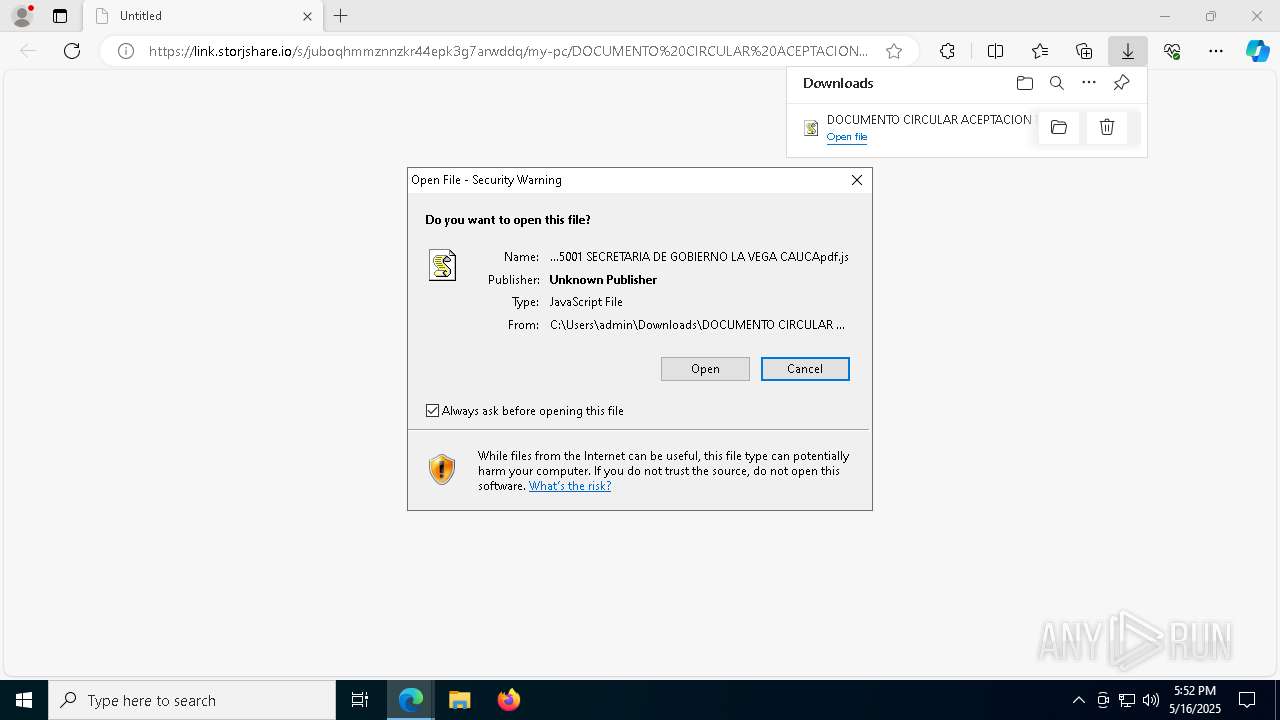
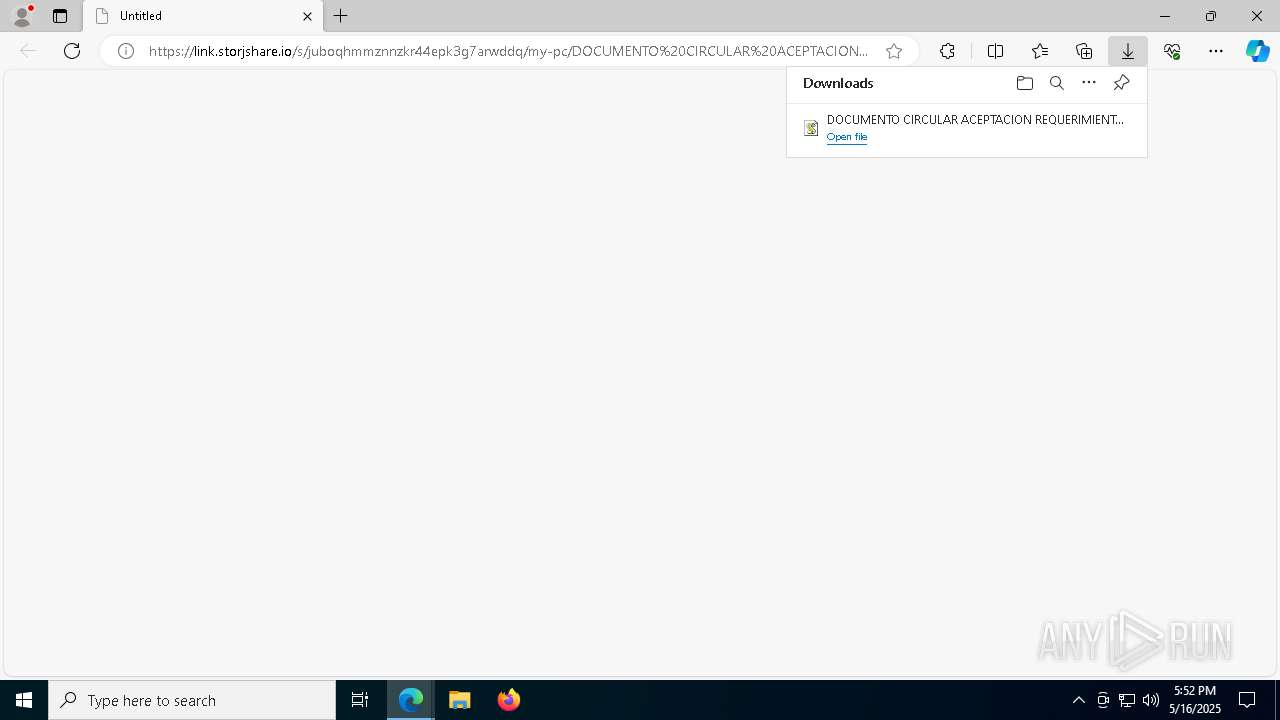
| URL: | https://link.storjshare.io/s/juboqhmmznnzkr44epk3g7arwddq/my-pc/DOCUMENTO%20CIRCULAR%20ACEPTACION%20REQUERIMIENTO%20POR%20INCUMPLIMIENTO%20RADICADO%20G20251605001%20SECRETARIA%20DE%20GOBIERNO%20LA%20VEGA%20CAUCApdf.js?download=1 |
| Full analysis: | https://app.any.run/tasks/02c87147-56e8-4a06-b064-3d880ea64b39 |
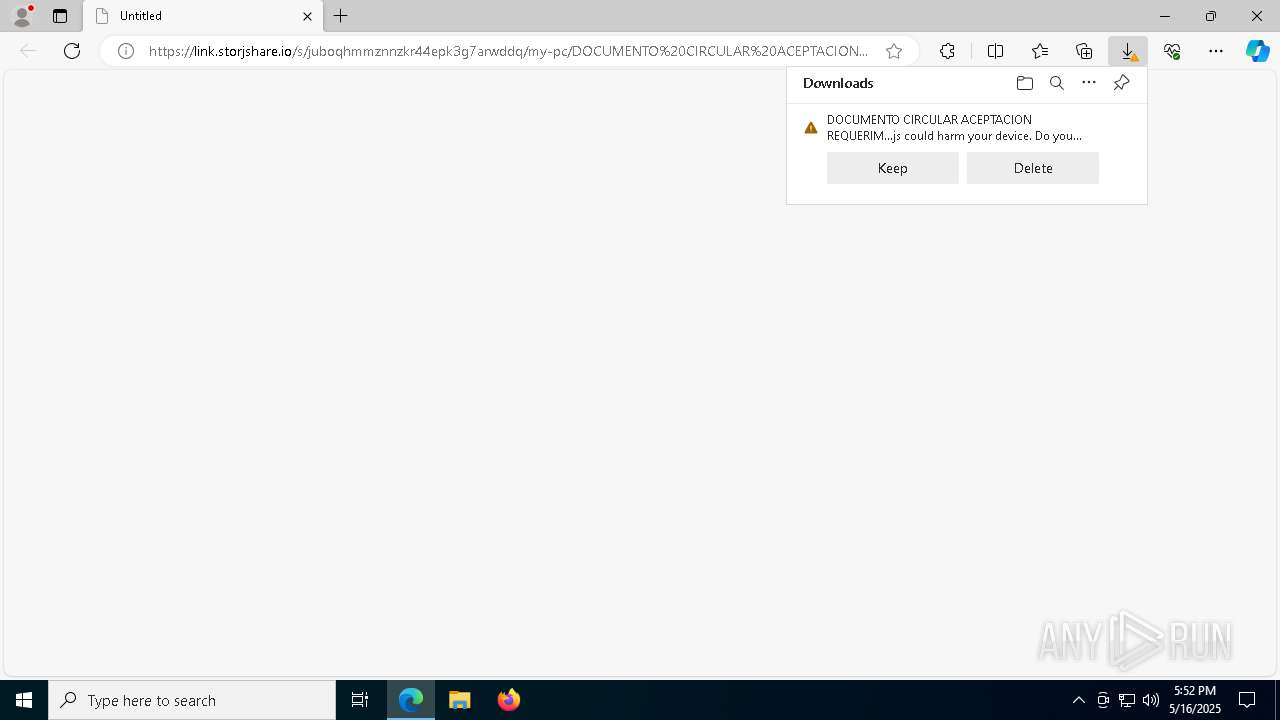
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 16, 2025, 17:52:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7127A66FA9A513092072823FE57375AD |
| SHA1: | E026FEBFB82A2CB63FD55831895D695C4046C71C |
| SHA256: | 95E75A6F8138966B5A36BF359D93E848265D02DFB4C0D718EA585BB9C27C2493 |
| SSDEEP: | 6:2Mgi4wiByBUTyBmirZ9ePxrUDwXnXBaC87hbXV0TrWAn:2MgiTmSFX4rUcoxNzK7 |
MALICIOUS
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 9116)
- wscript.exe (PID: 6028)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 9116)
- wscript.exe (PID: 6028)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 9116)
- wscript.exe (PID: 6028)
Run PowerShell with an invisible window
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Starts Visual C# compiler
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Steals credentials from Web Browsers
- csc.exe (PID: 6184)
Actions looks like stealing of personal data
- csc.exe (PID: 6184)
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 6184)
SUSPICIOUS
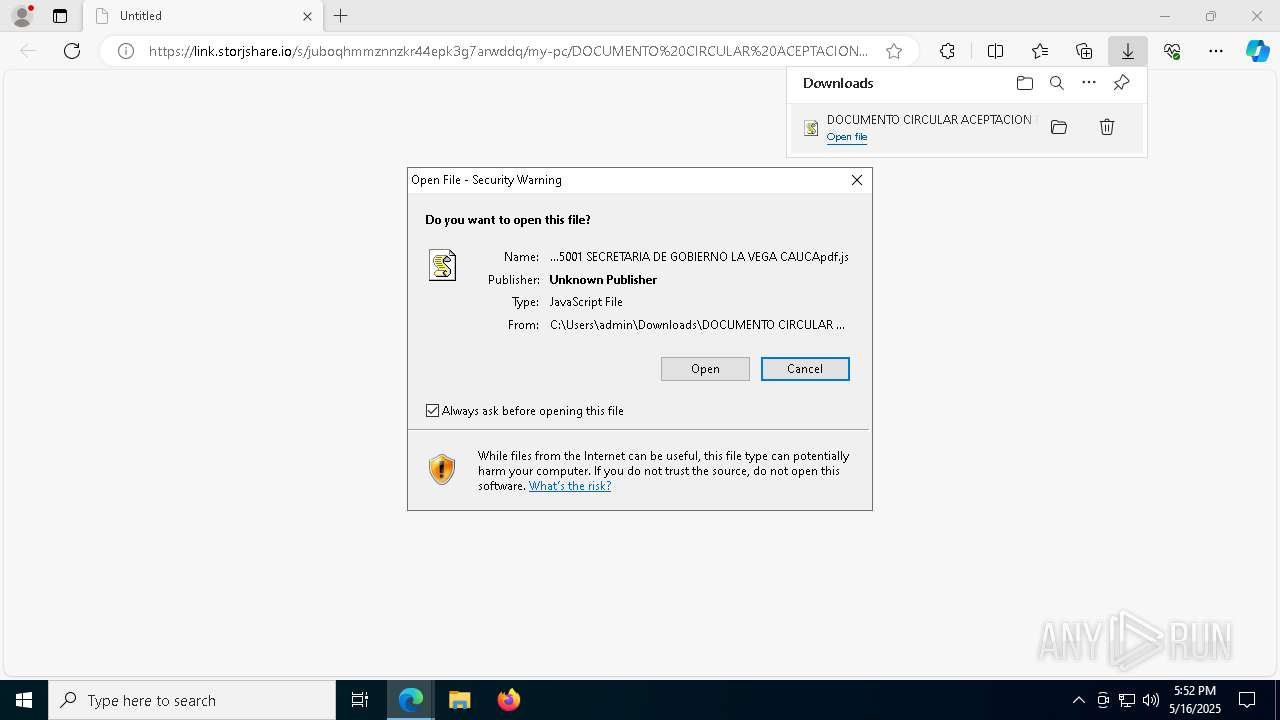
The process executes JS scripts
- msedge.exe (PID: 536)
Potential Corporate Privacy Violation
- wscript.exe (PID: 9116)
- powershell.exe (PID: 9192)
- wscript.exe (PID: 6028)
- powershell.exe (PID: 8348)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 9116)
- wscript.exe (PID: 6028)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 9116)
- wscript.exe (PID: 6028)
Executes script without checking the security policy
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 9116)
- wscript.exe (PID: 6028)
Base64-obfuscated command line is found
- wscript.exe (PID: 9116)
- wscript.exe (PID: 6028)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 9116)
- wscript.exe (PID: 6028)
Runs shell command (SCRIPT)
- wscript.exe (PID: 9116)
- wscript.exe (PID: 6028)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 2692)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 9192)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 6184)
Connects to unusual port
- csc.exe (PID: 6184)
INFO
Application launched itself
- msedge.exe (PID: 536)
Reads Environment values
- identity_helper.exe (PID: 8508)
Checks supported languages
- identity_helper.exe (PID: 8508)
- csc.exe (PID: 6184)
- csc.exe (PID: 4268)
Reads the computer name
- identity_helper.exe (PID: 8508)
- csc.exe (PID: 6184)
- csc.exe (PID: 4268)
Reads Microsoft Office registry keys
- msedge.exe (PID: 536)
Checks proxy server information
- wscript.exe (PID: 9116)
- powershell.exe (PID: 9192)
- wscript.exe (PID: 6028)
- powershell.exe (PID: 8348)
Disables trace logs
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Reads the machine GUID from the registry
- csc.exe (PID: 6184)
- csc.exe (PID: 4268)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Gets data length (POWERSHELL)
- powershell.exe (PID: 9192)
- powershell.exe (PID: 8348)
Reads the software policy settings
- csc.exe (PID: 6184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
41
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://link.storjshare.io/s/juboqhmmznnzkr44epk3g7arwddq/my-pc/DOCUMENTO%20CIRCULAR%20ACEPTACION%20REQUERIMIENTO%20POR%20INCUMPLIMIENTO%20RADICADO%20G20251605001%20SECRETARIA%20DE%20GOBIERNO%20LA%20VEGA%20CAUCApdf.js?download=1" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2692 | "C:\Windows\System32\cmd.exe" /C copy *.js "C:\Users\Public\Downloads\Ethiopia.js" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=5416 --field-trial-handle=2284,i,3754643006336546635,18229972398587617603,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4268 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6028 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\DOCUMENTO CIRCULAR ACEPTACION REQUERIMIENTO POR INCUMPLIMIENTO RADICADO G20251605001 SECRETARIA DE GOBIERNO LA VEGA CAUCApdf.js" | C:\Windows\System32\wscript.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 6184 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6564 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5948 --field-trial-handle=2284,i,3754643006336546635,18229972398587617603,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 7012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x308,0x30c,0x310,0x258,0x318,0x7ffc88765fd8,0x7ffc88765fe4,0x7ffc88765ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
22 952
Read events
22 932
Write events
20
Delete events
0
Modification events
| (PID) Process: | (536) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 169A91B9DA932F00 | |||
| (PID) Process: | (536) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0D2D9AB9DA932F00 | |||
| (PID) Process: | (536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3B9AD49C-FBA0-4A76-9096-C555B1C65613} | |||
| (PID) Process: | (536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262990 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BF7E65DB-1B47-4D8A-B799-BA11AF22F58D} | |||
| (PID) Process: | (536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (536) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8670BFB9DA932F00 | |||
| (PID) Process: | (536) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
6
Suspicious files
51
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b6de.TMP | — | |
MD5:— | SHA256:— | |||
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b6fd.TMP | — | |
MD5:— | SHA256:— | |||
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b71d.TMP | — | |
MD5:— | SHA256:— | |||
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b71d.TMP | — | |
MD5:— | SHA256:— | |||
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b71d.TMP | — | |
MD5:— | SHA256:— | |||
| 536 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
45
DNS requests
40
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.185:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
9116 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/QOSih5UY/0 | unknown | — | — | shared |
6028 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/QOSih5UY/0 | unknown | — | — | shared |
8728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.185:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
536 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7380 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
link.storjshare.io |
| malicious |
business.bing.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7380 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
7380 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Service Domain in DNS Lookup (link .storjshare .io) |
7380 | msedge.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Domain (link .storjshare .io in TLS SNI) |
7380 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Observed Commonly Actor Abused Online Service Domain (storjshare .io in TLS SNI) |
7380 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Commonly Actor Abused Online Service Domain (storjshare .io) |
7380 | msedge.exe | Misc activity | ET TA_ABUSED_SERVICES Commonly Actor Abused Online Service Domain (storjshare .io) |
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
9116 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
9192 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
6028 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |