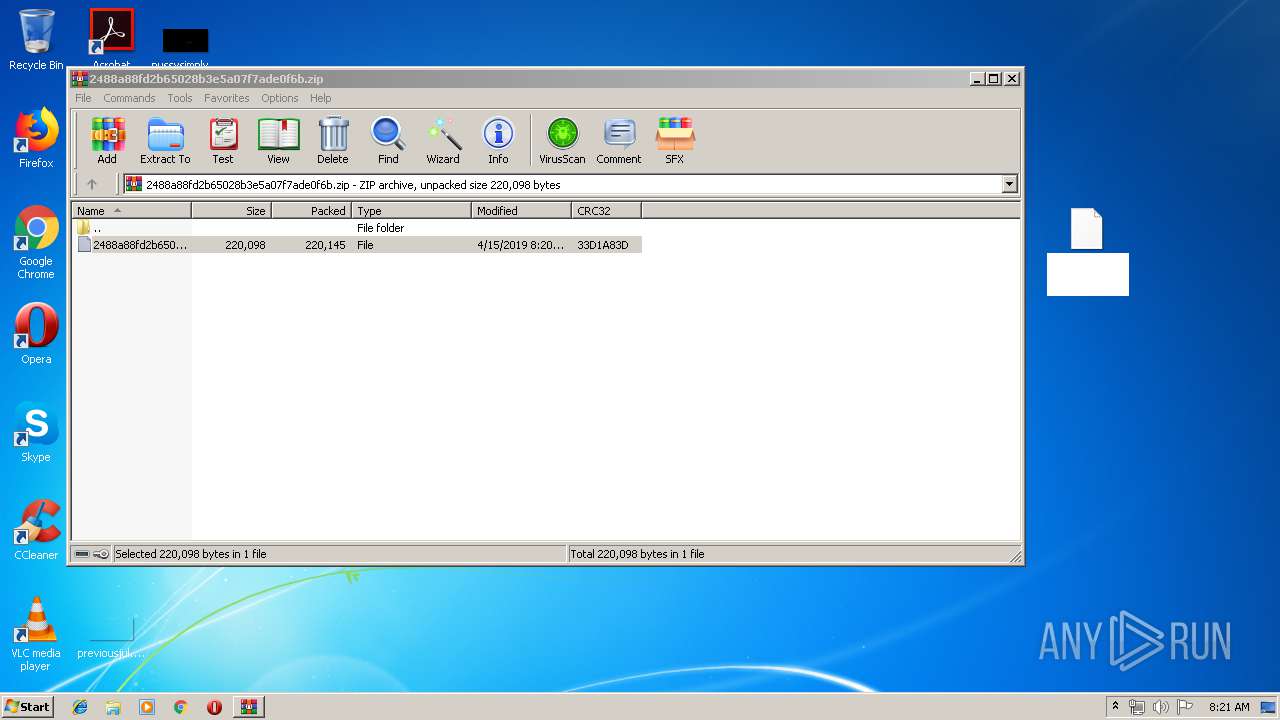
| File name: | 2488a88fd2b65028b3e5a07f7ade0f6b.zip |
| Full analysis: | https://app.any.run/tasks/26d67b63-e2ed-459a-92cf-032dbf7cdc7b |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | April 15, 2019, 07:20:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 96D22B020AA484DFC2D07003C2ABF688 |
| SHA1: | A98EE0CE12CD04767D8EFB10D197CEF444E786C7 |
| SHA256: | 953F180CDD9CB2F26F507726BC769BFE73B2E6DFC1E6599B617E36E1EB5443D8 |
| SSDEEP: | 6144:pZKy2lObVTclebv/6BKC2bPH5QXwRGHKZEBba:p8oesrSBK/v5QXwRGHK3 |
MALICIOUS
Renames files like Ransomware
- explorer.exe (PID: 2044)
Application was dropped or rewritten from another process
- Product List.exe (PID: 3160)
FORMBOOK was detected
- explorer.exe (PID: 2044)
Formbook was detected
- svchost.exe (PID: 2100)
- Firefox.exe (PID: 1488)
Uses SVCHOST.EXE for hidden code execution
- explorer.exe (PID: 2044)
Actions looks like stealing of personal data
- svchost.exe (PID: 2100)
Changes the autorun value in the registry
- svchost.exe (PID: 2100)
Connects to CnC server
- explorer.exe (PID: 2044)
Stealing of credential data
- svchost.exe (PID: 2100)
SUSPICIOUS
Reads Internet Cache Settings
- explorer.exe (PID: 2044)
Creates files in the user directory
- explorer.exe (PID: 2044)
- svchost.exe (PID: 2100)
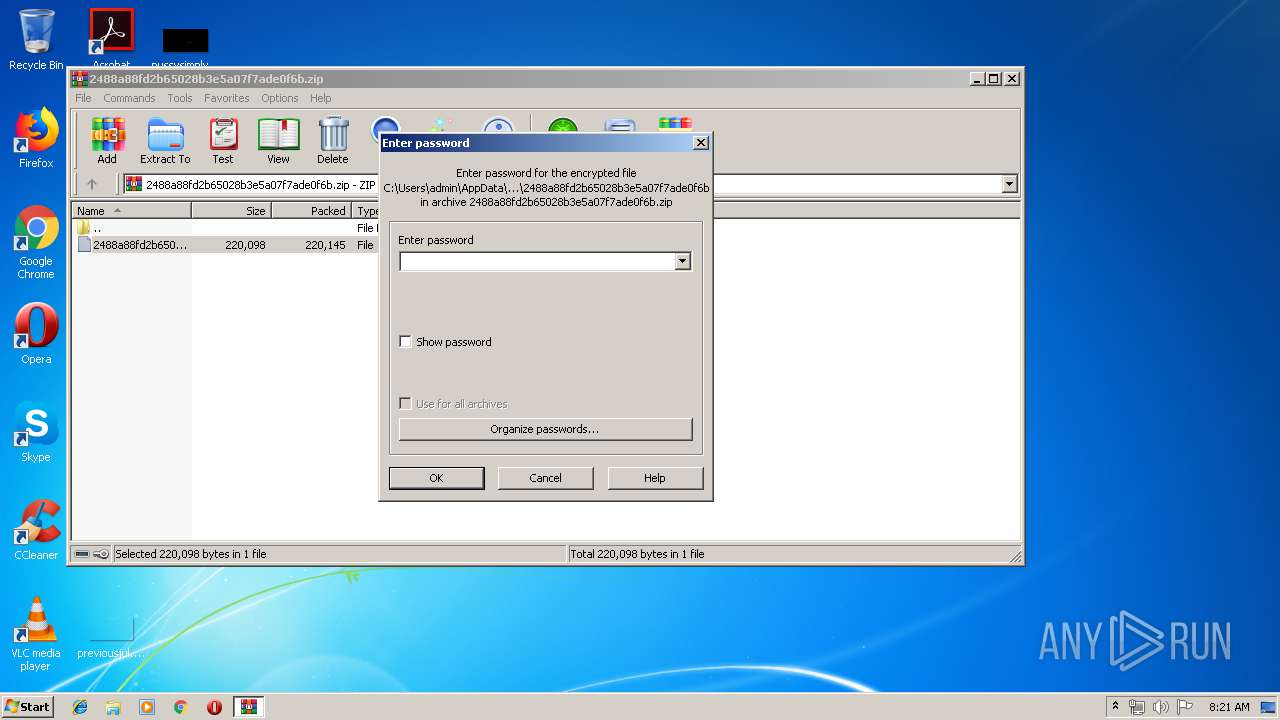
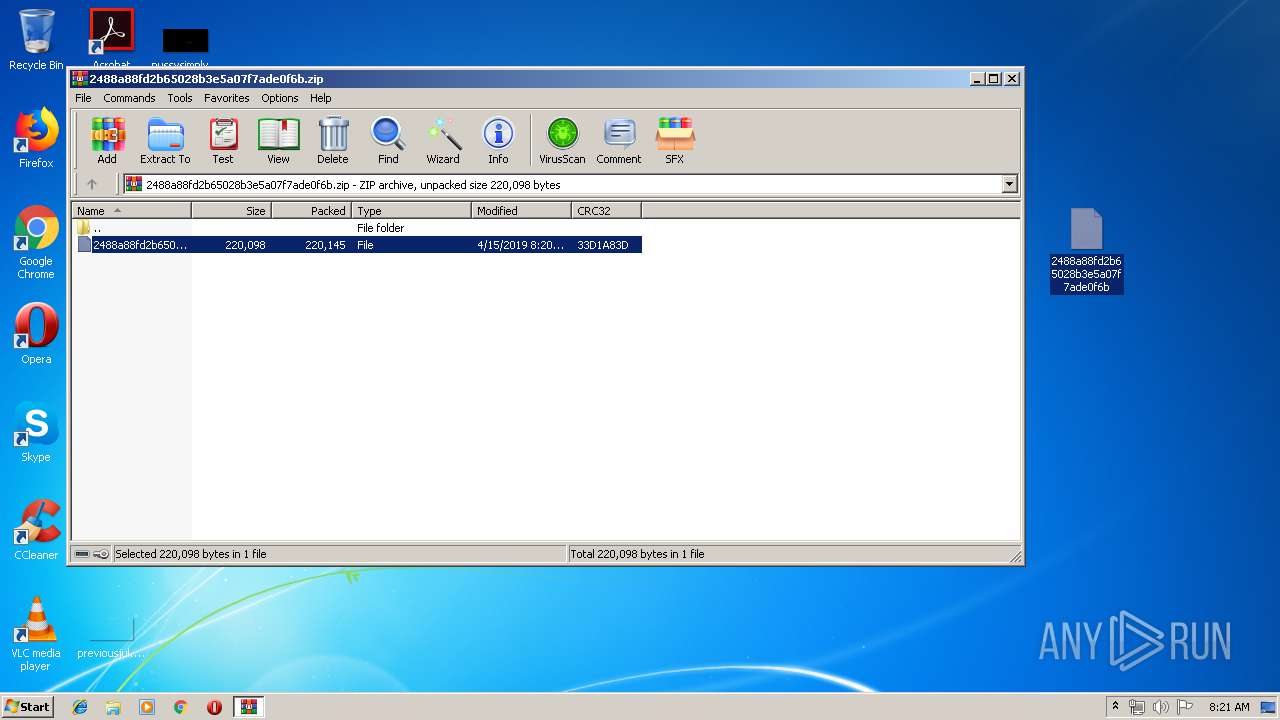
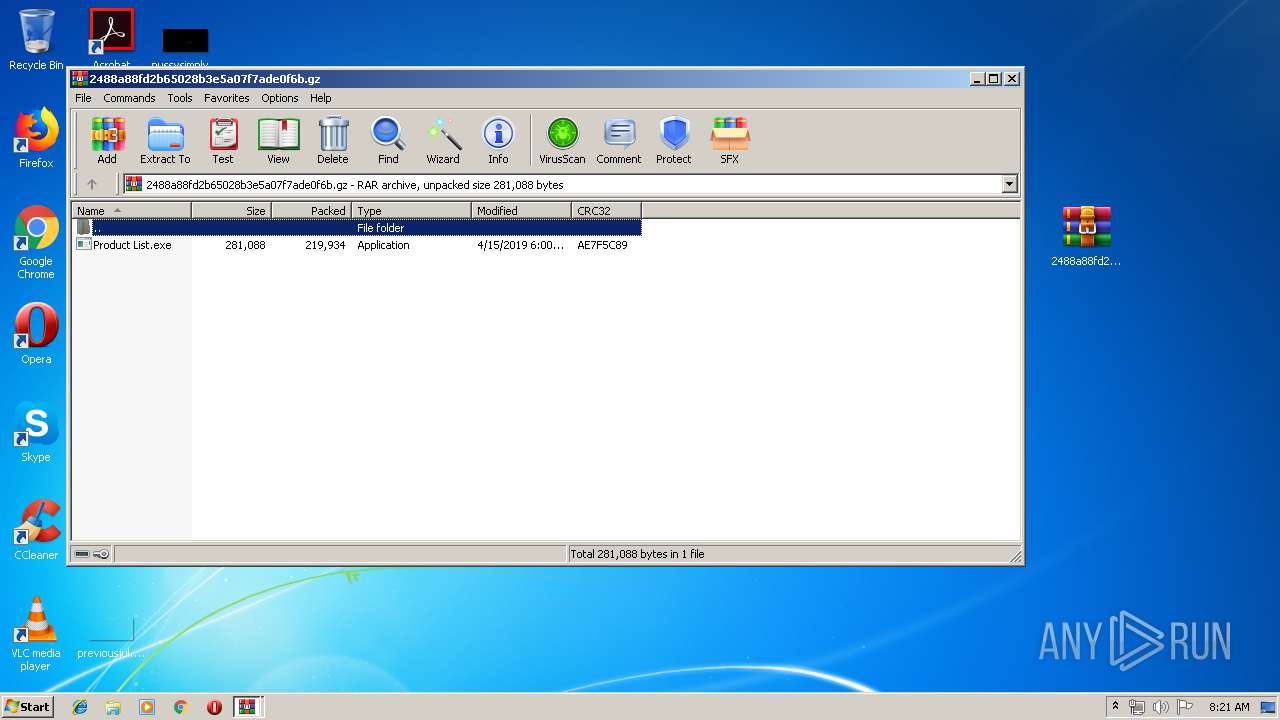
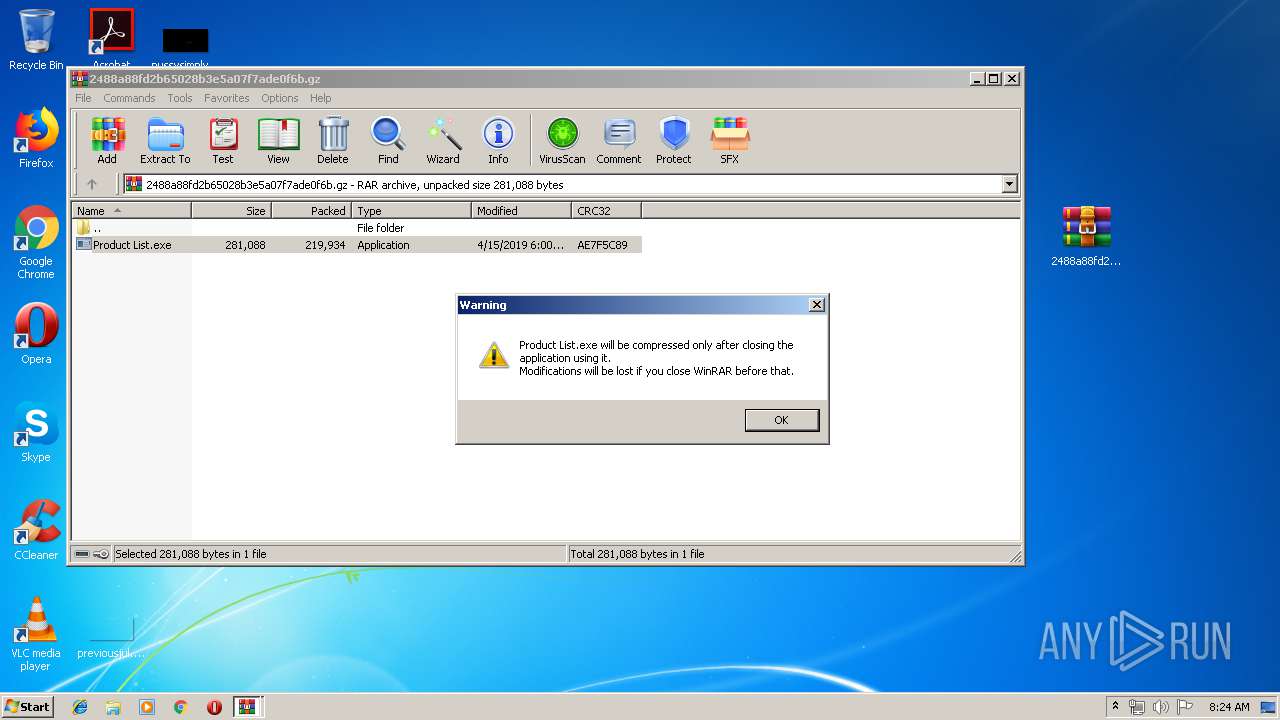
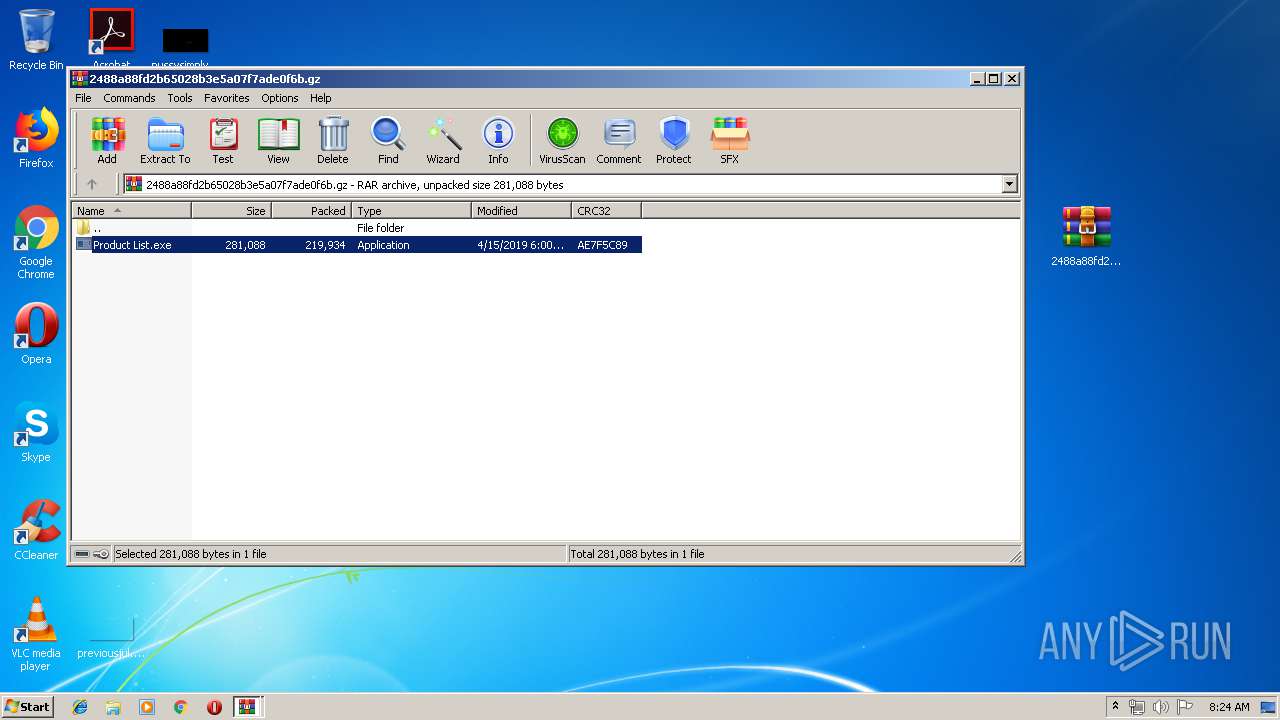
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3784)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 2100)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 2100)
INFO
Creates files in the user directory
- Firefox.exe (PID: 1488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
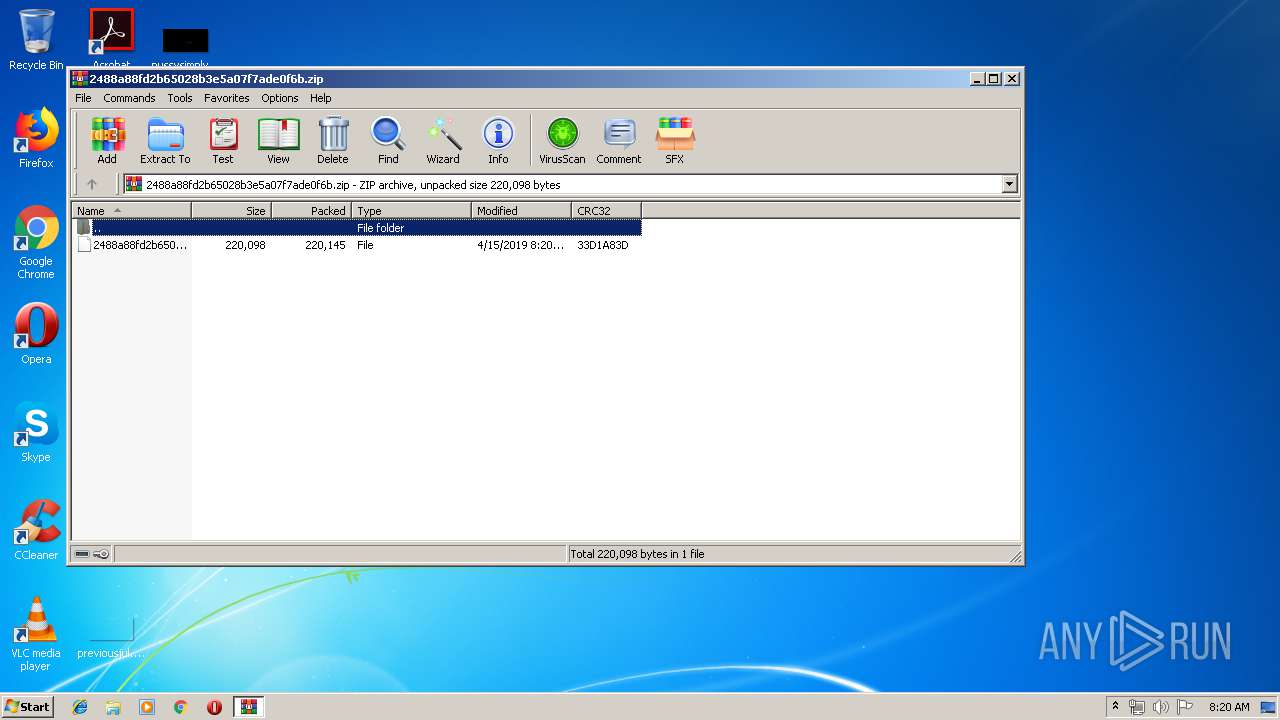
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:15 10:20:09 |
| ZipCRC: | 0x33d1a83d |
| ZipCompressedSize: | 220145 |
| ZipUncompressedSize: | 220098 |
| ZipFileName: | 2488a88fd2b65028b3e5a07f7ade0f6b |
Total processes
39
Monitored processes
7
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1488 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | svchost.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2044 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2100 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3784.38337\Product List.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3784.38337\Product List.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3292 | /c del "C:\Users\admin\AppData\Local\Temp\Rar$EXa3784.38337\Product List.exe" | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3784 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\2488a88fd2b65028b3e5a07f7ade0f6b.gz" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3848 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\2488a88fd2b65028b3e5a07f7ade0f6b.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 627
Read events
2 570
Write events
57
Delete events
0
Modification events
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2488a88fd2b65028b3e5a07f7ade0f6b.zip | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
1
Suspicious files
75
Text files
1
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3848.36308\2488a88fd2b65028b3e5a07f7ade0f6b | — | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\Desktop\2488a88fd2b65028b3e5a07f7ade0f6b | compressed | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 3784 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3784.38337\Product List.exe | executable | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019041520190416\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2100 | svchost.exe | C:\Users\admin\AppData\Roaming\1LRN9DEE\1LRlogrc.ini | binary | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\Desktop\2488a88fd2b65028b3e5a07f7ade0f6b.gz | compressed | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\2488a88fd2b65028b3e5a07f7ade0f6b.gz.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1488 | Firefox.exe | C:\Users\admin\AppData\Roaming\1LRN9DEE\1LRlogrf.ini | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
9
DNS requests
4
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | explorer.exe | GET | — | 50.63.202.52:80 | http://www.networkamericanexpress.com/mi/?GV1H=oflm98AGJqbDAYIAKxP5wYsNUEeATbpKKrQdAuWYCtX8IaxDpb1yt9yRxHZ3fUNYNpdy0g==&Aln=oHd0DbCpQZ | US | — | — | malicious |
2044 | explorer.exe | POST | — | 50.63.202.52:80 | http://www.networkamericanexpress.com/mi/ | US | — | — | malicious |
2044 | explorer.exe | POST | — | 192.64.115.228:80 | http://www.menflax.com/mi/ | US | — | — | malicious |
2044 | explorer.exe | POST | — | 50.63.202.52:80 | http://www.networkamericanexpress.com/mi/ | US | — | — | malicious |
2044 | explorer.exe | POST | 404 | 192.64.115.228:80 | http://www.menflax.com/mi/ | US | html | 291 b | malicious |
2044 | explorer.exe | GET | 404 | 192.195.77.95:80 | http://www.invincibledragon.com/mi/?GV1H=JIt6Zpkf9rwkwlyXG/5TjlgZ/qpQikXuVVsa+gXKqr3EP17blH9OahaaMy5UT/mwzsuO7g==&Aln=oHd0DbCpQZ | US | html | 1.33 Kb | malicious |
2044 | explorer.exe | GET | 404 | 192.64.115.228:80 | http://www.menflax.com/mi/?GV1H=8oV2fxf6fz//f8qaYFnbZYRGqsm/wxoip8/w2J8f8NU1nSd0QnXNdB7srmcEQzPRiNALhg==&Aln=oHd0DbCpQZ | US | html | 326 b | malicious |
2044 | explorer.exe | POST | 404 | 192.64.115.228:80 | http://www.menflax.com/mi/ | US | html | 291 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2044 | explorer.exe | 192.64.115.228:80 | www.menflax.com | Namecheap, Inc. | US | malicious |
2044 | explorer.exe | 192.195.77.95:80 | www.invincibledragon.com | 1&1 Internet SE | US | malicious |
2044 | explorer.exe | 50.63.202.52:80 | www.networkamericanexpress.com | GoDaddy.com, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.invincibledragon.com |
| unknown |
www.menflax.com |
| malicious |
www.mobilinbankasi-akbank.com |
| unknown |
www.networkamericanexpress.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2044 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
2044 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
2044 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
2044 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
2044 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
2044 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
2044 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
2044 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
6 ETPRO signatures available at the full report