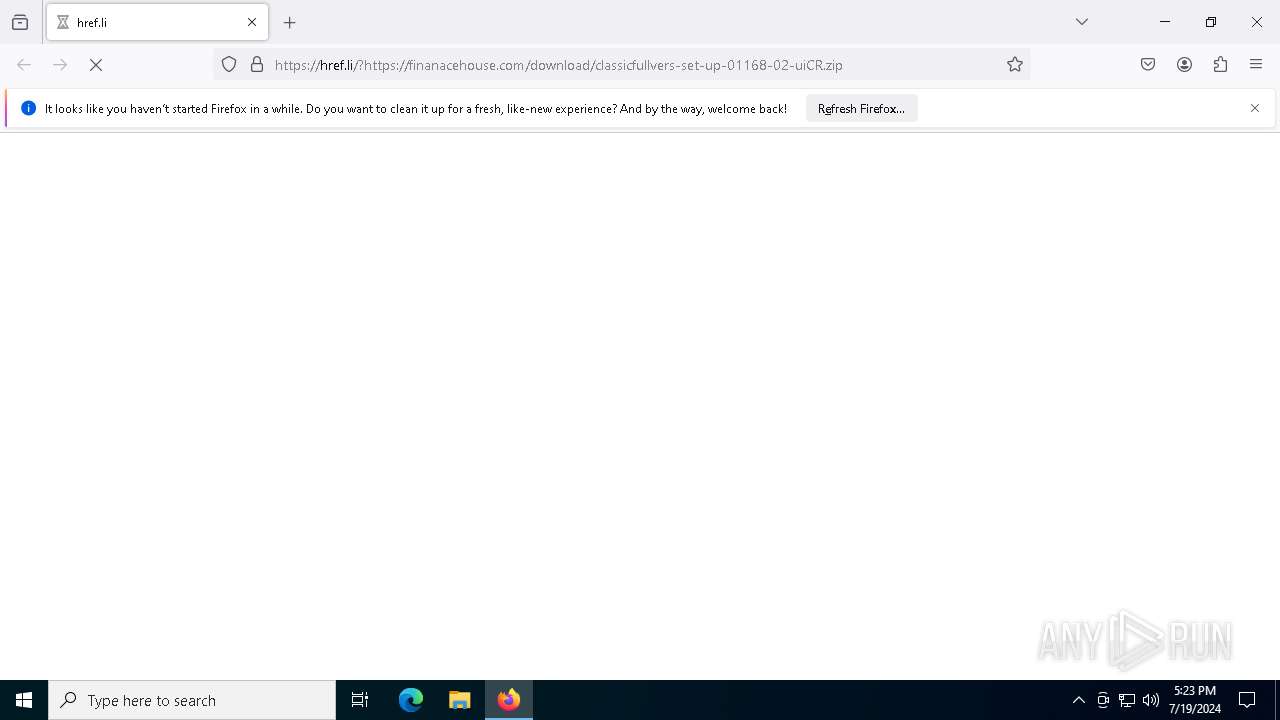
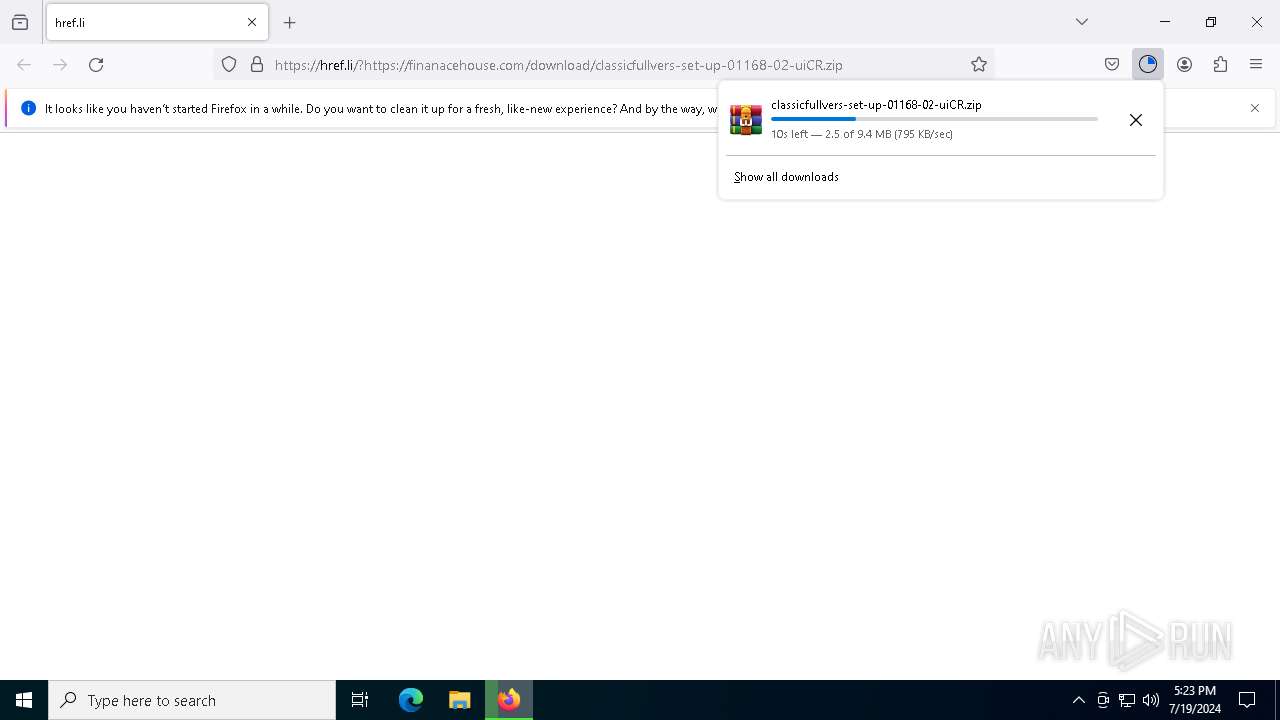
| URL: | https://href.li/?https://finanacehouse.com/download/classicfullvers-set-up-01168-02-uiCR.zip |
| Full analysis: | https://app.any.run/tasks/38271577-0df3-4e1e-9807-1d18c1446ef8 |
| Verdict: | Malicious activity |
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
| Analysis date: | July 19, 2024, 17:23:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 43D8781E53D8B111671D69397DD60434 |
| SHA1: | 504EF961CD0560C845B3922965CF278F85239C2E |
| SHA256: | 98C55F15FF903405152AAF0C4A7267BB61206D0597C7A5321AD95F5D13B5F5DE |
| SSDEEP: | 3:N8rmLJGysjZIKBKLbRMUQ2We9VXtMArMVn:2AJGP6BPRjQxo+r |
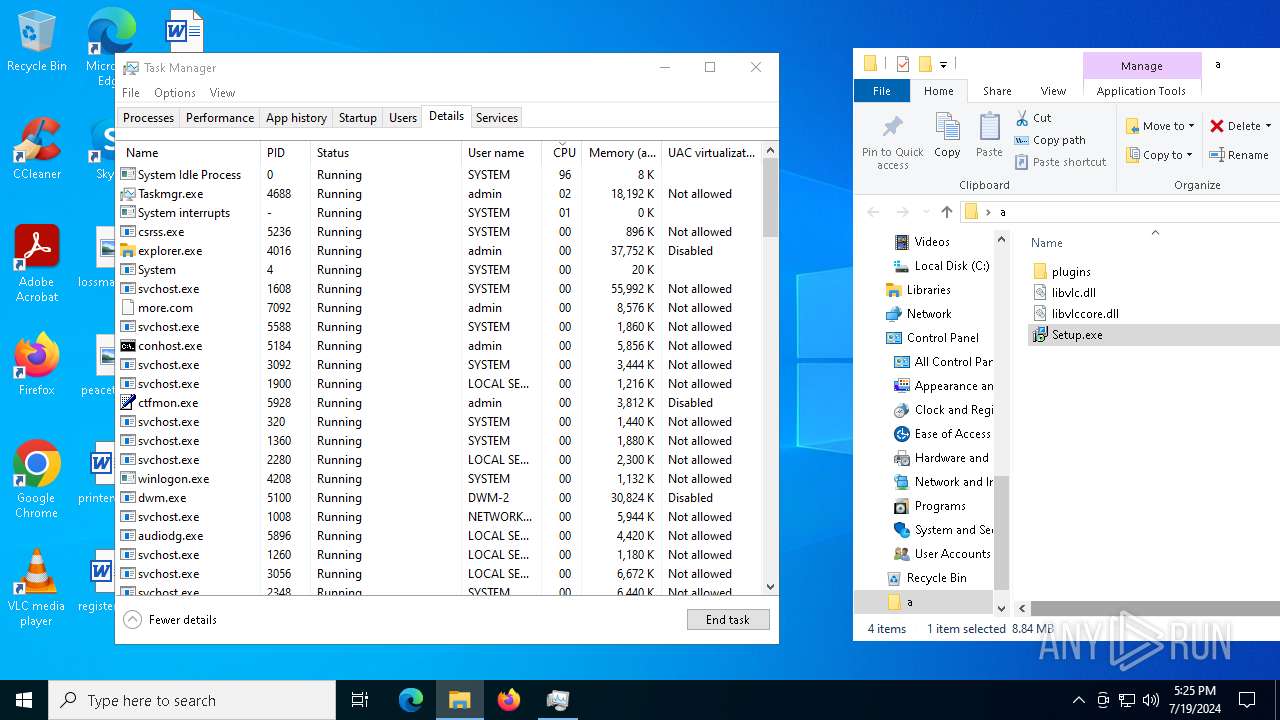
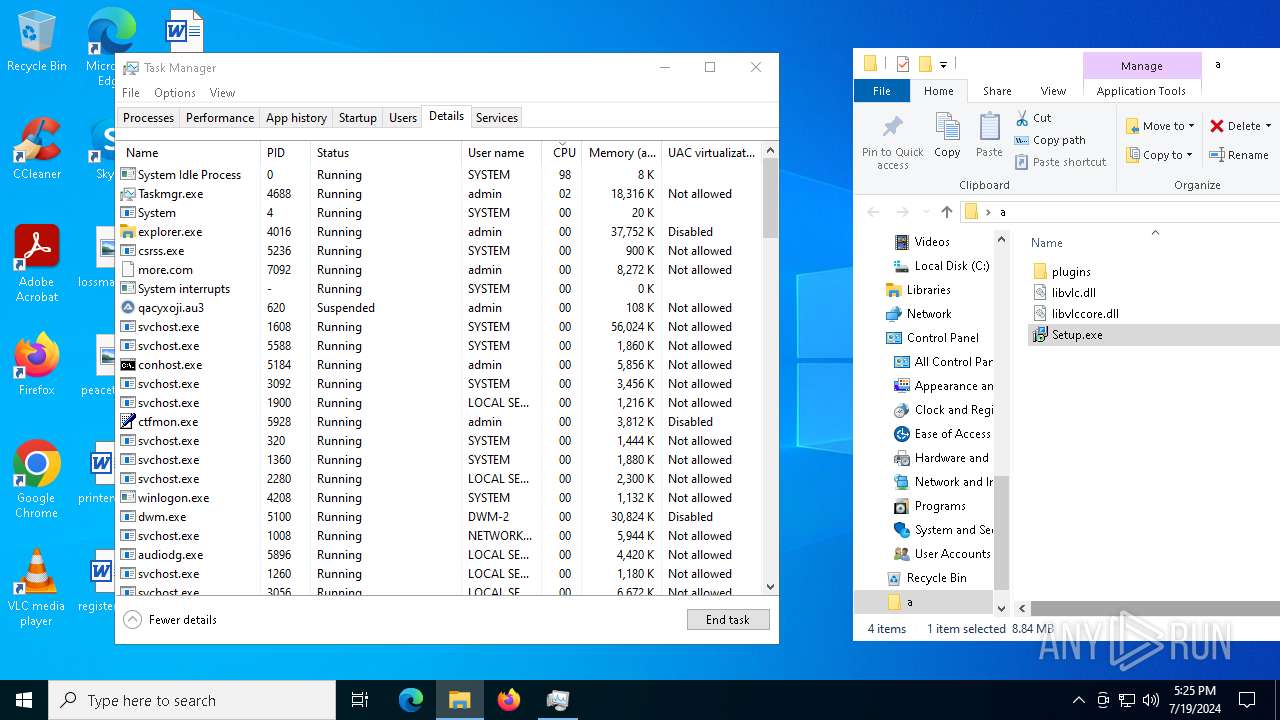
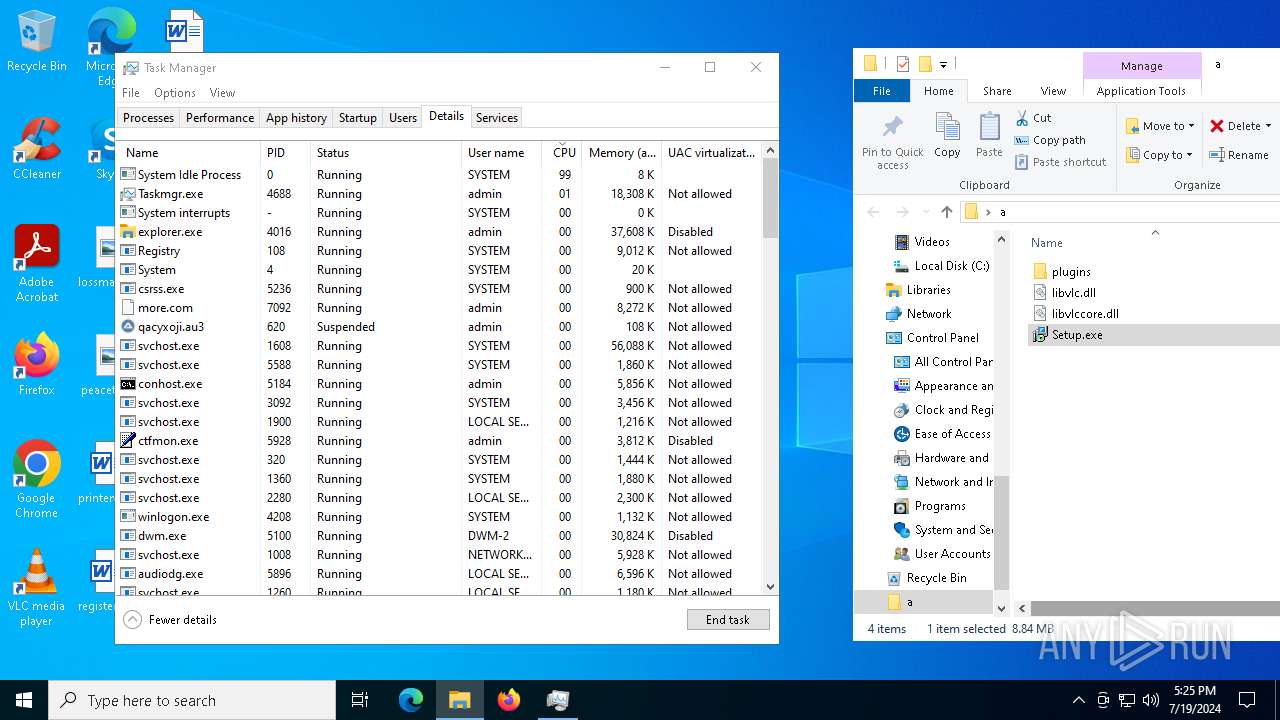
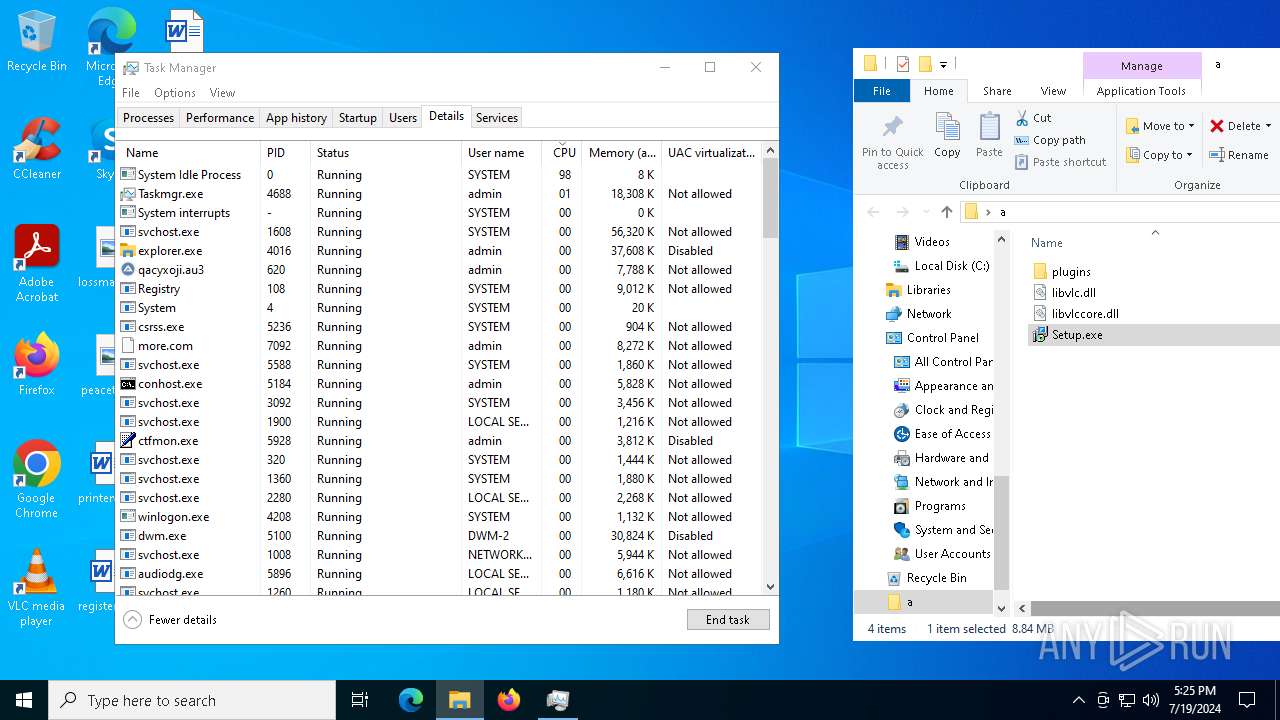
MALICIOUS
Stealers network behavior
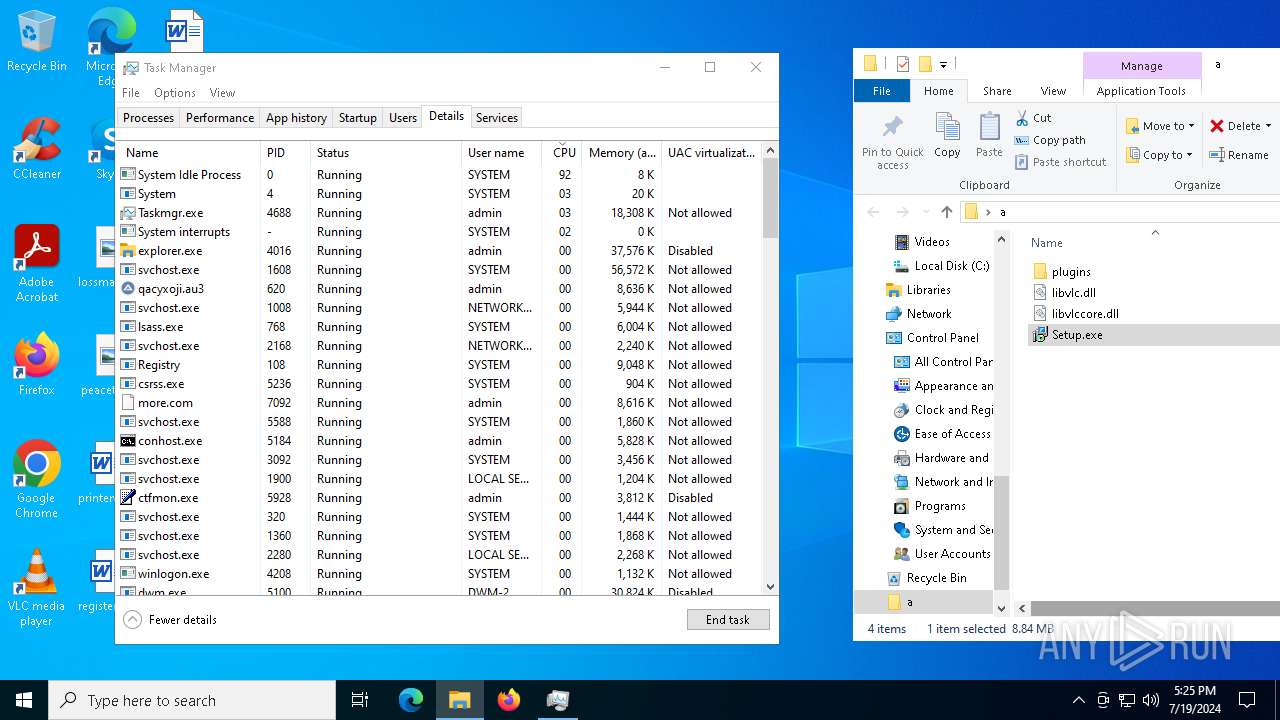
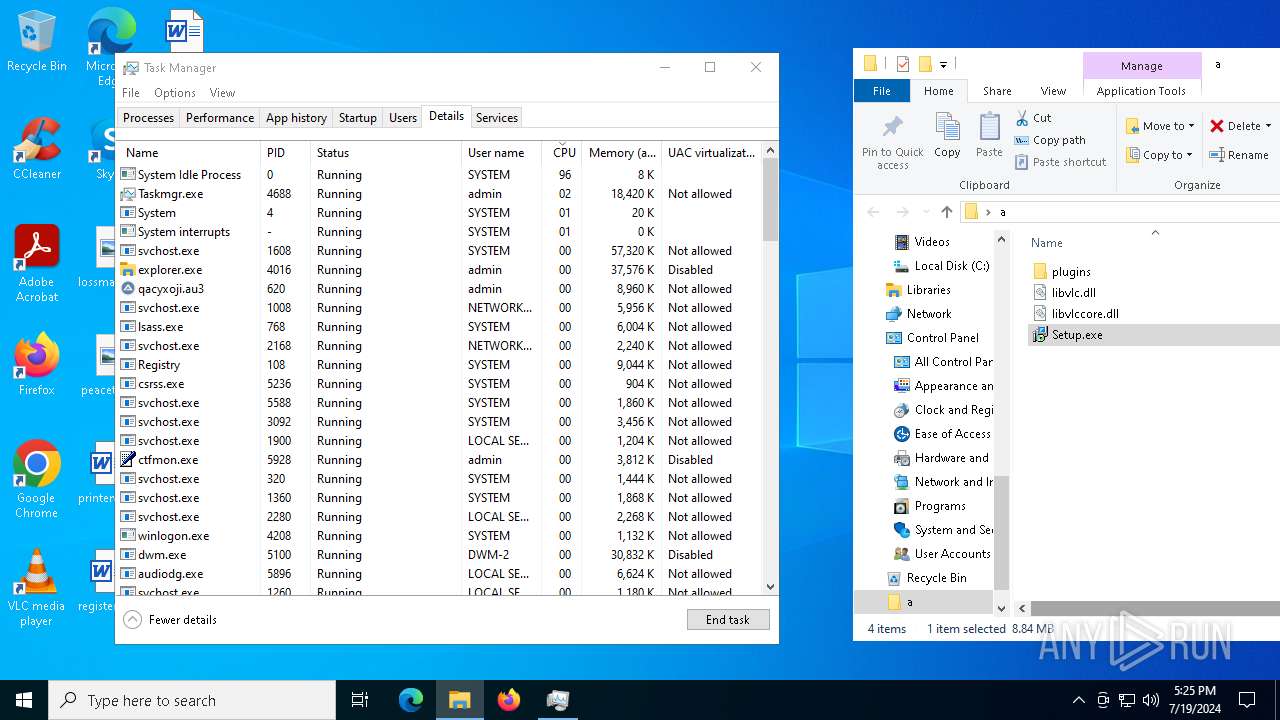
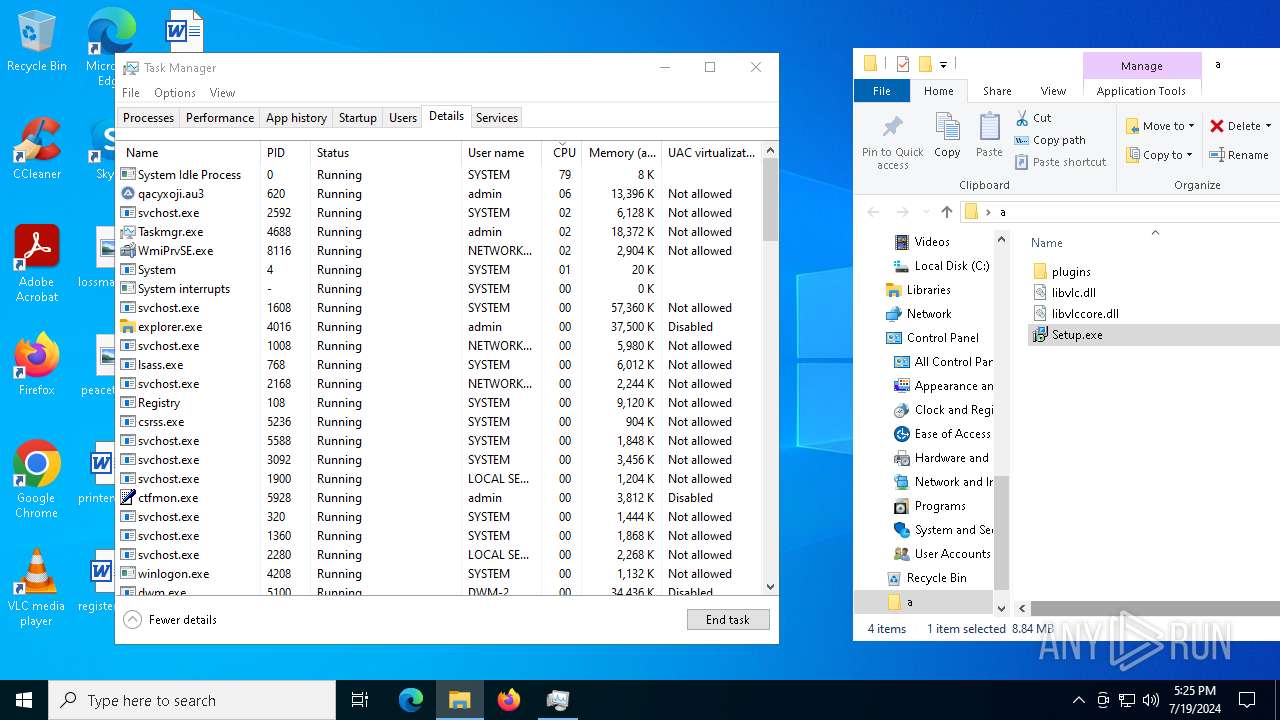
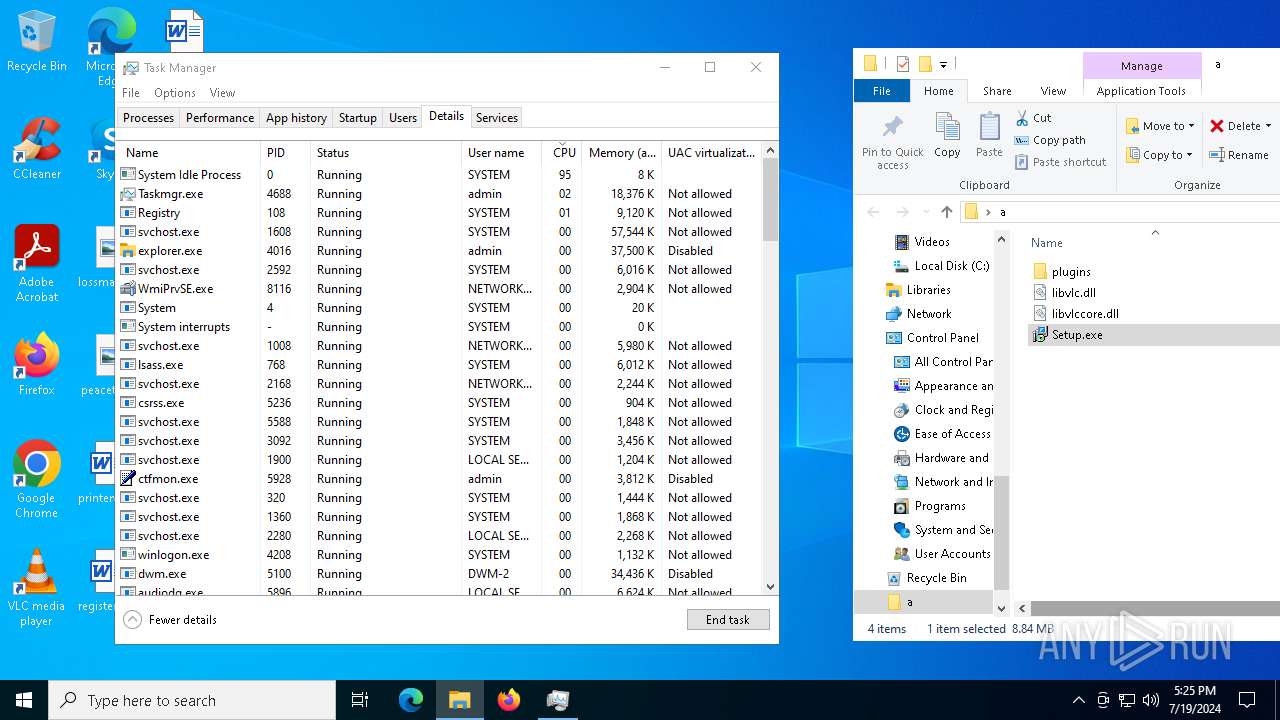
- qacyxoji.au3 (PID: 620)
Drops the executable file immediately after the start
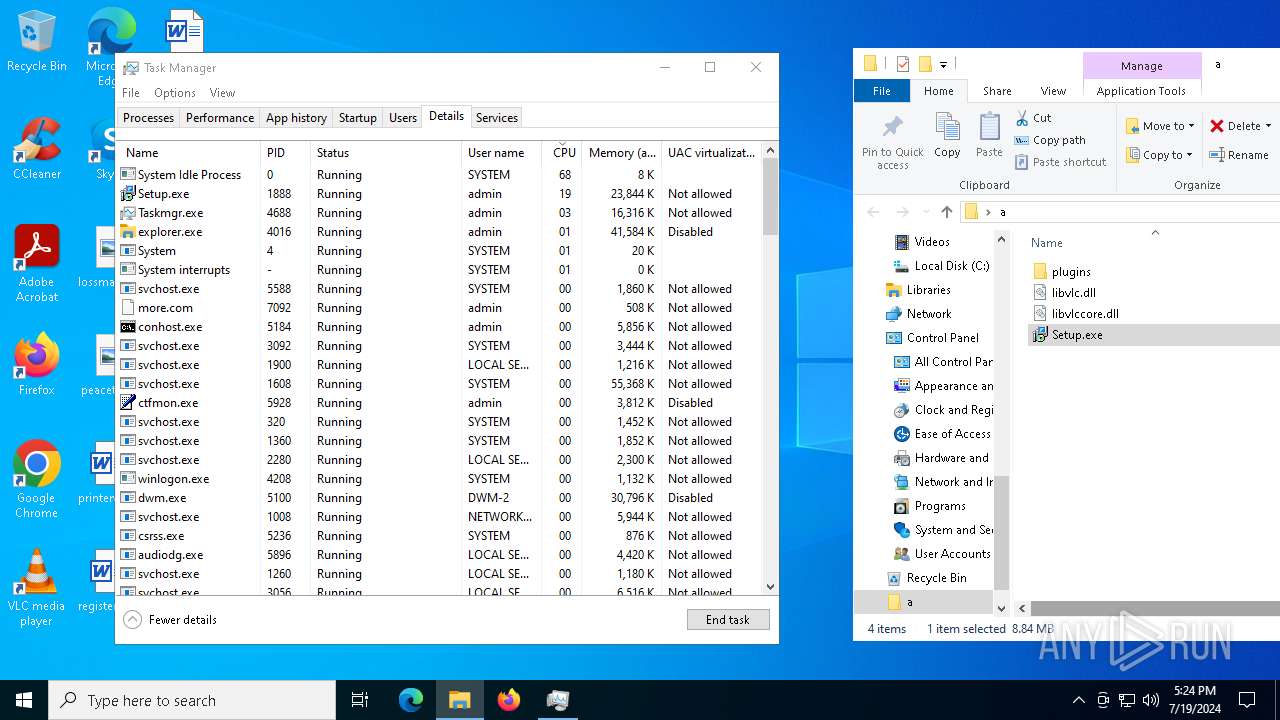
- more.com (PID: 7092)
LUMMA has been detected (YARA)
- more.com (PID: 7092)
- qacyxoji.au3 (PID: 620)
HIJACKLOADER has been detected (YARA)
- more.com (PID: 7092)
- qacyxoji.au3 (PID: 620)
LUMMA has been detected (SURICATA)
- qacyxoji.au3 (PID: 620)
Actions looks like stealing of personal data
- qacyxoji.au3 (PID: 620)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5108)
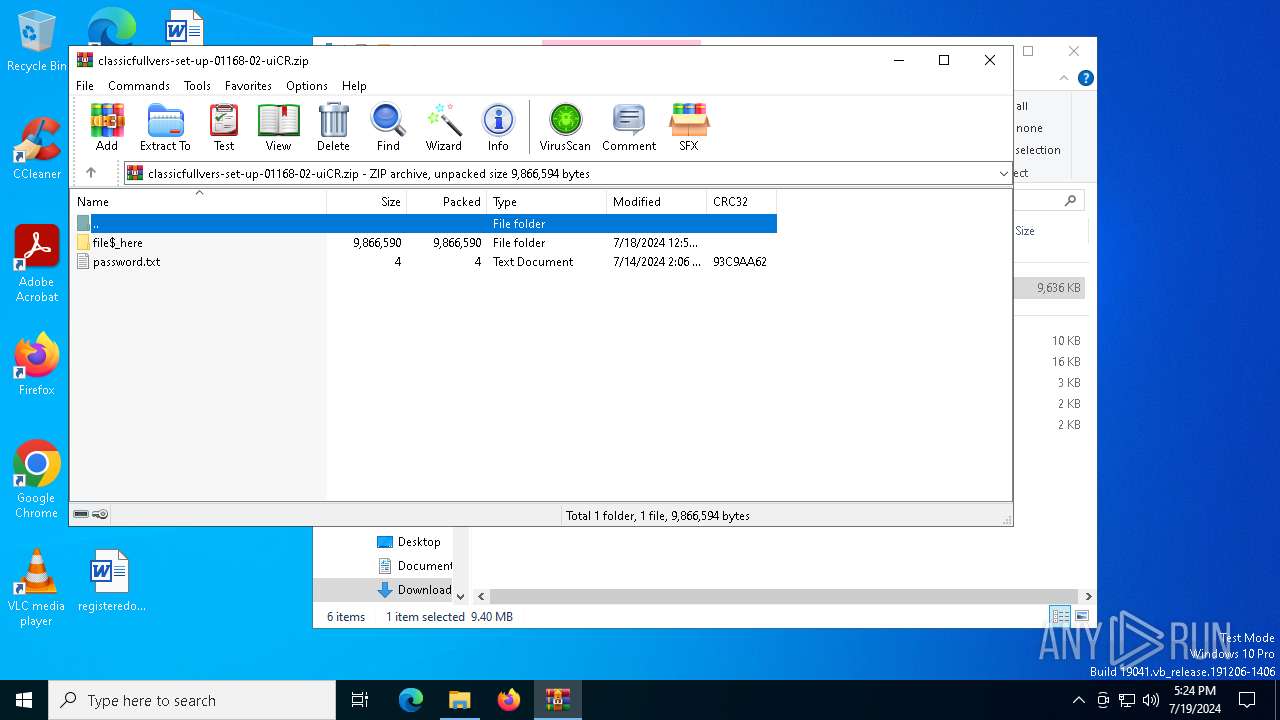
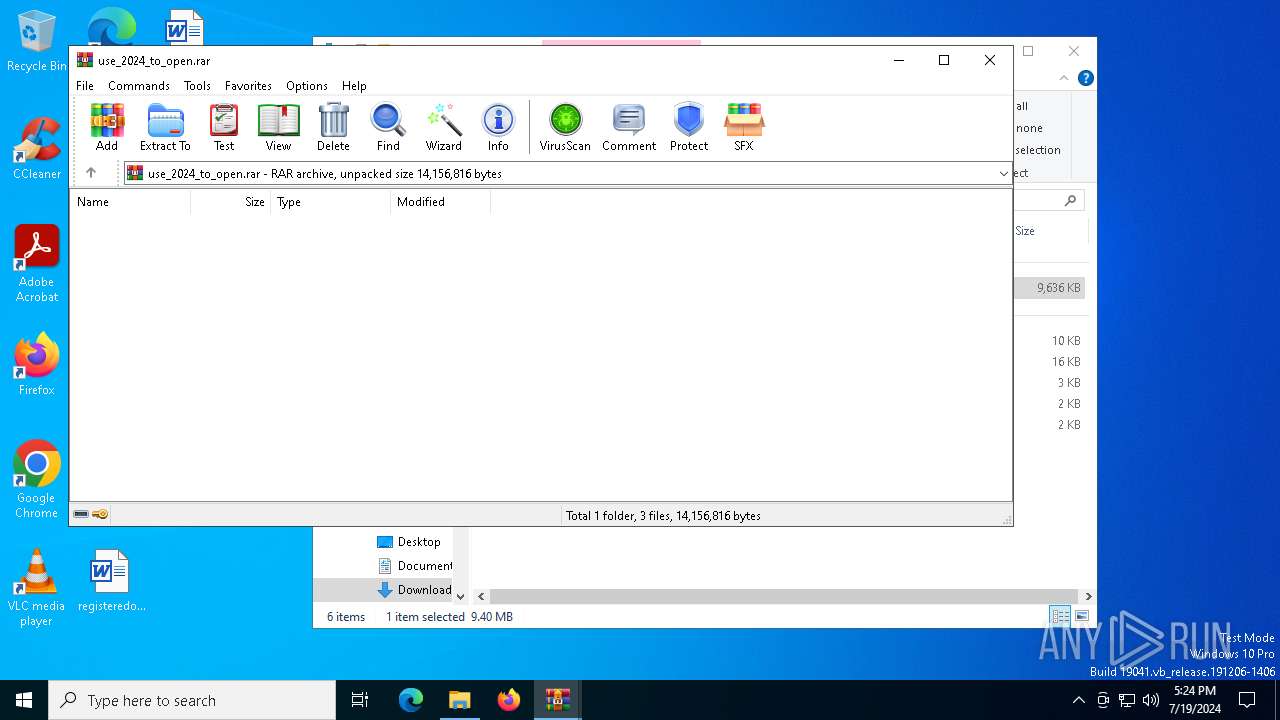
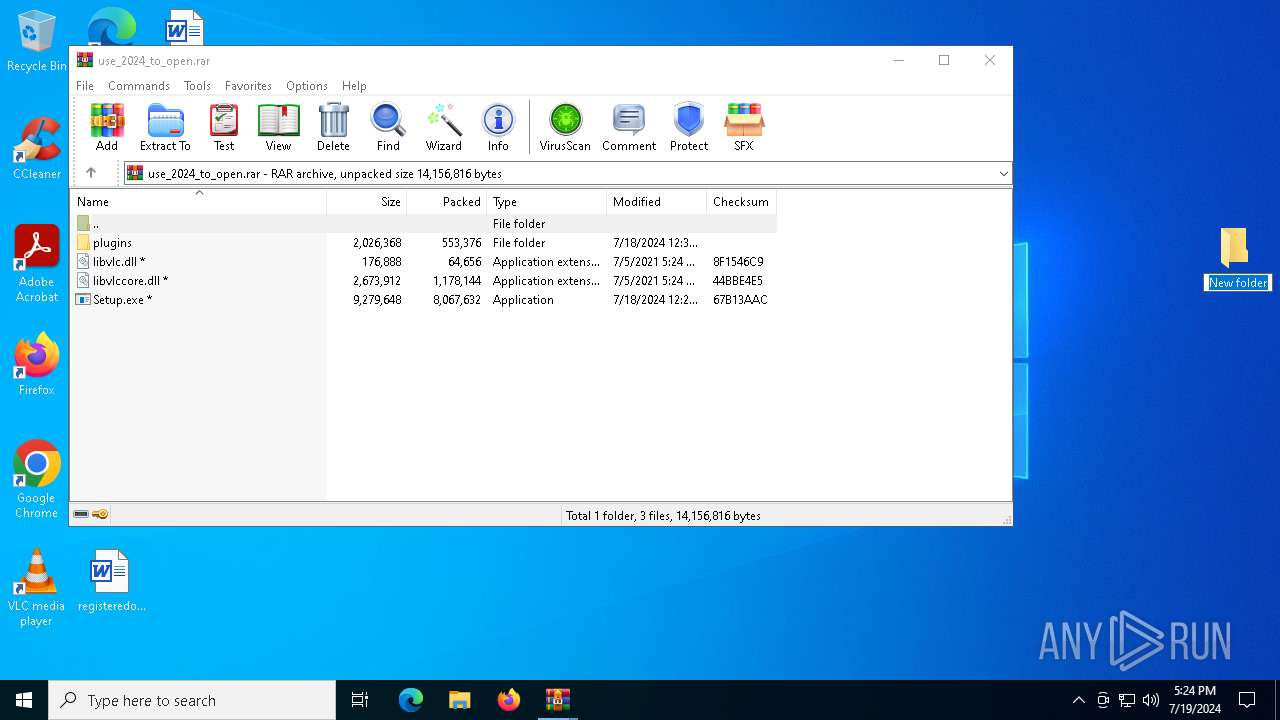
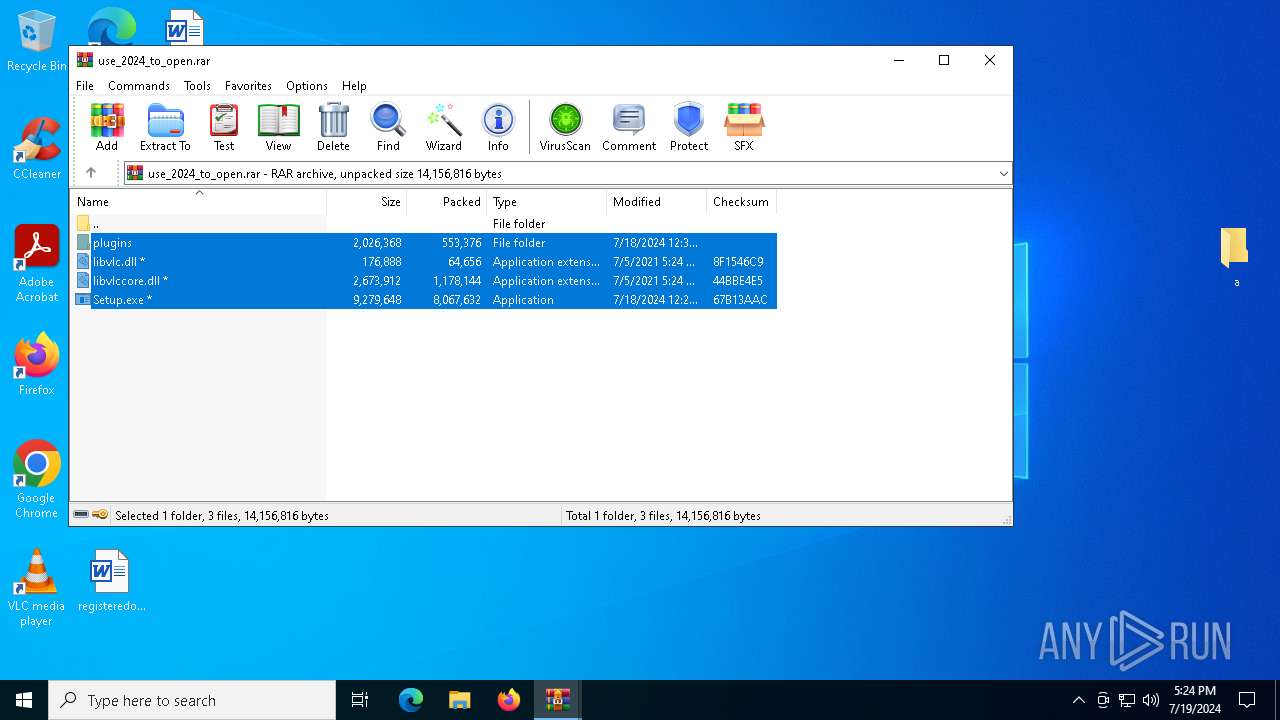
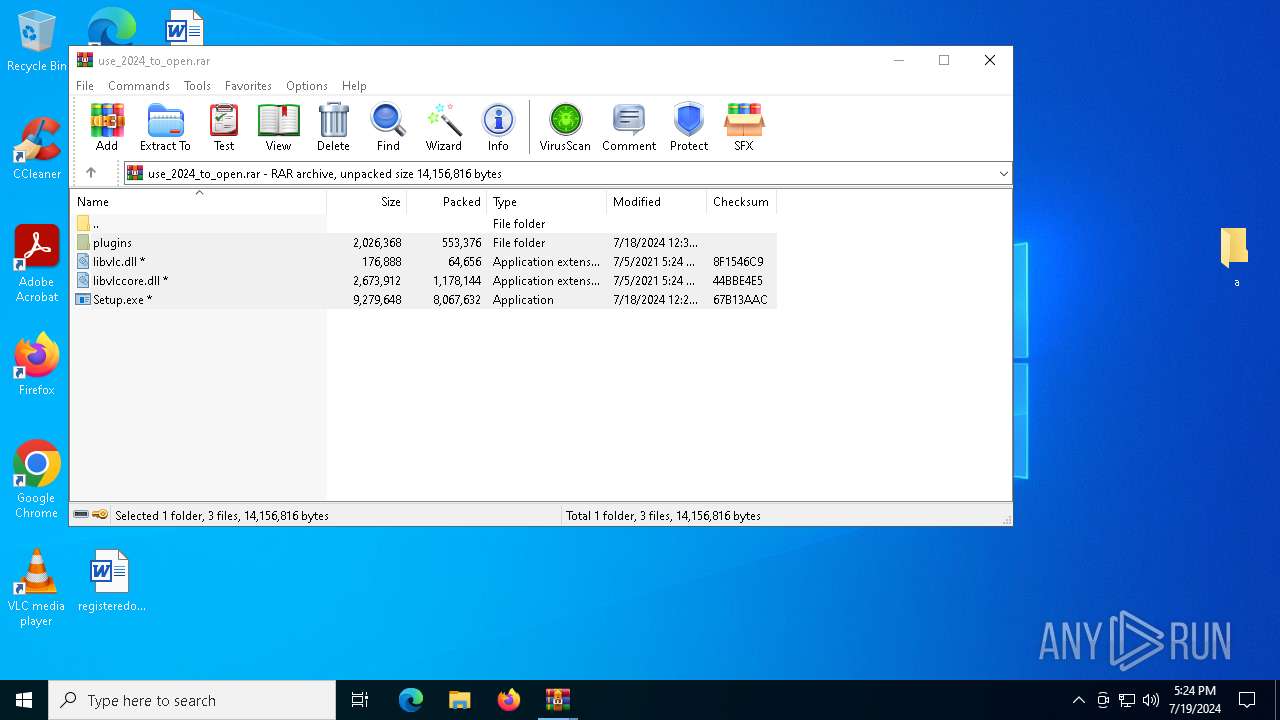
Process drops legitimate windows executable
- WinRAR.exe (PID: 7044)
Application launched itself
- WinRAR.exe (PID: 5108)
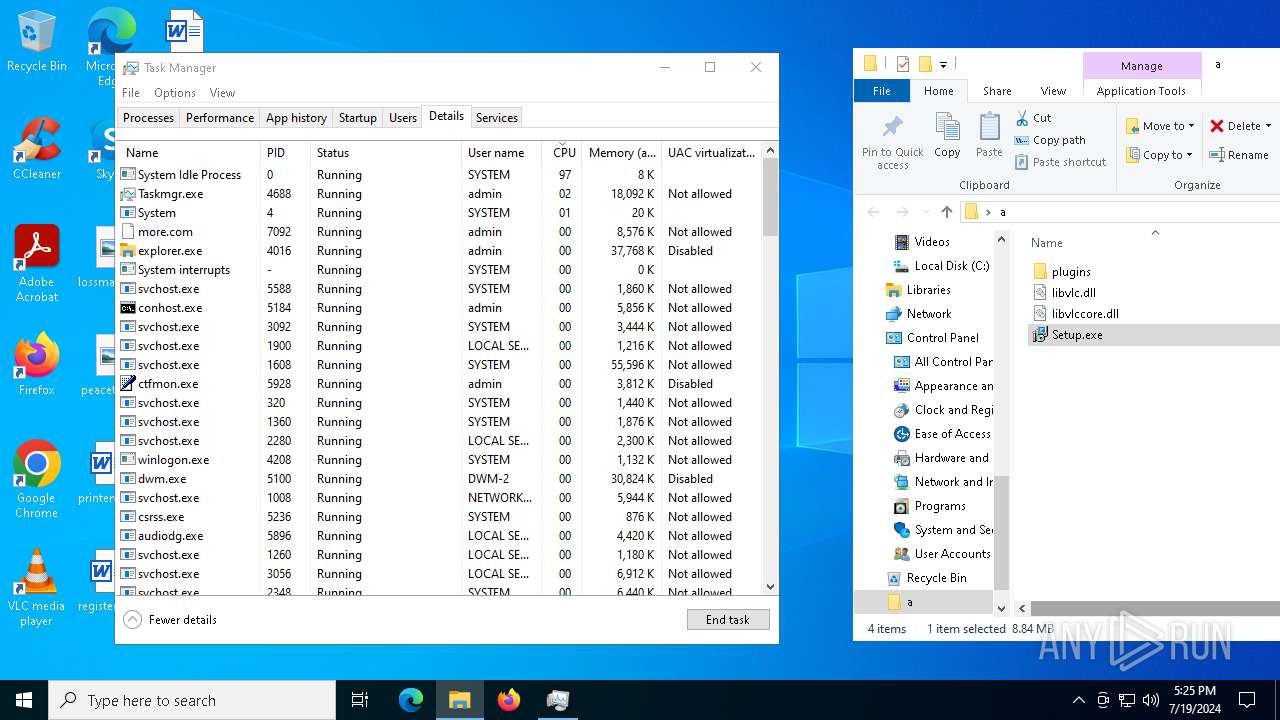
- Taskmgr.exe (PID: 7268)
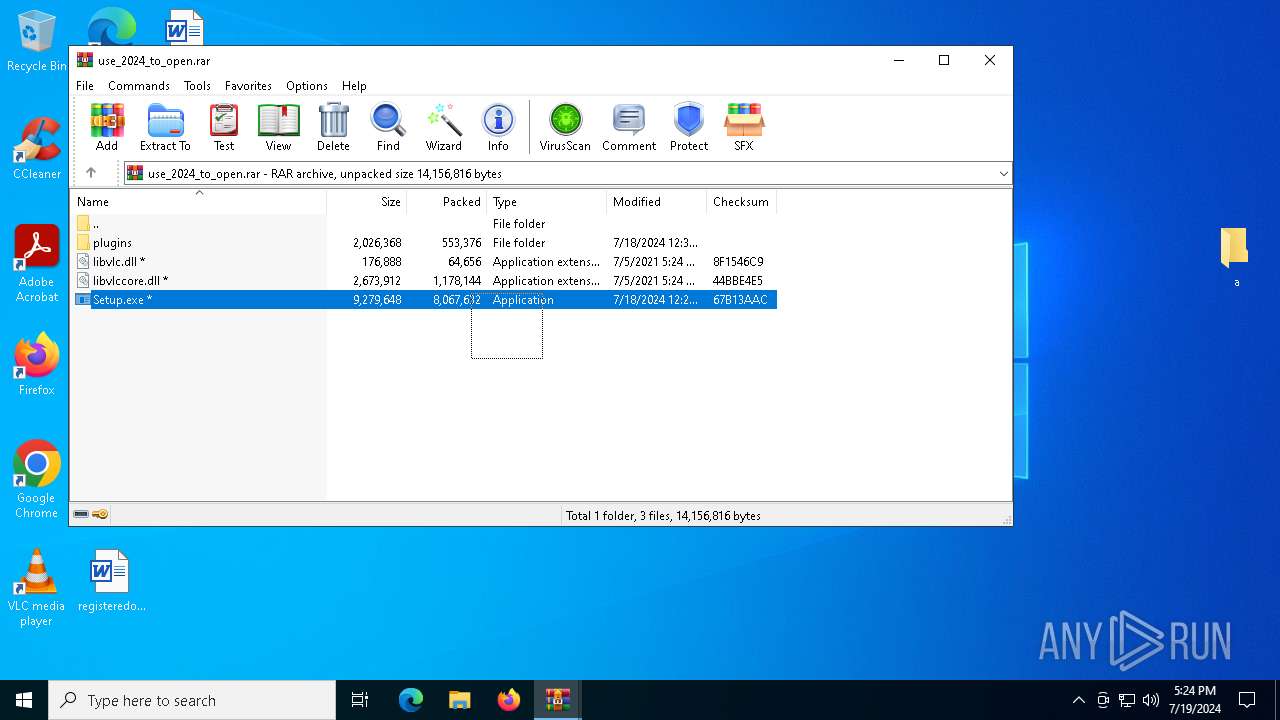
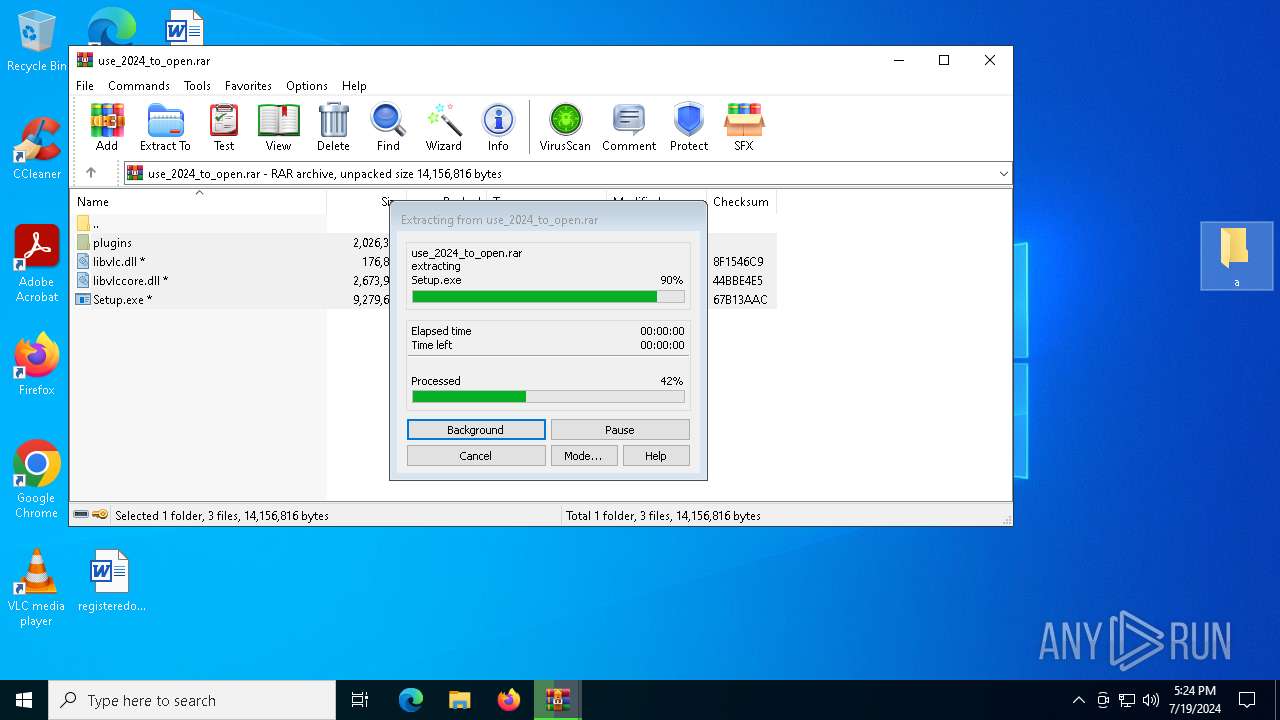
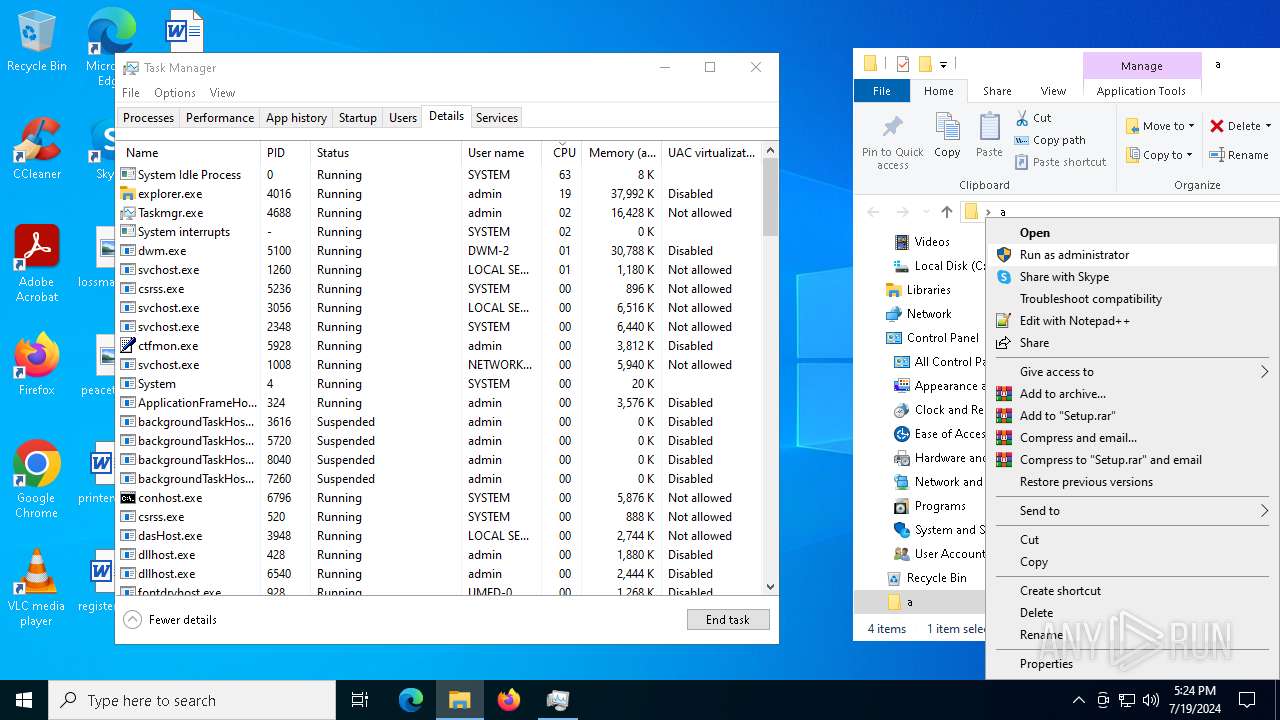
Starts application with an unusual extension
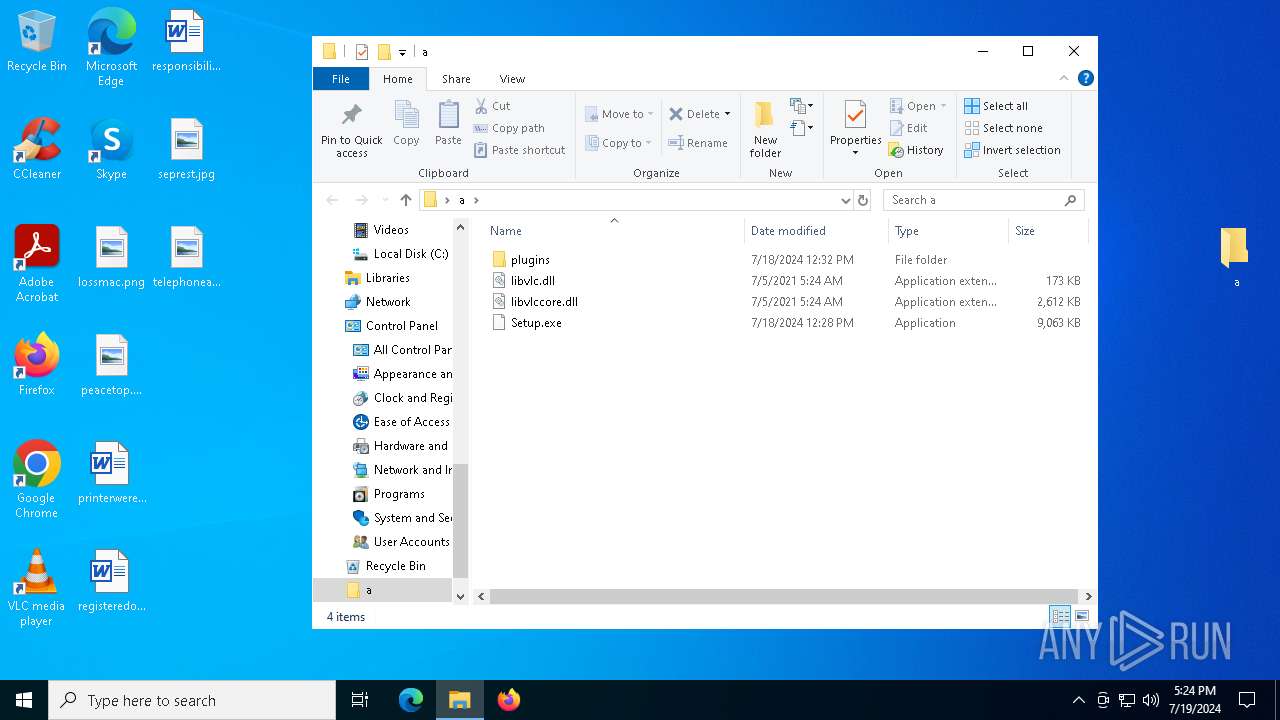
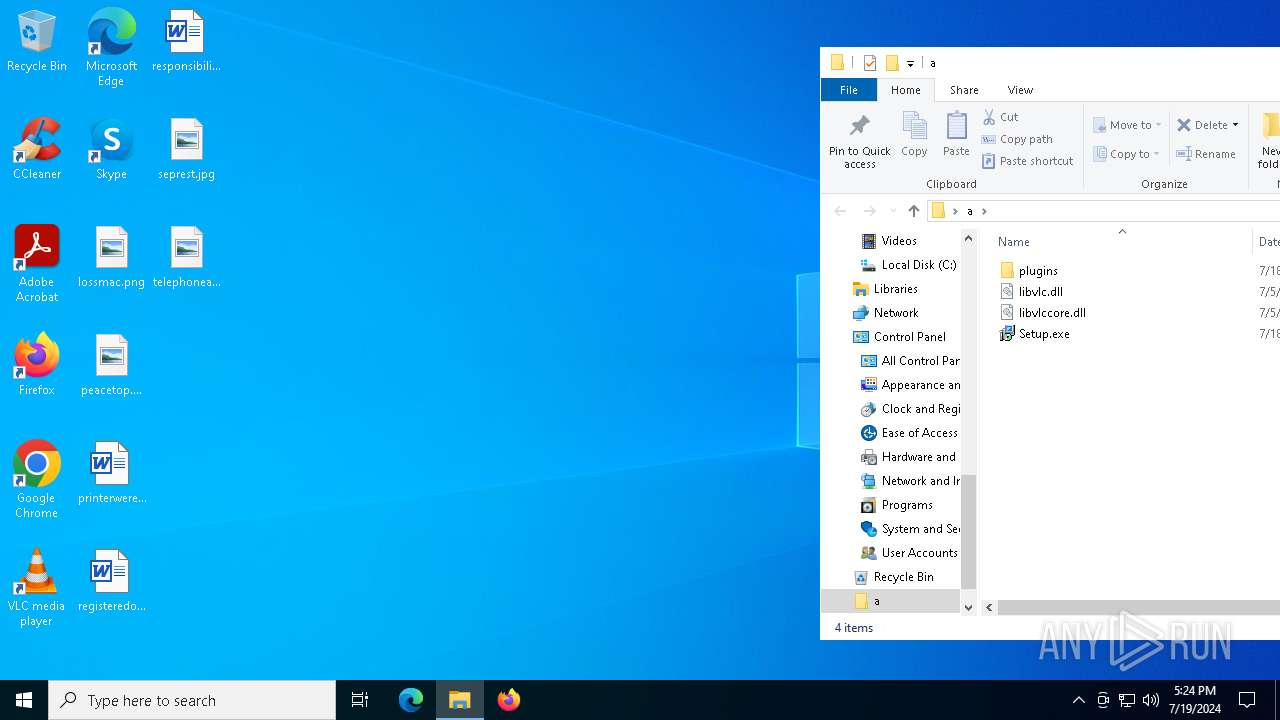
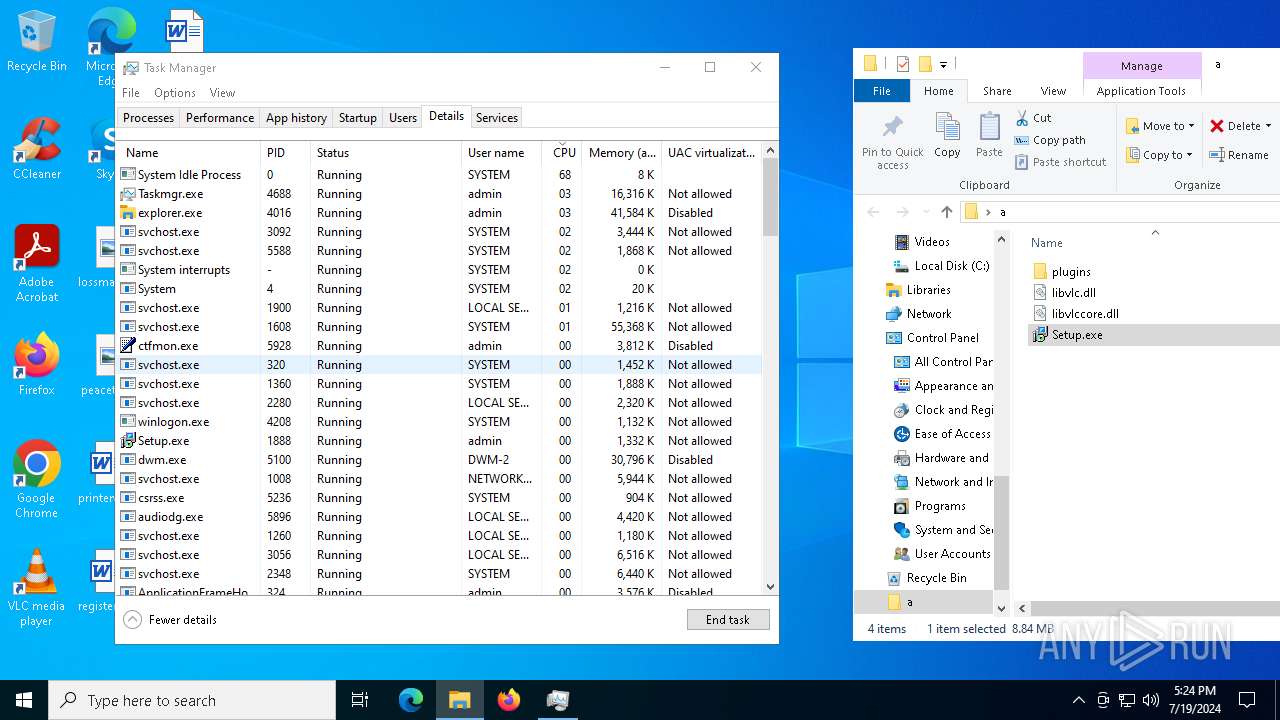
- Setup.exe (PID: 1888)
- more.com (PID: 7092)
Executable content was dropped or overwritten
- more.com (PID: 7092)
Searches for installed software
- qacyxoji.au3 (PID: 620)
INFO
Reads Microsoft Office registry keys
- firefox.exe (PID: 7612)
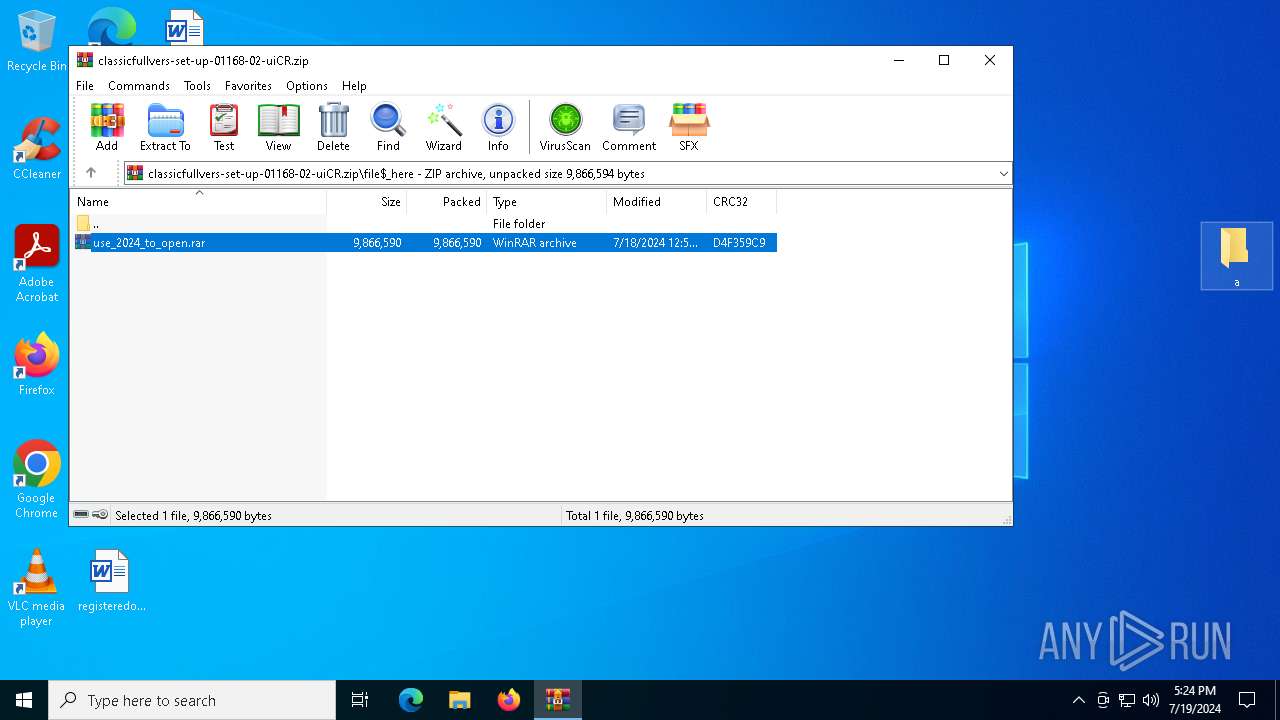
The process uses the downloaded file
- firefox.exe (PID: 7612)
- WinRAR.exe (PID: 5108)
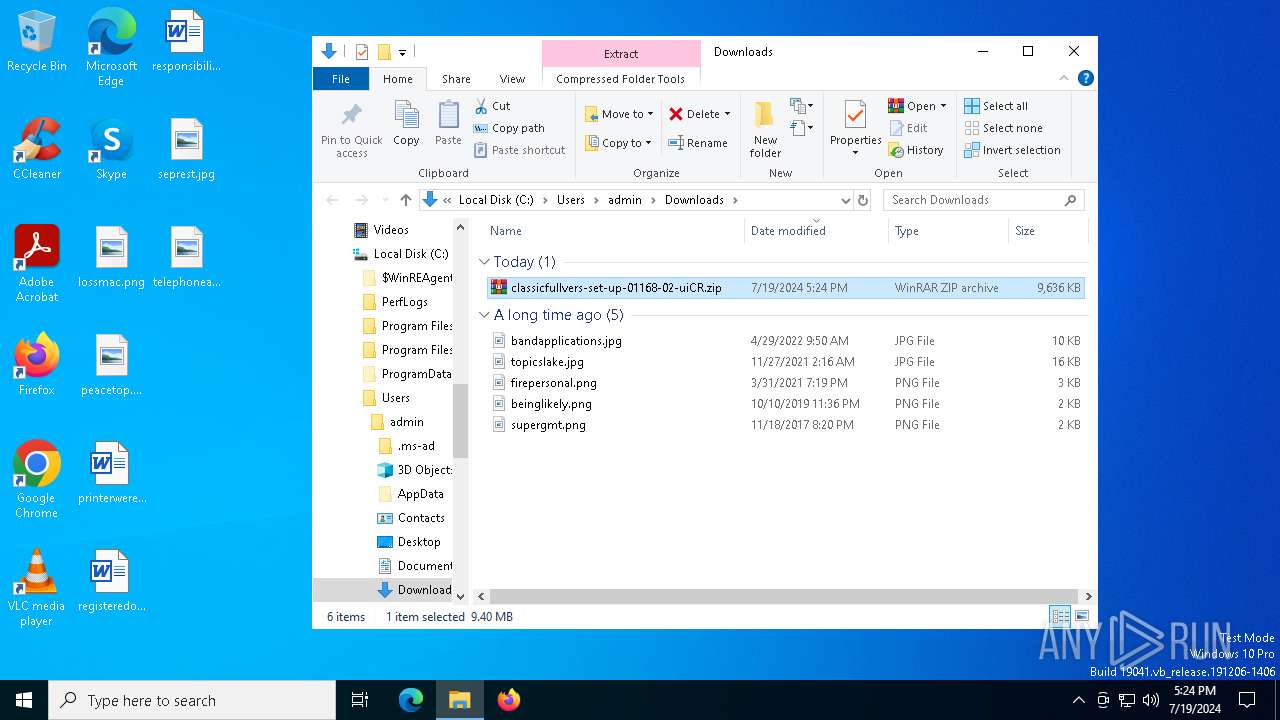
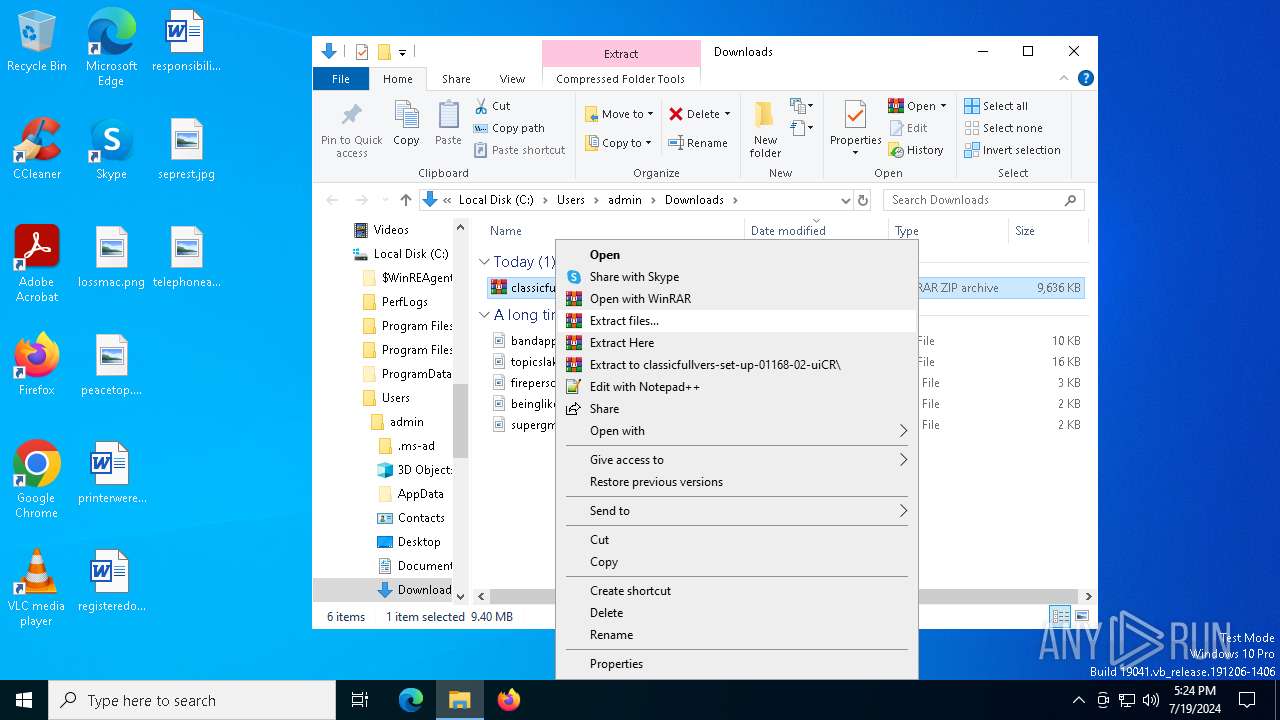
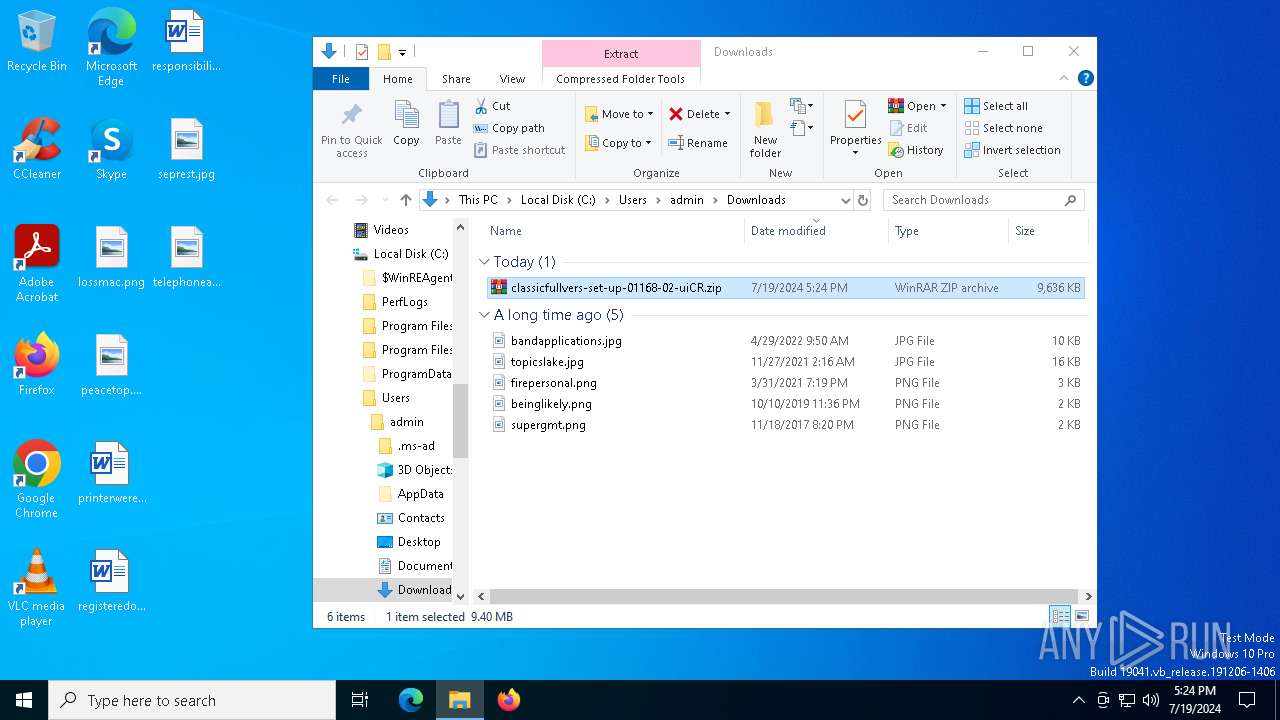
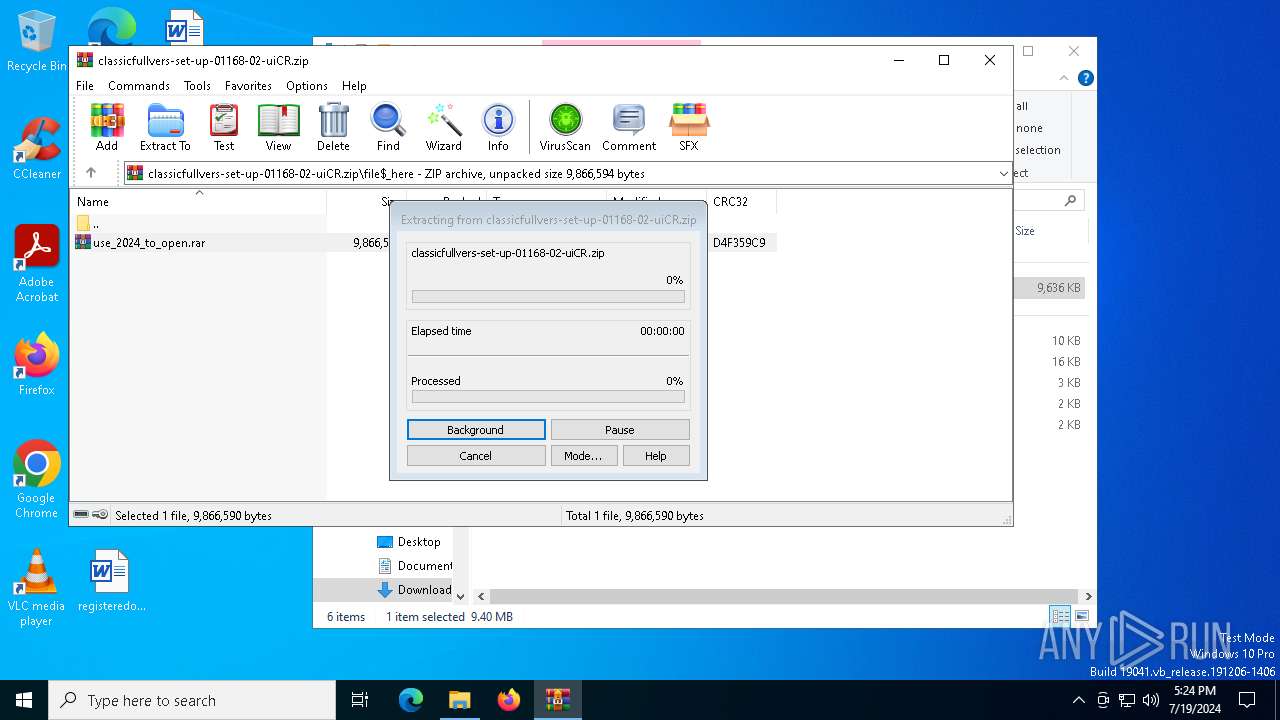
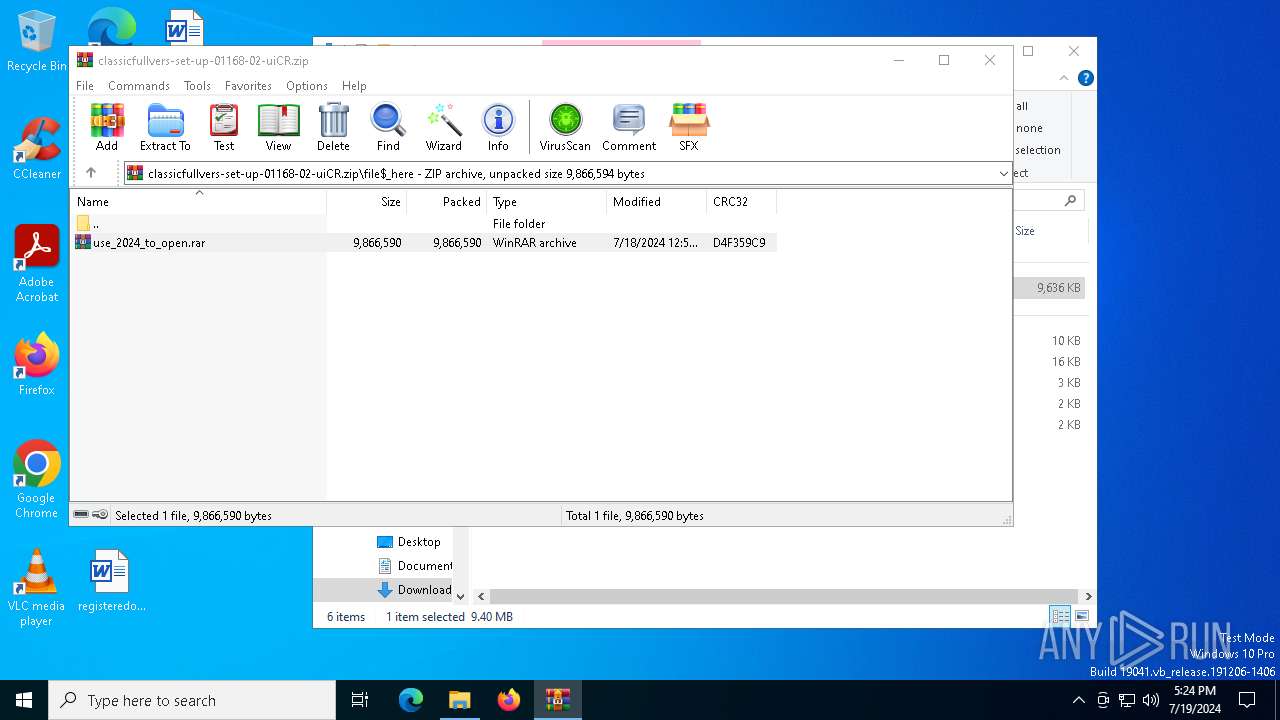
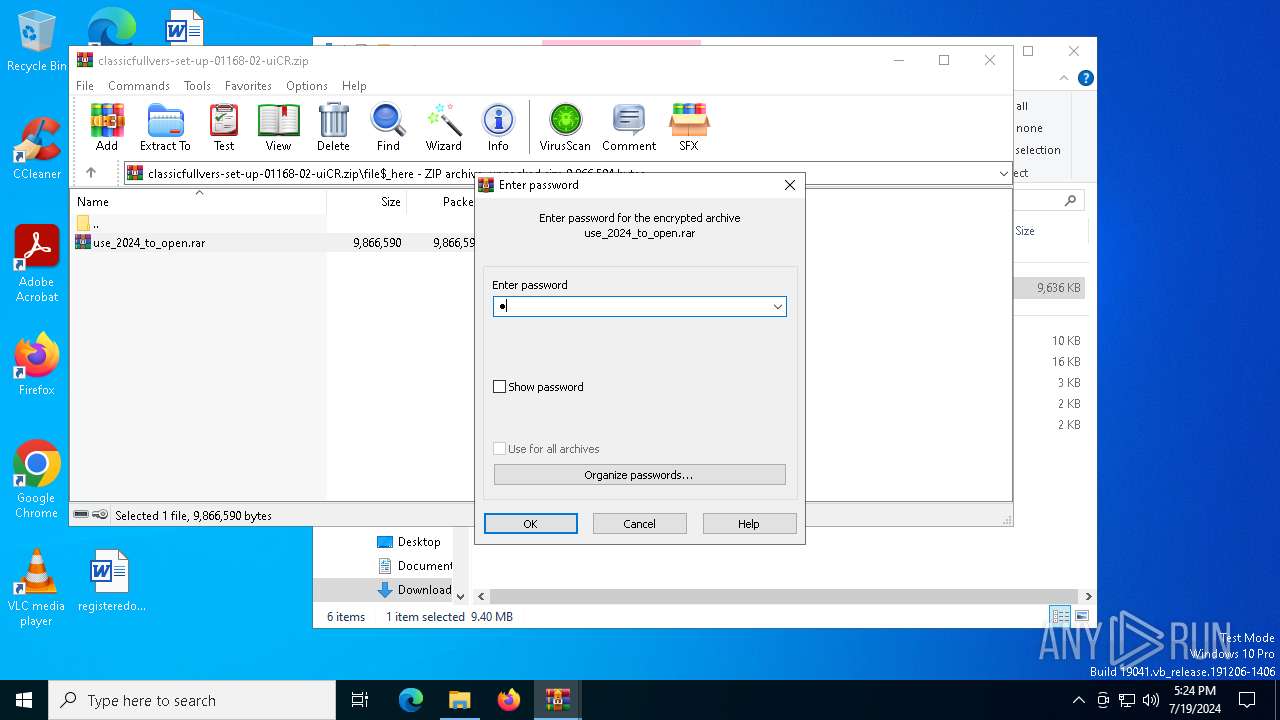
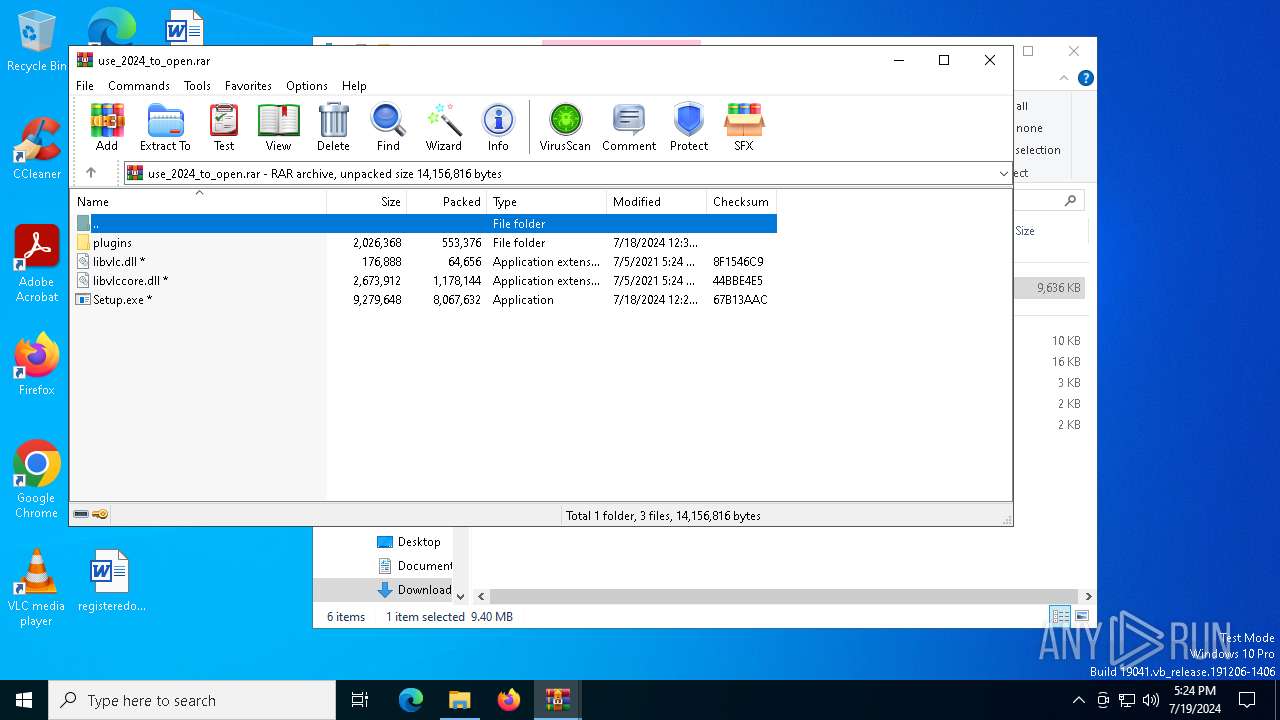
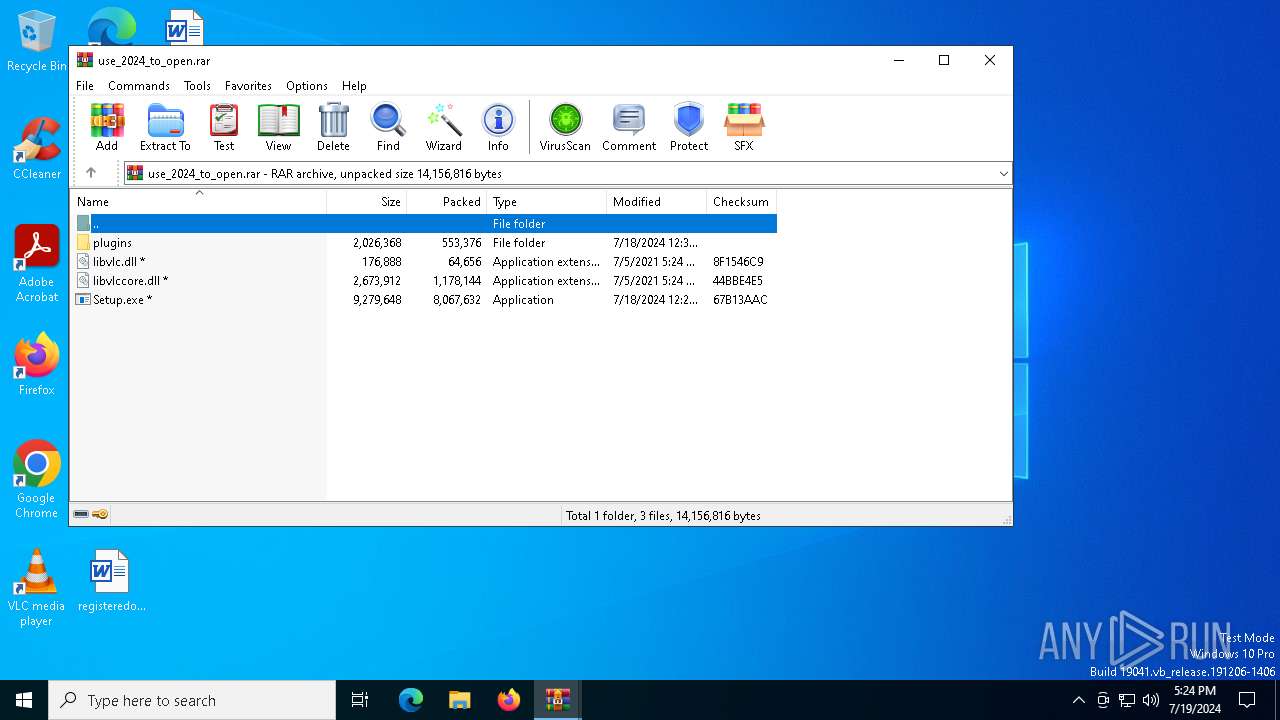
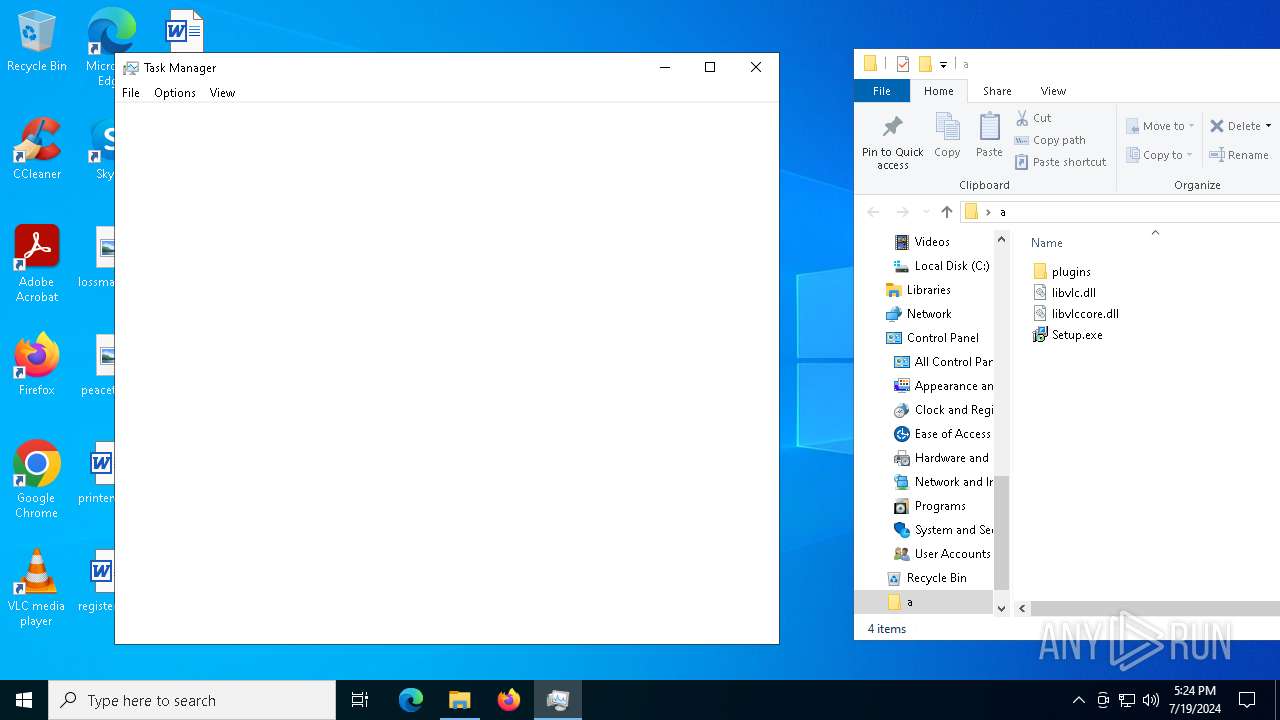
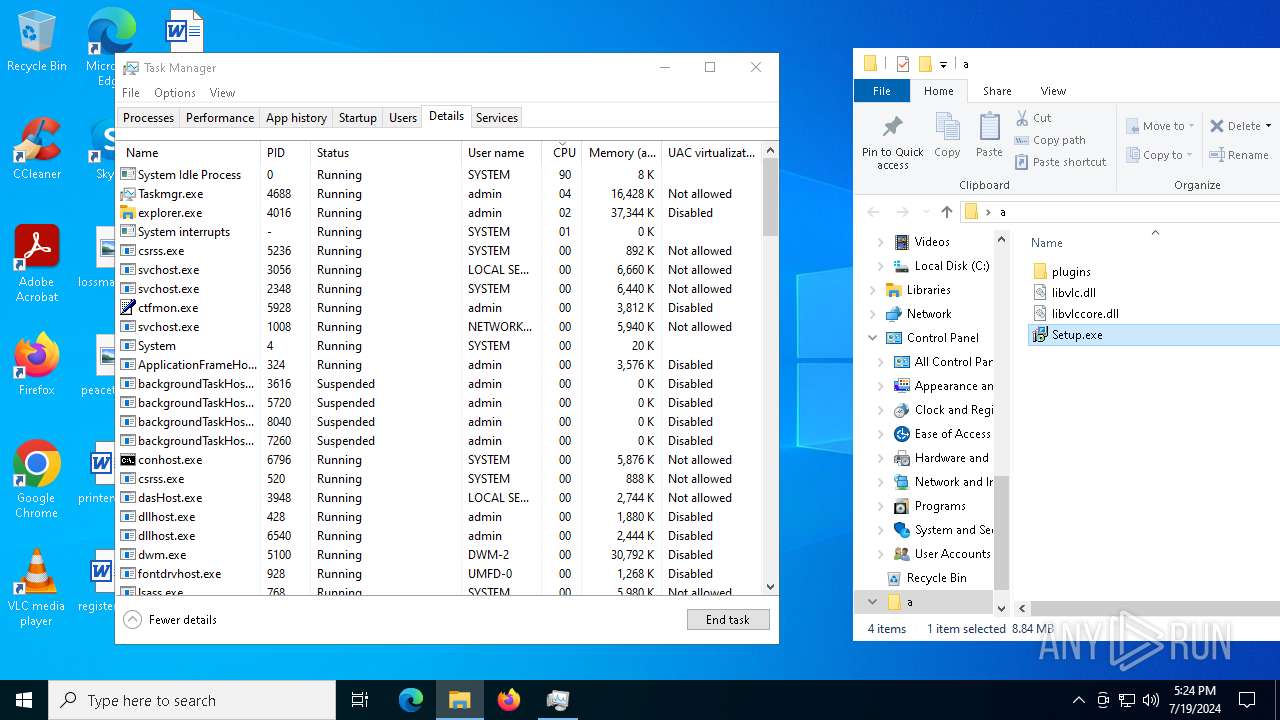
Manual execution by a user
- WinRAR.exe (PID: 5108)
- Taskmgr.exe (PID: 7268)
- Taskmgr.exe (PID: 7036)
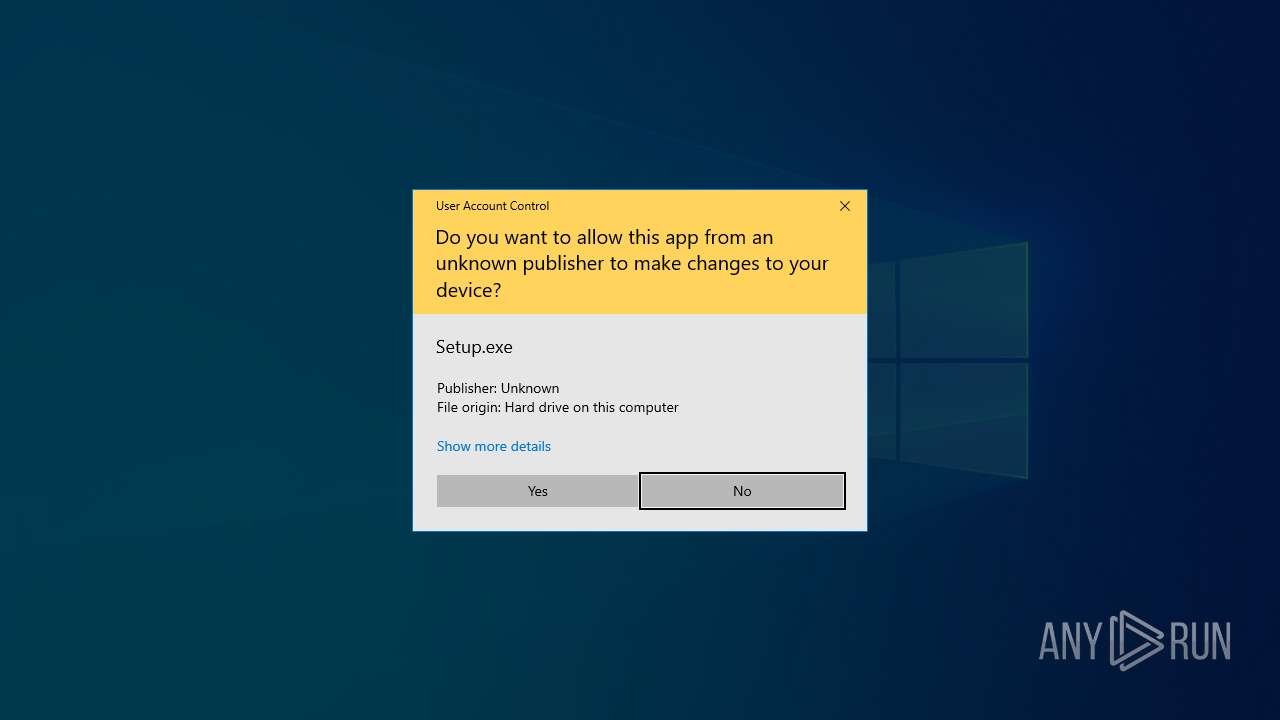
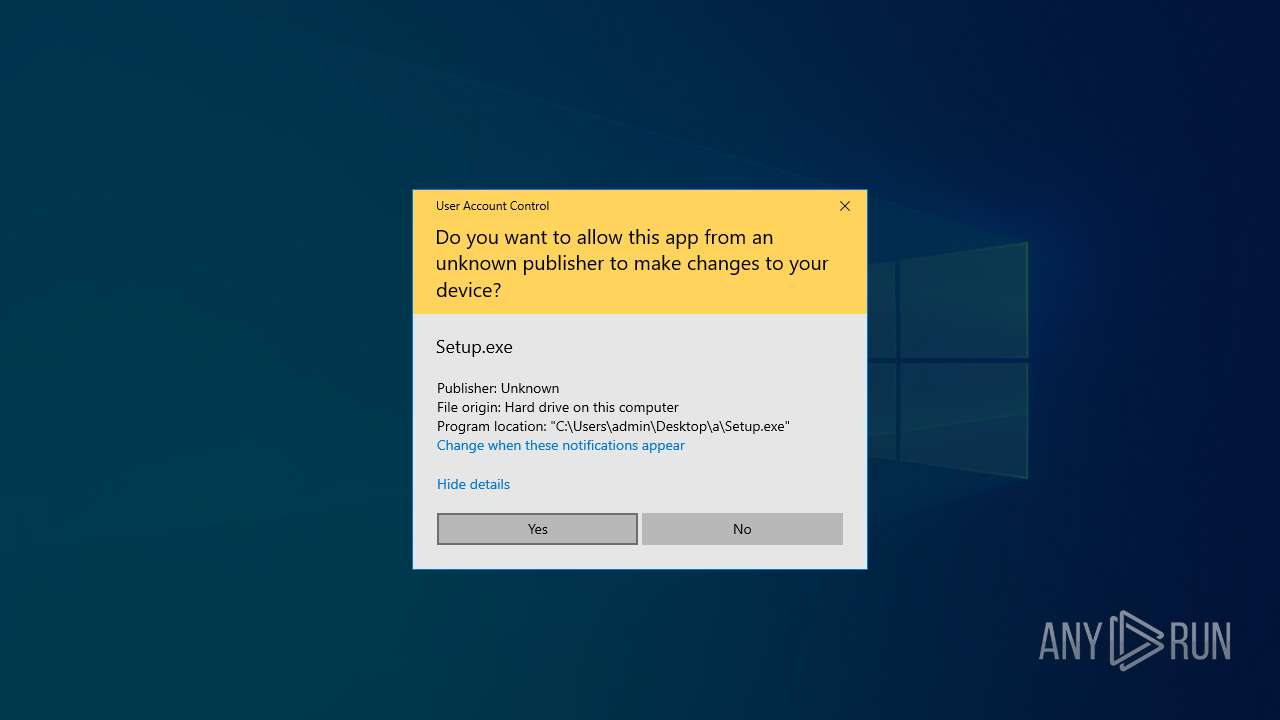
- Setup.exe (PID: 1888)
Application launched itself
- firefox.exe (PID: 7628)
- firefox.exe (PID: 7612)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7044)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 7044)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7268)
- Taskmgr.exe (PID: 4688)
Checks supported languages
- Setup.exe (PID: 1888)
- more.com (PID: 7092)
- qacyxoji.au3 (PID: 620)
Reads the computer name
- Setup.exe (PID: 1888)
- more.com (PID: 7092)
- qacyxoji.au3 (PID: 620)
Create files in a temporary directory
- more.com (PID: 7092)
- Setup.exe (PID: 1888)
Reads the software policy settings
- qacyxoji.au3 (PID: 620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(7092) more.com
C2 (9)upknittsoappz.shop
callosallsaospz.shop
outpointsozp.shop
shepherdlyopzc.shop
perceptivitysczio.shop
unseaffarignsk.shop
indexterityszcoxp.shop
liernessfornicsa.shop
lariatedzugspd.shop
(PID) Process(620) qacyxoji.au3
C2 (9)upknittsoappz.shop
callosallsaospz.shop
outpointsozp.shop
shepherdlyopzc.shop
perceptivitysczio.shop
unseaffarignsk.shop
indexterityszcoxp.shop
liernessfornicsa.shop
lariatedzugspd.shop
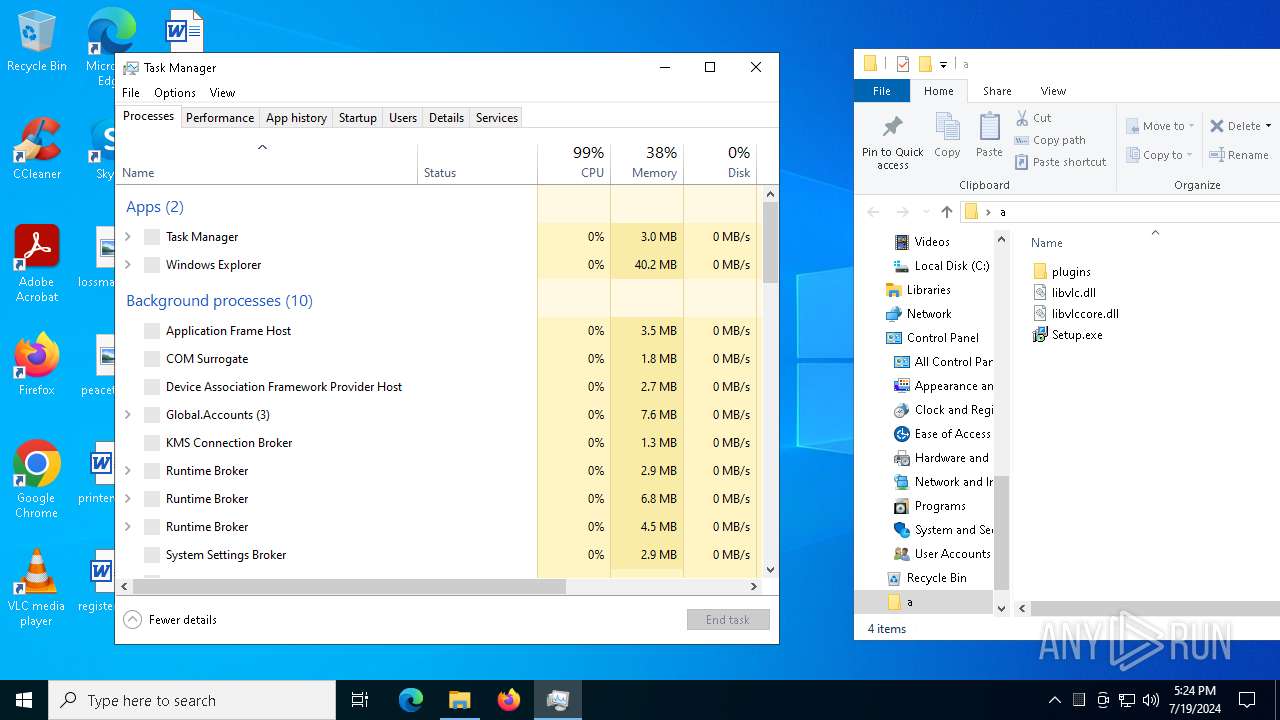
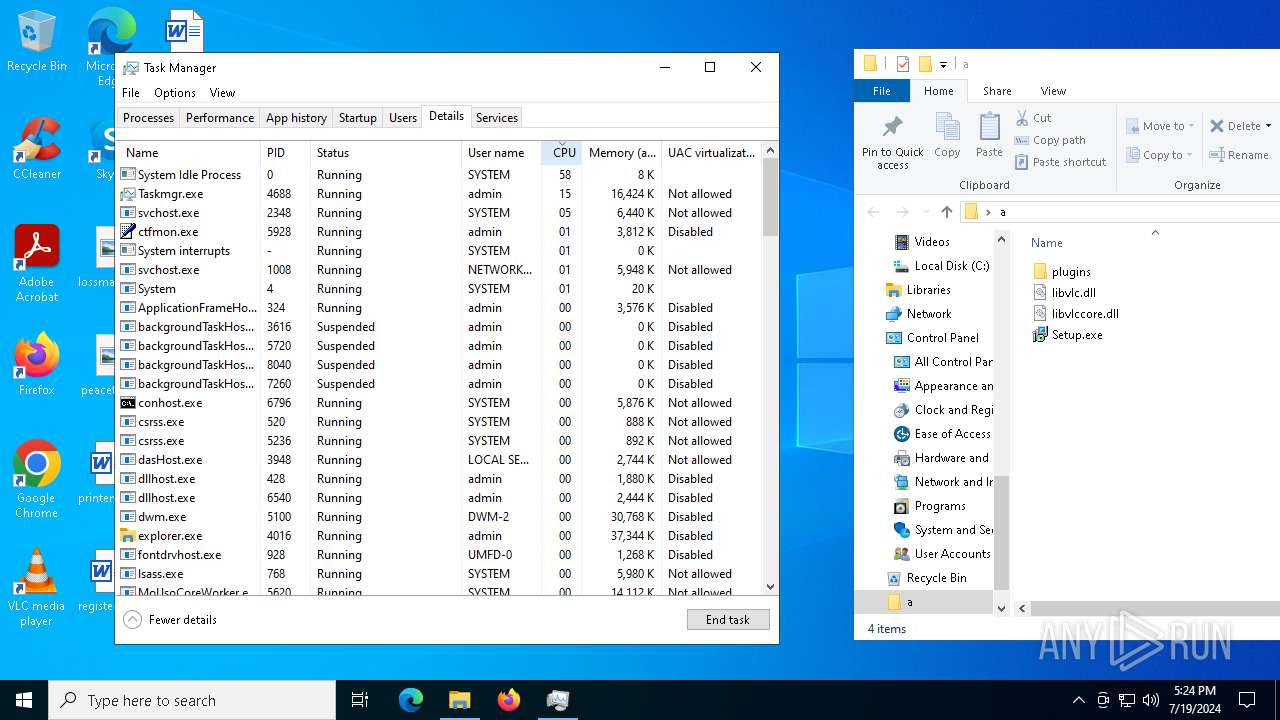
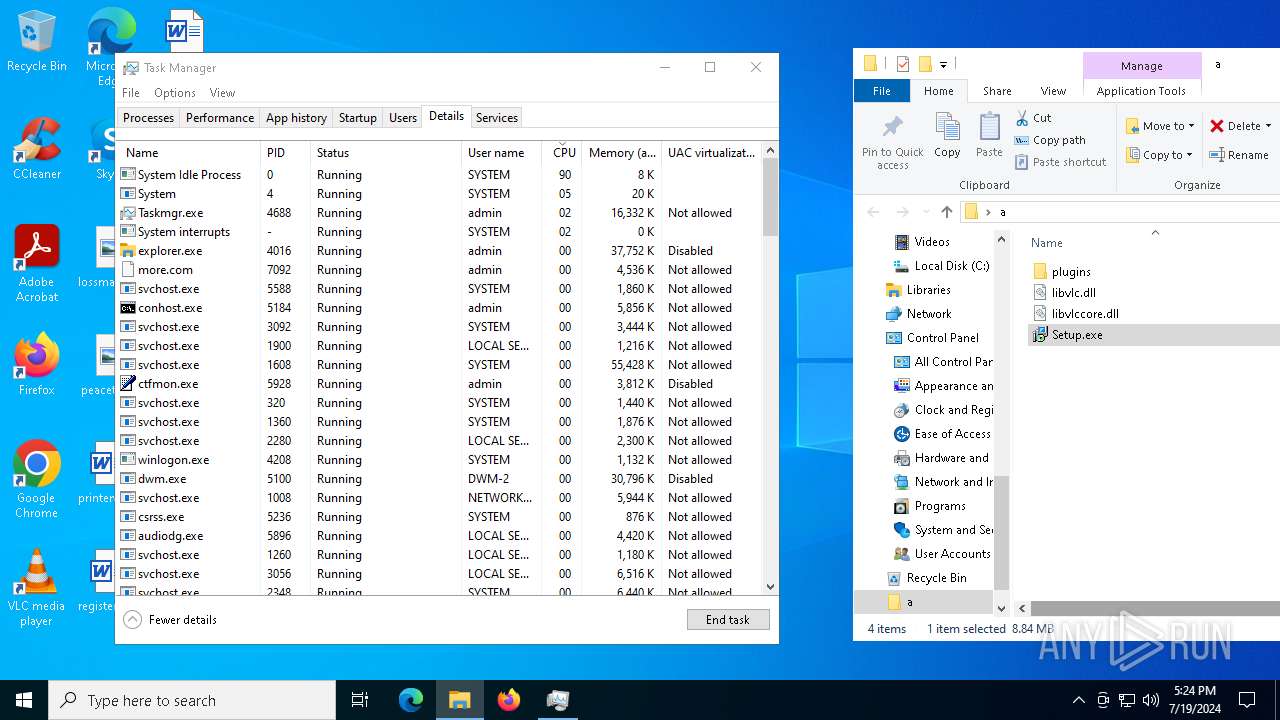
Total processes
162
Monitored processes
22
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | C:\Users\admin\AppData\Local\Temp\qacyxoji.au3 | C:\Users\admin\AppData\Local\Temp\qacyxoji.au3 | more.com | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: HIGH Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 5 Modules
Lumma(PID) Process(620) qacyxoji.au3 C2 (9)upknittsoappz.shop callosallsaospz.shop outpointsozp.shop shepherdlyopzc.shop perceptivitysczio.shop unseaffarignsk.shop indexterityszcoxp.shop liernessfornicsa.shop lariatedzugspd.shop | |||||||||||||||
| 1492 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5392 -childID 4 -isForBrowser -prefsHandle 5596 -prefMapHandle 5592 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1440 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {63029429-66ba-41bc-8e9d-c8c5f963def3} 7612 "\\.\pipe\gecko-crash-server-pipe.7612" 1744c6484d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
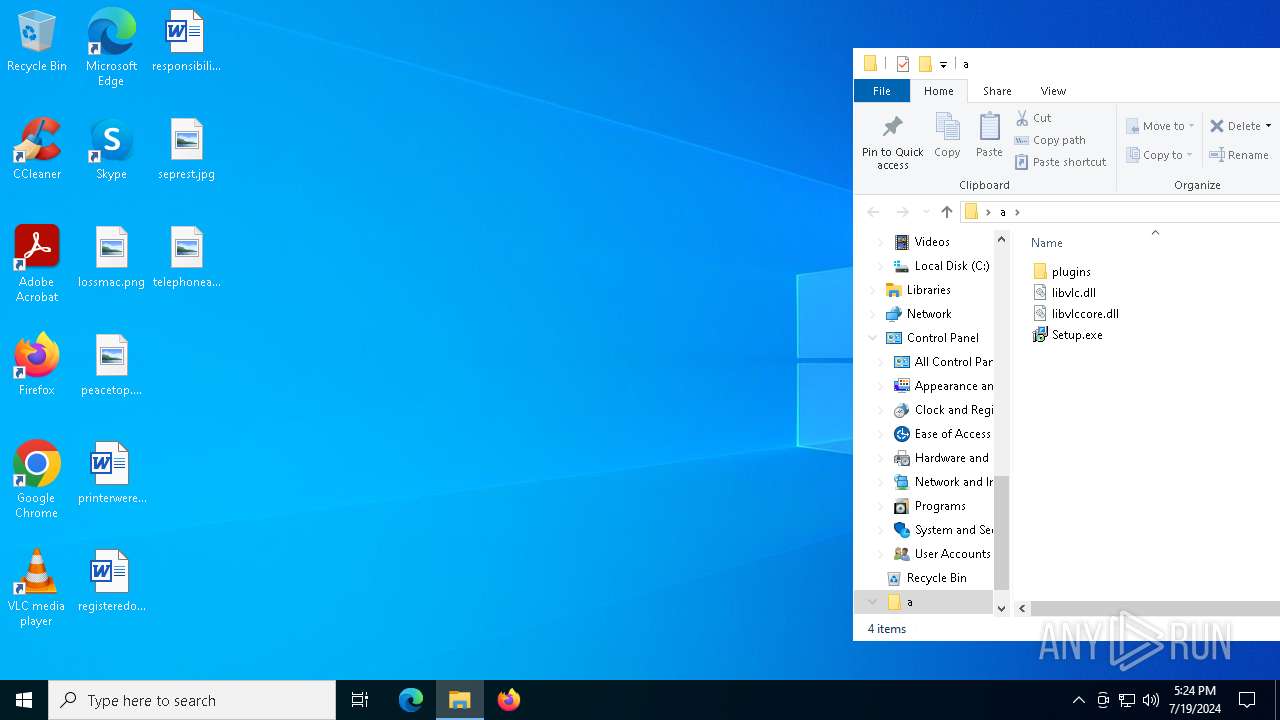
| 1888 | "C:\Users\admin\Desktop\a\Setup.exe" | C:\Users\admin\Desktop\a\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KeepDisplayOn is a tool to keep the display out of screensaver mode when running. Exit code: 1 Version: 1.2.0.0 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2980 -childID 1 -isForBrowser -prefsHandle 2992 -prefMapHandle 2988 -prefsLen 26706 -prefMapSize 244343 -jsInitHandle 1440 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {a68ed1c3-39ef-4bc2-b9de-530f28030b05} 7612 "\\.\pipe\gecko-crash-server-pipe.7612" 1744ae61150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5876 -childID 6 -isForBrowser -prefsHandle 5992 -prefMapHandle 6004 -prefsLen 34713 -prefMapSize 244343 -jsInitHandle 1440 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7d0e1b84-4996-41ba-aba1-2faec8b06c98} 7612 "\\.\pipe\gecko-crash-server-pipe.7612" 1744bc59a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3328 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
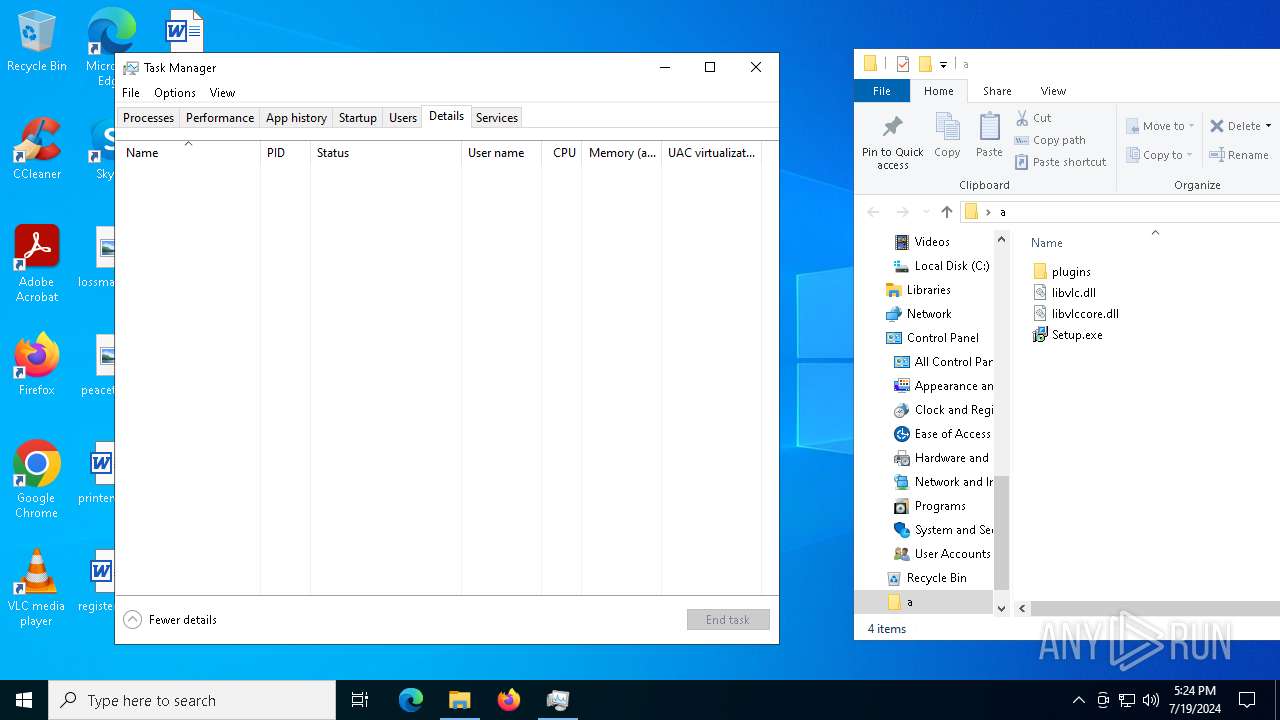
| 4688 | "C:\WINDOWS\system32\taskmgr.exe" /1 | C:\Windows\System32\Taskmgr.exe | — | Taskmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5108 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\classicfullvers-set-up-01168-02-uiCR.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5184 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5748 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4512 -childID 2 -isForBrowser -prefsHandle 4568 -prefMapHandle 4564 -prefsLen 36263 -prefMapSize 244343 -jsInitHandle 1440 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b7d87910-3756-47c8-9acd-c5e46bcb5647} 7612 "\\.\pipe\gecko-crash-server-pipe.7612" 1744d01dd90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
31 153
Read events
31 037
Write events
107
Delete events
9
Modification events
| (PID) Process: | (7628) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 7B31BDA303000000 | |||
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 4A86BFA303000000 | |||
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (7612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
Executable files
9
Suspicious files
157
Text files
17
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:E1CC35363E358090F08935957D76A27B | SHA256:958BE495364E3F8126A5EDAC5A69D5190F1AB84FC34F373A78CFC7E230734391 | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\protections.sqlite-journal | binary | |
MD5:F62B004F648E34419F3FAD1B4F408B7B | SHA256:FF287B8C694F413246CC81AE290AAF0CFBD30BE8A3F82AA10A7ECF72FC65EBD2 | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | sqlite | |
MD5:08CE75FC54C55883AE6663FB09923436 | SHA256:93E41E3E6BC38312DF19F0C212BA2577AC32F256D6FC1621D2CAD6E26AFE69CF | |||
| 7612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:E1CC35363E358090F08935957D76A27B | SHA256:958BE495364E3F8126A5EDAC5A69D5190F1AB84FC34F373A78CFC7E230734391 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
76
DNS requests
89
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7612 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7612 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7612 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
7612 | firefox.exe | POST | 200 | 95.101.54.130:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
7612 | firefox.exe | POST | 200 | 95.101.54.195:80 | http://r3.o.lencr.org/ | unknown | — | — | unknown |
7612 | firefox.exe | POST | 200 | 95.101.54.130:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
7612 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
7612 | firefox.exe | POST | 200 | 95.101.54.130:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
7612 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
7612 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4716 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5620 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
7856 | svchost.exe | 4.209.32.198:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2760 | svchost.exe | 40.113.103.199:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7612 | firefox.exe | 192.0.78.26:443 | href.li | AUTOMATTIC | US | malicious |
7612 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7612 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
7612 | firefox.exe | 142.250.186.170:443 | safebrowsing.googleapis.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
href.li |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
620 | qacyxoji.au3 | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
5 ETPRO signatures available at the full report