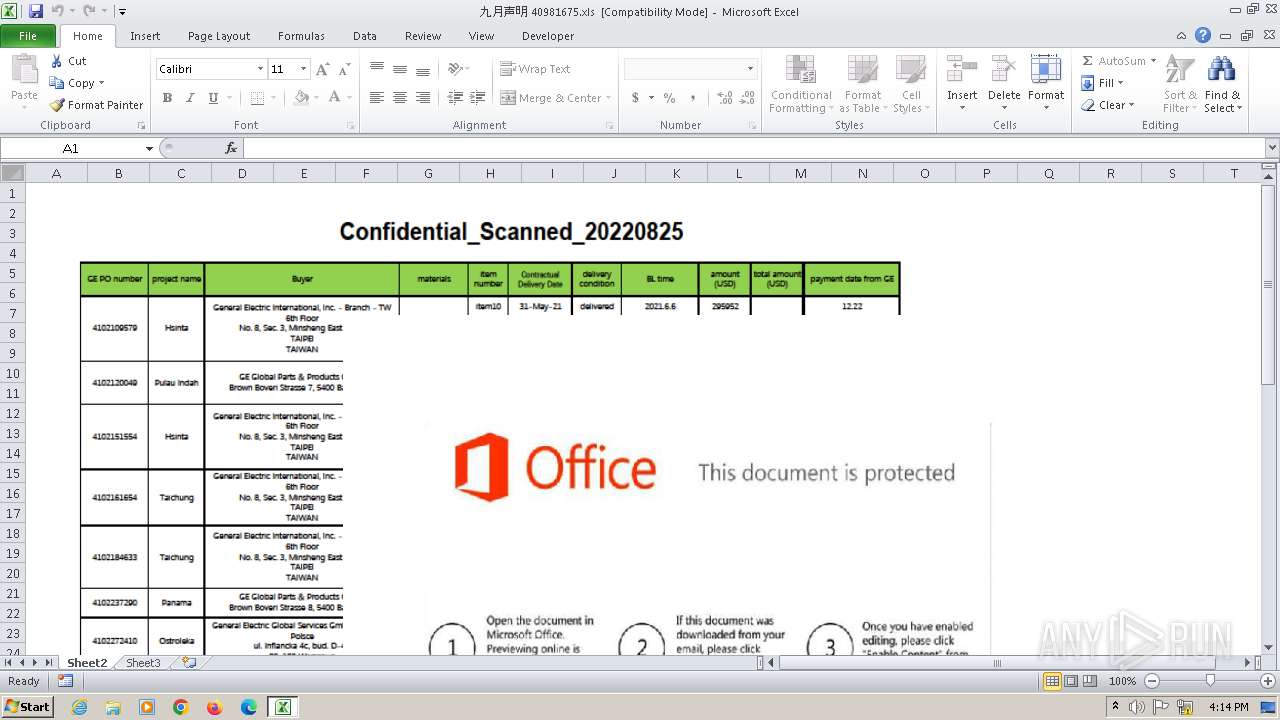
| File name: | 九月声明 40981675.xls |
| Full analysis: | https://app.any.run/tasks/12a00a62-2df1-43ce-9b9a-a29b18bbaca9 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 18, 2023, 16:13:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Name of Creating Application: Microsoft Excel, Create Time/Date: Sat Sep 16 01:00:00 2006, Last Saved Time/Date: Tue Oct 17 16:56:09 2023, Security: 0 |
| MD5: | BEBDE97040EEECB866DB4F6EFF2A0F3C |
| SHA1: | EEF9D50A9EE55ACC5C4C389D5A0F3105A14CCF96 |
| SHA256: | 95F512905D4B5EBE18EC19E3A3B2DFFBD727E91FDC0177667512B44FC7F5D857 |
| SSDEEP: | 49152:aTlbNqjBHZdFtSgJLP6J5sAT1vNyUOF+4u31a0mF9EdFi3LaCDNzYsAW5sAT1vNZ:exqJXSgJLP67sAkFkWLZDR1JsA+FVWL3 |
MALICIOUS
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 2508)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 2508)
Application was dropped or rewritten from another process
- audiodgse.exe (PID: 848)
- audiodgse.exe (PID: 2844)
Drops the executable file immediately after the start
- EQNEDT32.EXE (PID: 2508)
FORMBOOK has been detected (YARA)
- msdt.exe (PID: 1696)
SUSPICIOUS
Reads the Internet Settings
- EQNEDT32.EXE (PID: 2508)
Connects to the server without a host name
- EQNEDT32.EXE (PID: 2508)
Process requests binary or script from the Internet
- EQNEDT32.EXE (PID: 2508)
Application launched itself
- audiodgse.exe (PID: 848)
Starts CMD.EXE for commands execution
- msdt.exe (PID: 1696)
INFO
Reads the machine GUID from the registry
- EQNEDT32.EXE (PID: 2508)
- audiodgse.exe (PID: 848)
Reads the computer name
- EQNEDT32.EXE (PID: 2508)
- audiodgse.exe (PID: 848)
- audiodgse.exe (PID: 2844)
Checks supported languages
- EQNEDT32.EXE (PID: 2508)
- audiodgse.exe (PID: 848)
- audiodgse.exe (PID: 2844)
Checks proxy server information
- EQNEDT32.EXE (PID: 2508)
Creates files or folders in the user directory
- EQNEDT32.EXE (PID: 2508)
Manual execution by a user
- autochk.exe (PID: 312)
- autochk.exe (PID: 2420)
- autochk.exe (PID: 2228)
- autochk.exe (PID: 2472)
- autochk.exe (PID: 2952)
- autochk.exe (PID: 2800)
- msdt.exe (PID: 1696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(1696) msdt.exe
C2www.nightoracle.com/rs10/
Strings (79)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
f-end
Decoy C2 (64)starryallure.com
mania-31.online
baba-bt-top1.buzz
jwilkinsartscapeinc.com
tallerhazop.com
lulu013.com
pontoimediato.com
stmc-company.com
thesoftwarepractitioner.com
makemoneywithsherrie.com
algaroba.com
smartbookmarks.info
burneysaw.com
fftsxxx.top
hvr998.com
sofisticars.store
clickit.fun
couches-sofas-16683.bond
ikkasolutions.com
oakvisa.com
totalkfood.com
guillaumecarreau.com
biomagnetismocolombia.com
jrszhiboz.com
rewmio.xyz
willowliy.com
calm-plants.com
robertjamesfineclothing.com
wgardsgm.live
dngbdk9jpusxpwr.com
slycepicklegear.com
mtauratarnt.com
simolified.com
mekkamochi.com
deeprootedleader.com
container-houses-vn.click
roundaboutlogistics.com
m-baer.com
electric-cars-19095.bond
destinydinos.com
taxretentionstrategiesgroup.com
zg9tywlubmftzw5ldzi0mdm.com
cleaning-products-29334.bond
metaastrologia.com
practicaloutsource.com
w1nb74.top
just-one.info
cryptarrow.com
omarshafie.online
latitudeinformatics.com
fhstbanknigeria.com
hdlive7.live
laserhairremovalkit.com
into-org.com
kzjsm.com
juara102-azura.com
digitsum.com
cabins-prefab.online
allisonparlinart.com
cpsgrantstream.com
everythingbutthetruck.com
w6k3v.com
alfarizkigrup.com
gs3ekdj3ixe.asia
TRiD
| .xls | | | Microsoft Excel sheet (31.2) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (25.5) |
EXIF
FlashPix
| Author: | - |
|---|---|
| LastModifiedBy: | - |
| Software: | Microsoft Excel |
| CreateDate: | 2006:09:16 00:00:00 |
| ModifyDate: | 2023:10:17 15:56:09 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| AppVersion: | 12 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
| CompObjUserTypeLen: | 38 |
| CompObjUserType: | Microsoft Office Excel 2003 Worksheet |
Total processes
43
Monitored processes
12
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Windows\SysWOW64\autochk.exe" | C:\Windows\SysWOW64\autochk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto Check Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 848 | "C:\Users\admin\AppData\Roaming\audiodgse.exe" | C:\Users\admin\AppData\Roaming\audiodgse.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Description: TriviaNow Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.4756.1000 Modules
| |||||||||||||||
| 1512 | /c del "C:\Users\admin\AppData\Roaming\audiodgse.exe" | C:\Windows\SysWOW64\cmd.exe | — | msdt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1696 | "C:\Windows\SysWOW64\msdt.exe" | C:\Windows\SysWOW64\msdt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Formbook(PID) Process(1696) msdt.exe C2www.nightoracle.com/rs10/ Strings (79)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start f-end Decoy C2 (64)starryallure.com mania-31.online baba-bt-top1.buzz jwilkinsartscapeinc.com tallerhazop.com lulu013.com pontoimediato.com stmc-company.com thesoftwarepractitioner.com makemoneywithsherrie.com algaroba.com smartbookmarks.info burneysaw.com fftsxxx.top hvr998.com sofisticars.store clickit.fun couches-sofas-16683.bond ikkasolutions.com oakvisa.com totalkfood.com guillaumecarreau.com biomagnetismocolombia.com jrszhiboz.com rewmio.xyz willowliy.com calm-plants.com robertjamesfineclothing.com wgardsgm.live dngbdk9jpusxpwr.com slycepicklegear.com mtauratarnt.com simolified.com mekkamochi.com deeprootedleader.com container-houses-vn.click roundaboutlogistics.com m-baer.com electric-cars-19095.bond destinydinos.com taxretentionstrategiesgroup.com zg9tywlubmftzw5ldzi0mdm.com cleaning-products-29334.bond metaastrologia.com practicaloutsource.com w1nb74.top just-one.info cryptarrow.com omarshafie.online latitudeinformatics.com fhstbanknigeria.com hdlive7.live laserhairremovalkit.com into-org.com kzjsm.com juara102-azura.com digitsum.com cabins-prefab.online allisonparlinart.com cpsgrantstream.com everythingbutthetruck.com w6k3v.com alfarizkigrup.com gs3ekdj3ixe.asia | |||||||||||||||
| 2228 | "C:\Windows\SysWOW64\autochk.exe" | C:\Windows\SysWOW64\autochk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto Check Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | "C:\Windows\SysWOW64\autochk.exe" | C:\Windows\SysWOW64\autochk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto Check Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Windows\SysWOW64\autochk.exe" | C:\Windows\SysWOW64\autochk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto Check Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2800 | "C:\Windows\SysWOW64\autochk.exe" | C:\Windows\SysWOW64\autochk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto Check Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 262
Read events
2 213
Write events
42
Delete events
7
Modification events
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: On | |||
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: On | |||
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: On | |||
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: On | |||
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: On | |||
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: On | |||
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: On | |||
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: On | |||
| (PID) Process: | (1492) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: On | |||
Executable files
2
Suspicious files
8
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1492 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRBD5F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1492 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DCB66A7B.emf | binary | |
MD5:6B54269F3B0EB61EAFA903D15B49F68F | SHA256:12811A4AB97A1A6764709C0D298A7D5EF9C58102A9AAF7C23E18024BB6267B59 | |||
| 1492 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\49B36A40.emf | binary | |
MD5:AB3C71DADD57C96DE74236A677761633 | SHA256:BE0B0602293E0078A54D37F29B03C21091D4450EDCF827A577D376E670A2C445 | |||
| 1492 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9AB1E541.emf | binary | |
MD5:A01B9617553432807B9B58025B338D97 | SHA256:7A0426ED2E2349916969FF7087C0F76089FB8CE7F4627F3D11CCBC1AAEFCEDCE | |||
| 1492 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C3B9DFE2.emf | binary | |
MD5:4A103FC1809C8EA381D2ACB5380EF4F6 | SHA256:1AB8F5ABD845FFD0C61A61BB09BFCF20569B80B4496BCCB58C623753CF40485C | |||
| 1492 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1FB98A4E.emf | binary | |
MD5:B10FFD43A43F55F6B43167A45E2F5157 | SHA256:6952BA72EB75E7D085B25D394D7CB8942710E24347E24F1D523A88BB0BE14C98 | |||
| 2508 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\audiodgse.exe | executable | |
MD5:89E7A2A15D1A8EAFF2F2570F39532C1C | SHA256:356025114ED69404543712922762409938A37D54CABD294C661D844CC547FC52 | |||
| 1492 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B2519F7.emf | binary | |
MD5:D69C22A341E111FEEA69DF6D8C655D60 | SHA256:05B2053BF1D070D6034B45CD79B54D80DA3C6D88D016671A345E75048B1A68DB | |||
| 1492 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E259BB8C.emf | binary | |
MD5:35E141964E2698FC12D087516D116C9A | SHA256:6A3A2ADDC5D6B554EED64B7C24B699E09BCF019E4F42AB14EC6D40C7CB749538 | |||
| 2508 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\K78MRVB5\smss[1].exe | executable | |
MD5:89E7A2A15D1A8EAFF2F2570F39532C1C | SHA256:356025114ED69404543712922762409938A37D54CABD294C661D844CC547FC52 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
0
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2508 | EQNEDT32.EXE | GET | 200 | 103.72.68.128:80 | http://103.72.68.128/T1710W/smss.exe | unknown | executable | 1.04 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2508 | EQNEDT32.EXE | 103.72.68.128:80 | — | — | — | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2508 | EQNEDT32.EXE | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2508 | EQNEDT32.EXE | Potentially Bad Traffic | ET HUNTING Suspicious smss.exe in URI |
2508 | EQNEDT32.EXE | A Network Trojan was detected | ET MALWARE Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
2508 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2508 | EQNEDT32.EXE | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2508 | EQNEDT32.EXE | A Network Trojan was detected | ET MALWARE Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
1 ETPRO signatures available at the full report