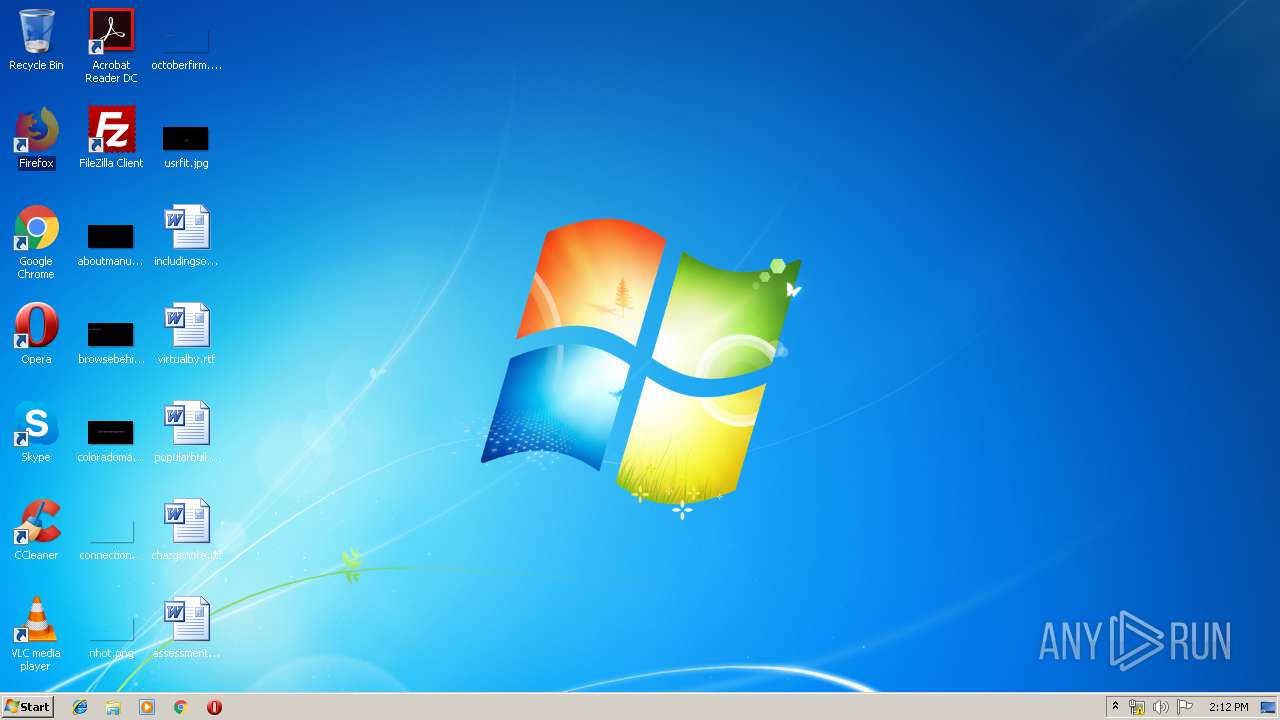
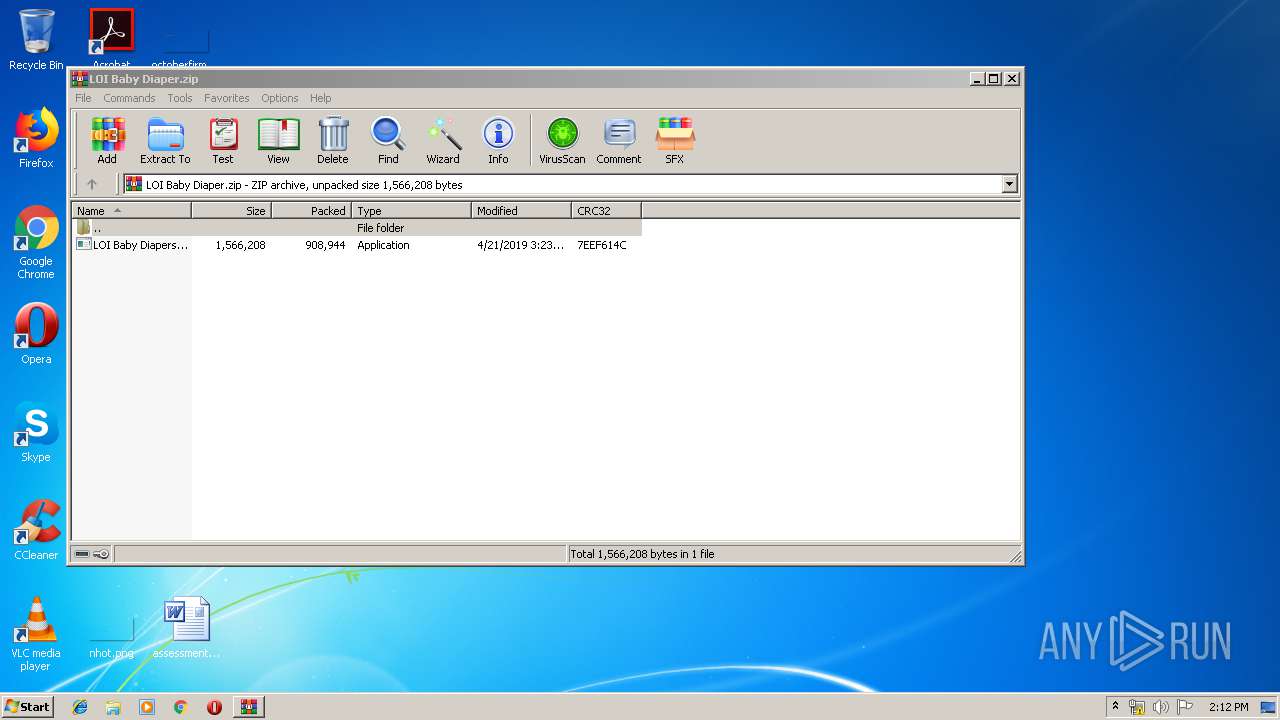
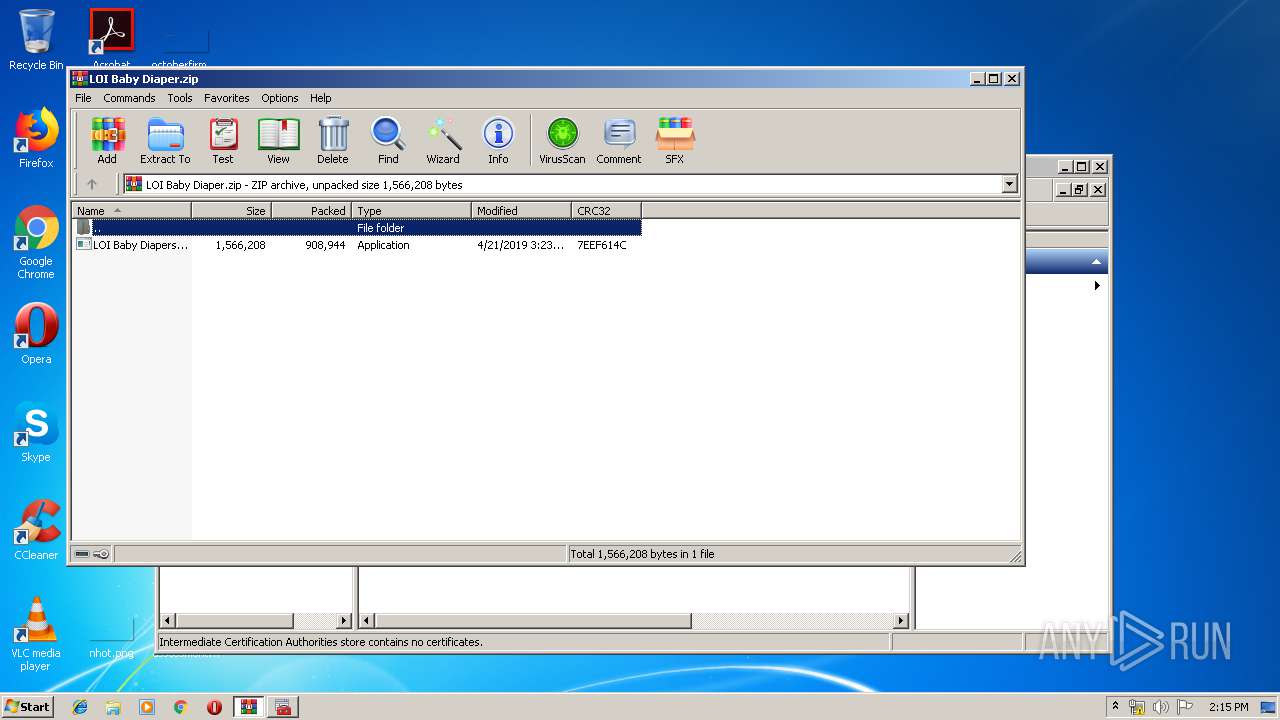
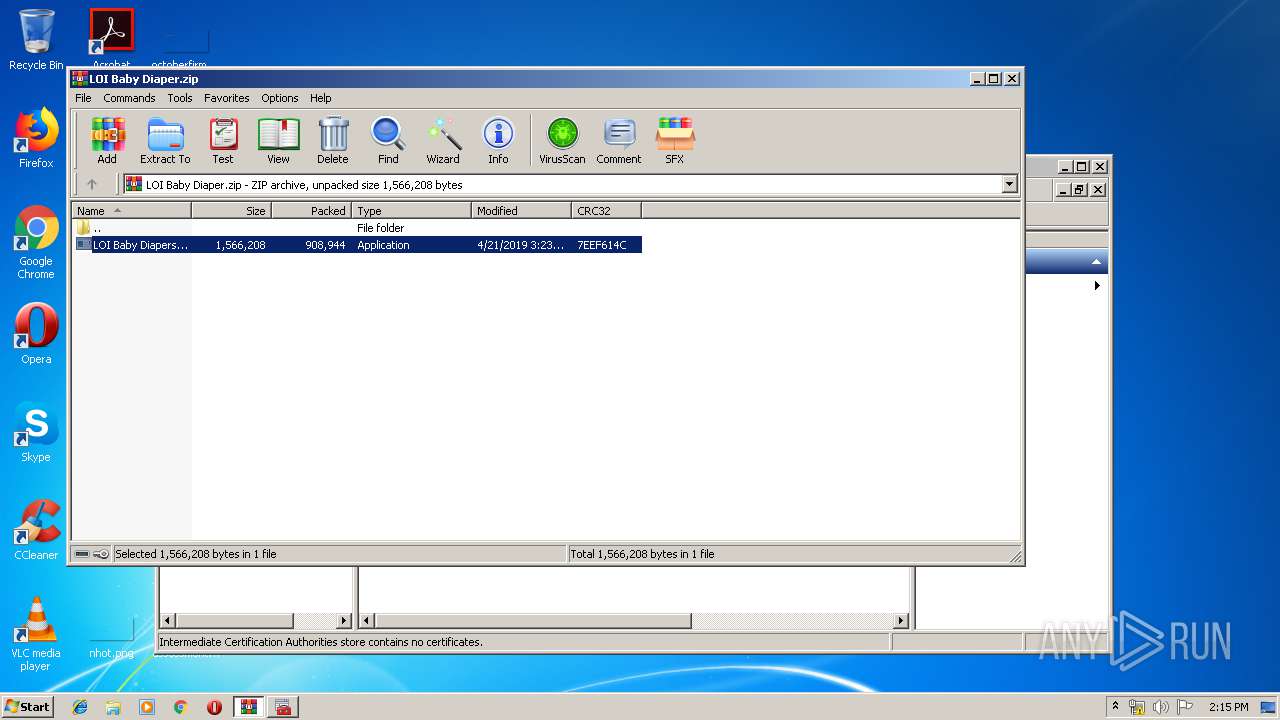
| File name: | LOI Baby Diaper.zip |
| Full analysis: | https://app.any.run/tasks/a975ecce-9172-46ff-a75b-6a3236fab2c9 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 21, 2019, 13:12:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3F3E045F4F9FF5278A16DC54EB54B22F |
| SHA1: | B05F48554DA0FA7A28574FBEFEC62D4DB90899E2 |
| SHA256: | 91C0ADD87B2CE751EEA20126DCE16D5B114FB4771D7F9D07BAAB74177219D36D |
| SSDEEP: | 24576:DSupe1Rp6BrZgXaMtyEU+kuZhQa2u0gp8GTv0blyJ3U:DSu2rIr3j8X0gPDKyu |
MALICIOUS
Application was dropped or rewritten from another process
- LOI Baby Diapers.exe (PID: 916)
- RegAsm.exe (PID: 2440)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 2440)
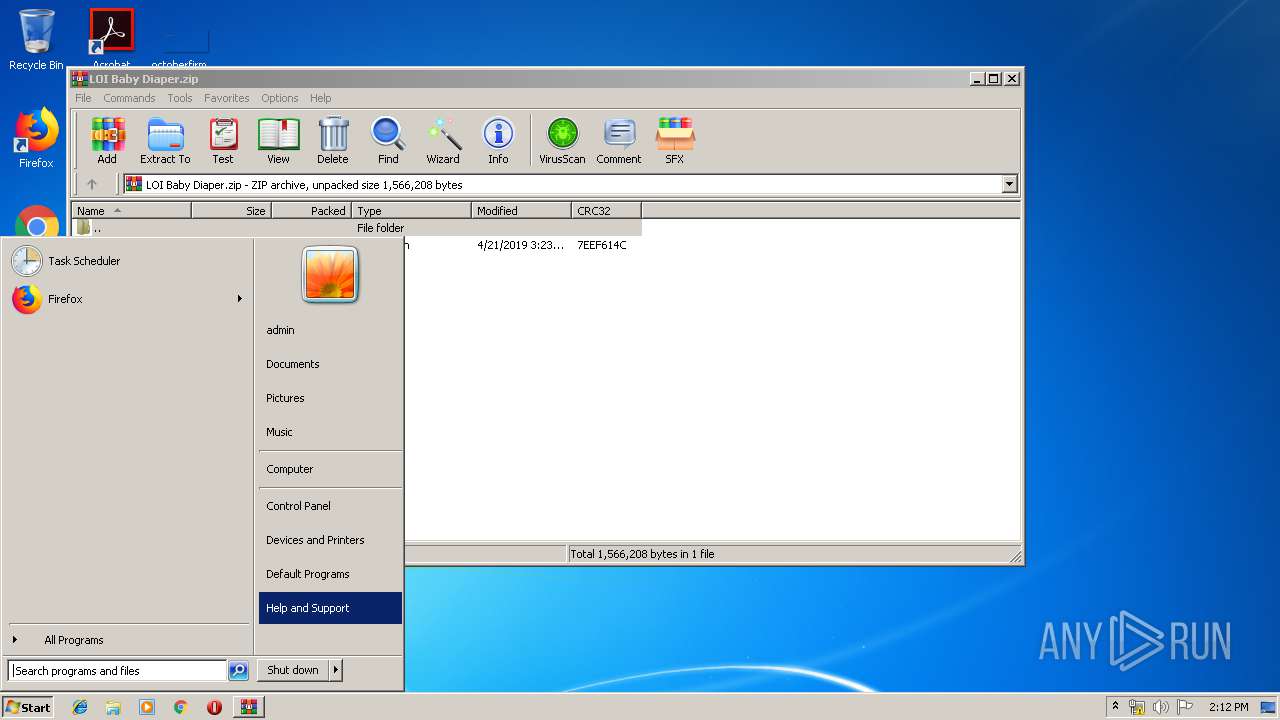
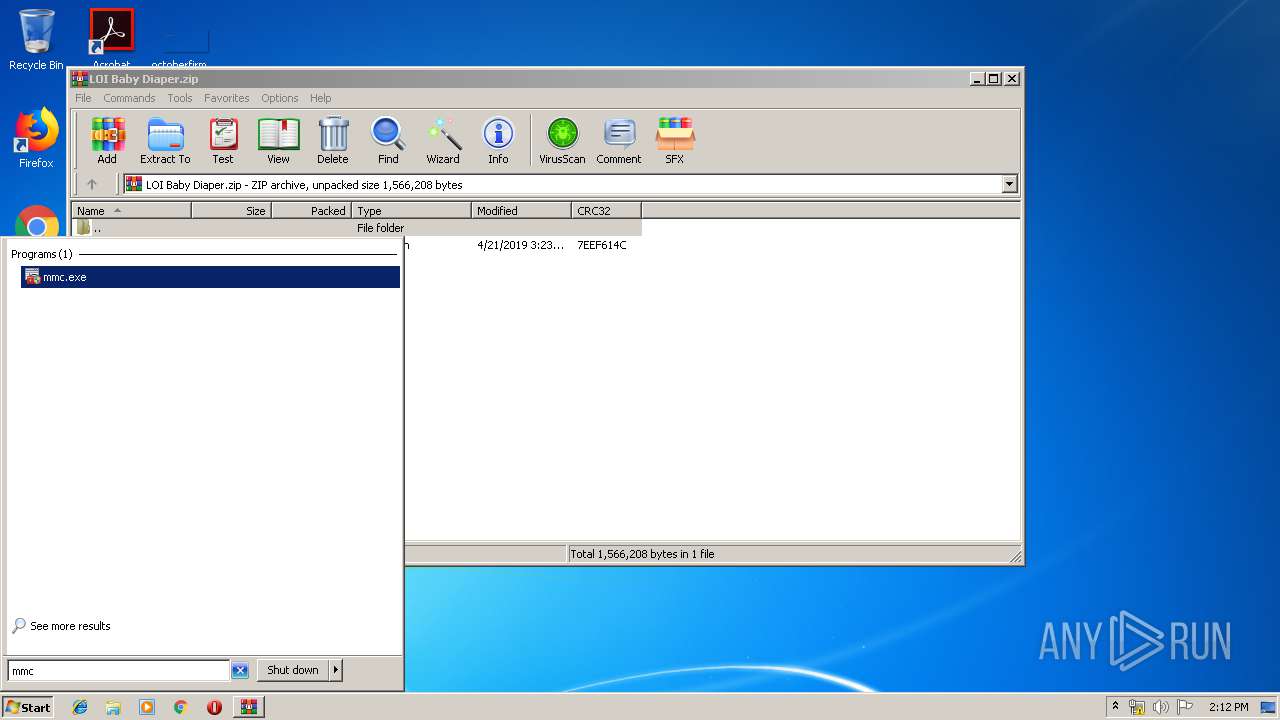
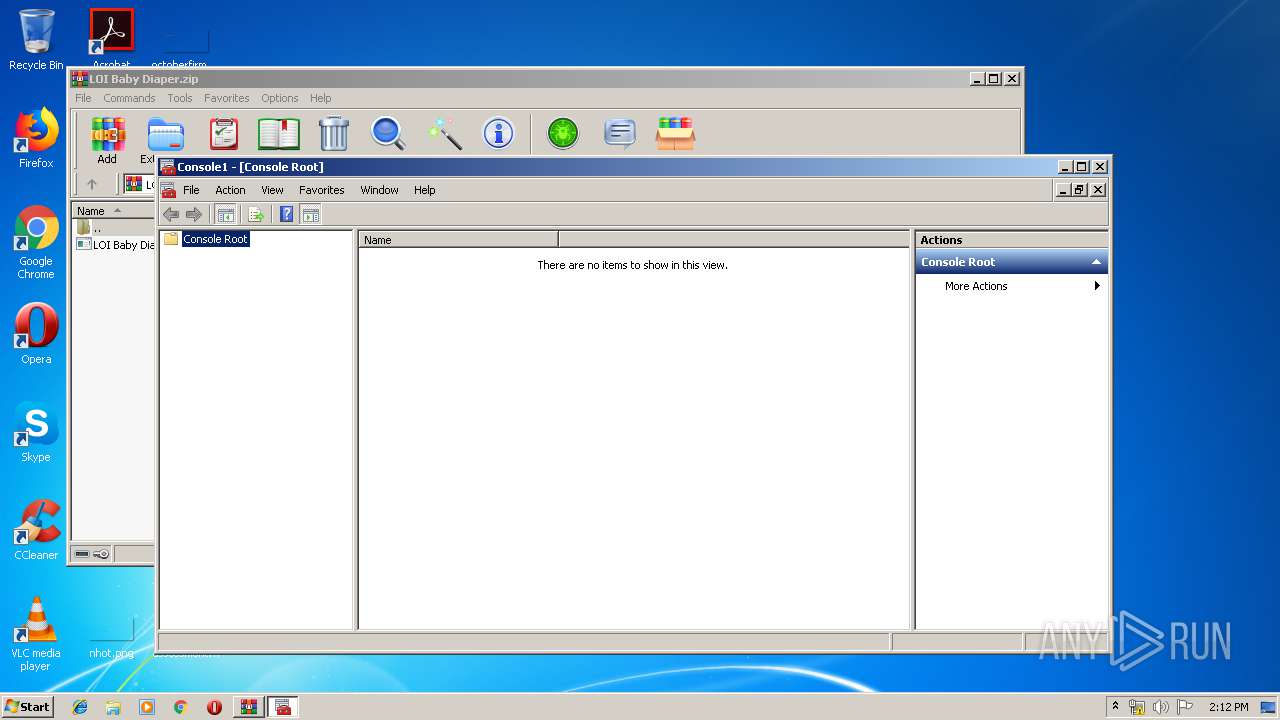
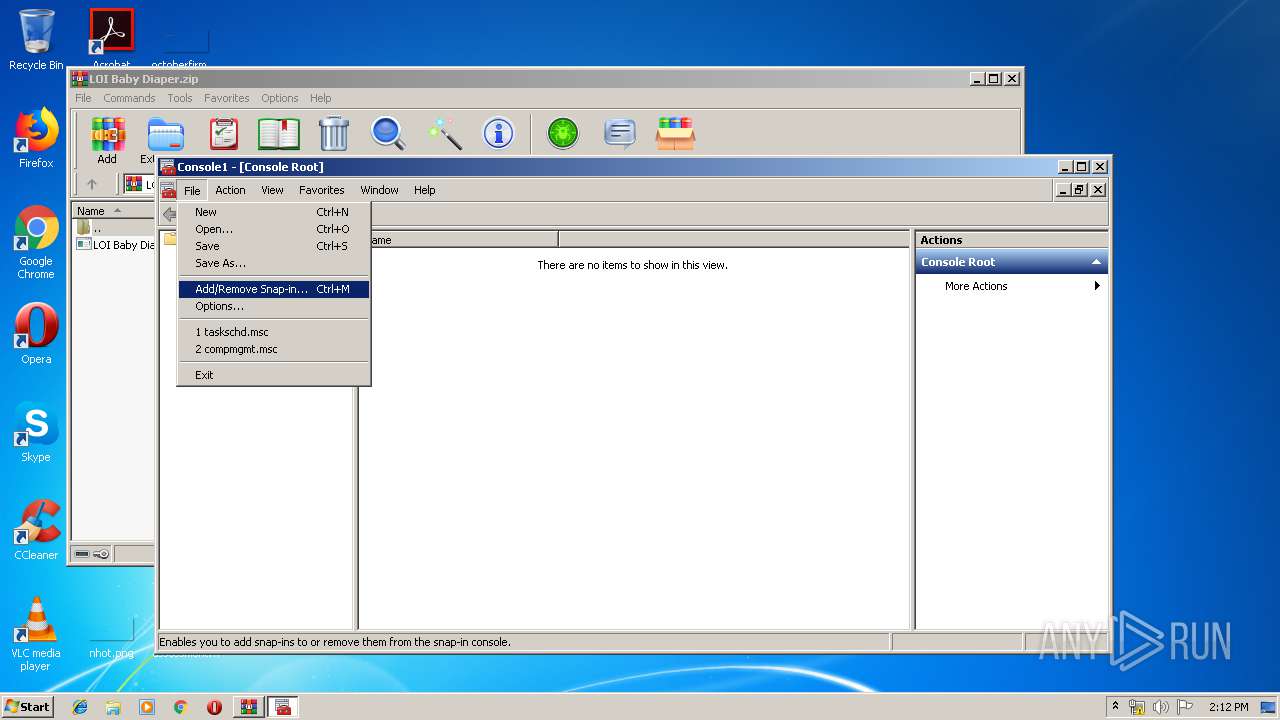
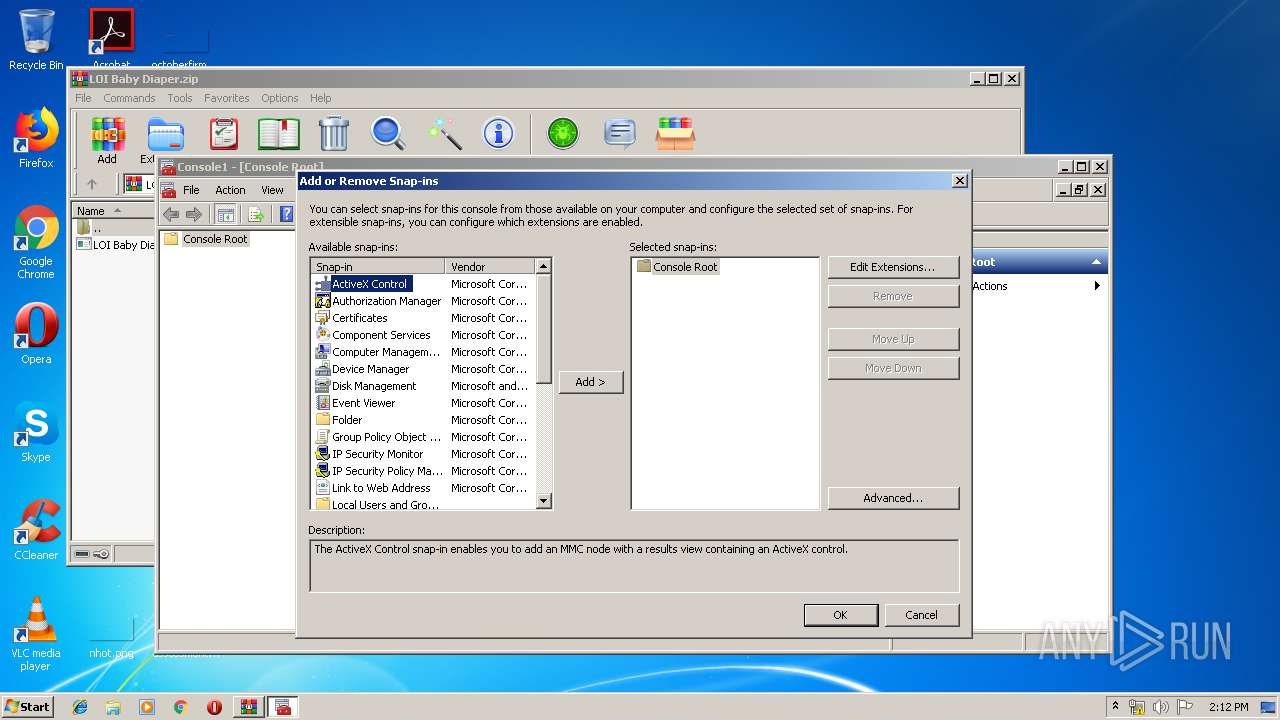
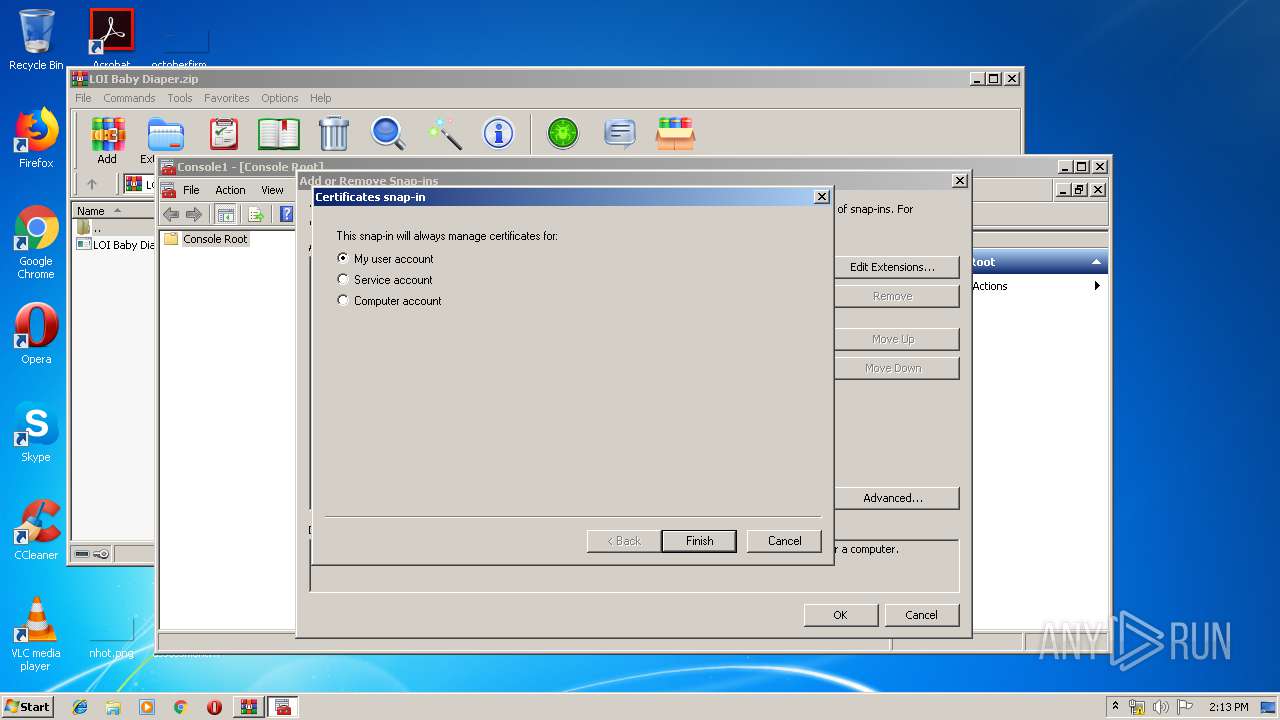
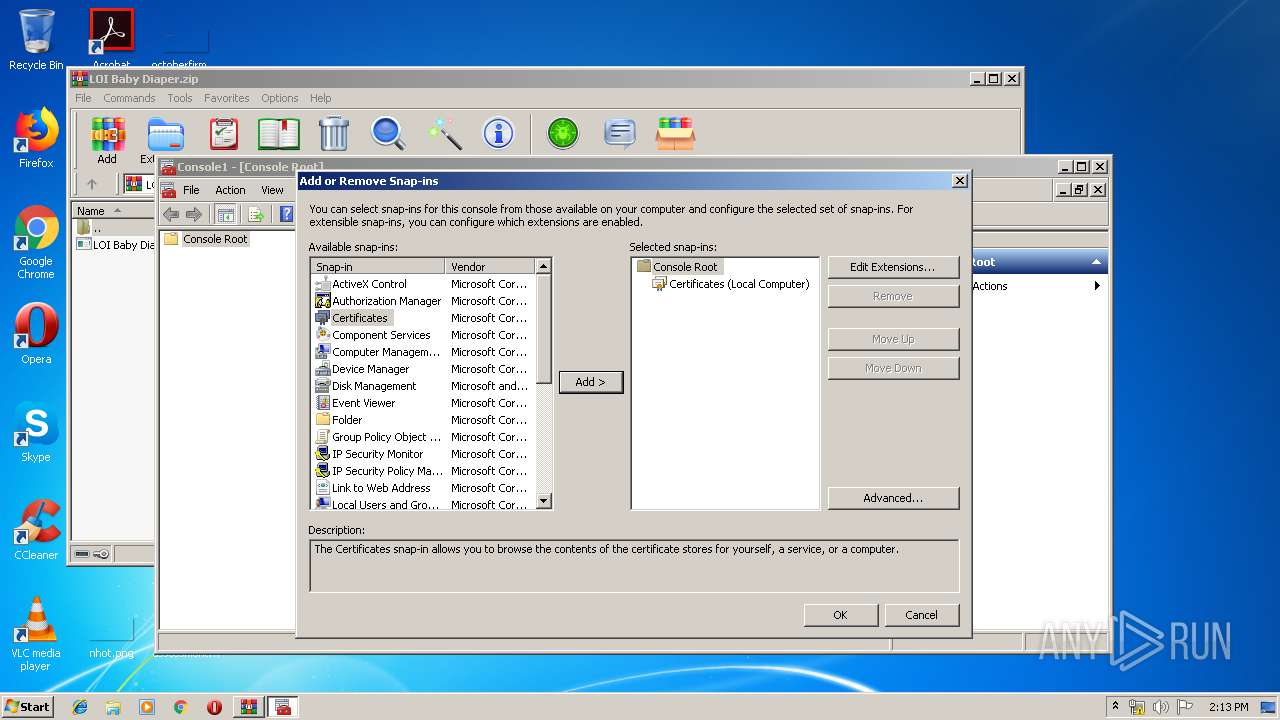
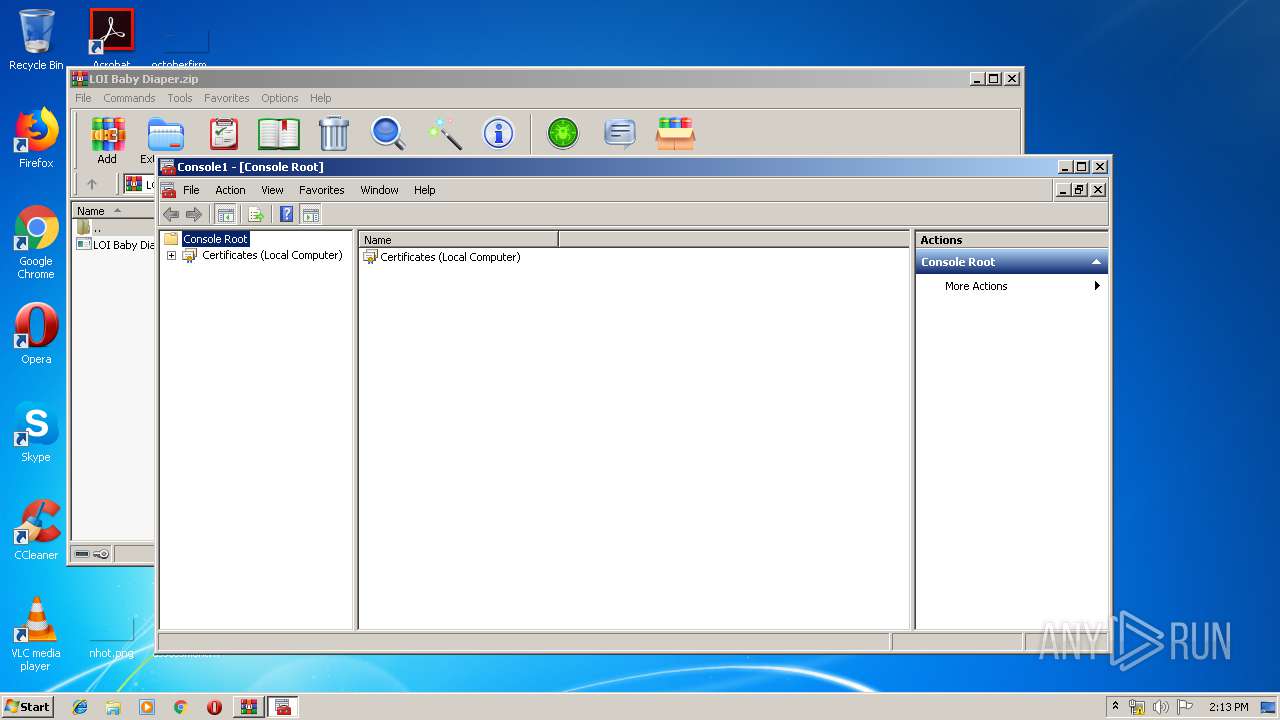
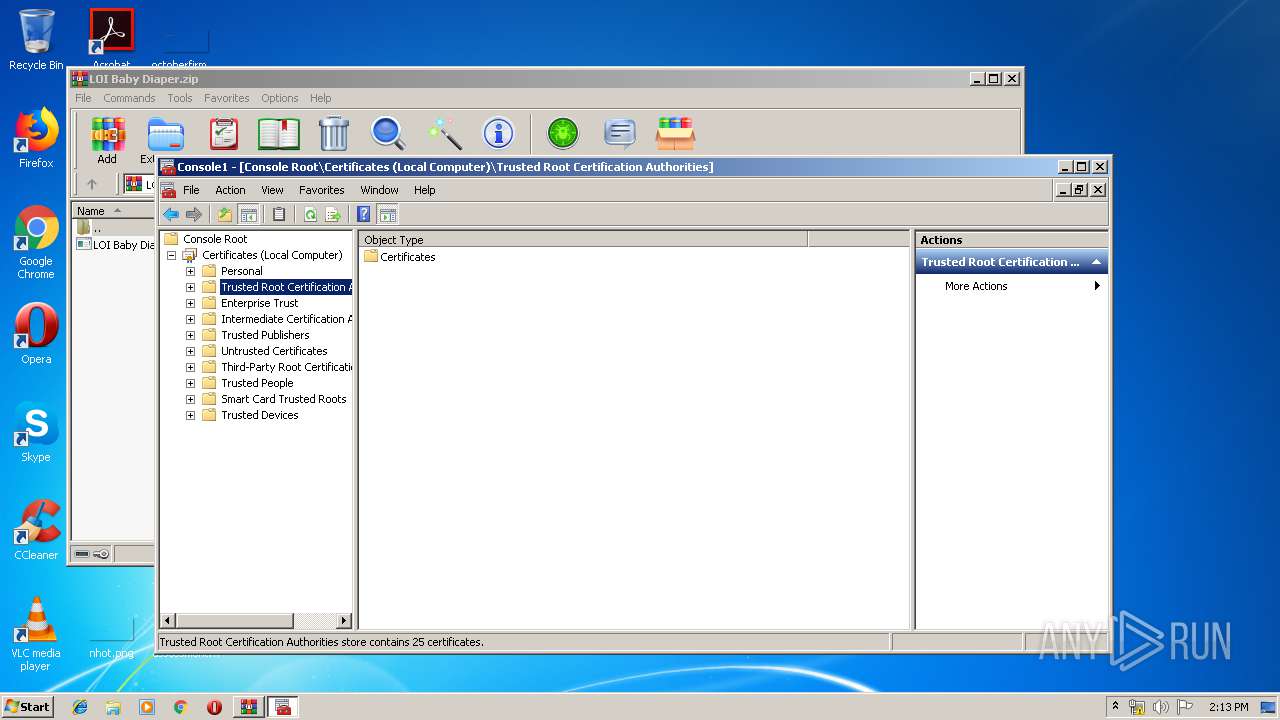
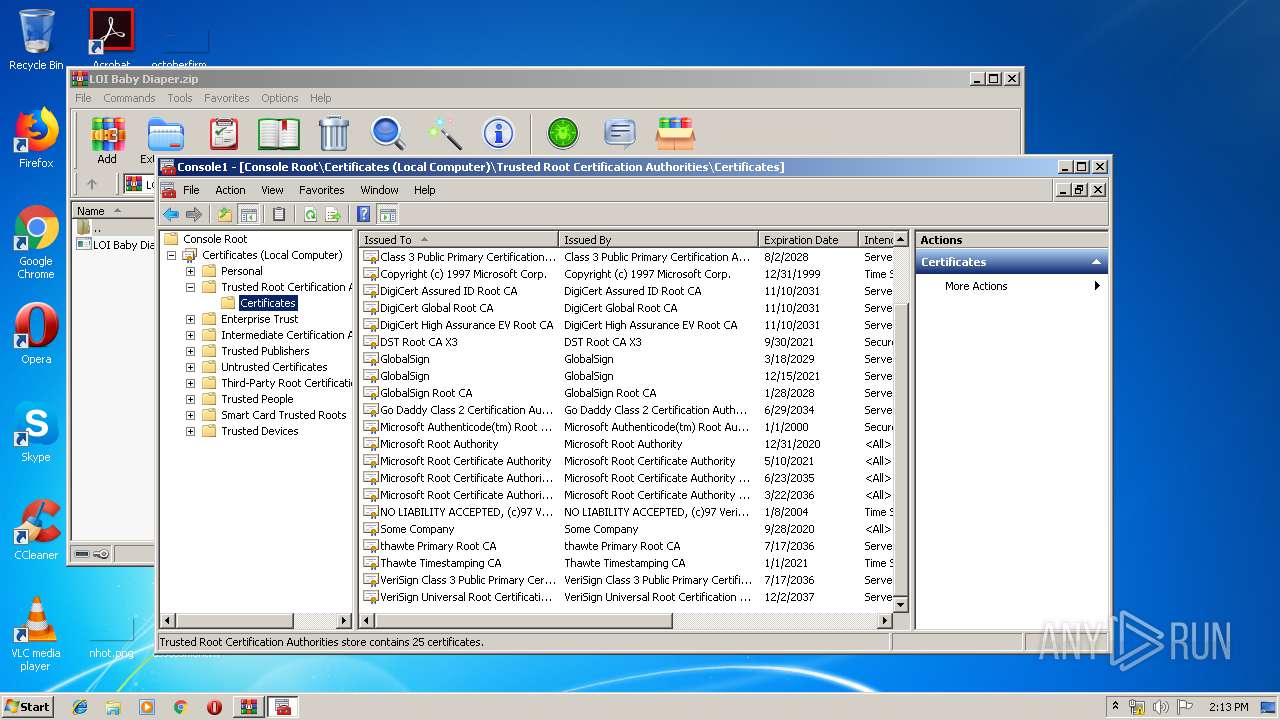
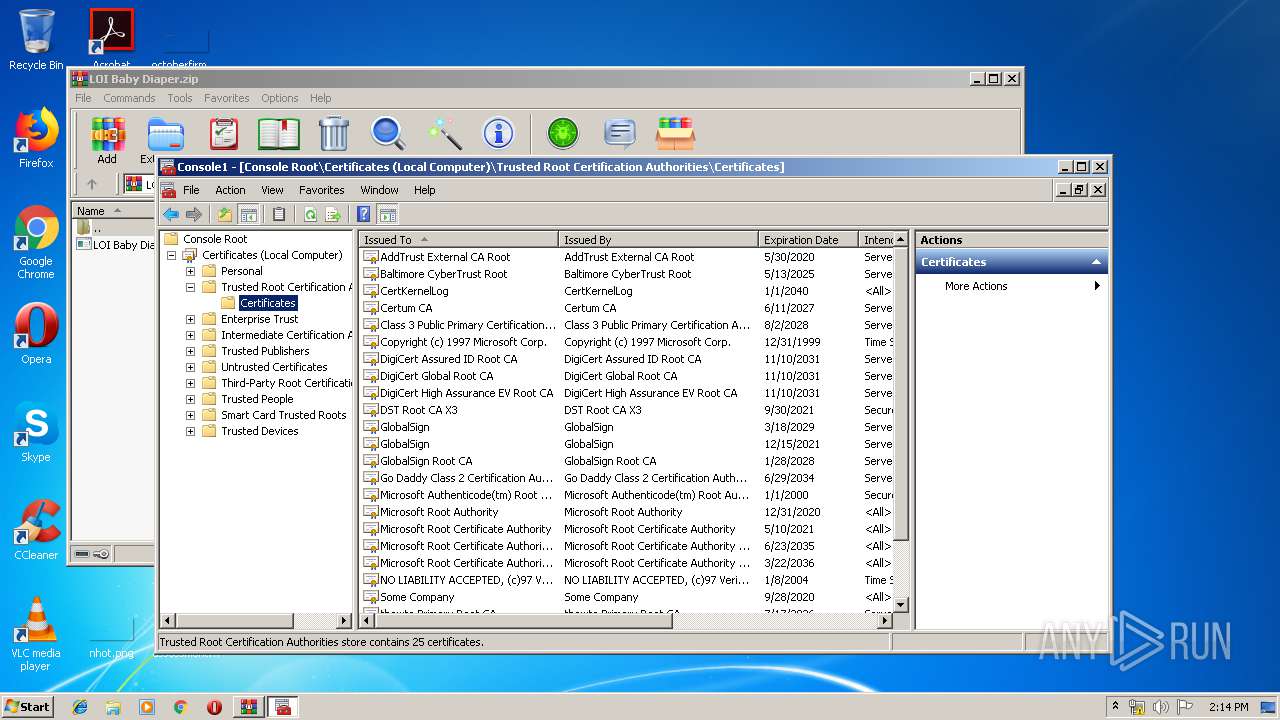
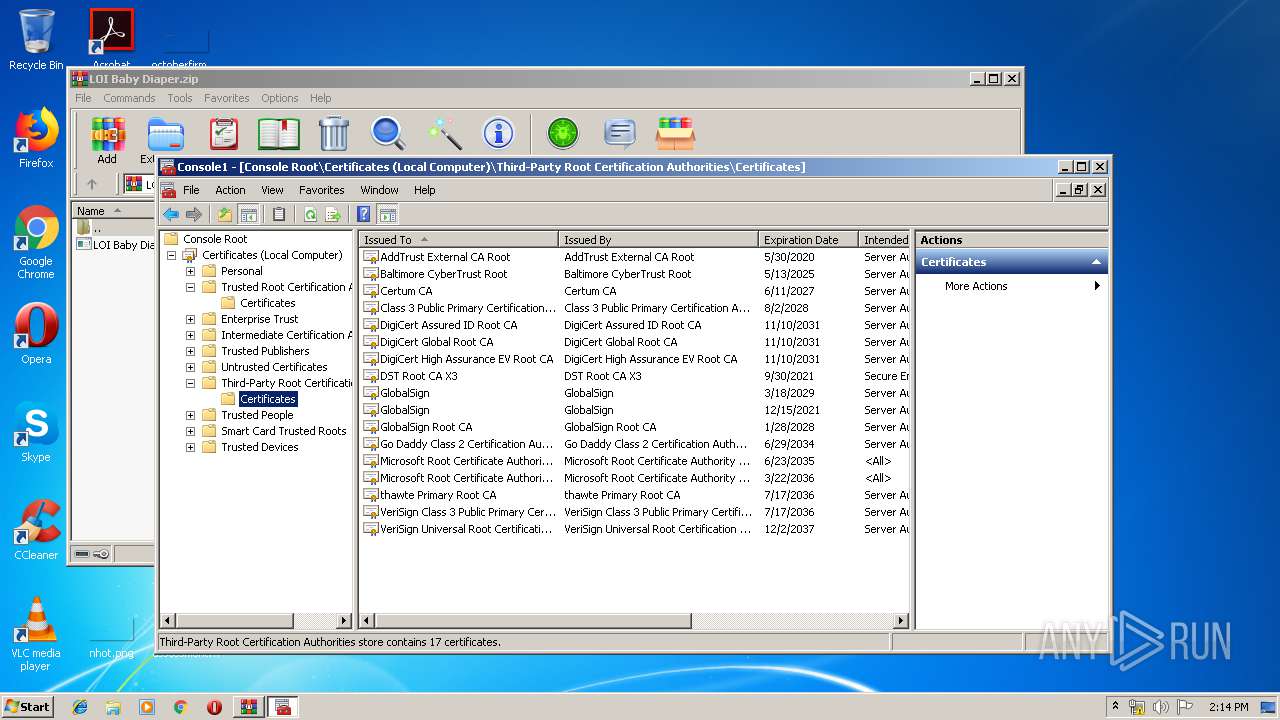
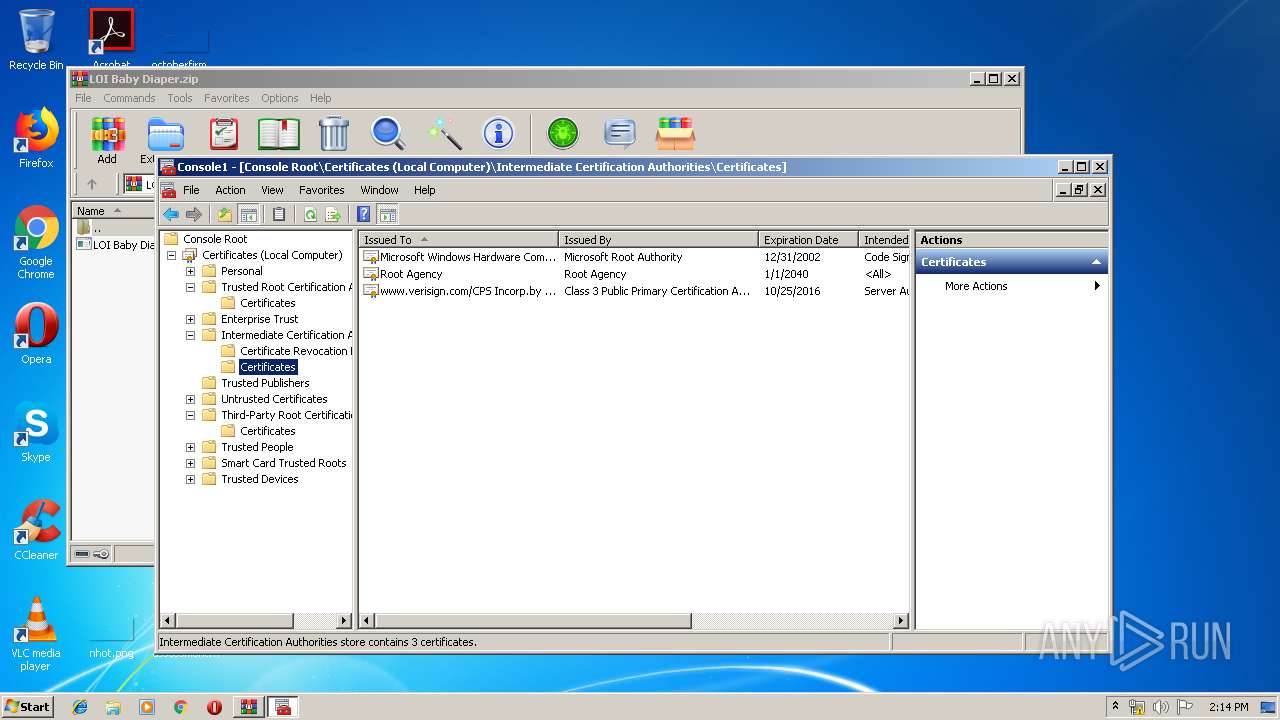
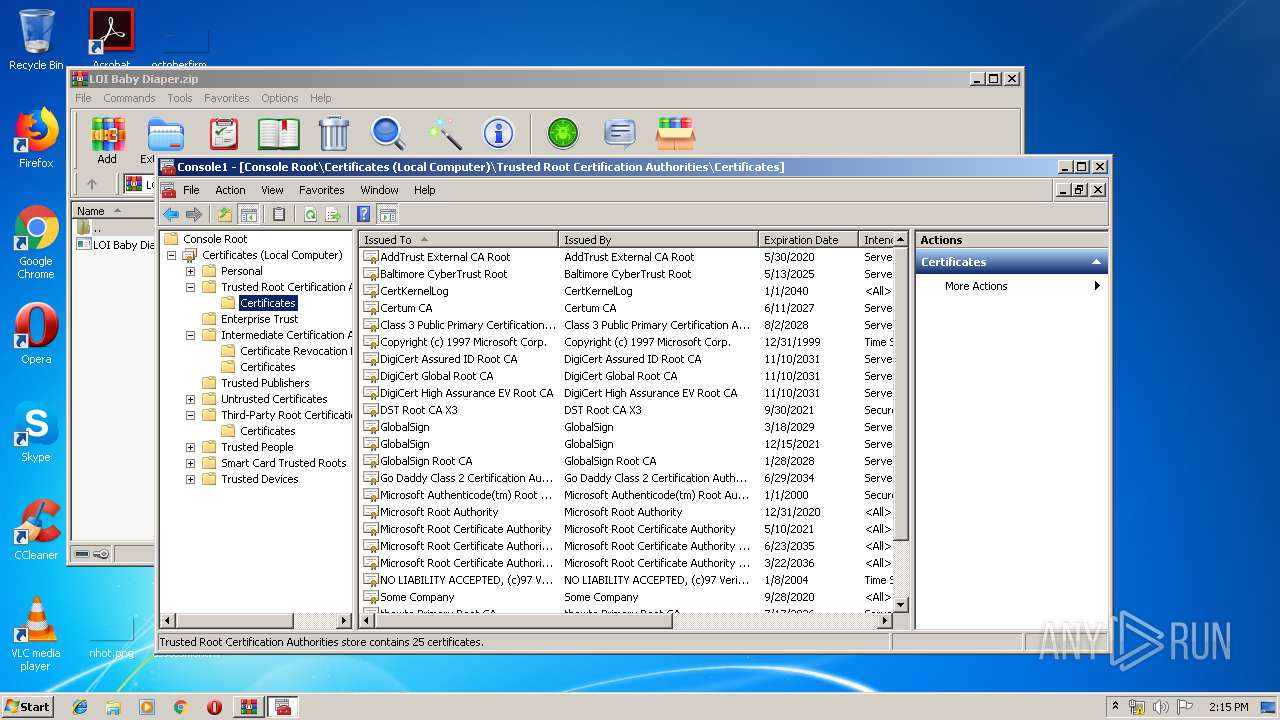
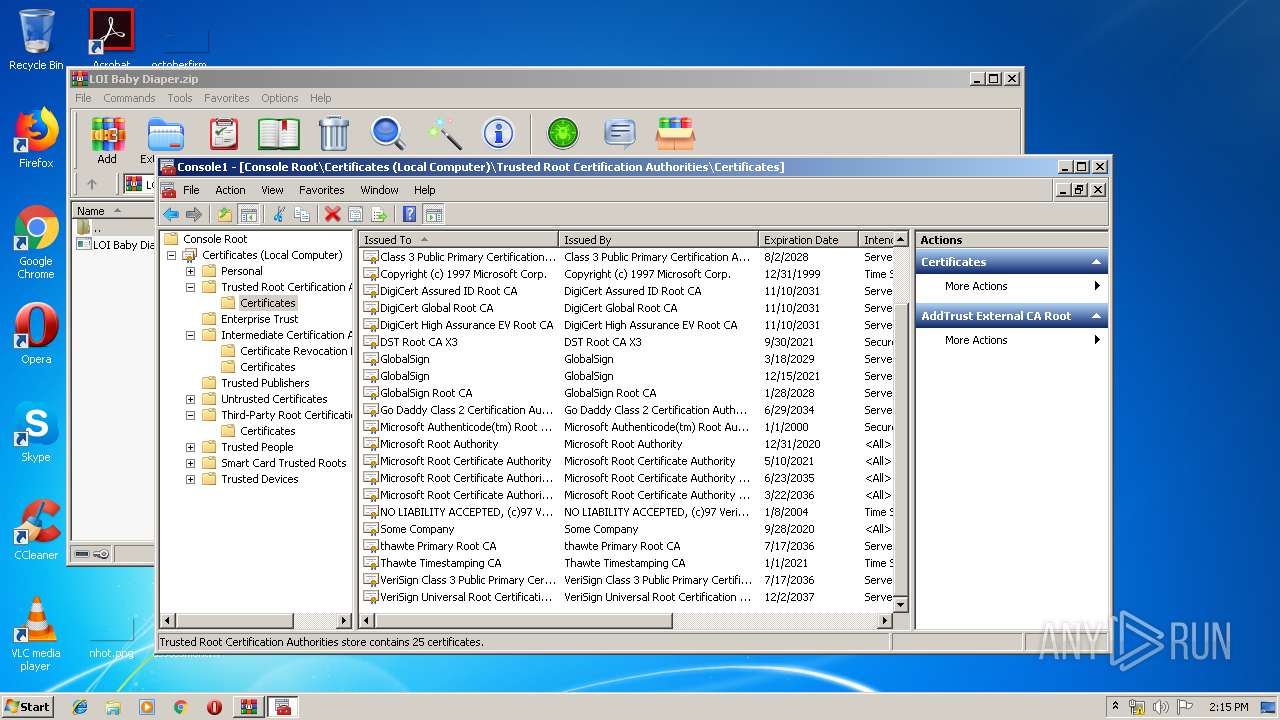
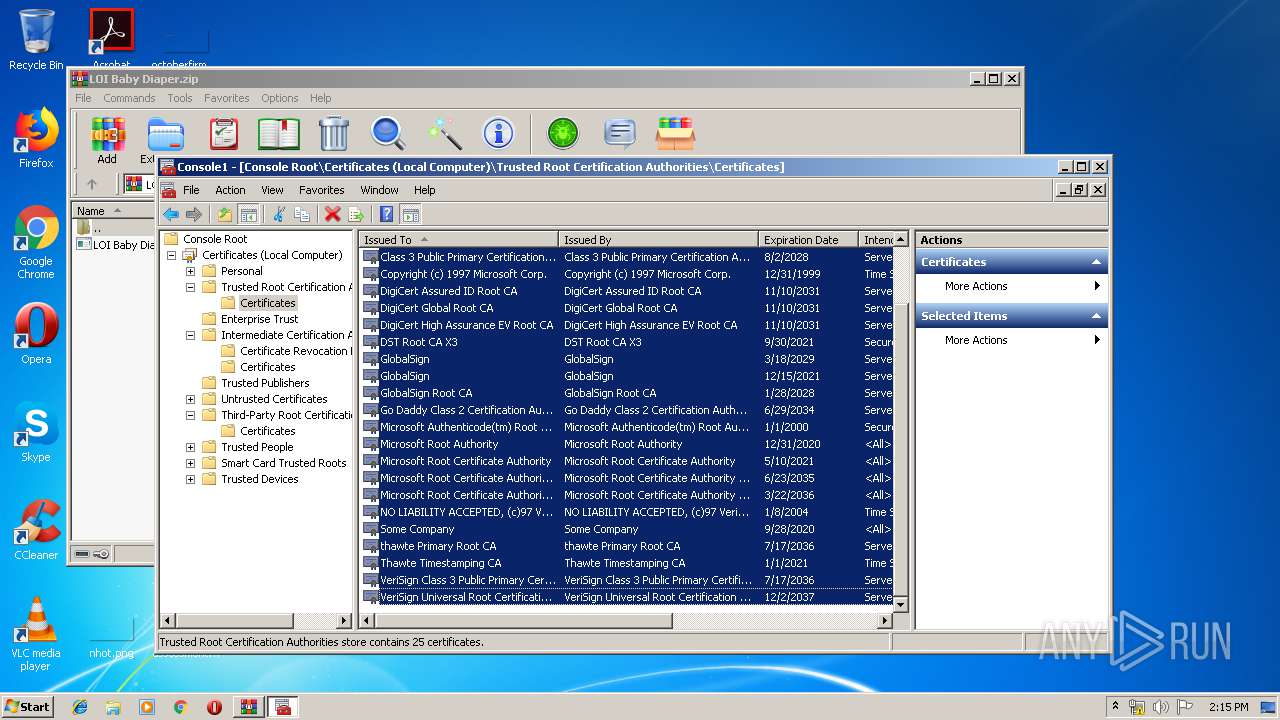
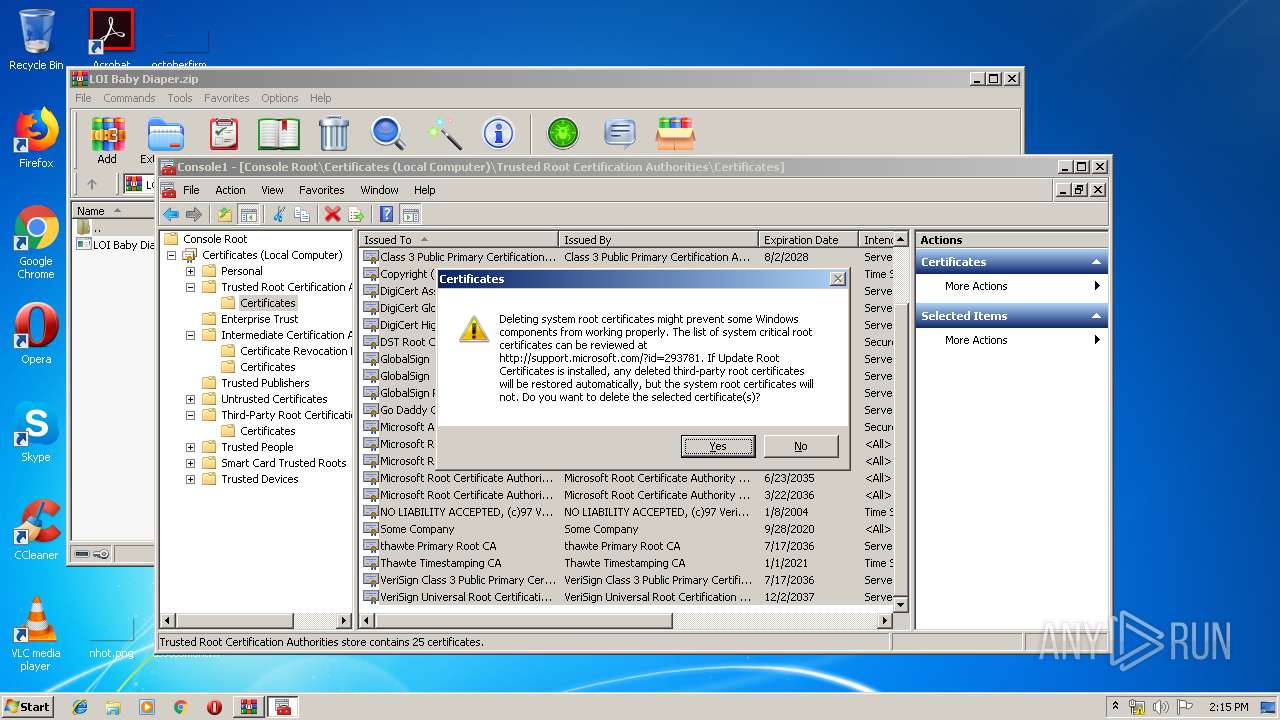
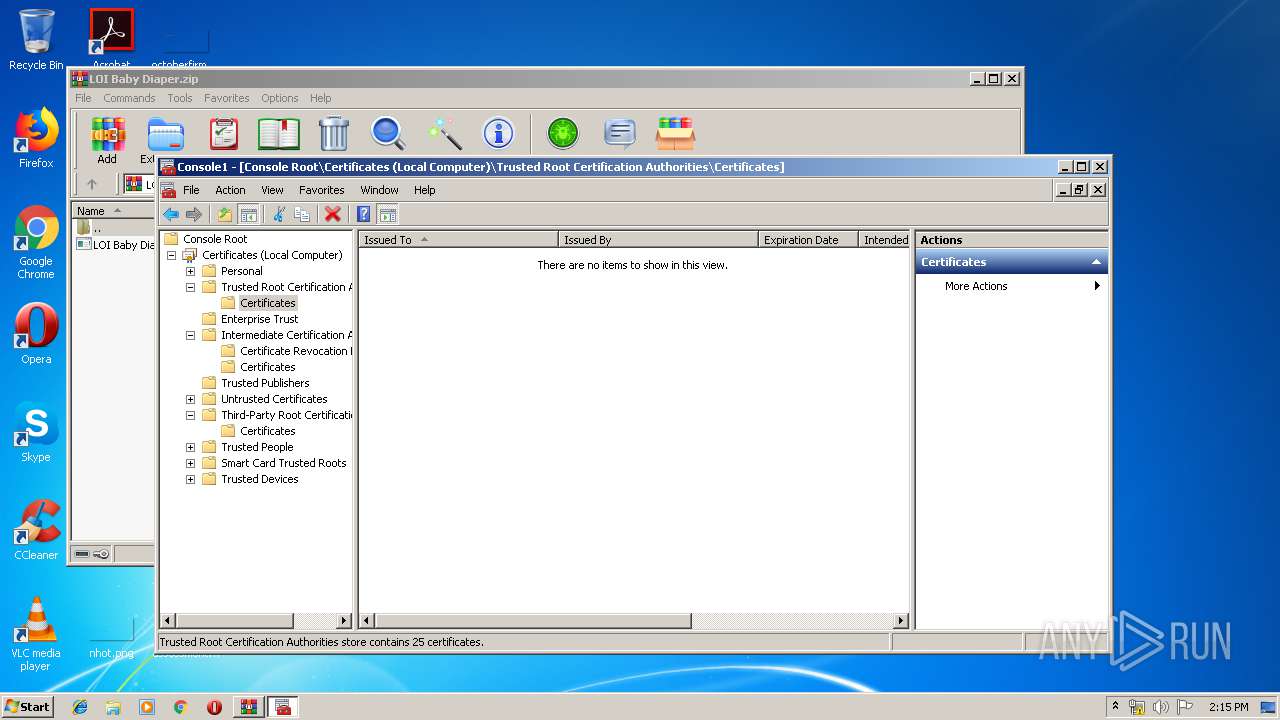
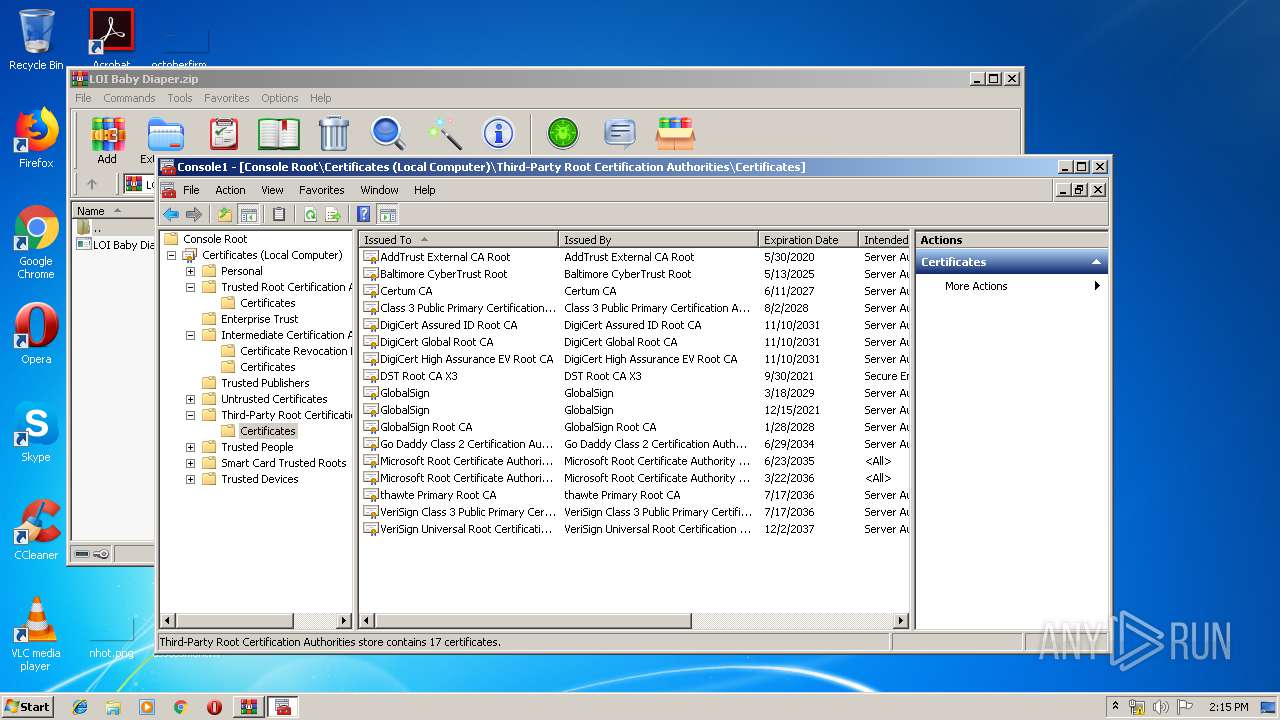
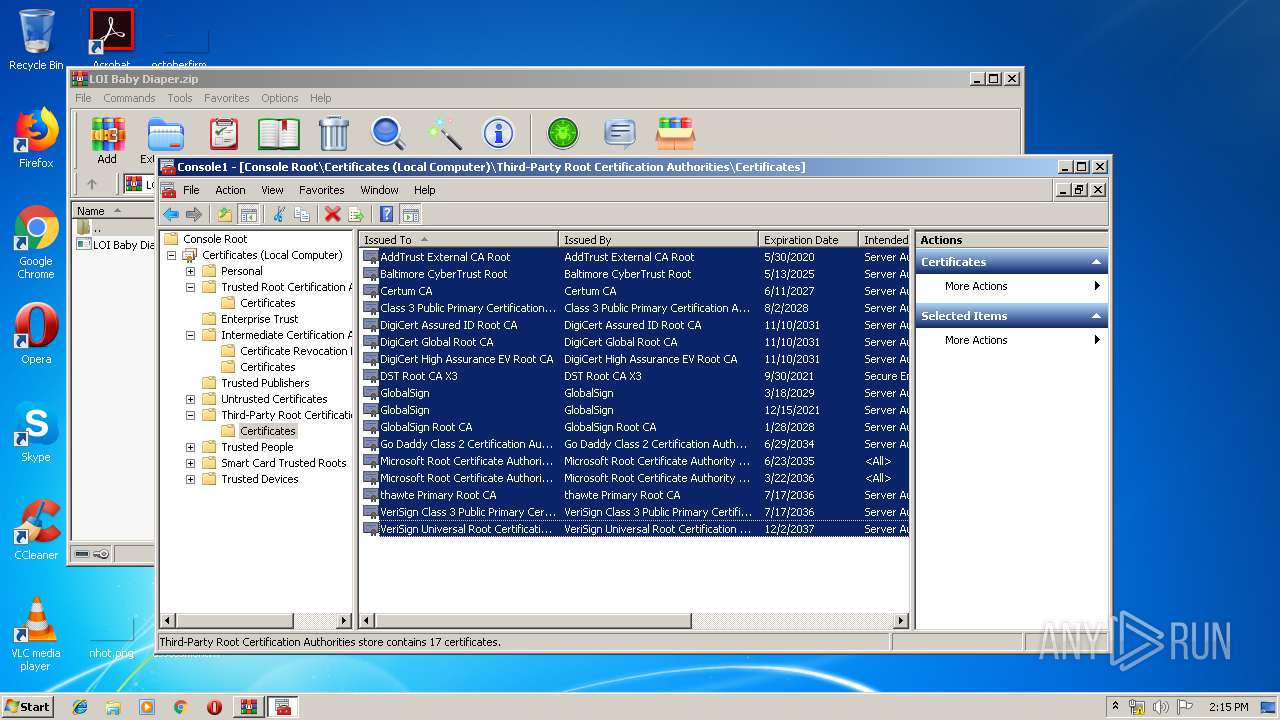
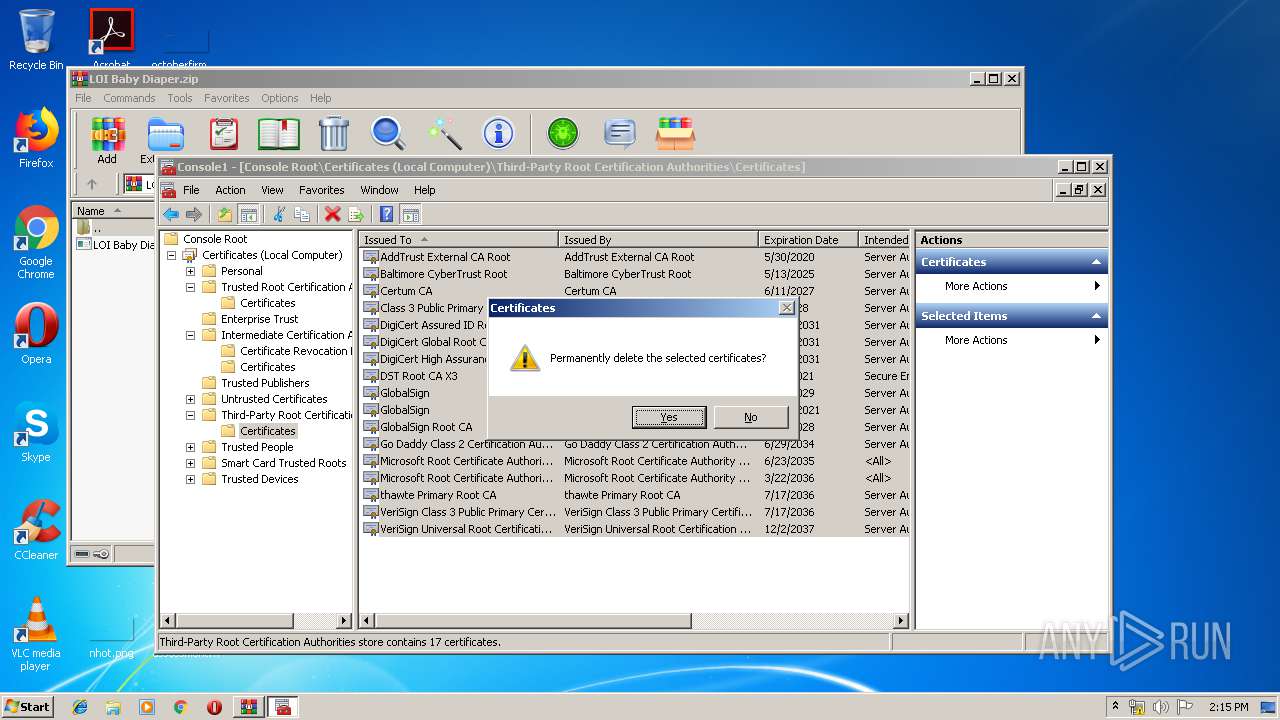
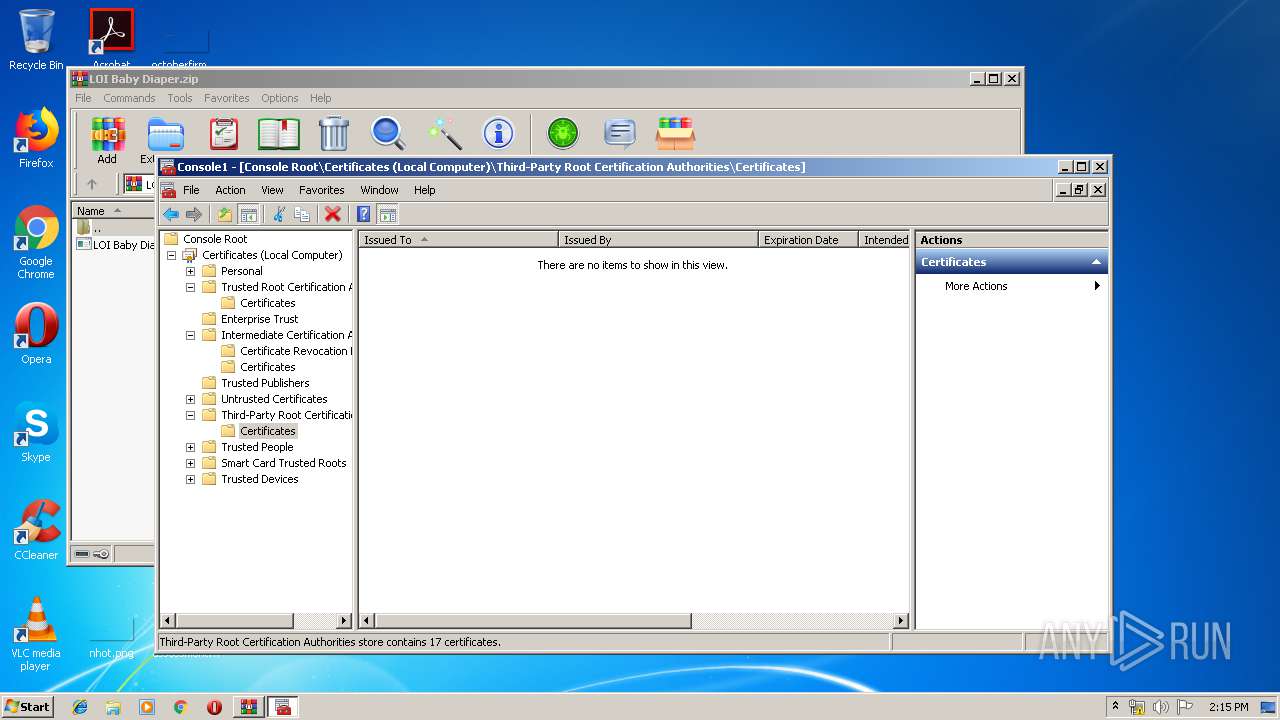
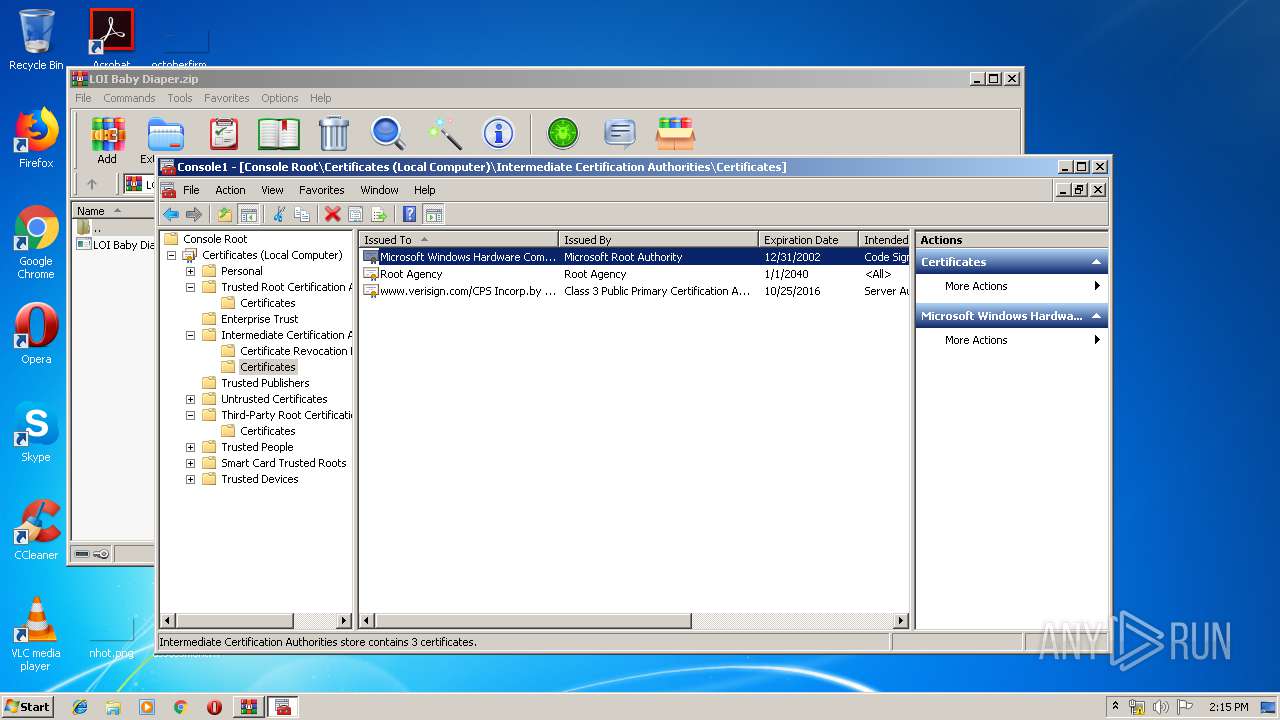
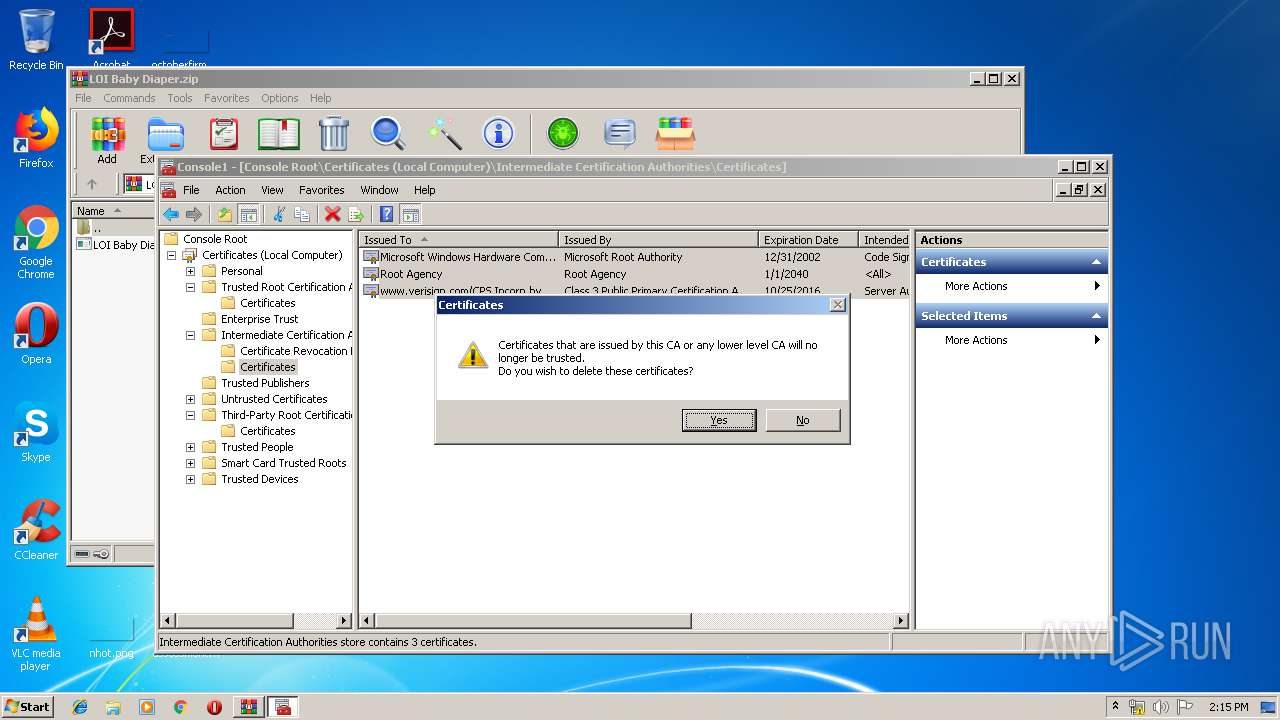
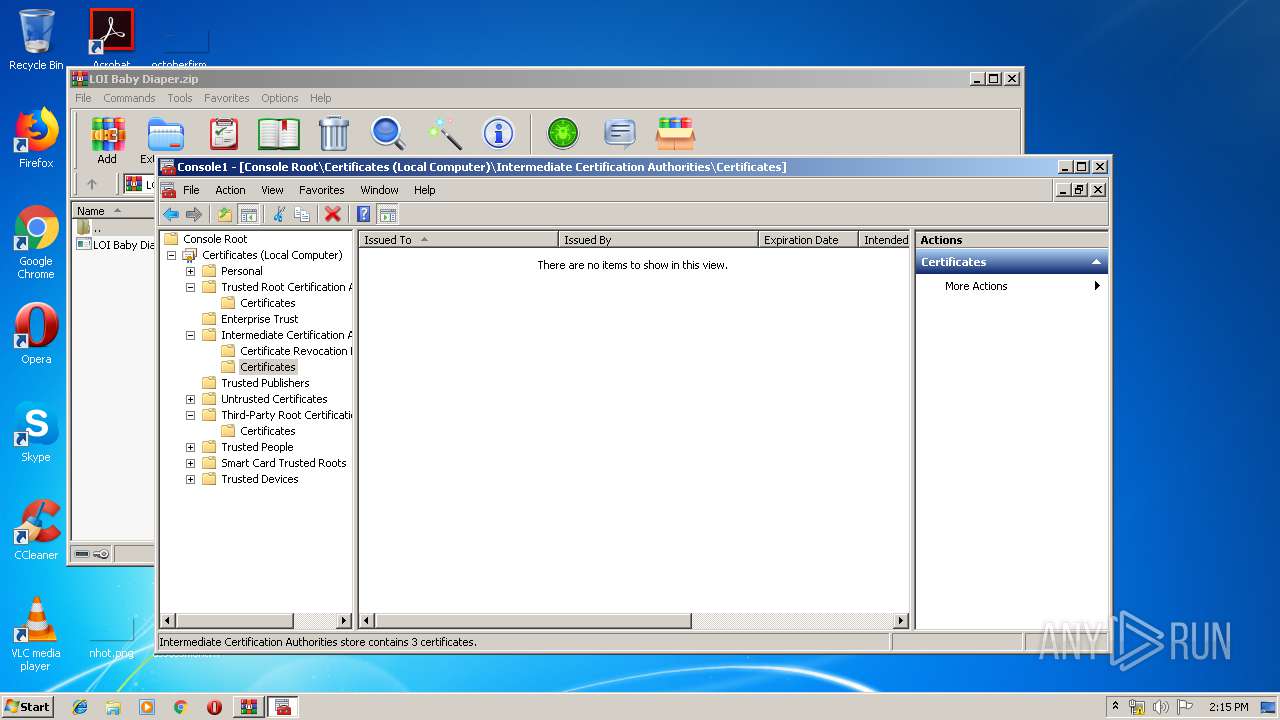
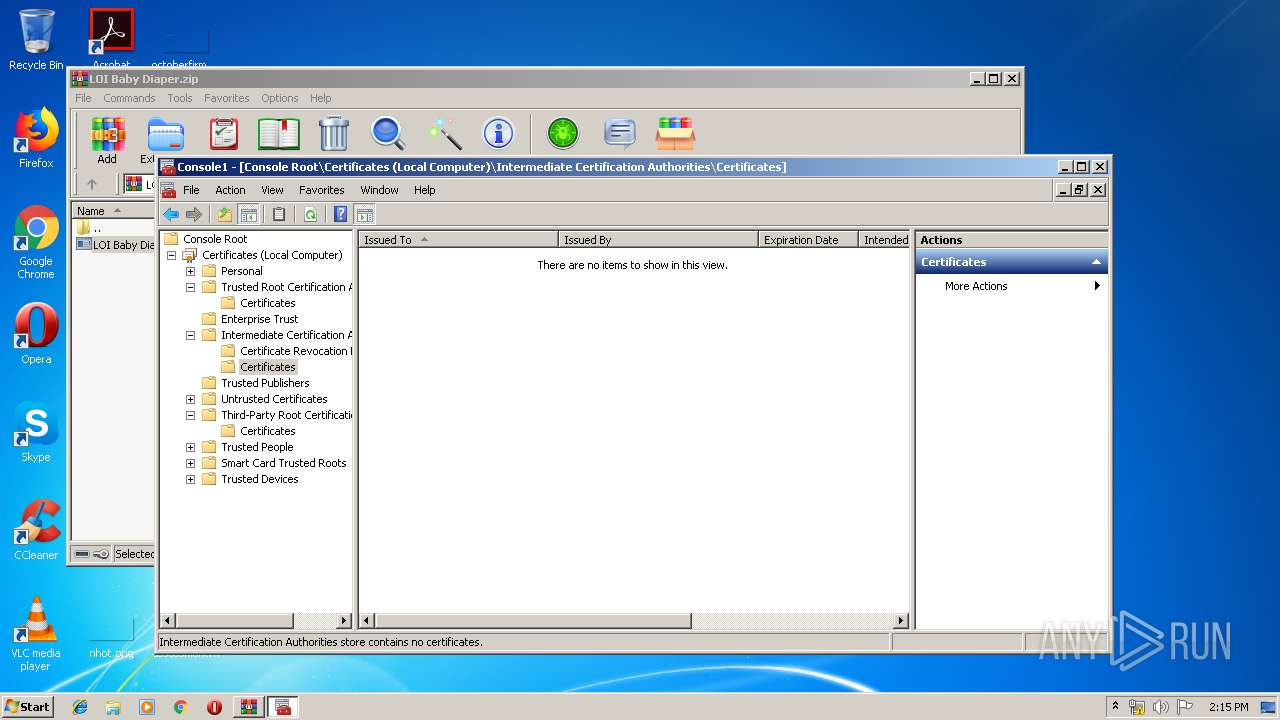
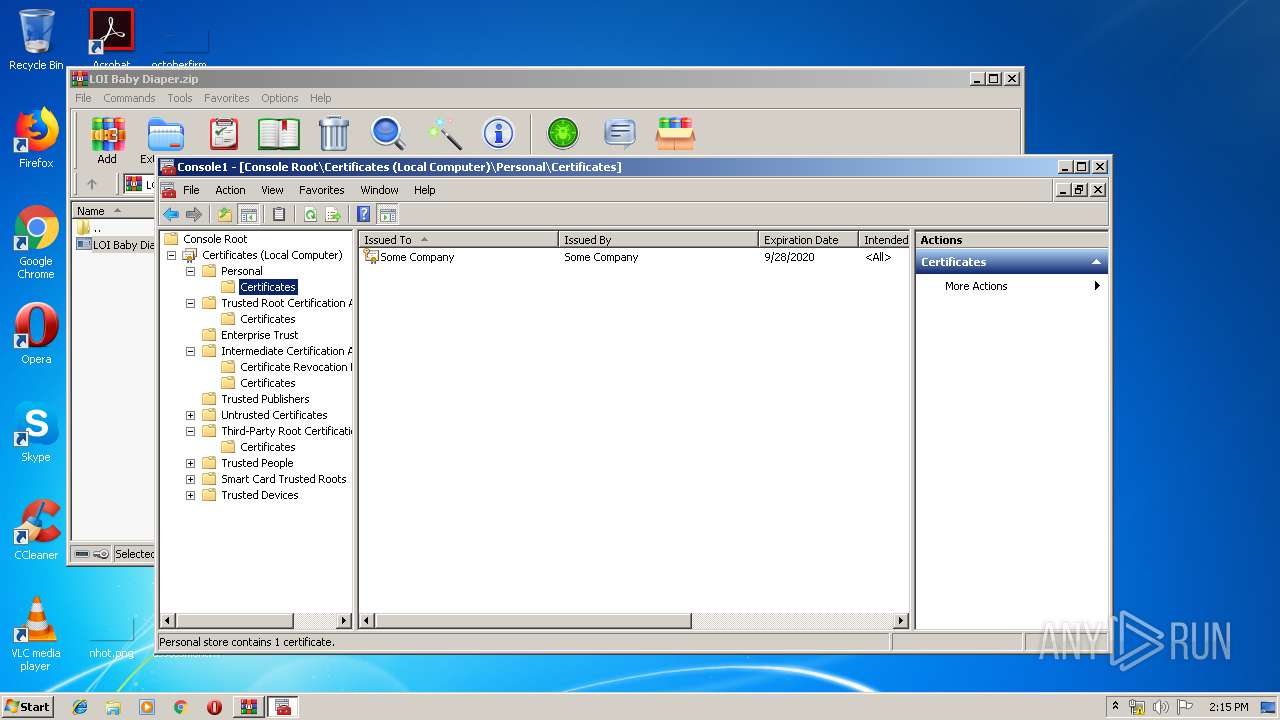
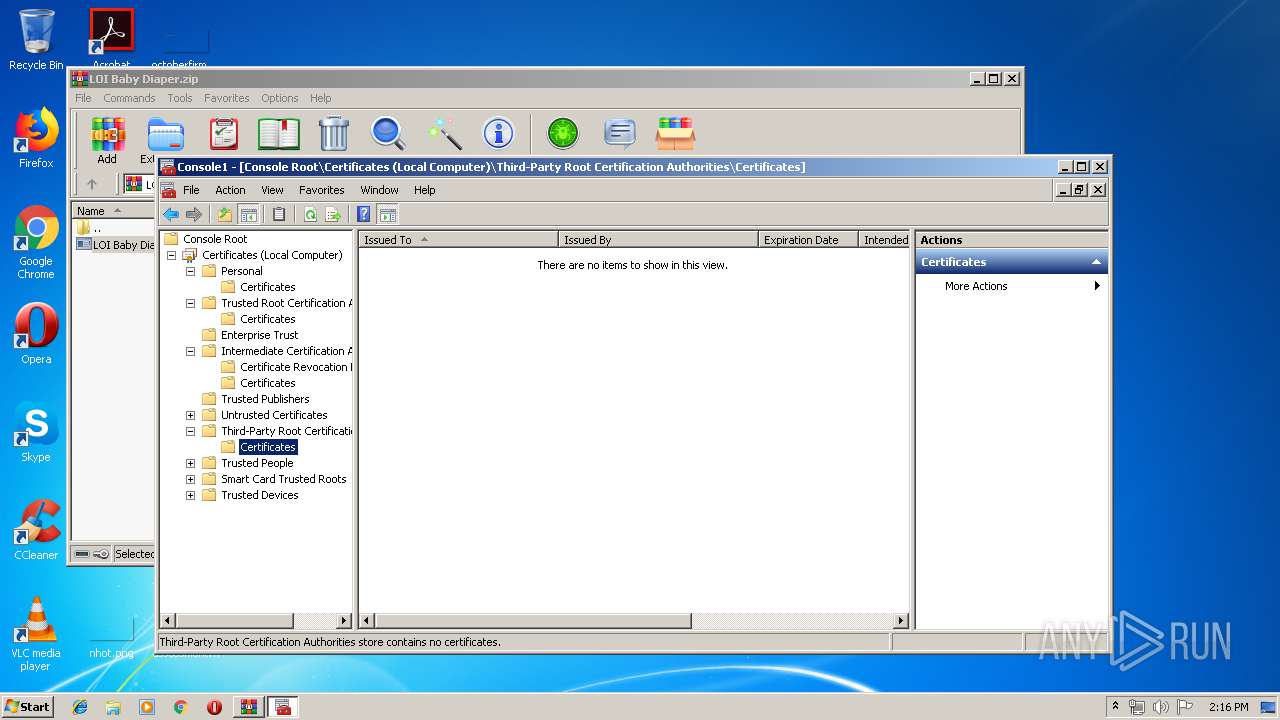
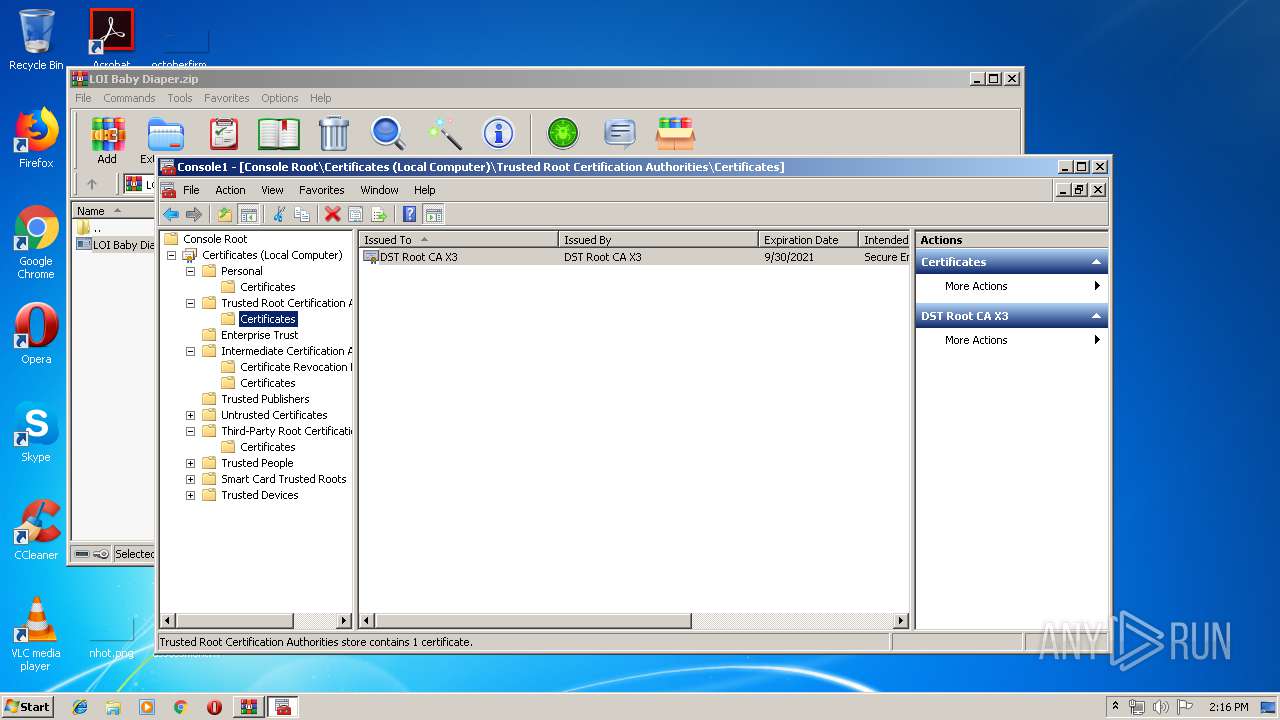
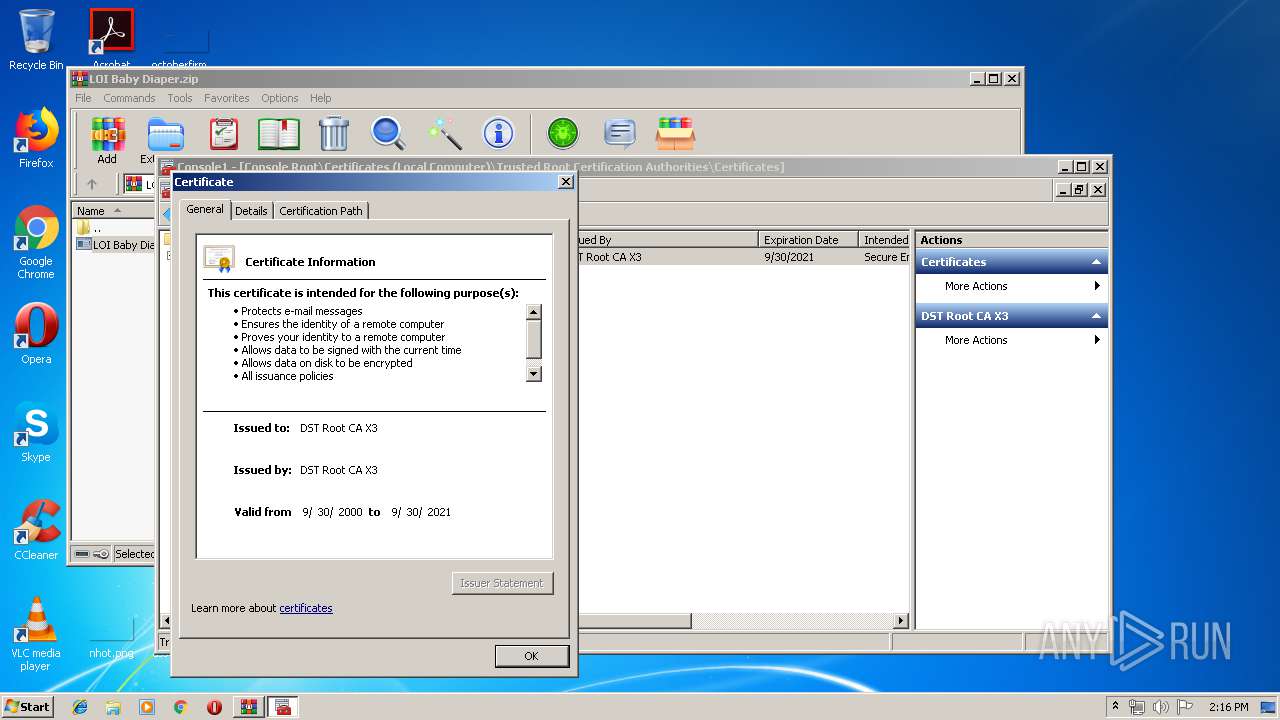
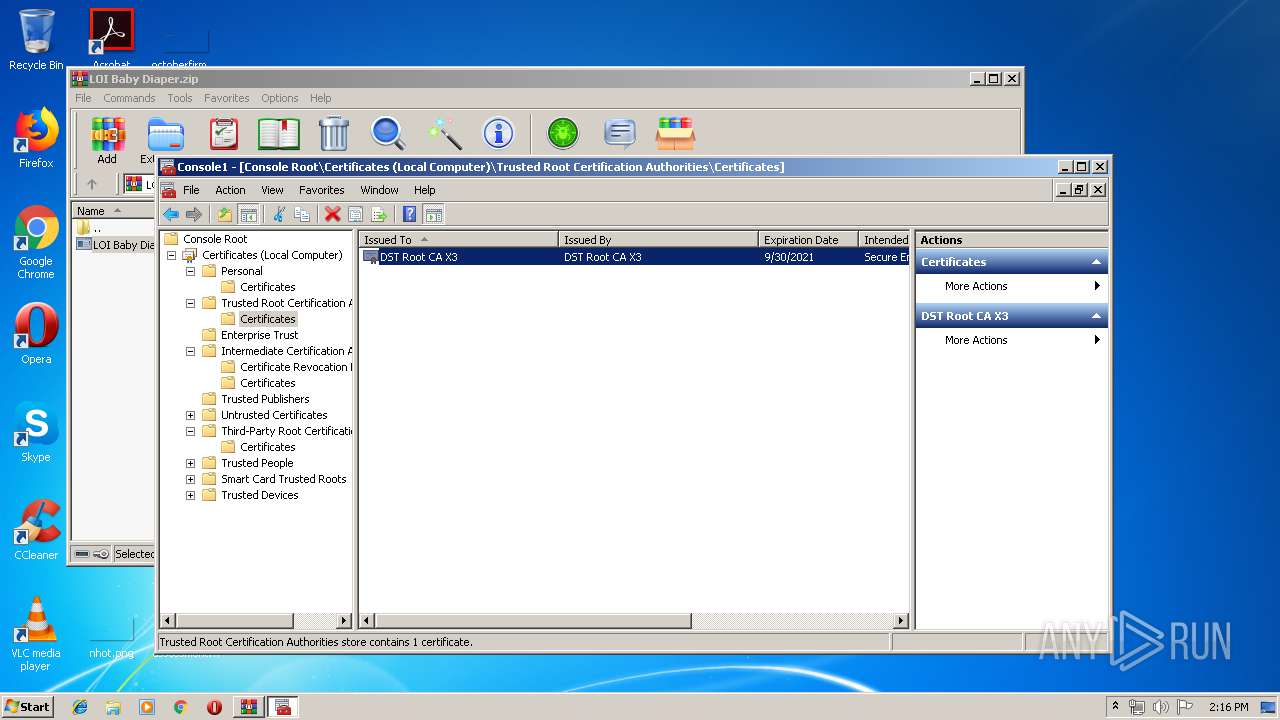
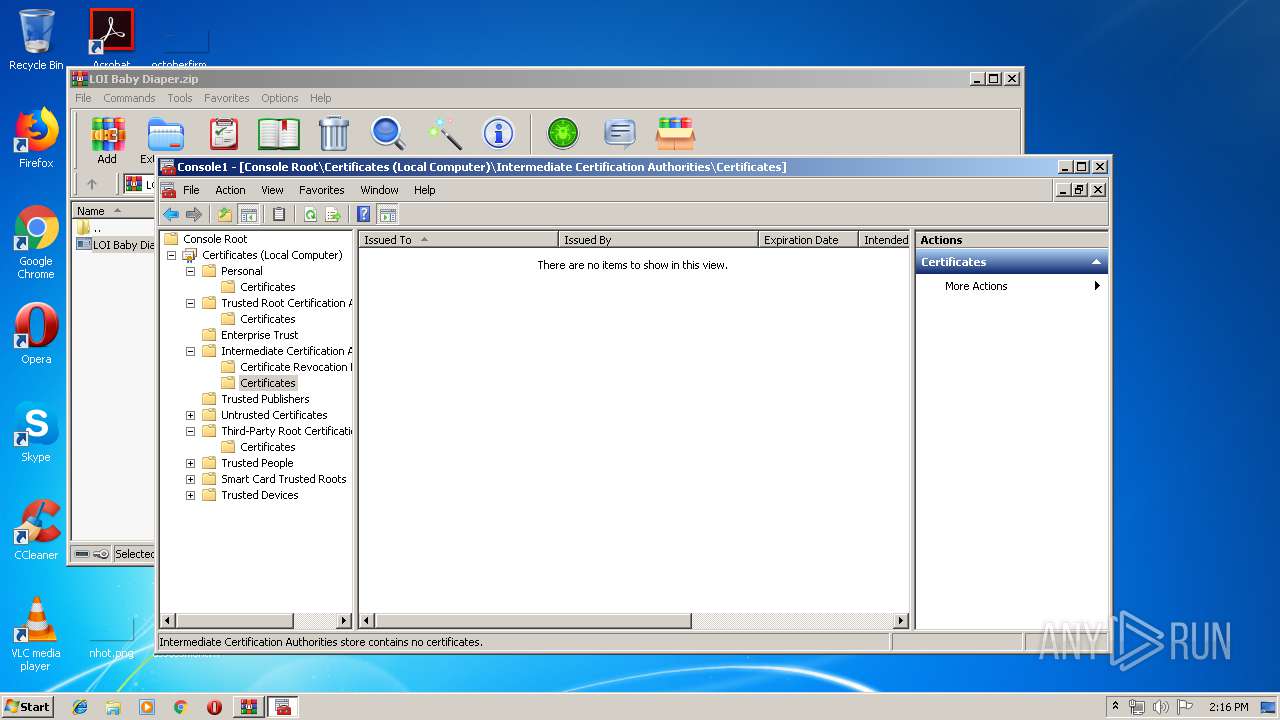
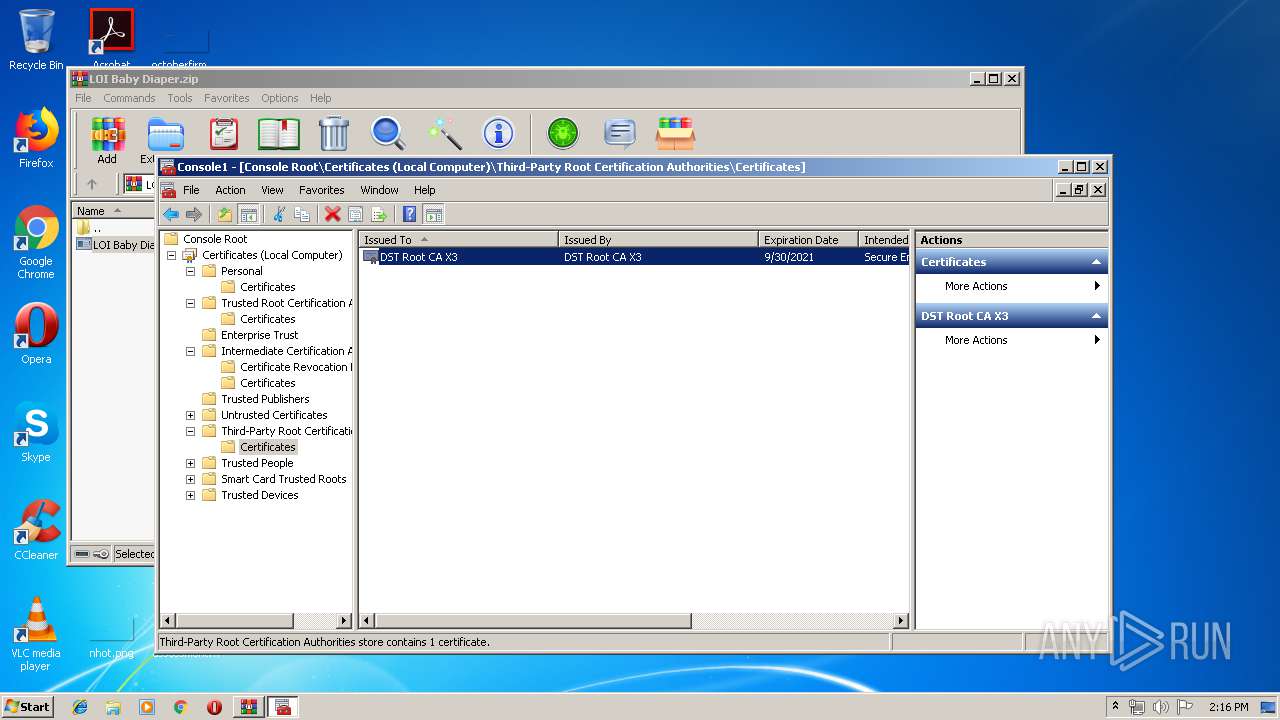
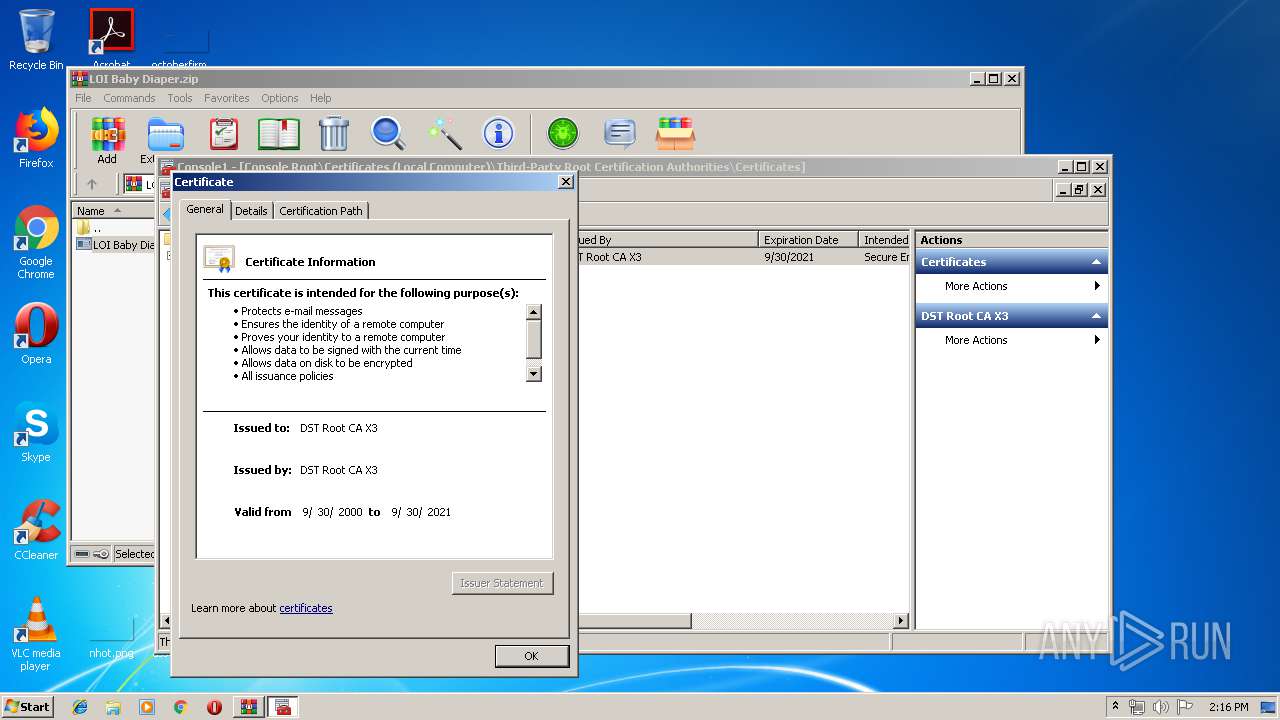
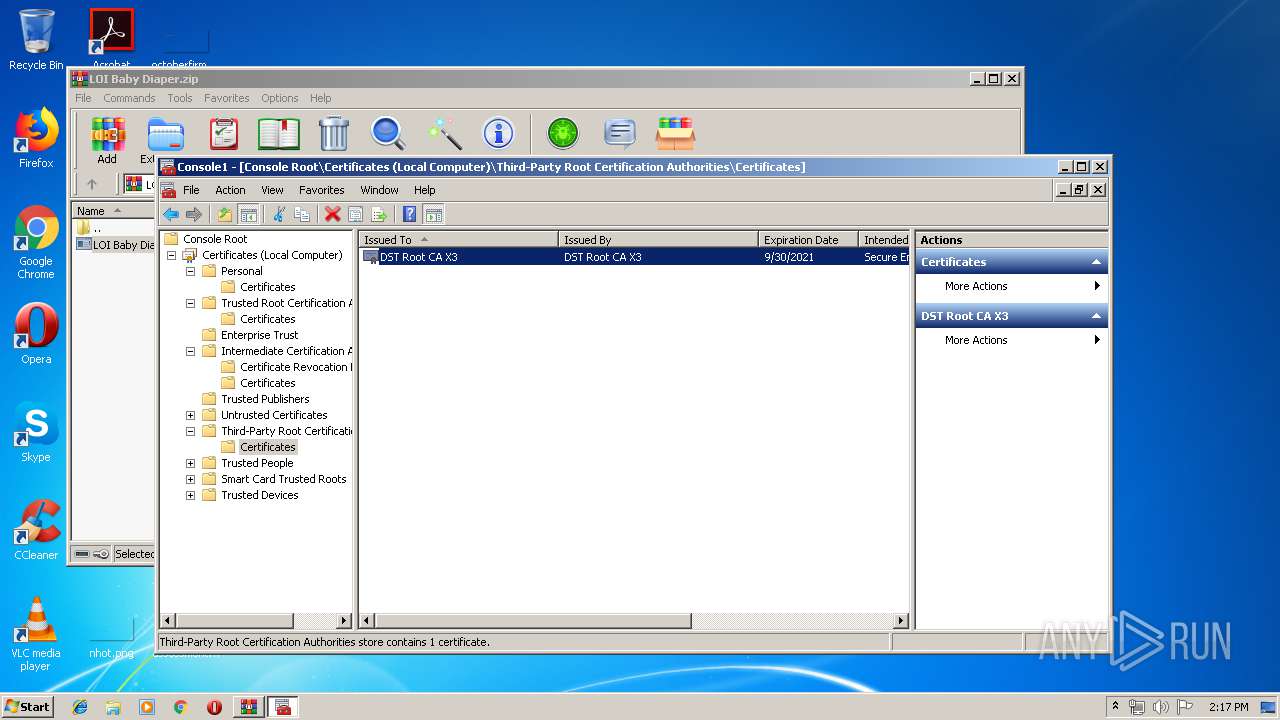
Changes settings of System certificates
- mmc.exe (PID: 3164)
Changes the autorun value in the registry
- RegAsm.exe (PID: 2440)
AGENTTESLA was detected
- RegAsm.exe (PID: 2440)
SUSPICIOUS
Adds / modifies Windows certificates
- mmc.exe (PID: 3164)
Checks for external IP
- RegAsm.exe (PID: 2440)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2192)
- RegAsm.exe (PID: 2440)
Creates files in the user directory
- RegAsm.exe (PID: 2440)
INFO
Reads settings of System Certificates
- mmc.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
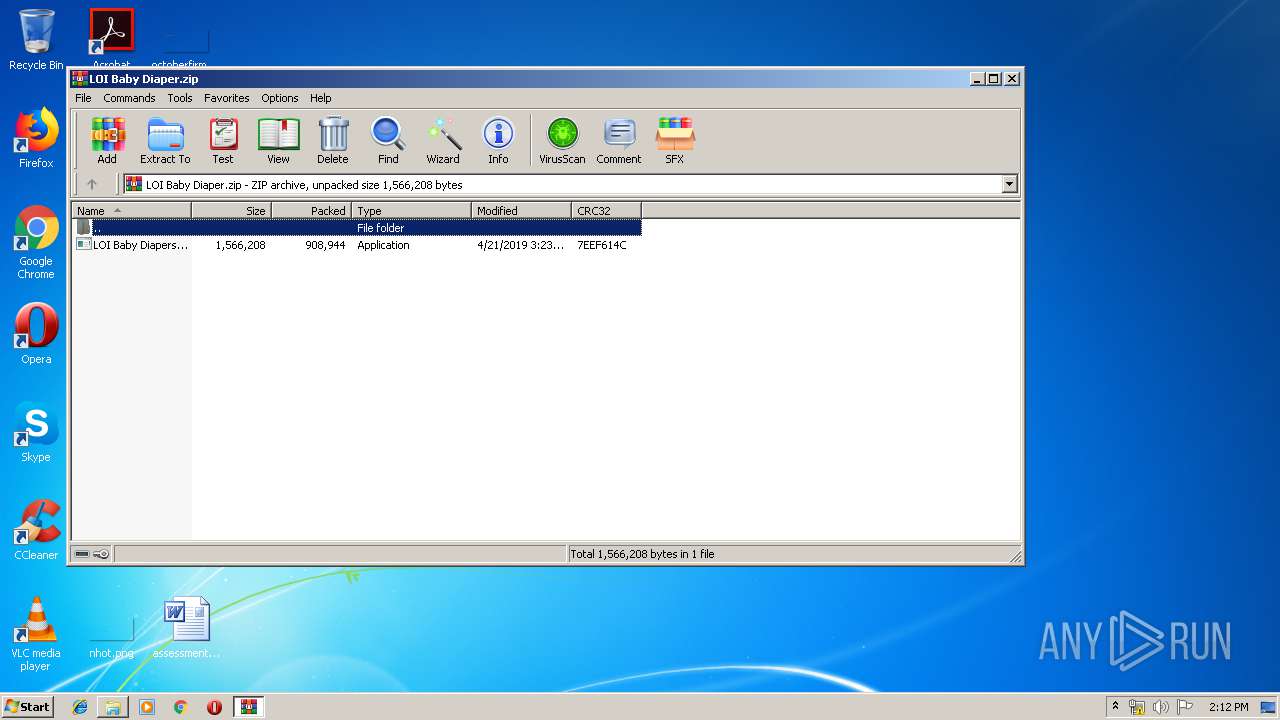
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:21 03:23:12 |
| ZipCRC: | 0x7eef614c |
| ZipCompressedSize: | 908944 |
| ZipUncompressedSize: | 1566208 |
| ZipFileName: | LOI Baby Diapers.exe |
Total processes
39
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2192.3984\LOI Baby Diapers.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2192.3984\LOI Baby Diapers.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1564 | "C:\Windows\system32\mmc.exe" | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\LOI Baby Diaper.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2440 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | LOI Baby Diapers.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3164 | "C:\Windows\system32\mmc.exe" | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
812
Read events
559
Write events
225
Delete events
28
Modification events
| (PID) Process: | (2192) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2192) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2192) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2192) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\LOI Baby Diaper.zip | |||
| (PID) Process: | (2192) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2192) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2192) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2192) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3164) mmc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3164) mmc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @mmcbase.dll,-14008 |
Value: Folder | |||
Executable files
2
Suspicious files
5
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2440 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\CabB255.tmp | — | |
MD5:— | SHA256:— | |||
| 2440 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\TarB256.tmp | — | |
MD5:— | SHA256:— | |||
| 2440 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\CabB40D.tmp | — | |
MD5:— | SHA256:— | |||
| 2440 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\TarB40E.tmp | — | |
MD5:— | SHA256:— | |||
| 2440 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFF55909D2135D890139AF266D697294 | binary | |
MD5:— | SHA256:— | |||
| 2440 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\94308059B57B3142E455B38A6EB92015 | binary | |
MD5:— | SHA256:— | |||
| 2440 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94308059B57B3142E455B38A6EB92015 | compressed | |
MD5:— | SHA256:— | |||
| 2440 | RegAsm.exe | C:\Users\admin\AppData\Roaming\Newapp\Newapp.exe | executable | |
MD5:278EDBD499374BF73621F8C1F969D894 | SHA256:C6999B9F79932C3B4F1C461A69D9DC8DC301D6A155ABC33EFE1B6E9E4A038391 | |||
| 2192 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2192.3984\LOI Baby Diapers.exe | executable | |
MD5:— | SHA256:— | |||
| 2440 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFF55909D2135D890139AF266D697294 | der | |
MD5:E1C07EA0AABBD4B77B84C228117808A7 | SHA256:885DE64C340E3EA70658F01E1145F957FCDA27AABEEA1AB9FAA9FDB0102D4077 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
5
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2440 | RegAsm.exe | GET | 200 | 18.211.215.84:80 | http://checkip.amazonaws.com/ | US | text | 14 b | malicious |
2440 | RegAsm.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
2440 | RegAsm.exe | GET | 200 | 23.57.4.240:80 | http://www.microsoft.com/pki/certs/MicrosoftRootCert.crt | US | der | 1.40 Kb | whitelisted |
1056 | svchost.exe | GET | 200 | 23.57.4.240:80 | http://www.microsoft.com/pki/certs/MicrosoftRootCert.crt | US | der | 1.40 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2440 | RegAsm.exe | 192.185.109.4:587 | mail.diamondsonearth.com | CyrusOne LLC | US | malicious |
2440 | RegAsm.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2440 | RegAsm.exe | 23.57.4.240:80 | www.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
1056 | svchost.exe | 23.57.4.240:80 | www.microsoft.com | Akamai Technologies, Inc. | US | whitelisted |
2440 | RegAsm.exe | 18.211.215.84:80 | checkip.amazonaws.com | — | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.diamondsonearth.com |
| malicious |
www.microsoft.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
checkip.amazonaws.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2440 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2 ETPRO signatures available at the full report