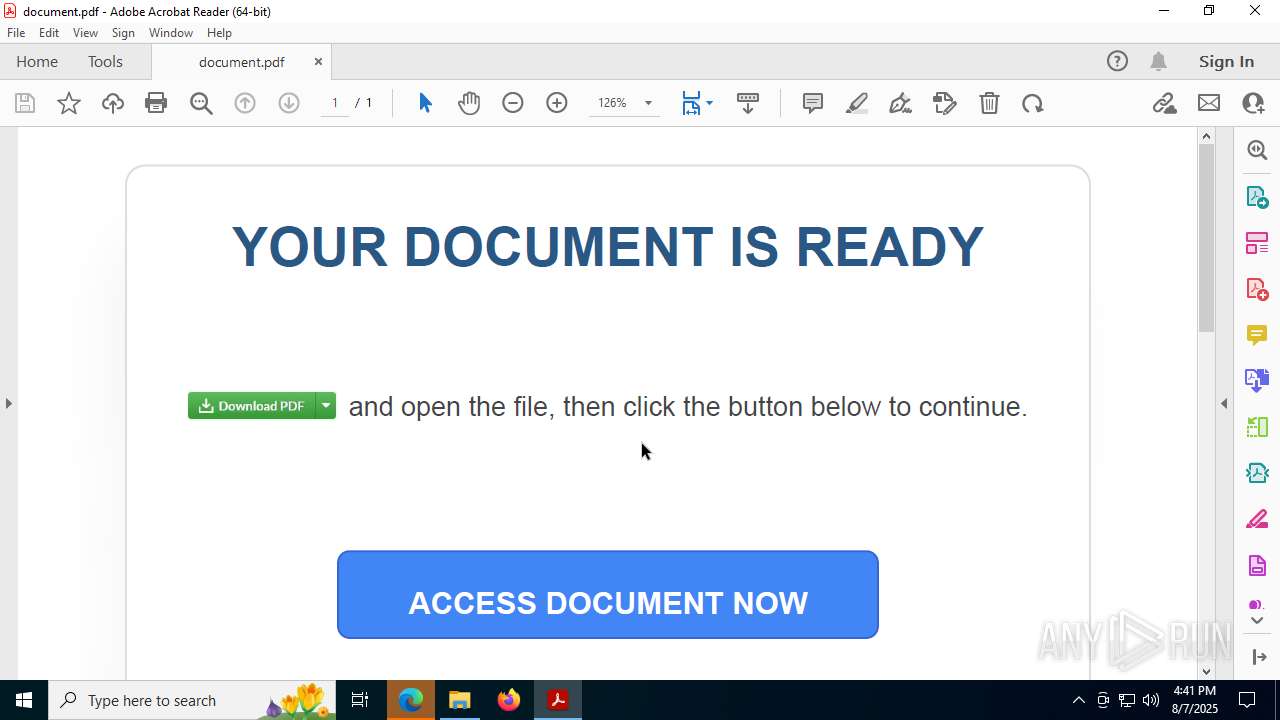
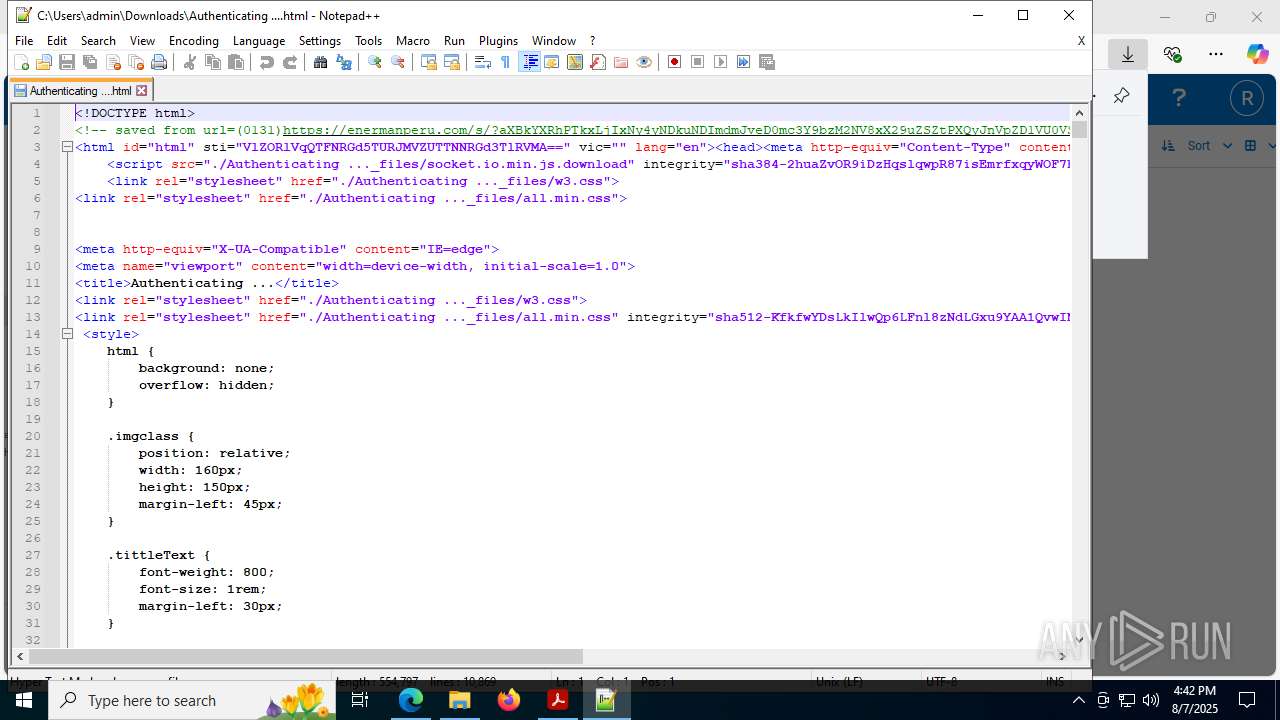
| URL: | https://url6450.formswift.com/ls/click?upn=u001.T8-2FTfWgYcIO3dd7tP2R-2BFFIm9UiyQ-2Fcyk-2B-2BX5-2Bn4Qbdhag7OSpFSpvBpW1Qv2kQ9q7XRw9KccM6hi2xymffjpxaQjd9Gul5Qa5uDBDhanuvOHGH94KLgmGHqEjuh6ywD2OUbMJ8X5tO3yPgHc7oClKVh84DAk13nNz6HeMu6OzmjCPmewbN-2BKA3uCMyv16wGy7bg-2F-2BB4FmSDhklftZpOSUjjozGRLoKttfZFyI7Yoik-3DTE7k_Zq48bdq-2F02-2BJJaHBYmqo8kT-2F-2Ff0-2Bqb5-2FELZhFVlEiIPfu8MyPOZ3BPF95514soGWxmkirF65-2B5QVxnR7AN2-2BZ669dEFEJ2Wo7FtIOmp6X8BzybEx7V0za-2FomRjoom4-2F-2FZjRENbzl-2BgyscevW6w2bYZRxxTNolNI0kOBxvloz9zT0-2Ft-2B8pIHrUd4GqswUj56WNwU7BZBAck6jBuaFplXXUA-3D-3D |
| Full analysis: | https://app.any.run/tasks/04ef3c74-8ea1-4179-99c9-6105fcbb80b2 |
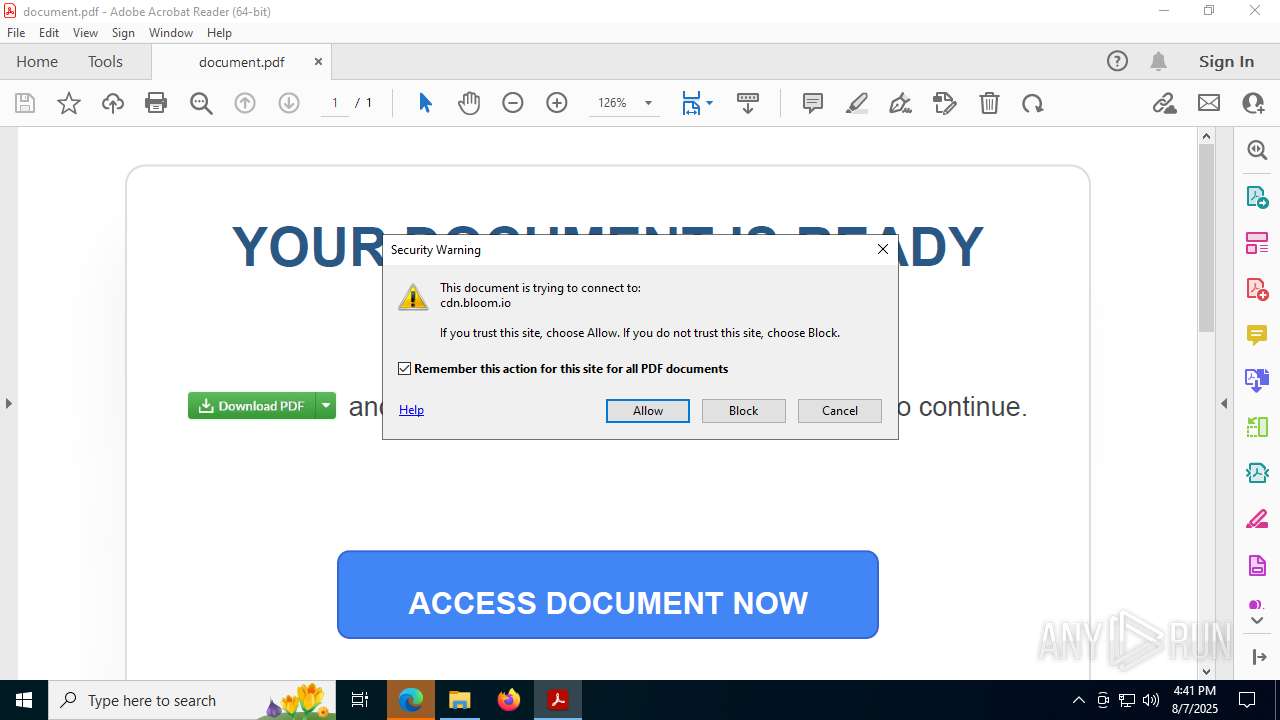
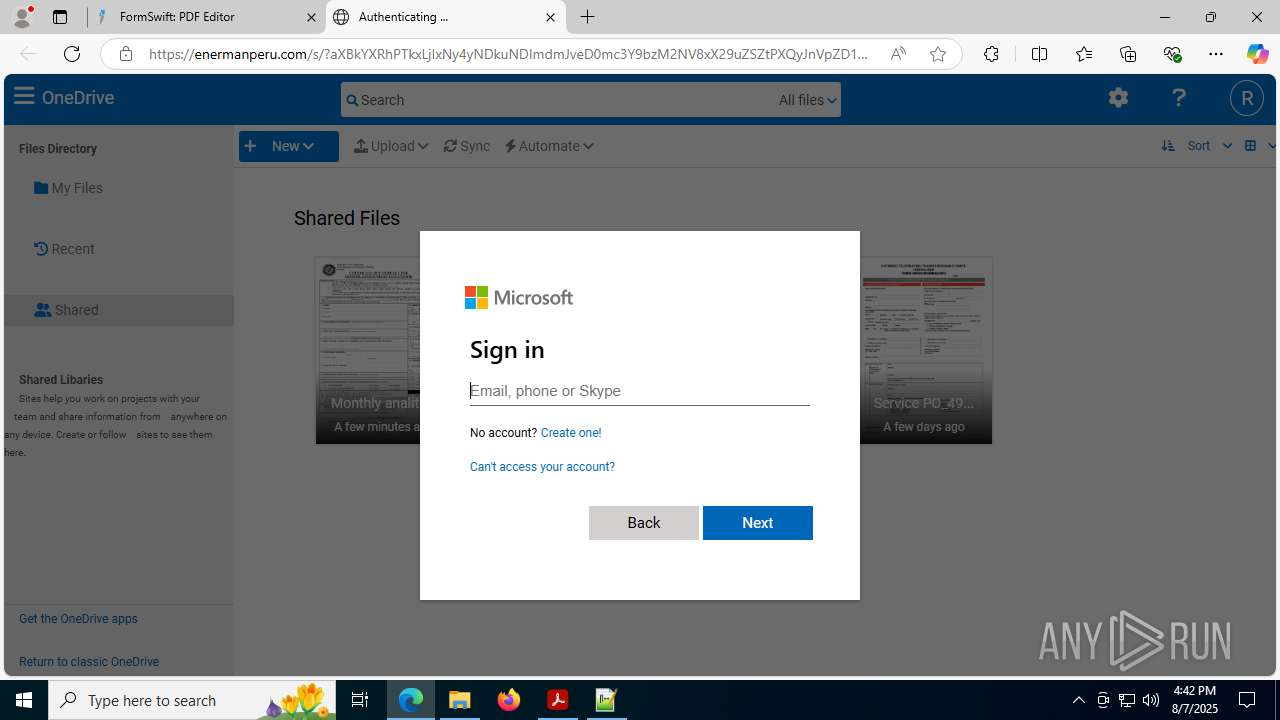
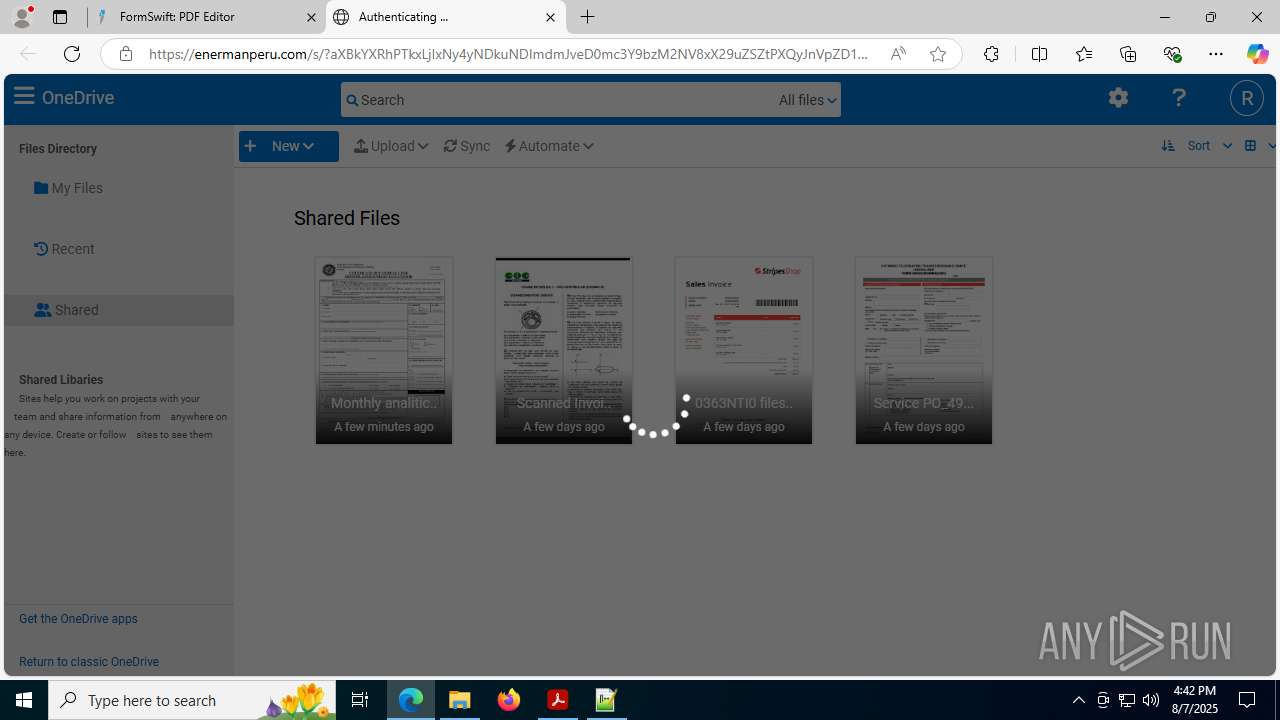
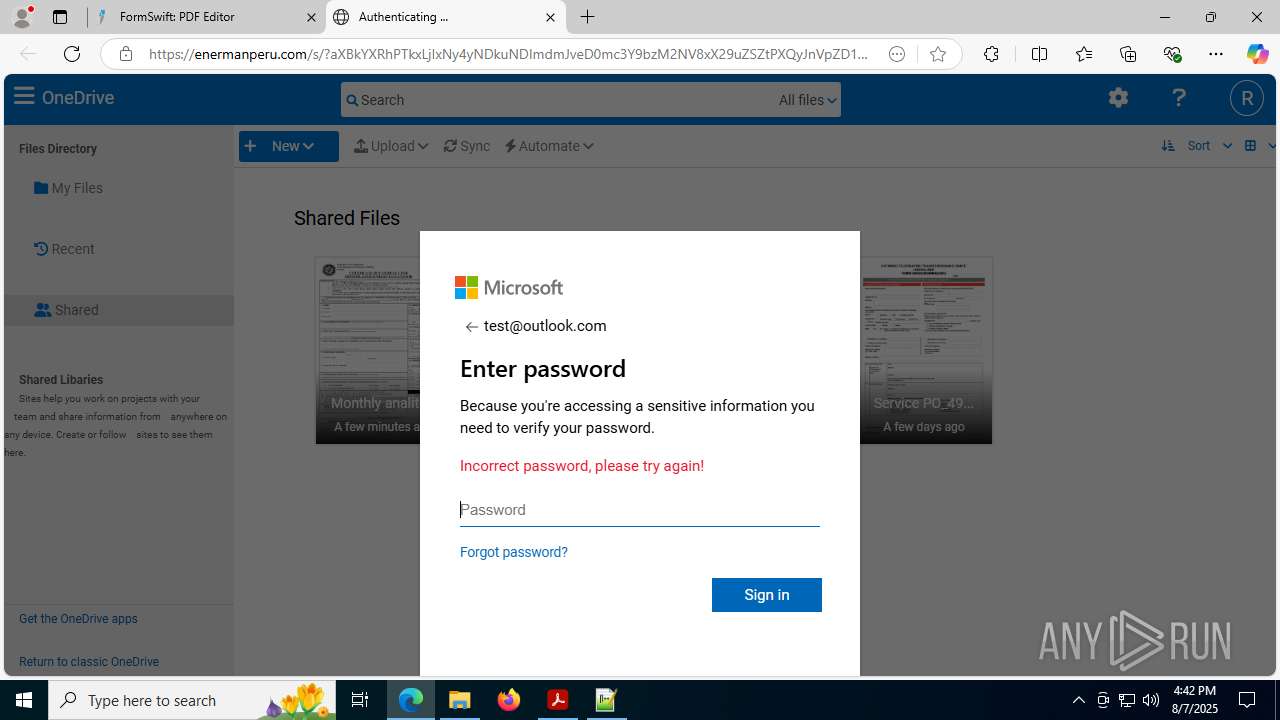
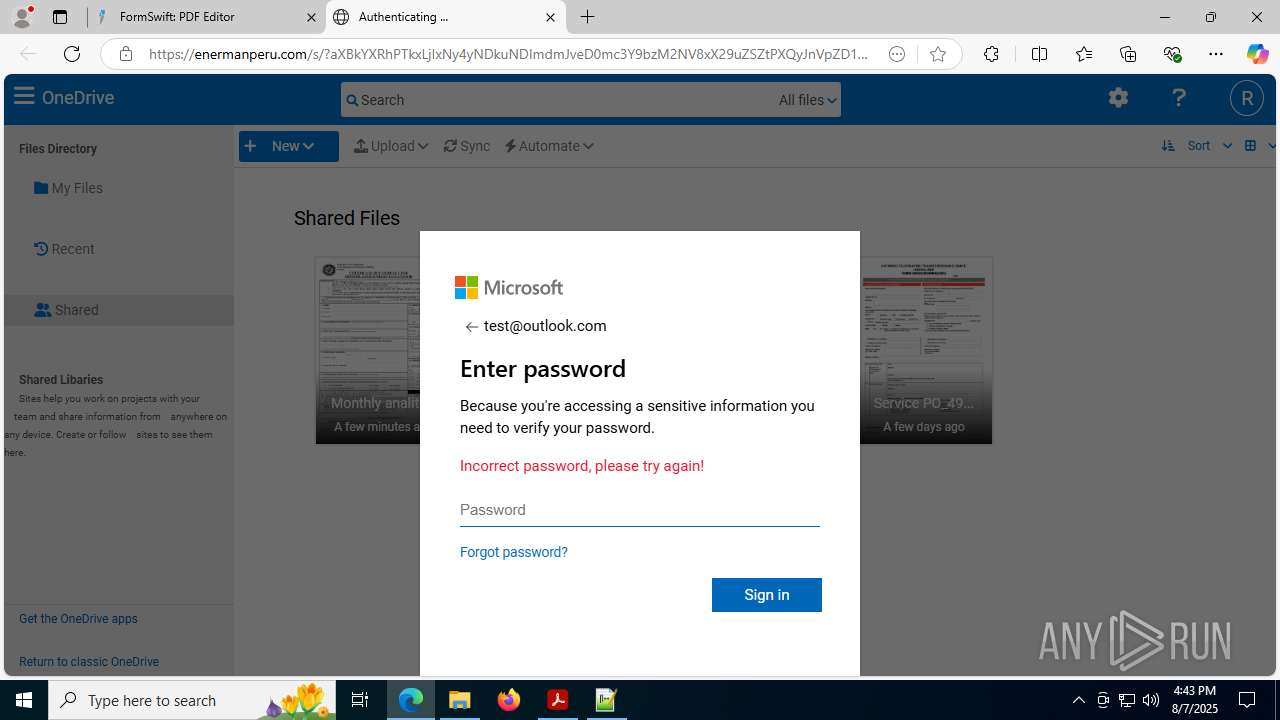
| Verdict: | Malicious activity |
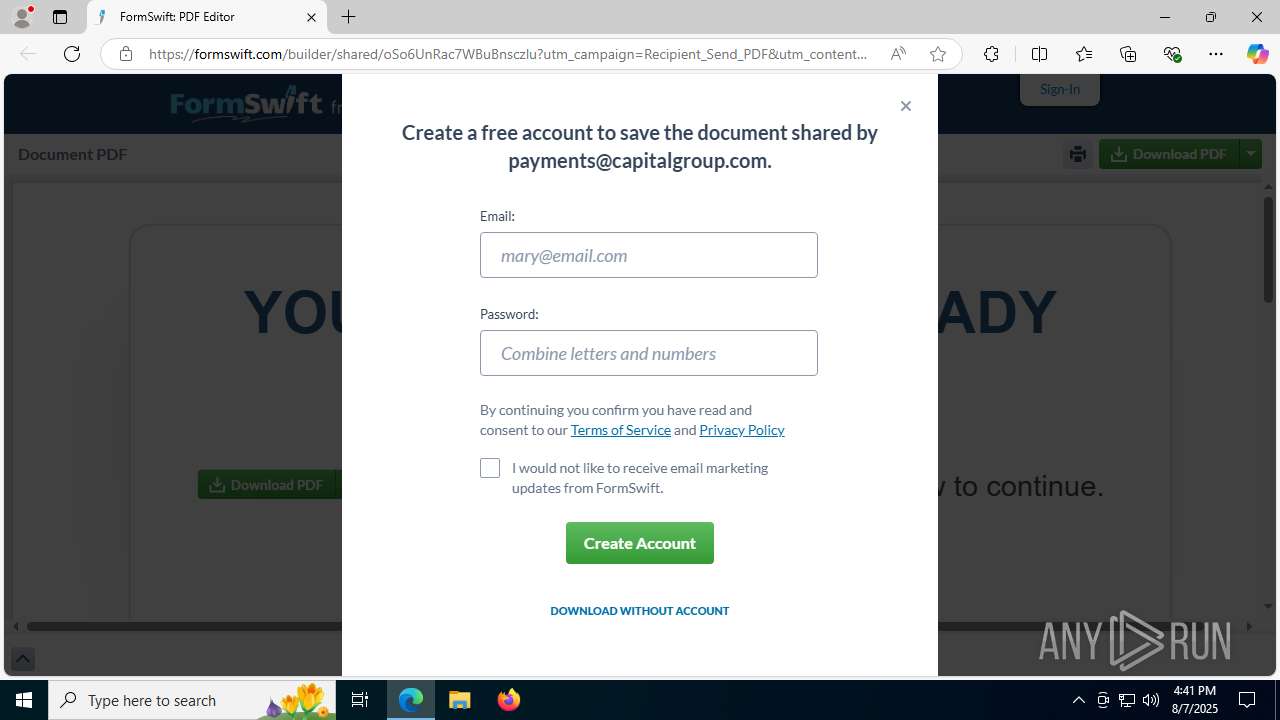
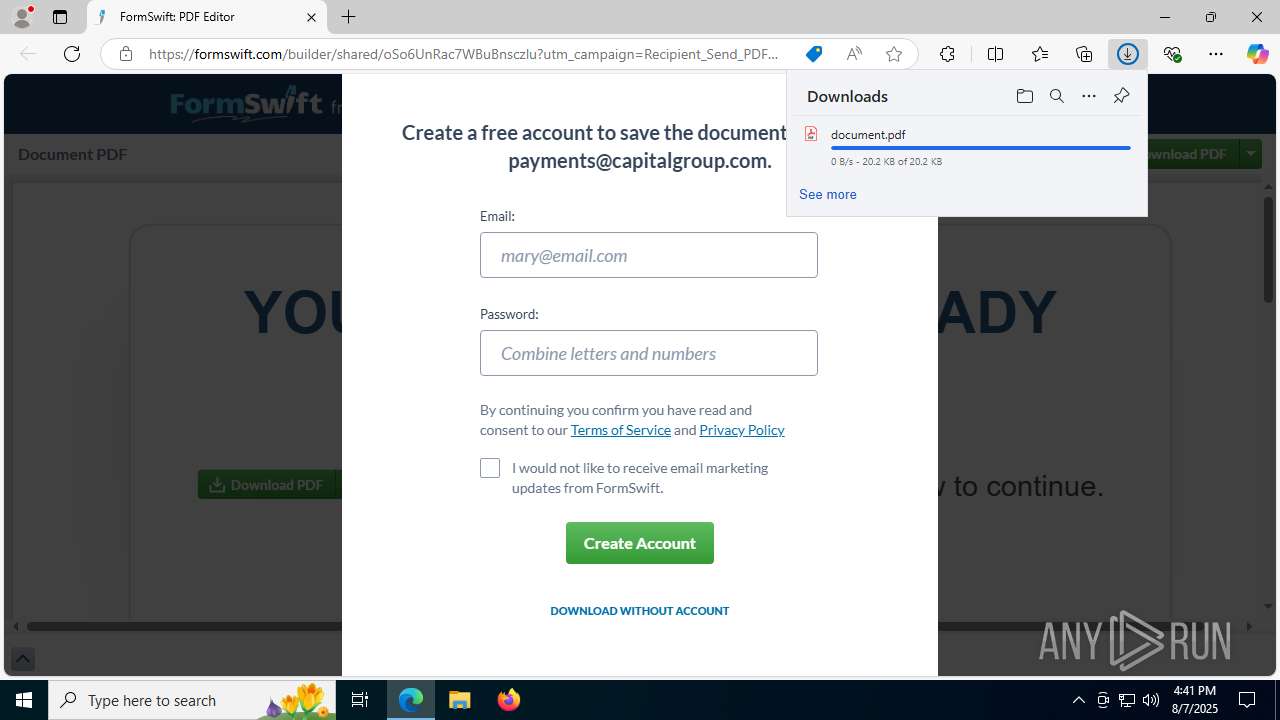
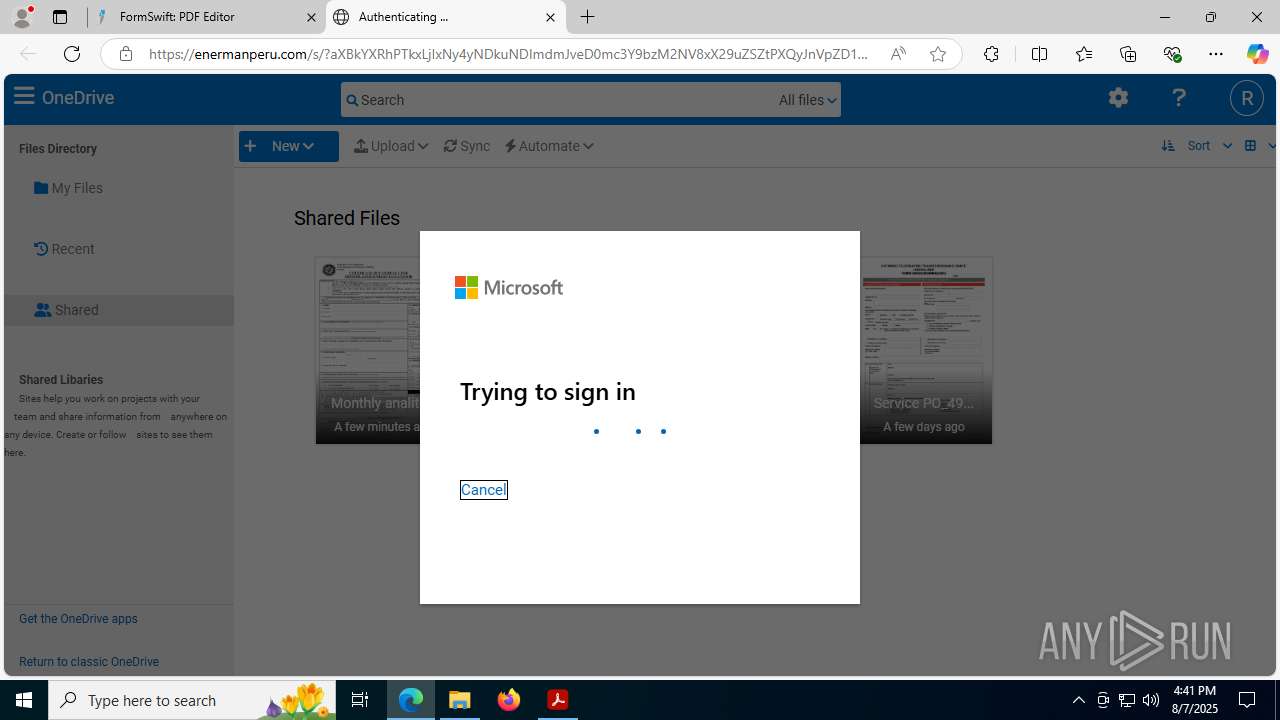
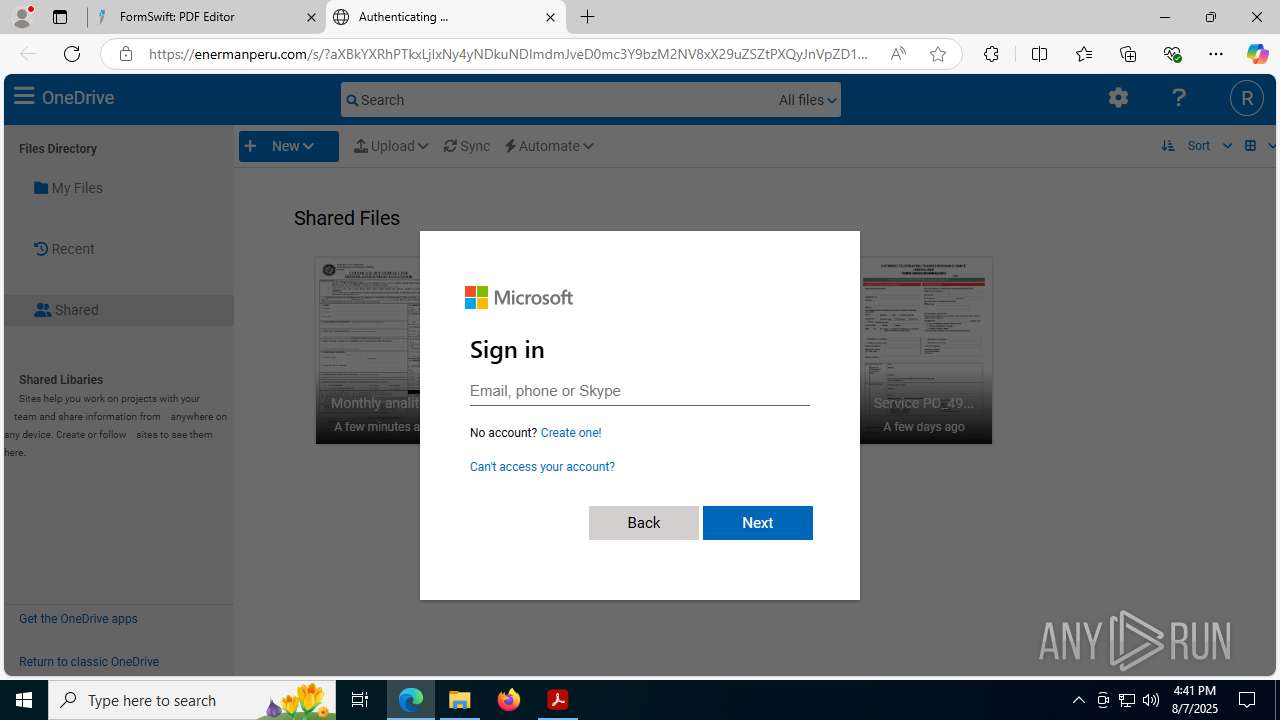
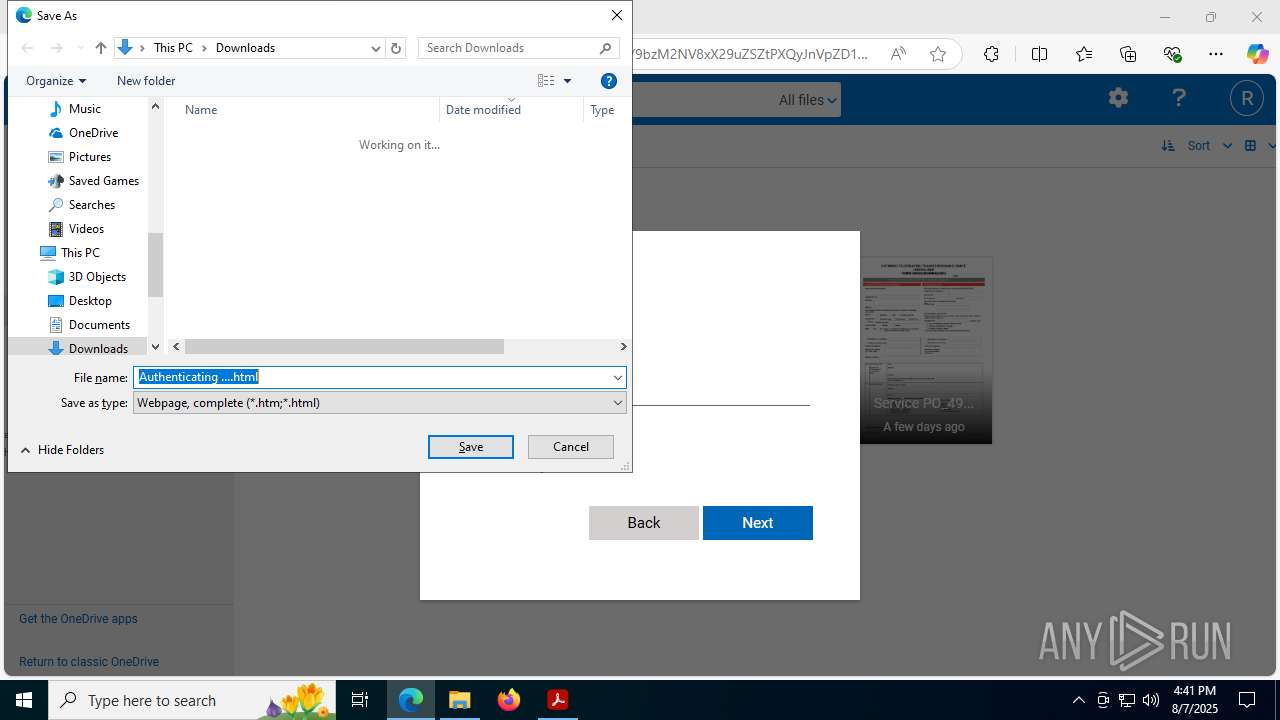
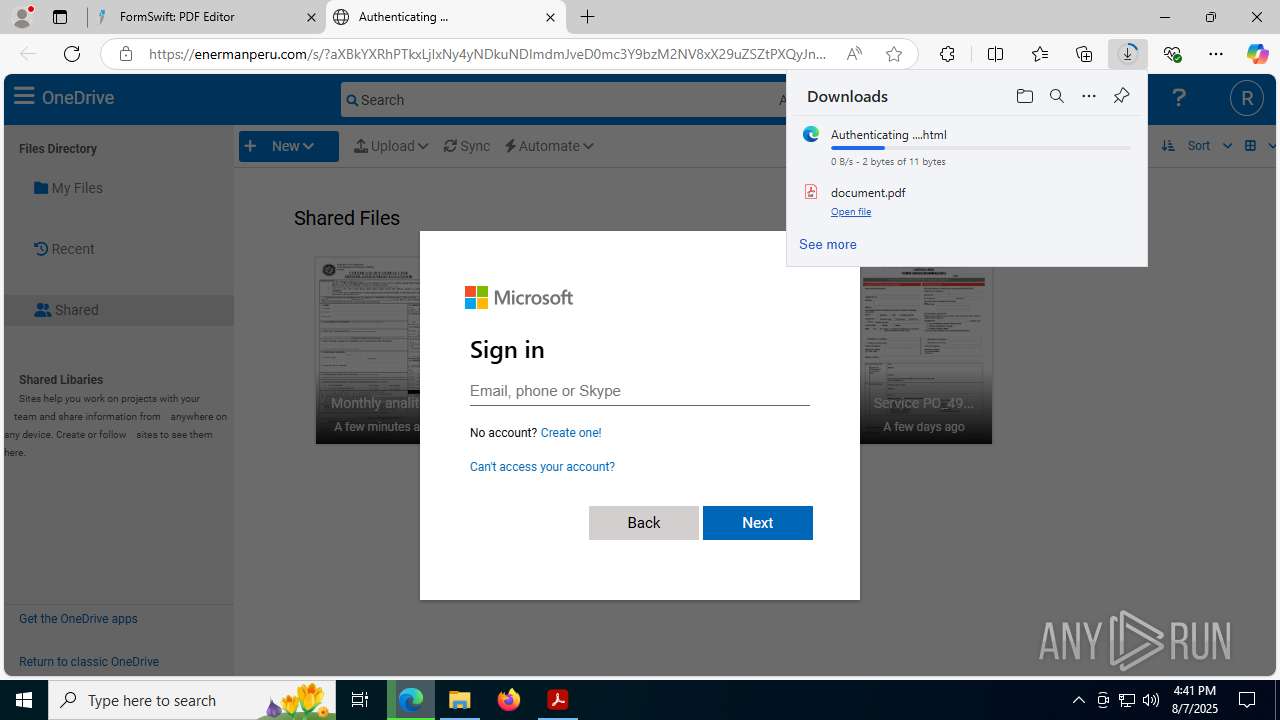
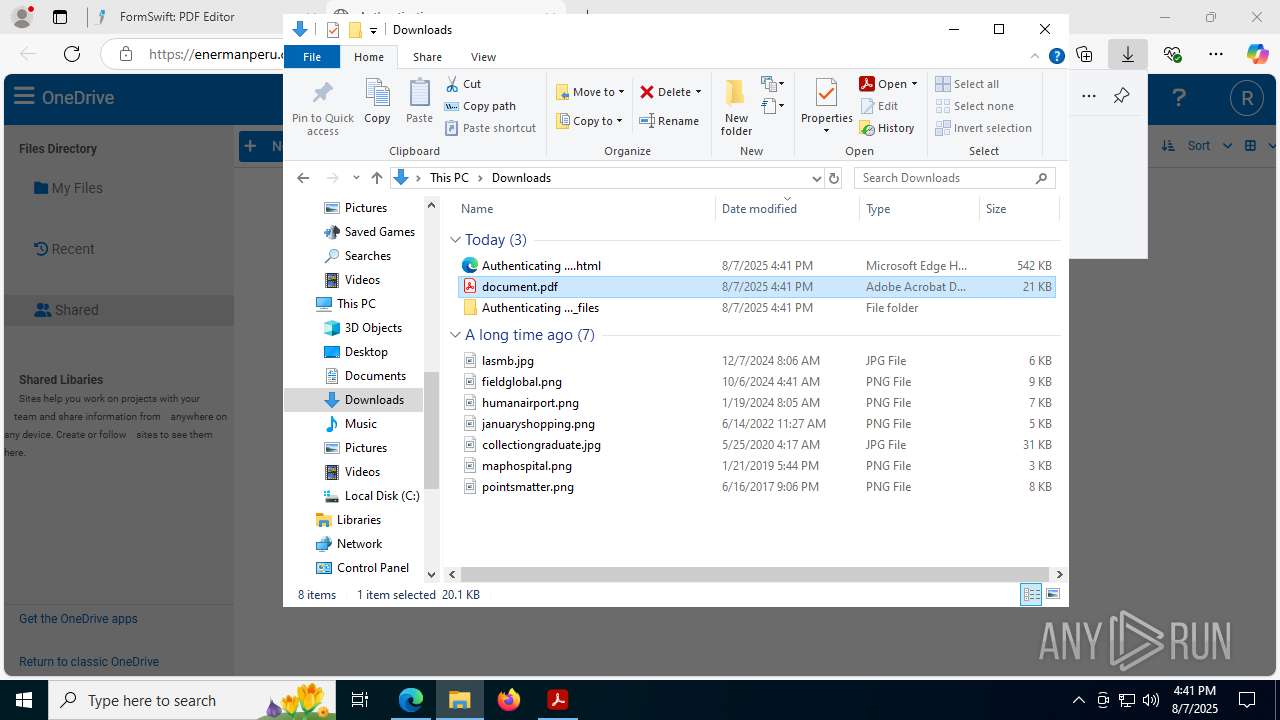
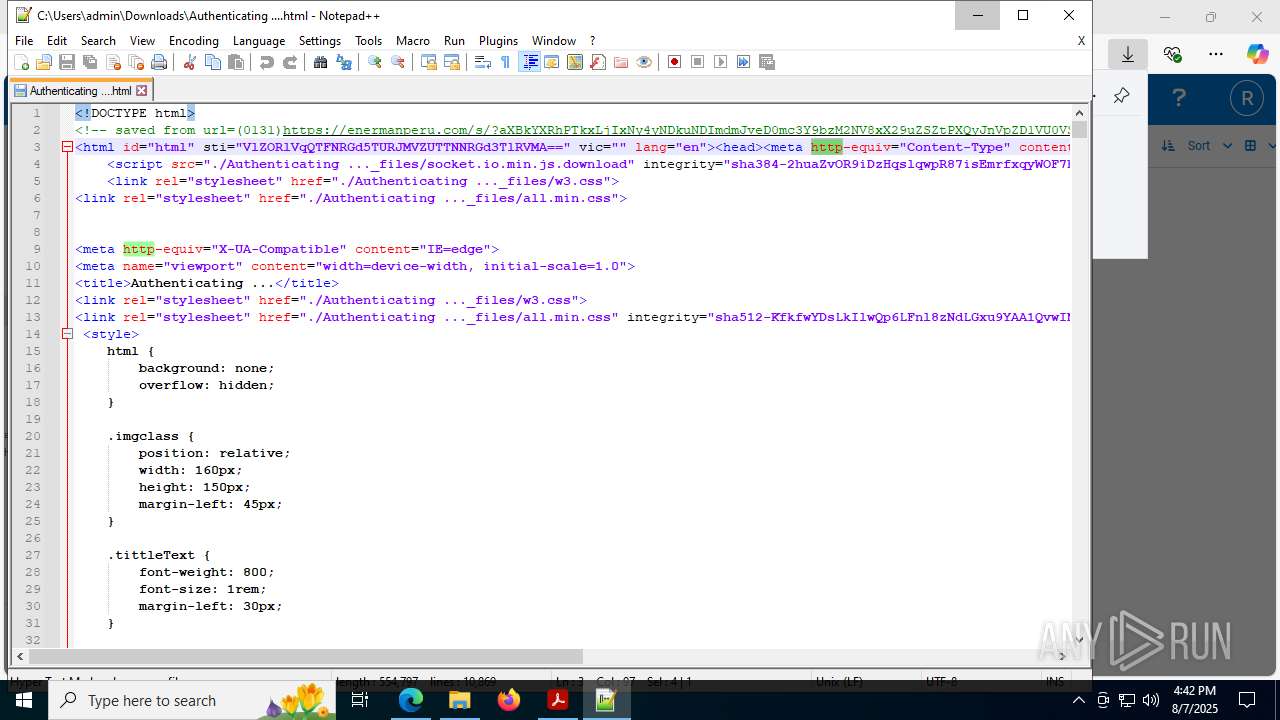
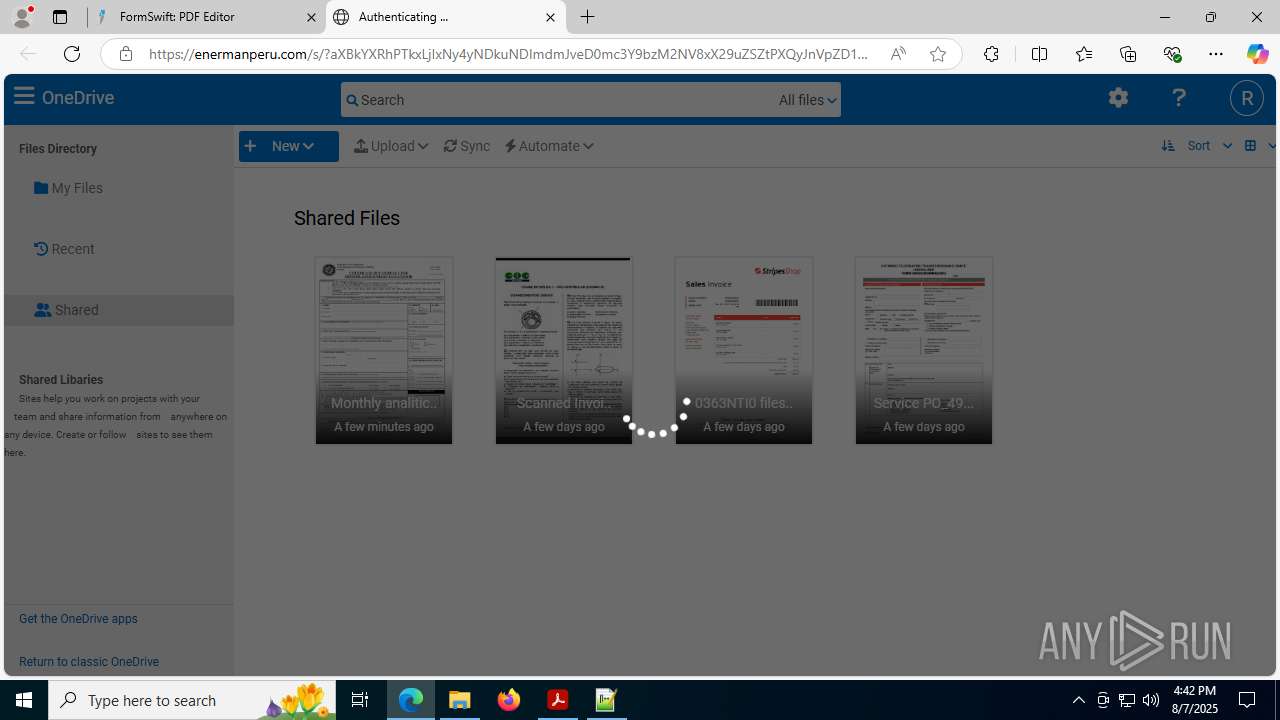
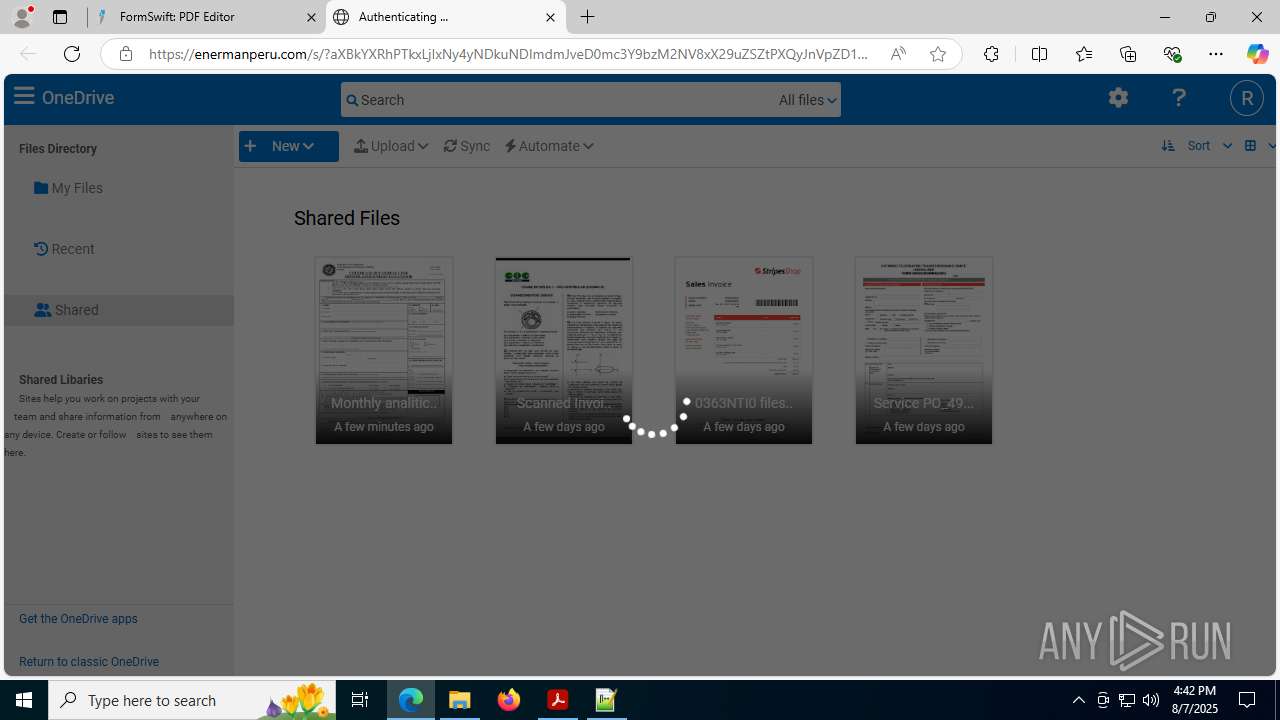
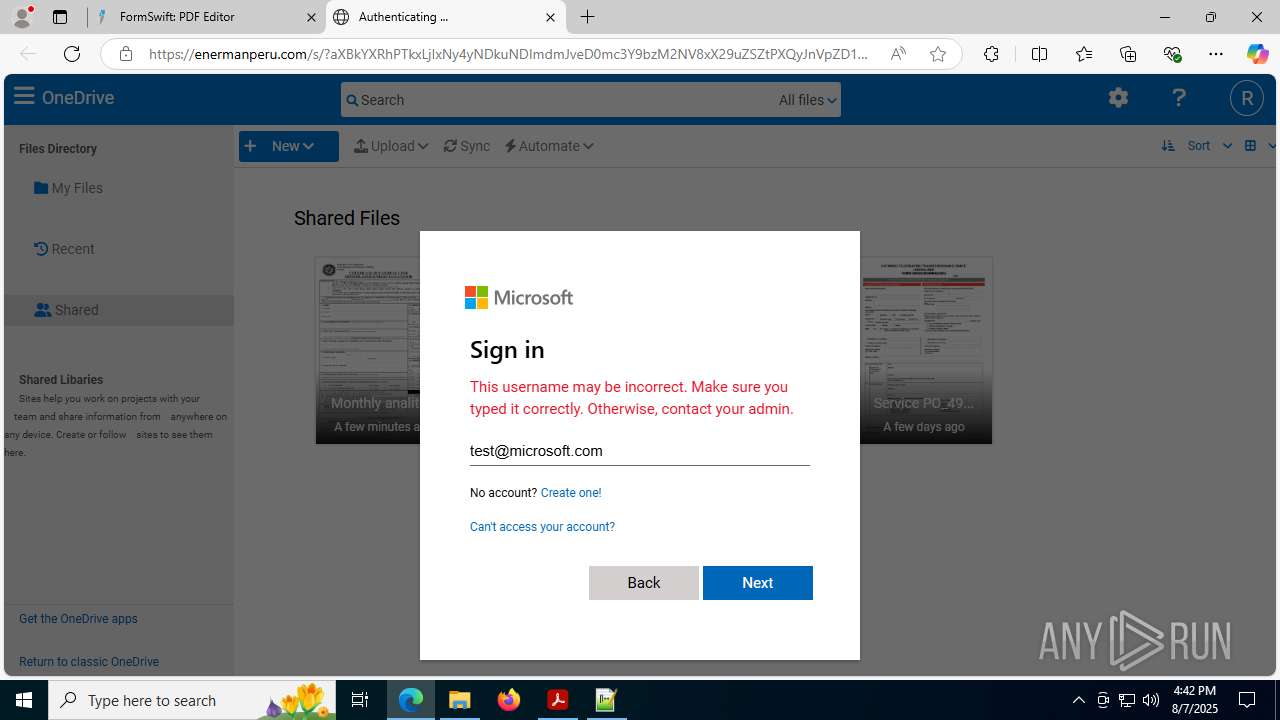
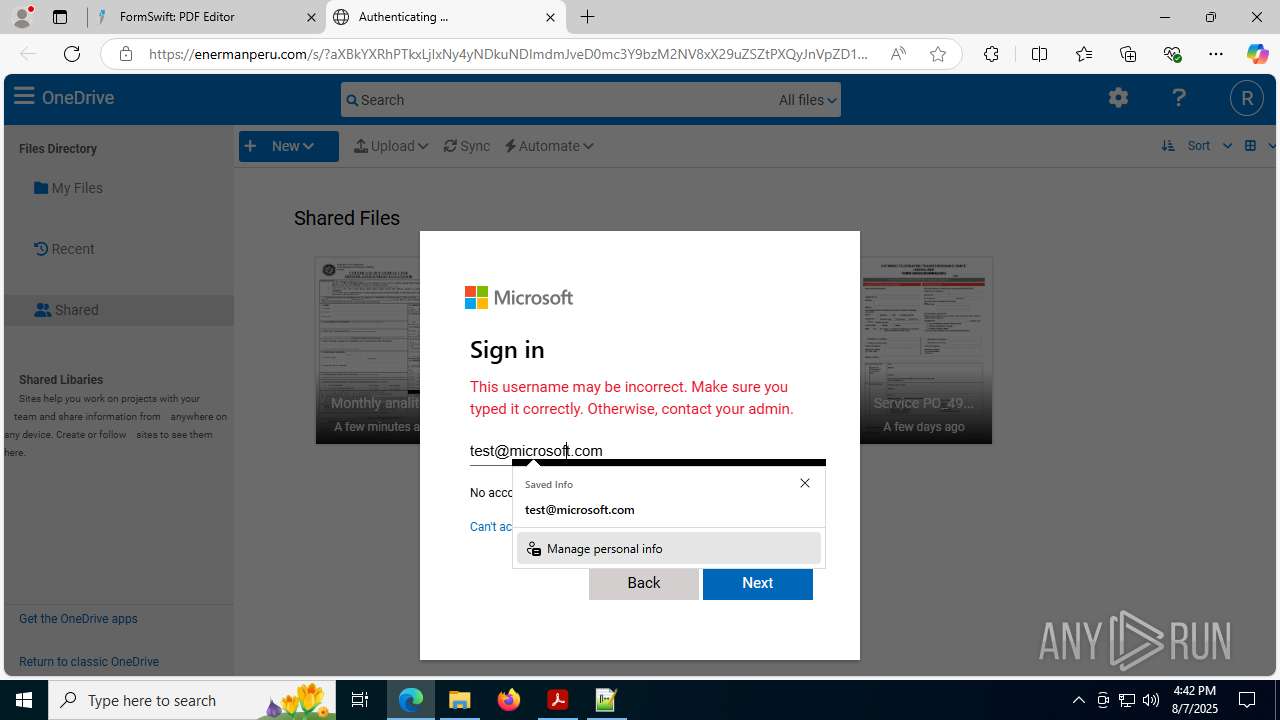
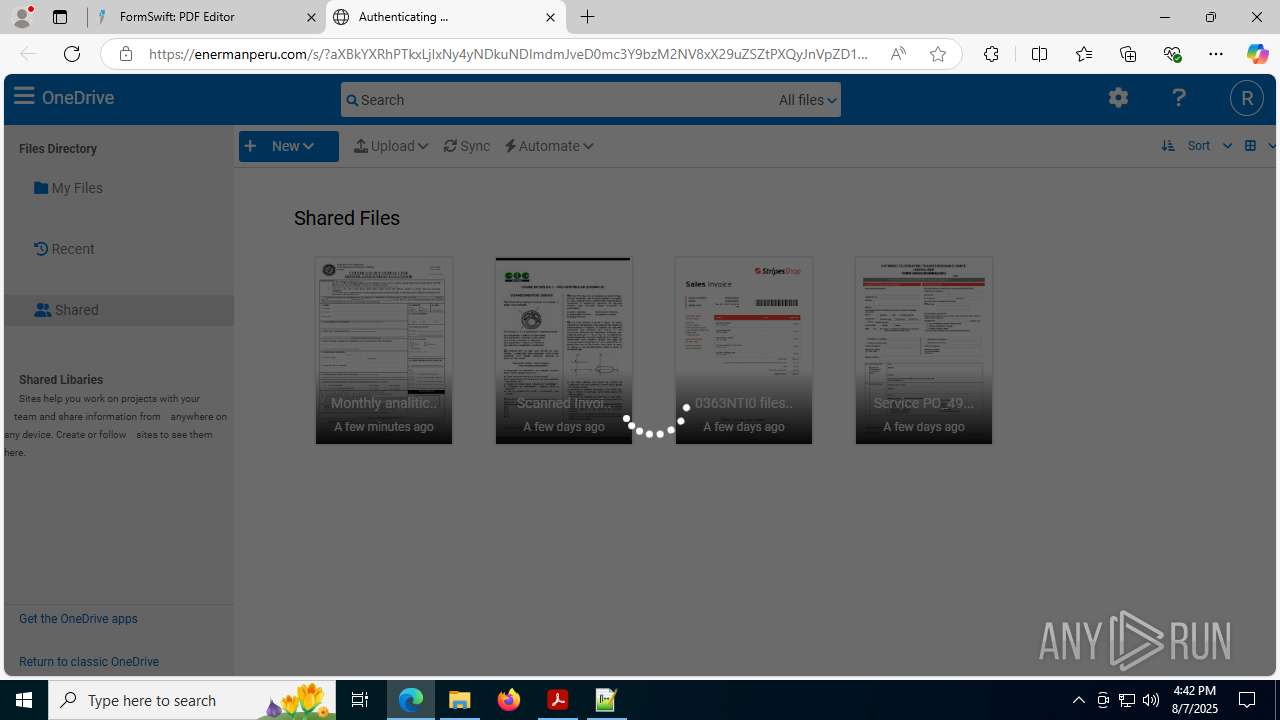
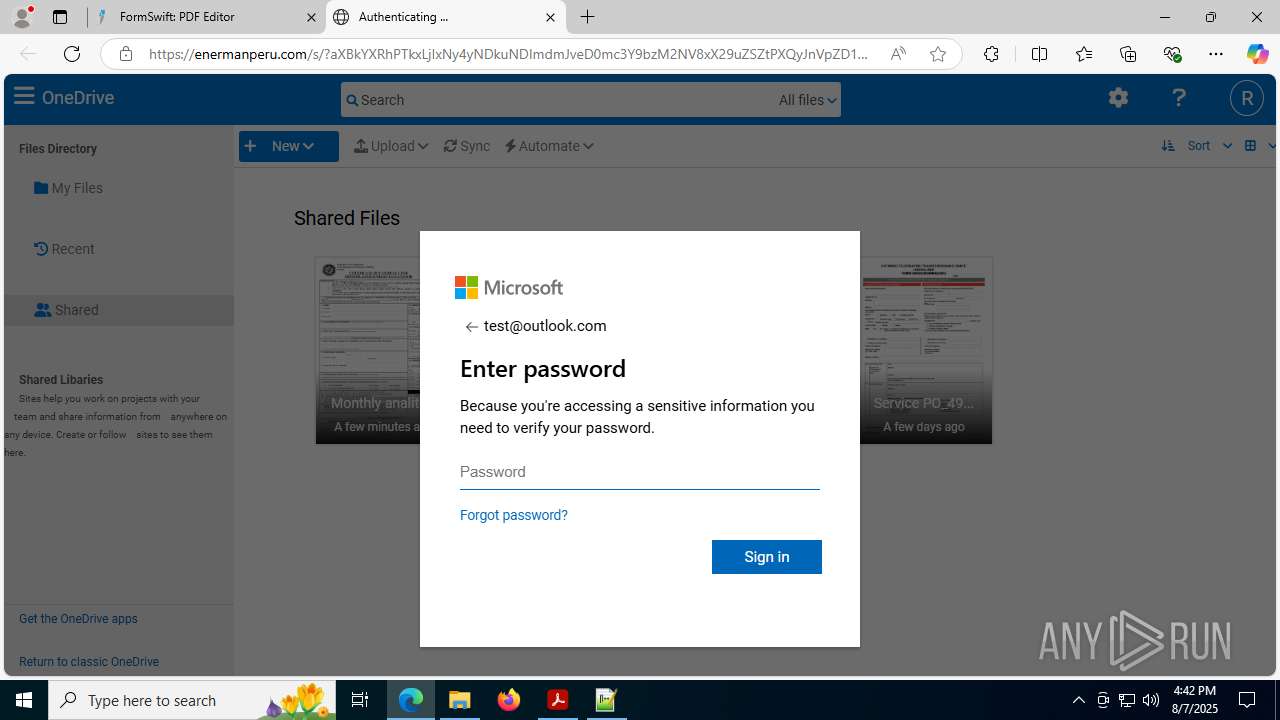
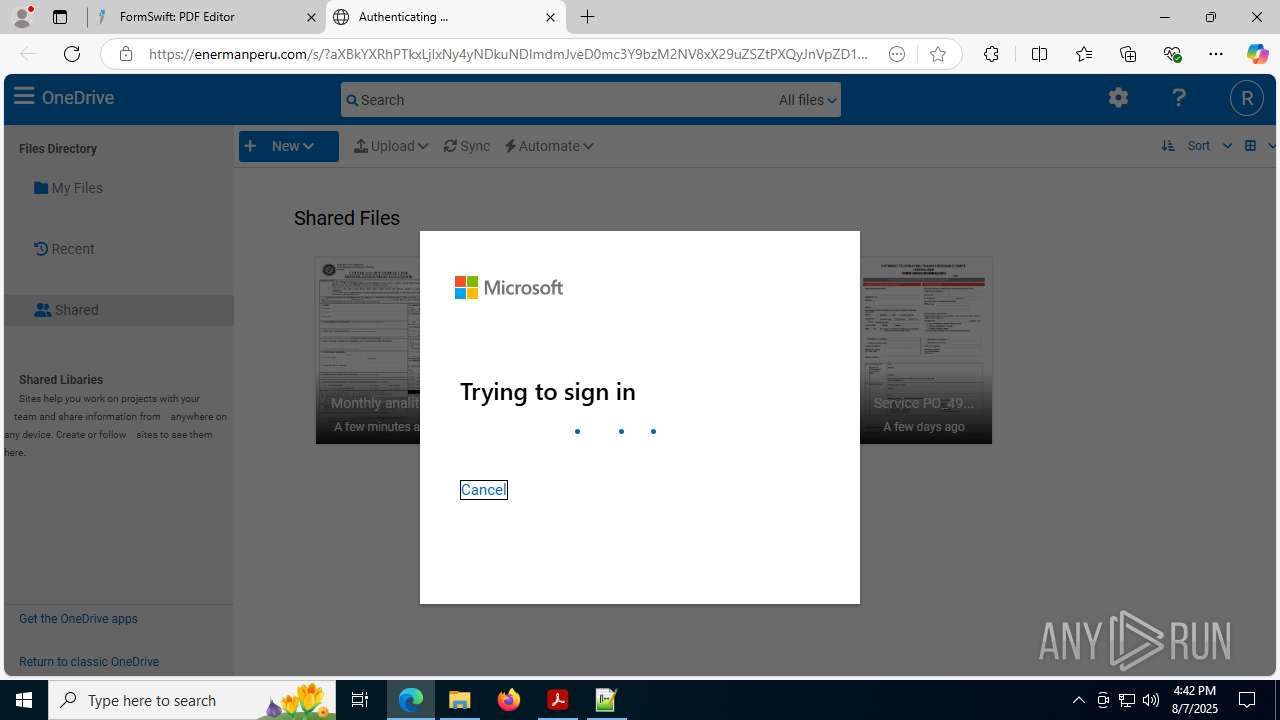
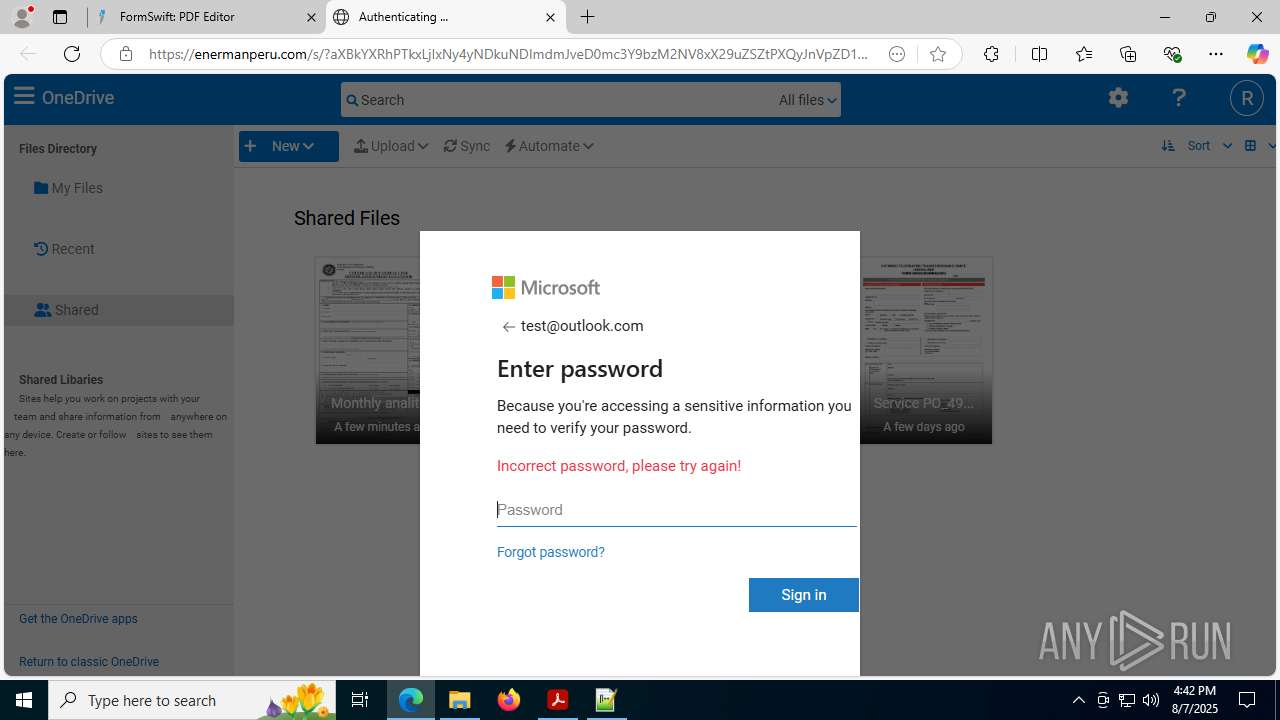
| Threats: | Mamba 2FA is an advanced phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) and target Microsoft 365 accounts. It focuses on intercepting authentication flows in real-time and enables threat actors to hijack user sessions and access sensitive systems even when additional security measures are in place. |
| Analysis date: | August 07, 2025, 16:41:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 99271C9D5251BDB885DC83251C3449E4 |
| SHA1: | 6AECD55DBB23C441E075724C4703976DE3A9E1CE |
| SHA256: | 9565299A184147700B76461C25670CB1059F74DD7F905DA4480AF89F67F4E64E |
| SSDEEP: | 12:2UdHYSxWIdXzTv+ZDx74dLDgus6IptAEsku5scNsPpgczh+gaCmIw0AkeP:2KMIF/+Zd74lguyD7VuCVpgeZmrk2 |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 2228)
SUSPICIOUS
No suspicious indicators.INFO
Reads the computer name
- identity_helper.exe (PID: 8148)
Checks supported languages
- identity_helper.exe (PID: 8148)
Application launched itself
- msedge.exe (PID: 2280)
- Acrobat.exe (PID: 1964)
- AcroCEF.exe (PID: 7000)
Reads Environment values
- identity_helper.exe (PID: 8148)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4788)
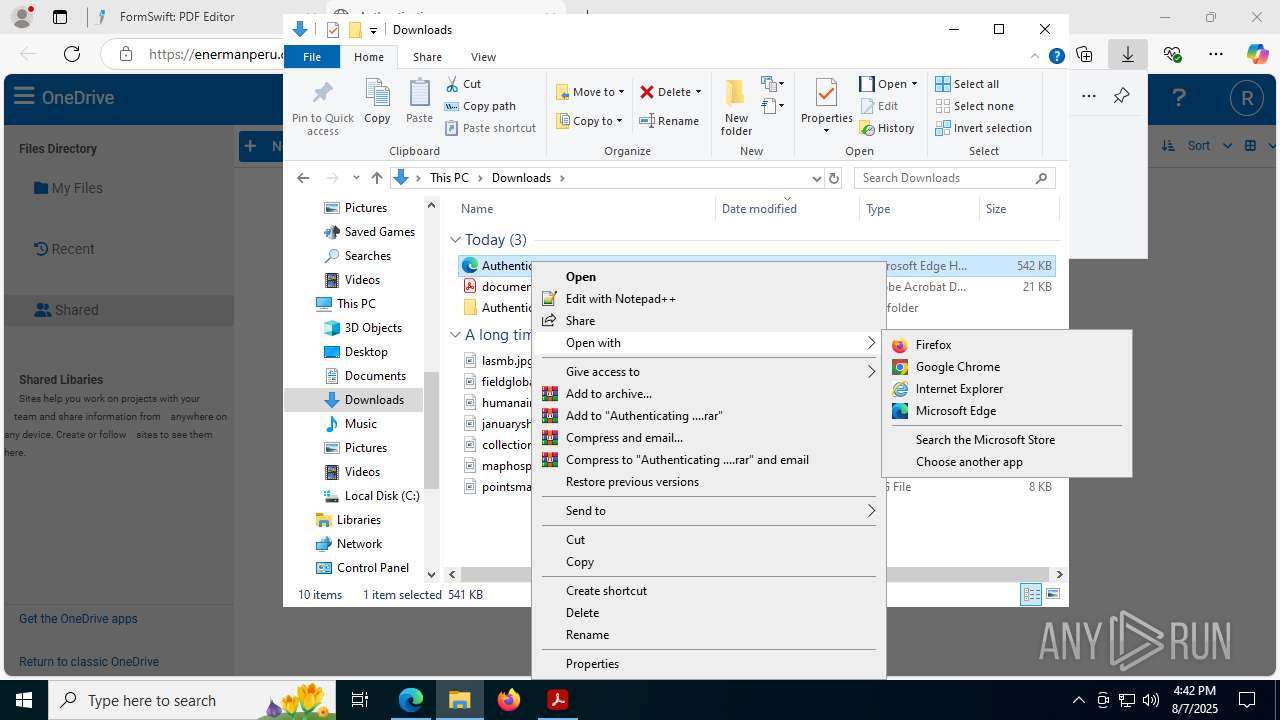
Manual execution by a user
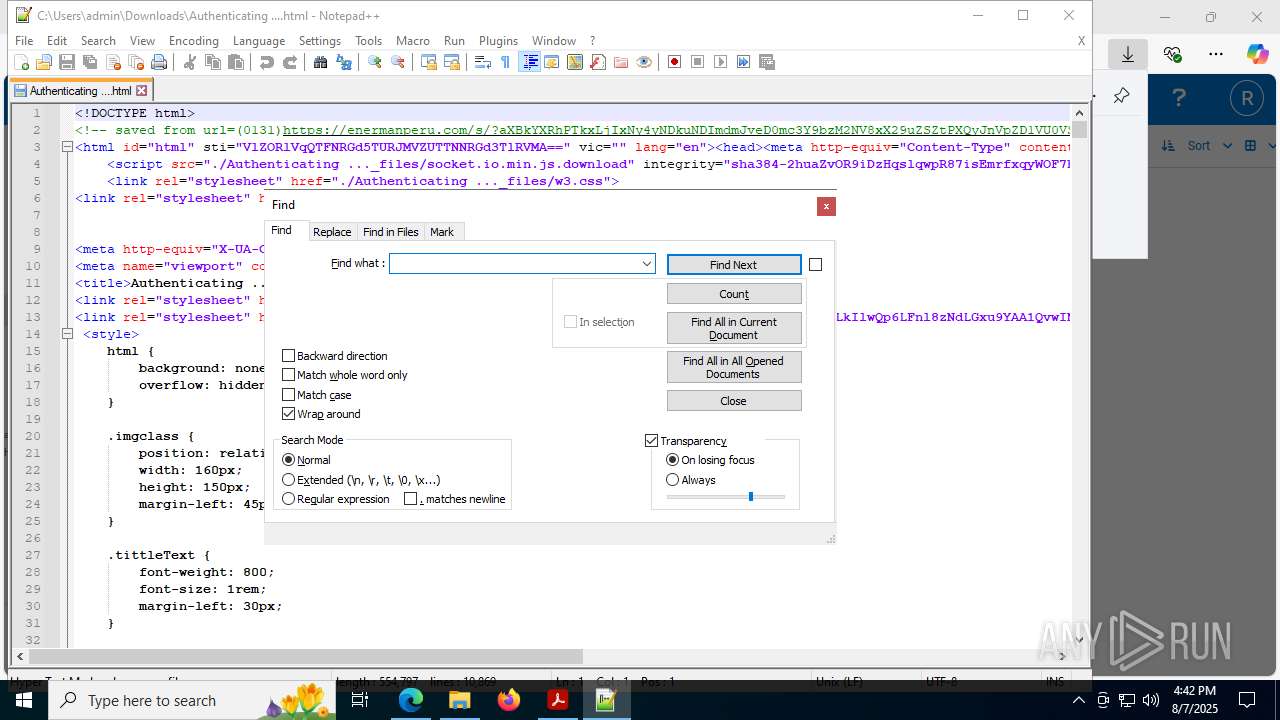
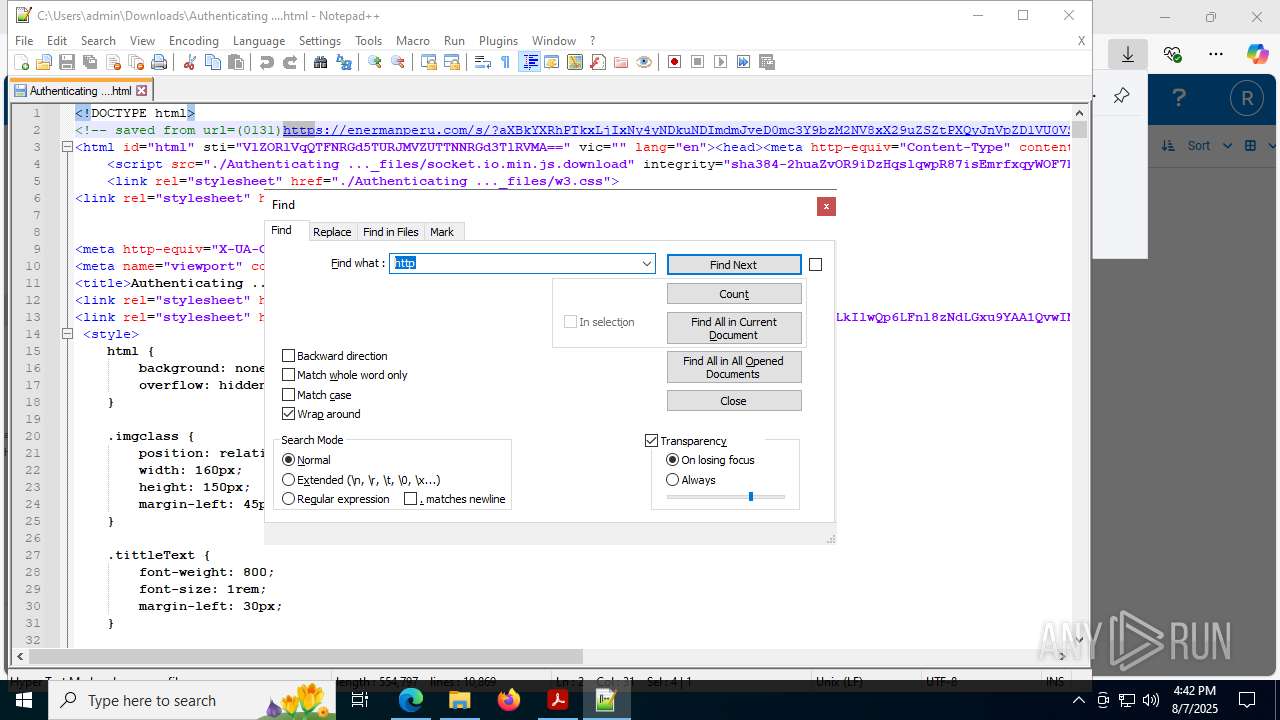
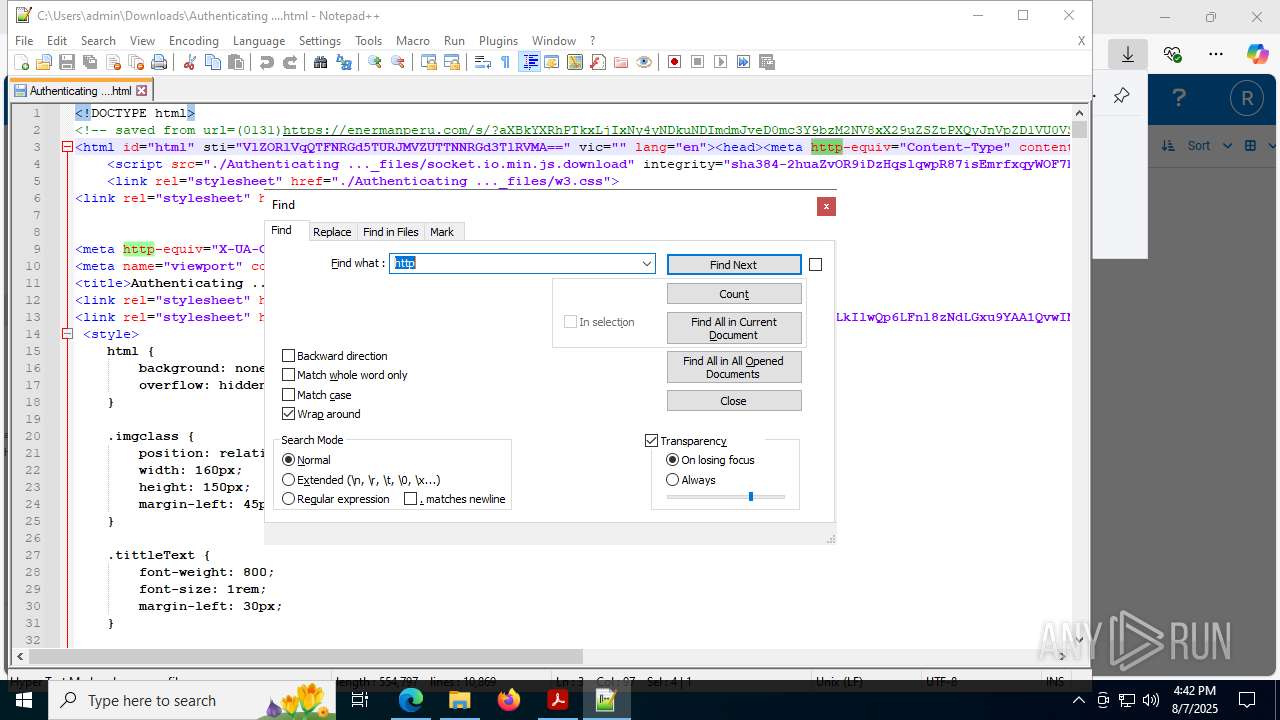
- notepad++.exe (PID: 9168)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 4788)
Reads the software policy settings
- slui.exe (PID: 7992)
Checks proxy server information
- slui.exe (PID: 7992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
204
Monitored processes
65
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
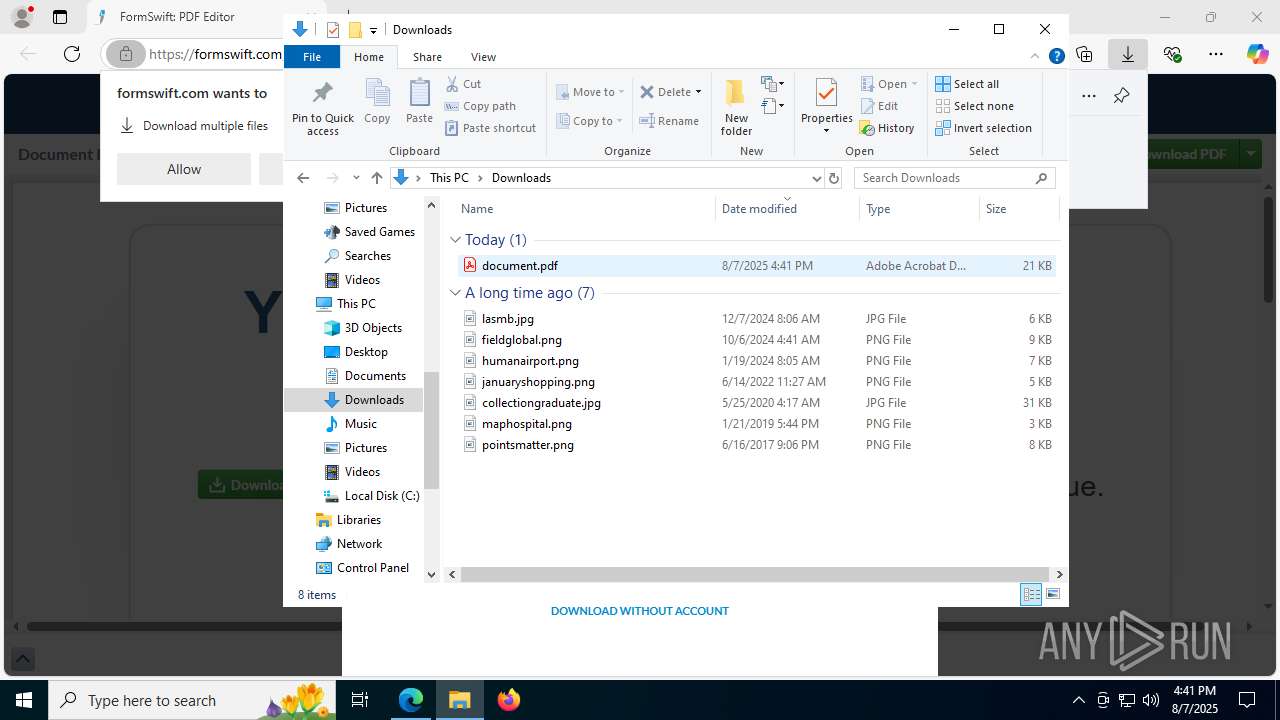
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1068 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1528 --field-trial-handle=1404,i,17312243586578728613,6629362367877422091,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --always-read-main-dll --field-trial-handle=7028,i,5573392083505399,8419710955573819921,262144 --variations-seed-version --mojo-platform-channel-handle=6964 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3616,i,5573392083505399,8419710955573819921,262144 --variations-seed-version --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7864,i,5573392083505399,8419710955573819921,262144 --variations-seed-version --mojo-platform-channel-handle=7652 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
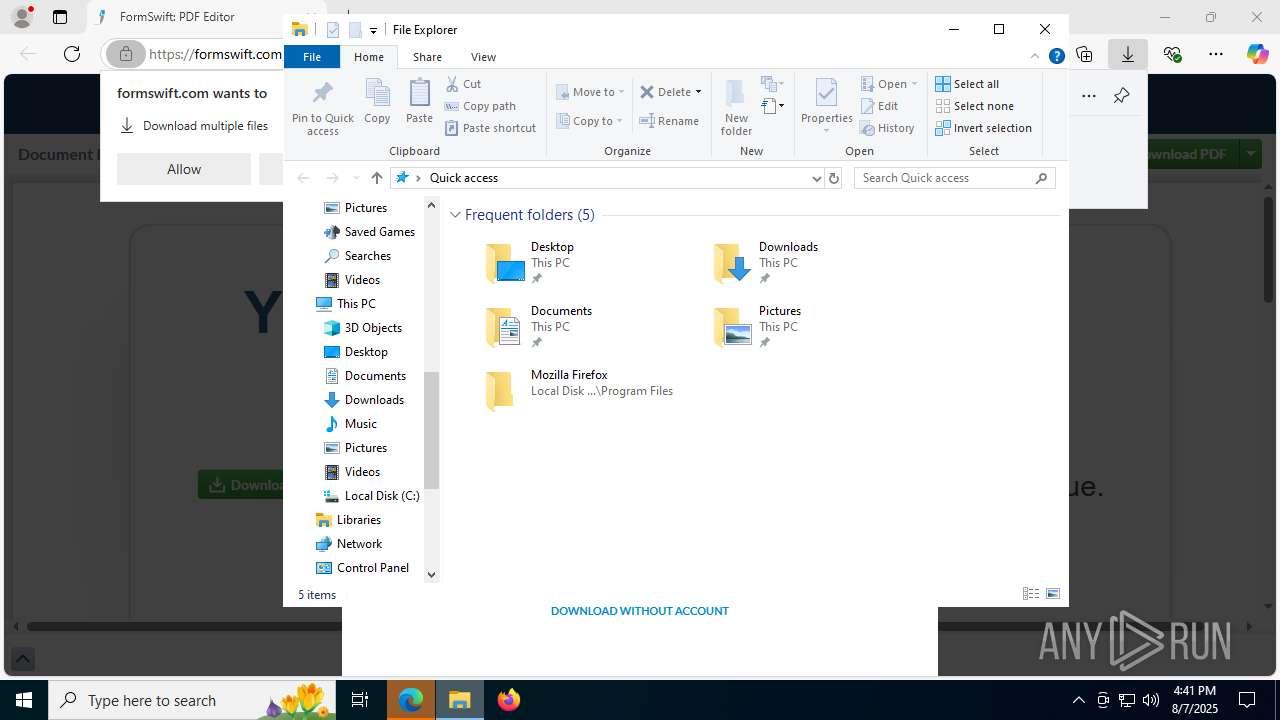
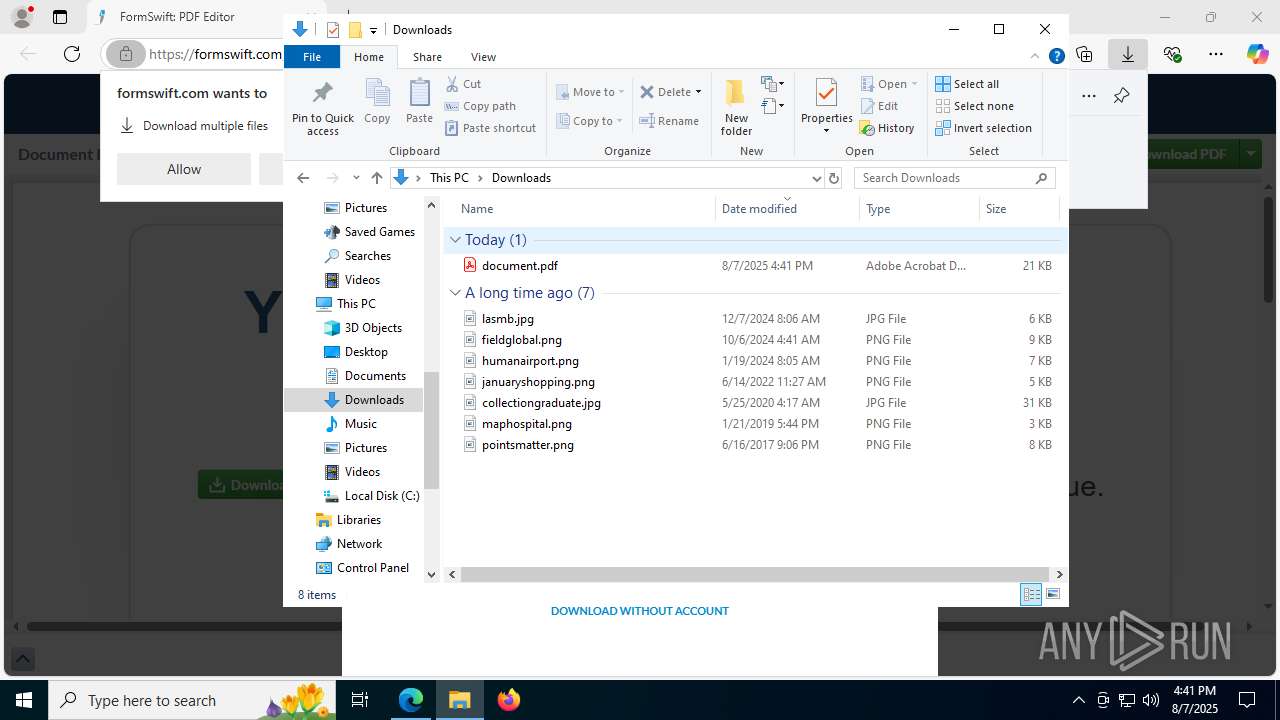
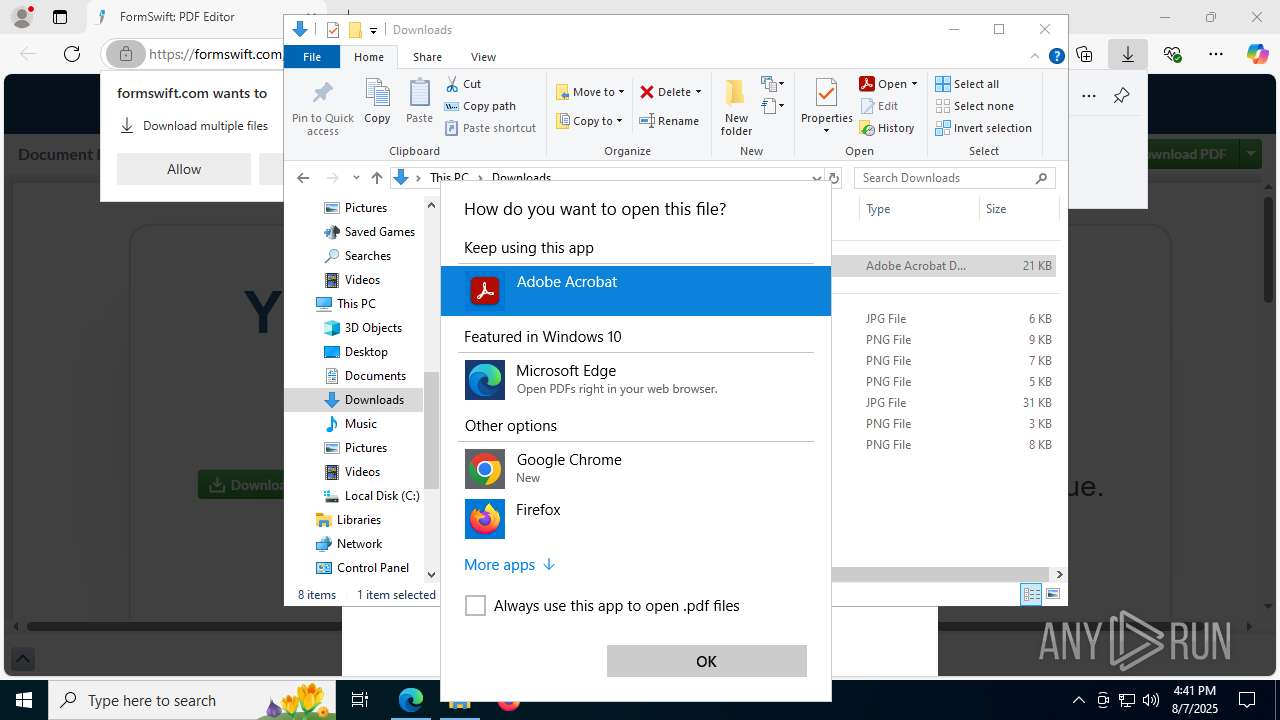
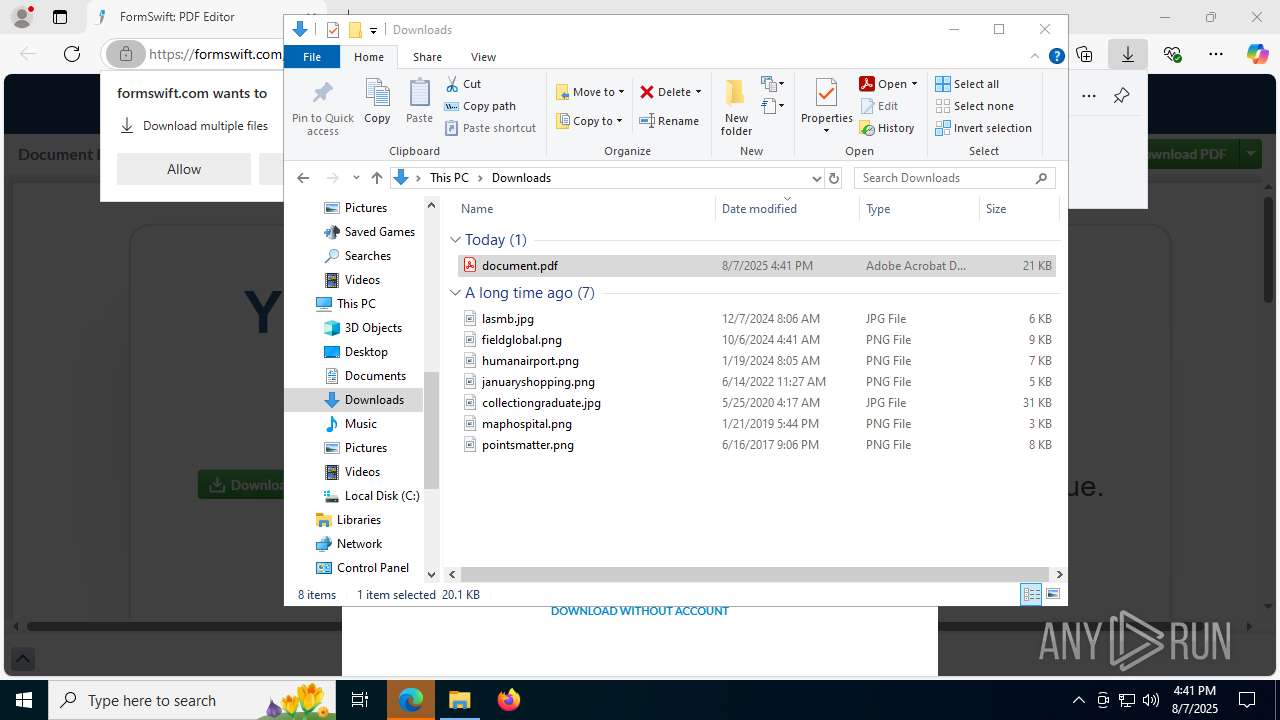
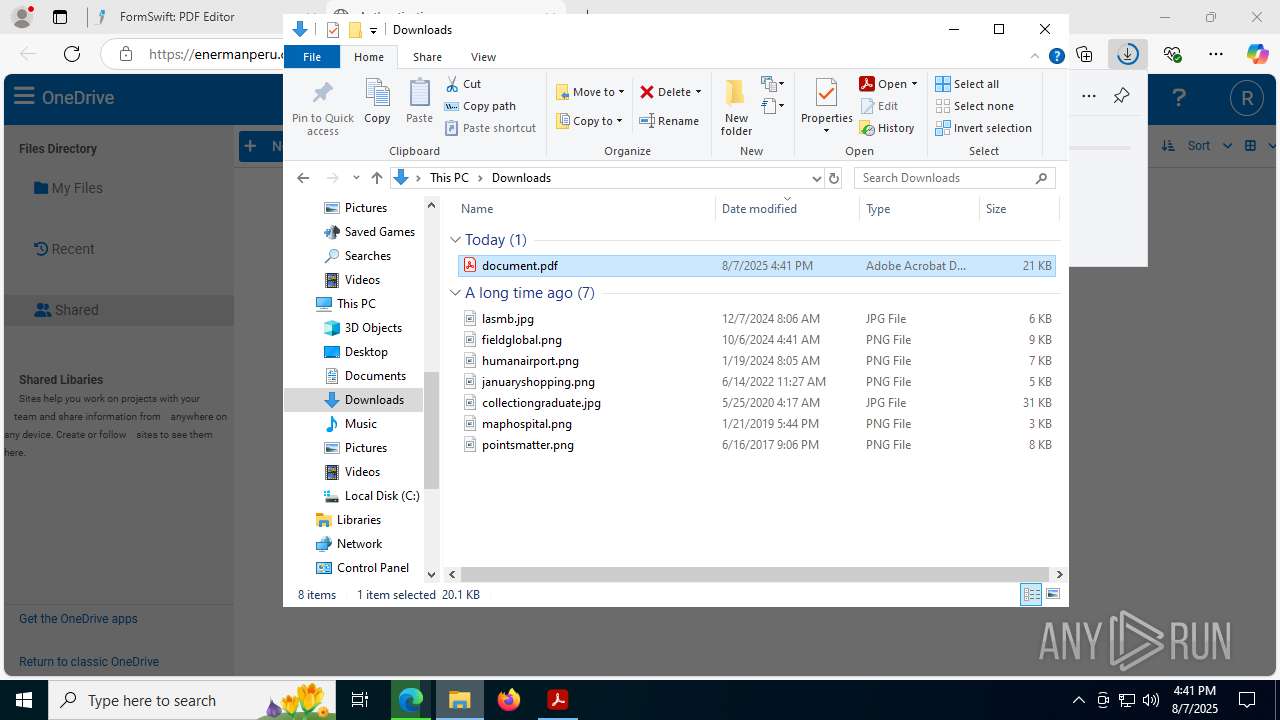
| 1964 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" "C:\Users\admin\Downloads\document.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | OpenWith.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2284,i,5573392083505399,8419710955573819921,262144 --variations-seed-version --mojo-platform-channel-handle=2280 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2216,i,5573392083505399,8419710955573819921,262144 --variations-seed-version --mojo-platform-channel-handle=2384 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://url6450.formswift.com/ls/click?upn=u001.T8-2FTfWgYcIO3dd7tP2R-2BFFIm9UiyQ-2Fcyk-2B-2BX5-2Bn4Qbdhag7OSpFSpvBpW1Qv2kQ9q7XRw9KccM6hi2xymffjpxaQjd9Gul5Qa5uDBDhanuvOHGH94KLgmGHqEjuh6ywD2OUbMJ8X5tO3yPgHc7oClKVh84DAk13nNz6HeMu6OzmjCPmewbN-2BKA3uCMyv16wGy7bg-2F-2BB4FmSDhklftZpOSUjjozGRLoKttfZFyI7Yoik-3DTE7k_Zq48bdq-2F02-2BJJaHBYmqo8kT-2F-2Ff0-2Bqb5-2FELZhFVlEiIPfu8MyPOZ3BPF95514soGWxmkirF65-2B5QVxnR7AN2-2BZ669dEFEJ2Wo7FtIOmp6X8BzybEx7V0za-2FomRjoom4-2F-2FZjRENbzl-2BgyscevW6w2bYZRxxTNolNI0kOBxvloz9zT0-2Ft-2B8pIHrUd4GqswUj56WNwU7BZBAck6jBuaFplXXUA-3D-3D" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2312 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4228,i,5573392083505399,8419710955573819921,262144 --variations-seed-version --mojo-platform-channel-handle=4288 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2720,i,5573392083505399,8419710955573819921,262144 --variations-seed-version --mojo-platform-channel-handle=2736 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
28 131
Read events
27 919
Write events
205
Delete events
7
Modification events
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2DCF90685F9A2F00 | |||
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590674 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6BAB738B-22C5-4B74-9A98-62B3596FAEFC} | |||
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590674 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8791FC49-308E-4A86-BA2A-56A80A132DC6} | |||
| (PID) Process: | (2280) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590674 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3C971348-AD8E-4B28-894F-5E22AE2FB50B} | |||
Executable files
0
Suspicious files
516
Text files
88
Unknown types
96
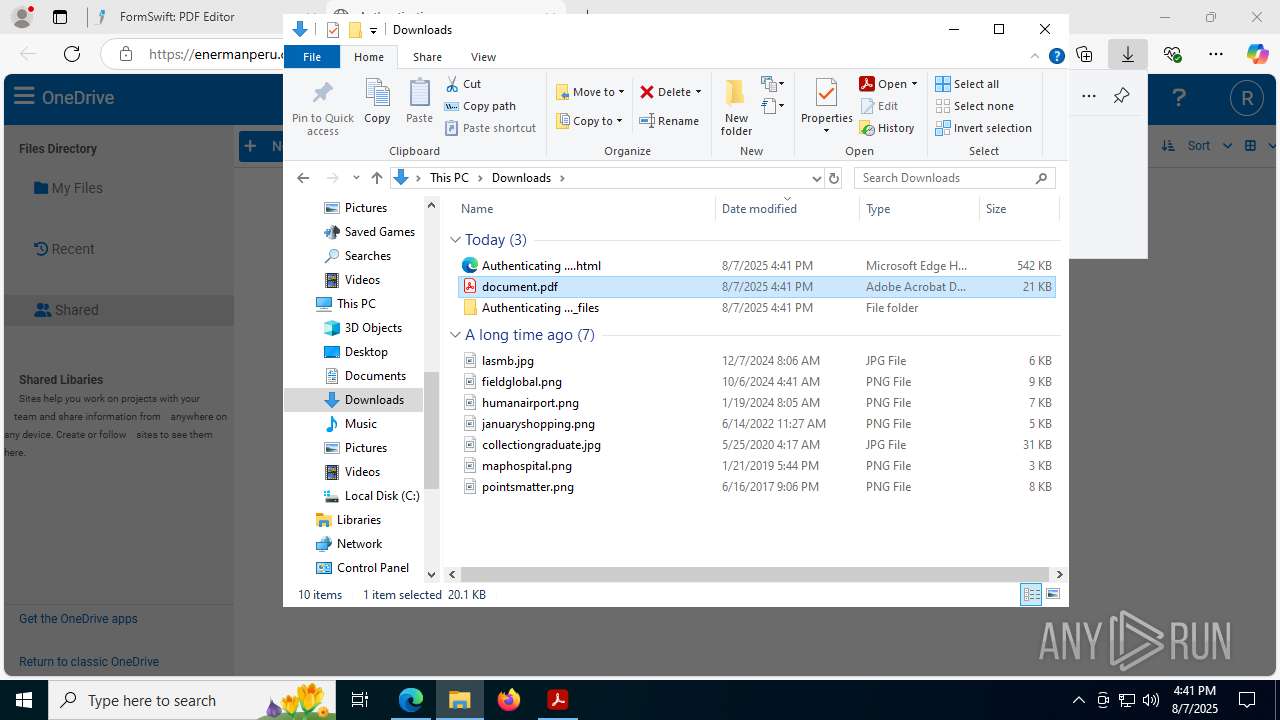
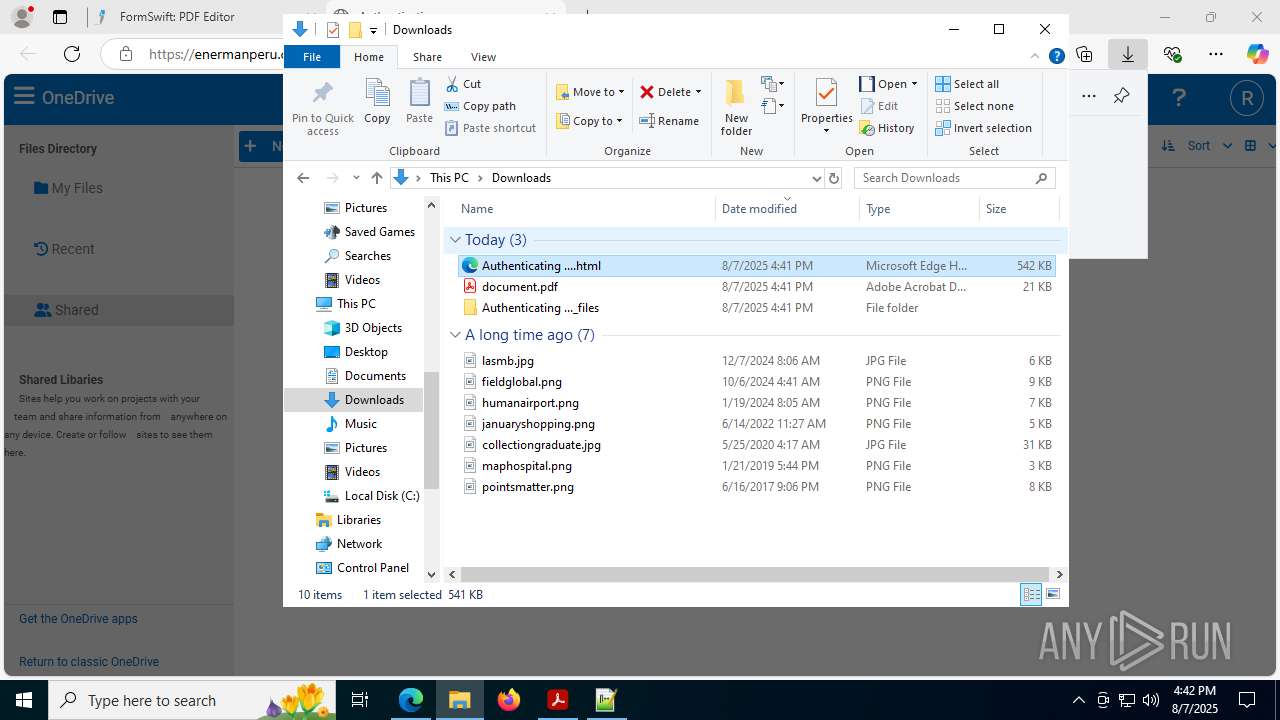
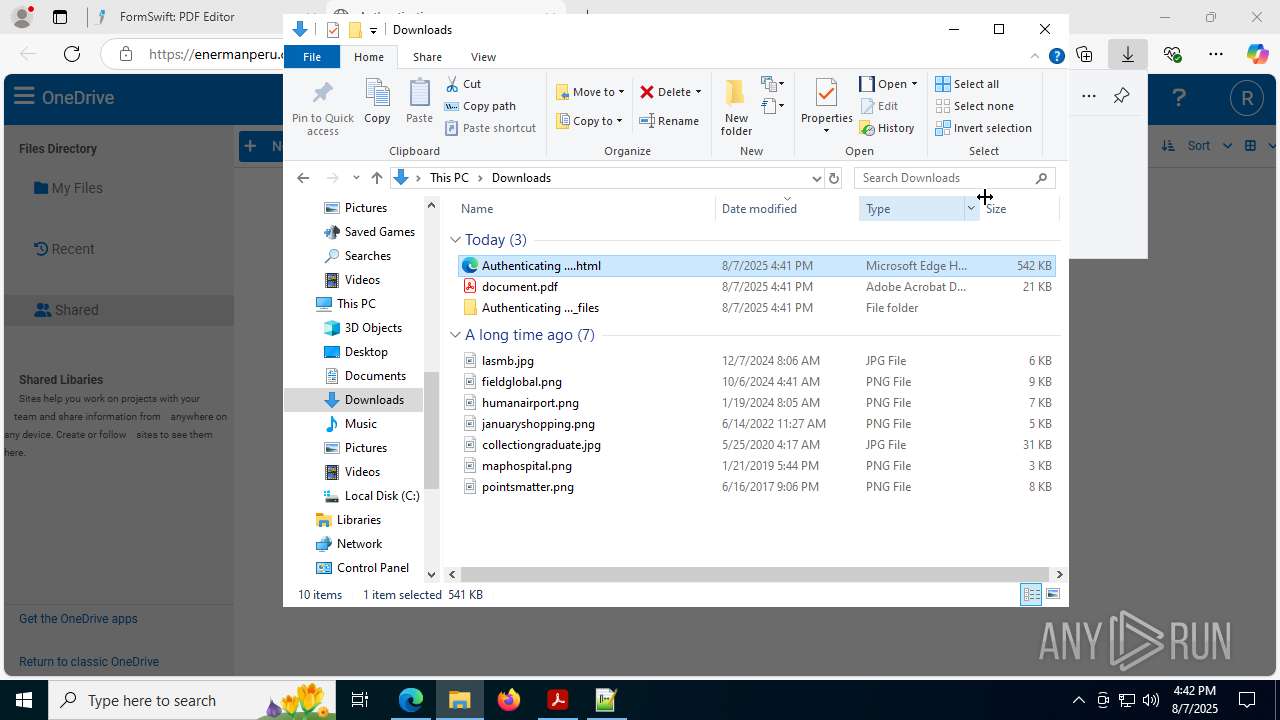
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d7ae.TMP | — | |
MD5:— | SHA256:— | |||
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d7cd.TMP | — | |
MD5:— | SHA256:— | |||
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d7cd.TMP | — | |
MD5:— | SHA256:— | |||
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d79e.TMP | — | |
MD5:— | SHA256:— | |||
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF18d7ec.TMP | — | |
MD5:— | SHA256:— | |||
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2280 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d7ec.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
184
DNS requests
202
Threats
52
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2228 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:etE5O8zfT0afTfVjXqsPg1C_j46jpWIcQlldVWKlMJ8&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1872 | SIHClient.exe | GET | 200 | 23.32.97.216:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4912 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1872 | SIHClient.exe | GET | 200 | 23.32.97.216:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7824 | svchost.exe | HEAD | 200 | 2.16.168.102:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1755052258&P2=404&P3=2&P4=gEBrFHcuVEc6eOnDFimMXZ%2bZt0BMVv6bakzRxdgkPpyXH3hlak7p8WOKKY8Rkq7saGAyatOAQ6jtSF2pqJdjlg%3d%3d | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7824 | svchost.exe | GET | 206 | 2.16.168.102:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1755052258&P2=404&P3=2&P4=gEBrFHcuVEc6eOnDFimMXZ%2bZt0BMVv6bakzRxdgkPpyXH3hlak7p8WOKKY8Rkq7saGAyatOAQ6jtSF2pqJdjlg%3d%3d | unknown | — | — | whitelisted |
7824 | svchost.exe | GET | 206 | 2.16.168.102:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1755052258&P2=404&P3=2&P4=gEBrFHcuVEc6eOnDFimMXZ%2bZt0BMVv6bakzRxdgkPpyXH3hlak7p8WOKKY8Rkq7saGAyatOAQ6jtSF2pqJdjlg%3d%3d | unknown | — | — | whitelisted |
1964 | Acrobat.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4944 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2228 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2228 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2228 | msedge.exe | 104.18.232.25:443 | url6450.formswift.com | CLOUDFLARENET | — | whitelisted |
2228 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2228 | msedge.exe | 23.3.89.122:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
url6450.formswift.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
formswift.com |
| whitelisted |
next-terraform.formswift.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2228 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|