| File name: | serverc.exe |
| Full analysis: | https://app.any.run/tasks/9c550af2-3309-420a-b064-34ee884b4771 |
| Verdict: | Malicious activity |
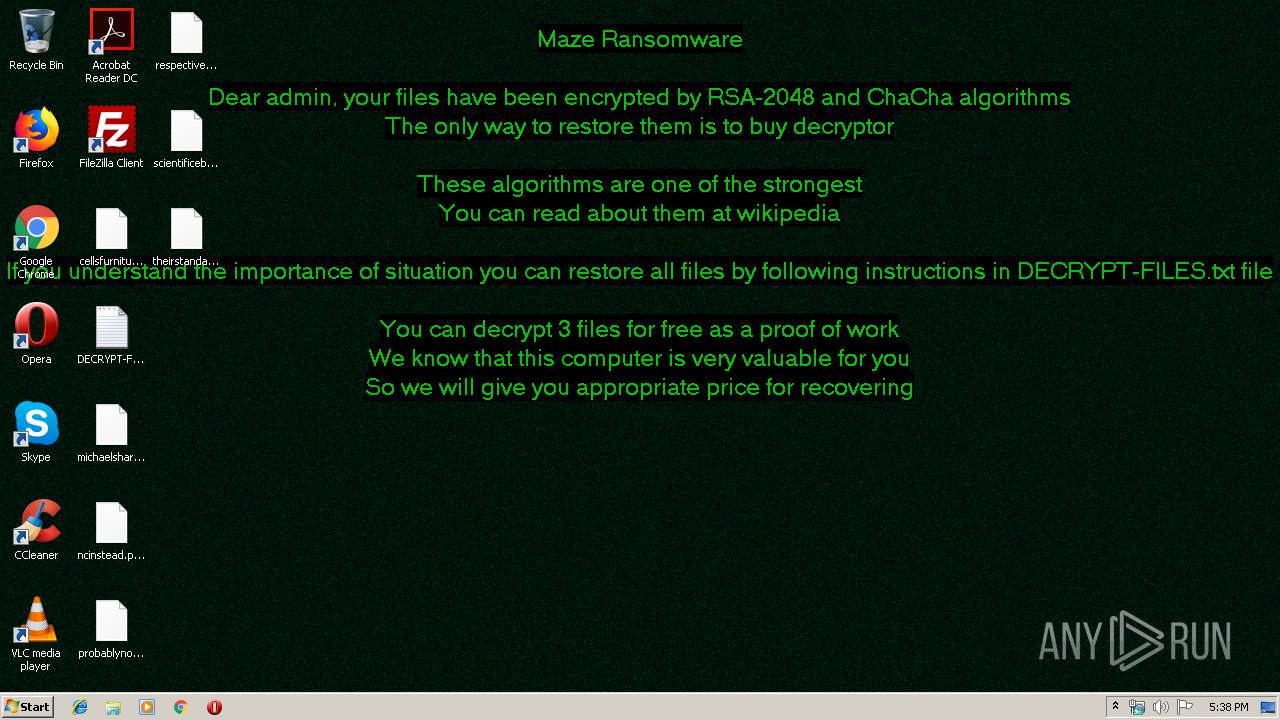
| Threats: | Maze is ransomware — a malware type that encrypts the victim’s files and restores the data in exchange for a ransom payment. One of the most distinguishable features of Maze is that it is one of the first malware of the kind to publicly release stolen data. |
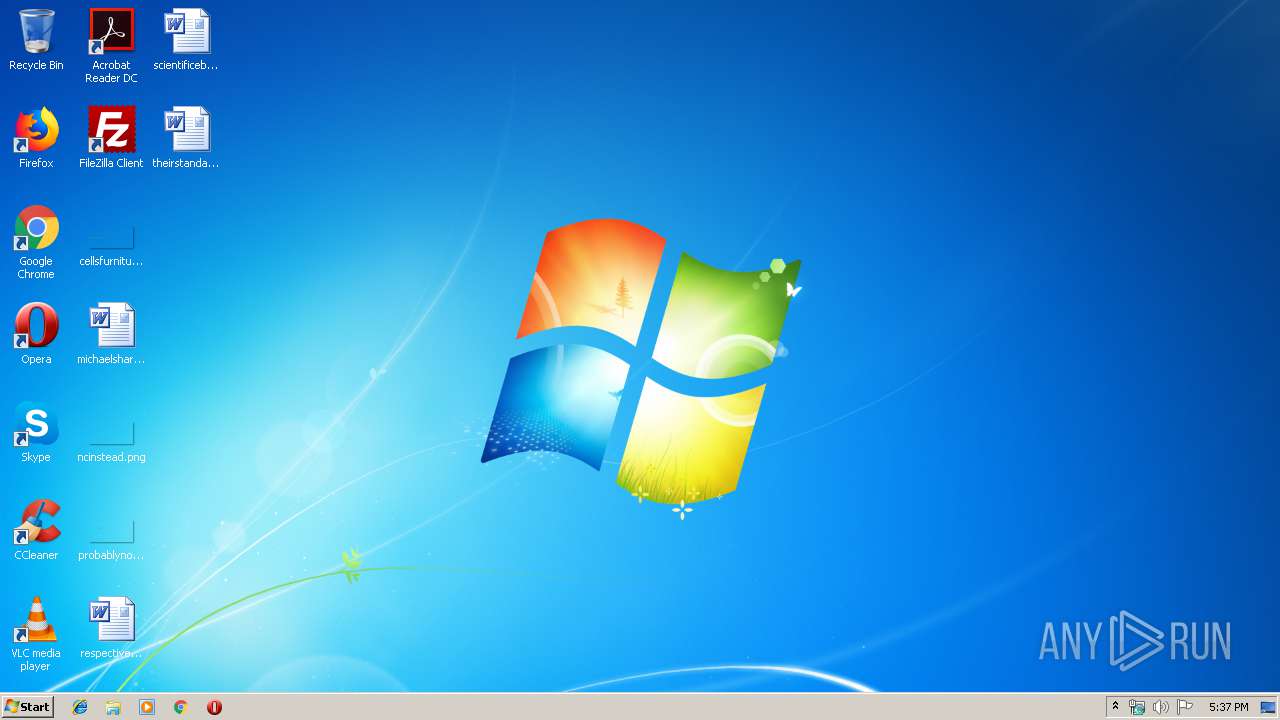
| Analysis date: | January 17, 2020, 17:37:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BCE024435A835ECF083279ABB845C352 |
| SHA1: | 52C7472F02198BF7F5E49A571FB81FBB66A2F79B |
| SHA256: | 943CAD70A3ACEED1D56F2BE794CFE9CDA6414212DE3EDF84D7D4A92D3C68AC85 |
| SSDEEP: | 12288:SrPN7SUmCePrBeyZ1doI0QQk1C1XmNr78QPzIdbT+a:EeFBFdoIok1Sc8+a |
MALICIOUS
Deletes shadow copies
- serverc.exe (PID: 2720)
Actions looks like stealing of personal data
- serverc.exe (PID: 2720)
Writes to a start menu file
- serverc.exe (PID: 2720)
Writes file to Word startup folder
- serverc.exe (PID: 2720)
Renames files like Ransomware
- serverc.exe (PID: 2720)
Connects to CnC server
- serverc.exe (PID: 2720)
MAZE was detected
- serverc.exe (PID: 2720)
Dropped file may contain instructions of ransomware
- serverc.exe (PID: 2720)
SUSPICIOUS
Creates files in the program directory
- serverc.exe (PID: 2720)
Creates files like Ransomware instruction
- serverc.exe (PID: 2720)
Reads the cookies of Mozilla Firefox
- serverc.exe (PID: 2720)
Creates files in the user directory
- serverc.exe (PID: 2720)
- wmic.exe (PID: 2428)
Connects to server without host name
- serverc.exe (PID: 2720)
INFO
Dropped object may contain TOR URL's
- serverc.exe (PID: 2720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:13 23:01:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 69120 |
| InitializedDataSize: | 706048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x685c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Unicode |
| CompanyName: | Kim Jong Un |
| FileDescription: | Coded by Gruja |
| FileVersion: | 1.0.0.1 |
| InternalName: | Fuck south korea |
| LegalCopyright: | Copyright (C) 2024 |
| OriginalFileName: | kim.exe |
| ProductName: | We love our Emperor, Kim Jong Un! |
| ProductVersion: | 1.0.0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jan-2020 22:01:35 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Kim Jong Un |
| FileDescription: | Coded by Gruja |
| FileVersion: | 1.0.0.1 |
| InternalName: | Fuck south korea |
| LegalCopyright: | Copyright (C) 2024 |
| OriginalFilename: | kim.exe |
| ProductName: | We love our Emperor, Kim Jong Un! |
| ProductVersion: | 1.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 13-Jan-2020 22:01:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00010D43 | 0x00010E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47444 |
.rdata | 0x00012000 | 0x00005312 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.61613 |
.data | 0x00018000 | 0x00002FC0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.4021 |
.rsrc | 0x0001B000 | 0x000A31B8 | 0x000A3200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.63332 |
.reloc | 0x000BF000 | 0x00000E84 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.25595 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0.87405 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 1.15103 | 38056 | UNKNOWN | English - United States | RT_ICON |
4 | 1.12509 | 21640 | UNKNOWN | English - United States | RT_ICON |
5 | 0.970284 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 1.24324 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 1.12297 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 1.36929 | 2440 | UNKNOWN | English - United States | RT_ICON |
9 | 1.20895 | 1128 | UNKNOWN | English - United States | RT_ICON |
101 | 5.99994 | 501720 | UNKNOWN | English - United States | RT_RCDATA |
Imports
KERNEL32.dll |
SHLWAPI.dll |
Total processes
40
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2264 | "C:\bb\onub\dvoo\..\..\..\Windows\fqrc\bot\..\..\system32\bkce\sdj\..\..\wbem\n\..\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | serverc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2428 | "C:\dfogr\wrkr\..\..\Windows\bb\wufv\dbi\..\..\..\system32\wxvb\rqk\..\..\wbem\vig\..\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | serverc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2720 | "C:\Users\admin\AppData\Local\Temp\serverc.exe" | C:\Users\admin\AppData\Local\Temp\serverc.exe | explorer.exe | ||||||||||||
User: admin Company: Kim Jong Un Integrity Level: MEDIUM Description: Coded by Gruja Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
227
Read events
123
Write events
104
Delete events
0
Modification events
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serverc_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serverc_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serverc_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serverc_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serverc_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serverc_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serverc_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serverc_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2720) serverc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\serverc_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
329
Text files
228
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2720 | serverc.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 2720 | serverc.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 2720 | serverc.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 2720 | serverc.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 2720 | serverc.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 2720 | serverc.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 2720 | serverc.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\DECRYPT-FILES.txt | text | |
MD5:— | SHA256:— | |||
| 2720 | serverc.exe | C:\Users\admin\AppData\Roaming\DECRYPT-FILES.txt | text | |
MD5:— | SHA256:— | |||
| 2720 | serverc.exe | C:\Users\admin\.oracle_jre_usage\DECRYPT-FILES.txt | text | |
MD5:— | SHA256:— | |||
| 2720 | serverc.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Collab\DECRYPT-FILES.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
28
DNS requests
0
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2720 | serverc.exe | POST | — | 91.218.114.25:80 | http://91.218.114.25/login/register/mpapy.asp?soqy=8&c=8fq | RU | — | — | malicious |
2720 | serverc.exe | POST | — | 91.218.114.31:80 | http://91.218.114.31/webauth/urujjktdb.cgi?i=o442m&et=r5 | RU | — | — | malicious |
2720 | serverc.exe | POST | — | 91.218.114.11:80 | http://91.218.114.11/s.php | RU | — | — | malicious |
2720 | serverc.exe | POST | 404 | 91.218.114.4:80 | http://91.218.114.4/webaccess/dfogr.cgi?r=sb0u3d | RU | html | 217 b | malicious |
2720 | serverc.exe | POST | — | 91.218.114.26:80 | http://91.218.114.26/create/prdnmm.asp?gau=3u20x4j04&cx=fx5u&e=m | RU | — | — | malicious |
2720 | serverc.exe | POST | — | 91.218.114.25:80 | http://91.218.114.25/webaccess/evdiohqp.cgi?qf=120fa&bfo=18&rth=325yc2u1td | RU | — | — | malicious |
2720 | serverc.exe | POST | — | 91.218.114.4:80 | http://91.218.114.4/webaccess/dfogr.cgi?r=sb0u3d | RU | — | — | malicious |
2720 | serverc.exe | POST | — | 91.218.114.26:80 | http://91.218.114.26/payout/k.action?e=cj&x=4dm6&dw=8 | RU | — | — | malicious |
2720 | serverc.exe | POST | — | 91.218.114.31:80 | http://91.218.114.31/xfafy.action?wp=v67&s=oxhk&a=08cl&sg=iq0 | RU | — | — | malicious |
2720 | serverc.exe | POST | — | 91.218.114.32:80 | http://91.218.114.32/bprowutvow.action?p=v&w=y&mk=mk0132c437&ul=fb5ao23 | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2720 | serverc.exe | 91.218.114.4:80 | — | Mir Telematiki Ltd | RU | malicious |
2720 | serverc.exe | 91.218.114.11:80 | — | Mir Telematiki Ltd | RU | malicious |
2720 | serverc.exe | 91.218.114.25:80 | — | Mir Telematiki Ltd | RU | malicious |
2720 | serverc.exe | 91.218.114.26:80 | — | Mir Telematiki Ltd | RU | malicious |
2720 | serverc.exe | 91.218.114.31:80 | — | Mir Telematiki Ltd | RU | malicious |
2720 | serverc.exe | 91.218.114.32:80 | — | Mir Telematiki Ltd | RU | malicious |
2720 | serverc.exe | 91.218.114.37:80 | — | Mir Telematiki Ltd | RU | malicious |
2720 | serverc.exe | 91.218.114.38:80 | — | Mir Telematiki Ltd | RU | malicious |
2720 | serverc.exe | 91.218.114.79:80 | — | Mir Telematiki Ltd | RU | malicious |
2720 | serverc.exe | 91.218.114.77:80 | — | Mir Telematiki Ltd | RU | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2720 | serverc.exe | A Network Trojan was detected | RANSOMWARE [PTsecurity] Maze |
2 ETPRO signatures available at the full report