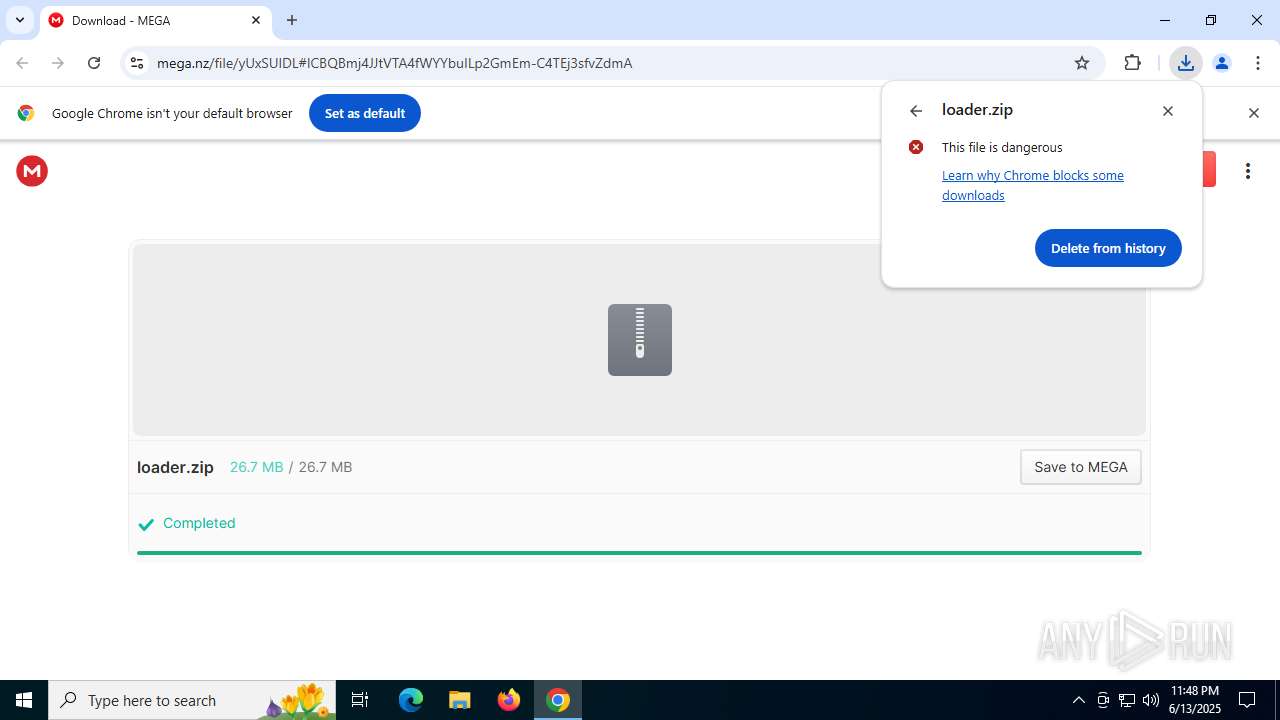
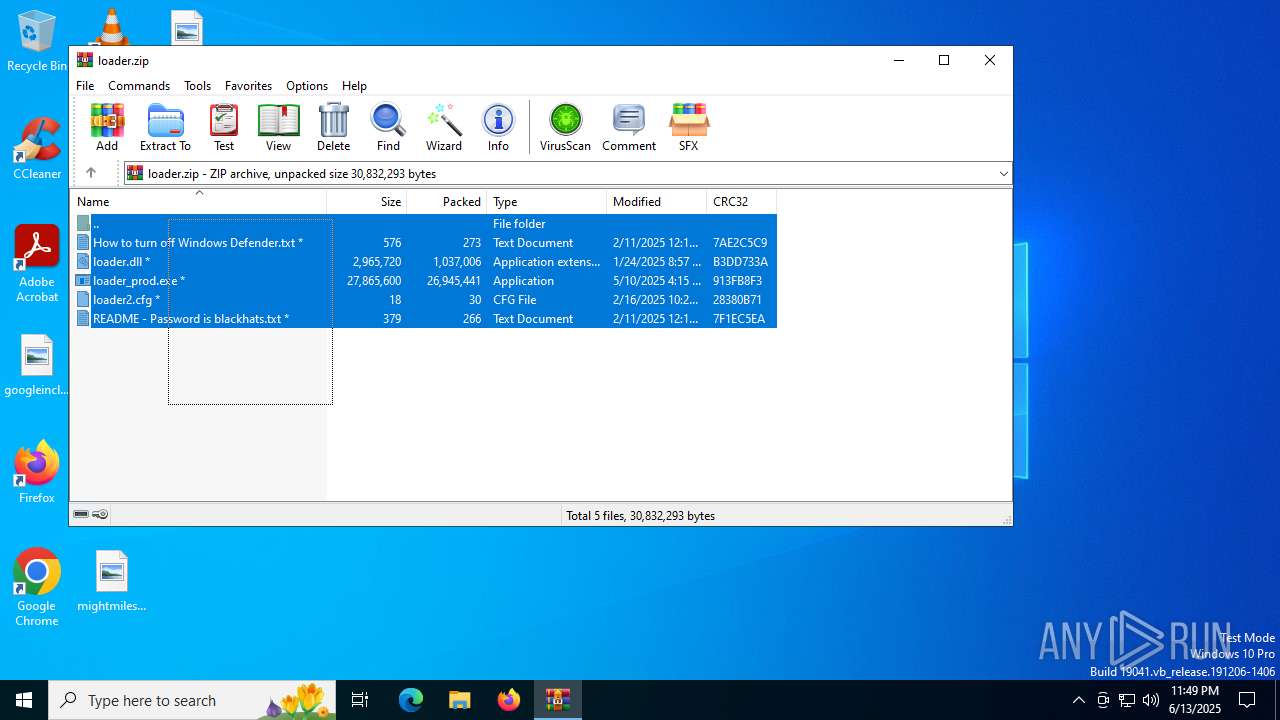
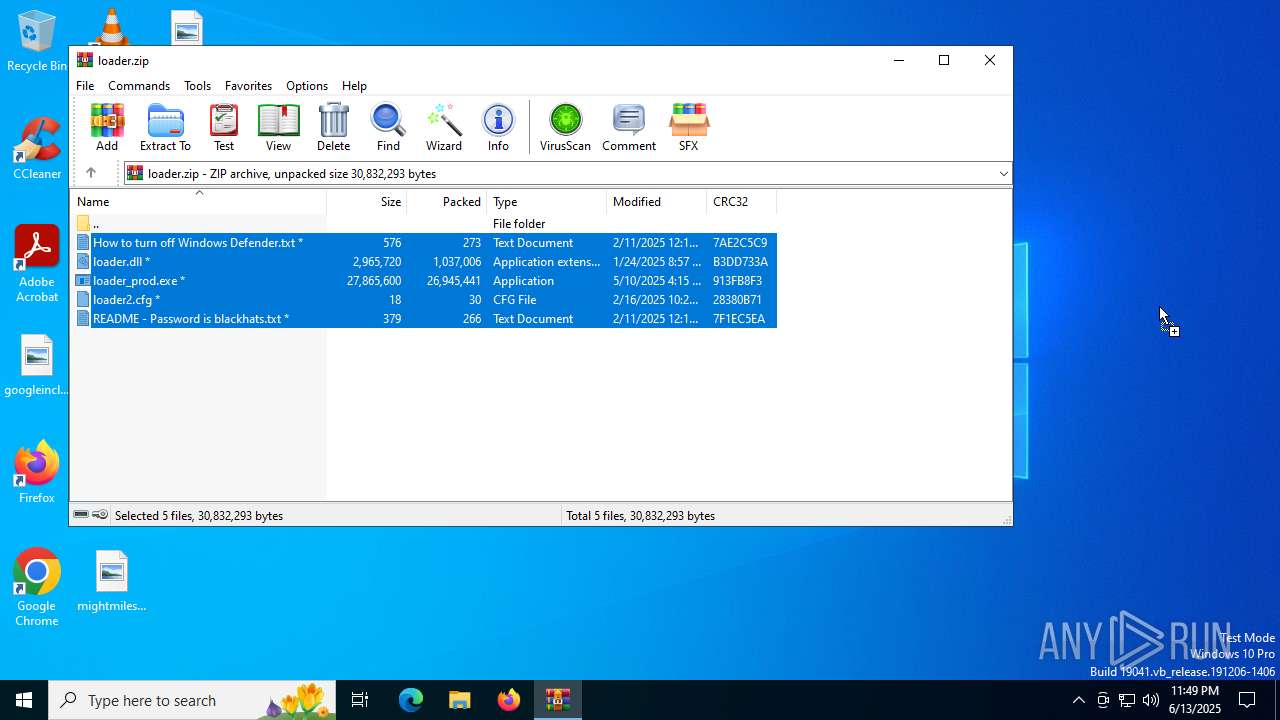
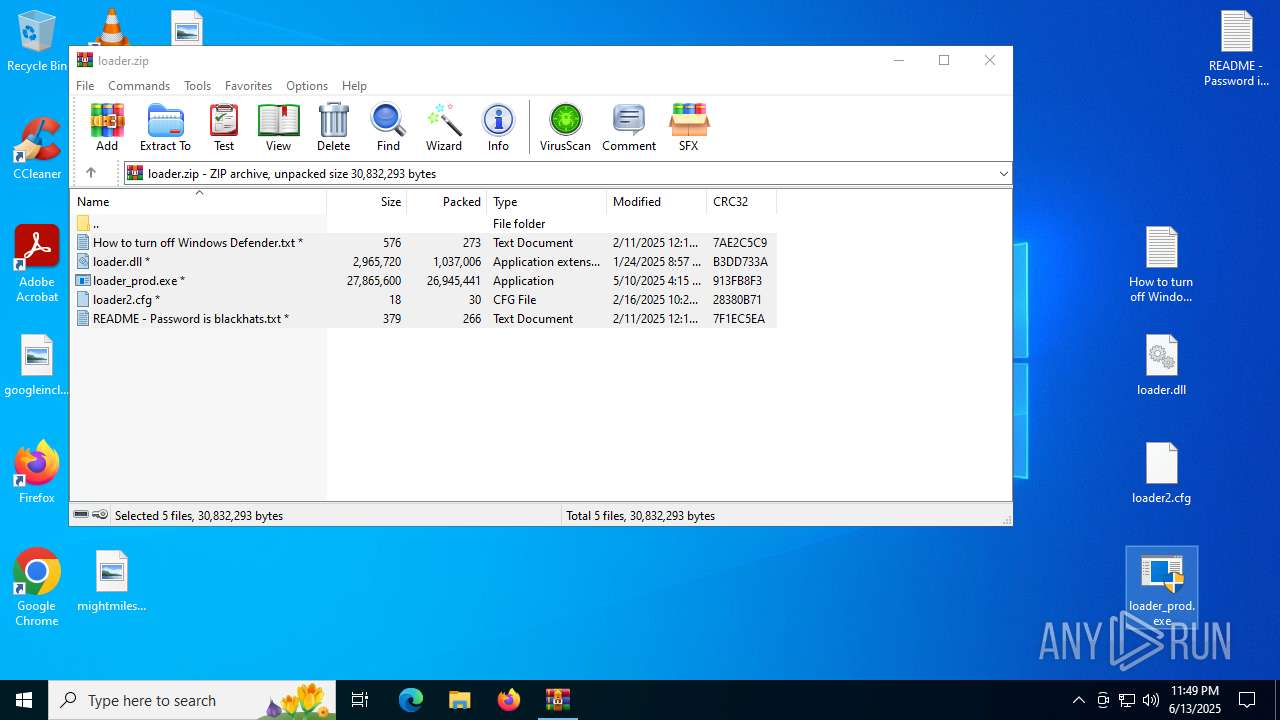
| URL: | https://mega.nz/file/yUxSUIDL#ICBQBmj4JJtVTA4fWYYbuILp2GmEm-C4TEj3sfvZdmA |
| Full analysis: | https://app.any.run/tasks/c3d4770b-58f2-4bf9-879c-cd53e116dcb6 |
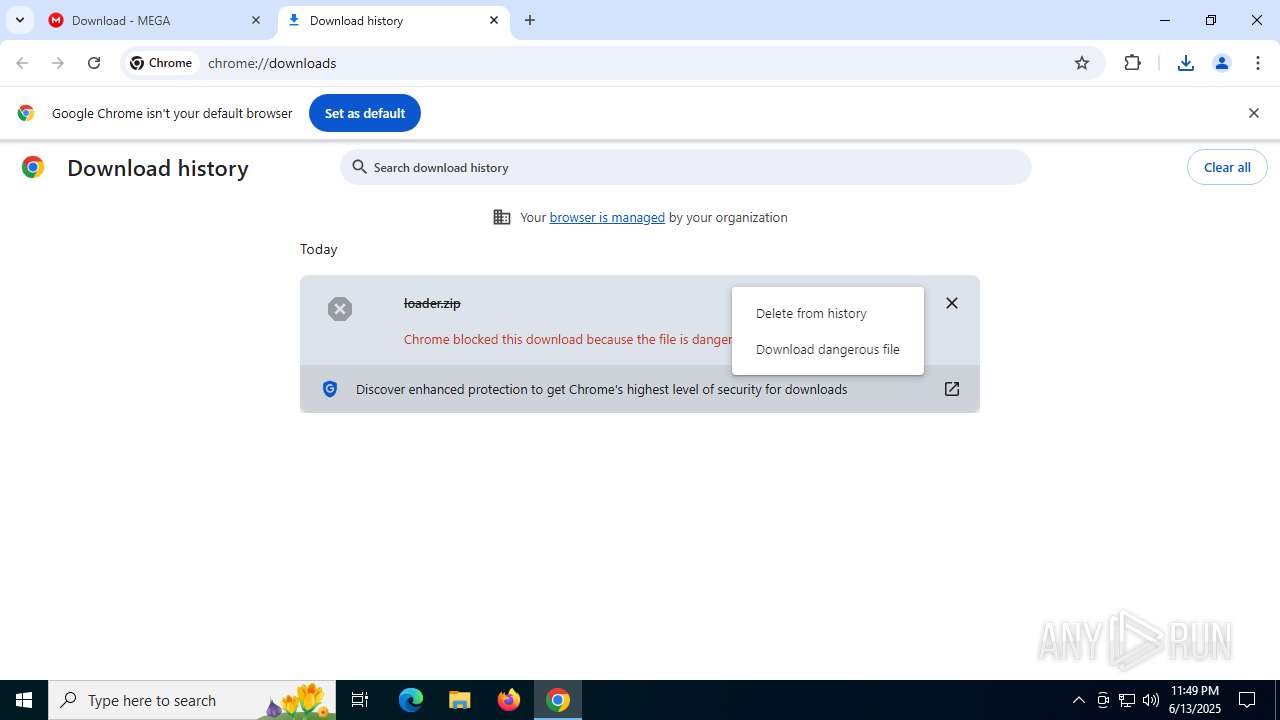
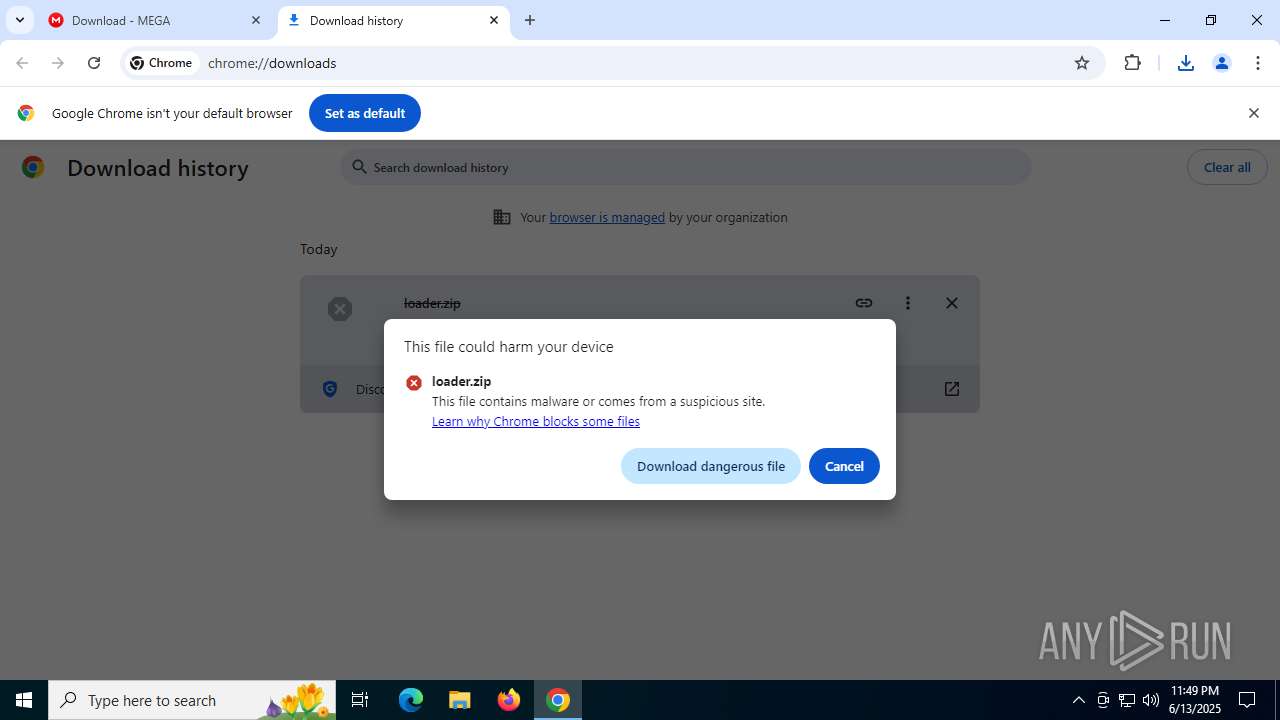
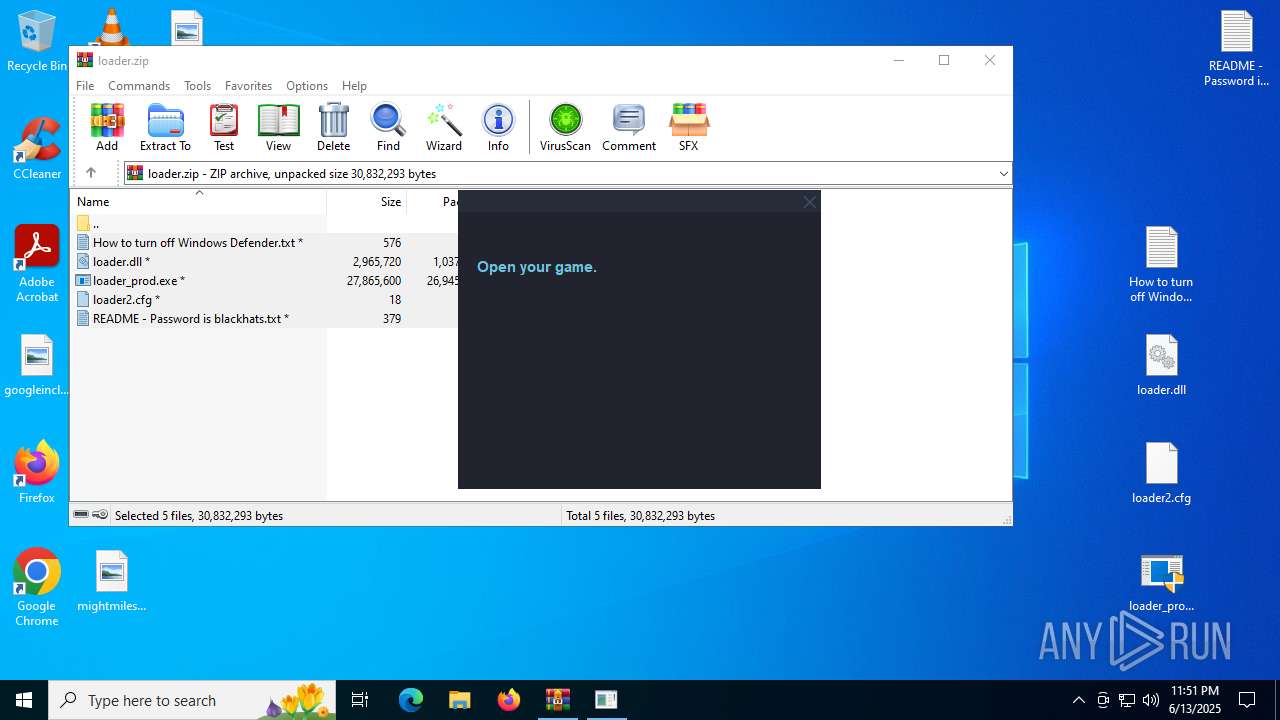
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | June 13, 2025, 23:48:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 861F5C3B76E8DE2A3E5DDF6FA567FFDA |
| SHA1: | EF9C22B2C7E783BC60916CE4D62E0C4567F67F2E |
| SHA256: | 95D23BC68A33CF9E53194546C6A694864F149D1B162886E458A71EBC76196D64 |
| SSDEEP: | 3:N8X/i9xmn0Ip3C8wsp9WHBIk:20xm5kHBZ |
MALICIOUS
TROX has been detected
- loader.exe (PID: 8056)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 4312)
Disables Windows Defender
- reg.exe (PID: 6320)
Adds extension to the Windows Defender exclusion list
- bastard.exe (PID: 8024)
- svchost.exe (PID: 7368)
Changes Windows Defender settings
- bastard.exe (PID: 8024)
- svchost.exe (PID: 7368)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 4884)
- cmd.exe (PID: 4688)
Vulnerable driver has been detected
- svchost.exe (PID: 7368)
Connects to the CnC server
- dialer.exe (PID: 6536)
MINER has been detected (SURICATA)
- dialer.exe (PID: 6536)
ASYNCRAT has been detected (YARA)
- svchost.exe (PID: 7284)
SUSPICIOUS
Executable content was dropped or overwritten
- loader_prod.exe (PID: 7856)
- loader.exe (PID: 8056)
- svchost.exe (PID: 7984)
- bastard.exe (PID: 8024)
- svchost.exe (PID: 7368)
Base64-obfuscated command line is found
- loader_prod.exe (PID: 7856)
BASE64 encoded PowerShell command has been detected
- loader_prod.exe (PID: 7856)
Starts POWERSHELL.EXE for commands execution
- loader_prod.exe (PID: 7856)
- bastard.exe (PID: 8024)
- svchost.exe (PID: 7368)
Reads security settings of Internet Explorer
- loader_prod.exe (PID: 7856)
- runtime.exe (PID: 7956)
- svchost.exe (PID: 7984)
The process creates files with name similar to system file names
- loader_prod.exe (PID: 7856)
- svchost.exe (PID: 7984)
Loads Python modules
- loader.exe (PID: 8088)
The process drops C-runtime libraries
- loader.exe (PID: 8056)
Application launched itself
- loader.exe (PID: 8056)
Reads the date of Windows installation
- svchost.exe (PID: 7984)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 7984)
- bastard.exe (PID: 8024)
- svchost.exe (PID: 7368)
Process drops legitimate windows executable
- loader.exe (PID: 8056)
Process drops python dynamic module
- loader.exe (PID: 8056)
Uses base64 encoding (POWERSHELL)
- runtime.exe (PID: 7956)
Checks a user's role membership (POWERSHELL)
- runtime.exe (PID: 7956)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7172)
The executable file from the user directory is run by the CMD process
- svchost.exe (PID: 7284)
Uses REG/REGEDIT.EXE to modify registry
- runtime.exe (PID: 7956)
Executing commands from a ".bat" file
- svchost.exe (PID: 7984)
Connects to unusual port
- svchost.exe (PID: 7284)
- dialer.exe (PID: 6536)
Script adds exclusion extension to Windows Defender
- bastard.exe (PID: 8024)
- svchost.exe (PID: 7368)
Script adds exclusion path to Windows Defender
- bastard.exe (PID: 8024)
- svchost.exe (PID: 7368)
Stops a currently running service
- sc.exe (PID: 6148)
- sc.exe (PID: 4816)
- sc.exe (PID: 7508)
- sc.exe (PID: 6304)
- sc.exe (PID: 1932)
- sc.exe (PID: 5600)
- sc.exe (PID: 7520)
- sc.exe (PID: 2448)
- sc.exe (PID: 4920)
- sc.exe (PID: 6504)
- sc.exe (PID: 7692)
Process uninstalls Windows update
- wusa.exe (PID: 3960)
- wusa.exe (PID: 4444)
Manipulates environment variables
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7360)
Uses powercfg.exe to modify the power settings
- bastard.exe (PID: 8024)
- svchost.exe (PID: 7368)
Executes as Windows Service
- svchost.exe (PID: 7368)
Creates a new Windows service
- sc.exe (PID: 432)
Starts SC.EXE for service management
- bastard.exe (PID: 8024)
- svchost.exe (PID: 7368)
Windows service management via SC.EXE
- sc.exe (PID: 5008)
- sc.exe (PID: 5368)
Drops a system driver (possible attempt to evade defenses)
- svchost.exe (PID: 7368)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2200)
There is functionality for taking screenshot (YARA)
- loader.exe (PID: 8088)
Potential Corporate Privacy Violation
- dialer.exe (PID: 6536)
INFO
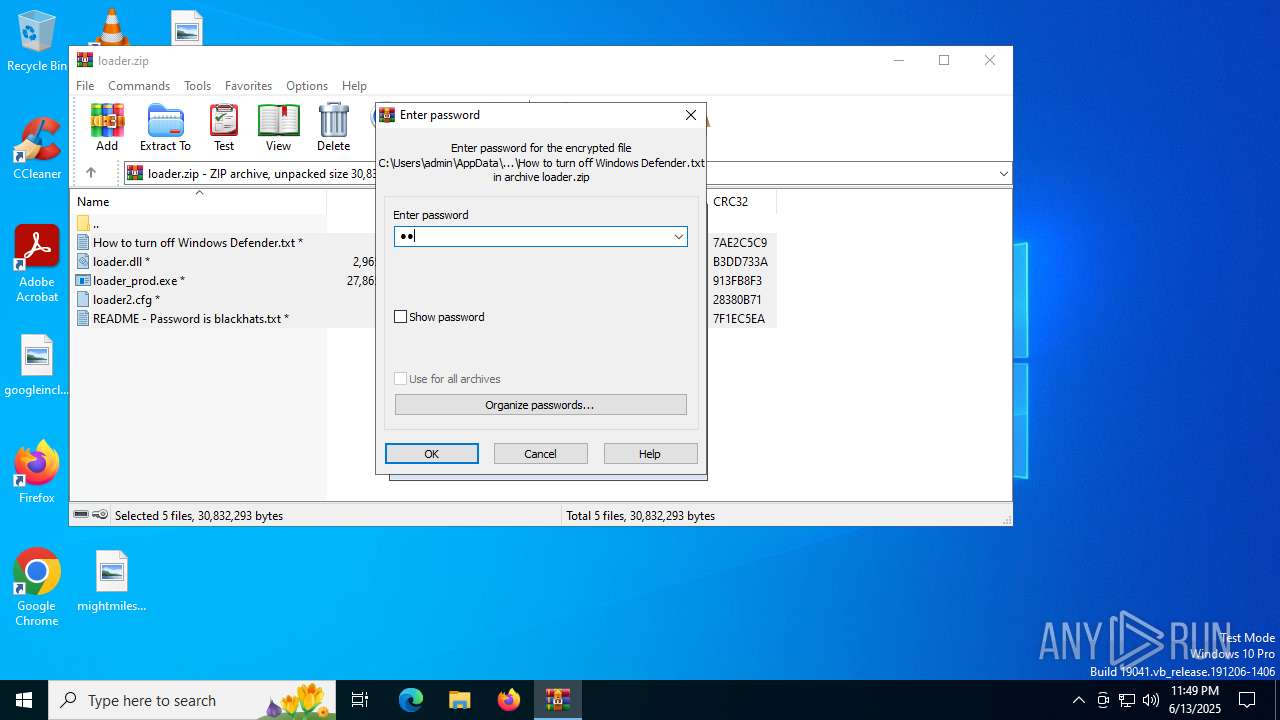
Launching a file from the Downloads directory
- chrome.exe (PID: 3520)
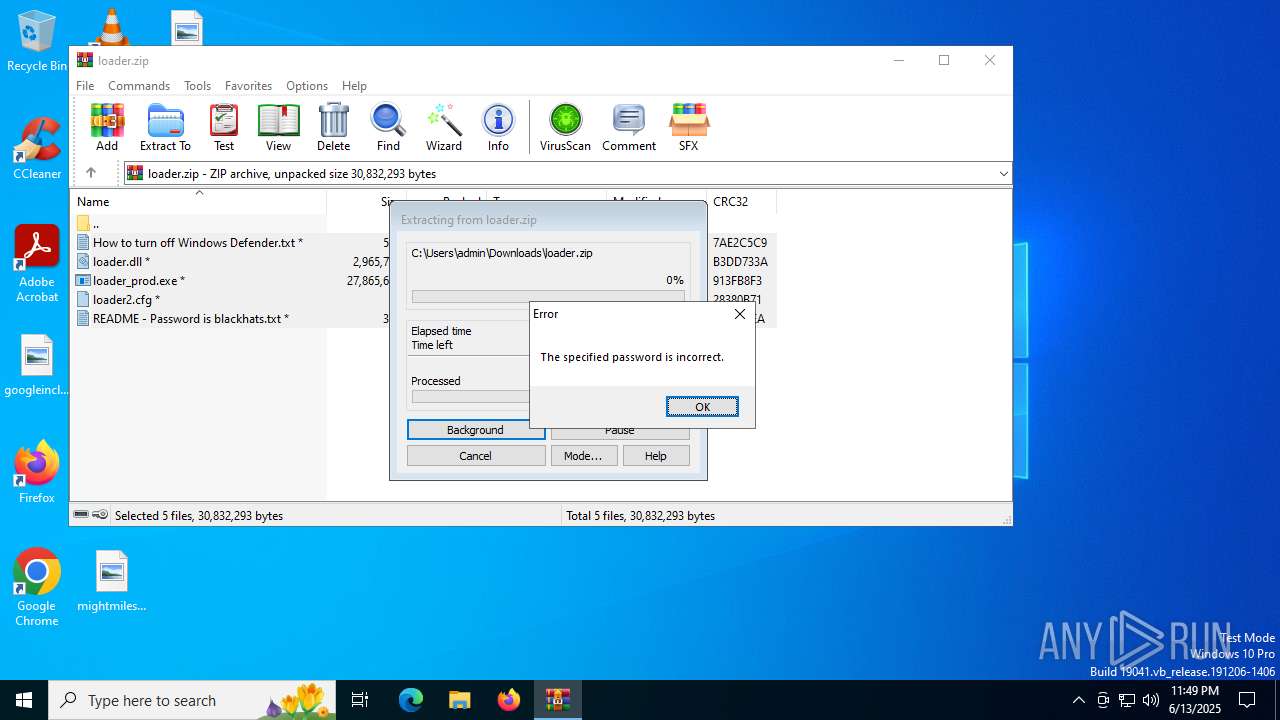
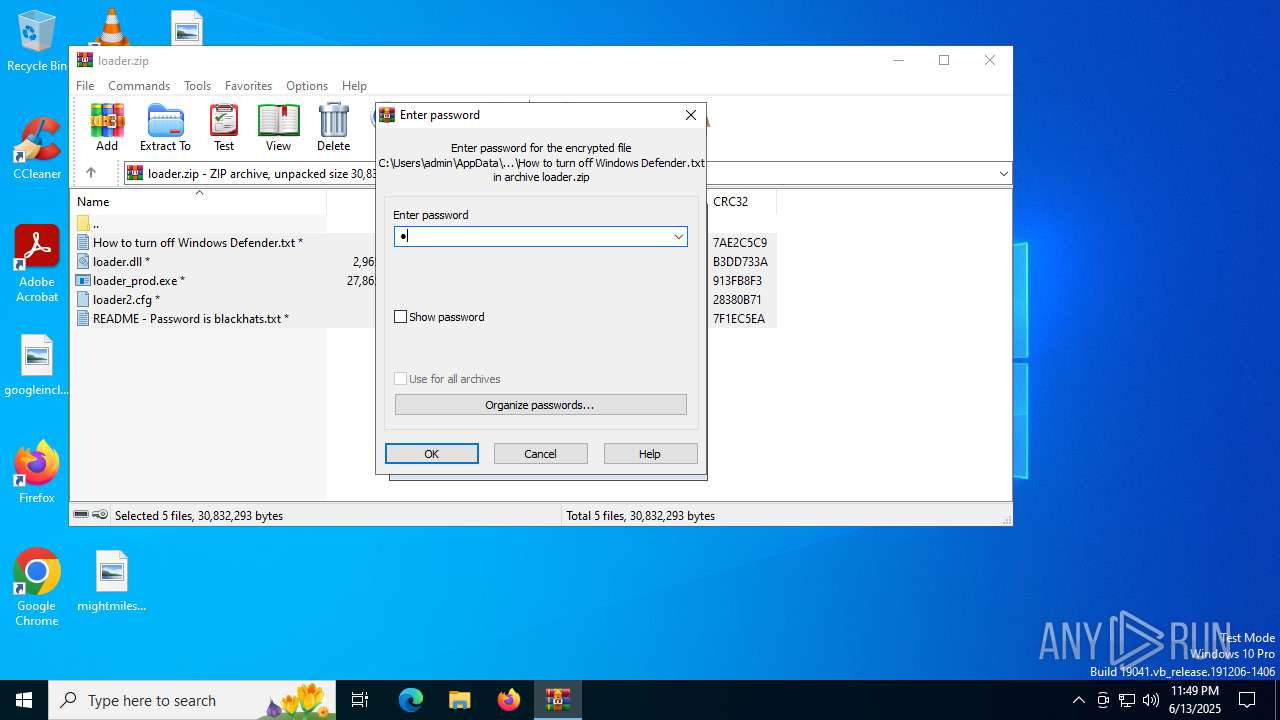
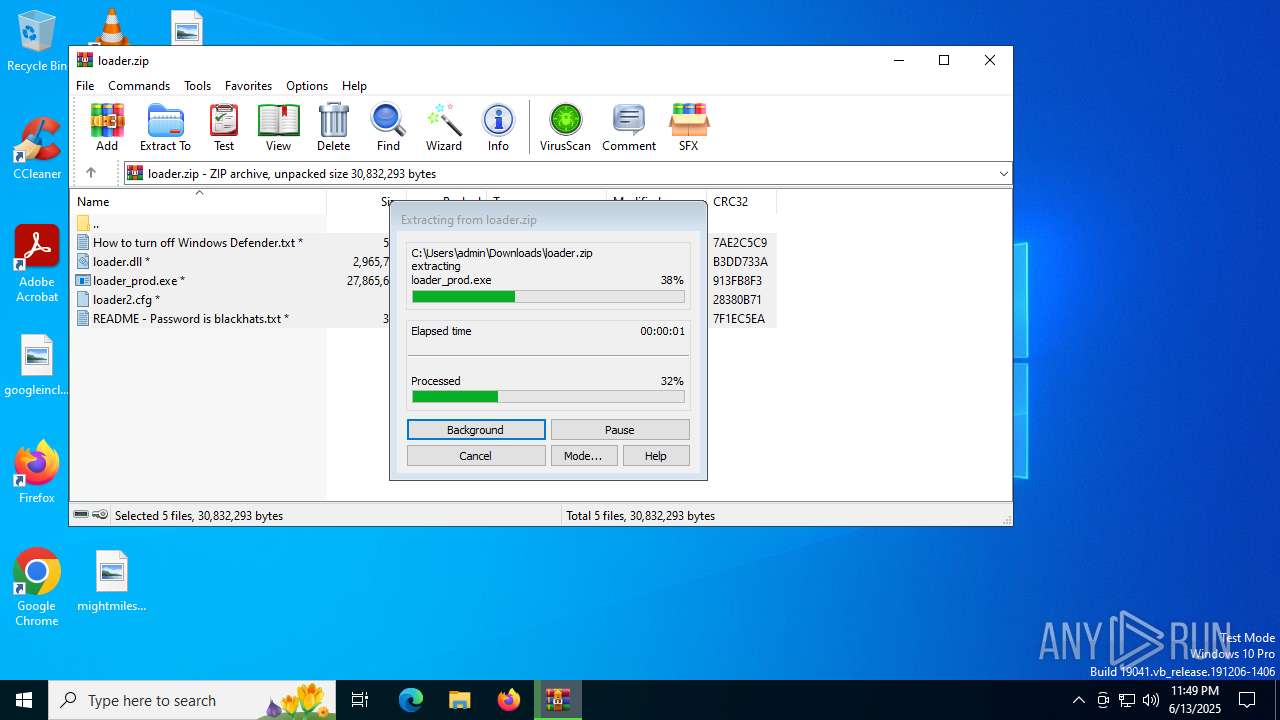
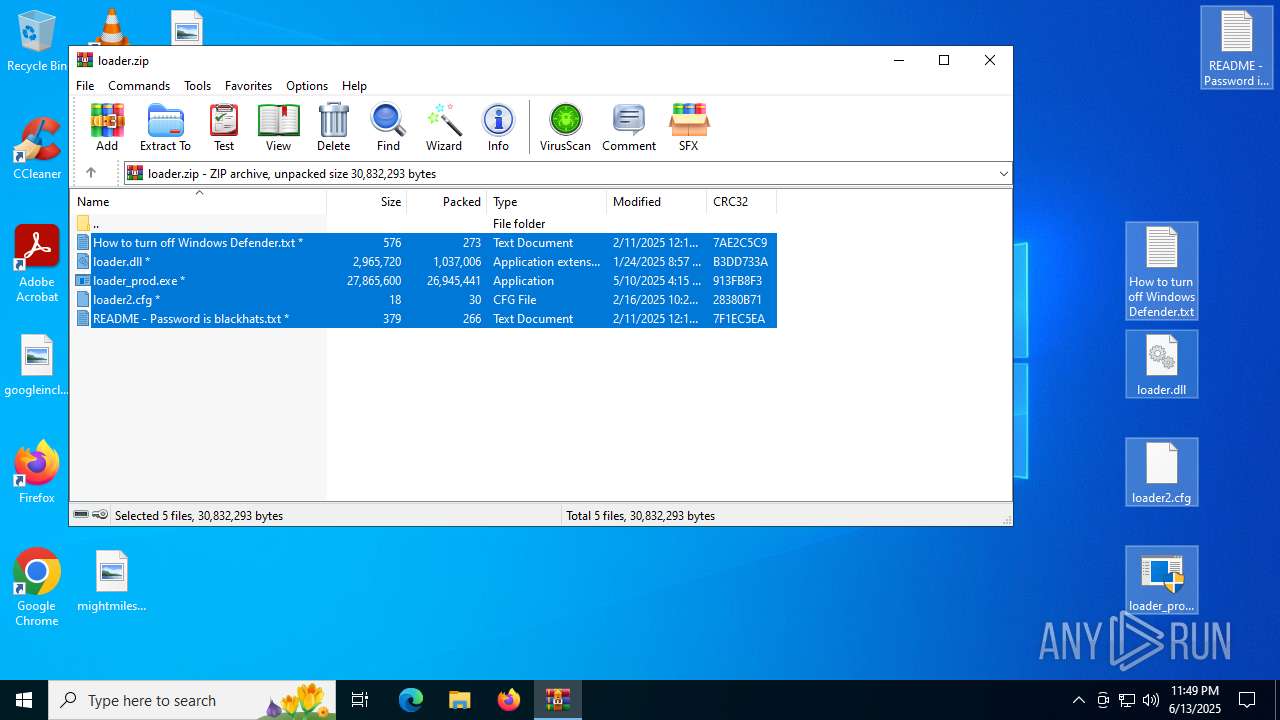
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7600)
Reads Microsoft Office registry keys
- chrome.exe (PID: 3520)
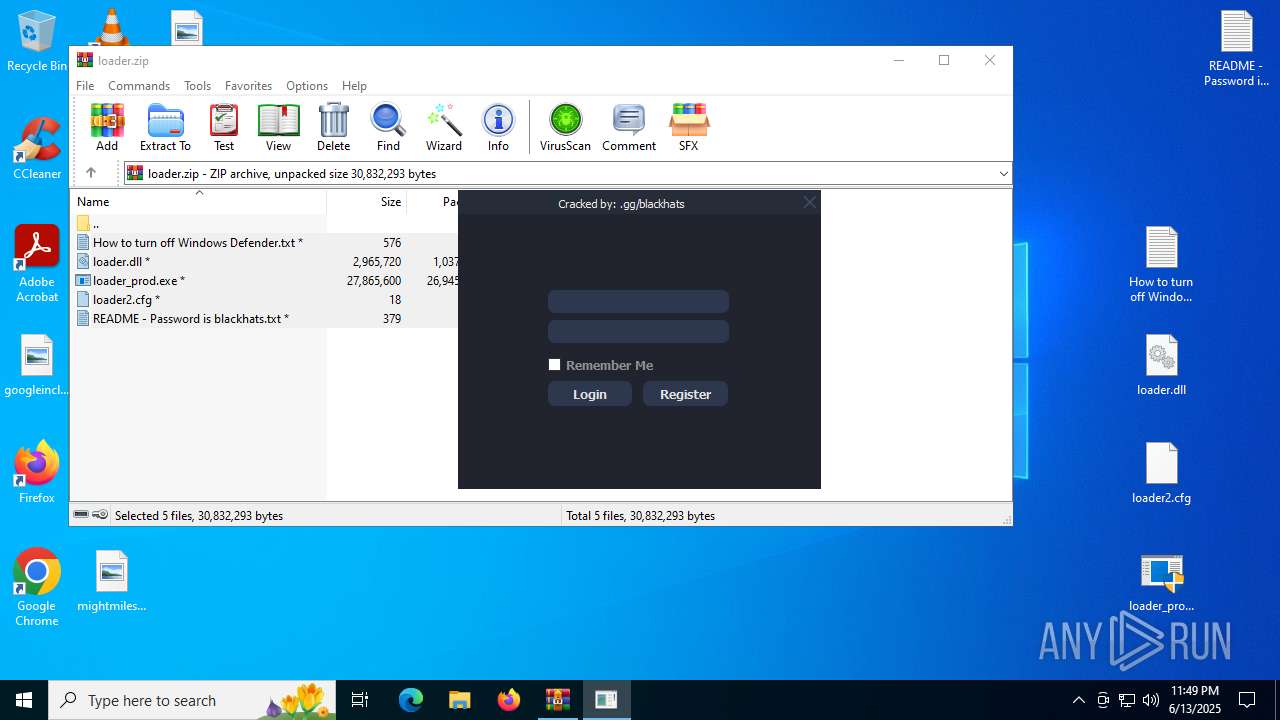
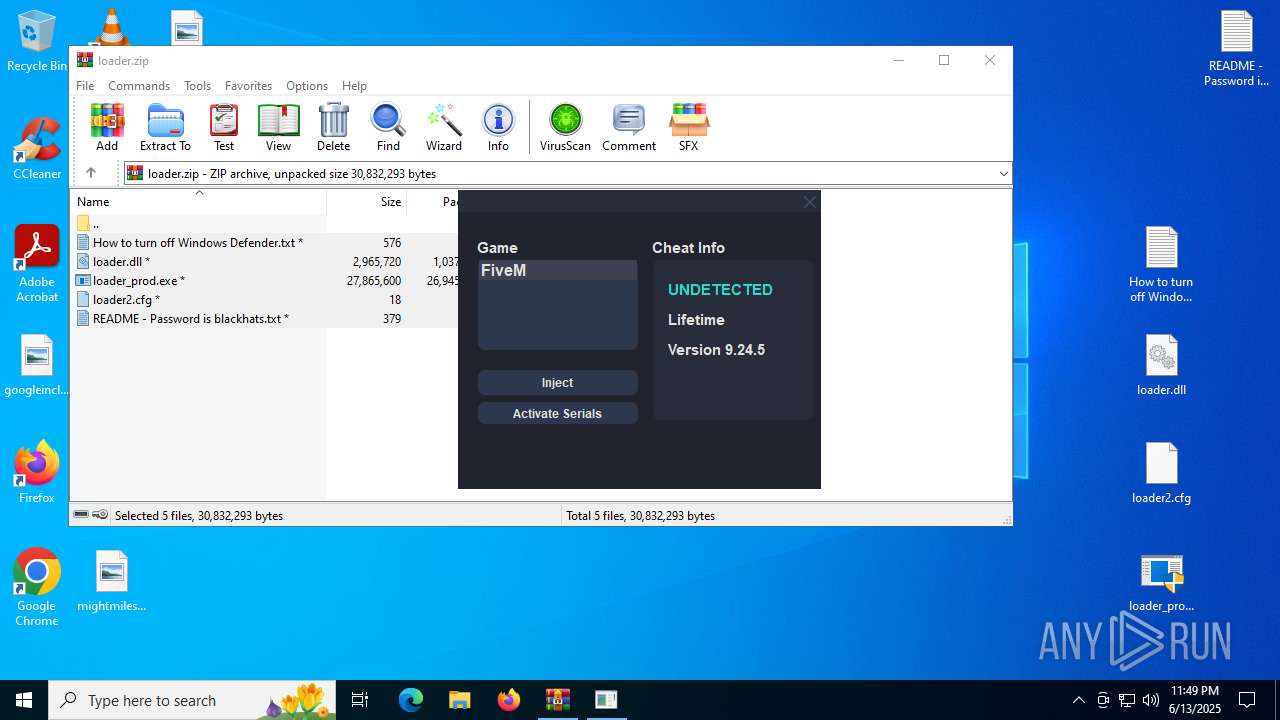
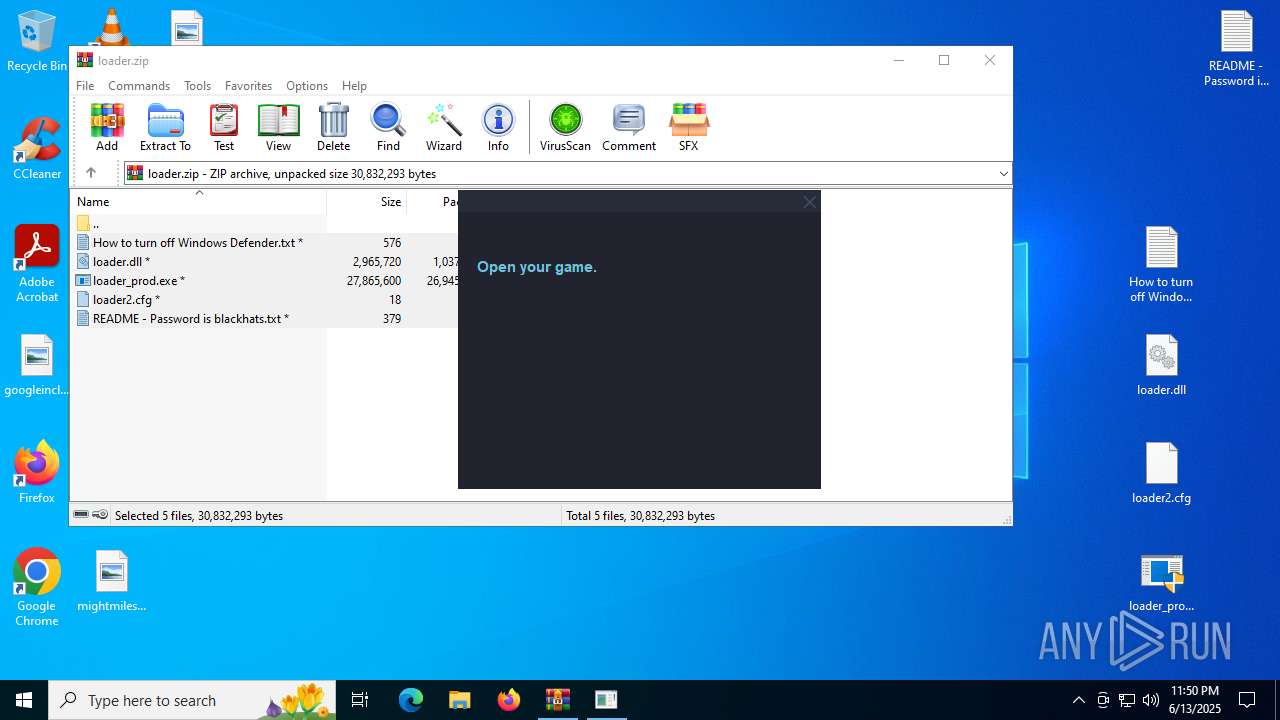
Manual execution by a user
- loader_prod.exe (PID: 7808)
- loader_prod.exe (PID: 7856)
Reads the computer name
- loader_prod.exe (PID: 7856)
- runtime.exe (PID: 7956)
- svchost.exe (PID: 7984)
- loader.exe (PID: 8088)
- svchost.exe (PID: 7284)
Application launched itself
- chrome.exe (PID: 3520)
Checks supported languages
- bastard.exe (PID: 8024)
- loader_prod.exe (PID: 7856)
- loader.exe (PID: 8056)
- loader.exe (PID: 8088)
- svchost.exe (PID: 7984)
- svchost.exe (PID: 7284)
- runtime.exe (PID: 7956)
Create files in a temporary directory
- loader_prod.exe (PID: 7856)
- runtime.exe (PID: 7956)
- svchost.exe (PID: 7984)
- loader.exe (PID: 8056)
Reads Environment values
- svchost.exe (PID: 7984)
- runtime.exe (PID: 7956)
- svchost.exe (PID: 7284)
Reads the machine GUID from the registry
- svchost.exe (PID: 7984)
- runtime.exe (PID: 7956)
- svchost.exe (PID: 7284)
Process checks computer location settings
- loader_prod.exe (PID: 7856)
- svchost.exe (PID: 7984)
The sample compiled with english language support
- loader.exe (PID: 8056)
Creates files or folders in the user directory
- svchost.exe (PID: 7984)
Reads the software policy settings
- runtime.exe (PID: 7956)
- svchost.exe (PID: 7284)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7912)
- runtime.exe (PID: 7956)
- powershell.exe (PID: 7428)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7912)
- powershell.exe (PID: 7428)
Checks proxy server information
- svchost.exe (PID: 7284)
Disables trace logs
- svchost.exe (PID: 7284)
The sample compiled with japanese language support
- svchost.exe (PID: 7368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
235
Monitored processes
97
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | C:\WINDOWS\system32\sc.exe create "svchost" binpath= "C:\ProgramData\nfouatgdtoce\svchost.exe" start= "auto" | C:\Windows\System32\sc.exe | — | bastard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | C:\WINDOWS\system32\powercfg.exe /x -standby-timeout-dc 0 | C:\Windows\System32\powercfg.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --string-annotations --field-trial-handle=4328,i,4022755835230171348,11704008028224824084,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4388 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1480 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | C:\WINDOWS\system32\powercfg.exe /x -standby-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1932 | C:\WINDOWS\system32\sc.exe stop dosvc | C:\Windows\System32\sc.exe | — | bastard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 579
Read events
33 552
Write events
26
Delete events
1
Modification events
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
72
Suspicious files
73
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF17635d.TMP | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF17636d.TMP | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF17637c.TMP | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF17637c.TMP | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17637c.TMP | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF17637c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
90
DNS requests
99
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7652 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7652 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
5240 | chrome.exe | GET | 200 | 142.250.185.174:80 | http://clients2.google.com/time/1/current?cup2key=8:c7NfDprqGgZR0gkg9CKc37HO6PjeUWUt9Fa6sp7kpUA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2288 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4512 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5240 | chrome.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
5240 | chrome.exe | 142.250.185.174:80 | clients2.google.com | GOOGLE | US | whitelisted |
5240 | chrome.exe | 172.217.18.10:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
5240 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5240 | chrome.exe | 172.217.23.106:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
mega.nz |
| whitelisted |
accounts.google.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
eu.static.mega.co.nz |
| whitelisted |
g.api.mega.co.nz |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5240 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5240 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5240 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
5240 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5240 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5240 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
5240 | chrome.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
5240 | chrome.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
5240 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
5240 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
Process | Message |
|---|---|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 33,36,46,255'
|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 39,44,57,255'
|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 33,36,46,255'
|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 39,44,57,255'
|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 45,55,78,255'
|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 45,55,78,255'
|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 45,55,78,255'
|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 45,55,78,255'
|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 33,36,46,255'
|
loader.exe | QCssParser::parseColorValue: Specified color without alpha value but alpha given: 'rgb 45,55,78,255'
|