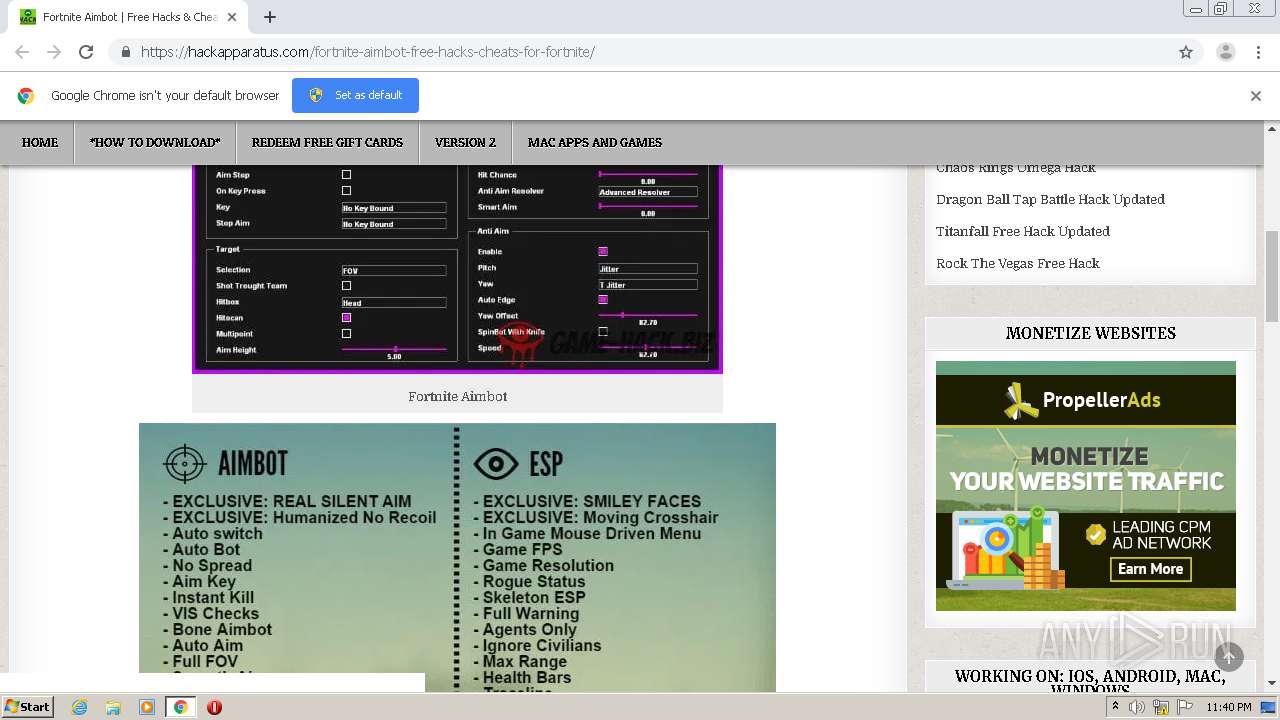
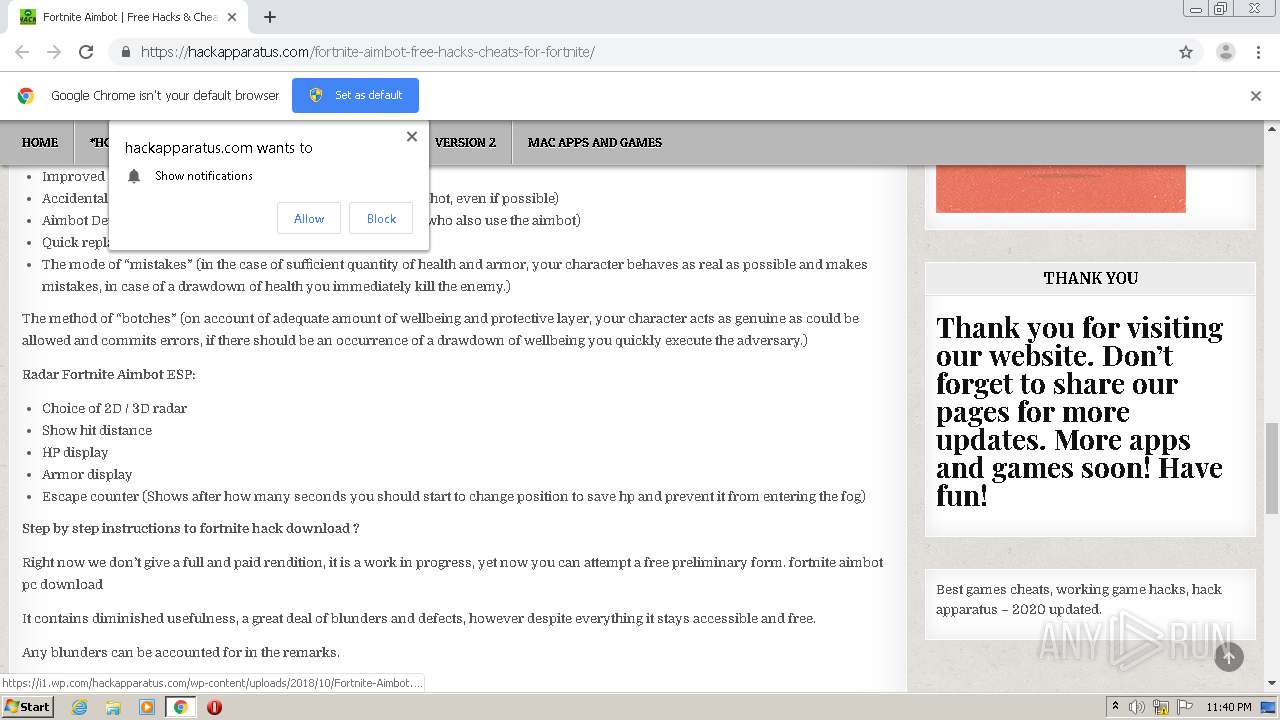
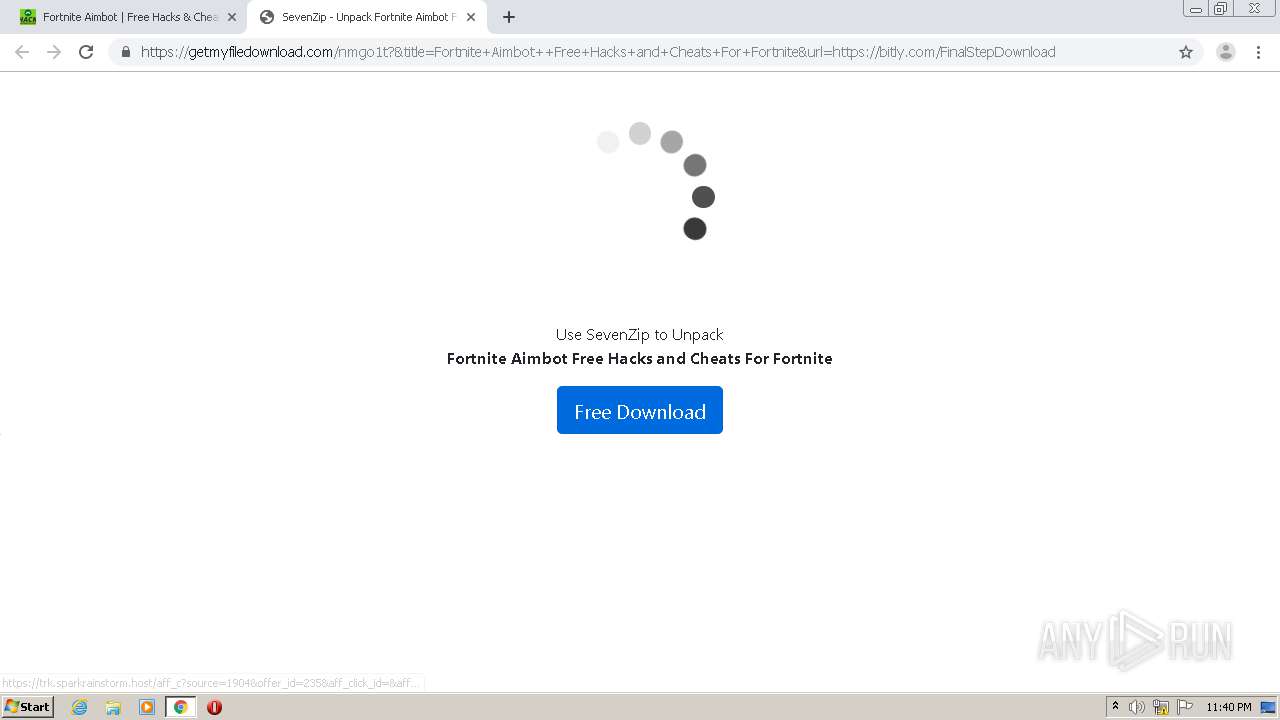
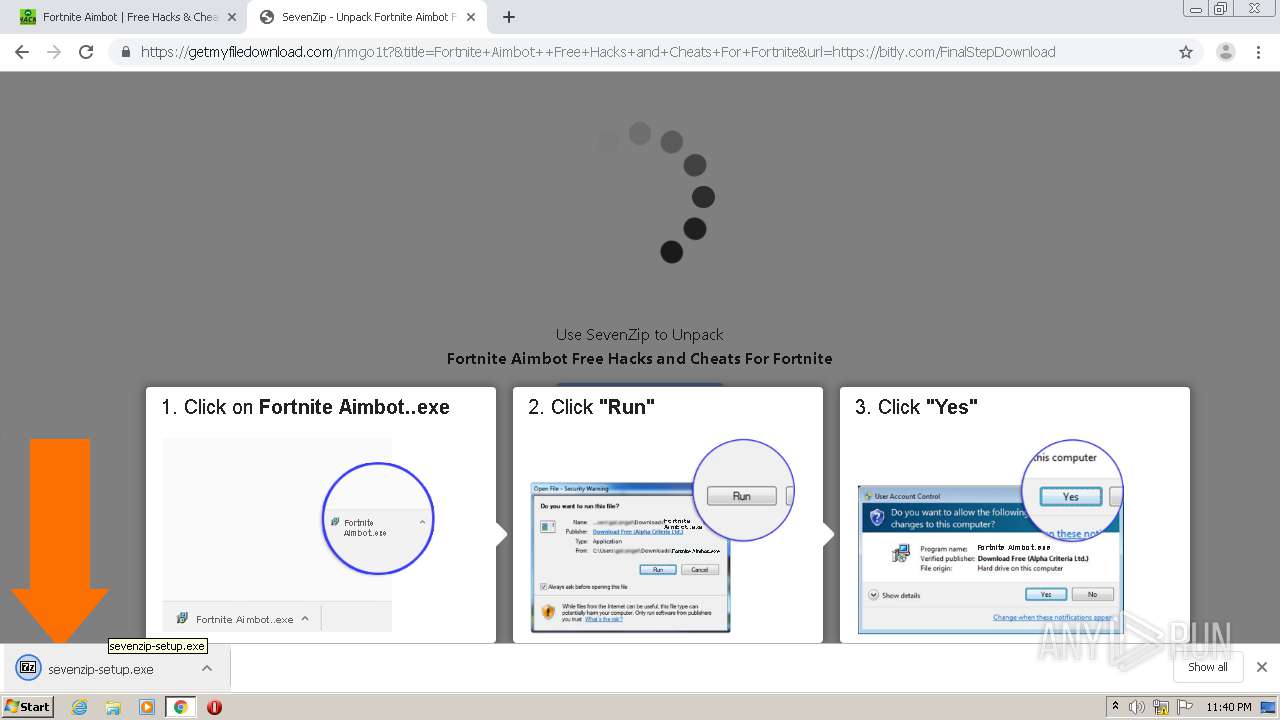
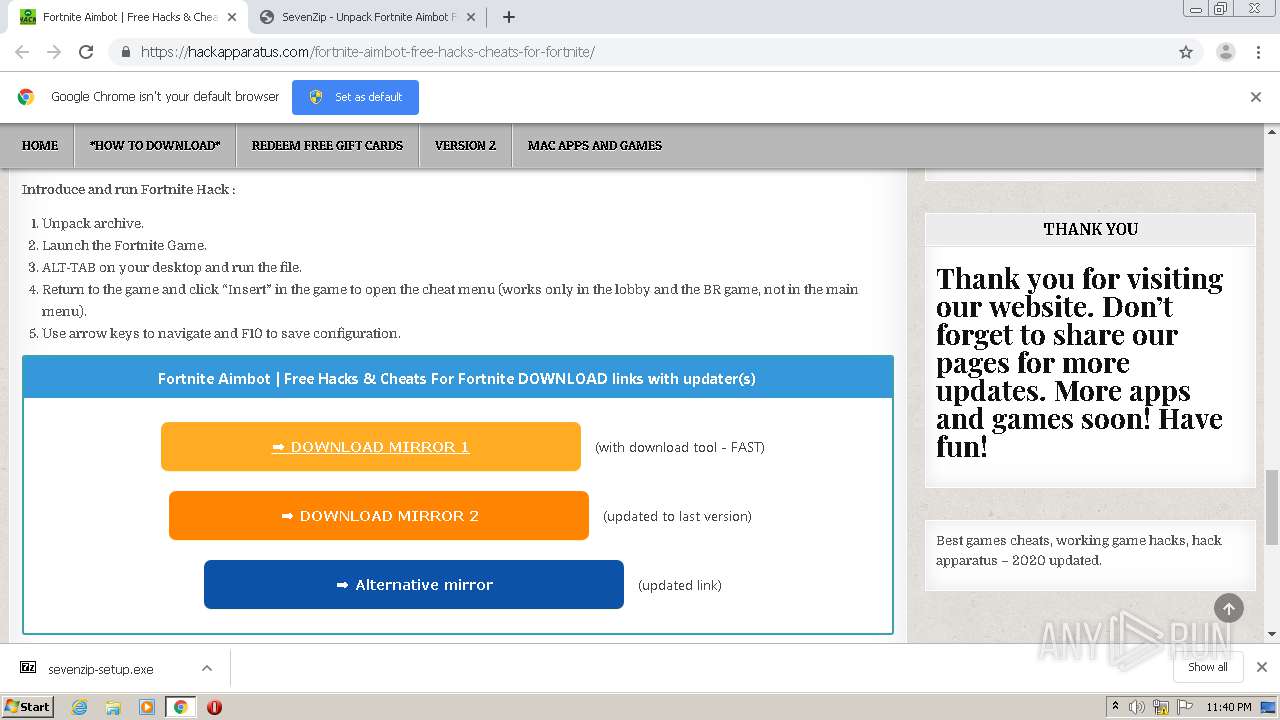
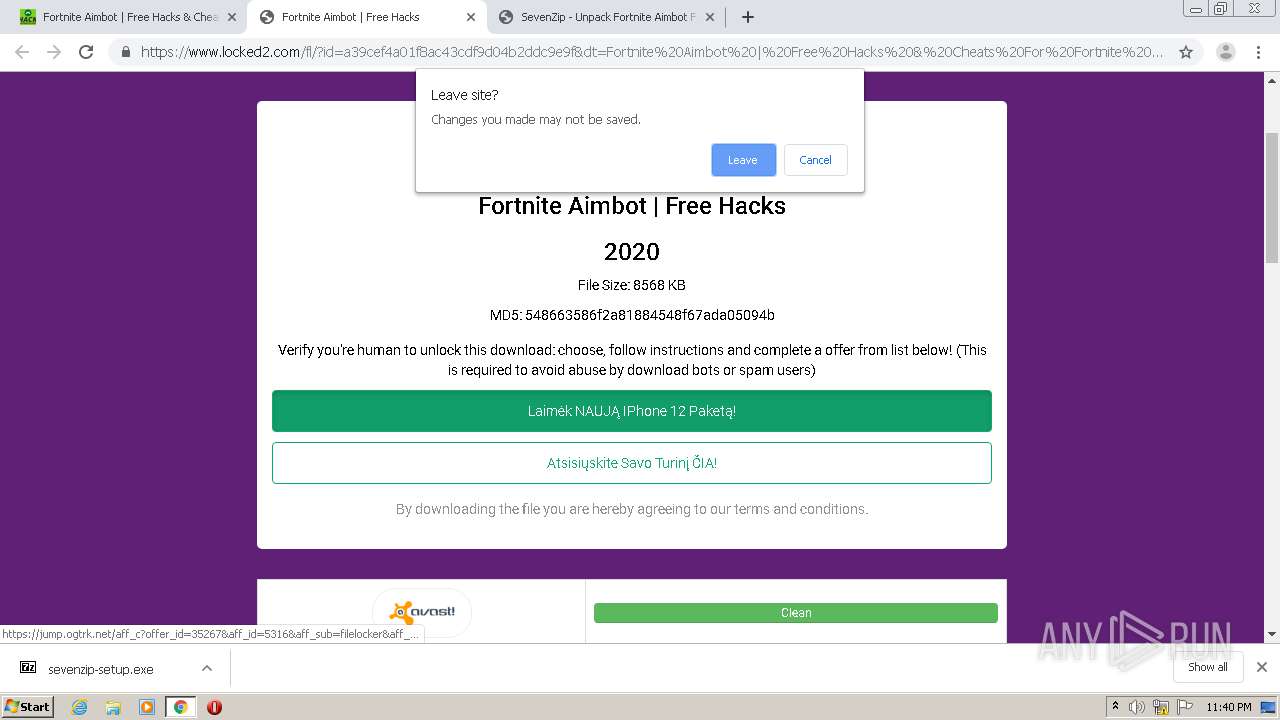
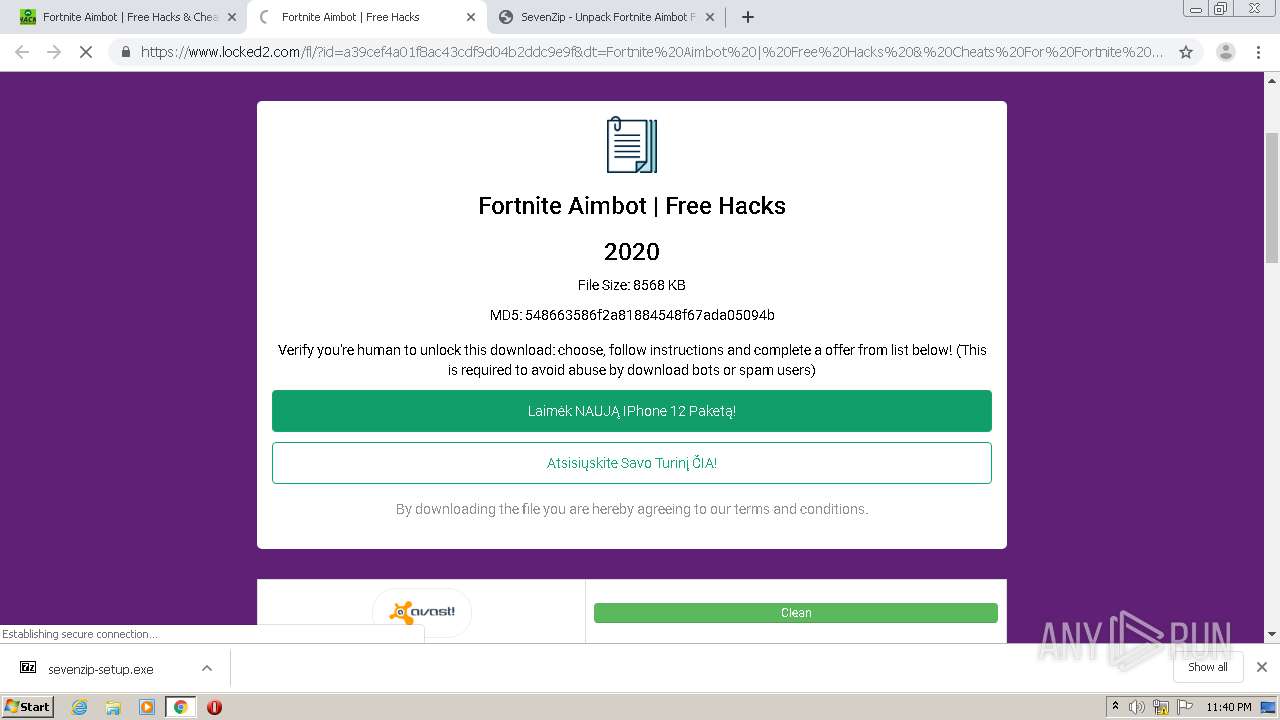
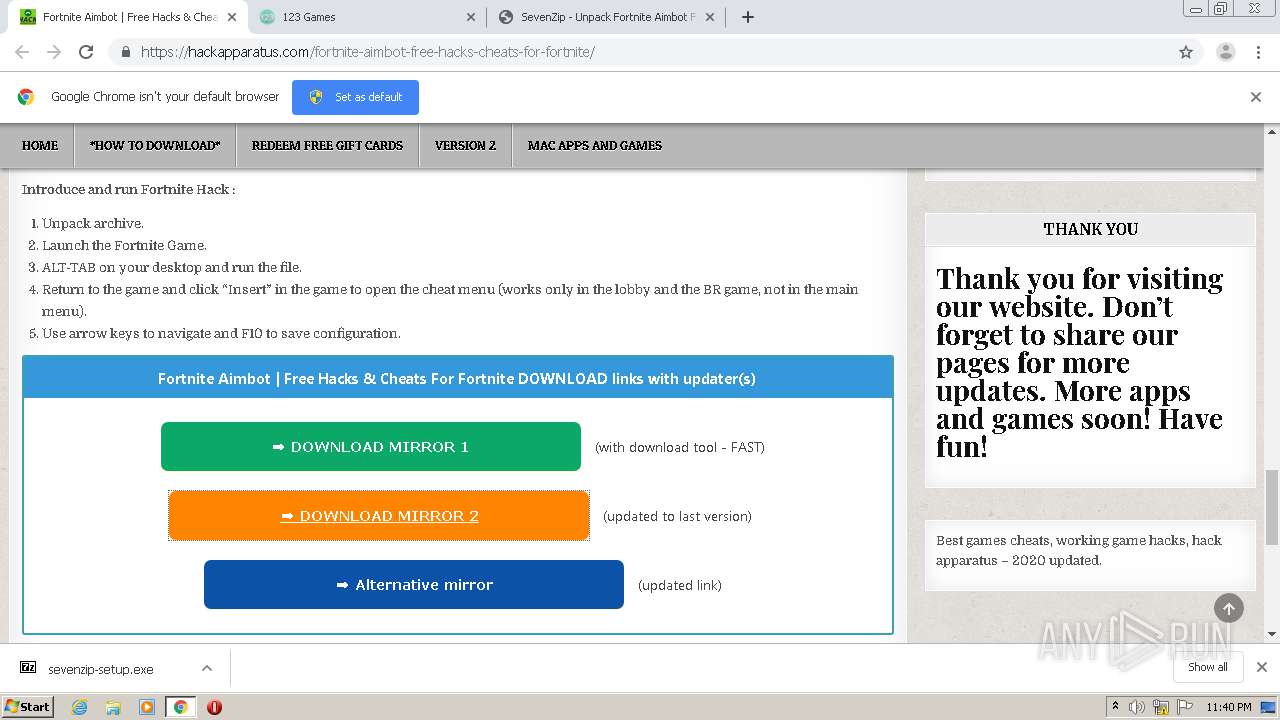
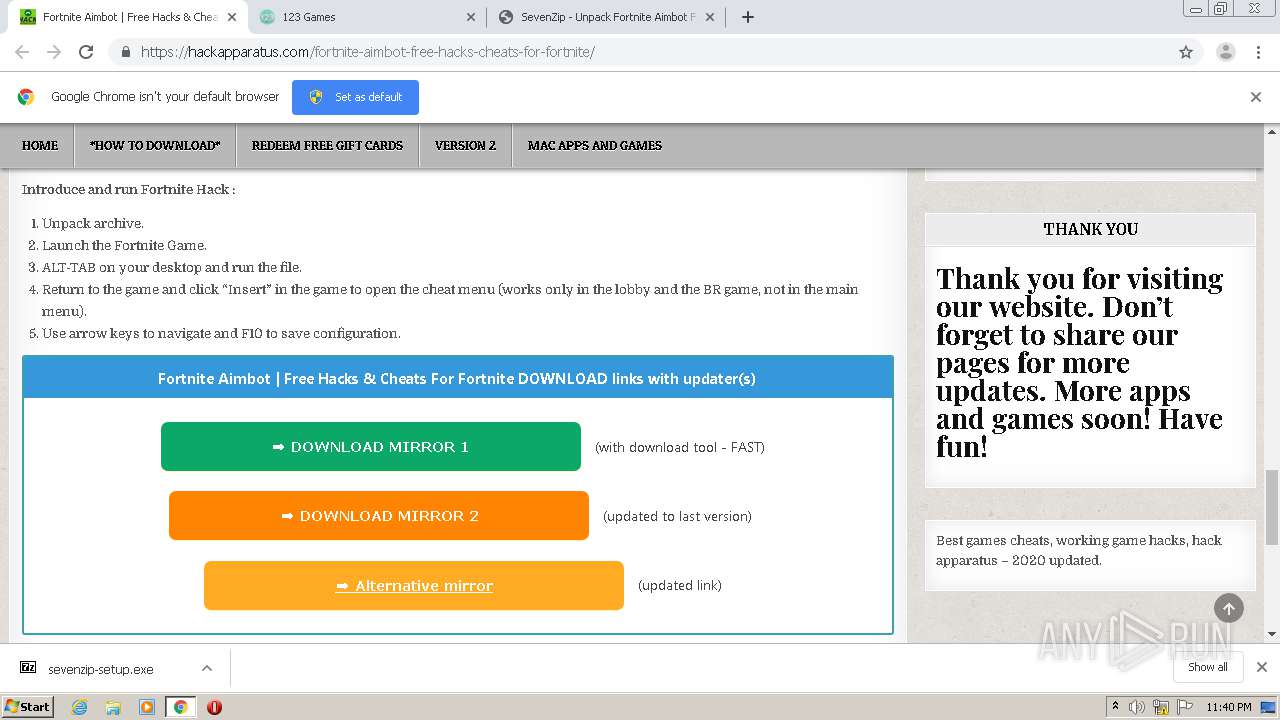
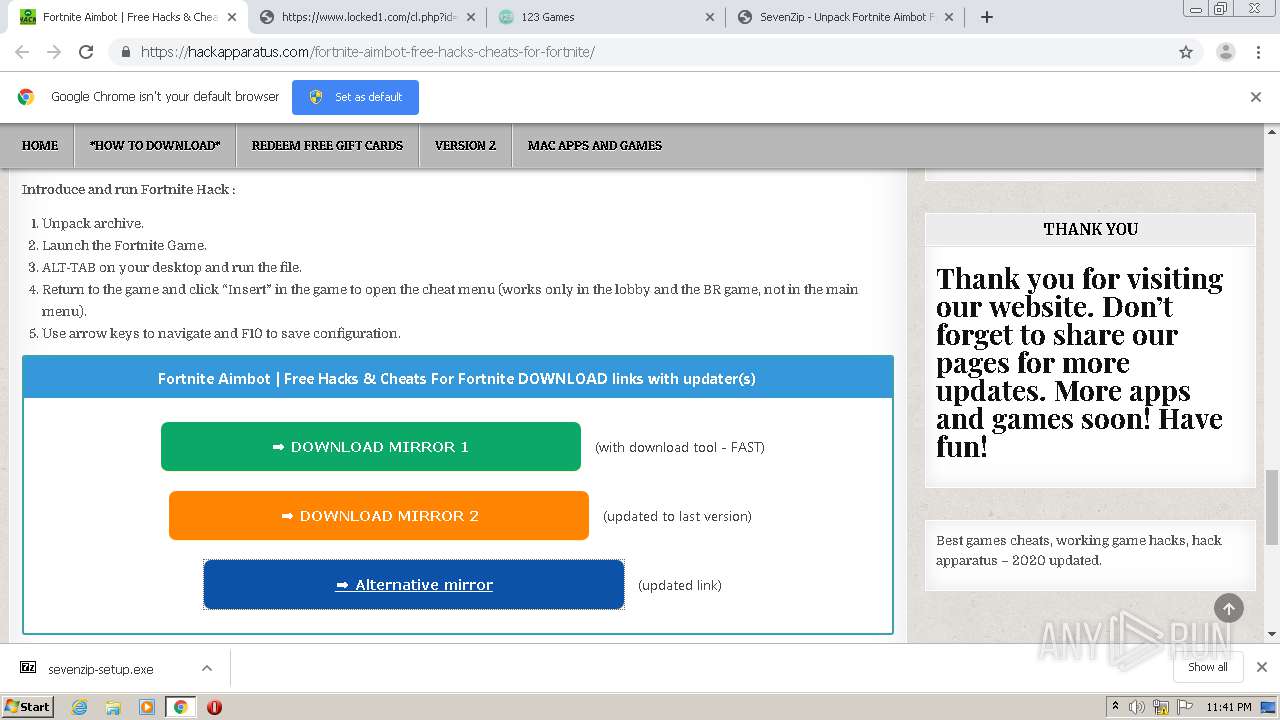
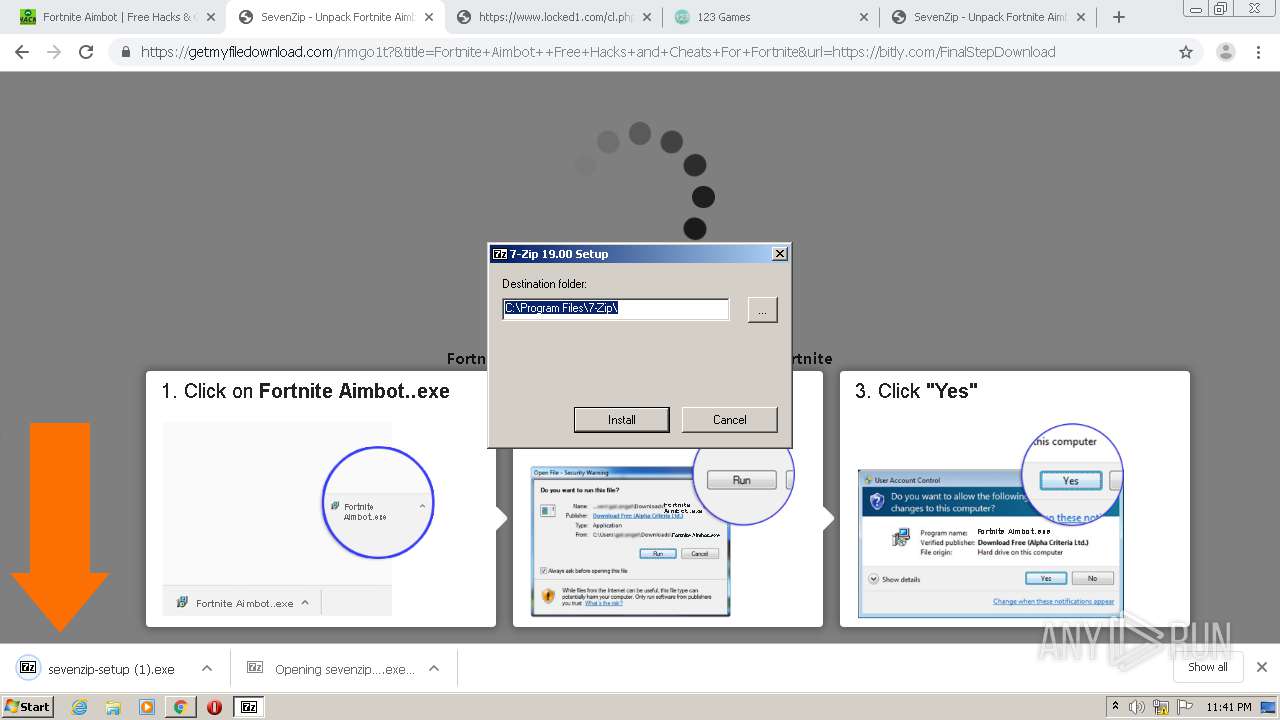
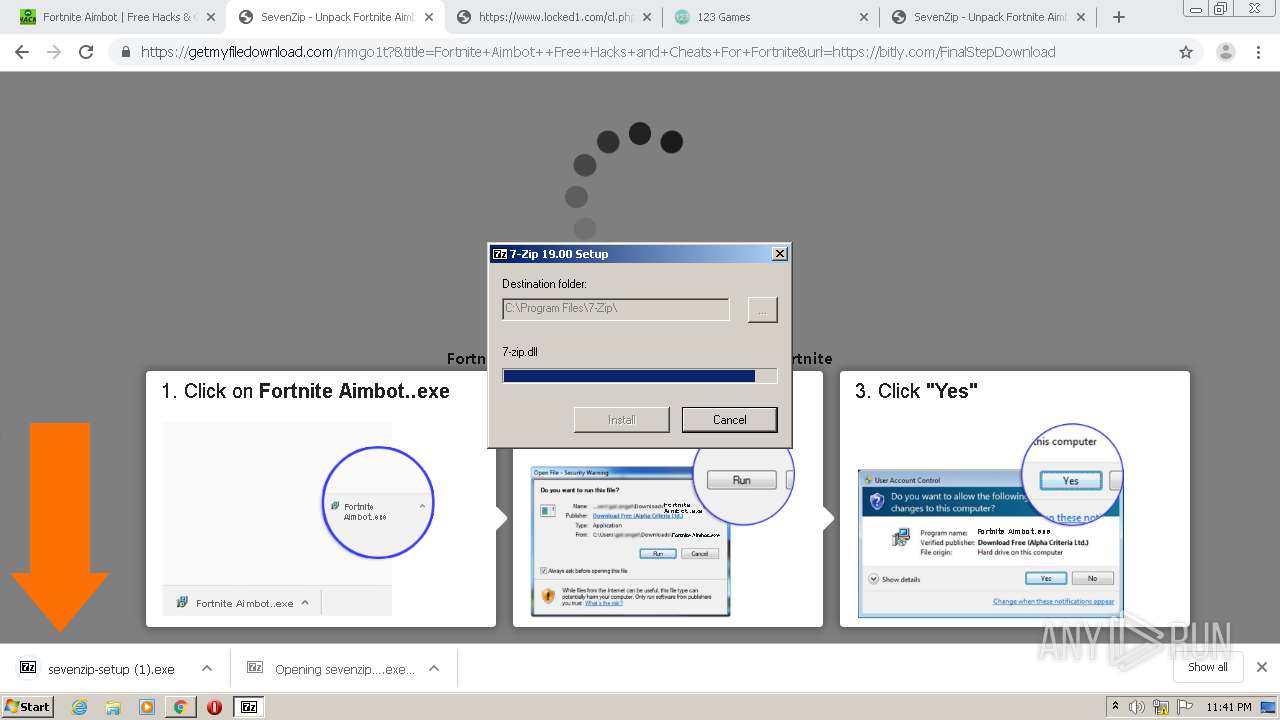
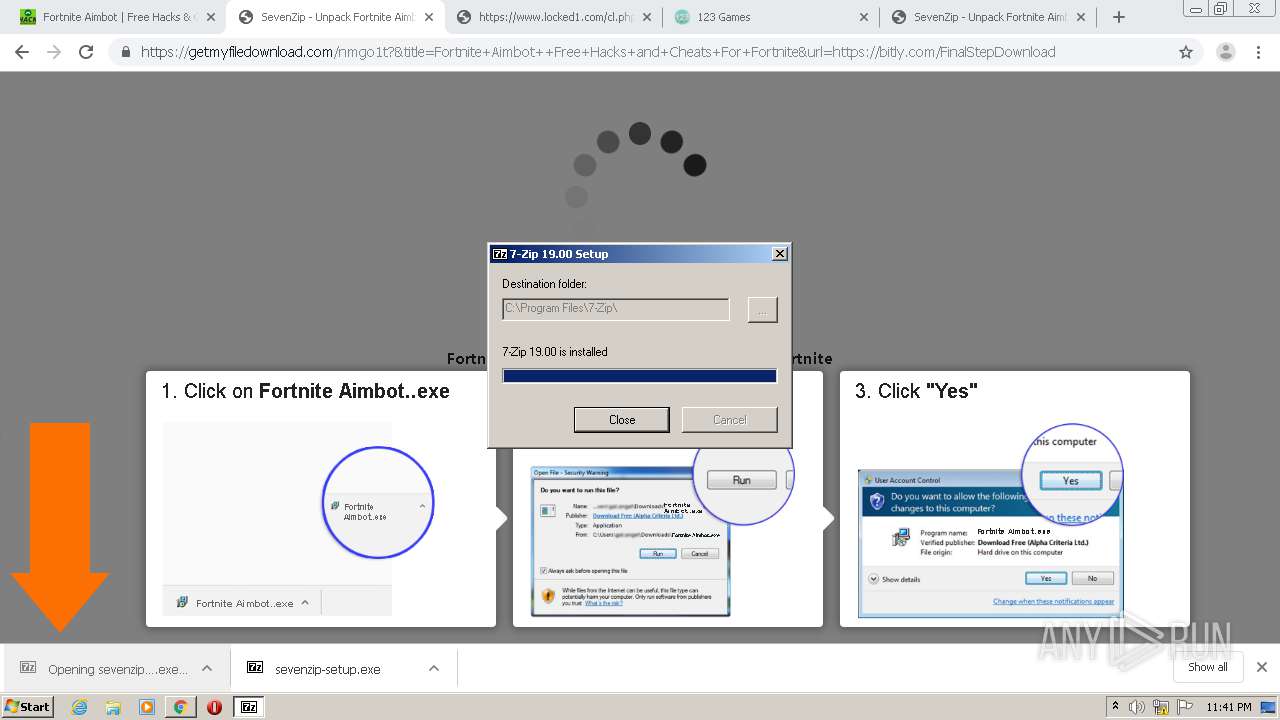
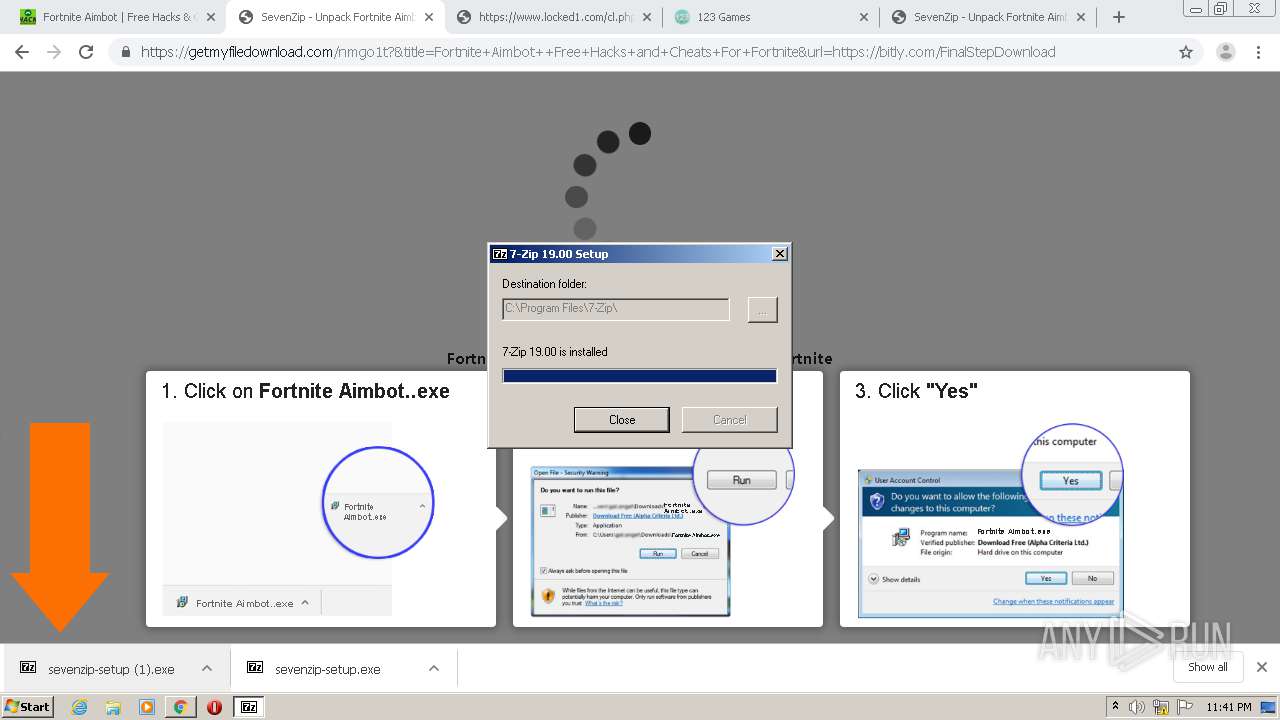
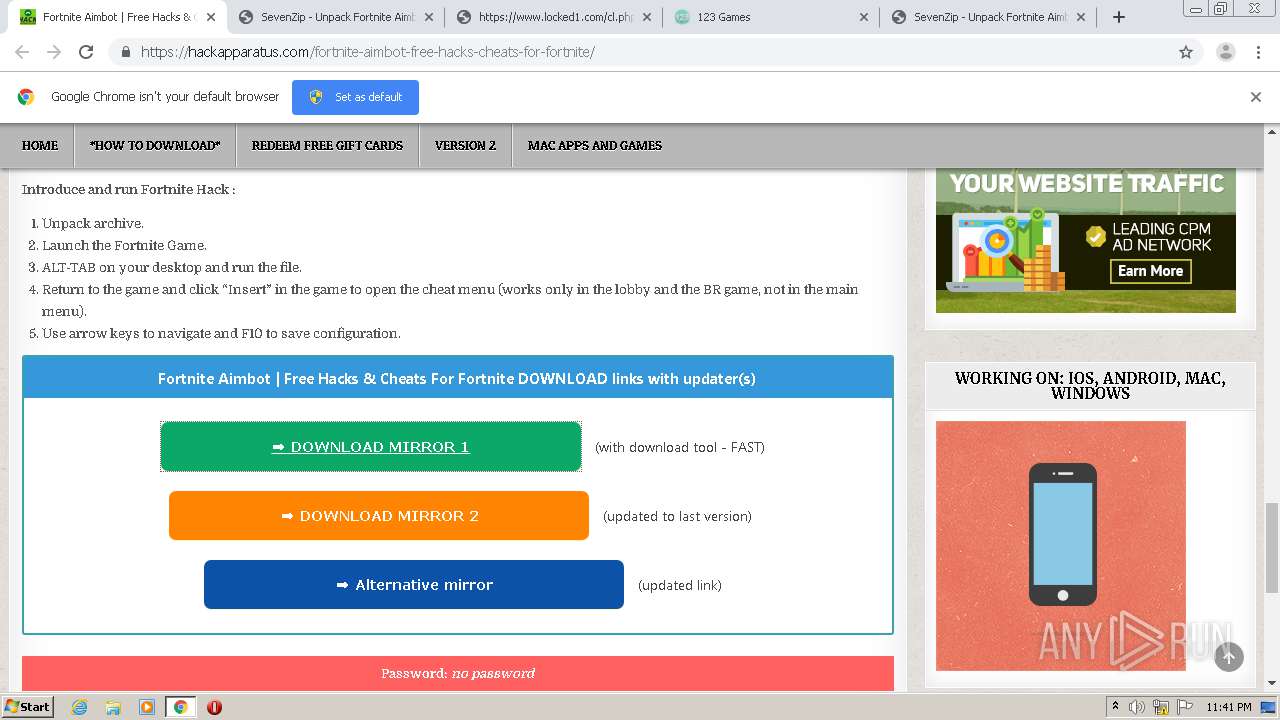
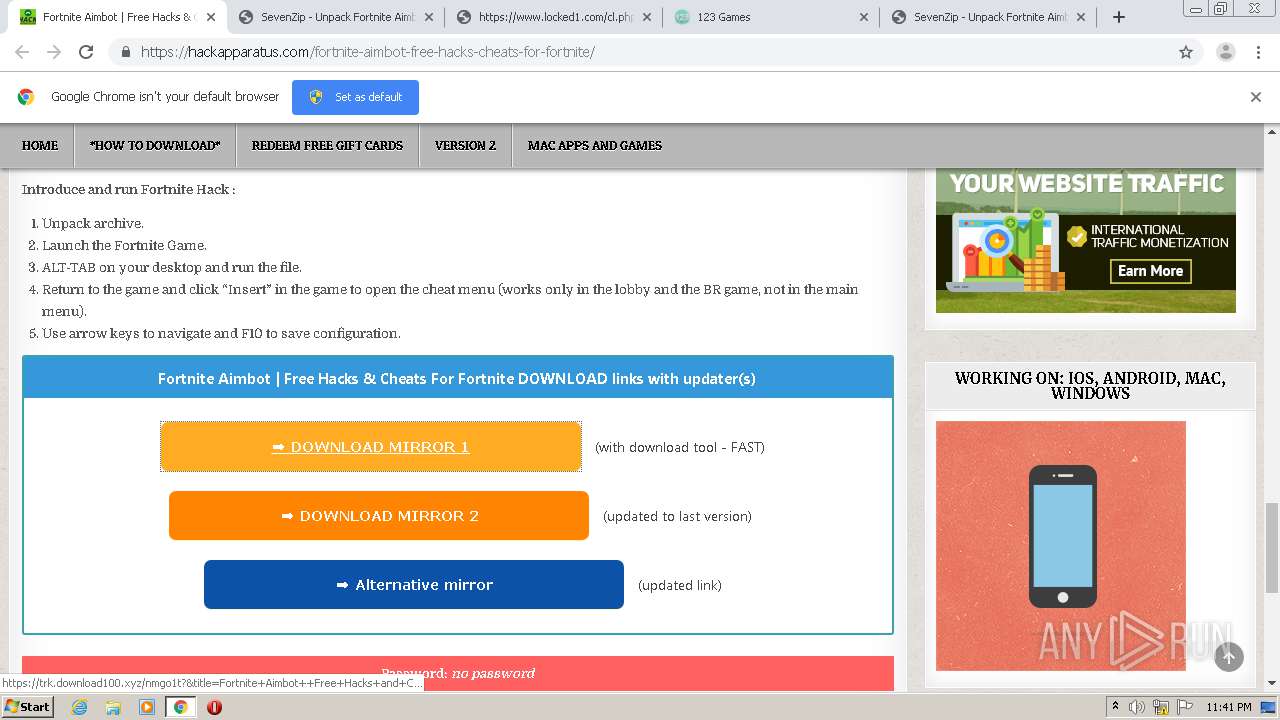
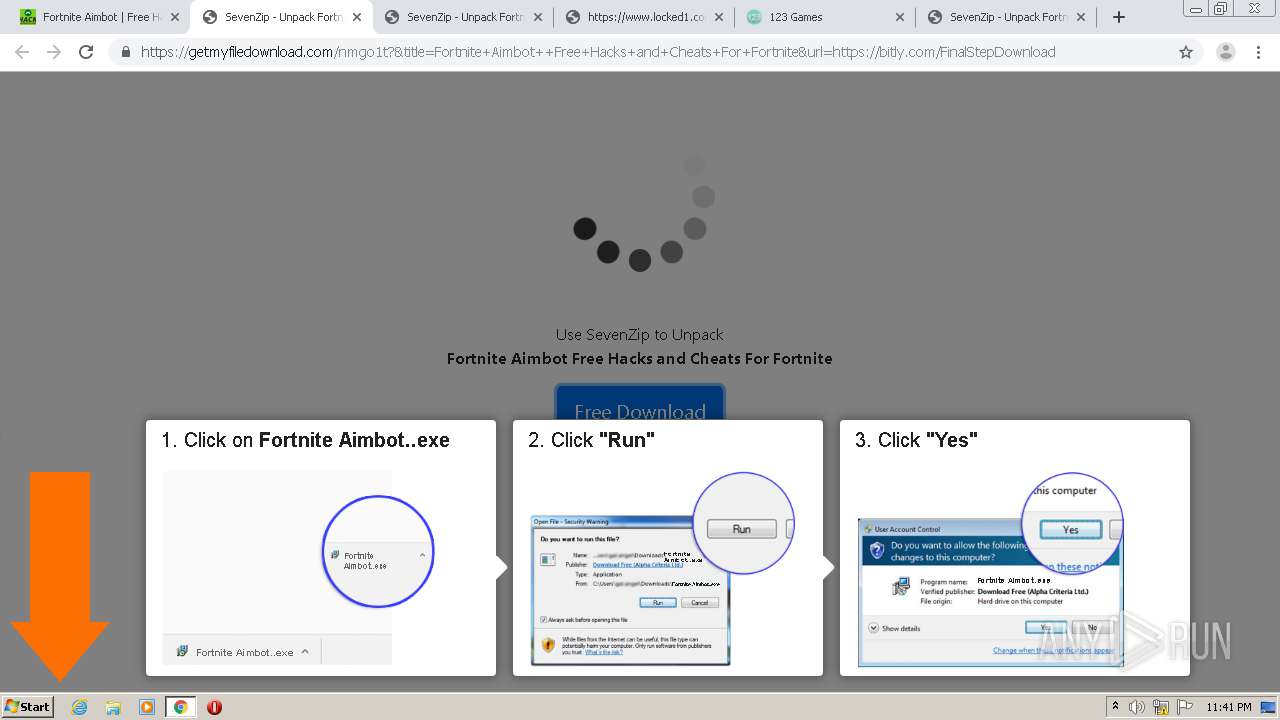
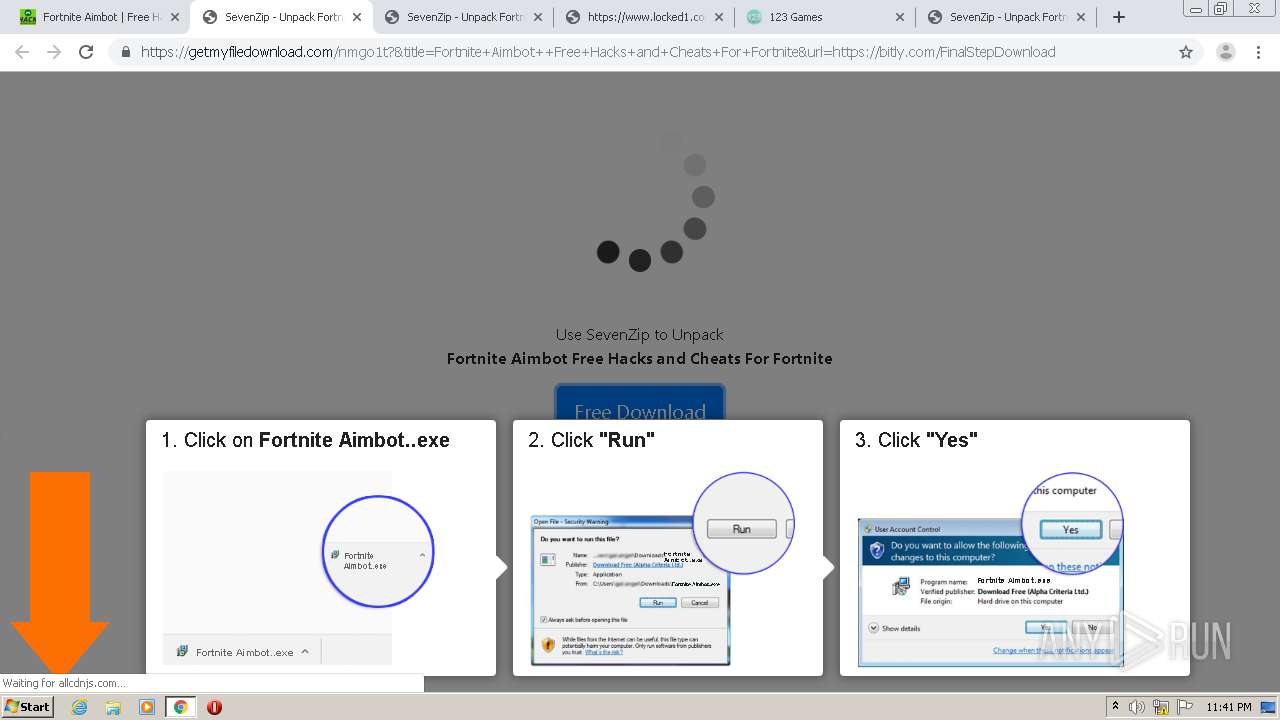
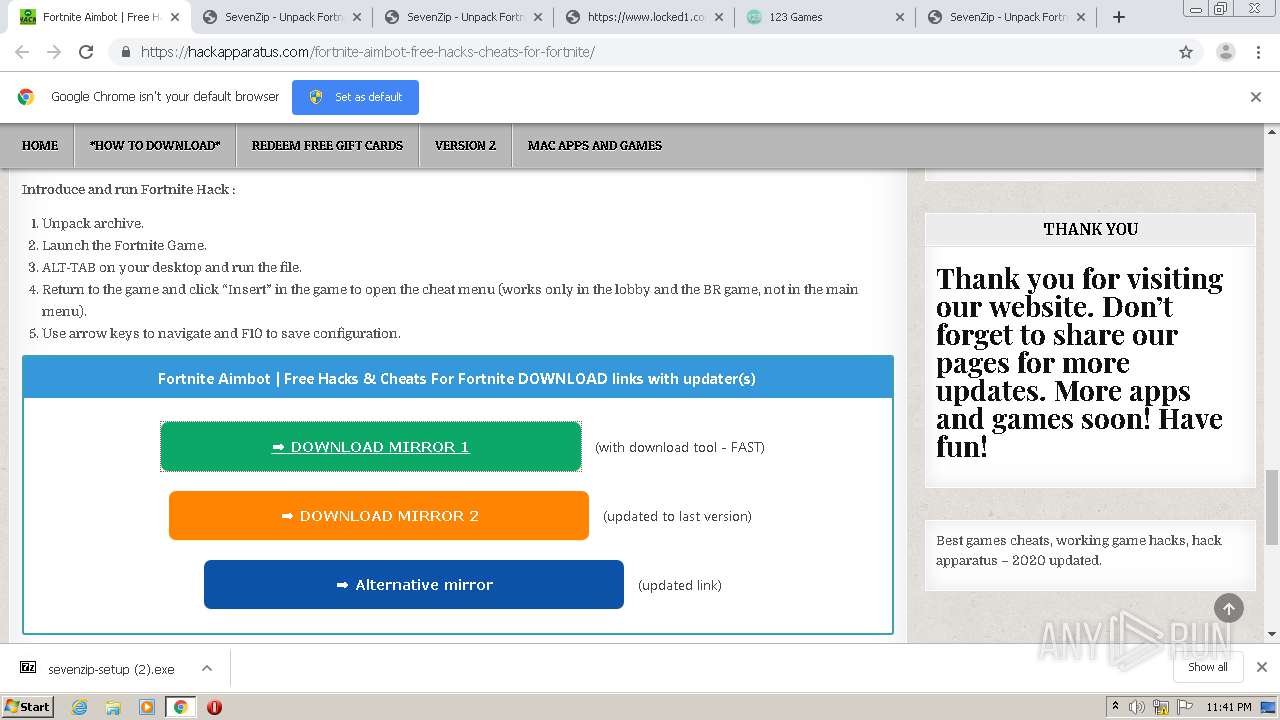
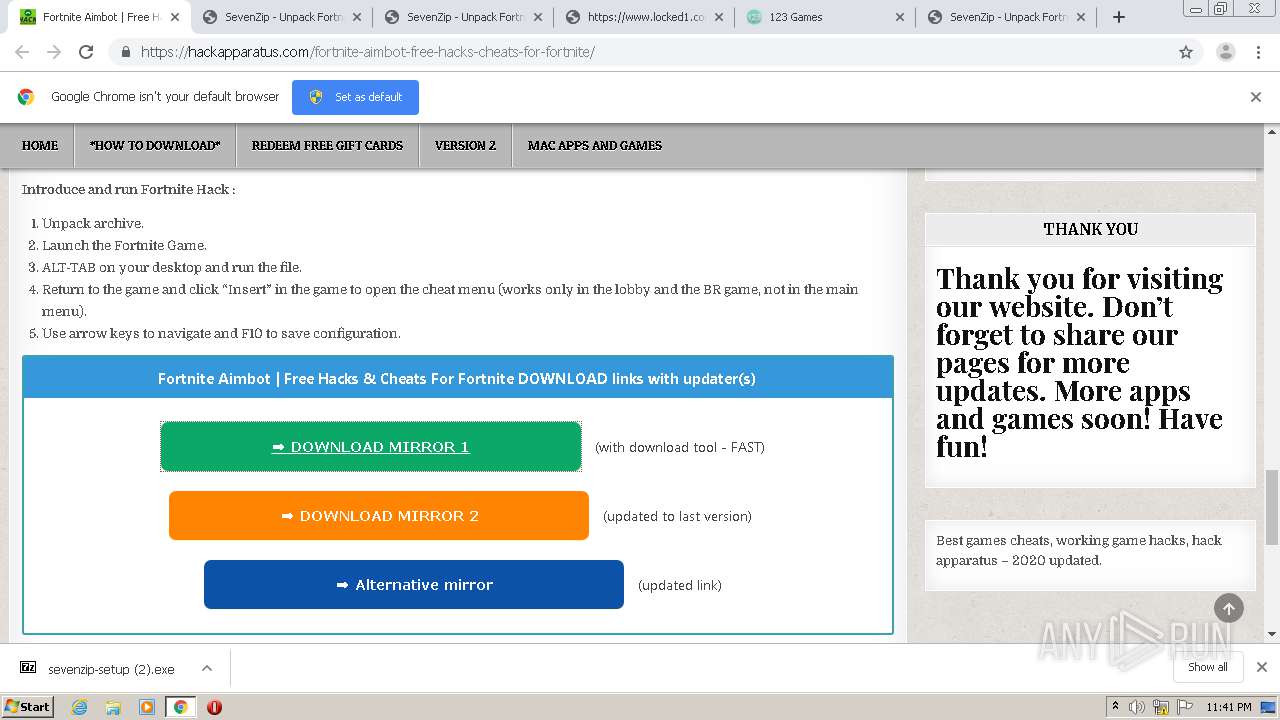
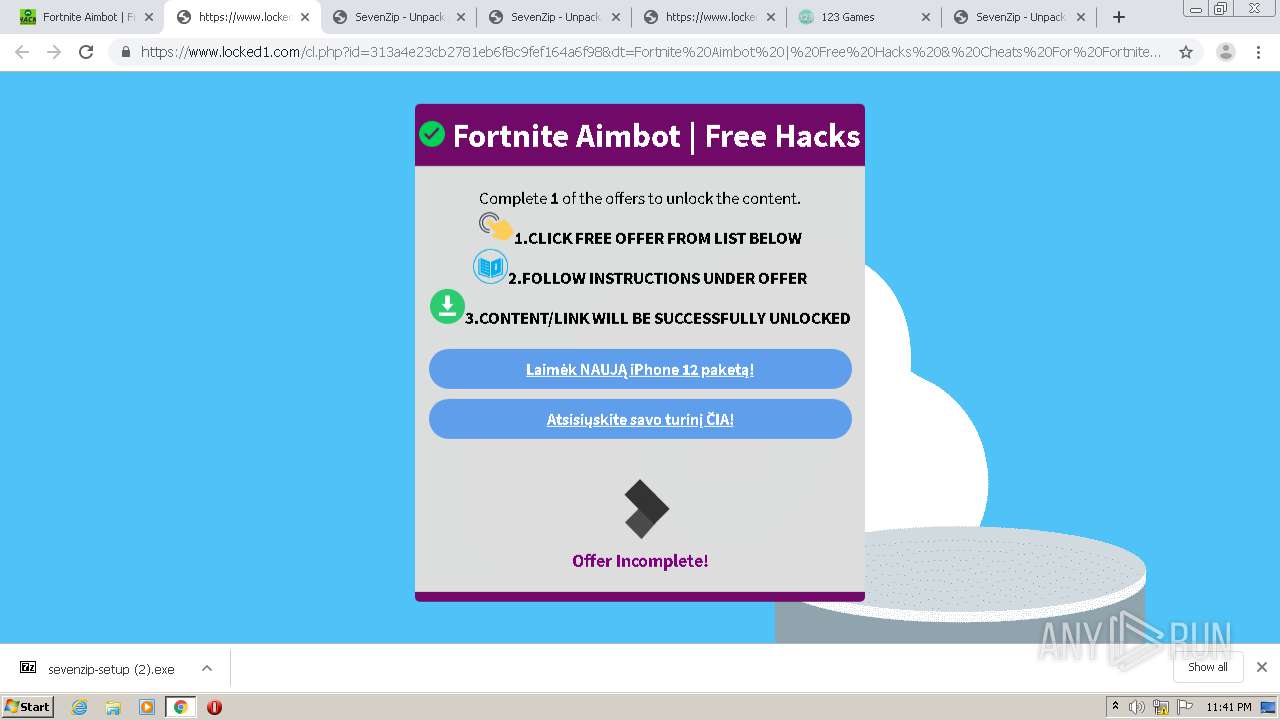
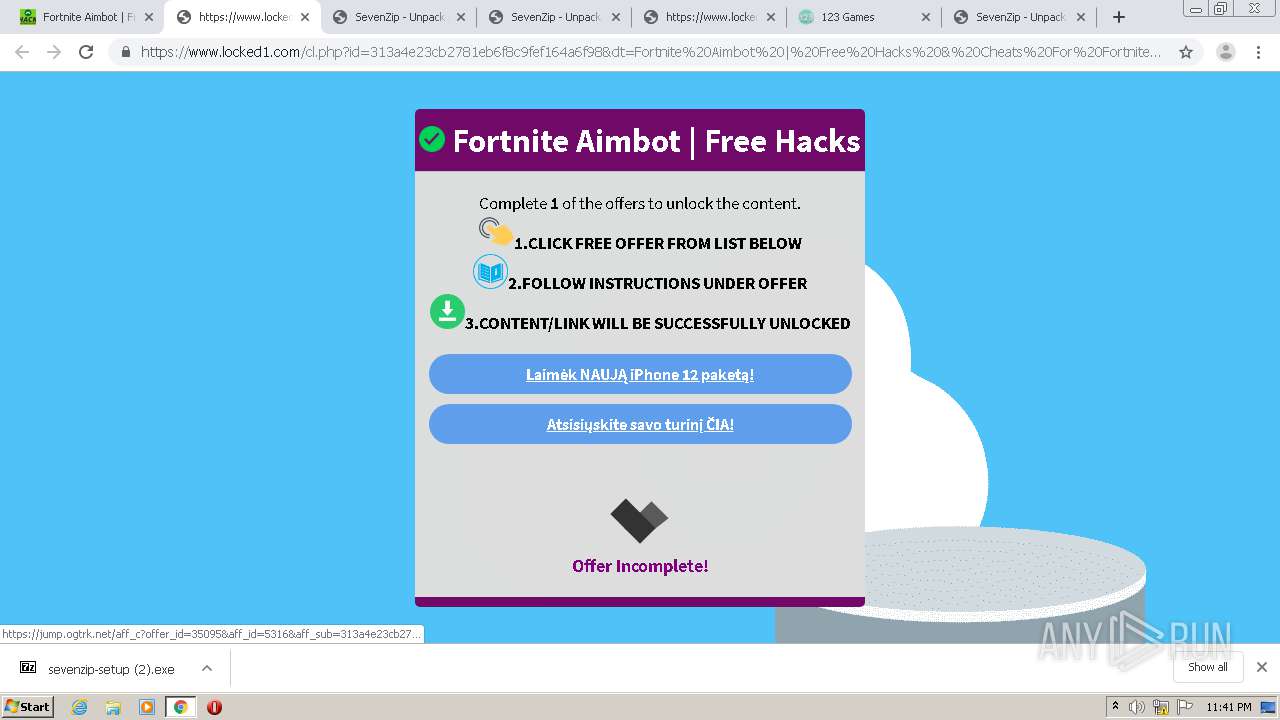
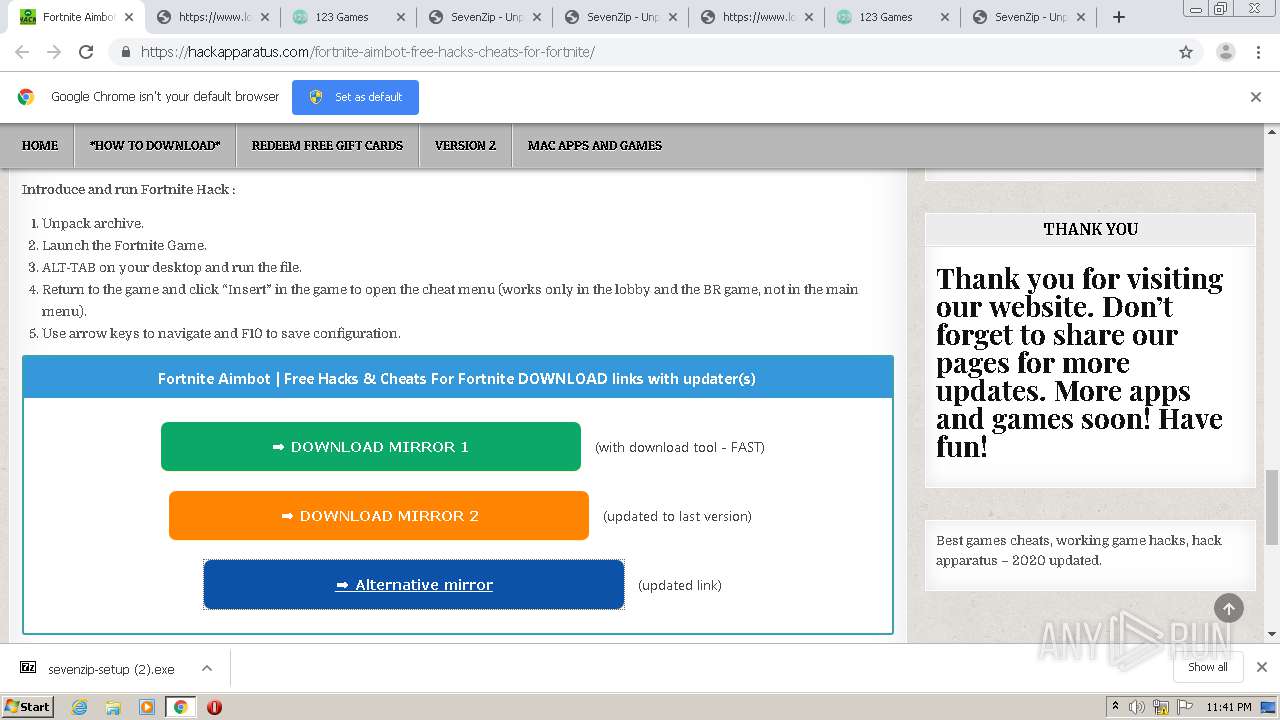
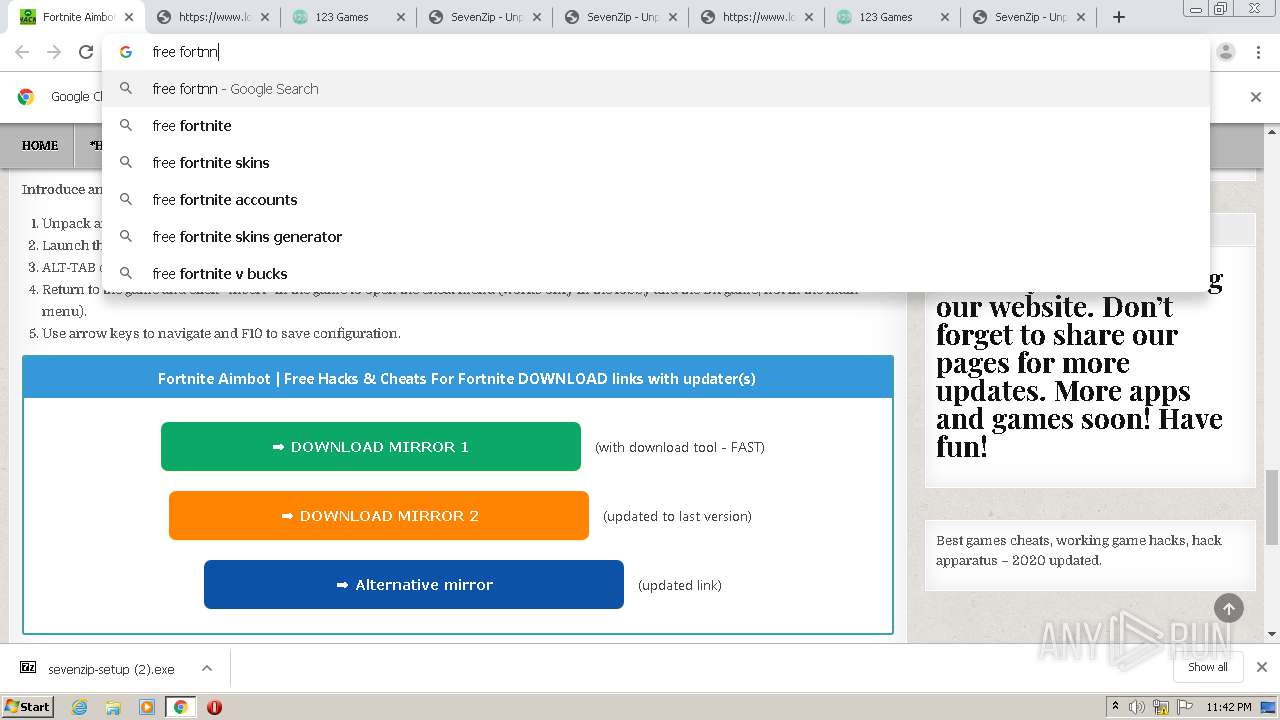
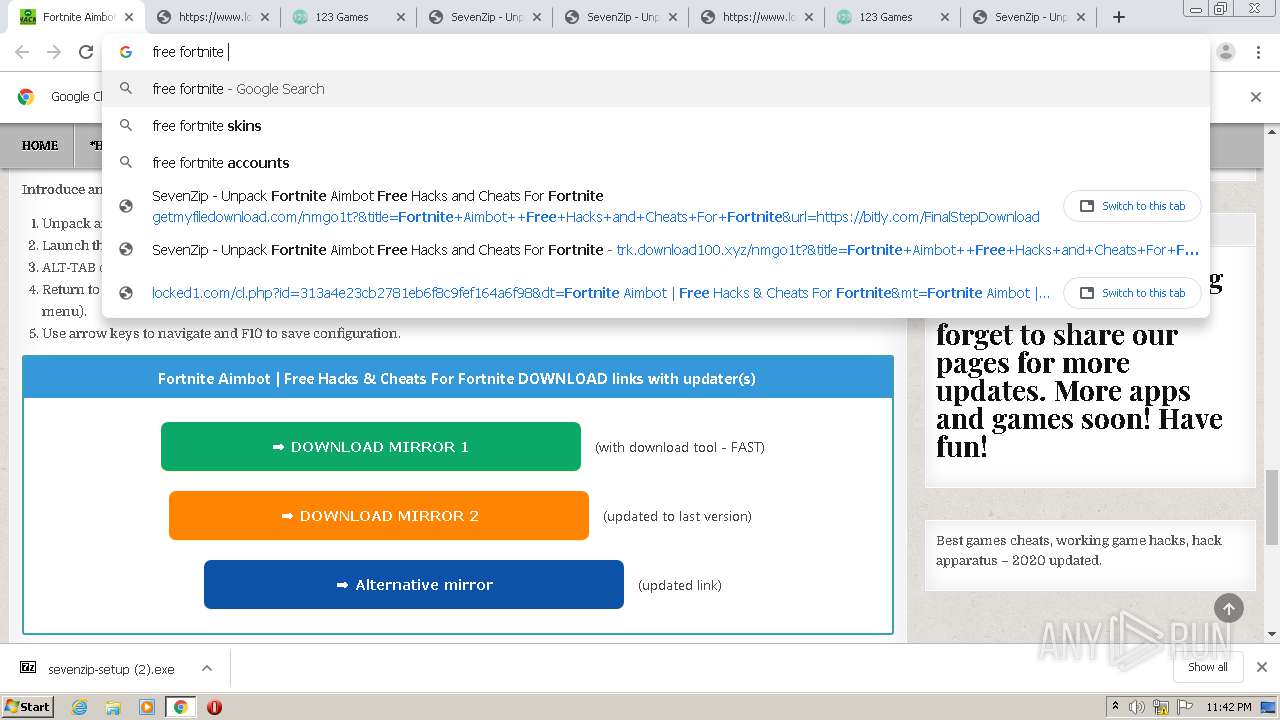
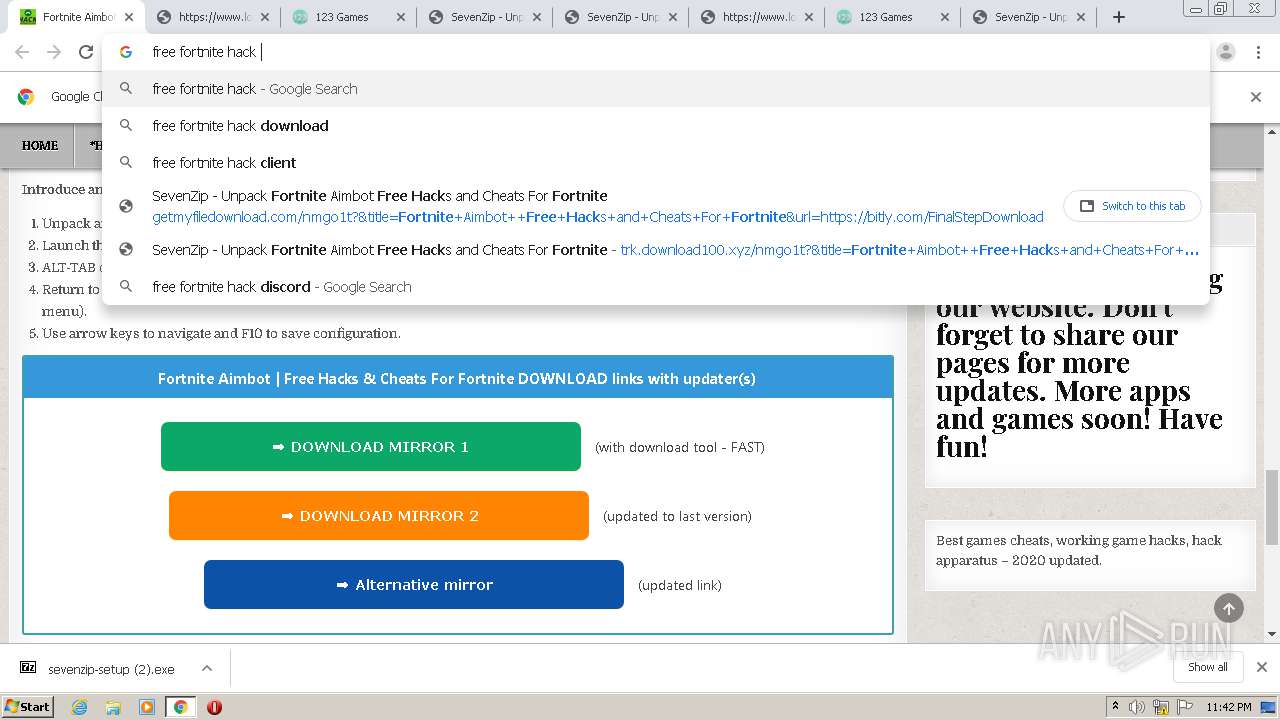
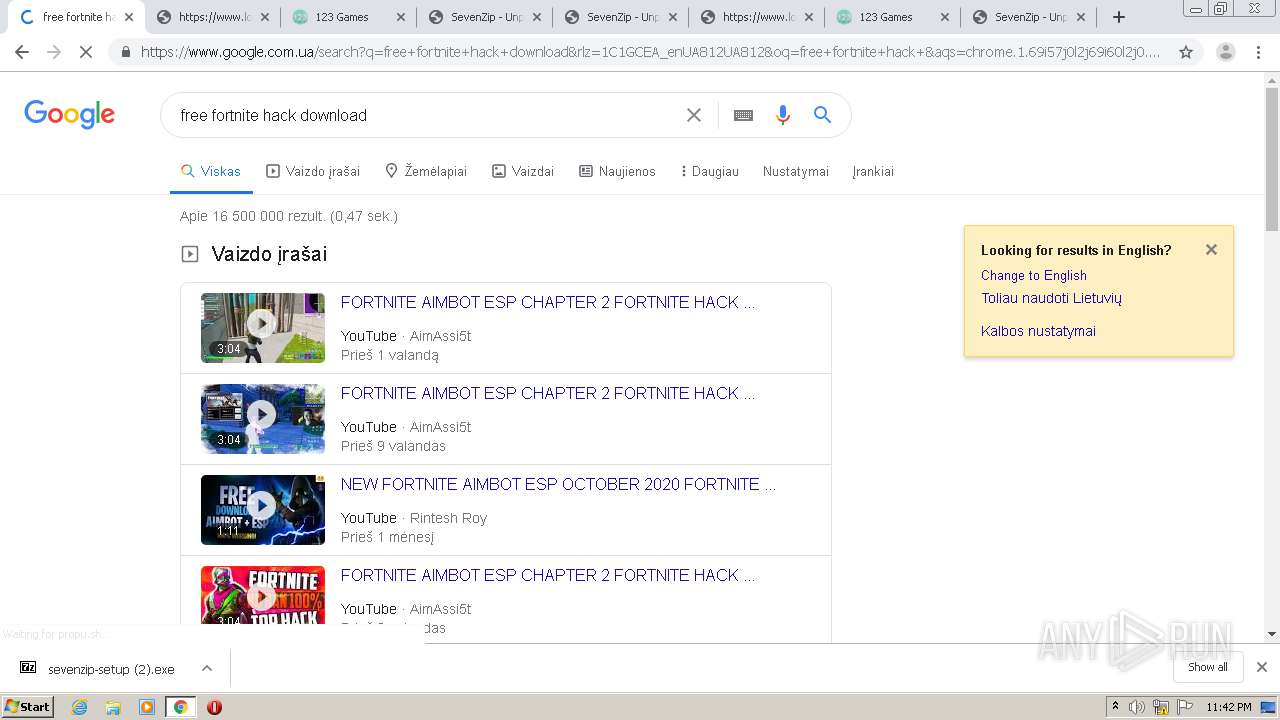
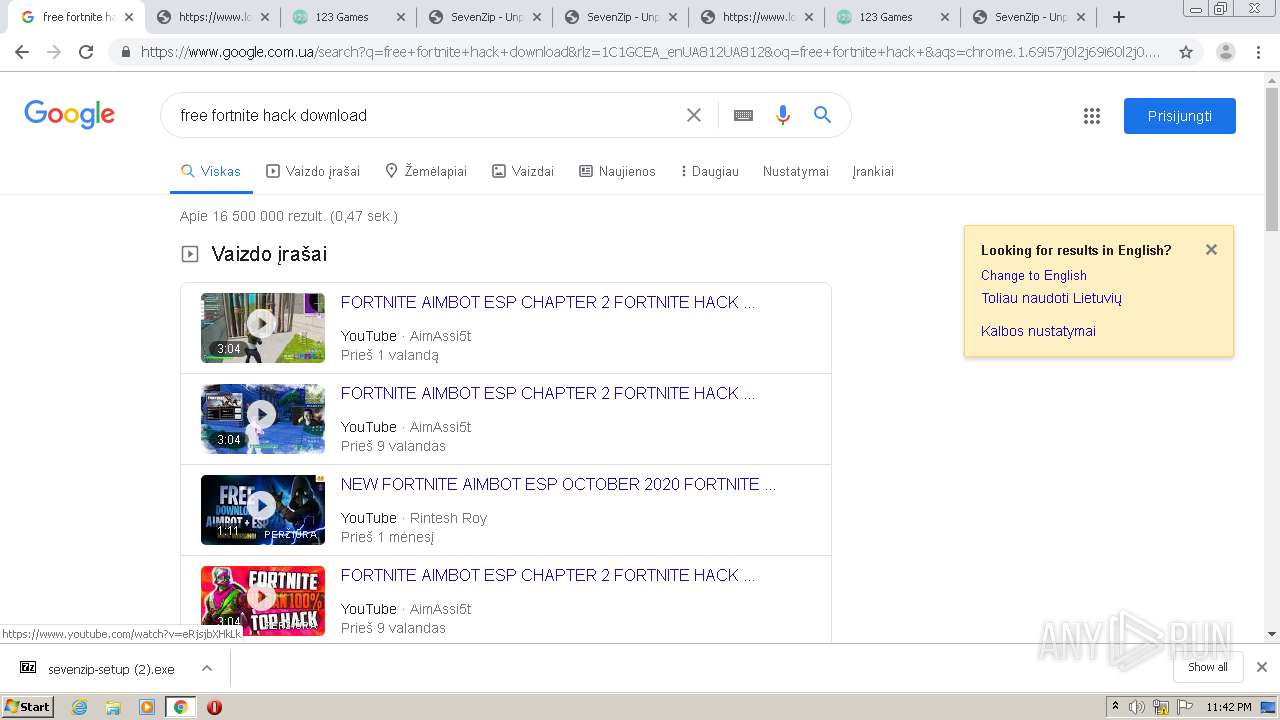
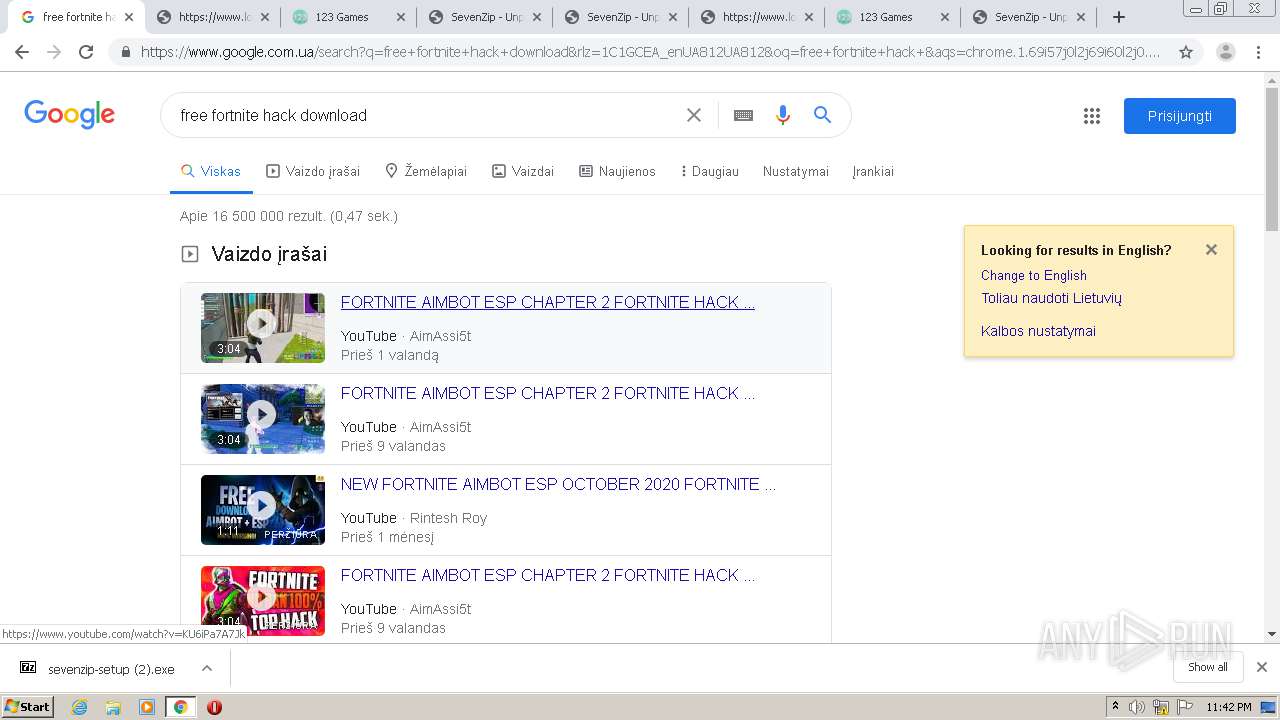
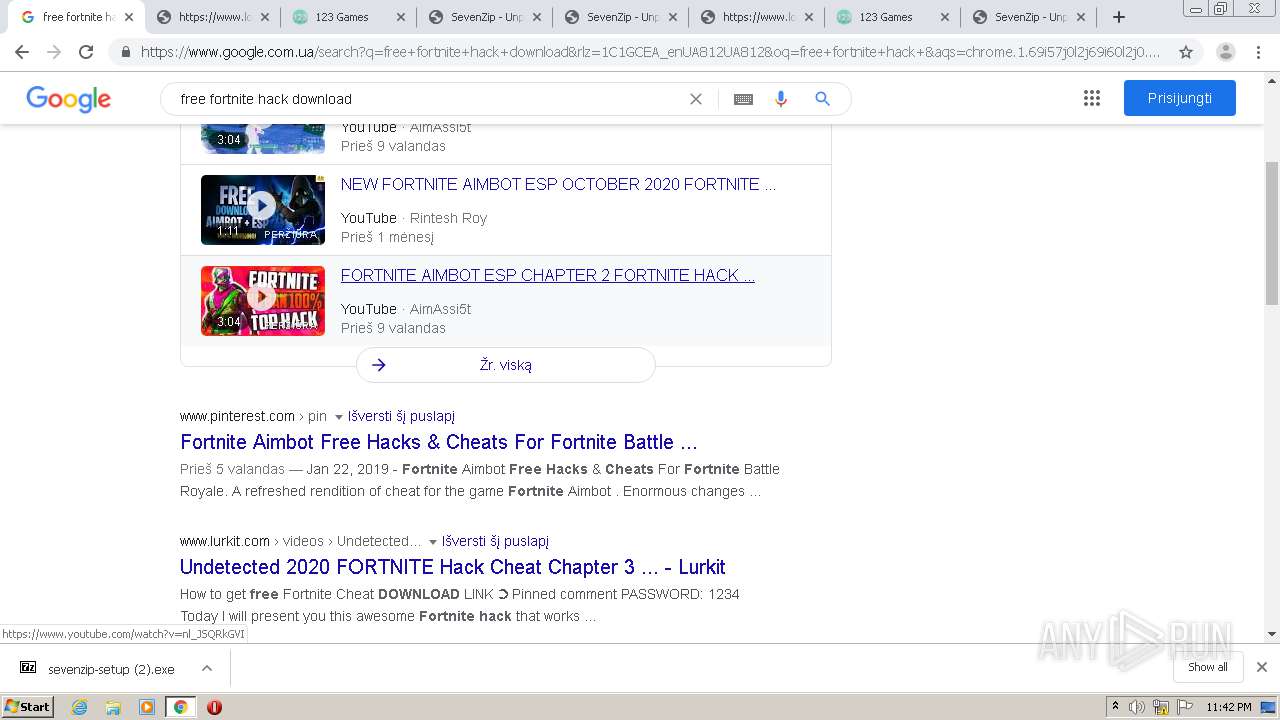
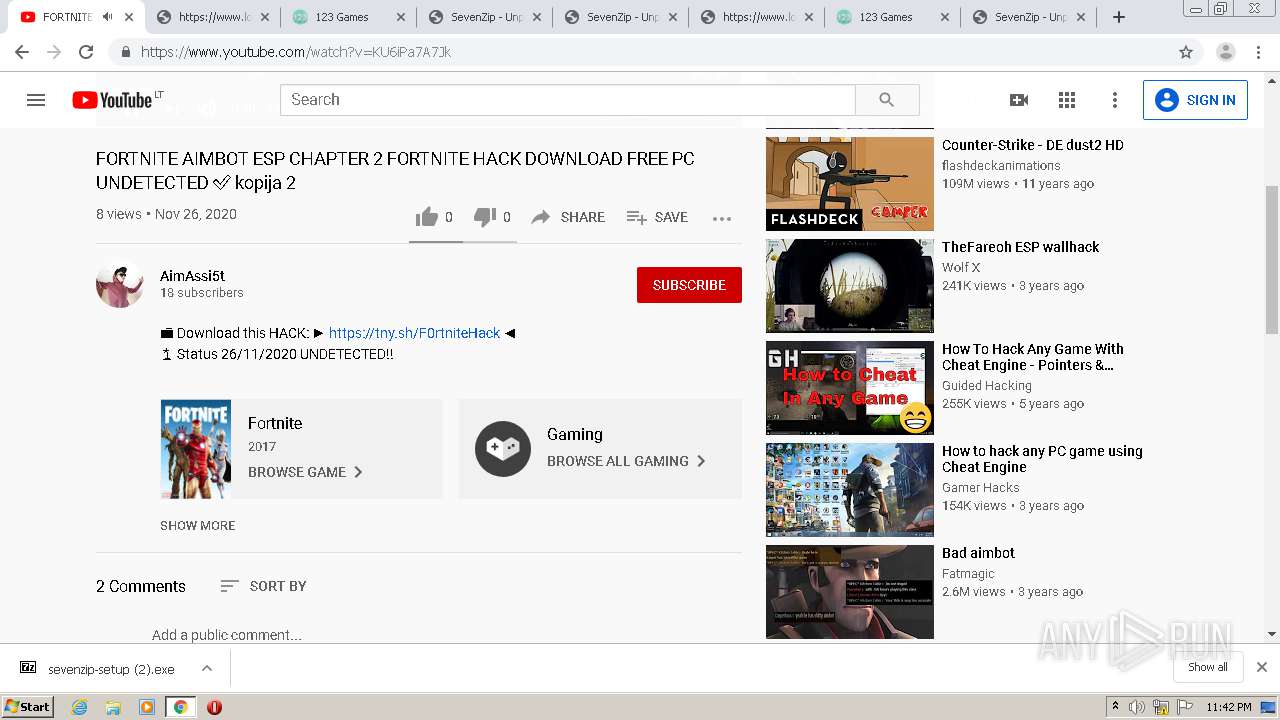
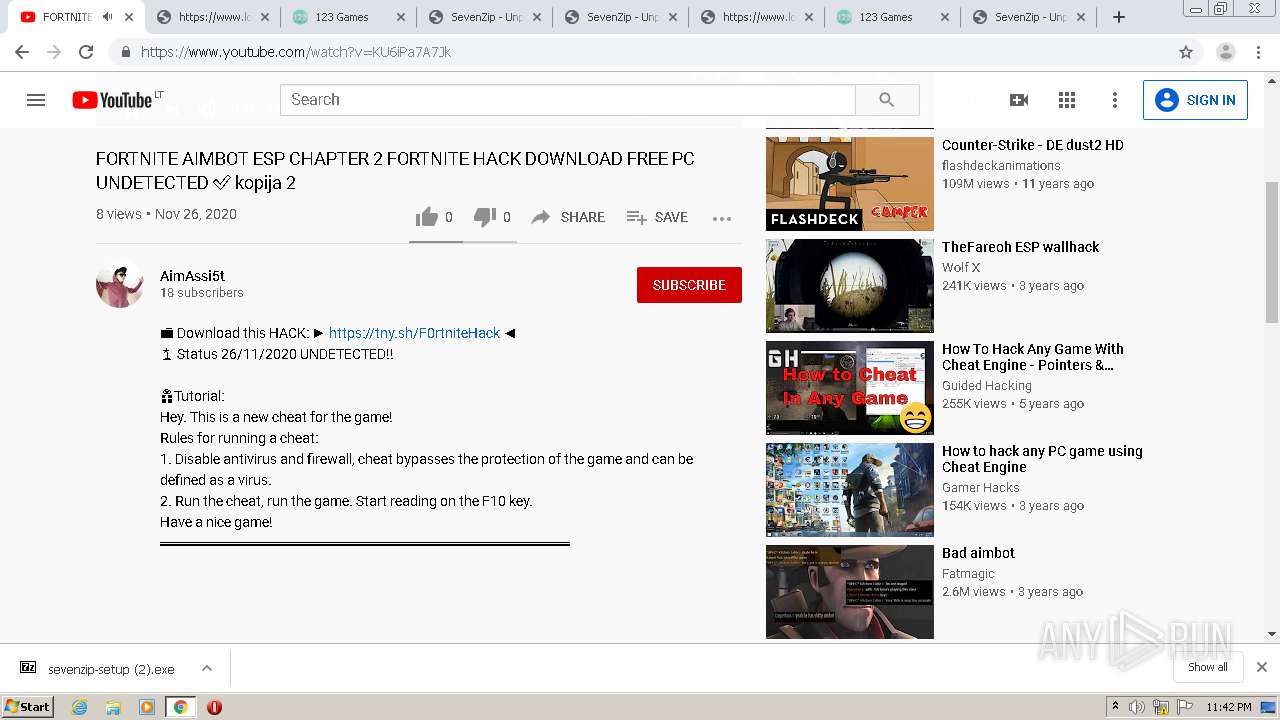
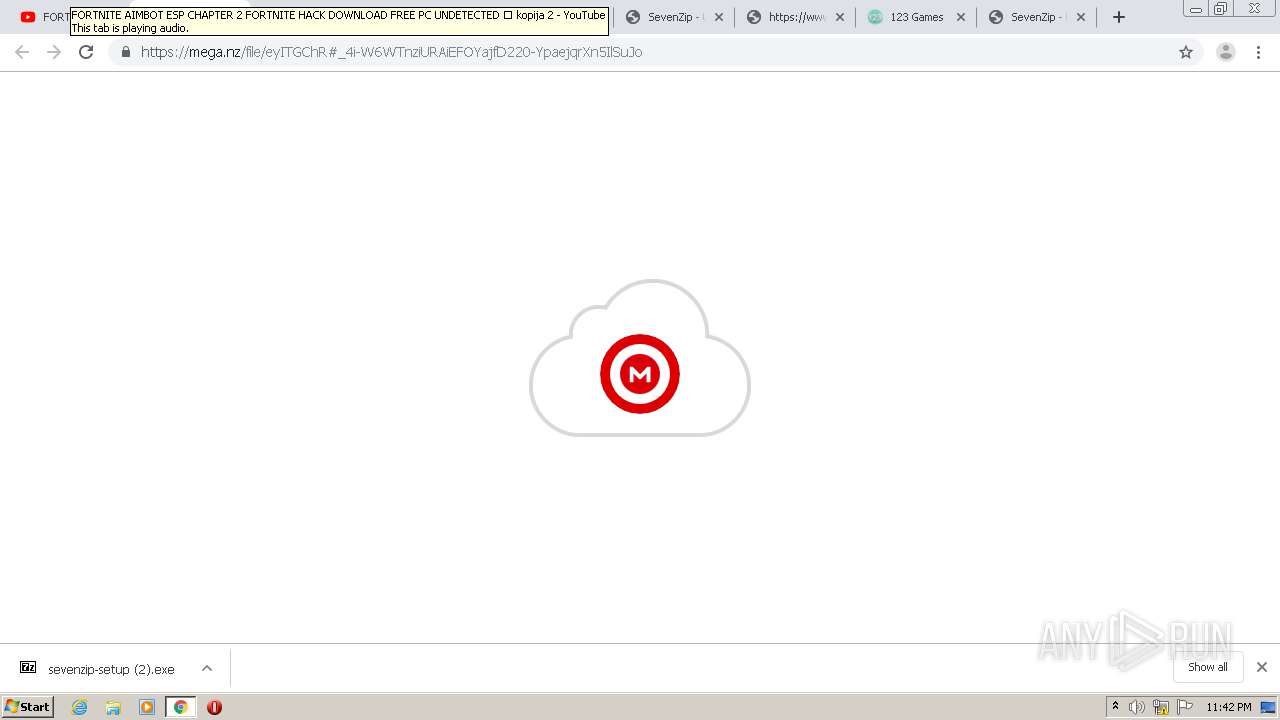
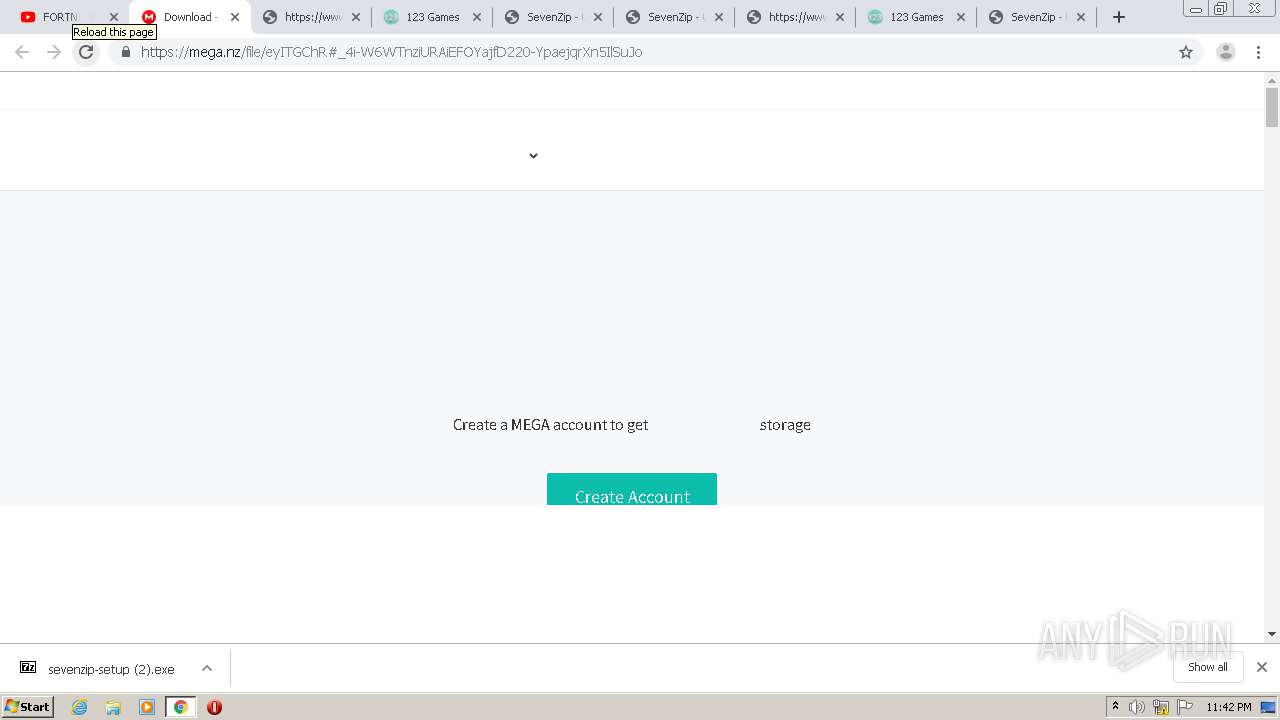
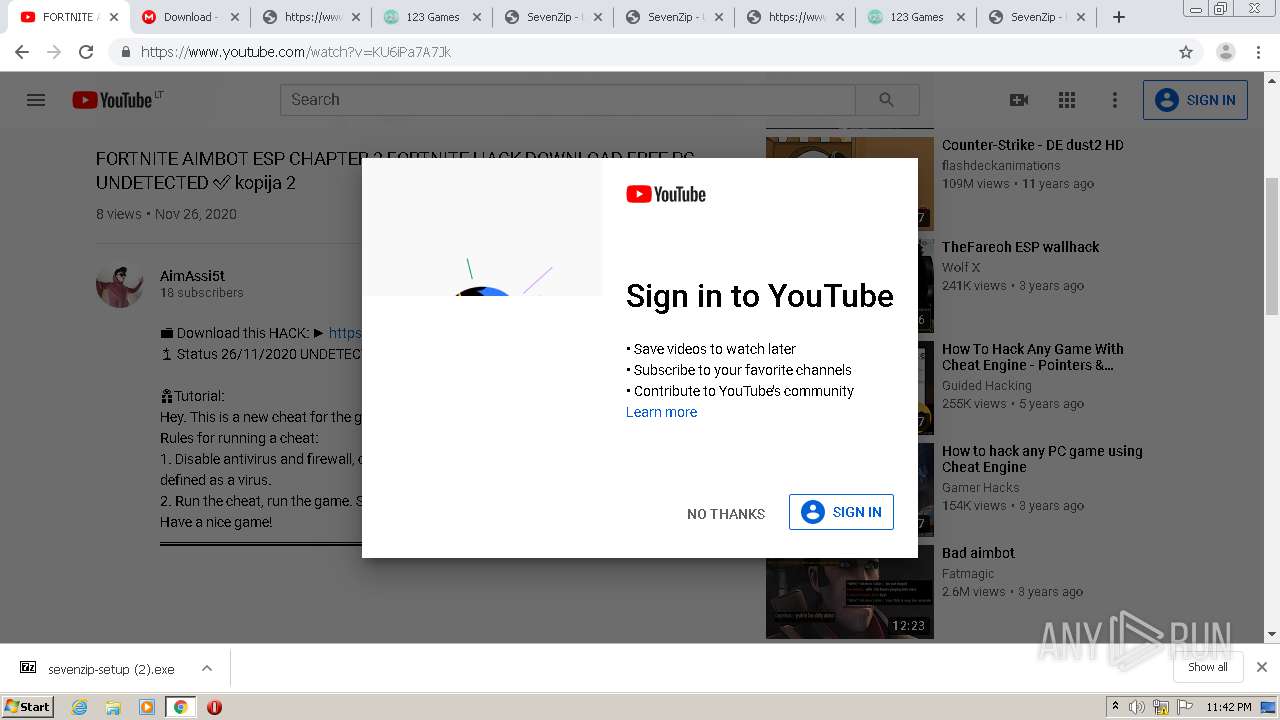
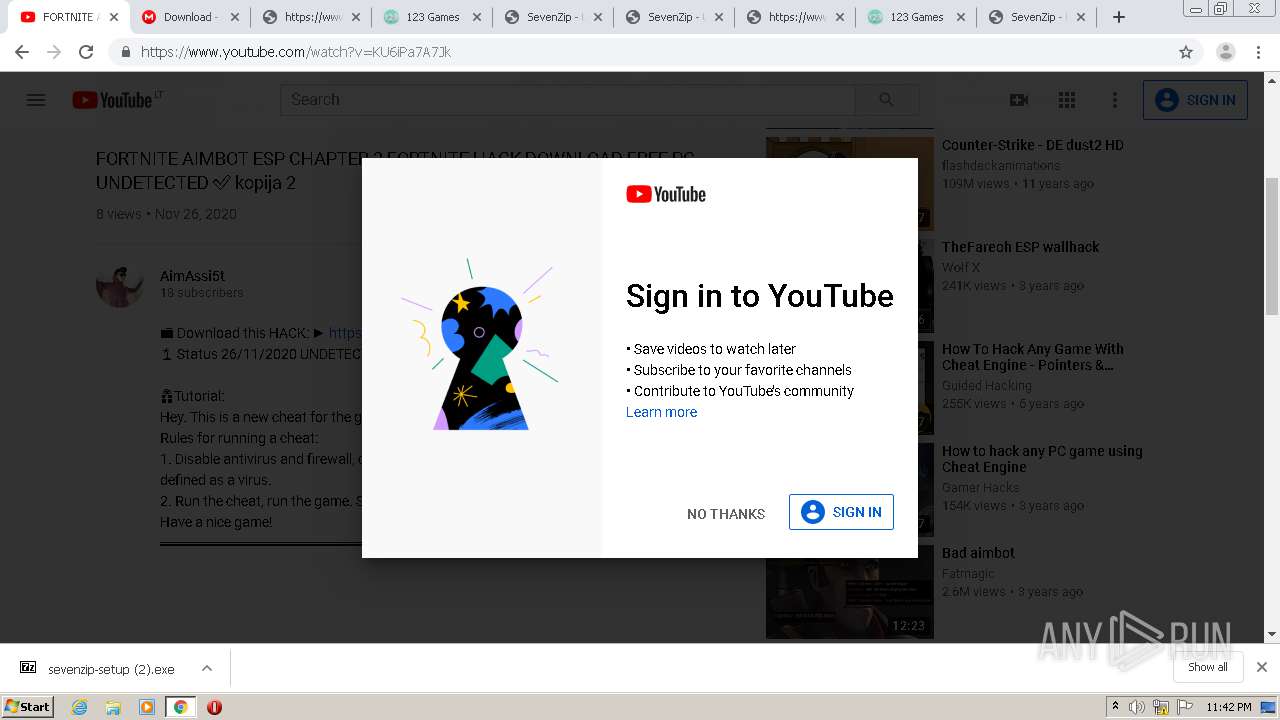
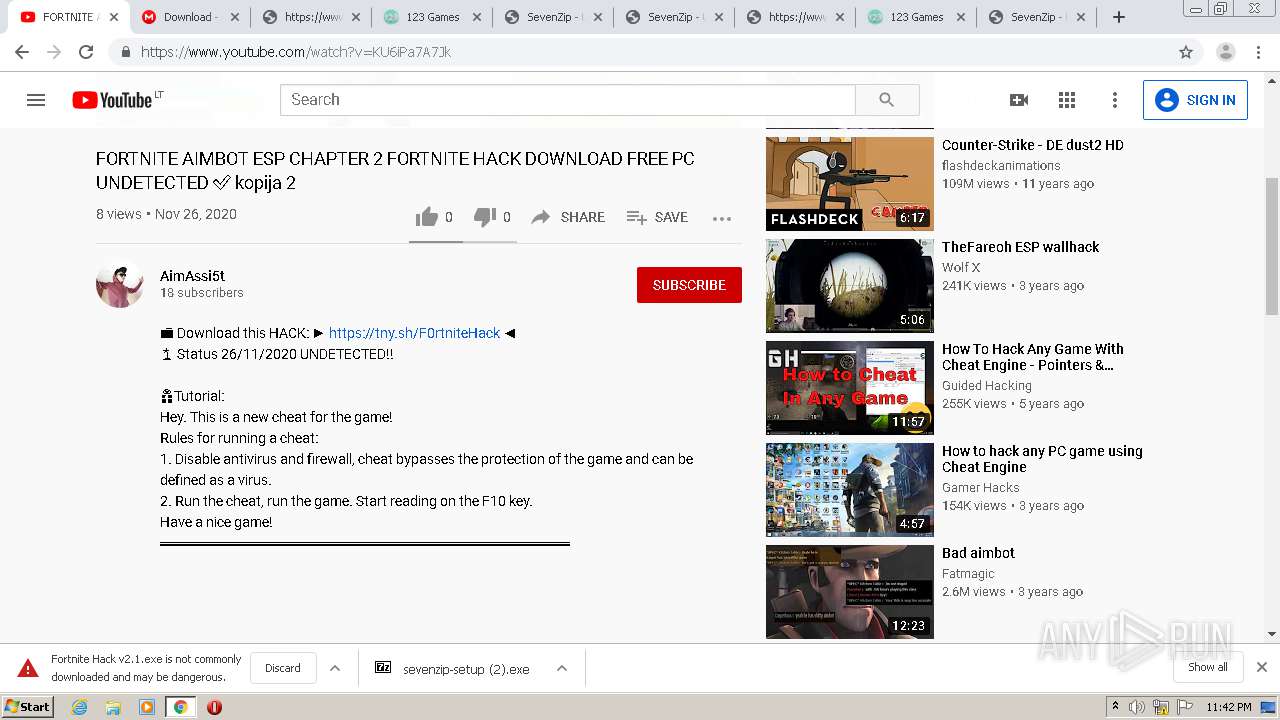
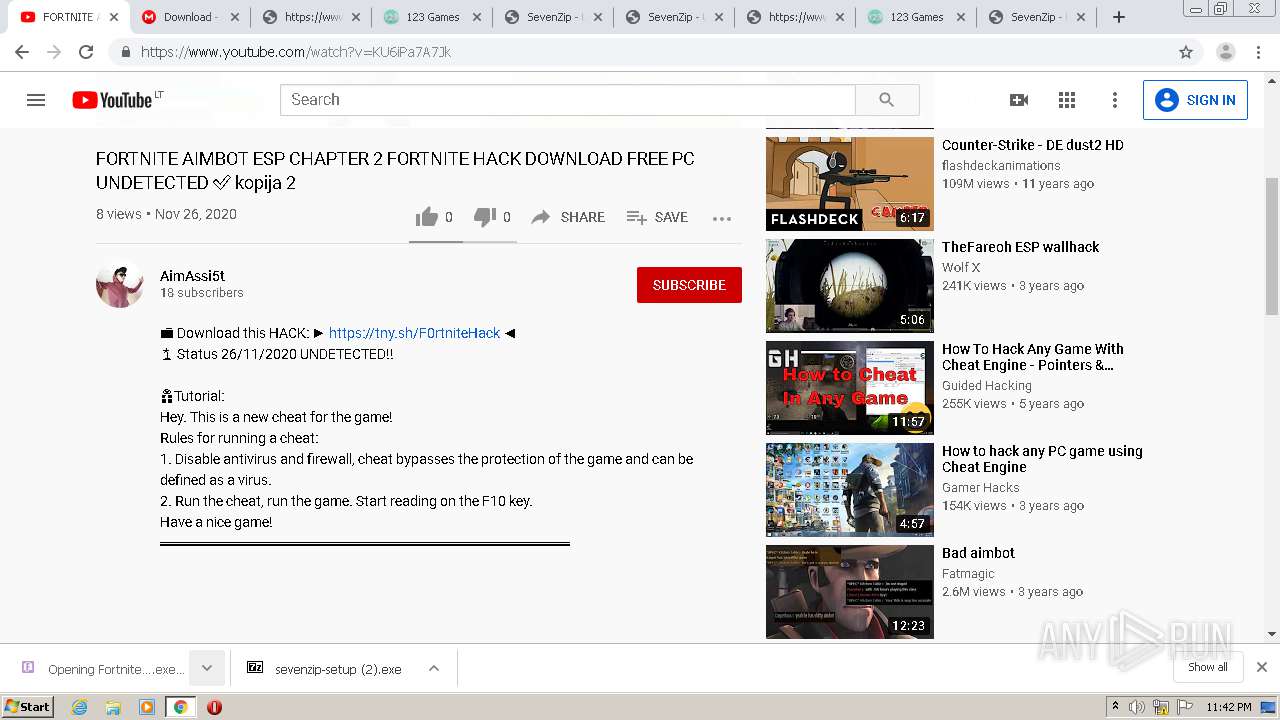
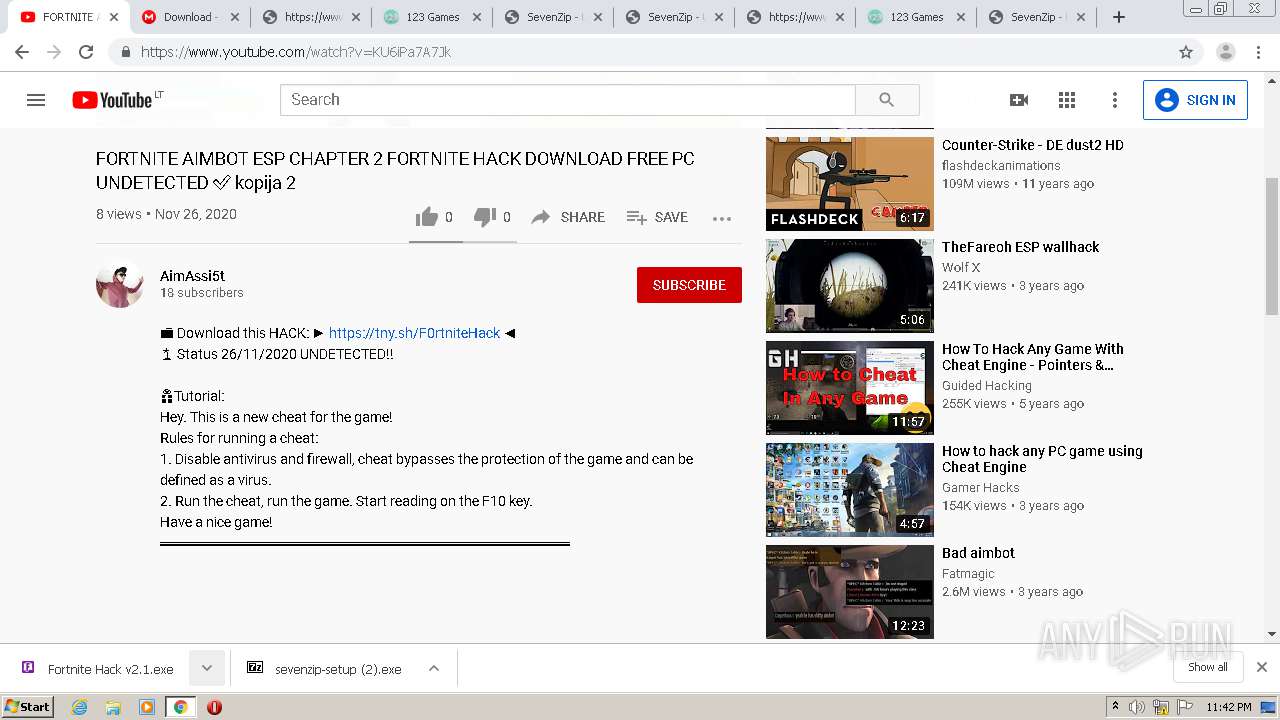
| URL: | https://hackapparatus.com/fortnite-aimbot-free-hacks-cheats-for-fortnite/ |
| Full analysis: | https://app.any.run/tasks/a61f7d34-0709-47d4-a608-bc7c1896a976 |
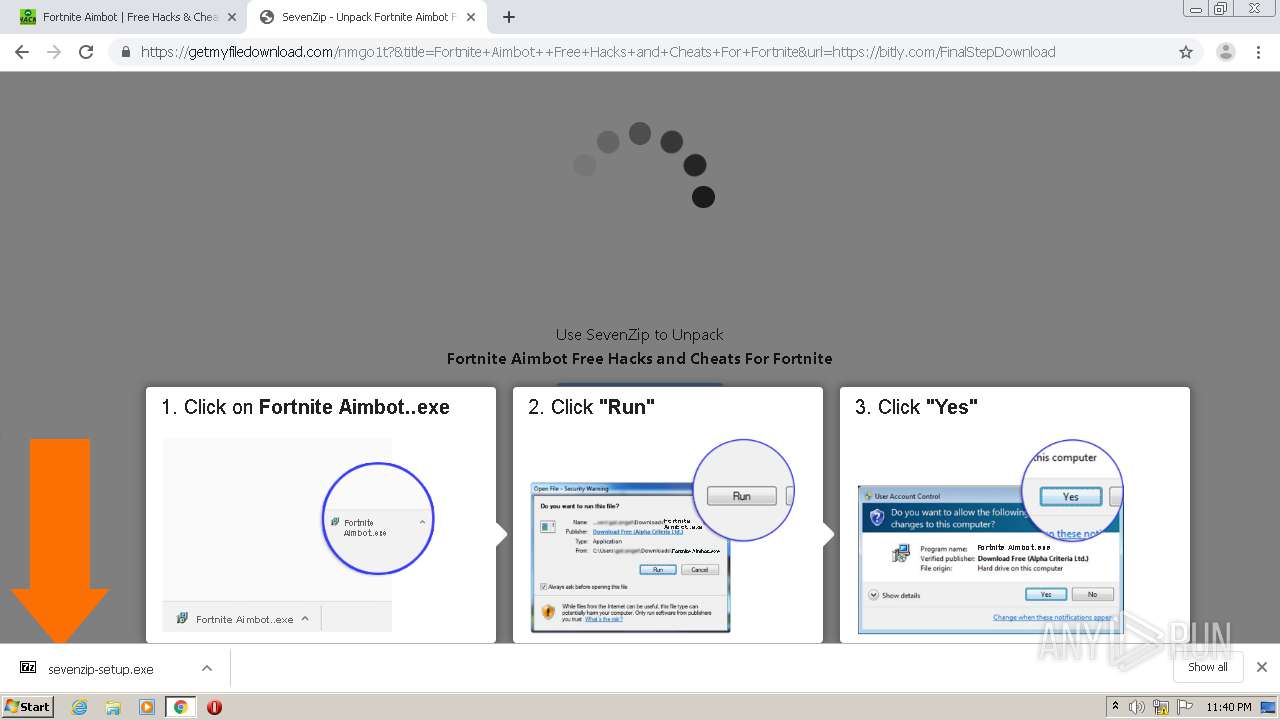
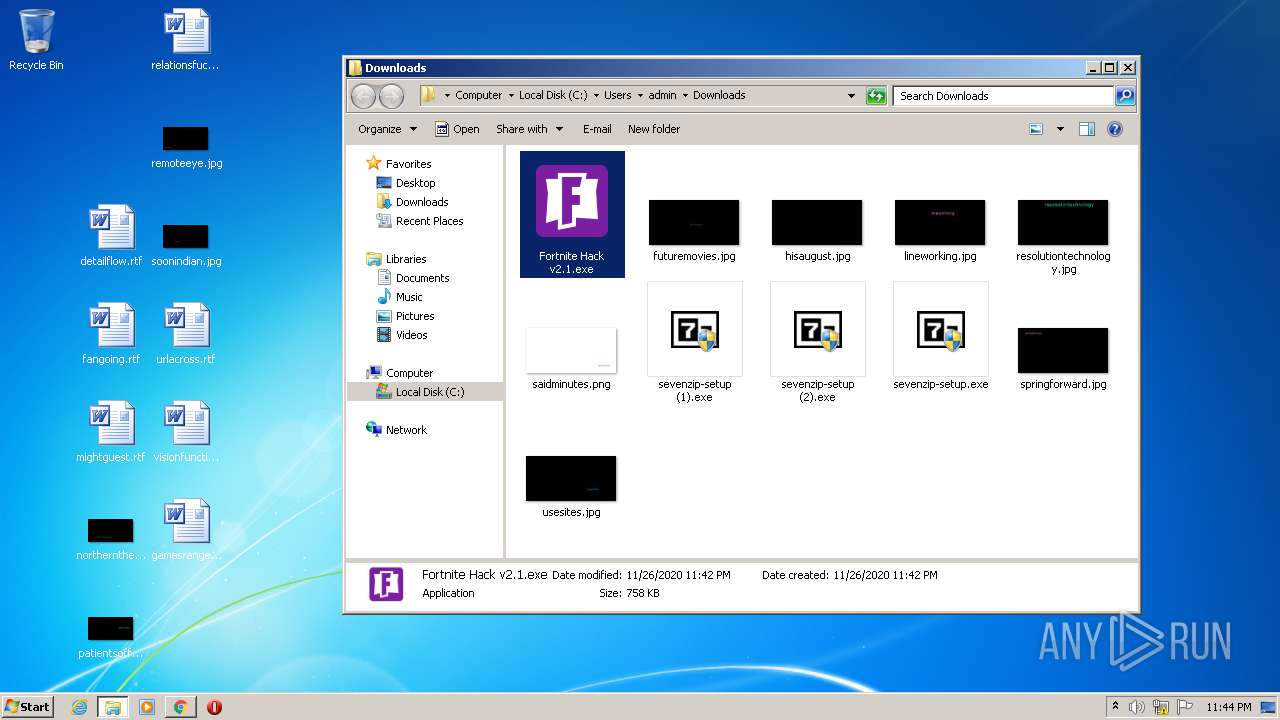
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
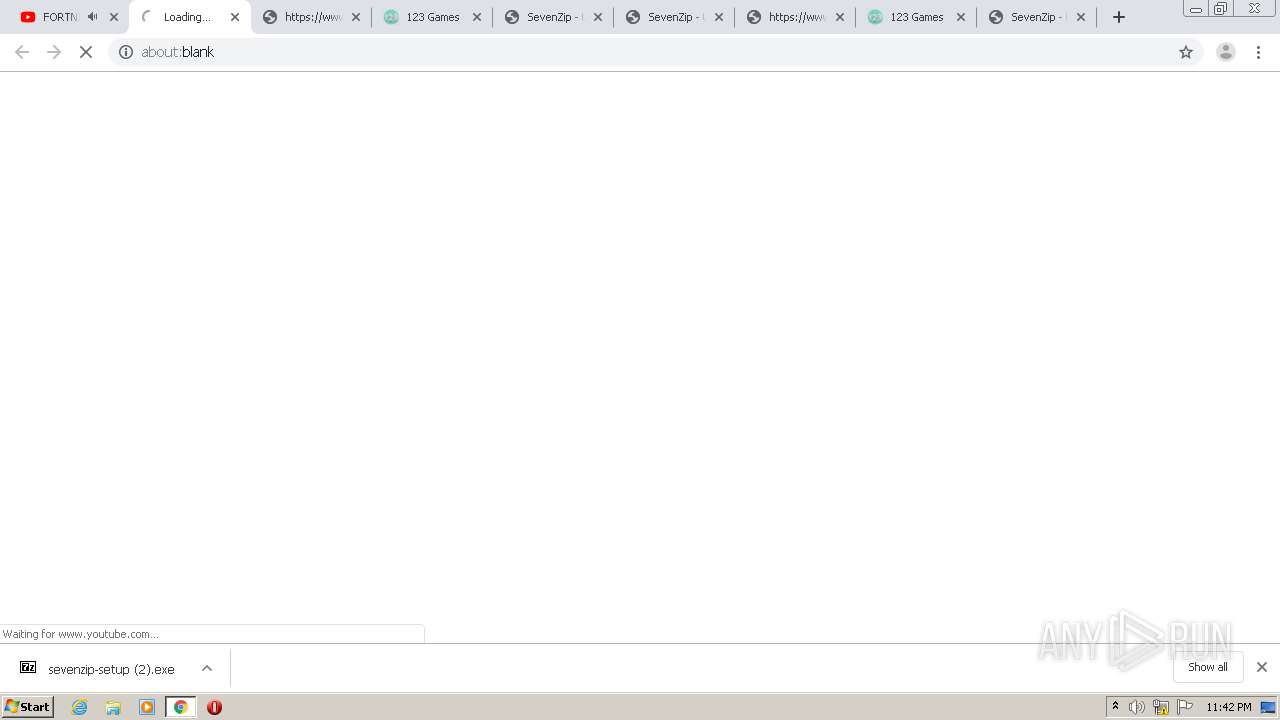
| Analysis date: | November 26, 2020, 23:39:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
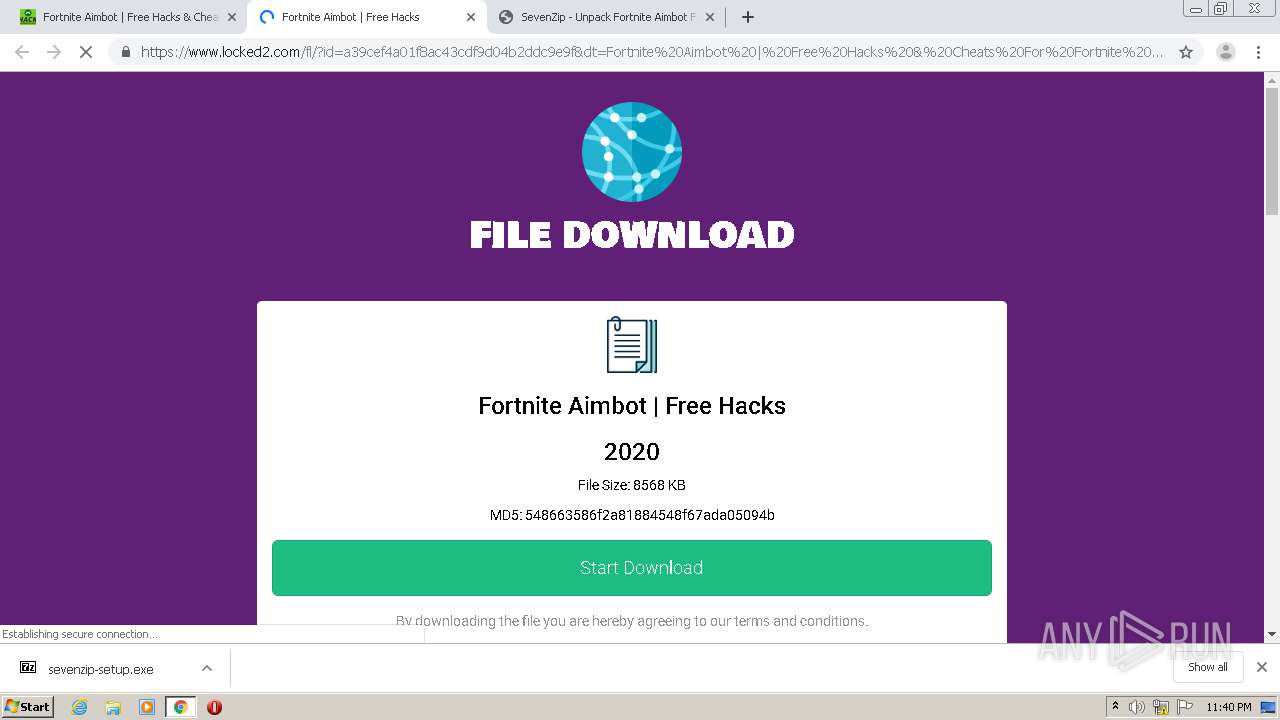
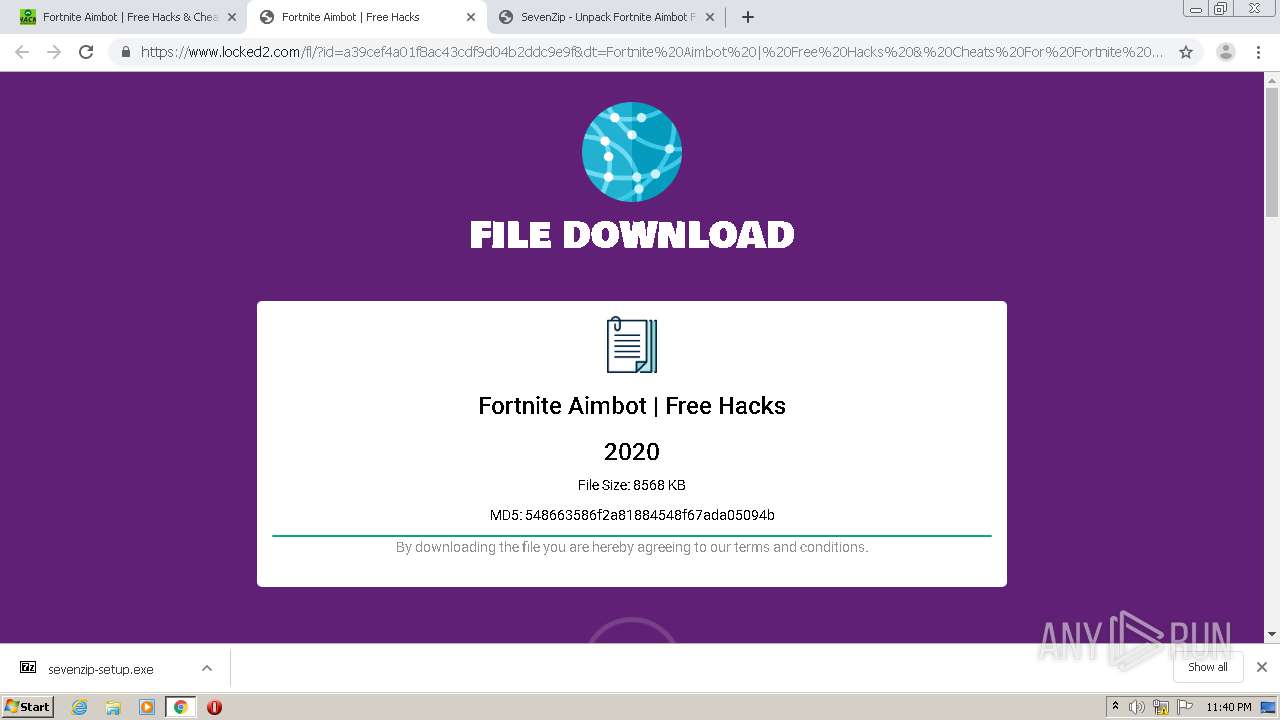
| MD5: | 84F06FBB24B6AC301E42D9E7857E0B50 |
| SHA1: | 1036BF0677B62BDE29119396573E7143D942701D |
| SHA256: | 9708C775A2BE50A796923CD7AF323ECC260EA4A22994838B36FC4549EEEDDCD3 |
| SSDEEP: | 3:N84fEUTYdtEJHKdtNW+OXtQvn:24dTgSHKdt43Xyn |
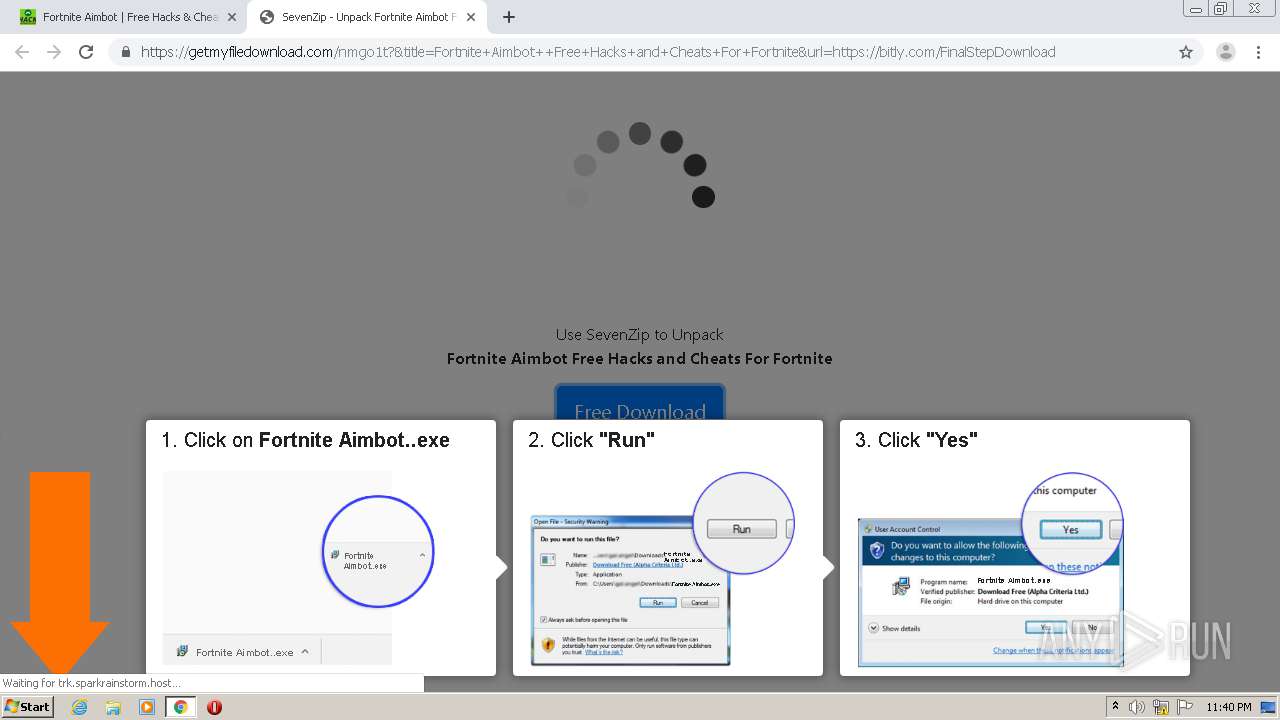
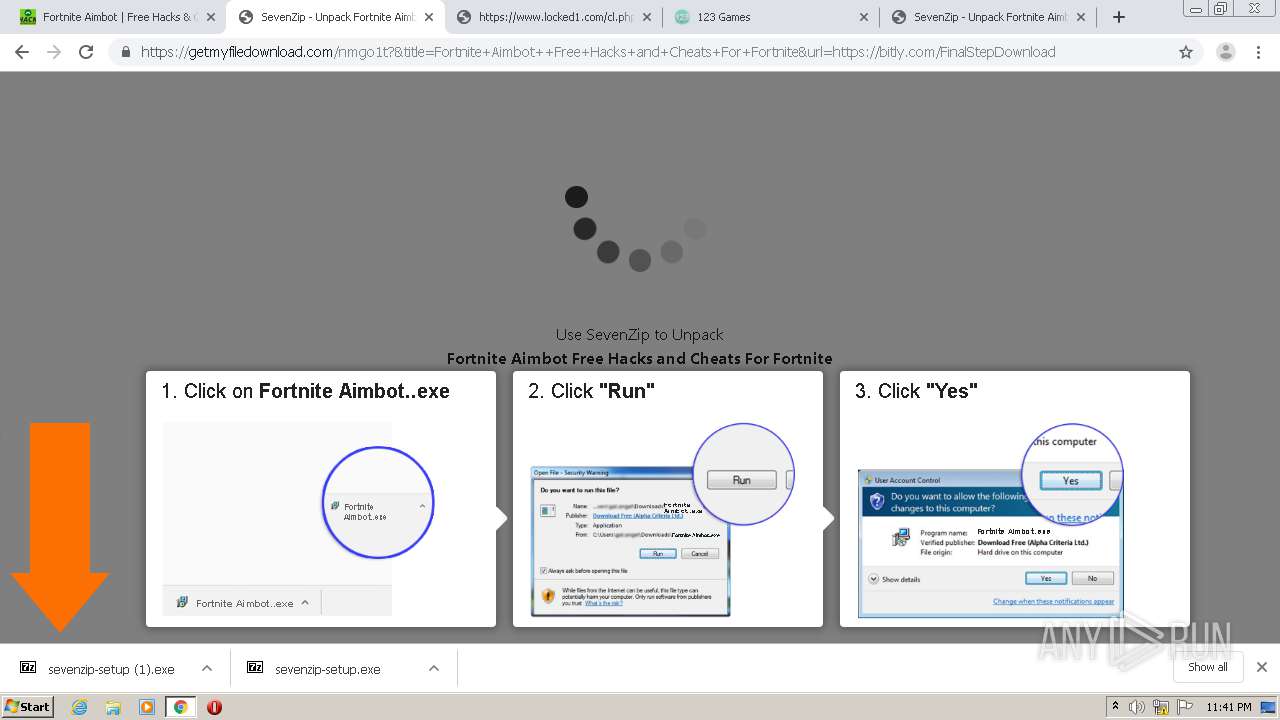
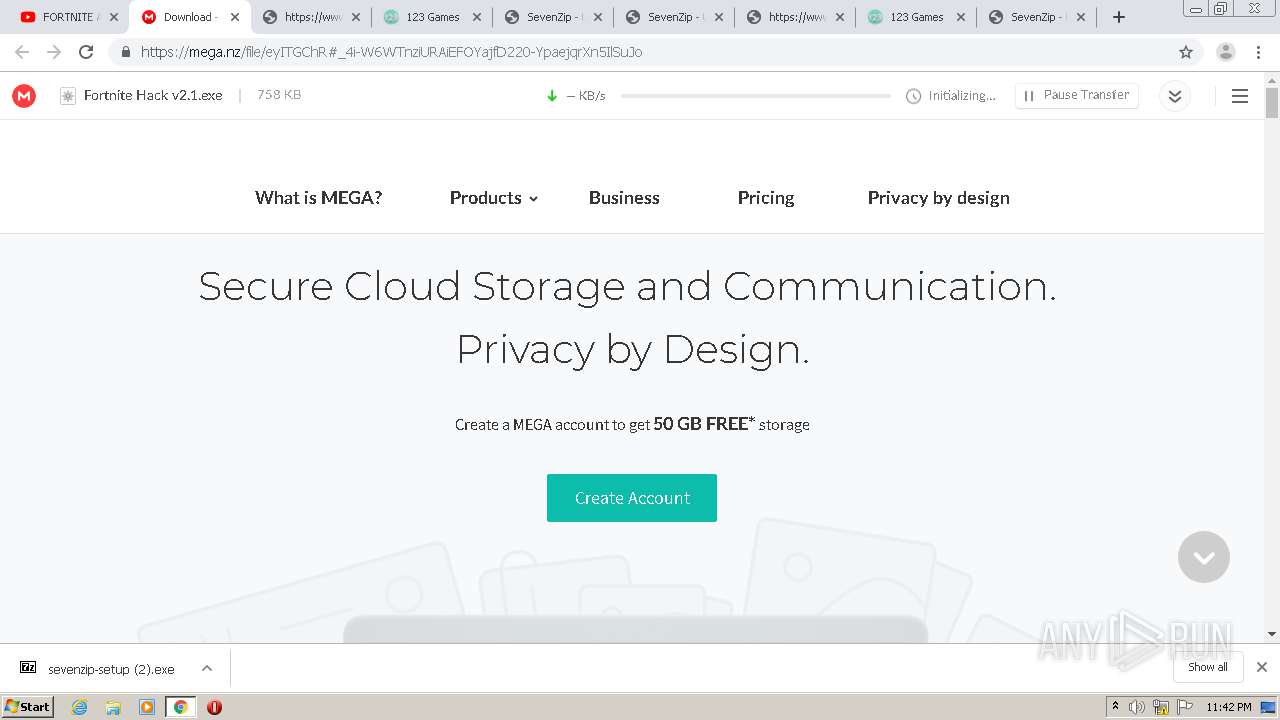
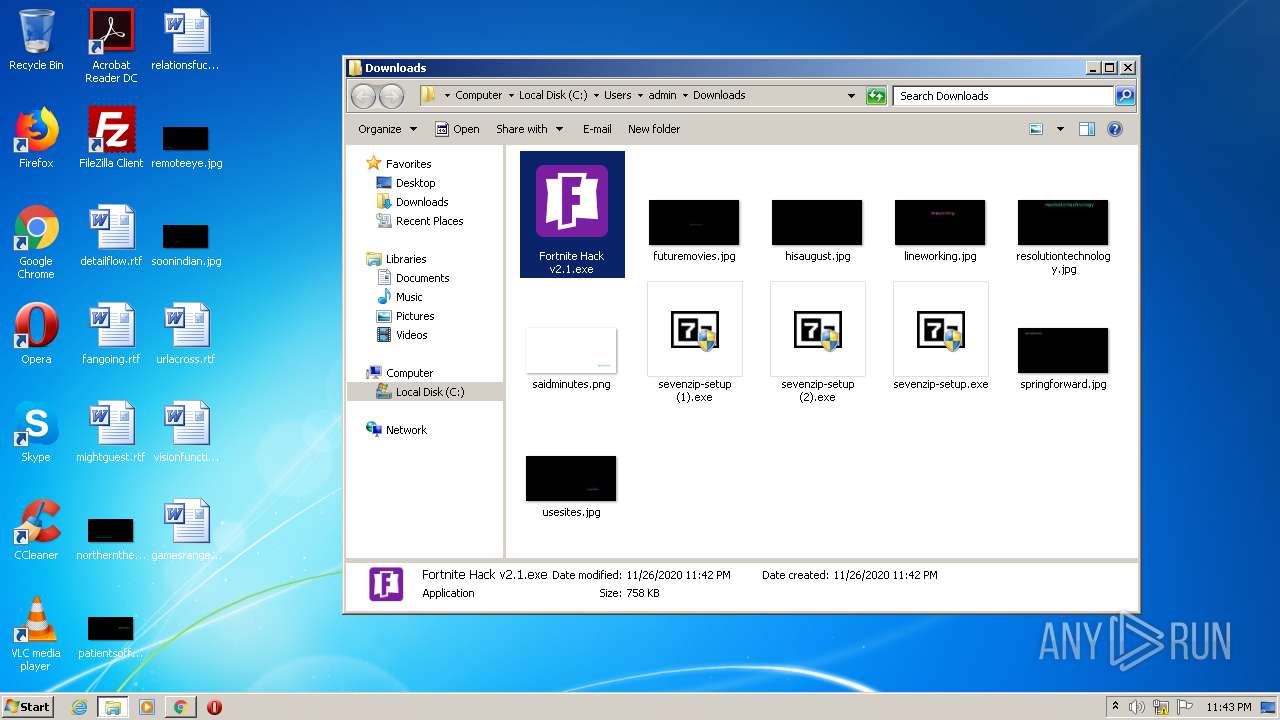
MALICIOUS
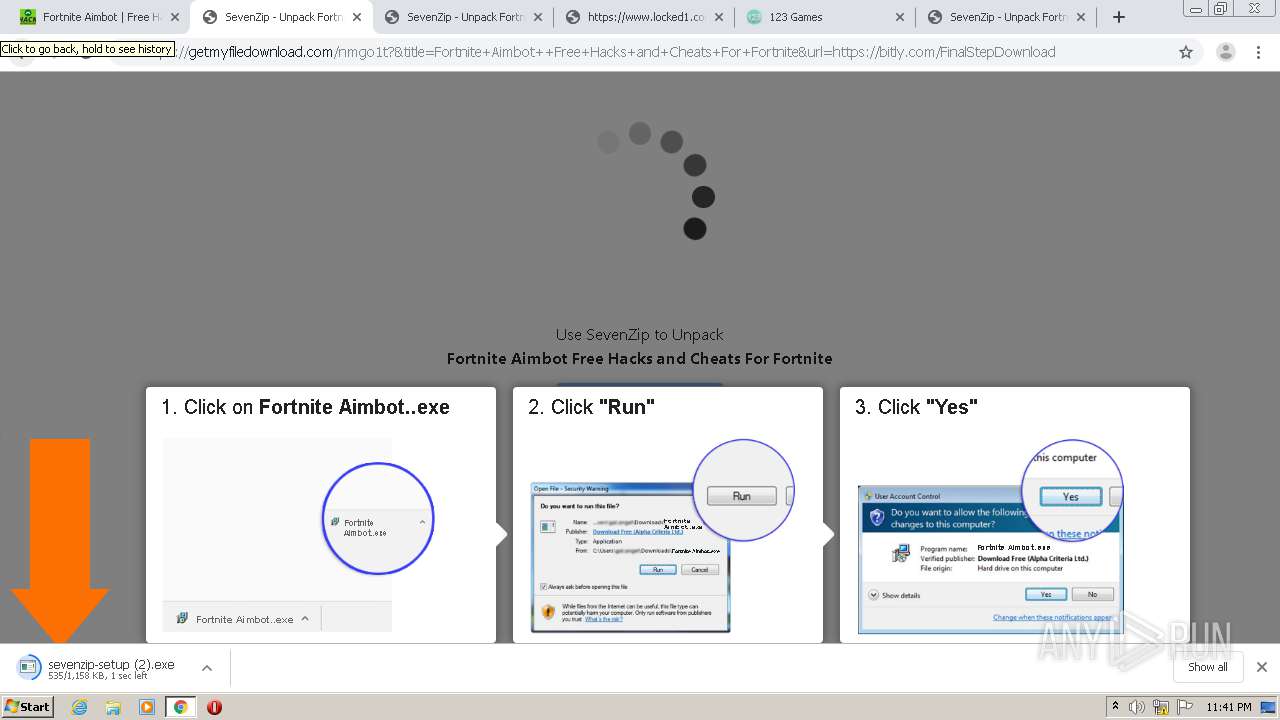
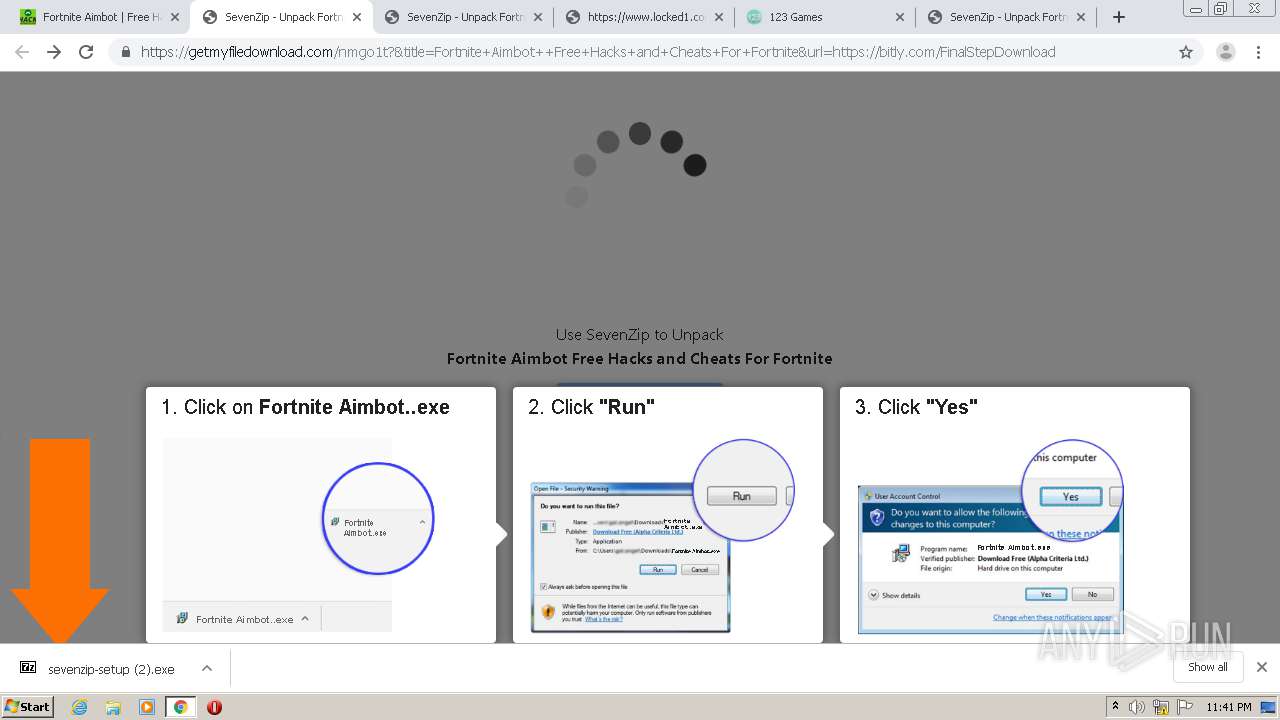
Application was dropped or rewritten from another process
- sevenzip-setup.exe (PID: 252)
- sevenzip-setup.exe (PID: 892)
- sevenzip-setup (1).exe (PID: 2980)
- sevenzip-setup (1).exe (PID: 2148)
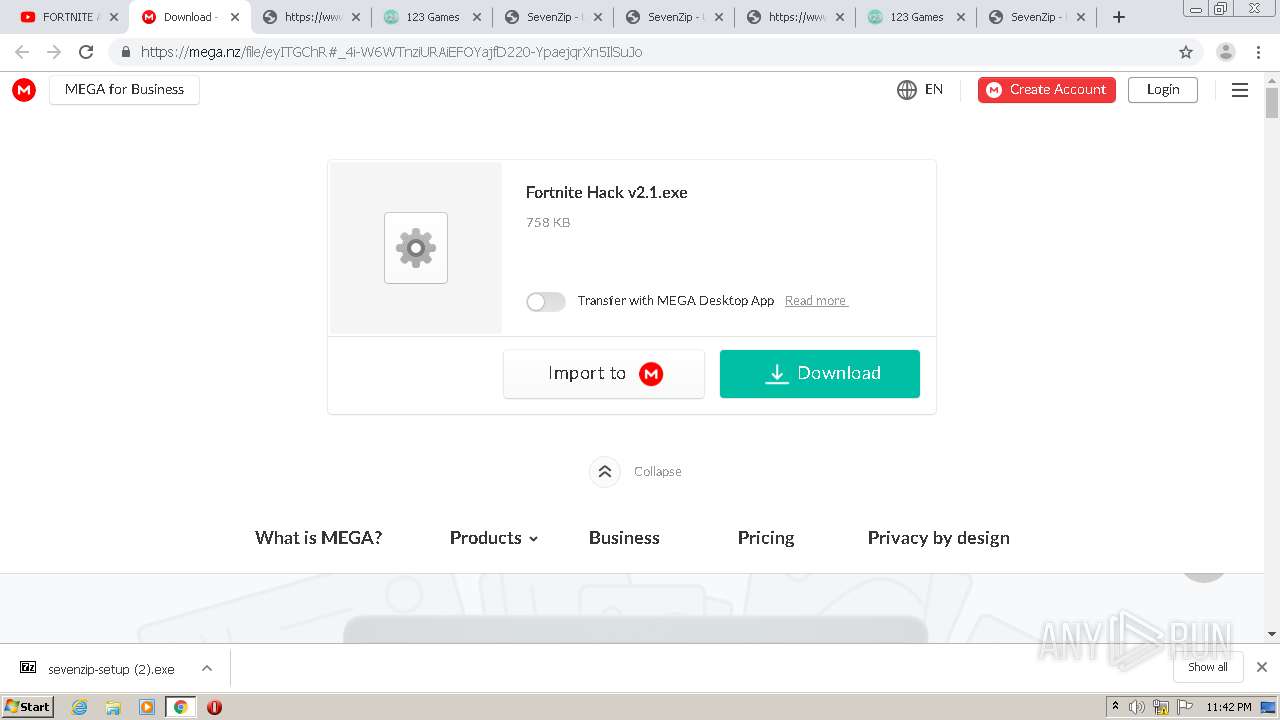
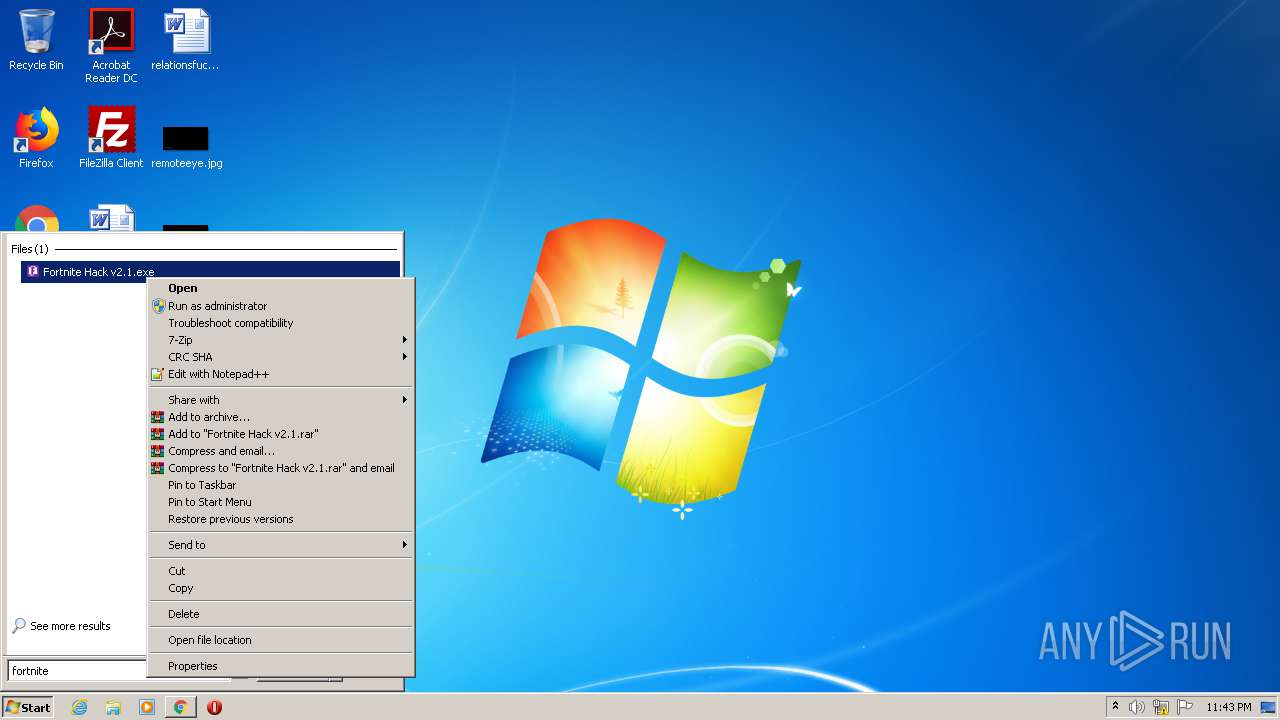
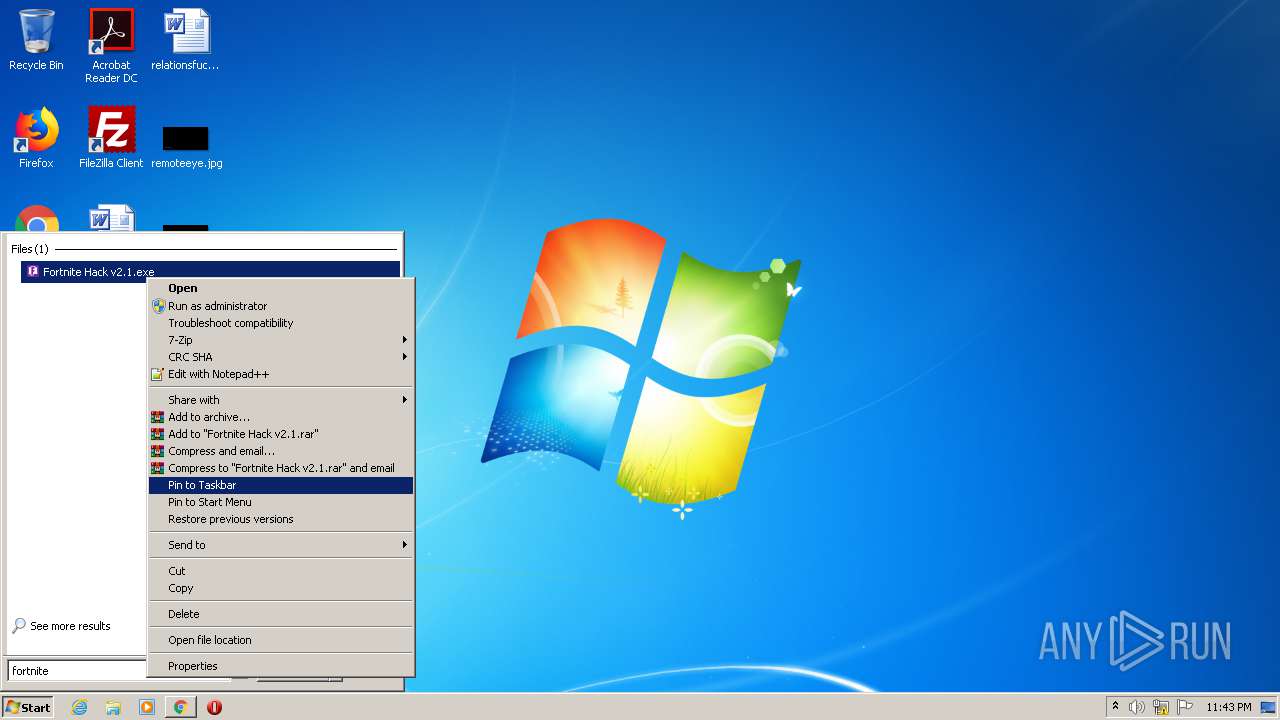
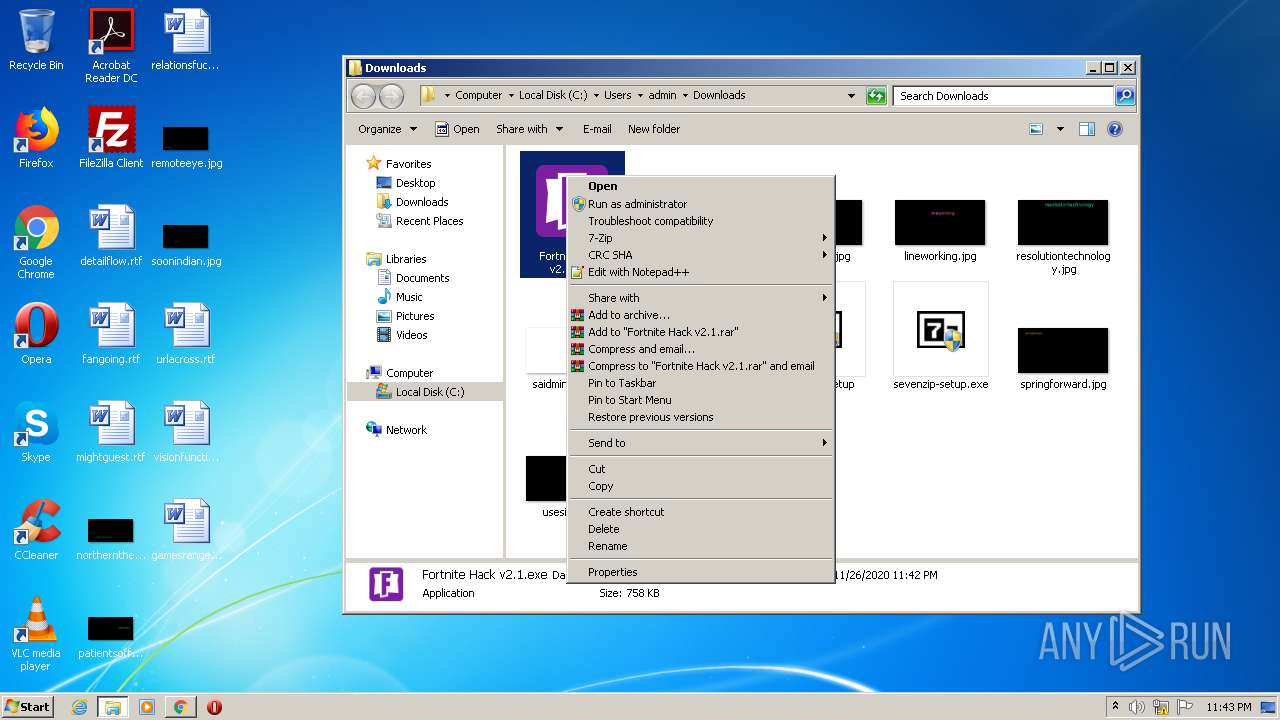
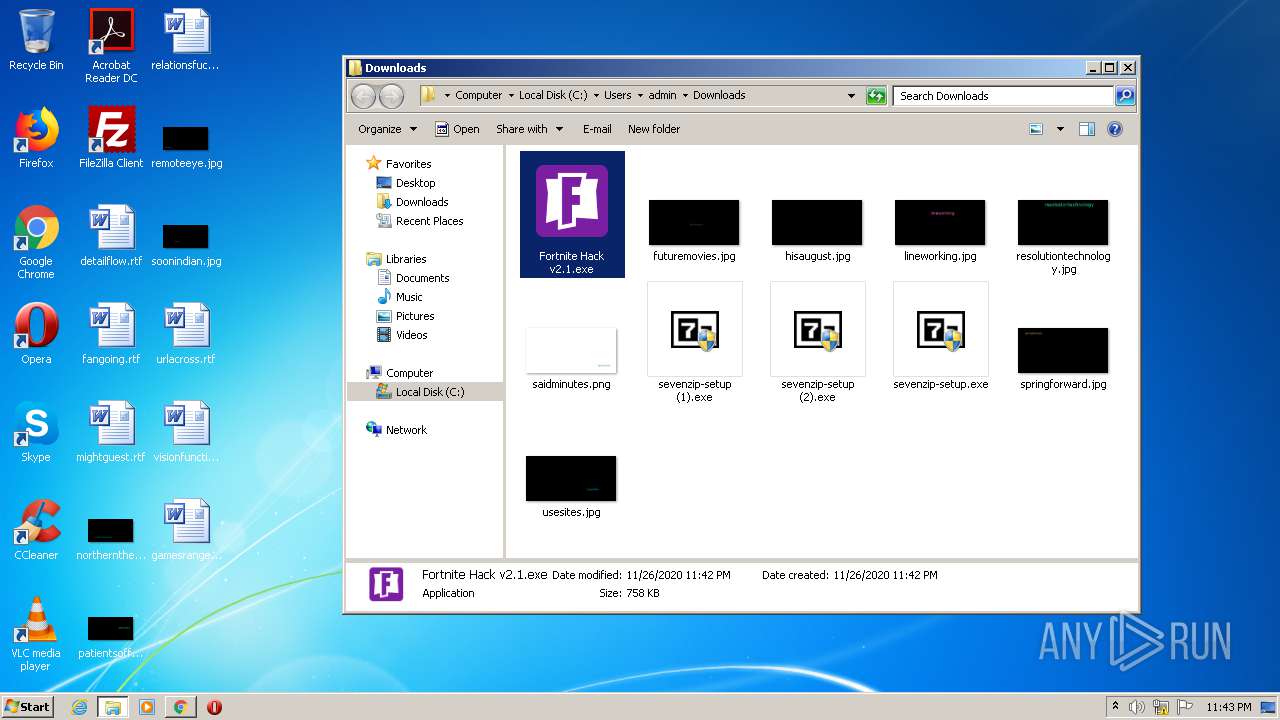
- Fortnite Hack v2.1.exe (PID: 3304)
- Fortnite Hack v2.1.exe (PID: 1212)
- Fortnite Hack v2.1.exe (PID: 1480)
- Fortnite Hack v2.1.exe (PID: 3392)
- Fortnite Hack v2.1.exe (PID: 1000)
- Fortnite Hack v2.1.exe (PID: 3224)
- Fortnite Hack v2.1.exe (PID: 2600)
- Fortnite Hack v2.1.exe (PID: 2932)
Loads dropped or rewritten executable
- svchost.exe (PID: 868)
Connects to CnC server
- Fortnite Hack v2.1.exe (PID: 3392)
- Fortnite Hack v2.1.exe (PID: 2600)
- Fortnite Hack v2.1.exe (PID: 3224)
- Fortnite Hack v2.1.exe (PID: 2932)
DCRAT was detected
- Fortnite Hack v2.1.exe (PID: 3392)
- Fortnite Hack v2.1.exe (PID: 2600)
- Fortnite Hack v2.1.exe (PID: 3224)
- Fortnite Hack v2.1.exe (PID: 2932)
Actions looks like stealing of personal data
- Fortnite Hack v2.1.exe (PID: 3392)
- Fortnite Hack v2.1.exe (PID: 2600)
- Fortnite Hack v2.1.exe (PID: 3224)
- Fortnite Hack v2.1.exe (PID: 2932)
Disables Windows Defender
- Fortnite Hack v2.1.exe (PID: 3224)
Changes settings of System certificates
- Fortnite Hack v2.1.exe (PID: 3224)
SUSPICIOUS
Creates a directory in Program Files
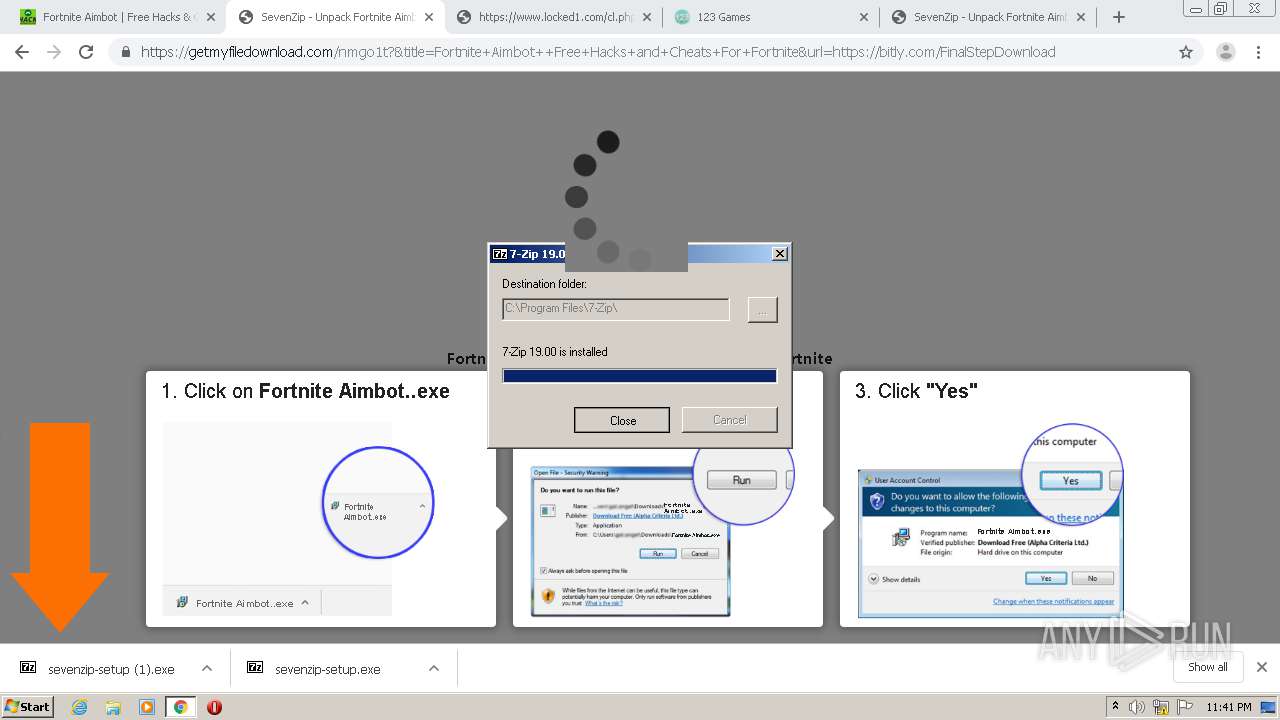
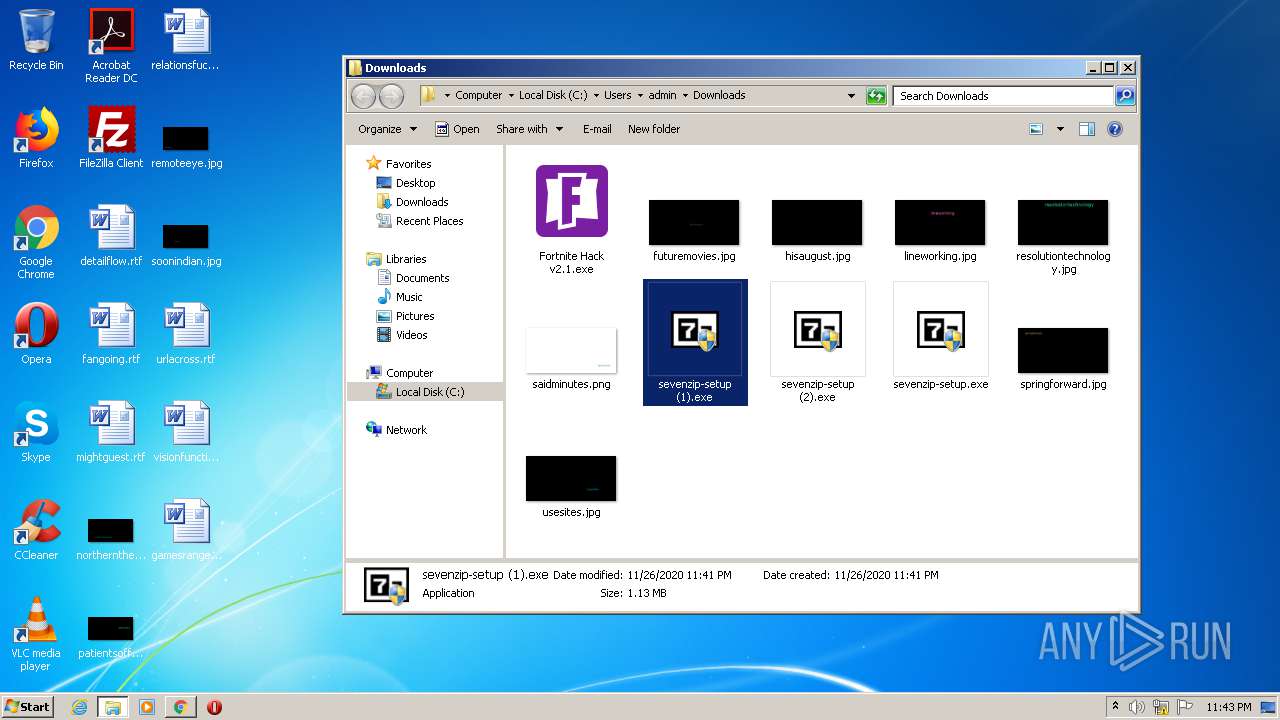
- sevenzip-setup.exe (PID: 252)
Creates COM task schedule object
- sevenzip-setup.exe (PID: 252)
- sevenzip-setup (1).exe (PID: 2148)
Executable content was dropped or overwritten
- sevenzip-setup.exe (PID: 252)
- chrome.exe (PID: 2652)
- sevenzip-setup (1).exe (PID: 2148)
Creates files in the program directory
- sevenzip-setup.exe (PID: 252)
Creates a software uninstall entry
- sevenzip-setup.exe (PID: 252)
- sevenzip-setup (1).exe (PID: 2148)
Drops a file with a compile date too recent
- chrome.exe (PID: 2652)
Reads the cookies of Google Chrome
- Fortnite Hack v2.1.exe (PID: 3392)
- Fortnite Hack v2.1.exe (PID: 2600)
- Fortnite Hack v2.1.exe (PID: 3224)
- Fortnite Hack v2.1.exe (PID: 2932)
Reads the cookies of Mozilla Firefox
- Fortnite Hack v2.1.exe (PID: 3392)
- Fortnite Hack v2.1.exe (PID: 2600)
- Fortnite Hack v2.1.exe (PID: 3224)
- Fortnite Hack v2.1.exe (PID: 2932)
Application launched itself
- Fortnite Hack v2.1.exe (PID: 1480)
- Fortnite Hack v2.1.exe (PID: 3304)
- Fortnite Hack v2.1.exe (PID: 1212)
- Fortnite Hack v2.1.exe (PID: 1000)
Executed via COM
- DllHost.exe (PID: 1504)
Checks for external IP
- Fortnite Hack v2.1.exe (PID: 3392)
- Fortnite Hack v2.1.exe (PID: 2600)
- Fortnite Hack v2.1.exe (PID: 3224)
- Fortnite Hack v2.1.exe (PID: 2932)
Creates files in the user directory
- powershell.exe (PID: 3852)
Executes PowerShell scripts
- Fortnite Hack v2.1.exe (PID: 3224)
Adds / modifies Windows certificates
- Fortnite Hack v2.1.exe (PID: 3224)
INFO
Reads the hosts file
- chrome.exe (PID: 2652)
- chrome.exe (PID: 2412)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2652)
Application launched itself
- chrome.exe (PID: 2652)
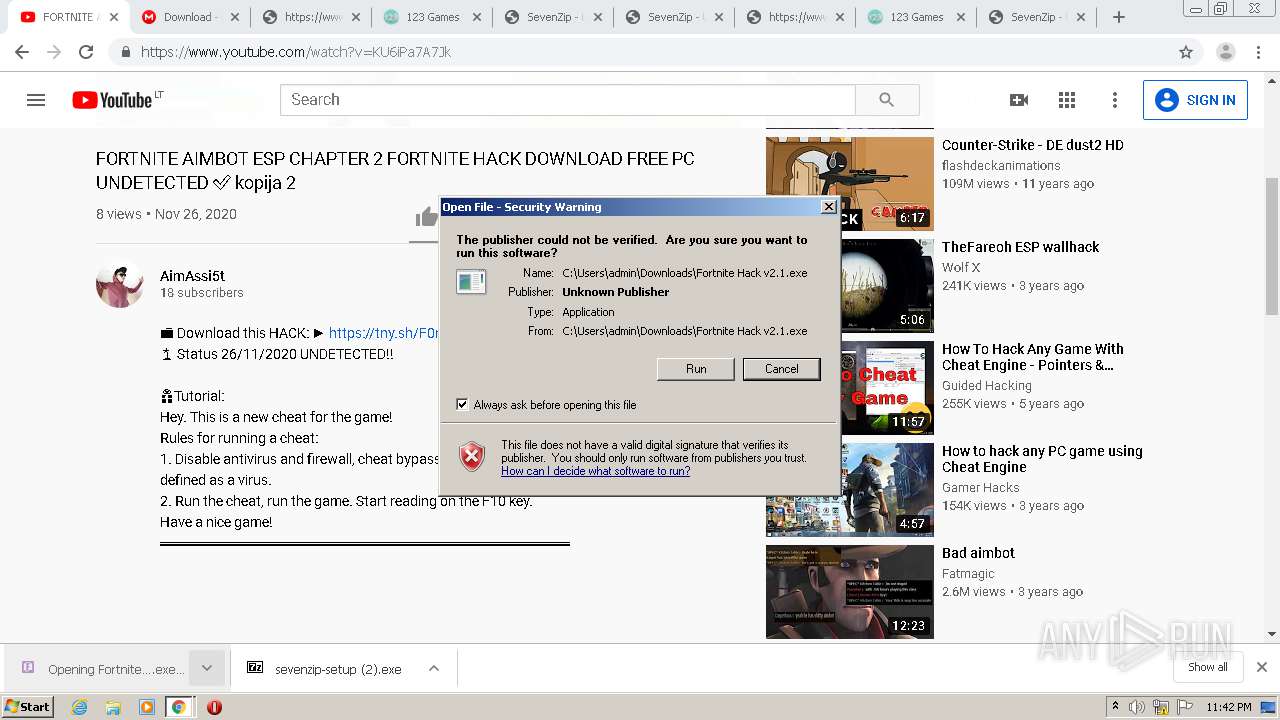
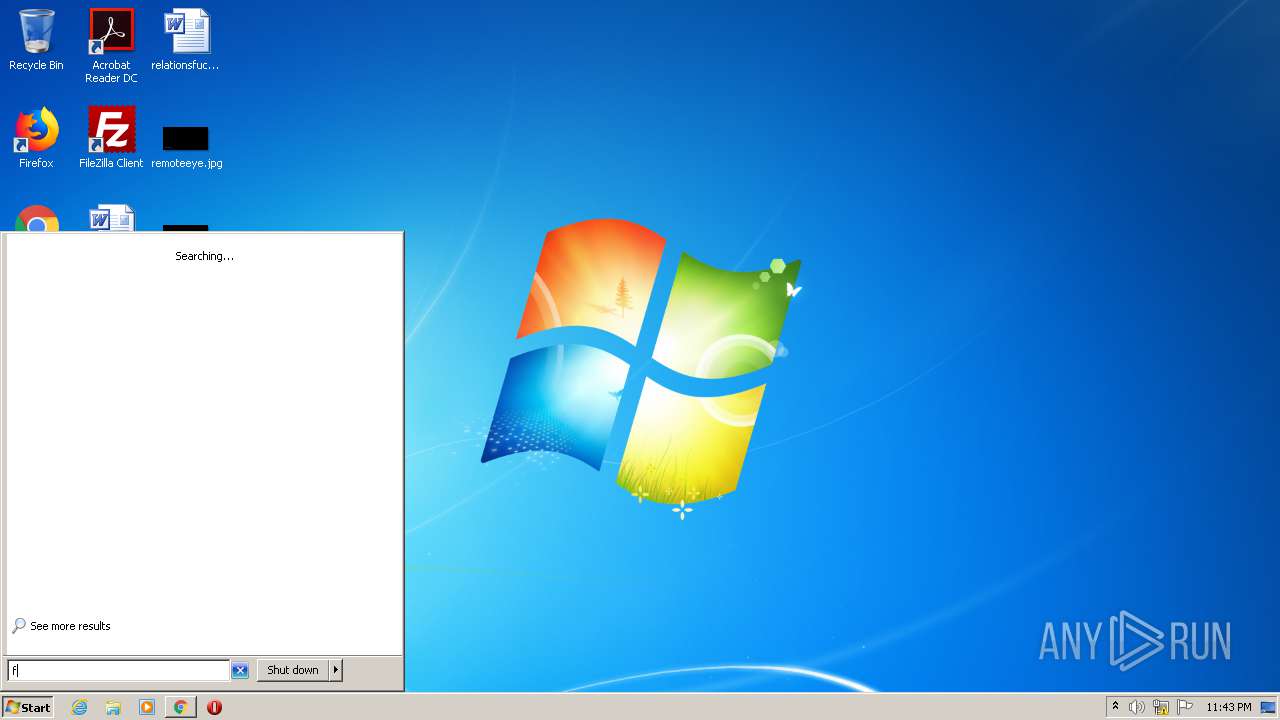
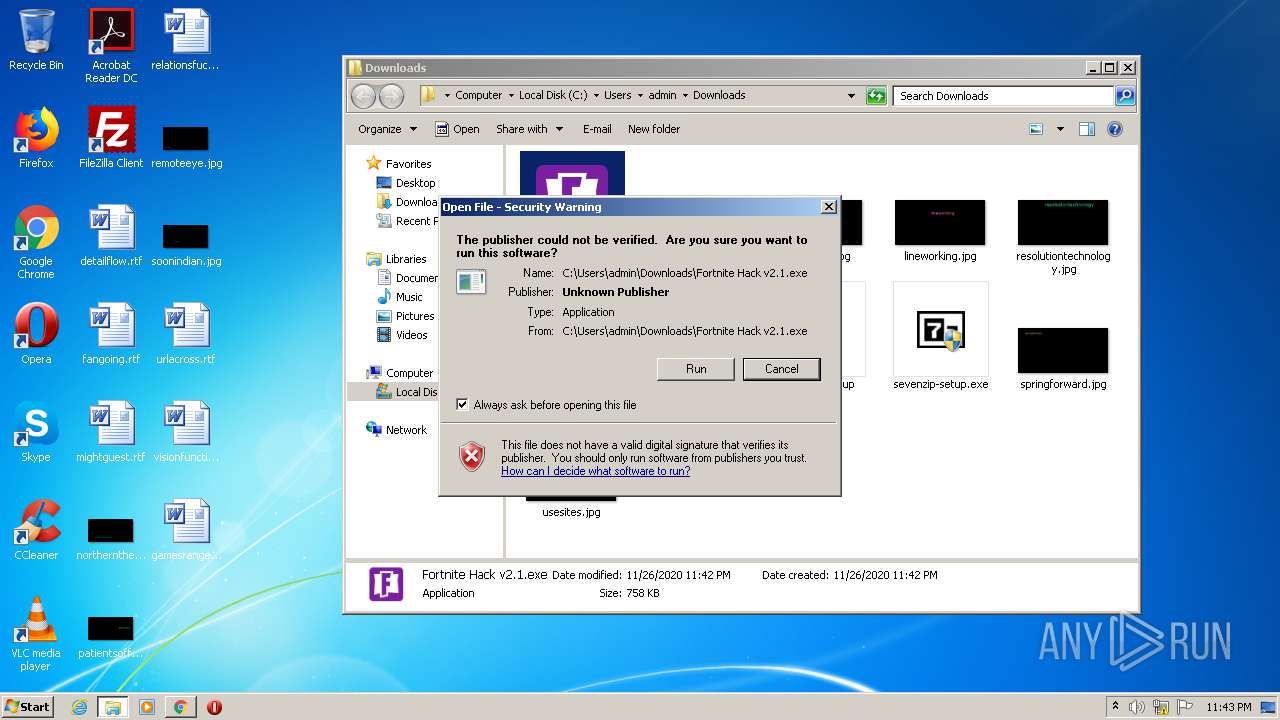
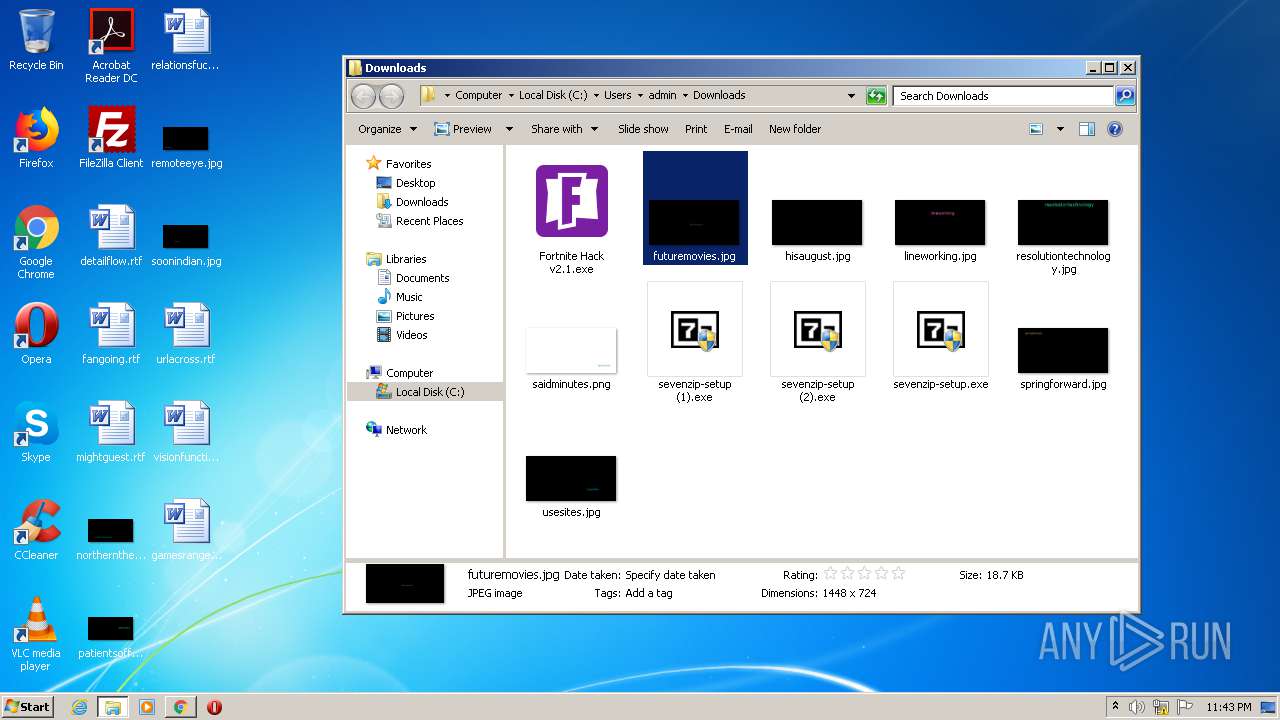
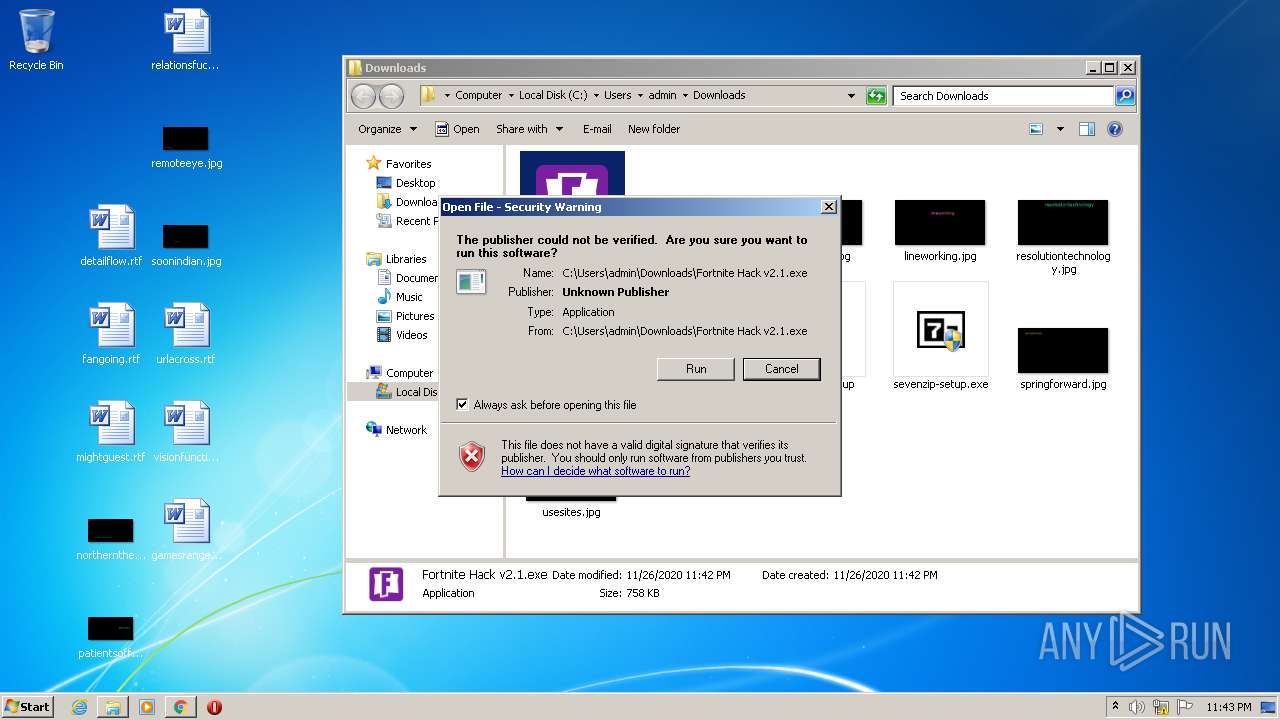
Manual execution by user
- Fortnite Hack v2.1.exe (PID: 1212)
- Fortnite Hack v2.1.exe (PID: 1480)
- Fortnite Hack v2.1.exe (PID: 1000)
Reads settings of System Certificates
- Fortnite Hack v2.1.exe (PID: 3392)
- Fortnite Hack v2.1.exe (PID: 2600)
- Fortnite Hack v2.1.exe (PID: 3224)
- Fortnite Hack v2.1.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
57
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Users\admin\Downloads\sevenzip-setup.exe" | C:\Users\admin\Downloads\sevenzip-setup.exe | chrome.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4772271363067150492,9789110525990657994,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4820733392957742234 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,4772271363067150492,9789110525990657994,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11072770381432264237 --mojo-platform-channel-handle=928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4772271363067150492,9789110525990657994,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5797176112227899511 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 868 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | "C:\Users\admin\Downloads\sevenzip-setup.exe" | C:\Users\admin\Downloads\sevenzip-setup.exe | — | chrome.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Installer Exit code: 3221226540 Version: 19.00 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4772271363067150492,9789110525990657994,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11911021996478013319 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2624 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Users\admin\Downloads\Fortnite Hack v2.1.exe" | C:\Users\admin\Downloads\Fortnite Hack v2.1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Foortnite Hack v2.1 Exit code: 0 Version: 2.0.1.0 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4772271363067150492,9789110525990657994,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=823398977638472548 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4632 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4772271363067150492,9789110525990657994,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9555456754848329284 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 628
Read events
2 349
Write events
276
Delete events
3
Modification events
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2640) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2652-13250907610347375 |
Value: 259 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2652) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
26
Suspicious files
175
Text files
337
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC03CDB-A5C.pma | — | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\54fb2a54-517c-4439-9bba-9e51506cd486.tmp | — | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 868 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1543d9.TMP | text | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF154407.TMP | text | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1543d9.TMP | text | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF154456.TMP | text | |
MD5:— | SHA256:— | |||
| 2652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
71
TCP/UDP connections
170
DNS requests
90
Threats
49
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/1ddc4dff972043b3cc3cd65e3a4bbba8858c94e3.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&0e50b3b0d8bef5ad2c2bb9edb8721e7b=91a2774ef46a80eb0650e9432d7cd6c6&mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69 | RU | text | 71 b | malicious |
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/rv02en3fbacrepzf75m9hyqm8g116j2z5p56jqqwaaxbot3k9k/c7781d9228e2754700b35da4021369bb.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&a5a3f15227a1a125b83febd085c24dd3=gjZ3QjN3cjNzY2NldjNkhjYyITMzUWY4UmYidDZidTY3YjMhdTYhVDM&5137d53830f54cffb1c8b0fa61a6caf7=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&be2b793e6423d4034ef30d375573ecd1=gLu4ycll2av92Ygcmbph2Y0VmR&059aa23dd3a1c7bca7b747a1247c2235=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&9da00d7d13a2737fe04e5433ada7a3d8=YjM3YTM0cjM0QzNhlDO0kDMyczY1MDZ0QmZxMjN3QWY | RU | text | 39 b | malicious |
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/1ddc4dff972043b3cc3cd65e3a4bbba8858c94e3.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&c4dd8bfc18308df8531c1be327fdb674=7a1463ba18bc7a09ba6c604708be9fa8&b0a930b8b134c49257d3a60794ab6d8a=afbddd404b6e908834ec01647b97c946c53a6d64&mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69 | RU | text | 150 b | malicious |
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/rv02en3fbacrepzf75m9hyqm8g116j2z5p56jqqwaaxbot3k9k/c7781d9228e2754700b35da4021369bb.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&a5a3f15227a1a125b83febd085c24dd3=gjZ3QjN3cjNzY2NldjNkhjYyITMzUWY4UmYidDZidTY3YjMhdTYhVDM&5137d53830f54cffb1c8b0fa61a6caf7=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&1644a9350a68040511a9d02c5536133e=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&d45d6dc64f77c99dbb08a9224f22ca46=YzM0MGO0YmNkRDZhdzN5Y2MwAjMlJDMmJmM3EWZ5UmM&be2b793e6423d4034ef30d375573ecd1=9JyckF2bs52dvRkI6IydvRmbpdFVDFkIs0nIoRXdhdmbpN3cp12Lc9Wau8mZulGcp9CXvwlOzBHd0hmI6ISZtRWYlJnIsIyc1lmbslmVvwVZw9mc1VkI6ISZu9mel1Wa0JCLiEDMwYzNiojIsFGdz9GciwiICFUVgwycvpWan9Gbv5GajVGdgIXagM3btVGdzl2cgMXZul2Yh1mcvZmbJBiM3ITM2MVQiojInJ3biwiI3YTMz4yMywyMzMTOuUTNiojIj9GbiwiIUxkI6ISeyRnb192YiwiIpFWasVXYpNlI6Iibvl2ZlJnIsISahlGb1FWagKchDLiOikHdpNmIsIybm5WauQWdvx2YhJmLygTL2YTMtYDMy0SN4IiOiUWbh5Gdz9GaiwiIygjL2YTMuYDMy4SN4IiOiAXaisnOi8mZulEcJJCLiIiOicUQUJCLi4WatRWYiojIl1WYOJXZzVlIsIyQQ1iUFNVViojIl1WYONEUiwiI0lmQgIzMgwWYu9WazNXZm9mcQByNgM3dvRmbpdlI6IiclZlbpdlIsIiTiojIulWbkF0cpJCLi4kI6ISbhNmYld1cpJCLiklI6ISZu9Gaw9mcjlWTzlmIsIyMuQjLzIiOiIXZWJXZ2JXZTJCLiMyQiojIlBXeUJXZ2JXZTJye&059aa23dd3a1c7bca7b747a1247c2235=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&9da00d7d13a2737fe04e5433ada7a3d8=YGO3IzYiRDO3AjM4ATO0IWO0gzMwYTY4gDNyEjYlhzM | RU | text | 39 b | malicious |
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/rv02en3fbacrepzf75m9hyqm8g116j2z5p56jqqwaaxbot3k9k/c7781d9228e2754700b35da4021369bb.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&a5a3f15227a1a125b83febd085c24dd3=gjZ3QjN3cjNzY2NldjNkhjYyITMzUWY4UmYidDZidTY3YjMhdTYhVDM&5137d53830f54cffb1c8b0fa61a6caf7=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&be2b793e6423d4034ef30d375573ecd1=4iLuMXby9mZgcmbph2Y0VmR&059aa23dd3a1c7bca7b747a1247c2235=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&9da00d7d13a2737fe04e5433ada7a3d8=YjM3YTM0cjM0QzNhlDO0kDMyczY1MDZ0QmZxMjN3QWY | RU | text | 39 b | malicious |
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/rv02en3fbacrepzf75m9hyqm8g116j2z5p56jqqwaaxbot3k9k/c7781d9228e2754700b35da4021369bb.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&a5a3f15227a1a125b83febd085c24dd3=gjZ3QjN3cjNzY2NldjNkhjYyITMzUWY4UmYidDZidTY3YjMhdTYhVDM&5137d53830f54cffb1c8b0fa61a6caf7=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&be2b793e6423d4034ef30d375573ecd1=4iLuM0Qgcmbph2Y0VmR&059aa23dd3a1c7bca7b747a1247c2235=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&9da00d7d13a2737fe04e5433ada7a3d8=YjM3YTM0cjM0QzNhlDO0kDMyczY1MDZ0QmZxMjN3QWY | RU | text | 39 b | malicious |
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/rv02en3fbacrepzf75m9hyqm8g116j2z5p56jqqwaaxbot3k9k/c7781d9228e2754700b35da4021369bb.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&a5a3f15227a1a125b83febd085c24dd3=gjZ3QjN3cjNzY2NldjNkhjYyITMzUWY4UmYidDZidTY3YjMhdTYhVDM&5137d53830f54cffb1c8b0fa61a6caf7=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&be2b793e6423d4034ef30d375573ecd1=%00&059aa23dd3a1c7bca7b747a1247c2235=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&9da00d7d13a2737fe04e5433ada7a3d8=kzYyMzYldTM0MzY4UTMlZTOxQGZldjNkRzMzEWOiJzM | RU | text | 39 b | malicious |
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/rv02en3fbacrepzf75m9hyqm8g116j2z5p56jqqwaaxbot3k9k/c7781d9228e2754700b35da4021369bb.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&a5a3f15227a1a125b83febd085c24dd3=gjZ3QjN3cjNzY2NldjNkhjYyITMzUWY4UmYidDZidTY3YjMhdTYhVDM&5137d53830f54cffb1c8b0fa61a6caf7=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&be2b793e6423d4034ef30d375573ecd1=4iLu0WYydWZsVGVgcmbph2Y0VmR&059aa23dd3a1c7bca7b747a1247c2235=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&9da00d7d13a2737fe04e5433ada7a3d8=YjM3YTM0cjM0QzNhlDO0kDMyczY1MDZ0QmZxMjN3QWY | RU | text | 39 b | malicious |
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/rv02en3fbacrepzf75m9hyqm8g116j2z5p56jqqwaaxbot3k9k/c7781d9228e2754700b35da4021369bb.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&a5a3f15227a1a125b83febd085c24dd3=gjZ3QjN3cjNzY2NldjNkhjYyITMzUWY4UmYidDZidTY3YjMhdTYhVDM&5137d53830f54cffb1c8b0fa61a6caf7=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&ba89ba86b7fc9f28dcfb4f7c915b2378=QfiMHZh9Gbud3bExFXulWbkFGXcNnclNXVcxlODJiOigGdhBlIsIiMucjL0IiOi42bpNnclZ1ay92dl1WYyZkIsIib39mbr5WViojIoRXYQ1WYydWZsVGViwiIiojIzBHcB1WYlR3UiwiIud3butmbVJiOiQUSyV2cV1WYlR3UiwiIz92ZpJHZhJ3XsVWayJWYnJiOiIXZzVVbhVGdTJCLsxWdupjIn5WYM1WYlR3UiwiItFWZ0N3LcNXZslmZg0WYyd2byB3LcpzYiojIoRXYQ1WYlR3UiwiIuxlcclybpRWdBByN5cyQBByalRHbhVmUoAibJBSZulGTuxlcc9WakVXQgcTOnMUQgsWZ0xWYlJFKgUmbvhGcvJ3Yp1kI6Iycl52boB3byNWaNJCLi4GXyxVMZFETQNVSExFXuwFXcxlI6IycuVWZyN2UiwiIiojIz1WYjJWZXJCLzgTNzojINFkUiwiIB9CXOJiOiQmch9mYyVGa09WTiwiIB9CXOJiOiwGbhdXZylmRiwiIB9CXOJiOiMXdylmdpRnbBJCLi0iI6ICUJ5UQMJCLiwETFRkI6IyUPlkQiwiI6h0RwcjLyACQgUFUDBCMwQjNtUTagkSTUhSZy92QgkiUowWZ05WSiojIl1WYOVFUDJCLiIXZ0BXYkFEIzNWaoBXYydEIBdkVgQmchRmbhR3UiojIl1WYOVFUHJye&5c8f12243091ebe823a0155426da6b33=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&85f243359999ceb35dc644148a0d3ee1=kzYyMzYldTM0MzY4UTMlZTOxQGZldjNkRzMzEWOiJzM | RU | text | 39 b | malicious |
3392 | Fortnite Hack v2.1.exe | GET | 200 | 82.146.55.112:80 | http://82.146.55.112/6huyl2umba586hf96eo7192ukywa72yiqmrmy1bhtgkjupozgzw7x0r8pzsl4qv90890y/t6k241xpmz/rv02en3fbacrepzf75m9hyqm8g116j2z5p56jqqwaaxbot3k9k/c7781d9228e2754700b35da4021369bb.php?mOSVZMxFddL1NAd6p6tg7y7n9n8=2B9TNX9g7sXwlYJcovXU&dImkn2xRpVwOK=ce2ozB69&a5a3f15227a1a125b83febd085c24dd3=gjZ3QjN3cjNzY2NldjNkhjYyITMzUWY4UmYidDZidTY3YjMhdTYhVDM&5137d53830f54cffb1c8b0fa61a6caf7=QNhhDN5YjYzMWMlJzMiNGZjJTN0E2YiljMxcjZ2ImYjRmY0UDZhJ2Y&1644a9350a68040511a9d02c5536133e=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&d45d6dc64f77c99dbb08a9224f22ca46=YzM0MGO0YmNkRDZhdzN5Y2MwAjMlJDMmJmM3EWZ5UmM&be2b793e6423d4034ef30d375573ecd1=9JyckF2bs52dvRkI6IydvRmbpdFVDFkIs0nIoRXdhdmbpN3cp12Lc9Wau8mZulGcp9CXvwlOzBHd0hmI6ISZtRWYlJnIsIyc1lmbslmVvwVZw9mc1VkI6ISZu9mel1Wa0JCLiEDMwYzNiojIsFGdz9GciwiICFUVgwycvpWan9Gbv5GajVGdgIXagM3btVGdzl2cgMXZul2Yh1mcvZmbJBiM3ITM2MVQiojInJ3biwiI3YTMz4yMywyMzMTOuUTNiojIj9GbiwiIUxkI6ISeyRnb192YiwiIpFWasVXYpNlI6Iibvl2ZlJnIsISahlGb1FWagKchDLiOikHdpNmIsIybm5WauQWdvx2YhJmLygTL2YTMtYDMy0SN4IiOiUWbh5Gdz9GaiwiIygjL2YTMuYDMy4SN4IiOiAXaisnOi8mZulEcJJCLiIiOicUQUJCLi4WatRWYiojIl1WYOJXZzVlIsIyQQ1iUFNVViojIl1WYONEUiwiI0lmQgIzMgwWYu9WazNXZm9mcQByNgM3dvRmbpdlI6IiclZlbpdlIsIiTiojIulWbkF0cpJCLi4kI6ISbhNmYld1cpJCLiklI6ISZu9Gaw9mcjlWTzlmIsIyMuQjLzIiOiIXZWJXZ2JXZTJCLiMyQiojIlBXeUJXZ2JXZTJye&059aa23dd3a1c7bca7b747a1247c2235=gjN0QmY5AjMjljM2QWMzQDZjdTNzgDM1UWOhVTYldjM&9da00d7d13a2737fe04e5433ada7a3d8=YGO3IzYiRDO3AjM4ATO0IWO0gzMwYTY4gDNyEjYlhzM | RU | text | 39 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2412 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
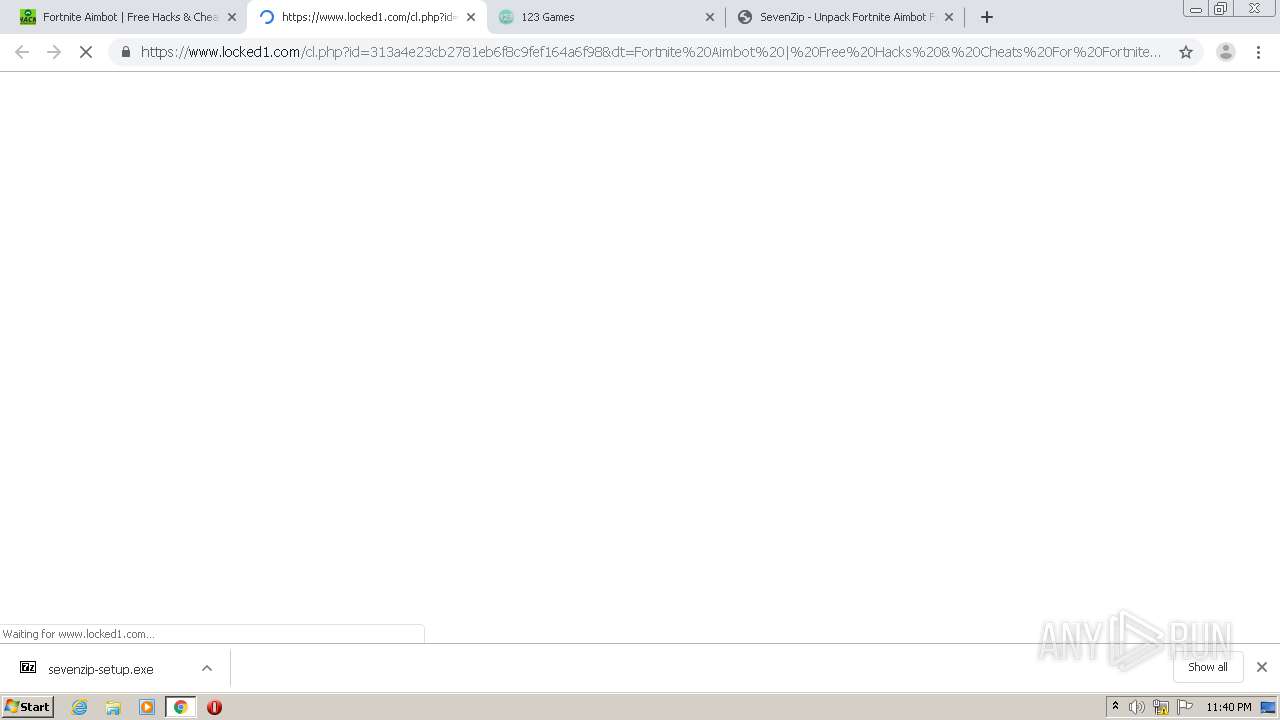
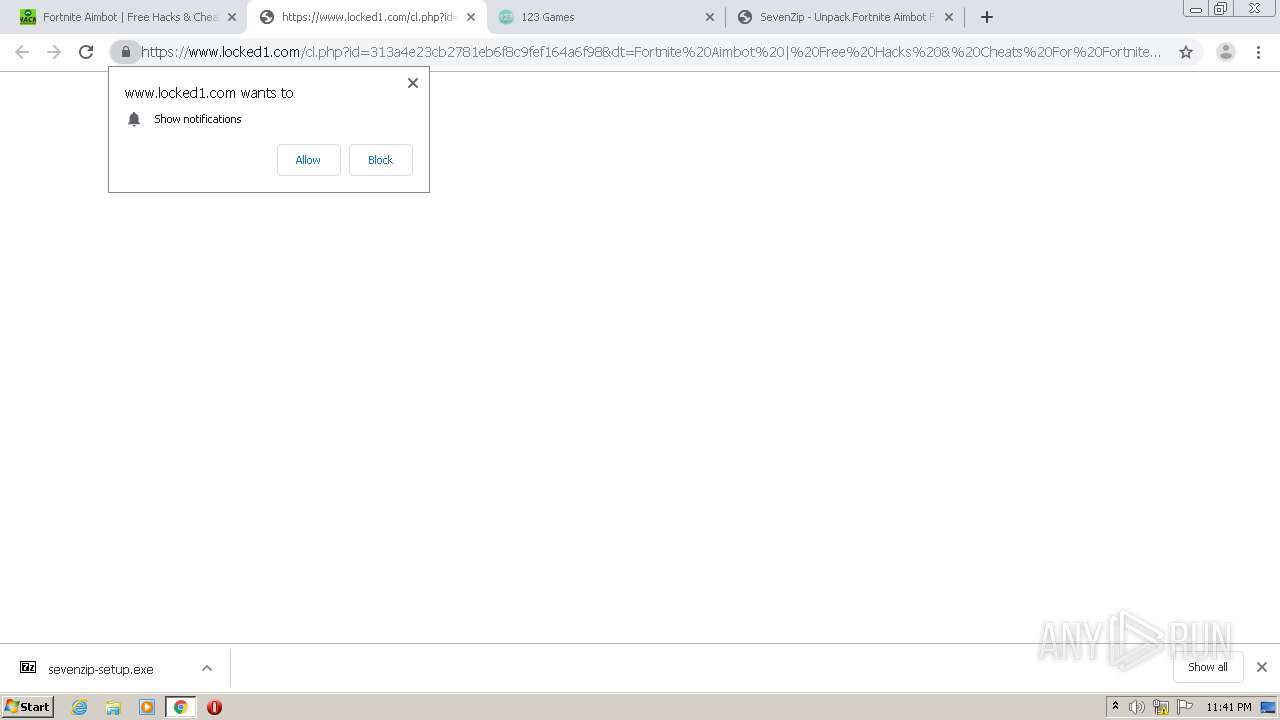
2412 | chrome.exe | 104.168.220.120:443 | hackapparatus.com | Hostwinds LLC. | US | unknown |
2412 | chrome.exe | 192.0.77.2:443 | i1.wp.com | Automattic, Inc | US | suspicious |
2412 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
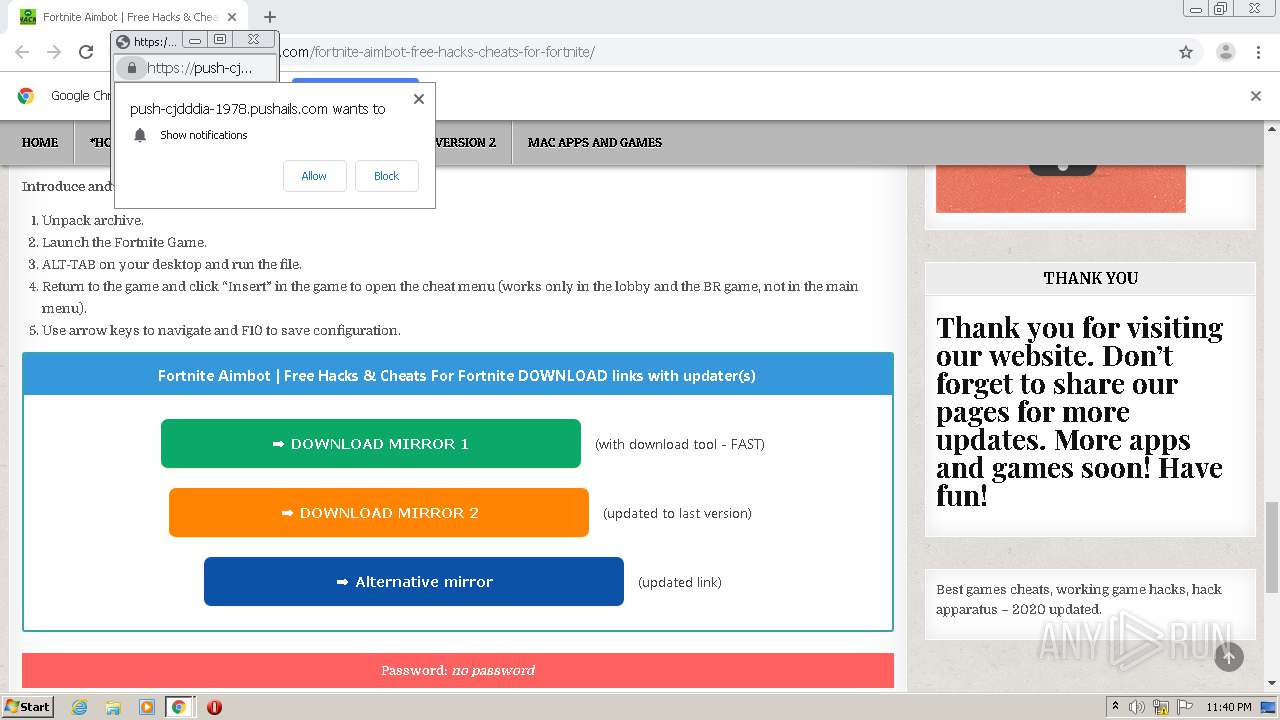
2412 | chrome.exe | 139.45.196.132:443 | propu.sh | — | US | suspicious |
2412 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
2412 | chrome.exe | 66.102.1.188:5228 | mtalk.google.com | Google Inc. | US | whitelisted |
2412 | chrome.exe | 139.45.196.208:443 | push-cjdddia-1978.pushails.com | — | US | suspicious |
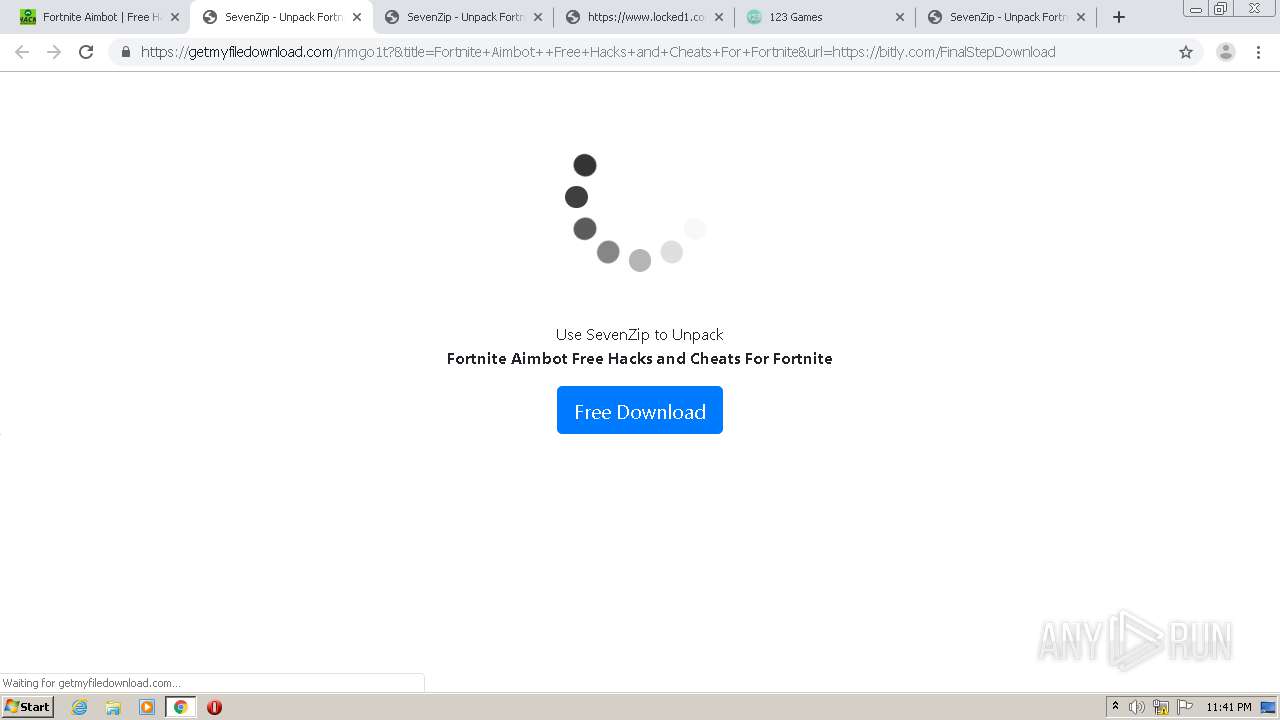
2412 | chrome.exe | 104.24.121.18:443 | getmyfiledownload.com | Cloudflare Inc | US | shared |
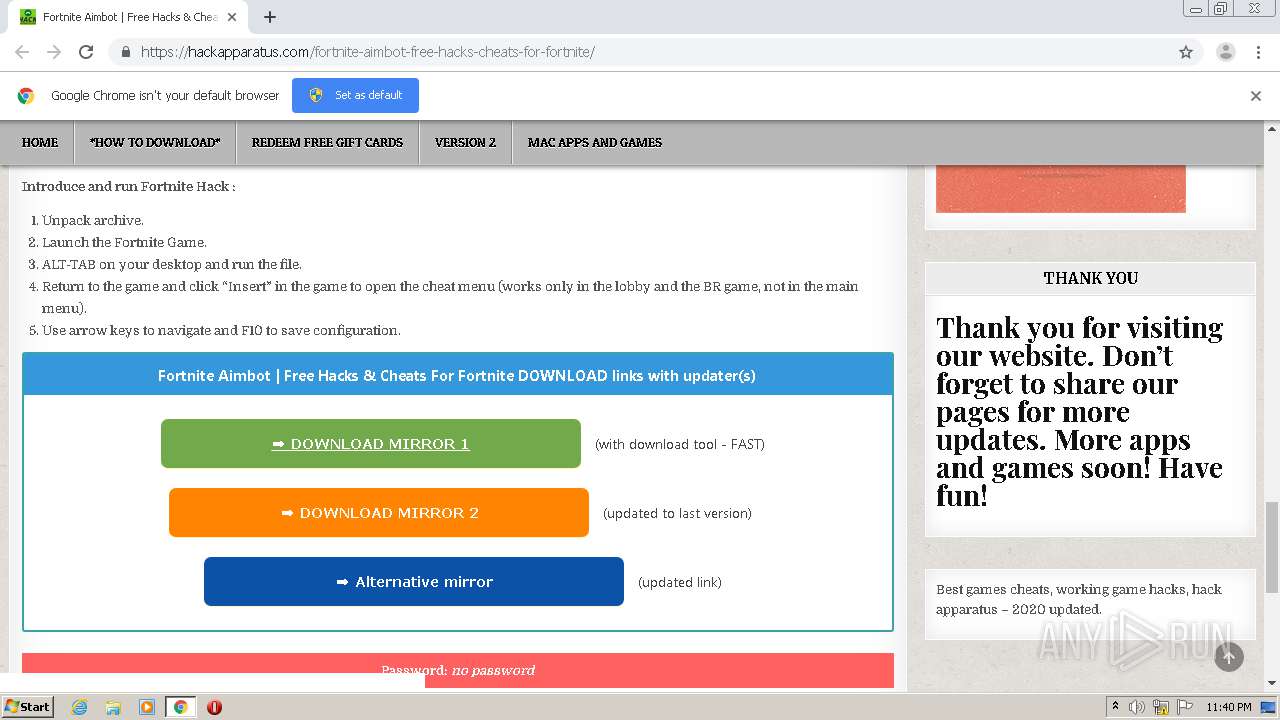
2412 | chrome.exe | 104.18.35.199:443 | trk.download100.xyz | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hackapparatus.com |
| suspicious |
accounts.google.com |
| shared |
fonts.gstatic.com |
| whitelisted |
i1.wp.com |
| whitelisted |
propu.sh |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
i0.wp.com |
| whitelisted |
i2.wp.com |
| whitelisted |
my.rtmark.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
2412 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
3392 | Fortnite Hack v2.1.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3392 | Fortnite Hack v2.1.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2600 | Fortnite Hack v2.1.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
2600 | Fortnite Hack v2.1.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2600 | Fortnite Hack v2.1.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2600 | Fortnite Hack v2.1.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
2600 | Fortnite Hack v2.1.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
2600 | Fortnite Hack v2.1.exe | A Network Trojan was detected | REMOTE [PTsecurity] DCRat |
4 ETPRO signatures available at the full report