| File name: | svchost.exe |
| Full analysis: | https://app.any.run/tasks/d5cea3a4-180b-4a06-9fe6-49740aa04909 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 26, 2023, 14:57:36 |
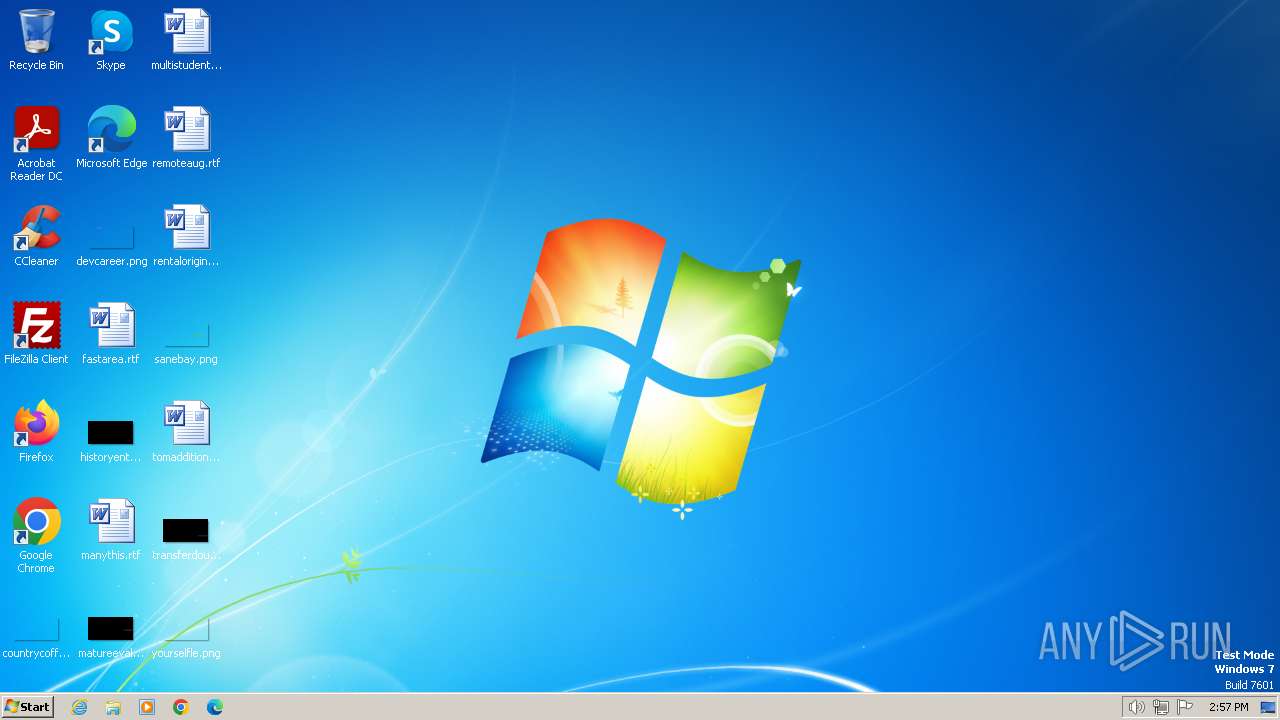
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 1421378B1FA1B2BEC518C7B05C137359 |
| SHA1: | F9434EDD2D2519865F650AD4983722B84B006310 |
| SHA256: | 9536B587FA1B06BE4579CFB144CDB5D0EE43E265647A4D1E02205E0C845ED9D1 |
| SSDEEP: | 49152:+fEcsT90z2NkvSCmRf7uY1+DVlYZ+hHjGmt/3Dg109mGkCWlRqYn1wyXFi7D2ozN:E2NkKCmRf7uY1+DVlYZ+hHaIDgdovJ |
MALICIOUS
QUASAR has been detected (SURICATA)
- Client.exe (PID: 1072)
ASYNCRAT has been detected (SURICATA)
- Client.exe (PID: 1072)
Connects to the CnC server
- Client.exe (PID: 1072)
QUASAR has been detected (YARA)
- Client.exe (PID: 1072)
SUSPICIOUS
Reads settings of System Certificates
- Client.exe (PID: 1072)
Connects to unusual port
- Client.exe (PID: 1072)
Reads the Internet Settings
- Client.exe (PID: 1072)
INFO
Reads the computer name
- svchost.exe (PID: 120)
- Client.exe (PID: 1072)
Checks supported languages
- svchost.exe (PID: 120)
- Client.exe (PID: 1072)
Drops the executable file immediately after the start
- svchost.exe (PID: 120)
- RdrCEF.exe (PID: 1792)
Starts itself from another location
- svchost.exe (PID: 120)
Creates files or folders in the user directory
- svchost.exe (PID: 120)
Reads the machine GUID from the registry
- svchost.exe (PID: 120)
- Client.exe (PID: 1072)
Reads Environment values
- svchost.exe (PID: 120)
- Client.exe (PID: 1072)
Create files in a temporary directory
- Client.exe (PID: 1072)
Manual execution by a user
- AcroRd32.exe (PID: 1604)
Application launched itself
- AcroRd32.exe (PID: 1604)
- RdrCEF.exe (PID: 1792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(1072) Client.exe
Version1.4.1
C2 (2)brofisthej.ddns.net:4822
Sub_DirSubDir
Install_NameClient.exe
Mutexbba16831-38af-412f-a8c5-a3e7484d19bf
StartupQuasar Client Startup
TagOffice04
LogDirLogs
SignatureUpr+6WQNjQ9NkGouoyCvzEKtYONplVr4kV4yUOFKVEenYzhqnV1j4mE4cuaXftsPqVwaLRDSCILZE4g+aU2LgF/v82hhHPXbB5PVqru65I4LTe/x5162BlxMg0djvaZAZkYHsfJZD/XanpkzaIN/+cPzTIx2lDsHcz153CxmddSBLuDz3m5PrBrxMqCYzFr9gjKONJvvUsYMjrZv3yoOLi7AgA1CfQnDN0SRrUbWkY6EqzZq6p2MQgop4pTjbQcaTP5Tc0/yHthsQWmRVVAa9F0jHIixGRQIYzoSKJLjvUc2...
CertificateMIIE9DCCAtygAwIBAgIQANjQaWGbQ6C7qZX/TPNaBTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMTIyMjE3MzIxNVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEArbSQqzlqUgjC54yRdUkyZGf4Y/8KFNq19TyOXppOb2cb8+doXIUbOCy5Ahm96Iym5znTOorz...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:12 17:16:39+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 3261952 |
| InitializedDataSize: | 3584 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31e40e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.4.9 |
| ProductVersionNumber: | 1.1.2.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | svchost |
| FileDescription: | svchost |
| FileVersion: | 1.5.4.9 |
| InternalName: | svchost.exe |
| LegalCopyright: | Microsoft@2023 |
| LegalTrademarks: | Microsoft |
| OriginalFileName: | svchost.exe |
| ProductName: | svchost.exe |
| ProductVersion: | 1.1.2.4 |
| AssemblyVersion: | 1.1.2.4 |
Total processes
46
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Users\admin\AppData\Local\Temp\svchost.exe" | C:\Users\admin\AppData\Local\Temp\svchost.exe | — | explorer.exe | |||||||||||
User: admin Company: svchost Integrity Level: MEDIUM Description: svchost Exit code: 3 Version: 1.5.4.9 Modules
| |||||||||||||||
| 1072 | "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | svchost.exe | ||||||||||||
User: admin Company: svchost Integrity Level: MEDIUM Description: svchost Exit code: 0 Version: 1.5.4.9 Modules
Quasar(PID) Process(1072) Client.exe Version1.4.1 C2 (2)brofisthej.ddns.net:4822 Sub_DirSubDir Install_NameClient.exe Mutexbba16831-38af-412f-a8c5-a3e7484d19bf StartupQuasar Client Startup TagOffice04 LogDirLogs SignatureUpr+6WQNjQ9NkGouoyCvzEKtYONplVr4kV4yUOFKVEenYzhqnV1j4mE4cuaXftsPqVwaLRDSCILZE4g+aU2LgF/v82hhHPXbB5PVqru65I4LTe/x5162BlxMg0djvaZAZkYHsfJZD/XanpkzaIN/+cPzTIx2lDsHcz153CxmddSBLuDz3m5PrBrxMqCYzFr9gjKONJvvUsYMjrZv3yoOLi7AgA1CfQnDN0SRrUbWkY6EqzZq6p2MQgop4pTjbQcaTP5Tc0/yHthsQWmRVVAa9F0jHIixGRQIYzoSKJLjvUc2... CertificateMIIE9DCCAtygAwIBAgIQANjQaWGbQ6C7qZX/TPNaBTANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIzMTIyMjE3MzIxNVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEArbSQqzlqUgjC54yRdUkyZGf4Y/8KFNq19TyOXppOb2cb8+doXIUbOCy5Ahm96Iym5znTOorz... | |||||||||||||||
| 1316 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1180,14350190256270406937,5282226607595340060,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=1308069199148078100 --mojo-platform-channel-handle=1204 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1180,14350190256270406937,5282226607595340060,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3048031219924328090 --renderer-client-id=6 --mojo-platform-channel-handle=1388 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1180,14350190256270406937,5282226607595340060,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17853171748596072484 --renderer-client-id=2 --mojo-platform-channel-handle=1188 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1180,14350190256270406937,5282226607595340060,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=13869928338044172686 --mojo-platform-channel-handle=1264 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1180,14350190256270406937,5282226607595340060,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2627981671846119663 --renderer-client-id=7 --mojo-platform-channel-handle=2380 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
Total events
18 957
Read events
18 824
Write events
132
Delete events
1
Modification events
| (PID) Process: | (120) svchost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1072) Client.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1316) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 1 | |||
| (PID) Process: | (1316) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\SessionManagement |
| Operation: | write | Name: | bNormalExit |
Value: 1 | |||
| (PID) Process: | (1604) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1316) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | uLastAppLaunchTimeStamp |
Value: 738908672 | |||
| (PID) Process: | (1316) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | iNumReaderLaunches |
Value: 5 | |||
| (PID) Process: | (1316) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\HomeWelcomeFirstMileReader |
| Operation: | write | Name: | iCardCountShown |
Value: 1 | |||
| (PID) Process: | (1604) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1604) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
1
Suspicious files
140
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1792 | RdrCEF.exe | — | ||
MD5:— | SHA256:— | |||
| 1072 | Client.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1072 | Client.exe | C:\Users\admin\AppData\Local\Temp\Tar14DC.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 1072 | Client.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:C8FAFE604B59222580781BAD37E89FF2 | SHA256:374AAEF7200B17F14BC1DAA1ABA931841F1E2E4641D861017E5FDC89E3C9A976 | |||
| 1072 | Client.exe | C:\Users\admin\AppData\Local\Temp\Cab14DB.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 120 | svchost.exe | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | executable | |
MD5:1421378B1FA1B2BEC518C7B05C137359 | SHA256:9536B587FA1B06BE4579CFB144CDB5D0EE43E265647A4D1E02205E0C845ED9D1 | |||
| 1316 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Reader\Files\TESTING | mp3 | |
MD5:DC84B0D741E5BEAE8070013ADDCC8C28 | SHA256:81FF65EFC4487853BDB4625559E69AB44F19E0F5EFBD6D5B2AF5E3AB267C8E06 | |||
| 1316 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Reader\SOPHIA.json | binary | |
MD5:01F233C92A89C705229A0D63D09F846A | SHA256:62137C4381ACC2DE8BCA158AD9D9CE730BD7A96A39A2FB64CE7CFA5C861CF7B4 | |||
| 1792 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\0786087c3c360803_0 | binary | |
MD5:968086DBC34FE11FB36E00F73BD18520 | SHA256:D86DC8AF7085BD133D7FECE946C30FE560874ECF3A80E186A0275FE2EB31D2EF | |||
| 1792 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\2a426f11fd8ebe18_0 | binary | |
MD5:6164D30ACA36ABEB1323173EED2D0573 | SHA256:FE51B96BA92BFEA81D7F0E389AB09CFD95DB738DCC1CB62CC97EEEB14C9D01B7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
8
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1072 | Client.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0f50a1535e5779d5 | unknown | compressed | 65.2 Kb | unknown |
1604 | AcroRd32.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
1604 | AcroRd32.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9eebde7a6842aeef | unknown | compressed | 4.66 Kb | unknown |
1604 | AcroRd32.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1c8eb978cd2a7dc7 | unknown | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1072 | Client.exe | 2.70.186.204:4822 | brofisthej.ddns.net | Hi3G Access AB | SE | unknown |
1072 | Client.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1072 | Client.exe | 195.201.57.90:443 | ipwho.is | Hetzner Online GmbH | DE | unknown |
1792 | RdrCEF.exe | 2.19.105.74:443 | geo2.adobe.com | AKAMAI-AS | DE | whitelisted |
1792 | RdrCEF.exe | 3.219.243.226:443 | p13n.adobe.io | AMAZON-AES | US | unknown |
1792 | RdrCEF.exe | 184.30.20.134:443 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
1604 | AcroRd32.exe | 104.124.11.64:443 | acroipm2.adobe.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
brofisthej.ddns.net |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ipwho.is |
| malicious |
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
1072 | Client.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
1072 | Client.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (Quasar CnC) |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO External IP Lookup Domain in DNS Lookup (ipwho .is) |
1072 | Client.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] QuasarRAT Successful Connection (GCM_SHA384) |