| File name: | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30 |
| Full analysis: | https://app.any.run/tasks/4b795fd4-28b6-42e7-9e39-e89fddcdff85 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 10, 2025, 03:06:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 30833F0632F3EE8531CEDDC3A8992342 |
| SHA1: | A834D486A6BD89B229EFC44D7A13F0E04D8FC287 |
| SHA256: | 94504751F5C82674DEE1B25F9729AB7E94646376ADFE98CC7F1C1508A75E0A30 |
| SSDEEP: | 49152:gV31g5xcYlY/tdTazlXwBtWwTXf3on/KwVFjcn21QQDzvX8HGz7Cb51mG:gHgStMtwHLTXfYSwVF11rUi7CWG |
MALICIOUS
Steals credentials from Web Browsers
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
Executing a file with an untrusted certificate
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
Actions looks like stealing of personal data
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
AGENTTESLA has been detected (SURICATA)
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
AGENTTESLA has been detected (YARA)
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
SUSPICIOUS
Executable content was dropped or overwritten
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
Reads security settings of Internet Explorer
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
Connects to the server without a host name
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
Malware-specific behavior (creating "System.dll" in Temp)
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
There is functionality for taking screenshot (YARA)
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
Checks for external IP
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
- svchost.exe (PID: 2196)
Connects to SMTP port
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
Contacting a server suspected of hosting an CnC
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
Application launched itself
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
The process creates files with name similar to system file names
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
INFO
Checks supported languages
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
The sample compiled with english language support
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
Checks proxy server information
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
- slui.exe (PID: 7852)
Reads the computer name
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
Disables trace logs
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
Creates files or folders in the user directory
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
Reads the software policy settings
- slui.exe (PID: 7852)
Reads the machine GUID from the registry
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7456)
Create files in a temporary directory
- 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe (PID: 7344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(7456) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe
Protocolsmtp
Hostmail.rvoccte.com
Port587
Usernamenewfile@rvoccte.com
PasswordPJtiky;+*ayY
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 21:50:48+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x344a |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.0.0 |
| ProductVersionNumber: | 3.5.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | betlerne forargelsers |
| FileDescription: | underprikningen sceniske |
| InternalName: | kavalkades.exe |
| LegalCopyright: | tidsskriftsamlingens |
| ProductName: | uskadeliggjorte folkepartier |
| ProductVersion: | 3.5.0.0 |
Total processes
125
Monitored processes
4
Malicious processes
2
Suspicious processes
0
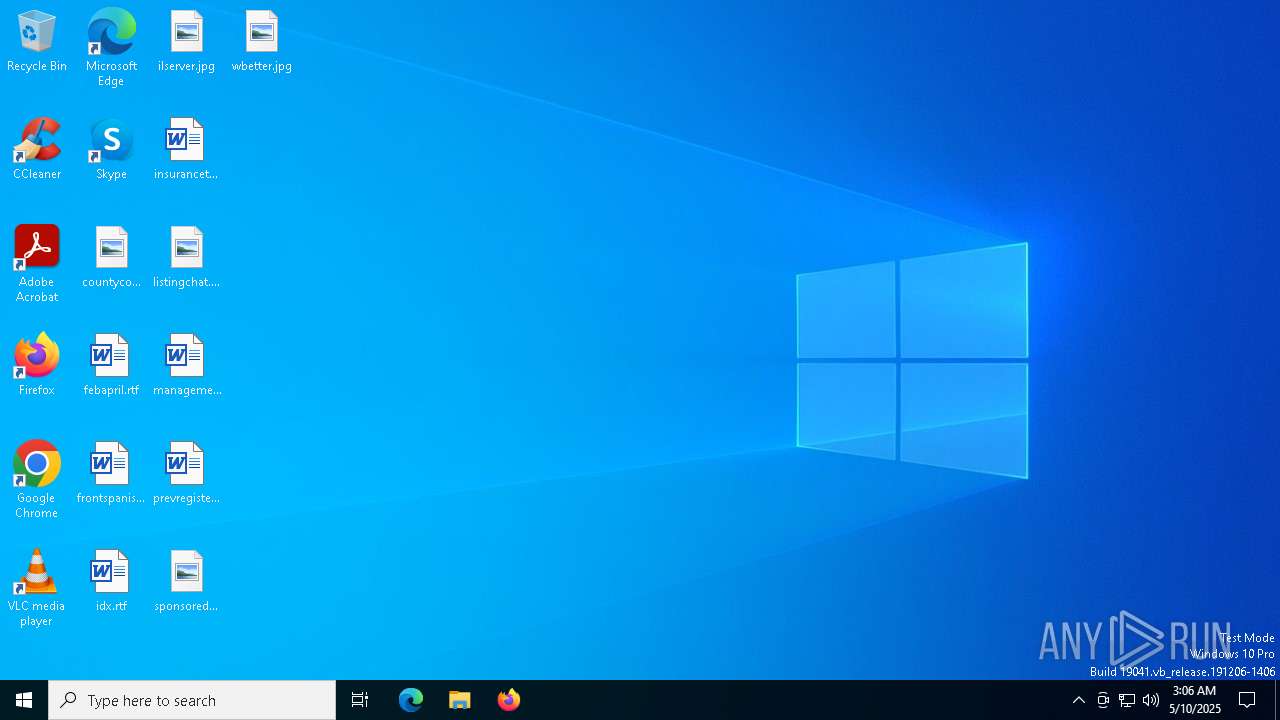
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7344 | "C:\Users\admin\AppData\Local\Temp\94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe" | C:\Users\admin\AppData\Local\Temp\94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: underprikningen sceniske Exit code: 0 Modules
| |||||||||||||||
| 7456 | "C:\Users\admin\AppData\Local\Temp\94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe" | C:\Users\admin\AppData\Local\Temp\94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: underprikningen sceniske Modules
AgentTesla(PID) Process(7456) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe Protocolsmtp Hostmail.rvoccte.com Port587 Usernamenewfile@rvoccte.com PasswordPJtiky;+*ayY | |||||||||||||||
| 7852 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 446
Read events
1 980
Write events
466
Delete events
0
Modification events
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: u | |||
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\bolette\rabbitries\Nonreduction |
| Operation: | write | Name: | sammensnrer |
Value: 8155 | |||
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: us | |||
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: use | |||
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user | |||
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user3 | |||
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32 | |||
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32: | |||
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32:: | |||
| (PID) Process: | (7344) 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Locales Approx |
| Operation: | write | Name: | C Langs |
Value: user32::S | |||
Executable files
1
Suspicious files
5
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\Floatability234\Maltfabrikkens\Girted\Nonhistoricalness49.jpg | image | |
MD5:14BE28BB5C554627B928D87A10767E52 | SHA256:D27084ADA390FF9057ACCADAFB0DA002A9634684A58A1C3CC600CCA4F39E192F | |||
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\nsoDA55.tmp | — | |
MD5:— | SHA256:— | |||
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\Floatability234\Maltfabrikkens\Girted\Audient.Uni | binary | |
MD5:F6E4FE4FA1D2894C1CB86A703C281016 | SHA256:63A74CF7362DAC4A5A464A71E00BB39F4C36C6439EF879537B944CDEA45AE489 | |||
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\Floatability234\Maltfabrikkens\Maltreatment\slagvolumeners\aakirkebyboen.ini | text | |
MD5:3CD2895E391C9512F262364428DCA749 | SHA256:F87F5C7937F3D8591A5B4DE2348AEE3C6A9E894C0D34A233F30B2E3658D56F43 | |||
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\Floatability234\Maltfabrikkens\Girted\Cafeteriaejerne163.udg | binary | |
MD5:3CBA4D64B2824C589FC5F582F927CEA6 | SHA256:8FEF897764629FCFED511E1728A52BBD21F4CE1CB42E5D2F840F0E1CE23B64BC | |||
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\Floatability234\Maltfabrikkens\Maltreatment\slagvolumeners\afsnitsnummerering.sti | binary | |
MD5:AB0BC3BCD617A7C5C35064CEADCB2D49 | SHA256:437A887DD29CB7C3654A2C4672F303FAA7A16DC03C71EFC367B8BD7BE7CD4CD7 | |||
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\Floatability234\Maltfabrikkens\Maltreatment\Rosvrdigst69.txt | text | |
MD5:1DCB756BC971269FC0636CADF4BEEC90 | SHA256:545BDCDA80DA5CAF14B2454448C4E9657A427D0313B600AA9DC3D1DBE5F8C942 | |||
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\Floatability234\Maltfabrikkens\Girted\Hamburgerryg140.ini | text | |
MD5:31ADB5B51F043396F300C551162610DE | SHA256:58DDF806A779D025EE5536D04031A4B54B1D38DB207B90822B1AD9A6CEBE6025 | |||
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\Floatability234\Maltfabrikkens\Girted\Presumedly147.fly | binary | |
MD5:6B6917A293B806150C17787C1E718FE6 | SHA256:74BBBF0D4DE1D445A2F4A099DB217E245E2A6997DBBE3F8FA7468E63BE64D86C | |||
| 7344 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | C:\Users\admin\AppData\Local\Temp\Floatability234\Maltfabrikkens\Girted\Obliquenesses.ini | text | |
MD5:385993D3A40ABD1835C34168E4CE5697 | SHA256:876B36A02E99994C314C68481A53A4315C2DC35825452804FF928D71627DFE9E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
24
DNS requests
16
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.2.24:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7592 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7592 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7456 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
7456 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | GET | 200 | 192.3.176.134:80 | http://192.3.176.134/zZhMVUfbRgMs102.bin | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.2.24:80 | crl.microsoft.com | Akamai International B.V. | CZ | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7592 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7592 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7456 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | 192.3.176.134:80 | — | AS-COLOCROSSING | US | unknown |
7592 | SIHClient.exe | 52.165.164.15:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
ip-api.com |
| whitelisted |
mail.rvoccte.com |
| malicious |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7456 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
7456 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
7456 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7456 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Misc activity | INFO [ANY.RUN] SMTP email client opens transfer with server (EHLO) |
7456 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | Malware Command and Control Activity Detected | ET MALWARE MSIL/Kryptik.XSY Data Exfil via SMTP |
7456 | 94504751f5c82674dee1b25f9729ab7e94646376adfe98cc7f1c1508a75e0a30.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration SMTP (Base64 encoded) |