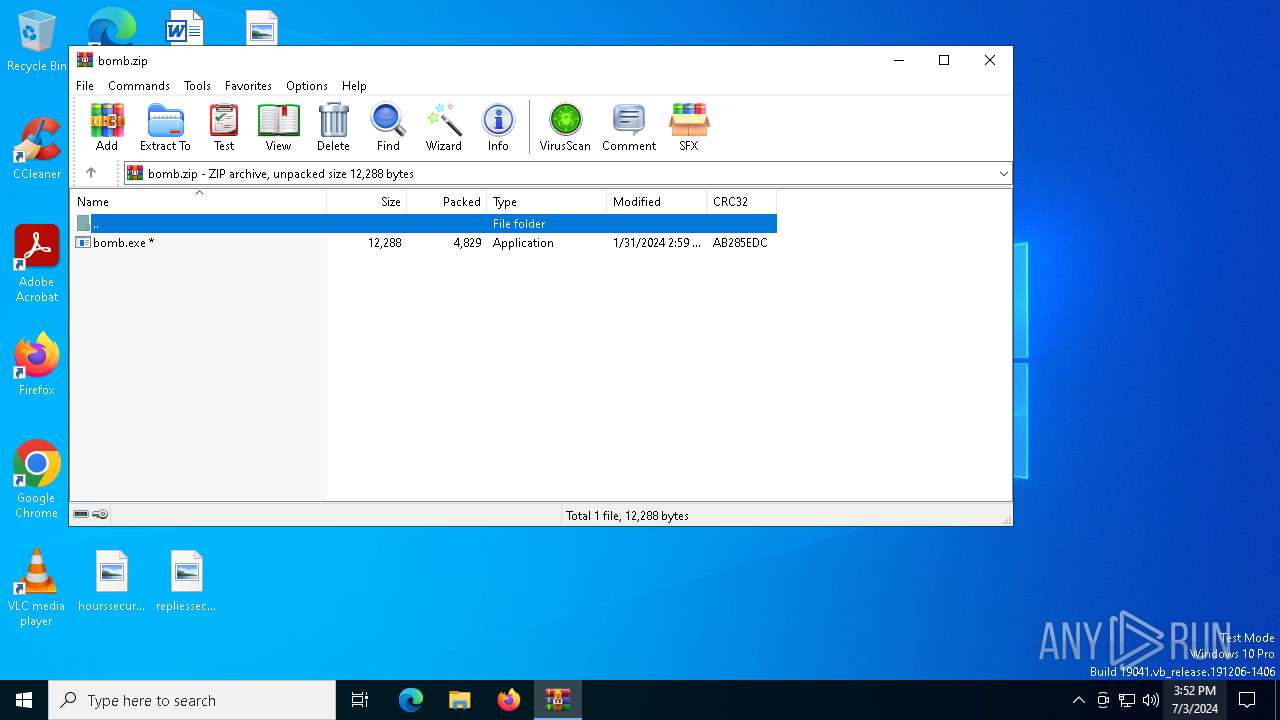
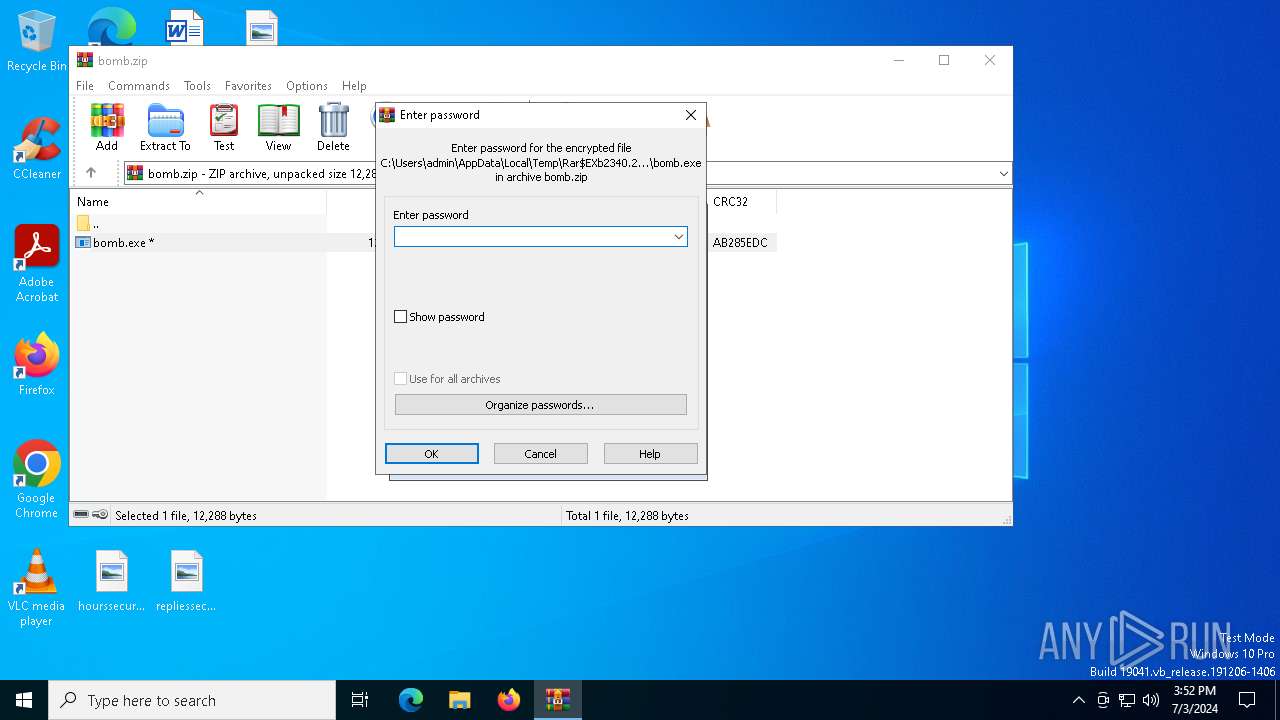
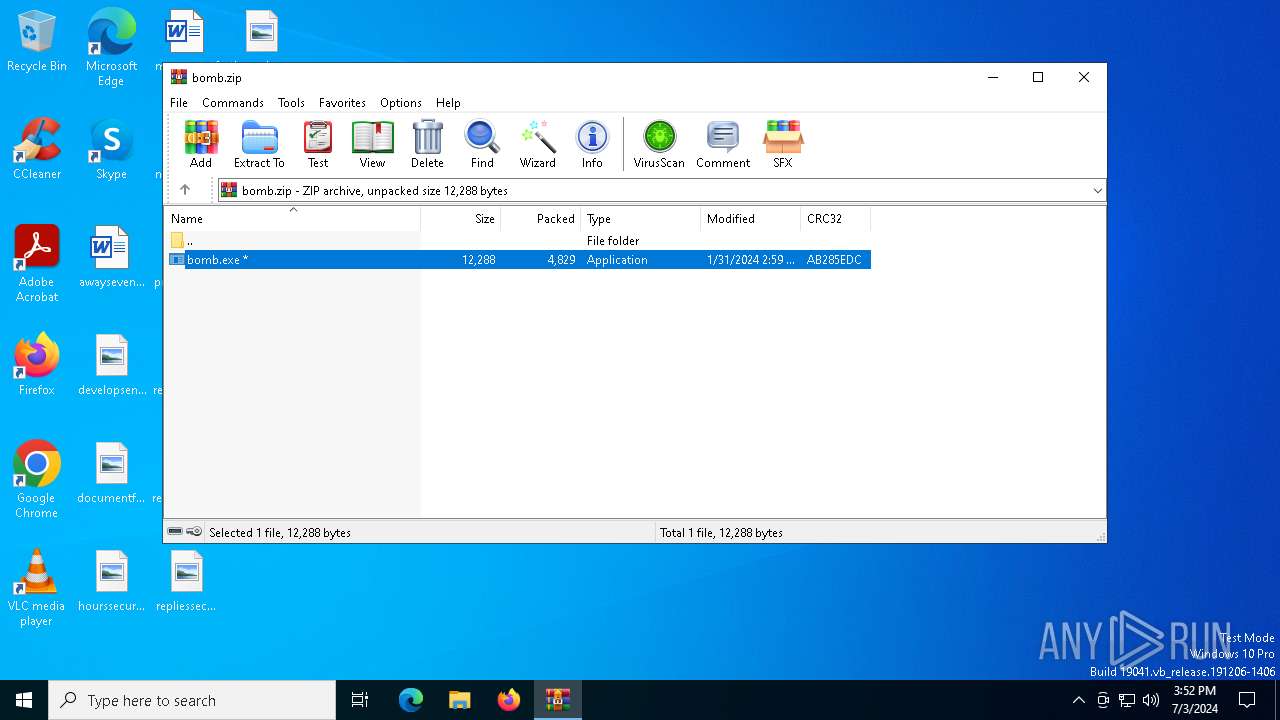
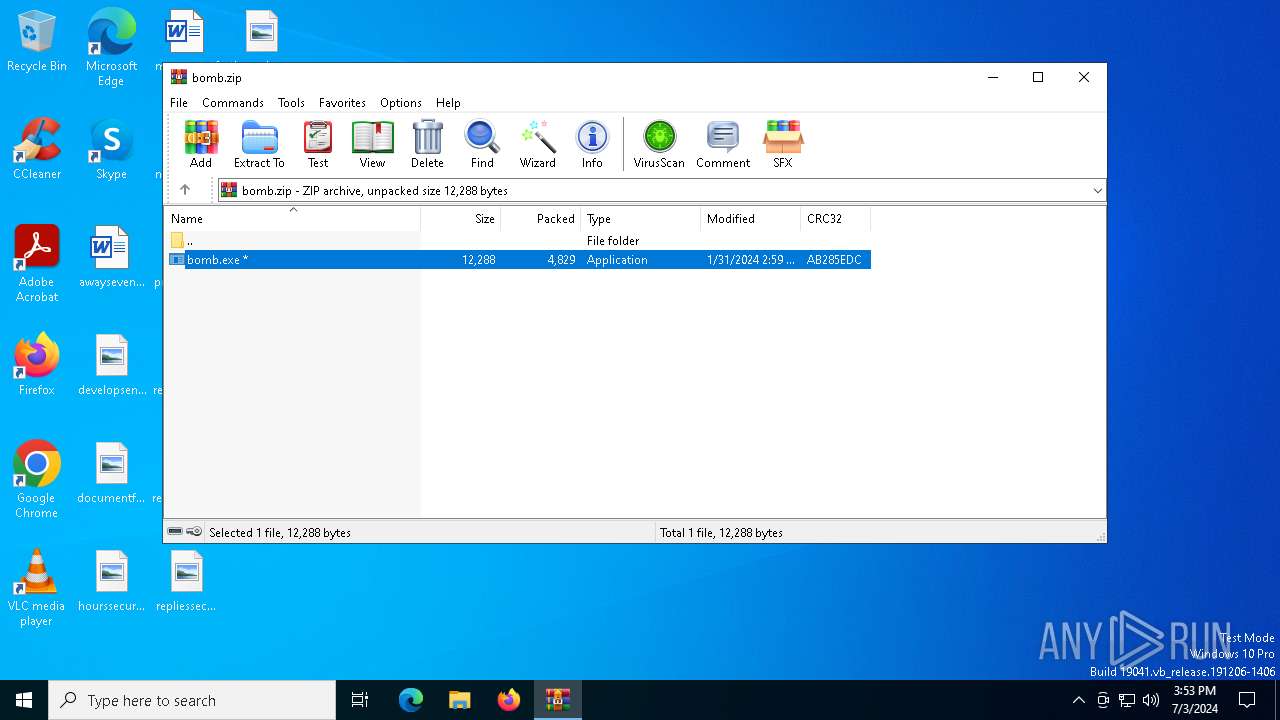
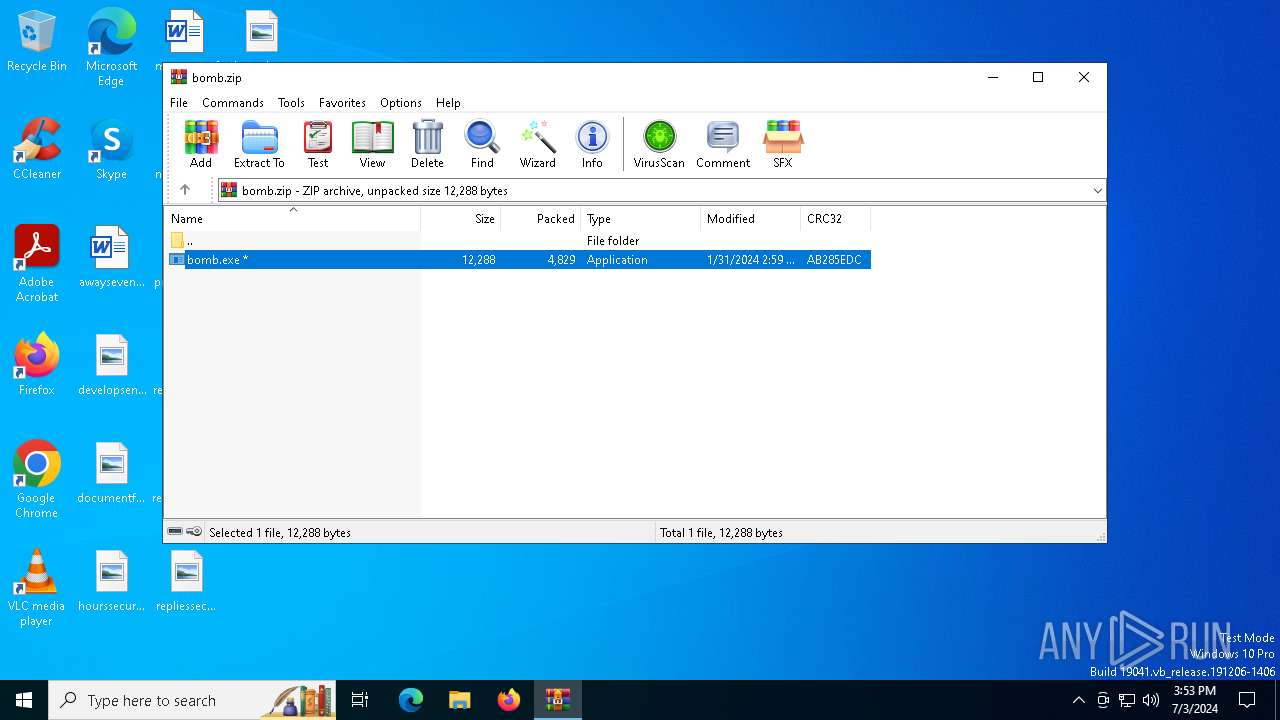
| File name: | bomb.zip |
| Full analysis: | https://app.any.run/tasks/71807ba9-49fa-4b3f-b4ee-ade52978b55c |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | July 03, 2024, 15:52:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 4D9BD8DAFB8299D0FC3FC98F8B8C27D4 |
| SHA1: | F3B375208D793E65FAABFD237C5391B49F381908 |
| SHA256: | 94936FB4C7BED2E7233FADE7980425B0300451D76A7AC9329C604886E2A9A013 |
| SSDEEP: | 192:aEuBYvQPc0QskFQBTPwR8Ac4Q7SbFL8H/Pj3UhrMj:aEznFcTPwRVASbVYXj/j |
MALICIOUS
Drops the executable file immediately after the start
- bomb.exe (PID: 2916)
- httptwizt.netnewtpp.exe.exe (PID: 6652)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- http185.215.113.66pei.exe.exe (PID: 2272)
- Hkbsse.exe (PID: 6504)
- 1385825516.exe (PID: 5300)
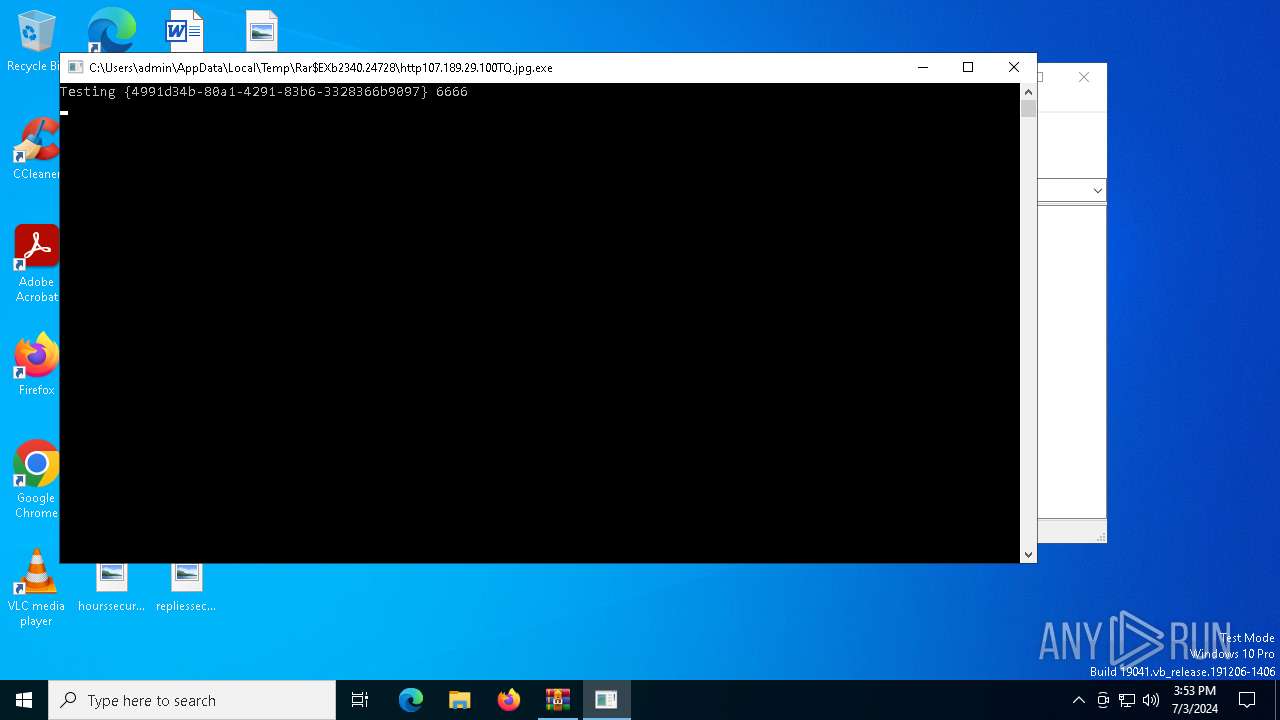
- http107.189.29.100TQ.jpg.exe (PID: 3152)
- http94.228.166.74wp-includespoop.exe.exe (PID: 1920)
- 1100632059.exe (PID: 1724)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
Changes the autorun value in the registry
- httptwizt.netnewtpp.exe.exe (PID: 6652)
Changes Security Center notification settings
- sysmablsvr.exe (PID: 7024)
Amadey has been detected
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- Hkbsse.exe (PID: 6504)
- Hkbsse.exe (PID: 1052)
Changes the Windows auto-update feature
- sysmablsvr.exe (PID: 7024)
Changes appearance of the Explorer extensions
- sysmablsvr.exe (PID: 7024)
Connects to the CnC server
- Hkbsse.exe (PID: 6504)
- sysmablsvr.exe (PID: 7024)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 7040)
- 1100632059.exe (PID: 1724)
- RegAsm.exe (PID: 6932)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- http94.228.166.74wp-includespoop.exe.exe (PID: 1920)
Starts Visual C# compiler
- http172.245.135.155T0207Wcsrss.exe.exe (PID: 700)
- http185.96.166.113Project1.exe.exe (PID: 6712)
REMCOS has been detected
- csc.exe (PID: 2860)
- csc.exe (PID: 6924)
- csc.exe (PID: 6924)
AMADEY has been detected (SURICATA)
- Hkbsse.exe (PID: 6504)
Runs injected code in another process
- 1.exe (PID: 4764)
Application was injected by another process
- explorer.exe (PID: 4612)
REMCOS has been detected (SURICATA)
- csc.exe (PID: 6924)
- csc.exe (PID: 2860)
STEALC has been detected (SURICATA)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
Steals credentials from Web Browsers
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
DCRAT has been detected (YARA)
- bomb.exe (PID: 2916)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2340)
- bomb.exe (PID: 2916)
- http185.215.113.66pei.exe.exe (PID: 2272)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- Hkbsse.exe (PID: 6504)
- sysmablsvr.exe (PID: 7024)
- 1385825516.exe (PID: 5300)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- 441019944.exe (PID: 1852)
- csc.exe (PID: 6924)
- csc.exe (PID: 2860)
- httpsp3c0der.github.iodfvfddfvrealtekdriver.exe.exe (PID: 6260)
- http77.221.157.163systemd.exe.exe (PID: 6756)
Executable content was dropped or overwritten
- bomb.exe (PID: 2916)
- httptwizt.netnewtpp.exe.exe (PID: 6652)
- http185.215.113.66pei.exe.exe (PID: 2272)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- Hkbsse.exe (PID: 6504)
- 1385825516.exe (PID: 5300)
- http107.189.29.100TQ.jpg.exe (PID: 3152)
- http94.228.166.74wp-includespoop.exe.exe (PID: 1920)
- 1100632059.exe (PID: 1724)
Reads the date of Windows installation
- bomb.exe (PID: 2916)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- Hkbsse.exe (PID: 6504)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- httpsp3c0der.github.iodfvfddfvrealtekdriver.exe.exe (PID: 6260)
Starts itself from another location
- httptwizt.netnewtpp.exe.exe (PID: 6652)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
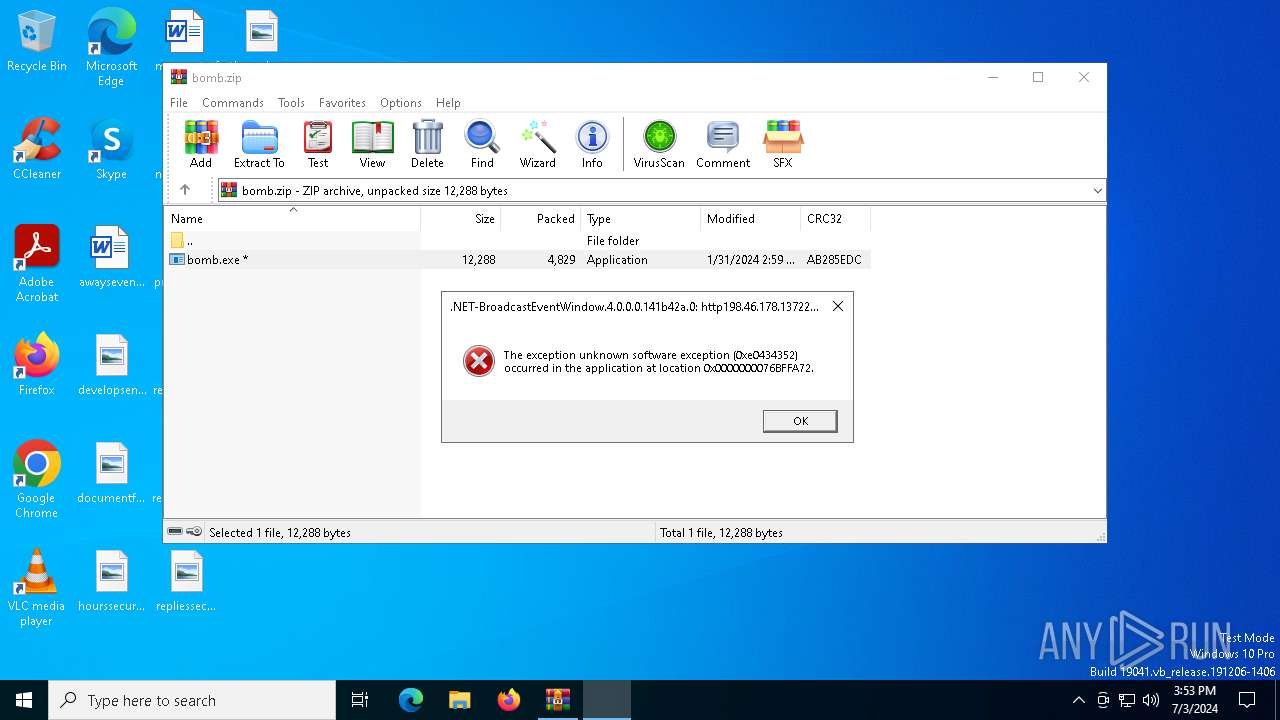
Executes application which crashes
- httpsp3c0der.github.ioeeecrypted.exe.exe (PID: 6684)
- http172.245.135.155T0207Wcsrss.exe.exe (PID: 700)
- http77.105.132.27lumma0207.exe.exe (PID: 3800)
- http198.46.178.13722033igccu.exe.exe (PID: 5460)
Potential Corporate Privacy Violation
- bomb.exe (PID: 2916)
- http185.215.113.66pei.exe.exe (PID: 2272)
- Hkbsse.exe (PID: 6504)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- 1385825516.exe (PID: 5300)
The process creates files with name similar to system file names
- bomb.exe (PID: 2916)
Checks Windows Trust Settings
- Hkbsse.exe (PID: 6504)
- http77.221.157.163systemd.exe.exe (PID: 6756)
Searches for installed software
- RegAsm.exe (PID: 7040)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- RegAsm.exe (PID: 6932)
Connects to the server without a host name
- Hkbsse.exe (PID: 6504)
- sysmablsvr.exe (PID: 7024)
- bomb.exe (PID: 2916)
- 1385825516.exe (PID: 5300)
- http185.96.166.113Project1.exe.exe (PID: 6712)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
Process drops legitimate windows executable
- bomb.exe (PID: 2916)
Process requests binary or script from the Internet
- 1385825516.exe (PID: 5300)
- bomb.exe (PID: 2916)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- Hkbsse.exe (PID: 6504)
Starts a Microsoft application from unusual location
- http107.189.29.100wmi.jpg.exe (PID: 6492)
Connects to unusual port
- http77.91.77.81lendnewlogs.exe.exe (PID: 2120)
- csc.exe (PID: 2860)
- csc.exe (PID: 6924)
- bomb.exe (PID: 2916)
- sysmablsvr.exe (PID: 7024)
The process executes via Task Scheduler
- Hkbsse.exe (PID: 1052)
Windows Defender mutex has been found
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 6924)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- csc.exe (PID: 2860)
Checks for external IP
- csc.exe (PID: 6924)
- csc.exe (PID: 2860)
Starts CMD.EXE for commands execution
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- httpsp3c0der.github.iodfvfddfvrealtekdriver.exe.exe (PID: 6260)
INFO
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2340)
Reads the machine GUID from the registry
- bomb.exe (PID: 2916)
- http77.91.77.81lendnewlogs.exe.exe (PID: 2120)
- Hkbsse.exe (PID: 6504)
- httpsp3c0der.github.iodfvfddfvrealtekdriver.exe.exe (PID: 6260)
- http172.245.135.155T0207Wcsrss.exe.exe (PID: 700)
- csc.exe (PID: 6924)
- http198.46.178.13722033igccu.exe.exe (PID: 5460)
- csc.exe (PID: 2860)
- http107.189.29.100TQ.jpg.exe (PID: 3152)
- SearchApp.exe (PID: 7888)
- http77.221.157.163systemd.exe.exe (PID: 6756)
- sysmablsvr.exe (PID: 7024)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2340)
Checks supported languages
- bomb.exe (PID: 2916)
- http185.215.113.66pei.exe.exe (PID: 2272)
- httptwizt.netnewtpp.exe.exe (PID: 6652)
- sysmablsvr.exe (PID: 7024)
- httpsp3c0der.github.ioeeecrypted.exe.exe (PID: 6684)
- RegAsm.exe (PID: 7040)
- 1722027313.exe (PID: 2452)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- http77.91.77.81lendnewlogs.exe.exe (PID: 2120)
- Hkbsse.exe (PID: 6504)
- 1385825516.exe (PID: 5300)
- httpsp3c0der.github.iodfvfddfvrealtekdriver.exe.exe (PID: 6260)
- http77.221.157.163systemd.exe.exe (PID: 6756)
- 1.exe (PID: 4764)
- http172.245.135.155T0207Wcsrss.exe.exe (PID: 700)
- 1100632059.exe (PID: 1724)
- http107.189.29.100wmi.jpg.exe (PID: 6492)
- http185.96.166.113Project1.exe.exe (PID: 6712)
- csc.exe (PID: 2860)
- 441019944.exe (PID: 1852)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- csc.exe (PID: 6924)
- Hkbsse.exe (PID: 1052)
- http198.46.178.13722033igccu.exe.exe (PID: 5460)
- http77.105.132.27lumma0207.exe.exe (PID: 3800)
- http94.228.166.74wp-includespoop.exe.exe (PID: 1920)
- http107.189.29.100TQ.jpg.exe (PID: 3152)
- RegAsm.exe (PID: 6932)
- MS19.exe (PID: 1908)
- SearchApp.exe (PID: 7888)
Create files in a temporary directory
- bomb.exe (PID: 2916)
- http185.215.113.66pei.exe.exe (PID: 2272)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- Hkbsse.exe (PID: 6504)
- sysmablsvr.exe (PID: 7024)
- 1385825516.exe (PID: 5300)
- 441019944.exe (PID: 1852)
- http107.189.29.100TQ.jpg.exe (PID: 3152)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4612)
Reads the computer name
- bomb.exe (PID: 2916)
- http185.215.113.66pei.exe.exe (PID: 2272)
- RegAsm.exe (PID: 7040)
- http77.91.77.81lendnewlogs.exe.exe (PID: 2120)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- Hkbsse.exe (PID: 6504)
- sysmablsvr.exe (PID: 7024)
- httpsp3c0der.github.iodfvfddfvrealtekdriver.exe.exe (PID: 6260)
- 1385825516.exe (PID: 5300)
- http172.245.135.155T0207Wcsrss.exe.exe (PID: 700)
- http185.96.166.113Project1.exe.exe (PID: 6712)
- csc.exe (PID: 2860)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- csc.exe (PID: 6924)
- http198.46.178.13722033igccu.exe.exe (PID: 5460)
- 441019944.exe (PID: 1852)
- RegAsm.exe (PID: 6932)
- http94.228.166.74wp-includespoop.exe.exe (PID: 1920)
- http107.189.29.100TQ.jpg.exe (PID: 3152)
- MS19.exe (PID: 1908)
- SearchApp.exe (PID: 7888)
- http77.221.157.163systemd.exe.exe (PID: 6756)
Reads Environment values
- bomb.exe (PID: 2916)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- Hkbsse.exe (PID: 6504)
- csc.exe (PID: 2860)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- csc.exe (PID: 6924)
- SearchApp.exe (PID: 7888)
Reads the software policy settings
- bomb.exe (PID: 2916)
- RegAsm.exe (PID: 7040)
- Hkbsse.exe (PID: 6504)
- WerFault.exe (PID: 1220)
- WerFault.exe (PID: 2556)
- RegAsm.exe (PID: 6932)
- WerFault.exe (PID: 780)
- SearchApp.exe (PID: 7888)
- http77.221.157.163systemd.exe.exe (PID: 6756)
Disables trace logs
- bomb.exe (PID: 2916)
Checks proxy server information
- bomb.exe (PID: 2916)
- http185.215.113.66pei.exe.exe (PID: 2272)
- Hkbsse.exe (PID: 6504)
- sysmablsvr.exe (PID: 7024)
- WerFault.exe (PID: 1220)
- 1385825516.exe (PID: 5300)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- WerFault.exe (PID: 2556)
- 441019944.exe (PID: 1852)
- csc.exe (PID: 6924)
- WerFault.exe (PID: 780)
- csc.exe (PID: 2860)
- SearchApp.exe (PID: 7888)
- explorer.exe (PID: 4612)
- http77.221.157.163systemd.exe.exe (PID: 6756)
Process checks computer location settings
- bomb.exe (PID: 2916)
- Hkbsse.exe (PID: 6504)
- http185.172.128.116Freshbuild.exe.exe (PID: 2196)
- SearchApp.exe (PID: 7888)
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
- httpsp3c0der.github.iodfvfddfvrealtekdriver.exe.exe (PID: 6260)
Creates files or folders in the user directory
- http185.215.113.66pei.exe.exe (PID: 2272)
- sysmablsvr.exe (PID: 7024)
- Hkbsse.exe (PID: 6504)
- WerFault.exe (PID: 1220)
- 1385825516.exe (PID: 5300)
- csc.exe (PID: 6924)
- csc.exe (PID: 2860)
Reads product name
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
Reads CPU info
- http77.91.77.80chupaleva.exe.exe (PID: 4148)
Process checks Internet Explorer phishing filters
- SearchApp.exe (PID: 7888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(2916) bomb.exe
C2 (2)http://senten.org/forum/index.php
http://77.91.77.81/Kiru9gu/index.php
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:01:30 21:59:18 |
| ZipCRC: | 0xab285edc |
| ZipCompressedSize: | 4829 |
| ZipUncompressedSize: | 12288 |
| ZipFileName: | bomb.exe |
Total processes
189
Monitored processes
46
Malicious processes
21
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\http172.245.135.155T0207Wcsrss.exe.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\http172.245.135.155T0207Wcsrss.exe.exe | bomb.exe | ||||||||||||
User: admin Company: Ugawomavufamed Integrity Level: MEDIUM Description: Uwutejapa Ejutatohumaza Itadocucayuyexiq Orerobumofe Asezikepi. Exit code: 3221226356 Version: 9.8.924.32 Modules
| |||||||||||||||
| 780 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3800 -s 280 | C:\Windows\SysWOW64\WerFault.exe | http77.105.132.27lumma0207.exe.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | "C:\Users\admin\AppData\Local\Temp\b66a8ae076\Hkbsse.exe" | C:\Users\admin\AppData\Local\Temp\b66a8ae076\Hkbsse.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1188 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_wp.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet_wp.exe | — | http172.245.135.155T0207Wcsrss.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: aspnet_wp.exe Version: 4.8.9220.0 built by: NET481REL1LAST_C | |||||||||||||||
| 1220 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6684 -s 348 | C:\Windows\SysWOW64\WerFault.exe | httpsp3c0der.github.ioeeecrypted.exe.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1724 | C:\Users\admin\AppData\Local\Temp\1100632059.exe | C:\Users\admin\AppData\Local\Temp\1100632059.exe | 1385825516.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1852 | C:\Users\admin\AppData\Local\Temp\441019944.exe | C:\Users\admin\AppData\Local\Temp\441019944.exe | sysmablsvr.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1908 | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\MS19.exe -l 6666 -p C:\ProgramData\MSSQLH.exe -t * | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\MS19.exe | — | http107.189.29.100TQ.jpg.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\http94.228.166.74wp-includespoop.exe.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\http94.228.166.74wp-includespoop.exe.exe | bomb.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\http77.91.77.81lendnewlogs.exe.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\http77.91.77.81lendnewlogs.exe.exe | bomb.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: XHP Version: 12.9.1.22 Modules
| |||||||||||||||
Total events
60 935
Read events
60 692
Write events
238
Delete events
5
Modification events
| (PID) Process: | (4612) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F0062000000000000000000000001000000000000006D000000 | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\bomb.zip | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4612) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000090142 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456249F86704CD0354CAF53943DFF6B26B6 | |||
Executable files
35
Suspicious files
29
Text files
180
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | bomb.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\httpswww.dropbox.comsclfig9av2b7ibnmc0tek3bxakZharkBOT.exerlkey=ayd8sr8hdnhxxjtycgn8le9sc&st=278idrdg&dl=1.exe | html | |
MD5:CDA96A30D26C7F82F7D787904B7E0870 | SHA256:AB449E22857DA2D1EEF6C0F4BC0643126DCB06BF8383BECACD7481A0140BBFC1 | |||
| 2340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\bomb.exe | executable | |
MD5:A14E63D27E1AC1DF185FA062103AA9AA | SHA256:DDA39F19837168845DE33959DE34BCFB7EE7F3A29AE55C9FA7F4CB12CB27F453 | |||
| 2916 | bomb.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\httpswww.dropbox.comsclfig9av2b7ibnmc0tek3bxakZharkBOT.exerlkey=ayd8sr8hdnhxxjtycgn8le9sc&st=24za4j29&dl=1.exe | html | |
MD5:A67D615E593A2082956A5FF3005E00DE | SHA256:EA747D234735C2A5E0501525DFF7A405F6EAD14EB2FDEDC061201AAD0F887095 | |||
| 2916 | bomb.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\http185.215.113.66pei.exe.exe | executable | |
MD5:8D8E6C7952A9DC7C0C73911C4DBC5518 | SHA256:FEB4C3AE4566F0ACBB9E0F55417B61FEFD89DC50A4E684DF780813FB01D61278 | |||
| 2916 | bomb.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\http185.172.128.116Freshbuild.exe.exe | executable | |
MD5:07101CAC5B9477BA636CD8CA7B9932CB | SHA256:488385CD54D14790B03FA7C7DC997EBEA3F7B2A8499E5927EB437A3791102A77 | |||
| 2916 | bomb.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2340.24728\httpssolutionhub.ccdownloadZharkBOT.exe.exe | html | |
MD5:587A2CCC82B568A86A19114CBB4D0BC1 | SHA256:2FC269B030A1ABE7C12CFF94EE380D24C10DD03EB92A0A588212BE938C81A21F | |||
| 1220 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER7583.tmp.xml | xml | |
MD5:7E94B6716885B9B35C3DD04711ECA026 | SHA256:85F613AECEEF36440005CB97D7C9C39AB0CBDB8DAA221AF038D3CA9269DB2C38 | |||
| 2196 | http185.172.128.116Freshbuild.exe.exe | C:\WINDOWS\Tasks\Hkbsse.job | binary | |
MD5:188A4BCC834FF0A4BC57D1D1324F7695 | SHA256:F0EF31AF6C319E4D1A29D4146E7C9192B540A09670D4113F178662EB63E7E122 | |||
| 1220 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_httpsp3c0der.git_d88d4c203a183319bfcea27fa9d7c2736dc79e8b_7a7e199e_e4e3a1d7-c6a8-4820-a9e3-fc1ea9f194a6\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1220 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER7467.tmp.dmp | dmp | |
MD5:C3FE985562755A1F0370AF7BAAADA9AE | SHA256:D302F876E35BCAFF02B1BF44F5A07585B37AC0AB99BEE5C5DA8BEA53E333BDB9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
82
TCP/UDP connections
223
DNS requests
48
Threats
156
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6064 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
5184 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
2916 | bomb.exe | GET | 200 | 185.215.113.66:80 | http://185.215.113.66/pei.exe | unknown | — | — | unknown |
2916 | bomb.exe | GET | 200 | 185.215.113.66:80 | http://twizt.net/newtpp.exe | unknown | — | — | unknown |
6200 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
2916 | bomb.exe | GET | 200 | 172.245.135.155:80 | http://172.245.135.155/T0207W/csrss.exe | unknown | — | — | unknown |
2916 | bomb.exe | GET | 200 | 77.91.77.81:80 | http://77.91.77.81/lend/newbuild.exe | unknown | — | — | unknown |
2916 | bomb.exe | GET | 403 | 141.8.194.149:80 | http://a1000750.xsph.ru/img/pic3.jpg | unknown | — | — | unknown |
6440 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6440 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6064 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6064 | svchost.exe | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
2204 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1060 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
188 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3040 | OfficeClickToRun.exe | 52.111.236.21:443 | nexusrules.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
twizt.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | svchost.exe | Misc activity | ET INFO Observed DNS Query to xsph .ru Domain |
2916 | bomb.exe | Potentially Bad Traffic | ET HUNTING Suspicious csrss.exe in URI |
2916 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2916 | bomb.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2916 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2916 | bomb.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2916 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2916 | bomb.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
2916 | bomb.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2916 | bomb.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
17 ETPRO signatures available at the full report