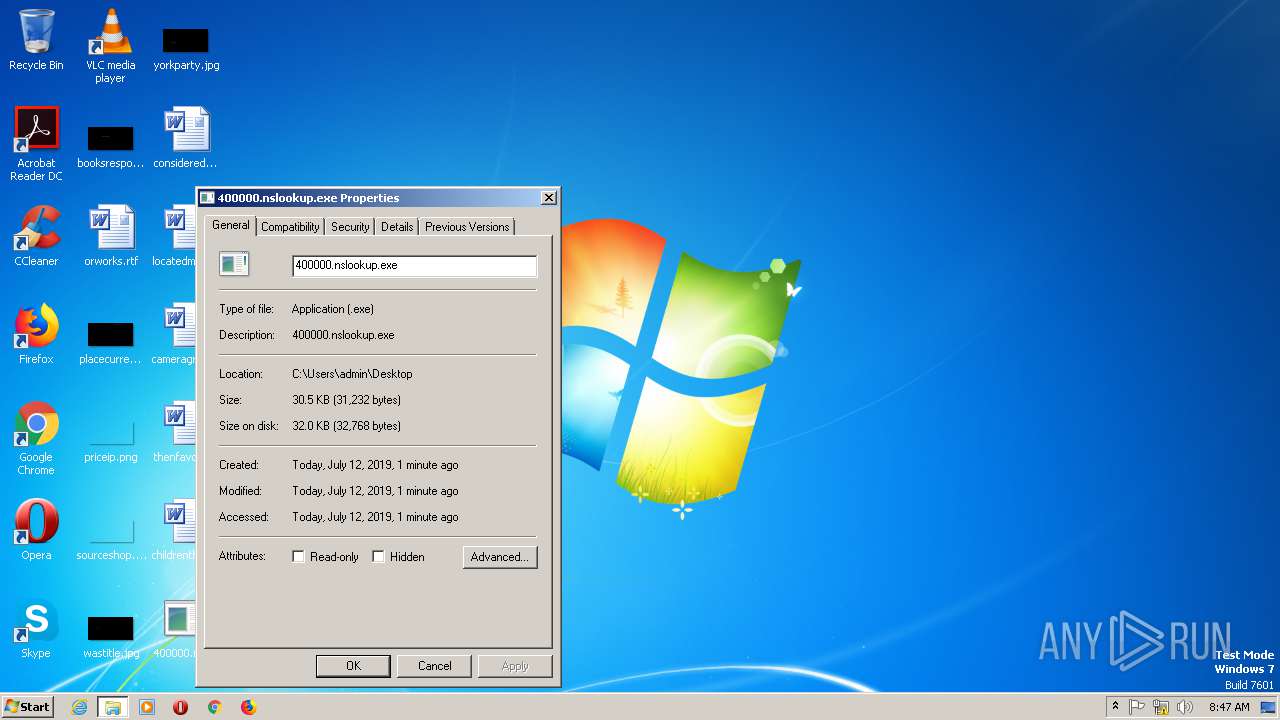
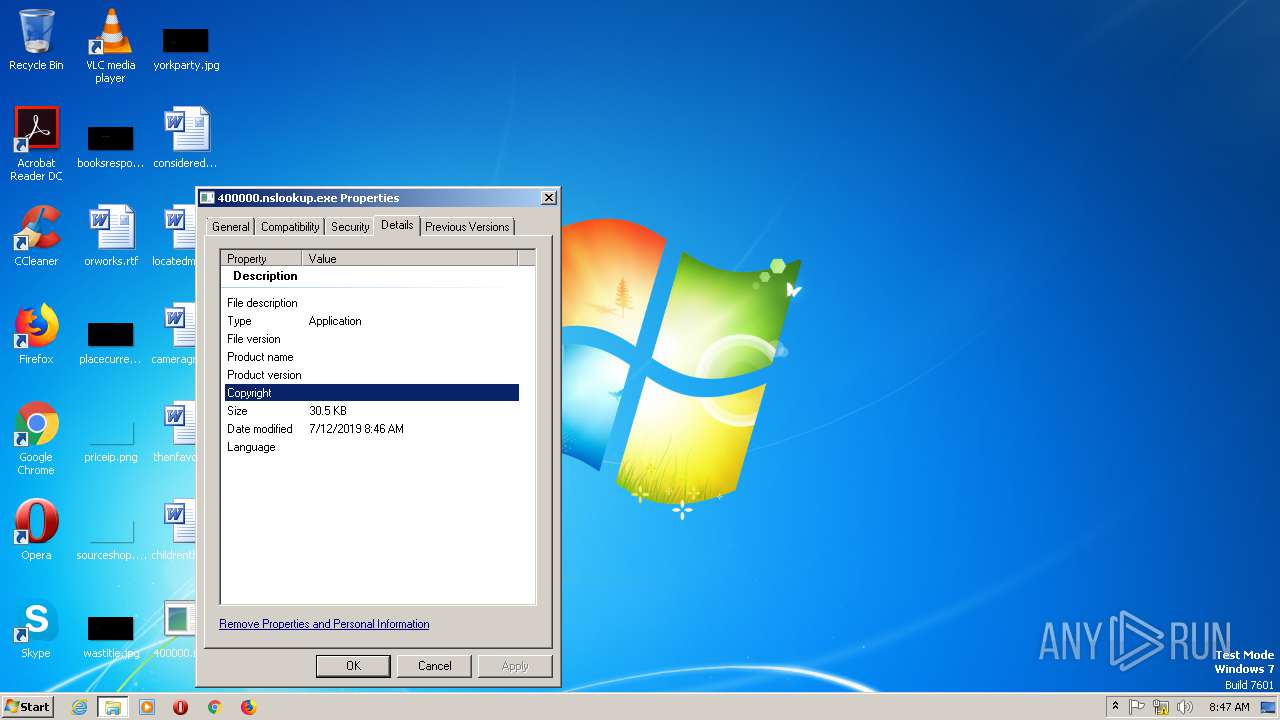
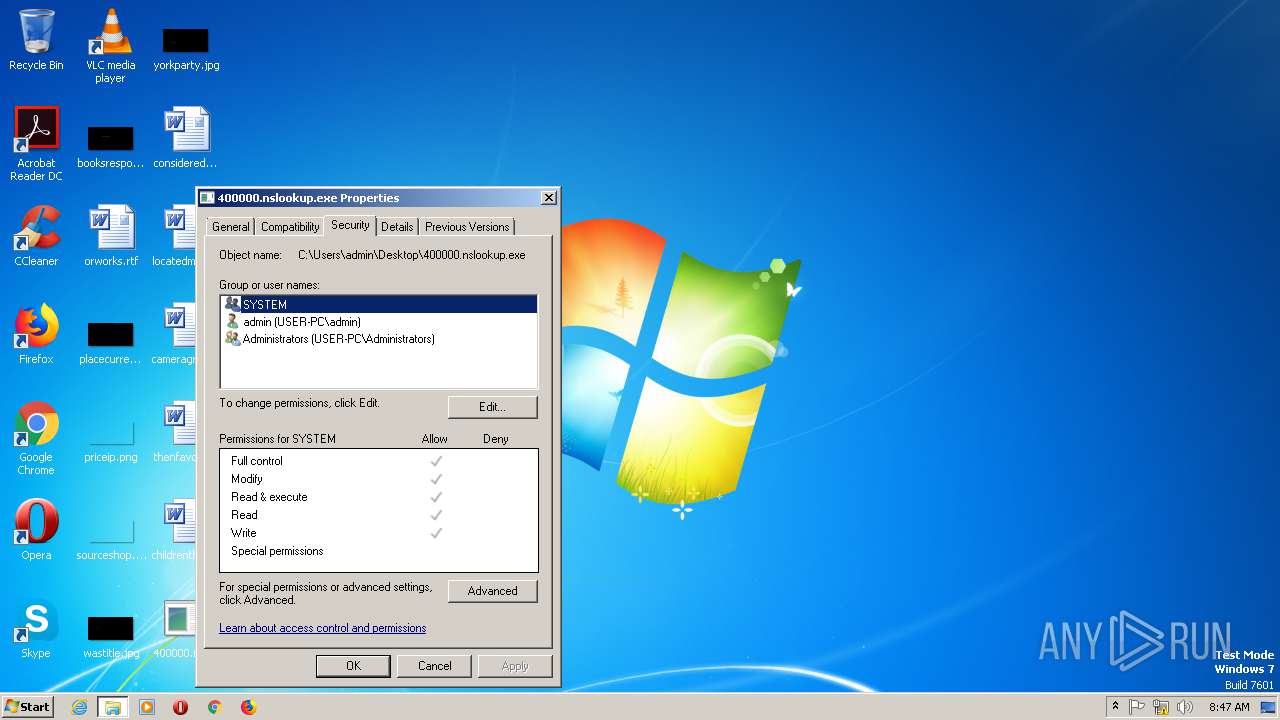
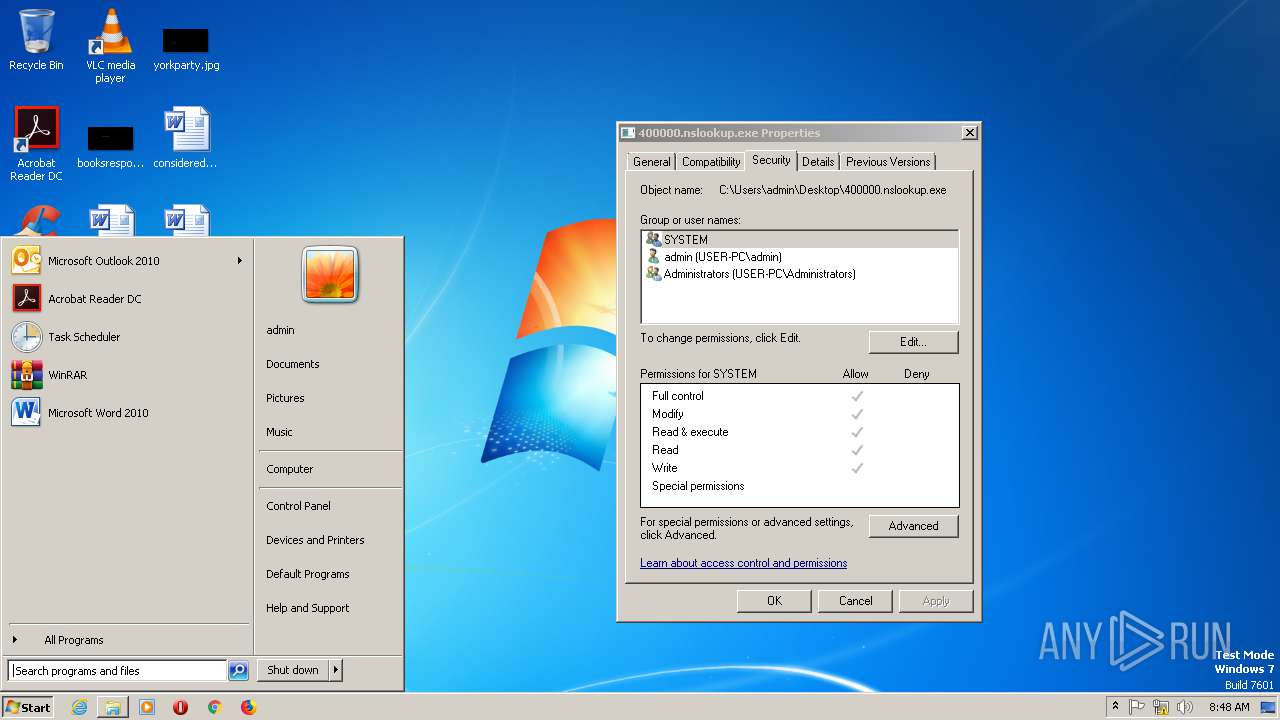
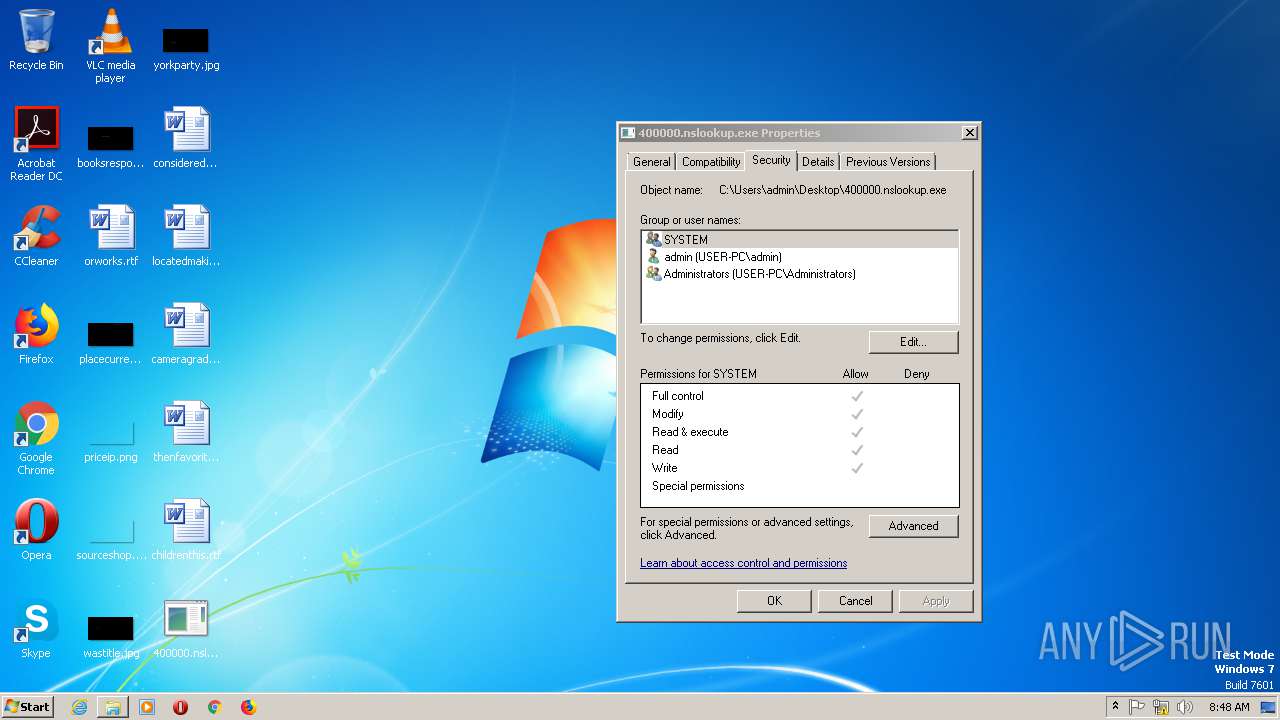
| File name: | 400000.nslookup.exe |
| Full analysis: | https://app.any.run/tasks/3e79eedc-12ed-4397-8887-2013f996216a |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | July 12, 2019, 08:46:21 |
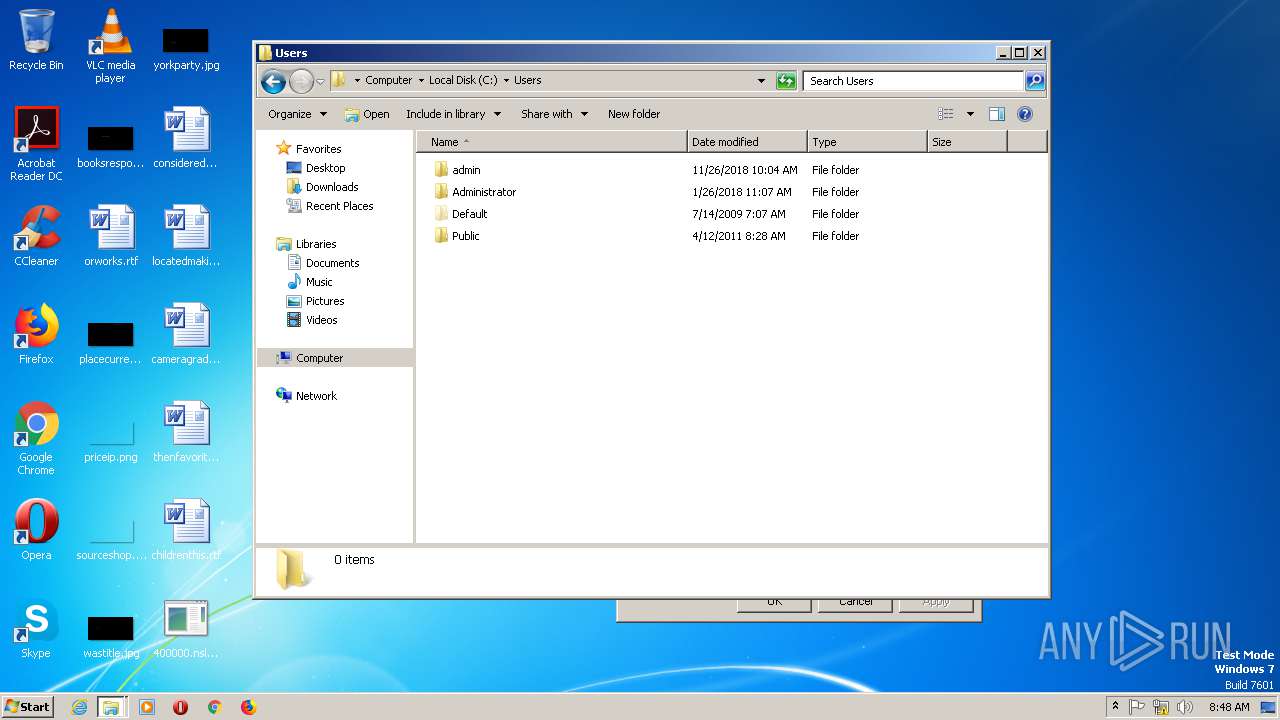
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | AECB32883857E09E013B01882D6CFBB8 |
| SHA1: | D58571D09D5ADA5807639BDD00054BD076BDFAB1 |
| SHA256: | 93F5ADA9F453527769DD5A55B93BAB669371247B7D29FB545499797276A1890D |
| SSDEEP: | 384:5Zcsr9MNC3HD0Fz8u3t1EB4MDgDbo74vCTHrGLjq:5nbj0l9meMDgHosSX |
MALICIOUS
AMADEY was detected
- 400000.nslookup.exe (PID: 2856)
- kntd.exe (PID: 2684)
- kntd.exe (PID: 1980)
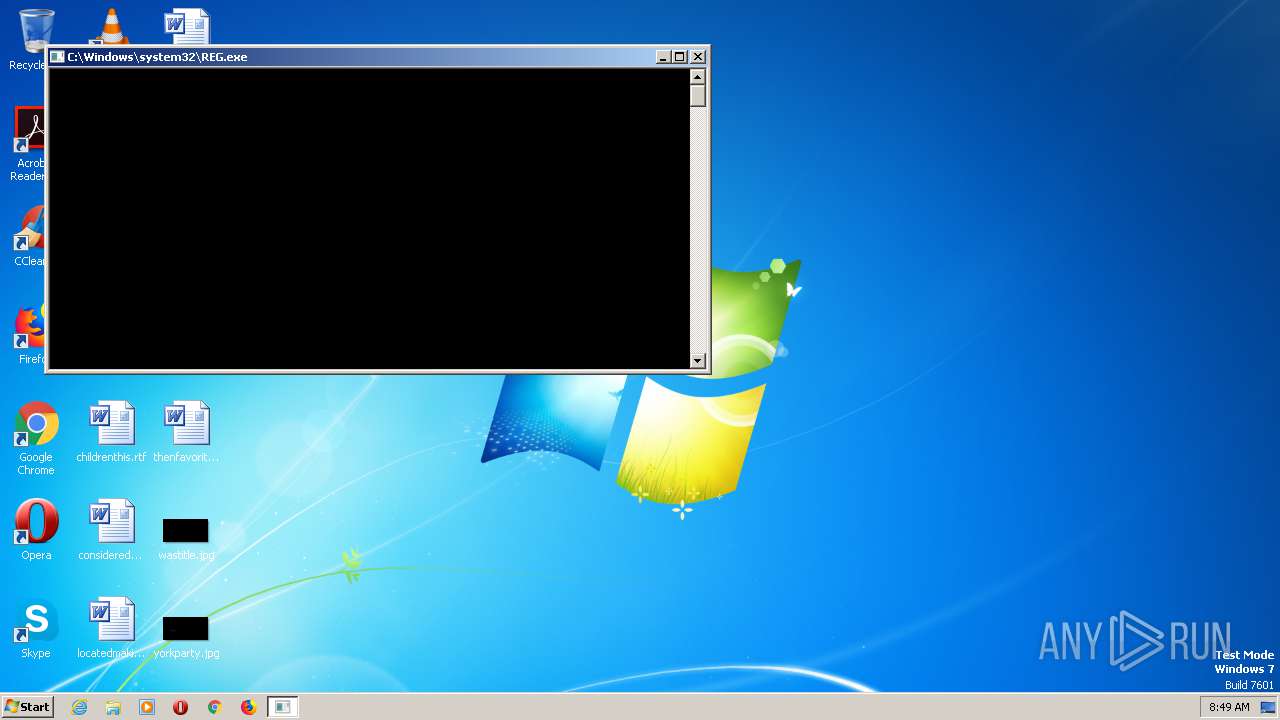
Changes the Startup folder
- REG.exe (PID: 2460)
- REG.exe (PID: 2788)
Connects to CnC server
- kntd.exe (PID: 2684)
- kntd.exe (PID: 1980)
SUSPICIOUS
Creates files in the program directory
- 400000.nslookup.exe (PID: 2856)
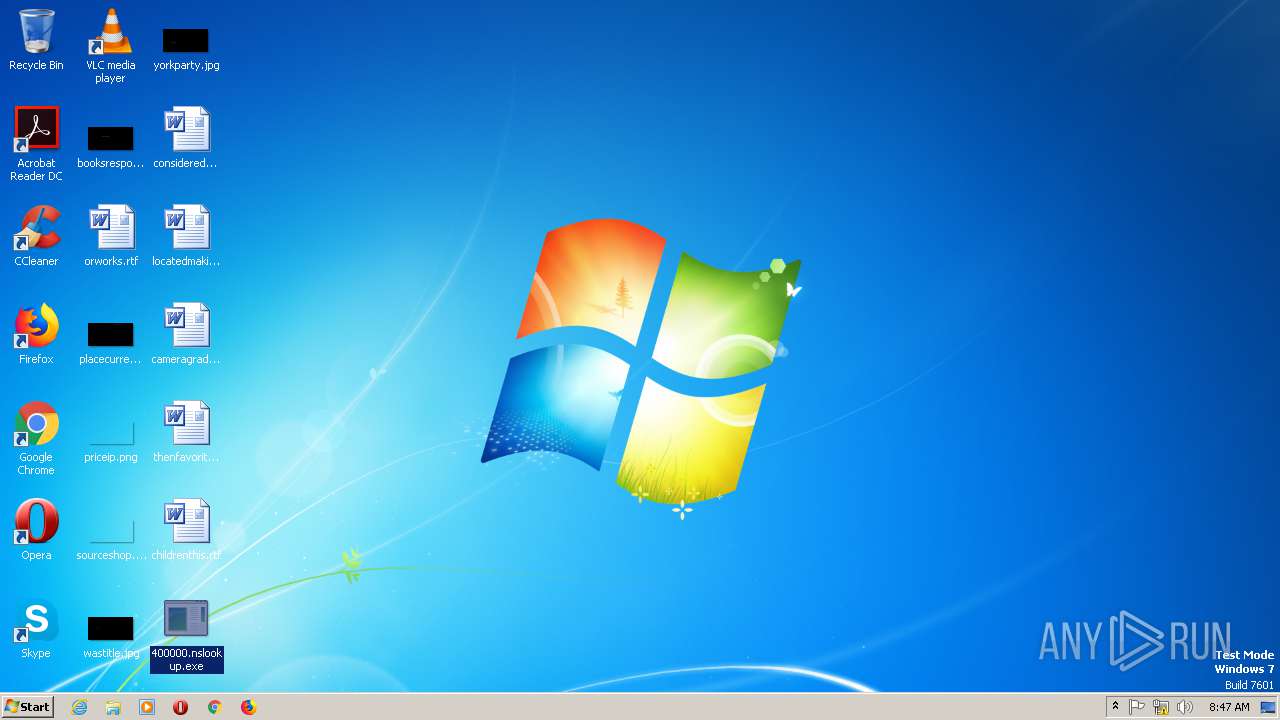
Starts itself from another location
- 400000.nslookup.exe (PID: 2856)
Uses REG.EXE to modify Windows registry
- kntd.exe (PID: 2684)
- kntd.exe (PID: 1980)
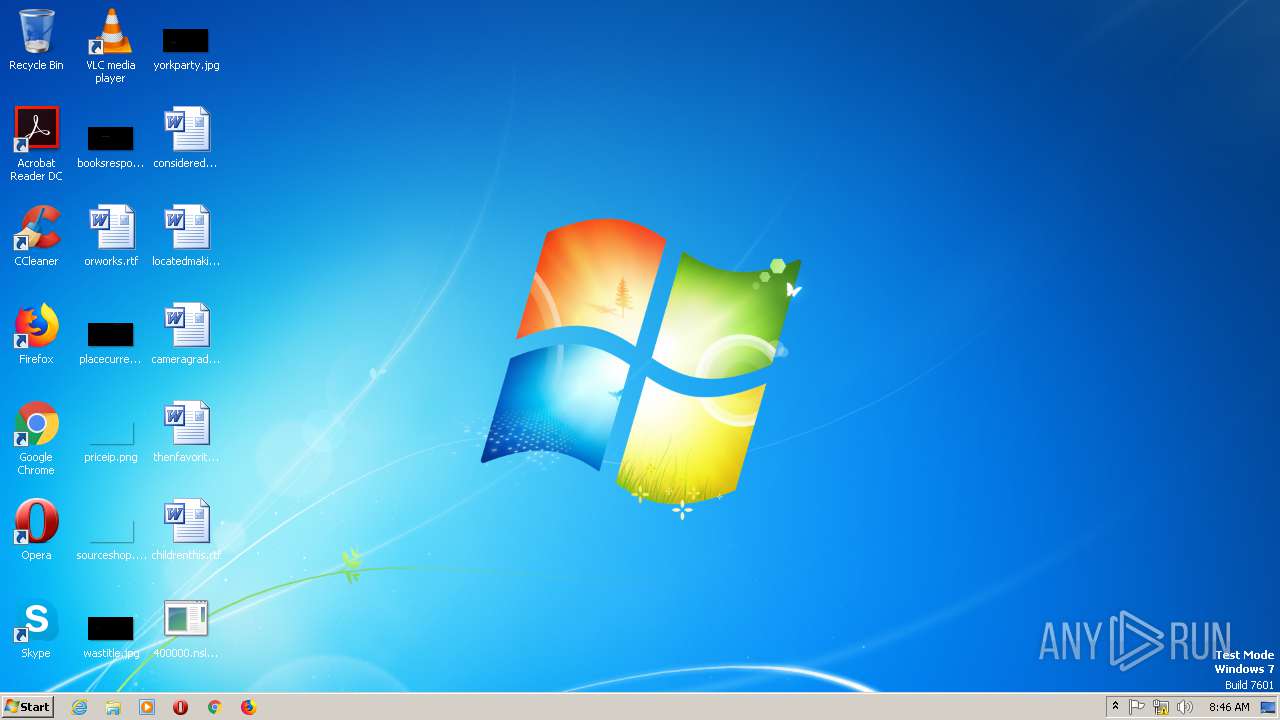
Executable content was dropped or overwritten
- 400000.nslookup.exe (PID: 2856)
Connects to server without host name
- kntd.exe (PID: 1980)
- kntd.exe (PID: 2684)
INFO
Manual execution by user
- kntd.exe (PID: 1980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:05 09:11:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 14336 |
| InitializedDataSize: | 30208 |
| UninitializedDataSize: | 85504 |
| EntryPoint: | 0x1240 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Jul-2019 07:11:56 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 05-Jul-2019 07:11:56 |
| Pointer to Symbol Table: | 0x00007A00 |
| Number of symbols: | 1208 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000037D4 | 0x00003800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.50995 |
.data | 0x00005000 | 0x00002060 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.833131 |
.rdata | 0x00008000 | 0x00000100 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.18742 |
.bss | 0x00009000 | 0x00014DB0 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.edata | 0x0001E000 | 0x00000AD2 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14511 |
.idata | 0x0001F000 | 0x000008C0 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.84604 |
.reloc | 0x00020000 | 0x00000310 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.61168 |
Imports
ADVAPI32.DLL |
KERNEL32.dll |
SHELL32.DLL |
USER32.dll |
WSOCK32.DLL |
msvcrt.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_Z10aBypassUACv | 1 | 0x00003DEC |
_Z10aCharToIntPc | 2 | 0x000016F4 |
_Z10aGetOsArchv | 3 | 0x00001B72 |
_Z10aIntToChari | 4 | 0x000016B6 |
_Z10bBasicTH_1Pv@4 | 5 | 0x0000393A |
_Z10bBasicTH_2Pv@4 | 6 | 0x0000394A |
_Z10bBasicTH_3Pv@4 | 7 | 0x0000395A |
_Z11aAutoRunSetPc | 8 | 0x00003CFE |
_Z11aCheckAdminv | 9 | 0x00001B0E |
_Z11aCreateFilePc | 10 | 0x0000162A |
Total processes
79
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1980 | "C:\ProgramData\0433b5cdb4\kntd.exe" | C:\ProgramData\0433b5cdb4\kntd.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2460 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /f /v Startup /t REG_SZ /d C:\ProgramData\0433b5cdb4 | C:\Windows\SysWOW64\REG.exe | kntd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | c:\programdata\0433b5cdb4\kntd.exe | c:\programdata\0433b5cdb4\kntd.exe | 400000.nslookup.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1073807364 Modules
| |||||||||||||||
| 2788 | REG ADD "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /f /v Startup /t REG_SZ /d C:\ProgramData\0433b5cdb4 | C:\Windows\SysWOW64\REG.exe | kntd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
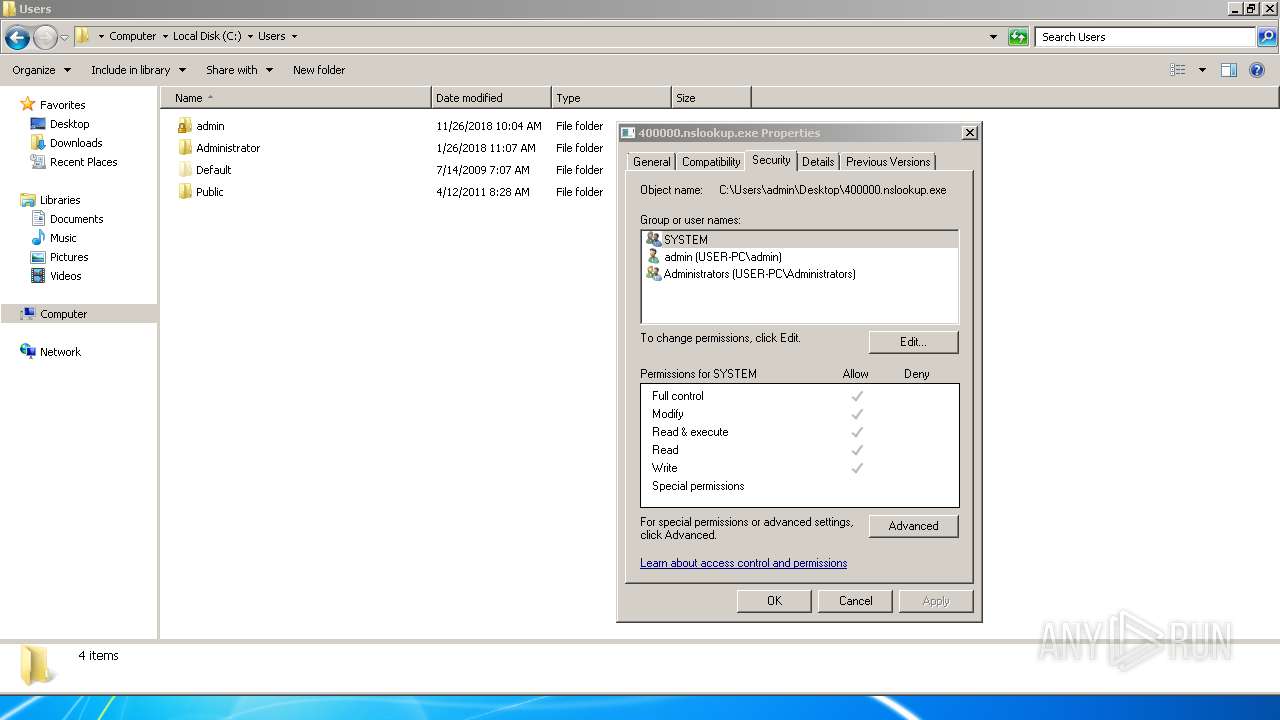
| 2856 | "C:\Users\admin\Desktop\400000.nslookup.exe" | C:\Users\admin\Desktop\400000.nslookup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2
Read events
0
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2460) REG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders |
| Operation: | write | Name: | Startup |
Value: C:\ProgramData\0433b5cdb4 | |||
| (PID) Process: | (2788) REG.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders |
| Operation: | write | Name: | Startup |
Value: C:\ProgramData\0433b5cdb4 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | 400000.nslookup.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 2856 | 400000.nslookup.exe | C:\programdata\0433b5cdb4\kntd.exe:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2684 | kntd.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 1980 | kntd.exe | C:\ProgramData\0 | — | |
MD5:— | SHA256:— | |||
| 2856 | 400000.nslookup.exe | C:\programdata\0433b5cdb4\kntd.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
1
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2684 | kntd.exe | POST | 200 | 46.166.129.157:80 | http://46.166.129.157/index.php | NL | text | 6 b | malicious |
2684 | kntd.exe | POST | 200 | 46.166.129.157:80 | http://46.166.129.157/index.php | NL | text | 6 b | malicious |
1980 | kntd.exe | POST | 200 | 46.166.129.157:80 | http://46.166.129.157/index.php | NL | text | 6 b | malicious |
2684 | kntd.exe | POST | 200 | 46.166.129.157:80 | http://46.166.129.157/index.php | NL | text | 6 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2684 | kntd.exe | 46.166.129.157:80 | — | NForce Entertainment B.V. | NL | malicious |
1980 | kntd.exe | 46.166.129.157:80 | — | NForce Entertainment B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
teredo.ipv6.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2684 | kntd.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
2684 | kntd.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |
2684 | kntd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2684 | kntd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2684 | kntd.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
2684 | kntd.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |
2684 | kntd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2684 | kntd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2684 | kntd.exe | A Network Trojan was detected | ET TROJAN Amadey CnC Check-In |
2684 | kntd.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |