| File name: | Client.exe |
| Full analysis: | https://app.any.run/tasks/c0f429f3-02d1-4097-82ab-59e3efeb4c50 |
| Verdict: | Malicious activity |
| Threats: | Spyware is a stealth form of malware whose primary objective is to gather sensitive information, such as personal data, login credentials, and financial details, by monitoring user activities and exploiting system vulnerabilities. Spyware operates secretly in the background, evading detection while transmitting collected data to cybercriminals, who can then use it for malicious purposes like identity theft, financial fraud, or espionage. |
| Analysis date: | October 24, 2024, 12:55:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 405A0AFEFCA34384AA557C1F38E1229F |
| SHA1: | E905F9BAF3CEE740A5EB848332FD9DF6BDABE55C |
| SHA256: | 960CF0536840EA58D1323518B344035E74C6119C06457CD9A51B33784371E58D |
| SSDEEP: | 1536:YSSSsK9E4UGqS291swASb2LAhDdLtpqKmY7:YSSG9E4UH7ASb28RR2z |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6764)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 6740)
SUSPICIOUS
Executable content was dropped or overwritten
- Client.exe (PID: 1452)
Application launched itself
- Client.exe (PID: 6044)
- chrome.exe (PID: 7656)
- Client.exe (PID: 7160)
The process executes via Task Scheduler
- chrome.exe (PID: 7656)
Starts CMD.EXE for commands execution
- Client.exe (PID: 1452)
INFO
Reads the computer name
- Client.exe (PID: 6044)
Manual execution by a user
- Client.exe (PID: 7160)
- mspaint.exe (PID: 3644)
Checks supported languages
- Client.exe (PID: 6044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:06:01 15:28:05+00:00 |
| ImageFileCharacteristics: | Executable |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 72704 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x139fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.7.0 |
| ProductVersionNumber: | 1.0.7.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.7.0 |
| InternalName: | Client.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | Client.exe |
| ProductName: | - |
| ProductVersion: | 1.0.7.0 |
| AssemblyVersion: | 1.0.7.0 |
Total processes
151
Monitored processes
14
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1452 | "C:\Users\admin\Desktop\Client.exe" | C:\Users\admin\Desktop\Client.exe | Client.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.7.0 | |||||||||||||||
| 1552 | "C:\Users\admin\chrome.exe" | C:\Users\admin\chrome.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.7.0 | |||||||||||||||
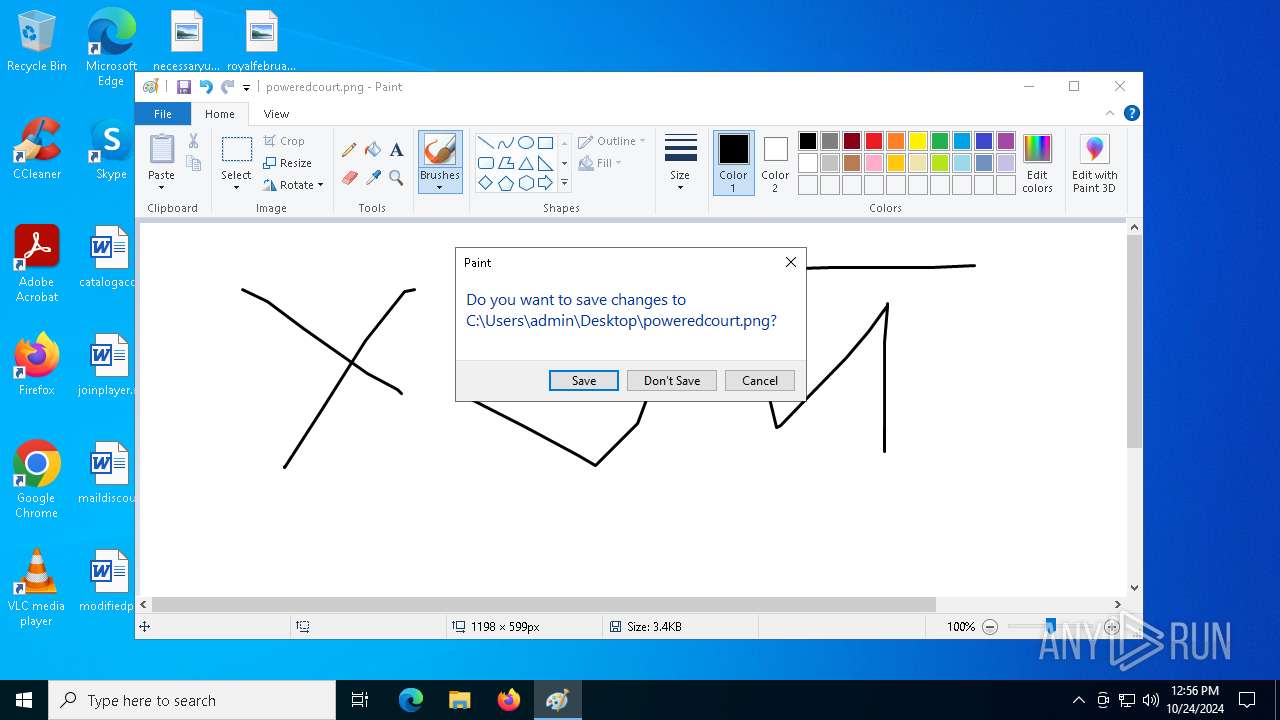
| 3644 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Desktop\poweredcourt.png" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) | |||||||||||||||
| 4476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 5232 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 5452 | "C:\Users\admin\Desktop\Client.exe" | C:\Users\admin\Desktop\Client.exe | Client.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.0.7.0 | |||||||||||||||
| 5532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 5680 | schtasks /create /f /sc minute /mo 1 /tn "chrome.exe" /tr "C:\Users\admin\chrome.exe" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 6044 | "C:\Users\admin\Desktop\Client.exe" | C:\Users\admin\Desktop\Client.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1000 Version: 1.0.7.0 Modules
| |||||||||||||||
| 6184 | schtasks /create /f /sc onlogon /rl highest /tn "chrome.exe" /tr '"C:\Users\admin\chrome.exe"' | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
19
Read events
19
Write events
0
Delete events
0
Modification events
Executable files
5
Suspicious files
121
Text files
31
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1452 | Client.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 5232 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133742481772882744.txt~RF90db0.TMP | — | |
MD5:— | SHA256:— | |||
| 1452 | Client.exe | C:\Users\admin\chrome.exe | executable | |
MD5:405A0AFEFCA34384AA557C1F38E1229F | SHA256:960CF0536840EA58D1323518B344035E74C6119C06457CD9A51B33784371E58D | |||
| 1452 | Client.exe | C:\Windows\chrome.exe | executable | |
MD5:405A0AFEFCA34384AA557C1F38E1229F | SHA256:960CF0536840EA58D1323518B344035E74C6119C06457CD9A51B33784371E58D | |||
| 1452 | Client.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V01.log | binary | |
MD5:486CD8236301DF8C2C9F8D7A2690DC44 | SHA256:E4D68074E135F27345B0581919028FF7FF011D743605967CBBB47BE88D090839 | |||
| 1452 | Client.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.jfm | dbf | |
MD5:D9B564344B4BA22444A4C31F49E7D87E | SHA256:83F5E8553258B4B84D4D1AEDEFC80011C1FC75A3E3D20F67BFEAF1126FC51611 | |||
| 5232 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\INetCache\P26HLZ9S\-UAIppANYxiGpRWJy2NDph4qOEw.gz[1].js | binary | |
MD5:9E527B91C2D8B31B0017B76049B5E4E3 | SHA256:38EDF0F961C1CCB287880B88F12F370775FC65B2E28227EEE215E849CDBE9BBC | |||
| 7160 | Client.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.AAD.BrokerPlugin_cw5n1h2txyewy\Settings\settings.dat | binary | |
MD5:489CBBB9CAC719606BDF6CE66247A67A | SHA256:F87839A2A69190AFF71B5ED996C254F5C9950775E99EB2DFF0134EC0DB989AC2 | |||
| 5232 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\DeviceSearchCache\AppCache133742481772882744.txt.~tmp | text | |
MD5:EBA9D627AEFA0148EA256382E454768F | SHA256:85F02886D53B7427792E54BCEE97D366AD46F78CF90AA25DCC3FAE29ED7FA7F8 | |||
| 5232 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:75DFF7B8874AFF45850BC83BB3B5AED6 | SHA256:A667D89A9AD1F417FF70010DD46408C3652FB1B436C14CC5EE0C243242978513 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
58
DNS requests
25
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 92.123.104.30:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.169:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.33:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
— | — | Misc activity | ET INFO Tunneling Service in DNS Lookup (* .ply .gg) |
— | — | Malware Command and Control Activity Detected | SPYWARE [ANY.RUN] SpyAgent.Bibleoteka TCP Packet |
— | — | Malware Command and Control Activity Detected | SPYWARE [ANY.RUN] SpyAgent.Bibleoteka TCP Packet |
— | — | Malware Command and Control Activity Detected | SPYWARE [ANY.RUN] SpyAgent.Bibleoteka TCP Packet |
— | — | Malware Command and Control Activity Detected | SPYWARE [ANY.RUN] SpyAgent.Bibleoteka TCP Packet |
— | — | Malware Command and Control Activity Detected | SPYWARE [ANY.RUN] SpyAgent.Bibleoteka TCP Packet |
— | — | Malware Command and Control Activity Detected | SPYWARE [ANY.RUN] SpyAgent.Bibleoteka TCP Packet |
— | — | Malware Command and Control Activity Detected | SPYWARE [ANY.RUN] SpyAgent.Bibleoteka TCP Packet |
— | — | Malware Command and Control Activity Detected | SPYWARE [ANY.RUN] SpyAgent.Bibleoteka TCP Packet |