| File name: | powershell.exe |
| Full analysis: | https://app.any.run/tasks/ed047acc-9729-4a82-814c-e7b7ae6e0b94 |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
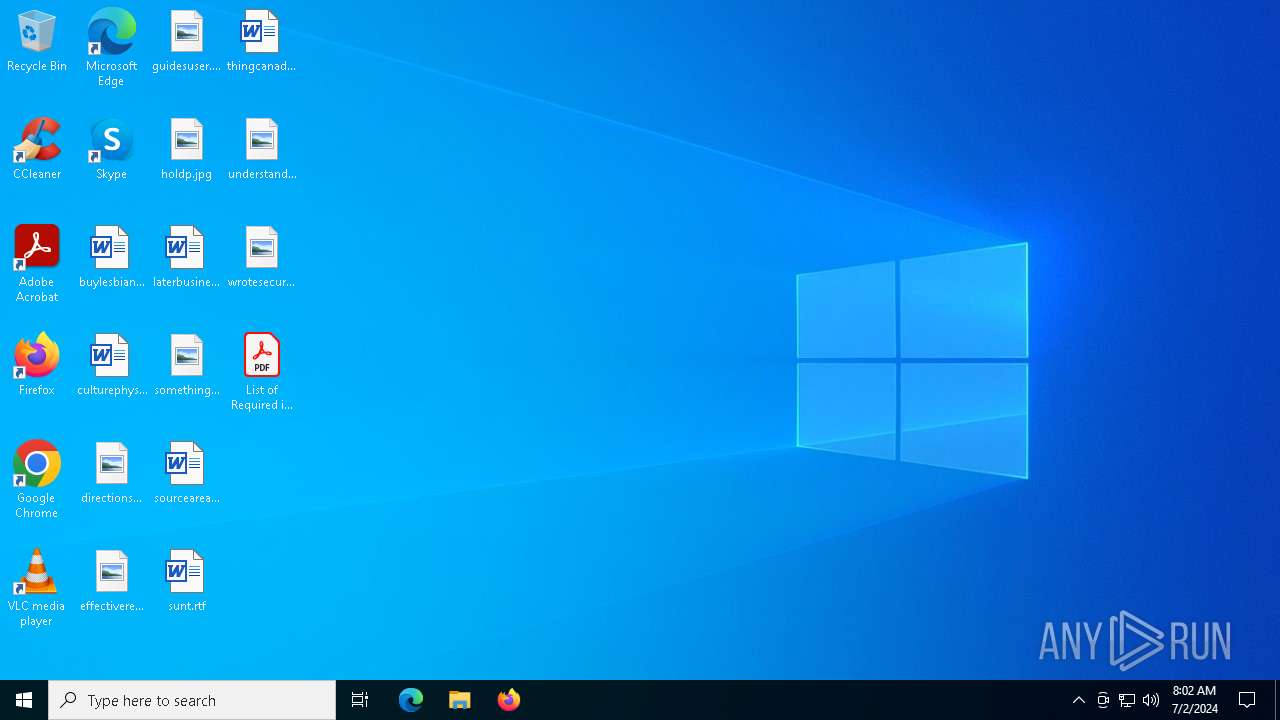
| Analysis date: | July 02, 2024, 08:02:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 2E5A8590CF6848968FC23DE3FA1E25F1 |
| SHA1: | 801262E122DB6A2E758962896F260B55BBD0136A |
| SHA256: | 9785001B0DCF755EDDB8AF294A373C0B87B2498660F724E76C4D53F9C217C7A3 |
| SSDEEP: | 12288:oufZaQ9EEEEEEEE4OvnEEEEEEEE4NDzw9jXhVXVVVV3+VVVVCNGxDx:outEEEEEEEE4MnEEEEEEEE4NDyjXbCx |
MALICIOUS
Drops the executable file immediately after the start
- powershell.exe (PID: 3532)
GULOADER has been detected
- powershell.exe (PID: 6348)
- powershell.exe (PID: 7000)
Run PowerShell with an invisible window
- powershell.exe (PID: 4804)
RHADAMANTHYS has been detected (SURICATA)
- OpenWith.exe (PID: 6832)
- OOBE-Maintenance.exe (PID: 5332)
RHADAMANTHYS has been detected (YARA)
- OOBE-Maintenance.exe (PID: 5332)
Actions looks like stealing of personal data
- OOBE-Maintenance.exe (PID: 5332)
SUSPICIOUS
Process drops legitimate windows executable
- powershell.exe (PID: 3532)
Reads the date of Windows installation
- powershell.exe (PID: 3532)
Starts a Microsoft application from unusual location
- powershell.exe (PID: 3532)
Checks Windows Trust Settings
- powershell.exe (PID: 3532)
- wab.exe (PID: 4544)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3532)
- wab.exe (PID: 4544)
Process checks Powershell history file
- powershell.exe (PID: 3532)
Application launched itself
- powershell.exe (PID: 5896)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 5896)
Likely accesses (executes) a file from the Public directory
- wscript.exe (PID: 6276)
The process executes VB scripts
- powershell.exe (PID: 5896)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6276)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 6276)
- powershell.exe (PID: 5896)
- powershell.exe (PID: 6348)
Base64-obfuscated command line is found
- wscript.exe (PID: 6276)
- powershell.exe (PID: 6348)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 6348)
- powershell.exe (PID: 7000)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 7000)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 7000)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 7000)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 6832)
Loads DLL from Mozilla Firefox
- OOBE-Maintenance.exe (PID: 5332)
Searches for installed software
- OOBE-Maintenance.exe (PID: 5332)
Contacting a server suspected of hosting an CnC
- OpenWith.exe (PID: 6832)
- OOBE-Maintenance.exe (PID: 5332)
Executes application which crashes
- wab.exe (PID: 4544)
INFO
Process checks computer location settings
- powershell.exe (PID: 3532)
Checks supported languages
- powershell.exe (PID: 3532)
- wmplayer.exe (PID: 6796)
- wab.exe (PID: 4544)
Reads the computer name
- powershell.exe (PID: 3532)
- wab.exe (PID: 4544)
Reads the machine GUID from the registry
- powershell.exe (PID: 3532)
- wmplayer.exe (PID: 6796)
- wab.exe (PID: 4544)
Process checks Powershell version
- powershell.exe (PID: 3532)
Create files in a temporary directory
- powershell.exe (PID: 3532)
Reads the software policy settings
- powershell.exe (PID: 3532)
- wab.exe (PID: 4544)
Reads Environment values
- powershell.exe (PID: 3532)
Checks current location (POWERSHELL)
- powershell.exe (PID: 3532)
Checks proxy server information
- powershell.exe (PID: 5896)
- powershell.exe (PID: 6348)
- wab.exe (PID: 4544)
Disables trace logs
- powershell.exe (PID: 5896)
- powershell.exe (PID: 6348)
Manual execution by a user
- powershell.exe (PID: 5896)
- OpenWith.exe (PID: 6832)
- OOBE-Maintenance.exe (PID: 5332)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5896)
Application launched itself
- Acrobat.exe (PID: 4804)
- AcroCEF.exe (PID: 6572)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4804)
- powershell.exe (PID: 7000)
Creates or changes the value of an item property via Powershell
- wscript.exe (PID: 6276)
- powershell.exe (PID: 6348)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 7000)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 7000)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6348)
- powershell.exe (PID: 7000)
Creates files or folders in the user directory
- wab.exe (PID: 4544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2096:03:14 04:00:21+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.2 |
| CodeSize: | 38400 |
| InitializedDataSize: | 418304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x42a0 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 10 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.19041.3996 |
| ProductVersionNumber: | 10.0.19041.3996 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows PowerShell |
| FileVersion: | 10.0.19041.3996 (WinBuild.160101.0800) |
| InternalName: | POWERSHELL |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | PowerShell.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.19041.3996 |
Total processes
160
Monitored processes
21
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1112 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" --type=renderer /prefetch:1 "C:\Users\admin\Desktop\List of Required items and services.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | Acrobat.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Exit code: 1 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1708 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4544 -s 1772 | C:\Windows\SysWOW64\WerFault.exe | — | wab.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2448 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3532 | "C:\Users\admin\AppData\Local\Temp\powershell.exe" | C:\Users\admin\AppData\Local\Temp\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3716 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | OOBE-Maintenance.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4544 | "C:\Program Files (x86)\windows mail\wab.exe" | C:\Program Files (x86)\Windows Mail\wab.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Contacts Exit code: 3221226505 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4804 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -win hidden C:\Windows\System32\WindowsPowerShell\v1.0=iex "[Environment]::GetEnvironmentVariable('public') + '\\f170vy.vbs'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4804 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" "C:\Users\admin\Desktop\List of Required items and services.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | powershell.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Exit code: 1 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 5332 | "C:\WINDOWS\system32\OOBE-Maintenance.exe" | C:\Windows\System32\OOBE-Maintenance.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: OOBE-Maintenance Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
40 979
Read events
40 822
Write events
142
Delete events
15
Modification events
| (PID) Process: | (3532) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3532) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3532) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3532) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5896) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5896) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5896) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5896) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5896) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5896) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
19
Text files
13
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5896 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CPPWC9FIYJDGDPUIO645.temp | binary | |
MD5:EDA8BF9D701B659DA393DA4EF2116DAC | SHA256:AACC68C197340D903D098D6F1C0295C68C59A73CA72233F2036031268D5B17E4 | |||
| 5896 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\b1a1c1d805115a10.customDestinations-ms | binary | |
MD5:EDA8BF9D701B659DA393DA4EF2116DAC | SHA256:AACC68C197340D903D098D6F1C0295C68C59A73CA72233F2036031268D5B17E4 | |||
| 3532 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0aoexsaz.5fc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4804 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:CC0BFE888AEF1ECE2B1F70ED6A028DA0 | SHA256:3C257BB0E7343BA5DE31BDF3329B140B941CCB059261ACF8AE38A3E7016C6F44 | |||
| 5896 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hhn3wmbt.tym.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3532 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | binary | |
MD5:A21E56FB21B540C23CF20C1DFB53E89F | SHA256:FC75D5F26C941A9BAE04D61A49C0A61AD572139A823A1537E6B27F3112E61882 | |||
| 1112 | Acrobat.exe | C:\USERS\ADMIN\APPDATA\LOCAL\ADOBE\ACROBAT\DC\SOPHIA\ACROBAT\SOPHIA.JSON | binary | |
MD5:79270D9595B259B53E39403366436A8E | SHA256:AD0552A8B392315C512F6DC945F318AD83B98FB64415C0CED694843A3C5D2083 | |||
| 1112 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\Files\TESTING | mp3 | |
MD5:DC84B0D741E5BEAE8070013ADDCC8C28 | SHA256:81FF65EFC4487853BDB4625559E69AB44F19E0F5EFBD6D5B2AF5E3AB267C8E06 | |||
| 5896 | powershell.exe | C:\Users\admin\Desktop\List of Required items and services.pdf | ||
MD5:E7CB275663A518442FD2400BFEB0D079 | SHA256:AC19E9EC19B3F120928995449C99DB63C22AD6EF7030EB113A8FCF29A82A69EA | |||
| 4804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_byrwsh0b.iaj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
76
DNS requests
25
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3872 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
3872 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
3828 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
6772 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
3032 | svchost.exe | GET | 304 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | unknown |
6772 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
4544 | wab.exe | GET | 200 | 95.101.54.130:80 | http://r10.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRpD%2BQVZ%2B1vf7U0RGQGBm8JZwdxcgQUdKR2KRcYVIUxN75n5gZYwLzFBXICEgSsCDX0WBxWLkQzam%2FqIWeexQ%3D%3D | unknown | — | — | unknown |
1812 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3872 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3560 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1320 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4656 | SearchApp.exe | 104.126.37.163:443 | — | Akamai International B.V. | DE | unknown |
1544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1544 | svchost.exe | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
1060 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3040 | OfficeClickToRun.exe | 40.79.189.58:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | JP | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.alaqalezdehar.com |
| unknown |
arc.msn.com |
| whitelisted |
www.fornid.com |
| unknown |
www.pineappletech.ae |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5332 | OOBE-Maintenance.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
OOBE-Maintenance.exe | [thresholding] image = 0000019ADD484D40 , (0 , 1190) (0 , 595)
|
OOBE-Maintenance.exe | [thresholding] image = 0000019ADEE10040 , (0 , 1889) (0 , 944)
|
OOBE-Maintenance.exe | [thresholding] image = 0000019ADEE6B040 , (0 , 1926) (0 , 963)
|
OOBE-Maintenance.exe | [thresholding] image = 0000019ADED8D040 , (0 , 1806) (0 , 903)
|
OOBE-Maintenance.exe | [thresholding] image = 0000019ADD1EBE20 , (0 , 1102) (0 , 551)
|