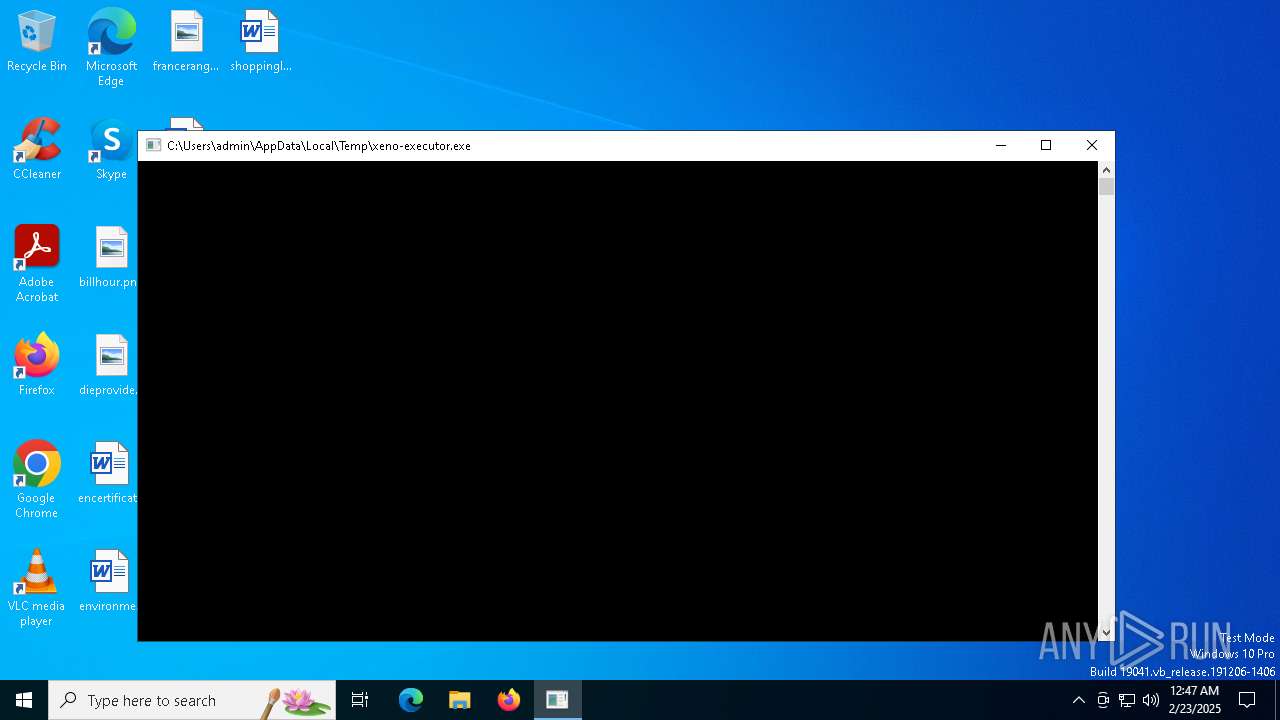
| File name: | xeno-executor.exe |
| Full analysis: | https://app.any.run/tasks/980ae354-c2bf-45b5-8dae-a68400f9d615 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 23, 2025, 00:47:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 5 sections |
| MD5: | 751D4C6B44926AC85A433D96D8AD60BE |
| SHA1: | 5B8B1F6822BF6E2D430609241B8C98D2ED0E395F |
| SHA256: | 96C874E0C83C0231DCFC1012AF391CFBC00477E3E3DAC185C815E7D97DFFB4DA |
| SSDEEP: | 24576:gPvKb1w+lYmYT0CnGMz/QVFpnE4PvKb1w+lYmYT0CnGMz/QVFpnEc:gnKb1w+OmYT0CnGMz/QVFpnDnKb1w+OA |
MALICIOUS
LUMMA mutex has been found
- xeno-executor.exe (PID: 6820)
Actions looks like stealing of personal data
- xeno-executor.exe (PID: 6820)
Steals credentials from Web Browsers
- xeno-executor.exe (PID: 6820)
SUSPICIOUS
Application launched itself
- xeno-executor.exe (PID: 6544)
Executes application which crashes
- xeno-executor.exe (PID: 6544)
Searches for installed software
- xeno-executor.exe (PID: 6820)
INFO
Checks supported languages
- xeno-executor.exe (PID: 6544)
- xeno-executor.exe (PID: 6820)
Reads the computer name
- xeno-executor.exe (PID: 6544)
- xeno-executor.exe (PID: 6820)
Reads the software policy settings
- xeno-executor.exe (PID: 6820)
- WerFault.exe (PID: 6996)
Creates files in the program directory
- xeno-executor.exe (PID: 6820)
Checks proxy server information
- WerFault.exe (PID: 6996)
Creates files or folders in the user directory
- WerFault.exe (PID: 6996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (81) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.2) |
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.2) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2045:09:06 15:45:24+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 7680 |
| InitializedDataSize: | 1024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x36d2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
131
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6544 | "C:\Users\admin\AppData\Local\Temp\xeno-executor.exe" | C:\Users\admin\AppData\Local\Temp\xeno-executor.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 6552 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | xeno-executor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6820 | "C:\Users\admin\AppData\Local\Temp\xeno-executor.exe" | C:\Users\admin\AppData\Local\Temp\xeno-executor.exe | xeno-executor.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6996 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6544 -s 140 | C:\Windows\SysWOW64\WerFault.exe | xeno-executor.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 648
Read events
3 648
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
19
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6820 | xeno-executor.exe | C:\ProgramData\13056D6BF158F657.dat | — | |
MD5:— | SHA256:— | |||
| 6820 | xeno-executor.exe | C:\ProgramData\A22C49F7F2EC163A.dat | binary | |
MD5:FDDE63730E15DD2E18C540BA52B6A945 | SHA256:40740EAABD14FC0E08D3B5EE340C1E1B372E158F61EF58AEED1EE4B3A3F4492E | |||
| 6996 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_xeno-executor.ex_2fd9be16ea48ae111b33f451c21f94d7aecbe6b_4f36ae49_c614fe75-025e-47c4-af12-01ee5610e4f8\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6996 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\xeno-executor.exe.6544.dmp | — | |
MD5:— | SHA256:— | |||
| 6820 | xeno-executor.exe | C:\ProgramData\C1EFFF6FAFA618D2.dat | binary | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
| 6820 | xeno-executor.exe | C:\ProgramData\13BD99861F3507A7.dat | binary | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
| 6820 | xeno-executor.exe | C:\ProgramData\CC80E06D26DE1311.dat | binary | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 6820 | xeno-executor.exe | C:\ProgramData\4420B607E1B8DC3A.dat | binary | |
MD5:19BA68C3ECBCA72C2B90AFADDE745DC6 | SHA256:8B3758EE2D2C0A07EE7003F902F0667ABE5D9667941F8617EDA3CDF94C78E7B8 | |||
| 6820 | xeno-executor.exe | C:\ProgramData\F0D0CA6BA1164E56.dat | binary | |
MD5:C52CD961FB8188CE1B3D97815AA02978 | SHA256:FE95CAC7B0F158D55188CE091428A8623DB31C927EDA38DC35411D4CB67EA71E | |||
| 6820 | xeno-executor.exe | C:\ProgramData\09933C10C80A6FC9.dat | binary | |
MD5:0FF3BCDD0BE077B9EB8194B5C09F453C | SHA256:225D669E47EB14D8C969799C92AAEF27B66CD984872EA09284E48DB46521E651 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
40
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6996 | WerFault.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6996 | WerFault.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
836 | SIHClient.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
836 | SIHClient.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6680 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 92.123.104.28:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6820 | xeno-executor.exe | 104.21.42.12:443 | pirtyoffensiz.bet | CLOUDFLARENET | — | unknown |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pirtyoffensiz.bet |
| unknown |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |