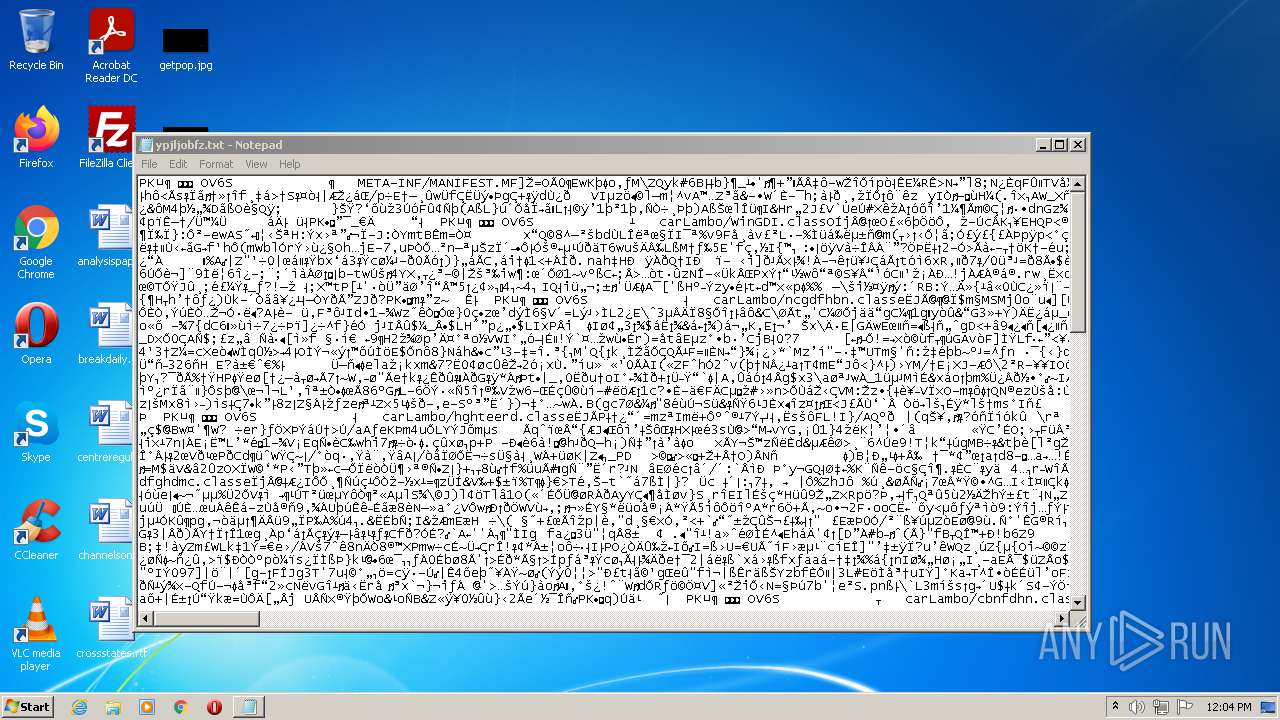
| File name: | Proof of payment.js |
| Full analysis: | https://app.any.run/tasks/beeba4f7-115e-4a2a-8de1-6f0458a5f58b |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | October 03, 2021, 11:03:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 34A653C2523056E055C378285398F72D |
| SHA1: | D9813CDA6DA576F77D09AE3665F2C0C5DD37FEF1 |
| SHA256: | 93B8B4B95575FBAEADF2548F59BFE6E9F7A540EB02A75CE575EE7662BFB6CA52 |
| SSDEEP: | 3072:o9pZV7cIa1MmOQe+rABEBj+6fXB+Tcu01xI8xE9Ye+eLvLusOTi1N253:o9PVD+OyrABEBjFBpRjeJKEN253 |
MALICIOUS
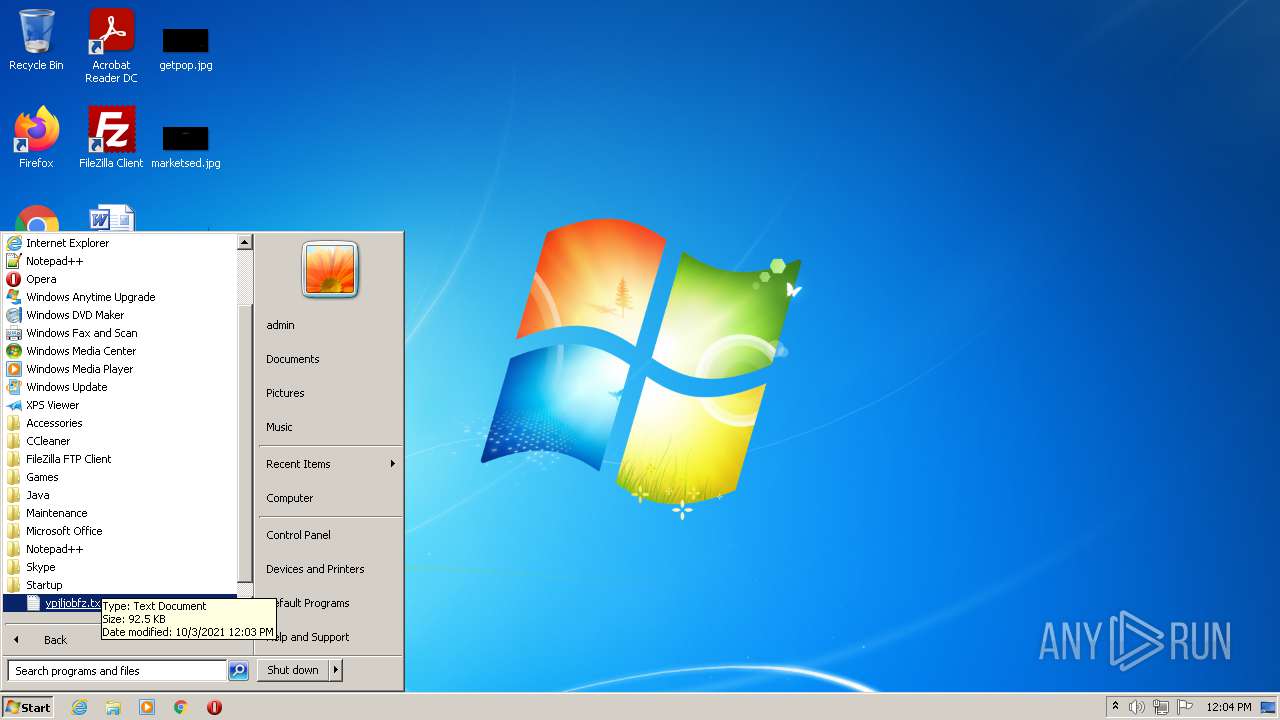
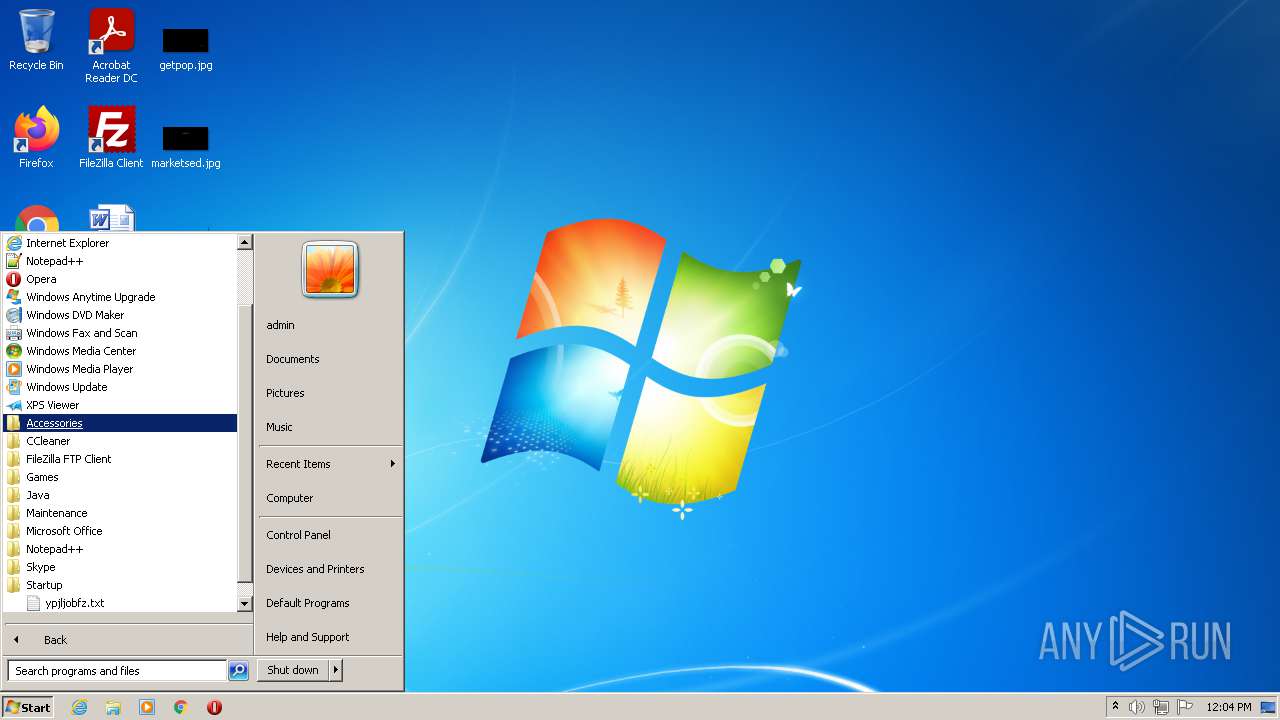
Writes to a start menu file
- java.exe (PID: 128)
Loads dropped or rewritten executable
- java.exe (PID: 128)
- java.exe (PID: 1932)
Changes the autorun value in the registry
- java.exe (PID: 128)
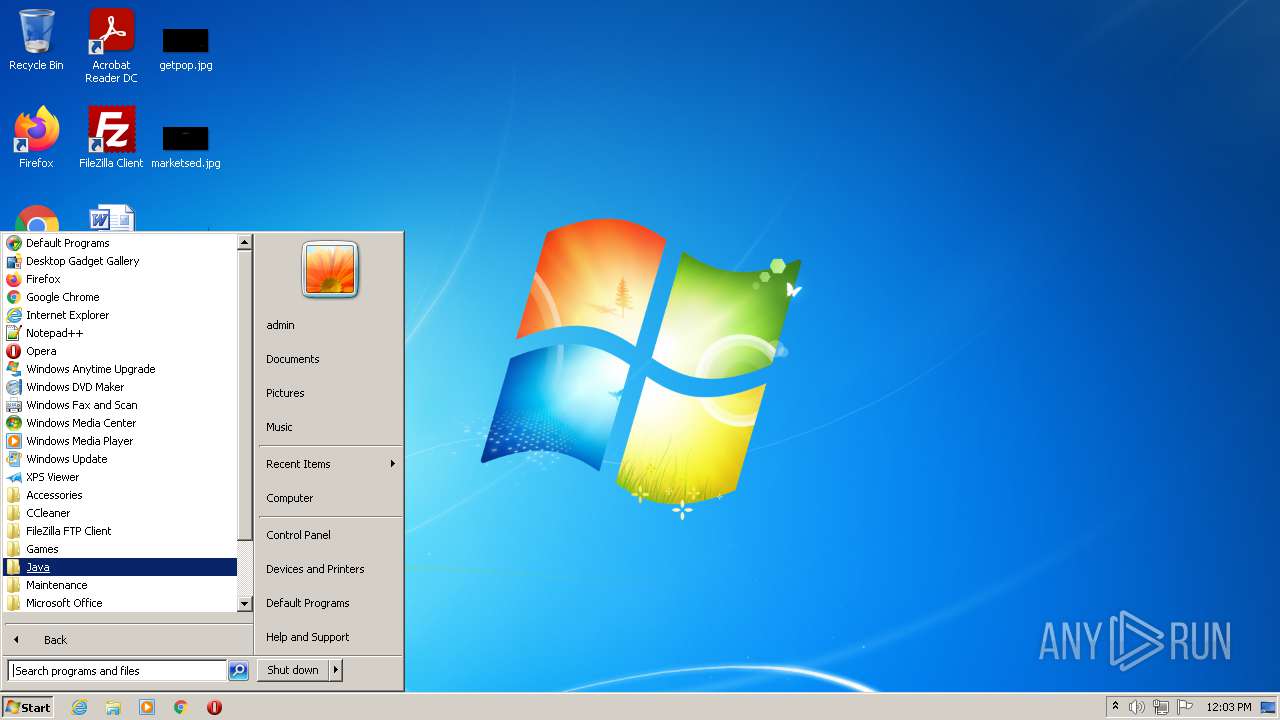
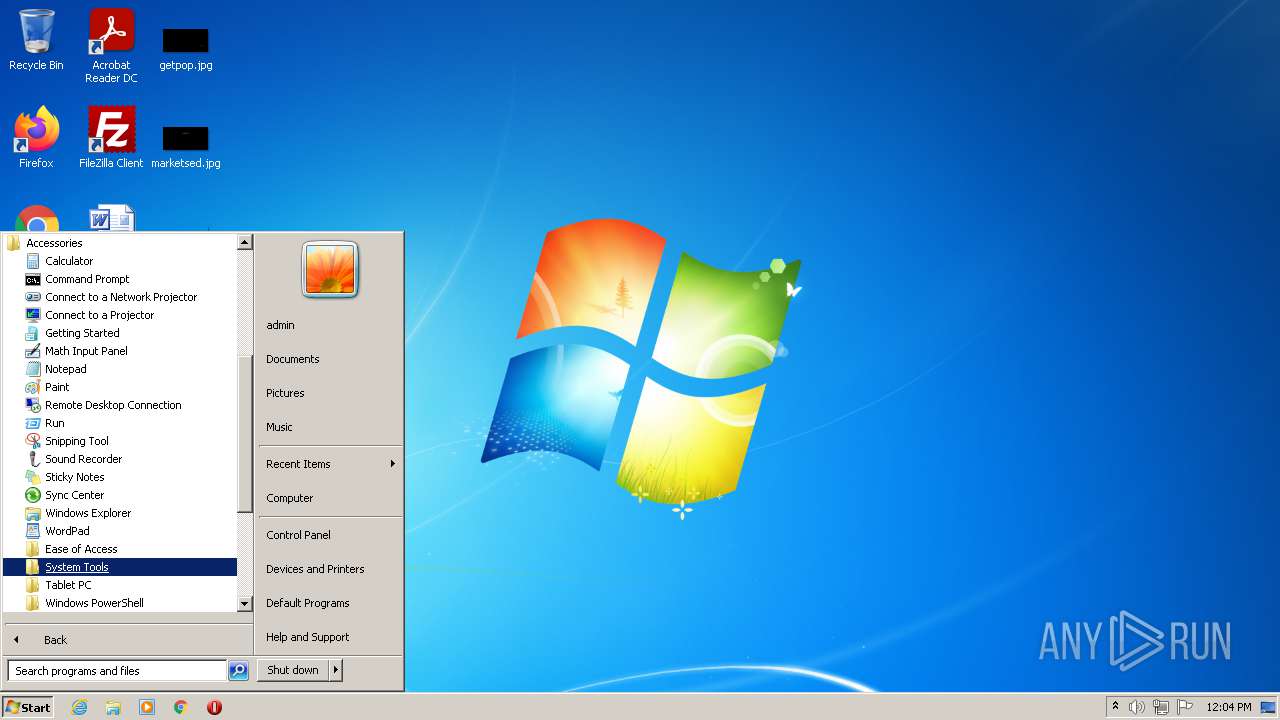
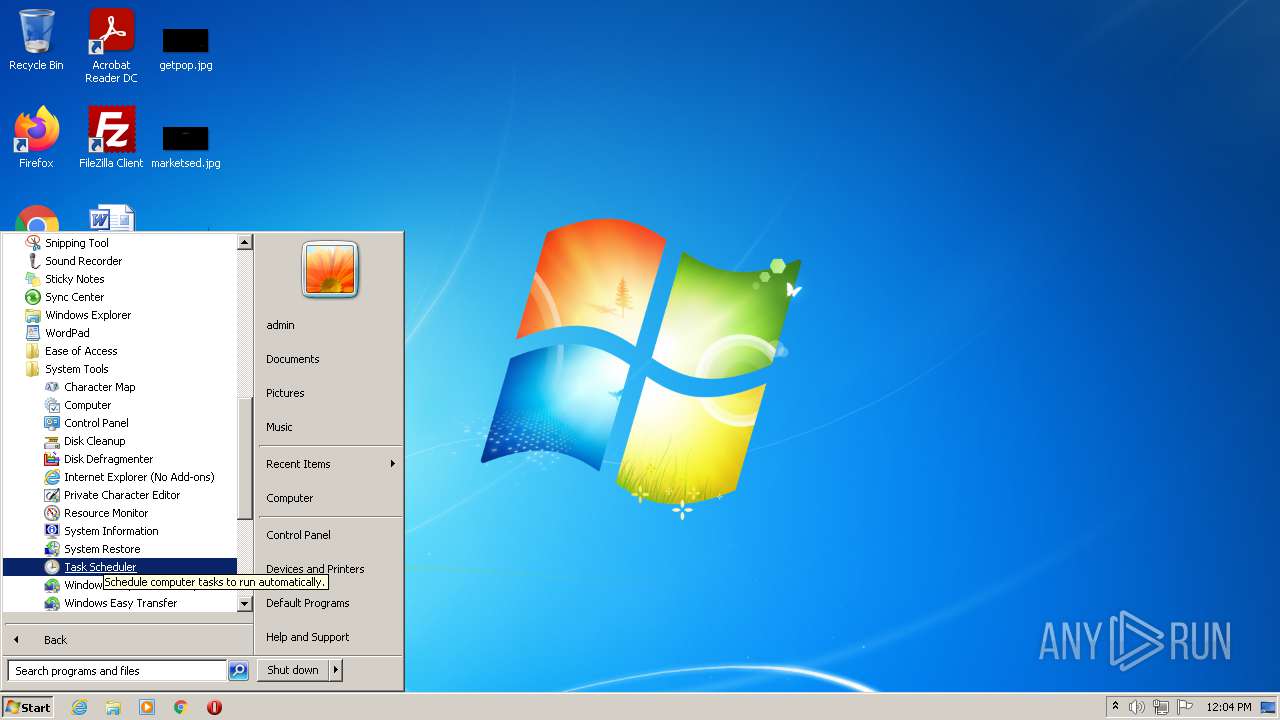
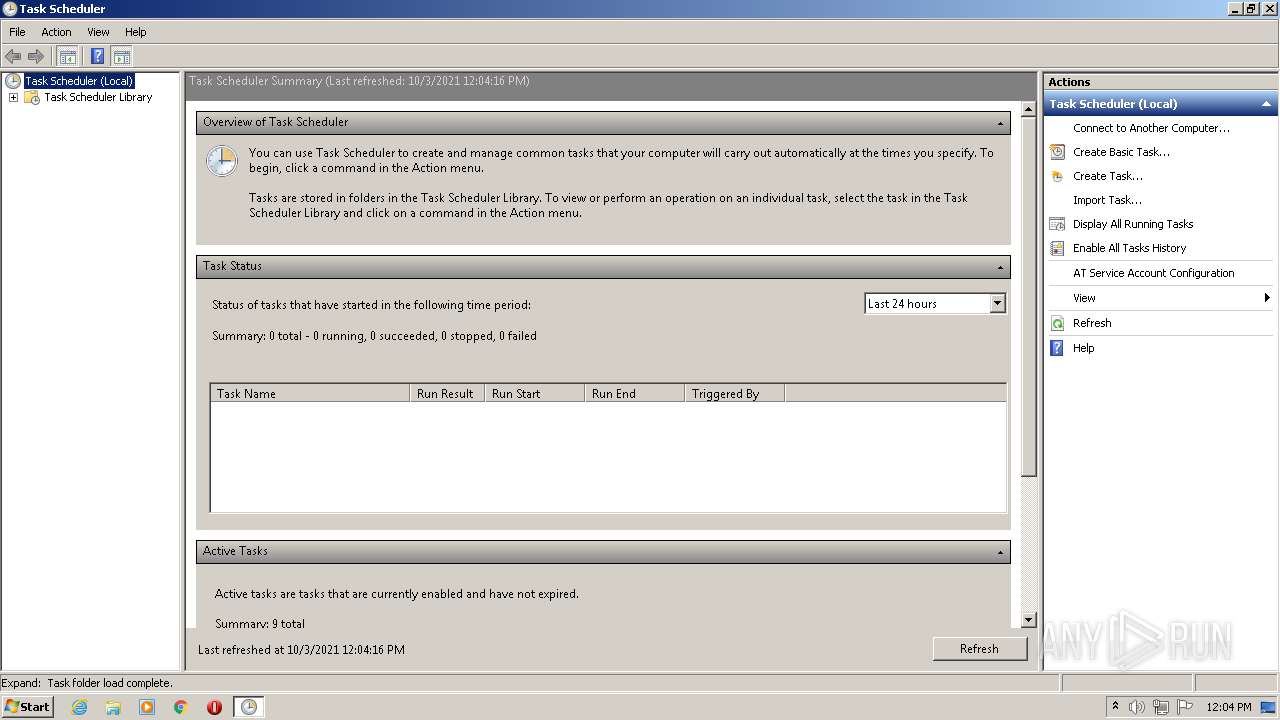
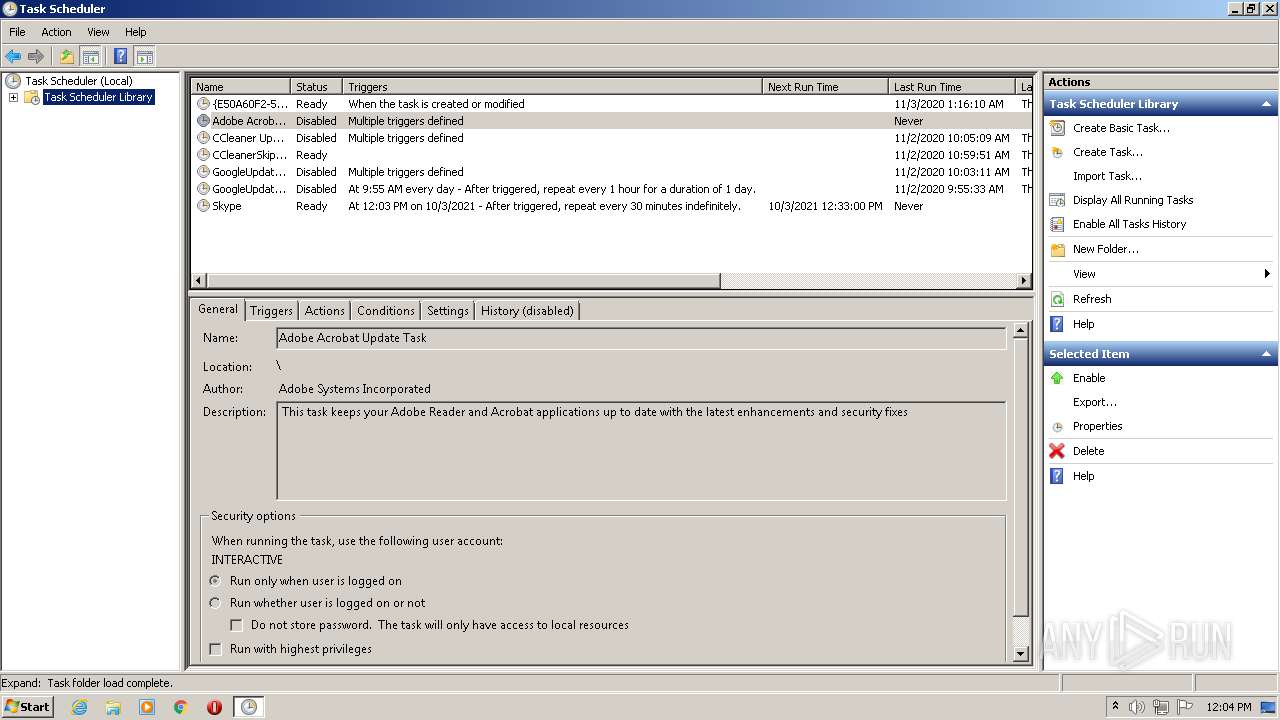
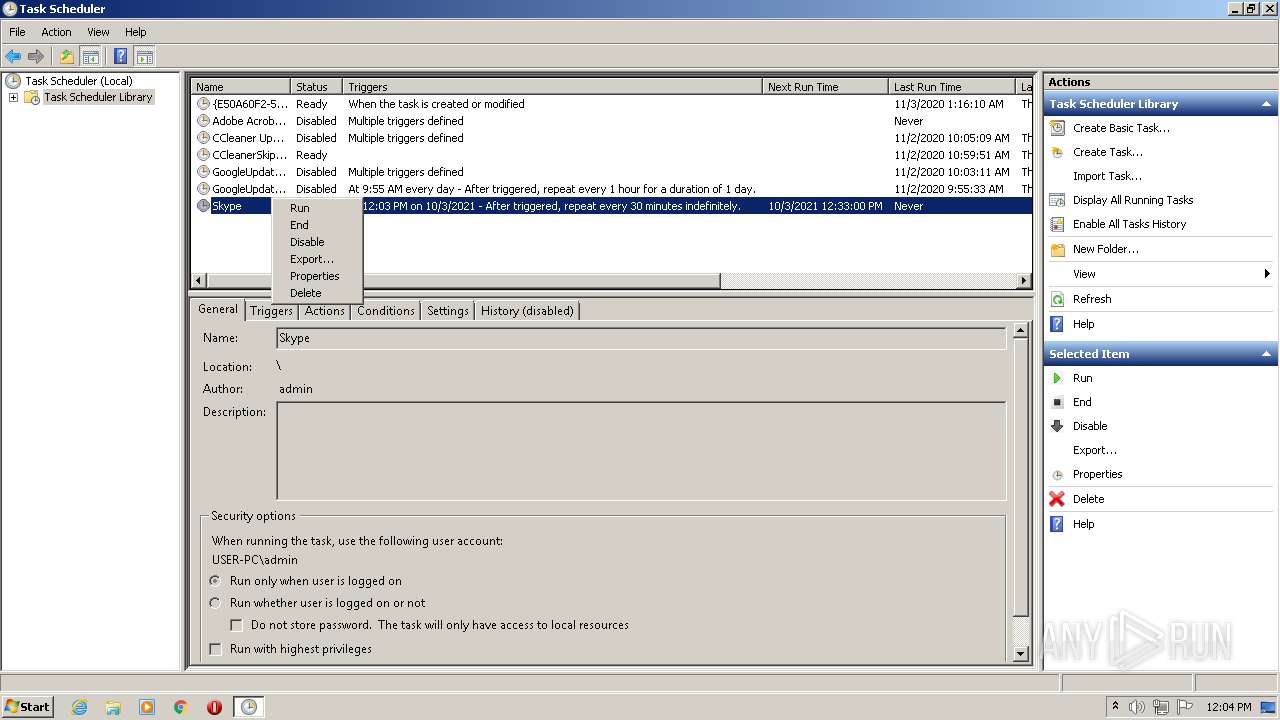
Uses Task Scheduler to run other applications
- cmd.exe (PID: 996)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3244)
- mmc.exe (PID: 2628)
STRRAT was detected
- java.exe (PID: 1932)
Connects to CnC server
- java.exe (PID: 1932)
SUSPICIOUS
Reads the computer name
- WScript.exe (PID: 3224)
- javaw.exe (PID: 2152)
- java.exe (PID: 128)
- java.exe (PID: 1932)
- WMIC.exe (PID: 4000)
- WMIC.exe (PID: 1072)
- WMIC.exe (PID: 2392)
- WMIC.exe (PID: 3092)
Checks supported languages
- WScript.exe (PID: 3224)
- javaw.exe (PID: 2152)
- java.exe (PID: 128)
- cmd.exe (PID: 996)
- java.exe (PID: 1932)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 1608)
- WMIC.exe (PID: 4000)
- WMIC.exe (PID: 1072)
- cmd.exe (PID: 1588)
- WMIC.exe (PID: 2392)
- cmd.exe (PID: 2424)
- WMIC.exe (PID: 3092)
Check for Java to be installed
- WScript.exe (PID: 3224)
Creates files in the user directory
- WScript.exe (PID: 3224)
- java.exe (PID: 128)
Creates files in the program directory
- javaw.exe (PID: 2152)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 2152)
Executes JAVA applets
- WScript.exe (PID: 3224)
- javaw.exe (PID: 2152)
- java.exe (PID: 128)
Executable content was dropped or overwritten
- java.exe (PID: 128)
- java.exe (PID: 1932)
Application launched itself
- java.exe (PID: 128)
Starts CMD.EXE for commands execution
- java.exe (PID: 128)
- java.exe (PID: 1932)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 1608)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 1588)
- cmd.exe (PID: 2424)
Uses WMIC.EXE to obtain a list of AntiViruses
- cmd.exe (PID: 3968)
Executed via Task Scheduler
- NOTEPAD.EXE (PID: 2388)
Checks for external IP
- java.exe (PID: 1932)
INFO
Checks supported languages
- icacls.exe (PID: 3800)
- schtasks.exe (PID: 3244)
- mmc.exe (PID: 2628)
- NOTEPAD.EXE (PID: 2388)
Checks Windows Trust Settings
- WScript.exe (PID: 3224)
Reads the computer name
- icacls.exe (PID: 3800)
- schtasks.exe (PID: 3244)
- mmc.exe (PID: 2628)
Manual execution by user
- mmc.exe (PID: 2628)
- mmc.exe (PID: 3524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
18
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Java\jre1.8.0_271\bin\java.exe" -jar "C:\Users\admin\ypjljobfz.txt" | C:\Program Files\Java\jre1.8.0_271\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 996 | cmd /c schtasks /create /sc minute /mo 30 /tn Skype /tr "C:\Users\admin\AppData\Roaming\ypjljobfz.txt" | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1072 | wmic /node:localhost /namespace:'\\root\securitycenter' path antivirusproduct get displayname /format:list | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1588 | cmd.exe /c "wmic /node:. /namespace:'\\root\cimv2' path win32_logicaldisk get volumeserialnumber /format:list" | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1608 | cmd.exe /c "wmic /node:. /namespace:'\\root\cimv2' path win32_operatingsystem get version /format:list" | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Java\jre1.8.0_271\bin\java.exe" -jar "C:\Users\admin\AppData\Roaming\ypjljobfz.txt" | C:\Program Files\Java\jre1.8.0_271\bin\java.exe | java.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\AppData\Roaming\ypjljobfz.txt" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | WScript.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2388 | C:\Windows\system32\NOTEPAD.EXE "C:\Users\admin\AppData\Roaming\ypjljobfz.txt" | C:\Windows\system32\NOTEPAD.EXE | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2392 | wmic /node:. /namespace:'\\root\cimv2' path win32_logicaldisk get volumeserialnumber /format:list | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | cmd.exe /c "wmic /node:. /namespace:'\\root\cimv2' path win32_operatingsystem get caption,OSArchitecture /format:list" | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 319
Read events
3 306
Write events
12
Delete events
1
Modification events
| (PID) Process: | (3224) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3224) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3224) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3224) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (128) java.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ypjljobfz |
Value: "C:\Users\admin\AppData\Roaming\ypjljobfz.txt" | |||
| (PID) Process: | (2628) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | HelpTopic |
Value: C:\Windows\Help\taskscheduler.chm | |||
| (PID) Process: | (2628) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | LinkedHelpTopics |
Value: C:\Windows\Help\taskscheduler.chm | |||
| (PID) Process: | (2628) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2628) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File1 |
Value: C:\Windows\system32\taskschd.msc | |||
Executable files
8
Suspicious files
9
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:— | SHA256:— | |||
| 2152 | javaw.exe | C:\Users\admin\ypjljobfz.txt | compressed | |
MD5:— | SHA256:— | |||
| 128 | java.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\ypjljobfz.txt | compressed | |
MD5:— | SHA256:— | |||
| 2628 | mmc.exe | C:\Users\admin\AppData\Roaming\Microsoft\MMC\taskschd | xml | |
MD5:— | SHA256:— | |||
| 3224 | WScript.exe | C:\Users\admin\AppData\Roaming\ypjljobfz.txt | compressed | |
MD5:— | SHA256:— | |||
| 2152 | javaw.exe | C:\Users\admin\lib\sqlite-jdbc-3.14.2.1.jar | compressed | |
MD5:B33387E15AB150A7BF560ABDC73C3BEC | SHA256:2EAE3DEA1C3DDE6104C49F9601074B6038FF6ABCF3BE23F4B56F6720A4F6A491 | |||
| 2152 | javaw.exe | C:\Users\admin\lib\jna-5.5.0.jar | java | |
MD5:ACFB5B5FD9EE10BF69497792FD469F85 | SHA256:B308FAEBFE4ED409DE8410E0A632D164B2126B035F6EACFF968D3908CAFB4D9E | |||
| 2152 | javaw.exe | C:\Users\admin\lib\system-hook-3.5.jar | compressed | |
MD5:E1AA38A1E78A76A6DE73EFAE136CDB3A | SHA256:2DDDA8AF6FAEF8BDE46ACF43EC546603180BCF8DCB2E5591FFF8AC9CD30B5609 | |||
| 2152 | javaw.exe | C:\Users\admin\lib\system-hook-3.5.jard | compressed | |
MD5:E1AA38A1E78A76A6DE73EFAE136CDB3A | SHA256:2DDDA8AF6FAEF8BDE46ACF43EC546603180BCF8DCB2E5591FFF8AC9CD30B5609 | |||
| 128 | java.exe | C:\Users\admin\AppData\Roaming\lib\jna-5.5.0.jar | java | |
MD5:ACFB5B5FD9EE10BF69497792FD469F85 | SHA256:B308FAEBFE4ED409DE8410E0A632D164B2126B035F6EACFF968D3908CAFB4D9E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
6
Threats
61
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1932 | java.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | text | 299 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2152 | javaw.exe | 185.199.108.154:443 | github-releases.githubusercontent.com | GitHub, Inc. | NL | suspicious |
2152 | javaw.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
1932 | java.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
1932 | java.exe | 31.210.20.226:3608 | harold.ns01.info | — | — | malicious |
2152 | javaw.exe | 199.232.192.209:443 | repo1.maven.org | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
repo1.maven.org |
| whitelisted |
github.com |
| malicious |
github-releases.githubusercontent.com |
| whitelisted |
str-master.pw |
| malicious |
harold.ns01.info |
| malicious |
ip-api.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
1932 | java.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
1932 | java.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1932 | java.exe | A Network Trojan was detected | ET TROJAN STRRAT CnC Checkin |
1932 | java.exe | A Network Trojan was detected | ET TROJAN STRRAT CnC Checkin |
1932 | java.exe | A Network Trojan was detected | ET TROJAN STRRAT CnC Checkin |
1932 | java.exe | A Network Trojan was detected | ET TROJAN STRRAT CnC Checkin |
1932 | java.exe | A Network Trojan was detected | ET TROJAN STRRAT CnC Checkin |
1932 | java.exe | A Network Trojan was detected | ET TROJAN STRRAT CnC Checkin |
1932 | java.exe | A Network Trojan was detected | ET TROJAN STRRAT CnC Checkin |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|