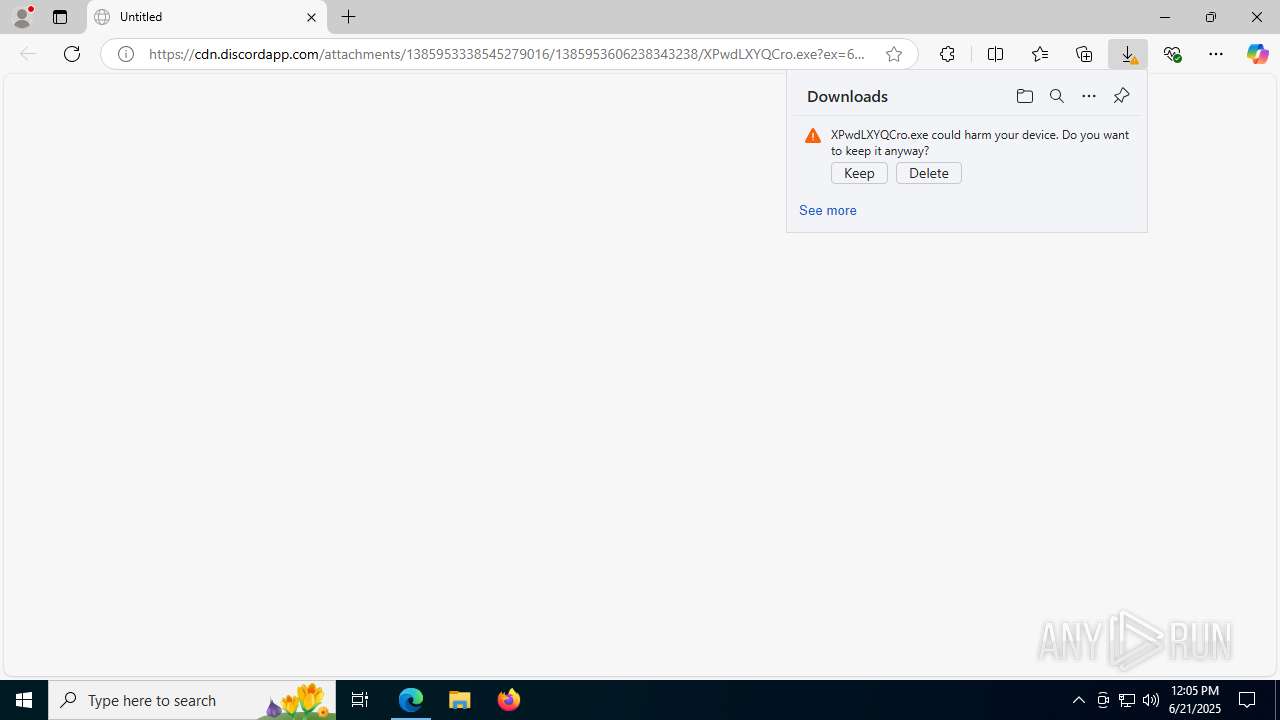
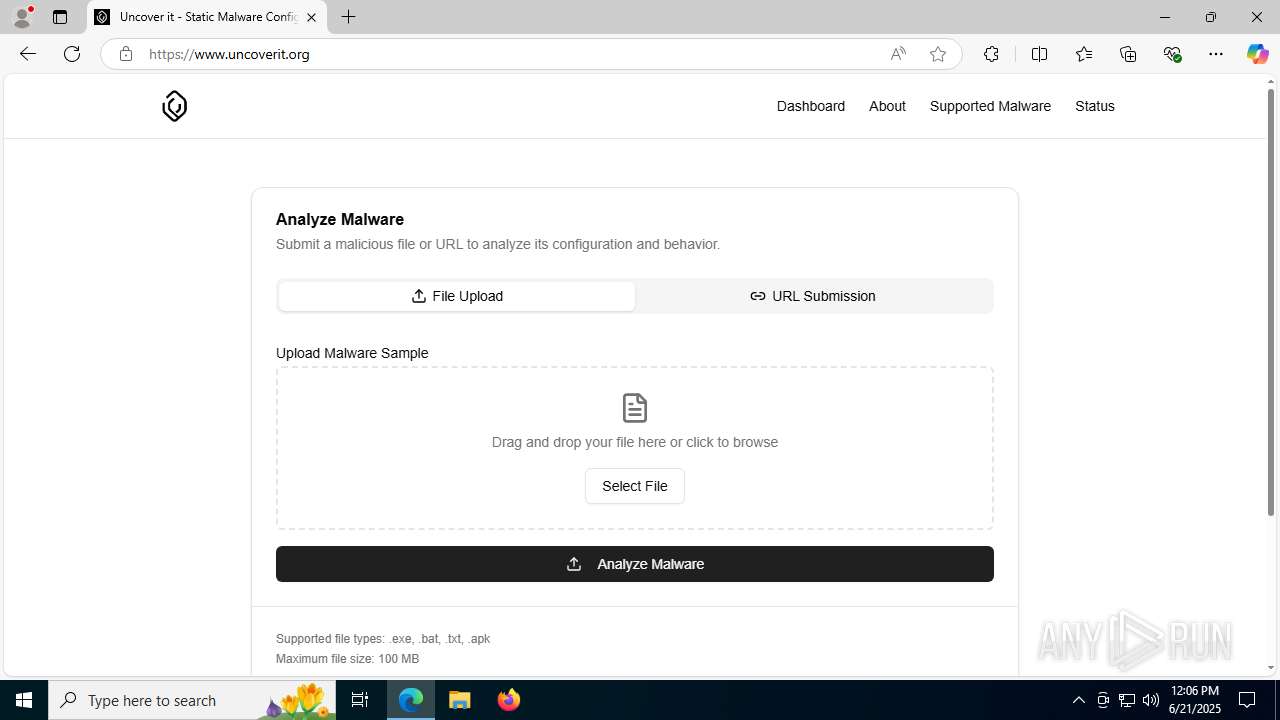
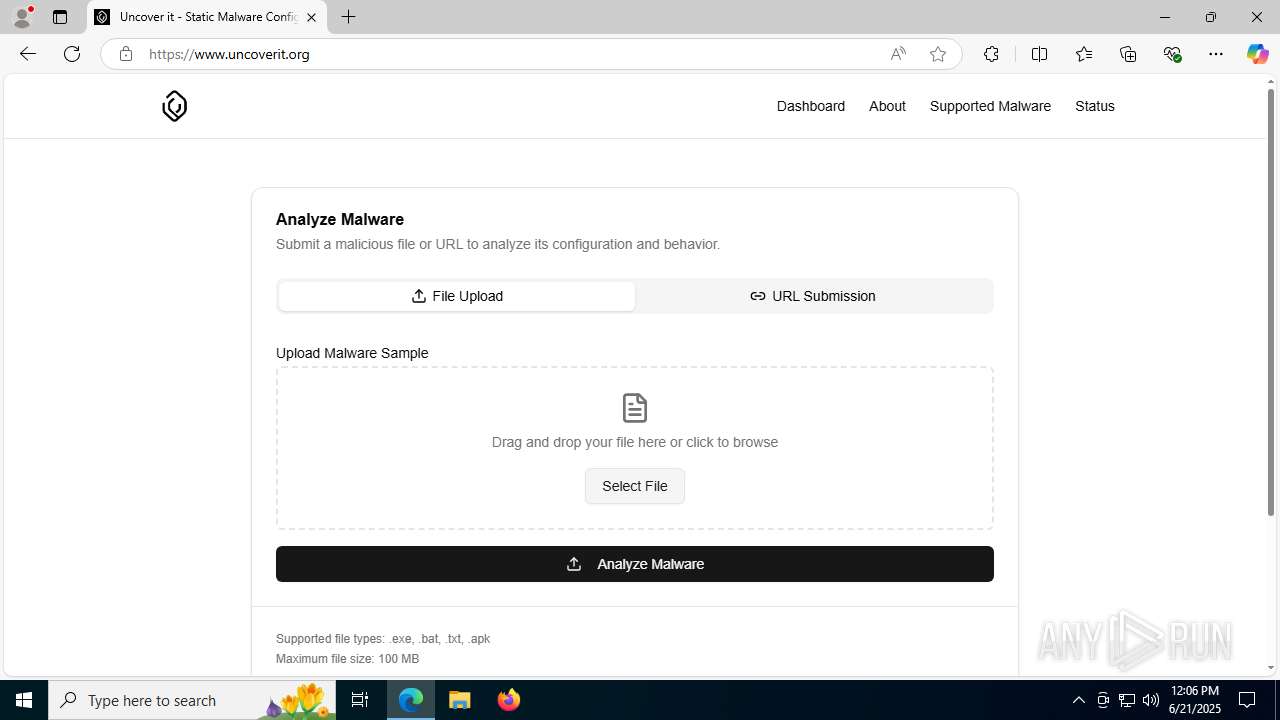
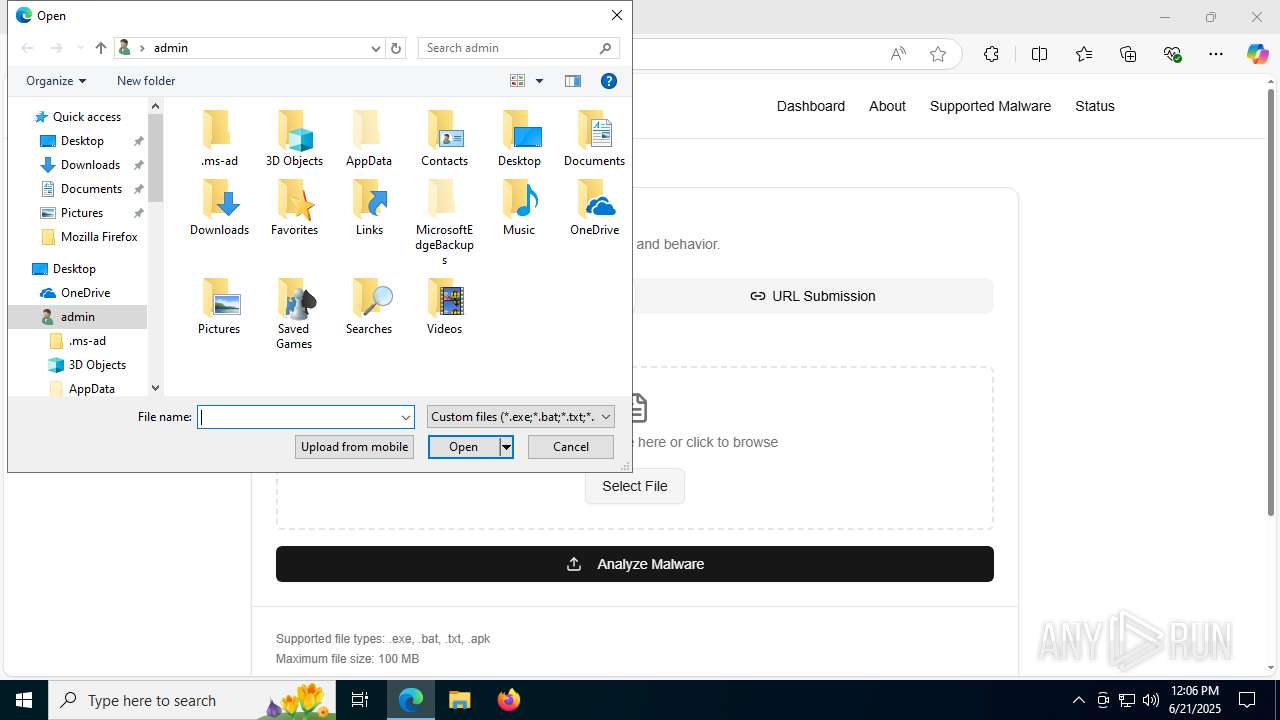
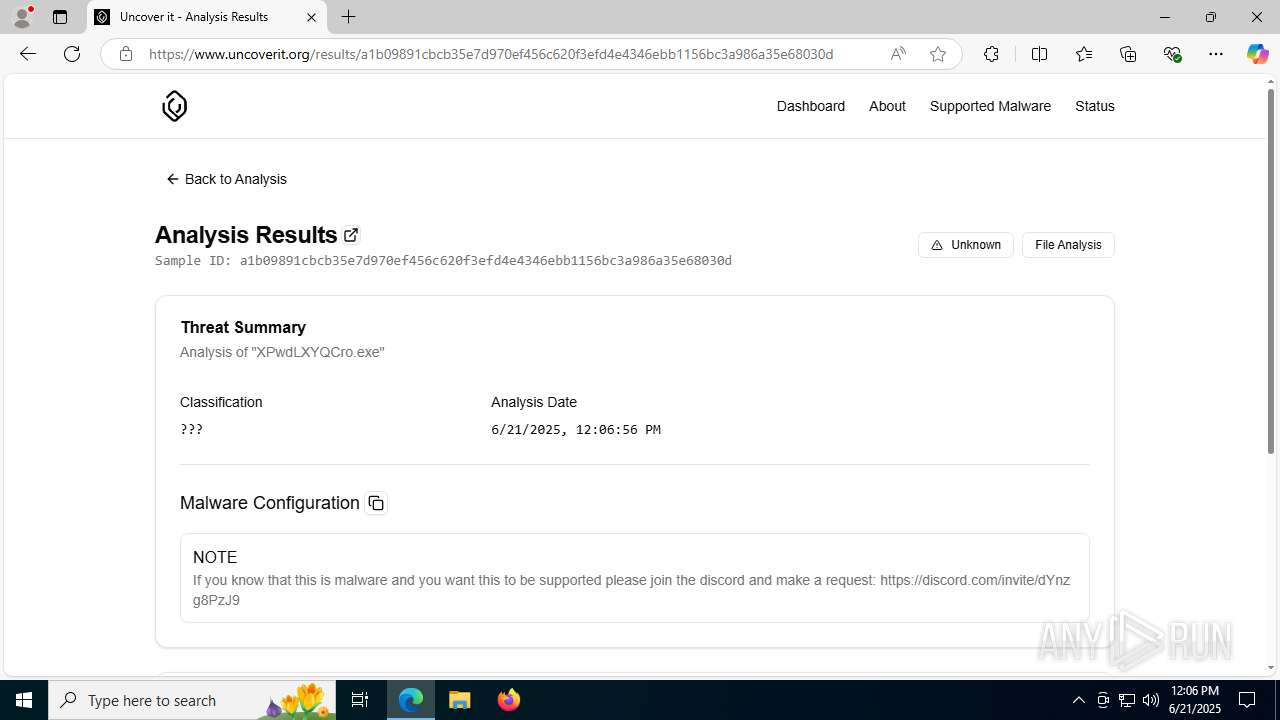
| URL: | https://cdn.discordapp.com/attachments/1385953338545279016/1385953606238343238/XPwdLXYQCro.exe?ex=6857f161&is=68569fe1&hm=0235f3fd102089e46abb8c2c681d56330703c524ec0e9acda60979951303e071& |
| Full analysis: | https://app.any.run/tasks/96928d47-e800-4a41-9c06-4a832a85afd9 |
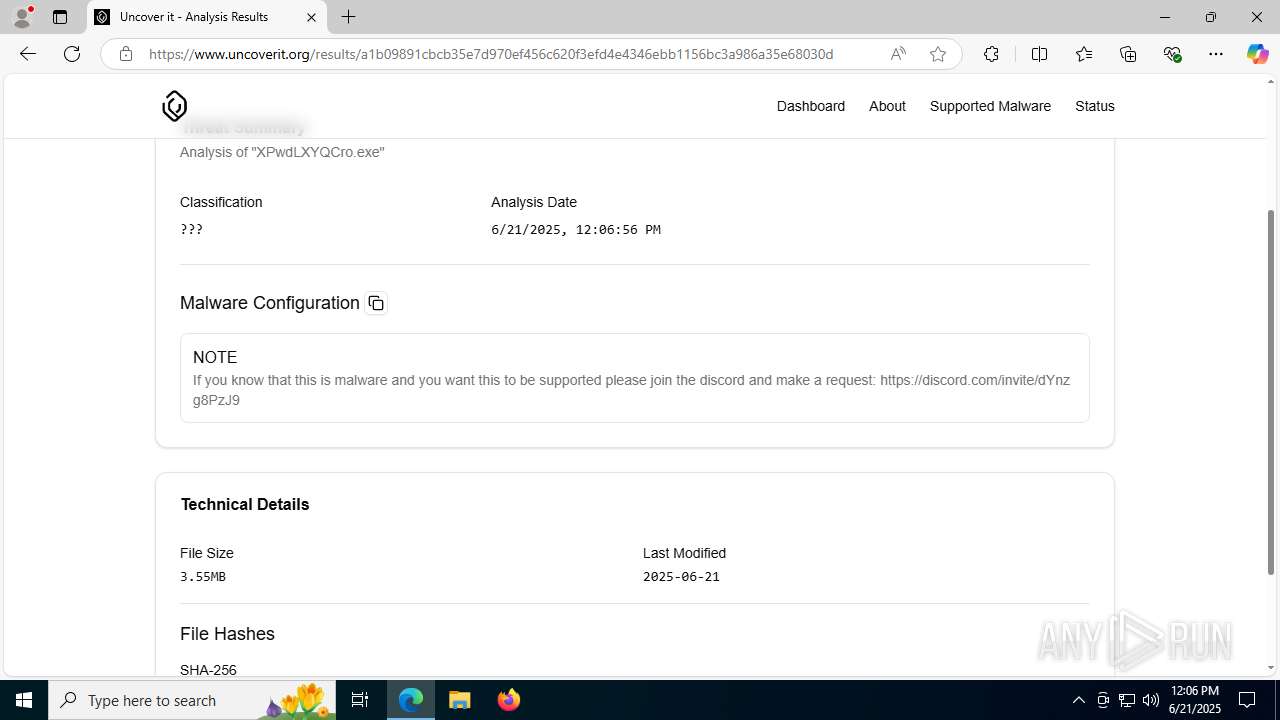
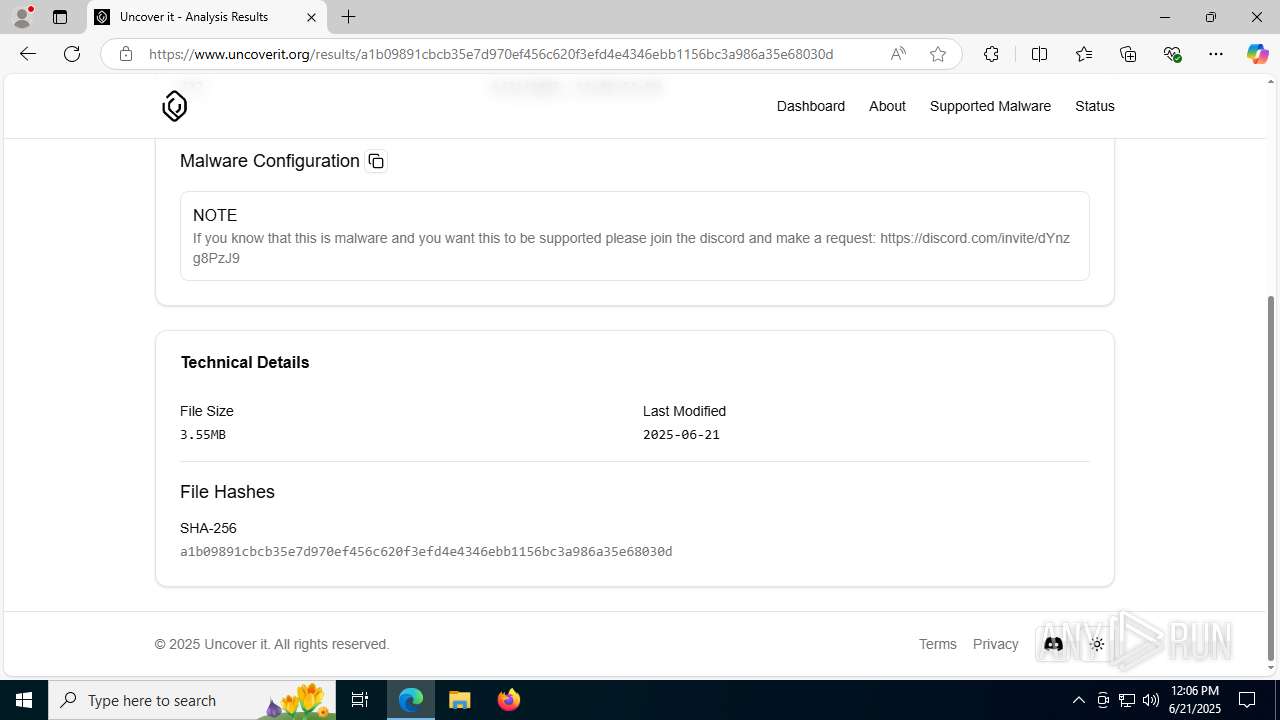
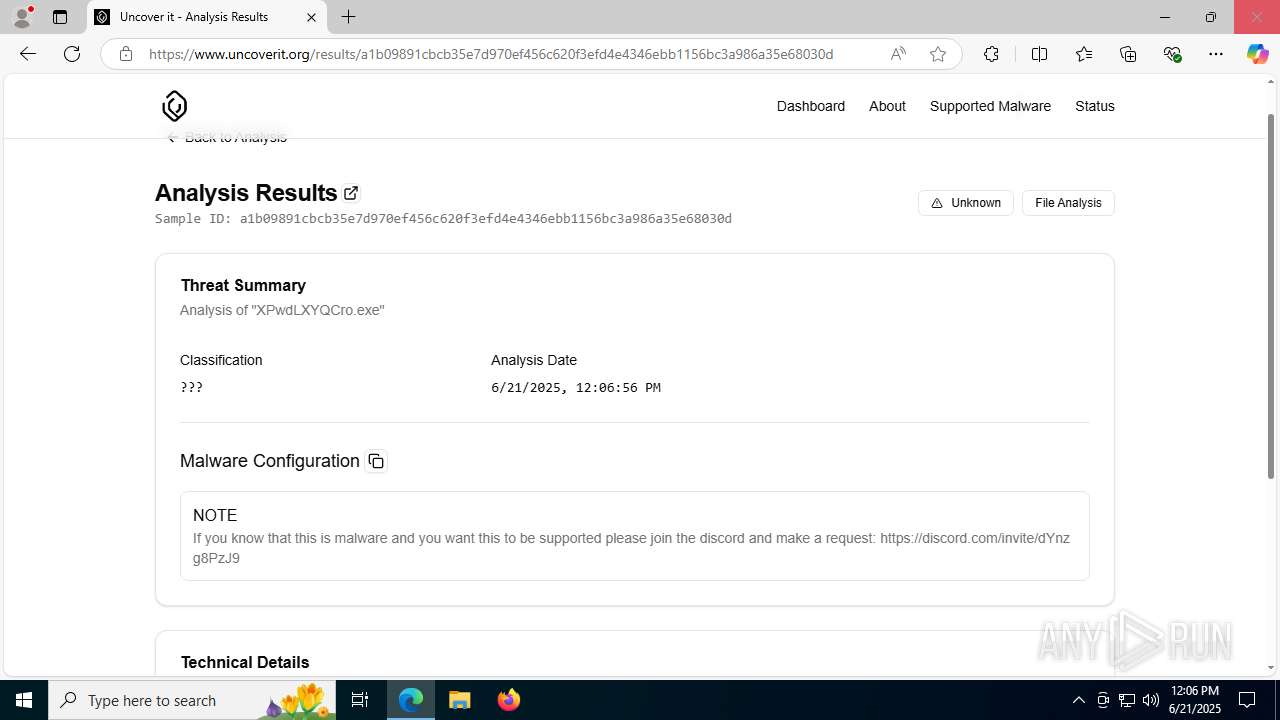
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 21, 2025, 12:05:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BD5C0CBFB8EE63DCE361D6494813300B |
| SHA1: | B4B4706BFACC73140ED509B399027D85AF707E31 |
| SHA256: | 97B5F395B8BCB945BD5AE95B9A6BD65520E639940235F6E003E67607CE42920B |
| SSDEEP: | 3:N8cCWdy6//PdQhWWcScsgQWTYdWiWdnQXQQYUQxVauc/ndGXGyBQTzSVUpAcEPkX:2cry6XPShRcSb1WiWdnFprazdGWyBQSA |
MALICIOUS
Changes the autorun value in the registry
- XPwdLXYQCro.exe (PID: 7916)
- XPwdLXYQCro.exe (PID: 8112)
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4236)
Changes Windows Defender settings
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4236)
LUMMA has been detected (SURICATA)
- msedge.exe (PID: 472)
SUSPICIOUS
Discord domain found in command line (probably downloading payload)
- msedge.exe (PID: 4676)
Executable content was dropped or overwritten
- XPwdLXYQCro.exe (PID: 7916)
- XPwdLXYQCro.exe (PID: 8112)
Reads security settings of Internet Explorer
- XPwdLXYQCro.exe (PID: 7916)
Starts NET.EXE to display or manage information about active sessions
- XPwdLXYQCro.exe (PID: 7916)
- net.exe (PID: 7952)
- XPwdLXYQCro.exe (PID: 8112)
- net.exe (PID: 8164)
Application launched itself
- XPwdLXYQCro.exe (PID: 7916)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4236)
Reads the date of Windows installation
- XPwdLXYQCro.exe (PID: 7916)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4236)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4236)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 8052)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7336)
- XPwdLXYQCro.exe (PID: 8112)
- powershell.exe (PID: 4236)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4236)
BASE64 encoded PowerShell command has been detected
- XPwdLXYQCro.exe (PID: 8112)
Base64-obfuscated command line is found
- XPwdLXYQCro.exe (PID: 8112)
Detected use of alternative data streams (AltDS)
- XPwdLXYQCro.exe (PID: 8112)
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 472)
INFO
Launching a file from a Registry key
- XPwdLXYQCro.exe (PID: 7916)
- XPwdLXYQCro.exe (PID: 8112)
Reads the computer name
- XPwdLXYQCro.exe (PID: 7916)
- identity_helper.exe (PID: 7496)
Executable content was dropped or overwritten
- msedge.exe (PID: 472)
- msedge.exe (PID: 4676)
Application launched itself
- msedge.exe (PID: 4676)
Checks supported languages
- identity_helper.exe (PID: 7496)
- XPwdLXYQCro.exe (PID: 8112)
- XPwdLXYQCro.exe (PID: 7916)
Process checks computer location settings
- XPwdLXYQCro.exe (PID: 7916)
Gets data length (POWERSHELL)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4236)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 8052)
Creates files or folders in the user directory
- XPwdLXYQCro.exe (PID: 8112)
- XPwdLXYQCro.exe (PID: 7916)
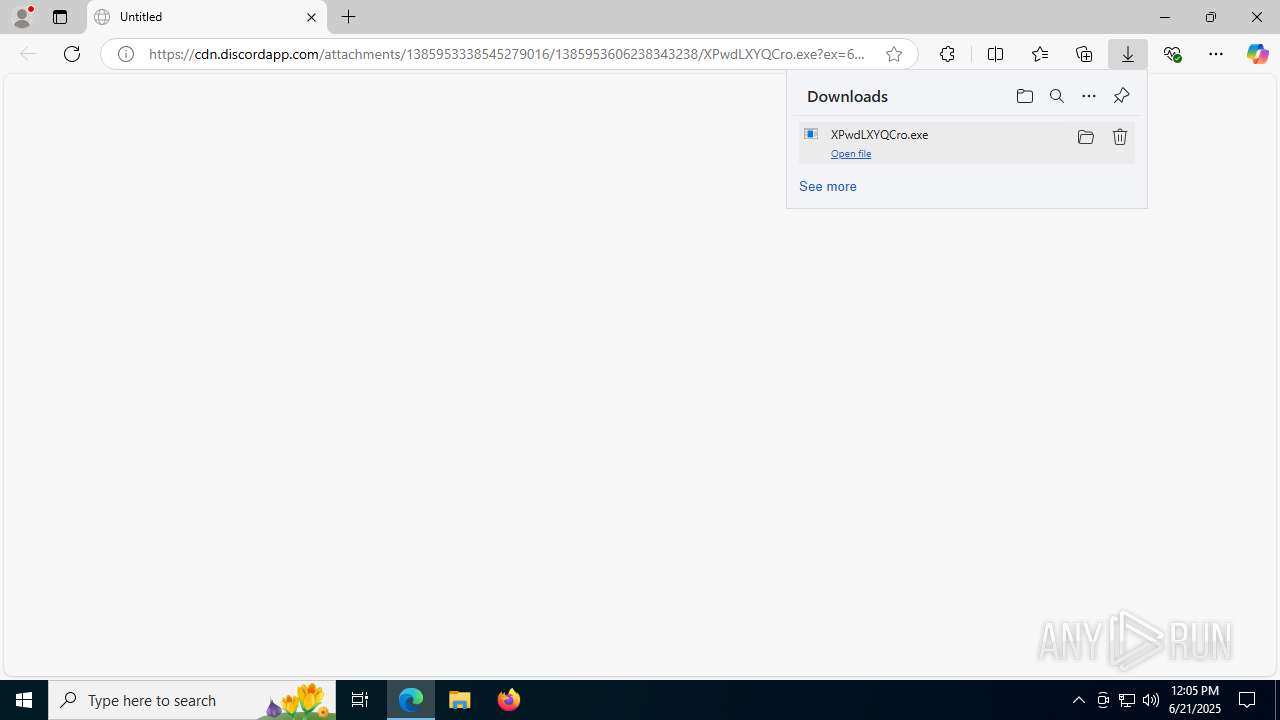
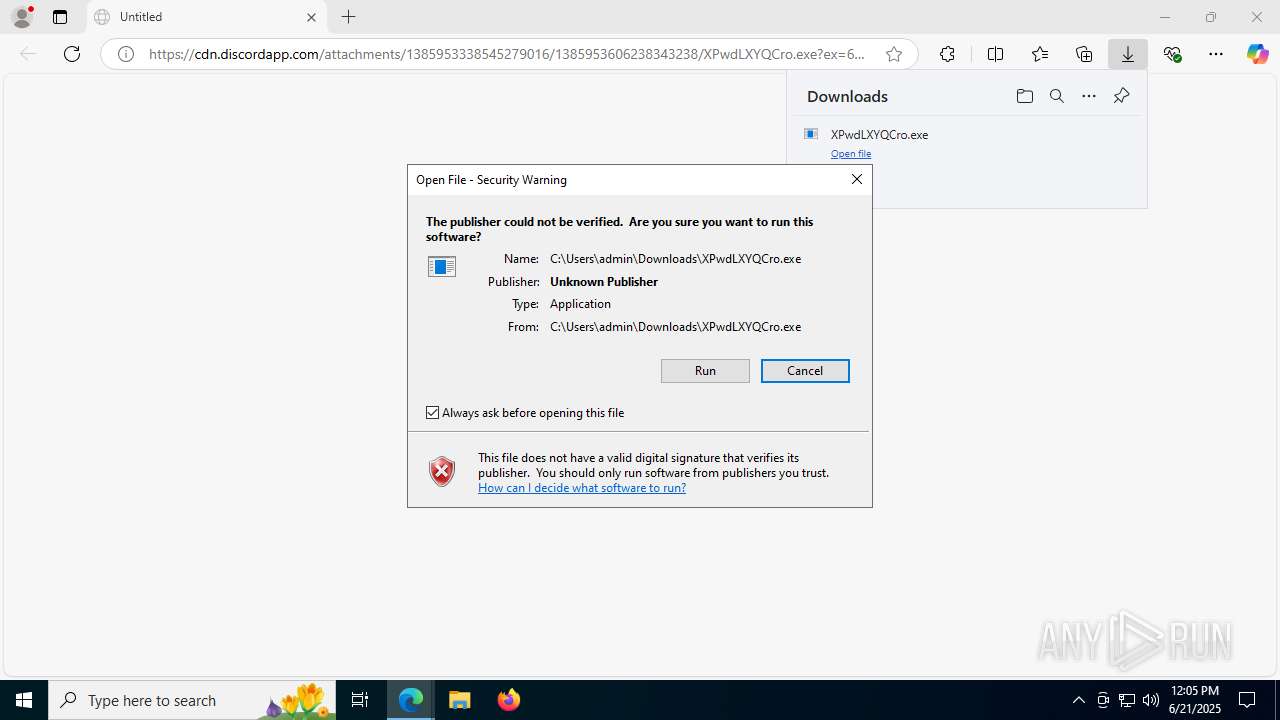
Launching a file from the Downloads directory
- msedge.exe (PID: 4676)
Reads Environment values
- identity_helper.exe (PID: 7496)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 592)
- powershell.exe (PID: 7972)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 8052)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7972)
- powershell.exe (PID: 592)
Found Base64 encoded text manipulation via PowerShell (YARA)
- XPwdLXYQCro.exe (PID: 8112)
Found Base64 encoded access to Windows Identity via PowerShell (YARA)
- XPwdLXYQCro.exe (PID: 8112)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
194
Monitored processes
54
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2100,i,14219769310672711836,15740008008866280327,262144 --variations-seed-version --mojo-platform-channel-handle=2600 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 592 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4876,i,14219769310672711836,15740008008866280327,262144 --variations-seed-version --mojo-platform-channel-handle=6248 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5096,i,14219769310672711836,15740008008866280327,262144 --variations-seed-version --mojo-platform-channel-handle=5564 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6096,i,14219769310672711836,15740008008866280327,262144 --variations-seed-version --mojo-platform-channel-handle=6112 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --always-read-main-dll --field-trial-handle=5796,i,14219769310672711836,15740008008866280327,262144 --variations-seed-version --mojo-platform-channel-handle=5808 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --always-read-main-dll --field-trial-handle=7068,i,14219769310672711836,15740008008866280327,262144 --variations-seed-version --mojo-platform-channel-handle=4868 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2364,i,14219769310672711836,15740008008866280327,262144 --variations-seed-version --mojo-platform-channel-handle=2360 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3844 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4116,i,14219769310672711836,15740008008866280327,262144 --variations-seed-version --mojo-platform-channel-handle=3720 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3876 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
41 966
Read events
41 864
Write events
100
Delete events
2
Modification events
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 34C07715AA962F00 | |||
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
| (PID) Process: | (4676) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721714 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4F709A43-8189-443E-9B88-BEBADF82D09F} | |||
Executable files
11
Suspicious files
141
Text files
47
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176e98.TMP | — | |
MD5:— | SHA256:— | |||
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176ea8.TMP | — | |
MD5:— | SHA256:— | |||
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176eb7.TMP | — | |
MD5:— | SHA256:— | |||
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176ec7.TMP | — | |
MD5:— | SHA256:— | |||
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176ec7.TMP | — | |
MD5:— | SHA256:— | |||
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176eb7.TMP | — | |
MD5:— | SHA256:— | |||
| 4676 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
107
DNS requests
97
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7632 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
472 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:J3fmZVhJ-ASAXO759fxVg7Bcr6oUt6bhenx6c0a-OSU&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.24.77.22:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1200 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
472 | msedge.exe | GET | 200 | 46.37.14.19:80 | http://uncover.it/stileV2015.css | unknown | — | — | unknown |
1268 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7632 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
472 | msedge.exe | GET | 200 | 142.250.184.202:80 | http://fonts.googleapis.com/css?family=Lato%3A300%2C400%2C700%2C400italic%7CMontserrat%3A700%7CHomemade+Apple&subset=latin%2Clatin-ext | unknown | — | — | whitelisted |
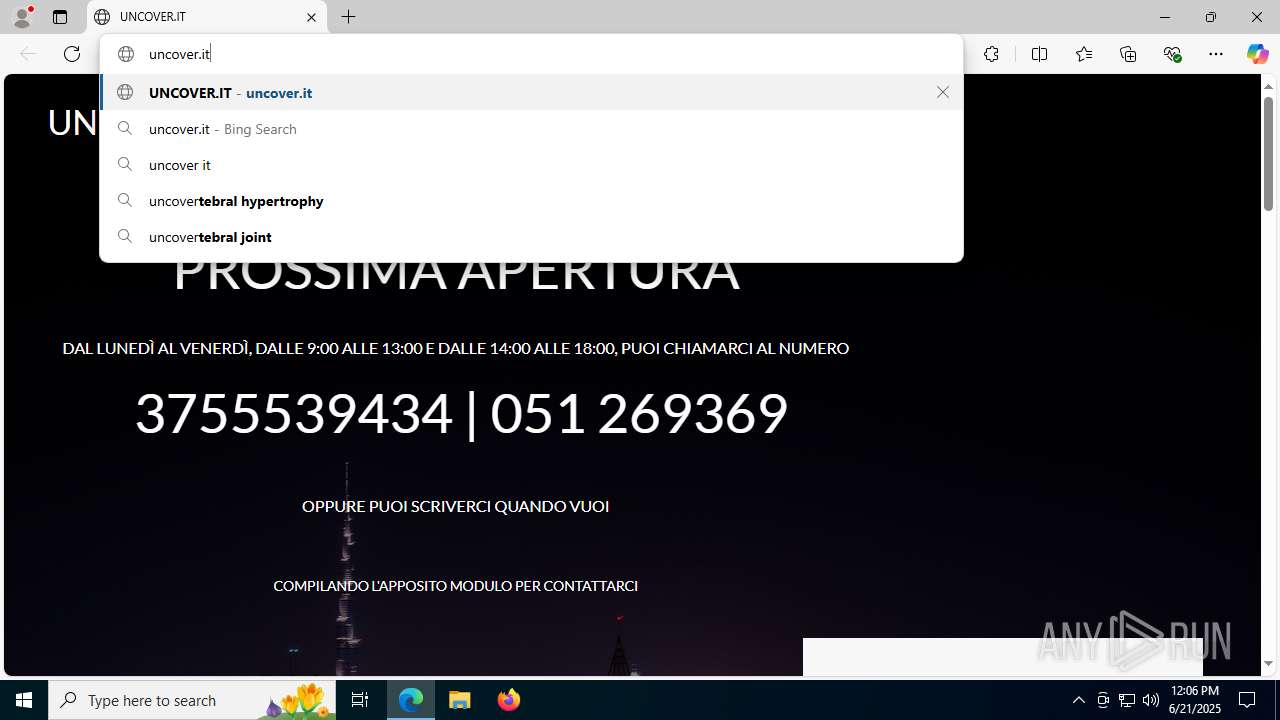
472 | msedge.exe | GET | 200 | 46.37.14.19:80 | http://uncover.it/ | unknown | — | — | unknown |
472 | msedge.exe | GET | 200 | 46.37.14.19:80 | http://uncover.it/immagini/aportataTEMP175.jpg | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2276 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
472 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
472 | msedge.exe | 162.159.130.233:443 | cdn.discordapp.com | CLOUDFLARENET | — | whitelisted |
472 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
472 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
472 | msedge.exe | 2.16.204.153:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
cdn.discordapp.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
472 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
472 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
472 | msedge.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Suspected Lumma domain by CrossDomain (uncoverit .org) |
472 | msedge.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Suspected Lumma domain by CrossDomain (uncoverit .org) |
472 | msedge.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Suspected Lumma domain by CrossDomain (uncoverit .org) |
472 | msedge.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Suspected Lumma domain by CrossDomain (uncoverit .org) |
472 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |