| File name: | sample.exe |
| Full analysis: | https://app.any.run/tasks/f50bf434-cd69-4fa4-9d42-daf43951298a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 20, 2025, 07:49:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 8EAB32C808E341725964B1652BF9D897 |
| SHA1: | 356A38BCDFF89E4CD0C044886B204CFE81A54221 |
| SHA256: | 95BB86DE13D70EE84FAFB0E047BE5EF337E1BD4AC195AC3D3D336276D96DB1D6 |
| SSDEEP: | 49152:OWcYd3vZsTx9NQBPfOyBPGZ4zMqosBEr83RYQGnwoVtlU9AZ6xCg9QM5/l6I8oDr:OWcYd3vZsTx9NQBPfOyBPGZ4zMqosBEW |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- sample.exe (PID: 3952)
Actions looks like stealing of personal data
- sample.exe (PID: 3952)
Connects to the CnC server
- svchost.exe (PID: 2192)
Steals credentials from Web Browsers
- sample.exe (PID: 3952)
LUMMA has been detected (YARA)
- sample.exe (PID: 3952)
Executing a file with an untrusted certificate
- Dashboard.exe (PID: 2280)
- Dashboard.exe (PID: 2800)
- Dashboard.exe (PID: 2088)
Known privilege escalation attack
- dllhost.exe (PID: 4996)
LUMMA mutex has been found
- sample.exe (PID: 3952)
SUSPICIOUS
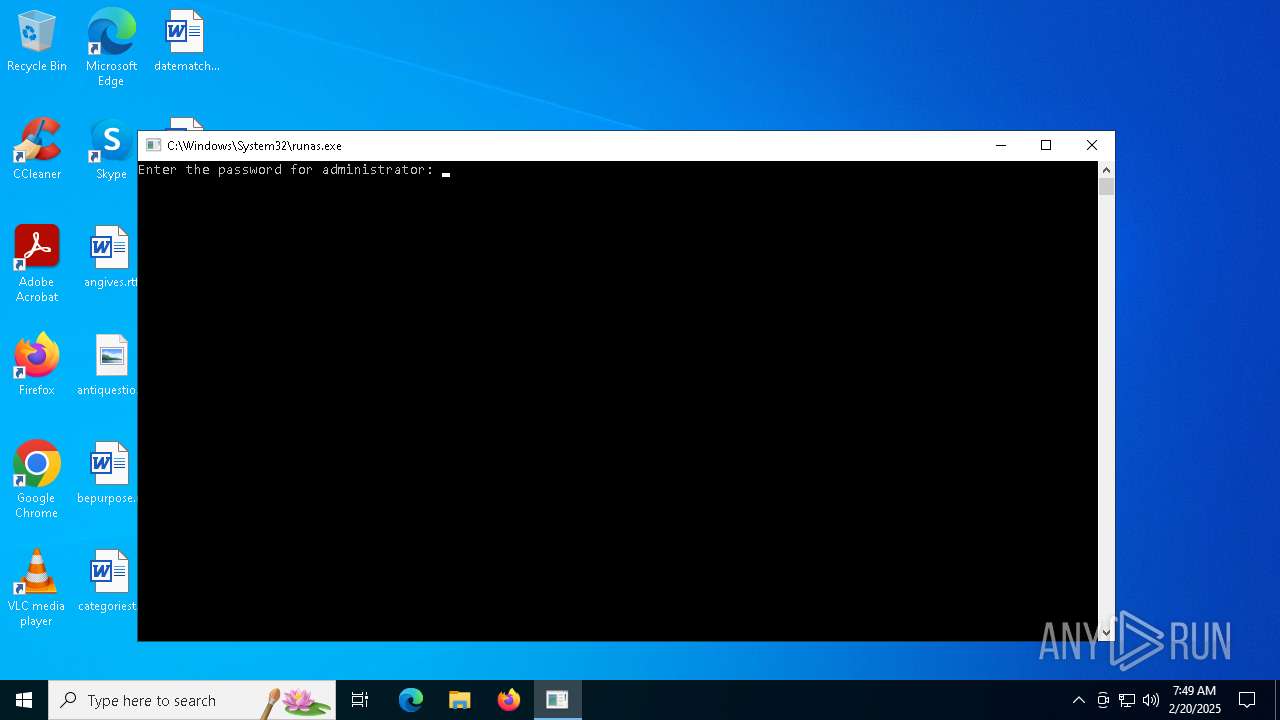
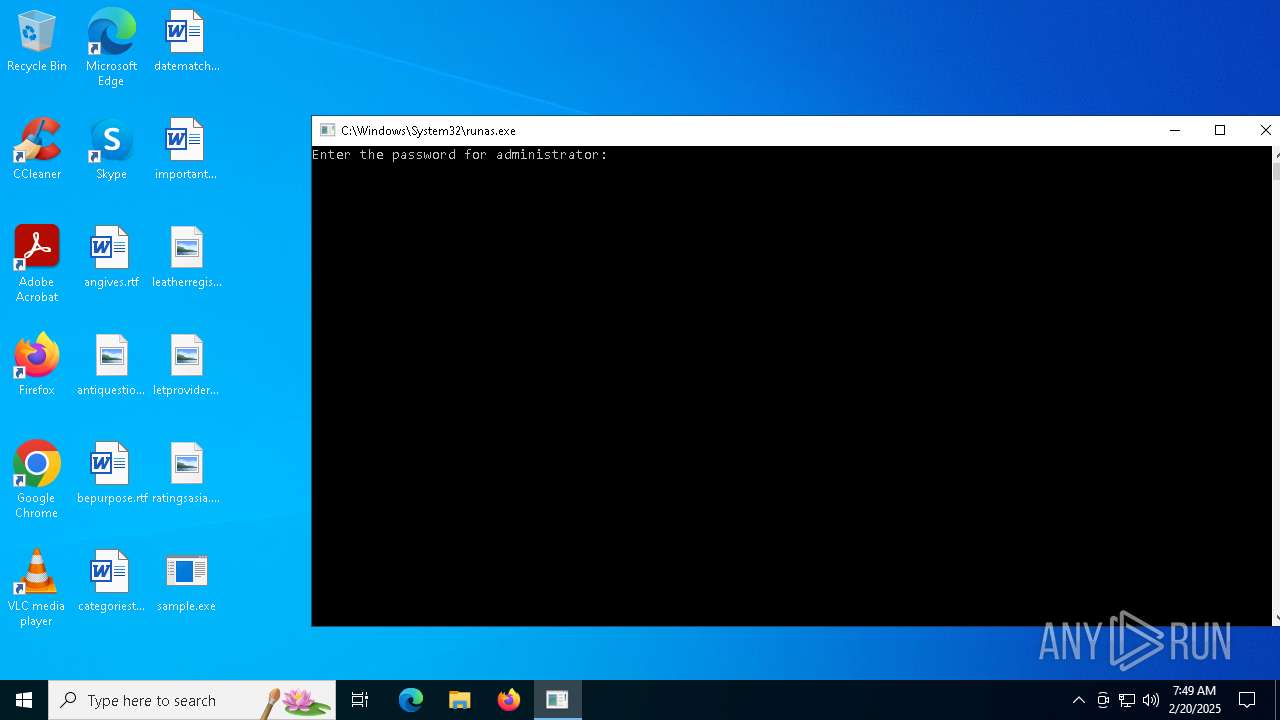
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 3612)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
- sample.exe (PID: 3952)
There is functionality for taking screenshot (YARA)
- sample.exe (PID: 3952)
Searches for installed software
- sample.exe (PID: 3952)
Executable content was dropped or overwritten
- sample.exe (PID: 3952)
- Dashboard.exe (PID: 2280)
The process drops C-runtime libraries
- sample.exe (PID: 3952)
- Dashboard.exe (PID: 2280)
Process drops legitimate windows executable
- sample.exe (PID: 3952)
- Dashboard.exe (PID: 2280)
Starts a Microsoft application from unusual location
- Dashboard.exe (PID: 2280)
Starts itself from another location
- Dashboard.exe (PID: 2280)
Starts CMD.EXE for commands execution
- Dashboard.exe (PID: 2800)
- Dashboard.exe (PID: 2088)
Connects to unusual port
- explorer.exe (PID: 4944)
INFO
Reads the computer name
- sample.exe (PID: 4136)
- sample.exe (PID: 3952)
- Dashboard.exe (PID: 2800)
- Dashboard.exe (PID: 2280)
- Dashboard.exe (PID: 2088)
Reads the machine GUID from the registry
- sample.exe (PID: 4136)
Reads the software policy settings
- sample.exe (PID: 3952)
- sample.exe (PID: 4136)
- explorer.exe (PID: 4944)
Checks supported languages
- sample.exe (PID: 4136)
- sample.exe (PID: 3952)
- Dashboard.exe (PID: 2280)
- Dashboard.exe (PID: 2800)
- Dashboard.exe (PID: 2088)
Checks proxy server information
- sample.exe (PID: 4136)
Creates files in the program directory
- sample.exe (PID: 3952)
Disables trace logs
- sample.exe (PID: 4136)
Manual execution by a user
- sample.exe (PID: 3952)
- sample.exe (PID: 4136)
The sample compiled with english language support
- sample.exe (PID: 3952)
- Dashboard.exe (PID: 2280)
Create files in a temporary directory
- sample.exe (PID: 3952)
- Dashboard.exe (PID: 2800)
- Dashboard.exe (PID: 2088)
Creates files or folders in the user directory
- Dashboard.exe (PID: 2280)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 4996)
Detects GO elliptic curve encryption (YARA)
- explorer.exe (PID: 4944)
Application based on Golang
- explorer.exe (PID: 4944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:02:18 16:20:17+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1347072 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ac04 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Ywikj |
| FileVersion: | 1.0.0.0 |
| InternalName: | Ywikj.exe |
| LegalCopyright: | Copyright © 2010 |
| LegalTrademarks: | - |
| OriginalFileName: | Ywikj.exe |
| ProductName: | Ywikj |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
142
Monitored processes
14
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe" | C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Live installer client executable Exit code: 1 Version: 12.0.1202.0516 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | "C:\Users\admin\AppData\Local\Temp\PVAR17DWAEM9O1GY49J9Y2\Dashboard.exe" | C:\Users\admin\AppData\Local\Temp\PVAR17DWAEM9O1GY49J9Y2\Dashboard.exe | sample.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Live installer client executable Exit code: 0 Version: 12.0.1202.0516 Modules
| |||||||||||||||
| 2800 | C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe | C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe | — | Dashboard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Live installer client executable Exit code: 1 Version: 12.0.1202.0516 Modules
| |||||||||||||||
| 2904 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | Dashboard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runas.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3612 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\Desktop\sample.exe | C:\Windows\System32\runas.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3656 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3952 | "C:\Users\admin\Desktop\sample.exe" | C:\Users\admin\Desktop\sample.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Ywikj Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
5 501
Read events
5 487
Write events
14
Delete events
0
Modification events
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4136) sample.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sample_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
12
Suspicious files
16
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3952 | sample.exe | C:\ProgramData\2D16B833BEAB00A1.dat | — | |
MD5:— | SHA256:— | |||
| 3952 | sample.exe | C:\Users\admin\AppData\Local\Temp\PVAR17DWAEM9O1GY49J9Y2\obedientiary.accdb | — | |
MD5:— | SHA256:— | |||
| 3952 | sample.exe | C:\Users\admin\AppData\Local\Temp\PVAR17DWAEM9O1GY49J9Y2\UXCore.dll | — | |
MD5:— | SHA256:— | |||
| 3952 | sample.exe | C:\ProgramData\691C101E0340AE0E.dat | binary | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
| 3952 | sample.exe | C:\ProgramData\A062DE5ADD6BA545.dat | binary | |
MD5:C52CD961FB8188CE1B3D97815AA02978 | SHA256:FE95CAC7B0F158D55188CE091428A8623DB31C927EDA38DC35411D4CB67EA71E | |||
| 3952 | sample.exe | C:\ProgramData\0F0F37E5009514FF.dat | binary | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
| 3952 | sample.exe | C:\Users\admin\AppData\Local\Temp\PVAR17DWAEM9O1GY49J9Y2\stdvcl40.ja | executable | |
MD5:28C260E1F9CBFA884FBE8F34D6A0D882 | SHA256:8998412837B8B675EC9B0B57270CBF2F0CB06E521E15CE01ED096056973747F6 | |||
| 3952 | sample.exe | C:\ProgramData\3063AC17E8E724EA.dat | binary | |
MD5:46D9FCA6032297F8AEE08D73418312BA | SHA256:865856FA4C33C4AEE52E15FBB370B6611468FE947E76E197F0E50D0AD62CB1B4 | |||
| 3952 | sample.exe | C:\ProgramData\81DBFB798429CD5E.dat | binary | |
MD5:0FF3BCDD0BE077B9EB8194B5C09F453C | SHA256:225D669E47EB14D8C969799C92AAEF27B66CD984872EA09284E48DB46521E651 | |||
| 3952 | sample.exe | C:\ProgramData\B233FF46DB65EF7D.dat | binary | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
48
DNS requests
32
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5004 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5004 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5992 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5892 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5892 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
1176 | svchost.exe | 20.190.160.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
download2287.mediafire.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2192 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (nestlecompany .world) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (generalmills .pro) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (mercharena .biz) |
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (stormlegue .com) |
3952 | sample.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (stormlegue .com in TLS SNI) |
3952 | sample.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (stormlegue .com in TLS SNI) |
3952 | sample.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (stormlegue .com in TLS SNI) |
3952 | sample.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (stormlegue .com in TLS SNI) |