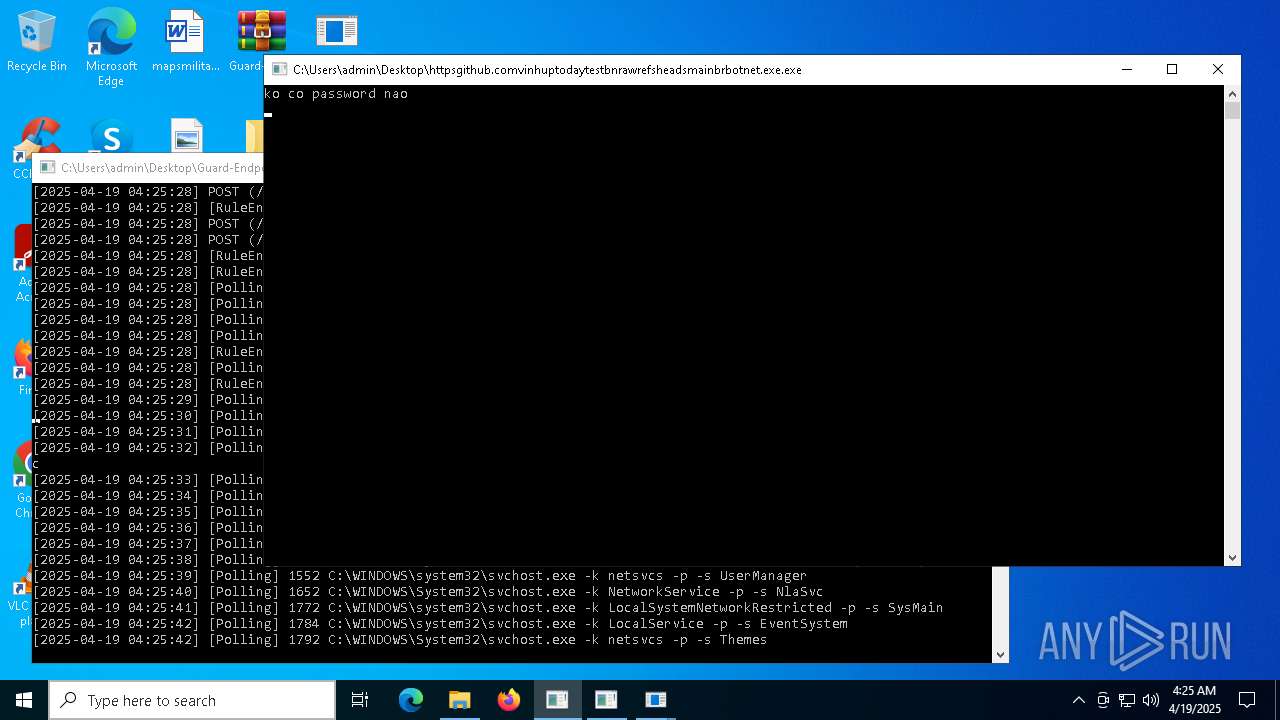
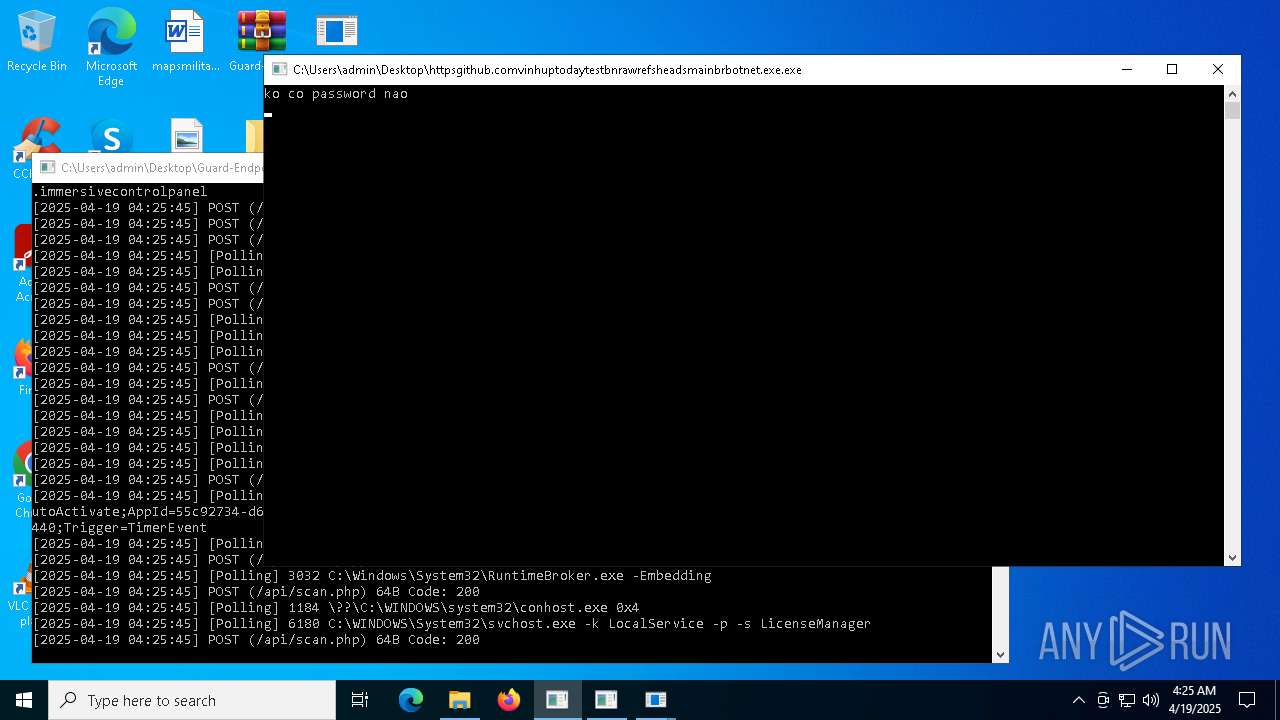
| 1660 | "C:\Users\admin\Desktop\httpsgithub.comvinhuptodaytestbnrawrefsheadsmainbrbotnet.exe.exe" | C:\Users\admin\Desktop\httpsgithub.comvinhuptodaytestbnrawrefsheadsmainbrbotnet.exe.exe | — | bomb.exe | |||||||||||
User: admin Company: i Integrity Level: MEDIUM Description: WindowsSharp Version: 1.09.9879.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | HeimdallGuard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4892 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | http176.65.134.79HOSTCZXCVTD.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4976 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | "C:\Users\admin\Desktop\bomb.exe" | C:\Users\admin\Desktop\bomb.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
10 870
Read events
10 809
Write events
61
Delete events
0
Modification events
| (PID) Process: | (5892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5892) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4980) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4980) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4980) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4980) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4980) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4980) bomb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\bomb_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
7
Suspicious files
1
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5736 | HeimdallGuard.exe | C:\Users\admin\Desktop\Guard-Endpoint\debug.log | text | |
MD5:7D4462A72F05588FA66734042FF5DAE2 | SHA256:9C9FCB986DD474ADBF55EEEEEADB127AC99991AD785CE23580352DCB00D96052 | |||
| 7804 | http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe | C:\Users\admin\AppData\Local\Temp\nsp7405.tmp\pic\empty_bg.png | image | |
MD5:580EC3E3BAD21F36E42245222301B665 | SHA256:BF977B73C5C3E2BF4B5CDA35806E7BE1DEE360BEDF01B6DCBB32EDAD9E8A6491 | |||
| 7804 | http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe | C:\Users\admin\AppData\Local\Temp\nsp7405.tmp\pic\checkbox.png | image | |
MD5:7C24A95DF573051C42420C5C5B3F3F8A | SHA256:52323F1C1F9855D097FDBE3089260162D27E4C6D250E1C68689579782B4D6596 | |||
| 7804 | http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe | C:\Users\admin\AppData\Local\Temp\nsp7405.tmp\pic\bg1.png | image | |
MD5:42A008DD2C74D9D5738C22169372C947 | SHA256:63DD2B43B14EEB9461F2682D542CD88D7DCEC065B07A6A7DA013D818BAE34FC7 | |||
| 7804 | http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe | C:\Users\admin\AppData\Local\Temp\nsp7405.tmp\FoxPlugin.dll | executable | |
MD5:3439CADFCDAC59C75D23876525966ECC | SHA256:C42126DF06DD51A8BDA6C4D36F0C3E03266852AD95EB33959AEADDD6A0D9507E | |||
| 1660 | httpsgithub.comvinhuptodaytestbnrawrefsheadsmainbrbotnet.exe.exe | C:\Users\admin\AppData\Local\Temp\brnettt_pYBgAmcYt7 | binary | |
MD5:29A644B1F0D96166A05602FE27B3F4AD | SHA256:BF96902FEB97E990A471492F78EE8386BCF430D66BDAEFDEAFBF912C8CF7CE46 | |||
| 7804 | http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe | C:\Users\admin\AppData\Local\Temp\nsp7405.tmp\pic\strongbtn.png | image | |
MD5:778740651ED84FA80761AB369A807537 | SHA256:888B93397451DC4B51F5D4D3A732C24E013113CE9FF624959D6AF213FF691D26 | |||
| 7804 | http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe | C:\Users\admin\AppData\Local\Temp\nsp7405.tmp\InstallHelper.dll | executable | |
MD5:DE122D16CBC5663A69C04E836B396F39 | SHA256:854F91C5463C1BAD6E87E90CC264D80FC77C40C32C24F1F16130627589FE177C | |||
| 7804 | http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe | C:\Users\admin\AppData\Local\Temp\nsp7405.tmp\pic\slogan.png | image | |
MD5:6DF4EAE215A8DF422C57DBFB29A4F1A0 | SHA256:EAF36E8460B7721DBFCEDE56FFC4171CD486926EDC97B37D923AF2A31BE84915 | |||
| 7804 | http176.65.134.79HOSTFoxmailSetup_7.2.25.375.exe.exe | C:\Users\admin\AppData\Local\Temp\nsp7405.tmp\pic\shadow_active.png | image | |
MD5:7BA99F4C2A4CE1B7DC6A1A553D7CF0FF | SHA256:925965AC5EE1E2382E0559A34610B35E9CAFB1341F2E38FFFA4270C50B869D3B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
186
DNS requests
21
Threats
92
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4980 | bomb.exe | GET | 200 | 176.65.134.79:80 | http://176.65.134.79/HOST/FoxmailSetup_7.2.25.375.exe | unknown | — | — | malicious |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
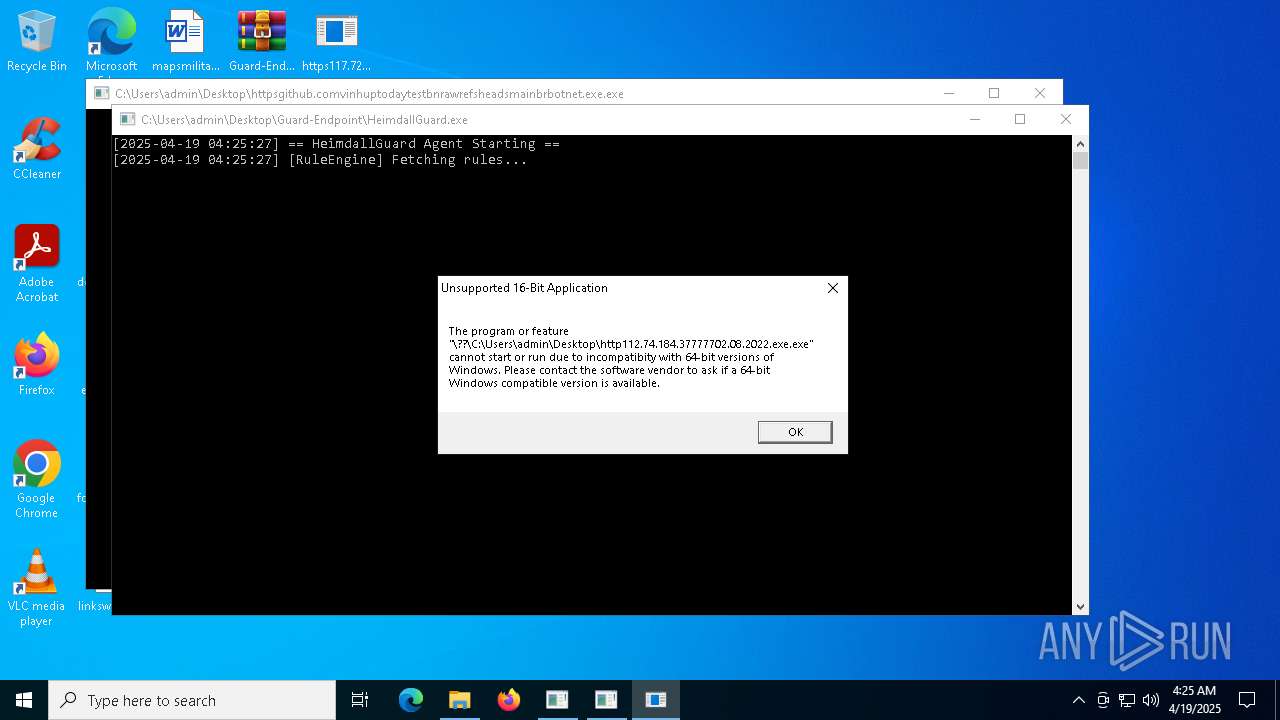
4980 | bomb.exe | GET | 200 | 112.74.184.37:7777 | http://112.74.184.37:7777/02.08.2022.exe | unknown | — | — | unknown |
6564 | http176.65.134.79HOSTCZXCVTD.exe.exe | GET | 200 | 176.65.134.79:80 | http://176.65.134.79/HOST/NEWDEVVV.txt | unknown | — | — | malicious |
4980 | bomb.exe | GET | 200 | 176.65.134.79:80 | http://176.65.134.79/HOST/CZXCVTD.exe | unknown | — | — | malicious |
4980 | bomb.exe | GET | 200 | 114.96.89.69:8088 | http://114.96.89.69:8088/02.08.2022.exe | unknown | — | — | unknown |
4980 | bomb.exe | GET | 200 | 23.95.193.207:9178 | http://23.95.193.207:9178/02.08.2022.exe | unknown | — | — | unknown |
616 | RegAsm.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4980 | bomb.exe | 188.114.97.3:443 | maper.info | CLOUDFLARENET | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
maper.info |
| malicious |
www.google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
github.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4980 | bomb.exe | Potential Corporate Privacy Violation | ET INFO IP Logger Redirect Domain in SNI |
4980 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
4980 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
4980 | bomb.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
4980 | bomb.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
4980 | bomb.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
4980 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
4980 | bomb.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
4980 | bomb.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |