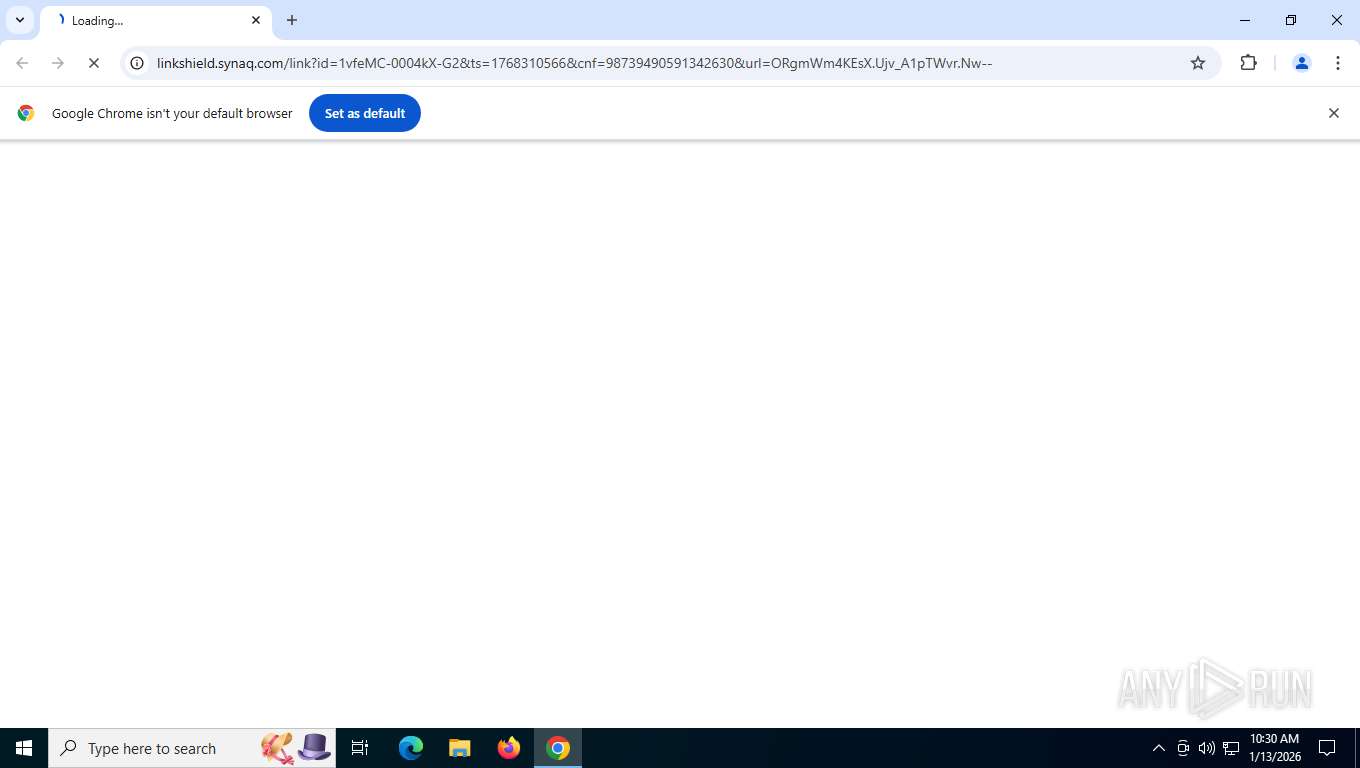
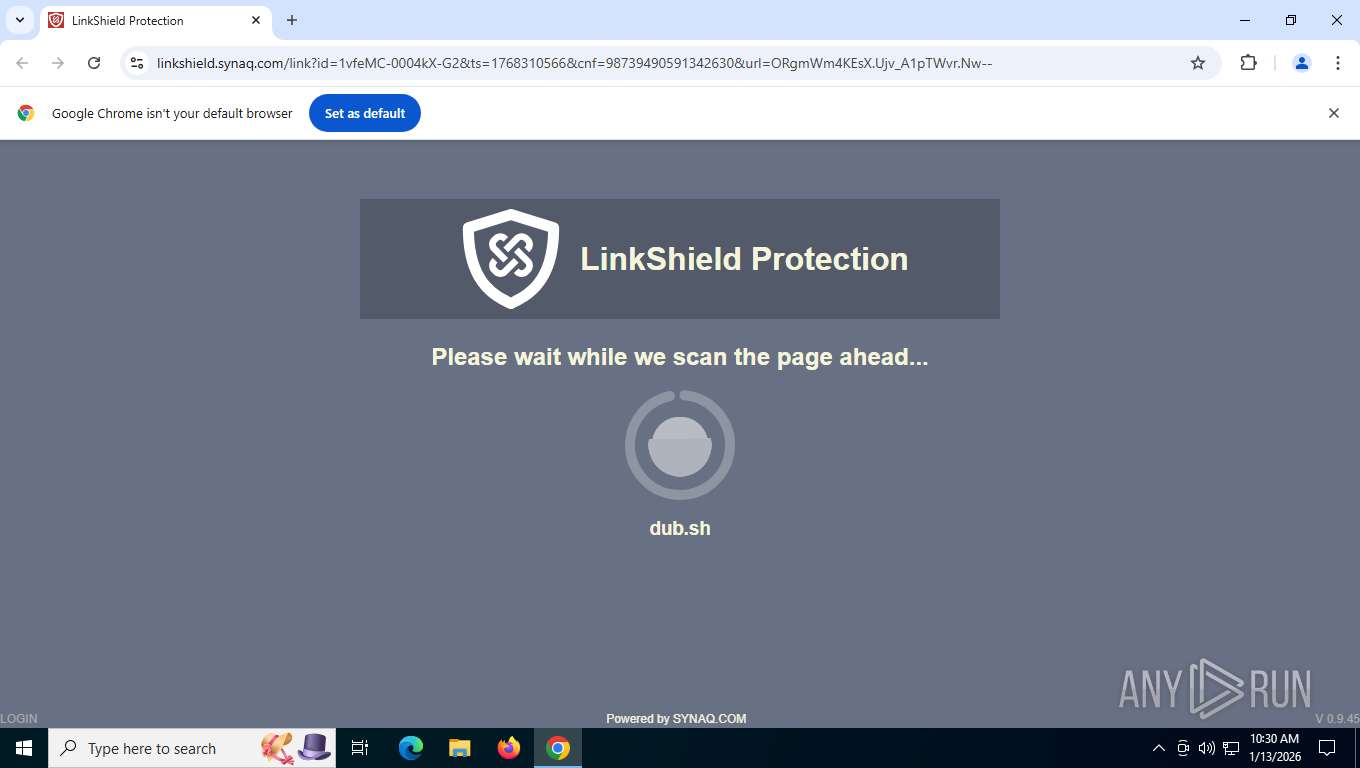
| URL: | https://linkshield.synaq.com/link?id=1vfeMC-0004kX-G2&ts=1768310566&cnf=98739490591342630&url=ORgmWm4KEsX.Ujv_A1pTWvr.Nw-- |
| Full analysis: | https://app.any.run/tasks/8bf79d5a-c528-45b2-a38e-fd3096251d2d |
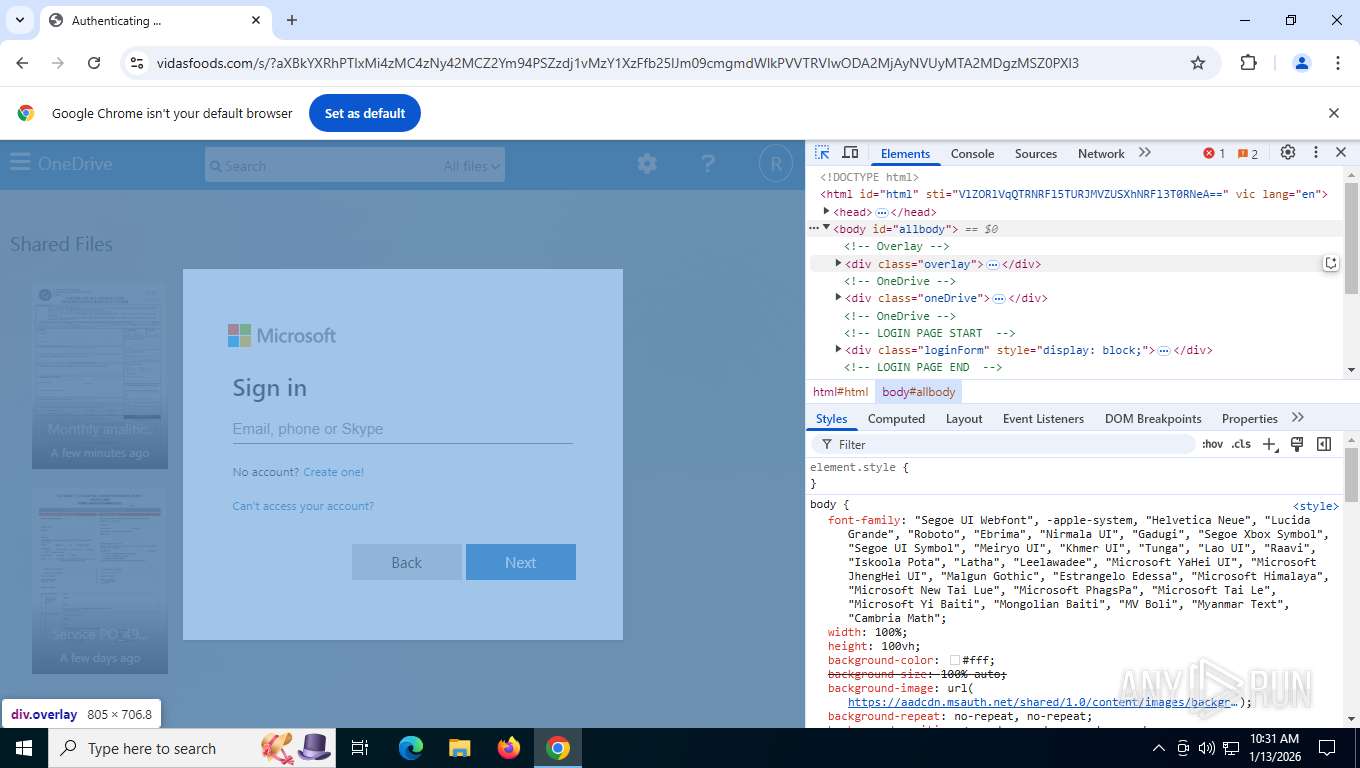
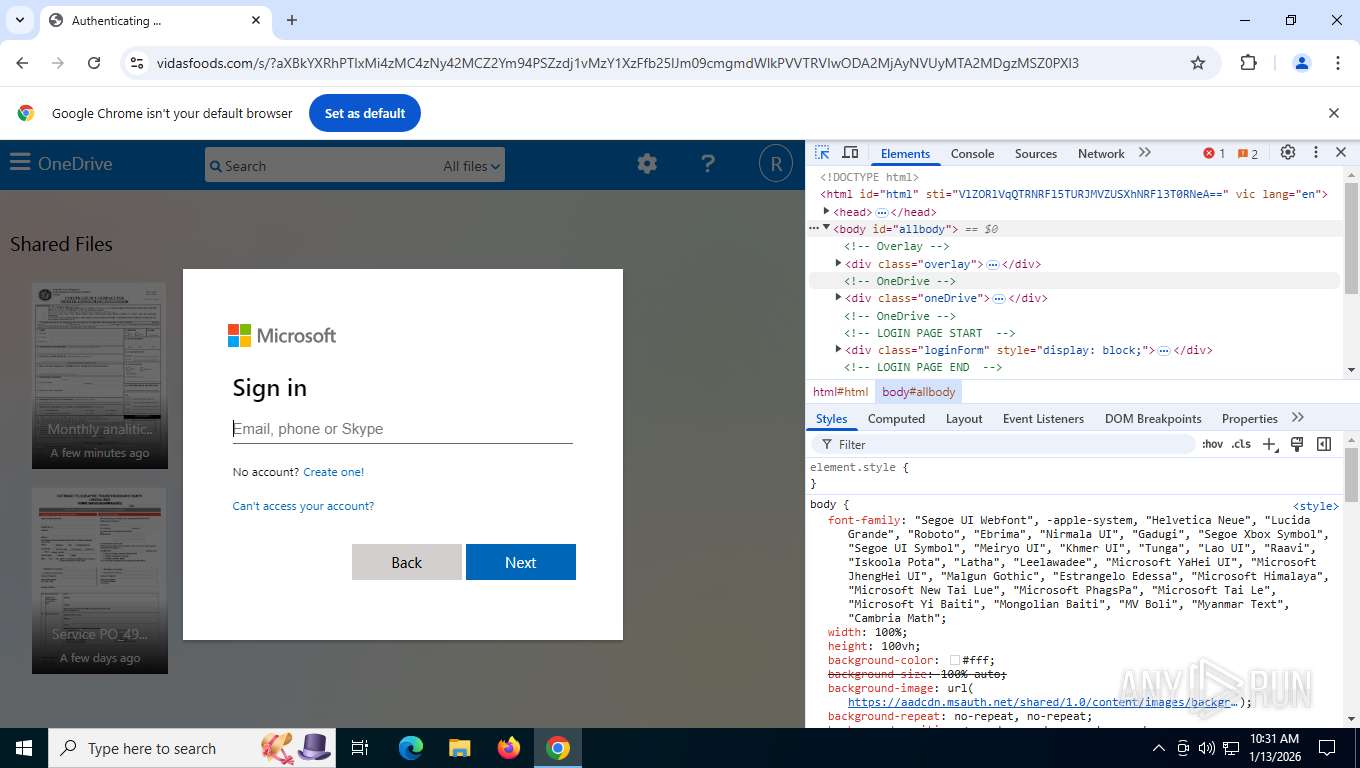
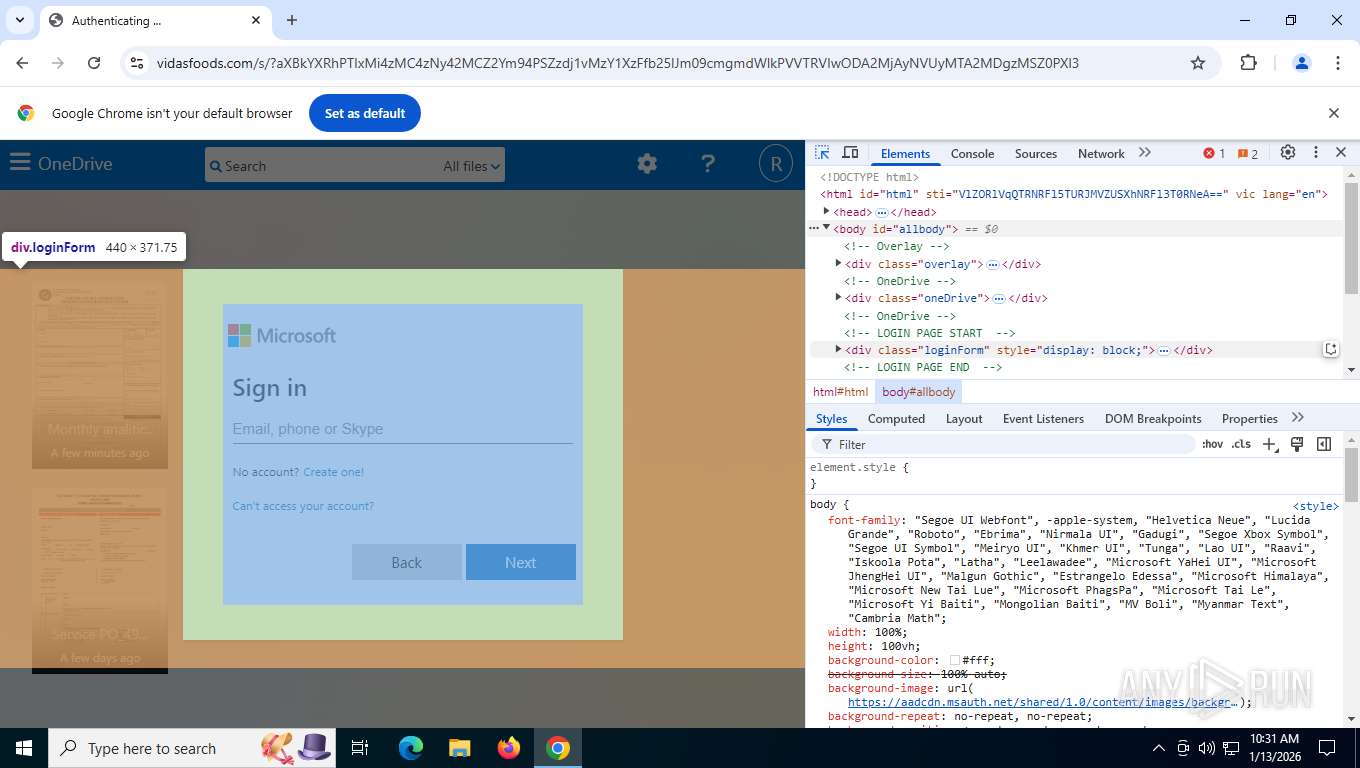
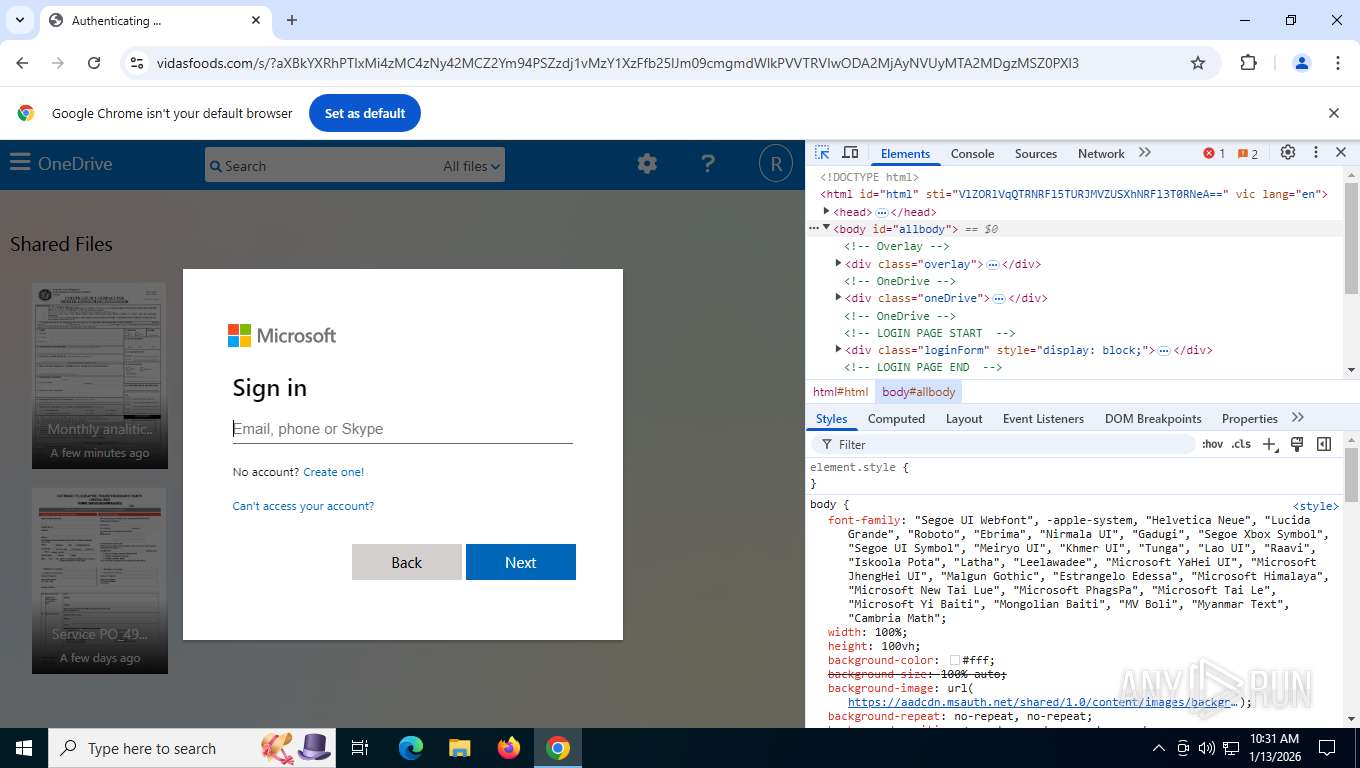
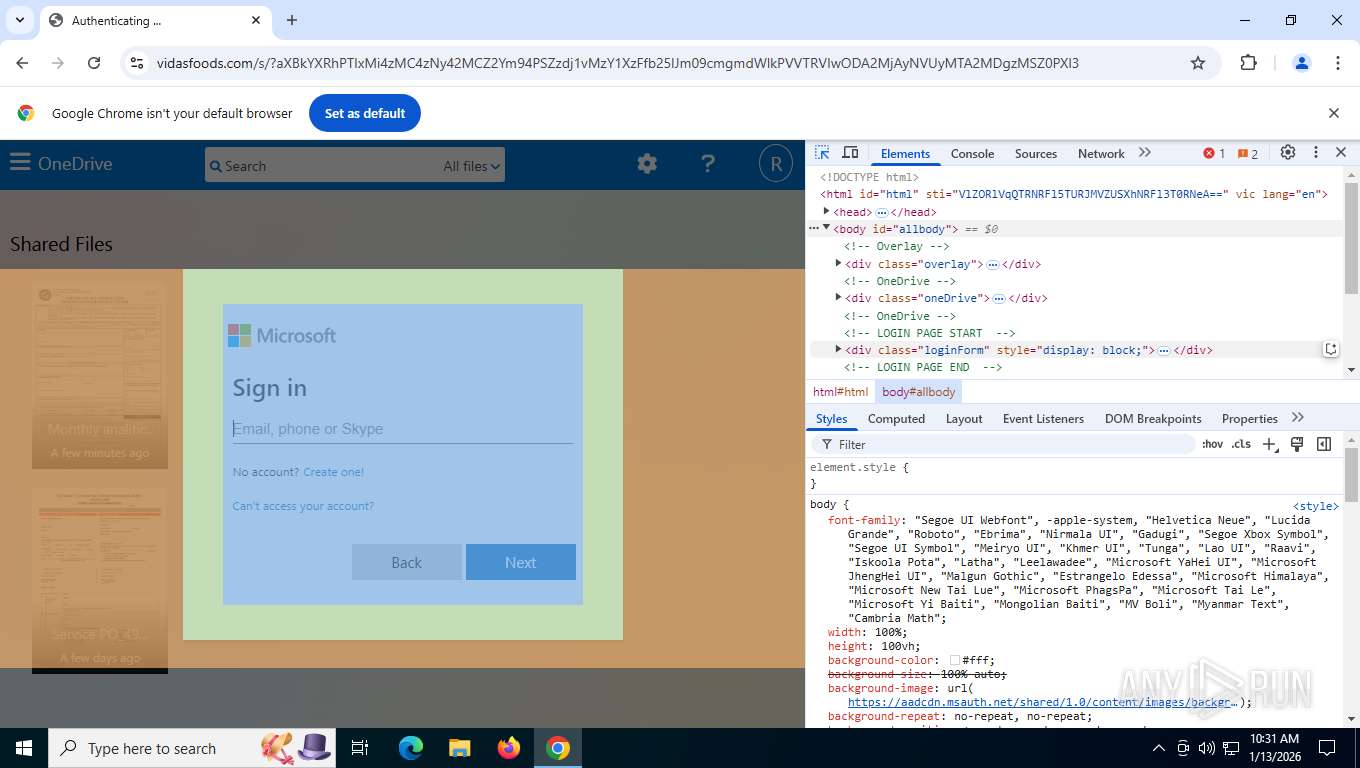
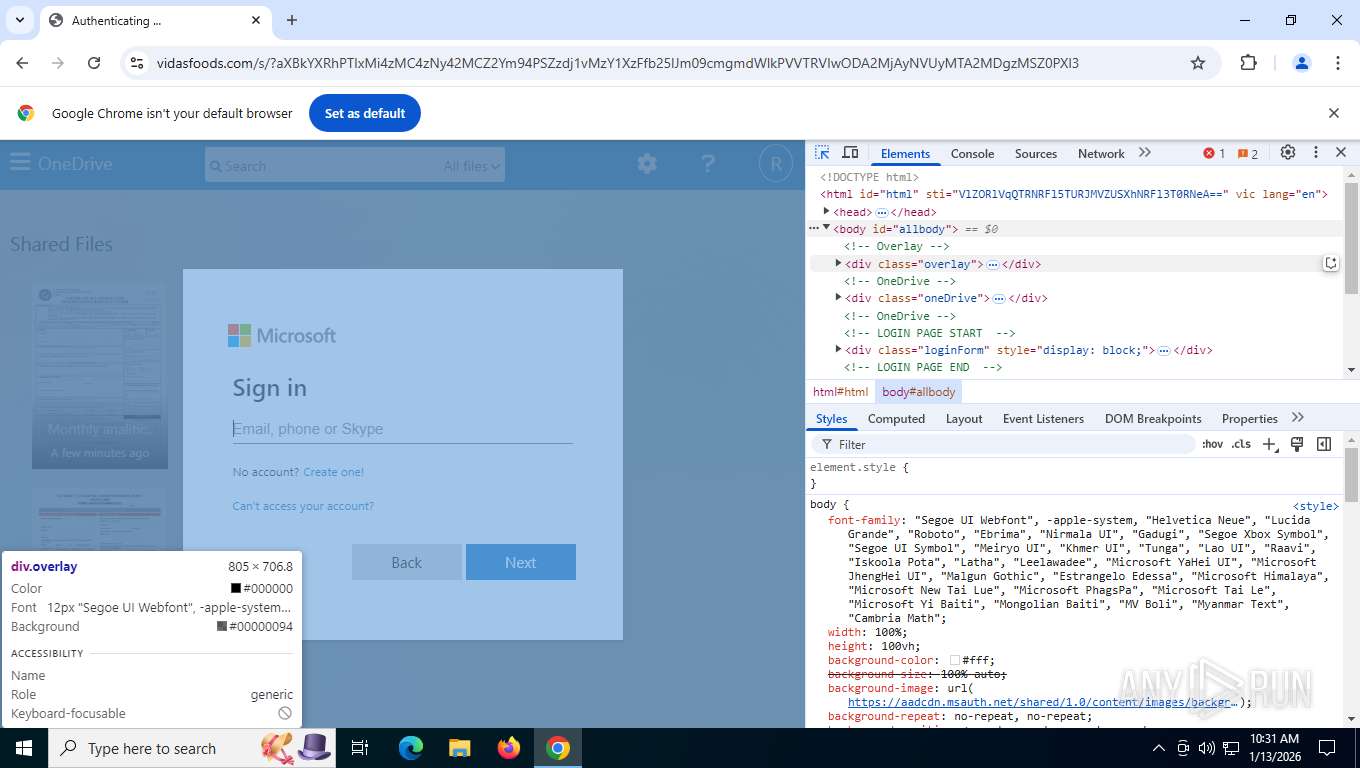
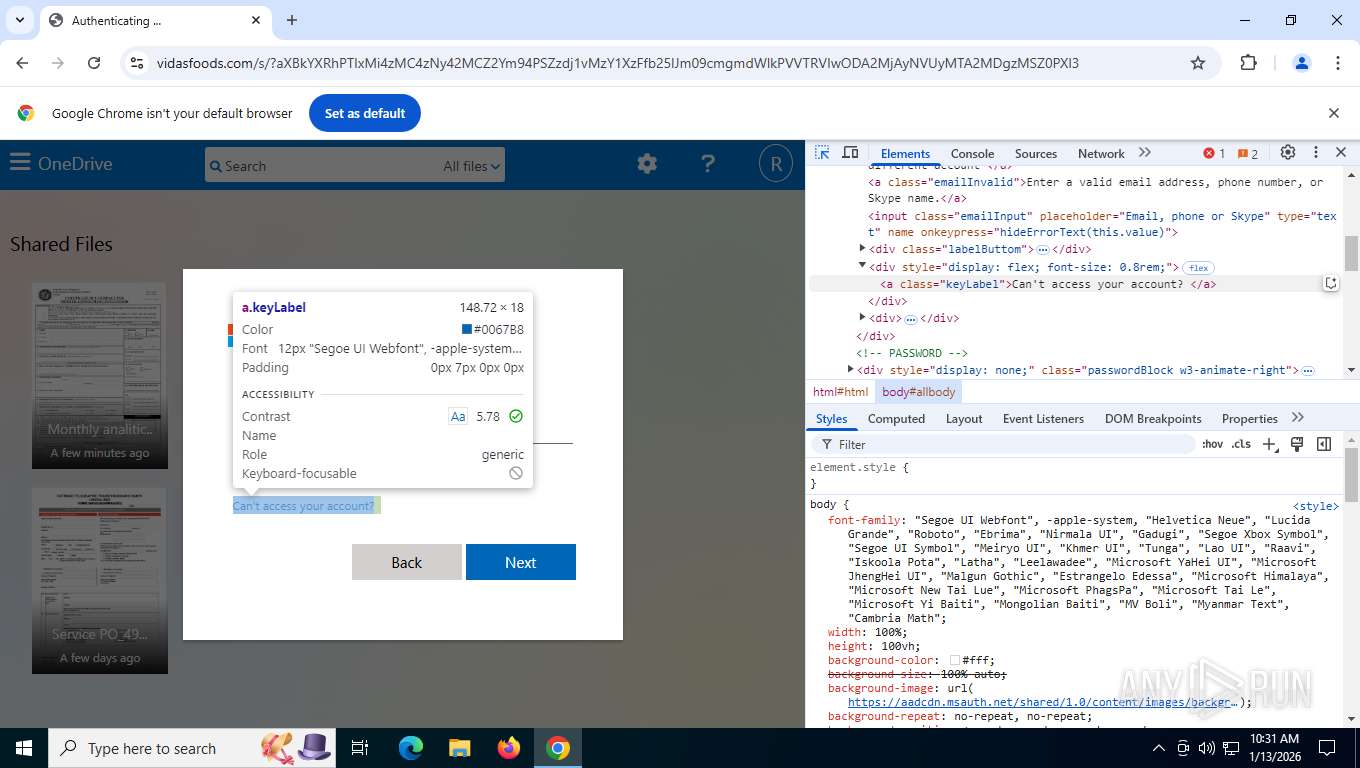
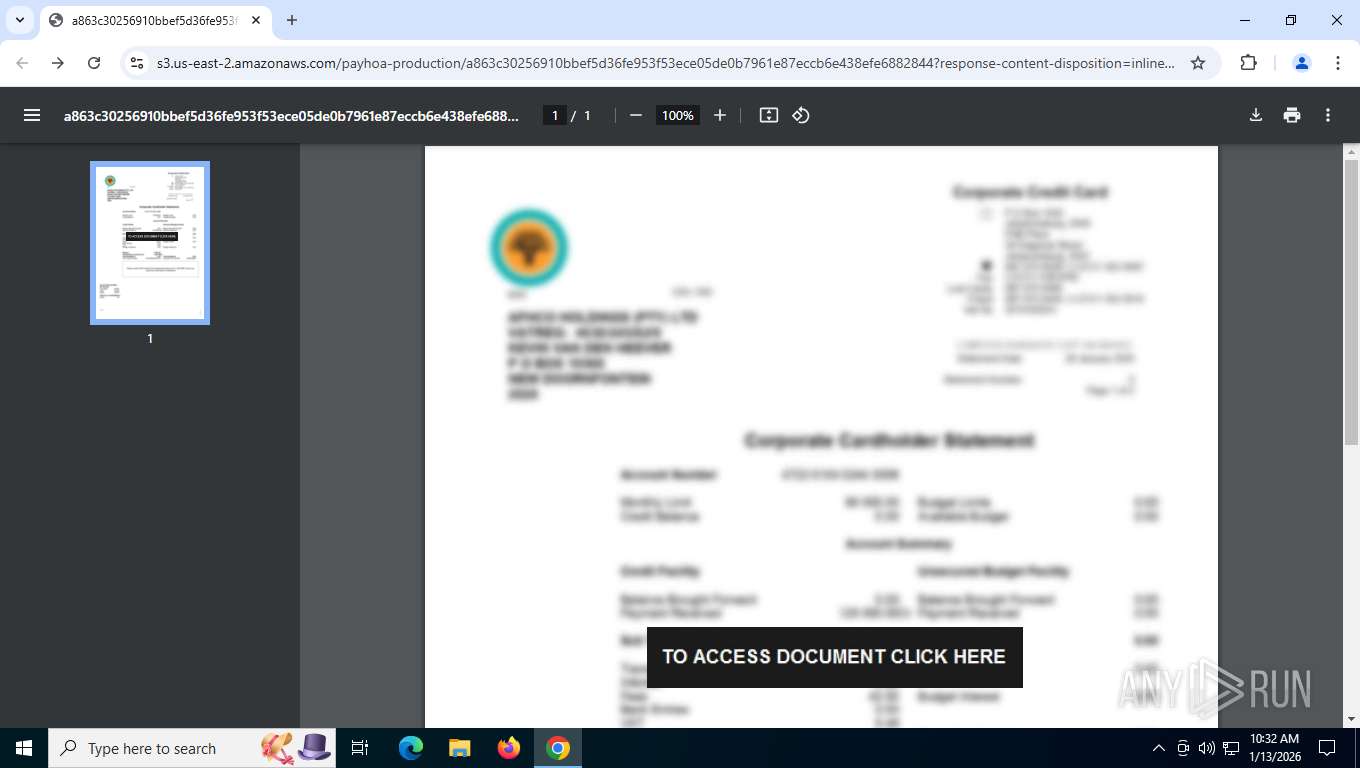
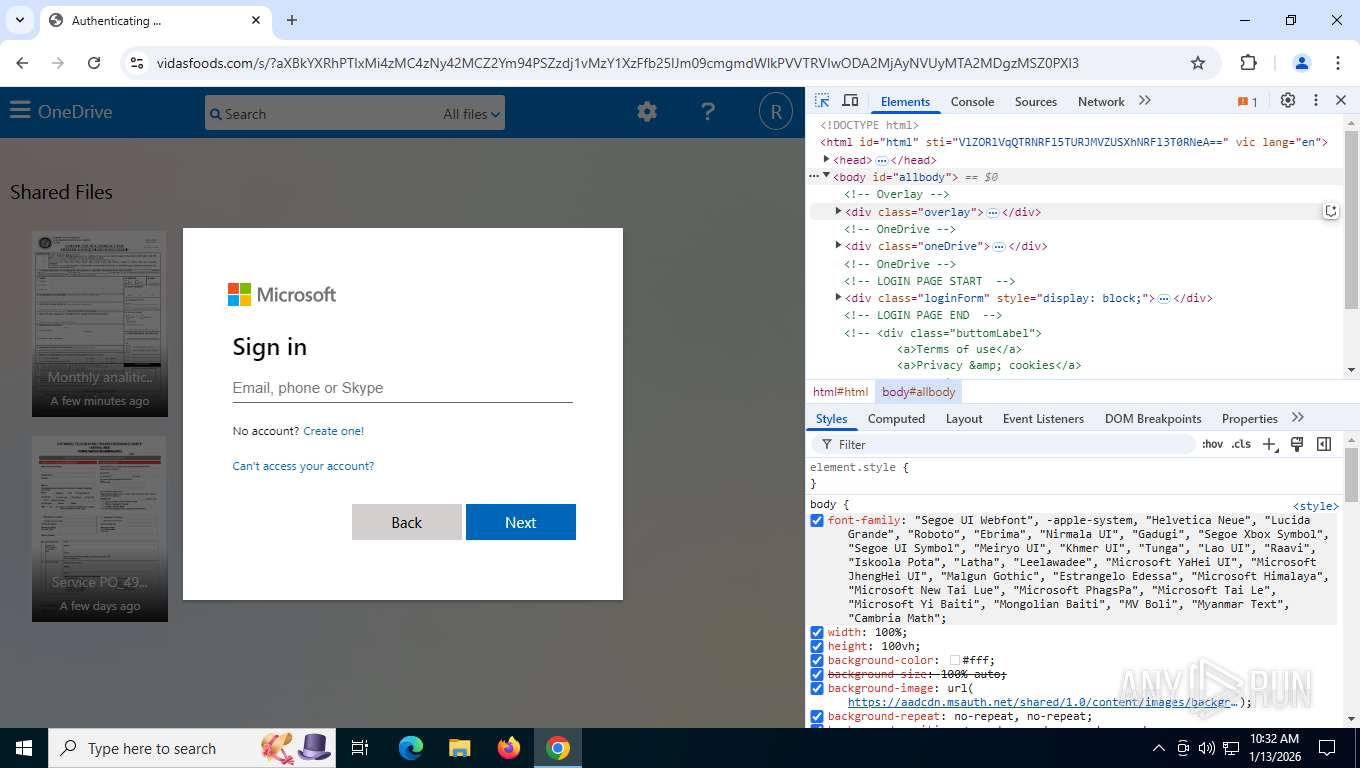
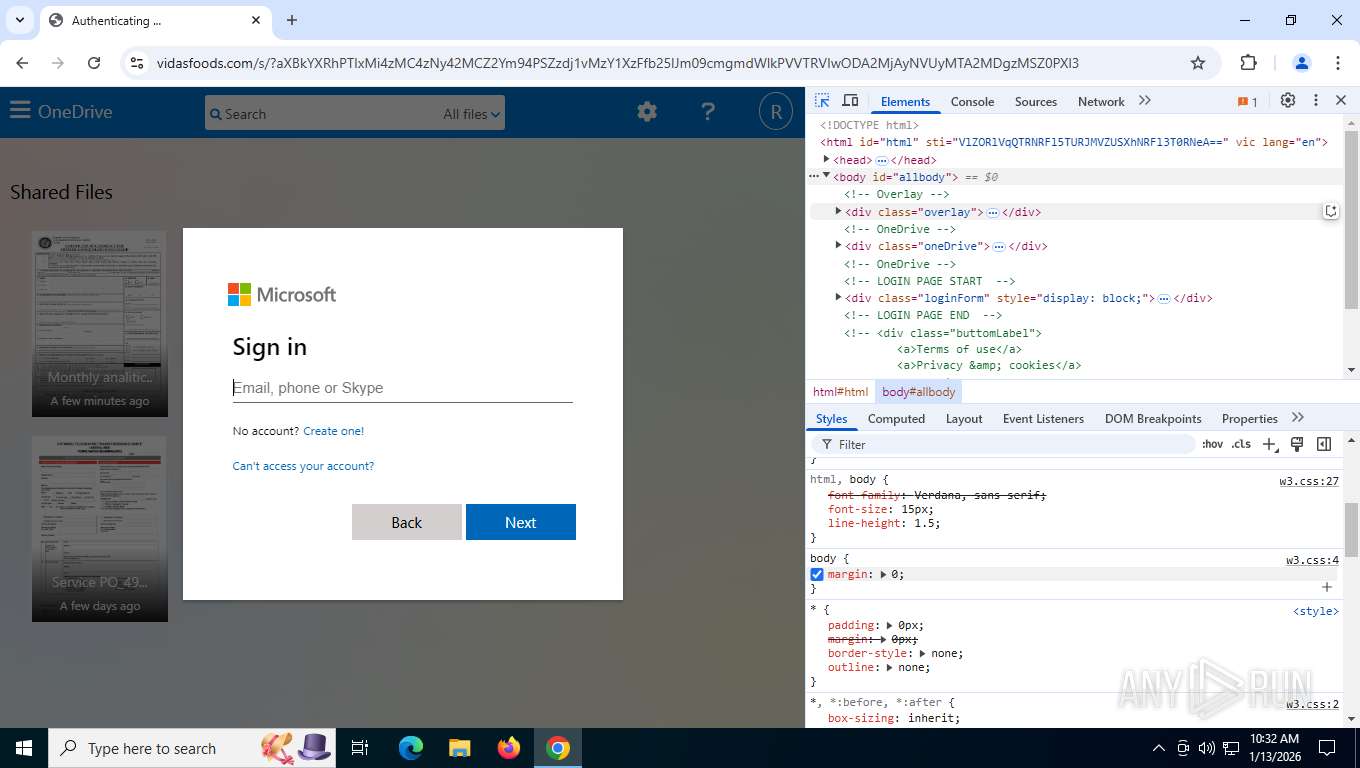
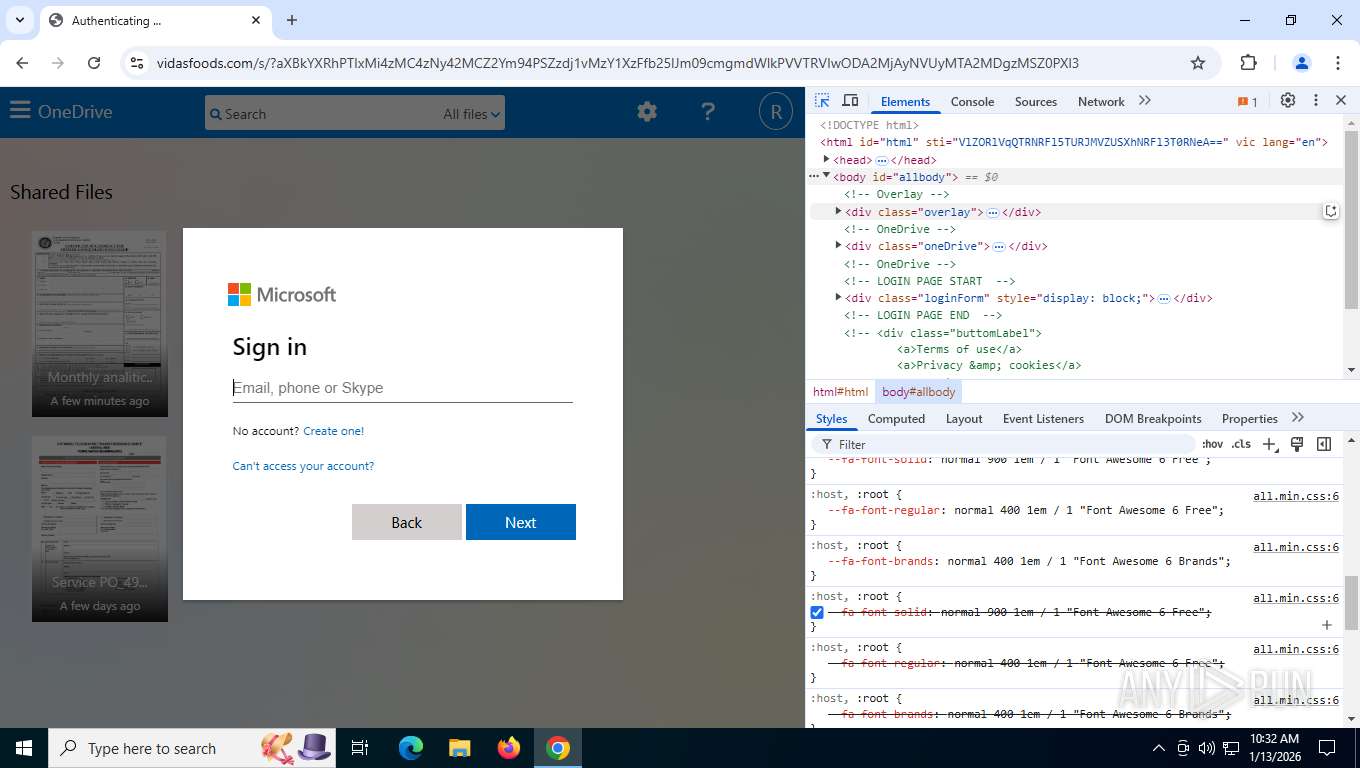
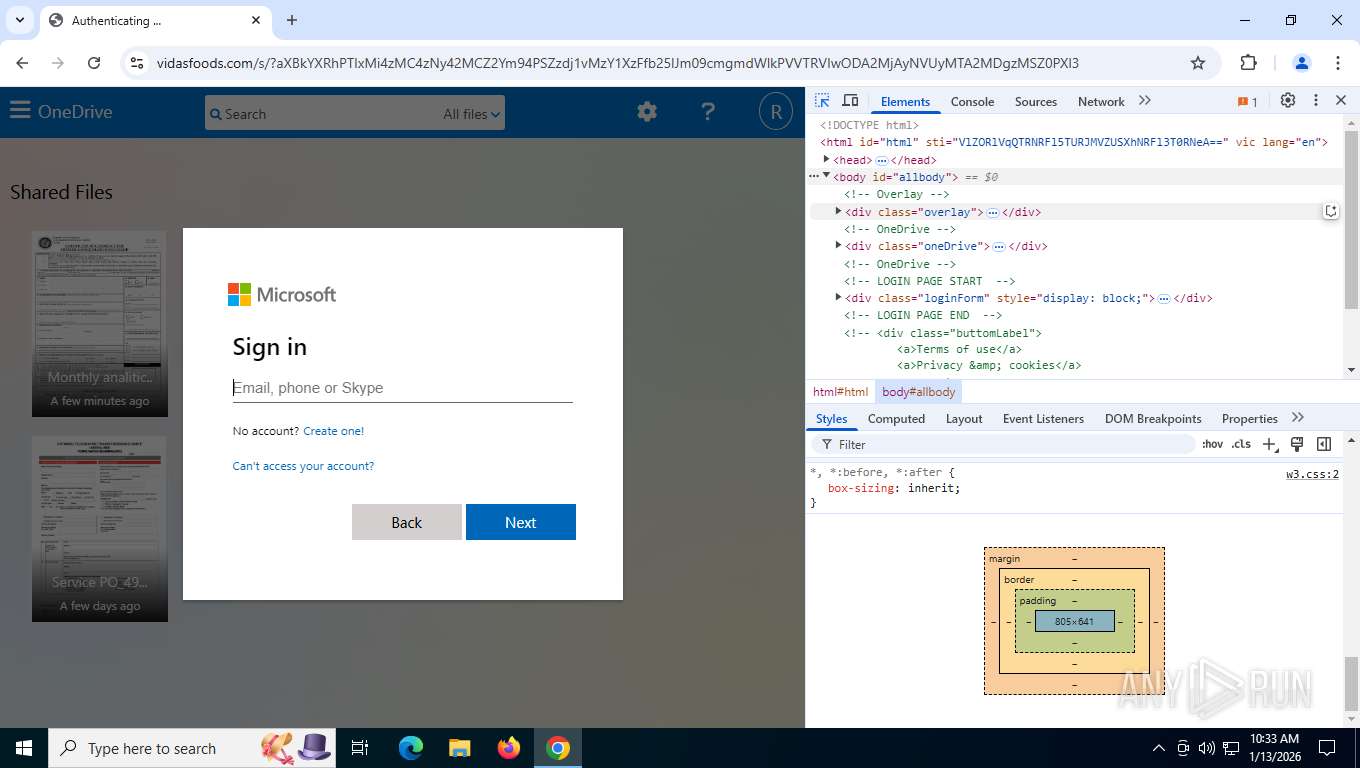
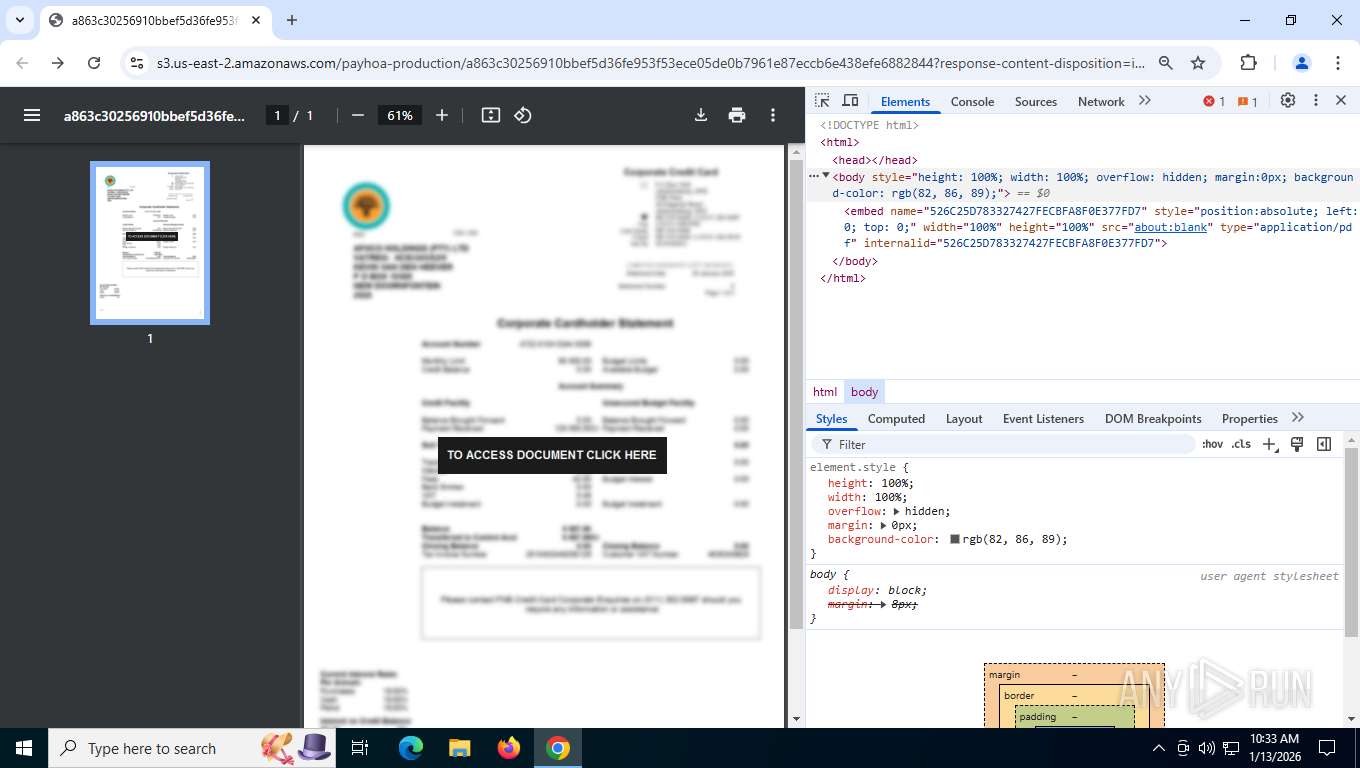
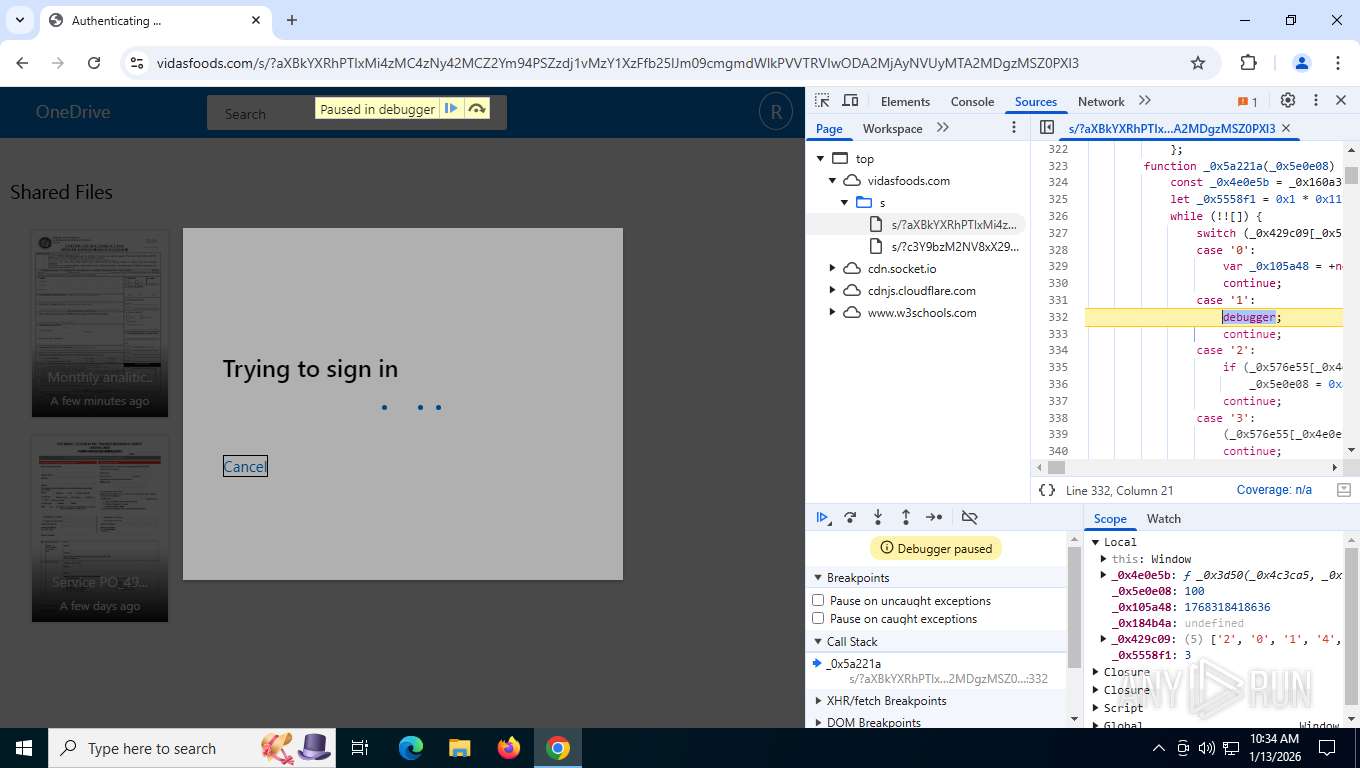
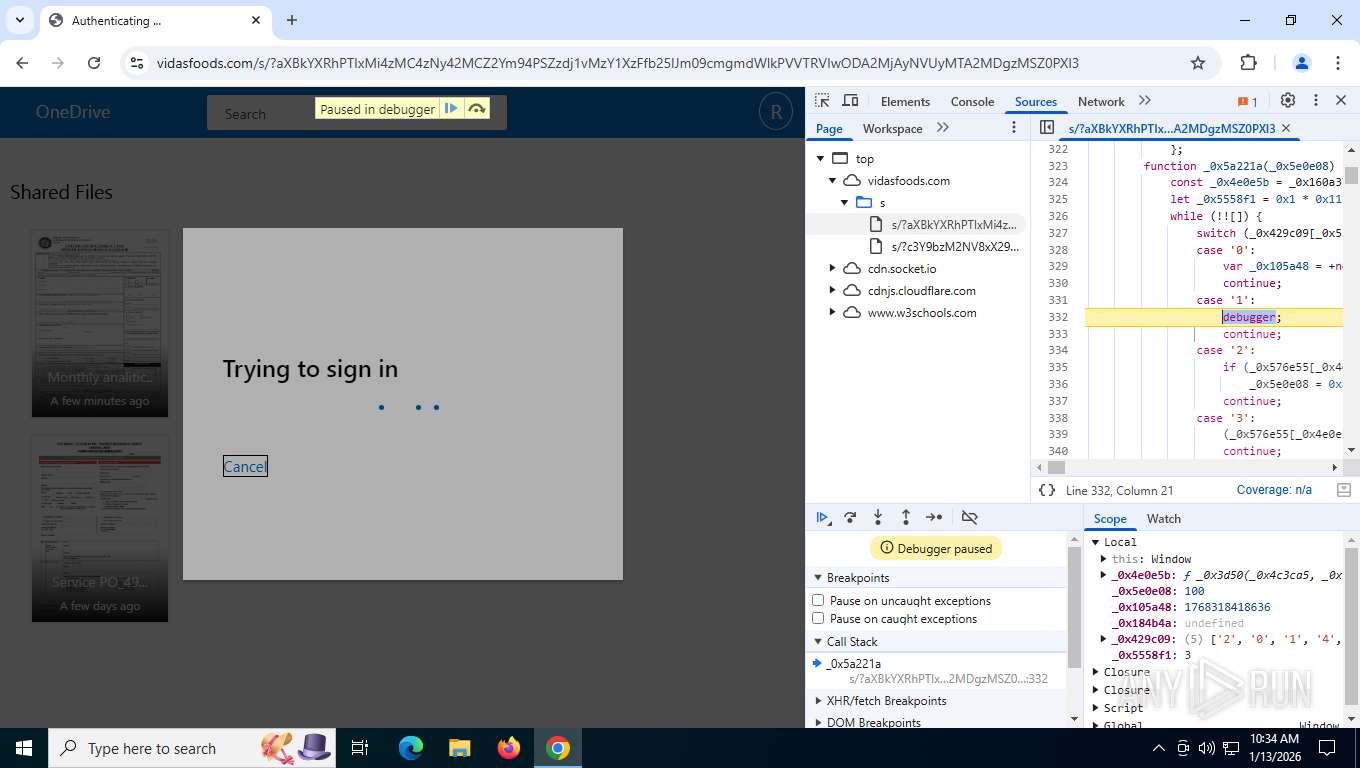
| Verdict: | Malicious activity |
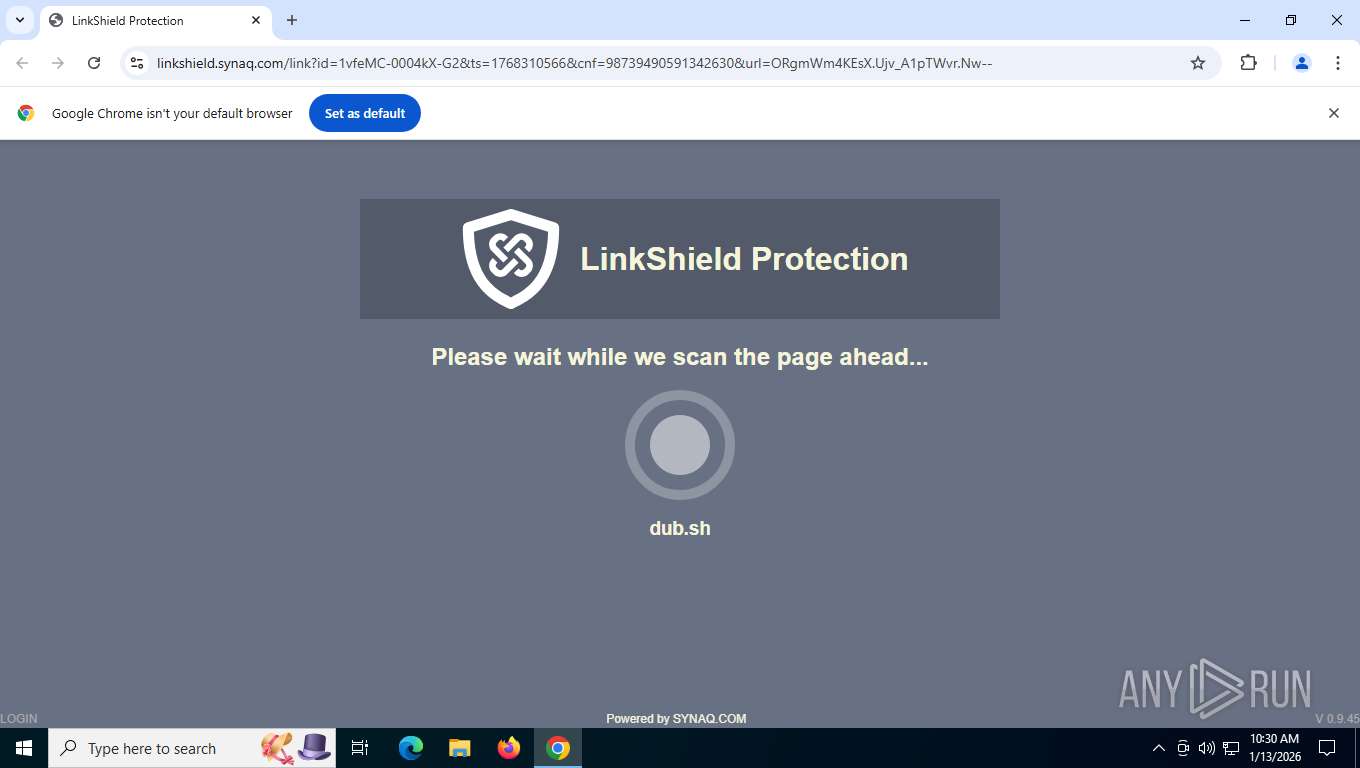
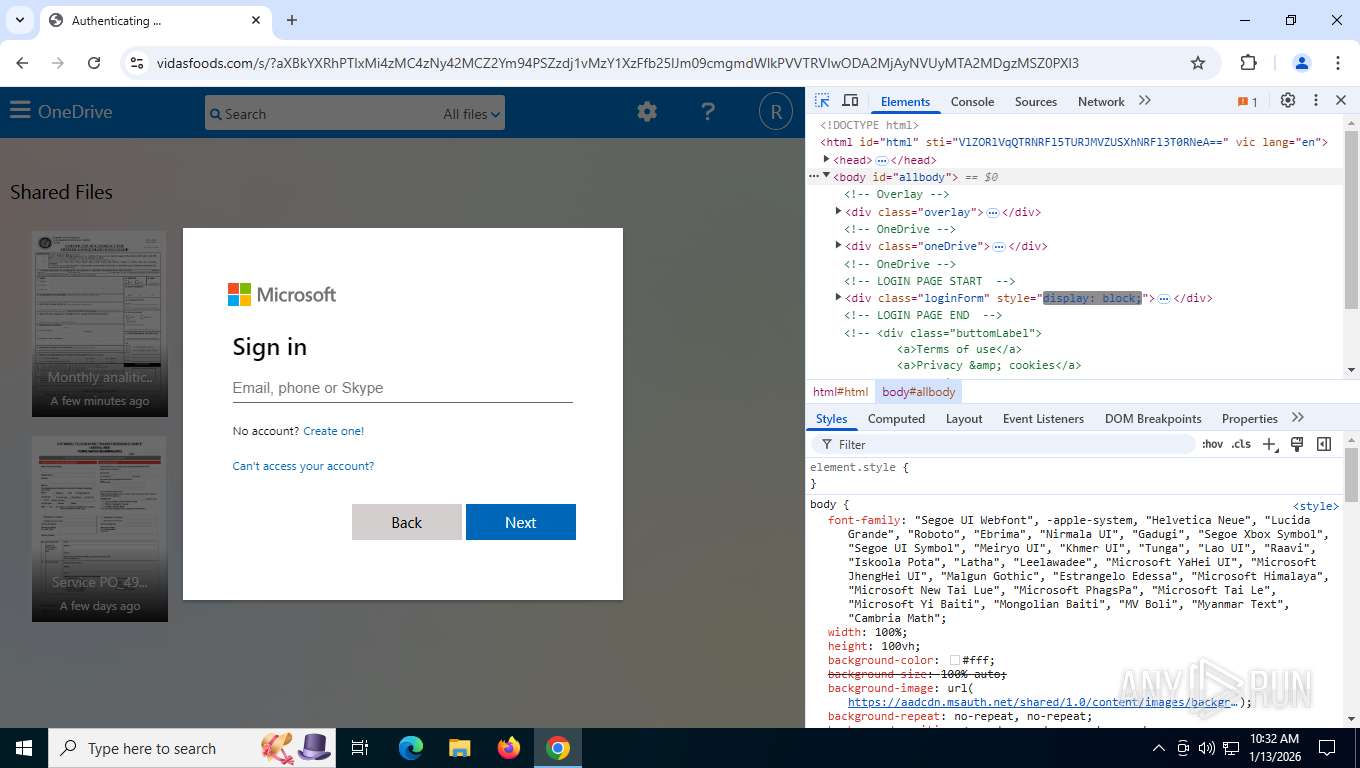
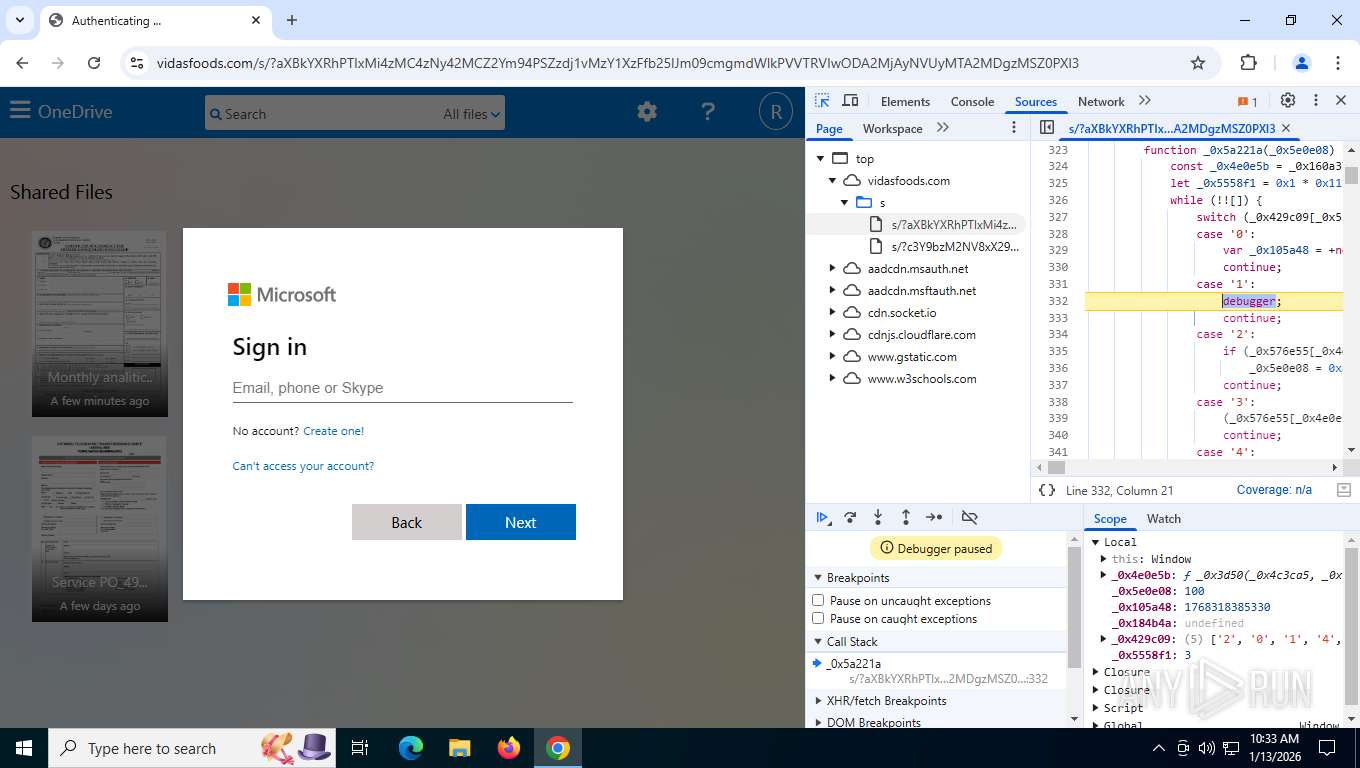
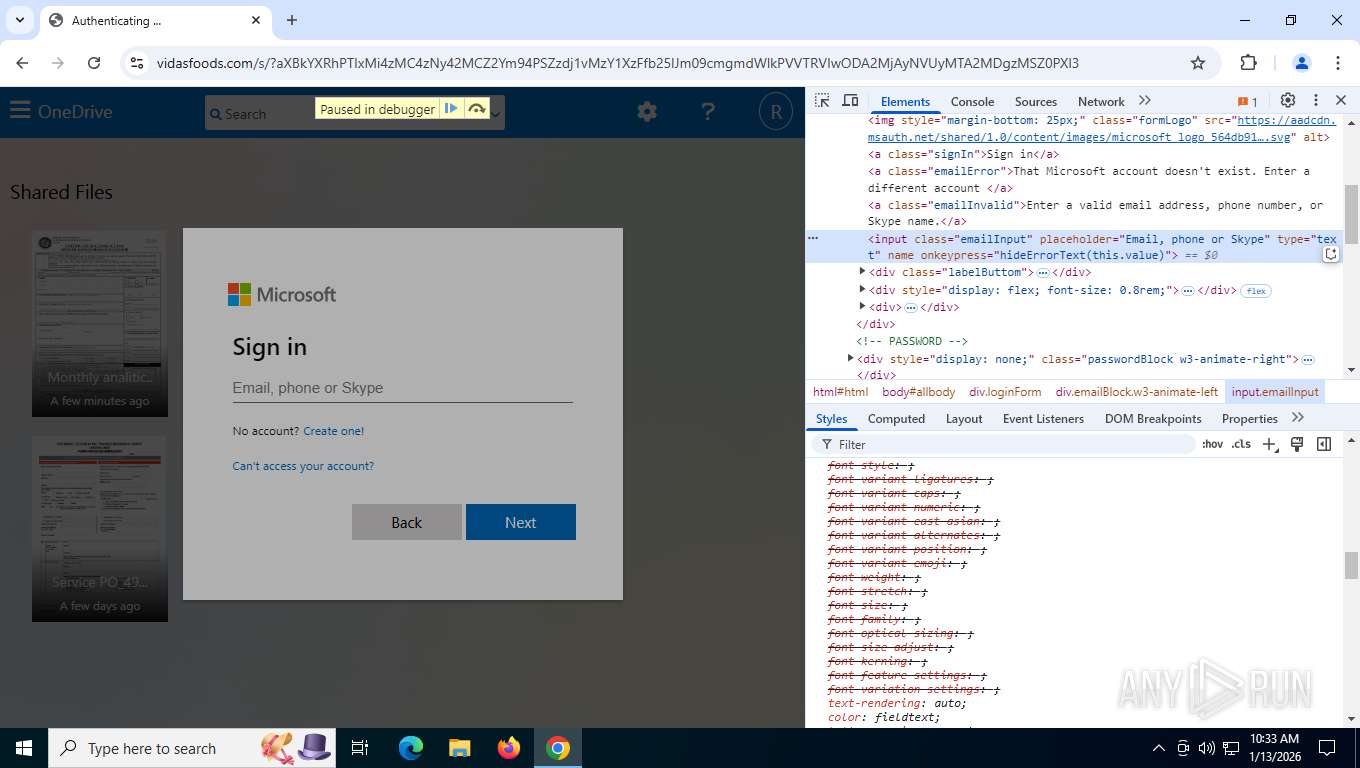
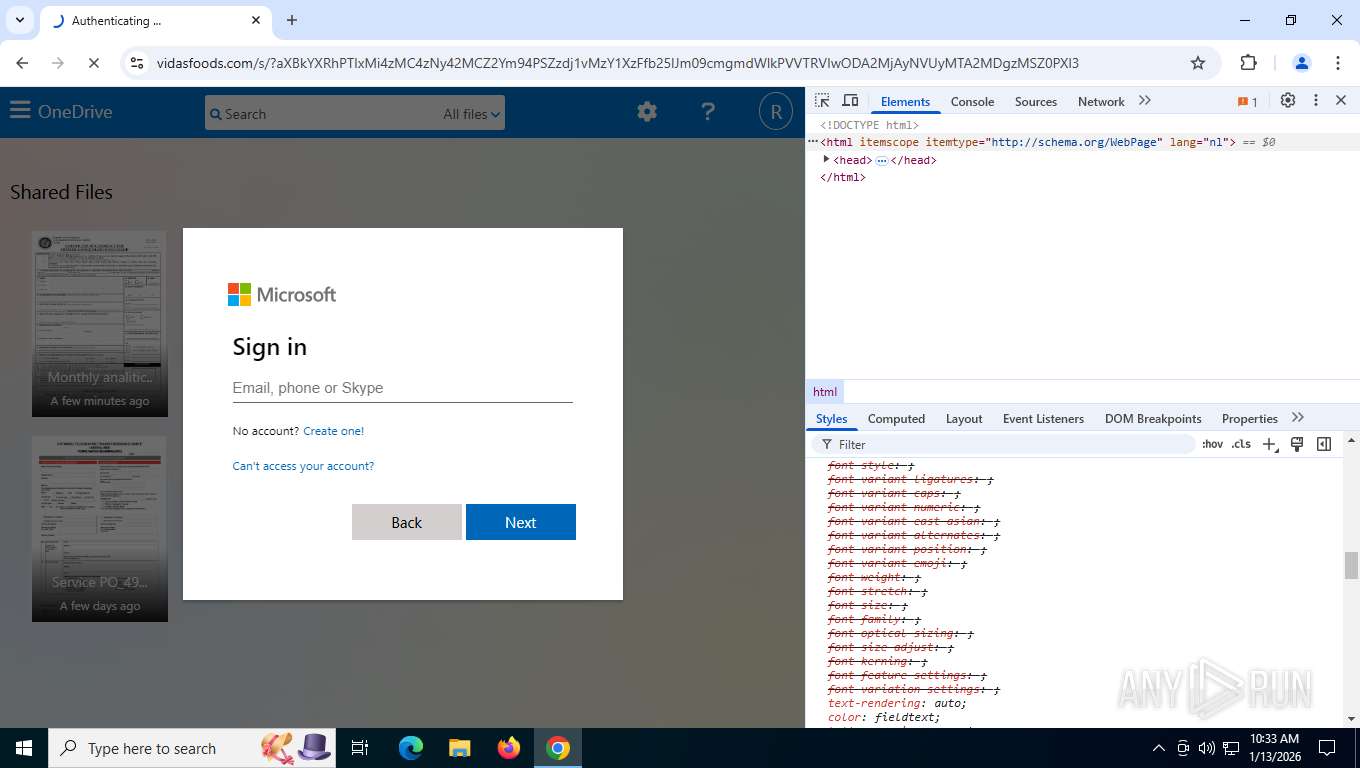
| Threats: | Mamba 2FA is an advanced phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) and target Microsoft 365 accounts. It focuses on intercepting authentication flows in real-time and enables threat actors to hijack user sessions and access sensitive systems even when additional security measures are in place. |
| Analysis date: | January 13, 2026, 15:29:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FEF23486EDD793713D8F42A2A4761541 |
| SHA1: | 7E19E0C2A7CE398967F5551DECB9E3BBC968C3AC |
| SHA256: | 9745EF178DF72F4A66542EBD9BEEC10562CD21538DC99DB8DF52414A147F706B |
| SSDEEP: | 3:N8MLAOBMKBNcU/oq0uKrQMxTwDMCI4eP2kHzS1:2MUO6a30lr34eb4 |
MALICIOUS
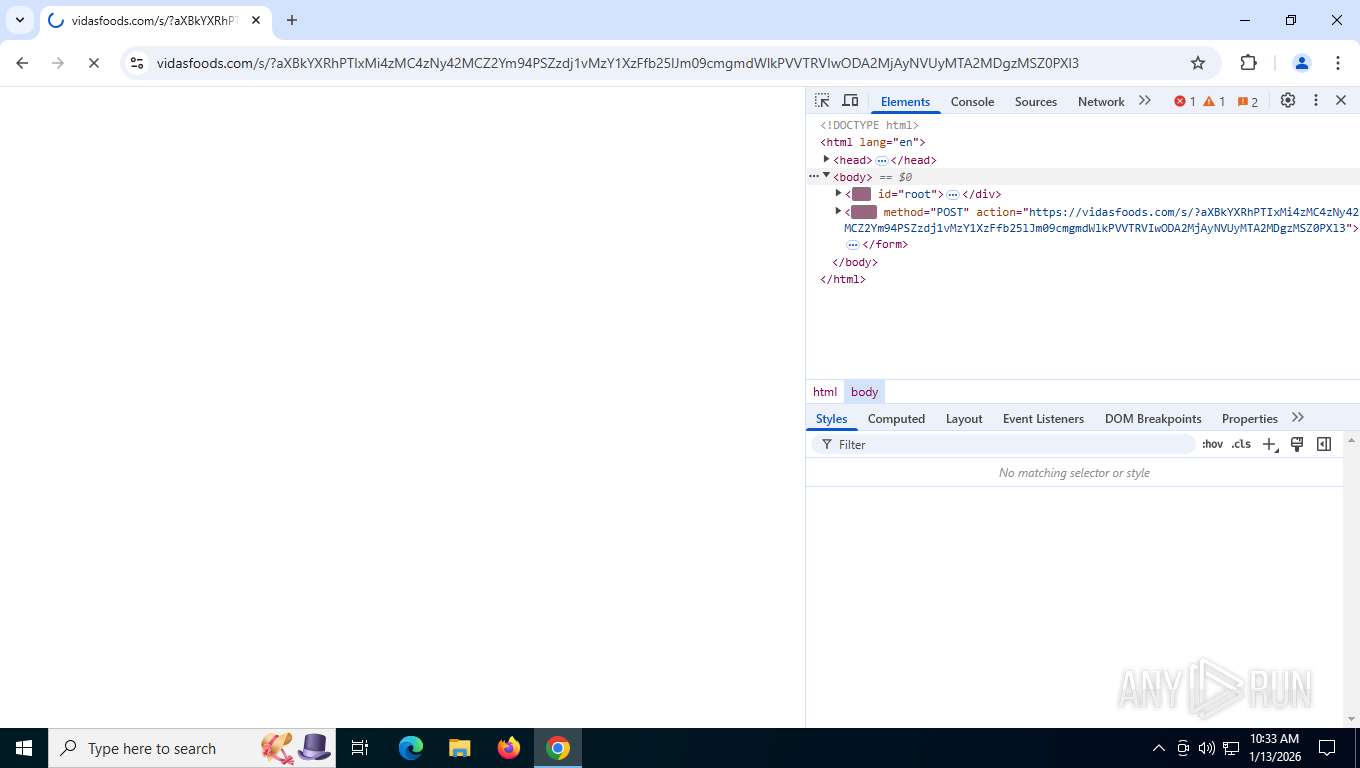
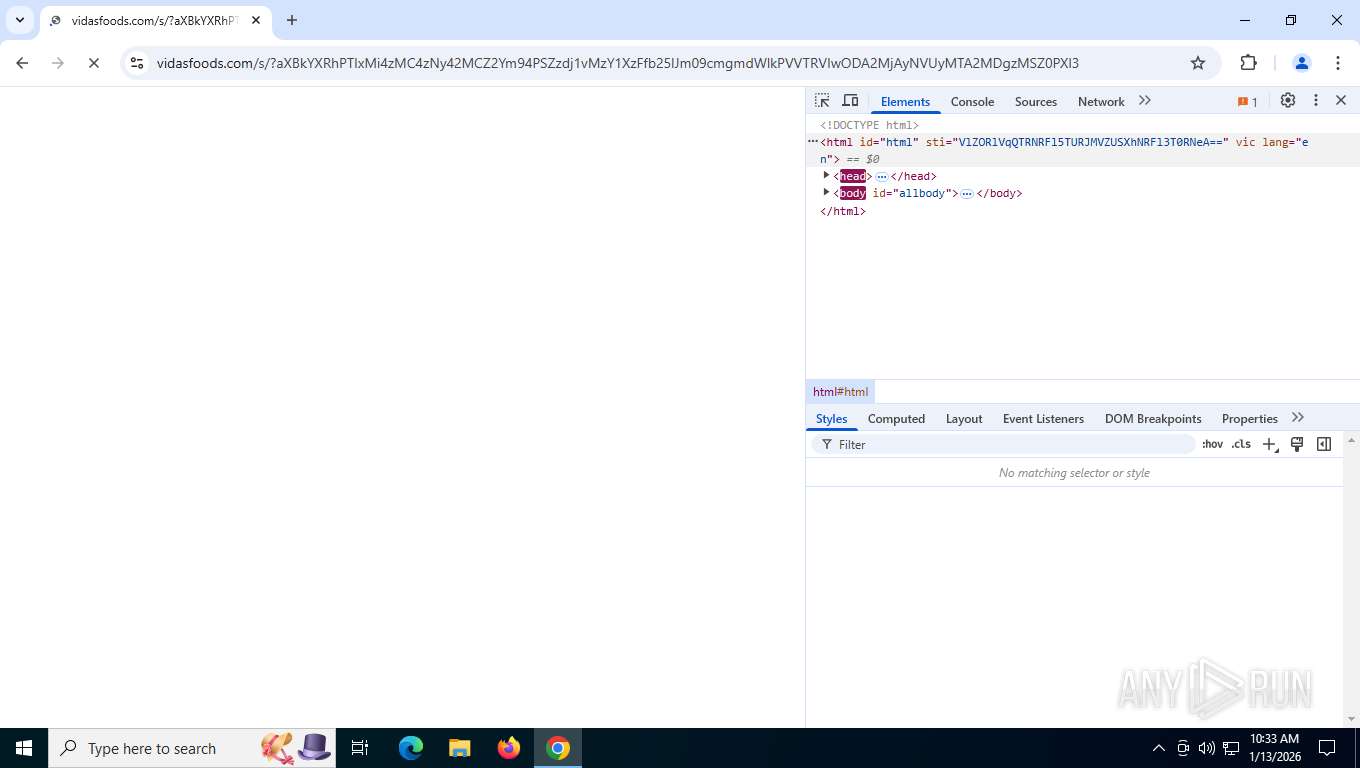
Phishing has been detected
- chrome.exe (PID: 7876)
- chrome.exe (PID: 7876)
- chrome.exe (PID: 7876)
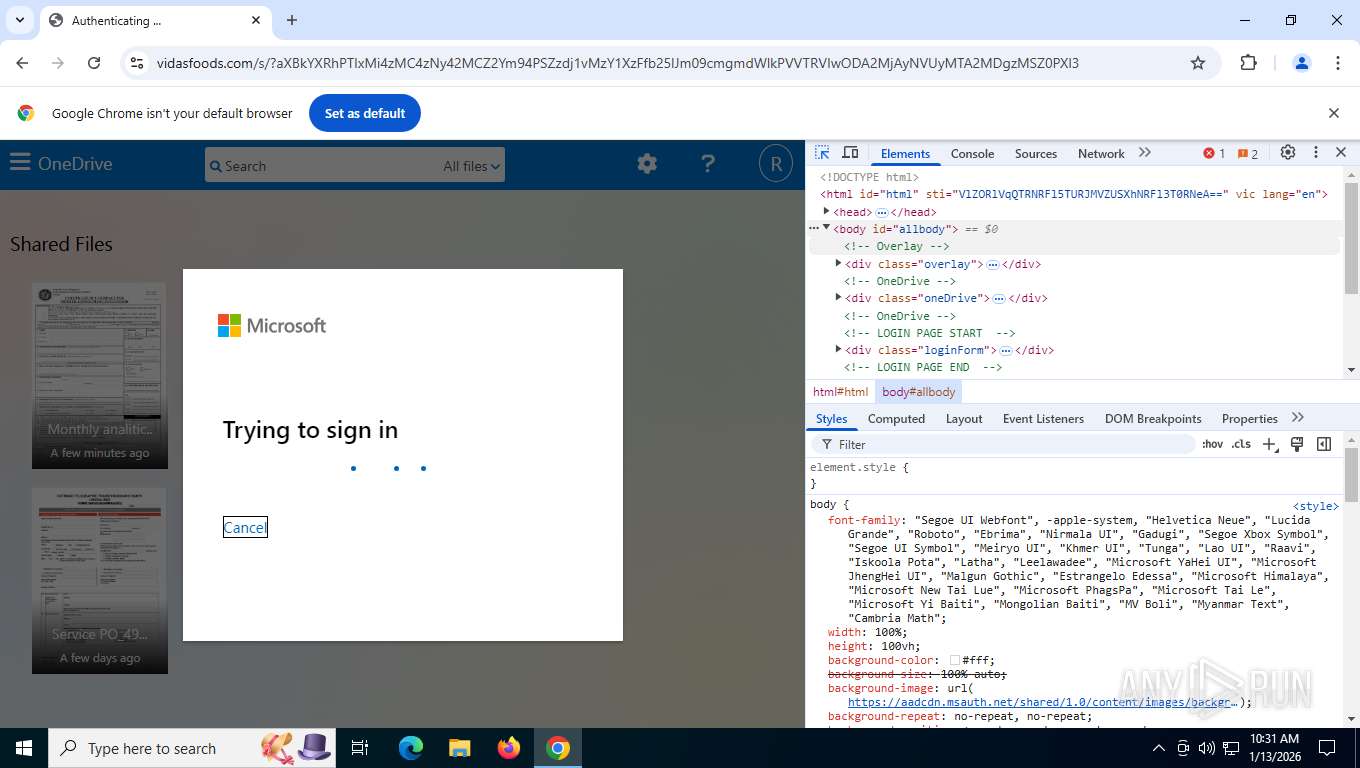
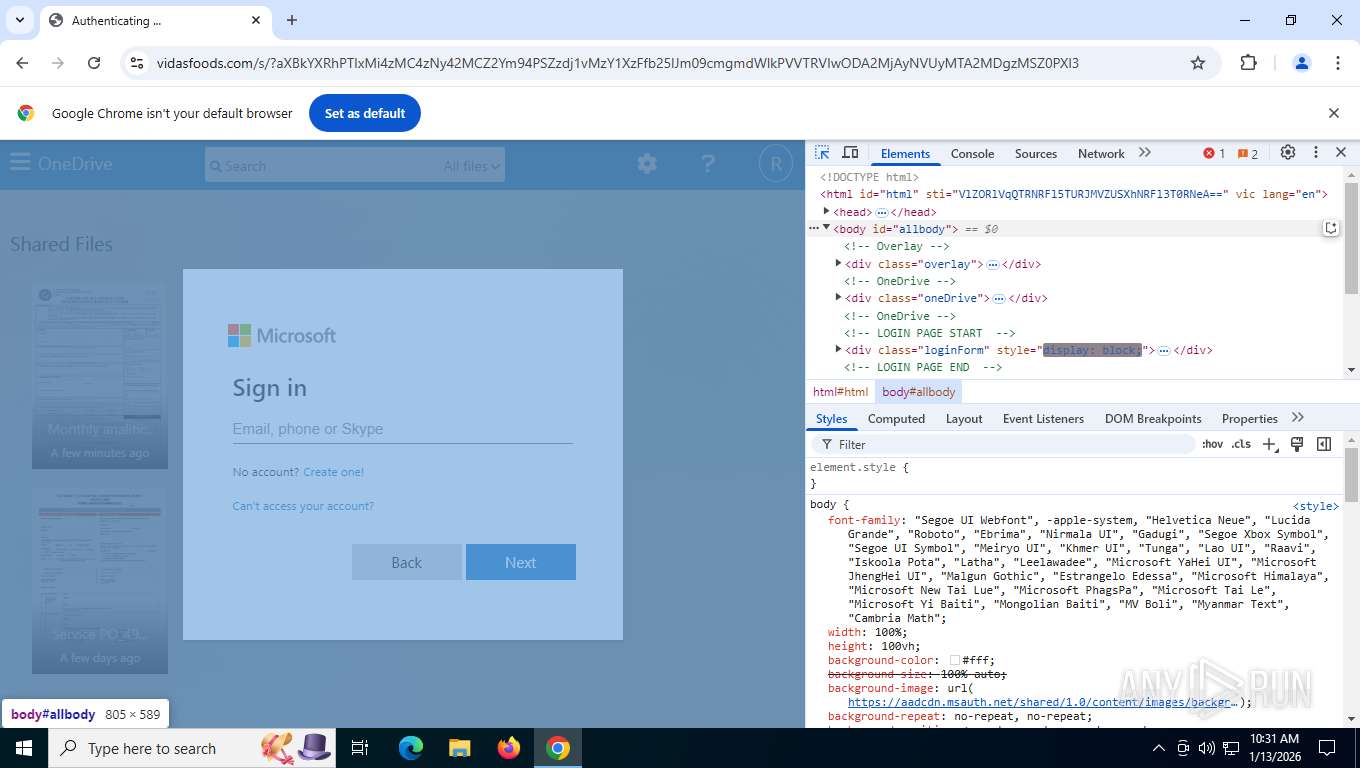
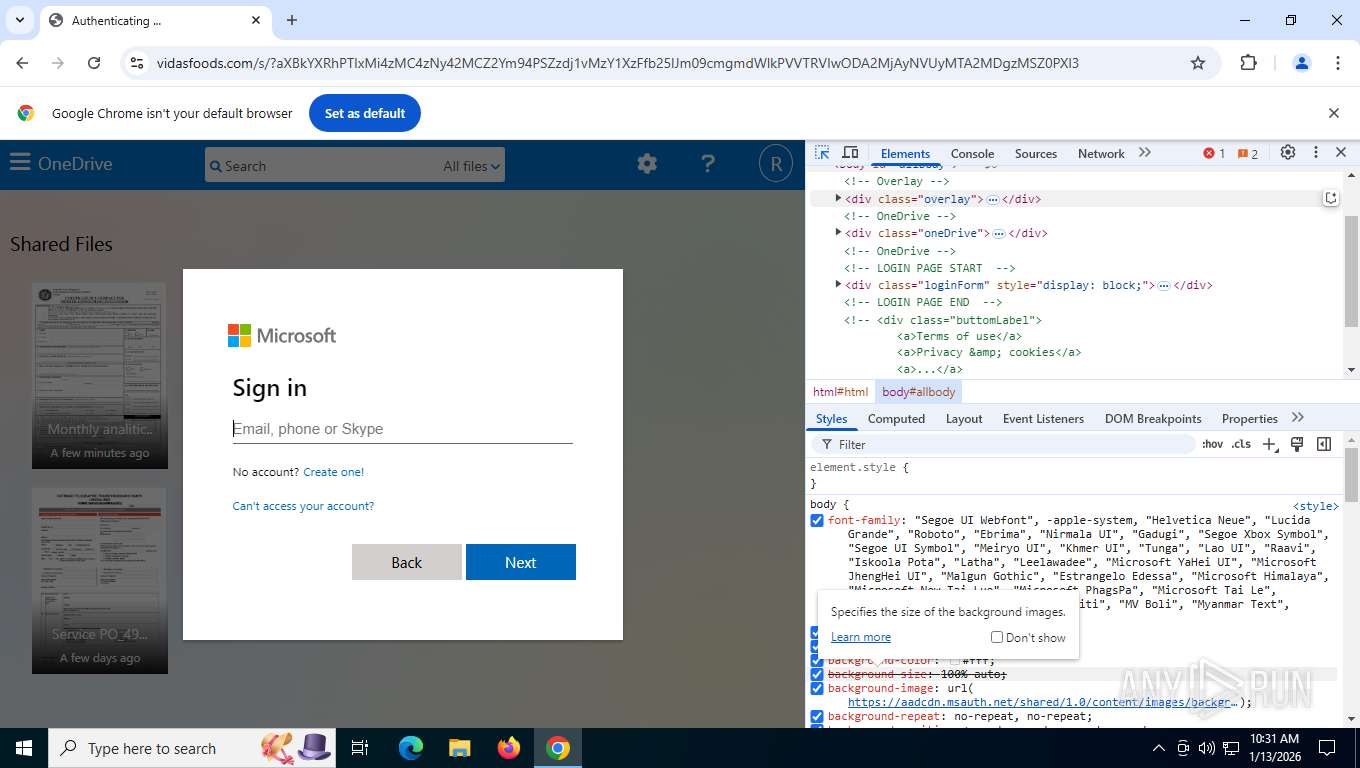
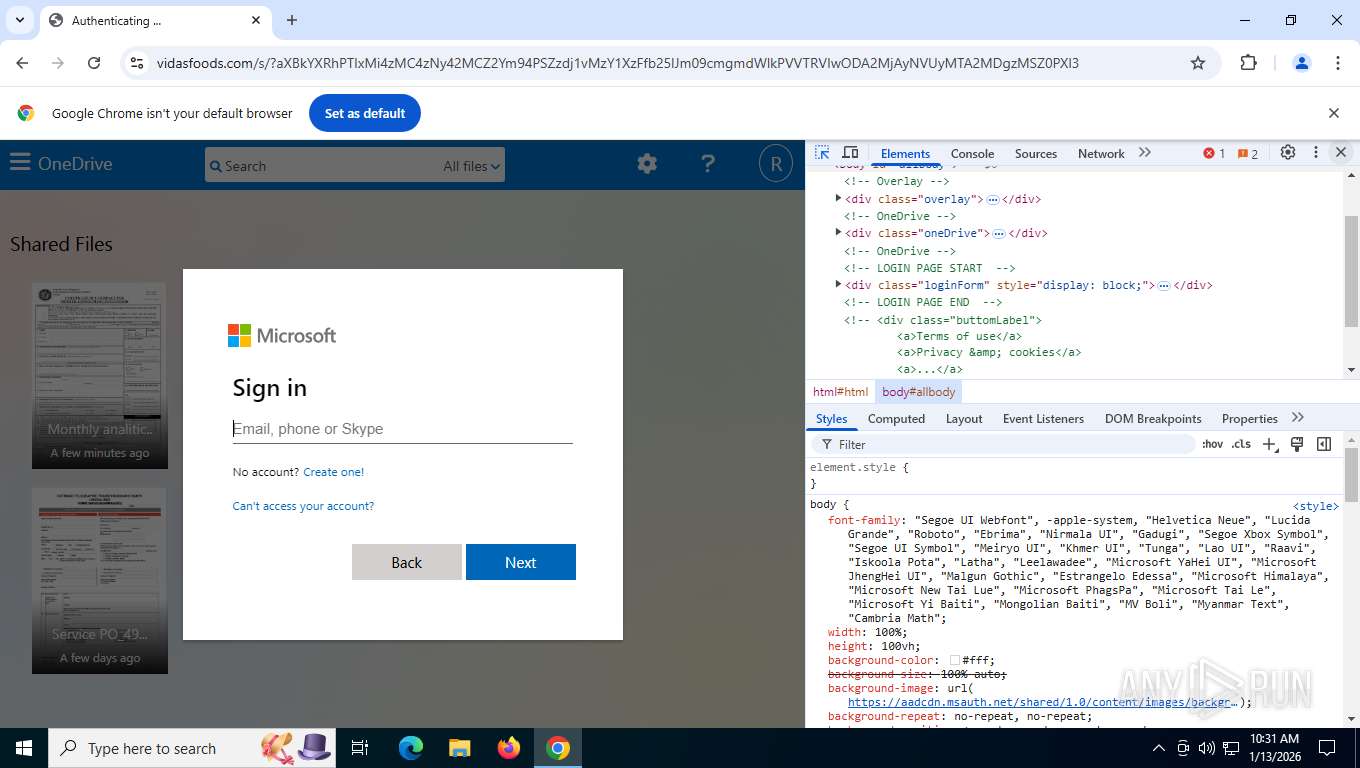
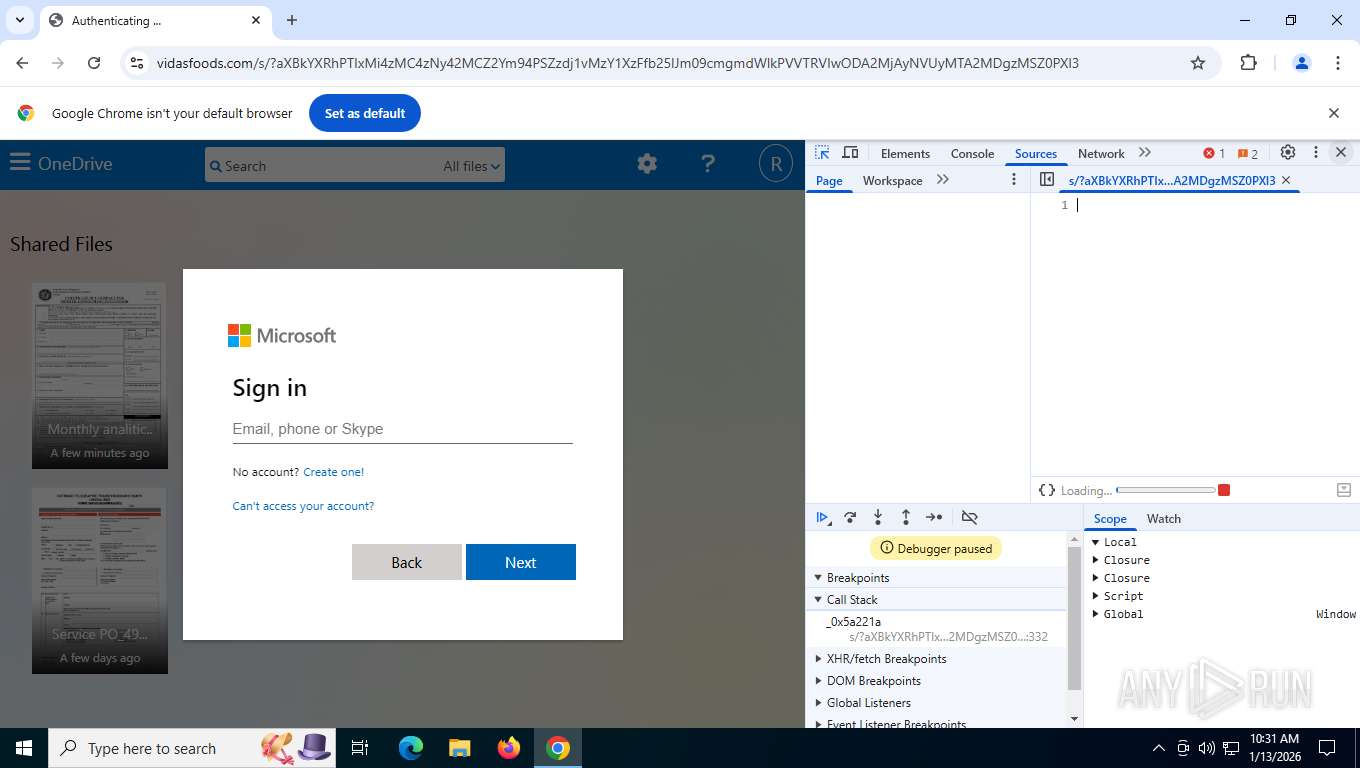
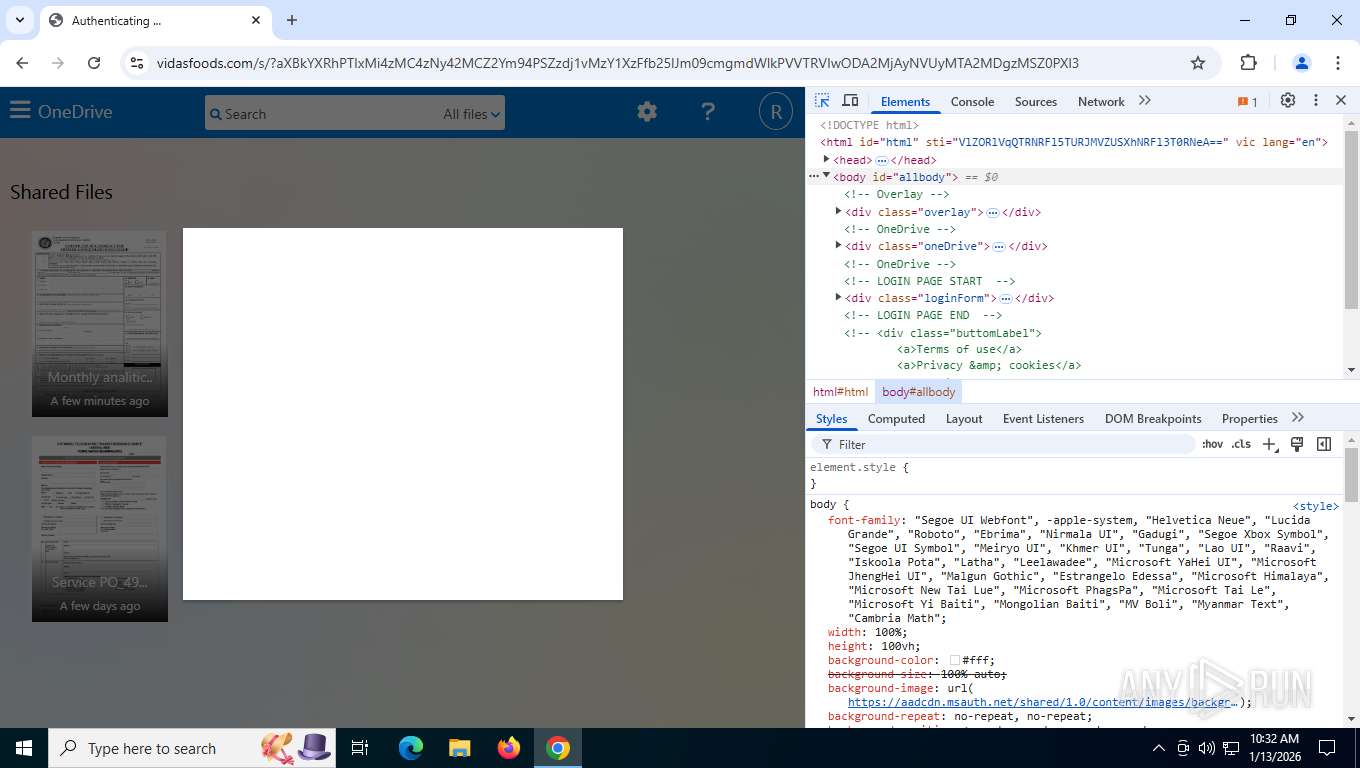
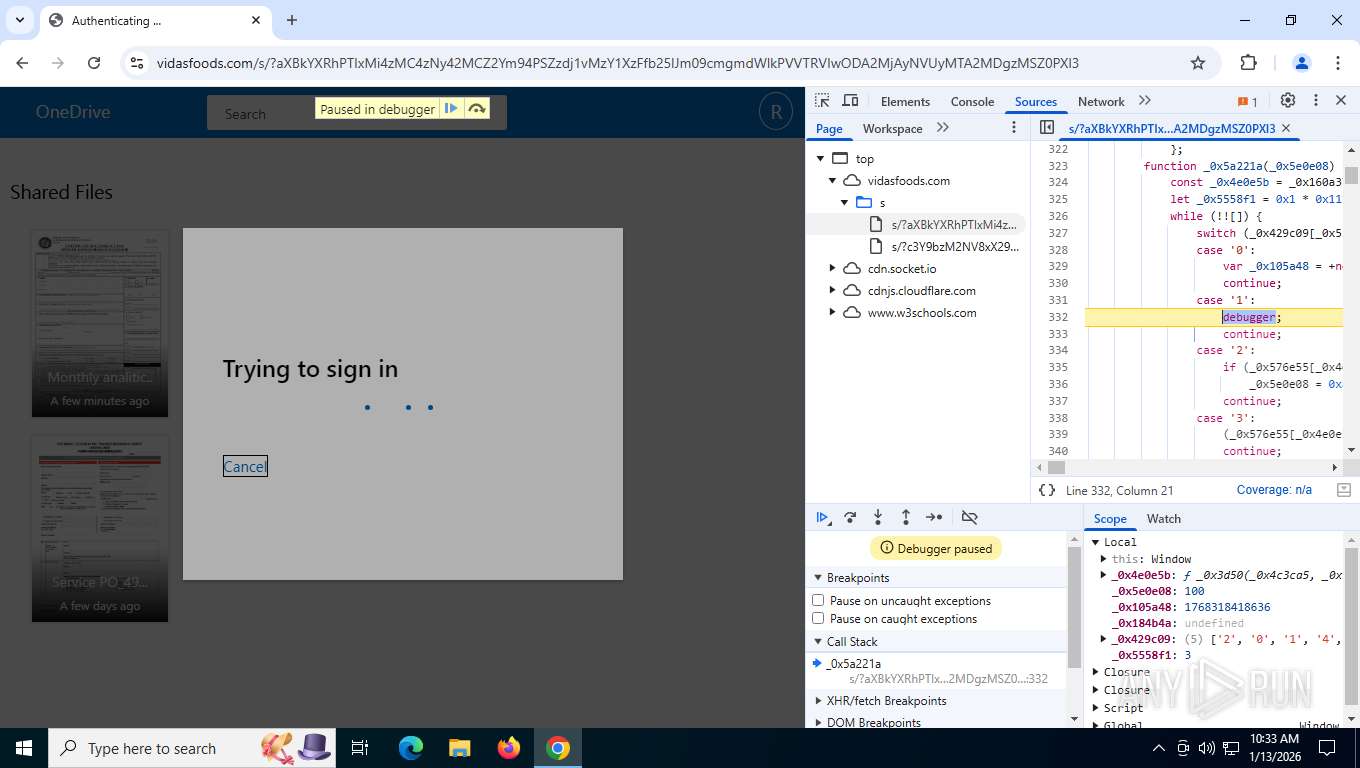
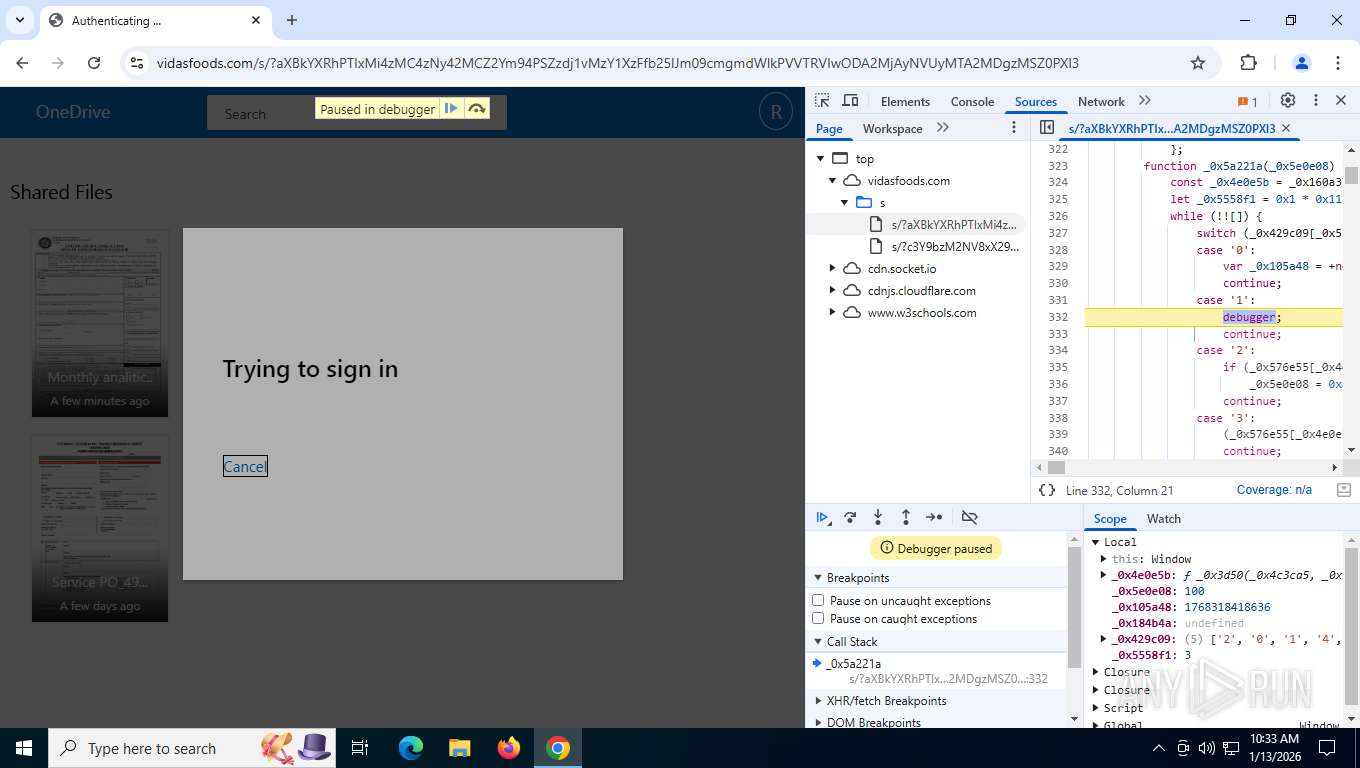
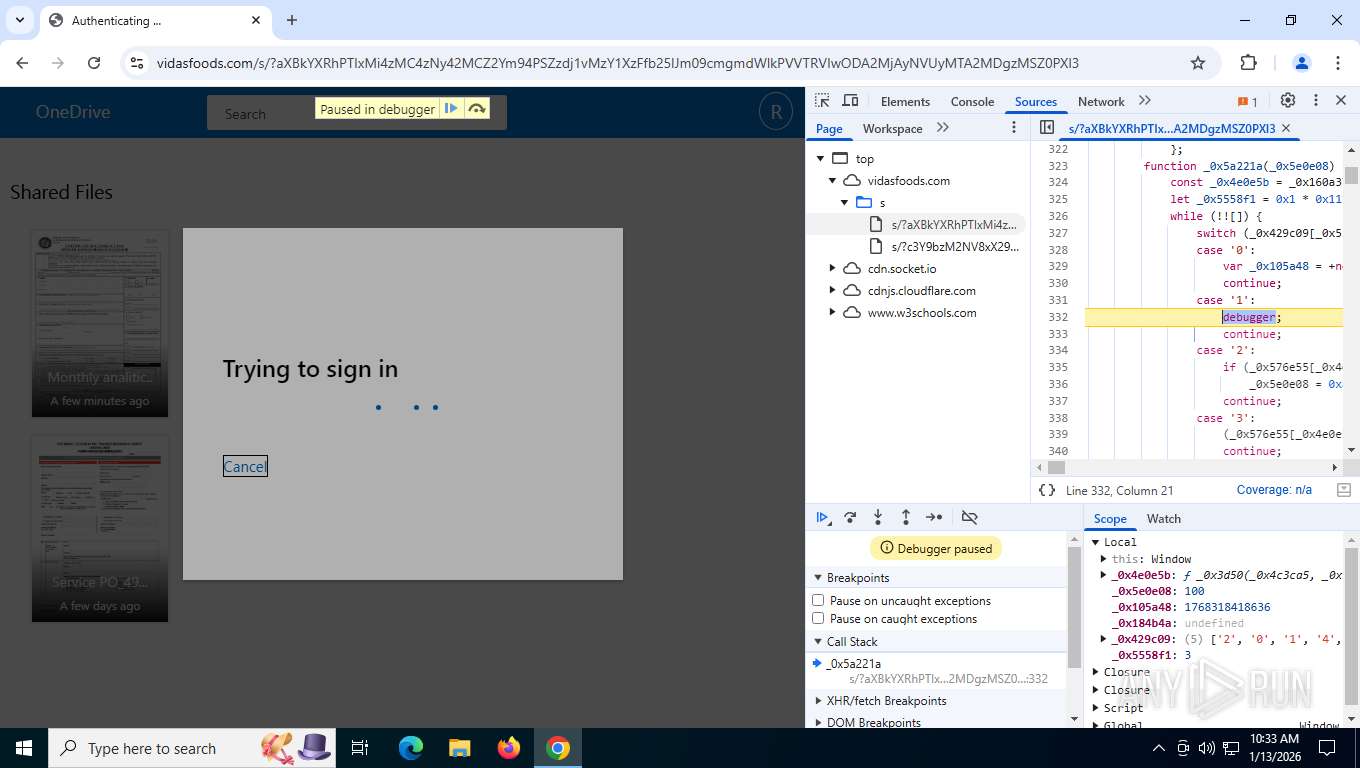
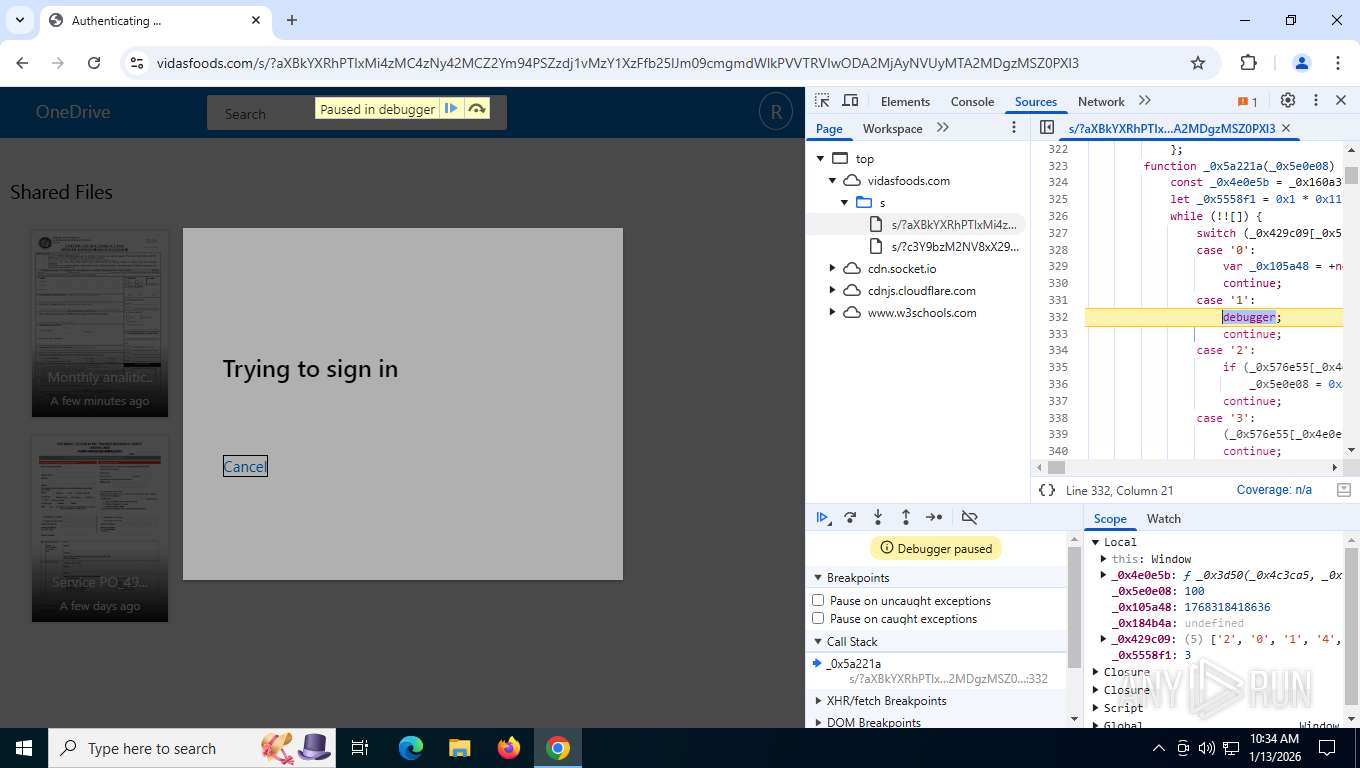
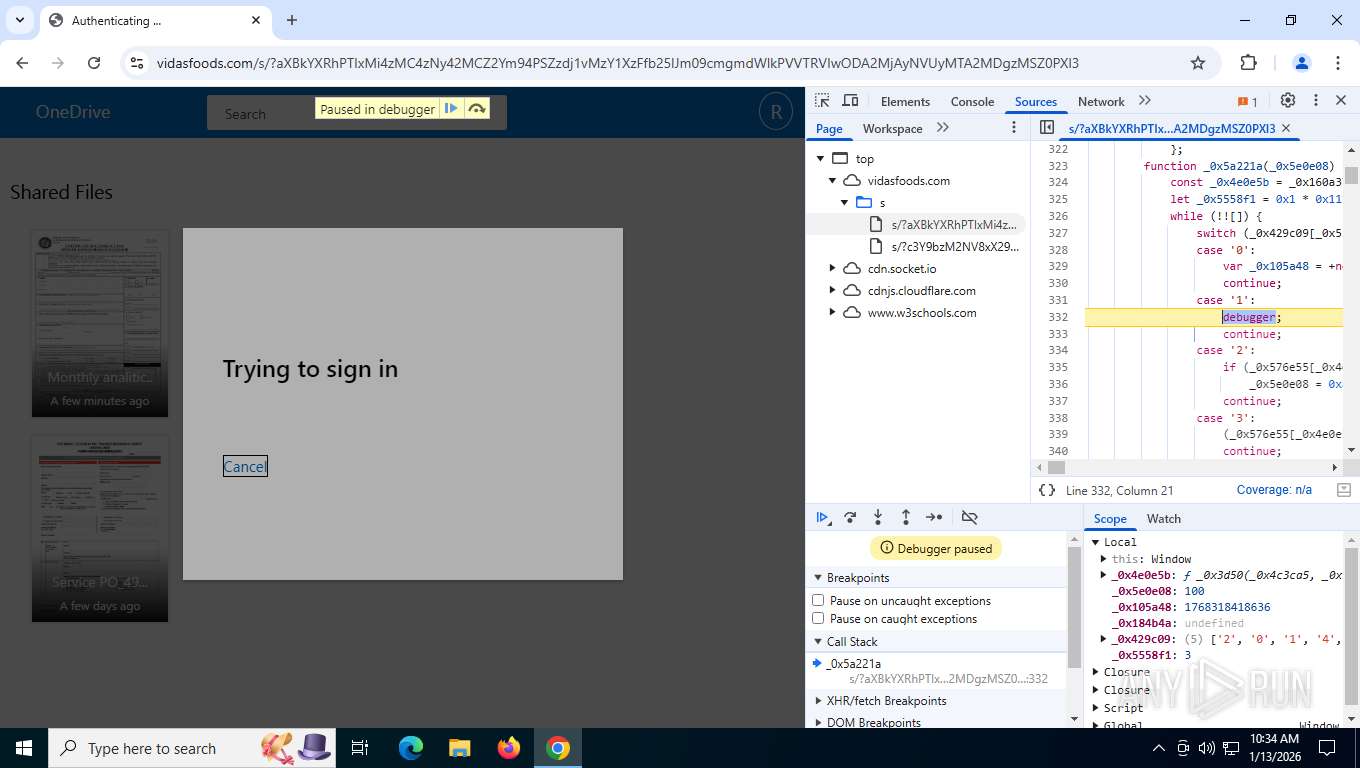
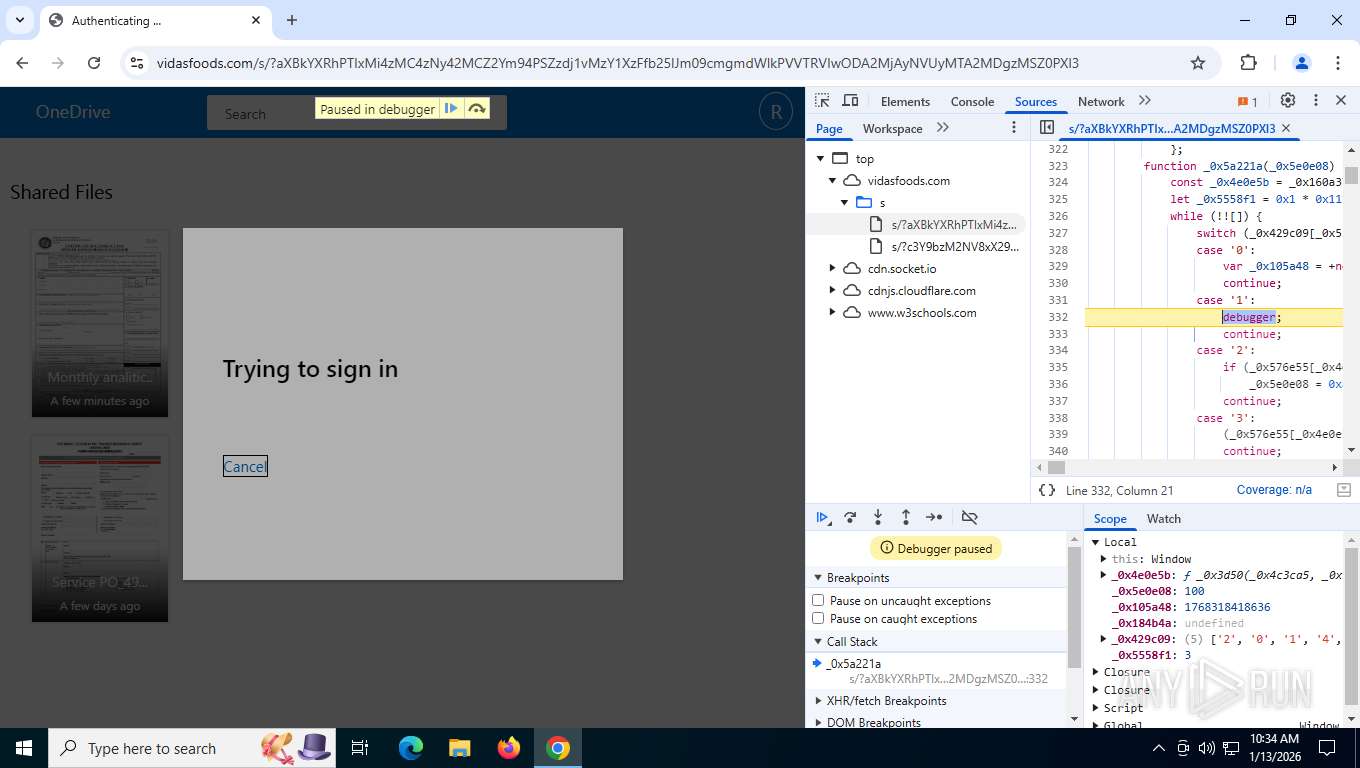
Fake Microsoft Authentication Page has been detected
- chrome.exe (PID: 7604)
PHISHING has been detected (SURICATA)
- chrome.exe (PID: 7876)
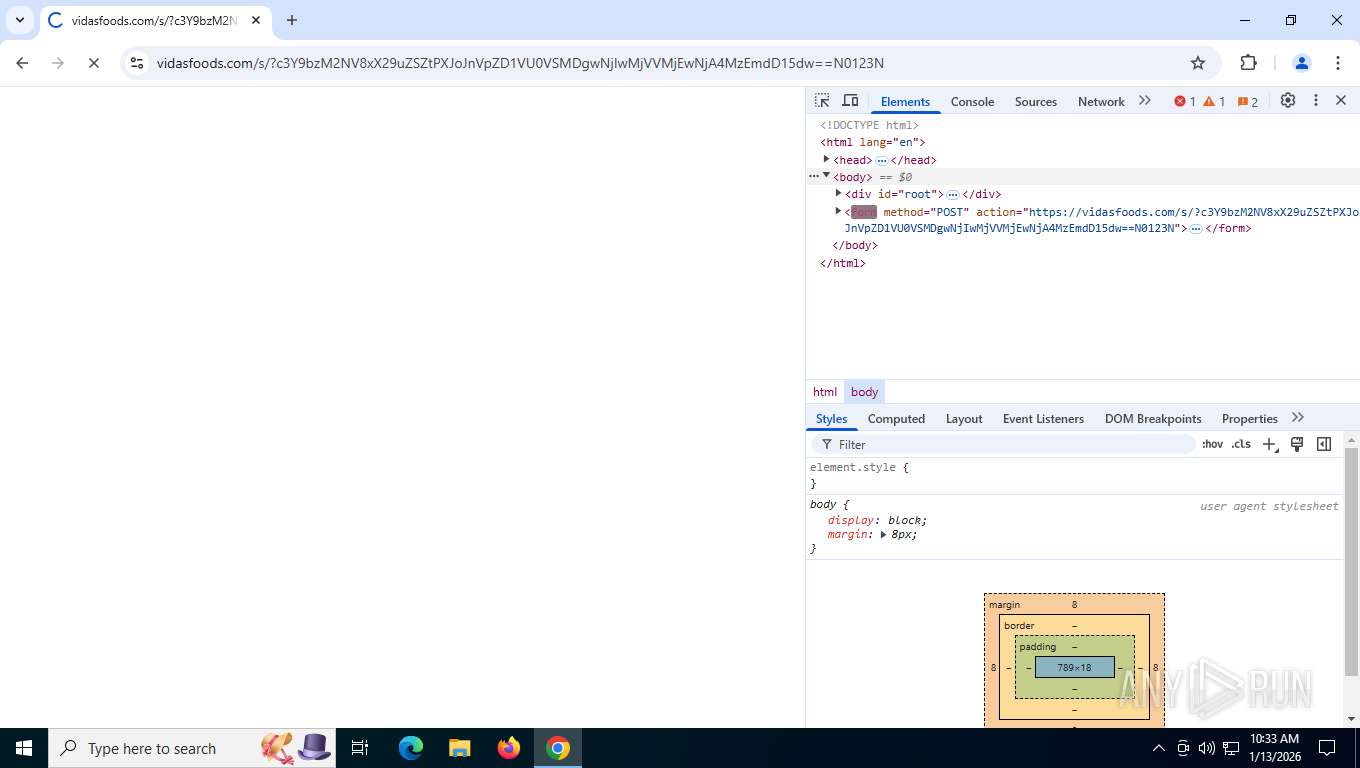
Mamba 2FA phishing kit has been detected
- chrome.exe (PID: 7604)
PHISHING has been detected (ML)
- chrome.exe (PID: 7604)
SUSPICIOUS
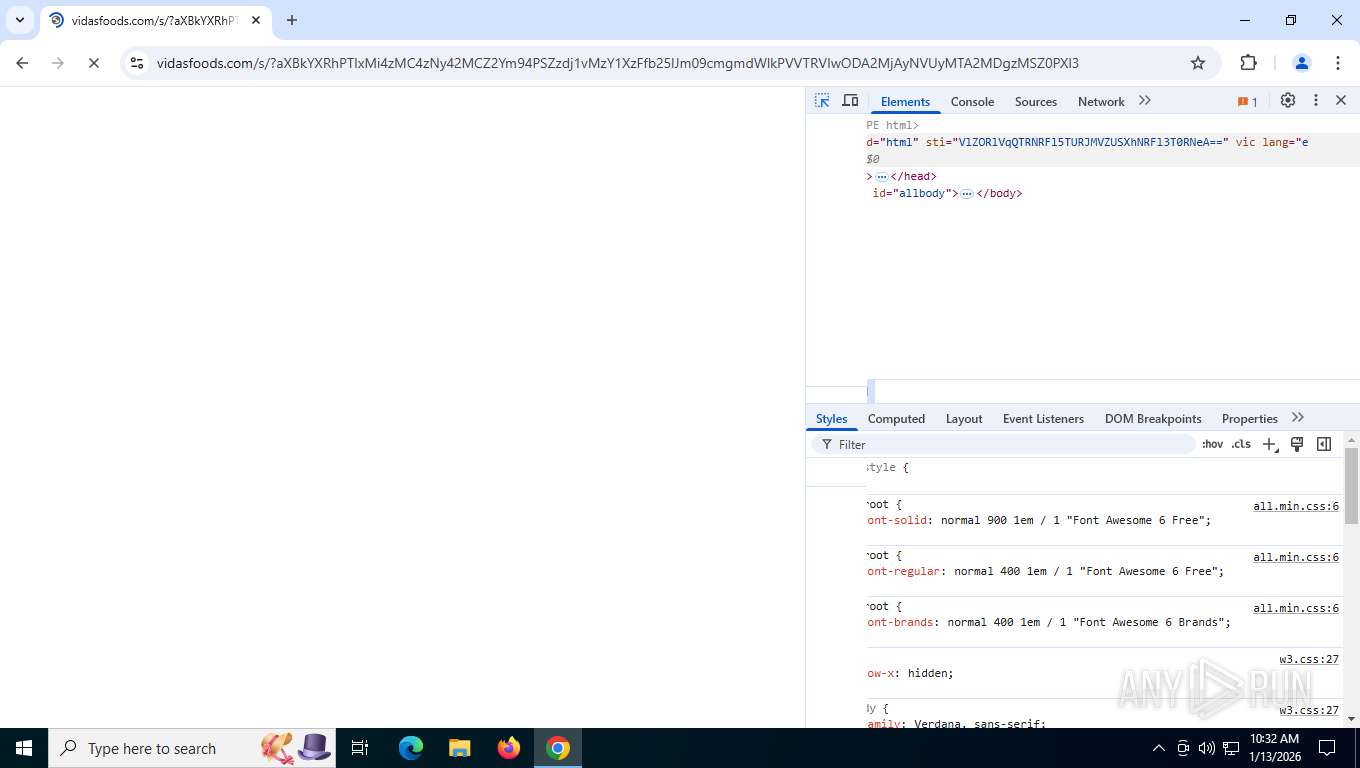
Canvas fingerprinting is present
- chrome.exe (PID: 7604)
INFO
Application launched itself
- chrome.exe (PID: 7604)
Checks supported languages
- TextInputHost.exe (PID: 7460)
Reads the computer name
- TextInputHost.exe (PID: 7460)
Page contains obfuscated JavaScript
- chrome.exe (PID: 7604)
Checks proxy server information
- slui.exe (PID: 7172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
187
Monitored processes
38
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=14 --field-trial-handle=2932,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --init-isolate-as-foreground --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=20 --field-trial-handle=3136,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5676 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --pdf-renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--jitless --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --field-trial-handle=3188,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=28 --field-trial-handle=3760,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=34 --field-trial-handle=6520,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --pdf-renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--jitless --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=22 --field-trial-handle=5088,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=18 --field-trial-handle=5992,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5708 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=13 --field-trial-handle=5940,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=30 --field-trial-handle=5844,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=29 --field-trial-handle=5080,i,17404648549819496885,10240112943907951595,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5656 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
3 882
Read events
3 882
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
9
Text files
83
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RFfe1eb.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RFfe1eb.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RFfe1eb.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RFfe1eb.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFfe1eb.TMP | — | |
MD5:— | SHA256:— | |||
| 7604 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFfe1db.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
351
TCP/UDP connections
112
DNS requests
128
Threats
51
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
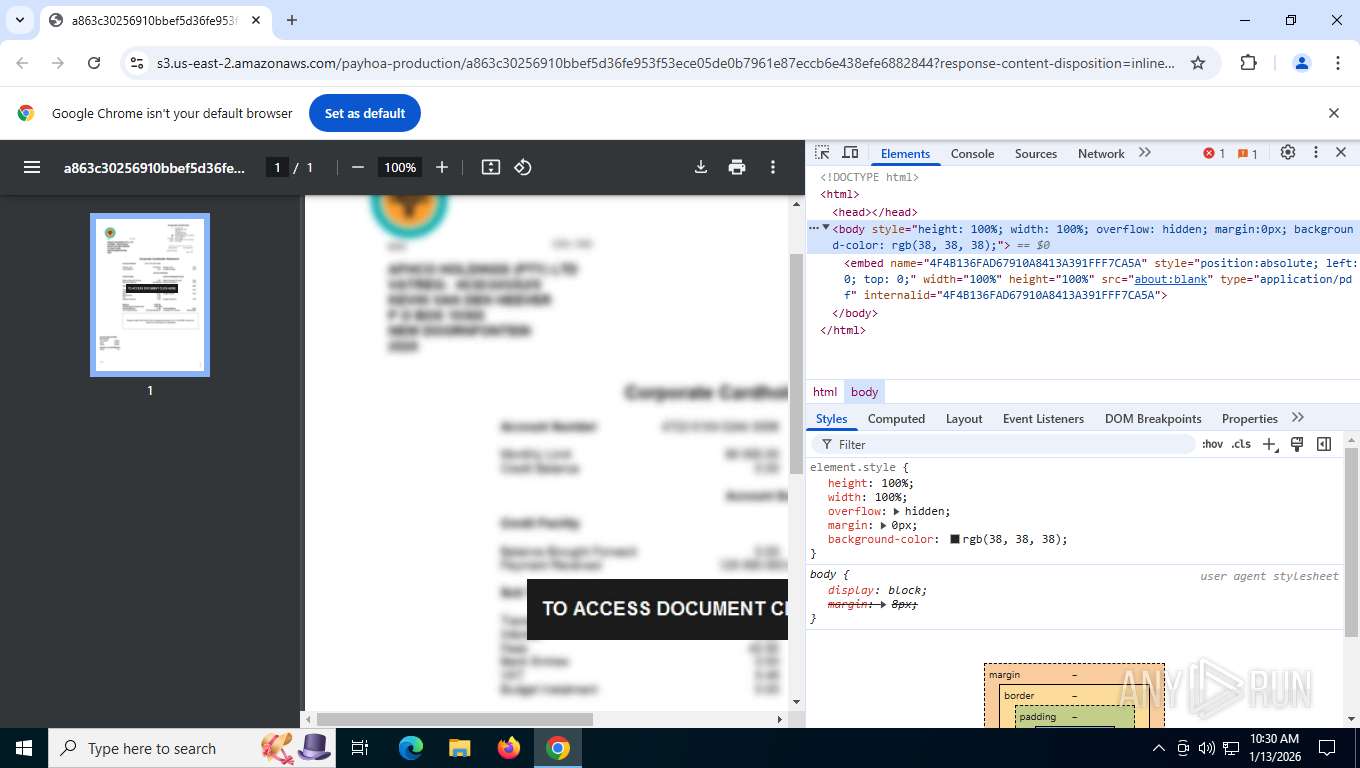
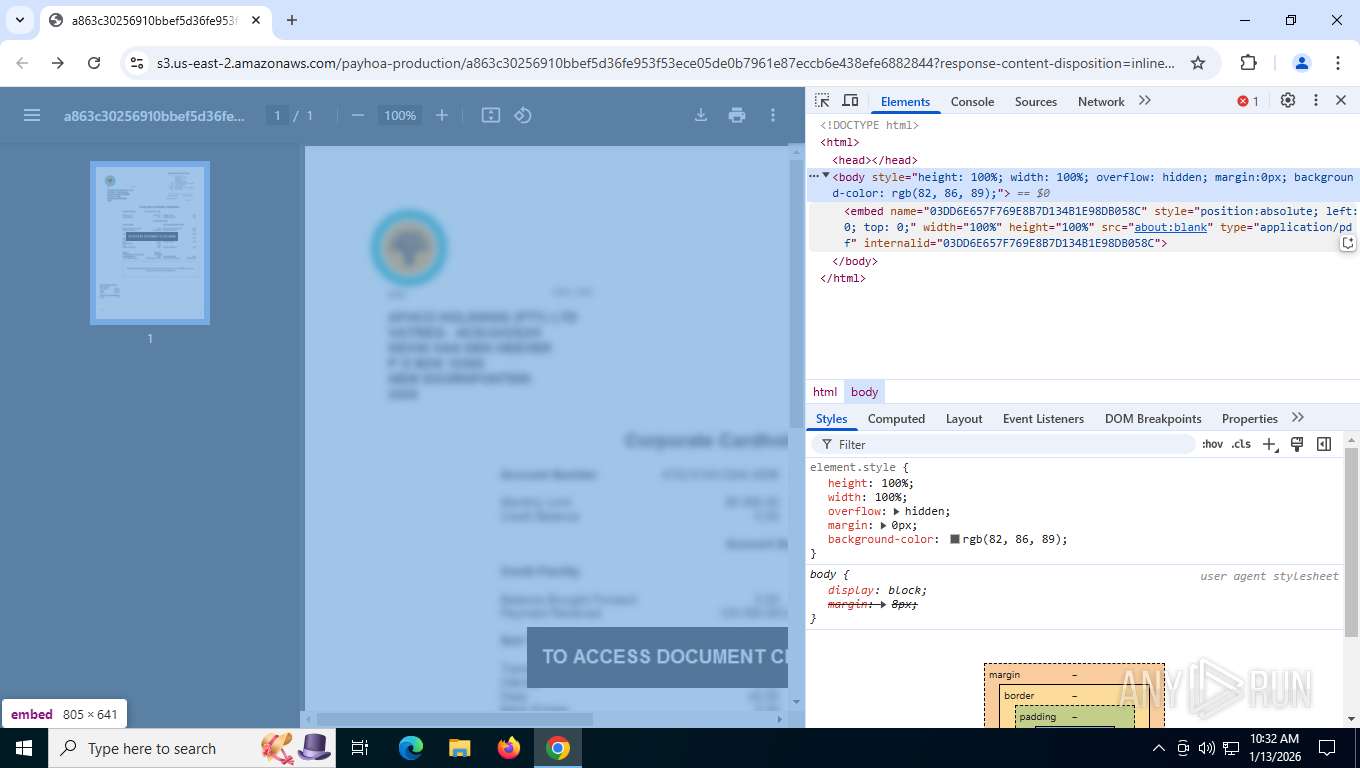
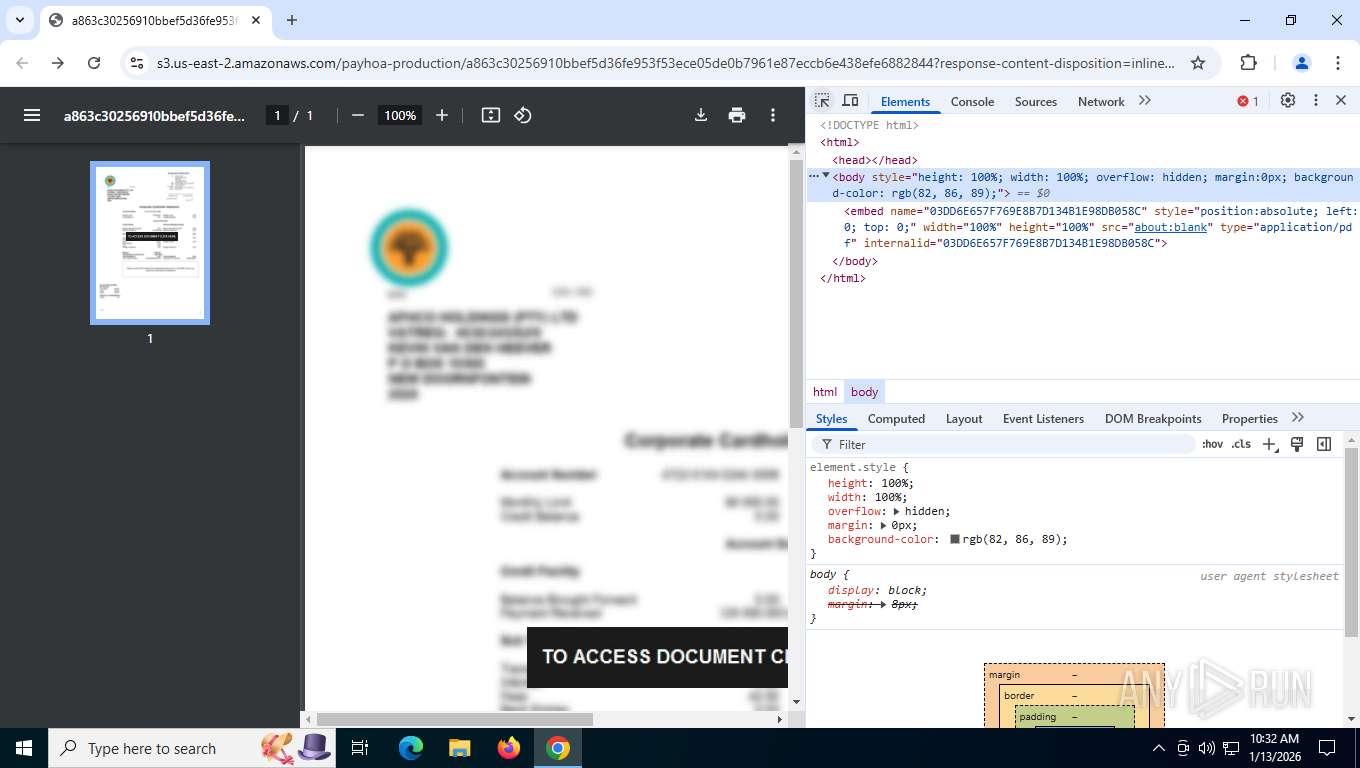
7876 | chrome.exe | GET | 302 | 65.8.131.67:443 | https://eu-west-1.protection.sophos.com/?d=s3.us-east-2.amazonaws.com&u=aHR0cHM6Ly9zMy51cy1lYXN0LTIuYW1hem9uYXdzLmNvbS9wYXlob2EtcHJvZHVjdGlvbi9hODYzYzMwMjU2OTEwYmJlZjVkMzZmZTk1M2Y1M2VjZTA1ZGUwYjc5NjFlODdlY2NiNmU0MzhlZmU2ODgyODQ0P3Jlc3BvbnNlLWNvbnRlbnQtZGlzcG9zaXRpb249aW5saW5lJTNCJTIwZmlsZW5hbWUlM0QlMjJQQVlNRU5UX0RPQy5wZGYlMjIlM0IlMjBmaWxlbmFtZSUyQSUzRFVURi04JTI3JTI3UEFZTUVOVCUyNTIwRE9DLnBkZiZYLUFtei1Db250ZW50LVNoYTI1Nj1VTlNJR05FRC1QQVlMT0FEJlgtQW16LUFsZ29yaXRobT1BV1M0LUhNQUMtU0hBMjU2JlgtQW16LUNyZWRlbnRpYWw9QUtJQUpJS0hHR0hJUFdOMkNKVkElMkYyMDI2MDExMyUyRnVzLWVhc3QtMiUyRnMzJTJGYXdzNF9yZXF1ZXN0JlgtQW16LURhdGU9MjAyNjAxMTNUMTI0NDA4WiZYLUFtei1TaWduZWRIZWFkZXJzPWhvc3QmWC1BbXotRXhwaXJlcz01MTg0MDAmWC1BbXotU2lnbmF0dXJlPTljYjgwZTBlNzQ5OGJjODc5ZmE5Mzg3N2Y2ZmFjNjQ3ZjMxNjVhOGVhYmEwZWE2NWQwNGUyNmYxODc5YmFiNGQ%3D&i=NjdmZTRhYzc2NGM0M2EyYTU5YWExZGQ5&t=TlhHR0NVN1hiVFU2emgwc2NlZkc1MDlsb1hWSXJML01iSjVDZDVzcFdkND0%3D&h=4af3af688ab34b3591d30fd67a33694e&s=AVNPUEhUT0NFTkNSWVBUSVY6stDr4ZrZPtv3nvzswtL6XoRHxmUJ3_zvfdJvuzkx6csRIIs272SenxRRntwYzIc | unknown | — | — | unknown |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
7876 | chrome.exe | GET | 200 | 142.250.186.138:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | binary | 41 b | whitelisted |
7876 | chrome.exe | GET | 200 | 142.250.185.110:80 | http://clients2.google.com/time/1/current?cup2key=8:oVhttWyCNCL_CzZNviXTqnOjrIIF5rocz9BpAdbbqWY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | unknown | — | — | whitelisted |
3412 | svchost.exe | PUT | — | 172.211.123.249:443 | 172.211.123.249:443 | unknown | — | — | unknown |
3412 | svchost.exe | PUT | — | 192.168.100.8:49750 | 192.168.100.8:49750 | unknown | — | — | unknown |
7876 | chrome.exe | POST | 200 | 64.233.184.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | text | 17 b | whitelisted |
7876 | chrome.exe | GET | 200 | 196.35.198.156:443 | https://linkshield.synaq.com/link?id=1vfeMC-0004kX-G2&ts=1768310566&cnf=98739490591342630&url=ORgmWm4KEsX.Ujv_A1pTWvr.Nw-- | unknown | html | 91.6 Kb | unknown |
7876 | chrome.exe | GET | 200 | 142.250.184.202:443 | https://content-autofill.googleapis.com/v1/pages/ChVDaHJvbWUvMTMzLjAuNjk0My4xMjcSIAnSo4O-q9eWbhIFDVNVgbUSBQ3OQUx6IaPvLMnsIhbZEiAJYT6Fp5Yvd4QSBQ34I46fEgUNpNIT0iHErRKKvG5iKg==?alt=proto | unknown | text | 56 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3488 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1784 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7876 | chrome.exe | 142.250.185.110:80 | clients2.google.com | GOOGLE | US | whitelisted |
7876 | chrome.exe | 142.250.186.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7876 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7876 | chrome.exe | 196.35.198.156:443 | linkshield.synaq.com | IS | ZA | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
linkshield.synaq.com |
| whitelisted |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
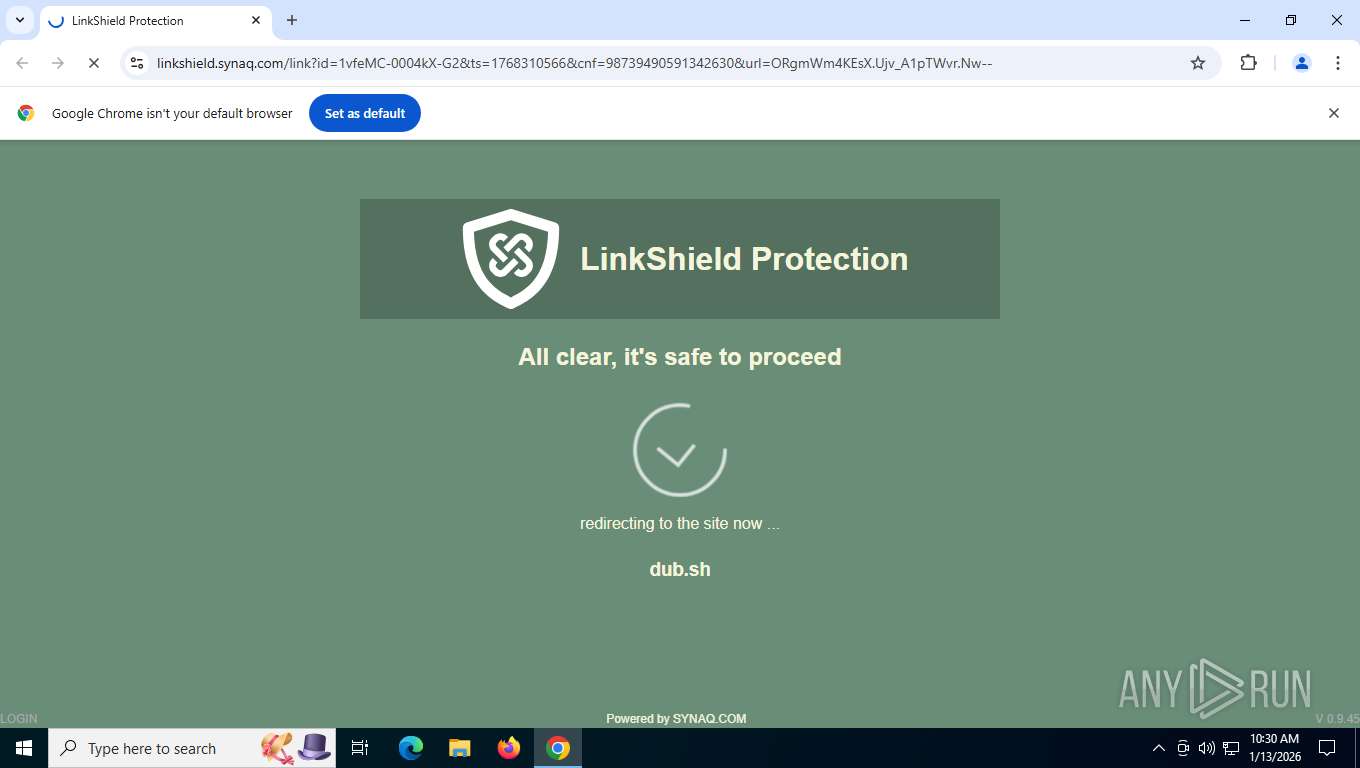
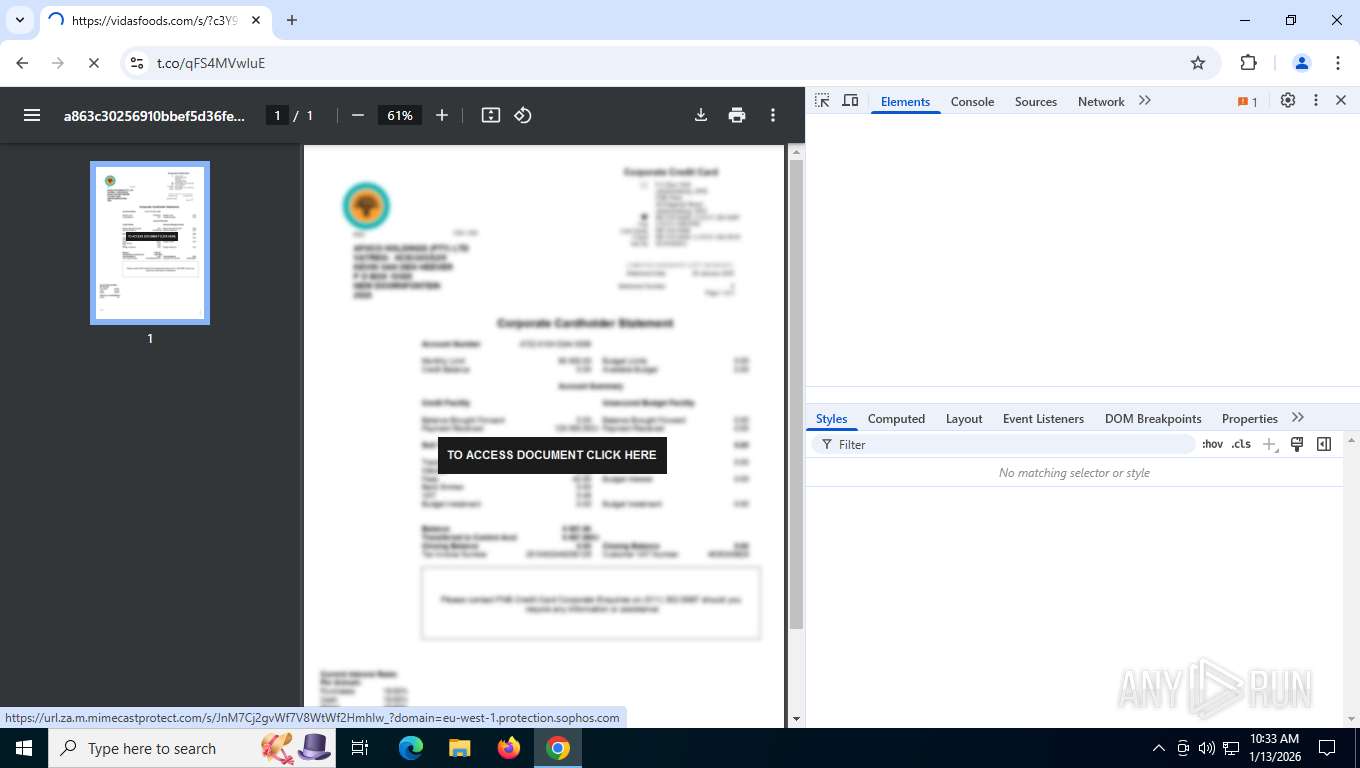
7876 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (dub .sh) |
7876 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (dub .sh) |
7876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google App Engine (appspot .com) |
7876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google App Engine (appspot .com) |
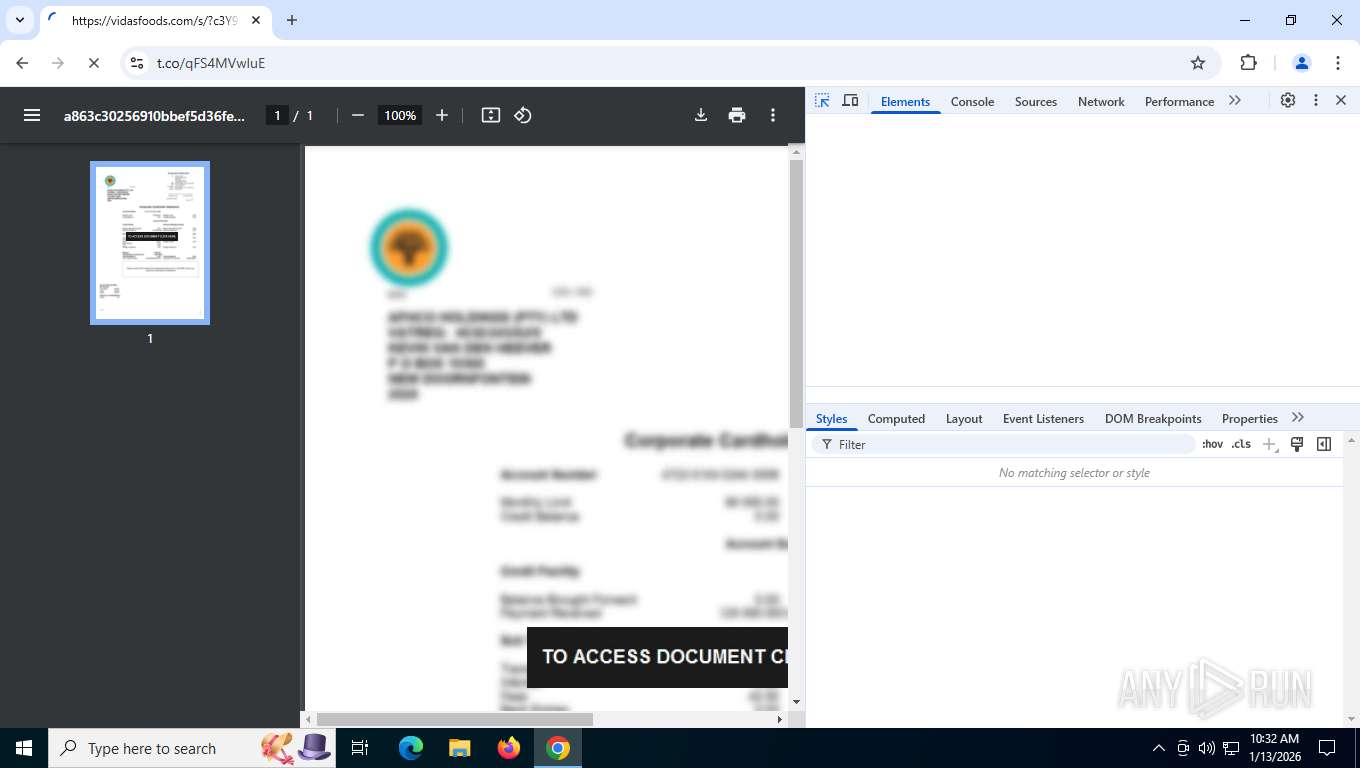
7876 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
7876 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (t .co) |
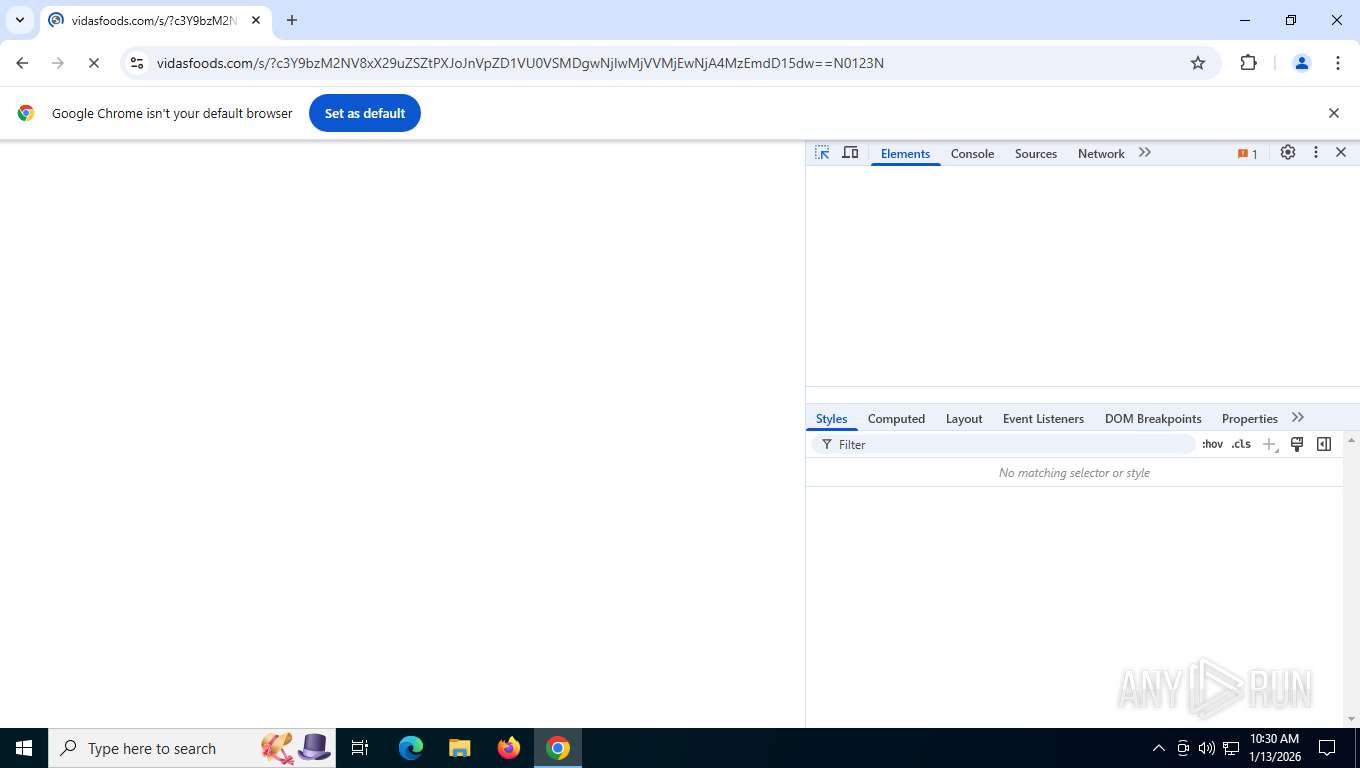
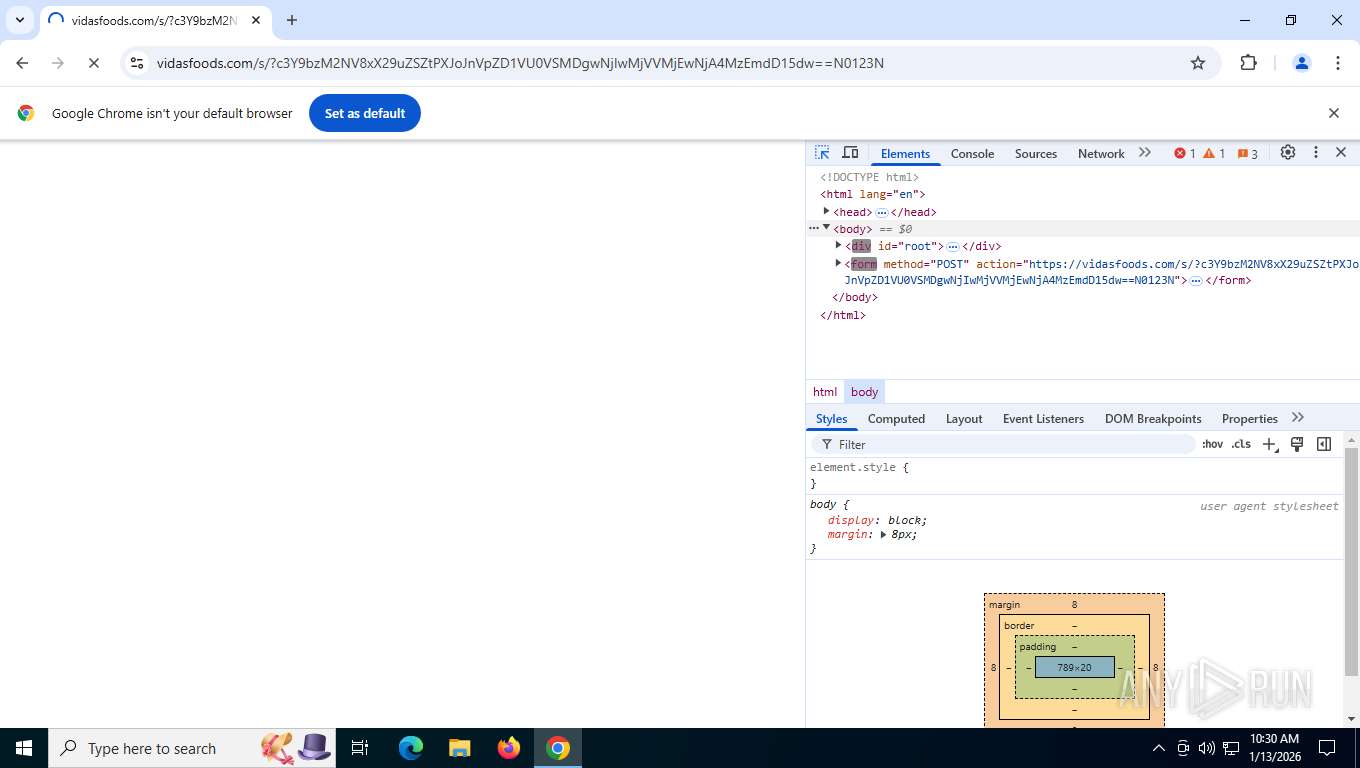
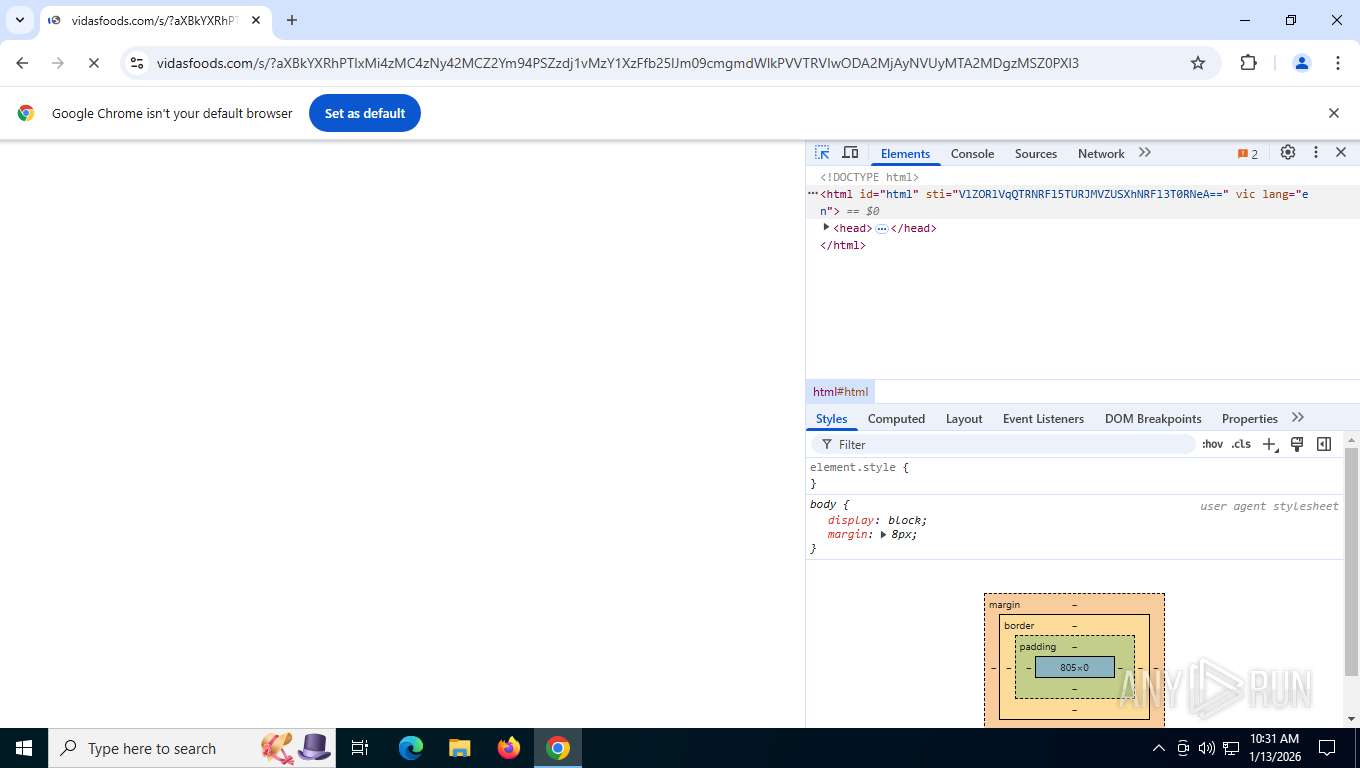
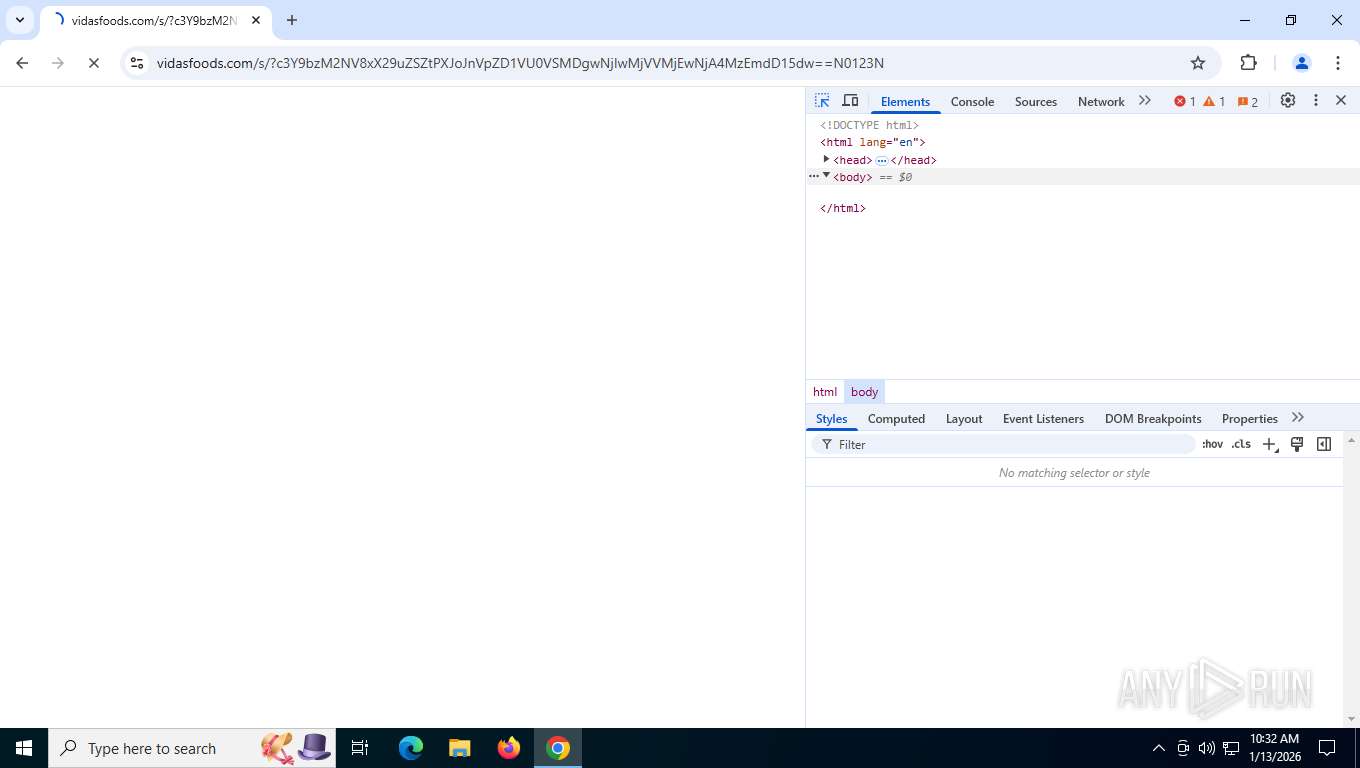
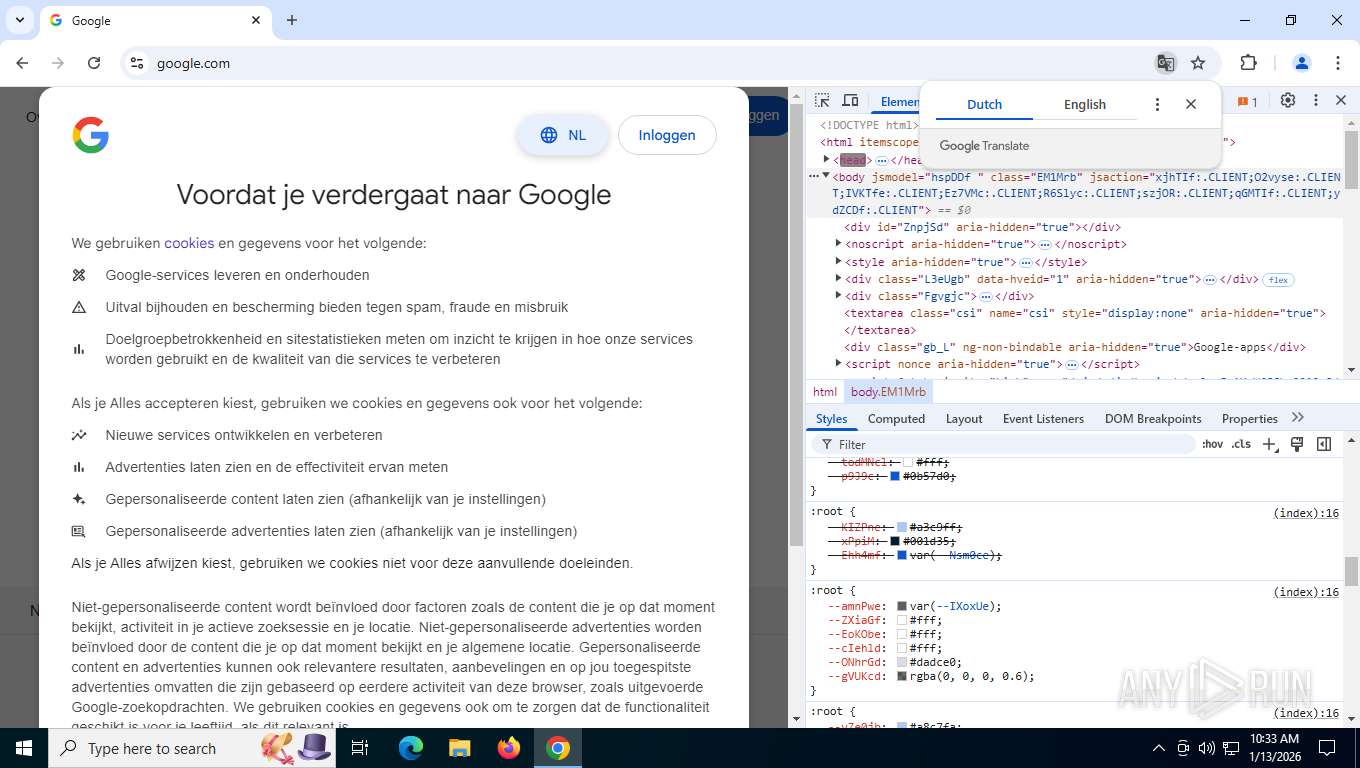
7876 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as Mamba2FA (vidasfoods .com) |
— | — | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Mamba2FA HTTP URL Observed (sv= b64-encoded) |
7876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7876 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |