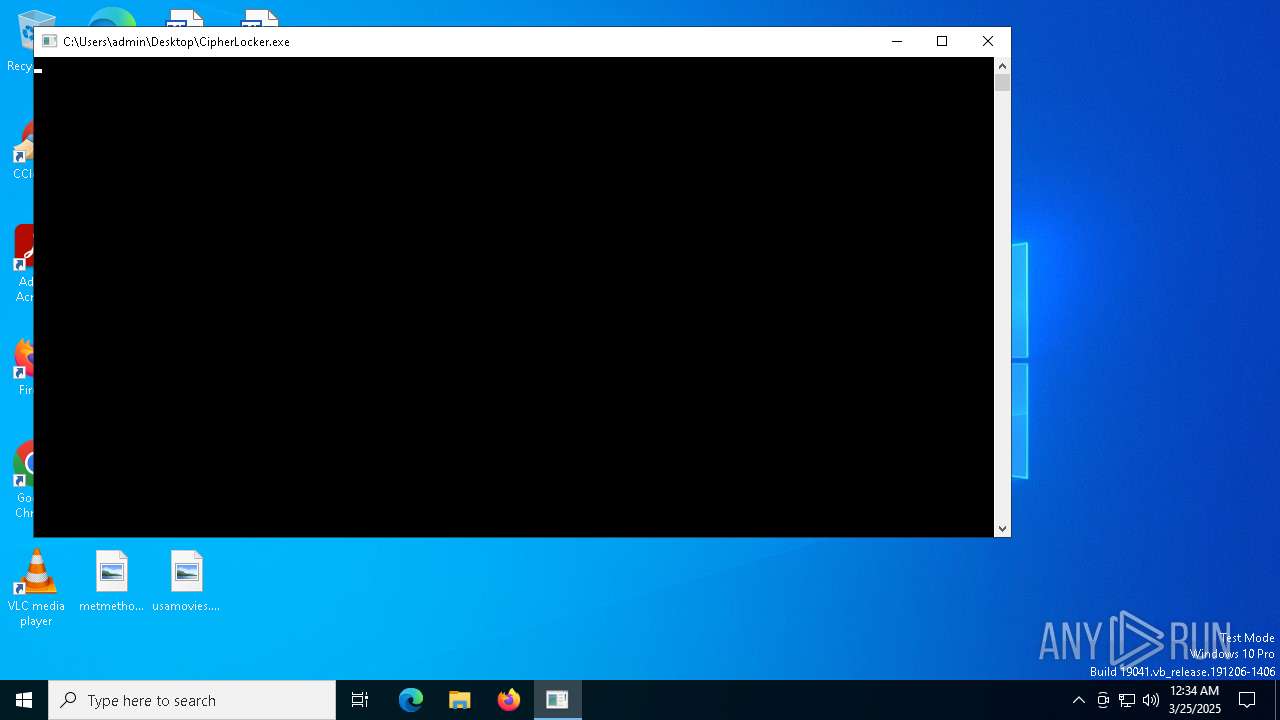
| File name: | CipherLocker.exe |
| Full analysis: | https://app.any.run/tasks/cd097b6c-c33b-4c27-8c00-7a0b0c20a9e2 |
| Verdict: | Malicious activity |
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
| Analysis date: | March 25, 2025, 00:34:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 627BF6F03E23F703FE180AF4629A07F8 |
| SHA1: | 7FA251D7E86E7F5BA55337068BEF751B040FA5EC |
| SHA256: | 98AA71A812319724EF6B52A6AF264CB6979E114405004B9E98FE9AA41E37648E |
| SSDEEP: | 768:+tYu64IOQF5BNu2HldKyqkKPf2vP2cXVKou:+K1Y4dKyqGLVK |
MALICIOUS
Actions looks like stealing of personal data
- certutil.exe (PID: 7000)
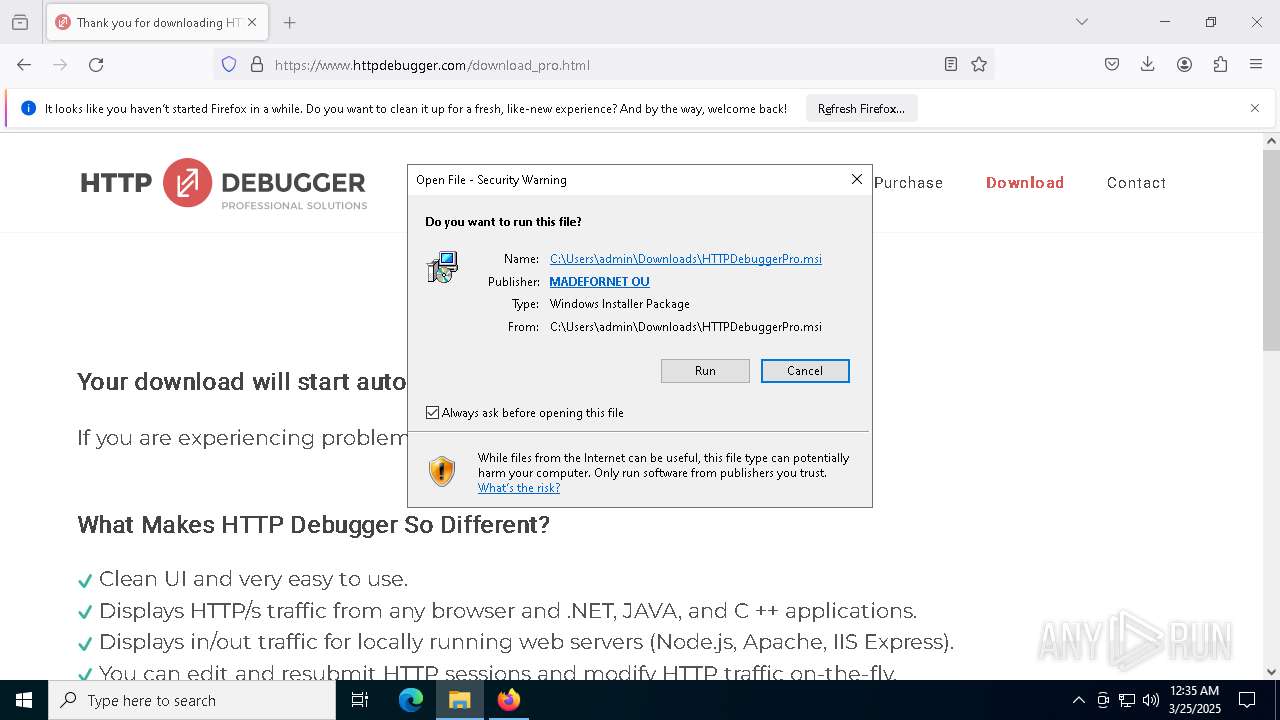
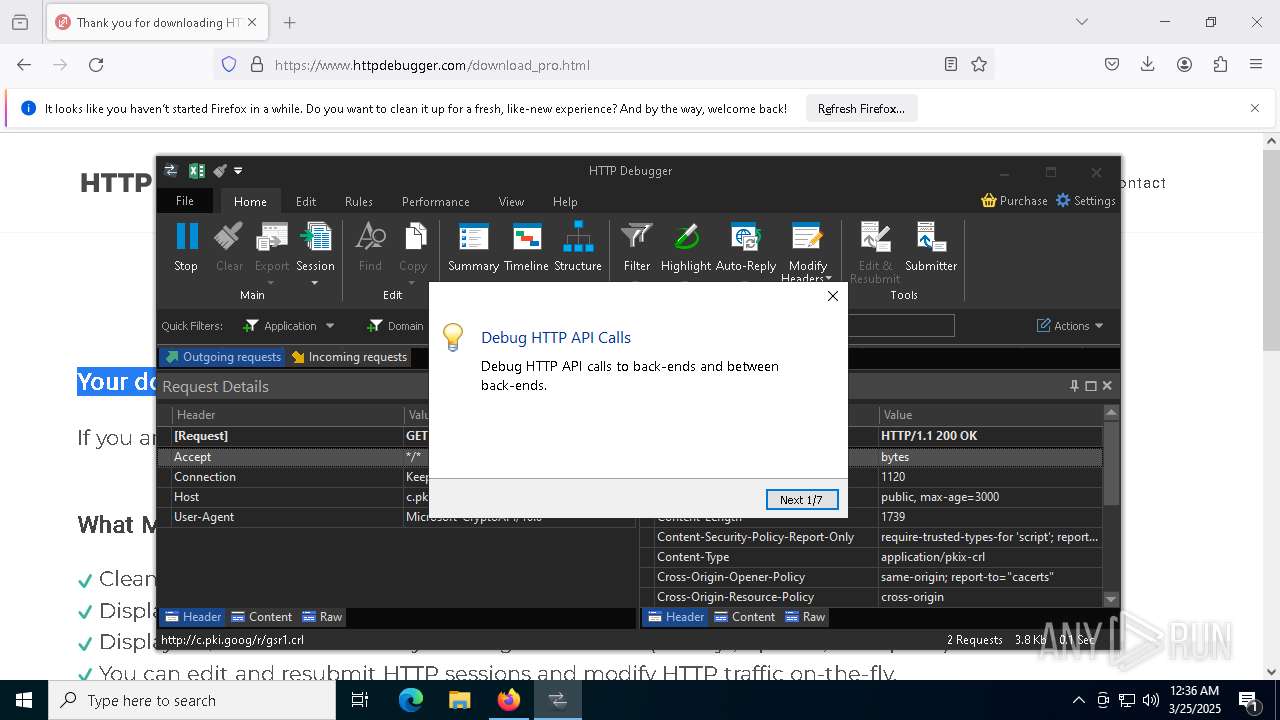
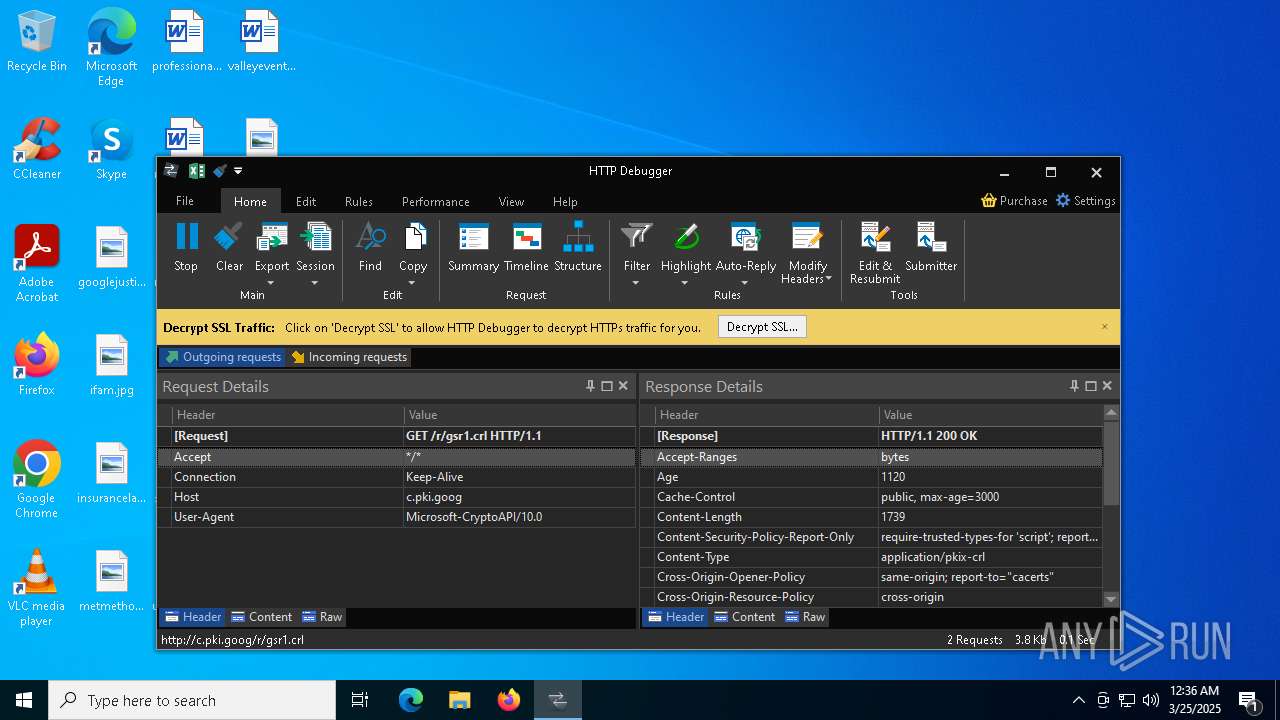
- HTTPDebuggerSvc.exe (PID: 4268)
CIPHERLOCKER has been detected
- CipherLocker.exe (PID: 2152)
SUSPICIOUS
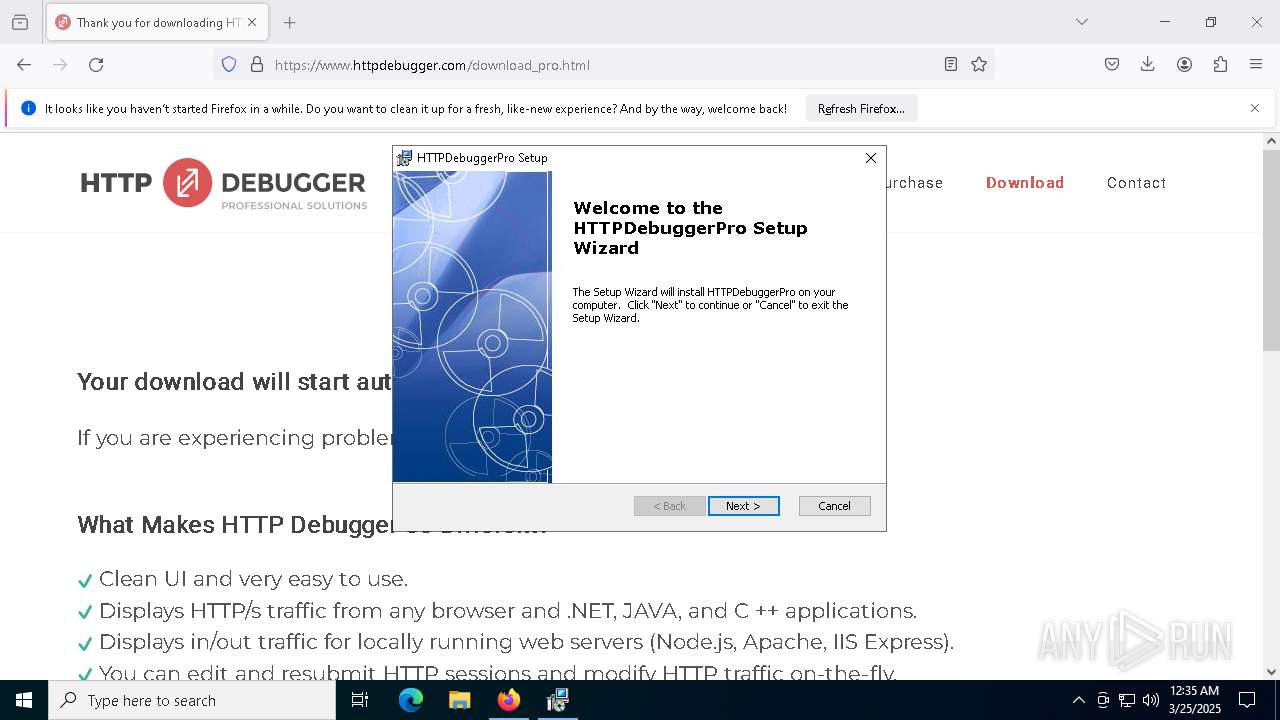
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 8292)
- msiexec.exe (PID: 8340)
Executes as Windows Service
- VSSVC.exe (PID: 8496)
- HTTPDebuggerSvc.exe (PID: 4268)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8340)
The process creates files with name similar to system file names
- msiexec.exe (PID: 8340)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 8340)
- HTTPDebuggerSvc.exe (PID: 4268)
Executable content was dropped or overwritten
- HTTPDebuggerSvc.exe (PID: 4268)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 7488)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 8380)
- HTTPDebuggerUI.exe (PID: 8092)
- ShellExperienceHost.exe (PID: 7916)
Reads Microsoft Outlook installation path
- HTTPDebuggerUI.exe (PID: 8092)
Reads Internet Explorer settings
- HTTPDebuggerUI.exe (PID: 8092)
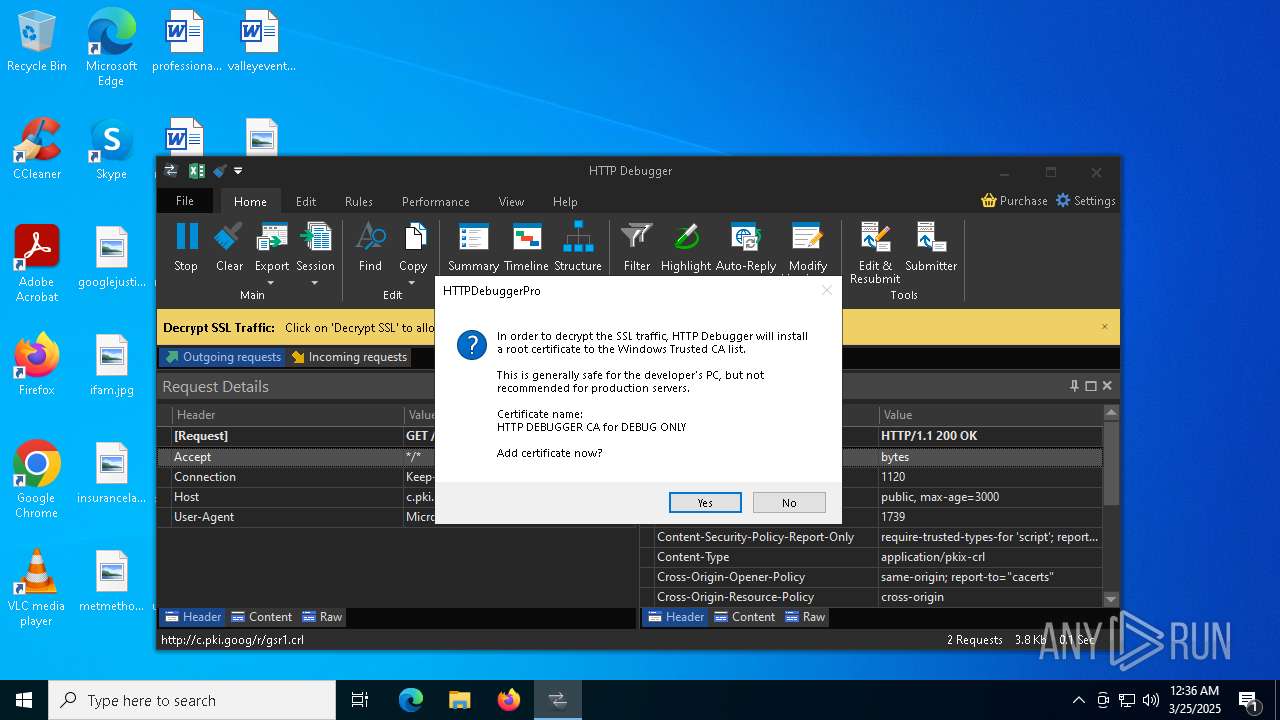
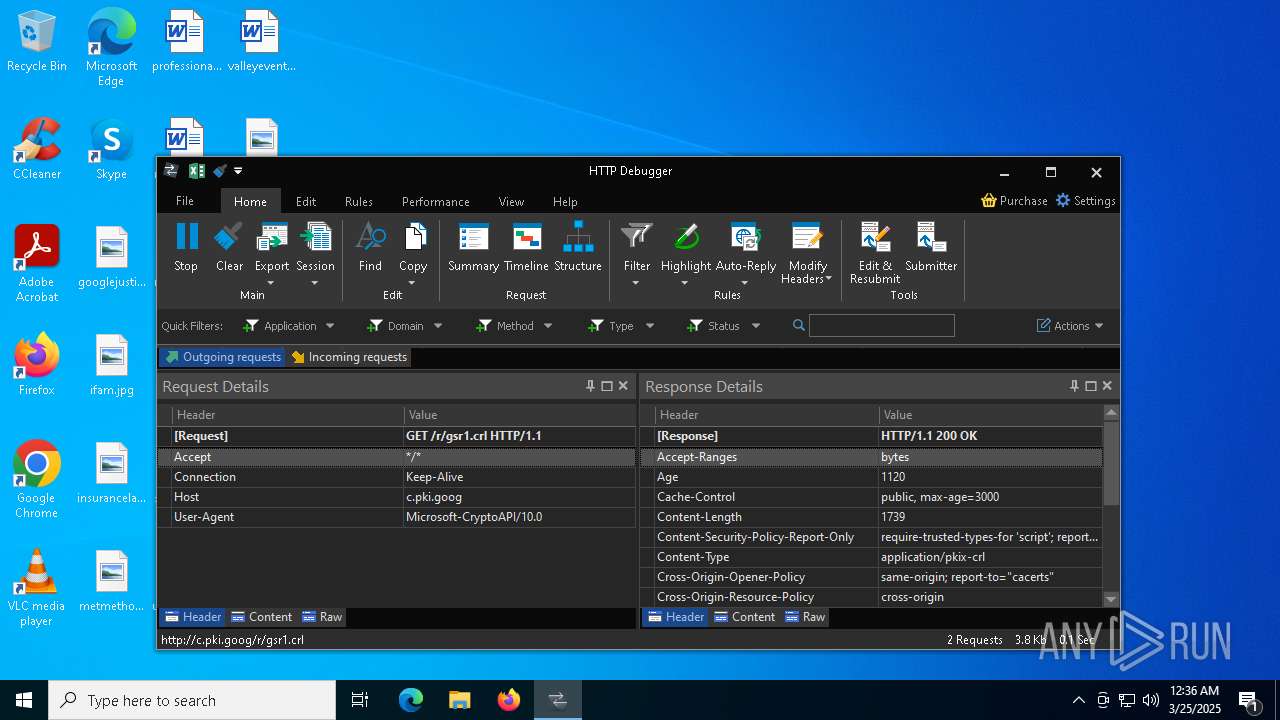
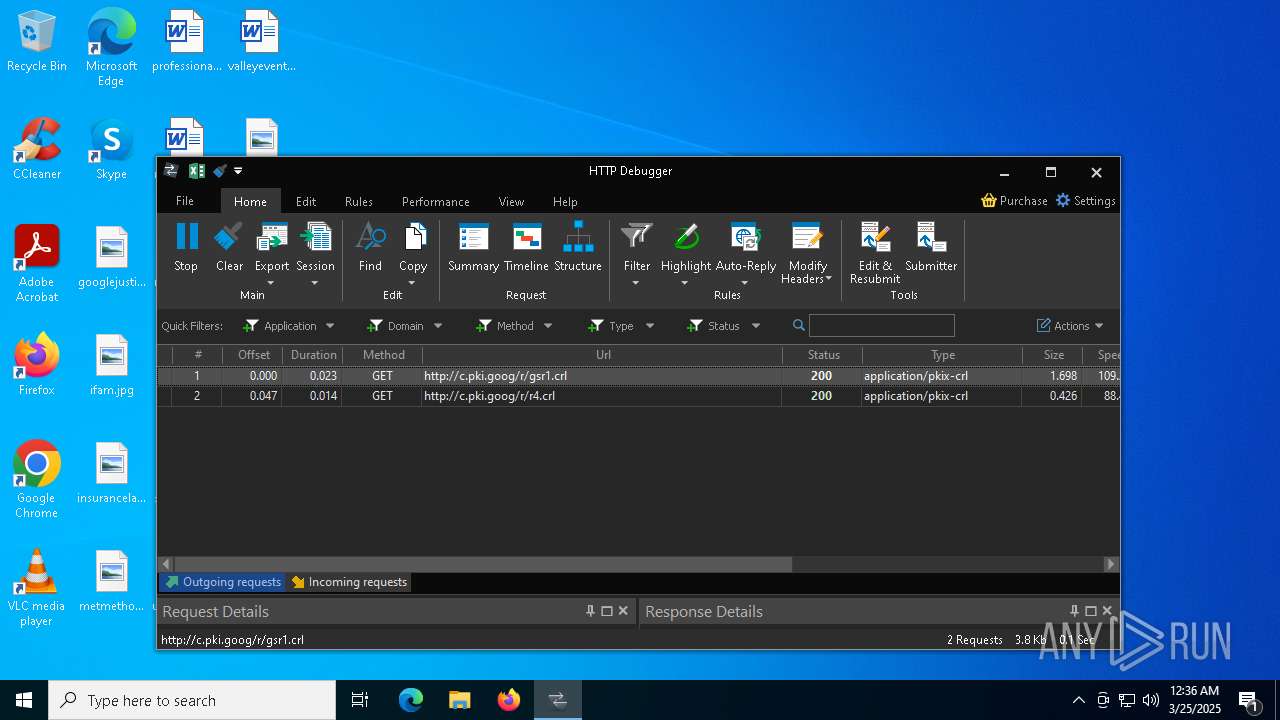
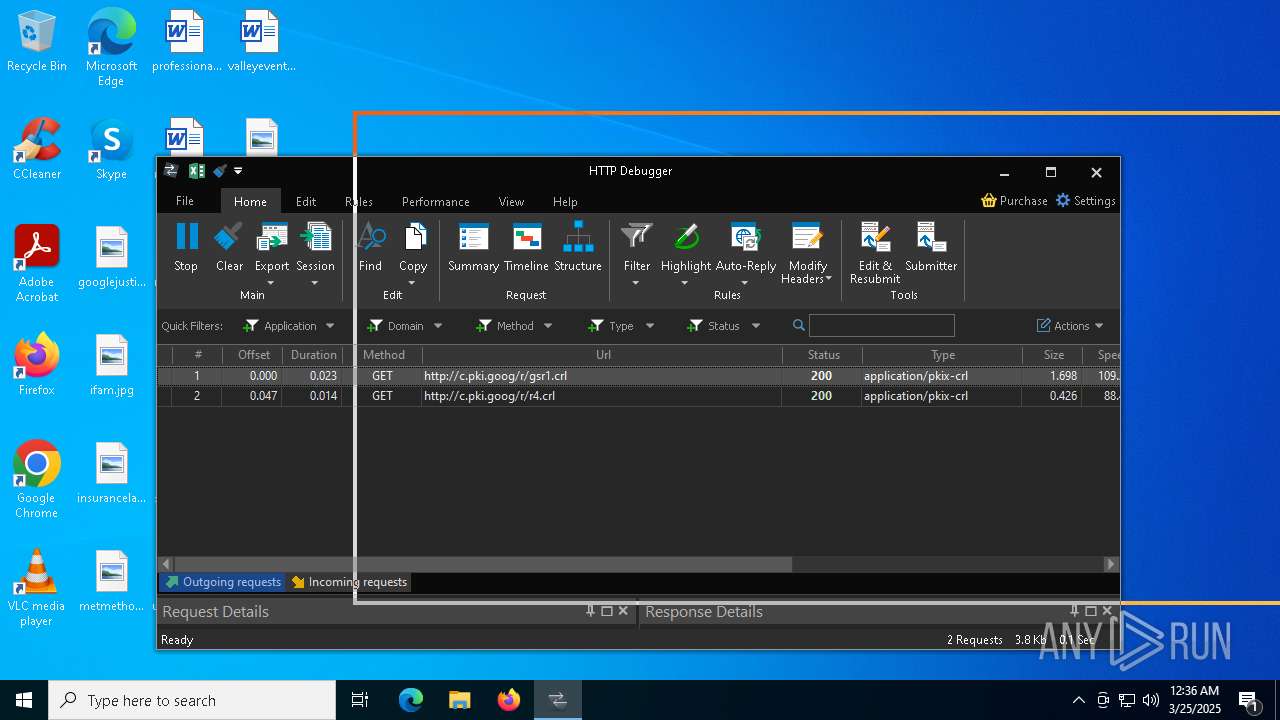
Adds/modifies Windows certificates
- HTTPDebuggerSvc.exe (PID: 4268)
There is functionality for taking screenshot (YARA)
- HTTPDebuggerUI.exe (PID: 8092)
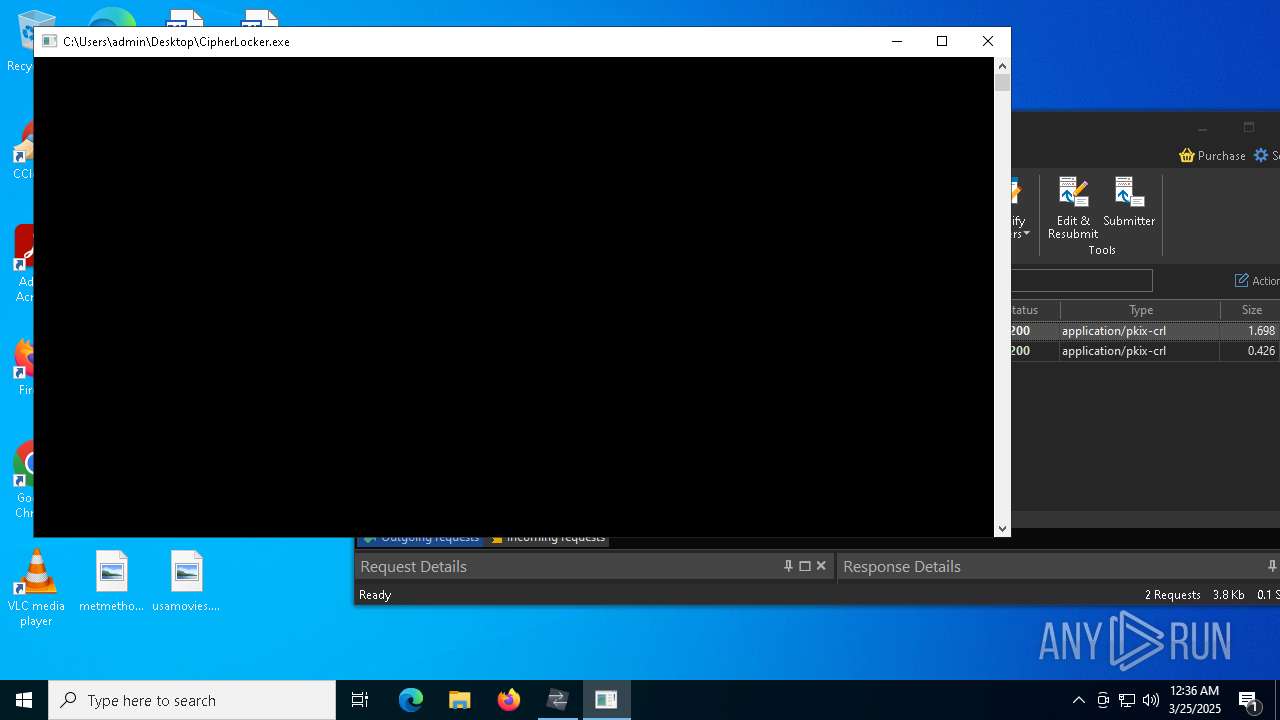
Starts CMD.EXE for commands execution
- CipherLocker.exe (PID: 2152)
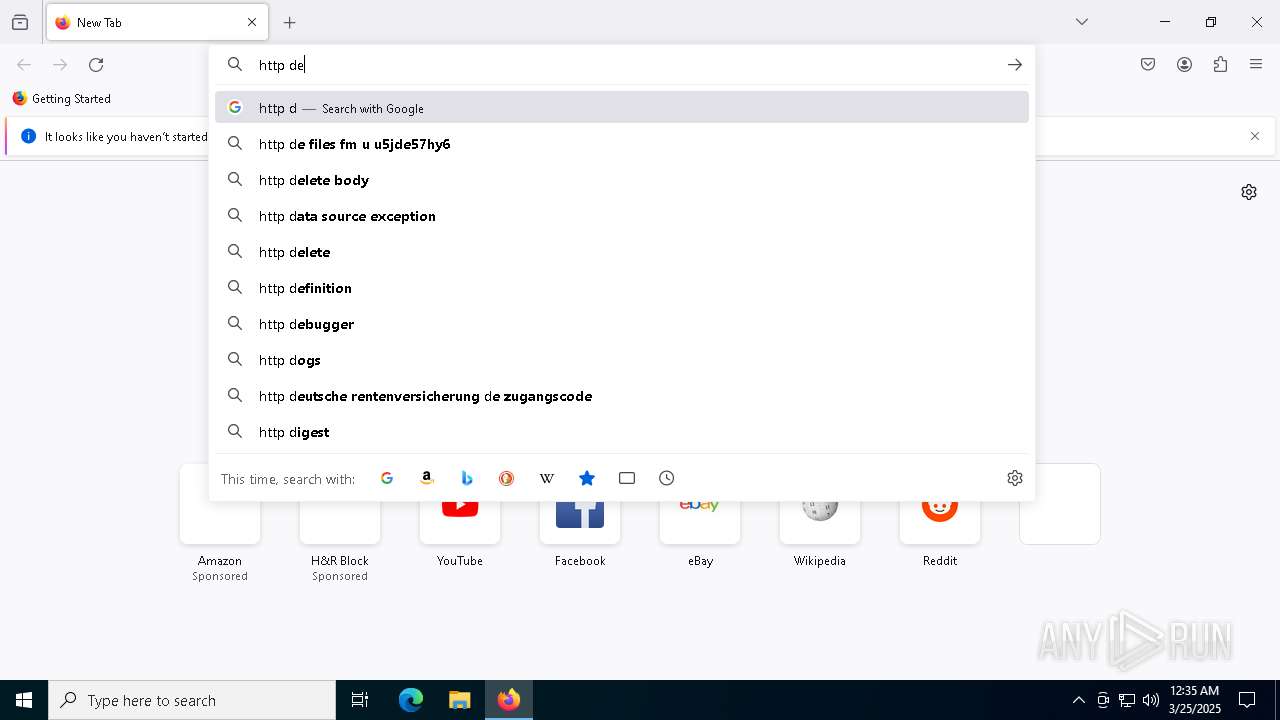
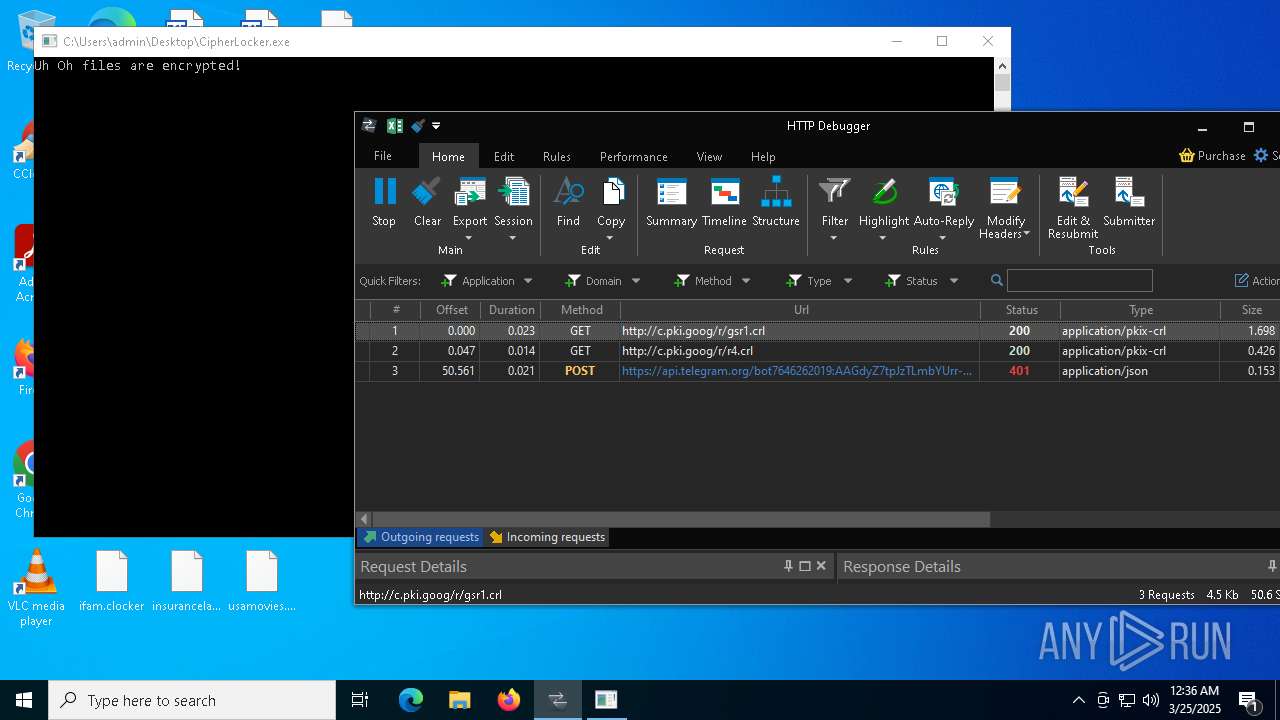
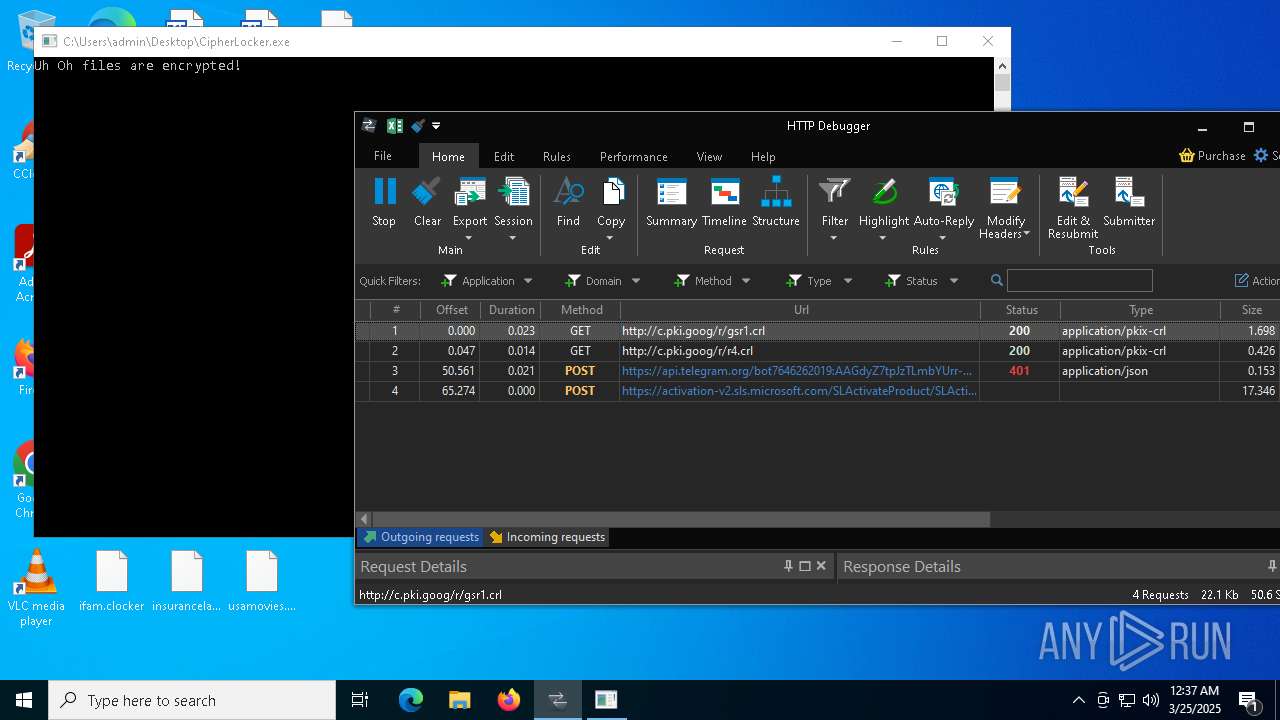
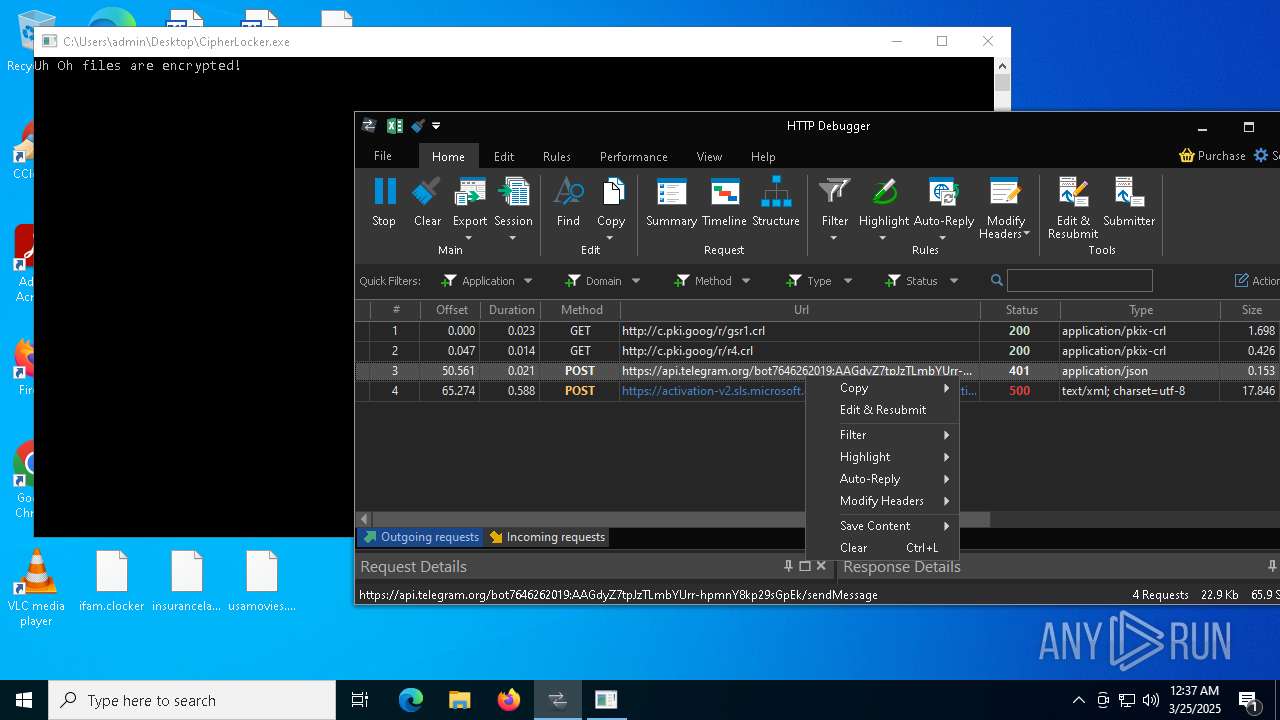
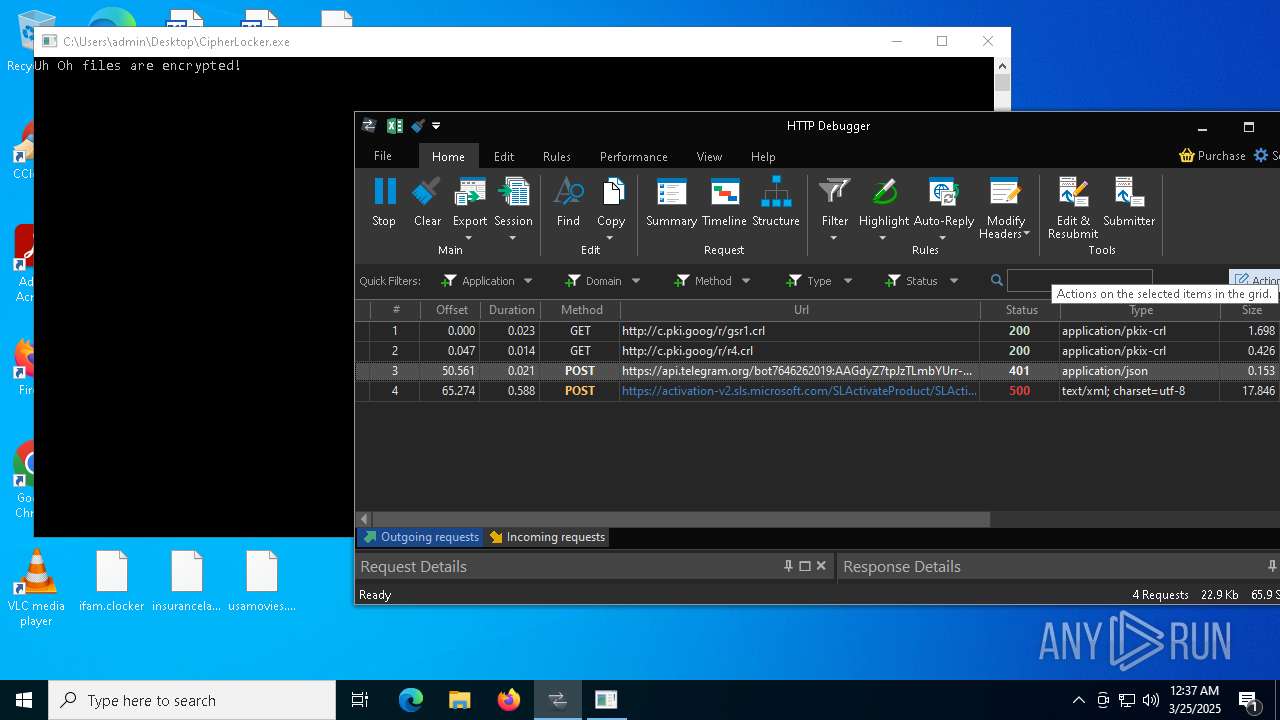
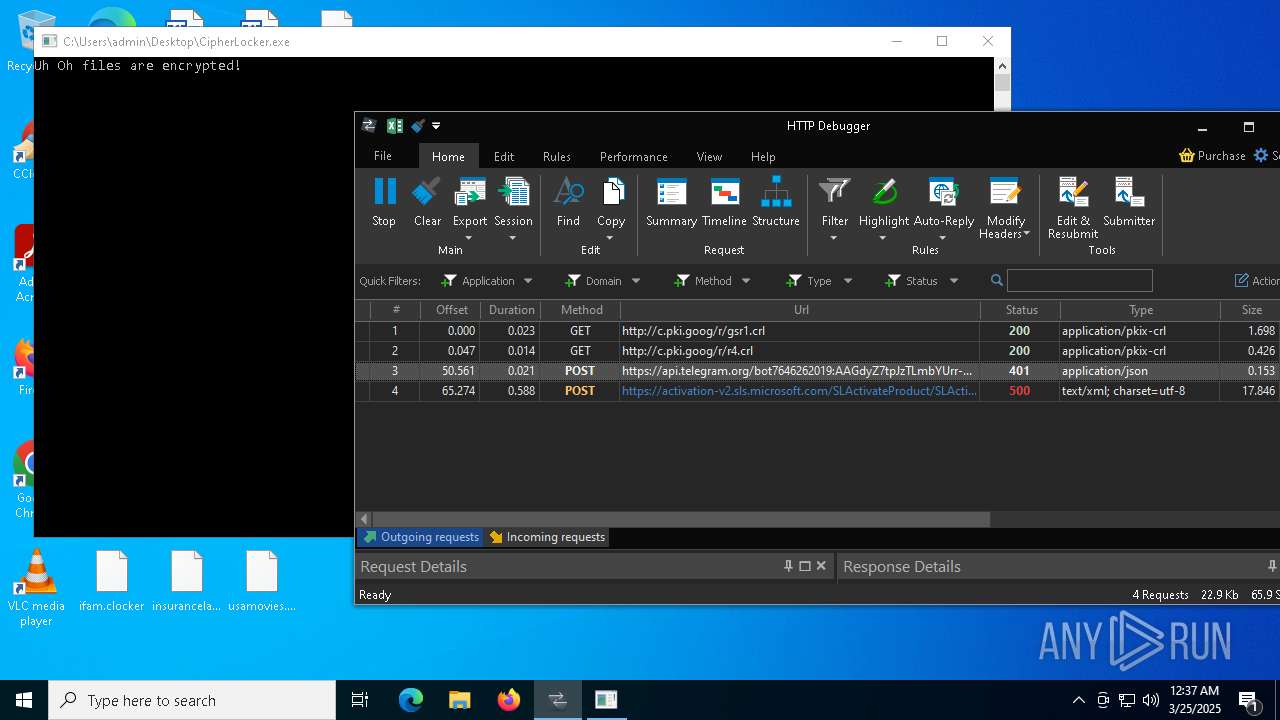
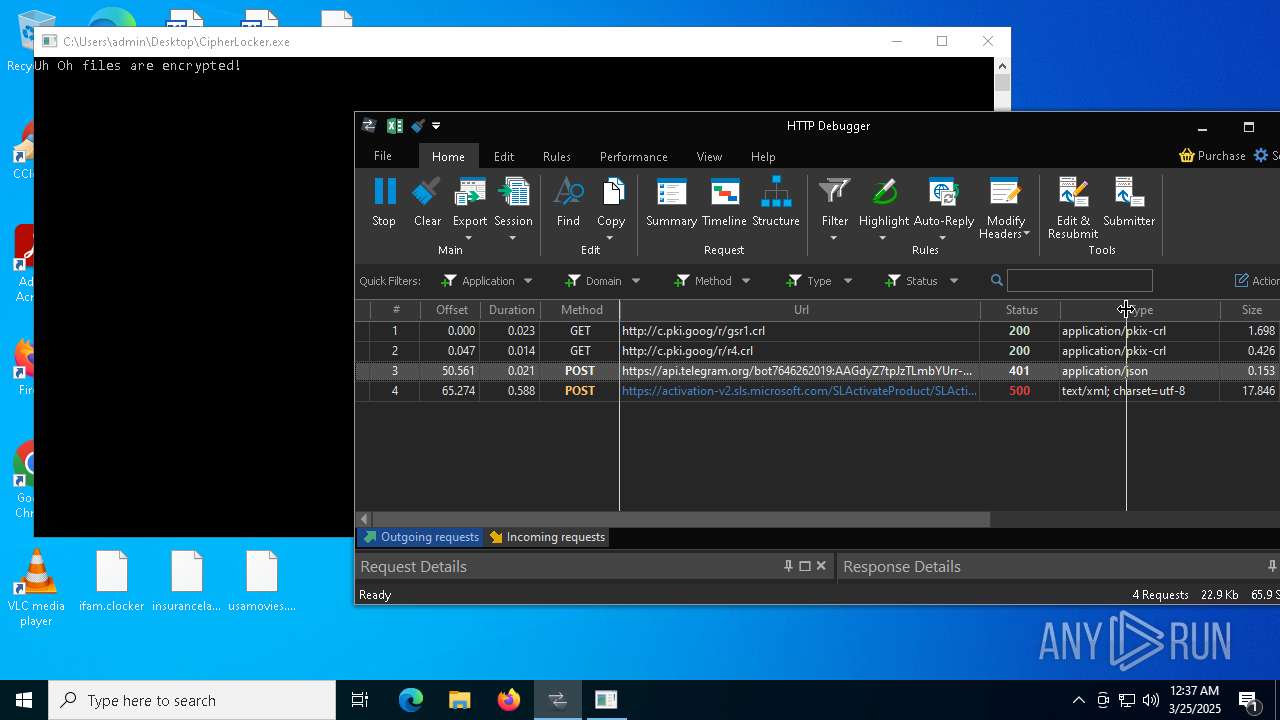
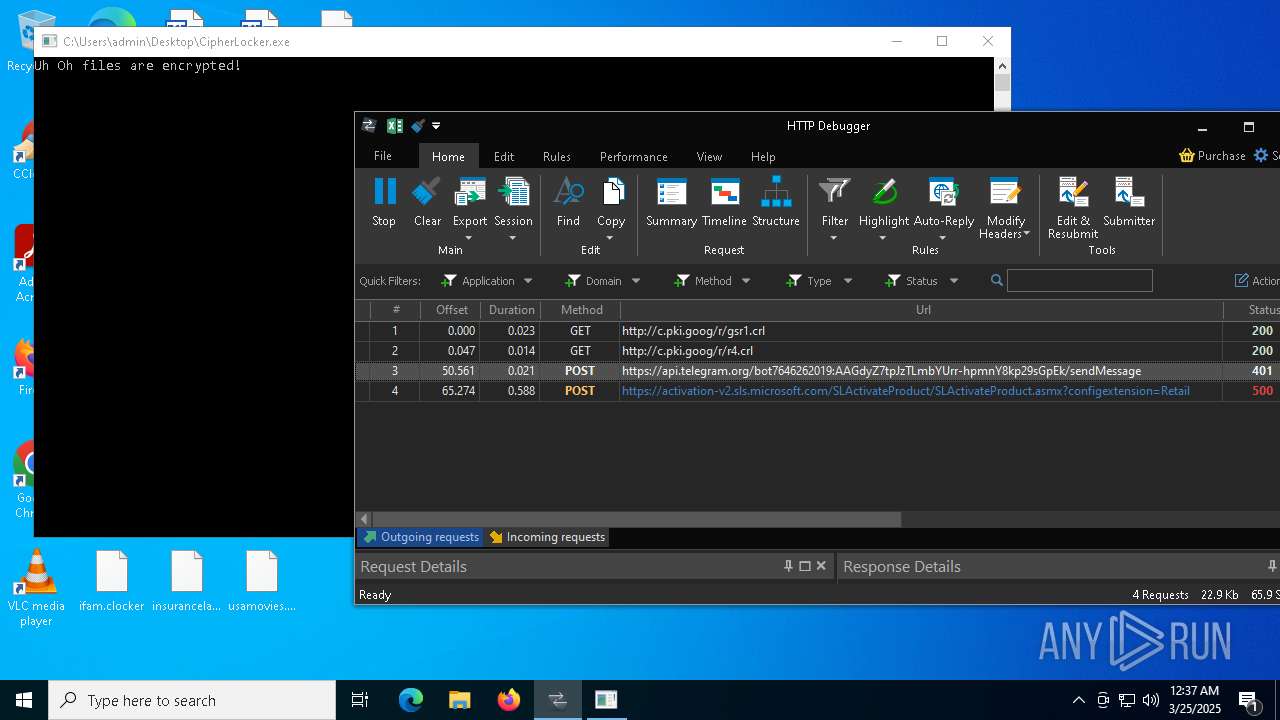
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- CipherLocker.exe (PID: 2152)
Creates files in the driver directory
- HTTPDebuggerSvc.exe (PID: 4268)
INFO
Checks supported languages
- CipherLocker.exe (PID: 7396)
- msiexec.exe (PID: 8380)
- msiexec.exe (PID: 8340)
- msiexec.exe (PID: 1512)
- HTTPDebuggerSvc.exe (PID: 4268)
- HTTPDebuggerUI.exe (PID: 8092)
- HTTPDebuggerSvc.exe (PID: 8420)
- ShellExperienceHost.exe (PID: 7916)
- certutil.exe (PID: 7000)
- CipherLocker.exe (PID: 2152)
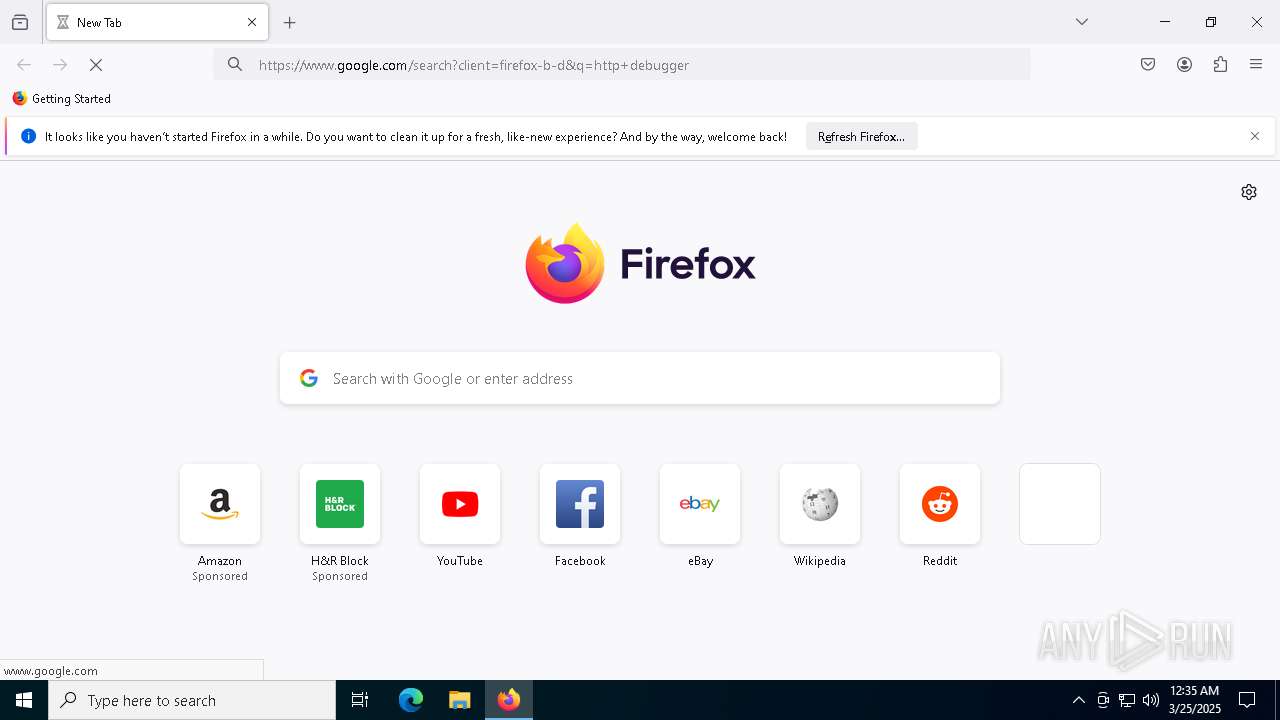
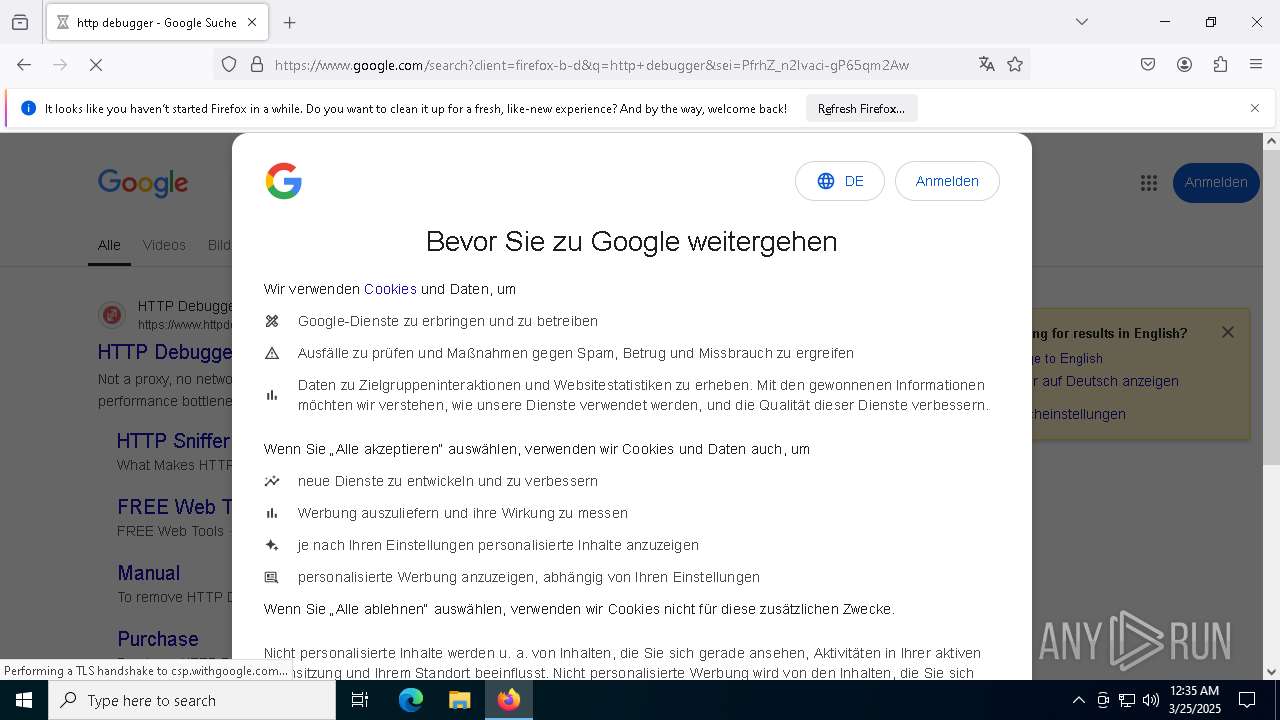
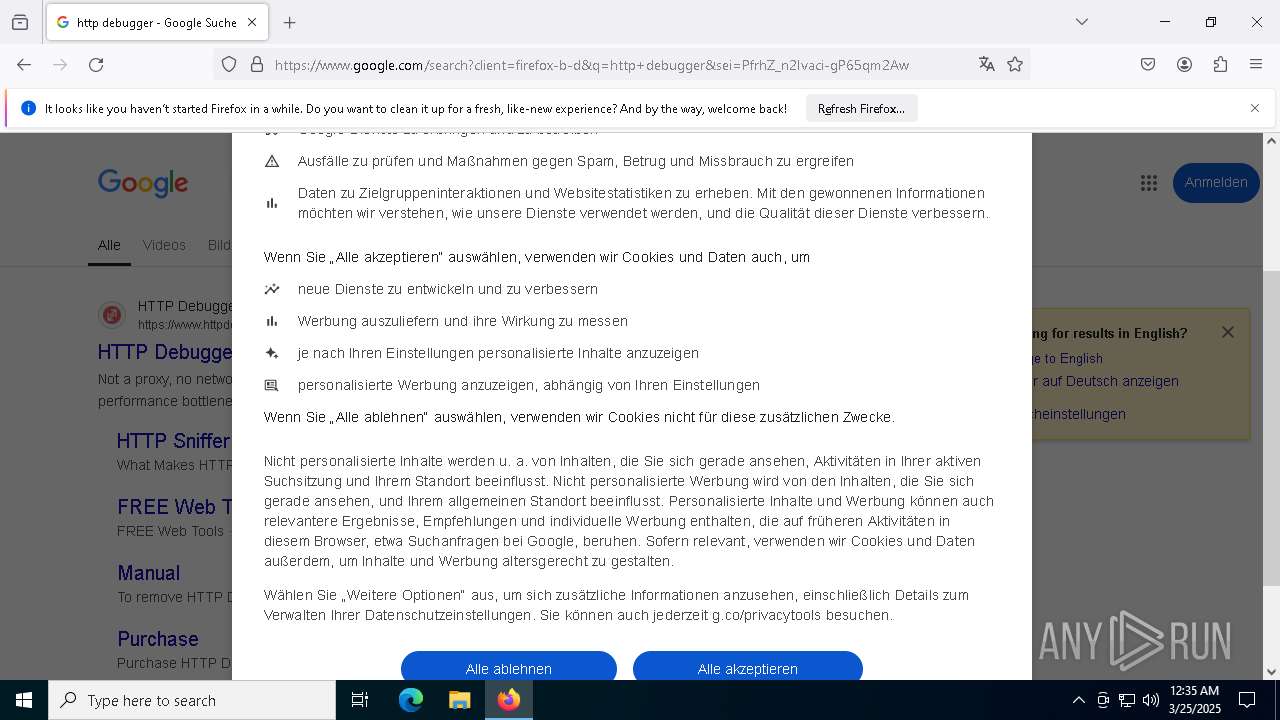
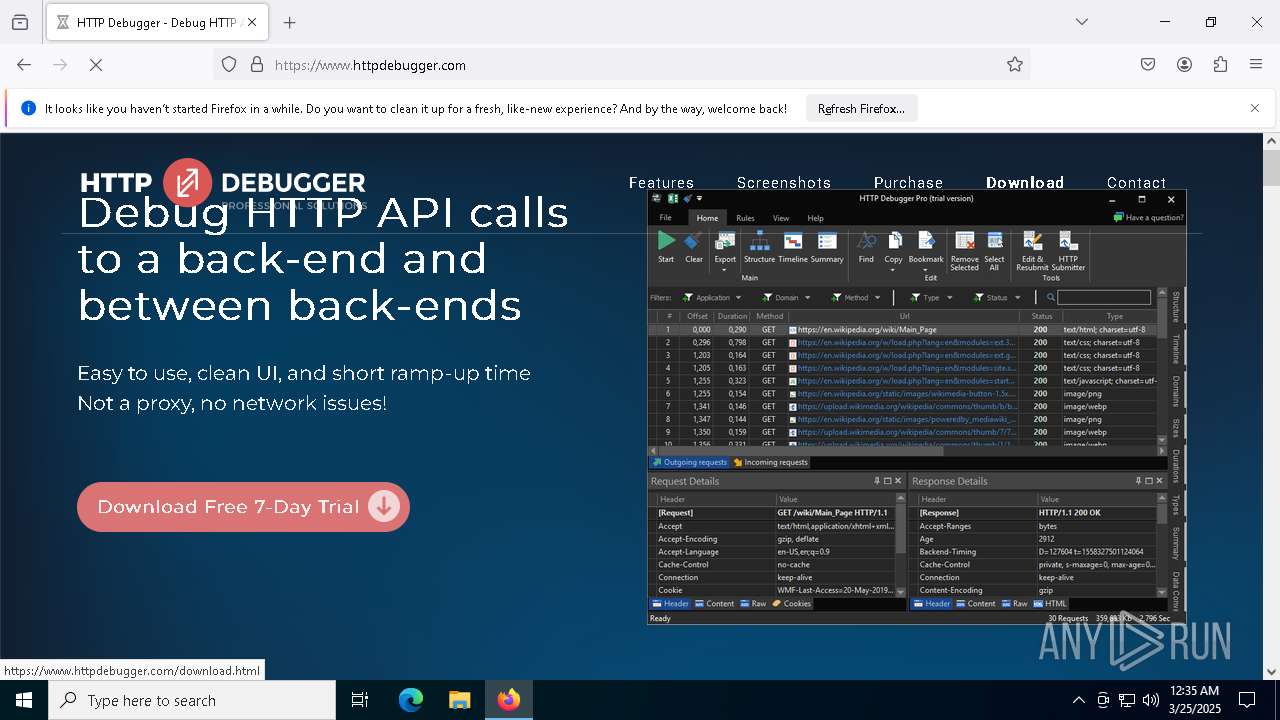
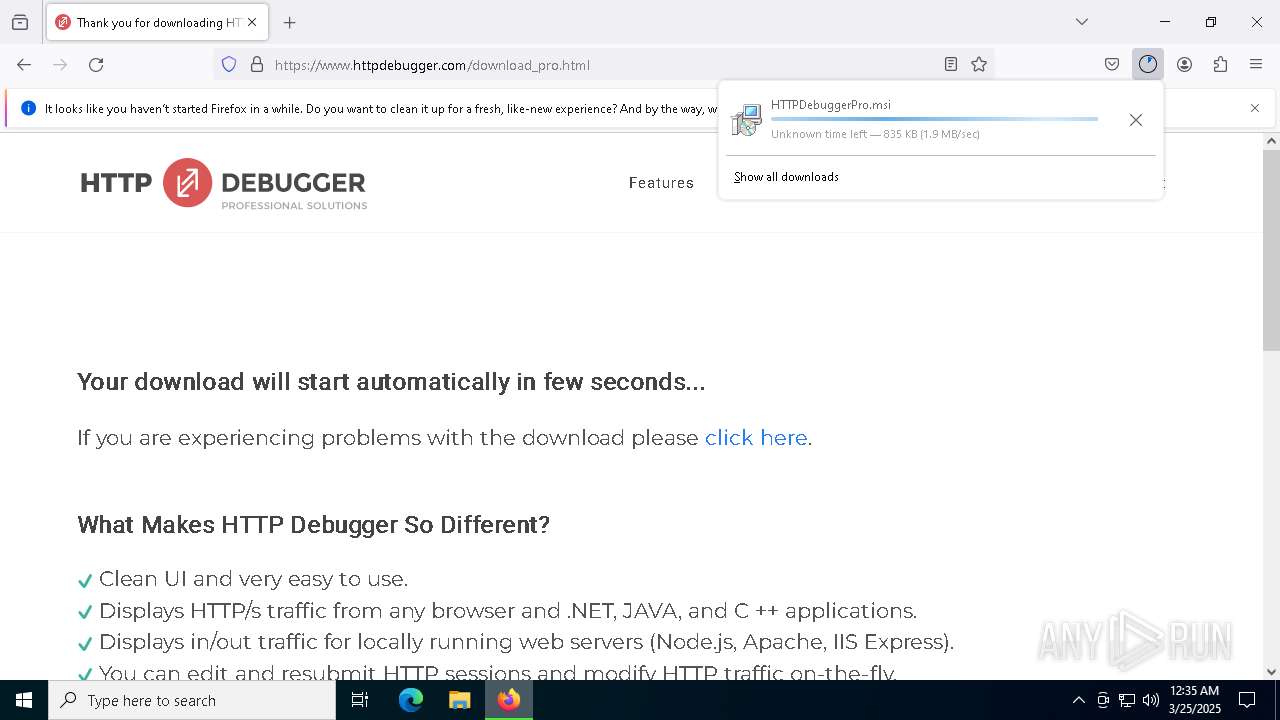
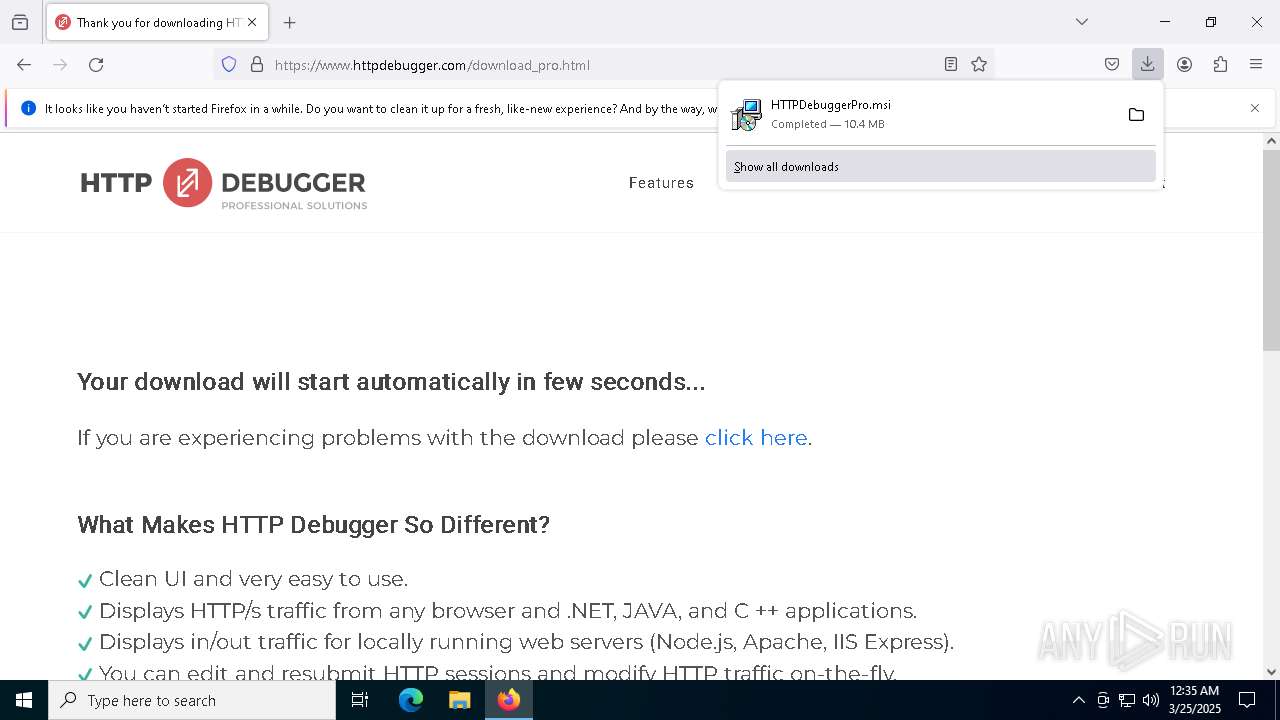
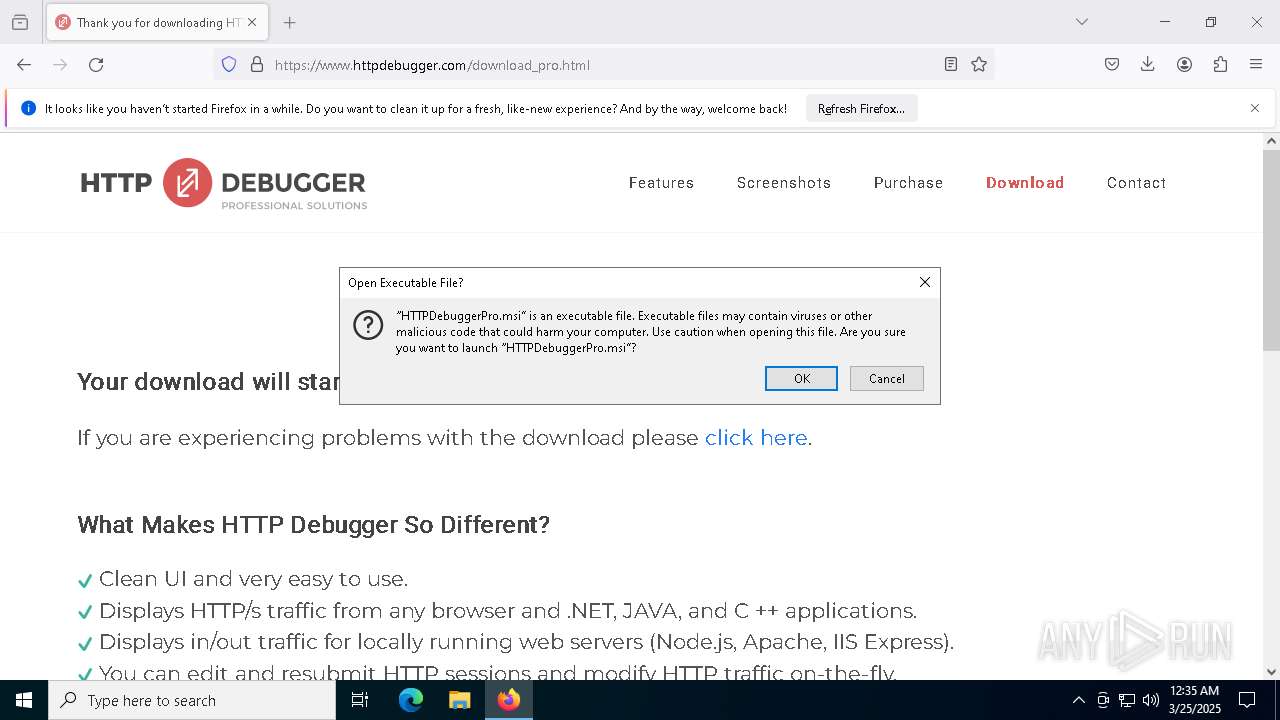
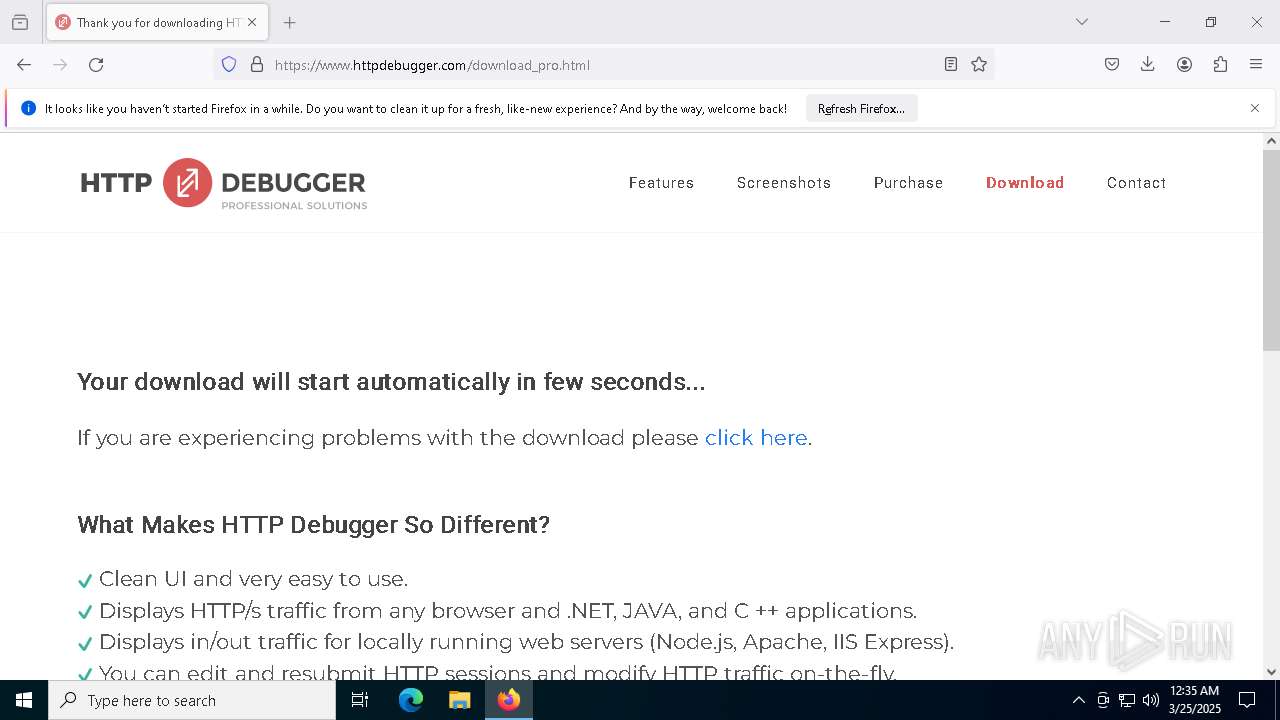
Manual execution by a user
- firefox.exe (PID: 8180)
Application launched itself
- firefox.exe (PID: 8180)
- firefox.exe (PID: 7180)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7784)
- BackgroundTransferHost.exe (PID: 7812)
- BackgroundTransferHost.exe (PID: 2268)
- explorer.exe (PID: 5492)
- msiexec.exe (PID: 8292)
- BackgroundTransferHost.exe (PID: 7820)
- BackgroundTransferHost.exe (PID: 7752)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 2268)
- explorer.exe (PID: 5492)
- HTTPDebuggerUI.exe (PID: 8092)
- CipherLocker.exe (PID: 2152)
- slui.exe (PID: 9020)
Reads the computer name
- CipherLocker.exe (PID: 7396)
- msiexec.exe (PID: 8380)
- msiexec.exe (PID: 8340)
- msiexec.exe (PID: 1512)
- HTTPDebuggerSvc.exe (PID: 4268)
- HTTPDebuggerSvc.exe (PID: 8420)
- HTTPDebuggerUI.exe (PID: 8092)
- ShellExperienceHost.exe (PID: 7916)
- certutil.exe (PID: 7000)
- CipherLocker.exe (PID: 2152)
Reads Microsoft Office registry keys
- explorer.exe (PID: 5492)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 2268)
- explorer.exe (PID: 5492)
- msiexec.exe (PID: 8292)
- msiexec.exe (PID: 8340)
- slui.exe (PID: 7528)
- HTTPDebuggerUI.exe (PID: 8092)
- CipherLocker.exe (PID: 2152)
- slui.exe (PID: 9020)
Creates files or folders in the user directory
- explorer.exe (PID: 5492)
- BackgroundTransferHost.exe (PID: 2268)
- HTTPDebuggerUI.exe (PID: 8092)
Autorun file from Downloads
- firefox.exe (PID: 7180)
The sample compiled with english language support
- msiexec.exe (PID: 8292)
- msiexec.exe (PID: 8340)
- HTTPDebuggerSvc.exe (PID: 4268)
Manages system restore points
- SrTasks.exe (PID: 9008)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8292)
- msiexec.exe (PID: 8340)
Reads the machine GUID from the registry
- msiexec.exe (PID: 8340)
- HTTPDebuggerSvc.exe (PID: 4268)
- HTTPDebuggerSvc.exe (PID: 8420)
- HTTPDebuggerUI.exe (PID: 8092)
- CipherLocker.exe (PID: 2152)
Creates a software uninstall entry
- msiexec.exe (PID: 8340)
Process checks computer location settings
- msiexec.exe (PID: 8380)
Creates files in the program directory
- HTTPDebuggerSvc.exe (PID: 4268)
Local mutex for internet shortcut management
- explorer.exe (PID: 5492)
Disables trace logs
- CipherLocker.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2083:10:07 15:03:22+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 29184 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x91f6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | CipherLocker |
| FileVersion: | 1.0.0.0 |
| InternalName: | CipherLocker.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | CipherLocker.exe |
| ProductName: | CipherLocker |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
186
Monitored processes
43
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1908 -parentBuildID 20240213221259 -prefsHandle 1844 -prefMapHandle 1836 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {7963b4df-7af6-44fb-84b7-d3b23d402419} 7180 "\\.\pipe\gecko-crash-server-pipe.7180" 2b2af7f1510 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 1512 | C:\Windows\syswow64\MsiExec.exe -Embedding D607138AB39354B6925DFBDABB7D5C88 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6200 -childID 10 -isForBrowser -prefsHandle 6208 -prefMapHandle 6212 -prefsLen 31366 -prefMapSize 244583 -jsInitHandle 1456 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {03e23d26-e49c-4842-87c5-bc8bc1d1c597} 7180 "\\.\pipe\gecko-crash-server-pipe.7180" 2b2b87fa150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\Desktop\CipherLocker.exe" | C:\Users\admin\Desktop\CipherLocker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: CipherLocker Version: 1.0.0.0 Modules
| |||||||||||||||
| 2268 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | "cmd.exe" /C vssadmin delete shadows /for=c: /quiet /ignorewarnings /noprompt | C:\Windows\SysWOW64\cmd.exe | — | CipherLocker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5736 -childID 7 -isForBrowser -prefsHandle 5824 -prefMapHandle 5828 -prefsLen 31285 -prefMapSize 244583 -jsInitHandle 1456 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {67b96197-f34d-4319-9ca1-7b2cd8d9734a} 7180 "\\.\pipe\gecko-crash-server-pipe.7180" 2b2ba27df50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4268 | "C:\Program Files (x86)\HTTPDebuggerPro\HTTPDebuggerSvc.exe" | C:\Program Files (x86)\HTTPDebuggerPro\HTTPDebuggerSvc.exe | services.exe | ||||||||||||
User: SYSTEM Company: HttpDebugger.com Integrity Level: SYSTEM Description: HTTP Debugger Windows Service Version: 9.0.0.12 Modules
| |||||||||||||||
| 4776 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2156 -parentBuildID 20240213221259 -prefsHandle 2148 -prefMapHandle 2120 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {836835de-6956-4ae1-a5d8-9cf2d979e077} 7180 "\\.\pipe\gecko-crash-server-pipe.7180" 2b2a2981b10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 5492 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
50 038
Read events
49 608
Write events
403
Delete events
27
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:00000000000802D2 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010015000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C000000150000000000000067006F006F0067006C0065006A007500730074006900630065002E0070006E0067003E002000200000000C000000000000006900660061006D002E006A00700067003E00200020000000160000000000000069006E0073007500720061006E00630065006C0061007400650072002E006A00700067003E0020002000000011000000000000006D00650074006D006500740068006F0064002E0070006E0067003E002000200000001B00000000000000700072006F00660065007300730069006F006E0061006C007400690063006B006500740073002E007200740066003E002000200000001500000000000000720061007000650064006500760065006C006F007000650064002E007200740066003E0020002000000017000000000000007200750073007300690061006E00720065006C00650061007300650073002E007200740066003E0020002000000016000000000000007300650061007200630068006500730065006E006F007500670068002E007200740066003E0020002000000014000000000000007300650078006300680061007200610063007400650072002E007200740066003E0020002000000011000000000000007500730061006D006F0076006900650073002E006A00700067003E002000200000001300000000000000760061006C006C00650079006500760065006E0074002E007200740066003E002000200000000F000000000000007700650062006F006F006B0073002E006A00700067003E0020002000000014000000000000004300690070006800650072004C006F0063006B00650072002E006500780065003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001500000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A040110000004040000000001200000040400000803F1300000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F070000004040000000401400 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 32FAE16700000000 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:00000000000802D2 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:00000000000A02D2 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppLaunch |
| Operation: | write | Name: | 308046B0AF4A39CB |
Value: 15 | |||
| (PID) Process: | (7180) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | write | Name: | 308046B0AF4A39CB |
Value: 21 | |||
| (PID) Process: | (7784) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
28
Suspicious files
264
Text files
31
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7180 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7180 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5492 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 7180 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7180 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7180 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:C216A4F2E4F533C14AC8C4A1B432705D | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
| 7180 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7180 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7180 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\activity-stream.discovery_stream.json.tmp | binary | |
MD5:A682F6318B2FC3843BDB7C8B775724F6 | SHA256:33B411AD792F857E0C8C4514E18C522543676802E31E85DCCAFF7C4A1C9F3E61 | |||
| 7180 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
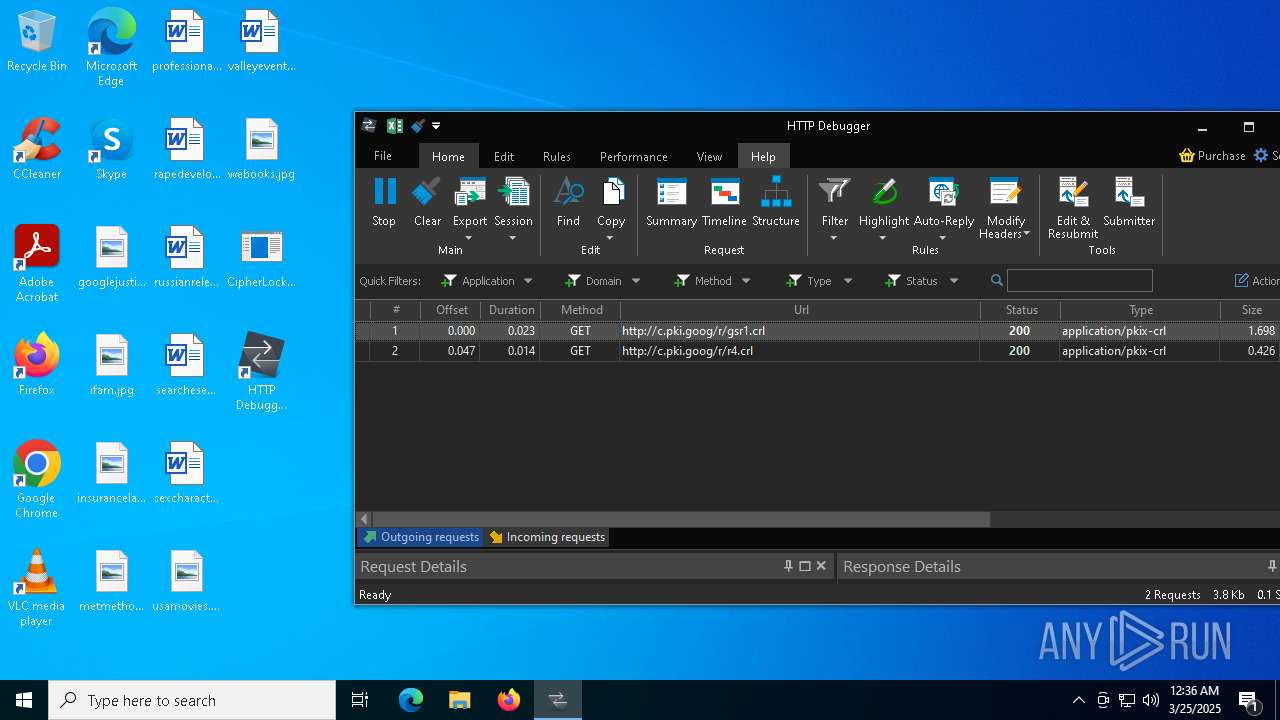
HTTP(S) requests
64
TCP/UDP connections
157
DNS requests
172
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7180 | firefox.exe | POST | 200 | 2.23.82.57:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7180 | firefox.exe | POST | 200 | 2.23.82.9:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7180 | firefox.exe | POST | 200 | 2.23.82.57:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7180 | firefox.exe | POST | 200 | 2.23.82.9:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7180 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7180 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7180 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/s/wr3/UTA | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7180 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7748 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
2152 | CipherLocker.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2152 | CipherLocker.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |