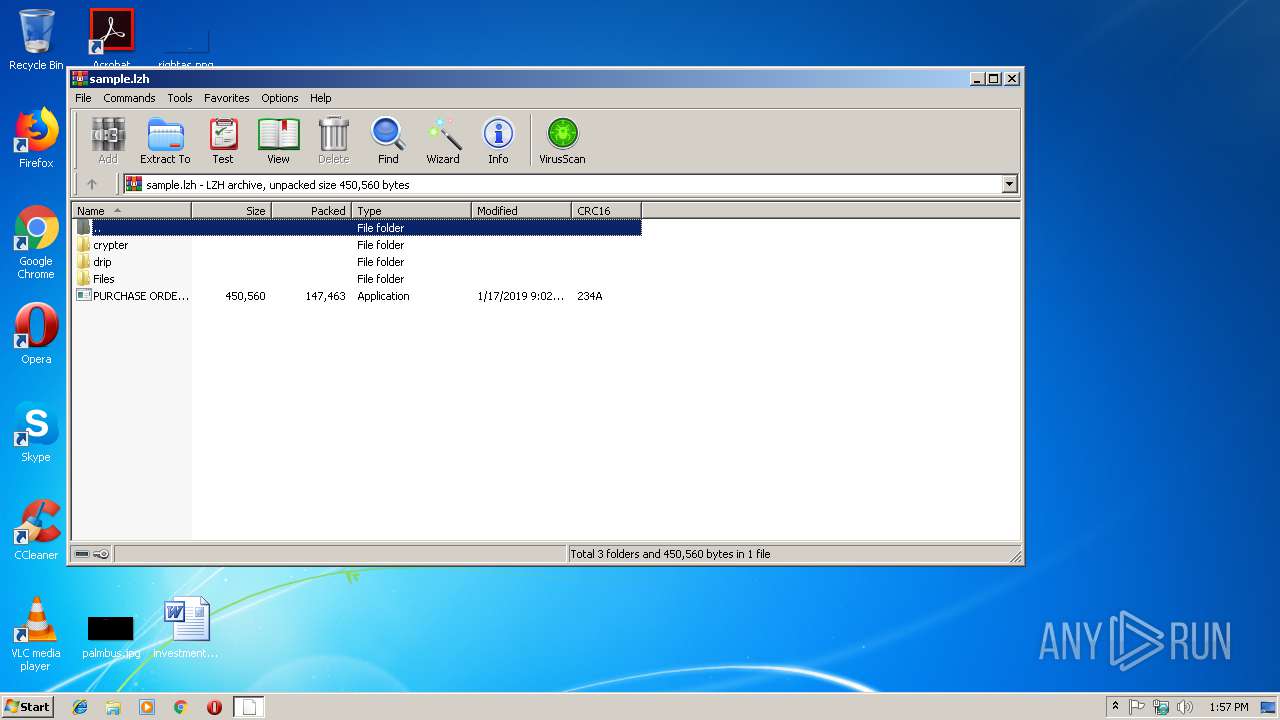
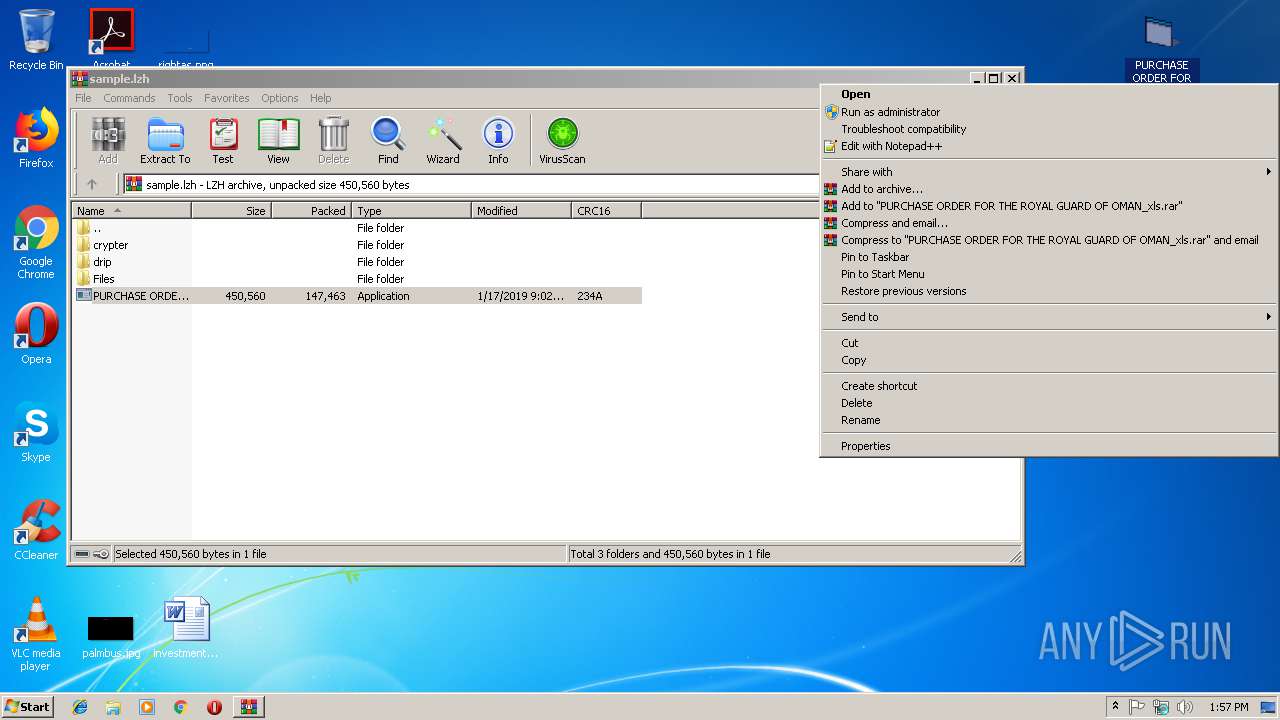
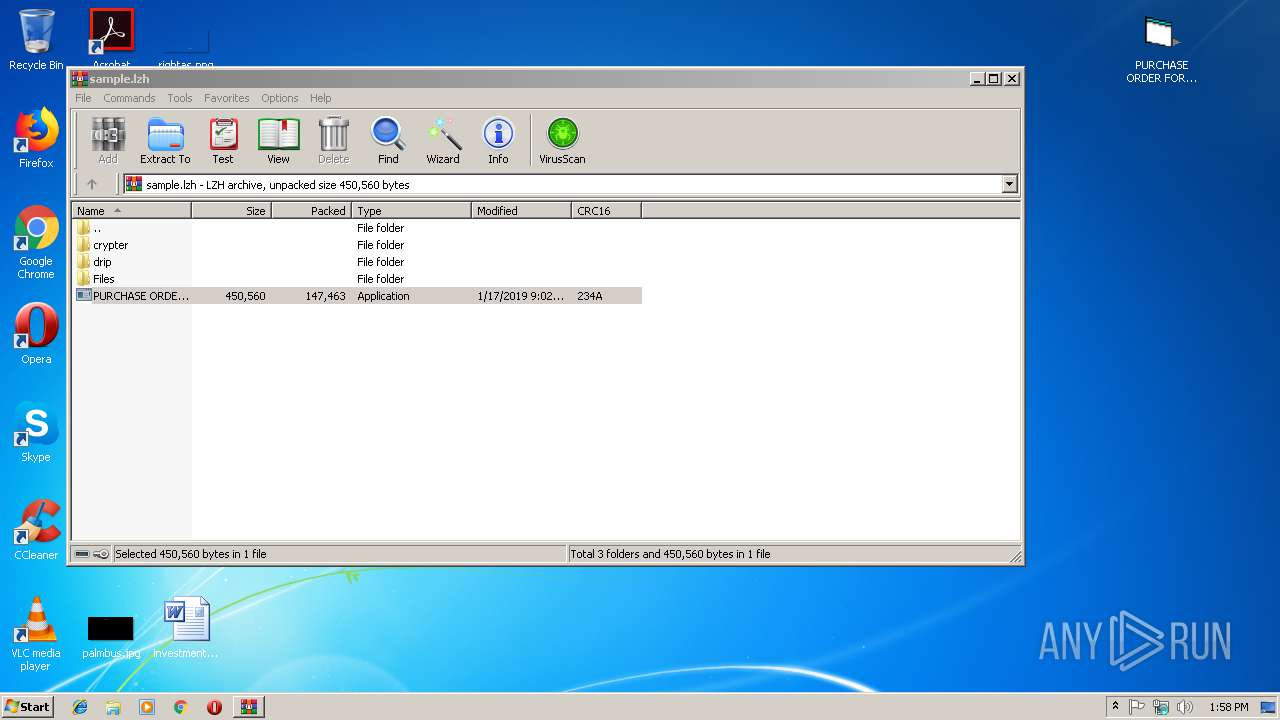
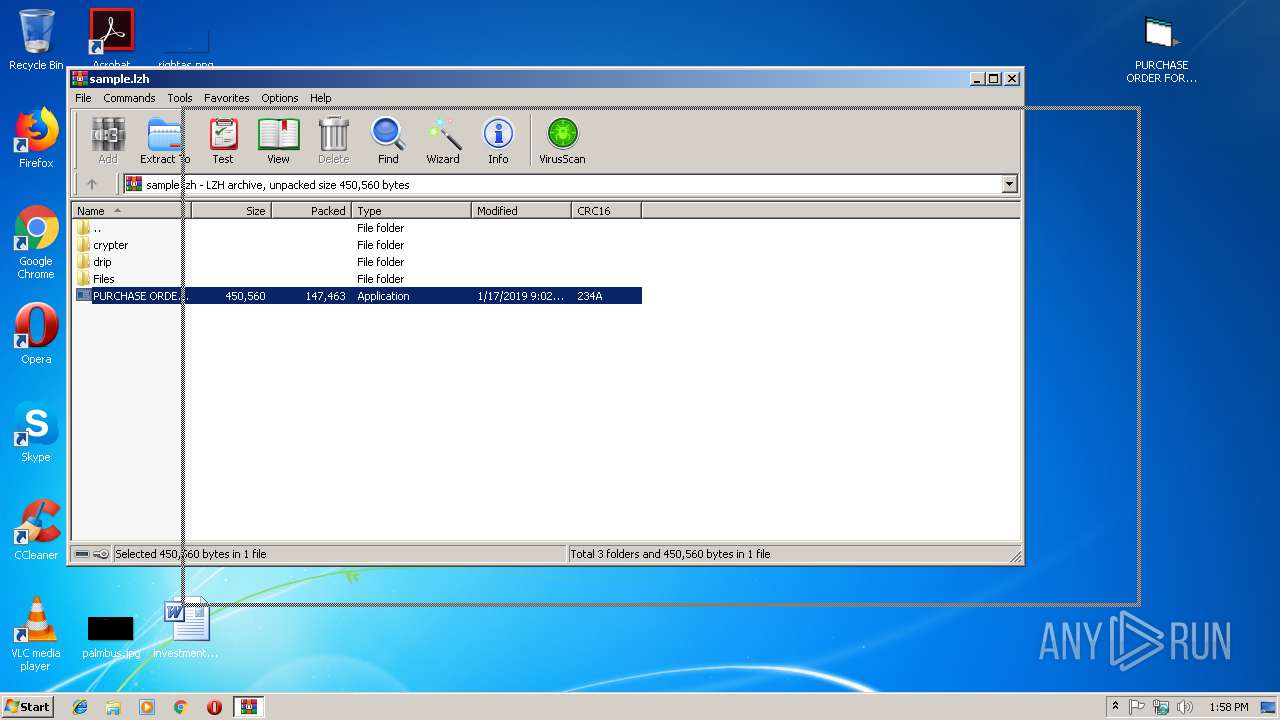
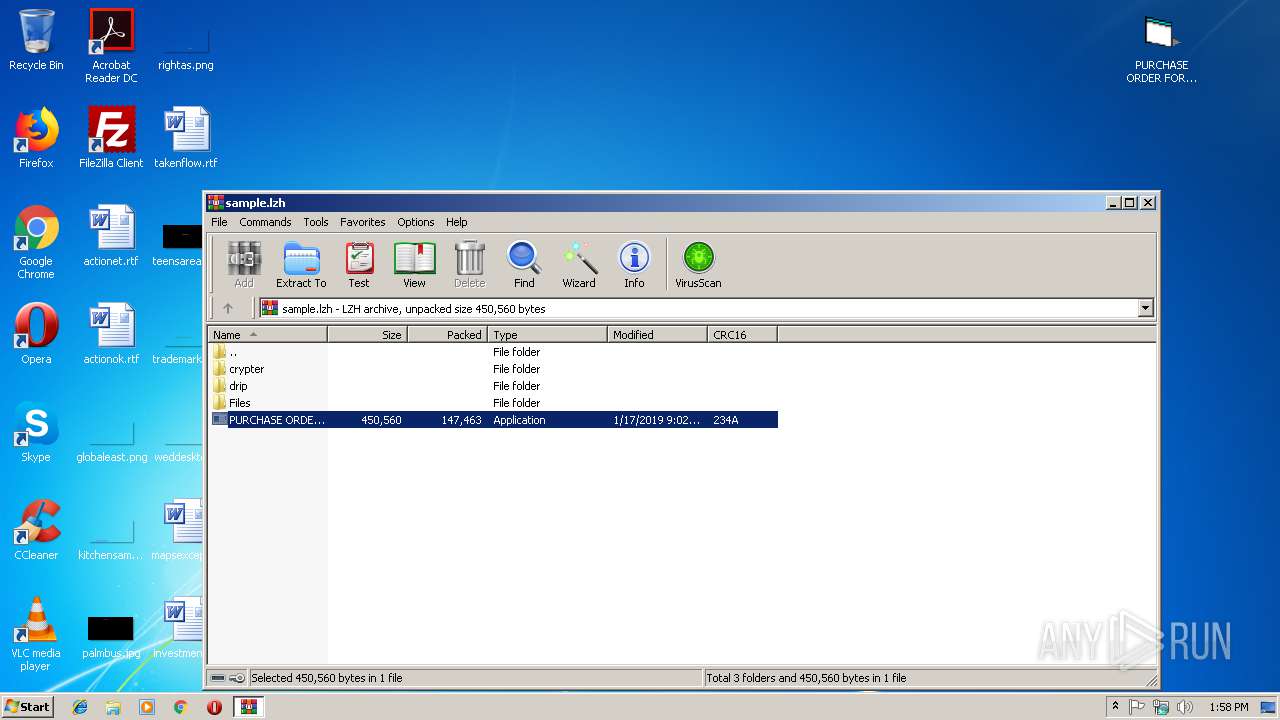
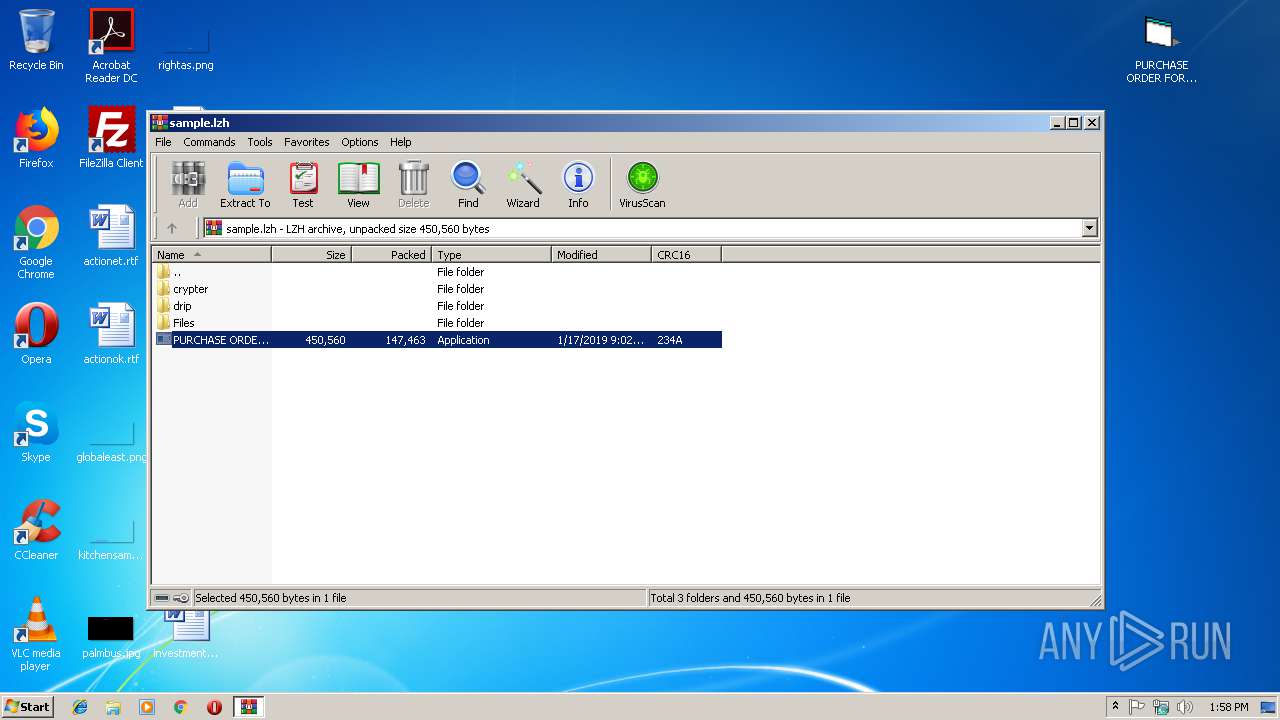
| File name: | sample.lzh |
| Full analysis: | https://app.any.run/tasks/5125b5b4-351f-4b0d-bd6f-b1c5487cd78b |
| Verdict: | Malicious activity |
| Threats: | Pony is a malware with two main functions — stealing information and dropping other viruses with different tasks on infected machines. It has been around since 2011, and it still actively attacks users in Europe and America. |
| Analysis date: | January 17, 2019, 13:57:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-lzh-compressed |
| File info: | LHa 2.x? archive data [lhd], with "crypter\builder\builder\" |
| MD5: | EA4502C707C9BD90AF97716A71C36D97 |
| SHA1: | 8F86F75D4269A741F4FC62B341CC1D3F321D0618 |
| SHA256: | 942D187B3948B2A1B744ABA61345D4DF51D9819E7FB3CF73EFA900B78295F1FA |
| SSDEEP: | 3072:JISQnELuHTtC9vvL5jh1ZzaJ2wdMQkffIfK3PsrMcQ:JXQELCUzLzU2wdJkfKK3PsoD |
MALICIOUS
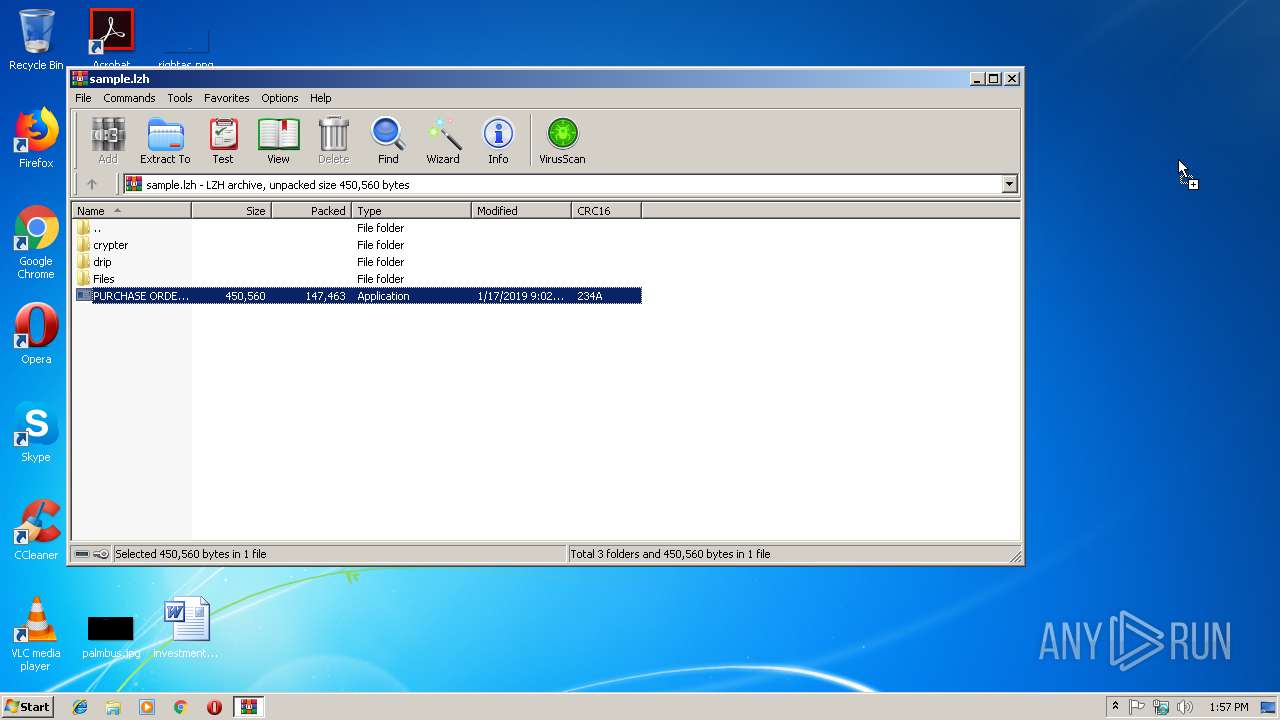
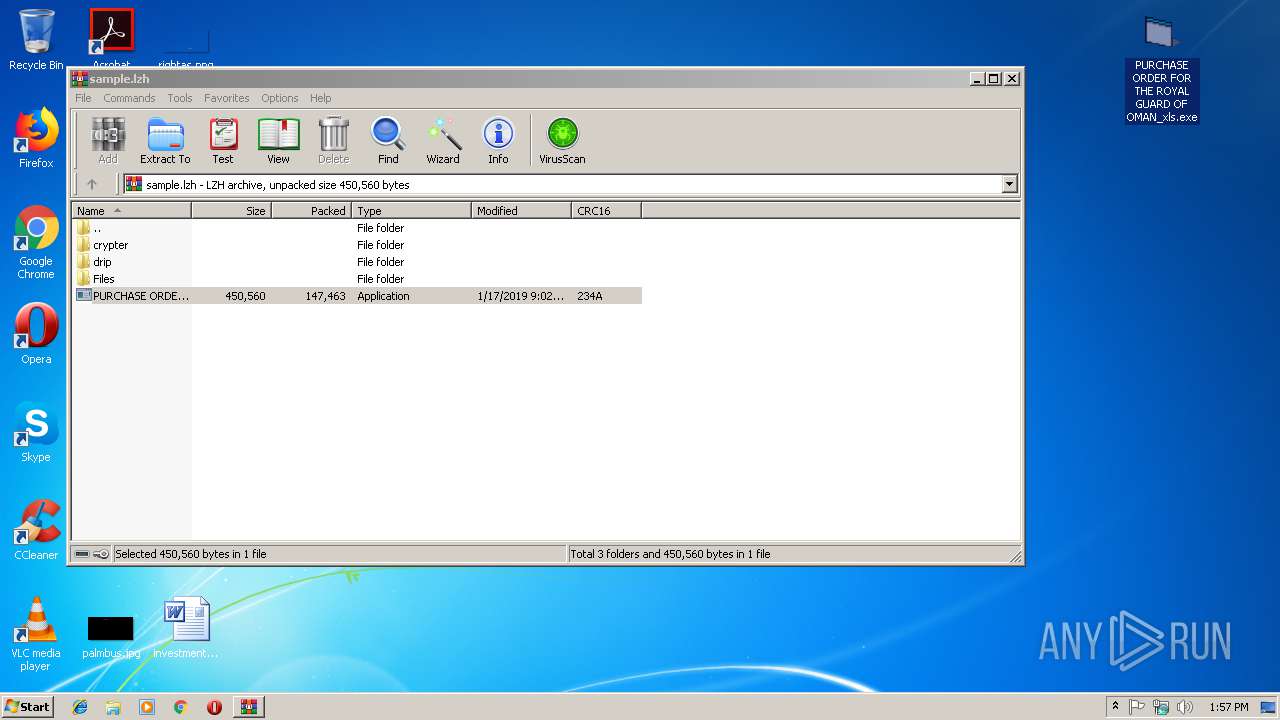
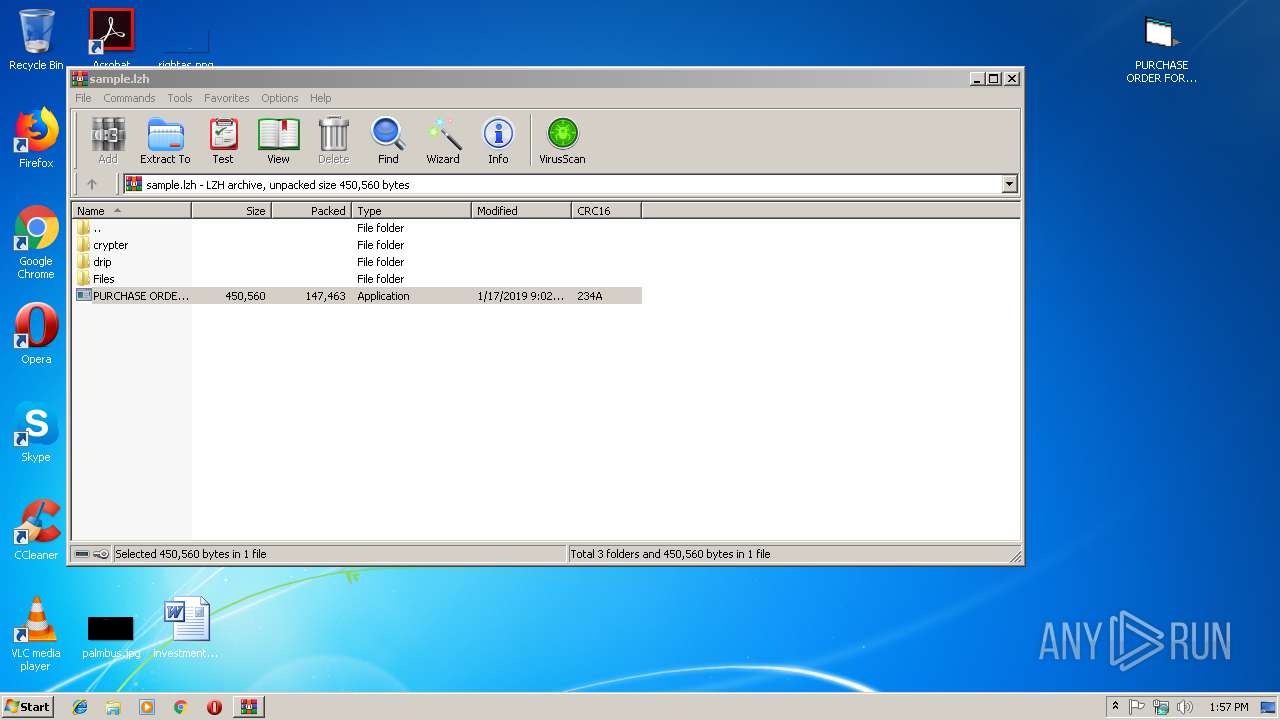
Application was dropped or rewritten from another process
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 4036)
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 2948)
Detected Pony/Fareit Trojan
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 4036)
PONY was detected
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 2948)
Connects to CnC server
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 2948)
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 4036)
Actions looks like stealing of personal data
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 4036)
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 2948)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2980)
Starts CMD.EXE for commands execution
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 2948)
- PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe (PID: 4036)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lzh/lha | | | LHARC/LZARK compressed archive (generic) (100) |
|---|
Total processes
37
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2108 | cmd /c ""C:\Users\admin\AppData\Local\Temp\2196578.bat" "C:\Users\admin\Desktop\PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe" " | C:\Windows\system32\cmd.exe | — | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2948 | "C:\Users\admin\Desktop\PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe" | C:\Users\admin\Desktop\PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | explorer.exe | ||||||||||||
User: admin Company: FACebOoK INc. Integrity Level: MEDIUM Description: SAMsuNg Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample.lzh" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3128 | cmd /c ""C:\Users\admin\AppData\Local\Temp\2204437.bat" "C:\Users\admin\Desktop\PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe" " | C:\Windows\system32\cmd.exe | — | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4036 | "C:\Users\admin\Desktop\PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe" | C:\Users\admin\Desktop\PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | explorer.exe | ||||||||||||
User: admin Company: FACebOoK INc. Integrity Level: MEDIUM Description: SAMsuNg Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
1 178
Read events
1 159
Write events
19
Delete events
0
Modification events
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample.lzh | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4036) PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR |
| Operation: | write | Name: | HWID |
Value: 7B33324537334342322D463533422D344345322D394544392D4234444236414646353638387D | |||
| (PID) Process: | (2948) PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR |
| Operation: | write | Name: | Client Hash |
Value: 63067A7A78A1B0D476D424FAD8FC6622 | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | C:\Users\admin\AppData\Local\Temp\2204437.bat | text | |
MD5:3880EEB1C736D853EB13B44898B718AB | SHA256:936D9411D5226B7C5A150ECAF422987590A8870C8E095E1CAA072273041A86E7 | |||
| 2948 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | C:\Users\admin\AppData\Local\Temp\2196578.bat | text | |
MD5:3880EEB1C736D853EB13B44898B718AB | SHA256:936D9411D5226B7C5A150ECAF422987590A8870C8E095E1CAA072273041A86E7 | |||
| 2980 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2980.47413\PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
2
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2948 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | POST | — | 142.4.215.104:80 | http://yellowork.com/drip/panel/gate.php | CA | — | — | malicious |
2948 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | GET | — | 142.4.215.104:80 | http://yellowork.com/drip/panel/drip.exe | CA | — | — | malicious |
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | POST | — | 142.4.215.104:80 | http://yellowork.com/drip/panel/gate.php | CA | — | — | malicious |
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | GET | — | 142.4.215.104:80 | http://yellowork.com/drip/panel/drip.exe | CA | — | — | malicious |
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | POST | — | 142.4.215.104:80 | http://yellowork.com/drip/panel/gate.php | CA | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | 142.4.215.104:80 | yellowork.com | OVH SAS | CA | suspicious |
2948 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | 142.4.215.104:80 | yellowork.com | OVH SAS | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
yellowork.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Internet Explorer Version MSIE 5. |
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
2948 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
2948 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
2948 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Internet Explorer Version MSIE 5. |
2948 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | A Network Trojan was detected | MALWARE [PTsecurity] Pony encrypted POST Data Request |
4036 | PURCHASE ORDER FOR THE ROYAL GUARD OF OMAN_xls.exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |
2 ETPRO signatures available at the full report