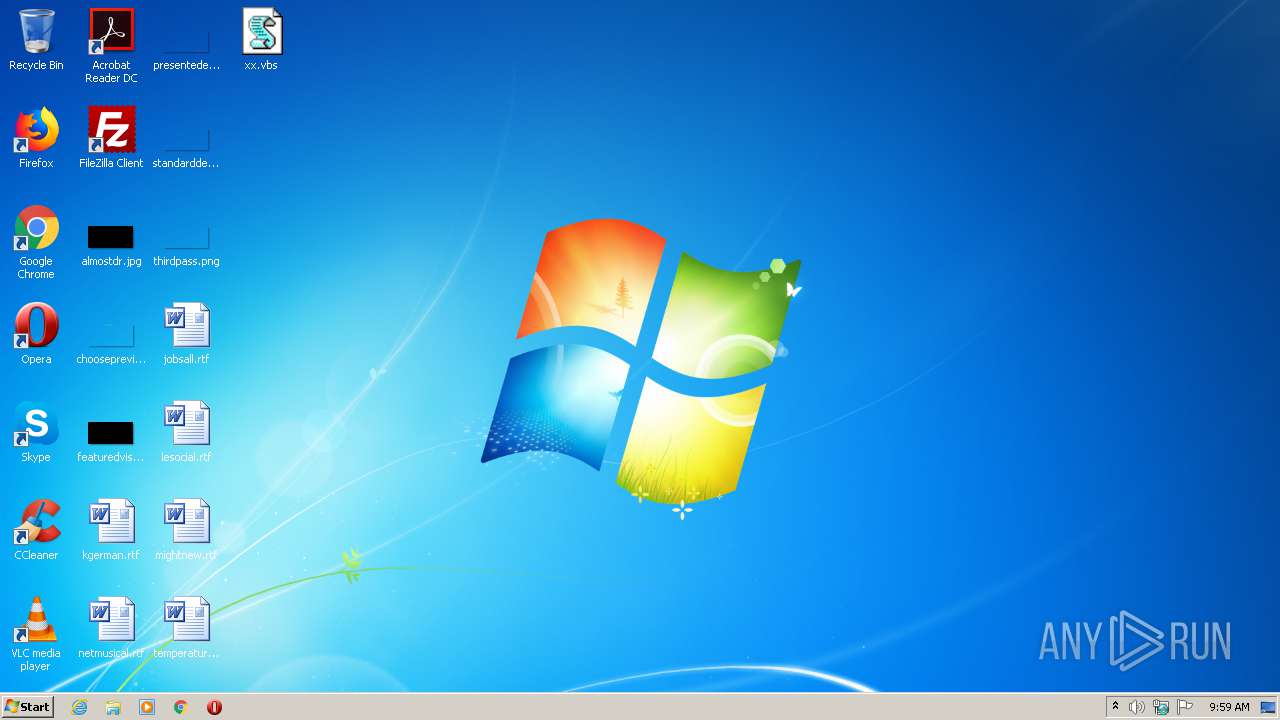
| File name: | xx.vbs |
| Full analysis: | https://app.any.run/tasks/1f9e2e15-ecb0-4cb3-8a40-0ee758e3513d |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | October 20, 2020, 08:58:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 15118F898CF36CD64AA4A04EDEB66928 |
| SHA1: | 8BF2B6788B8FAD031772F2847DE8570371DC37FD |
| SHA256: | 95F6BE98C0BE4C939CC22EC01686227CA8B0D2A1ACD0818544F6C9F37CEE380D |
| SSDEEP: | 96:z5O1k1zPP/w1Ji7Vkxlh2H6UCzyg49RLjAMLg6iprg+j3oIaFDHPSyo:lO1k5PP/wri7VkYcYRLpRsg+j32DHPxo |
MALICIOUS
Downloads executable files from IP
- WScript.exe (PID: 3160)
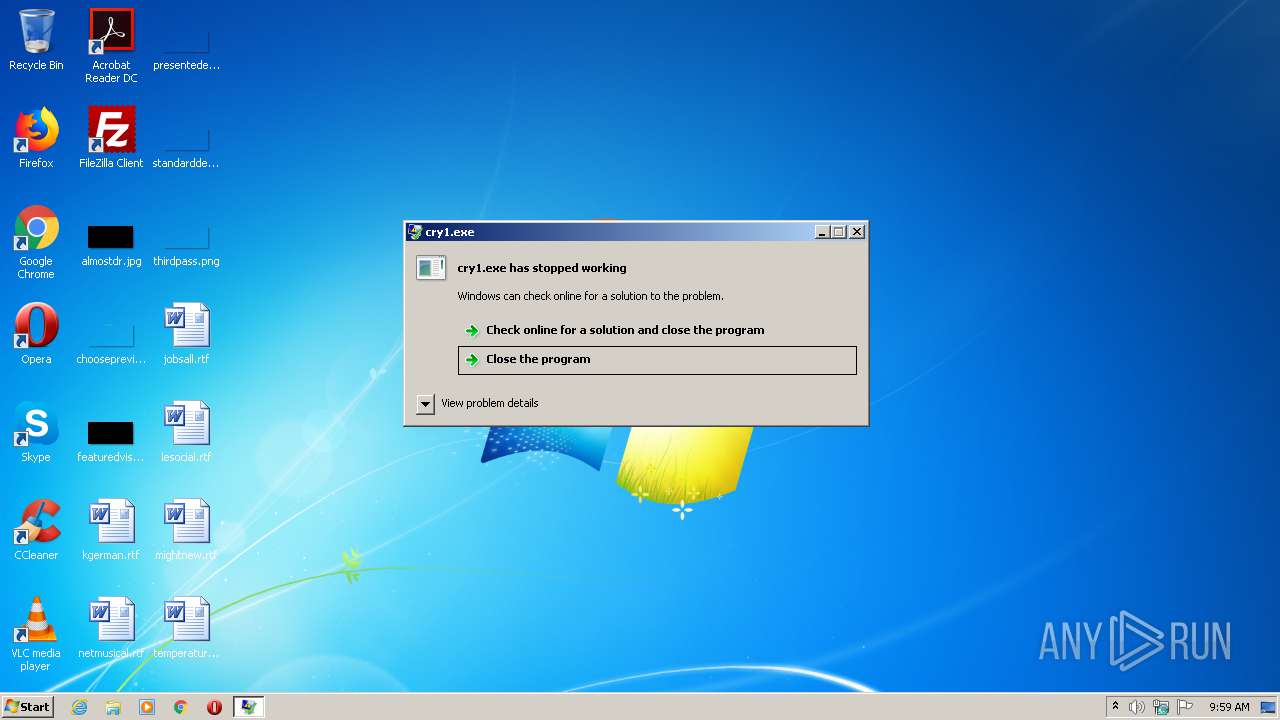
Changes the autorun value in the registry
- cry1.exe (PID: 3444)
Downloads executable files from the Internet
- WScript.exe (PID: 3160)
AVEMARIA was detected
- cry1.exe (PID: 3444)
Connects to CnC server
- cry1.exe (PID: 3444)
Application was dropped or rewritten from another process
- cry1.exe (PID: 3444)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 3160)
Creates files in the program directory
- WScript.exe (PID: 3160)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3160 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\xx.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3444 | "C:\ProgramData\cry1.exe" | C:\ProgramData\cry1.exe | WScript.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
94
Read events
87
Write events
7
Delete events
0
Modification events
| (PID) Process: | (3160) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3160) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3444) cry1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (3444) cry1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (3444) cry1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Images |
Value: C:\ProgramData\cry1.exe | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3160 | WScript.exe | C:\ProgramData\cry1.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
0
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3160 | WScript.exe | GET | 200 | 94.158.245.3:80 | http://94.158.245.3/cry1.exe | unknown | executable | 766 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3444 | cry1.exe | 94.158.245.3:6969 | — | — | — | malicious |
3160 | WScript.exe | 94.158.245.3:80 | — | — | — | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3160 | WScript.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3160 | WScript.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3160 | WScript.exe | Potentially Bad Traffic | ET INFO Request for EXE via WinHTTP M1 |
3160 | WScript.exe | Misc activity | ET INFO Packed Executable Download |
3160 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3160 | WScript.exe | A Network Trojan was detected | ET CURRENT_EVENTS WinHttpRequest Downloading EXE |
3160 | WScript.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
3160 | WScript.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
3444 | cry1.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
3444 | cry1.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
2 ETPRO signatures available at the full report