| download: | pe.exe |
| Full analysis: | https://app.any.run/tasks/6a76aa84-169f-4256-94cf-ed4b68da995f |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | February 25, 2020, 20:31:29 |
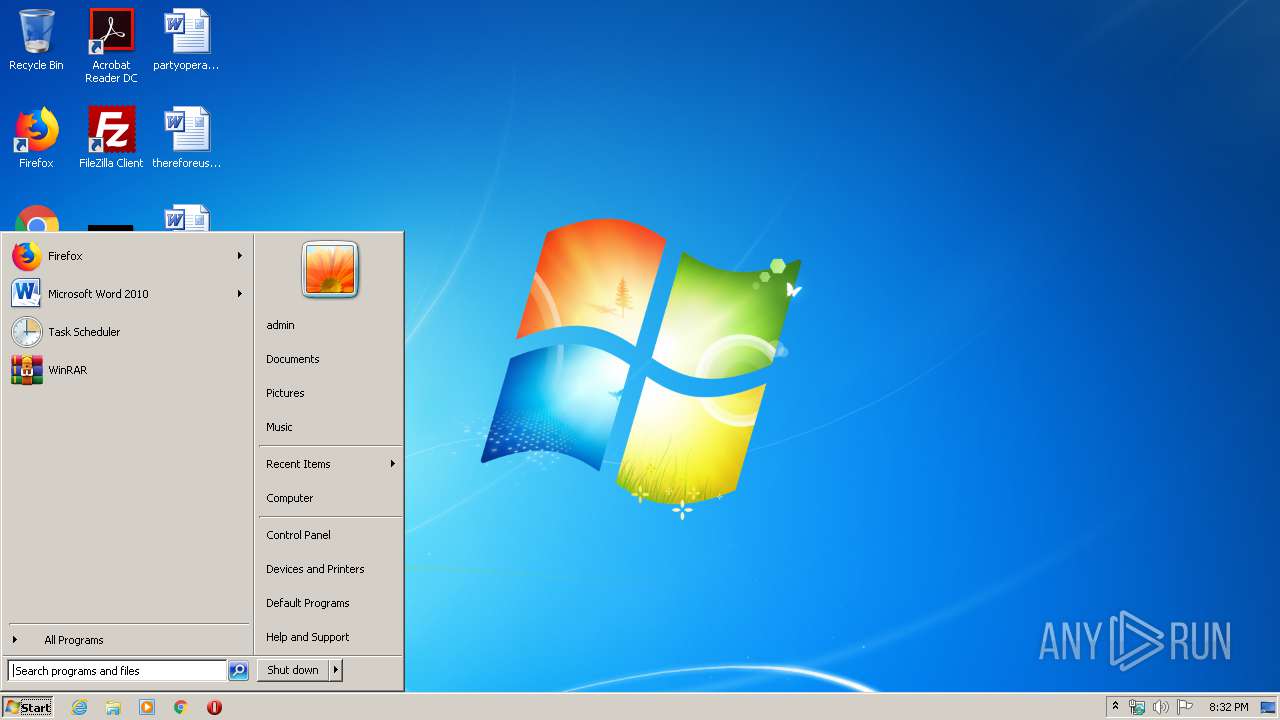
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 34311E09FD0A0882B21A4A62D590437B |
| SHA1: | C5D1E2A2A13C242FB5FC0120A68C2165373B46A5 |
| SHA256: | 924E3DB79C774FE1745AB19CBB4892CA54BE135E2CBCBDEF3179A26DAFCBD1BD |
| SSDEEP: | 6144:B2rlT++AMR7Ktth0CTJNQGfc2jSj+pE8S7C+L0keX1c:BU++ThK3h0CTwGU2jSSpa7C0d |
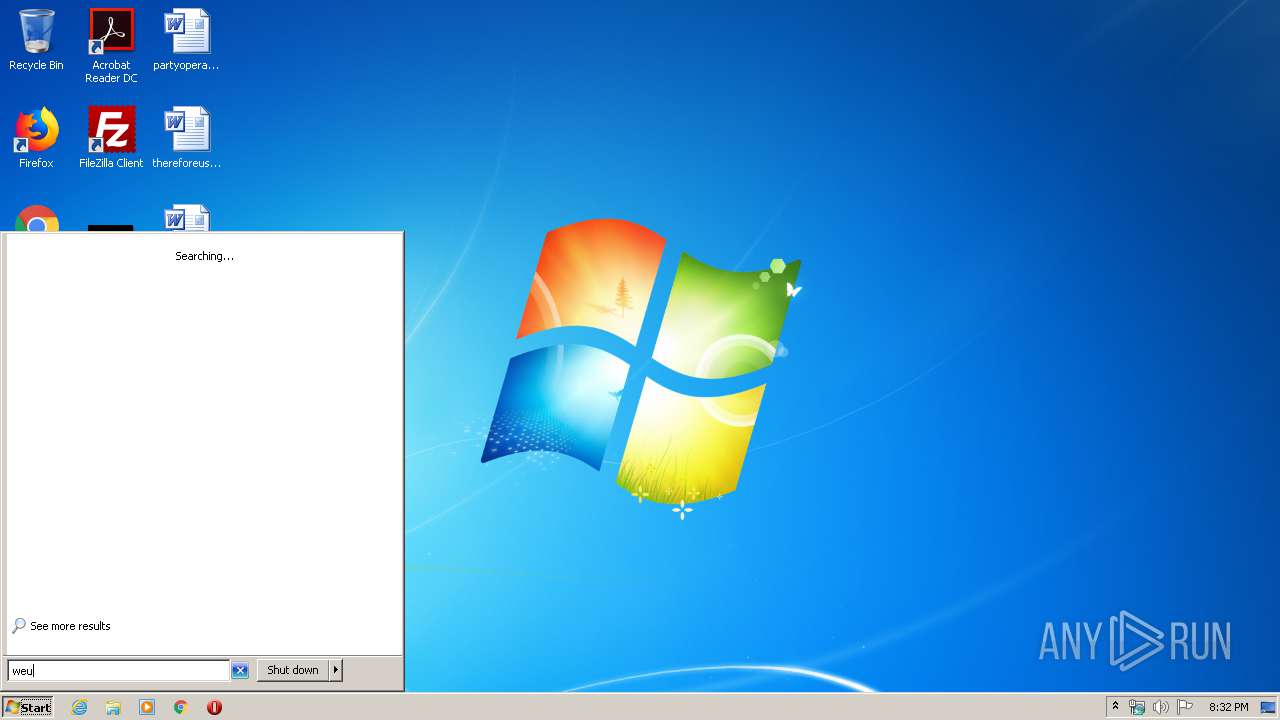
MALICIOUS
Disables Windows Defender
- svchost.exe (PID: 3076)
Changes the autorun value in the registry
- pe.exe (PID: 2892)
Changes Security Center notification settings
- svchost.exe (PID: 3076)
Application was dropped or rewritten from another process
- 1147331680.exe (PID: 1696)
- 1508120302.exe (PID: 3160)
- 2449512944.exe (PID: 3372)
MINER was detected
- wuapp.exe (PID: 3824)
Connects to CnC server
- wuapp.exe (PID: 3824)
PHORPIEX was detected
- svchost.exe (PID: 3076)
Writes to a start menu file
- wscript.exe (PID: 3792)
SUSPICIOUS
Executable content was dropped or overwritten
- pe.exe (PID: 2892)
- svchost.exe (PID: 3076)
- 1147331680.exe (PID: 1696)
Creates executable files which already exist in Windows
- pe.exe (PID: 2892)
Starts itself from another location
- pe.exe (PID: 2892)
- svchost.exe (PID: 3076)
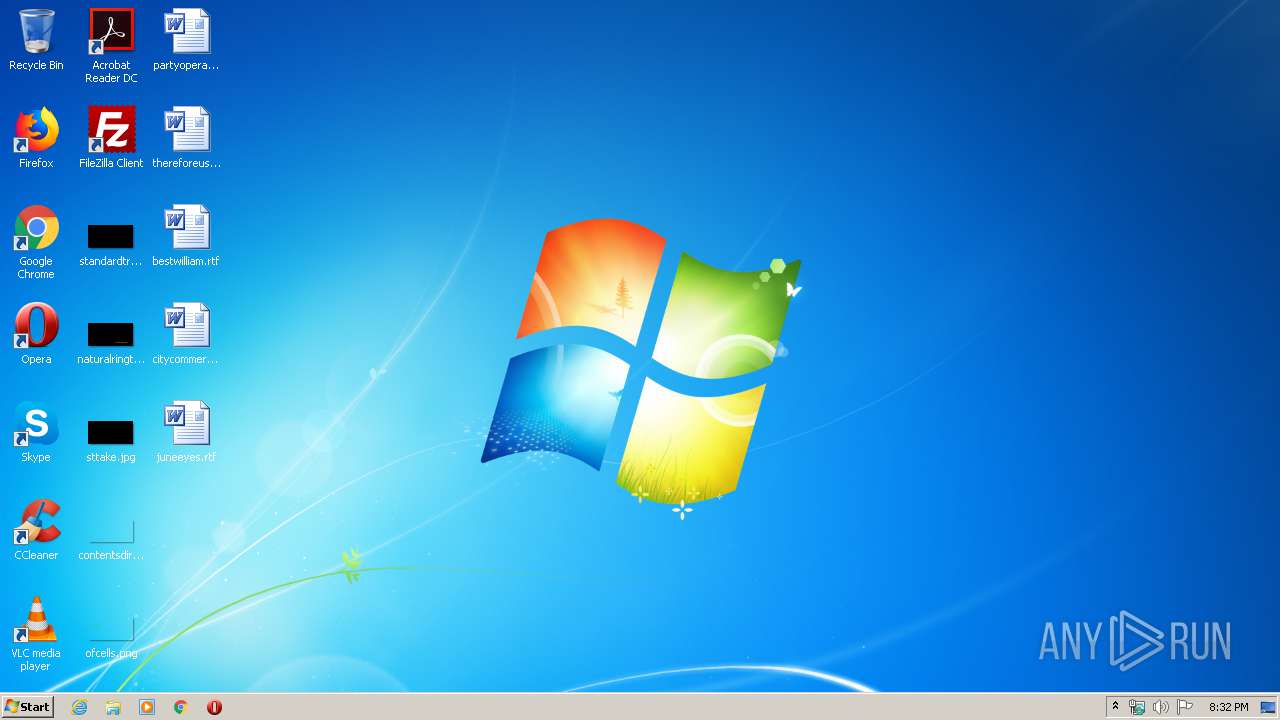
Creates files in the user directory
- svchost.exe (PID: 3076)
- 2449512944.exe (PID: 3372)
- wscript.exe (PID: 3792)
Reads Internet Cache Settings
- svchost.exe (PID: 3076)
- 2449512944.exe (PID: 3372)
Connects to SMTP port
- 1508120302.exe (PID: 3160)
Connects to unusual port
- wuapp.exe (PID: 3824)
Creates files in the program directory
- 1147331680.exe (PID: 1696)
Executes scripts
- cmd.exe (PID: 3316)
Checks for external IP
- 2449512944.exe (PID: 3372)
Starts CMD.EXE for commands execution
- 1147331680.exe (PID: 1696)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:30 16:54:48+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 155136 |
| InitializedDataSize: | 301056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3450 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jul-2019 14:54:48 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 30-Jul-2019 14:54:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00025C11 | 0x00025E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.82051 |
.rdata | 0x00027000 | 0x00008672 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75706 |
.data | 0x00030000 | 0x00030108 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.17593 |
.gujicum | 0x00061000 | 0x00002800 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.tls | 0x00064000 | 0x00001009 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.fazeza | 0x00066000 | 0x00000400 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.gehem | 0x00067000 | 0x00000400 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.davo | 0x00068000 | 0x00000003 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00069000 | 0x00008C58 | 0x00008E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.23719 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13891 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 2.47717 | 816 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 2.44093 | 304 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.697 | 3752 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 3.76287 | 2216 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 3.94238 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
9 | 2.73717 | 162 | UNKNOWN | UNKNOWN | RT_STRING |
10 | 3.34364 | 1126 | UNKNOWN | UNKNOWN | RT_STRING |
11 | 3.29371 | 1868 | UNKNOWN | UNKNOWN | RT_STRING |
12 | 3.29799 | 1760 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
KERNEL32.dll |
Total processes
42
Monitored processes
9
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1696 | C:\Users\admin\AppData\Local\Temp\1147331680.exe | C:\Users\admin\AppData\Local\Temp\1147331680.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2756 | C:\Users\admin\AppData\Local\Temp\2145711693.exe | C:\Users\admin\AppData\Local\Temp\2145711693.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2892 | "C:\Users\admin\AppData\Local\Temp\pe.exe" | C:\Users\admin\AppData\Local\Temp\pe.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3076 | C:\Users\admin\29511028618914\svchost.exe | C:\Users\admin\29511028618914\svchost.exe | pe.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3160 | C:\Users\admin\AppData\Local\Temp\1508120302.exe | C:\Users\admin\AppData\Local\Temp\1508120302.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3316 | cmd.exe /C WScript "C:\ProgramData\ZRBEbQTcgq\r.vbs" | C:\Windows\system32\cmd.exe | — | 1147331680.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3372 | C:\Users\admin\AppData\Local\Temp\2449512944.exe | C:\Users\admin\AppData\Local\Temp\2449512944.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3792 | WScript "C:\ProgramData\ZRBEbQTcgq\r.vbs" | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3824 | "C:\Windows\System32\wuapp.exe" -c "C:\ProgramData\ZRBEbQTcgq\cfg" | C:\Windows\System32\wuapp.exe | 1147331680.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Application Launcher Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
94
Read events
63
Write events
31
Delete events
0
Modification events
| (PID) Process: | (2892) pe.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Driver |
Value: C:\Users\admin\29511028618914\svchost.exe | |||
| (PID) Process: | (2892) pe.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Driver |
Value: C:\Users\admin\29511028618914\svchost.exe | |||
| (PID) Process: | (3076) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (3076) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
| (PID) Process: | (3076) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (3076) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (3076) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusOverride |
Value: 1 | |||
| (PID) Process: | (3076) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | UpdatesOverride |
Value: 1 | |||
| (PID) Process: | (3076) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | FirewallOverride |
Value: 1 | |||
| (PID) Process: | (3076) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusDisableNotify |
Value: 1 | |||
Executable files
9
Suspicious files
9
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3372 | 2449512944.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\WXY0TP32.htm | — | |
MD5:— | SHA256:— | |||
| 1696 | 1147331680.exe | C:\ProgramData\ZRBEbQTcgq\sysdrv32.exe | — | |
MD5:— | SHA256:— | |||
| 2892 | pe.exe | C:\Users\admin\29511028618914\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 3076 | svchost.exe | C:\Users\admin\AppData\Local\Temp\2449512944.exe | binary | |
MD5:— | SHA256:— | |||
| 1696 | 1147331680.exe | C:\ProgramData\ZRBEbQTcgq\cfg | text | |
MD5:— | SHA256:— | |||
| 3076 | svchost.exe | C:\Users\admin\AppData\Local\Temp\pe.exe | executable | |
MD5:— | SHA256:— | |||
| 3076 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\2[1] | binary | |
MD5:— | SHA256:— | |||
| 1696 | 1147331680.exe | C:\ProgramData\ZRBEbQTcgq\sysdrv32 | executable | |
MD5:— | SHA256:— | |||
| 3076 | svchost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\5[1] | binary | |
MD5:— | SHA256:— | |||
| 3076 | svchost.exe | C:\Users\admin\AppData\Local\Temp\2145711693.exe | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
14
DNS requests
75
Threats
58
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3076 | svchost.exe | GET | — | 92.63.197.190:80 | http://tldrbox.top/2 | RU | — | — | malicious |
3076 | svchost.exe | GET | — | 92.63.197.190:80 | http://tldrbox.top/4 | RU | — | — | malicious |
3076 | svchost.exe | GET | — | 92.63.197.190:80 | http://tldrbox.top/3 | RU | — | — | malicious |
3076 | svchost.exe | GET | — | 92.63.197.190:80 | http://tldrbox.top/5 | RU | — | — | malicious |
3076 | svchost.exe | GET | — | 92.63.197.190:80 | http://92.63.197.190/2 | RU | — | — | malicious |
3076 | svchost.exe | GET | — | 92.63.197.190:80 | http://92.63.197.190/5 | RU | — | — | malicious |
3076 | svchost.exe | GET | — | 92.63.197.190:80 | http://92.63.197.190/3 | RU | — | — | malicious |
3076 | svchost.exe | GET | 200 | 92.63.197.190:80 | http://tldrbox.top/3 | RU | binary | 235 Kb | malicious |
3076 | svchost.exe | GET | 200 | 92.63.197.190:80 | http://tldrbox.top/4 | RU | binary | 1.67 Mb | malicious |
3076 | svchost.exe | GET | 404 | 92.63.197.190:80 | http://tldrbox.top/1 | RU | html | 580 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3076 | svchost.exe | 92.63.197.190:80 | tldrbox.top | — | RU | malicious |
3824 | wuapp.exe | 92.63.197.190:5657 | tldrbox.top | — | RU | malicious |
3160 | 1508120302.exe | 67.195.204.77:25 | mta6.am0.yahoodns.net | — | US | unknown |
3372 | 2449512944.exe | 212.83.168.196:80 | api.wipmania.com | Online S.a.s. | FR | malicious |
— | — | 92.63.197.190:5657 | tldrbox.top | — | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tldrbox.top |
| malicious |
yahoo.com |
| whitelisted |
mta6.am0.yahoodns.net |
| whitelisted |
suogogurshodt.ru |
| malicious |
gegeagaegaert.ru |
| malicious |
aofhioaehfoht.ru |
| malicious |
ououruoshrgot.ru |
| malicious |
oahfoeaoueftt.ru |
| malicious |
afaefoahohgtt.ru |
| malicious |
twtwouwoturtt.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3076 | svchost.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3076 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Phorpiex.V |
3076 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Phorpiex.V |
3076 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Phorpiex.V |
3824 | wuapp.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
3824 | wuapp.exe | Misc activity | MINER [PTsecurity] CoinMiner CryptoNight XMRig JSON_RPC Client Login |
3824 | wuapp.exe | Misc activity | MINER [PTsecurity] Riskware/CoinMiner JSON_RPC Response |
3076 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Phorpiex.V |
3372 | 2449512944.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Attempt To Wipmania |
9 ETPRO signatures available at the full report