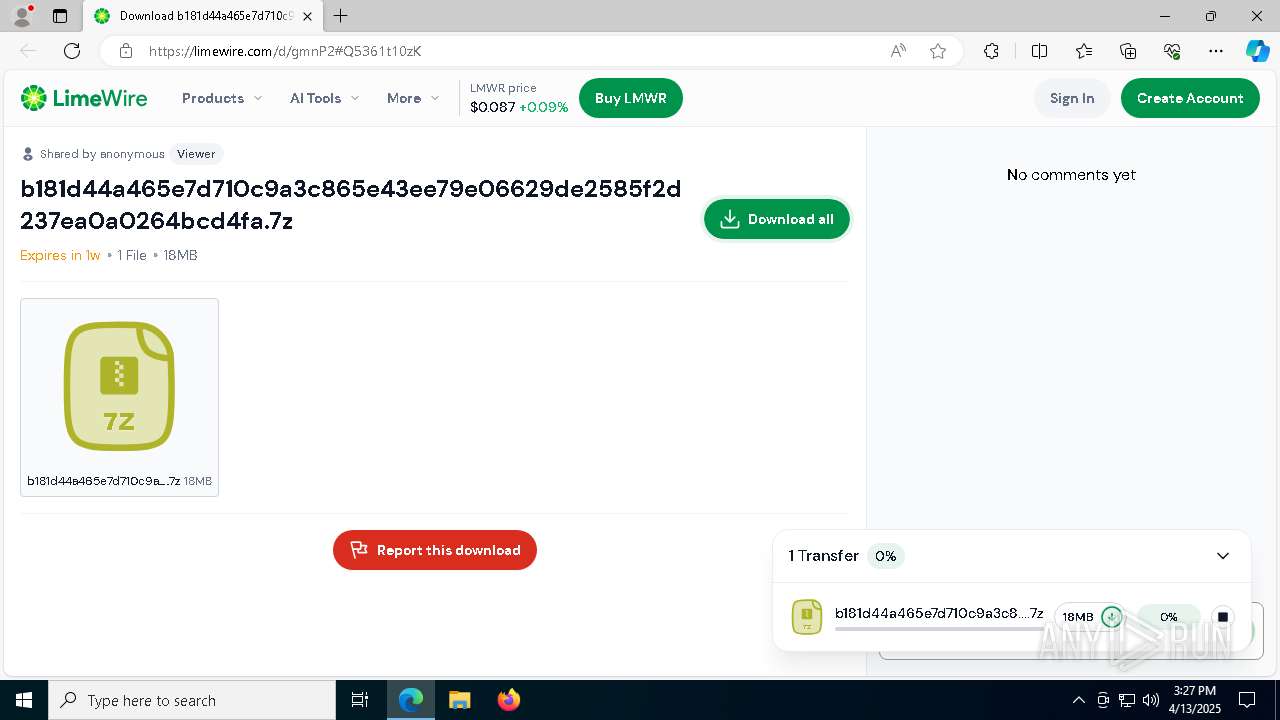
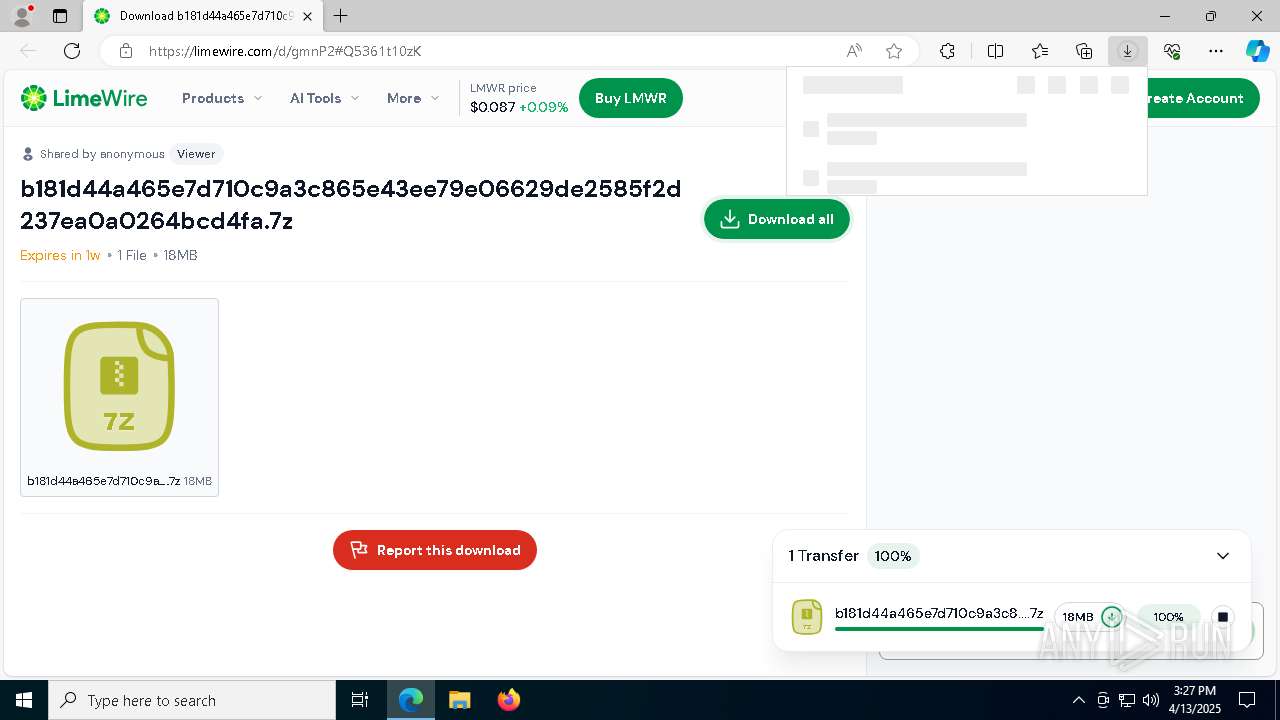
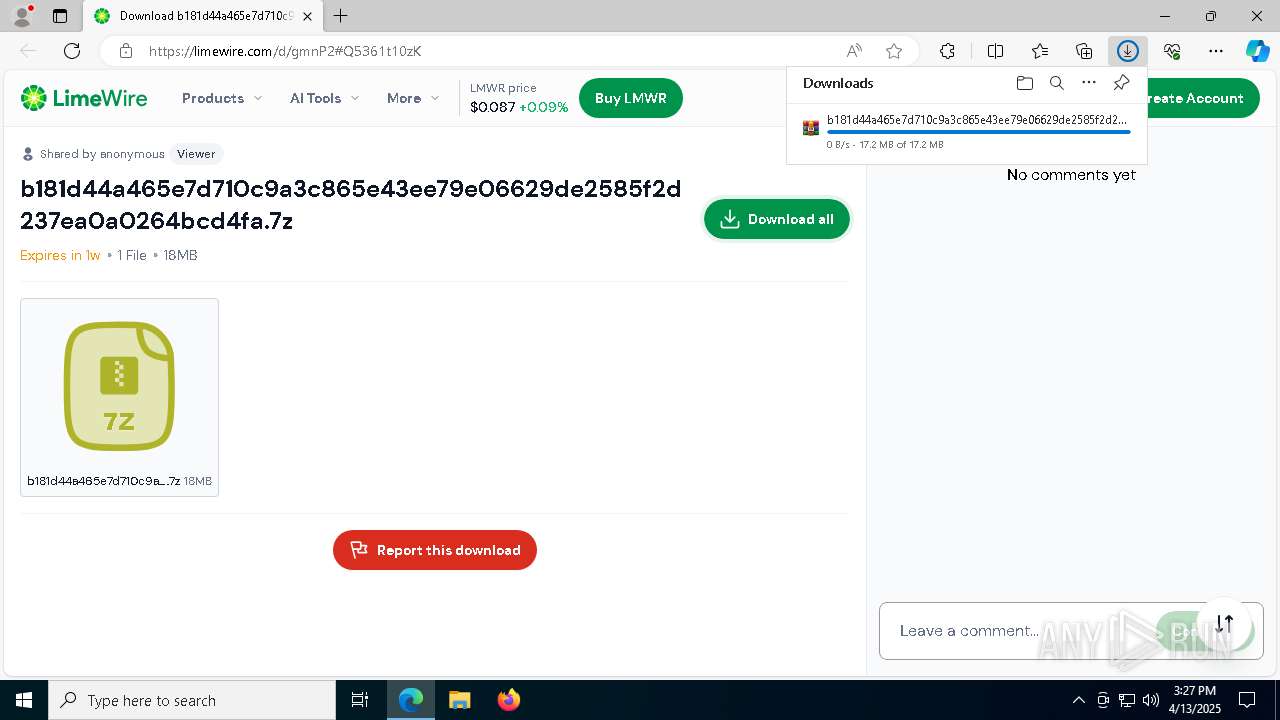
| URL: | https://limewire.com/d/gmnP2#Q5361t10zK |
| Full analysis: | https://app.any.run/tasks/d65ddfd0-eda8-4acb-bcbe-0c49f30ccc4d |
| Verdict: | Malicious activity |
| Threats: | Ramnit is a highly modular banking trojan and worm that evolved from a file-infecting virus into a powerful cybercrime tool. It specializes in financial fraud, credential theft, remote access, and malware delivery, being a serious threat to businesses and individuals. First spotted in 2010, Ramnit became popular after the 2014 takedown of the GameOver Zeus botnet, as cybercriminals sought alternatives for banking fraud. |
| Analysis date: | April 13, 2025, 15:27:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4F8FC51CC026B1AD38B76041C51E0C22 |
| SHA1: | 2CE95E2E183D8F04C3D8B4605F3F5DCC609AB558 |
| SHA256: | 9834590C2FE3AFFDC98564C001FE664CFBB8B0ED9706E4172BA012017159B83D |
| SSDEEP: | 3:N8MIA/enKLBW0sRU1un:2MIA/eKLBzsRxn |
MALICIOUS
Executing a file with an untrusted certificate
- netpass64.exe (PID: 7732)
- NetRouteView.exe (PID: 2140)
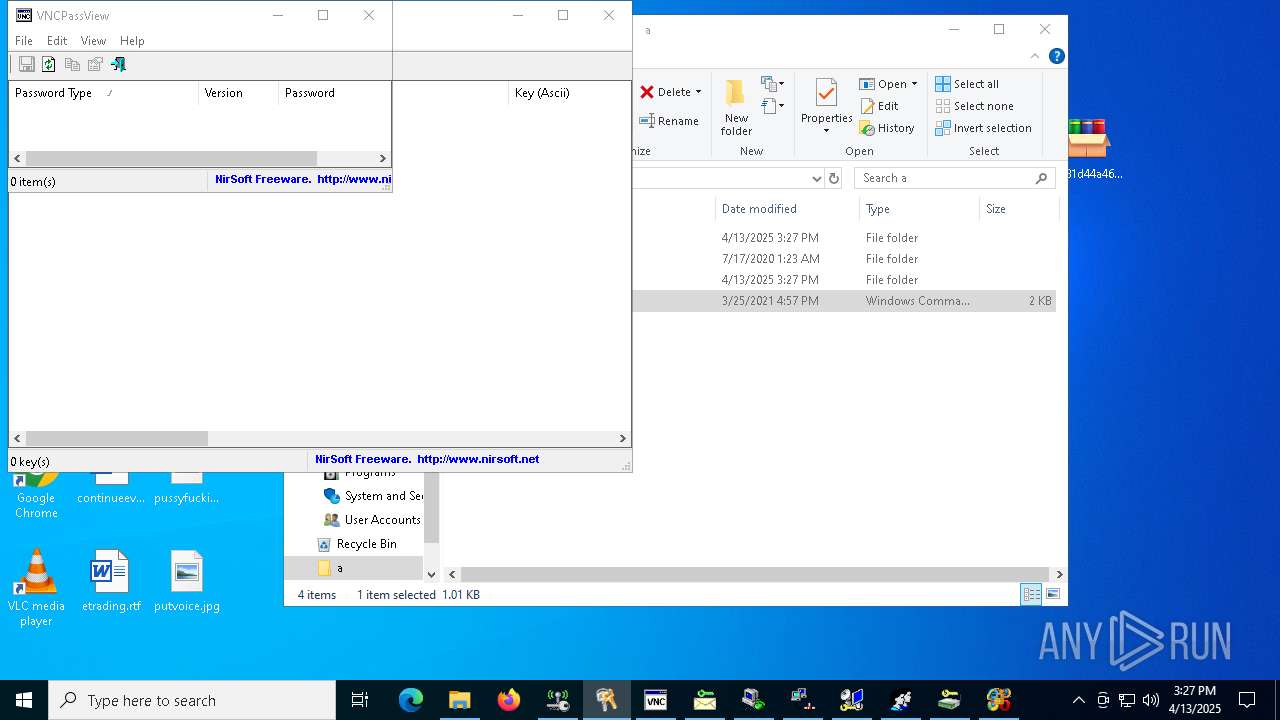
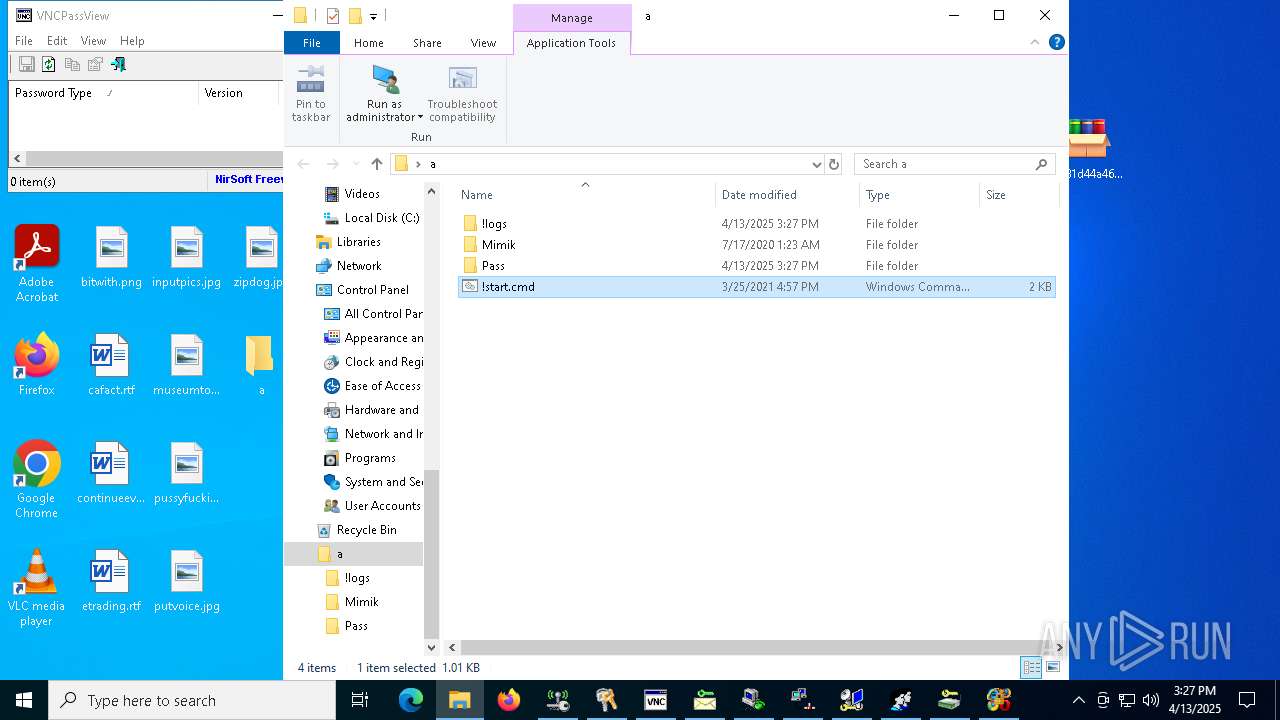
RAMNIT has been detected
- VNCPassViewSrv.exe (PID: 7208)
- mailpv.exe (PID: 4880)
- mspass.exe (PID: 6184)
- VNCPassView.exe (PID: 7312)
- mailpvSrv.exe (PID: 7440)
- DesktopLayer.exe (PID: 4784)
- mspassSrv.exe (PID: 4776)
- RouterPassViewSrv.exe (PID: 4728)
- rdpvSrv.exe (PID: 6252)
- RouterPassView.exe (PID: 5960)
- rdpv.exe (PID: 1096)
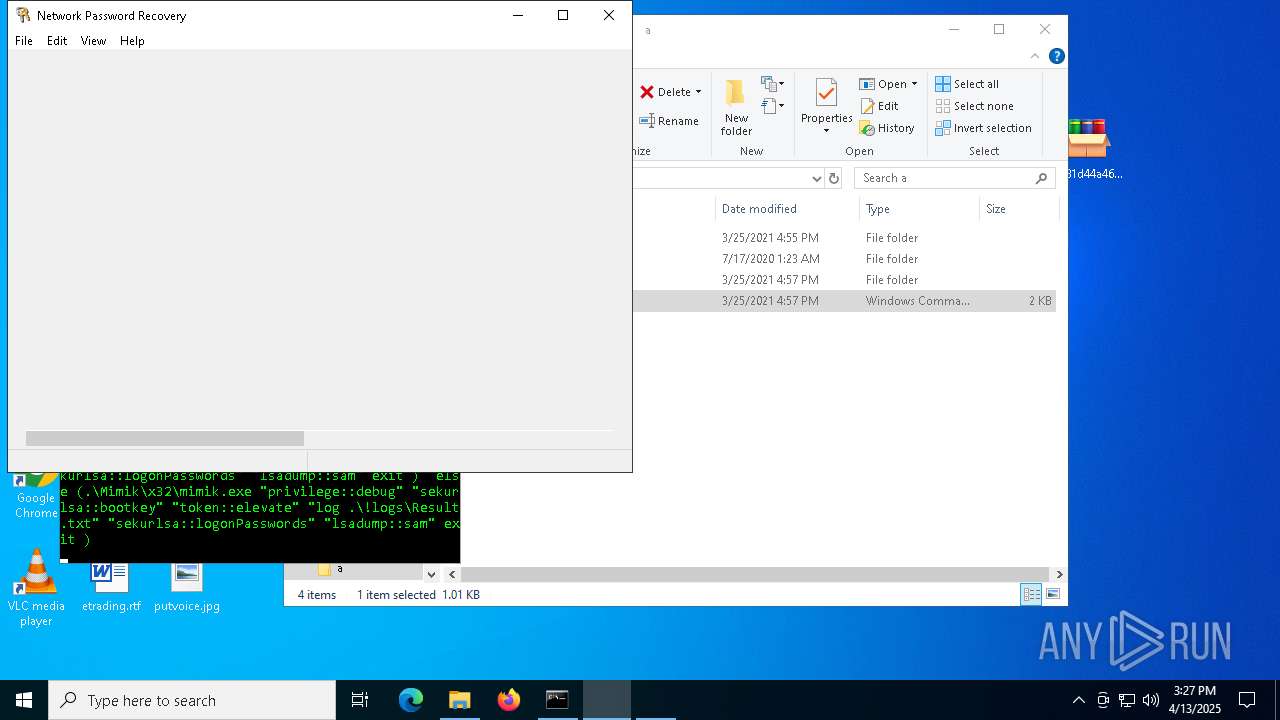
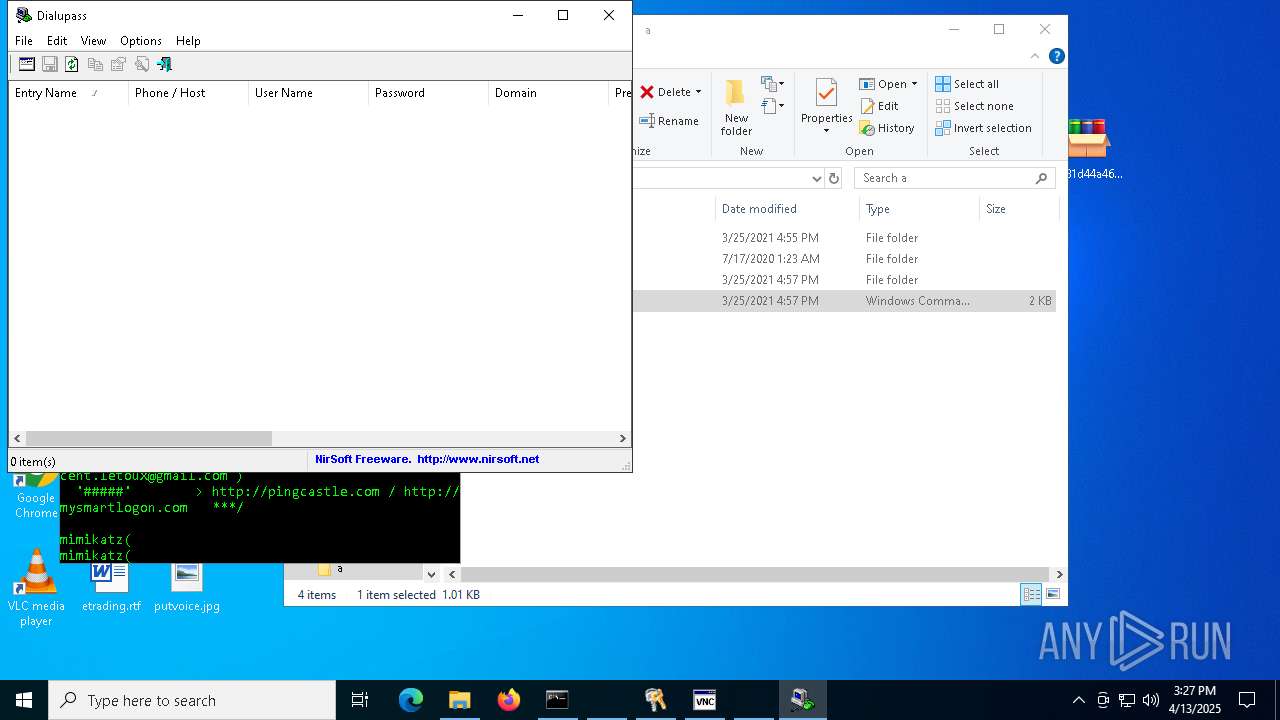
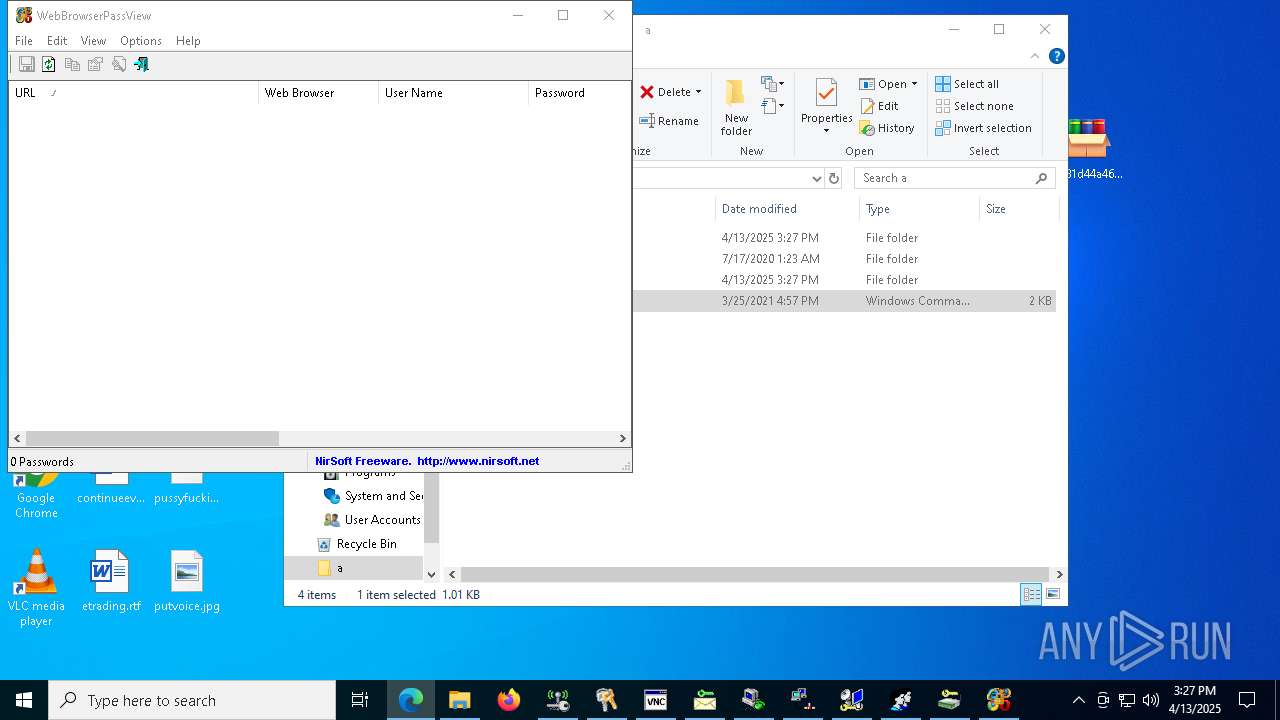
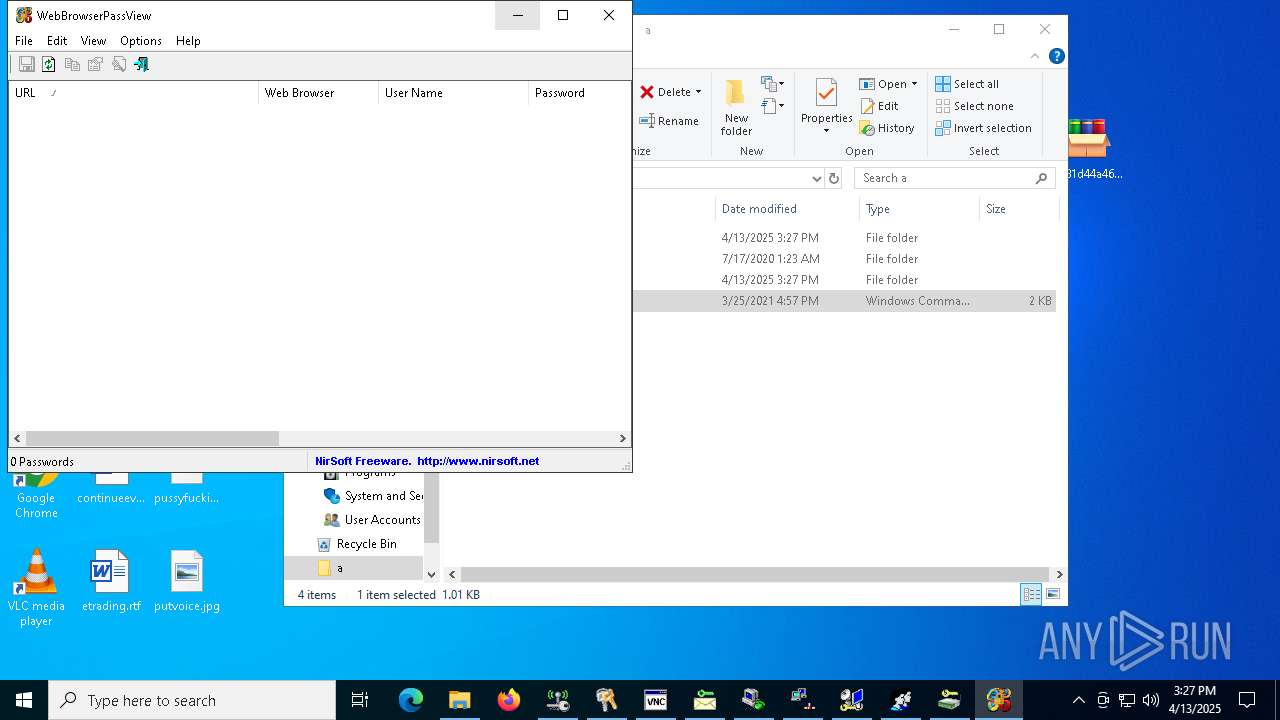
Password recovery utility (NirSoft) for browsers is detected
- WebBrowserPassView.exe (PID: 1628)
MIMIKATZ is used to impersonate a token
- mimik.exe (PID: 6192)
MIMIKATZ is used to list all available provider credentials
- mimik.exe (PID: 6192)
MIMIKATZ is used to get debug rights
- mimik.exe (PID: 6192)
MIMIKATZ is used to get the SysKey to decrypt SAM entries
- mimik.exe (PID: 6192)
Application was injected by another process
- lsass.exe (PID: 756)
Runs injected code in another process
- netpass64.exe (PID: 7732)
Actions looks like stealing of personal data
- mailpv.exe (PID: 4880)
- mspass.exe (PID: 6184)
- WebBrowserPassView.exe (PID: 1628)
Steals credentials from Web Browsers
- WebBrowserPassView.exe (PID: 1628)
SUSPICIOUS
Reads security settings of Internet Explorer
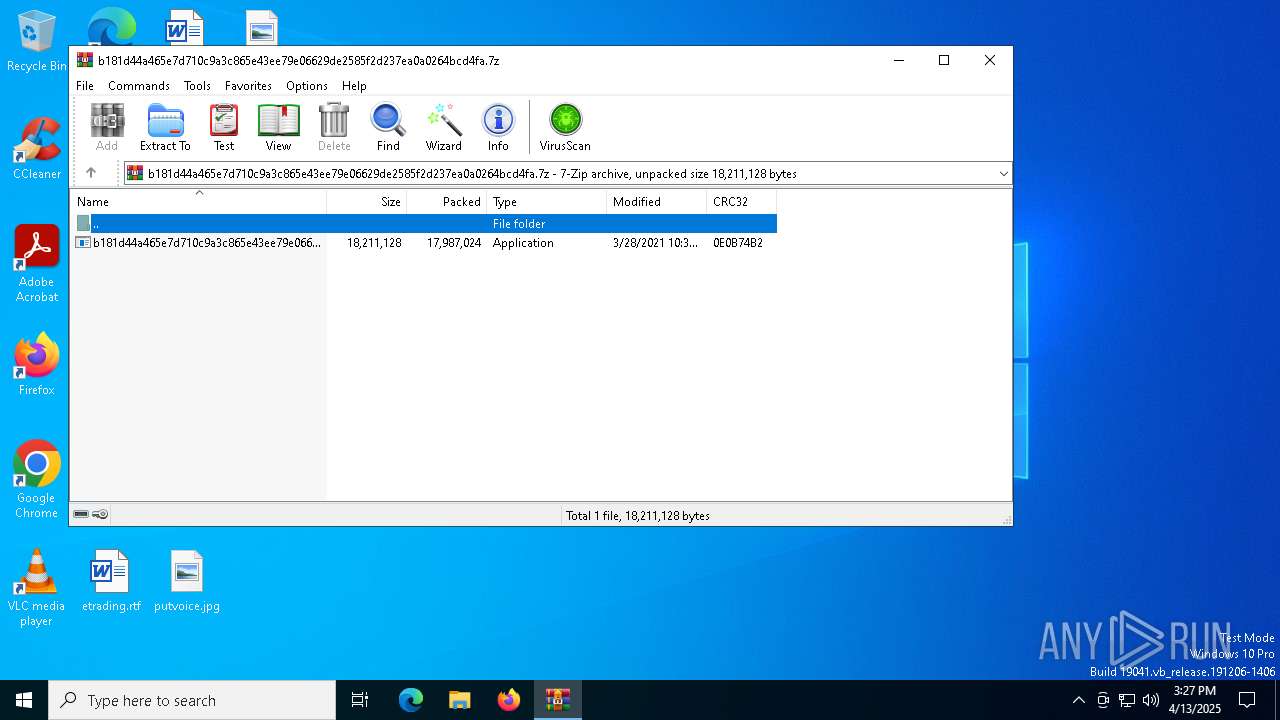
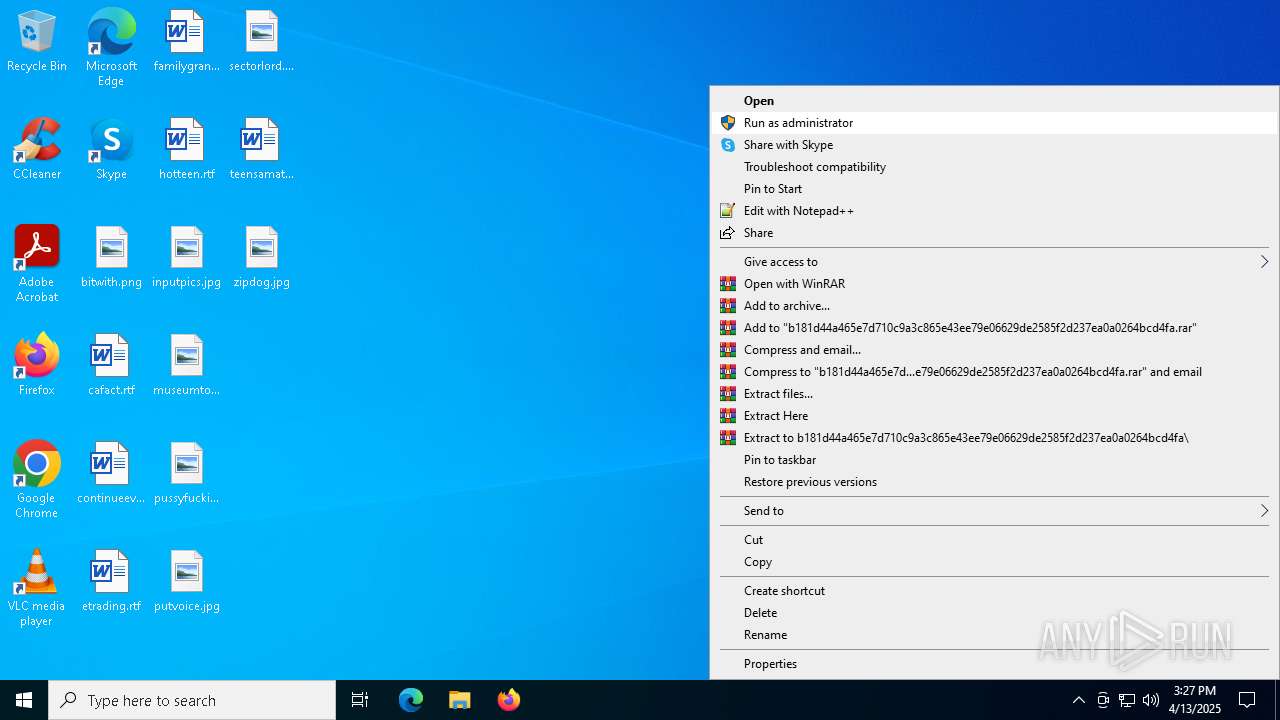
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
Reads Internet Explorer settings
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
Reads Microsoft Outlook installation path
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
The process creates files with name similar to system file names
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
Drops a system driver (possible attempt to evade defenses)
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
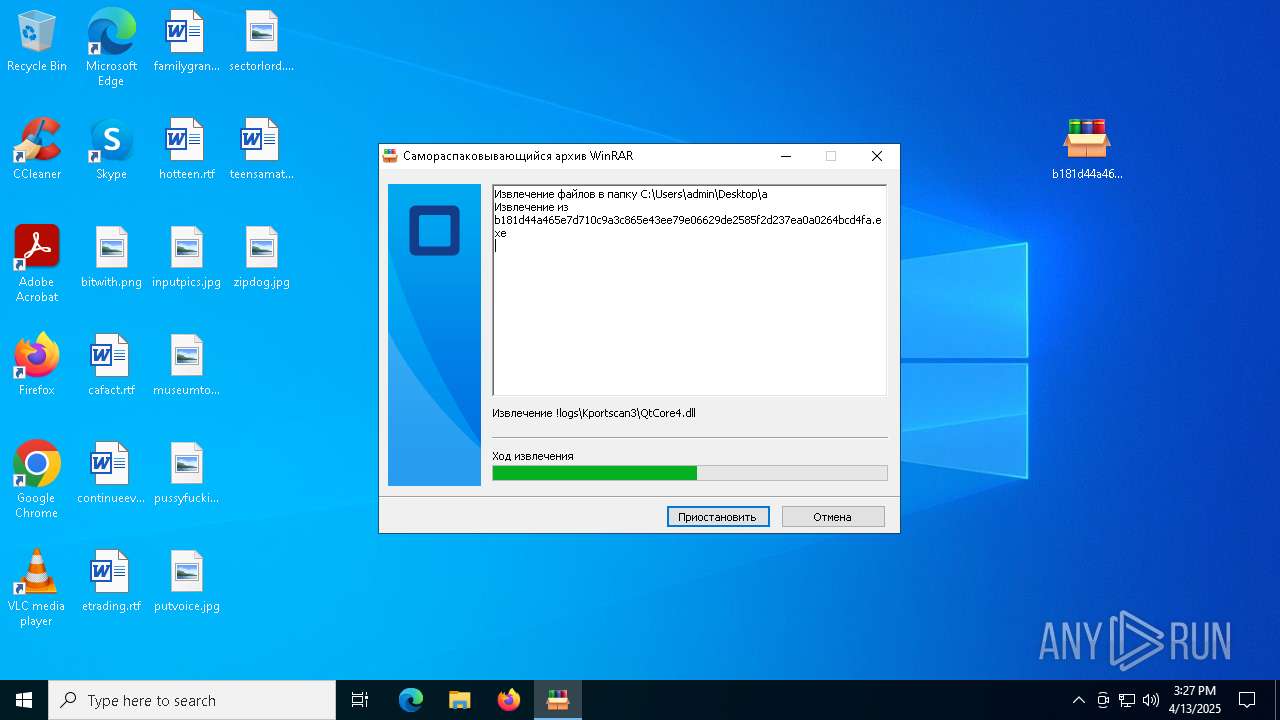
Executable content was dropped or overwritten
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
- VNCPassView.exe (PID: 7312)
- mailpv.exe (PID: 4880)
- VNCPassViewSrv.exe (PID: 7208)
- mspass.exe (PID: 6184)
- rdpv.exe (PID: 1096)
- RouterPassView.exe (PID: 5960)
Starts itself from another location
- VNCPassViewSrv.exe (PID: 7208)
BROWSERPASSVIEW has been detected
- cmd.exe (PID: 7480)
Application launched itself
- WirelessKeyView64.exe (PID: 3300)
The process executes VB scripts
- cmd.exe (PID: 7480)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7680)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7680)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 7680)
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 7680)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 7680)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 7680)
INFO
Creates files or folders in the user directory
- lsass.exe (PID: 756)
Application launched itself
- msedge.exe (PID: 7000)
- msedge.exe (PID: 5400)
- msedge.exe (PID: 4208)
Reads the software policy settings
- lsass.exe (PID: 756)
Checks supported languages
- identity_helper.exe (PID: 4980)
- identity_helper.exe (PID: 7364)
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
- mode.com (PID: 6592)
- netpass64.exe (PID: 7732)
- WirelessKeyView64.exe (PID: 3300)
- VNCPassView.exe (PID: 7312)
- VNCPassViewSrv.exe (PID: 7208)
- Dialupass.exe (PID: 5640)
- mailpv.exe (PID: 4880)
- mailpvSrv.exe (PID: 7440)
- mspass.exe (PID: 6184)
- DesktopLayer.exe (PID: 4784)
- WebBrowserPassView.exe (PID: 1628)
- mspassSrv.exe (PID: 4776)
- RouterPassView.exe (PID: 5960)
- rdpvSrv.exe (PID: 6252)
- RouterPassViewSrv.exe (PID: 4728)
- mimik.exe (PID: 6192)
- rdpv.exe (PID: 1096)
- NetRouteView.exe (PID: 2140)
- WirelessKeyView64.exe (PID: 7356)
- identity_helper.exe (PID: 6988)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7000)
Reads Environment values
- identity_helper.exe (PID: 4980)
- identity_helper.exe (PID: 7364)
- identity_helper.exe (PID: 6988)
Reads the computer name
- identity_helper.exe (PID: 4980)
- identity_helper.exe (PID: 7364)
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
- netpass64.exe (PID: 7732)
- WirelessKeyView64.exe (PID: 3300)
- mspass.exe (PID: 6184)
- VNCPassView.exe (PID: 7312)
- Dialupass.exe (PID: 5640)
- mimik.exe (PID: 6192)
- mailpv.exe (PID: 4880)
- rdpv.exe (PID: 1096)
- RouterPassView.exe (PID: 5960)
- NetRouteView.exe (PID: 2140)
- WirelessKeyView64.exe (PID: 7356)
- WebBrowserPassView.exe (PID: 1628)
- identity_helper.exe (PID: 6988)
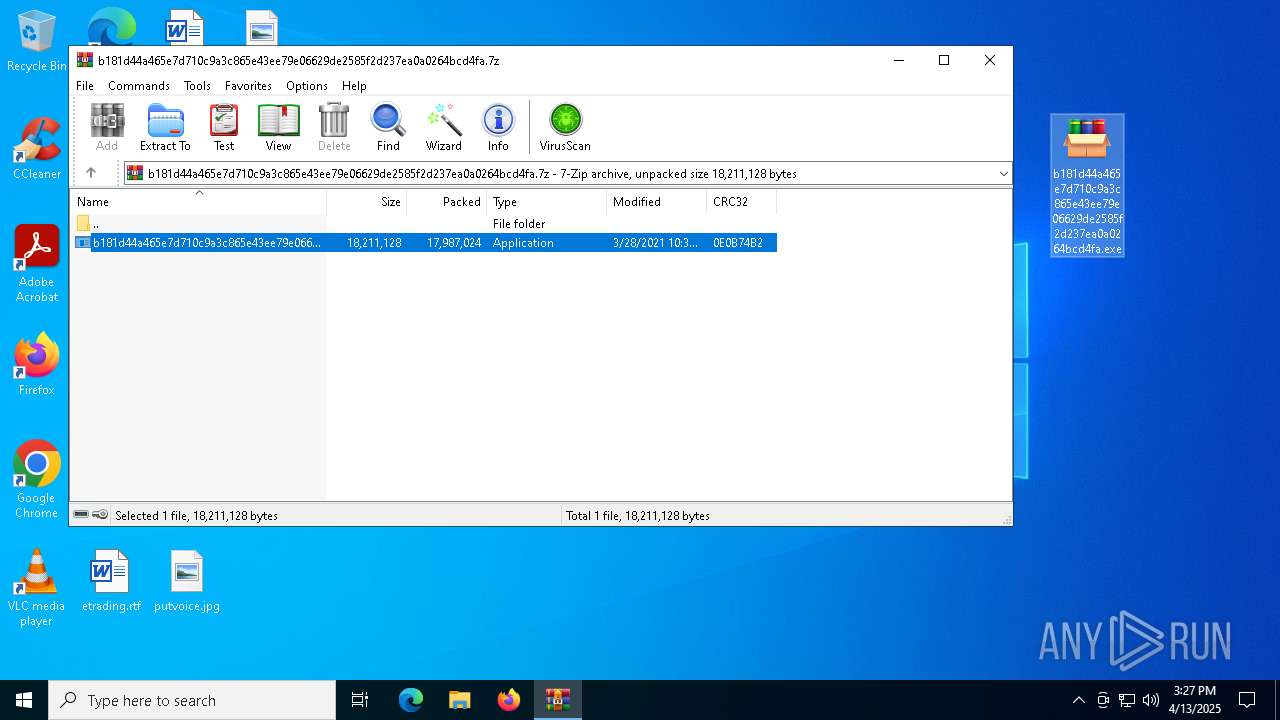
Autorun file from Downloads
- msedge.exe (PID: 864)
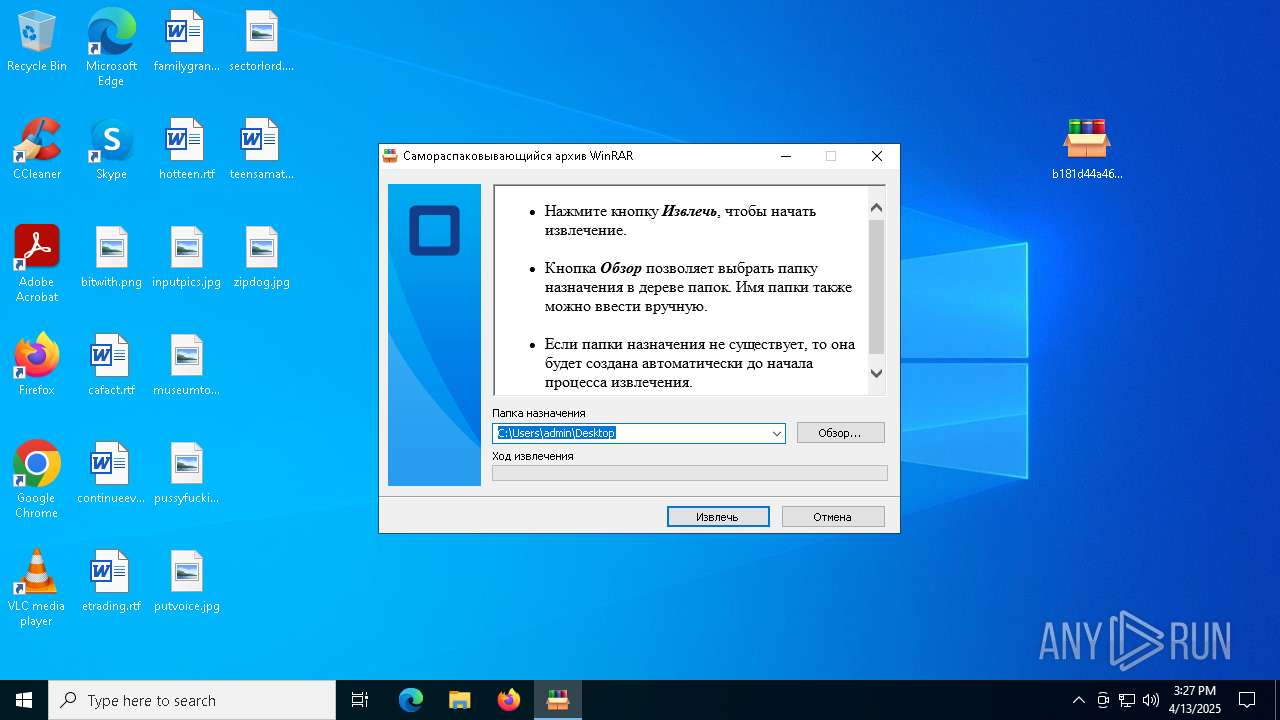
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7988)
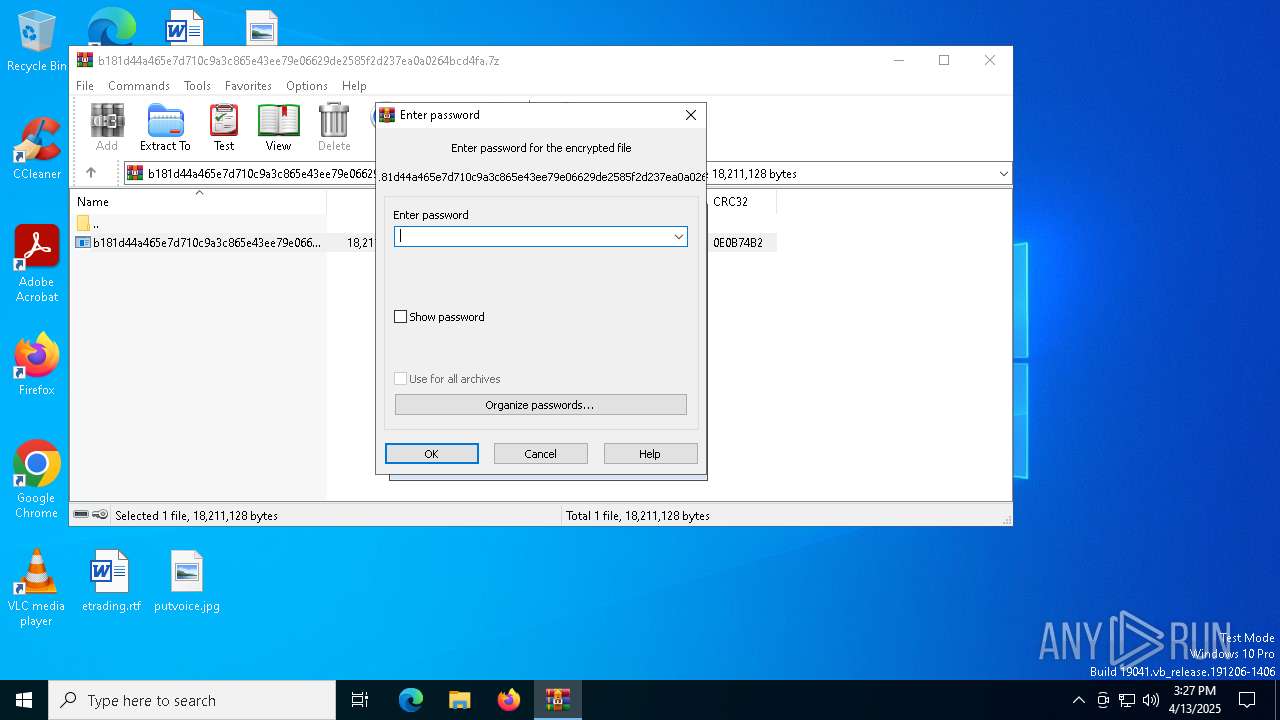
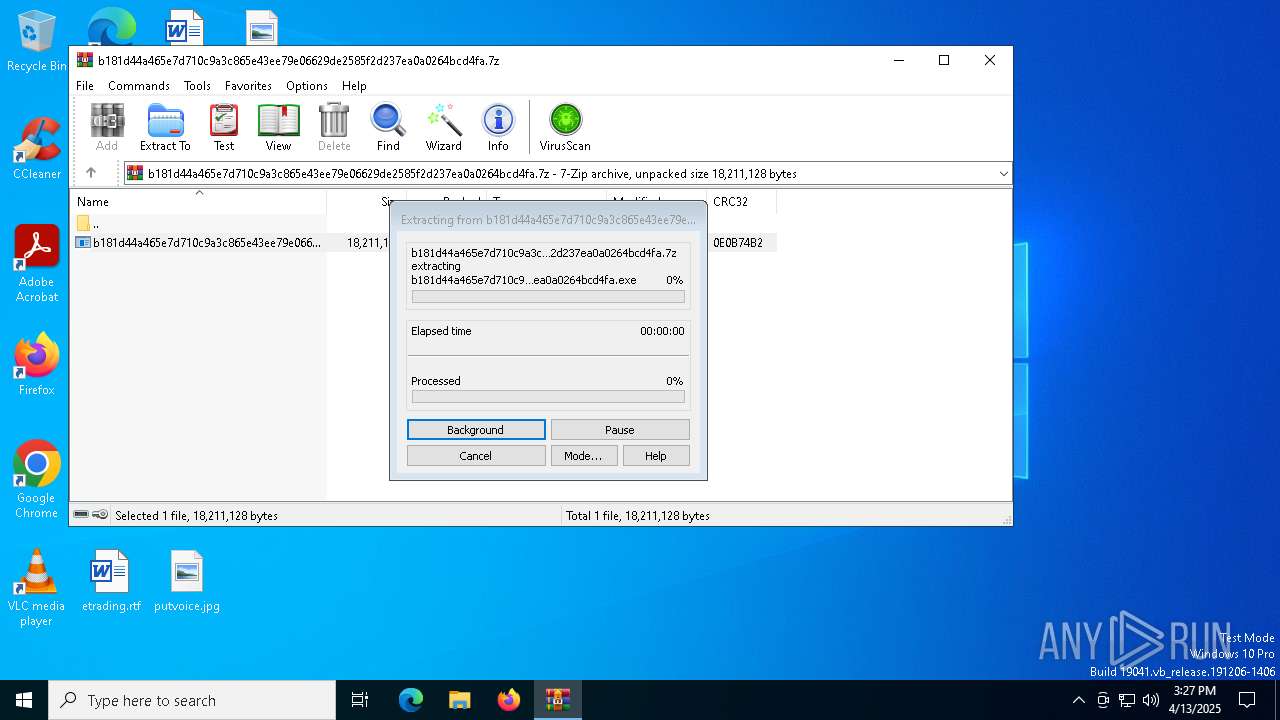
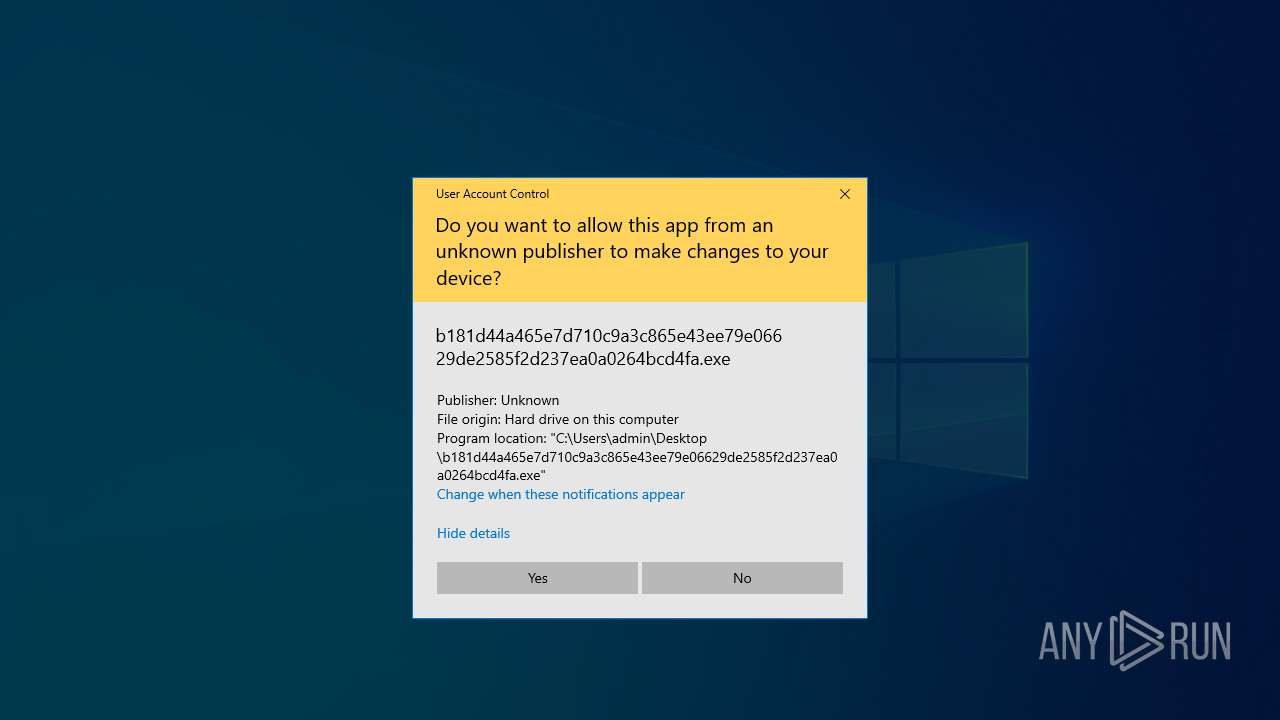
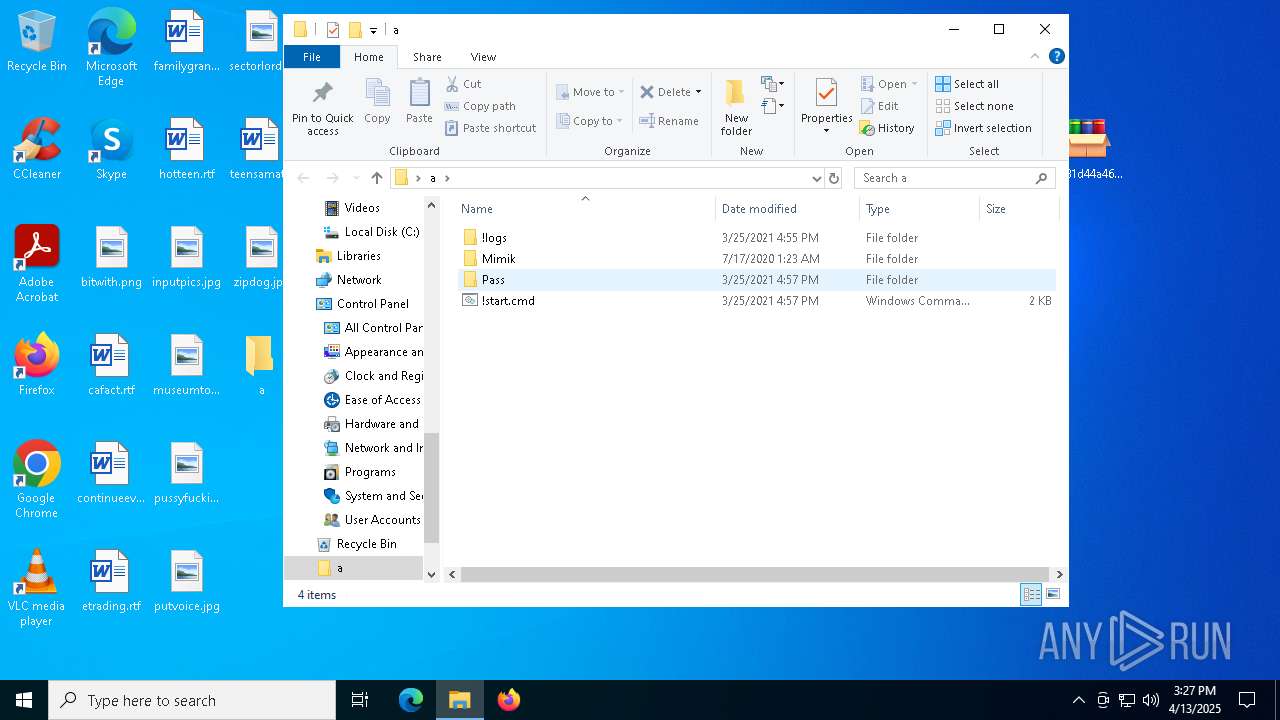
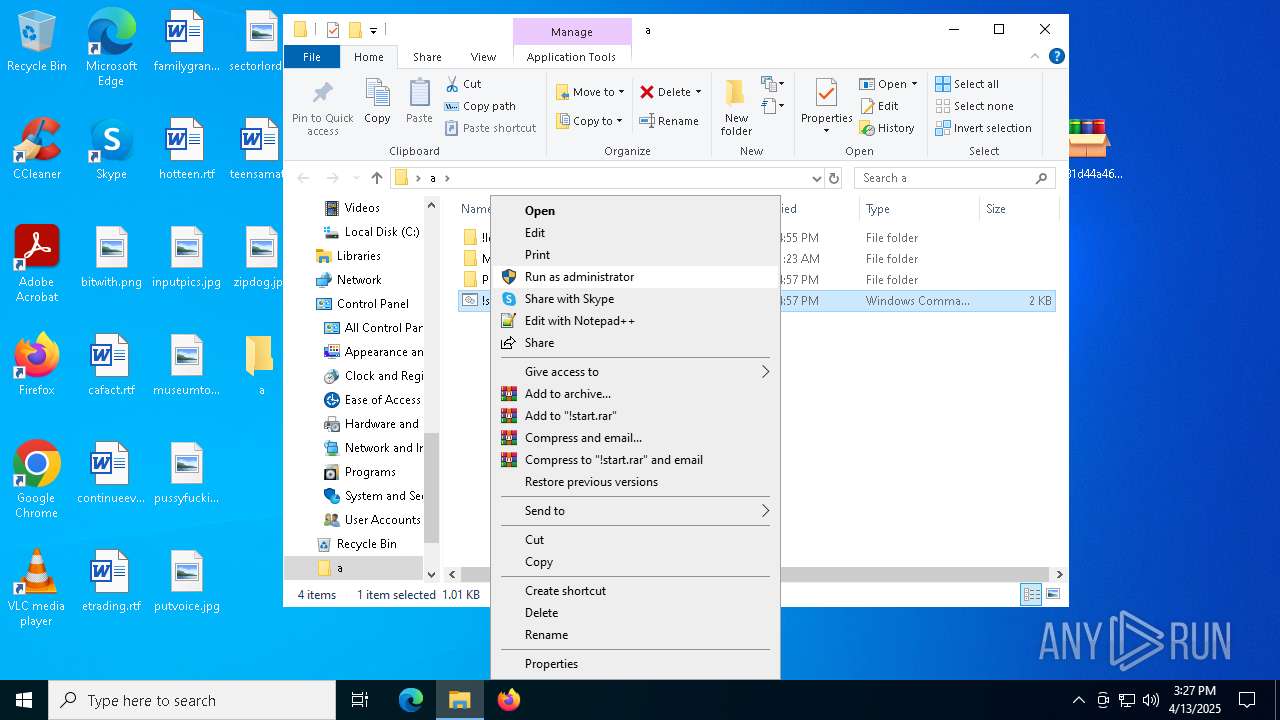
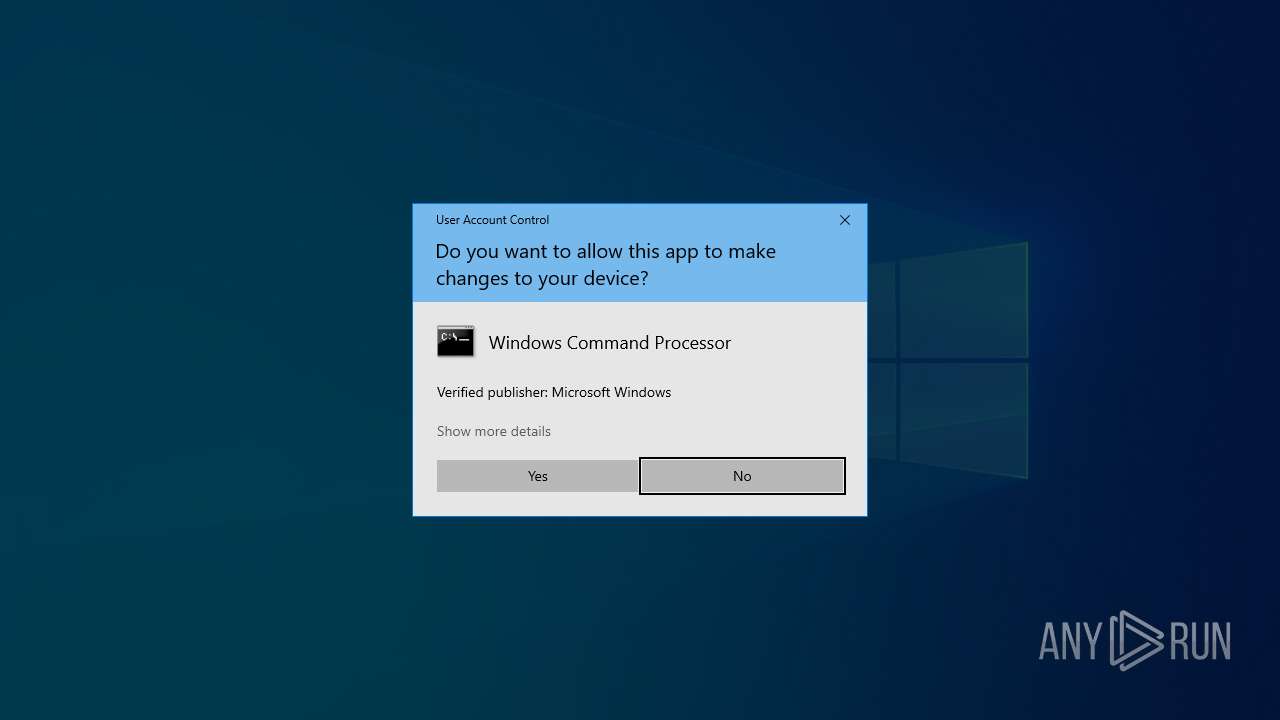
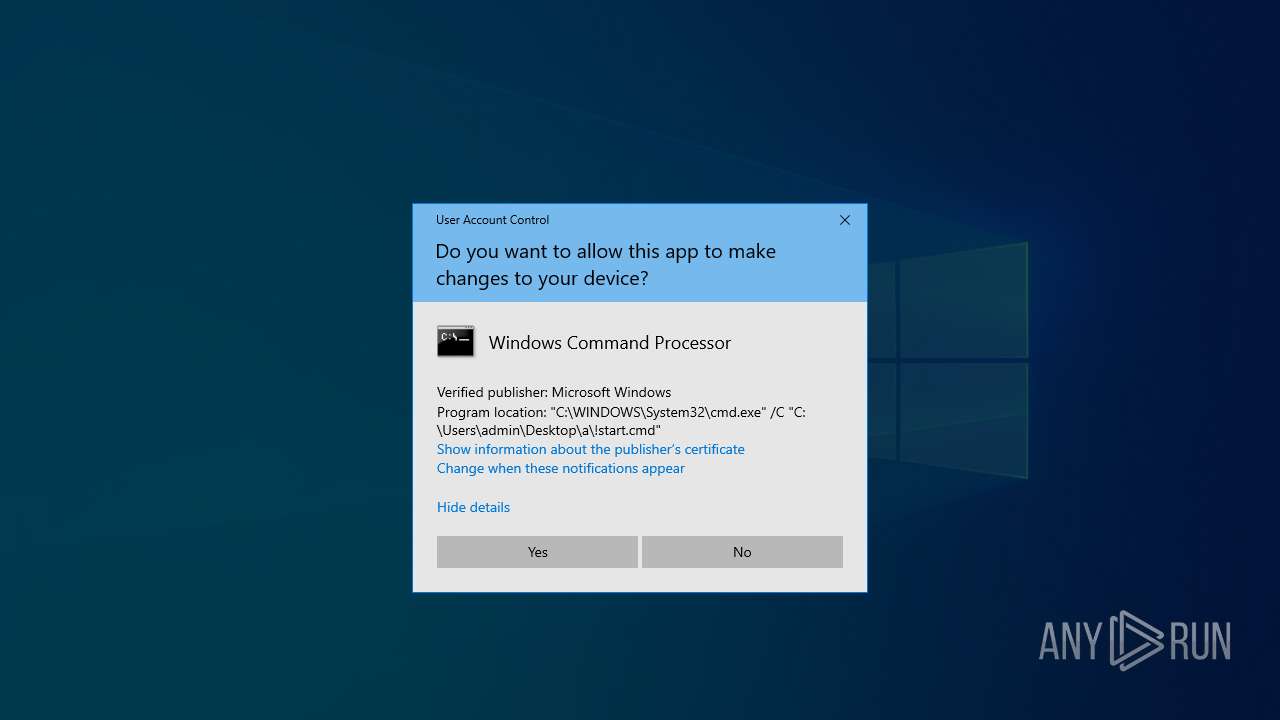
Manual execution by a user
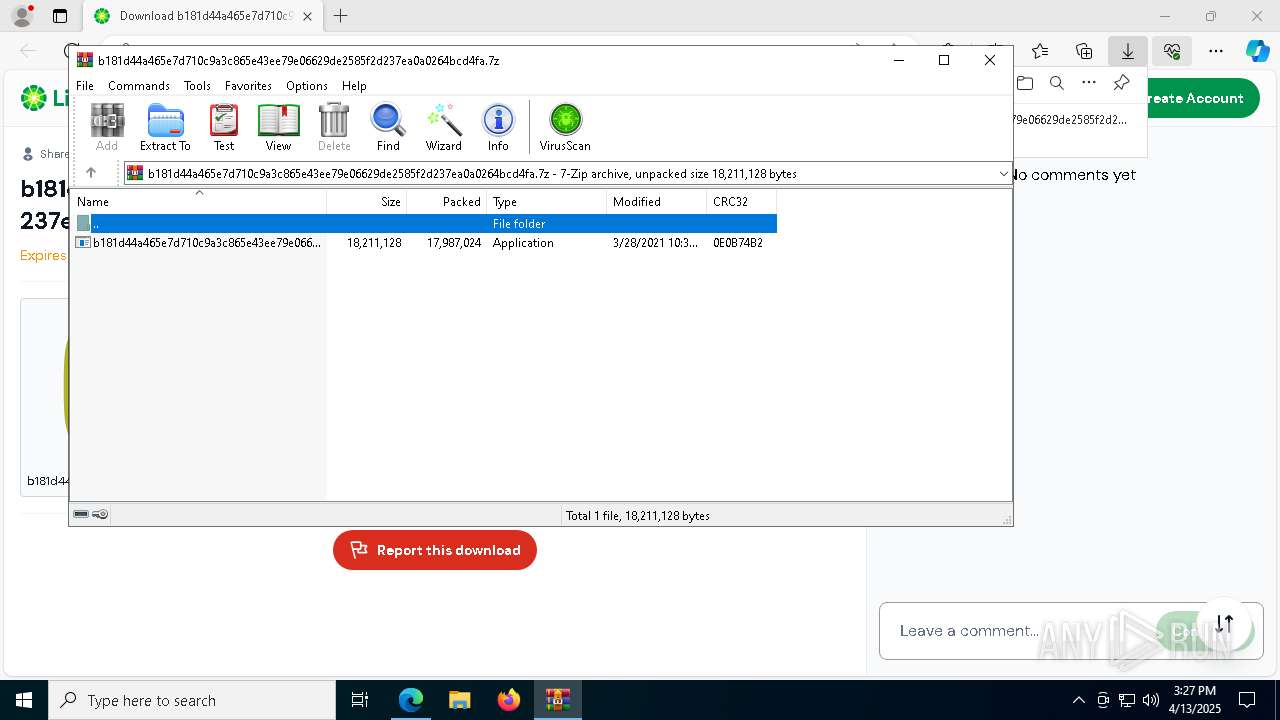
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
- cmd.exe (PID: 7480)
- mspaint.exe (PID: 8064)
Checks proxy server information
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
The sample compiled with english language support
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
- VNCPassView.exe (PID: 7312)
- VNCPassViewSrv.exe (PID: 7208)
- mailpv.exe (PID: 4880)
- mspass.exe (PID: 6184)
- rdpv.exe (PID: 1096)
- RouterPassView.exe (PID: 5960)
The sample compiled with chinese language support
- b181d44a465e7d710c9a3c865e43ee79e06629de2585f2d237ea0a0264bcd4fa.exe (PID: 6800)
Starts MODE.COM to configure console settings
- mode.com (PID: 6592)
NirSoft software is detected
- netpass64.exe (PID: 7732)
- VNCPassView.exe (PID: 7312)
- WirelessKeyView64.exe (PID: 3300)
- mspass.exe (PID: 6184)
- Dialupass.exe (PID: 5640)
- mailpv.exe (PID: 4880)
- rdpv.exe (PID: 1096)
- RouterPassView.exe (PID: 5960)
- NetRouteView.exe (PID: 2140)
- WirelessKeyView64.exe (PID: 7356)
Creates files in the program directory
- VNCPassViewSrv.exe (PID: 7208)
- mailpvSrv.exe (PID: 7440)
- mspassSrv.exe (PID: 4776)
- RouterPassViewSrv.exe (PID: 4728)
- rdpvSrv.exe (PID: 6252)
Reads the machine GUID from the registry
- mspass.exe (PID: 6184)
- mimik.exe (PID: 6192)
- WebBrowserPassView.exe (PID: 1628)
Create files in a temporary directory
- WebBrowserPassView.exe (PID: 1628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
240
Monitored processes
108
Malicious processes
18
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x304,0x308,0x30c,0x300,0x314,0x7ffc88825fd8,0x7ffc88825fe4,0x7ffc88825ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 756 | C:\WINDOWS\system32\lsass.exe | C:\Windows\System32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2872 --field-trial-handle=2344,i,8783817349315275988,8287688358508070361,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7388 --field-trial-handle=2292,i,1341734109439272818,12630183836362204656,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffc88825fd8,0x7ffc88825fe4,0x7ffc88825ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3348 --field-trial-handle=2352,i,15639505309592701005,7515091813501216733,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | .\Pass\rdpv.exe | C:\Users\admin\Desktop\a\Pass\rdpv.exe | cmd.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: Password Recovery for Remote Desktop Version: 1.02 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4804 --field-trial-handle=2344,i,8783817349315275988,8287688358508070361,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2804 --field-trial-handle=2352,i,15639505309592701005,7515091813501216733,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1628 | .\Pass\WebBrowserPassView.exe | C:\Users\admin\Desktop\a\Pass\WebBrowserPassView.exe | cmd.exe | ||||||||||||
User: admin Company: NirSoft Integrity Level: HIGH Description: Web Browser Password Viewer Version: 2.00 Modules
| |||||||||||||||
Total events
17 944
Read events
17 798
Write events
143
Delete events
3
Modification events
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B1A860DA40912F00 | |||
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 392F6ADA40912F00 | |||
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F1BC2919-2D0B-4880-B911-EC3D7BFC2897} | |||
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3F52ADAA-11EE-4DBB-AB5C-0BB4822FAC2E} | |||
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {724FB398-77FF-4168-BD7B-4150CA4124F3} | |||
| (PID) Process: | (7000) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262796 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F983C6AB-7C2A-457C-8966-9D71BC46EAE3} | |||
Executable files
86
Suspicious files
469
Text files
116
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b75b.TMP | — | |
MD5:— | SHA256:— | |||
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7000 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
74
DNS requests
85
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.238.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7444 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7444 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.32.238.34:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7000 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7200 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7200 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7200 | msedge.exe | 104.22.36.240:443 | limewire.com | CLOUDFLARENET | — | unknown |
7200 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
limewire.com |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7200 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
7200 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
7200 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7200 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |