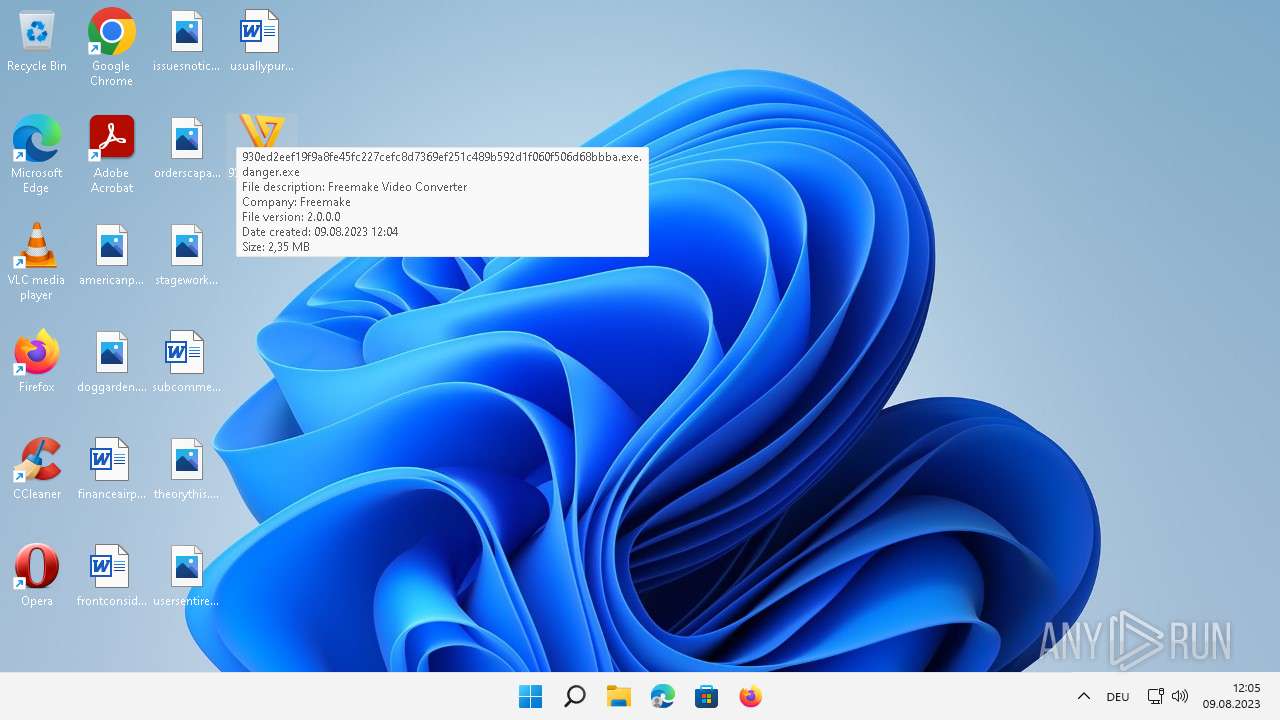
| File name: | 930ed2eef19f9a8fe45fc227cefc8d7369ef251c489b592d1f060f506d68bbba.exe.danger |
| Full analysis: | https://app.any.run/tasks/d9610f82-23fa-4d50-adfe-a49de265c3e5 |
| Verdict: | Malicious activity |
| Threats: | Parallax RAT is a versatile malware capable of stealing credentials, recording keystrokes, capturing screenshots, and exfiltrating sensitive data. It hides under legitimate processes like Notepad, uses diverse communication channels, and establishes persistence to maintain control over infected machines. |
| Analysis date: | August 09, 2023, 10:03:42 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F6637DD80C1BF55FDF7D31F1D857A155 |
| SHA1: | E7504EFA854C5C6B8DC423D2FE5ACE59B270B18B |
| SHA256: | 930ED2EEF19F9A8FE45FC227CEFC8D7369EF251C489B592D1F060F506D68BBBA |
| SSDEEP: | 49152:Ayr13C8ZAInUxXaqHBkuluNH3iYGnFDB9KYl+NVoQ8ngkfWEGWDv3XPjVAjknL2Z:717ZAIwXaqHJluNH3iY+DL6NVX8ngkf6 |
MALICIOUS
Create files in the Startup directory
- dllhost.exe (PID: 3496)
PARALLAX was detected
- pipanel.exe (PID: 1576)
SUSPICIOUS
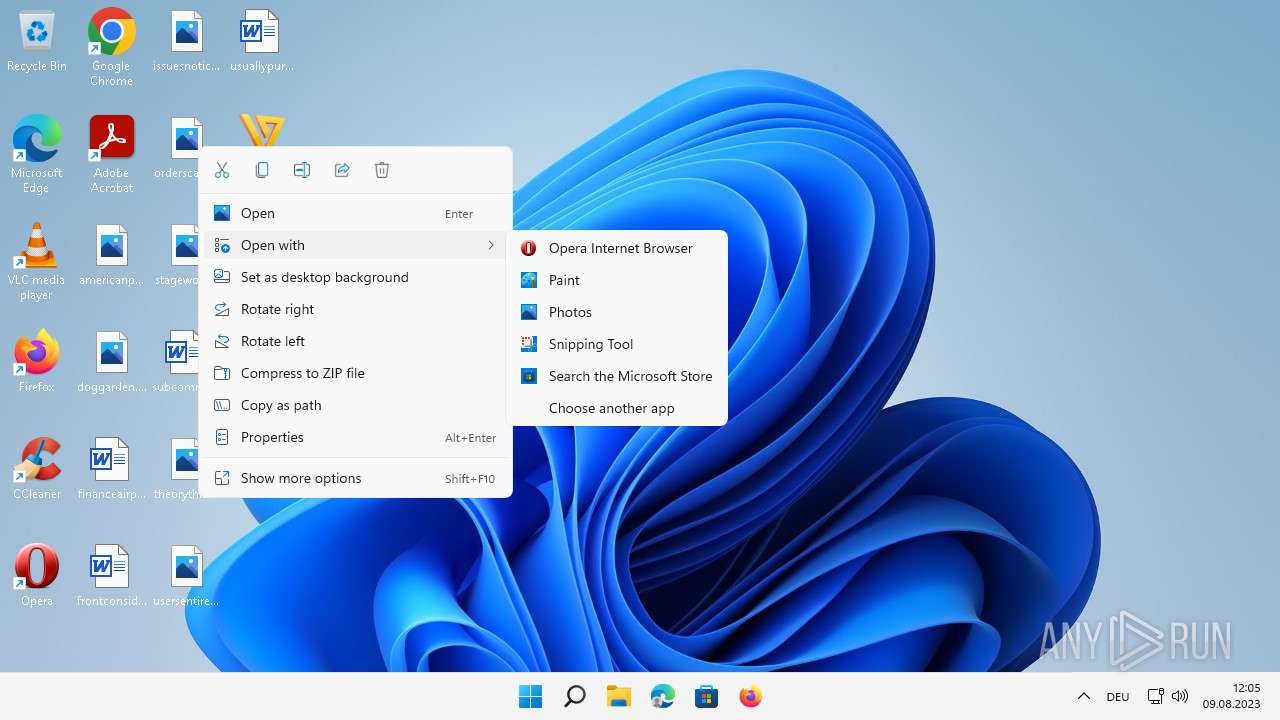
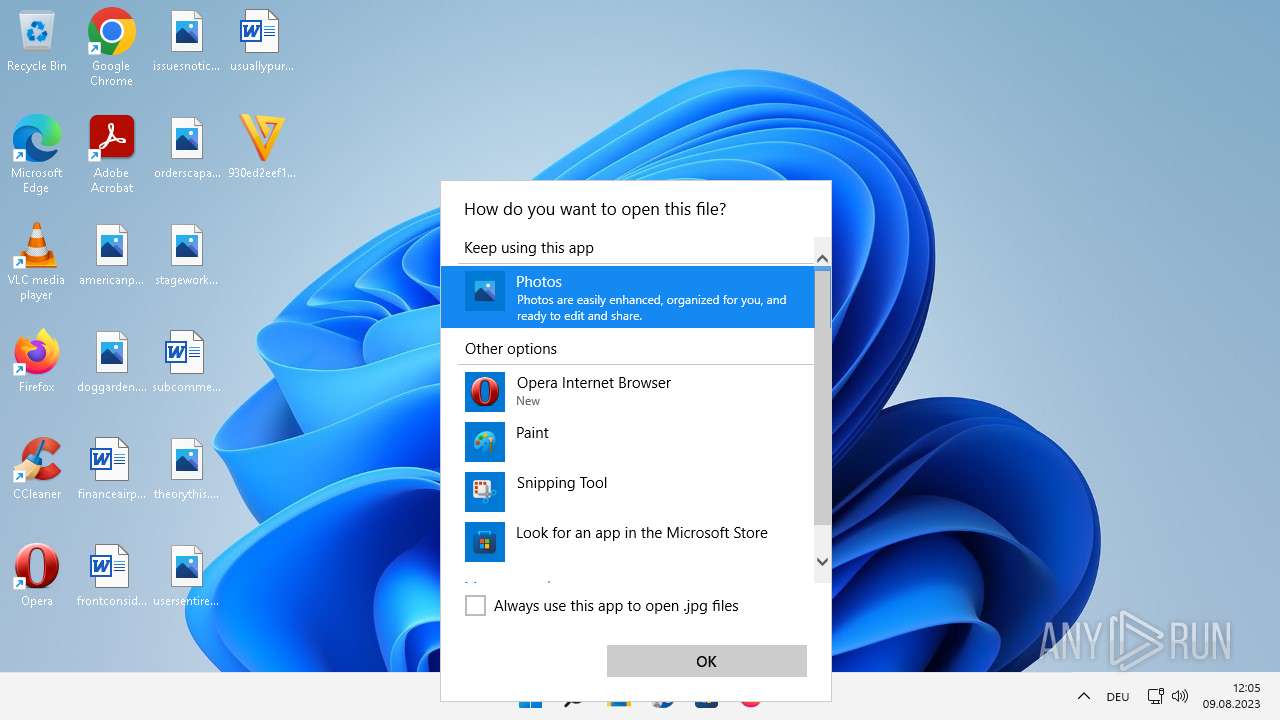
Reads the Internet Settings
- mspaint.exe (PID: 7084)
- OpenWith.exe (PID: 5596)
INFO
The process checks LSA protection
- 930ed2eef19f9a8fe45fc227cefc8d7369ef251c489b592d1f060f506d68bbba.exe.danger.exe (PID: 6540)
- dllhost.exe (PID: 3496)
- dllhost.exe (PID: 5924)
- mspaint.exe (PID: 7084)
- FileCoAuth.exe (PID: 1852)
- OpenWith.exe (PID: 5596)
Reads the computer name
- pipanel.exe (PID: 1576)
- 930ed2eef19f9a8fe45fc227cefc8d7369ef251c489b592d1f060f506d68bbba.exe.danger.exe (PID: 6540)
- mspaint.exe (PID: 7084)
- FileCoAuth.exe (PID: 1852)
- pipanel.exe (PID: 5472)
Checks supported languages
- pipanel.exe (PID: 1576)
- 930ed2eef19f9a8fe45fc227cefc8d7369ef251c489b592d1f060f506d68bbba.exe.danger.exe (PID: 6540)
- exgssi.exe (PID: 3740)
- pipanel.exe (PID: 5472)
- mspaint.exe (PID: 7084)
- FileCoAuth.exe (PID: 1852)
Creates files or folders in the user directory
- dllhost.exe (PID: 3496)
- FileCoAuth.exe (PID: 1852)
Manual execution by a user
- WINWORD.EXE (PID: 4708)
- WINWORD.EXE (PID: 2888)
- exgssi.exe (PID: 3740)
Reads Environment values
- pipanel.exe (PID: 5472)
- pipanel.exe (PID: 1576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 2.0.0.0 |
|---|---|
| ProductName: | Freemake Video Converter |
| OriginalFileName: | FreemakeStarter.Converter.exe |
| LegalCopyright: | Copyright © Freemake 2010-2019 |
| InternalName: | Freemake Video Converter |
| FileVersion: | 2.0.0.0 |
| FileDescription: | Freemake Video Converter |
| CompanyName: | Freemake |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 2.0.0.0 |
| FileVersionNumber: | 2.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0xf773f |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1089024 |
| CodeSize: | 1155072 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2022:12:26 06:42:31+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Dec-2022 06:42:31 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Freemake |
| FileDescription: | Freemake Video Converter |
| FileVersion: | 2.0.0.0 |
| InternalName: | Freemake Video Converter |
| LegalCopyright: | Copyright © Freemake 2010-2019 |
| OriginalFilename: | FreemakeStarter.Converter.exe |
| ProductName: | Freemake Video Converter |
| ProductVersion: | 2.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 26-Dec-2022 06:42:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00119F57 | 0x0011A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52648 |
.rdata | 0x0011B000 | 0x00042784 | 0x00042800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00242 |
.data | 0x0015E000 | 0x0000D6FC | 0x00005C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.69286 |
.rsrc | 0x0016C000 | 0x00097D28 | 0x00097E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.86796 |
.reloc | 0x00204000 | 0x00029B58 | 0x00029C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.86158 |
imhkvfk | 0x0022E000 | 0x000350B8 | 0x00035200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.98197 |
.deena | 0x00264000 | 0x0000105C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.24601 |
.brena | 0x00266000 | 0x00000200 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.23647 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.25711 | 832 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 3.90067 | 9640 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 4.05091 | 4264 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 4.40757 | 1128 | Latin 1 / Western European | Russian - Russia | RT_ICON |
5 | 3.02695 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 3.85367 | 1184 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 4.20102 | 338 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 2.51649 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
10 | 2.45401 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMDLG32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
243
Monitored processes
13
Malicious processes
1
Suspicious processes
1
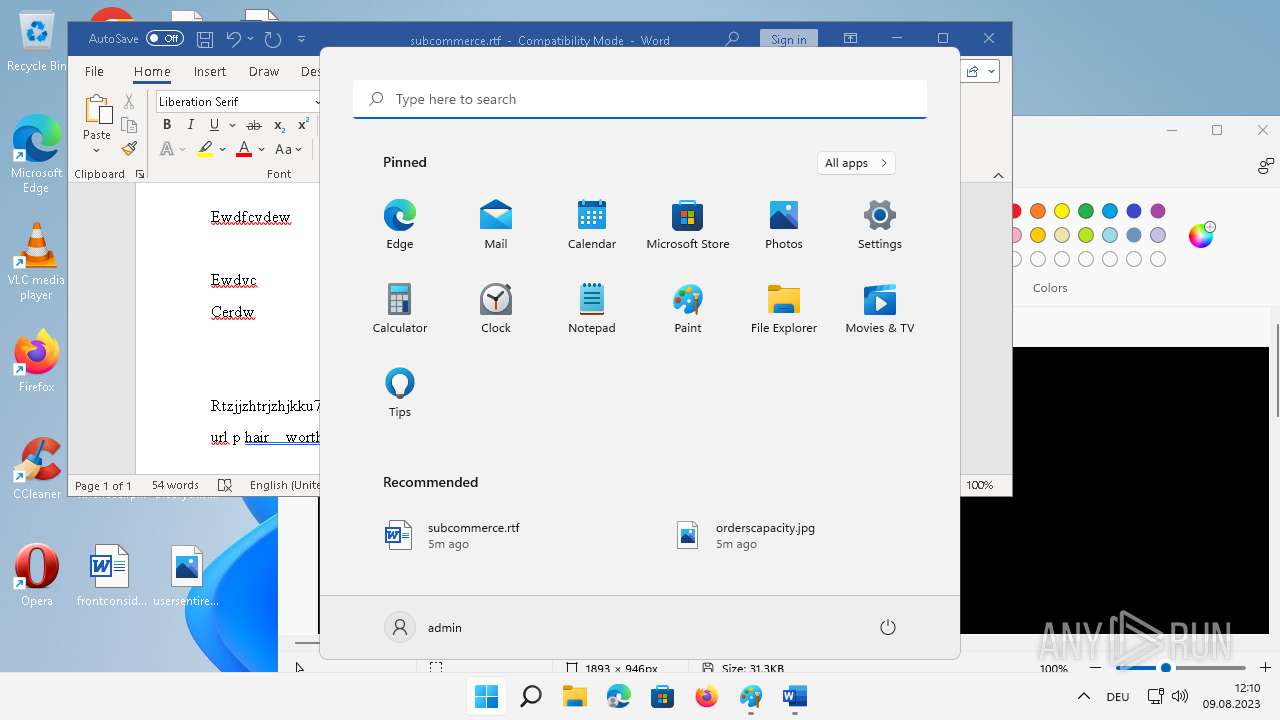
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\Microsoft Office\root\vfs\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "7FCEFB5F-0E6A-4166-88C3-8845ED8FAB5C" "FE5739A9-B277-4572-B6FC-05D551B4FBDD" "2888" "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" | C:\Program Files\Microsoft Office\root\vfs\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 0 Version: 0.14.4.0 Modules
| |||||||||||||||
| 1576 | "C:\Users\admin\Desktop\930ed2eef19f9a8fe45fc227cefc8d7369ef251c489b592d1f060f506d68bbba.exe.danger.exe" | C:\Program Files (x86)\Common Files\Microsoft Shared\ink\pipanel.exe | 930ed2eef19f9a8fe45fc227cefc8d7369ef251c489b592d1f060f506d68bbba.exe.danger.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Tablet PC Component Exit code: 1073807364 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1852 | "C:\Program Files (x86)\Microsoft OneDrive\22.077.0410.0007\FileCoAuth.exe" -Embedding | C:\Program Files (x86)\Microsoft OneDrive\22.077.0410.0007\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 22.077.0410.0007 Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\subcommerce.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 16.0.16626.20134 Modules
| |||||||||||||||
| 3496 | C:\Windows\SysWOW64\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3740 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\exgssi.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\exgssi.exe | — | explorer.exe | |||||||||||
User: admin Company: Freemake Integrity Level: MEDIUM Description: Freemake Video Converter Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 4708 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n "C:\Users\admin\Desktop\subcommerce.rtf" /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 1073807364 Version: 16.0.16626.20134 Modules
| |||||||||||||||
| 5248 | "C:\Program Files\Microsoft Office\root\vfs\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "2324187B-8B53-4902-A92B-1A50D81ABCBC" "CDF02A1A-A112-4AFD-BBDF-069298CE8397" "4708" "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" | C:\Program Files\Microsoft Office\root\vfs\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Exit code: 1073807364 Version: 0.14.4.0 Modules
| |||||||||||||||
| 5472 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\exgssi.exe" | C:\Program Files (x86)\Common Files\Microsoft Shared\ink\pipanel.exe | — | exgssi.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Tablet PC Component Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5596 | C:\Windows\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 098
Read events
30 827
Write events
210
Delete events
61
Modification events
| (PID) Process: | (5596) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5596) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5596) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5596) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (5596) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Zvpebfbsg.Cnvag_8jrxlo3q8oojr!Ncc |
Value: 000000000700000007000000289A0100000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF9C66D6998A2AD80100000000 | |||
| (PID) Process: | (5596) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000BE010000860300005C4C9501740000007F000000512F35004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E004500780070006C006F00720065007200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000740000007F000000512F35004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E004500780070006C006F00720065007200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000740000007F000000512F35004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E004500780070006C006F00720065007200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5596) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Zvpebfbsg.Cnvag_8jrxlo3q8oojr!Ncc |
Value: 000000000800000007000000289A0100000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFC05A5900A9CAD90100000000 | |||
| (PID) Process: | (5596) OpenWith.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000BF010000860300005C4C9501740000007F000000512F35004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E004500780070006C006F00720065007200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000740000007F000000512F35004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E004500780070006C006F00720065007200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000740000007F000000512F35004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E004500780070006C006F00720065007200000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5596) OpenWith.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Software\Microsoft\TIP\AggregateResults |
| Operation: | write | Name: | data |
Value: D9A7A80101000300EC03F46F000000002100000000000000D9A7A80102000800BAF9F550000000000A0000000000000049A8A801010203005C4614A6000000005300000000000000D1A8A8010102030064B65611000000001B02000001000000D1A8A80101000400FB3B54EB0000000074000000080000007545B801010002002972674D0000000002000000780C0000C8CCB901010000809261763600000000060000002D010000AFFBB9010100008055161AFB0000000002000000045B00004428C30101000080469996A2000000009A000000191100004428C30104000100541F4AF40000000009000000000000002C06D801010004008A1488B400000000010000002E0000004245D90101000700436CB73F0000000001000000B00700009F49DD010100008045734BE100000000D1000000000000006A44DF010100008054528C5D0000000002000000C600000081F7E10104000100C177129C00000000860000002300000081F7E101040002002AF214C2000000002100000069010000D81BE20104000500FCAC50C7000000000200000000000000AA26E701010000801490D0EE010000000100000008000000AA26E701010000801490D0EE020000000F0000006F000000DA49E80101000080C483AE790000000002000000820100007FE9E9010200050089B029380000000007000000B5010000C527EB01010000804B8D54FB000000000F000000A4000000510DED01010000801F39C11D0000000001000000A50000007C22ED01017F0080FE0EED550000000001000000100000008C5FF2010100030025B04D21000000000D00000039000000BA0BF30101000000248CDFD400000000040000008E0000006EFCF3010100010079586E990000000012000000880200006EFCF30101000200E2D270BF000000001C000000180200006EFCF301017F03004B4D73E50000000075080000EE0C00006EFCF30101000080105E37360000000086080000660000003F0EF40101000080E58C865C00000000CC00000099020000EE8FF801010000809096E6C20000000006000000E8000000E5140102017F00806B2E50070000000004000000390100003D4A060201000080C39240F000000000080000004A000000564A060201000080784A674B000000000200000041000000BFDE08020100008065B49D6B000000000D0000001A00000044240E020100008046DDF50500000000020000000900000044240E02040001005463A9570000000002000000000000005F37110201000080856D77FF0000000008000000F900000088531E0203000100A5067F52000000000200000061000000A410270201000080260FB9F9000000003F00000082000000FDBE49020302030002B3A81C000000000400000062000000FDBE490203001740163625F3000000000100000006000000 | |||
| (PID) Process: | (4708) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 016411000000001000AE4EF13C07000000000000000700000000000000 | |||
Executable files
2
Suspicious files
35
Text files
884
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4708 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:90D711CE78F0FF7228D4CE1539D77DE3 | SHA256:AA200F4710F89CF4059E81180649CDD844E21B7764B7B4D06EE42FC224610FD6 | |||
| 4708 | WINWORD.EXE | C:\Users\admin\Desktop\~$bcommerce.rtf | binary | |
MD5:C75ED28C6CD047ABB208710354F7201B | SHA256:9280EE0F03E90EE9BA3EC79859A156CBEA34CF4AD937720C1BDDAFEC6B667686 | |||
| 4708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\35CCEB14-36B4-428C-A506-9CE67ACF697F | xml | |
MD5:7FA81743E532F32F34EB9D0AE5817E99 | SHA256:E0B98FAF55EADDDDBD28EB12EEAE04738F4337F89741F24C47BD3CF960A4914F | |||
| 4708 | WINWORD.EXE | C:\USERS\ADMIN\APPDATA\LOCAL\MICROSOFT\TOKENBROKER\CACHE\56A61AEB75D8F5BE186C26607F4BB213ABE7C5EC.TBRES | binary | |
MD5:06067D2F4F03F8A5986FE56A69D30D70 | SHA256:925F1D4C93F23F94F1127A3792D965870CA7005BB37CA406B2636B3AC5BAF849 | |||
| 4708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\winword.exe_Rules\rule100043v0.xml | xml | |
MD5:E03148FECDFEA3BFD90CA19AA52AC2C1 | SHA256:6BBCCD4AEA9494B1FD31DE86E19B2634F3AC6E6C72506BCBFD5A5C849C67829C | |||
| 4708 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\subcommerce.rtf.LNK | binary | |
MD5:5285B62D567188711A9EA117245104B6 | SHA256:790E351DE85EC0B79BF57832811E699067D30A53969BB7EDCF897F73DE1084D0 | |||
| 4708 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GYZOV5KYFMNRKWCXQWHI.temp | binary | |
MD5:6237C888CB0DE0229B5ACE0B29F593FC | SHA256:1AAC4B2E012FD1DD9543CE981EA21712BD94ACE99A61D191D00AC043669B57A6 | |||
| 4708 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\UsageMetricsStore\FileActivityStoreV3\Word\ASkwMDAwMDAwMC0wMDAwLTAwMDAtMDAwMC0wMDAwMDAwMDAwMDBfTnVsbAA.S | binary | |
MD5:6B29912316667D33AB3C3363C8B34B5D | SHA256:797AEBF5ACED15A6BB3539D23FDFB2A09ABEDD6FB1D7A08D91944B0C50FADAE8 | |||
| 4708 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:8CACCD88D12DCE7D91FE0F94075C4073 | SHA256:2BB7931998B657601A3166B556E60BEFAFF1ED23F3BB14AA0A9B970D37900FF6 | |||
| 1852 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2023-08-09.1005.1852.1.odl | binary | |
MD5:7C60287E370F15DA79158FD99C504557 | SHA256:6735CD28621896998AE7EE6C3962C44C8F9B220AC73710D73B77A628121F4148 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
58
DNS requests
38
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4944 | SearchHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 2.21.20.155:80 | http://www.msftconnecttest.com/connecttest.txt | DE | text | 22 b | whitelisted |
— | — | POST | 200 | 138.91.171.81:80 | http://dmd.metaservices.microsoft.com/metadata.svc | US | xml | 1.69 Kb | whitelisted |
— | — | POST | 302 | 23.197.144.209:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | US | — | — | whitelisted |
— | — | POST | 200 | 138.91.171.81:80 | http://dmd.metaservices.microsoft.com/metadata.svc | US | xml | 1.69 Kb | whitelisted |
— | — | POST | 302 | 23.197.144.209:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3820 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3252 | smartscreen.exe | 20.8.16.139:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3284 | svchost.exe | 20.190.159.0:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | suspicious |
4708 | WINWORD.EXE | 52.109.32.24:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | GB | suspicious |
1576 | pipanel.exe | 5.8.18.42:443 | texasgrudgecompany.com | IP Volume inc | MD | malicious |
4708 | WINWORD.EXE | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
4708 | WINWORD.EXE | 40.79.150.120:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | suspicious |
4708 | WINWORD.EXE | 13.107.219.45:443 | otelrules.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
4944 | SearchHost.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | suspicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkappexec.microsoft.com |
| whitelisted |
texasgrudgecompany.com |
| malicious |
ecs.office.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
otelrules.azureedge.net |
| suspicious |
www.bing.com |
| whitelisted |
56cbb8495c65b3fba938598559b103f7.clo.footprintdns.com |
| suspicious |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
ln-ring.msedge.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1576 | pipanel.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Parallax RAT |
— | — | Misc activity | ET INFO Microsoft Connection Test |
— | — | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Parallax RAT |
— | — | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Parallax RAT |
— | — | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Parallax RAT |
— | — | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Parallax RAT |
— | — | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Parallax RAT |
— | — | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Parallax RAT |
— | — | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Parallax RAT |
— | — | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Parallax RAT |