| File name: | 1 (624) |
| Full analysis: | https://app.any.run/tasks/9b036181-7d30-4ef8-b816-51e8f1dd8241 |
| Verdict: | Malicious activity |
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
| Analysis date: | March 25, 2025, 02:27:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 059AECCF56DBCE54327011C433E3C130 |
| SHA1: | 15BD464823ADFED24D55BDEDF79EDDB96F047E6C |
| SHA256: | 91B0F13F6E4BA755FEB17FE762306C74D1A42447C1EE2799618CCB9E74384DBB |
| SSDEEP: | 3072:0nUFKt3AoncEpr1sYfQot/ImihzIYY5BV9UCuvAXBYIMkuBbtplkPWzYlbpza5cc:bFwf3oo5ImihMrfVFuvYYIMWzad |
MALICIOUS
GH0ST mutex has been found
- svchost.exe (PID: 3304)
- rundll32.exe (PID: 2504)
- rundll32.exe (PID: 5204)
- svchost.exe (PID: 6388)
Create files in the Startup directory
- rundll32.exe (PID: 2504)
- svchost.exe (PID: 6388)
- rundll32.exe (PID: 5204)
SUSPICIOUS
Creates file in the systems drive root
- rundll32.exe (PID: 2504)
- svchost.exe (PID: 3304)
- rundll32.exe (PID: 5204)
- svchost.exe (PID: 6388)
Executable content was dropped or overwritten
- rundll32.exe (PID: 2504)
Executes application which crashes
- svchost.exe (PID: 3304)
- rundll32.exe (PID: 2504)
- rundll32.exe (PID: 5204)
Connects to unusual port
- rundll32.exe (PID: 2504)
- rundll32.exe (PID: 5204)
- svchost.exe (PID: 6388)
Runs shell command (SCRIPT)
- mshta.exe (PID: 7432)
INFO
Creates files or folders in the user directory
- rundll32.exe (PID: 2504)
- WerFault.exe (PID: 7224)
- WerFault.exe (PID: 7468)
- WerFault.exe (PID: 7244)
- rundll32.exe (PID: 5204)
- WerFault.exe (PID: 1328)
- BackgroundTransferHost.exe (PID: 4756)
Autorun file from Startup directory
- rundll32.exe (PID: 2504)
- rundll32.exe (PID: 5204)
- svchost.exe (PID: 6388)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8184)
- BackgroundTransferHost.exe (PID: 4756)
- BackgroundTransferHost.exe (PID: 1020)
- BackgroundTransferHost.exe (PID: 6080)
- BackgroundTransferHost.exe (PID: 7900)
- BackgroundTransferHost.exe (PID: 6036)
Reads Internet Explorer settings
- mshta.exe (PID: 7432)
Manual execution by a user
- mshta.exe (PID: 7432)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 4756)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 4756)
- slui.exe (PID: 7608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, DLL, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 130560 |
| InitializedDataSize: | 9216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20c24 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
158
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5204 -s 1148 | C:\Windows\SysWOW64\WerFault.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2504 | "C:\WINDOWS\SysWOW64\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\1 (624).dll", #1 | C:\Windows\SysWOW64\rundll32.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225477 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3304 | C:\WINDOWS\system32\svchost.exe -k rundll32 | C:\Windows\SysWOW64\svchost.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4756 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
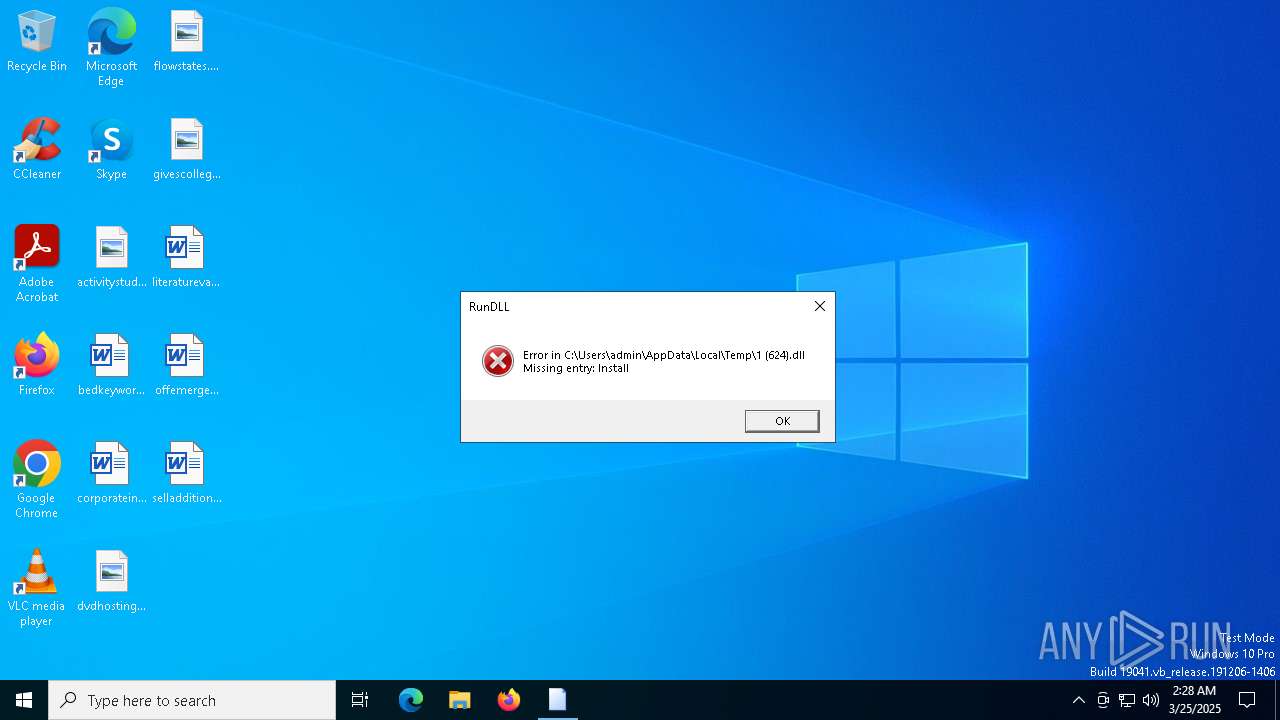
| 5204 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\1 (624).dll" Install | C:\Windows\SysWOW64\rundll32.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221226505 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6036 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6080 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6388 | C:\WINDOWS\system32\svchost.exe -k rundll32 | C:\Windows\SysWOW64\svchost.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6740 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 757
Read events
10 736
Write events
21
Delete events
0
Modification events
| (PID) Process: | (8184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7432) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7432) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7432) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1020) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1020) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1020) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4756) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
2
Suspicious files
14
Text files
10
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7224 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_svchost.exe_556d693e15d9b189d4d4da412622c9aebb38e6a_f941bfa1_d4752e6d-cf3d-4816-828f-709b7132989b\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7244 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_rundll32.exe_8b96a266d05a3f926744fb2133f041e775accbd3_67c333ae_e58b91c5-32a5-4d96-9feb-2af21d335360\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7468 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_svchost.exe_78294fd08906cb2cb896b7ccc94ada43e92dab7_f941bfa1_f17babc5-b428-41fa-a5d4-a76e8dbdb6a9\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4756 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\c03174c4-f540-4a91-bf20-127c35a640ee.down_data | — | |
MD5:— | SHA256:— | |||
| 2504 | rundll32.exe | C:\Temp\AppPatch\comb.dll | text | |
MD5:D00AB6B03765AE50127C2357A92C2A4F | SHA256:9BF461DF720806F129AEC98A2D72432700299B03E1D33523C41CF886BF41E958 | |||
| 7224 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC094.tmp.WERInternalMetadata.xml | binary | |
MD5:3D24019030B8A0DCBB621CAADC83B57F | SHA256:C2001DEE1F3CD29D41F3136F67F01A167DEEA286D155B730E3213F451BC96E87 | |||
| 2504 | rundll32.exe | C:\Windows\Temp\comb.dll | text | |
MD5:D00AB6B03765AE50127C2357A92C2A4F | SHA256:9BF461DF720806F129AEC98A2D72432700299B03E1D33523C41CF886BF41E958 | |||
| 7224 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERBF4A.tmp.dmp | binary | |
MD5:247F9D35F132B33EC9AD987D184D7B8A | SHA256:CBC5BE422E390B5EE95C80E569C078BD52C53180F6DDAB01FFFAF2F52F813461 | |||
| 2504 | rundll32.exe | C:\Temp\AppPatch\ComBack.Dll | executable | |
MD5:4303D8B74F47CAA3FE1BCD2F87A2798A | SHA256:A68483CC729B25C98BA1EA27D1B9B6EEAD7F927E9CFE6A88895A977A1B2ED581 | |||
| 2504 | rundll32.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Startup.hta | html | |
MD5:16314A598FE98F0CDA7F70B6121CA7AF | SHA256:3B58A824937D323B8A46822F9DD4309BFC7BFD3A72F7D2DAD7CD38CA5E72A60F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
31
DNS requests
22
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7308 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4756 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2316 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2316 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2504 | rundll32.exe | 221.10.93.196:2499 | — | CHINA UNICOM China169 Backbone | CN | unknown |
7308 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7308 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4756 | BackgroundTransferHost.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Guffery.3322.org |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to 3322.org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to 3322.org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to 3322.org Domain |