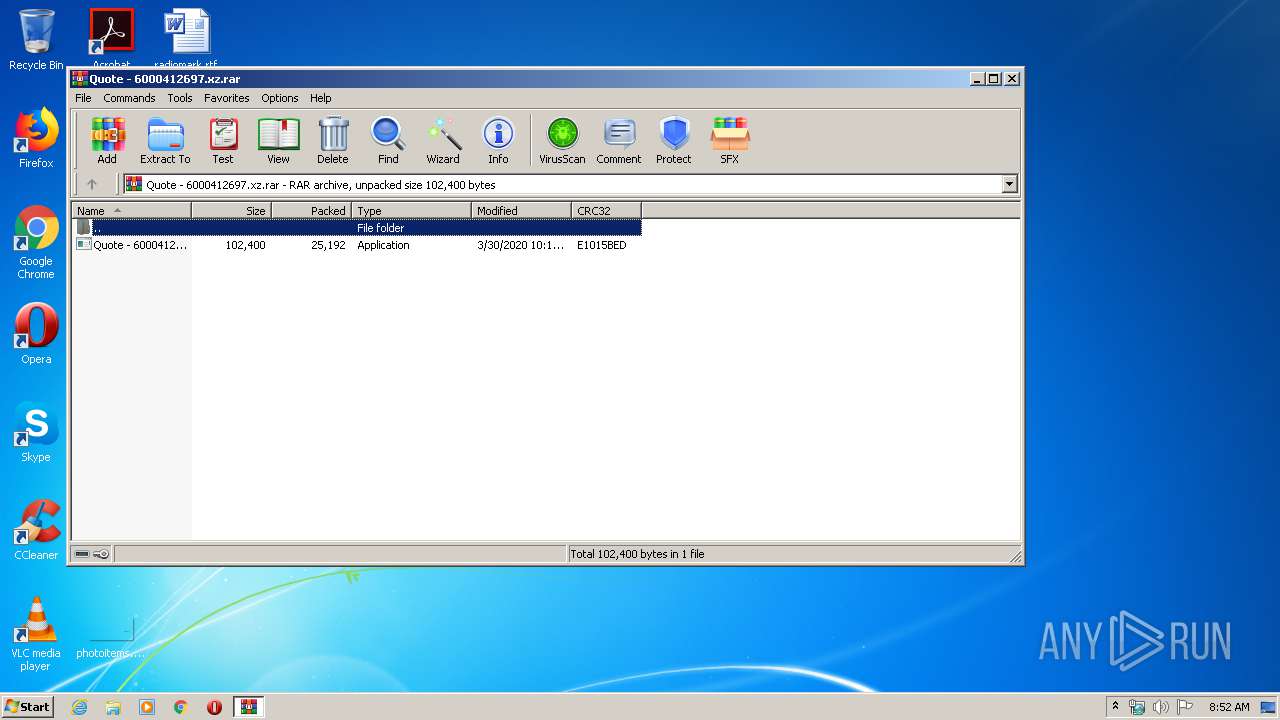
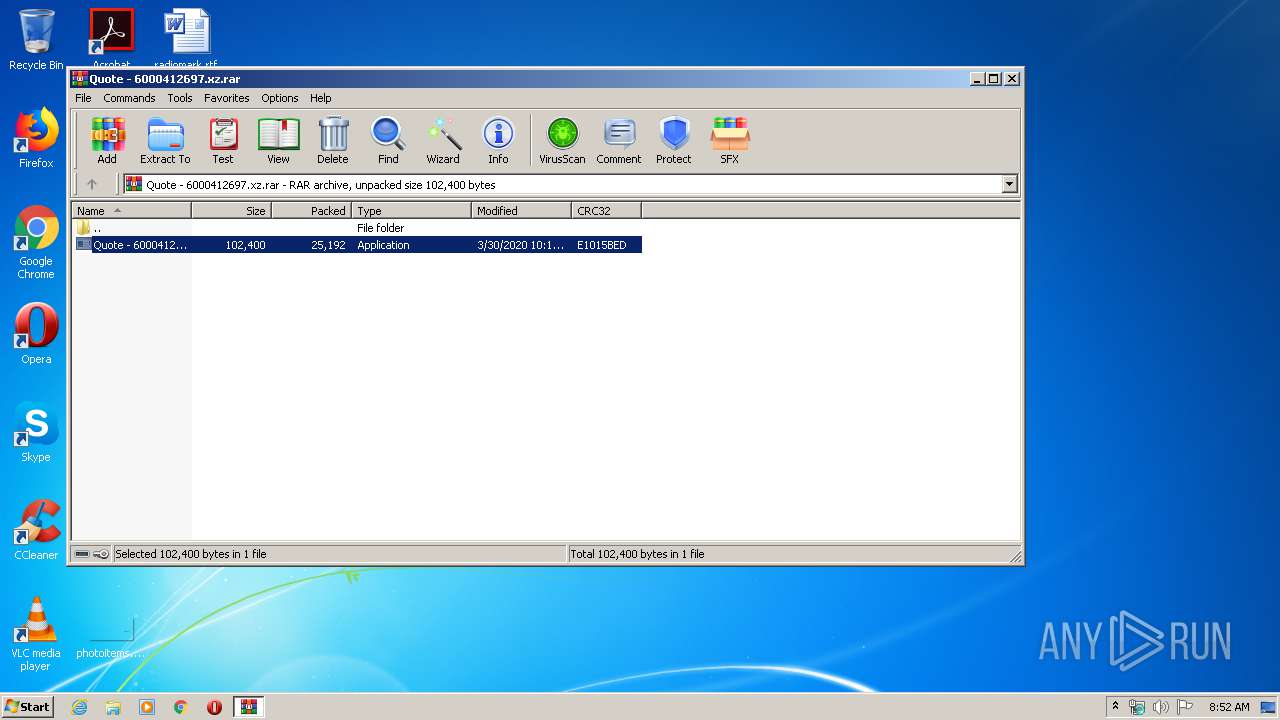
| File name: | Quote - 6000412697.xz |
| Full analysis: | https://app.any.run/tasks/dee8514a-7b9b-41ba-884a-3b0c453fabb6 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | March 31, 2020, 07:52:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2A132962FCB751485EB6913CB24EB39B |
| SHA1: | 8A8F2A673AD5DE726F8ADCC4B94FADF147691B83 |
| SHA256: | 9431A47B9B1F580FA968A89445FA95DA7B73C1784CA4FA860FAC3E6EC9E8D3DD |
| SSDEEP: | 768:iRNLauSCeXdjdYkQHhBo7HfoPe+W/2rTXgSWf:cNLLSCetjOHyfVT+bWf |
MALICIOUS
Application was dropped or rewritten from another process
- Quote - 6000412697.exe (PID: 2800)
- Quote - 6000412697.exe (PID: 3320)
FORMBOOK was detected
- explorer.exe (PID: 372)
- wscript.exe (PID: 3576)
- Firefox.exe (PID: 3480)
Connects to CnC server
- explorer.exe (PID: 372)
Changes the autorun value in the registry
- wscript.exe (PID: 3576)
Actions looks like stealing of personal data
- wscript.exe (PID: 3576)
Stealing of credential data
- wscript.exe (PID: 3576)
Changes settings of System certificates
- Quote - 6000412697.exe (PID: 2800)
SUSPICIOUS
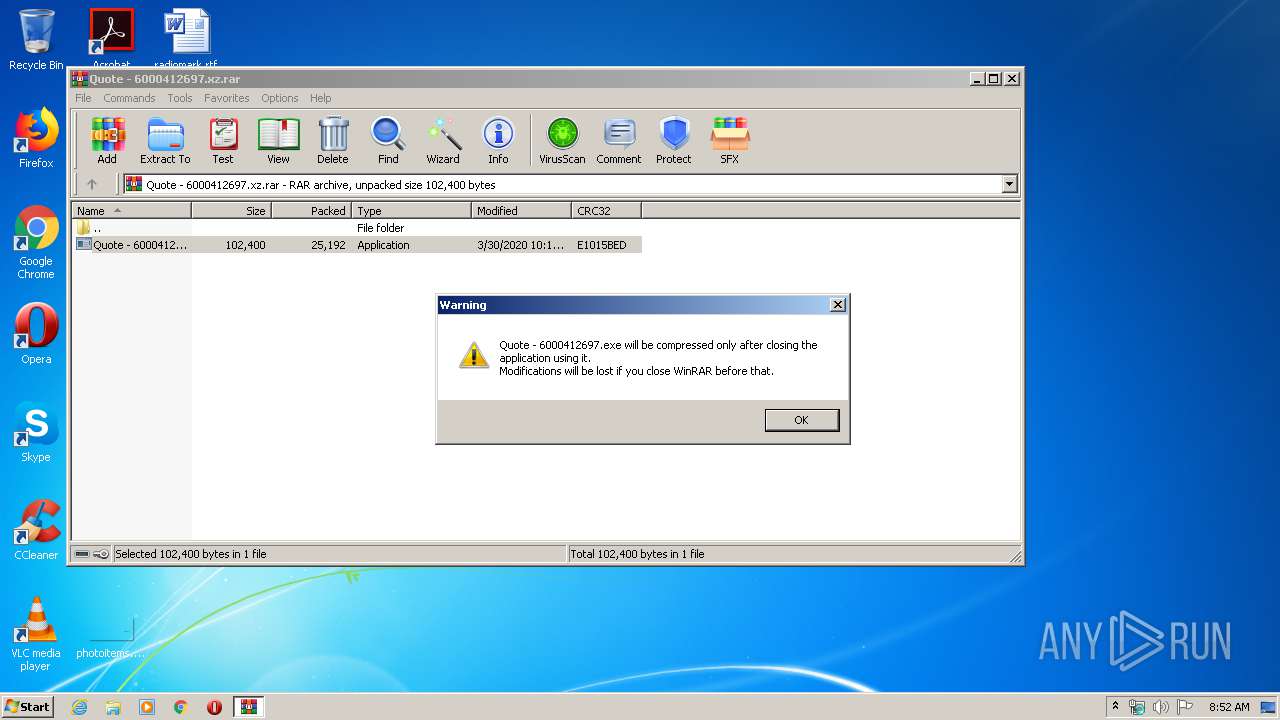
Executable content was dropped or overwritten
- WinRAR.exe (PID: 780)
Application launched itself
- Quote - 6000412697.exe (PID: 3320)
Reads Internet Cache Settings
- Quote - 6000412697.exe (PID: 2800)
Executes scripts
- explorer.exe (PID: 372)
Creates files in the user directory
- Quote - 6000412697.exe (PID: 2800)
- wscript.exe (PID: 3576)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3576)
Loads DLL from Mozilla Firefox
- wscript.exe (PID: 3576)
Adds / modifies Windows certificates
- Quote - 6000412697.exe (PID: 2800)
INFO
Manual execution by user
- wscript.exe (PID: 3576)
Reads the hosts file
- wscript.exe (PID: 3576)
Reads settings of System Certificates
- Quote - 6000412697.exe (PID: 2800)
Creates files in the user directory
- Firefox.exe (PID: 3480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
40
Monitored processes
7
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 780 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Quote - 6000412697.xz.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2800 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa780.48379\Quote - 6000412697.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa780.48379\Quote - 6000412697.exe | Quote - 6000412697.exe | ||||||||||||
User: admin Company: WONDerware Integrity Level: MEDIUM Description: Anterin3 Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3320 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa780.48379\Quote - 6000412697.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa780.48379\Quote - 6000412697.exe | — | WinRAR.exe | |||||||||||
User: admin Company: WONDerware Integrity Level: MEDIUM Description: Anterin3 Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3480 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | wscript.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3576 | "C:\Windows\System32\wscript.exe" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 4072 | /c del "C:\Users\admin\AppData\Local\Temp\Rar$EXa780.48379\Quote - 6000412697.exe" | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 057
Read events
475
Write events
2 395
Delete events
1 187
Modification events
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Quote - 6000412697.xz.rar | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (780) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (372) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
1
Suspicious files
88
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | Quote - 6000412697.exe | C:\Users\admin\AppData\Local\Temp\CabD346.tmp | — | |
MD5:— | SHA256:— | |||
| 2800 | Quote - 6000412697.exe | C:\Users\admin\AppData\Local\Temp\TarD347.tmp | — | |
MD5:— | SHA256:— | |||
| 2800 | Quote - 6000412697.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 2800 | Quote - 6000412697.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_BA8650709FF65A42B9202D73C10A8F29 | binary | |
MD5:— | SHA256:— | |||
| 3576 | wscript.exe | C:\Users\admin\AppData\Roaming\9389QUSF\938logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 3576 | wscript.exe | C:\Users\admin\AppData\Roaming\9389QUSF\938logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 3480 | Firefox.exe | C:\Users\admin\AppData\Roaming\9389QUSF\938logrf.ini | binary | |
MD5:— | SHA256:— | |||
| 780 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa780.48379\Quote - 6000412697.exe | executable | |
MD5:— | SHA256:— | |||
| 2800 | Quote - 6000412697.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BE8B021F9E811DFC8C8A28572A17C05A_0B97942EE72A6E3F514E8E84F294CC72 | der | |
MD5:— | SHA256:— | |||
| 2800 | Quote - 6000412697.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
5
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2800 | Quote - 6000412697.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFOOHQjK5IlqCAAAAAAyCmA%3D | US | der | 471 b | whitelisted |
372 | explorer.exe | GET | 301 | 52.26.226.99:80 | http://www.pilotshometrade.com/k19/?xbkhBh=fAFvR0WqBJTOxVrHtbDRSZzgRaoorQZ5CQ0BZUmBoeACfIXNnT+eRQGsXLyJ3URolO72Ng==&odsD=rVo0vl | US | html | 148 b | malicious |
2800 | Quote - 6000412697.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2800 | Quote - 6000412697.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2800 | Quote - 6000412697.exe | 216.58.207.78:443 | drive.google.com | Google Inc. | US | whitelisted |
2800 | Quote - 6000412697.exe | 172.217.23.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2800 | Quote - 6000412697.exe | 172.217.23.97:443 | doc-00-bk-docs.googleusercontent.com | Google Inc. | US | whitelisted |
372 | explorer.exe | 52.26.226.99:80 | www.pilotshometrade.com | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
drive.google.com |
| shared |
ocsp.pki.goog |
| whitelisted |
doc-00-bk-docs.googleusercontent.com |
| shared |
www.simplifiedqliking.com |
| unknown |
www.pilotshometrade.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
372 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
1 ETPRO signatures available at the full report