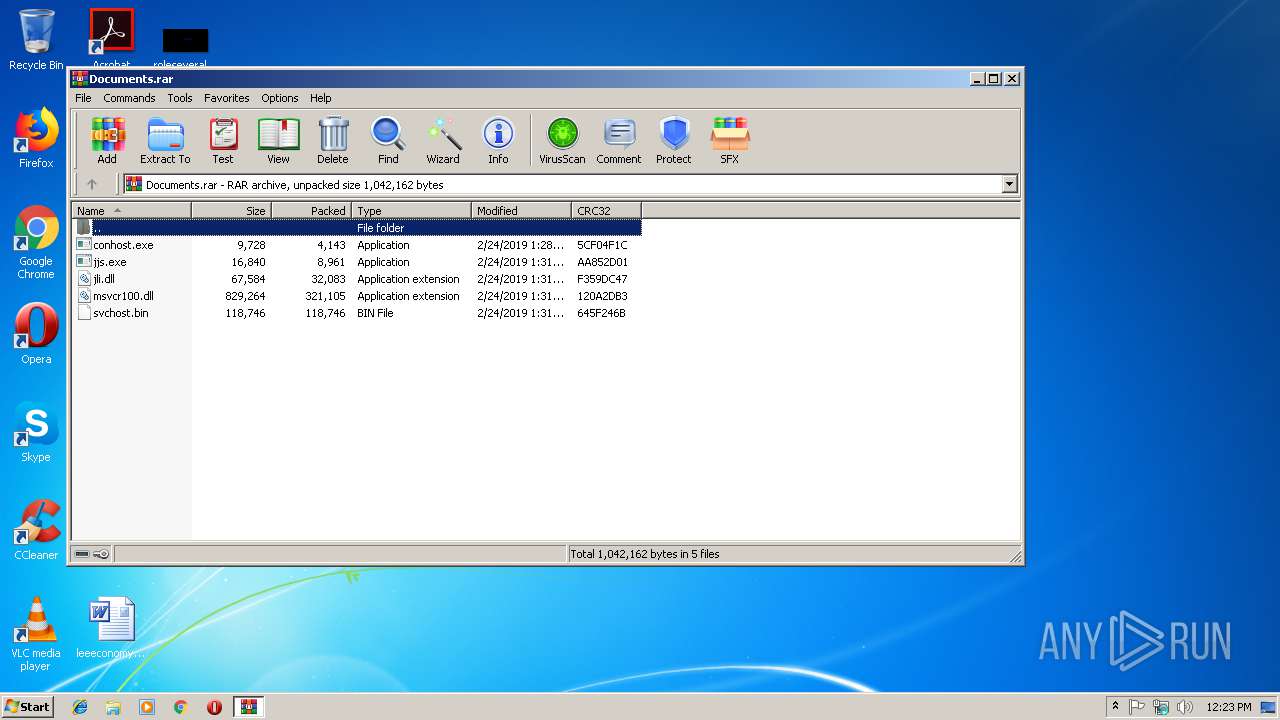
| File name: | Documents.rar |
| Full analysis: | https://app.any.run/tasks/9bd9e488-bf32-40c0-86cc-552adcd8ac05 |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
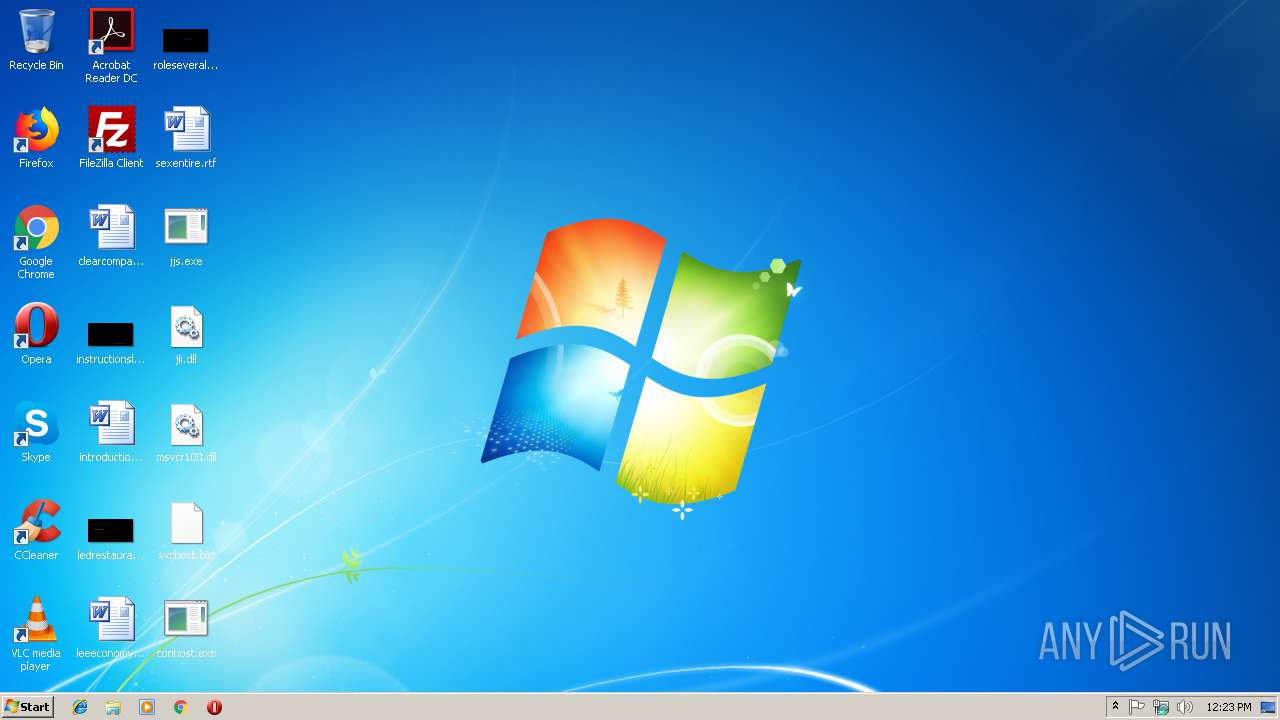
| Analysis date: | March 19, 2019, 12:23:21 |
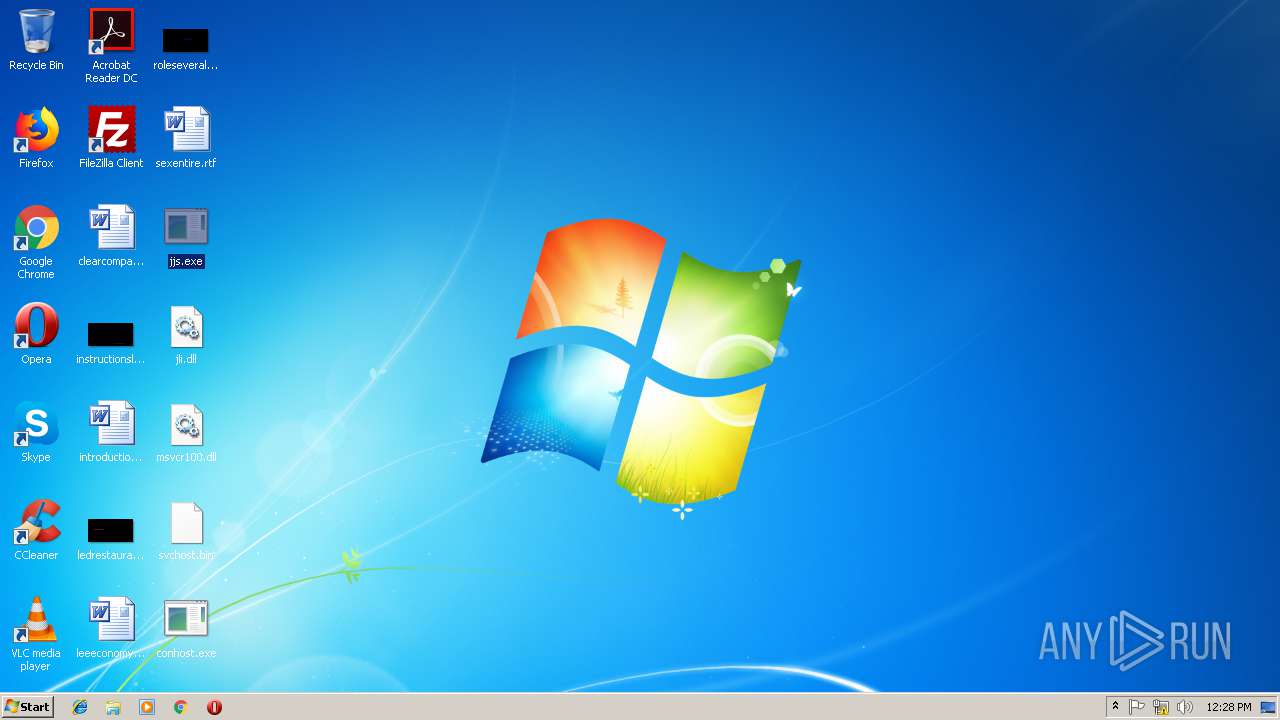
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | CAA6BB46CA715449FDC0ECA3ABE727DD |
| SHA1: | 7D6E1D9307295F698E35791000318B825FD77ADB |
| SHA256: | 95ECD23E496FD99C5F77F61F9B5C6743523AF4E1FB14D120702B12F70A325137 |
| SSDEEP: | 12288:P0fUBbp0d9AUwIaig2+5tYq1i/mHTkWIwm:0GUDQ2g6Ki/mzkum |
MALICIOUS
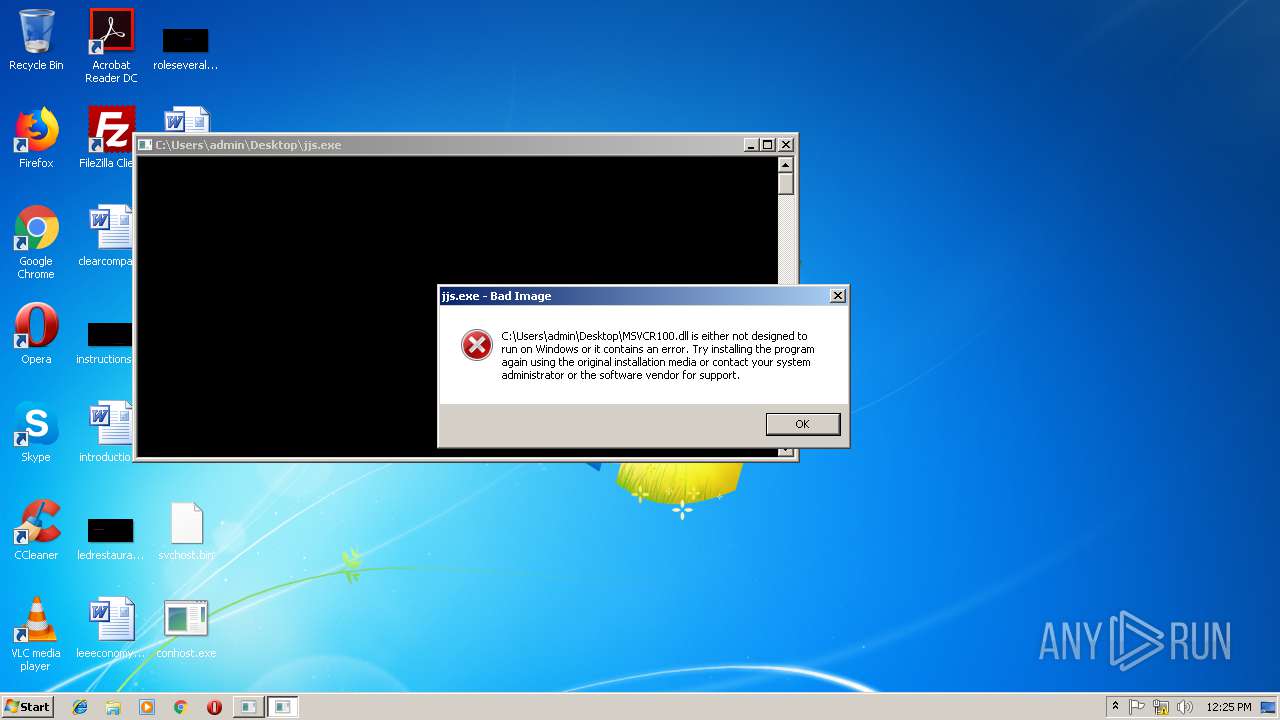
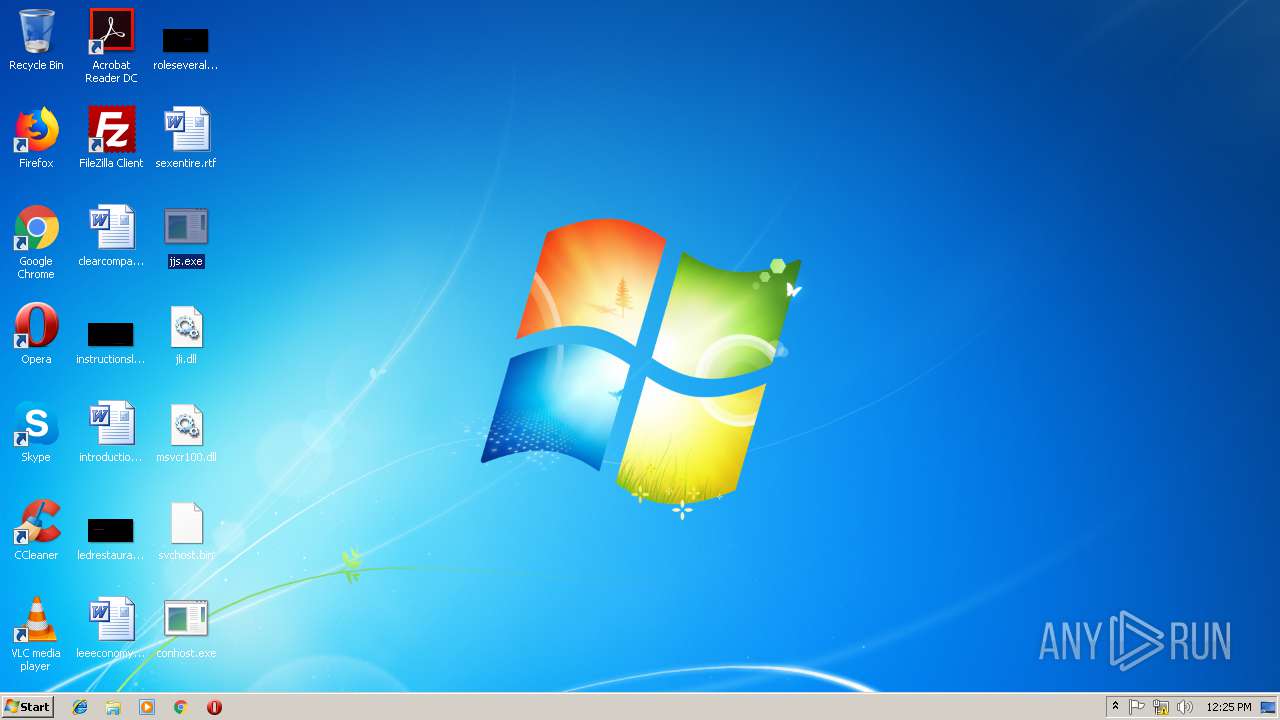
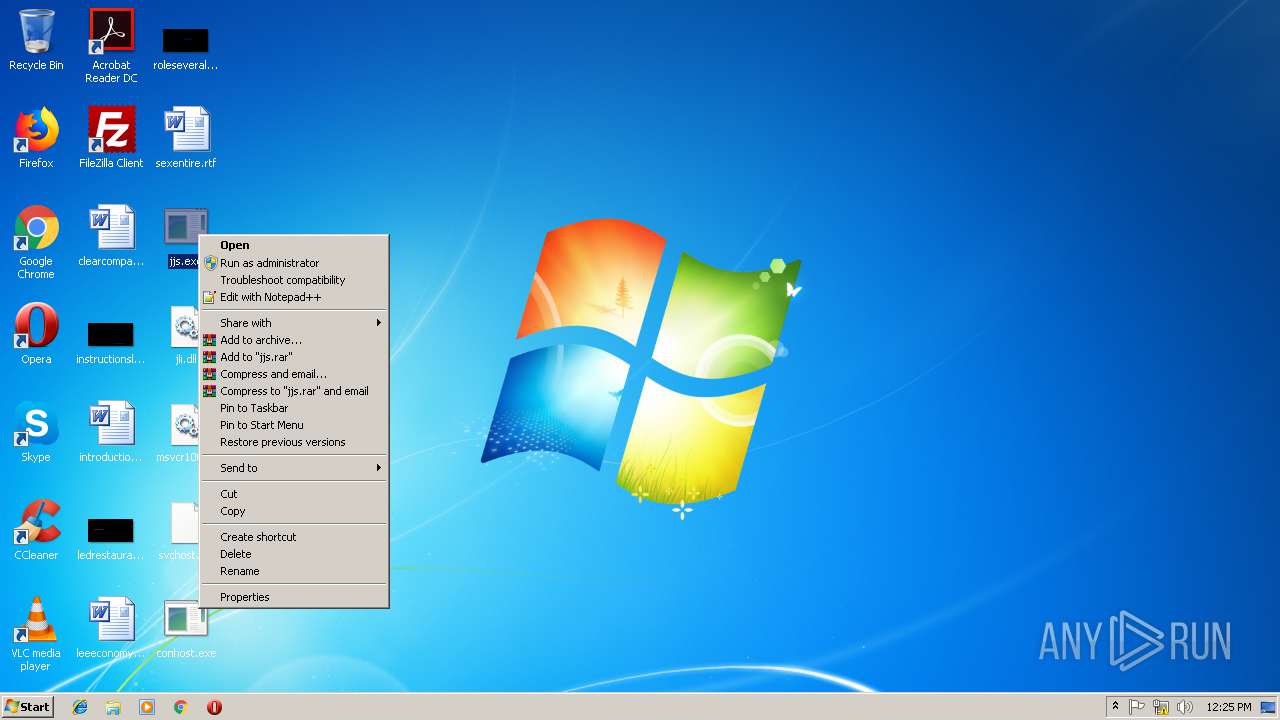
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1768)
- jjs.exe (PID: 2132)
- jjs.exe (PID: 3400)
Application was dropped or rewritten from another process
- jjs.exe (PID: 2132)
- jjs.exe (PID: 3400)
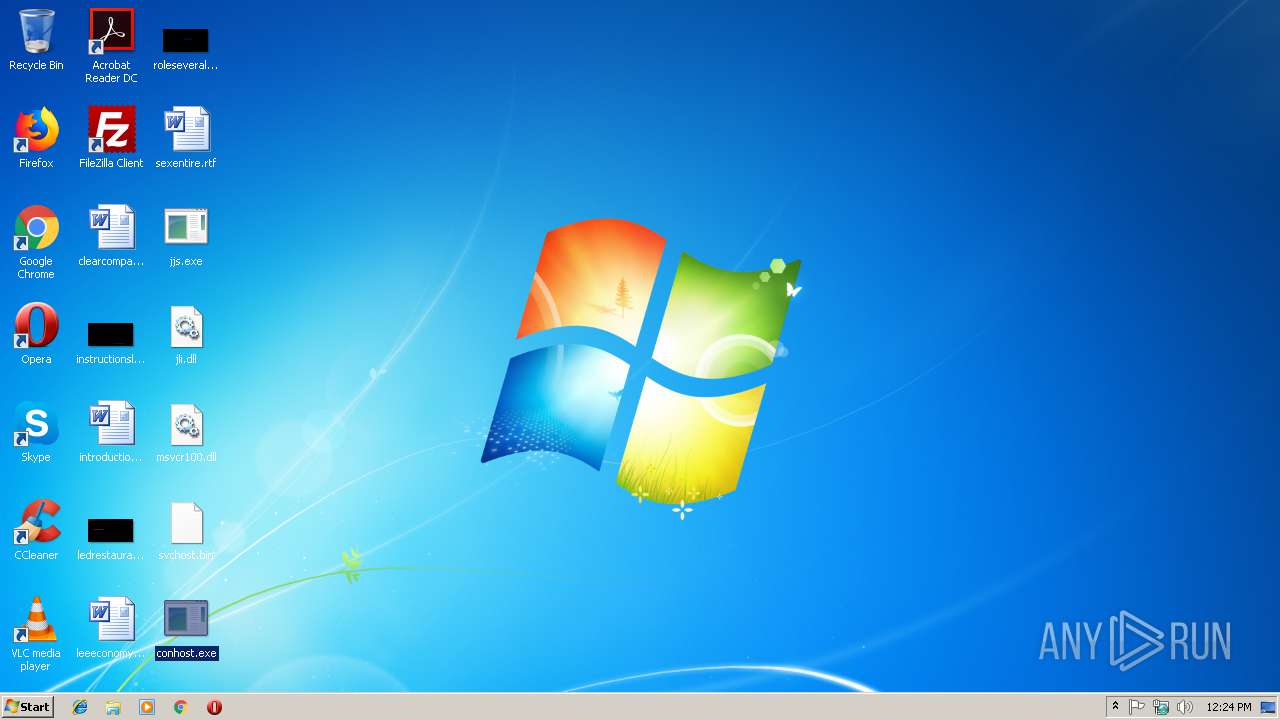
- conhost.exe (PID: 2324)
QUASAR was detected
- conhost.exe (PID: 2324)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3476)
Checks for external IP
- conhost.exe (PID: 2324)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1768 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
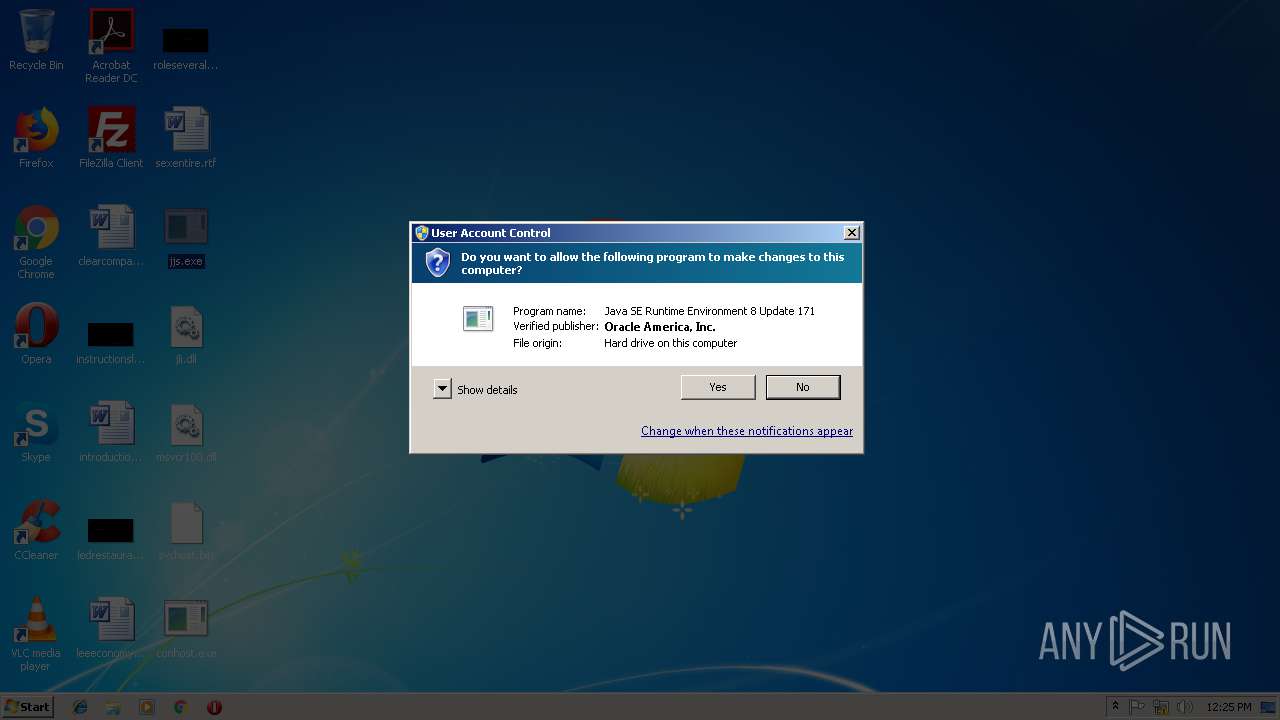
| 2132 | "C:\Users\admin\Desktop\jjs.exe" | C:\Users\admin\Desktop\jjs.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 3221226330 Version: 8.0.1710.11 Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\Desktop\conhost.exe" | C:\Users\admin\Desktop\conhost.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 控制台窗口主进程 Exit code: 0 Version: 10.0.17134.1 Modules
| |||||||||||||||
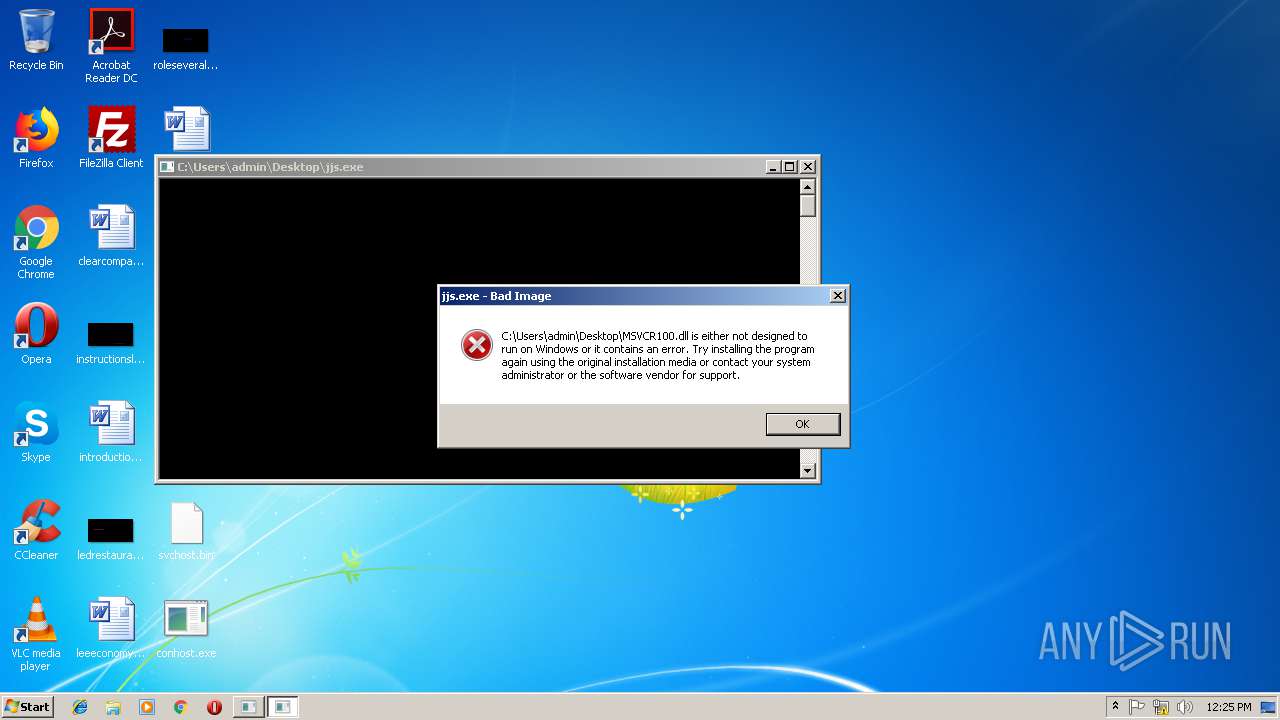
| 3400 | "C:\Users\admin\Desktop\jjs.exe" | C:\Users\admin\Desktop\jjs.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 3221226330 Version: 8.0.1710.11 Modules
| |||||||||||||||
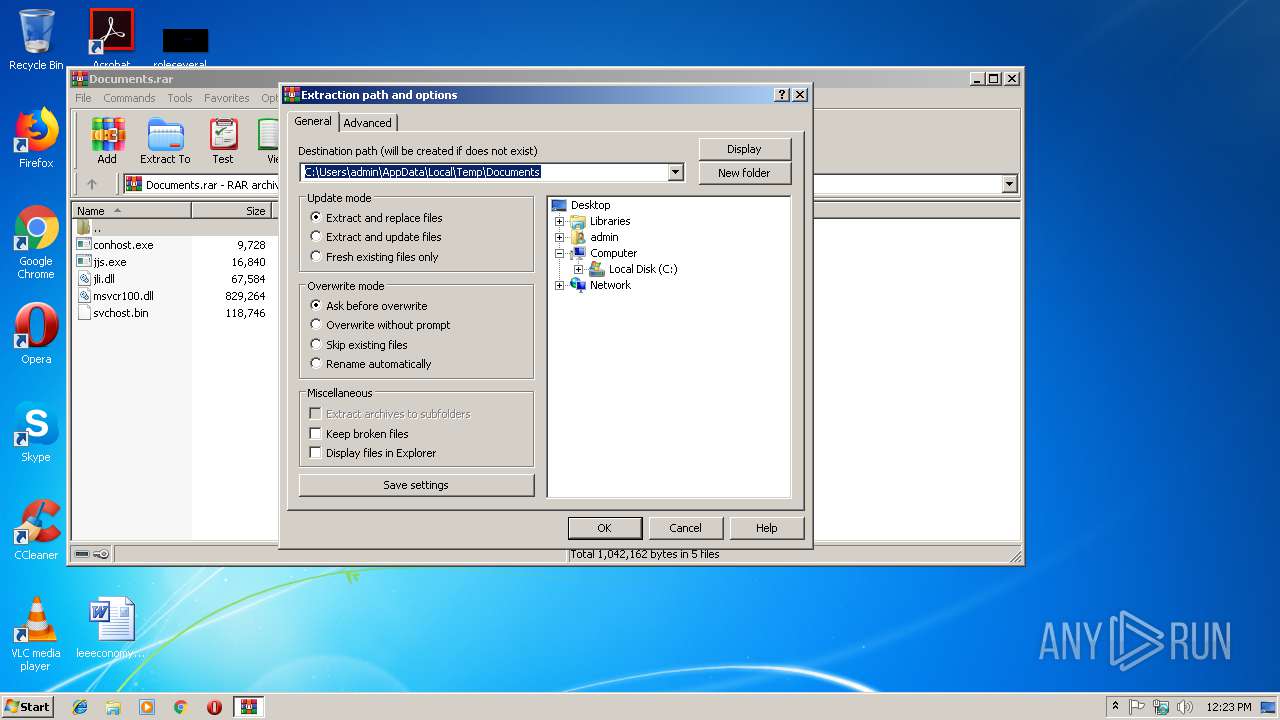
| 3476 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Documents.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
520
Read events
475
Write events
45
Delete events
0
Modification events
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Documents.rar | |||
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
4
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2324 | conhost.exe | C:\Users\admin\AppData\Local\Temp\Cab583E.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | conhost.exe | C:\Users\admin\AppData\Local\Temp\Tar583F.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | conhost.exe | C:\Users\admin\AppData\Local\Temp\Cab5850.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | conhost.exe | C:\Users\admin\AppData\Local\Temp\Tar5851.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | conhost.exe | C:\Users\admin\AppData\Local\Temp\Cab58CF.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | conhost.exe | C:\Users\admin\AppData\Local\Temp\Tar58D0.tmp | — | |
MD5:— | SHA256:— | |||
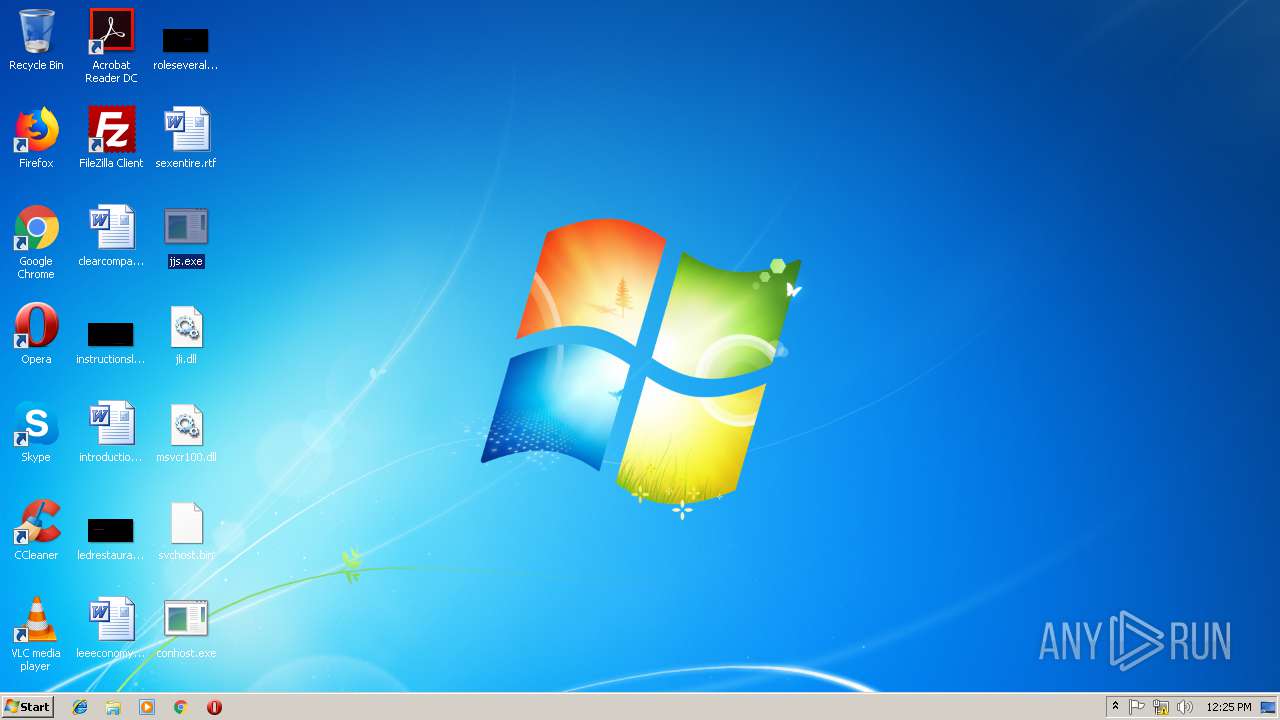
| 3476 | WinRAR.exe | C:\Users\admin\Desktop\svchost.bin | binary | |
MD5:— | SHA256:— | |||
| 3476 | WinRAR.exe | C:\Users\admin\Desktop\conhost.exe | executable | |
MD5:— | SHA256:— | |||
| 3476 | WinRAR.exe | C:\Users\admin\Desktop\jjs.exe | executable | |
MD5:64FDBD98584331982A15B1F2DF7F08DA | SHA256:B5DE10A0091B7AAF491BDB810BCE6DAB3F6B4A1C7A917722B5DE014E4A08B6EB | |||
| 2324 | conhost.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2324 | conhost.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 312 b | malicious |
2324 | conhost.exe | GET | 200 | 27.102.127.80:80 | http://ffca.caibi379.com/rwjh/qtinfo.txt | KR | text | 4.49 Mb | malicious |
2324 | conhost.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2324 | conhost.exe | 27.102.127.80:80 | ffca.caibi379.com | DAOU TECHNOLOGY | KR | unknown |
2324 | conhost.exe | 27.102.127.80:443 | ffca.caibi379.com | DAOU TECHNOLOGY | KR | unknown |
2324 | conhost.exe | 185.194.141.58:80 | ip-api.com | netcup GmbH | DE | unknown |
2324 | conhost.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ffca.caibi379.com |
| malicious |
ip-api.com |
| malicious |
cahe.microsofts.org |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2324 | conhost.exe | Misc activity | SUSPICIOUS [PTsecurity] Executable base64 Payload |
2324 | conhost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2324 | conhost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Quasar 1.3 RAT IP Lookup ip-api.com (HTTP headeer) |
1 ETPRO signatures available at the full report