| File name: | 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe |
| Full analysis: | https://app.any.run/tasks/ecdb6ae1-2196-4048-acbb-d7912dda2c67 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | June 19, 2019, 06:11:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9052EE928E7E6CE3BEDB56F4407CCD80 |
| SHA1: | 41258D89B718E3C43DE2689C216AF2D2E13C9B77 |
| SHA256: | 932E008A1D2A416C098C55A68D9D740B010EE583D7731B0819C0331D18DA89A7 |
| SSDEEP: | 6144:9QrKSY0vpByFJwVF+PqzGPpwlDnihRThmd2HKl:aAWyFJGcPqzGBwln0wd |
MALICIOUS
Application was dropped or rewritten from another process
- obj2unpurchased.exe (PID: 2844)
- obj2unpurchased.exe (PID: 2524)
- obj2unpurchased.exe (PID: 3496)
- obj2unpurchased.exe (PID: 2056)
- obj2unpurchased.exe (PID: 1004)
- images.exe (PID: 1356)
- images.exe (PID: 2848)
- obj2unpurchased.exe (PID: 3620)
Changes the autorun value in the registry
- obj2unpurchased.exe (PID: 3496)
- obj2unpurchased.exe (PID: 1004)
- obj2unpurchased.exe (PID: 2844)
AVEMARIA was detected
- obj2unpurchased.exe (PID: 3620)
Connects to CnC server
- obj2unpurchased.exe (PID: 3620)
SUSPICIOUS
Application launched itself
- 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe (PID: 2140)
- obj2unpurchased.exe (PID: 2844)
- obj2unpurchased.exe (PID: 3496)
- obj2unpurchased.exe (PID: 2056)
- images.exe (PID: 1356)
- obj2unpurchased.exe (PID: 2524)
Starts itself from another location
- images.exe (PID: 2848)
- obj2unpurchased.exe (PID: 1004)
Executable content was dropped or overwritten
- 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe (PID: 3880)
- obj2unpurchased.exe (PID: 1004)
Creates files in the user directory
- obj2unpurchased.exe (PID: 1004)
Reads the machine GUID from the registry
- obj2unpurchased.exe (PID: 3620)
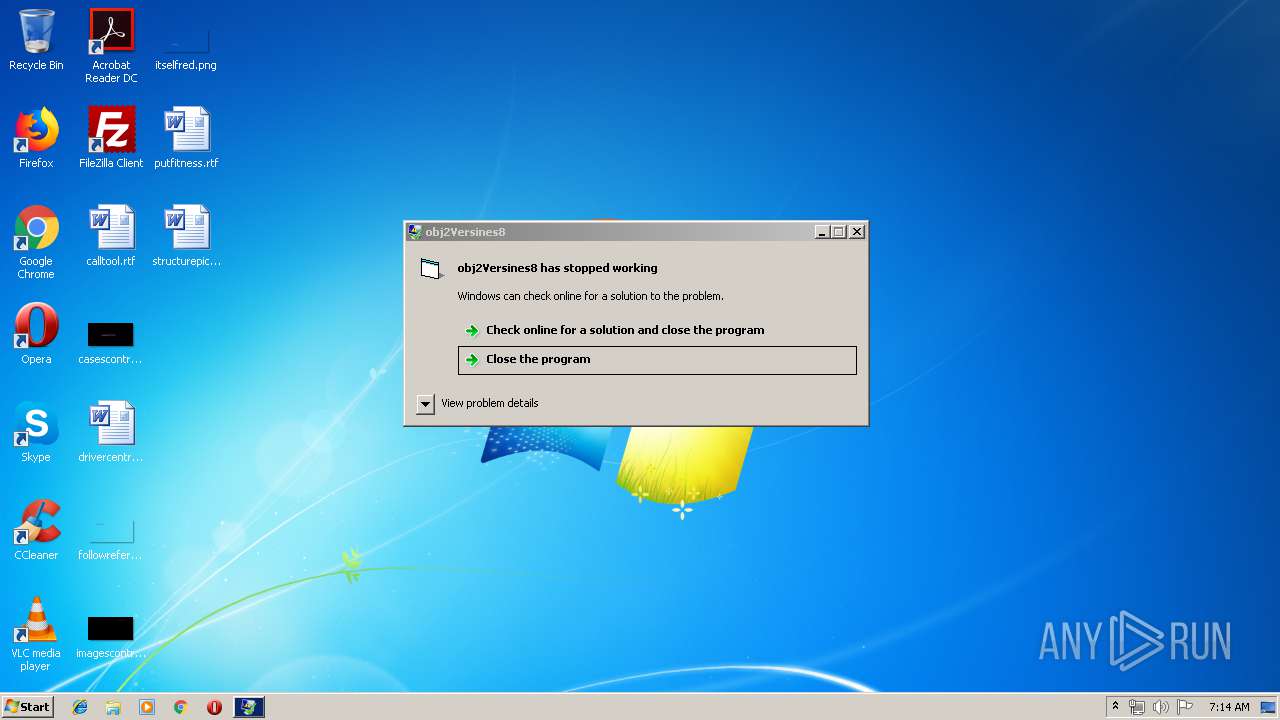
INFO
Application was crashed
- obj2unpurchased.exe (PID: 3620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:01:01 02:23:22+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 372736 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x156c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | PiOnEEr |
| ProductName: | obj2Versines8 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | obj2Sultet4 |
| OriginalFileName: | obj2Sultet4.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-2008 01:23:22 |
| Detected languages: |
|
| CompanyName: | PiOnEEr |
| ProductName: | obj2Versines8 |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | obj2Sultet4 |
| OriginalFilename: | obj2Sultet4.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Jan-2008 01:23:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0005ABEC | 0x0005B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.24643 |
.data | 0x0005C000 | 0x00003738 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00060000 | 0x00000950 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.03122 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.2228 | 556 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
7 | 0.545897 | 36 | Unicode (UTF 16LE) | Konkani - India | RT_STRING |
30001 | 2.57965 | 304 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 1.76987 | 744 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30003 | 2.07177 | 296 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
42
Monitored processes
10
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1004 | "C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe" | C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe | obj2unpurchased.exe | ||||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1356 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | — | obj2unpurchased.exe | |||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe" | C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe | — | obj2unpurchased.exe | |||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe" | C:\Users\admin\AppData\Local\Temp\932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | — | explorer.exe | |||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2524 | "C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe" | C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe | — | obj2unpurchased.exe | |||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2844 | "C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe" | C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe | images.exe | ||||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2848 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | — | images.exe | |||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe" | C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe | 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | ||||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3620 | "C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe" | C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe | obj2unpurchased.exe | ||||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 3221225477 Version: 1.00 Modules
| |||||||||||||||
| 3880 | "C:\Users\admin\AppData\Local\Temp\932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe" | C:\Users\admin\AppData\Local\Temp\932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | ||||||||||||
User: admin Company: PiOnEEr Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
237
Read events
221
Write events
16
Delete events
0
Modification events
| (PID) Process: | (3880) 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3880) 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3496) obj2unpurchased.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | obj2Counterconditioning |
Value: wscript "C:\Users\admin\AppData\Local\Temp\obj2unpurchased.vbs" | |||
| (PID) Process: | (1004) obj2unpurchased.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (1004) obj2unpurchased.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (1004) obj2unpurchased.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\WSIGXSJW9S |
| Operation: | write | Name: | inst |
Value: 390623963CFFFF942FDFB94CEFDE61E46B1E235920E044611BF9010B997296DE2570E0A67B998D8364B4D2FA7673FCA3CECE3E4B6CB0D6E948E4B454F0FDCF59B4A386C66AA9A37882C3E68398D8575FB1ADAEB2 | |||
| (PID) Process: | (1004) obj2unpurchased.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Images |
Value: C:\Users\admin\AppData\Roaming\images.exe | |||
| (PID) Process: | (2848) images.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2848) images.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2844) obj2unpurchased.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | obj2Counterconditioning |
Value: wscript "C:\Users\admin\AppData\Local\Temp\obj2unpurchased.vbs" | |||
Executable files
2
Suspicious files
0
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | C:\Users\admin\AppData\Local\Temp\obj2unpurchased.exe | executable | |
MD5:— | SHA256:— | |||
| 3880 | 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | C:\Users\admin\AppData\Local\Temp\obj2unpurchased.vbs | text | |
MD5:— | SHA256:— | |||
| 1004 | obj2unpurchased.exe | C:\Users\admin\AppData\Roaming\images.exe | executable | |
MD5:— | SHA256:— | |||
| 2140 | 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 3880 | 932e008a1d2a416c098c55a68d9d740b010ee583d7731b0819c0331d18da89a7.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 3496 | obj2unpurchased.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 2844 | obj2unpurchased.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 1356 | images.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 2848 | images.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 2524 | obj2unpurchased.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
2
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3620 | obj2unpurchased.exe | 173.254.223.74:1605 | idts.warzonedns.com | QuadraNet, Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
idts.warzonedns.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3620 | obj2unpurchased.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
3620 | obj2unpurchased.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
3 ETPRO signatures available at the full report