analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
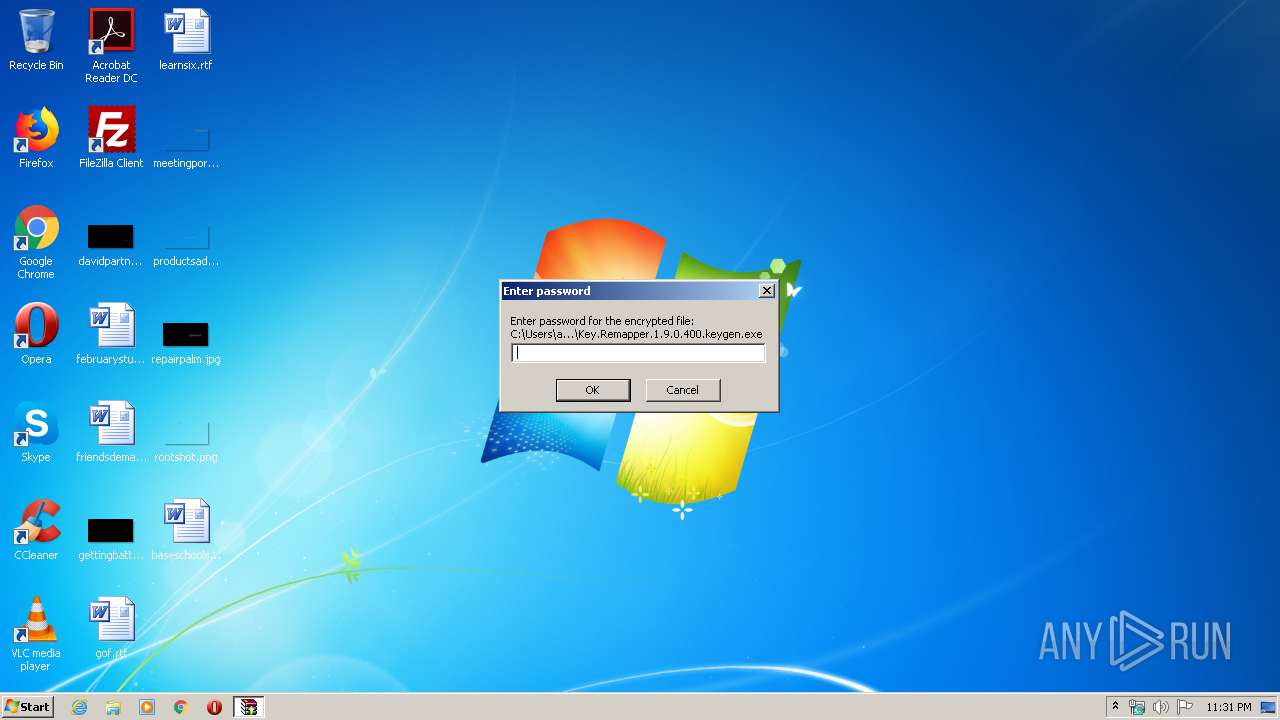
| File name: | Key.Remapper.1.9.0.400.keygen.exe |
| Full analysis: | https://app.any.run/tasks/52800ad3-d84e-4f50-931d-7ed6a5509d6f |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | March 30, 2020, 22:31:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 3DEEFF7ABE50249B14E8BA3623C503BB |
| SHA1: | 2730A2E8E6309BA7FBE7F0342AF5A9CE84C14BD9 |
| SHA256: | 98583906B7BE2A9955F1AEA8CFD96F3A56BBABCF4D347FA59604CF82F6A5976B |
| SSDEEP: | 49152:BFpIq+ZhbXStH6ybL7Y+BoFXFl88cCgl7sBhFu70M12RlN7+P6gOY7/O9qDupEKI:BFpb+xoHJ7XWFXj3GgTRM1+7LYnqEVL |
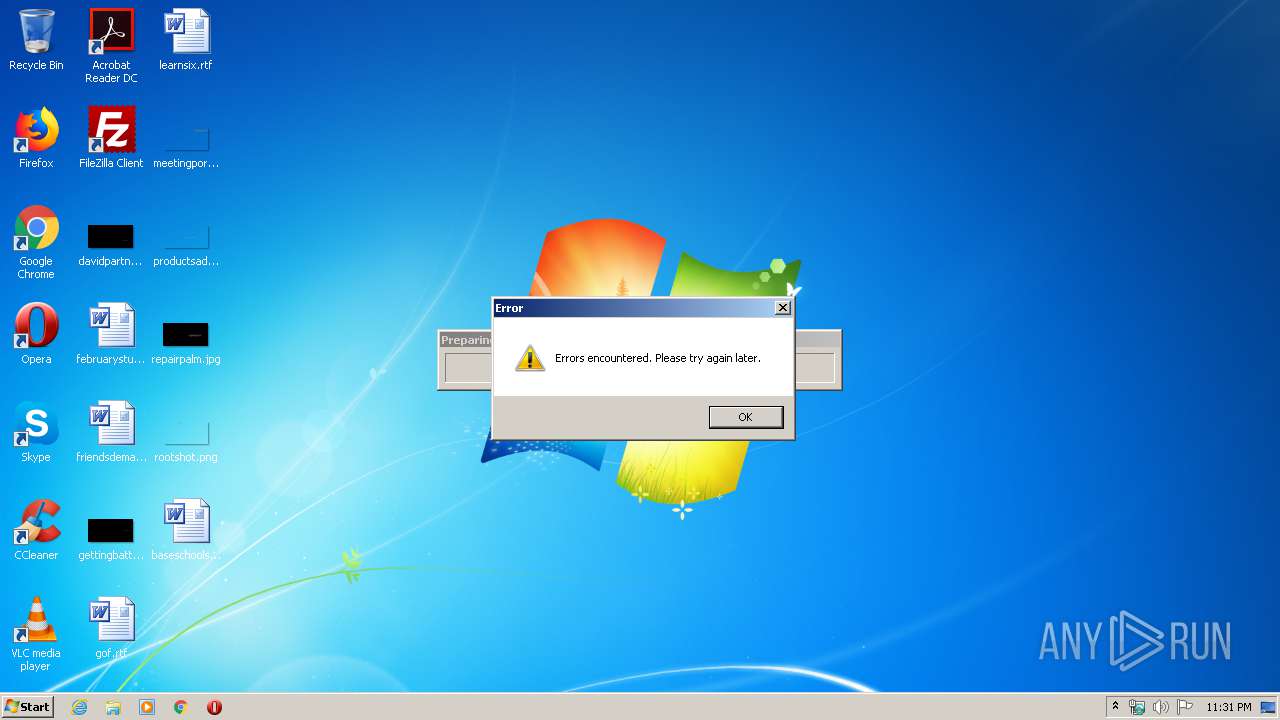
MALICIOUS
Application was dropped or rewritten from another process
- keygen-pr.exe (PID: 2784)
- key.exe (PID: 1632)
- keygen-step-3.exe (PID: 2952)
- adsman3.exe (PID: 3156)
- key.exe (PID: 2620)
- keygen-step-3.exe (PID: 3972)
- adsman3.exe (PID: 1092)
- adsman3.exe (PID: 2756)
- adsman3.exe (PID: 3612)
- main.exe (PID: 3100)
PREPSCRAM was detected
- keygen-step-3.exe (PID: 3972)
Connects to CnC server
- keygen-step-3.exe (PID: 3972)
- key.exe (PID: 1632)
Detected Pony/Fareit Trojan
- key.exe (PID: 1632)
PONY was detected
- key.exe (PID: 1632)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2936)
Actions looks like stealing of personal data
- key.exe (PID: 1632)
SUSPICIOUS
Executable content was dropped or overwritten
- Key.Remapper.1.9.0.400.keygen.exe (PID: 3084)
- keygen-pr.exe (PID: 2784)
- adsman3.exe (PID: 1092)
- adsman3.exe (PID: 2756)
Starts CMD.EXE for commands execution
- Key.Remapper.1.9.0.400.keygen.exe (PID: 3084)
- adsman3.exe (PID: 1092)
Application launched itself
- key.exe (PID: 1632)
- keygen-step-3.exe (PID: 2952)
Reads Windows owner or organization settings
- key.exe (PID: 2620)
Reads Environment values
- key.exe (PID: 2620)
Reads the Windows organization settings
- key.exe (PID: 2620)
Reads Windows Product ID
- key.exe (PID: 2620)
Creates files in the program directory
- adsman3.exe (PID: 1092)
- adsman3.exe (PID: 2756)
Creates files in the user directory
- adsman3.exe (PID: 1092)
- key.exe (PID: 1632)
Loads DLL from Mozilla Firefox
- key.exe (PID: 1632)
Searches for installed software
- key.exe (PID: 1632)
- key.exe (PID: 2620)
Reads Internet Cache Settings
- key.exe (PID: 1632)
Creates a software uninstall entry
- adsman3.exe (PID: 1092)
Executed as Windows Service
- adsman3.exe (PID: 2756)
Starts itself from another location
- adsman3.exe (PID: 2756)
INFO
Reads Microsoft Office registry keys
- key.exe (PID: 2620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:02:15 09:00:31+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 165888 |
| InitializedDataSize: | 175104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d7cb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Feb-2015 08:00:31 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-Feb-2015 08:00:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002878A | 0x00028800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71935 |
.rdata | 0x0002A000 | 0x00004FD3 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38998 |
.data | 0x0002F000 | 0x00021428 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.46555 |
.rsrc | 0x00051000 | 0x000044D8 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.65066 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.24822 | 1738 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
65
Monitored processes
20
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3084 | "C:\Users\admin\AppData\Local\Temp\Key.Remapper.1.9.0.400.keygen.exe" | C:\Users\admin\AppData\Local\Temp\Key.Remapper.1.9.0.400.keygen.exe | explorer.exe | |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 2860 | cmd /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\keygen.bat" " | C:\Windows\system32\cmd.exe | — | Key.Remapper.1.9.0.400.keygen.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 2784 | keygen-pr.exe -p83fsase3Ge | C:\Users\admin\AppData\Local\Temp\RarSFX0\keygen-pr.exe | cmd.exe | |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 2952 | keygen-step-3.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\keygen-step-3.exe | — | cmd.exe |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 3156 | adsman3.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\adsman3.exe | — | cmd.exe |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 1632 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\key.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\key.exe | keygen-pr.exe | |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 2372 | "C:\Windows\system32\CompMgmtLauncher.exe" | C:\Windows\system32\CompMgmtLauncher.exe | — | adsman3.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Computer Management Snapin Launcher Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 2620 | C:\Users\admin\AppData\Local\Temp\RarSFX1\key.exe -txt -scanlocal -file:potato.dat | C:\Users\admin\AppData\Local\Temp\RarSFX1\key.exe | — | key.exe |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 3020 | "C:\Windows\system32\CompMgmtLauncher.exe" | C:\Windows\system32\CompMgmtLauncher.exe | adsman3.exe | |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Computer Management Snapin Launcher Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3972 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\keygen-step-3.exe" keygen-step-3.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\keygen-step-3.exe | keygen-step-3.exe | |
User: admin Integrity Level: HIGH Exit code: 0 | ||||
Total events
3 483
Read events
3 401
Write events
0
Delete events
0
Modification events
Executable files
6
Suspicious files
10
Text files
21
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1092 | adsman3.exe | C:\Users\admin\AppData\Local\Temp\1585607506chrome.tmp | — | |
MD5:— | SHA256:— | |||
| 1092 | adsman3.exe | C:\Program Files\Google\Chrome\Application\75.0.3770.100\chrome.dll_ | — | |
MD5:— | SHA256:— | |||
| 1092 | adsman3.exe | C:\Program Files\Google\Chrome\Application\75.0.3770.100\chrome.dll | — | |
MD5:— | SHA256:— | |||
| 1092 | adsman3.exe | C:\Users\admin\AppData\Local\Temp\manifest.json | — | |
MD5:— | SHA256:— | |||
| 2620 | key.exe | C:\Users\admin\AppData\Local\Temp\tmpC934.tmp | — | |
MD5:— | SHA256:— | |||
| 1092 | adsman3.exe | C:\Users\admin\AppData\Local\Temp\70L4NUF7K7.js | — | |
MD5:— | SHA256:— | |||
| 1092 | adsman3.exe | C:\Users\admin\AppData\Local\Temp\XR2DOGF3S6.js | — | |
MD5:— | SHA256:— | |||
| 1092 | adsman3.exe | C:\Users\admin\AppData\Local\Temp\L4AYVPZ9CS.js | — | |
MD5:— | SHA256:— | |||
| 1092 | adsman3.exe | C:\Users\admin\AppData\Local\Temp\I39ZIWOBZ1.js | — | |
MD5:— | SHA256:— | |||
| 1092 | adsman3.exe | C:\Users\admin\AppData\Local\Temp\FEH4SEMBP3.js | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
54
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3972 | keygen-step-3.exe | GET | 200 | 143.204.208.103:80 | http://d3vngcy706h320.cloudfront.net/offer.php?affId=2966&trackingId=439079241&instId=3443&ho_trackingid=HO439079241&cc=&sb=x86&wv=7sp1&db=InternetExplorer&uac=1&cid=5d979308c3b6ea5ad7e984e628c8cac1&v=3&net=4.7.03062&ie=11%2e0%2e9600%2e17840&res=1280x720&osd=907&kid=hqmrb21c09kmu77j70t | US | — | — | whitelisted |
1632 | key.exe | POST | 200 | 80.211.174.156:80 | http://www.oldhorse.info/ | IT | binary | 20 b | malicious |
1632 | key.exe | POST | 200 | 80.211.174.156:80 | http://www.oldhorse.info/ | IT | binary | 20 b | malicious |
1632 | key.exe | POST | 200 | 80.211.174.156:80 | http://oldhorse.info/a.php | IT | — | — | malicious |
1632 | key.exe | POST | 200 | 80.211.174.156:80 | http://www.oldhorse.info/ | IT | binary | 20 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3972 | keygen-step-3.exe | 143.204.208.103:80 | d3vngcy706h320.cloudfront.net | — | US | malicious |
— | — | 104.24.104.147:443 | dinomobsonke.xyz | Cloudflare Inc | US | shared |
1092 | adsman3.exe | 104.24.104.147:443 | dinomobsonke.xyz | Cloudflare Inc | US | shared |
1632 | key.exe | 80.211.174.156:80 | oldhorse.info | Aruba S.p.A. | IT | malicious |
2756 | adsman3.exe | 104.24.104.147:443 | dinomobsonke.xyz | Cloudflare Inc | US | shared |
3100 | main.exe | 104.24.104.147:443 | dinomobsonke.xyz | Cloudflare Inc | US | shared |
3612 | adsman3.exe | 104.24.104.147:443 | dinomobsonke.xyz | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d3vngcy706h320.cloudfront.net |
| whitelisted |
dinomobsonke.xyz |
| unknown |
oldhorse.info |
| malicious |
www.oldhorse.info |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3972 | keygen-step-3.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
3972 | keygen-step-3.exe | Misc activity | ADWARE [PTsecurity] SoftwareBundler:Win32/Prepscram |
1632 | key.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Nebuler Checkin |
1632 | key.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
1632 | key.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony CnC Server stdResponse |
1632 | key.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
1632 | key.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony CnC Server stdResponse |
1632 | key.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
1632 | key.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony CnC Server stdResponse |
8 ETPRO signatures available at the full report