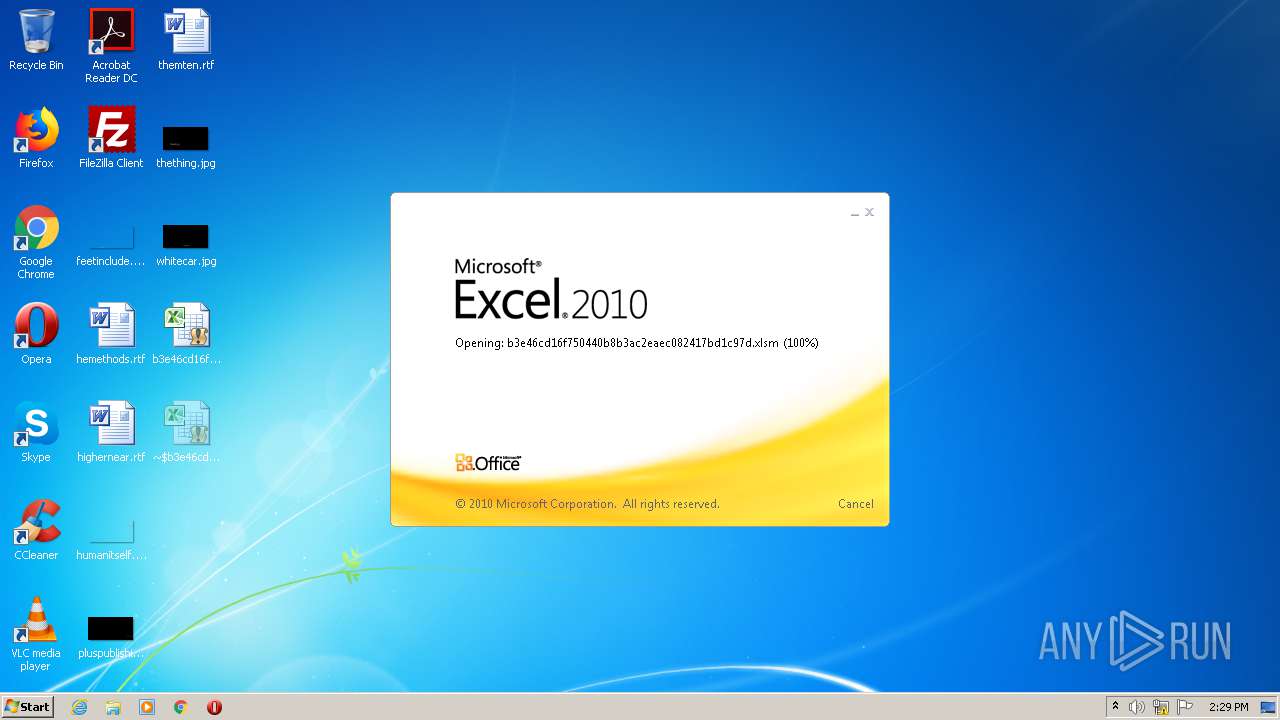
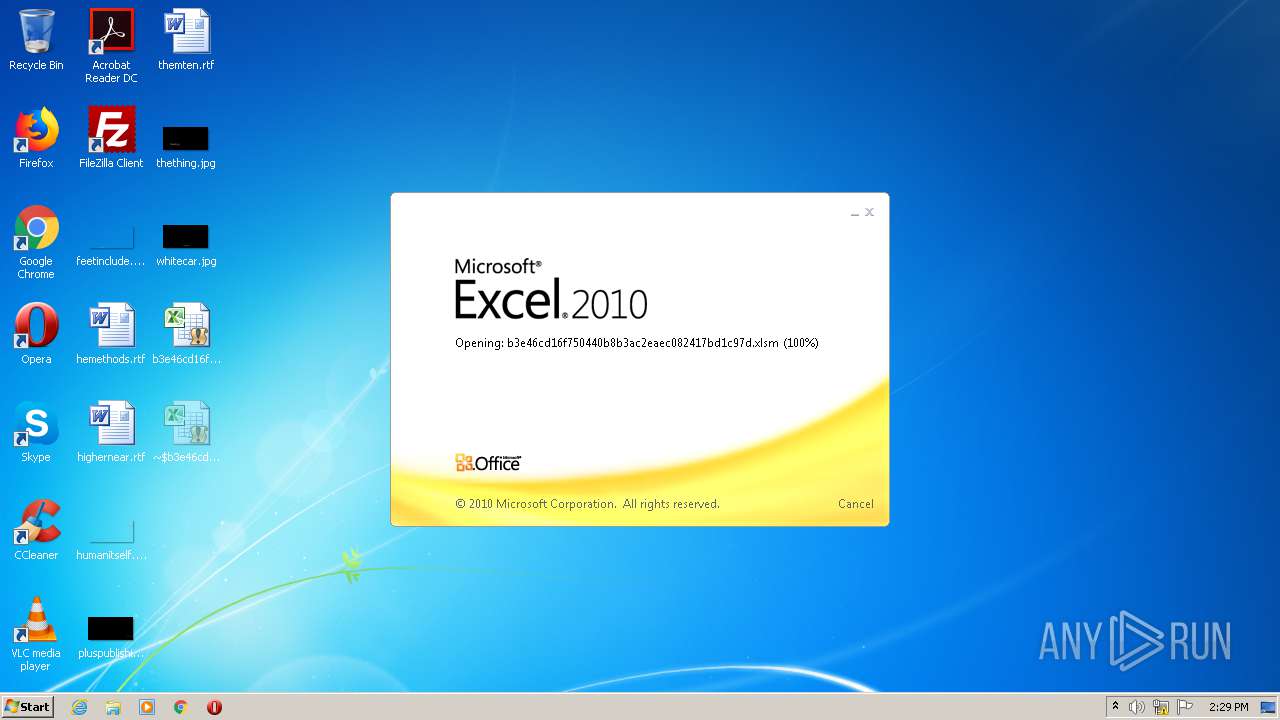
| File name: | b3e46cd16f750440b8b3ac2eaec082417bd1c97d.xlsm |
| Full analysis: | https://app.any.run/tasks/d65e415e-2d4c-461a-9fea-9a1bac515cb5 |
| Verdict: | Malicious activity |
| Threats: | Dridex is a very evasive and technically complex banking trojan. Despite being based on a relatively old malware code, it was substantially updated over the years and became capable of using very effective infiltration techniques that make this malware especially dangerous. |
| Analysis date: | September 30, 2020, 13:29:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 155C990DFB8E9456D6B44F3C01A3699B |
| SHA1: | B3E46CD16F750440B8B3AC2EAEC082417BD1C97D |
| SHA256: | 9852A64FF8DD64E99326DC917C70B9B68C1E80128260035FDAE275BF5FC66972 |
| SSDEEP: | 768:kbxfr648mkWPgDPGD1jWuiQkucJTSPZ9Ar0HP:uxfr64NXPgDA1jCQPcJuP3A4v |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2456)
DRIDEX was detected
- regsvr32.exe (PID: 3096)
Registers / Runs the DLL via REGSVR32.EXE
- EXCEL.EXE (PID: 2456)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2456)
SUSPICIOUS
Reads Internet Cache Settings
- regsvr32.exe (PID: 3096)
Searches for installed software
- regsvr32.exe (PID: 3096)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2456)
Reads settings of System Certificates
- regsvr32.exe (PID: 3096)
Creates files in the user directory
- EXCEL.EXE (PID: 2456)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsm | | | Excel Microsoft Office Open XML Format document (with Macro) (29.2) |
|---|---|---|
| .xlsx | | | Excel Microsoft Office Open XML Format document (17.3) |
| .zip | | | Open Packaging Conventions container (8.9) |
| .zip | | | ZIP compressed archive (2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x02a77f1b |
| ZipCompressedSize: | 482 |
| ZipUncompressedSize: | 1867 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | - |
|---|
XML
| LastModifiedBy: | - |
|---|---|
| CreateDate: | 2020:09:30 12:03:43Z |
| ModifyDate: | 2020:09:30 12:05:31Z |
| Application: | Microsoft Excel |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | Accounts Dept. |
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
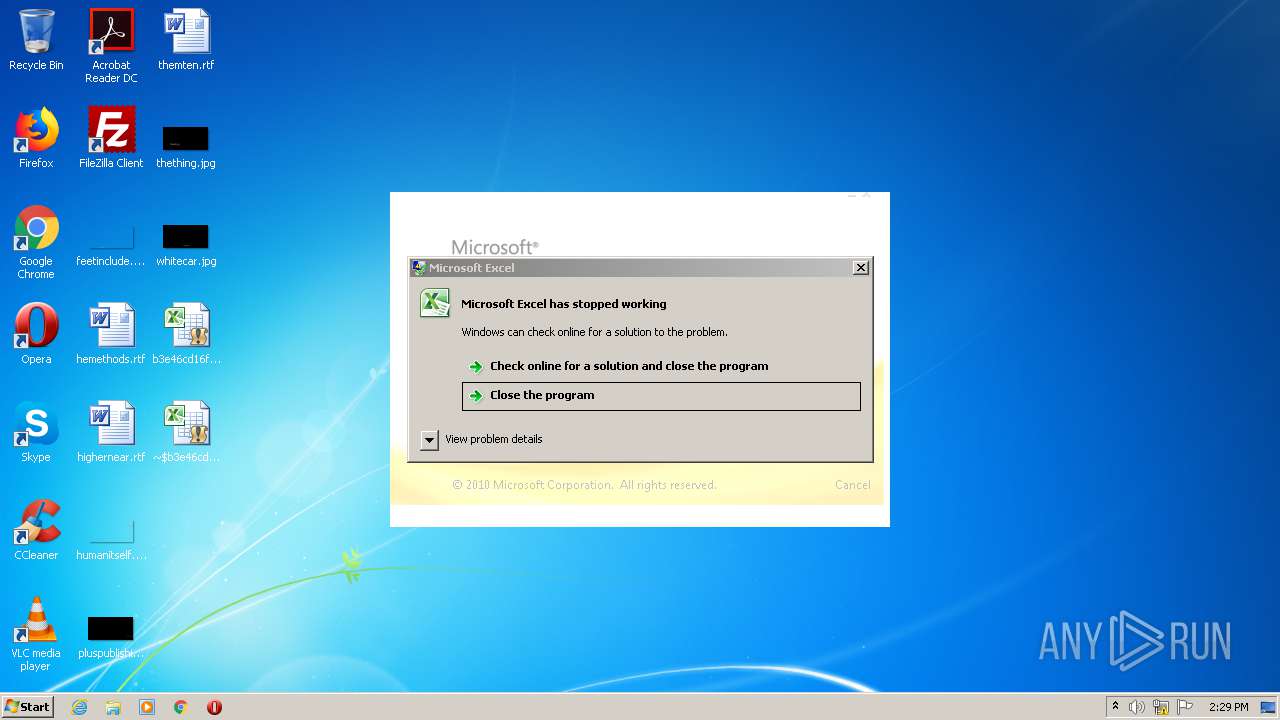
| 776 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 996 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3096 | "C:\Windows\System32\regsvr32.exe" -s C:\bQRmAmpj\YsnVxs\xVmDcR. | C:\Windows\System32\regsvr32.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3276 | C:\Windows\system32\dwwin.exe -x -s 996 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
985
Read events
822
Write events
147
Delete events
16
Modification events
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | /k |
Value: 2F6B200098090000010000000000000000000000 | |||
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2456) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
10
Text files
3
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRAF9F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2456 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CabE249.tmp | — | |
MD5:— | SHA256:— | |||
| 2456 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\TarE24A.tmp | — | |
MD5:— | SHA256:— | |||
| 2456 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\79334F4A.png | — | |
MD5:— | SHA256:— | |||
| 2456 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\576C82C3.png | — | |
MD5:— | SHA256:— | |||
| 2456 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\71A755E8.png | — | |
MD5:— | SHA256:— | |||
| 2456 | EXCEL.EXE | C:\Users\admin\Desktop\~$b3e46cd16f750440b8b3ac2eaec082417bd1c97d.xlsm | — | |
MD5:— | SHA256:— | |||
| 3096 | regsvr32.exe | C:\Users\admin\AppData\Local\Temp\Cab872E.tmp | — | |
MD5:— | SHA256:— | |||
| 3096 | regsvr32.exe | C:\Users\admin\AppData\Local\Temp\Tar872F.tmp | — | |
MD5:— | SHA256:— | |||
| 3096 | regsvr32.exe | C:\Users\admin\AppData\Local\Temp\Cab873F.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
7
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3096 | regsvr32.exe | GET | 304 | 8.238.6.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2456 | EXCEL.EXE | GET | 200 | 72.247.177.152:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
2456 | EXCEL.EXE | GET | 200 | 72.247.177.135:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPVY3MO9IytO9%2F4RrEnf12MMw%3D%3D | NL | der | 527 b | whitelisted |
3096 | regsvr32.exe | GET | 200 | 8.238.6.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA7yTSbUNi7CXXtef0luXqk%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2456 | EXCEL.EXE | 83.166.138.121:443 | seminelogistics.com | Infomaniak Network SA | CH | unknown |
1052 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3096 | regsvr32.exe | 146.164.126.197:443 | — | Fundacao de Amparo a Pesquisa/RJ | BR | malicious |
2456 | EXCEL.EXE | 72.247.177.135:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | NL | whitelisted |
3096 | regsvr32.exe | 69.16.193.166:9443 | — | Liquid Web, L.L.C | US | unknown |
2456 | EXCEL.EXE | 72.247.177.152:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | unknown |
3096 | regsvr32.exe | 8.238.6.126:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
seminelogistics.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3096 | regsvr32.exe | A Network Trojan was detected | ET TROJAN ABUSE.CH SSL Blacklist Malicious SSL certificate detected (Dridex) |