| File name: | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe |
| Full analysis: | https://app.any.run/tasks/581b01e1-be7b-4c3f-9ede-33f658ad6c76 |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | June 21, 2025, 20:40:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 4AB096EB513EED62B9206FB8AB273ABA |
| SHA1: | 15CA16C266031C2C03A050D53841410DC5476E44 |
| SHA256: | 989DB46562126CD83B6148DA103CB17D770ED14C5A09B899BD225E77FF1B054D |
| SSDEEP: | 24576:6PO+SPEyIHfePHfoHtq2+kVNDs966J9LRkAZOFOavGzNiG31eK4Mre:6PO+SPEyIHfePHfoHtq2+uN4966J9LRI |
MALICIOUS
REDLINE has been found (auto)
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
REDLINE has been detected (YARA)
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 7284)
SUSPICIOUS
Reads security settings of Internet Explorer
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
Application launched itself
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
Connects to unusual port
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 7284)
Reads Microsoft Outlook installation path
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
Multiple wallet extension IDs have been found
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 7284)
INFO
Reads the computer name
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 7284)
Checks supported languages
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 7284)
Reads the machine GUID from the registry
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 7284)
Reads the software policy settings
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
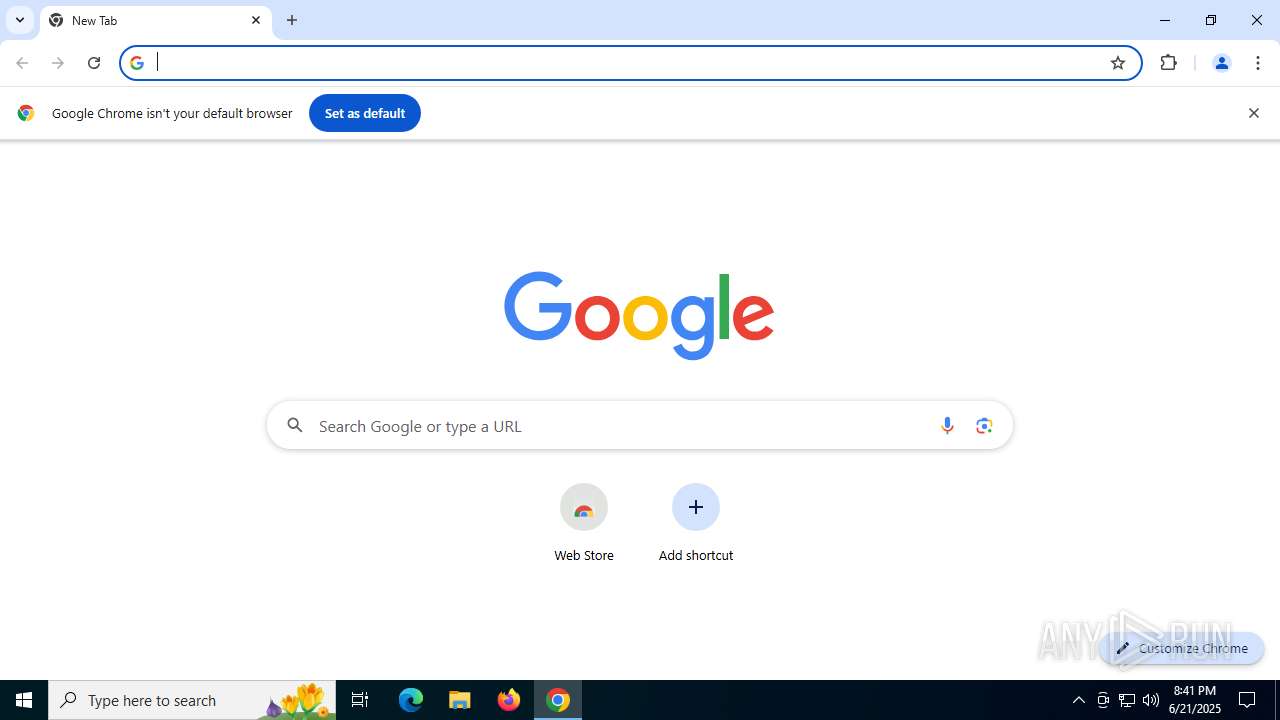
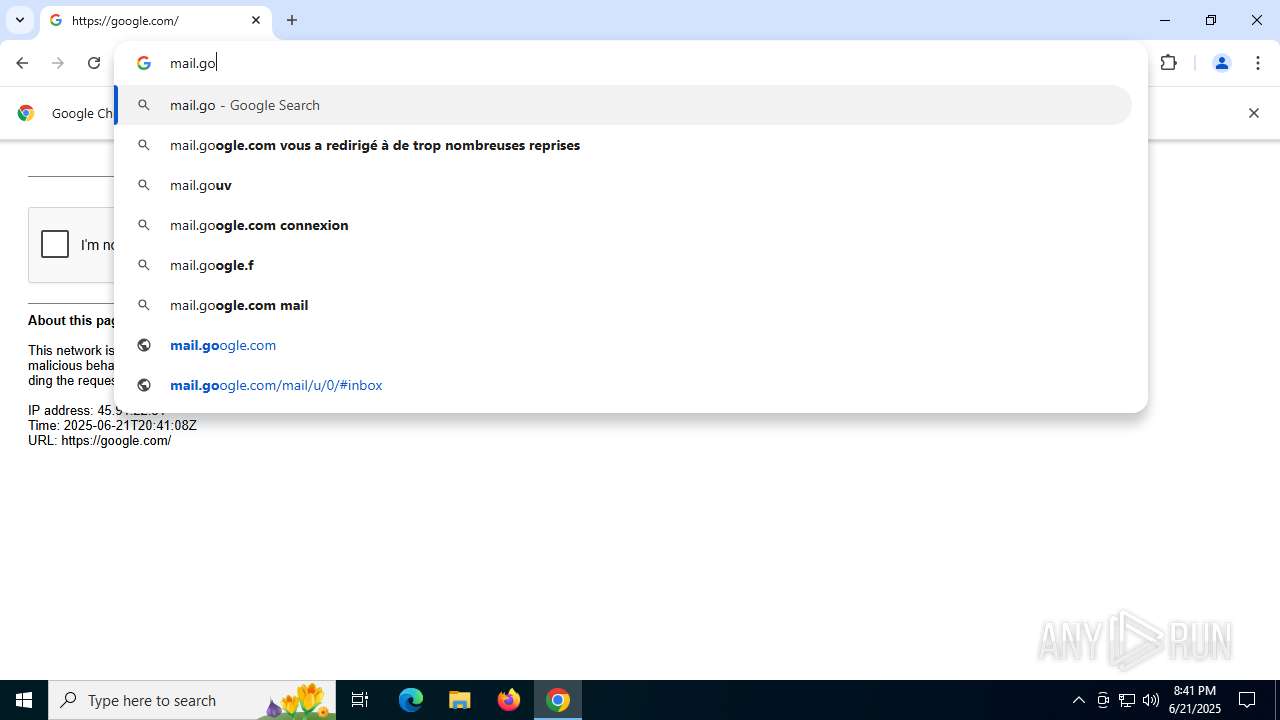
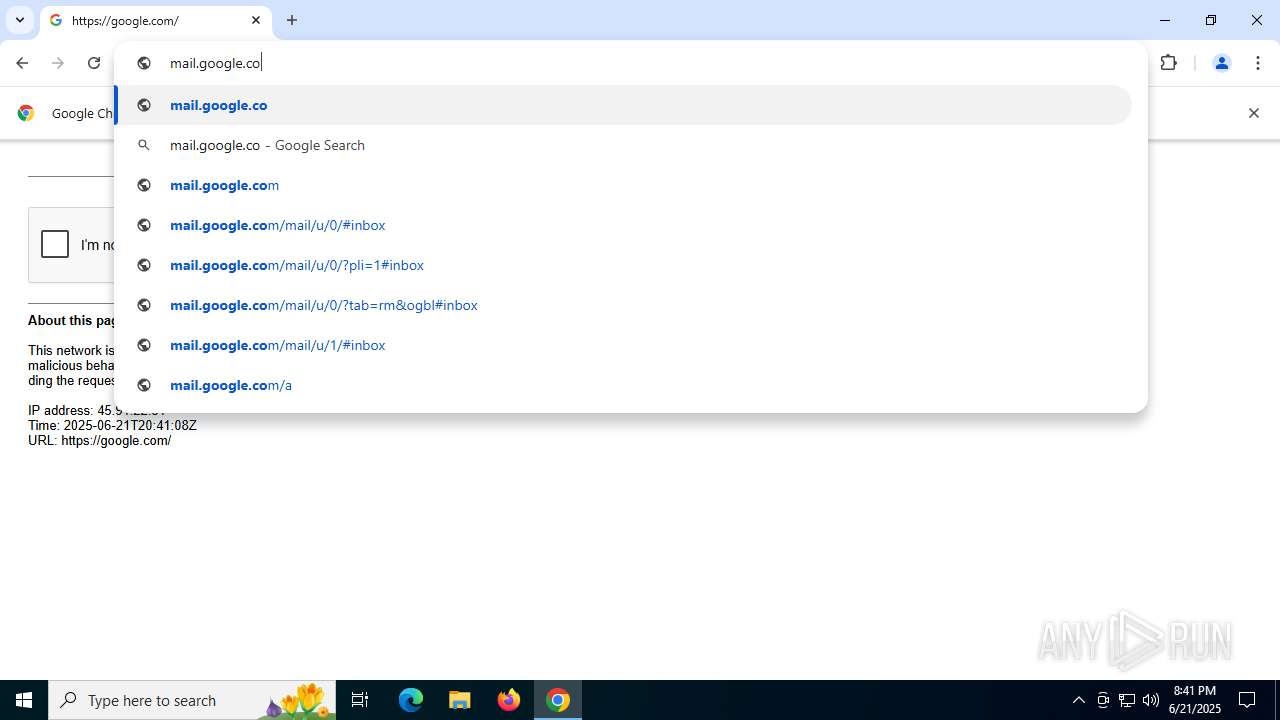
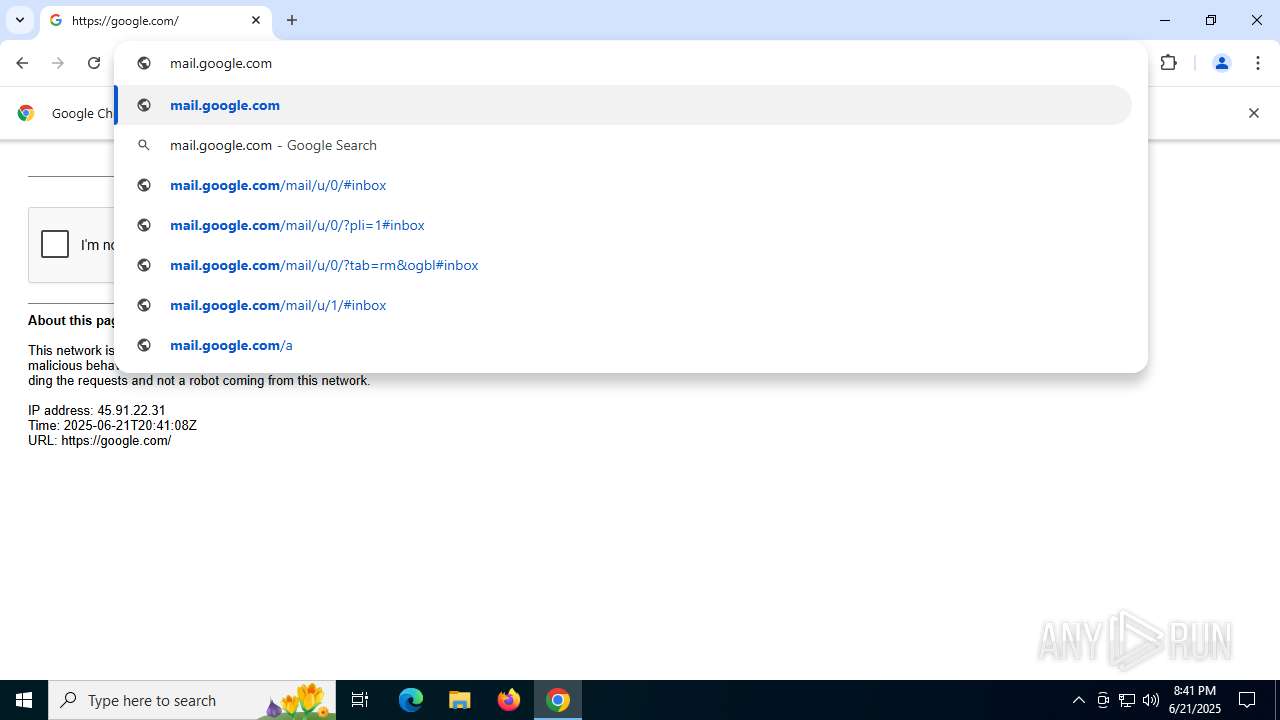
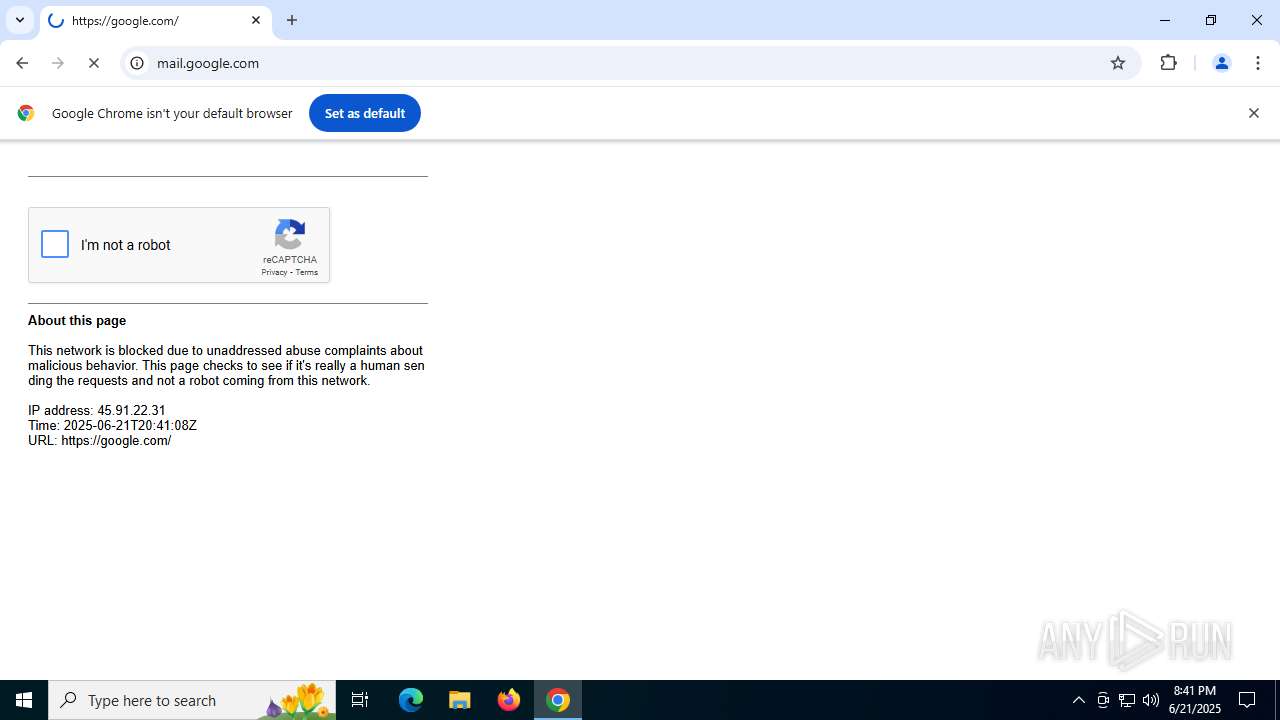
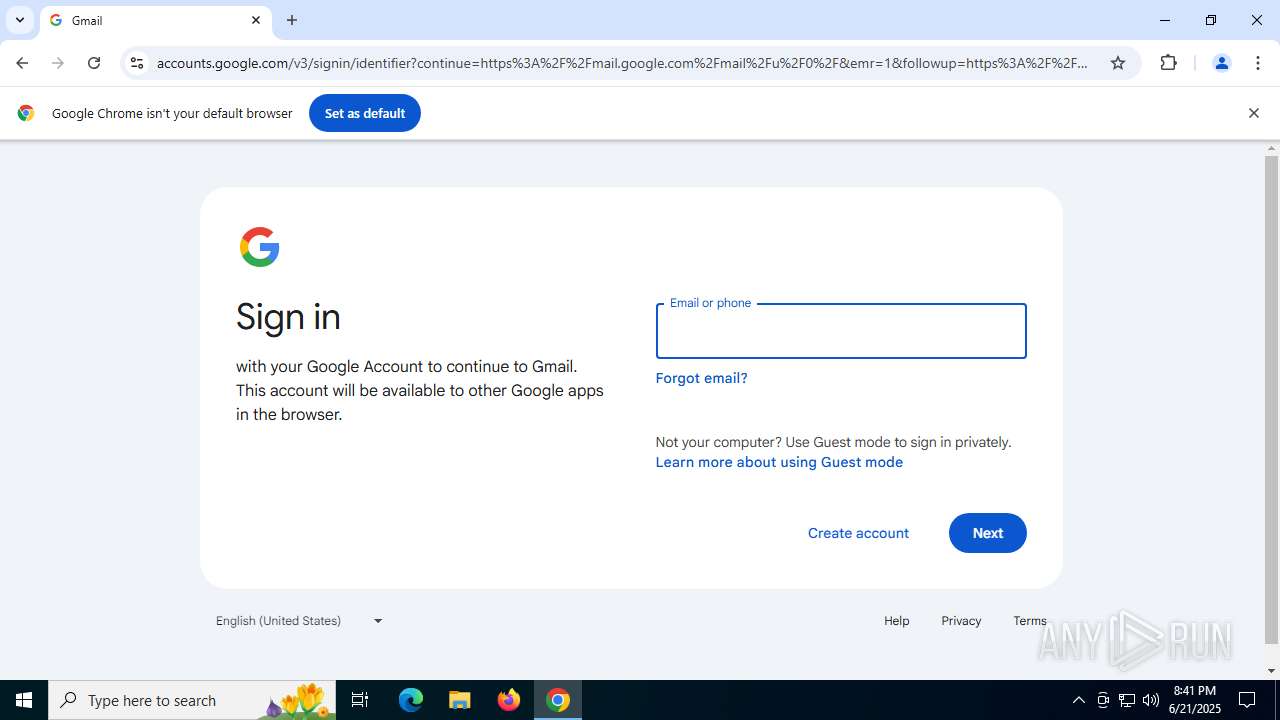
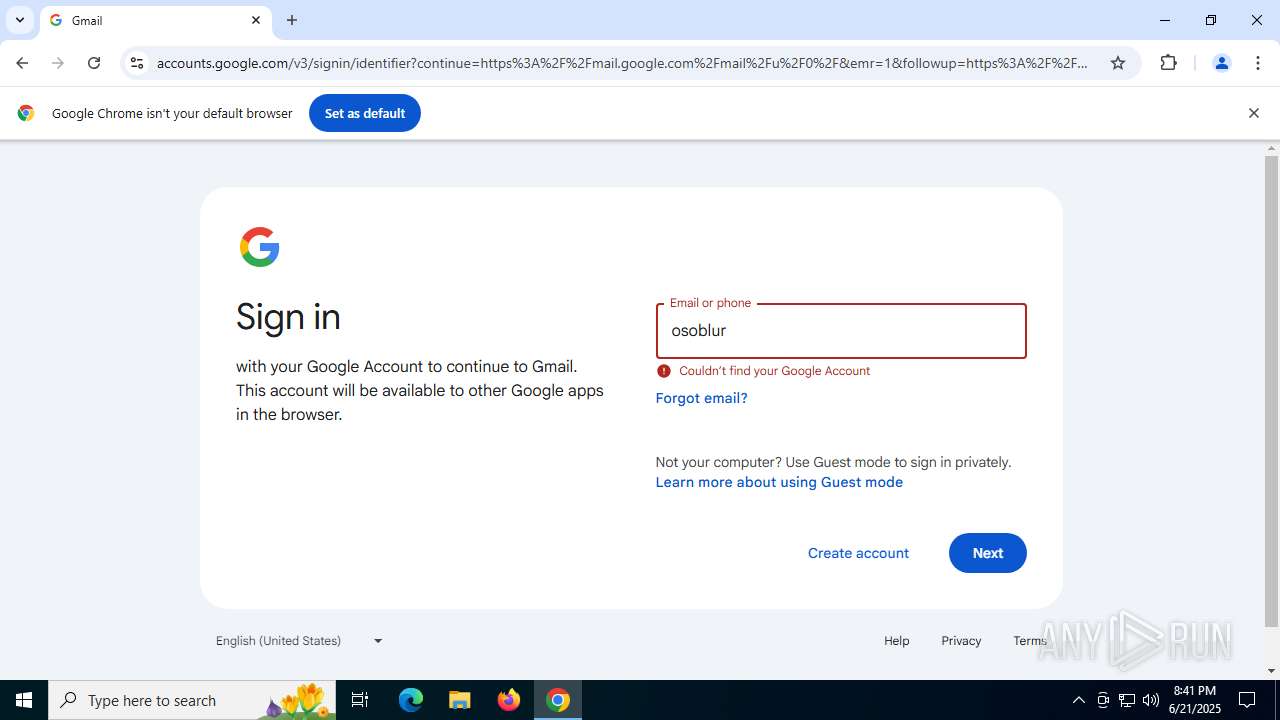
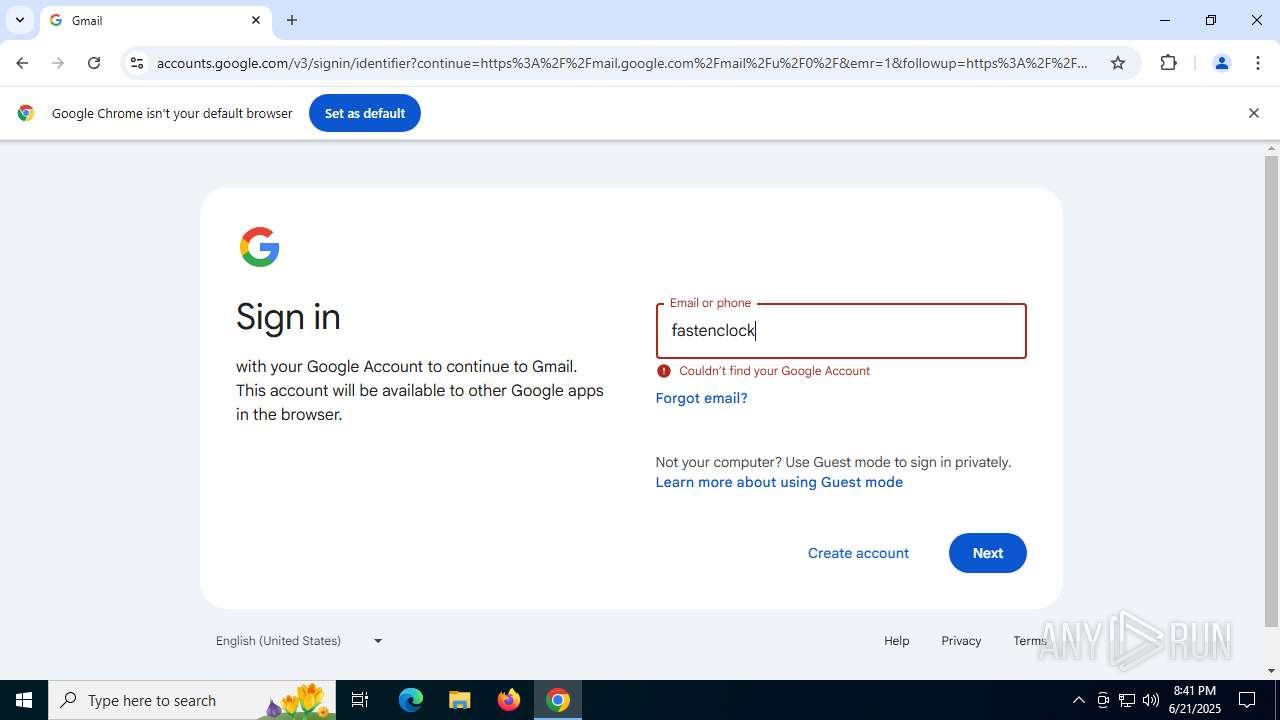
Manual execution by a user
- chrome.exe (PID: 6224)
Application launched itself
- chrome.exe (PID: 6224)
.NET Reactor protector has been detected
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
Disables trace logs
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 7284)
Creates files or folders in the user directory
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
Checks proxy server information
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 7284)
- 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(7284) 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe
C2 (1)45.137.22.242:55615
Botnetcheat
Keys
Xor
Options
ErrorMessage
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:03 01:11:18+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 565760 |
| InitializedDataSize: | 7168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8c01e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | 全功能人力资源管理平台,助力企业高效管理。 |
| CompanyName: | 智慧人事科技 |
| FileDescription: | 员工通企业版 |
| FileVersion: | 0.0.0.0 |
| InternalName: | inTk.exe |
| LegalCopyright: | © 智慧人事科技 乙巳年 |
| LegalTrademarks: | 员工通™ • 企业版 • 智慧系列 |
| OriginalFileName: | inTk.exe |
| ProductName: | 员工通 |
| ProductVersion: | 员工通.智慧.乙巳 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
158
Monitored processes
22
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3812,i,10096060074815417701,8626208513807813370,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3756 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2032,i,10096060074815417701,8626208513807813370,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2028 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5468,i,10096060074815417701,8626208513807813370,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2396,i,10096060074815417701,8626208513807813370,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2408 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2132,i,10096060074815417701,8626208513807813370,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2156 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3884 | "C:\Users\admin\AppData\Local\Temp\989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe" | C:\Users\admin\AppData\Local\Temp\989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | explorer.exe | ||||||||||||
User: admin Company: 智慧人事科技 Integrity Level: MEDIUM Description: 员工通企业版 Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 4664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x230,0x234,0x238,0x20c,0x23c,0x7ffc4456fff8,0x7ffc44570004,0x7ffc44570010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 5232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4848,i,10096060074815417701,8626208513807813370,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4924 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 5528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --field-trial-handle=5648,i,10096060074815417701,8626208513807813370,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5584 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 5848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3196,i,10096060074815417701,8626208513807813370,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
5 911
Read events
5 888
Write events
23
Delete events
0
Modification events
| (PID) Process: | (3884) 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3884) 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3884) 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6224) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6224) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6224) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6224) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6224) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6224) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (7284) 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
44
Text files
24
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1779c4.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1779d3.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1779e3.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1779e3.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RF1779f2.TMP | — | |
MD5:— | SHA256:— | |||
| 6224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1779f2.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
59
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | GET | 301 | 74.114.154.18:80 | http://45.media.tumblr.com/c09abeaae50b2b922e18a3ee47ba427c/tumblr_mwahfnhpEg1r3maj7o1_500.gif | unknown | — | — | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEQCCt2UF0MyK%2BnKMEqhCt6jq | unknown | — | — | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEQCRtIGhqxv2nGcM1oL8kmb%2F | unknown | — | — | whitelisted |
3108 | chrome.exe | GET | 200 | 142.250.185.110:80 | http://clients2.google.com/time/1/current?cup2key=8:5w_0CciIEuRx6pl145yOU9or5EP9KN48fFE4Dgk2CeU&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2552 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7660 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6012 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | 146.75.121.155:443 | media.giphy.com | FASTLY | US | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | 74.114.154.18:80 | 45.media.tumblr.com | AUTOMATTIC | US | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | 104.18.20.226:80 | ocsp2.globalsign.com | CLOUDFLARENET | — | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | 192.0.77.3:443 | 64.media.tumblr.com | AUTOMATTIC | US | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
3884 | 989db46562126cd83b6148da103cb17d770ed14c5a09b899bd225e77ff1b054d.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
media.giphy.com |
| whitelisted |
45.media.tumblr.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
64.media.tumblr.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |