| File name: | SharkHack.exe |
| Full analysis: | https://app.any.run/tasks/02d382bc-b5d9-4eb9-894a-71b5b5970b22 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | October 23, 2024, 20:53:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 4 sections |
| MD5: | ADDC37EF44B74205A75EDF882B91F87A |
| SHA1: | 5818795D54863B85050CAD0A4F978FF266BA8A04 |
| SHA256: | 94D7EA2F2E449BBAA4DB94F4E2857C36F28F1FC970A3CA67035243C17E53A803 |
| SSDEEP: | 98304:OqRXLgfIXx2dNXlDGg6UW4FJfH4f9kxoX5A1bktWHlJvUfyFkjIIKg5N7IyjIa+R:sJs0p |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7776)
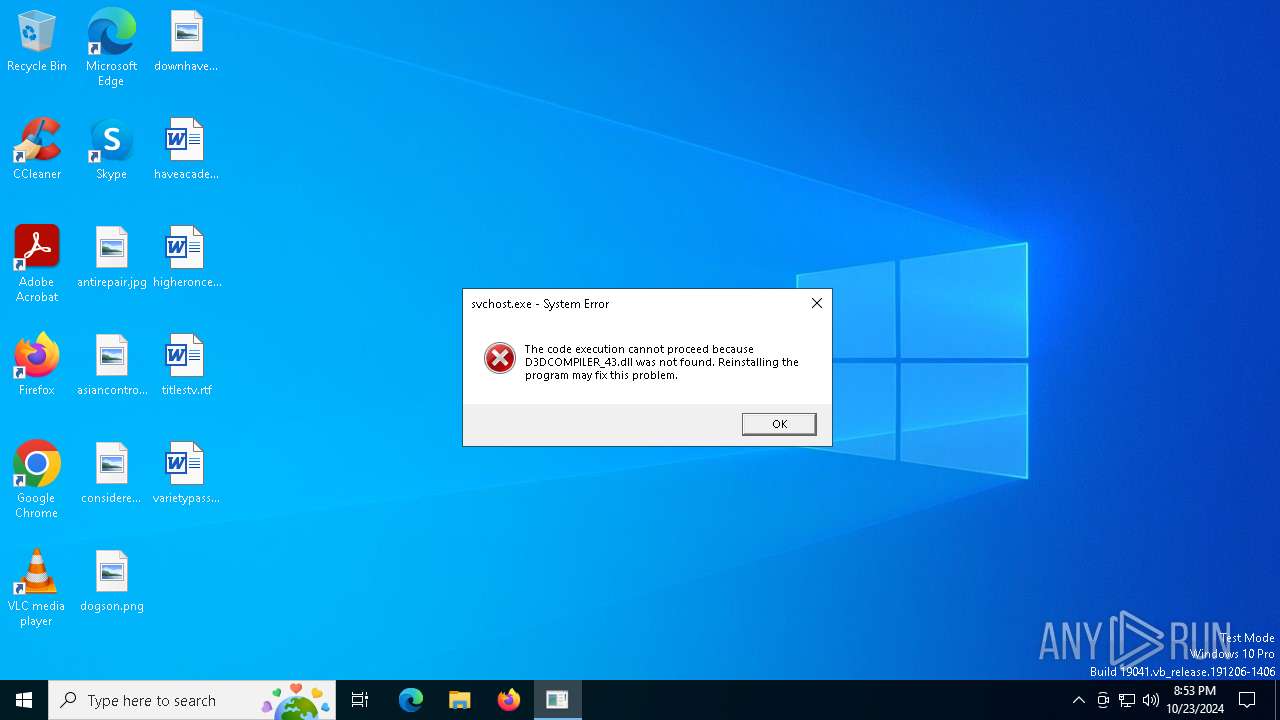
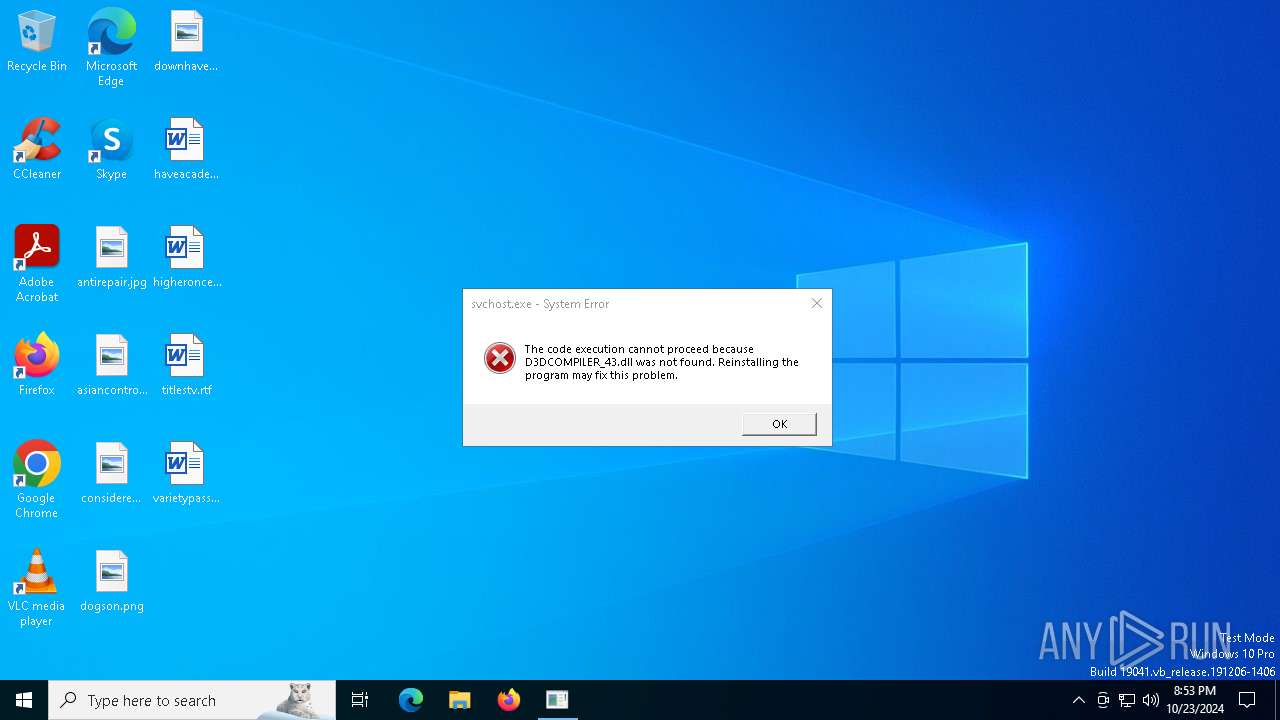
DIABLONET has been detected (SURICATA)
- javaw.exe (PID: 1372)
- javaw.exe (PID: 540)
- javaw.exe (PID: 6660)
DIABLONET has been detected (YARA)
- javaw.exe (PID: 1372)
SUSPICIOUS
The process creates files with name similar to system file names
- SharkHack.exe (PID: 5592)
Reads security settings of Internet Explorer
- SharkHack.exe (PID: 5592)
Starts CMD.EXE for commands execution
- java.exe (PID: 7564)
- javaw.exe (PID: 6660)
- javaw.exe (PID: 1372)
- javaw.exe (PID: 540)
Executable content was dropped or overwritten
- SharkHack.exe (PID: 5592)
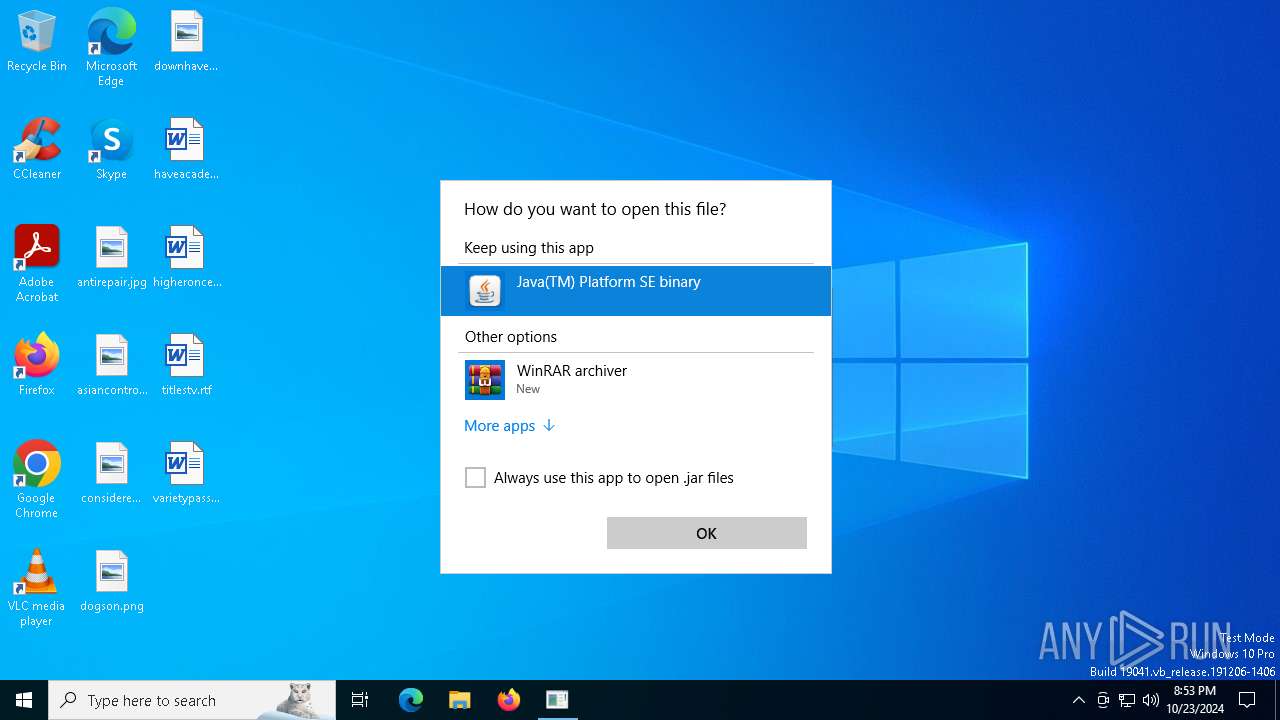
Checks for Java to be installed
- explorer.exe (PID: 4316)
The process executes via Task Scheduler
- javaw.exe (PID: 7184)
- javaw.exe (PID: 6660)
- javaw.exe (PID: 540)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4676)
- cmd.exe (PID: 7396)
- cmd.exe (PID: 5048)
Connects to unusual port
- javaw.exe (PID: 6660)
- javaw.exe (PID: 1372)
- javaw.exe (PID: 540)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 6664)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7908)
Contacting a server suspected of hosting an CnC
- javaw.exe (PID: 1372)
- javaw.exe (PID: 6660)
- javaw.exe (PID: 540)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7696)
INFO
Checks supported languages
- SharkHack.exe (PID: 5592)
- javaw.exe (PID: 5444)
- explorer.exe (PID: 4316)
Reads the computer name
- SharkHack.exe (PID: 5592)
The process uses the downloaded file
- SharkHack.exe (PID: 5592)
Create files in a temporary directory
- SharkHack.exe (PID: 5592)
- javaw.exe (PID: 5444)
Process checks computer location settings
- SharkHack.exe (PID: 5592)
Creates files in the program directory
- javaw.exe (PID: 5444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (26.2) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (11.1) |
| .exe | | | Win64 Executable (generic) (9.9) |
| .scr | | | Windows screen saver (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:10:22 18:12:54+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 4058112 |
| InitializedDataSize: | 74240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3e0bae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | payload.exe |
| LegalCopyright: | |
| OriginalFileName: | payload.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
165
Monitored processes
38
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\cache.jar" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | svchost.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1372 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\cache.jar" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | OpenWith.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Version: 8.0.2710.9 Modules
| |||||||||||||||
| 3744 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3912 | wmic cpu get name | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4316 | "C:\Users\admin\AppData\Local\Temp\explorer.exe" | C:\Users\admin\AppData\Local\Temp\explorer.exe | SharkHack.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4676 | cmd /c wmic /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get displayName /Format:List | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4816 | "C:\Users\admin\AppData\Local\Temp\explorer.exe" | C:\Users\admin\AppData\Local\Temp\explorer.exe | — | SharkHack.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 5048 | cmd /c wmic /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get displayName /Format:List | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5444 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\explorer.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
Total events
6 968
Read events
6 963
Write events
5
Delete events
0
Modification events
| (PID) Process: | (7564) java.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jar\OpenWithProgids |
| Operation: | write | Name: | jarfile |
Value: | |||
| (PID) Process: | (7928) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jar\OpenWithProgids |
| Operation: | write | Name: | jarfile |
Value: | |||
Executable files
5
Suspicious files
18
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7928 | OpenWith.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\IconCacheToDelete\icn4F0F.tmp | — | |
MD5:— | SHA256:— | |||
| 5592 | SharkHack.exe | C:\Users\admin\AppData\Local\Temp\svchost.exe | executable | |
MD5:C5007A4BE4FF3AD83C3EF0A2DA757F37 | SHA256:A5D53A3ABF21210DC69833F3C11C09CCE0802024E1B175FF98EBBD03FD5AF308 | |||
| 7928 | OpenWith.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\iconcache_16.db | binary | |
MD5:419A089E66B9E18ADA06C459B000CB4D | SHA256:C48E42E9AB4E25B92C43A7B0416D463B9FF7C69541E4623A39513BC98085F424 | |||
| 7928 | OpenWith.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\iconcache_48.db | binary | |
MD5:AE6FBDED57F9F7D048B95468DDEE47CA | SHA256:D3C9D1FF7B54B653C6A1125CAC49F52070338A2DD271817BBA8853E99C0F33A9 | |||
| 7928 | OpenWith.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\iconcache_idx.db | binary | |
MD5:DAF4DCB2A146416085AFD2B6F03D1A96 | SHA256:64BF9B9D560F9EF06AC83D096C2351FA62FA6752175172EA25BEF92BA7146178 | |||
| 7928 | OpenWith.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\iconcache_sr.db | binary | |
MD5:379523B9F5D5B954E719B664846DBF8F | SHA256:3C9002CAEDF0C007134A7E632C72588945A4892B6D7AD3977224A6A5A7457BF4 | |||
| 7928 | OpenWith.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\iconcache_2560.db | binary | |
MD5:2D84AD5CFDF57BD4E3656BCFD9A864EA | SHA256:D241584A3FD4A91976FAFD5EC427E88F6E60998954DEC39E388AF88316AF3552 | |||
| 7928 | OpenWith.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\iconcache_768.db | binary | |
MD5:D192F7C343602D02E3E020807707006E | SHA256:BB4D233C90BDBEE6EF83E40BFF1149EA884EFA790B3BEF496164DF6F90297C48 | |||
| 5444 | javaw.exe | C:\Users\admin\AppData\Local\Temp\tmp6777485167403702933.txt | text | |
MD5:F416CE743D070D6AFFDFED9463F1087E | SHA256:400CD5073FCD4C55E56B89BDB673AF4DDE0FEA27E12D5976F5D719AA9BEFE63F | |||
| 7928 | OpenWith.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\iconcache_96.db | binary | |
MD5:2A8875D2AF46255DB8324AAD9687D0B7 | SHA256:54097CCCAE0CFCE5608466BA5A5CA2A3DFEAC536964EEC532540F3B837F5A7C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
59
DNS requests
19
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5232 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7424 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1372 | javaw.exe | GET | 200 | 185.114.73.121:8080 | http://185.114.73.121:8080/initPySystem | unknown | — | — | unknown |
540 | javaw.exe | GET | 200 | 185.114.73.121:8080 | http://185.114.73.121:8080/initPySystem | unknown | — | — | unknown |
7424 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6660 | javaw.exe | GET | 200 | 185.114.73.121:8080 | http://185.114.73.121:8080/initPySystem | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1764 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4360 | SearchApp.exe | 92.123.104.11:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5232 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
s3.timeweb.cloud |
| unknown |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1372 | javaw.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] DiabloNet Initial Client Packet (TCP) |
6660 | javaw.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] DiabloNet Initial Client Packet (TCP) |
540 | javaw.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] DiabloNet Initial Client Packet (TCP) |