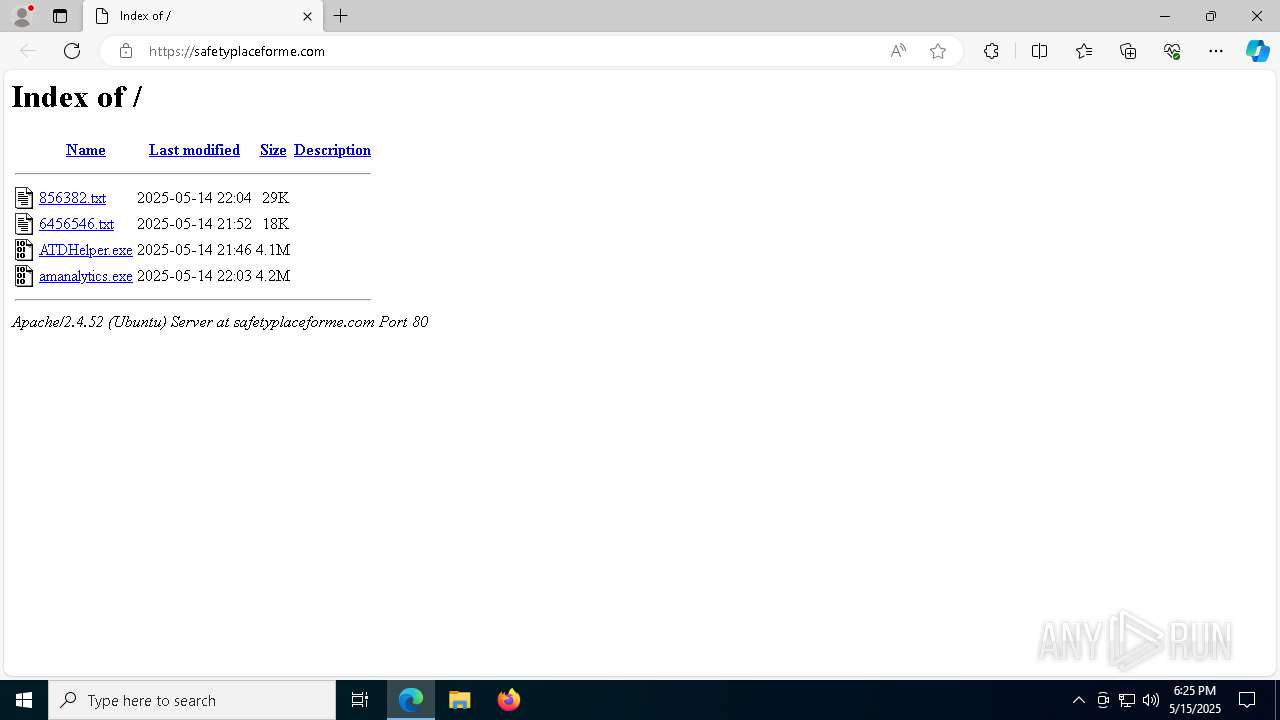
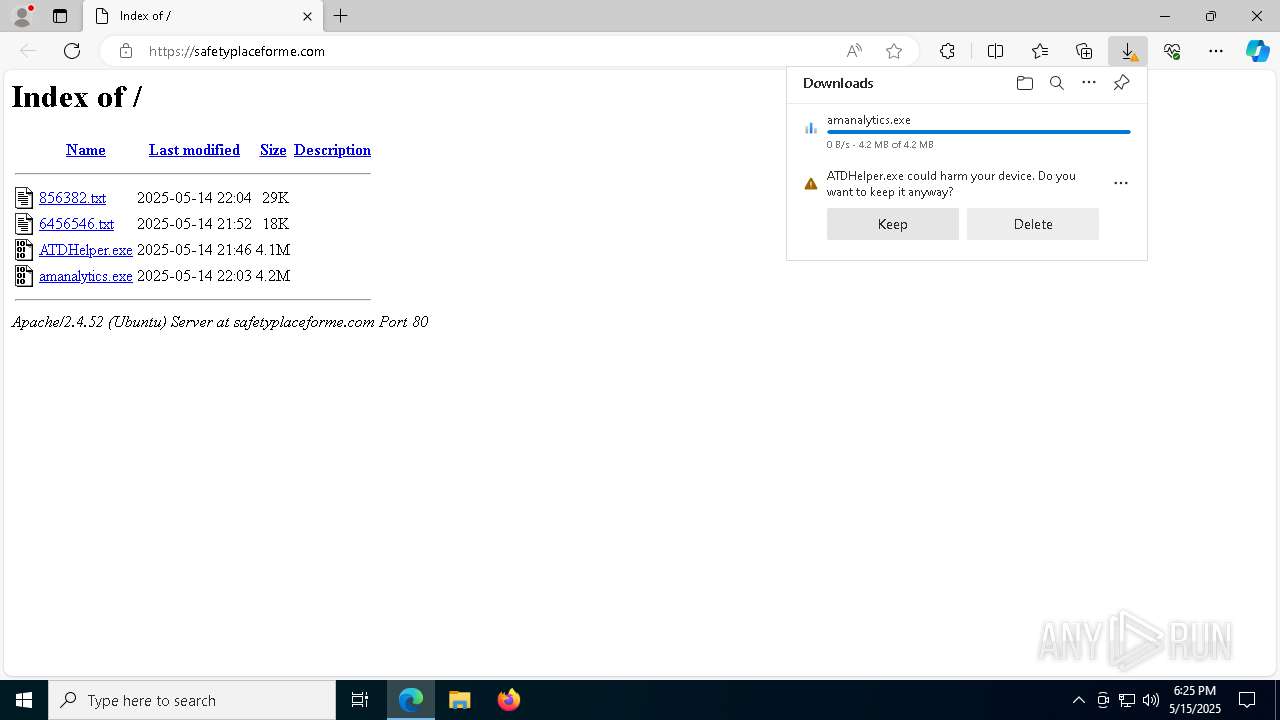
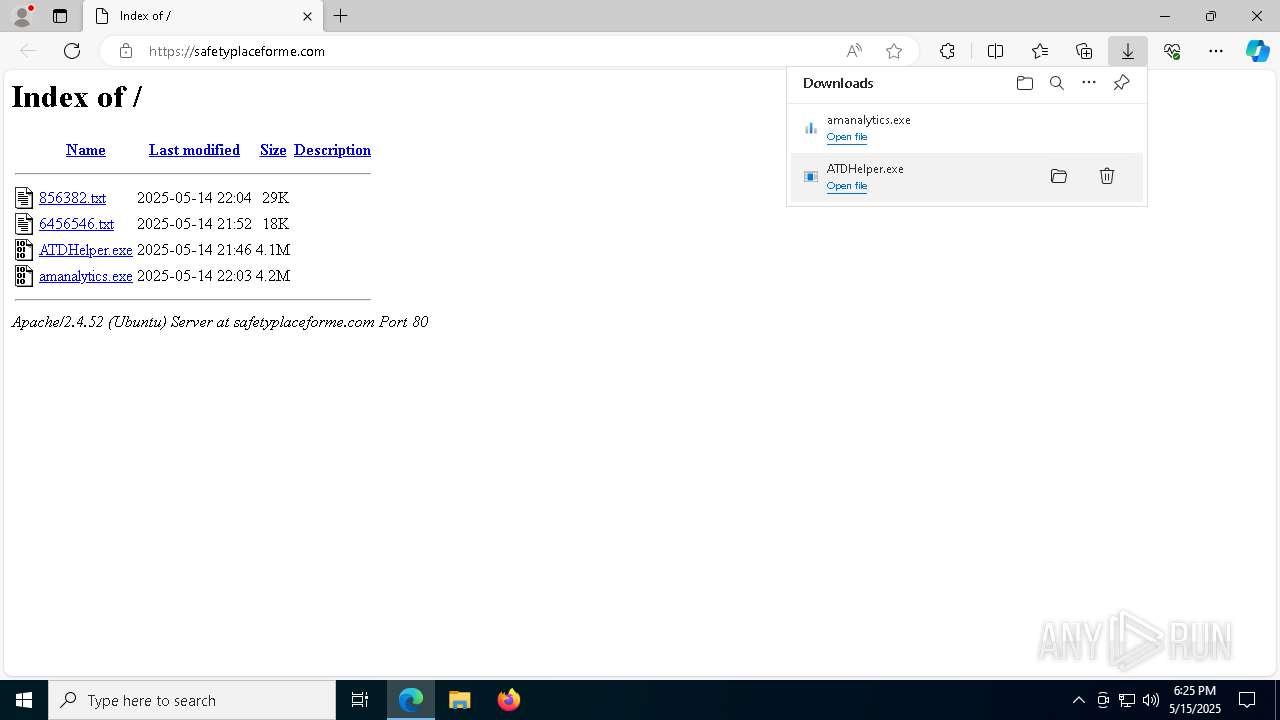
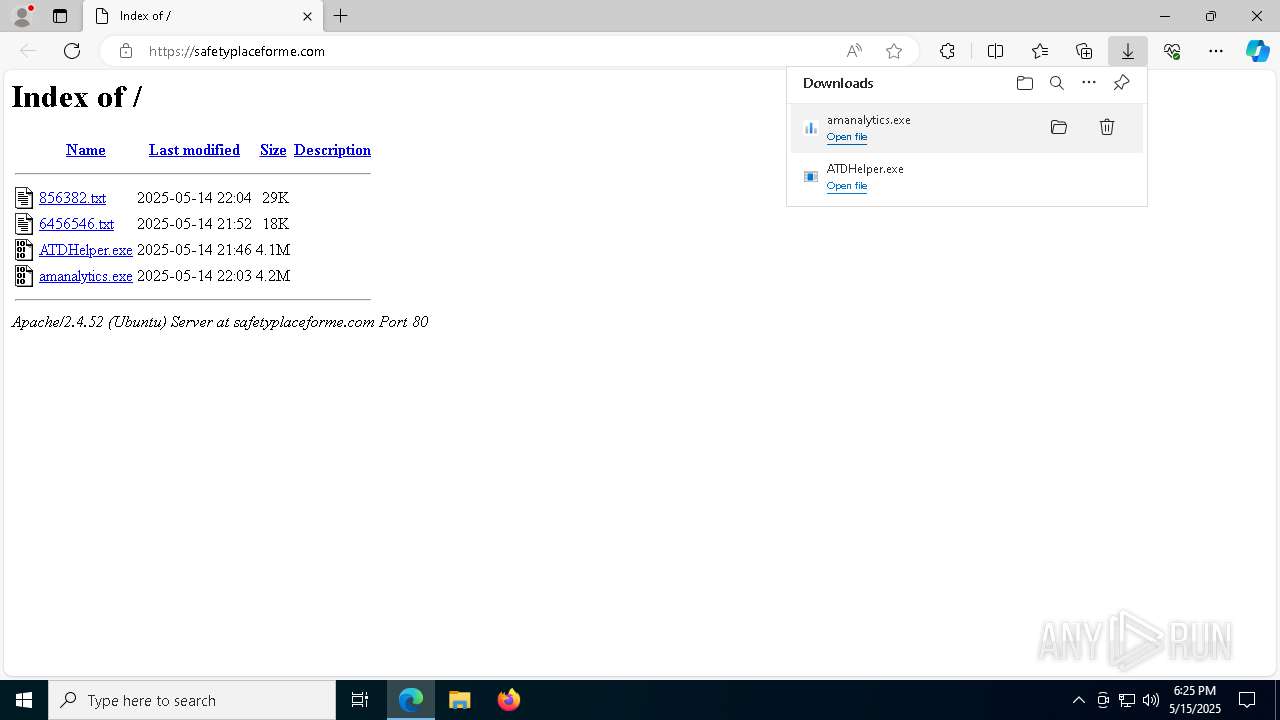
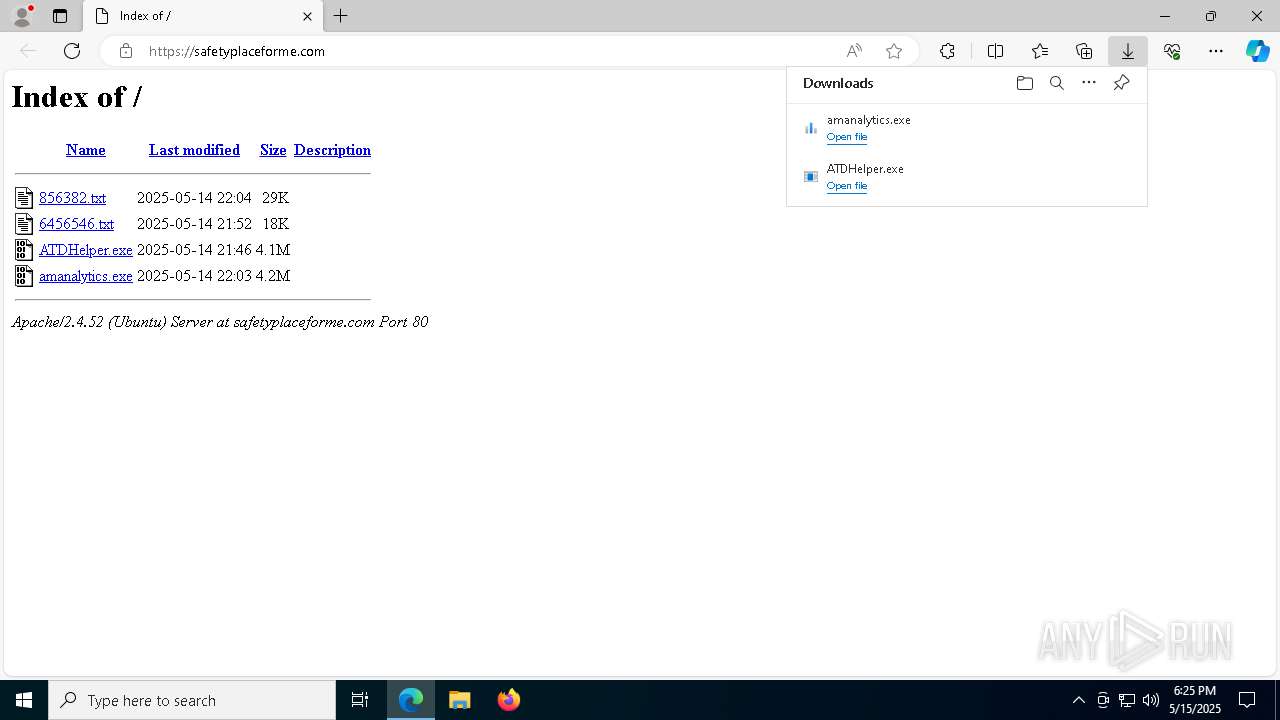
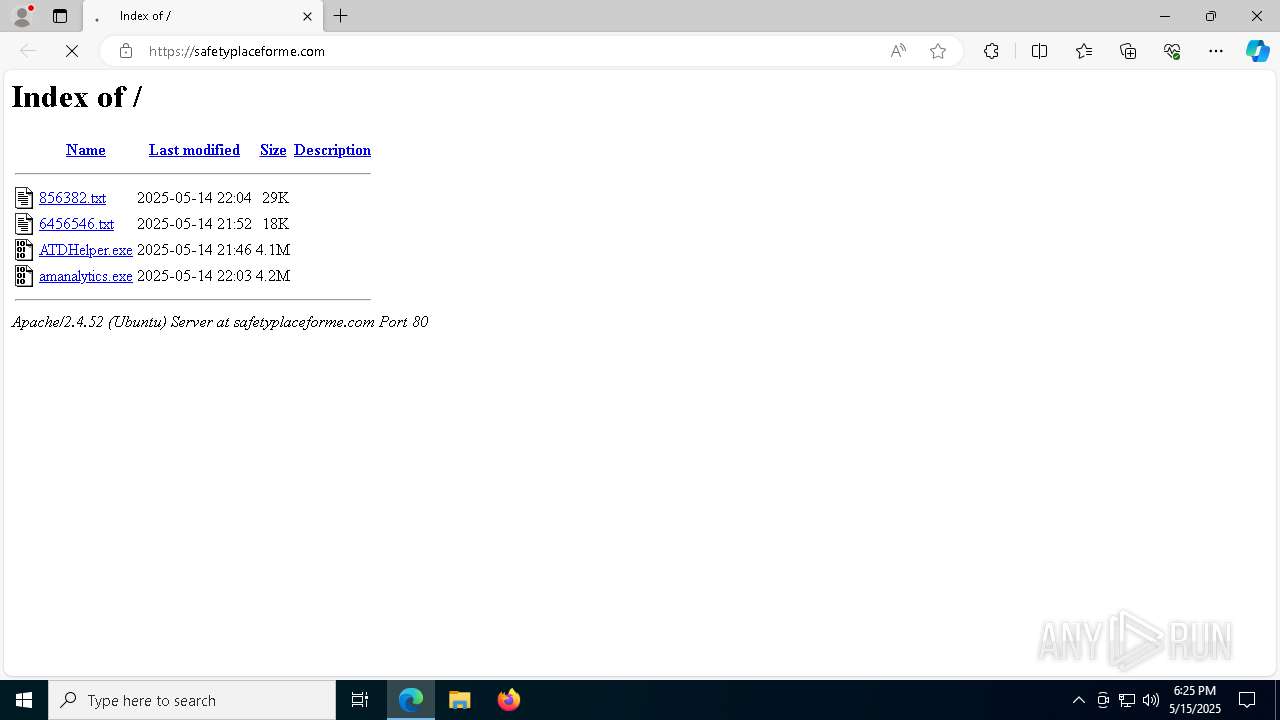
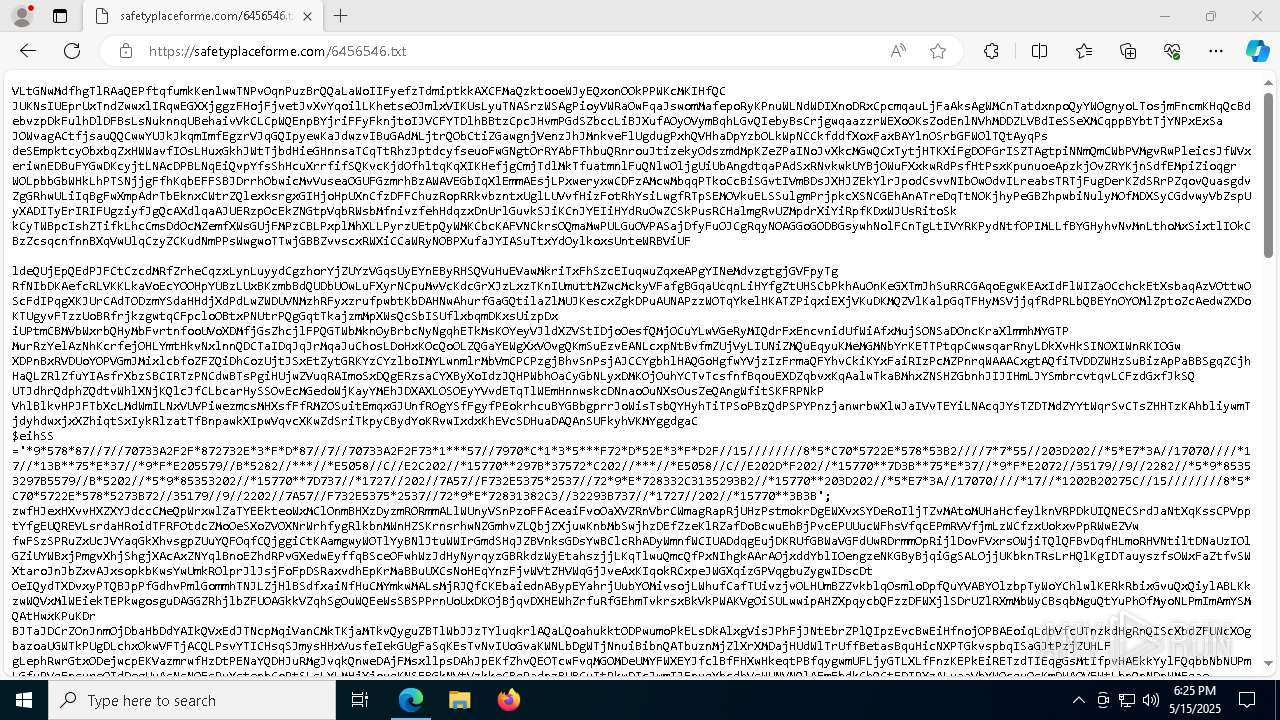
| URL: | safetyplaceforme.com |
| Full analysis: | https://app.any.run/tasks/d7369b76-8b12-4e43-9c5a-caa10abdce9d |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 15, 2025, 18:24:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 515EFAF6D6A79674623E4AD214FBE0C0 |
| SHA1: | 02E17BDBFBACA3547A7DA5E33C8810660D33DA14 |
| SHA256: | 95BD392B41699810437736D33DA216CD3D02EB1189D6E702F339474DF4891BEC |
| SSDEEP: | 3:ZuJEI:PI |
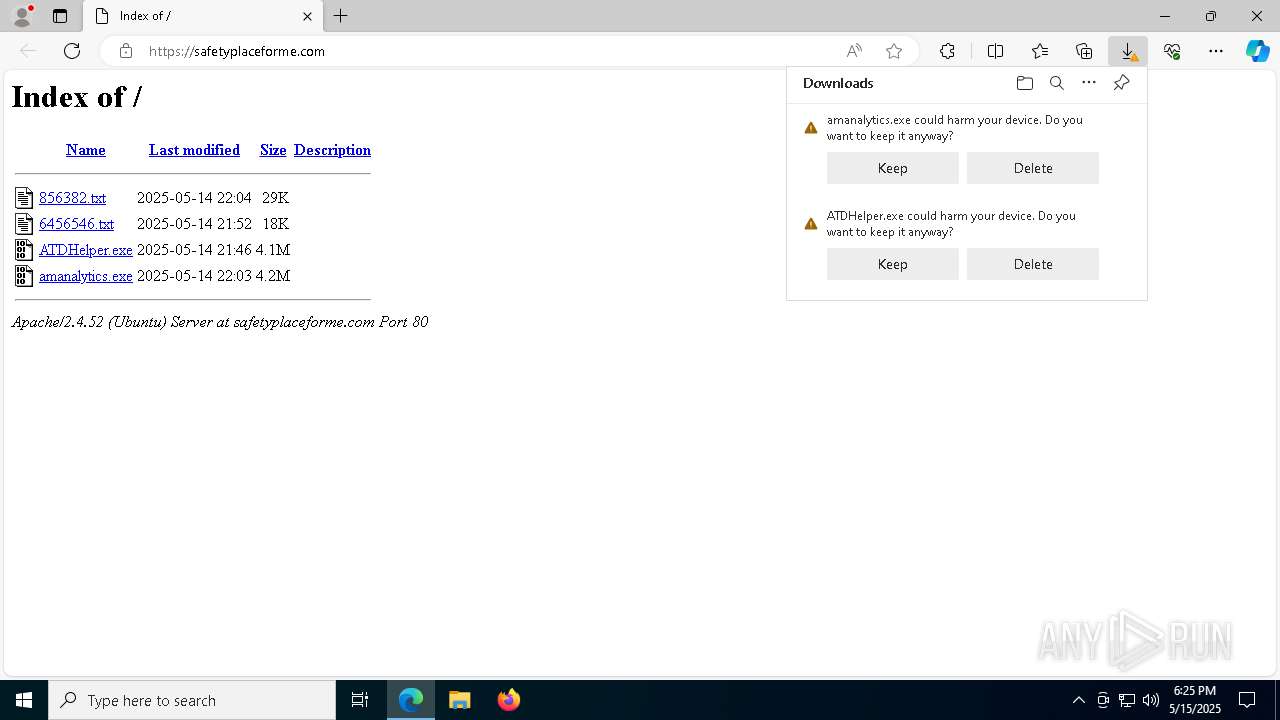
MALICIOUS
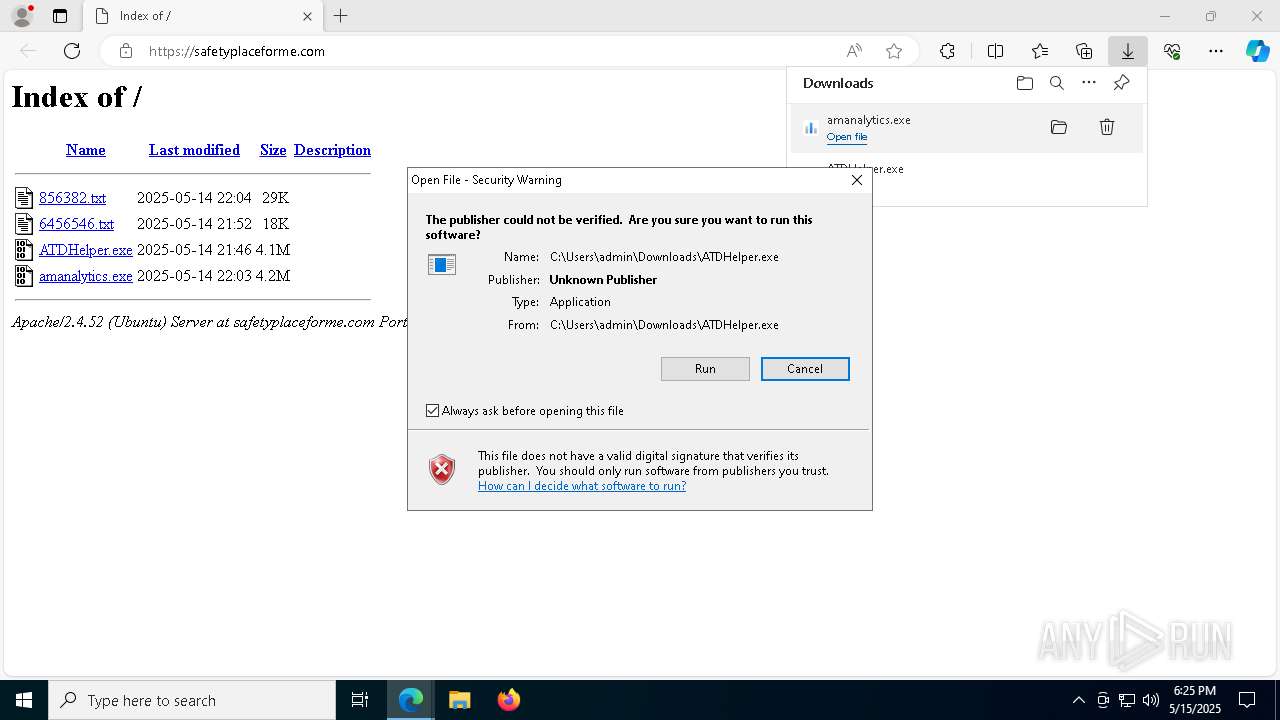
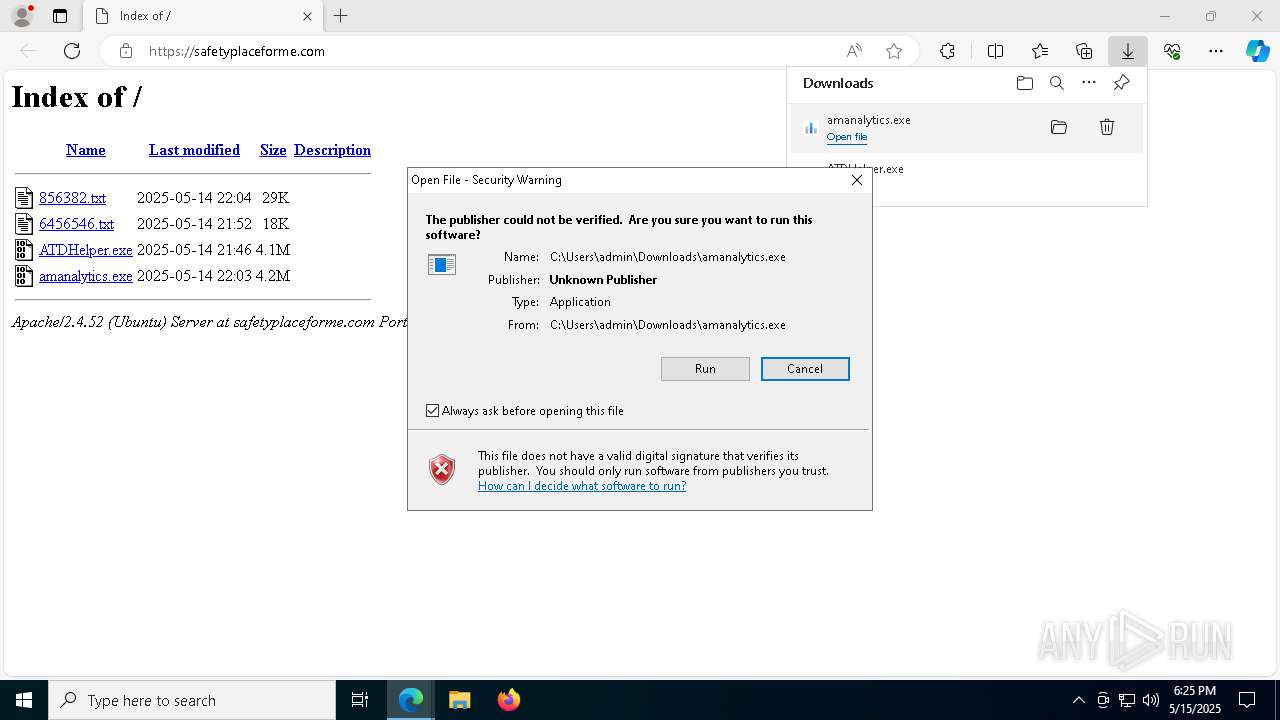
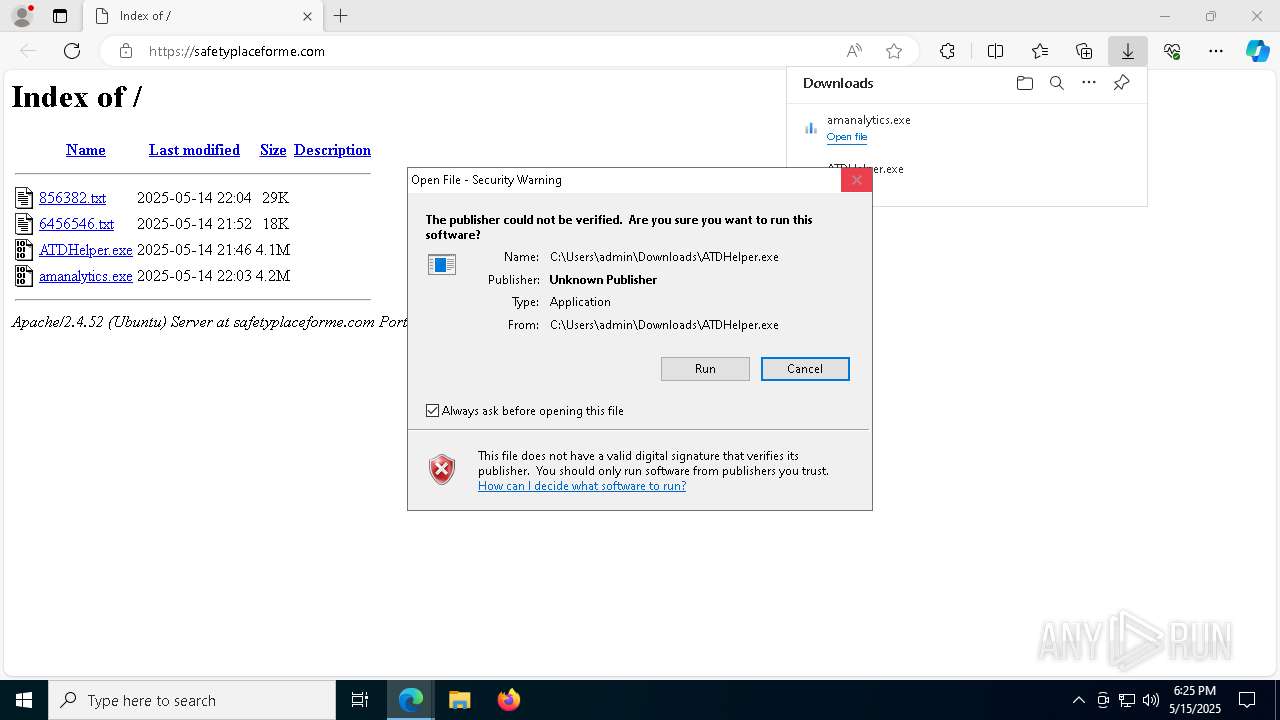
Executing a file with an untrusted certificate
- ATDHelper.exe (PID: 4452)
- amanalytics.exe (PID: 4040)
- ATDHelper.exe (PID: 1184)
VIDAR mutex has been found
- ATDHelper.exe (PID: 4452)
- ATDHelper.exe (PID: 1184)
Actions looks like stealing of personal data
- ATDHelper.exe (PID: 4452)
Steals credentials from Web Browsers
- ATDHelper.exe (PID: 4452)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- amanalytics.exe (PID: 4040)
Connects to the CnC server
- svchost.exe (PID: 2196)
SUSPICIOUS
Reads security settings of Internet Explorer
- ATDHelper.exe (PID: 4452)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- ATDHelper.exe (PID: 4452)
- ATDHelper.exe (PID: 1184)
The process hide an interactive prompt from the user
- ATDHelper.exe (PID: 4452)
- ATDHelper.exe (PID: 1184)
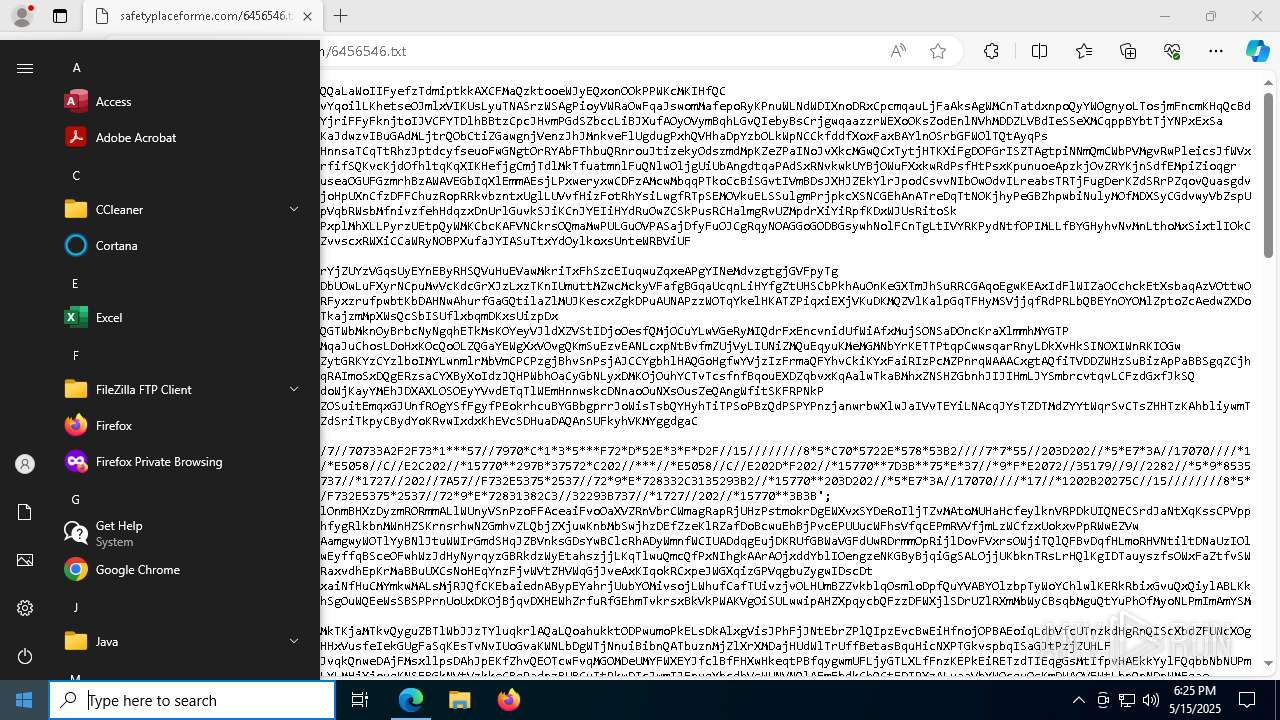
Searches for installed software
- ATDHelper.exe (PID: 4452)
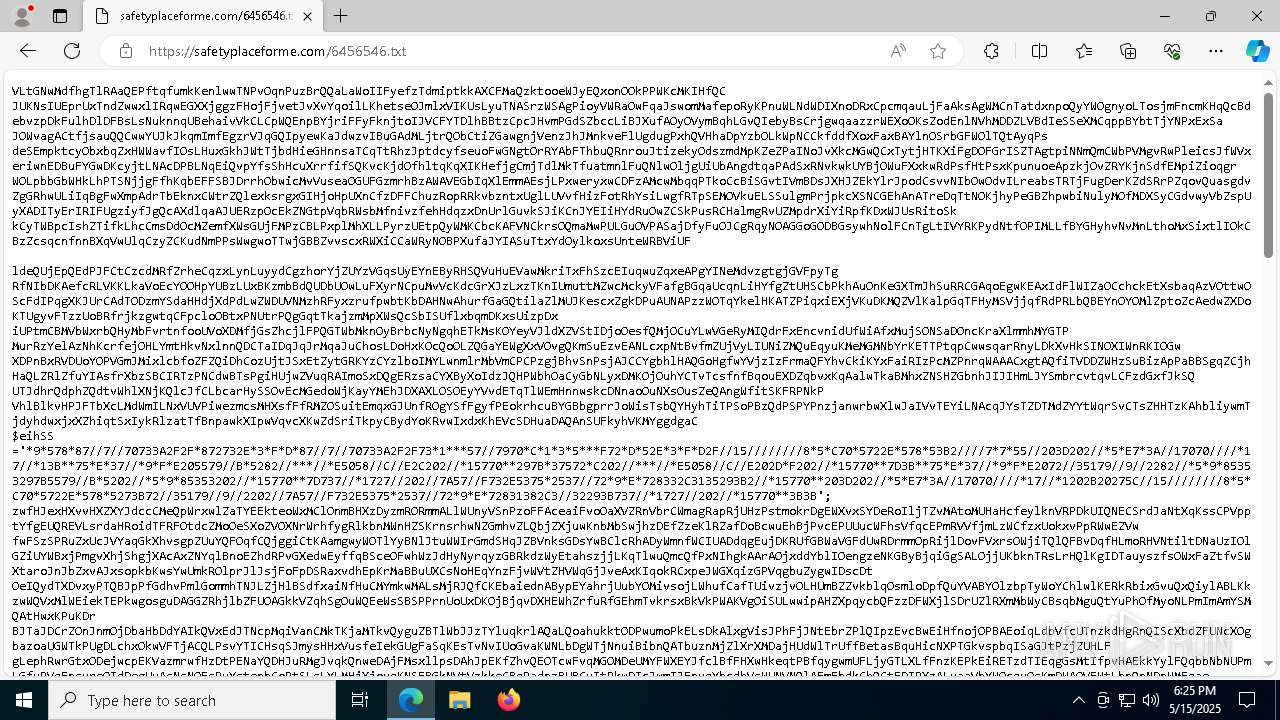
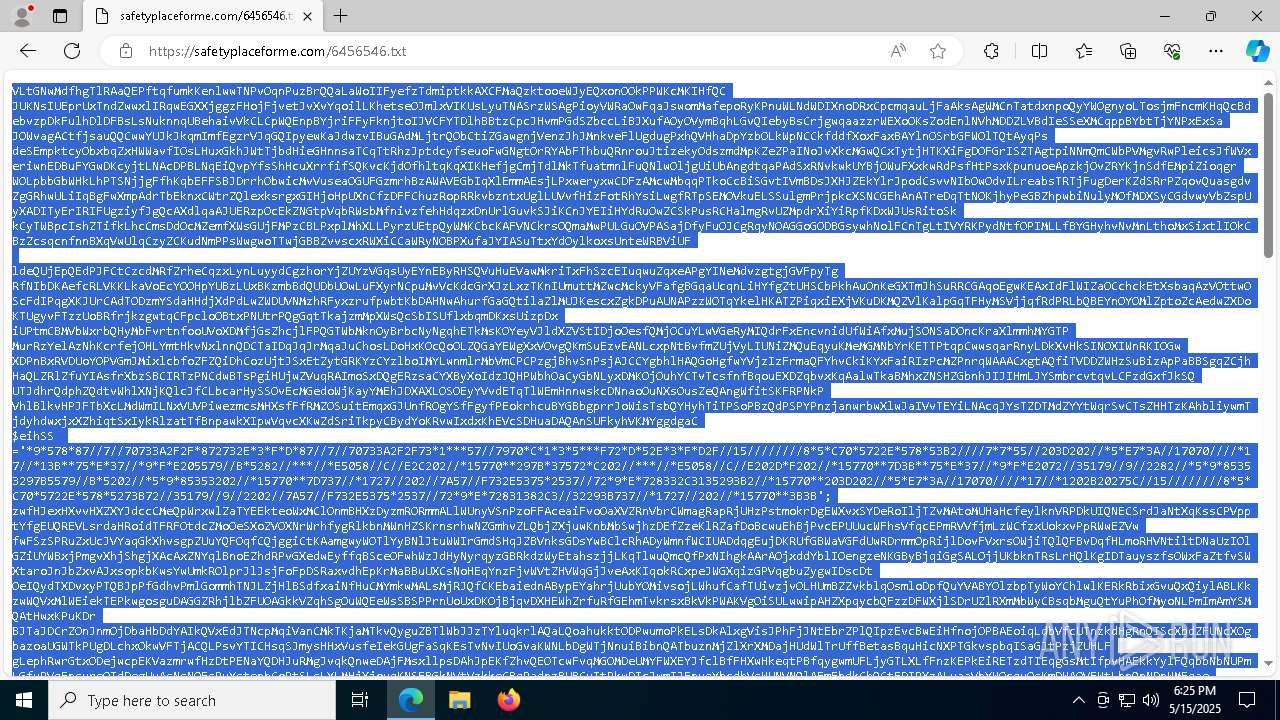
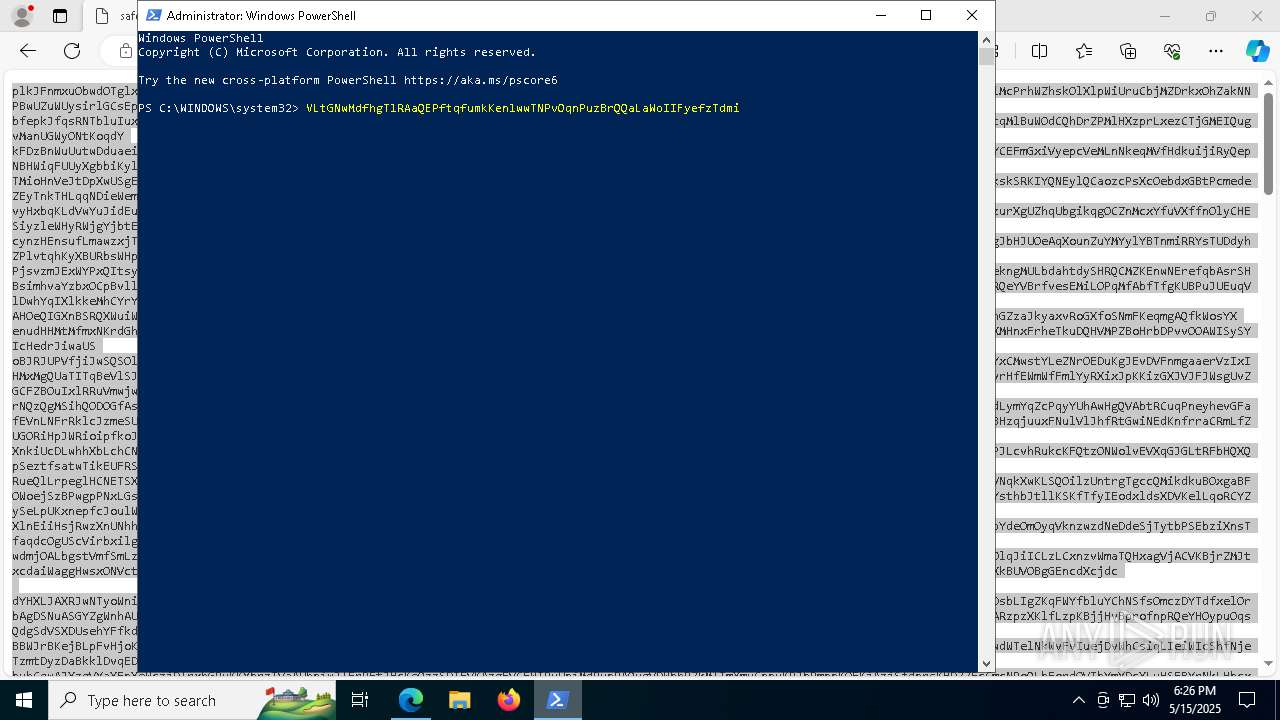
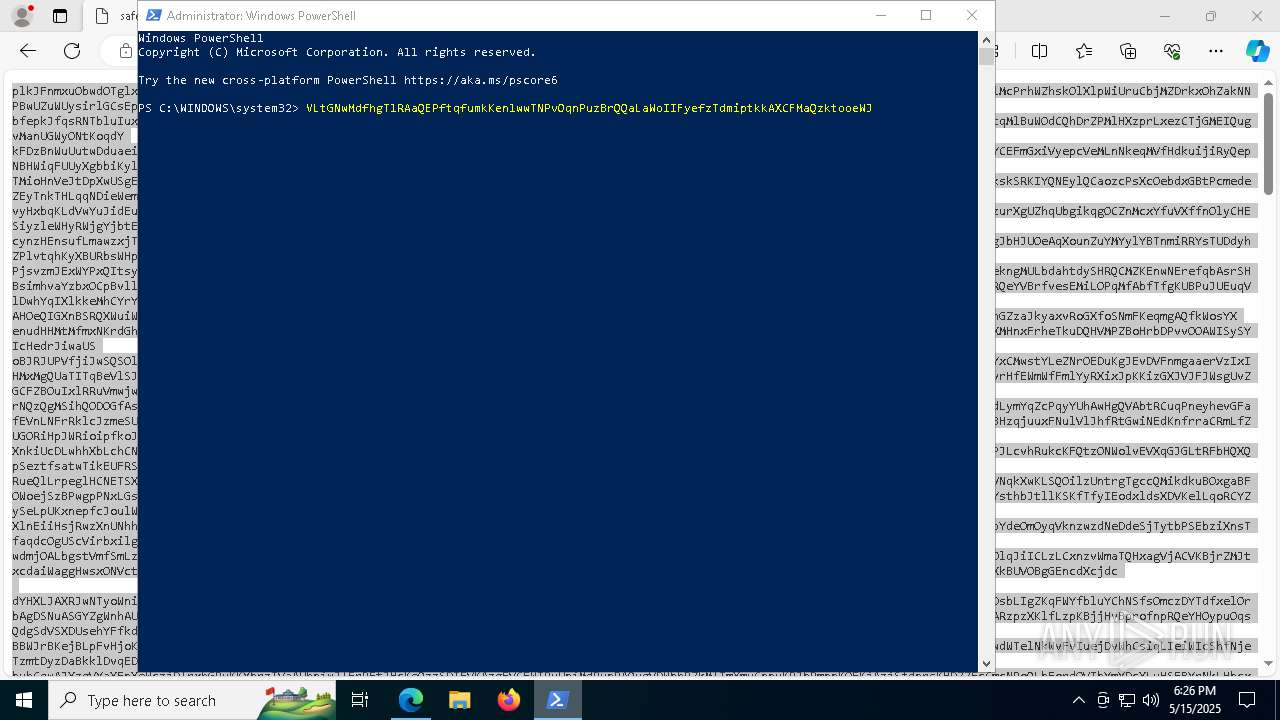
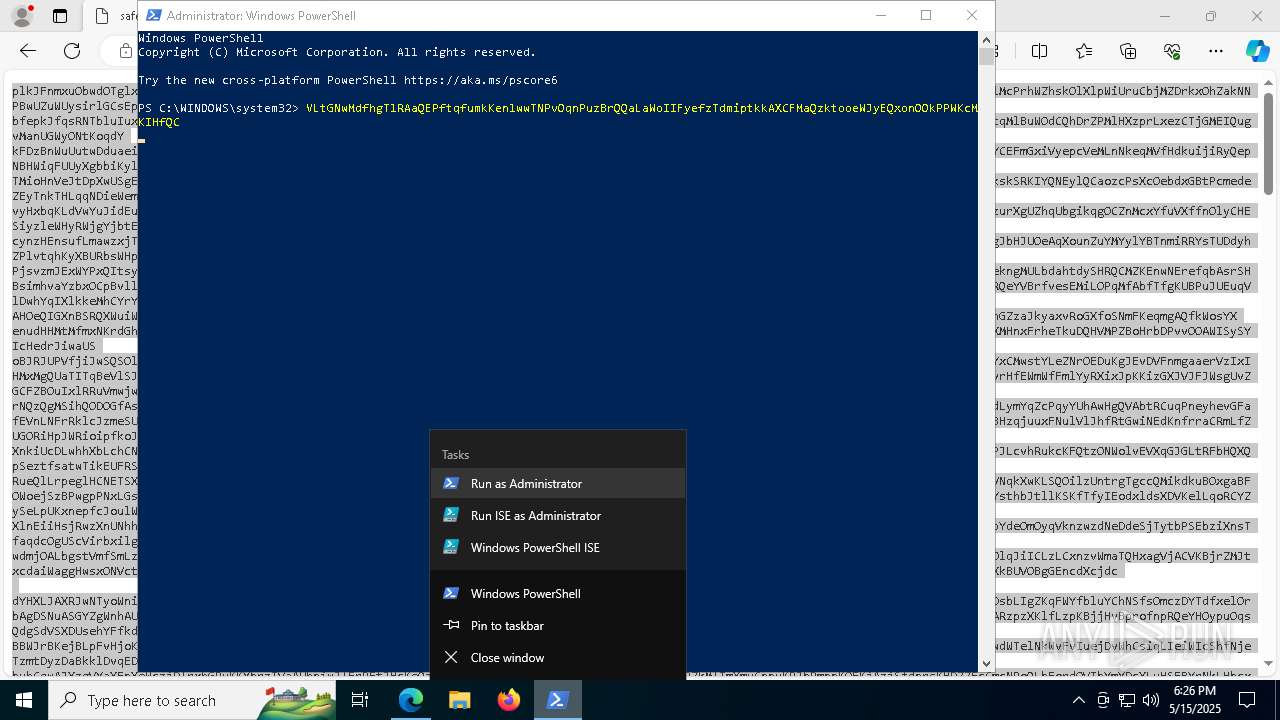
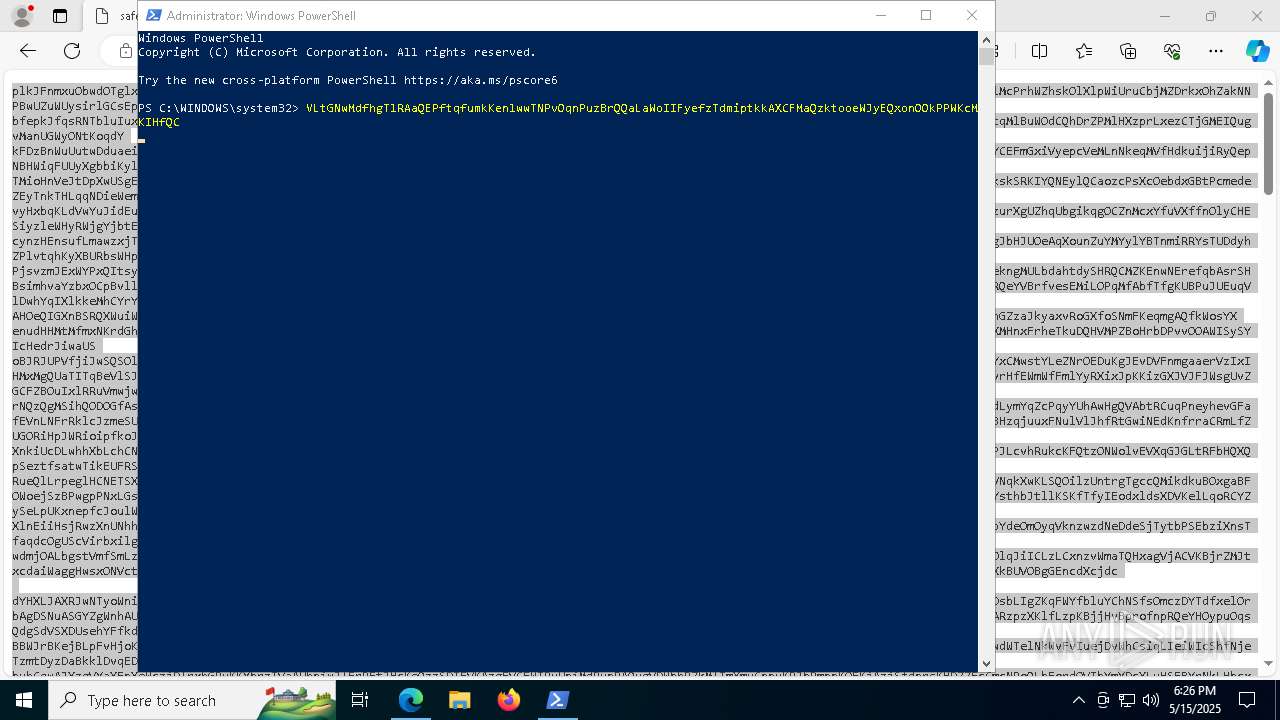
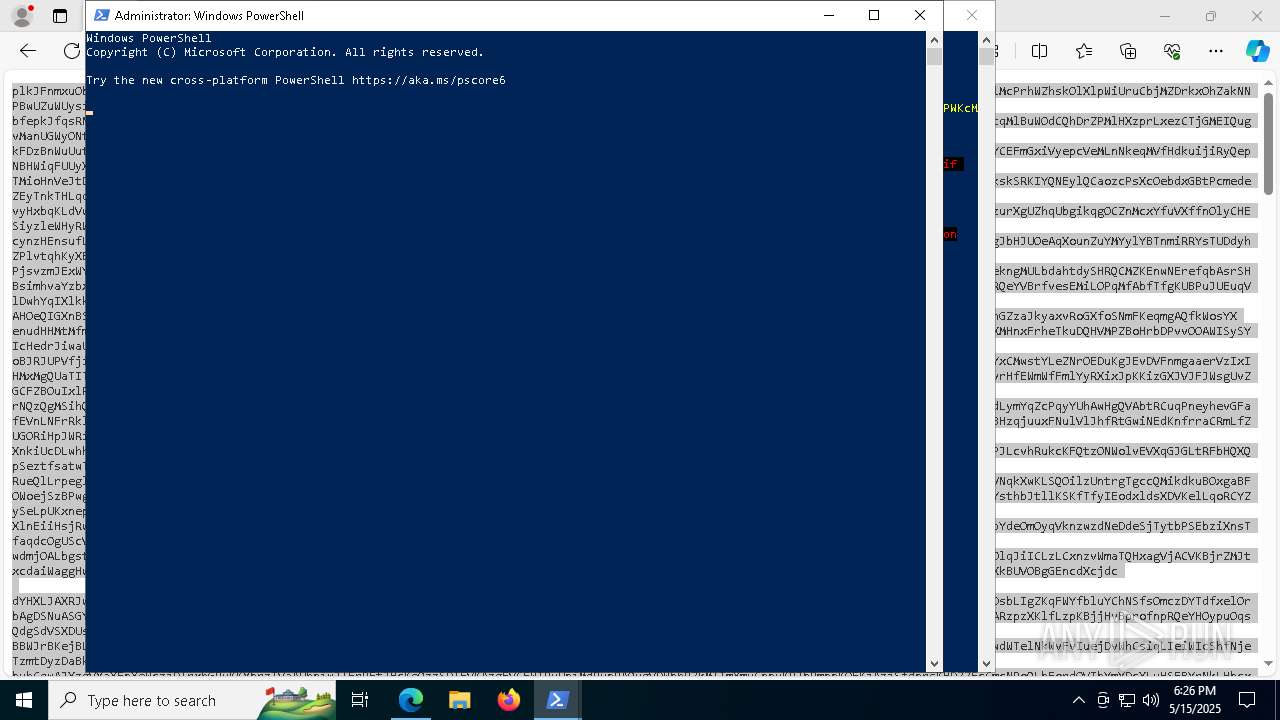
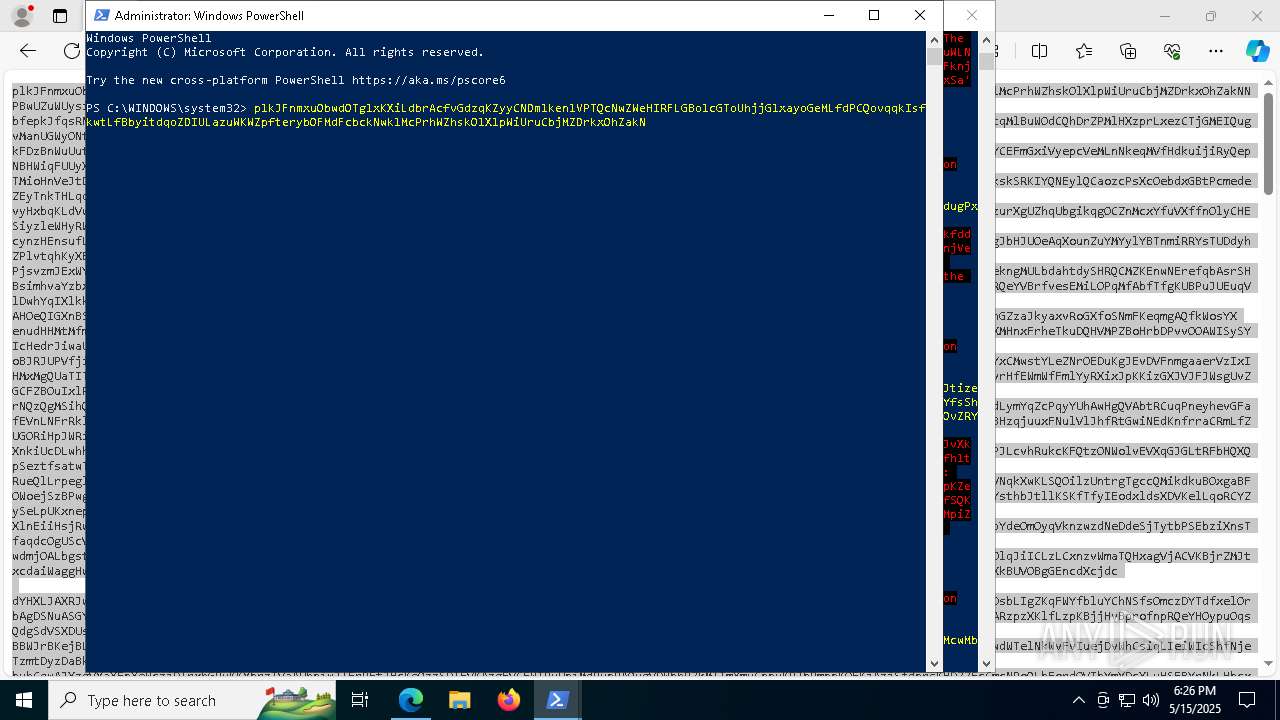
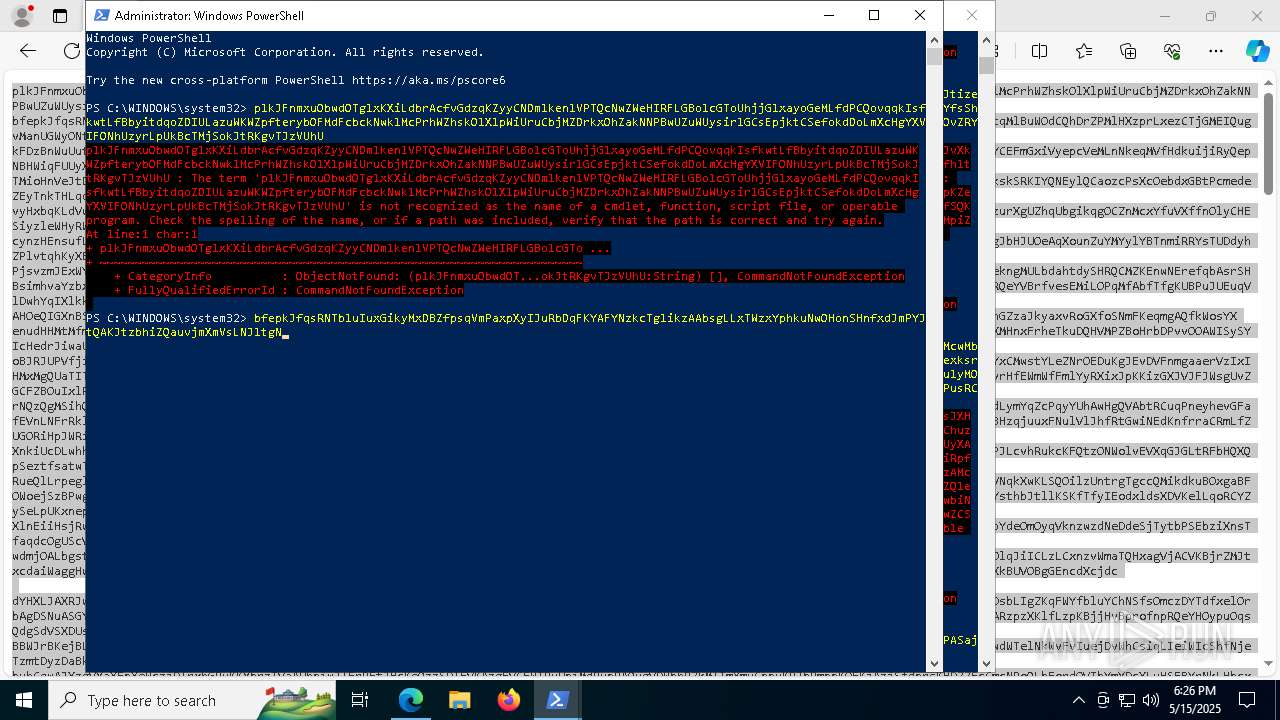
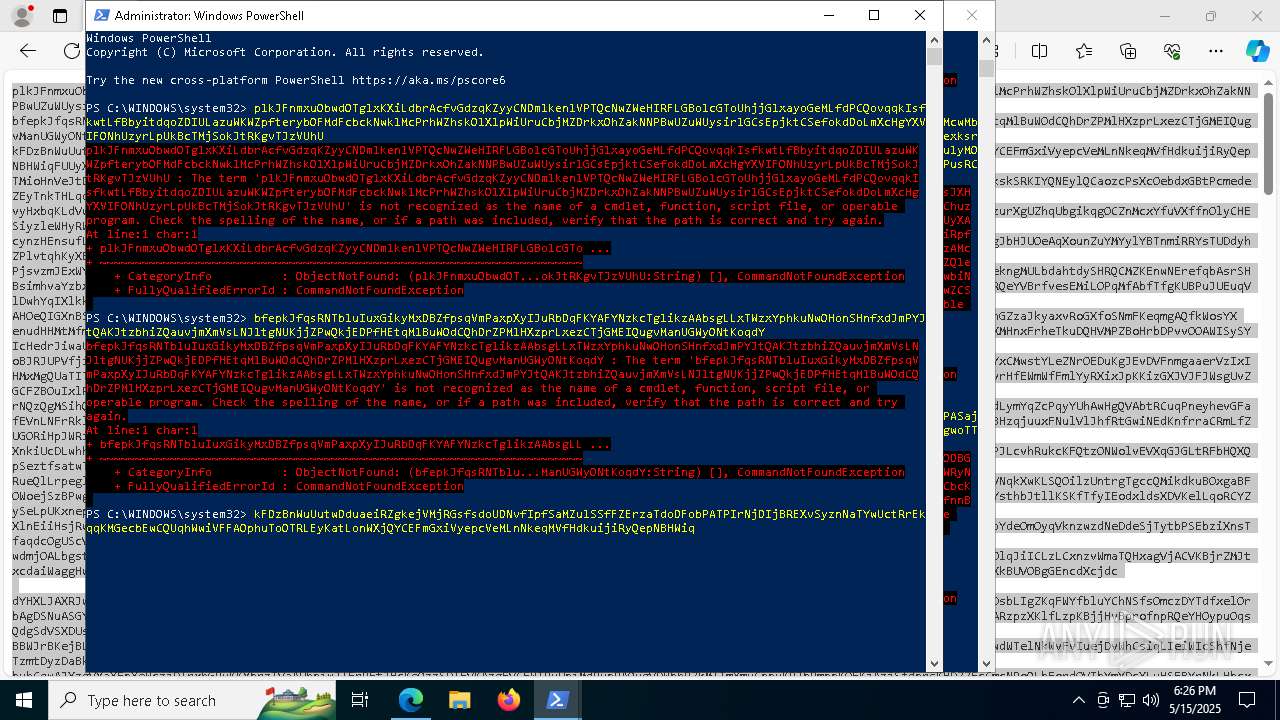
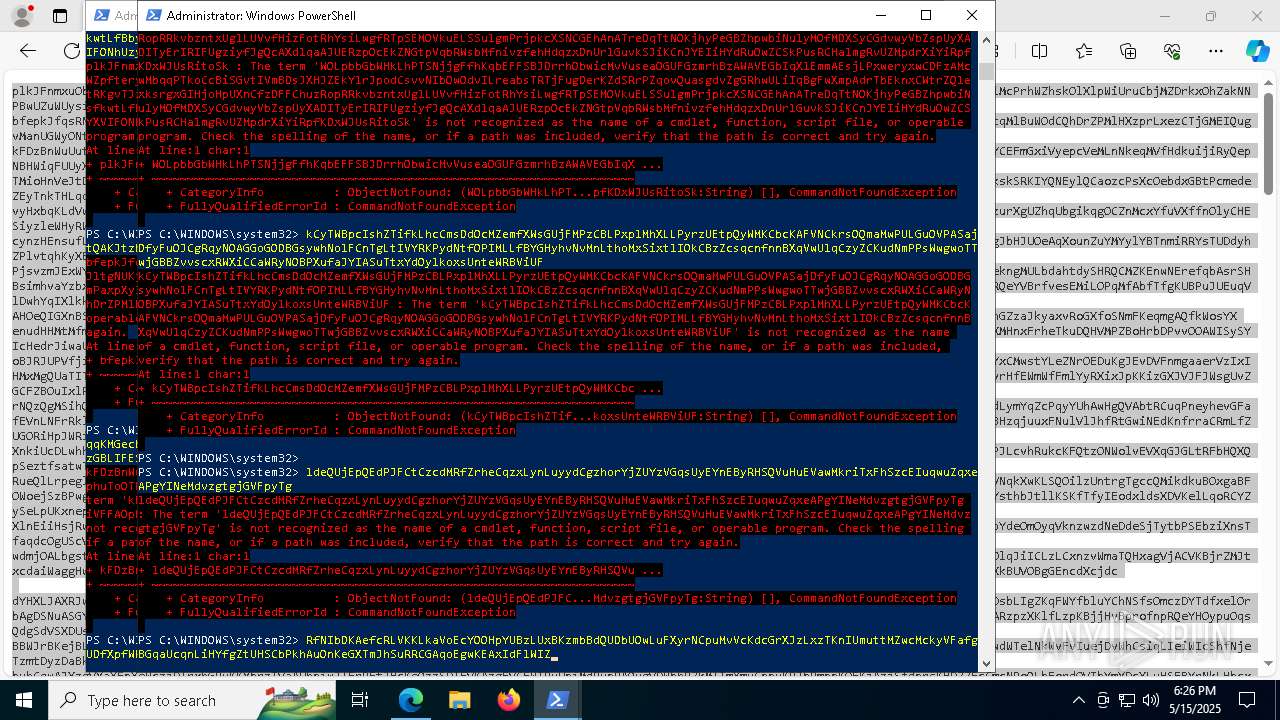
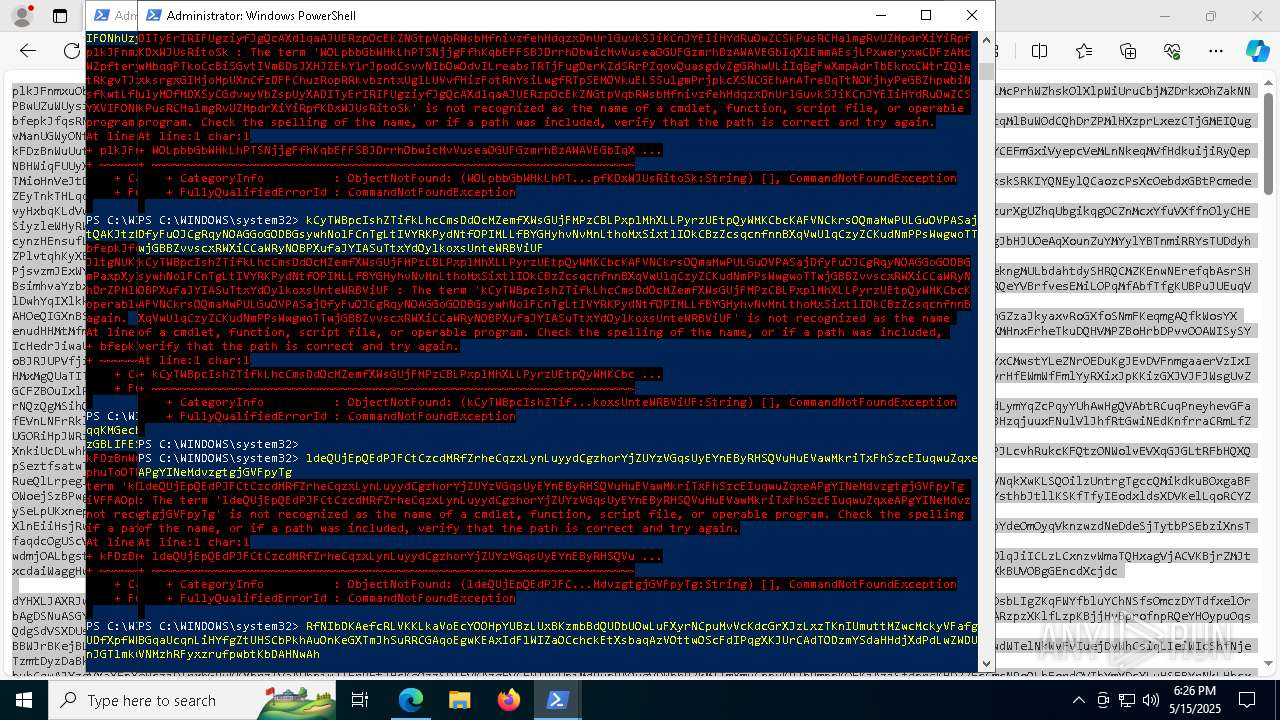
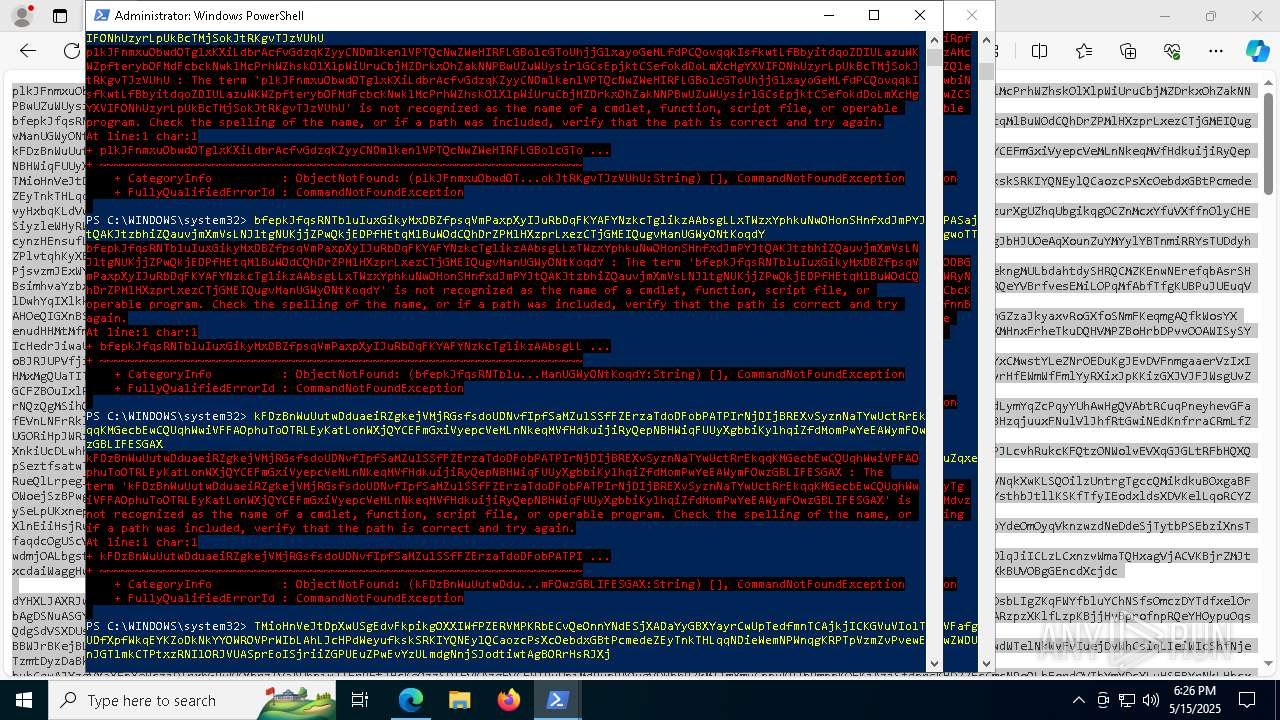
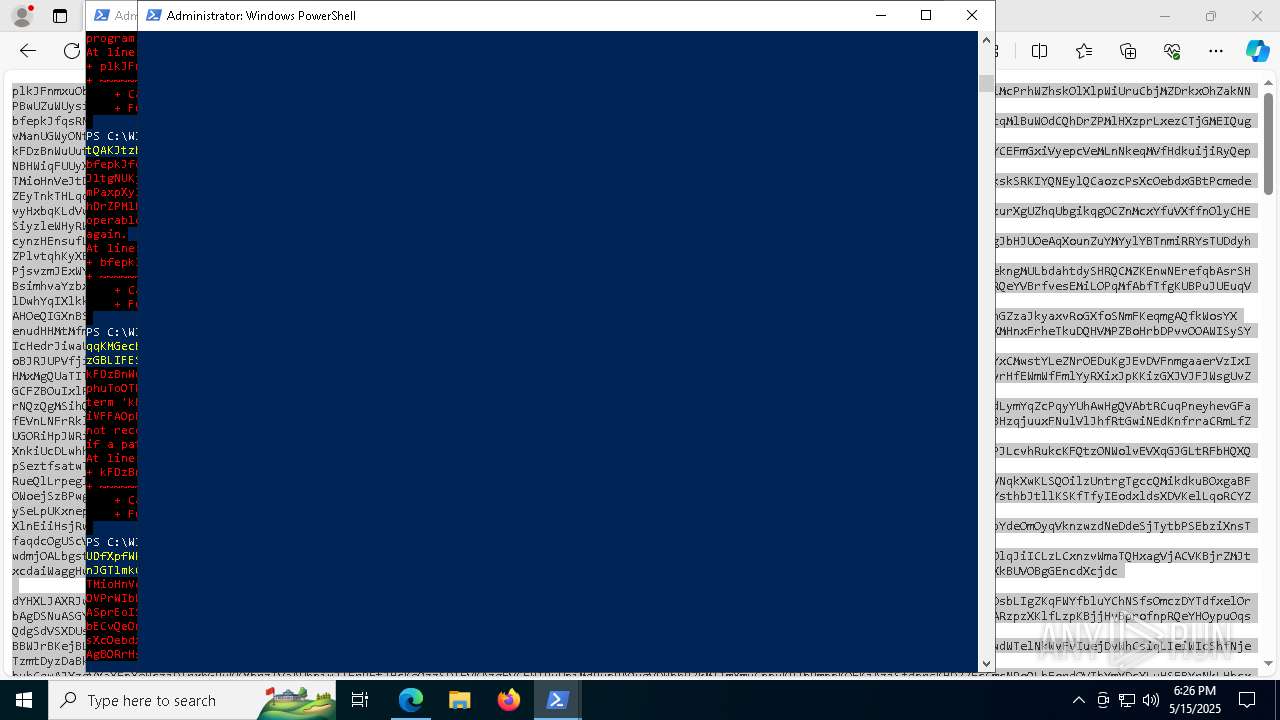
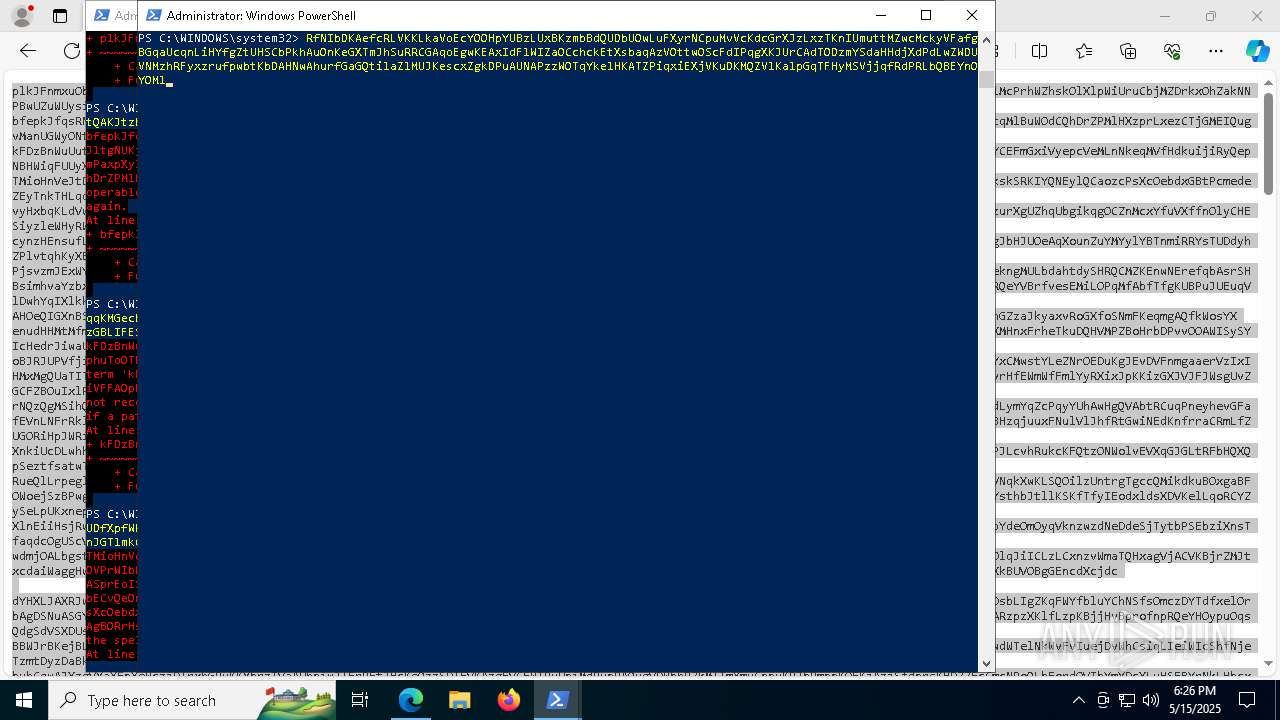
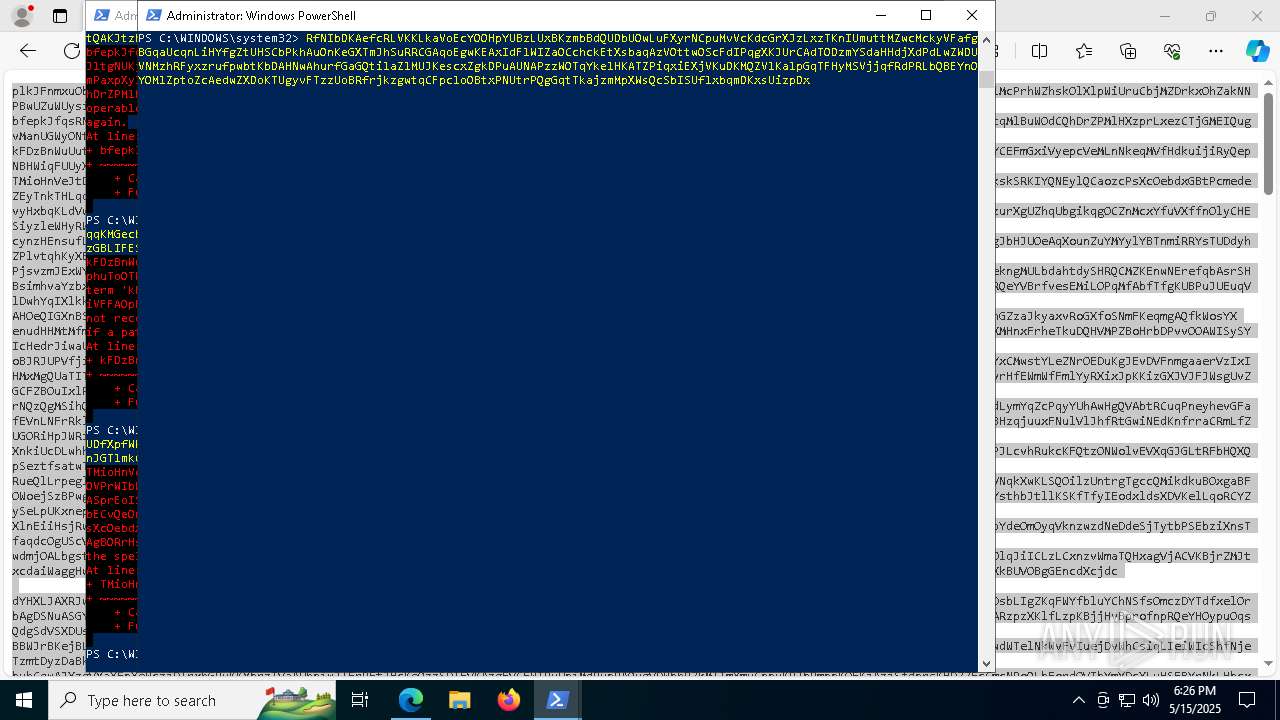
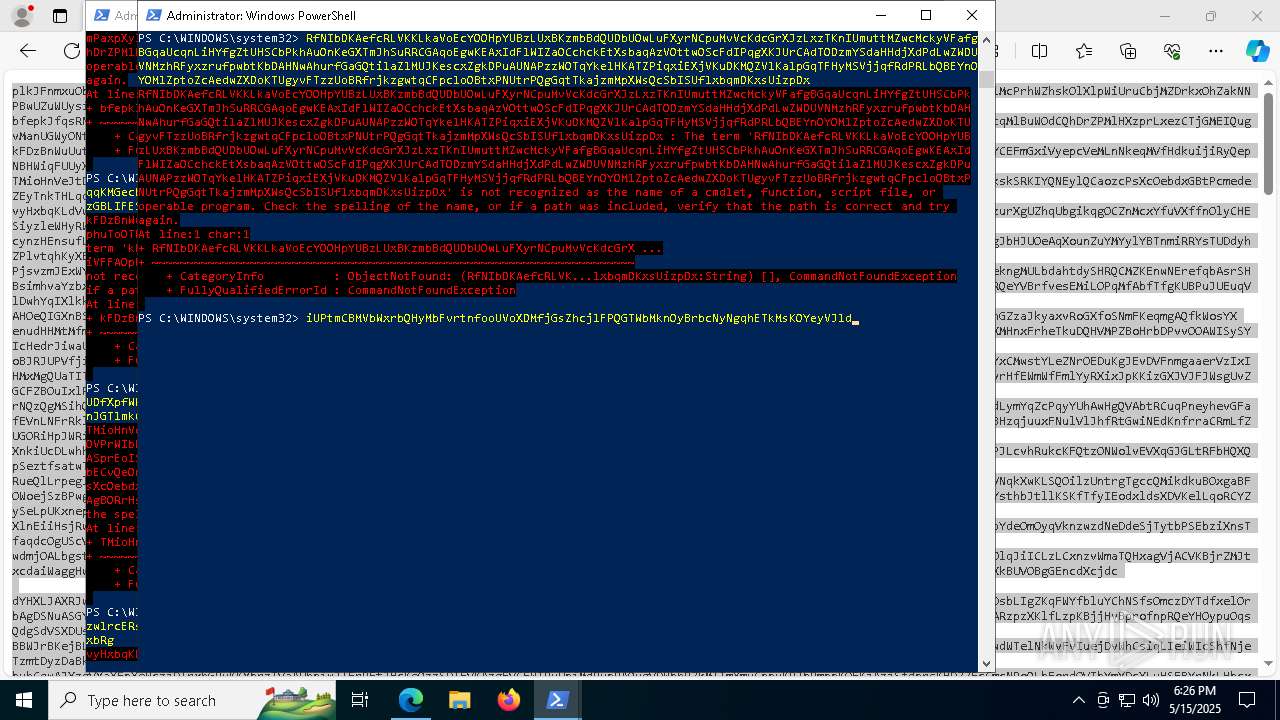
Base64-obfuscated command line is found
- ATDHelper.exe (PID: 4452)
- ATDHelper.exe (PID: 1184)
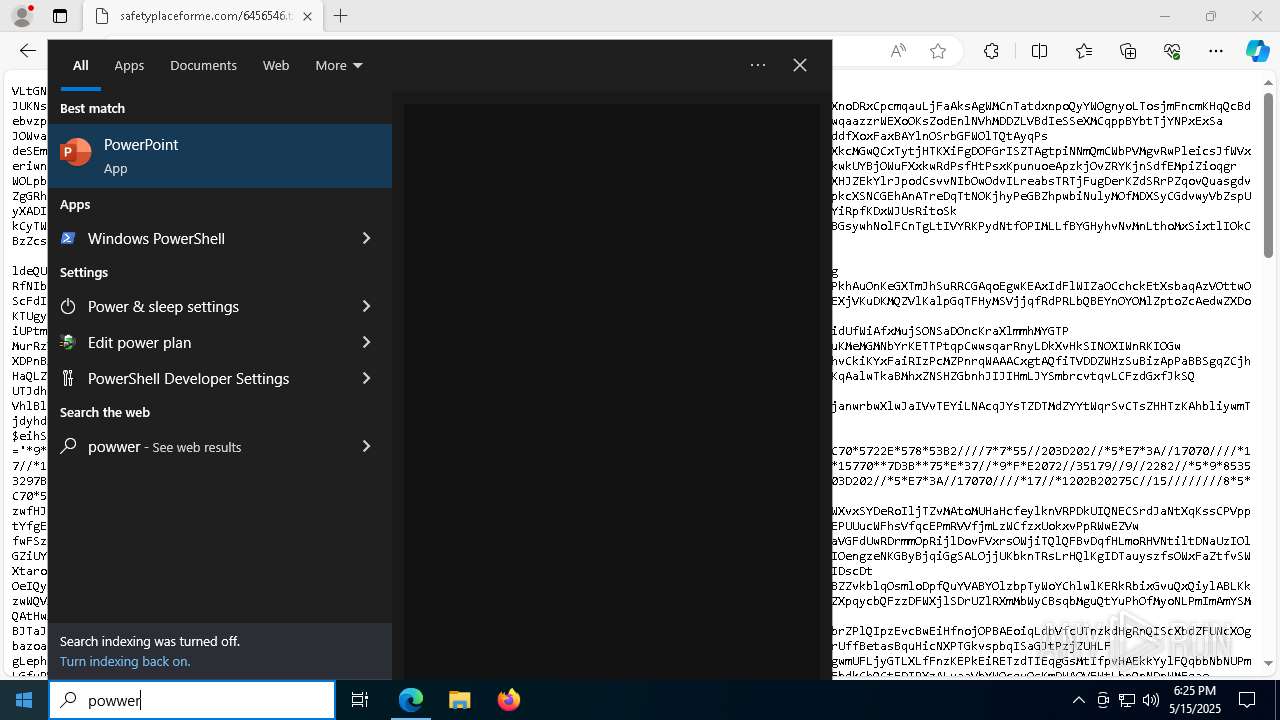
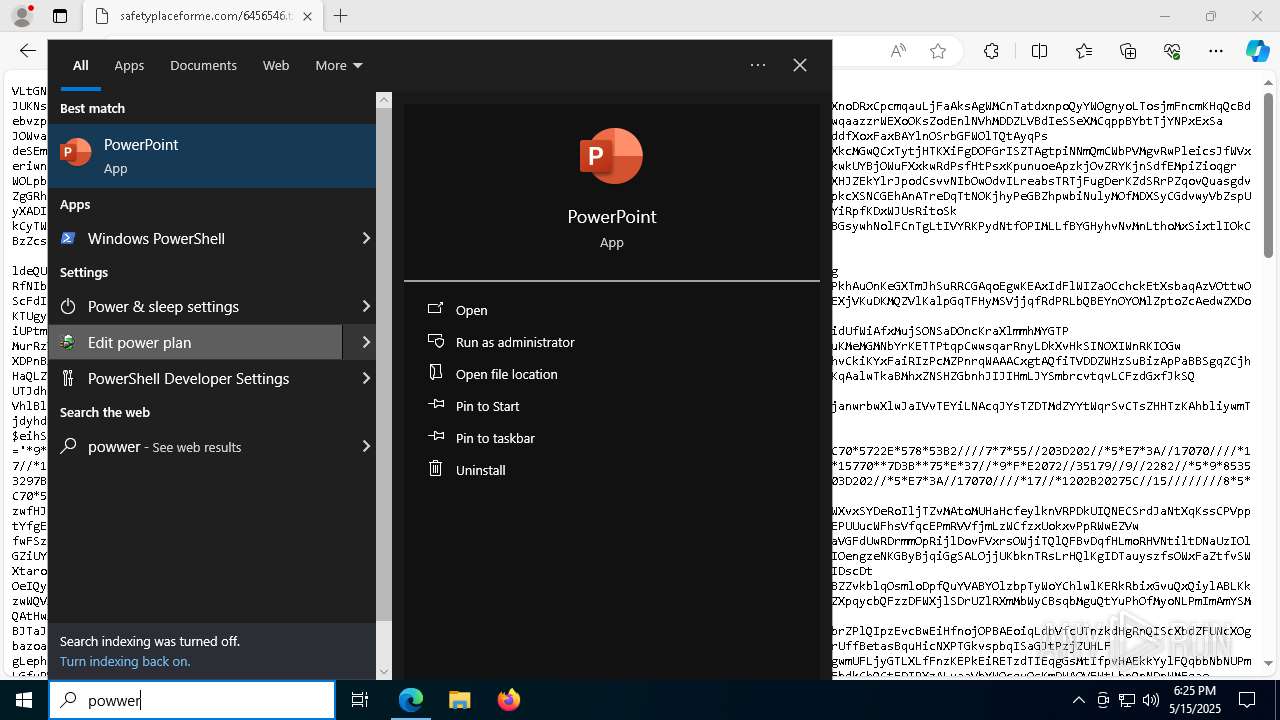
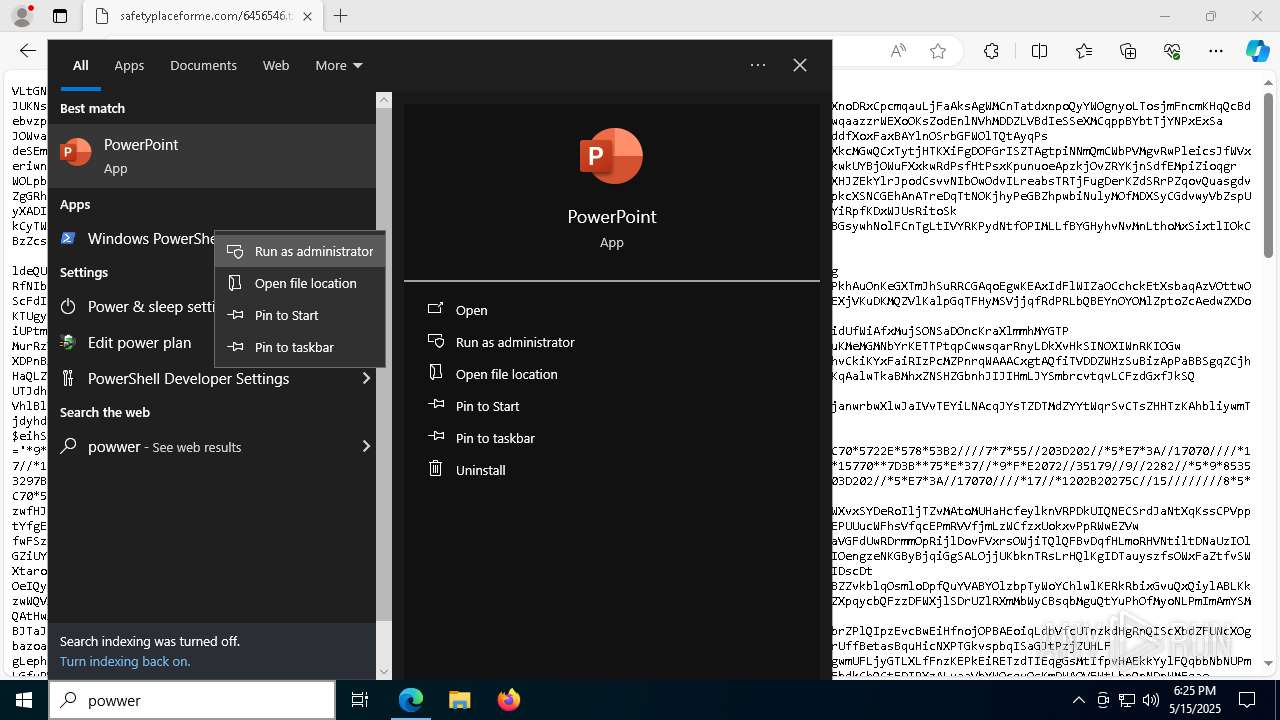
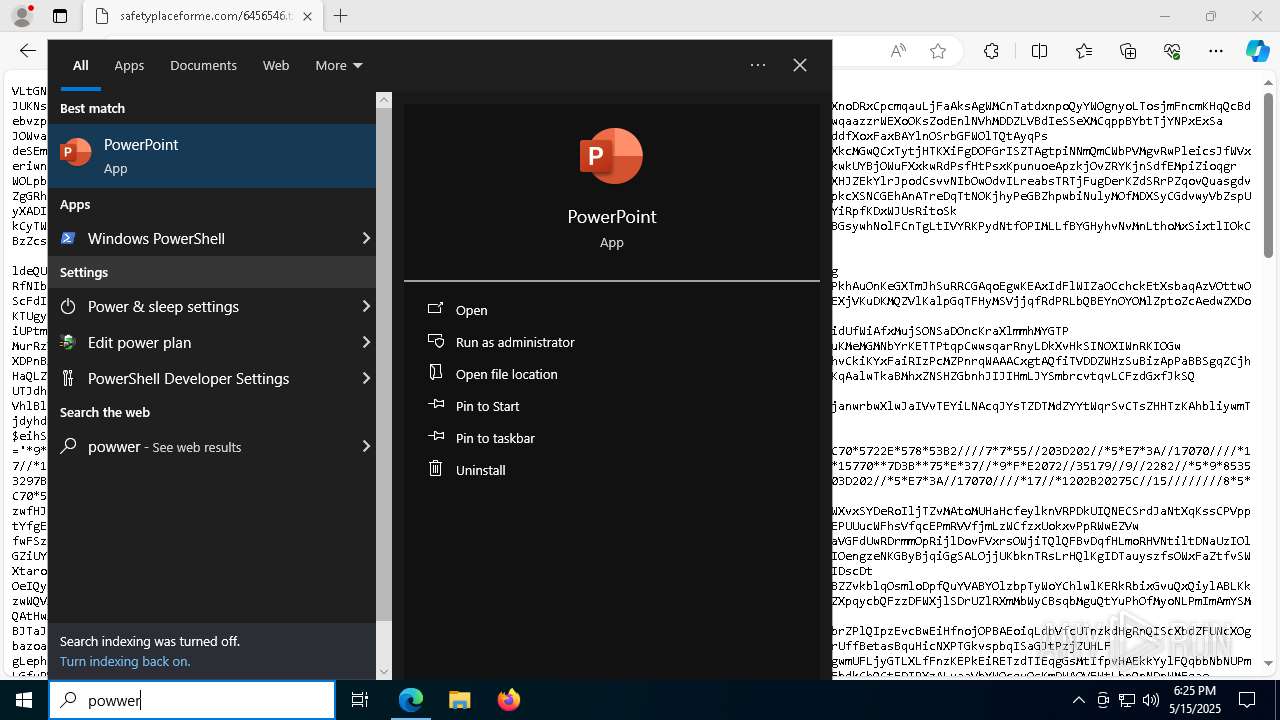
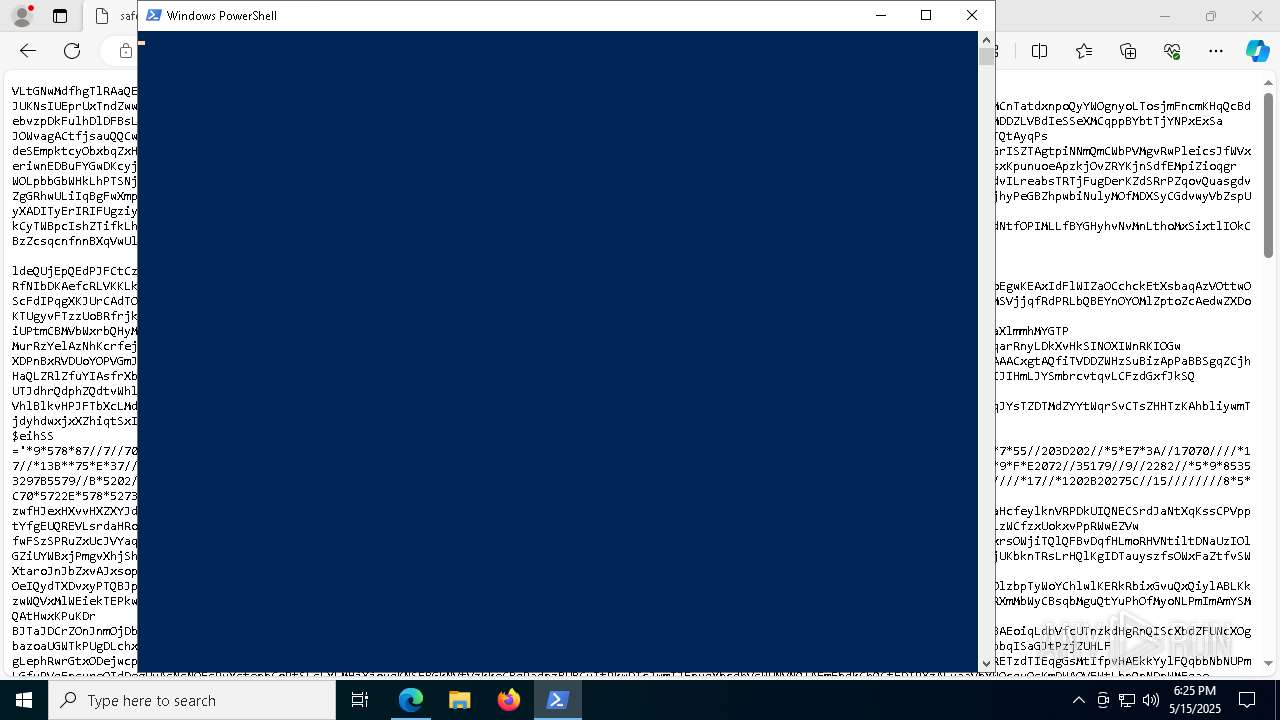
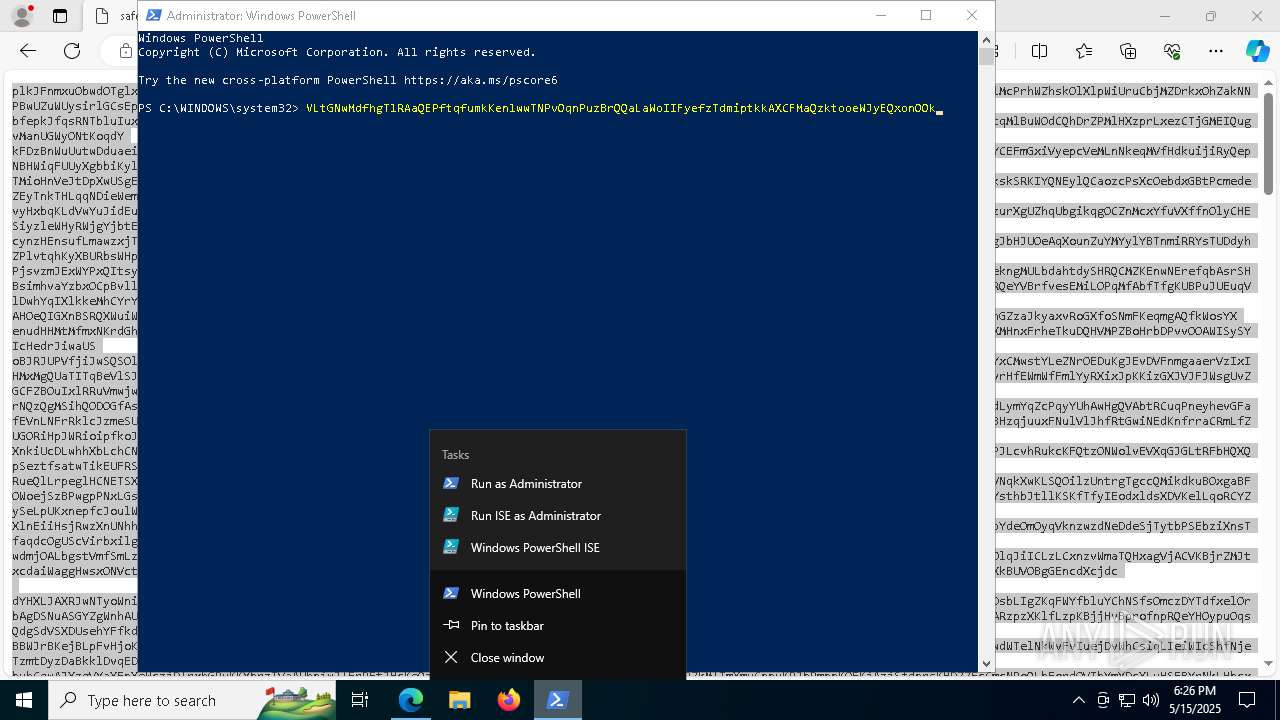
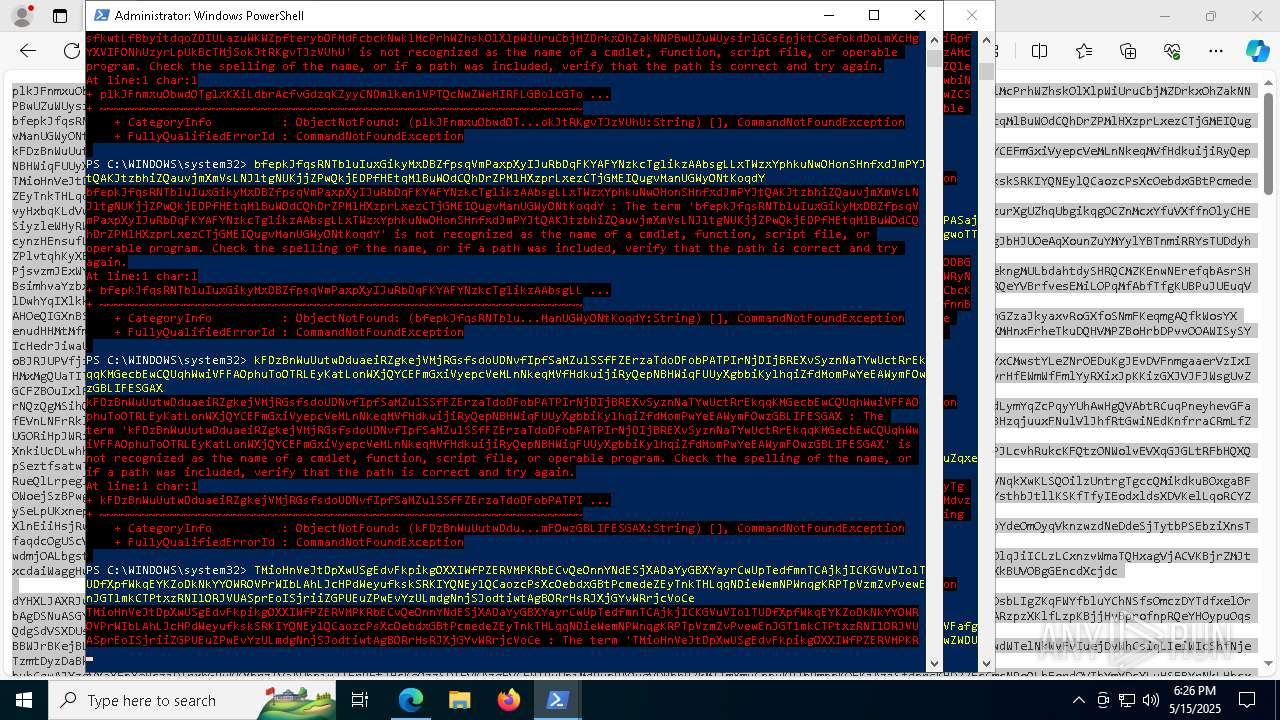
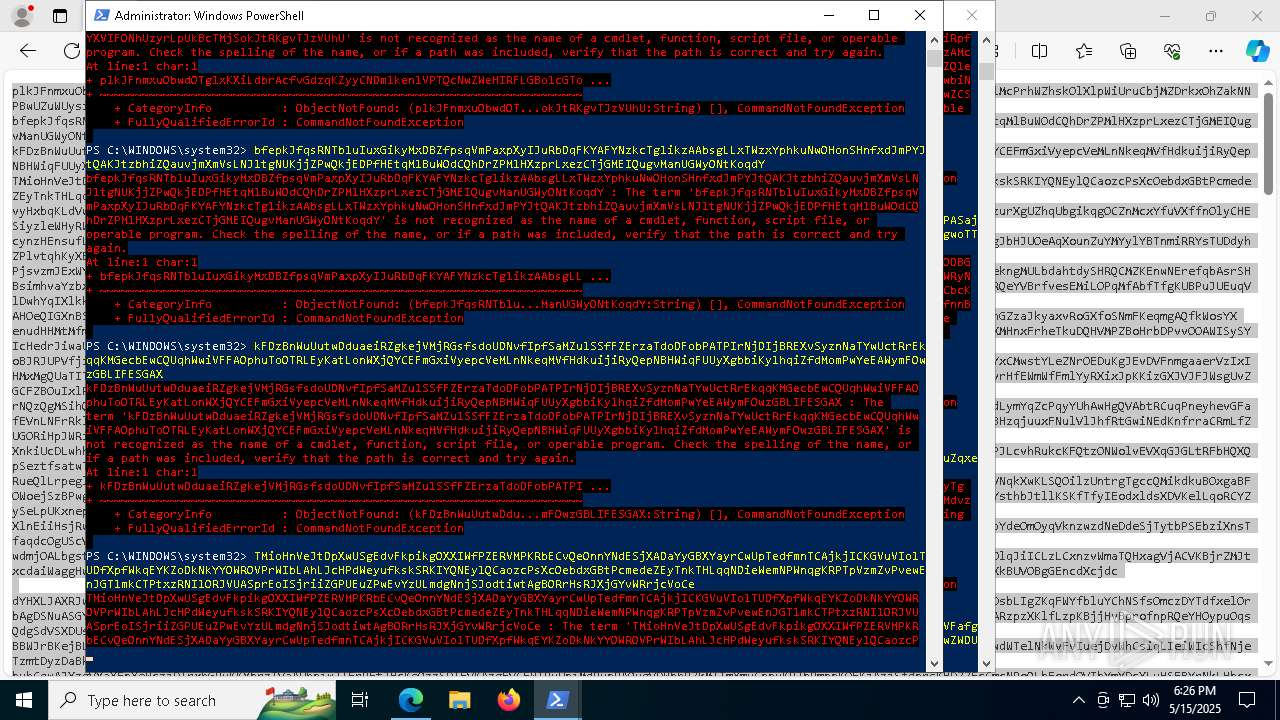
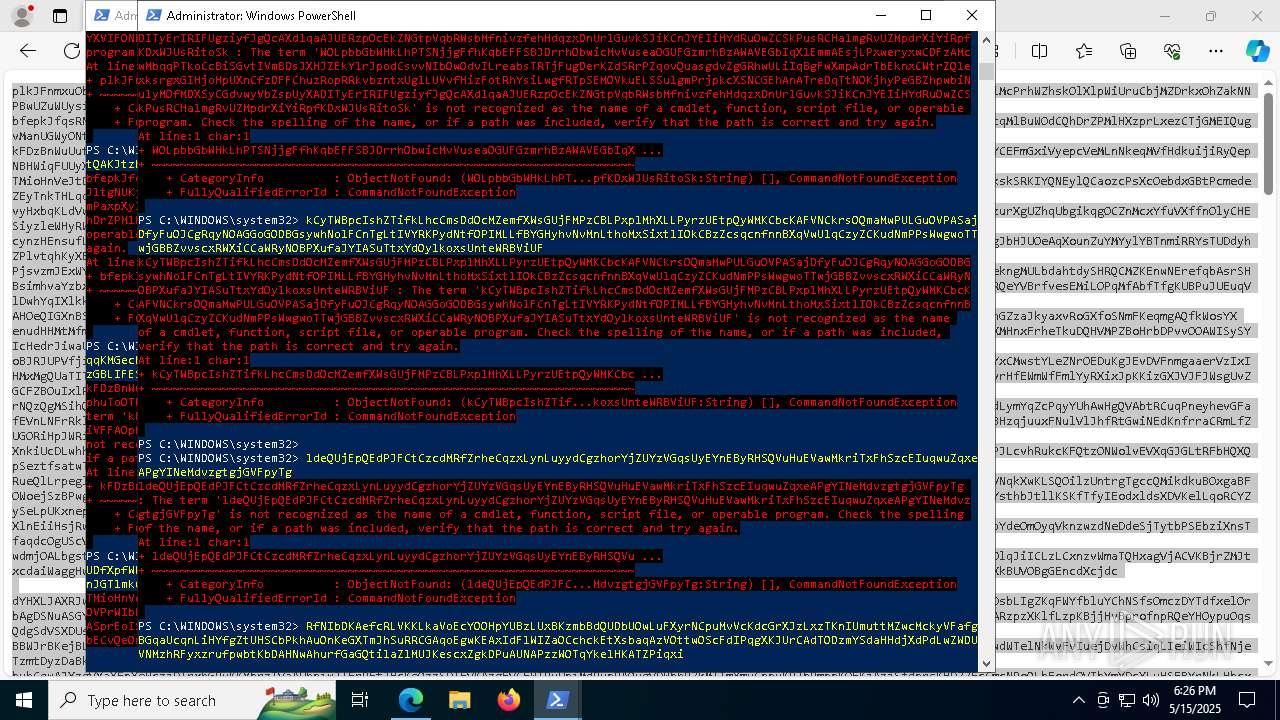
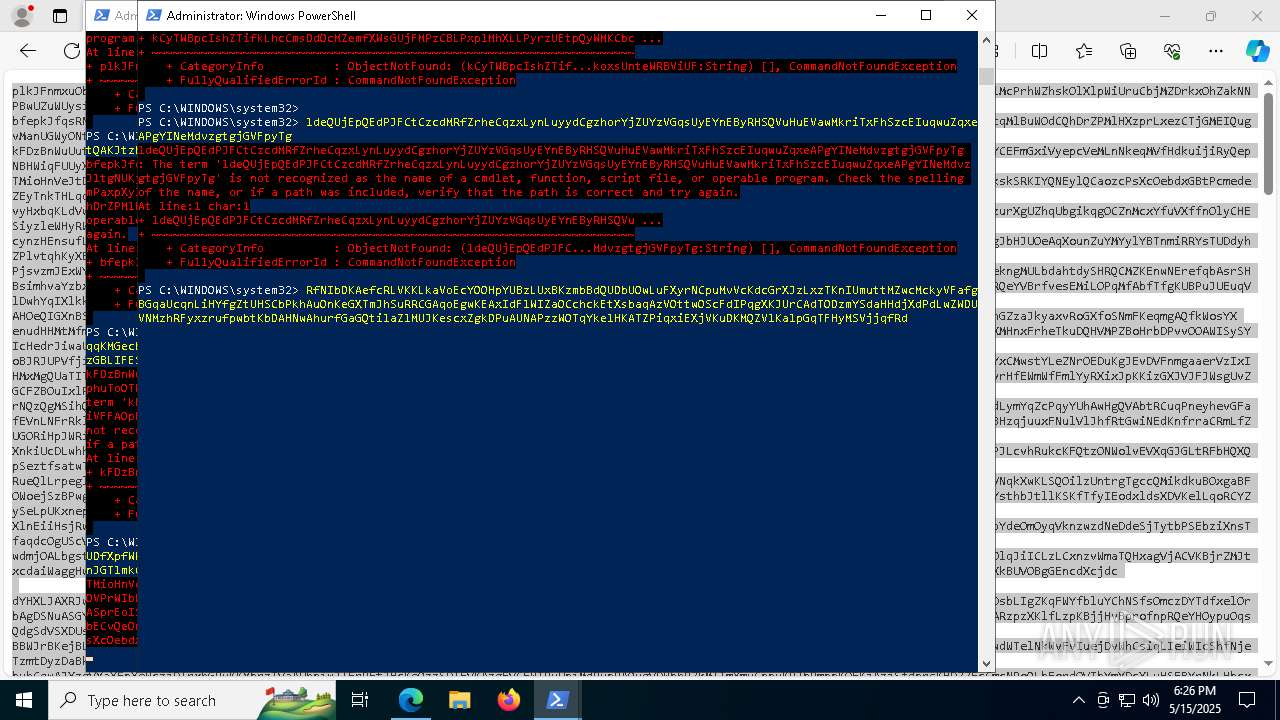
Starts POWERSHELL.EXE for commands execution
- ATDHelper.exe (PID: 4452)
- ATDHelper.exe (PID: 1184)
Executable content was dropped or overwritten
- csc.exe (PID: 8240)
- csc.exe (PID: 8532)
- csc.exe (PID: 9596)
- csc.exe (PID: 9692)
- csc.exe (PID: 872)
- csc.exe (PID: 10108)
- csc.exe (PID: 7372)
- csc.exe (PID: 6656)
- csc.exe (PID: 7524)
- csc.exe (PID: 9908)
- csc.exe (PID: 9512)
- csc.exe (PID: 10088)
- csc.exe (PID: 9872)
- csc.exe (PID: 9296)
- csc.exe (PID: 6744)
- csc.exe (PID: 4188)
- csc.exe (PID: 2432)
- csc.exe (PID: 7464)
- csc.exe (PID: 6256)
- csc.exe (PID: 900)
- csc.exe (PID: 9172)
- csc.exe (PID: 9896)
- csc.exe (PID: 10220)
- csc.exe (PID: 9068)
- csc.exe (PID: 6252)
- csc.exe (PID: 5864)
- csc.exe (PID: 8768)
- csc.exe (PID: 5960)
- csc.exe (PID: 7716)
- csc.exe (PID: 1164)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8532)
- csc.exe (PID: 7524)
- csc.exe (PID: 8240)
- csc.exe (PID: 9692)
- csc.exe (PID: 9908)
- csc.exe (PID: 6656)
- csc.exe (PID: 10108)
- csc.exe (PID: 7372)
- csc.exe (PID: 872)
- csc.exe (PID: 6744)
- csc.exe (PID: 9596)
- csc.exe (PID: 9512)
- csc.exe (PID: 10088)
- csc.exe (PID: 9872)
- csc.exe (PID: 9296)
- csc.exe (PID: 4188)
- csc.exe (PID: 5864)
- csc.exe (PID: 2432)
- csc.exe (PID: 7464)
- csc.exe (PID: 900)
- csc.exe (PID: 9896)
- csc.exe (PID: 9172)
- csc.exe (PID: 10220)
- csc.exe (PID: 9068)
- csc.exe (PID: 7716)
- csc.exe (PID: 8768)
- csc.exe (PID: 6256)
- csc.exe (PID: 1164)
- csc.exe (PID: 5960)
- csc.exe (PID: 6252)
BASE64 encoded PowerShell command has been detected
- ATDHelper.exe (PID: 4452)
- ATDHelper.exe (PID: 1184)
The process bypasses the loading of PowerShell profile settings
- ATDHelper.exe (PID: 4452)
- ATDHelper.exe (PID: 1184)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- amanalytics.exe (PID: 4040)
INFO
Checks supported languages
- identity_helper.exe (PID: 6048)
- ATDHelper.exe (PID: 4452)
- ATDHelper.exe (PID: 1184)
- amanalytics.exe (PID: 4040)
Reads Environment values
- identity_helper.exe (PID: 6048)
- ATDHelper.exe (PID: 4452)
Executable content was dropped or overwritten
- msedge.exe (PID: 7452)
- msedge.exe (PID: 7180)
Application launched itself
- msedge.exe (PID: 7180)
- chrome.exe (PID: 4212)
- chrome.exe (PID: 8920)
- chrome.exe (PID: 8356)
- chrome.exe (PID: 8512)
- chrome.exe (PID: 8624)
- chrome.exe (PID: 8768)
- chrome.exe (PID: 9056)
- chrome.exe (PID: 4208)
- chrome.exe (PID: 720)
- chrome.exe (PID: 7216)
- chrome.exe (PID: 8820)
- chrome.exe (PID: 9132)
- chrome.exe (PID: 9984)
- chrome.exe (PID: 10232)
- chrome.exe (PID: 6264)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 9052)
- chrome.exe (PID: 7204)
- chrome.exe (PID: 8756)
- chrome.exe (PID: 9196)
- chrome.exe (PID: 10168)
- chrome.exe (PID: 9740)
- chrome.exe (PID: 9096)
- chrome.exe (PID: 6488)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 9776)
- chrome.exe (PID: 4692)
- chrome.exe (PID: 4236)
- chrome.exe (PID: 9828)
- chrome.exe (PID: 5980)
- msedge.exe (PID: 6300)
Reads the computer name
- identity_helper.exe (PID: 6048)
- ATDHelper.exe (PID: 4452)
- ATDHelper.exe (PID: 1184)
- amanalytics.exe (PID: 4040)
The sample compiled with english language support
- msedge.exe (PID: 7452)
- msedge.exe (PID: 7180)
Creates files in the program directory
- ATDHelper.exe (PID: 4452)
Checks proxy server information
- ATDHelper.exe (PID: 4452)
Reads the machine GUID from the registry
- ATDHelper.exe (PID: 4452)
Reads the software policy settings
- ATDHelper.exe (PID: 4452)
- amanalytics.exe (PID: 4040)
Reads product name
- ATDHelper.exe (PID: 4452)
Reads CPU info
- ATDHelper.exe (PID: 4452)
Create files in a temporary directory
- ATDHelper.exe (PID: 4452)
Creates files or folders in the user directory
- ATDHelper.exe (PID: 4452)
Manual execution by a user
- powershell.exe (PID: 6048)
- powershell.exe (PID: 10116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
406
Monitored processes
266
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | C:\WINDOWS\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {c82192ee-6cb5-4bc0-9ef0-fb818773790a} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2036 --field-trial-handle=2080,i,16255307182849570944,1195386711193201536,262144 --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7300 --field-trial-handle=2140,i,6897289754848140258,15580308199561753083,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x240,0x244,0x248,0x21c,0x24c,0x7ffc8945dc40,0x7ffc8945dc4c,0x7ffc8945dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | ATDHelper.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 21 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=5784 --field-trial-handle=2140,i,6897289754848140258,15580308199561753083,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESCDBD.tmp" "c:\Users\admin\AppData\Local\Temp\CSC2EEA4905136A4F739B8C82282890F189.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 872 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\rcwfiusp.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 896 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\2q20wogi.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
200 367
Read events
200 232
Write events
135
Delete events
0
Modification events
| (PID) Process: | (6436) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6436) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6436) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6436) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (6436) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (6436) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7180) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
53
Suspicious files
252
Text files
321
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ca85.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ca95.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ca95.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ca85.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10cab4.TMP | — | |
MD5:— | SHA256:— | |||
| 7180 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
119
DNS requests
92
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7180 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
7180 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
7180 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEAo8CbcVhHpJiSTn1ZOLlMU%3D | unknown | — | — | whitelisted |
7180 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | unknown | — | — | whitelisted |
7180 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVD%2BnGf79Hpedv3mhy6uKMVZkPCQQUDyrLIIcouOxvSK4rVKYpqhekzQwCEQDgTz9beMpNcQ8Vir%2F%2BBQ%2BX | unknown | — | — | whitelisted |
1272 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1272 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1852 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7452 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7180 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7452 | msedge.exe | 188.114.96.3:443 | safetyplaceforme.com | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
safetyplaceforme.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7452 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7452 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
4452 | ATDHelper.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (flowerexju .bet) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (zmedtipp .live) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (araucahkbm .live) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (easterxeen .run) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (overcovtcg .top) |
4040 | amanalytics.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (overcovtcg .top) in TLS SNI |