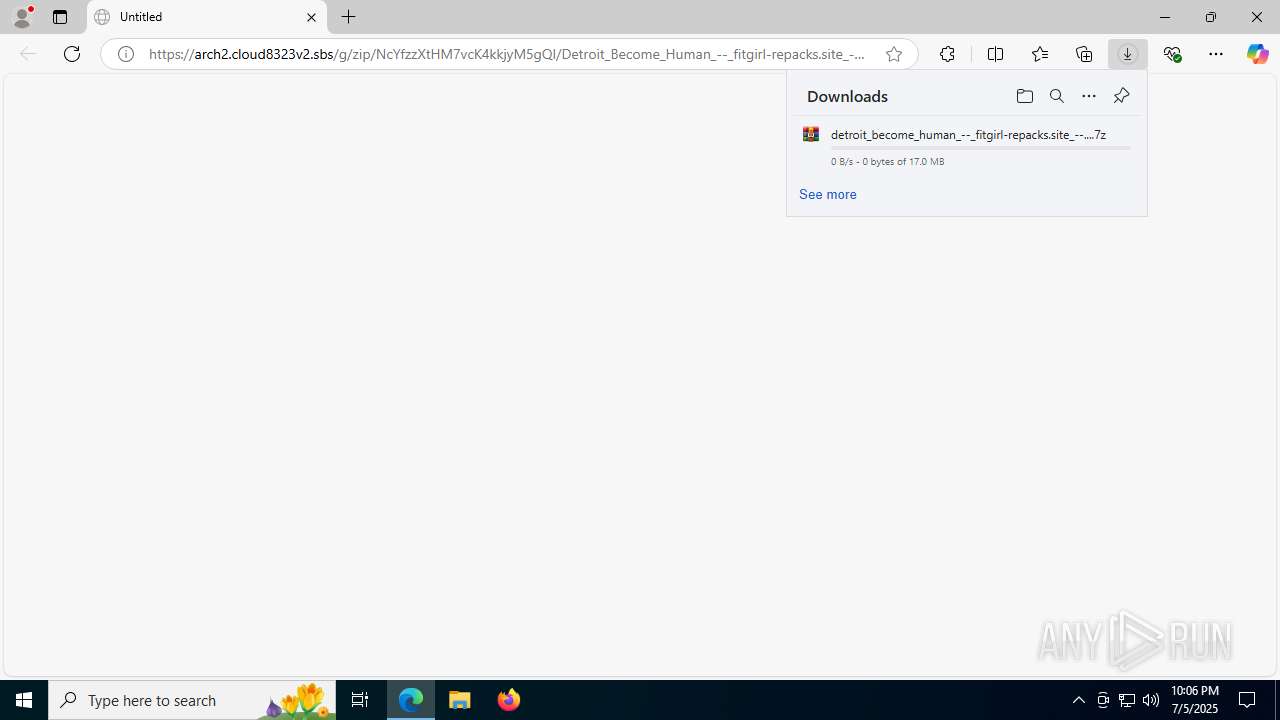
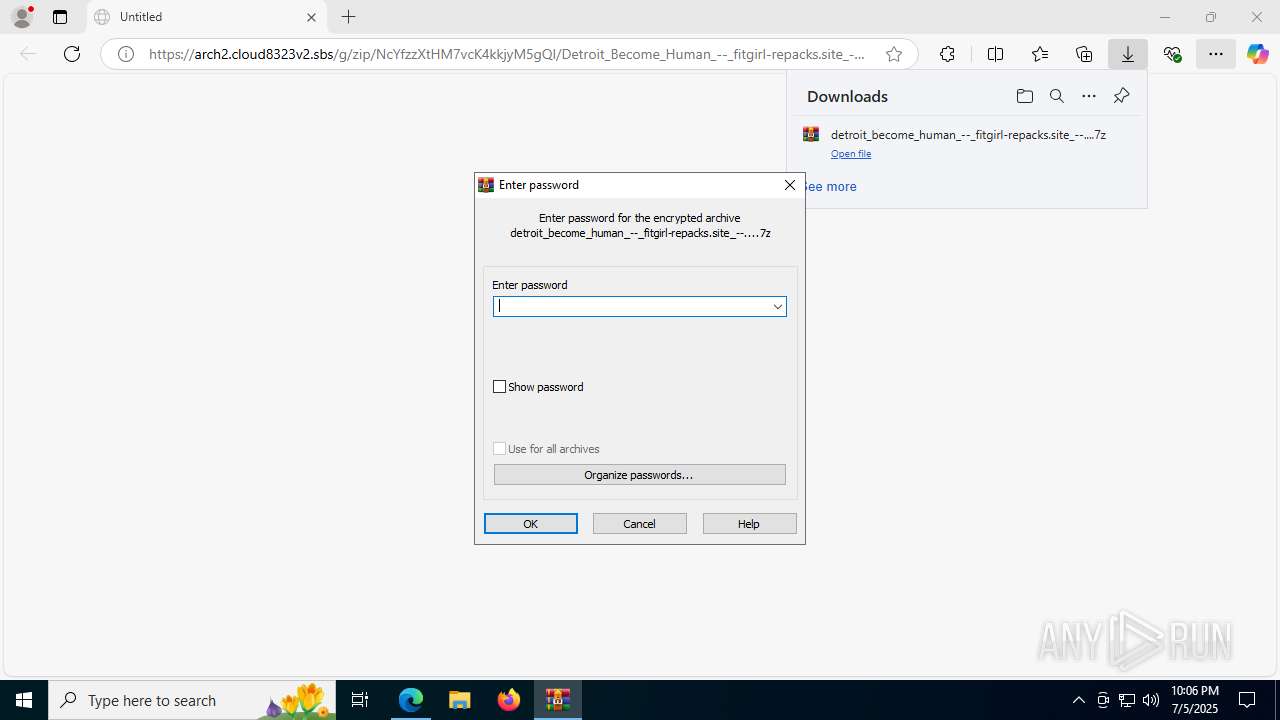
| URL: | https://arch2.cloud8323v2.sbs/g/zip/NcYfzzXtHM7vcK4kkjyM5gQI/Detroit_Become_Human_--_fitgirl-repacks.site_--....zip |
| Full analysis: | https://app.any.run/tasks/f6fadbe3-4184-4921-890f-64e9c26de306 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | July 05, 2025, 22:06:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
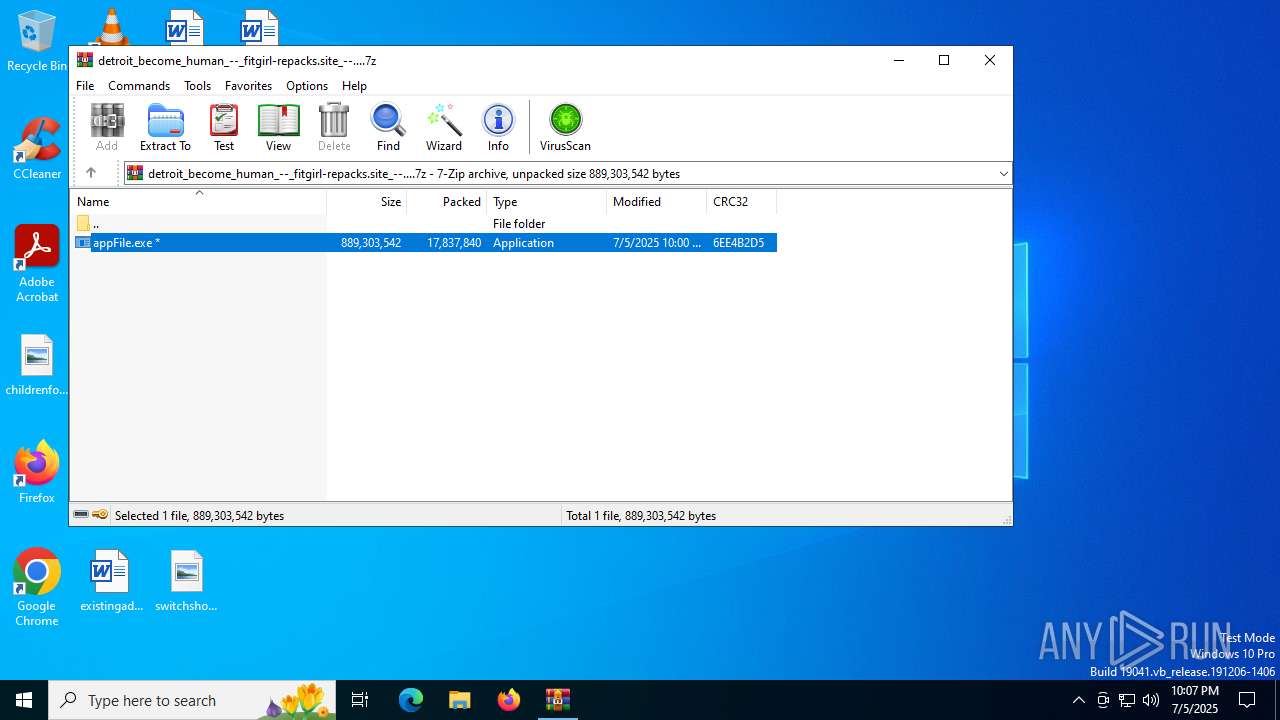
| MD5: | 89EAB686EBB3B155FCFAF1DAC9E71E7A |
| SHA1: | CE6555F7F56AC64F37DF52F61DCA8144FE556674 |
| SHA256: | 91890C337A86490304CF55F42974383E833254E1319169D8D3A49BF4695BD876 |
| SSDEEP: | 3:N8ox6nP7tr5ROgchsFaQlZnIyMXlJOXMmyQV:2oozt5oZhKaAZI/sVjV |
MALICIOUS
LUMMA mutex has been found
- Telephone.com (PID: 7156)
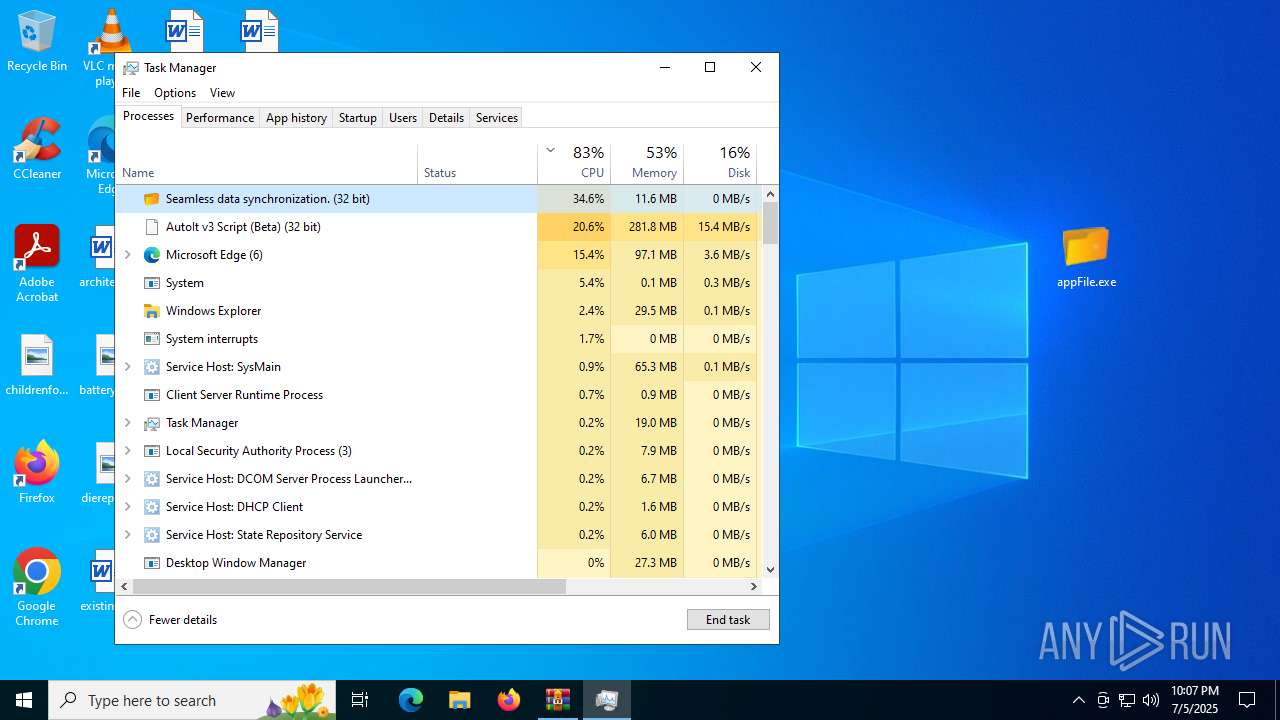
Steals credentials from Web Browsers
- Telephone.com (PID: 7156)
Actions looks like stealing of personal data
- Telephone.com (PID: 7156)
SUSPICIOUS
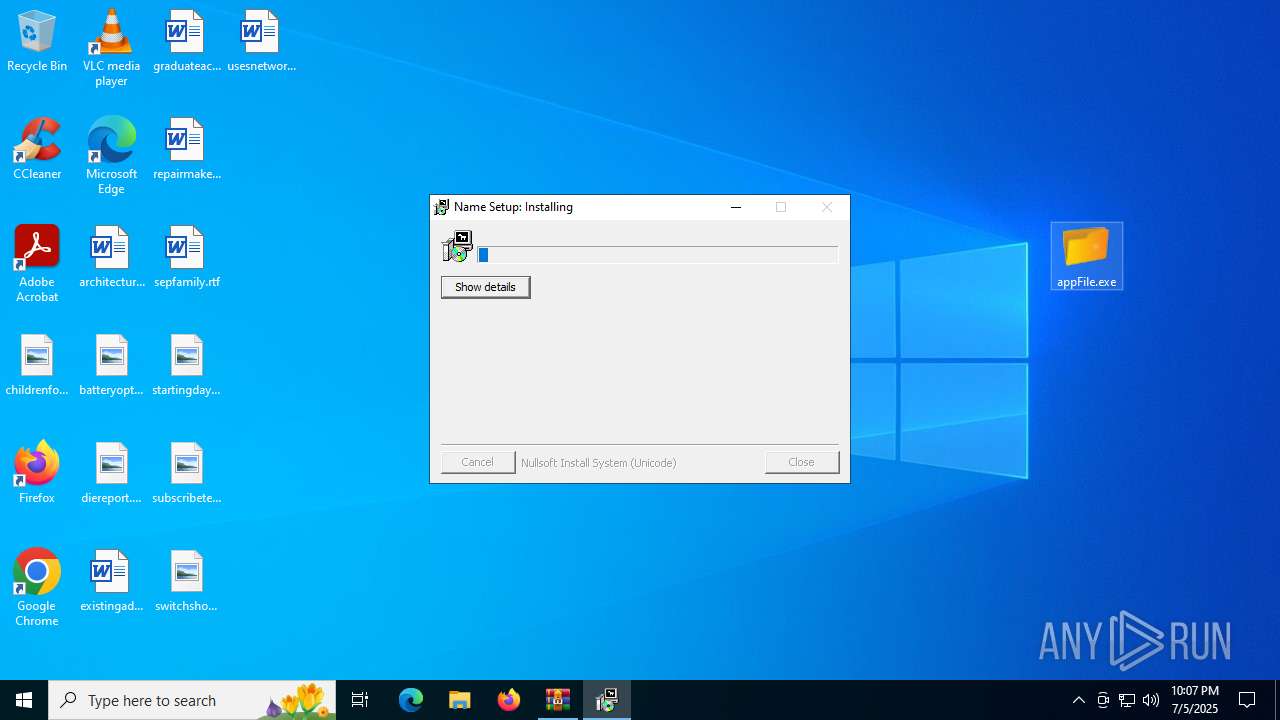
Reads security settings of Internet Explorer
- appFile.exe (PID: 8072)
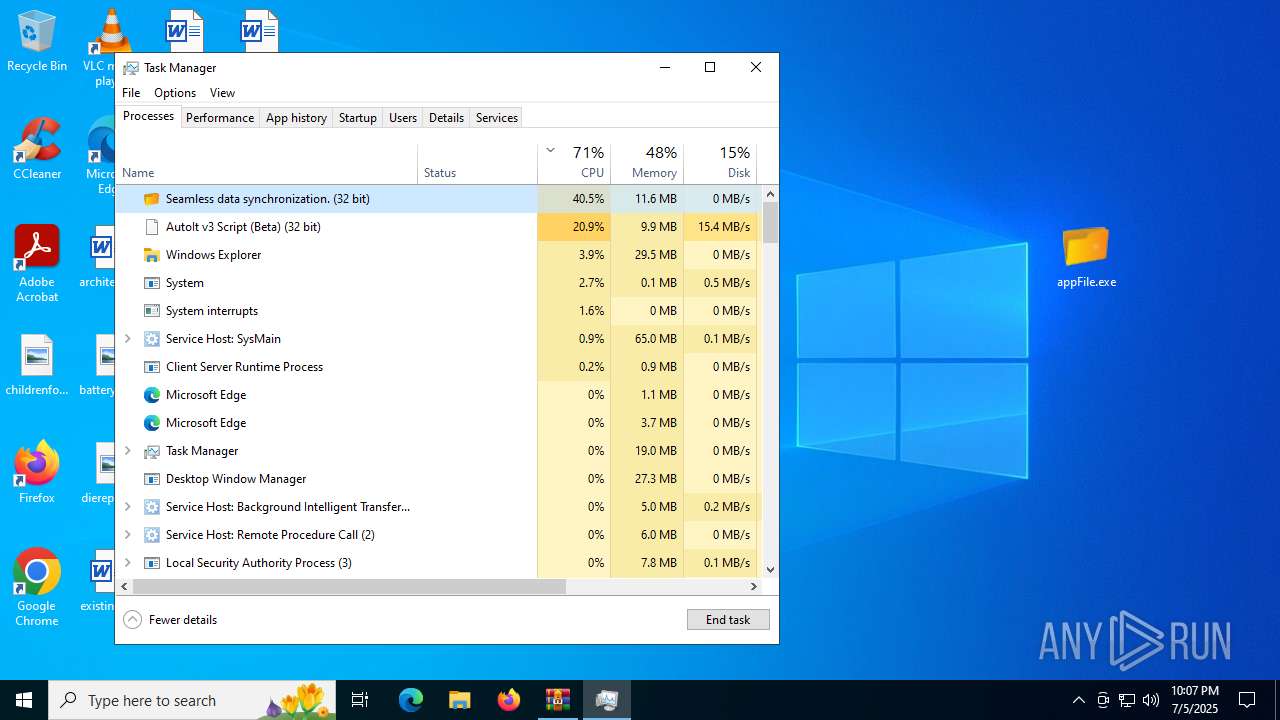
Executing commands from a ".bat" file
- appFile.exe (PID: 8072)
Starts CMD.EXE for commands execution
- appFile.exe (PID: 8072)
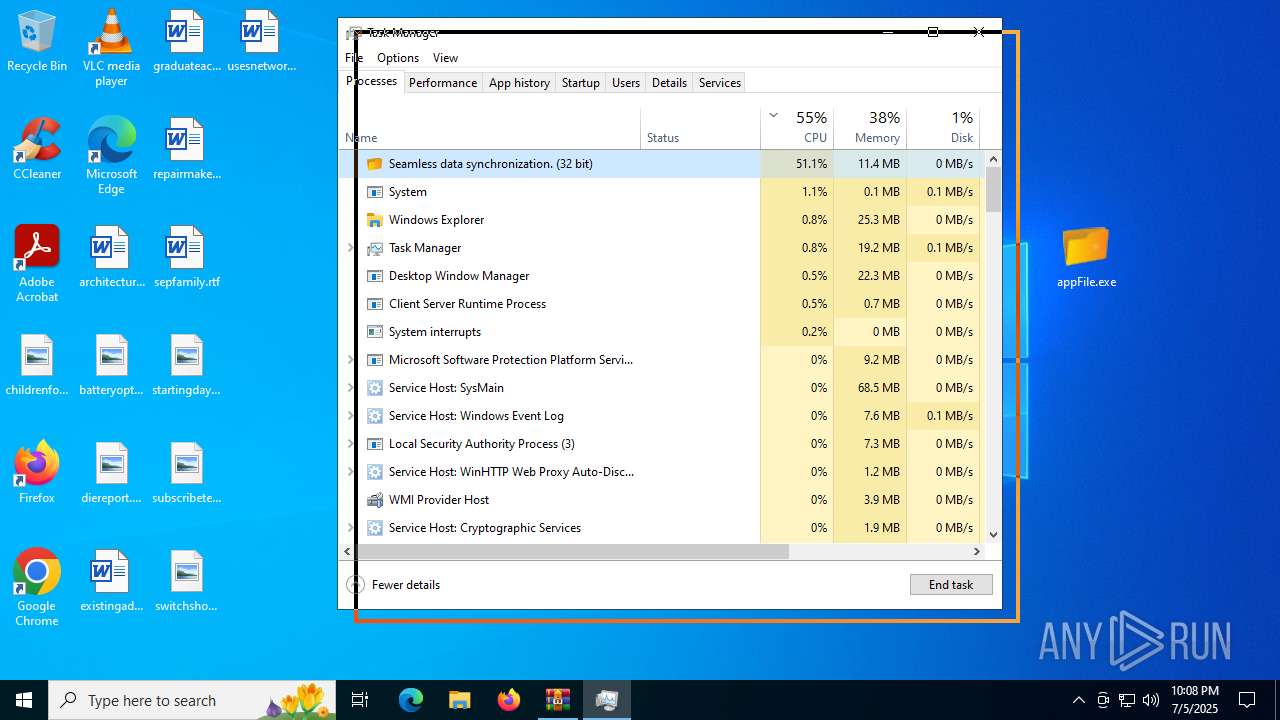
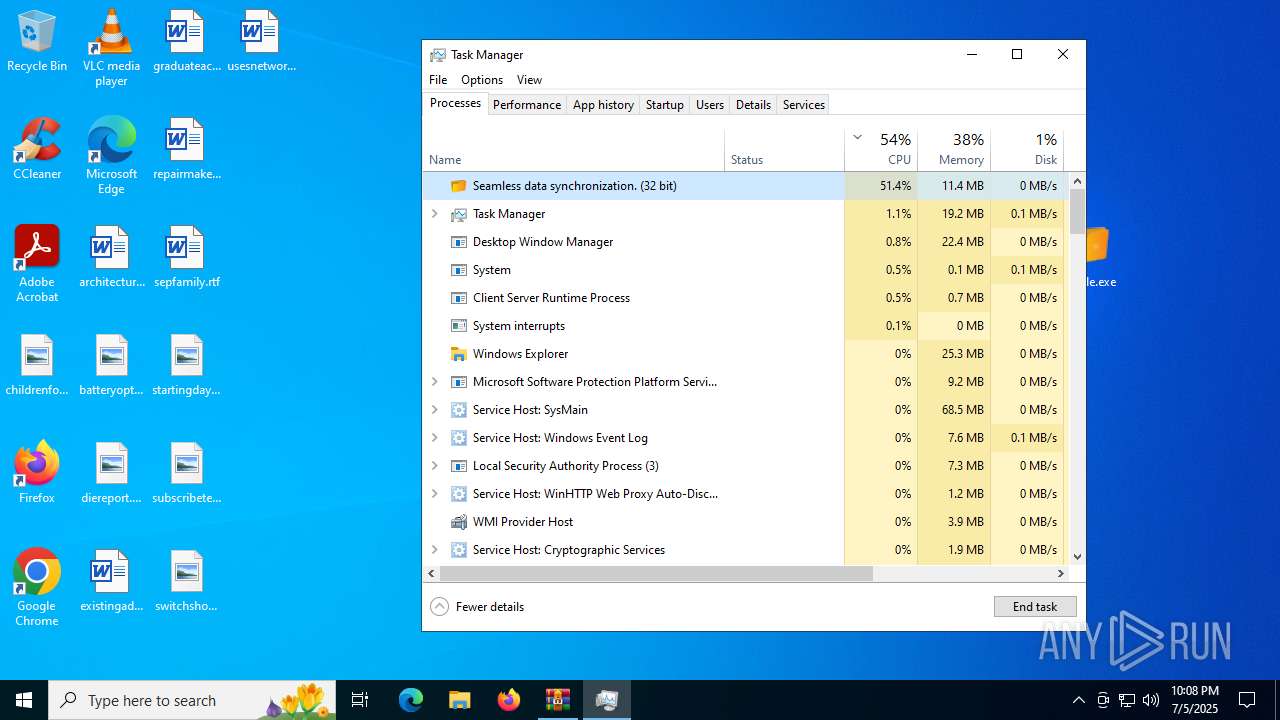
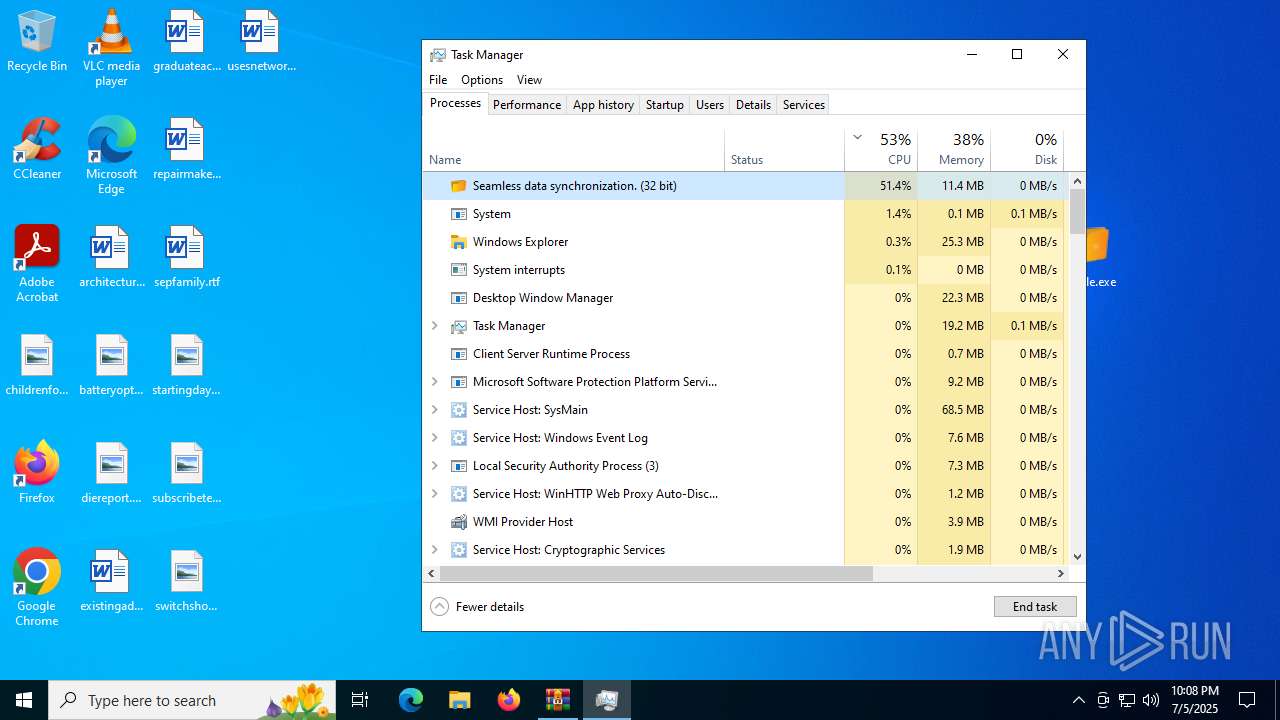
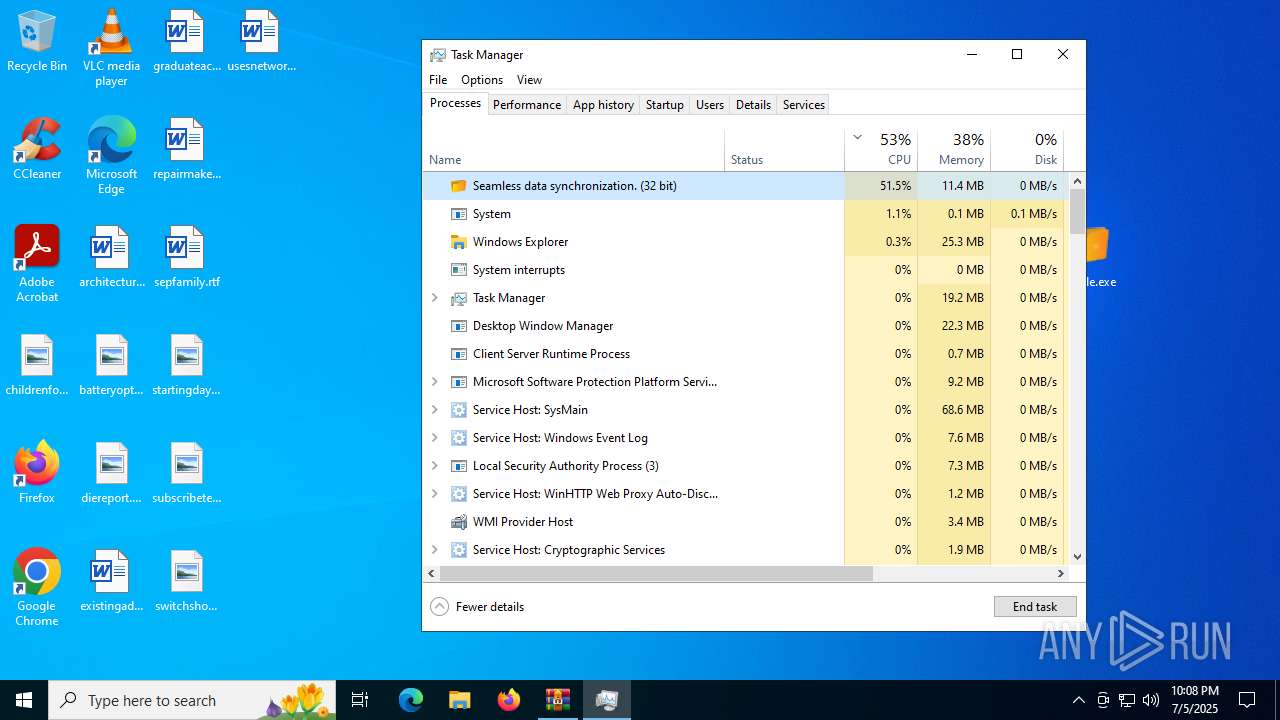
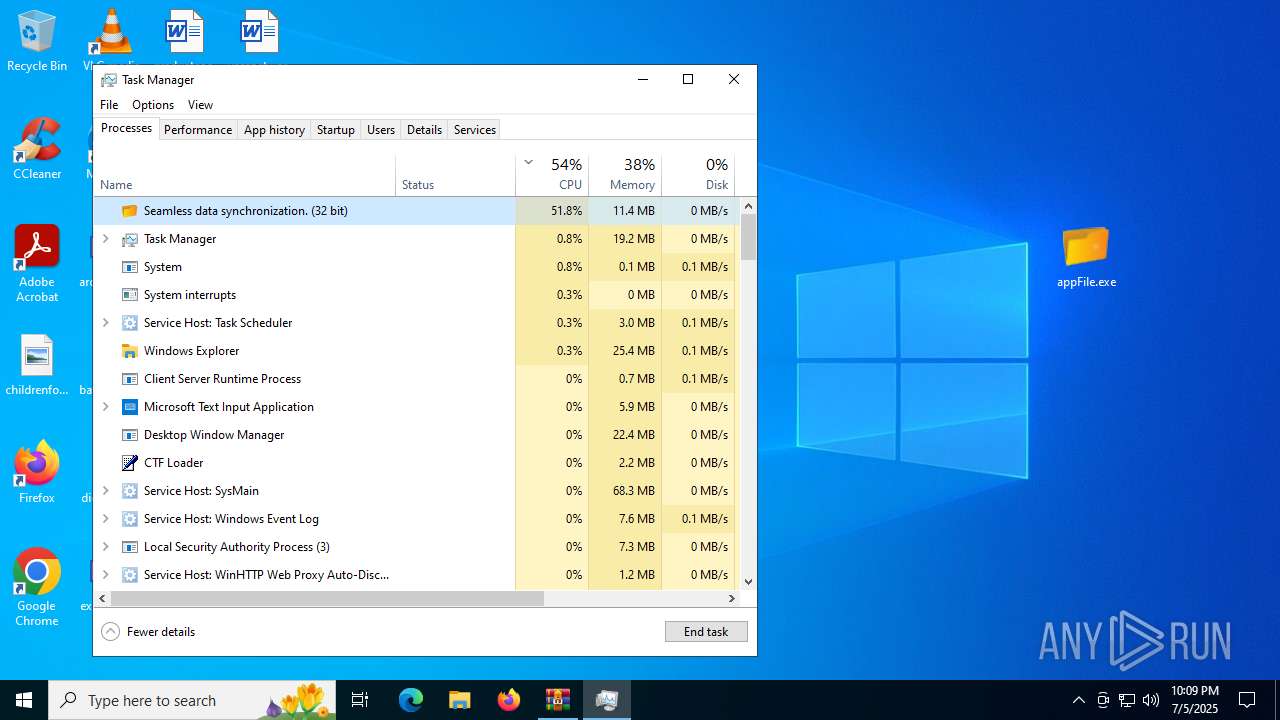
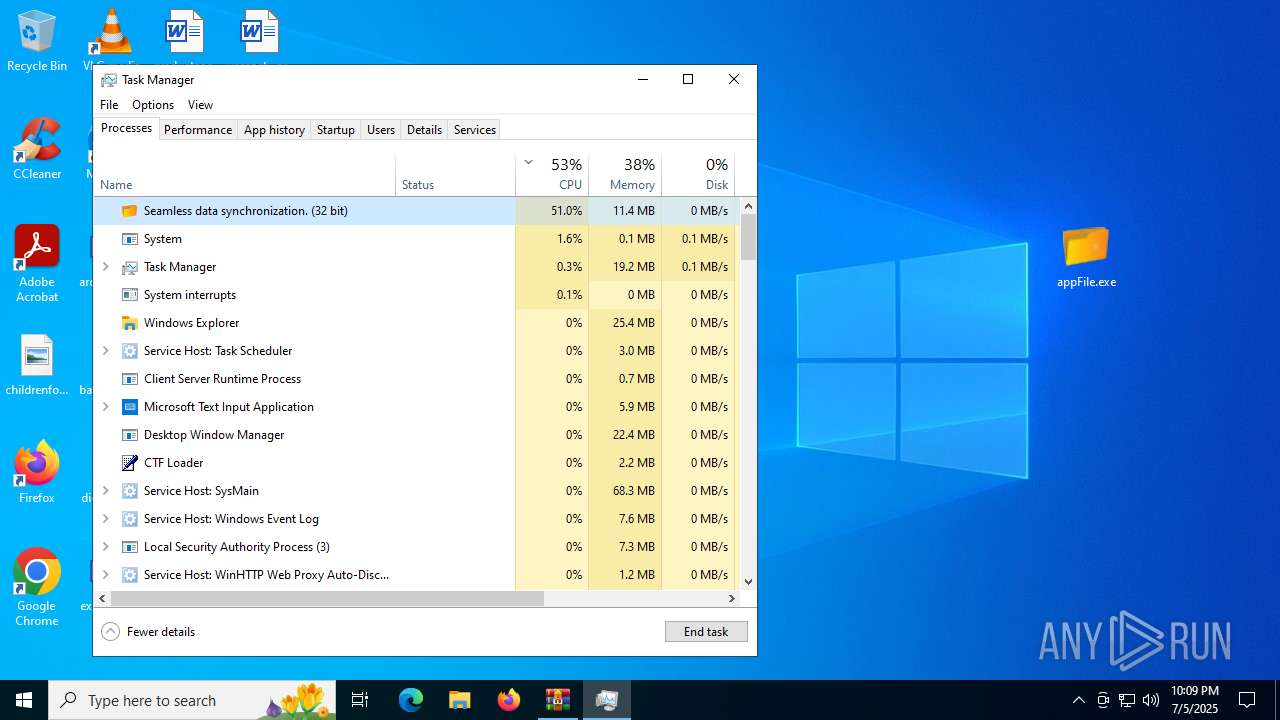
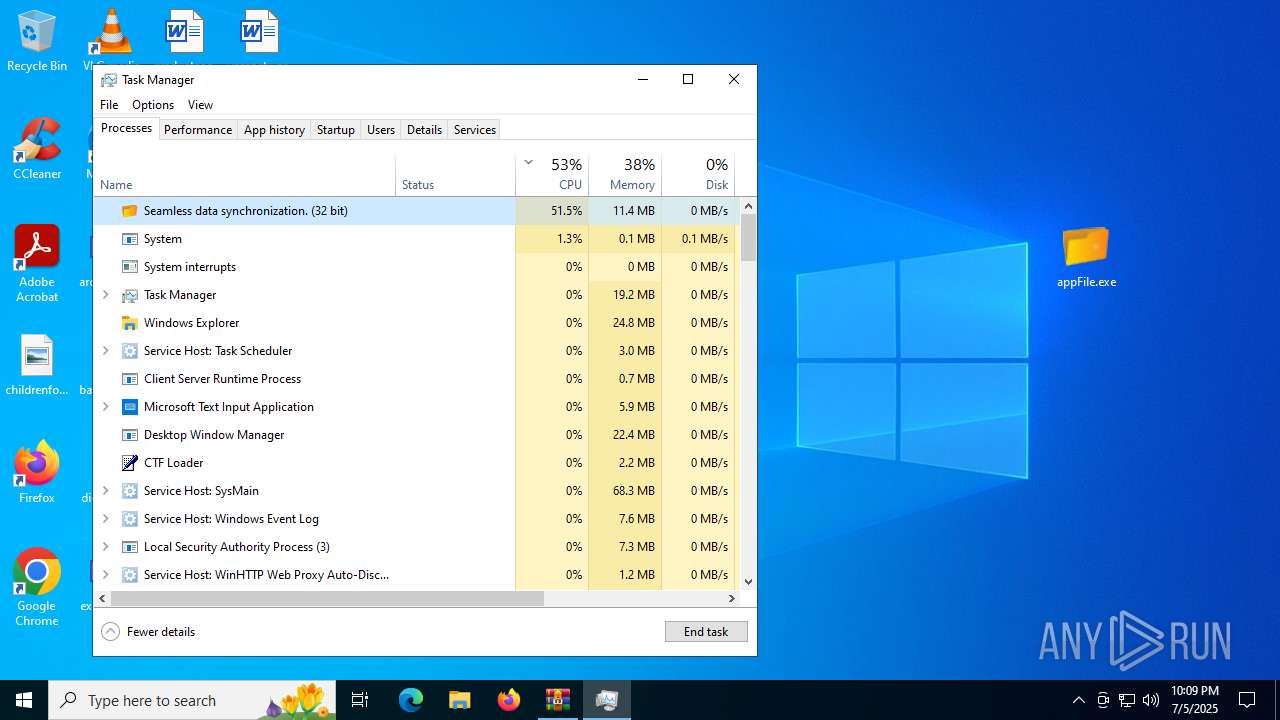
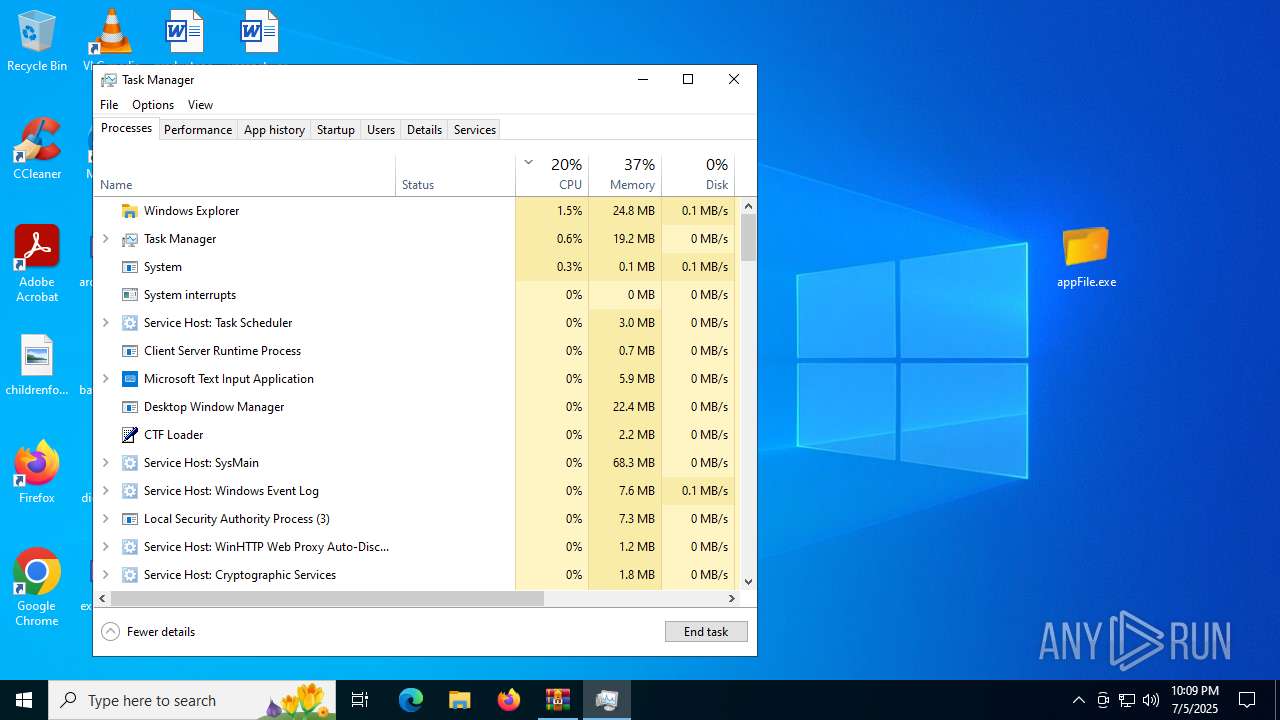
Get information on the list of running processes
- cmd.exe (PID: 7632)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7632)
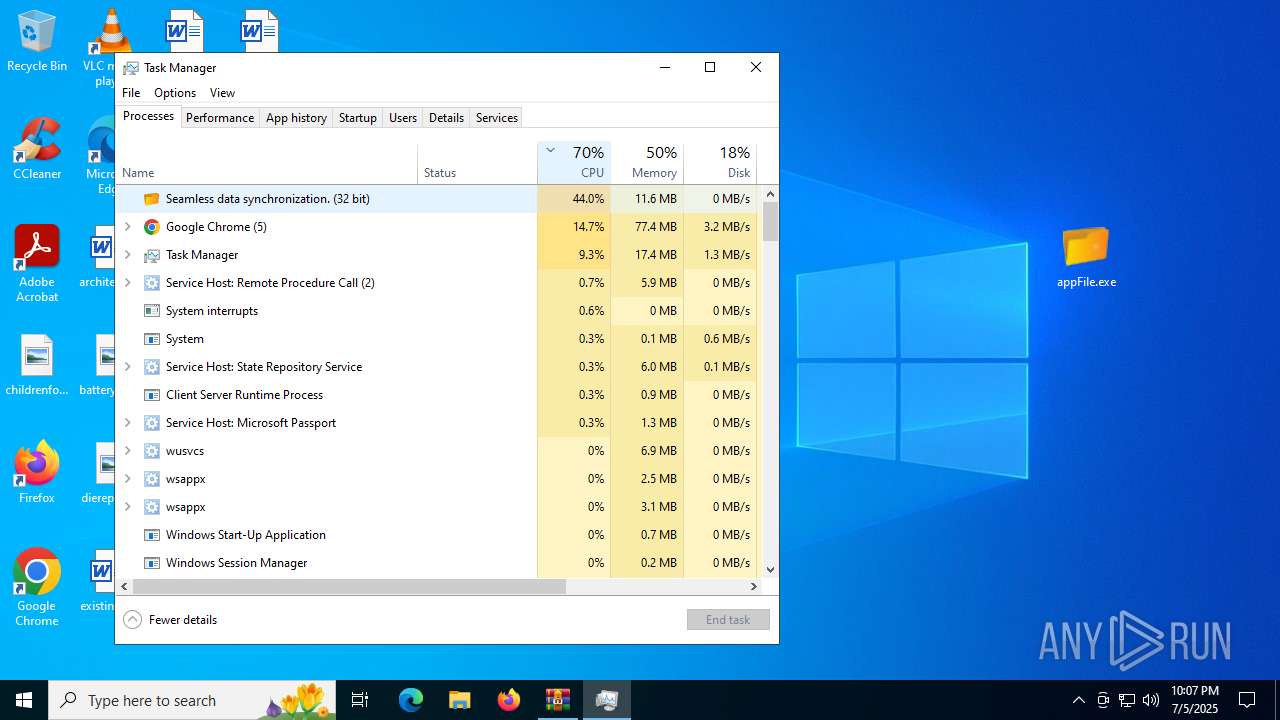
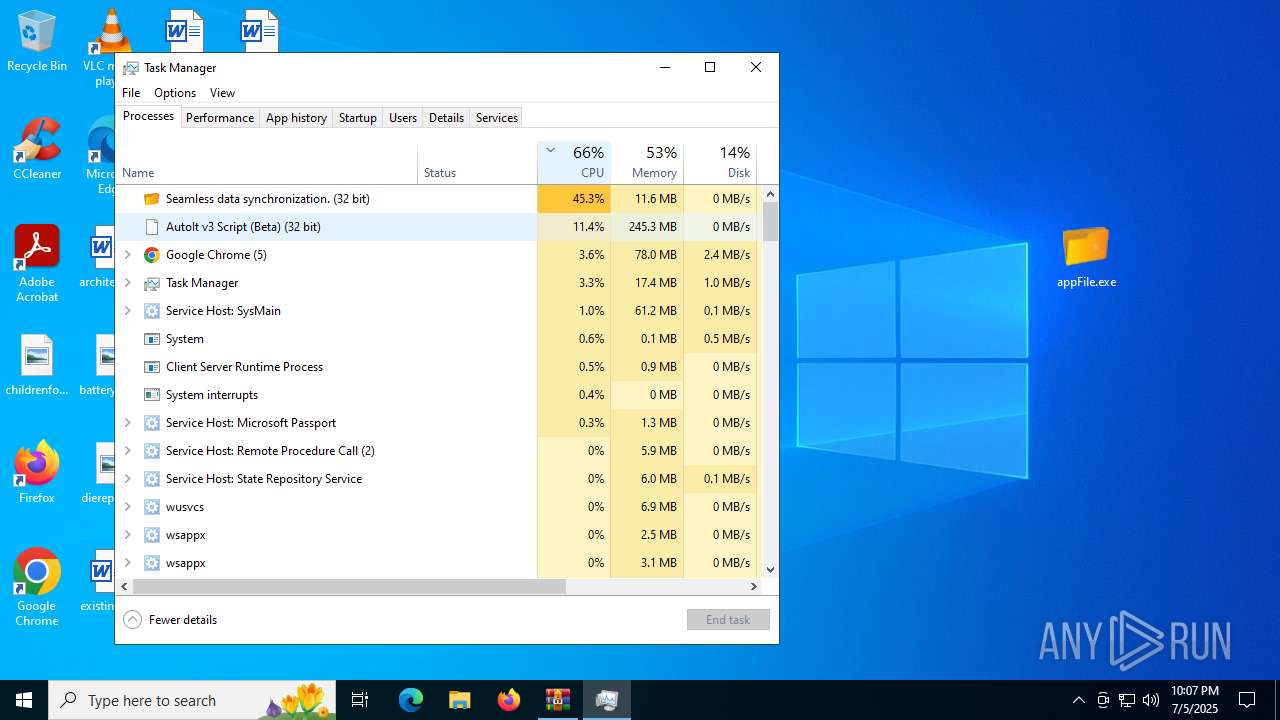
Starts the AutoIt3 executable file
- cmd.exe (PID: 7632)
Starts application with an unusual extension
- cmd.exe (PID: 7632)
The executable file from the user directory is run by the CMD process
- Telephone.com (PID: 7156)
There is functionality for taking screenshot (YARA)
- Telephone.com (PID: 7156)
Searches for installed software
- Telephone.com (PID: 7156)
INFO
Application launched itself
- msedge.exe (PID: 2976)
- msedge.exe (PID: 8088)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 5960)
- msedge.exe (PID: 728)
- msedge.exe (PID: 6320)
- msedge.exe (PID: 7164)
- msedge.exe (PID: 8128)
- msedge.exe (PID: 8152)
- msedge.exe (PID: 2428)
- msedge.exe (PID: 2648)
- chrome.exe (PID: 5884)
- chrome.exe (PID: 6892)
- msedge.exe (PID: 7576)
Reads Environment values
- identity_helper.exe (PID: 7564)
- identity_helper.exe (PID: 2512)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2976)
Checks supported languages
- identity_helper.exe (PID: 2512)
- identity_helper.exe (PID: 7564)
- appFile.exe (PID: 8072)
- extrac32.exe (PID: 2716)
- Telephone.com (PID: 7156)
Reads the computer name
- identity_helper.exe (PID: 7564)
- identity_helper.exe (PID: 2512)
- appFile.exe (PID: 8072)
- extrac32.exe (PID: 2716)
- Telephone.com (PID: 7156)
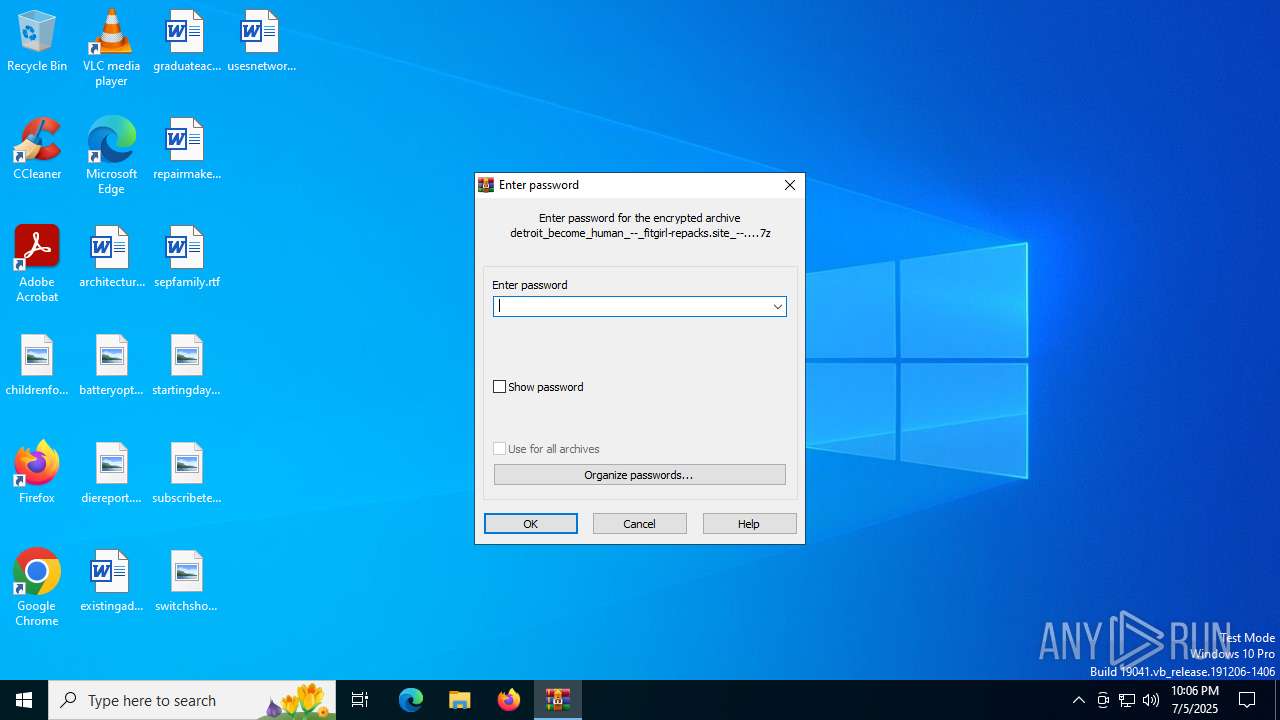
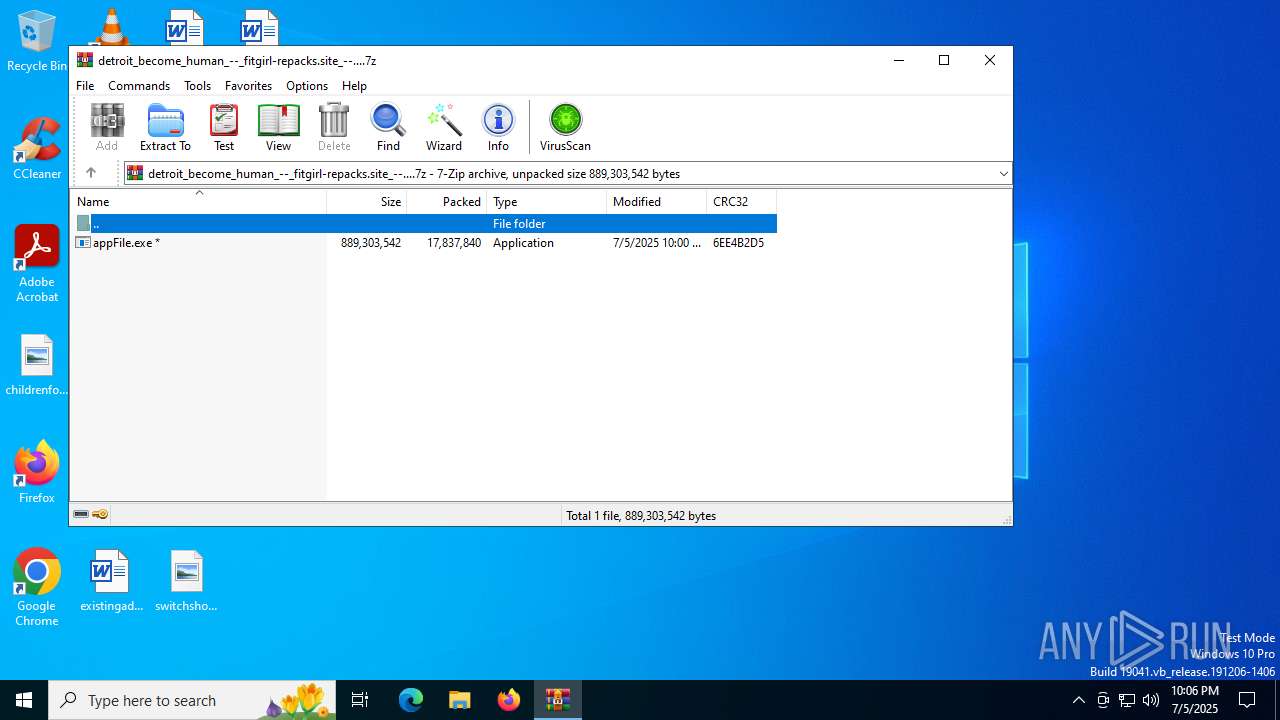
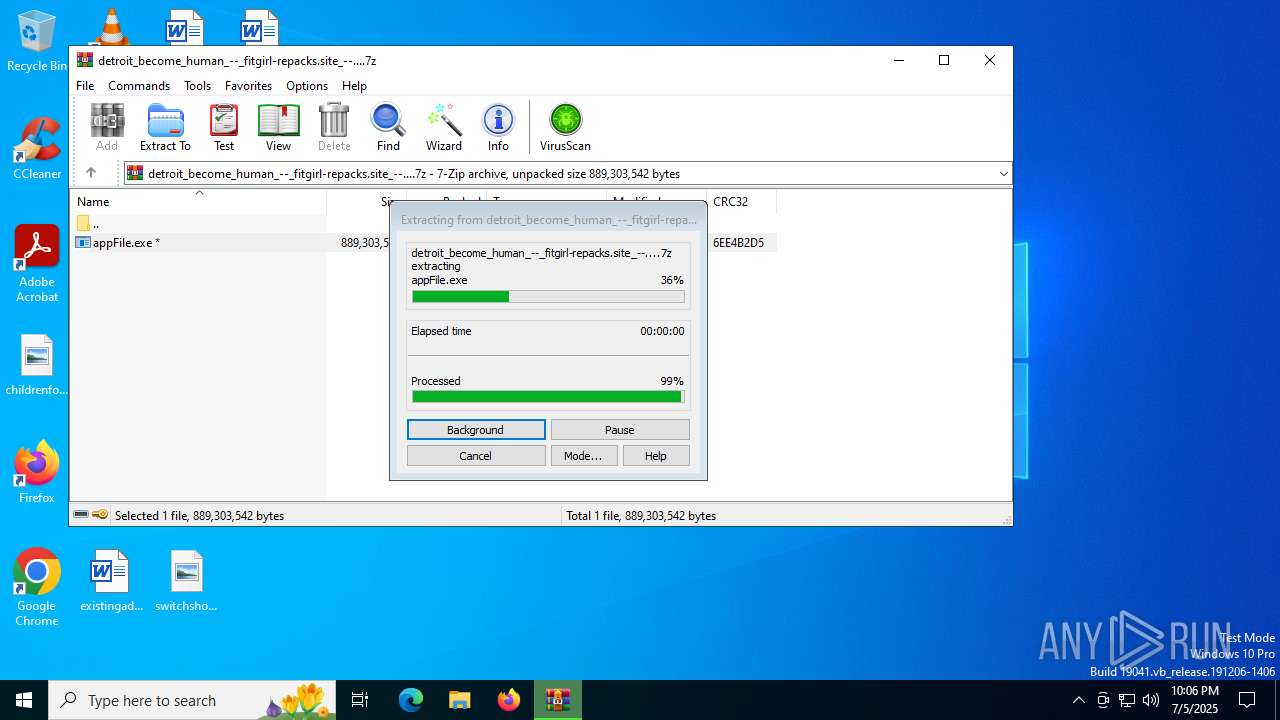
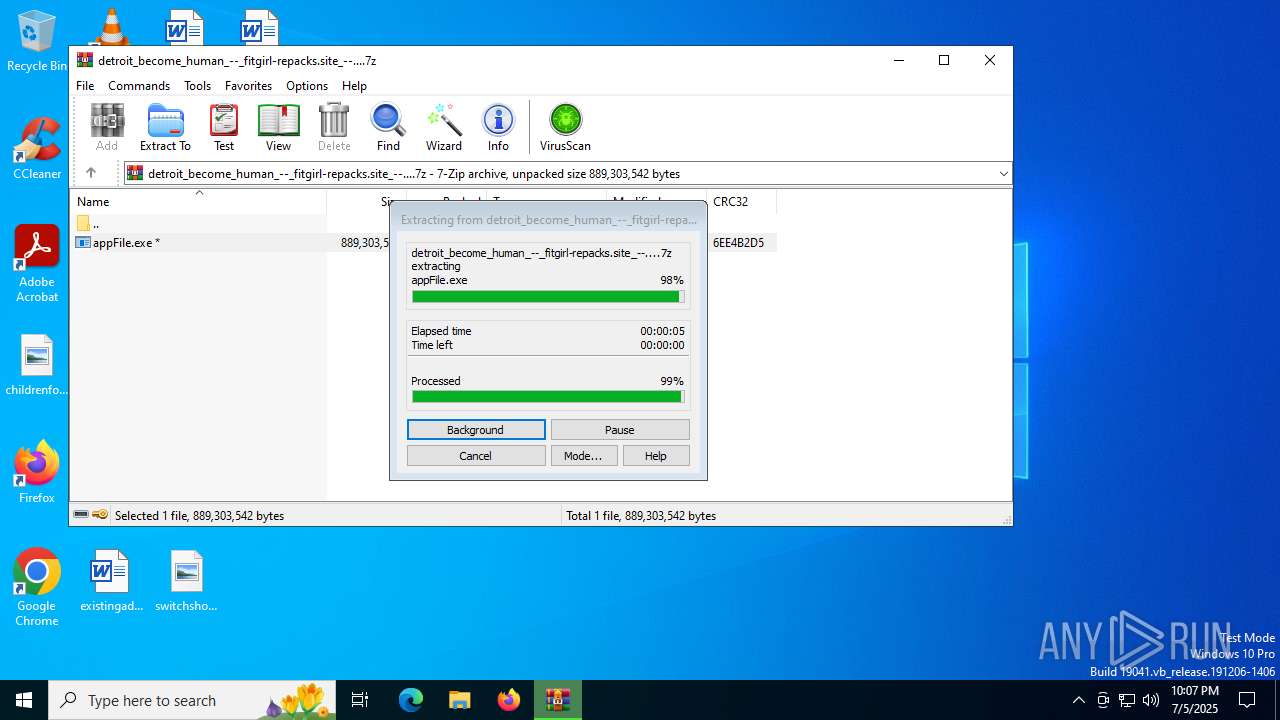
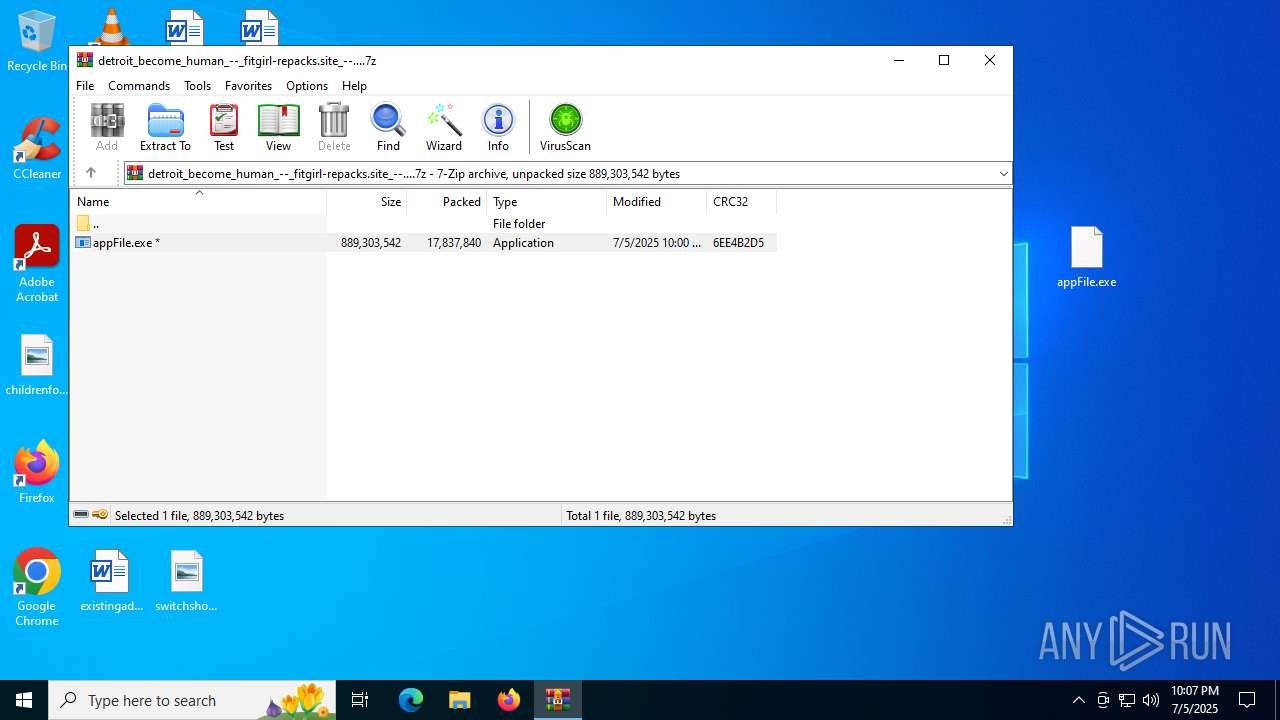
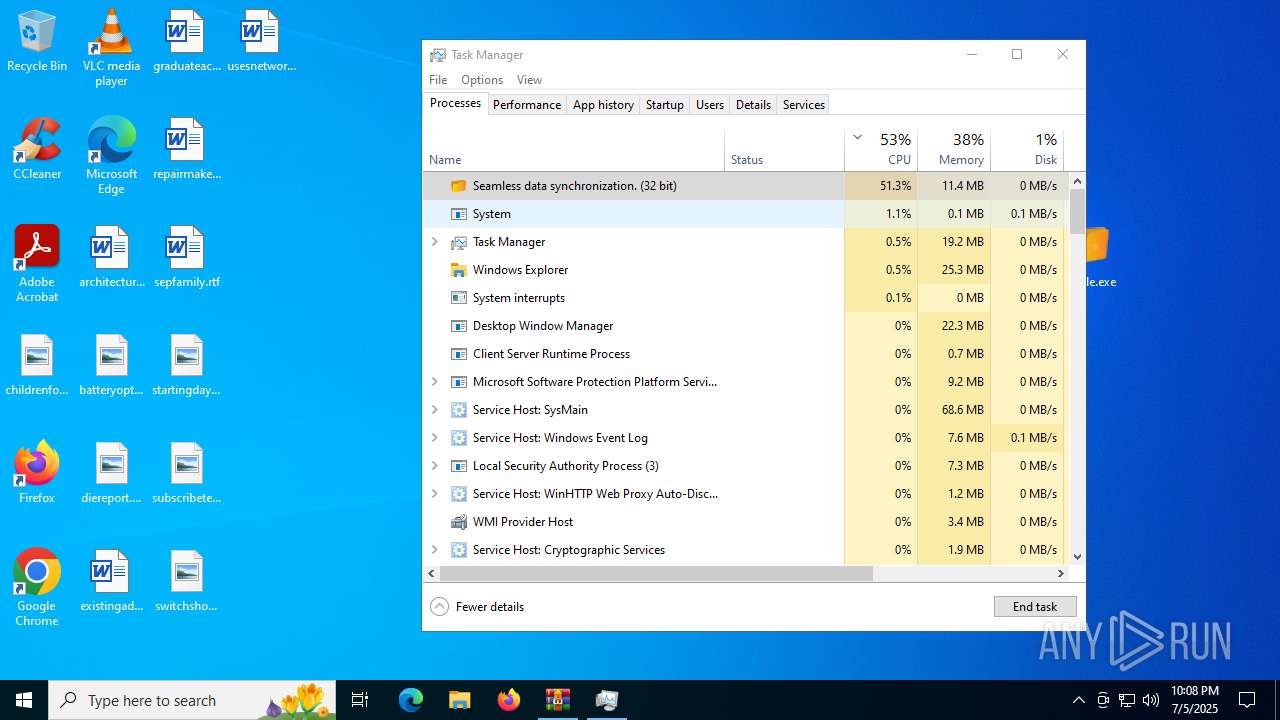
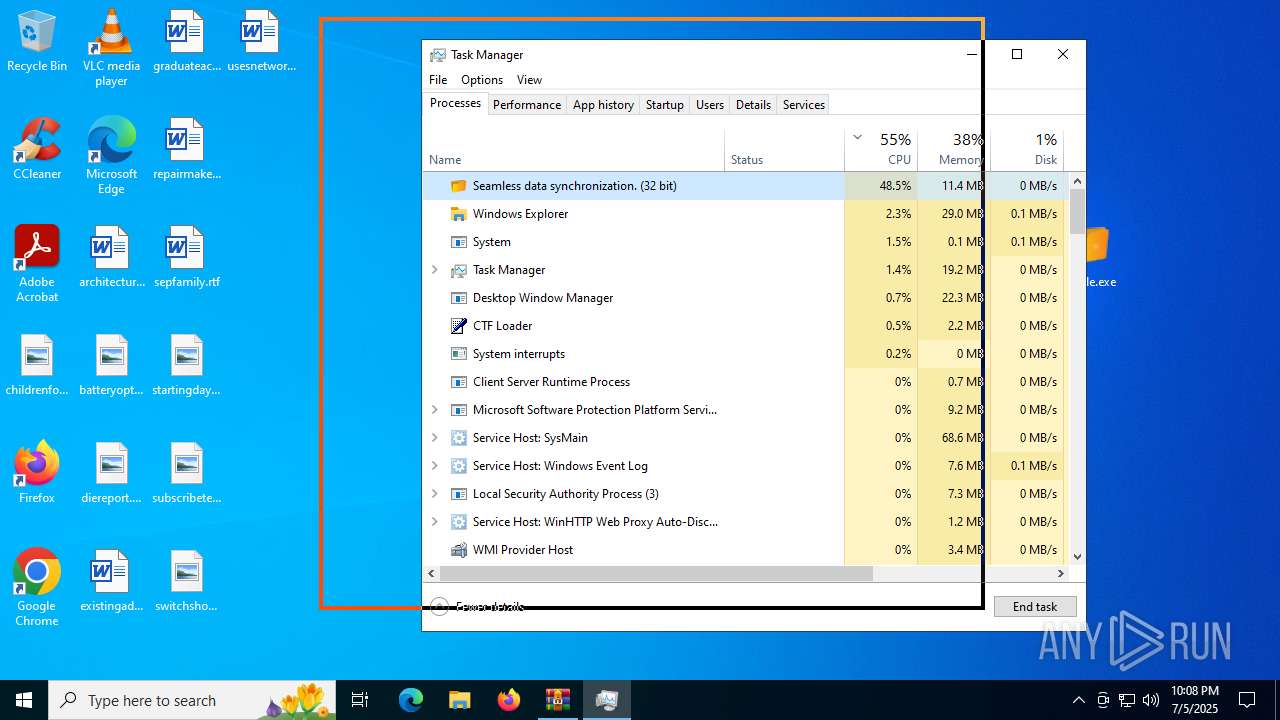
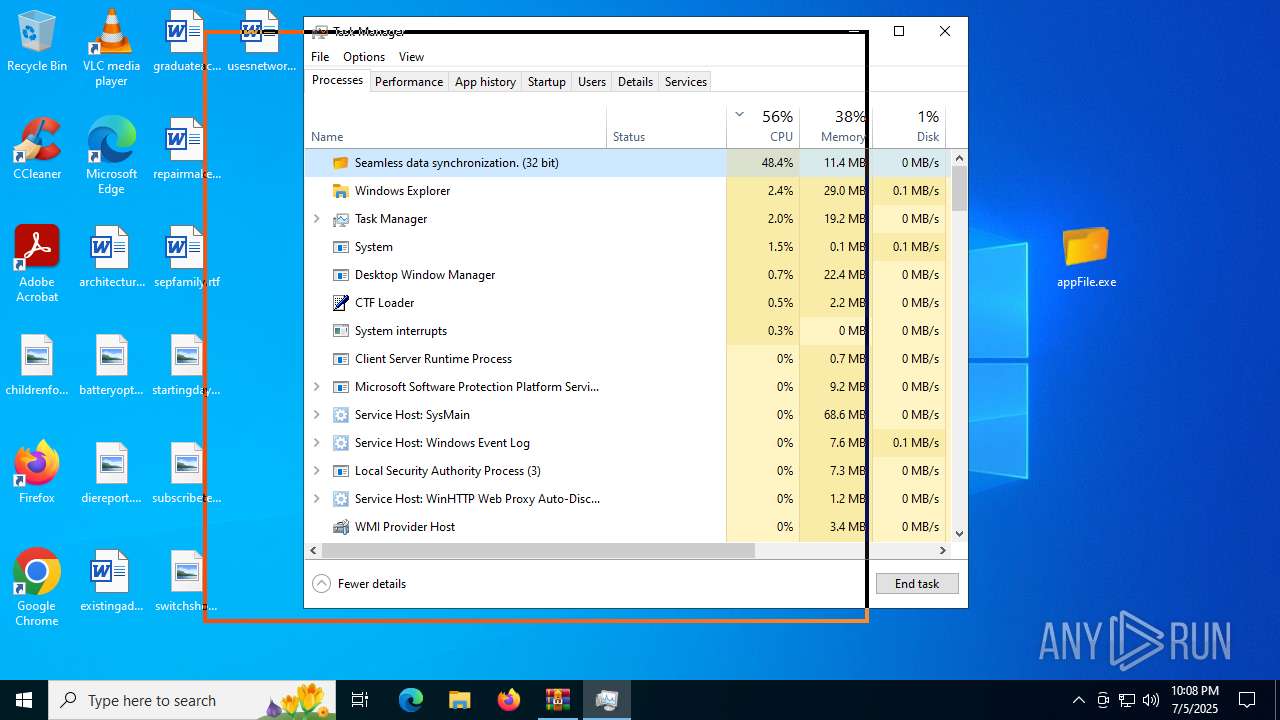
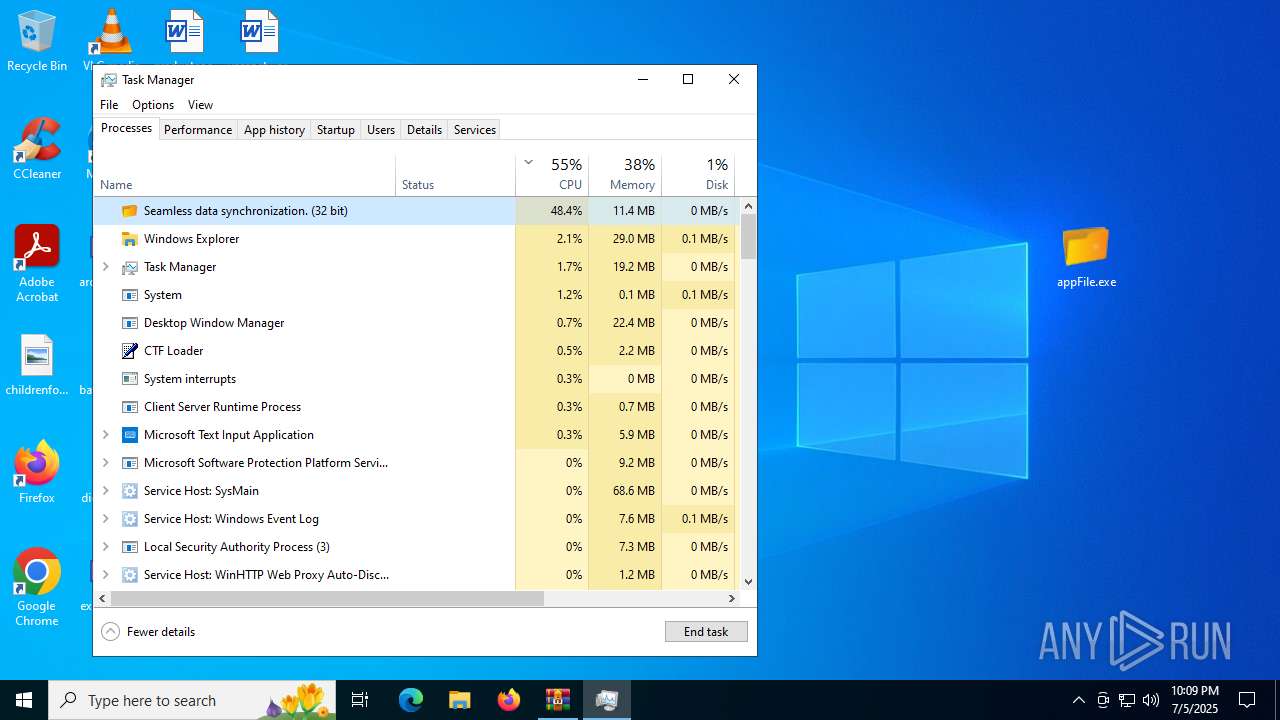
Manual execution by a user
- appFile.exe (PID: 8072)
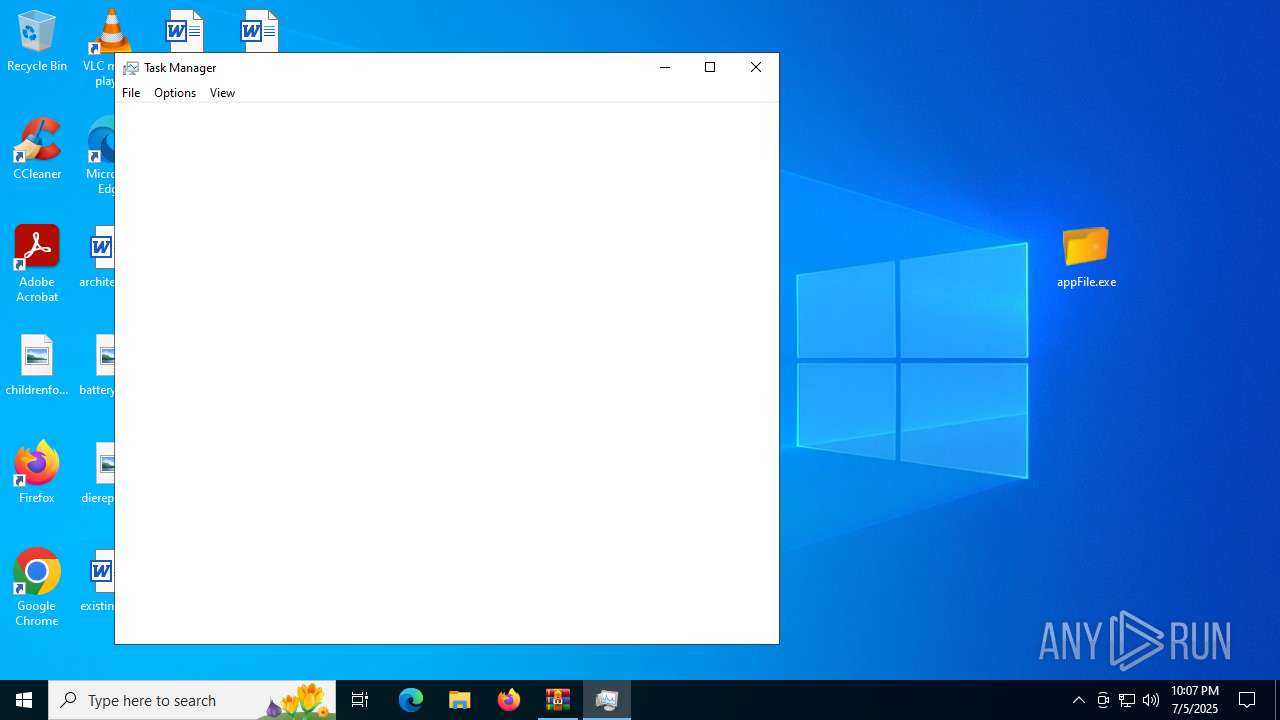
- Taskmgr.exe (PID: 6256)
- Taskmgr.exe (PID: 7320)
Create files in a temporary directory
- appFile.exe (PID: 8072)
- extrac32.exe (PID: 2716)
Process checks computer location settings
- appFile.exe (PID: 8072)
Reads mouse settings
- Telephone.com (PID: 7156)
Reads the software policy settings
- Telephone.com (PID: 7156)
- slui.exe (PID: 6164)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7320)
Checks proxy server information
- slui.exe (PID: 6164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
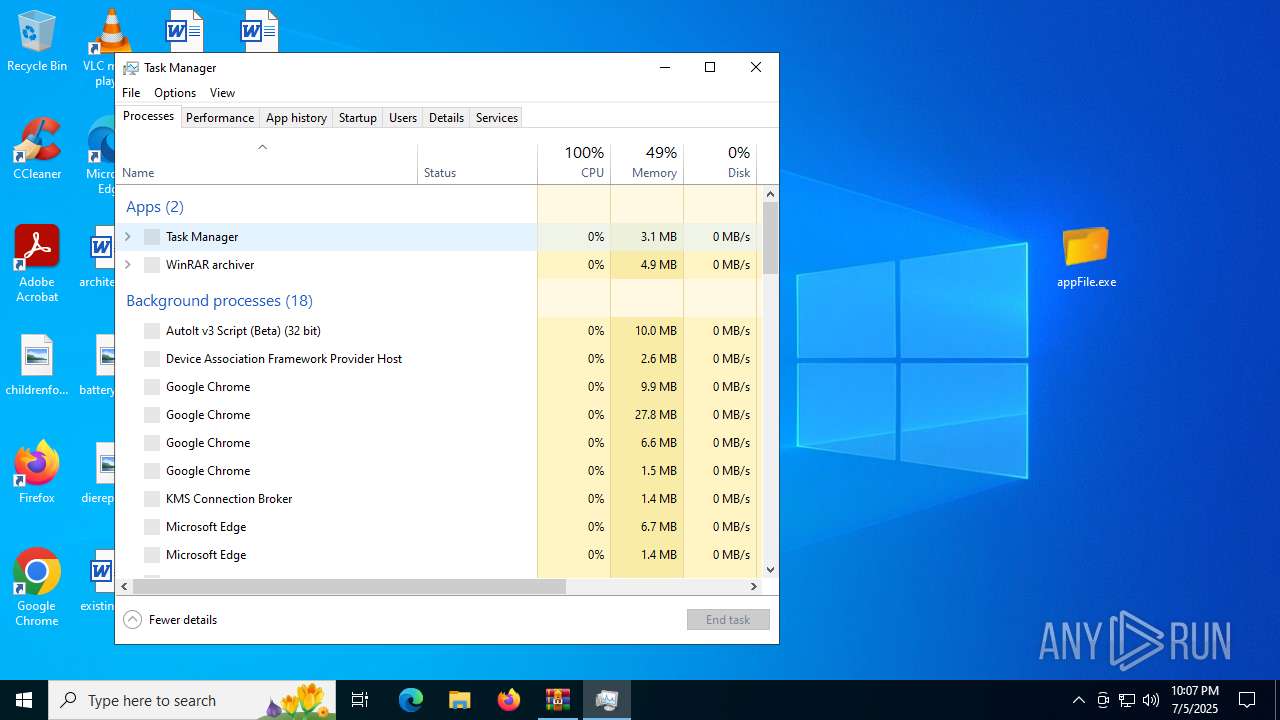
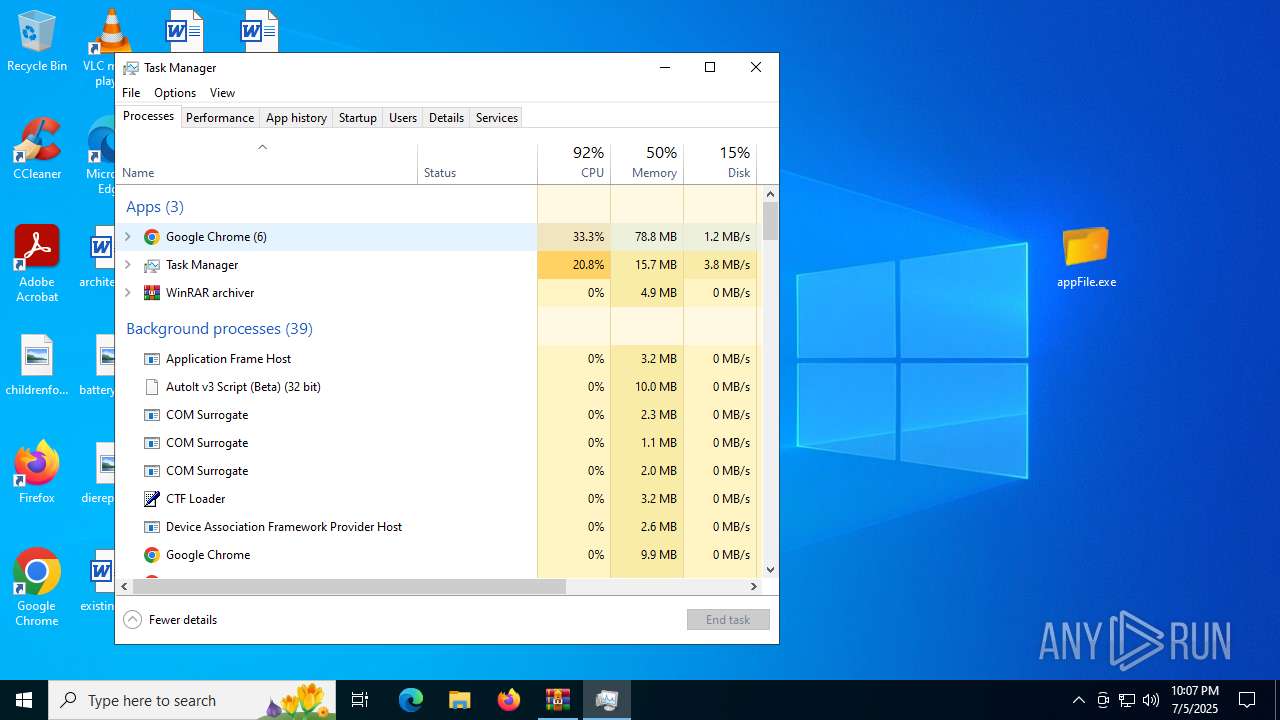
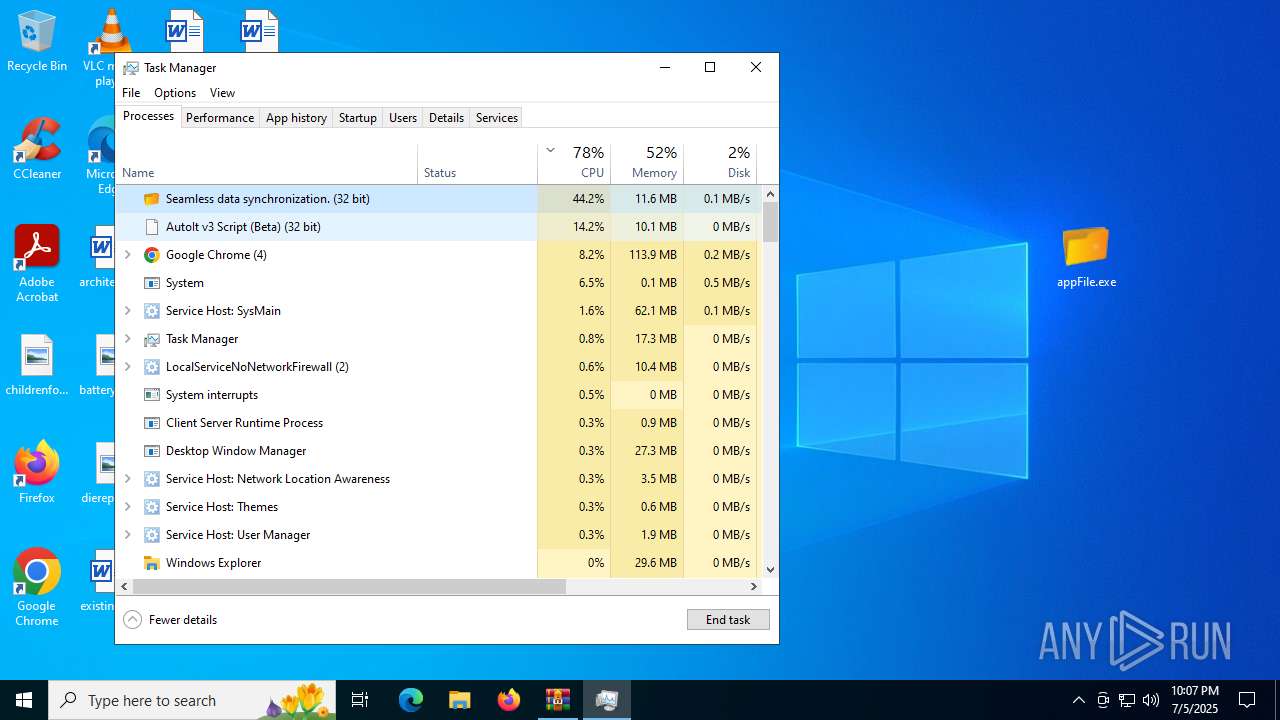
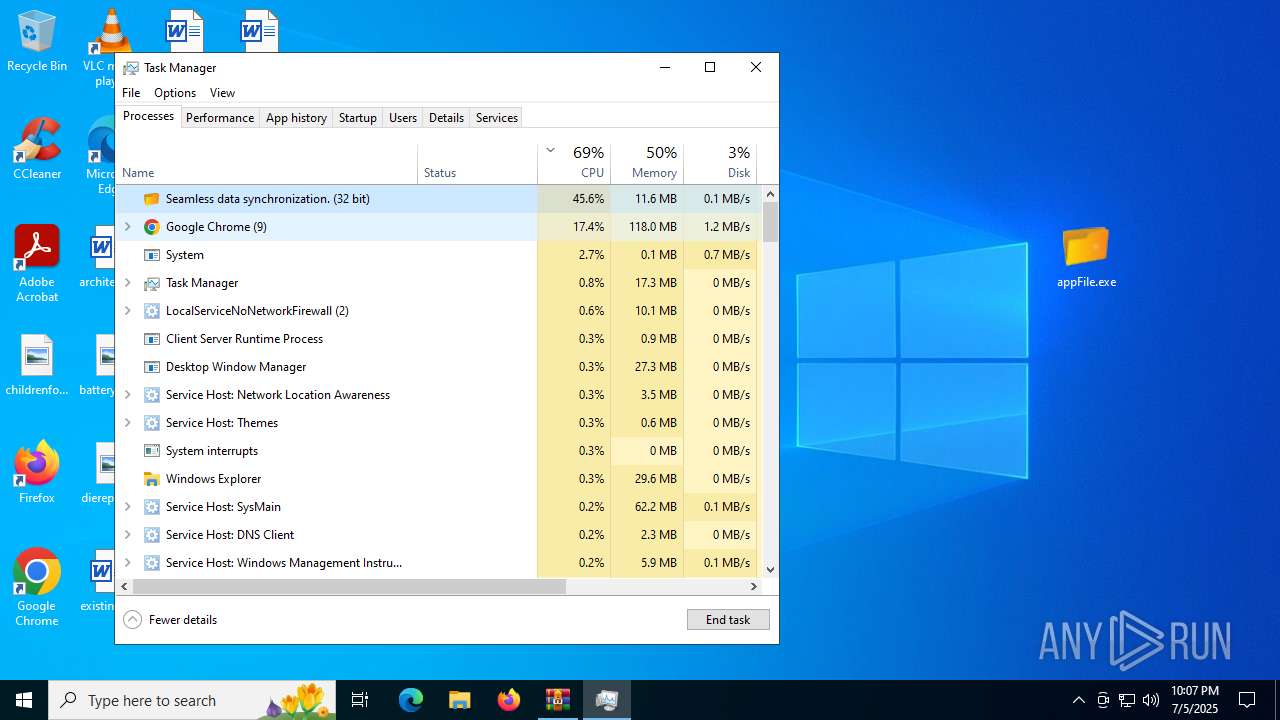
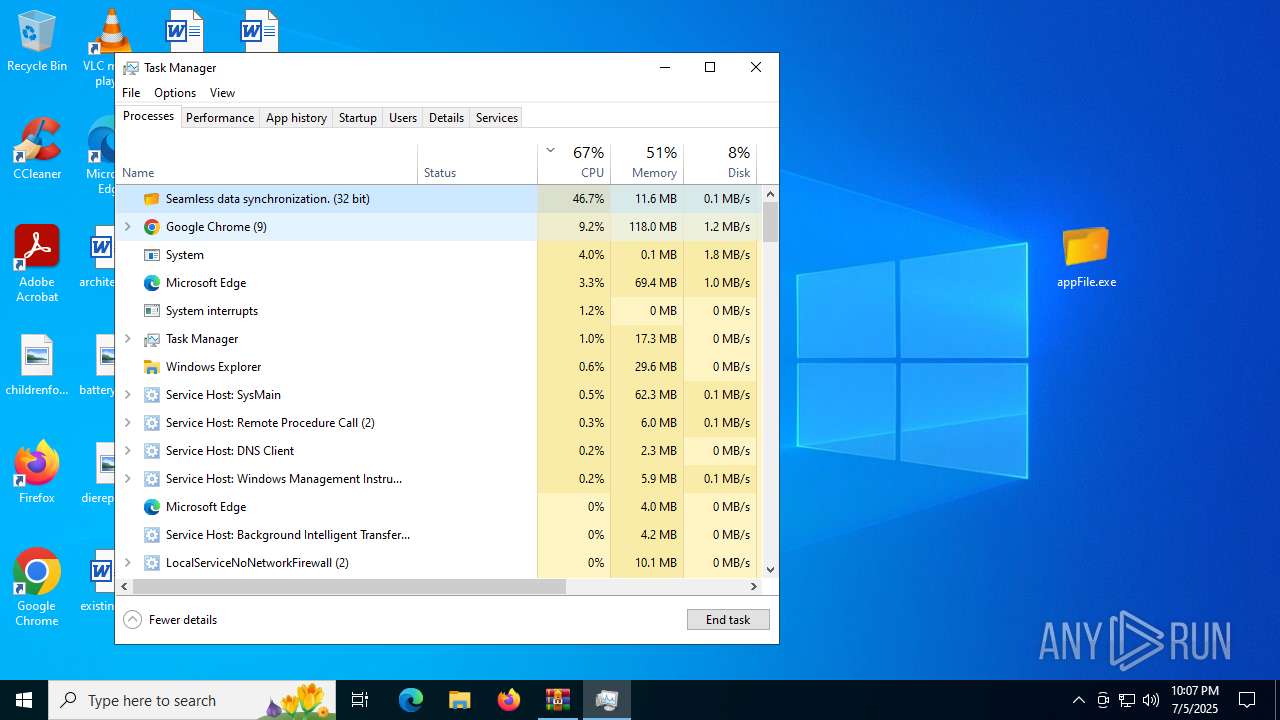
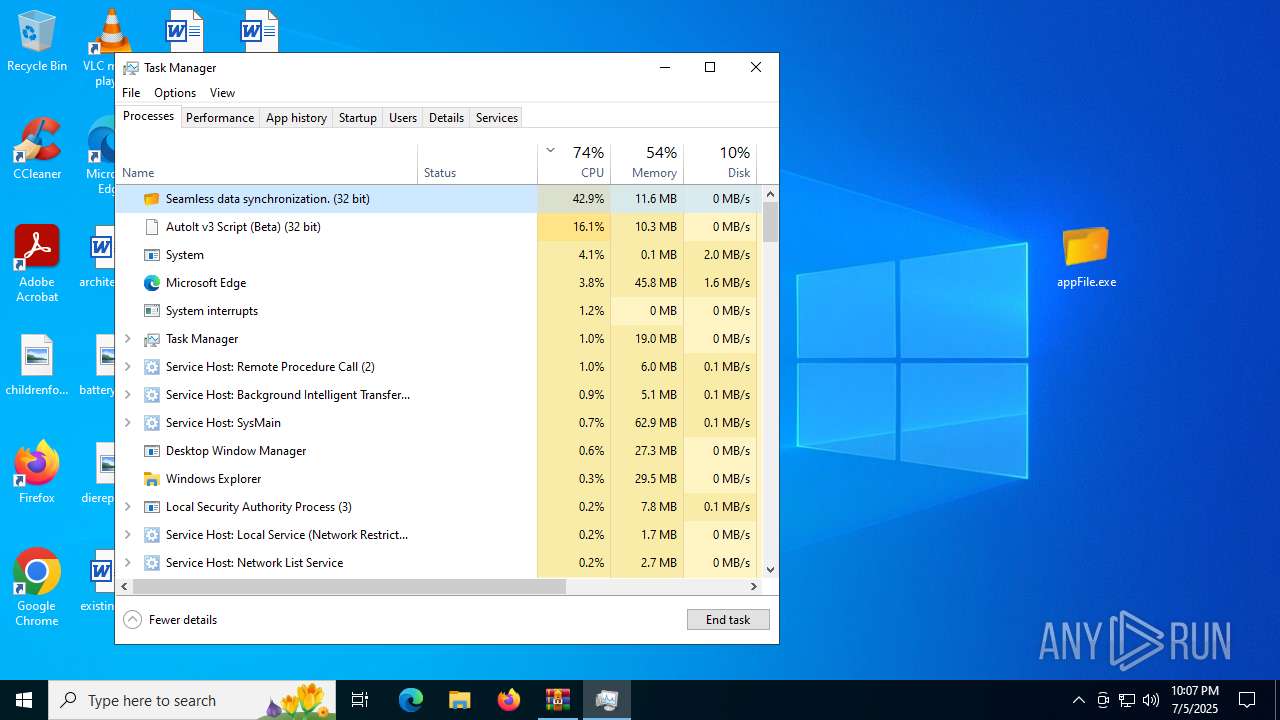
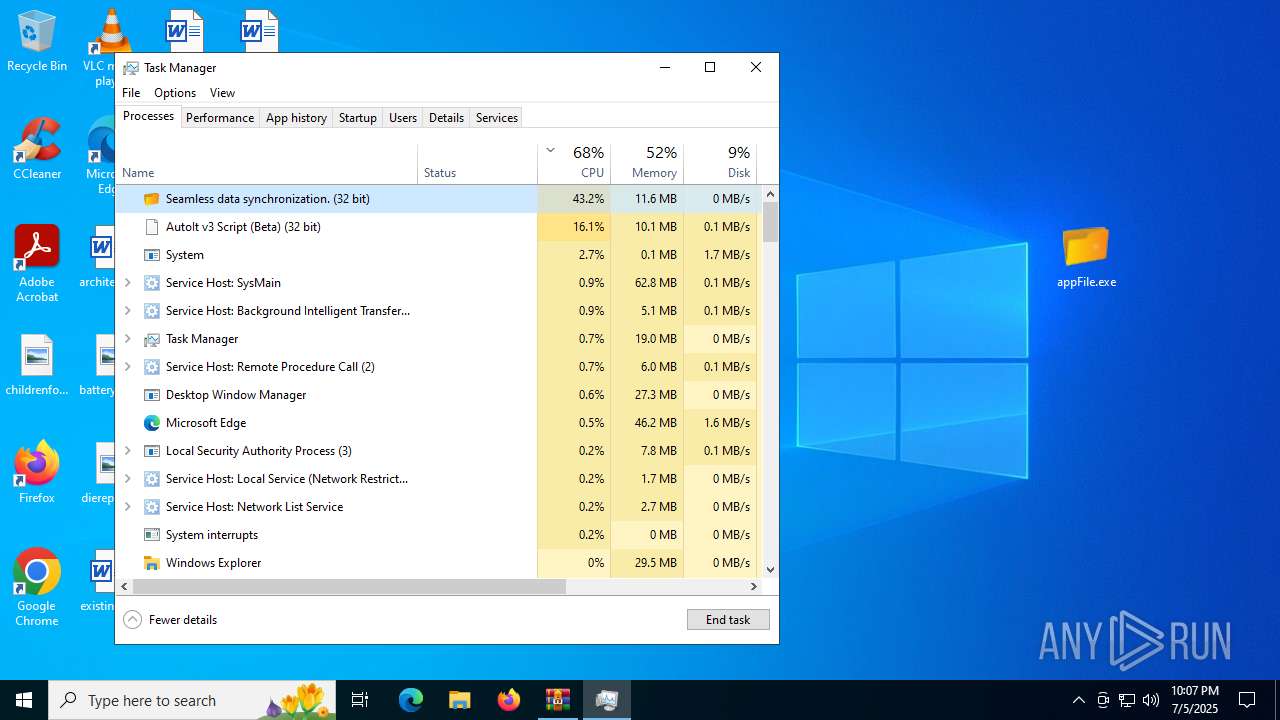
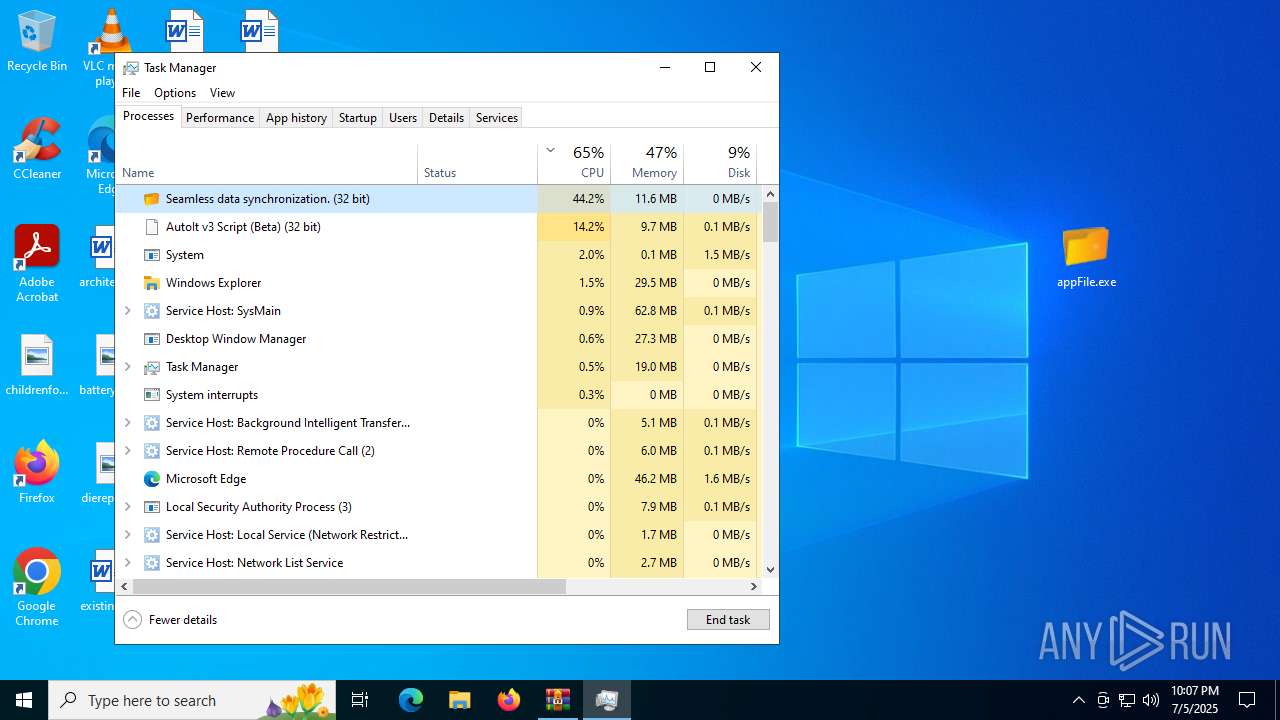
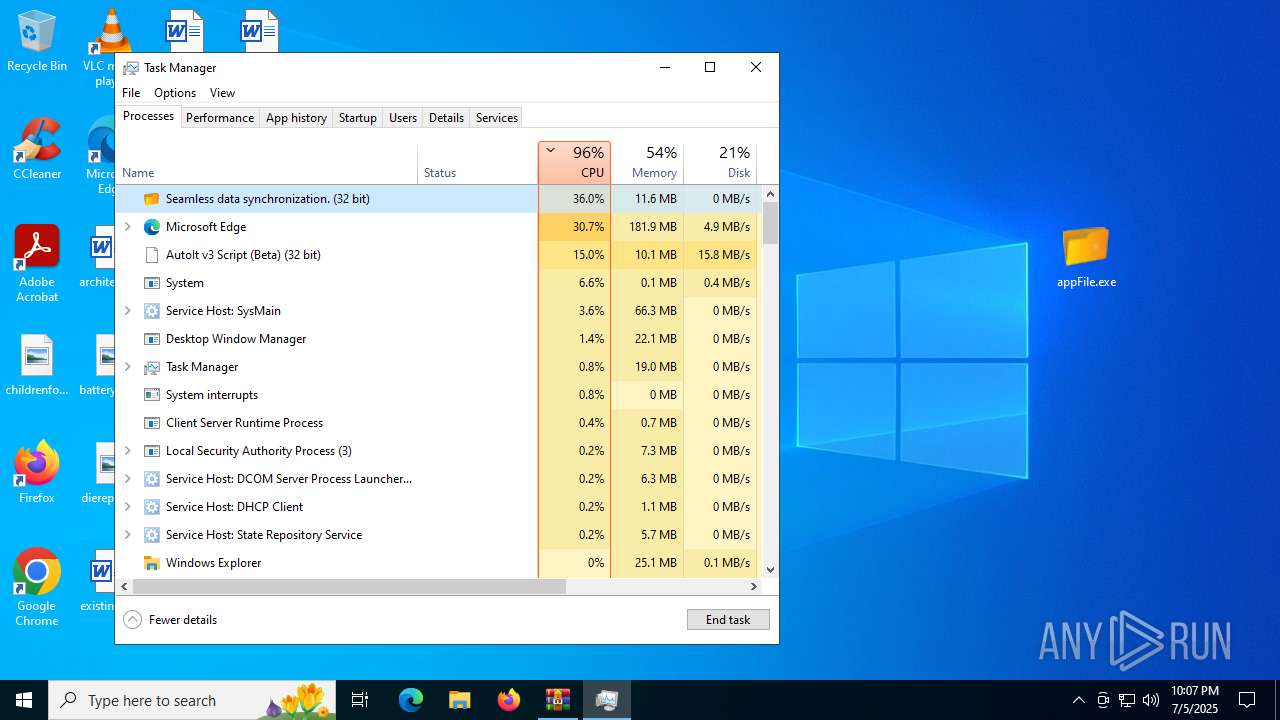
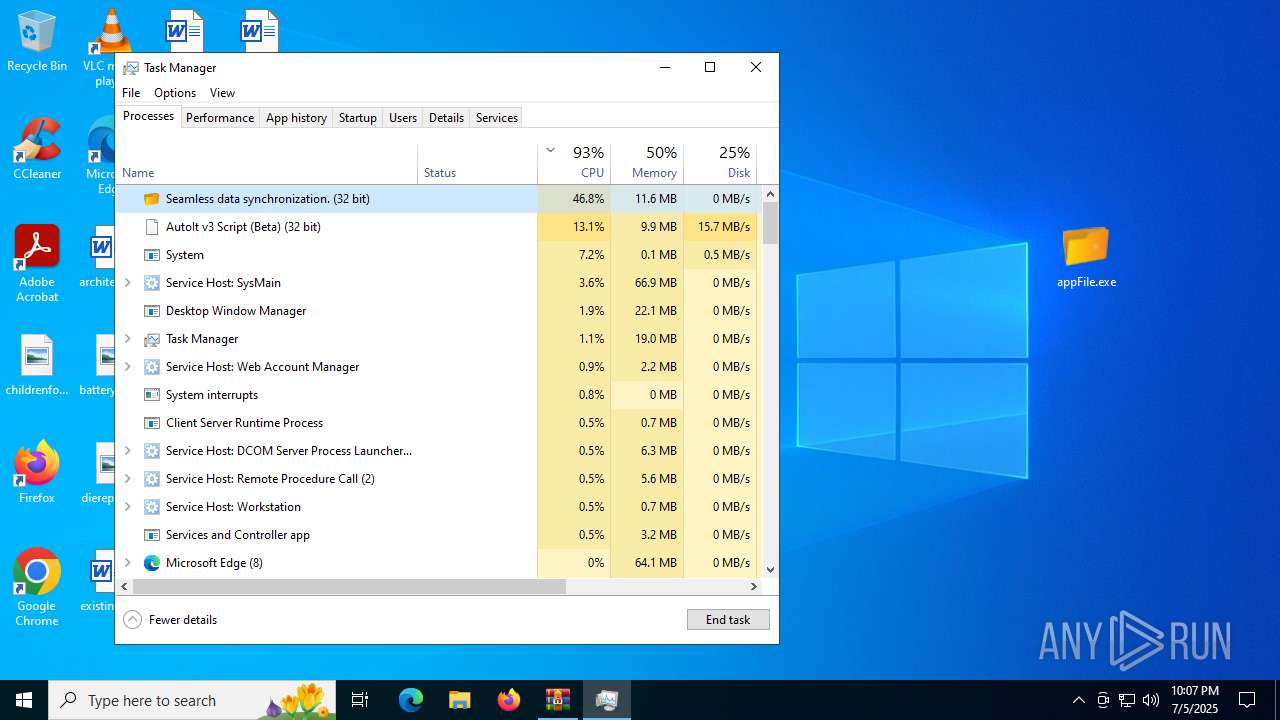
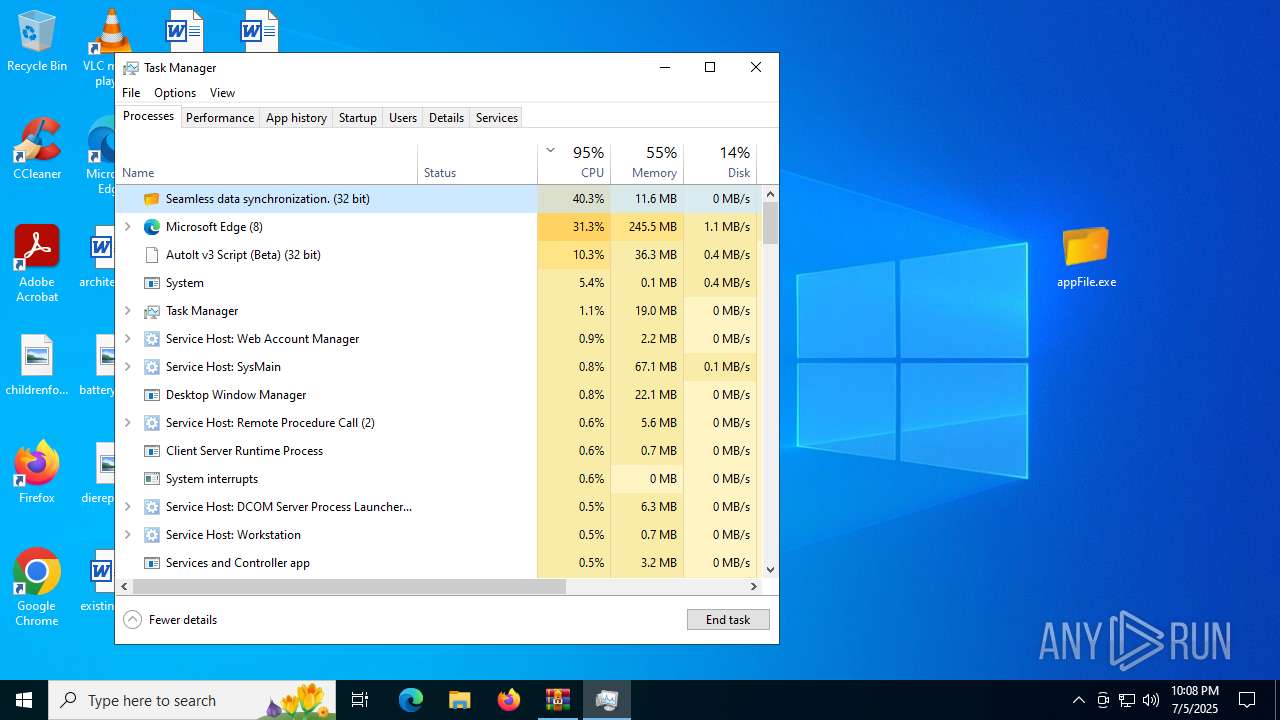
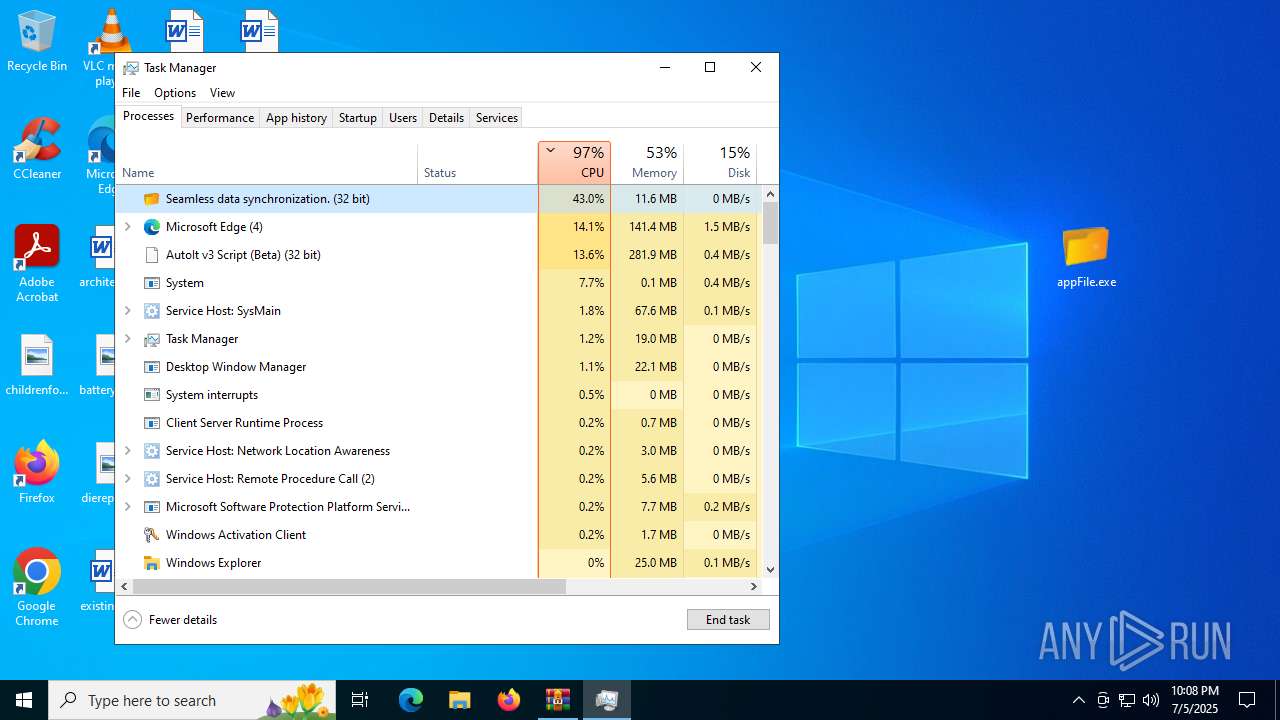
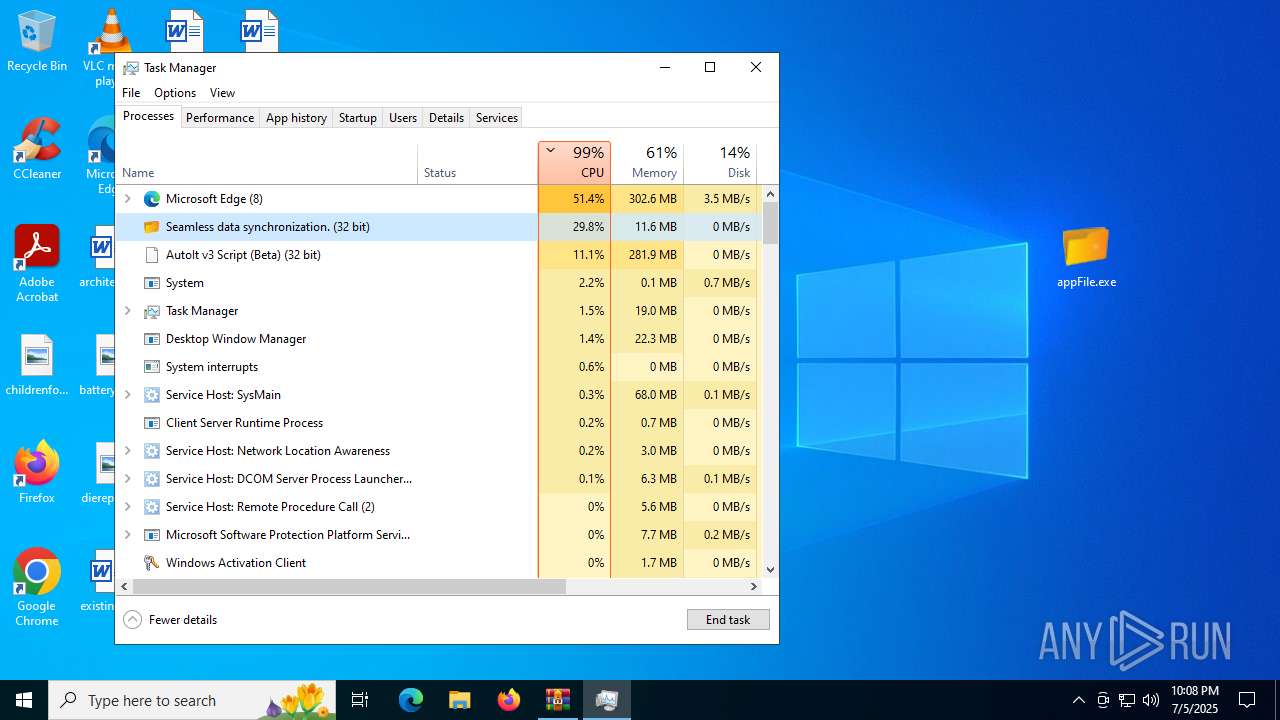
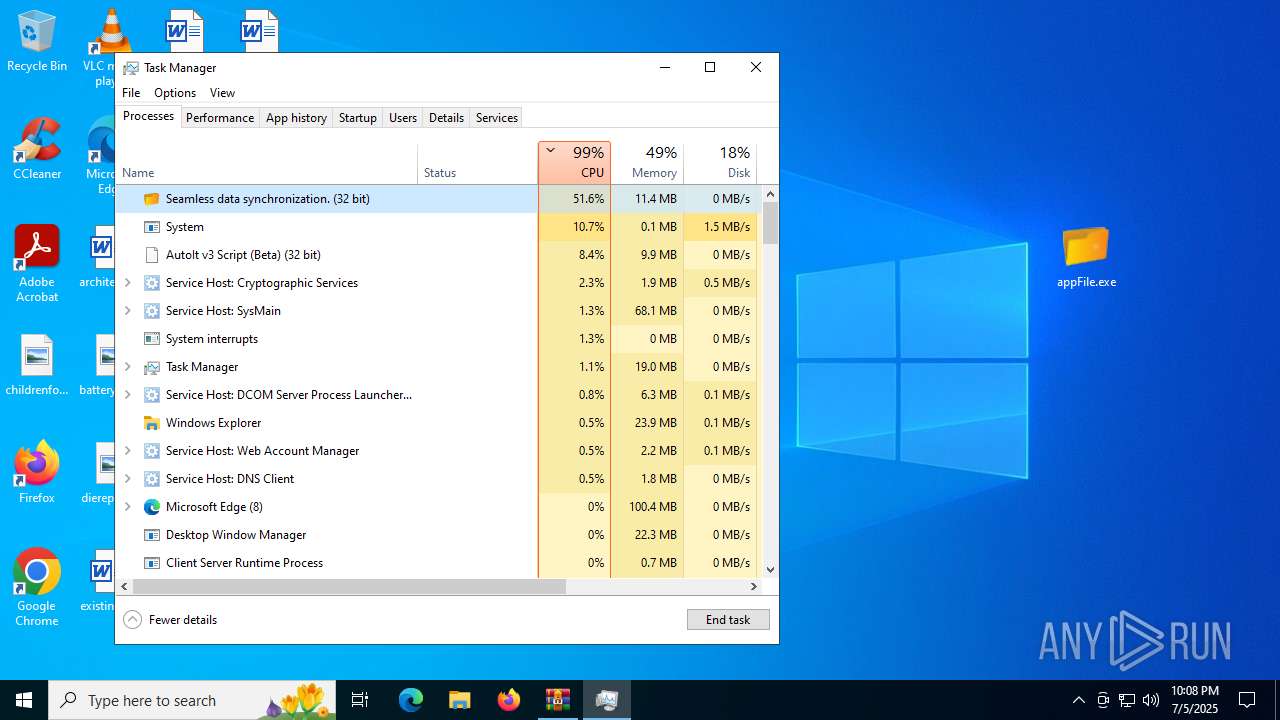
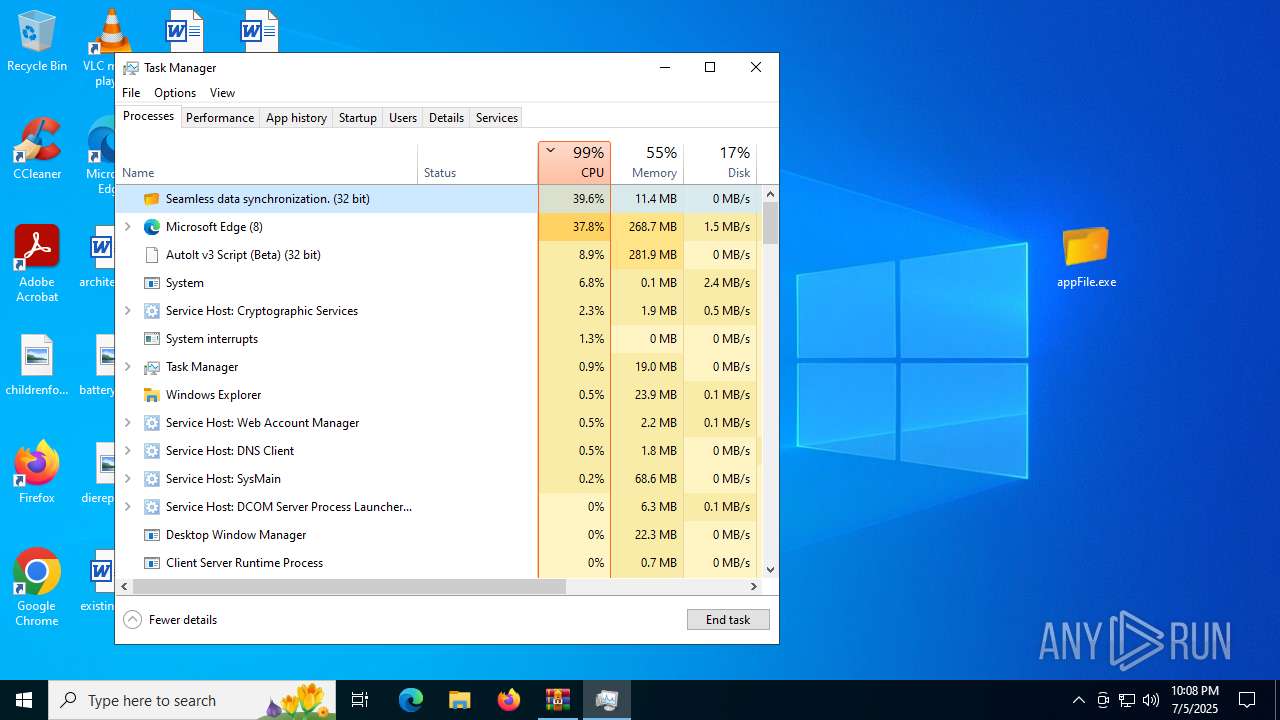
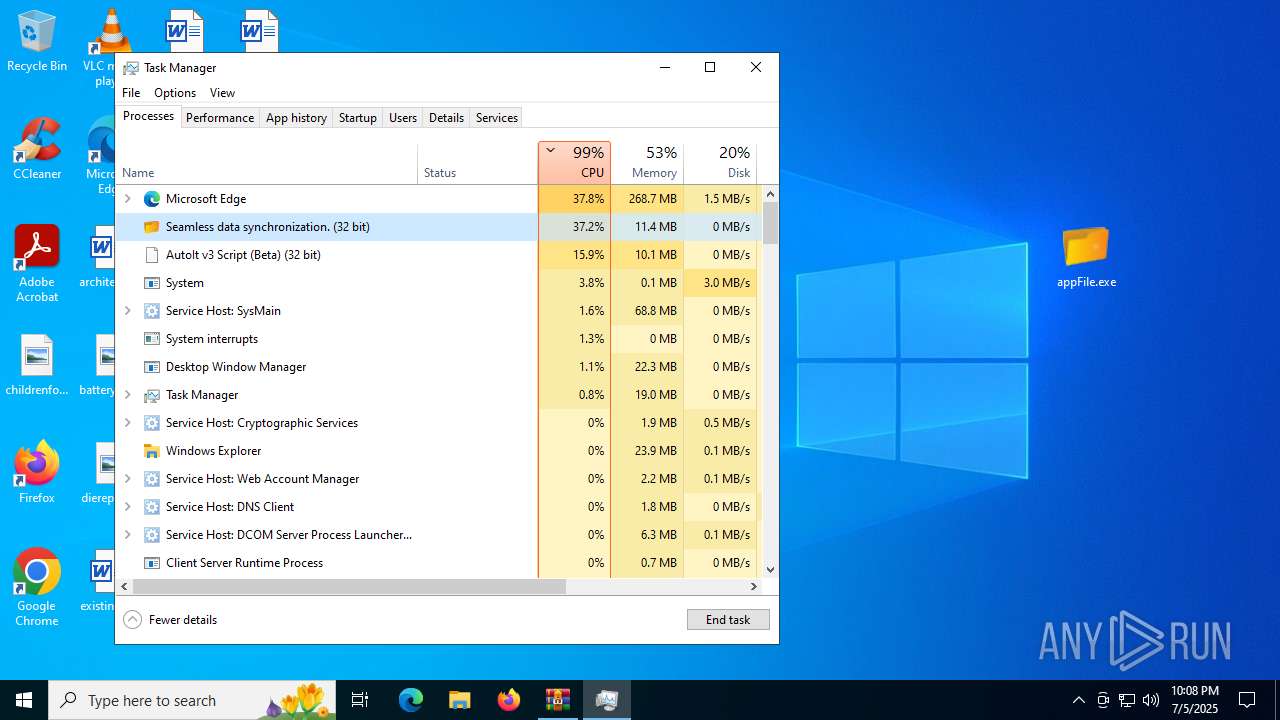
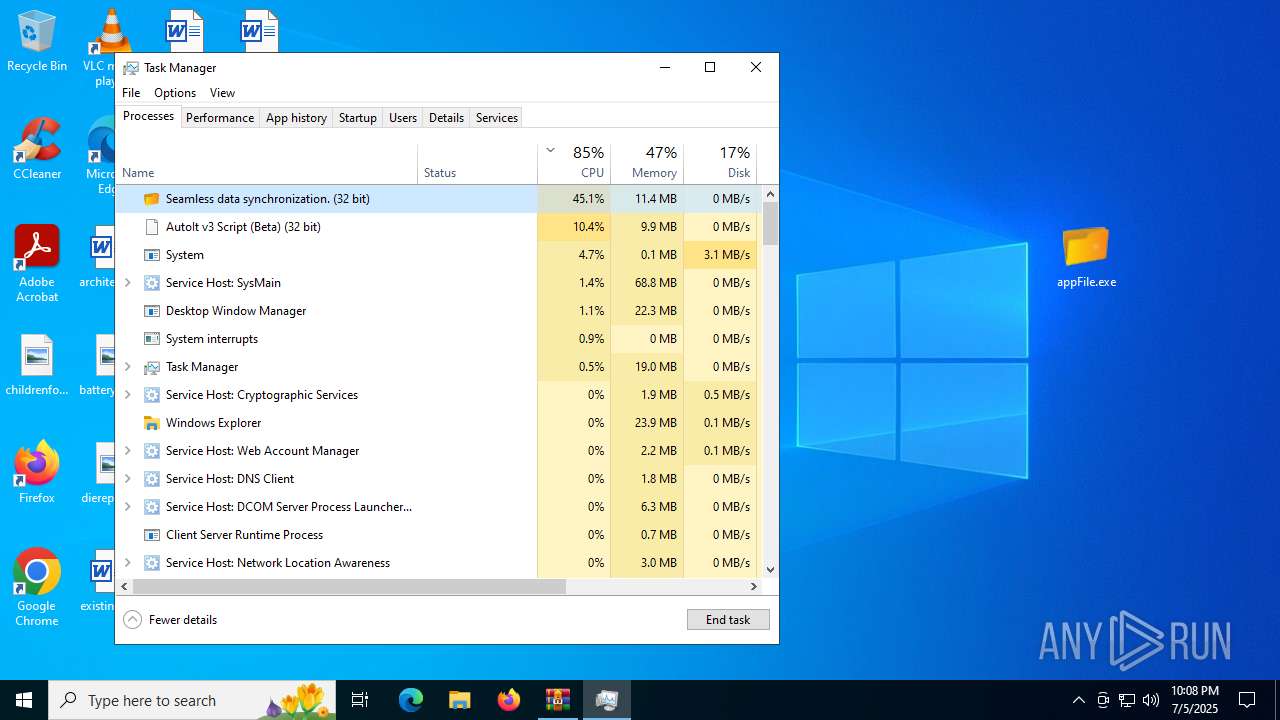
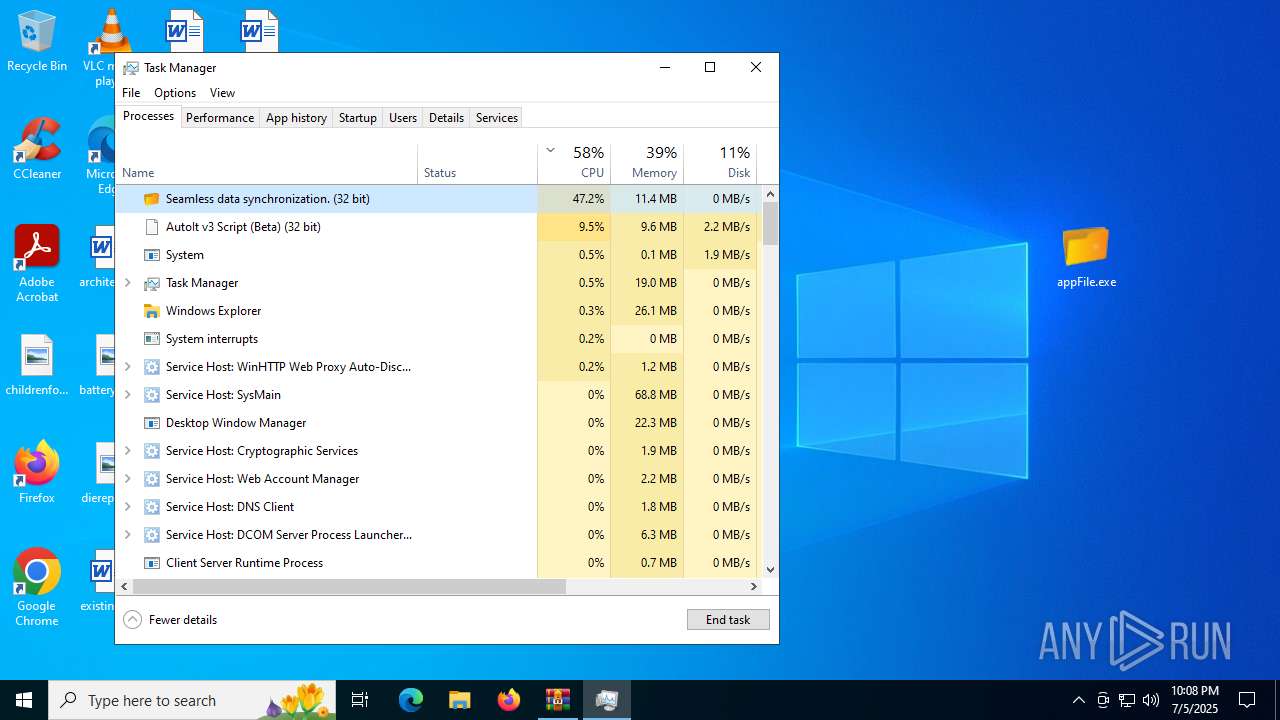
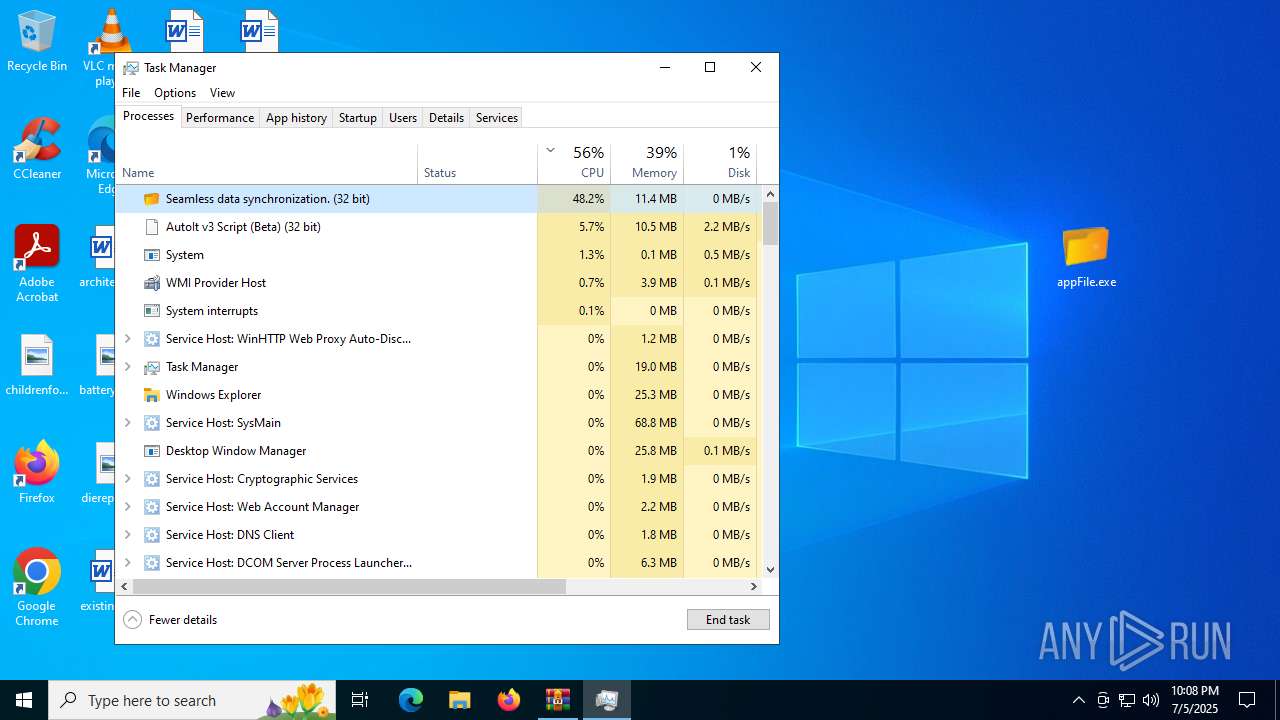
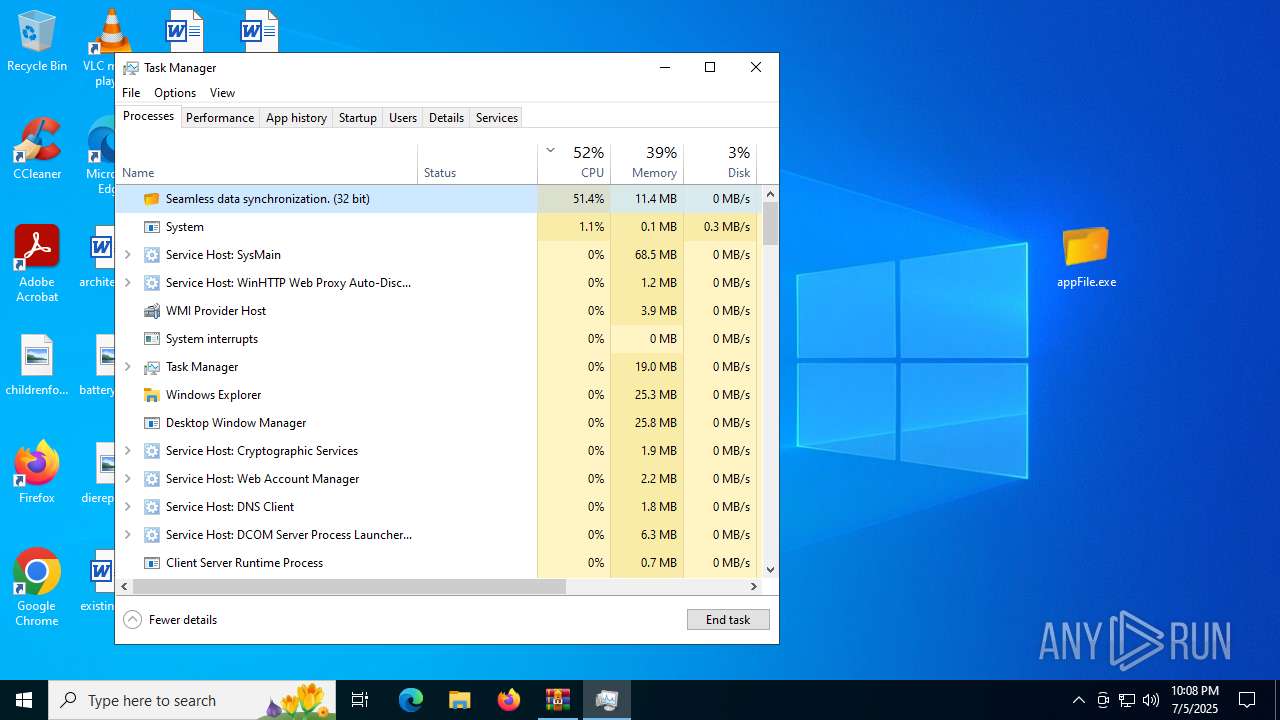
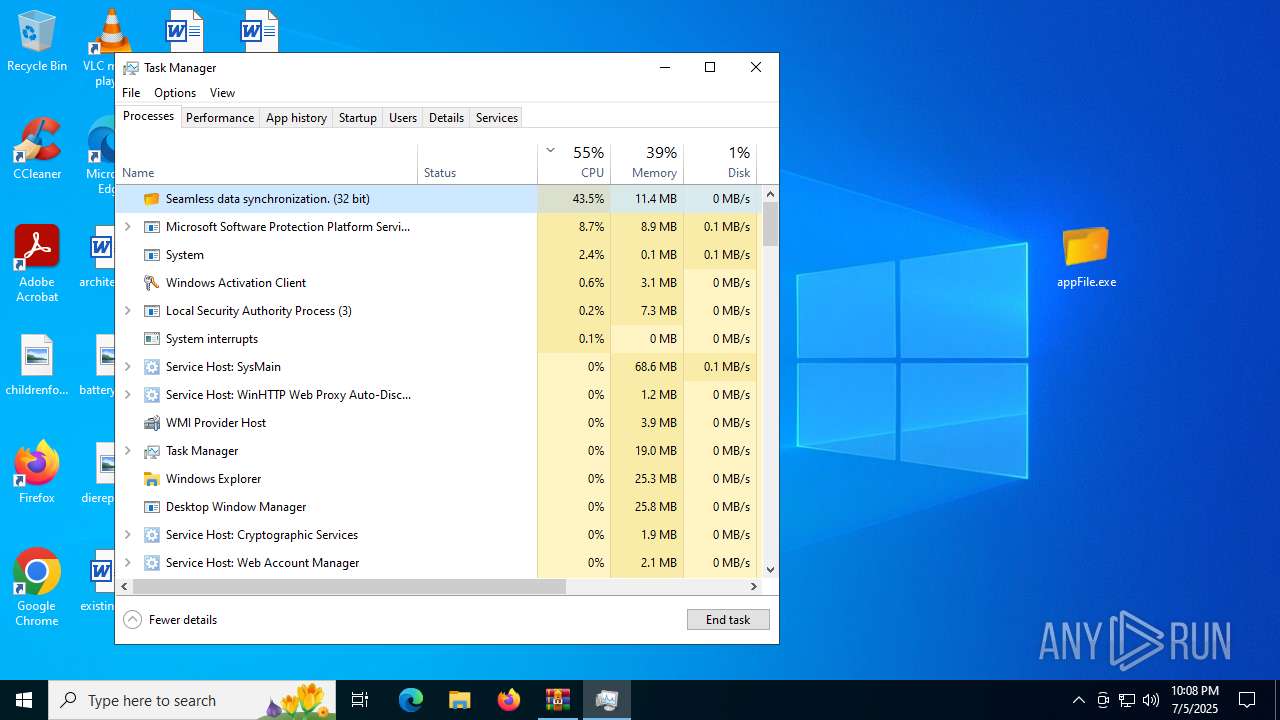
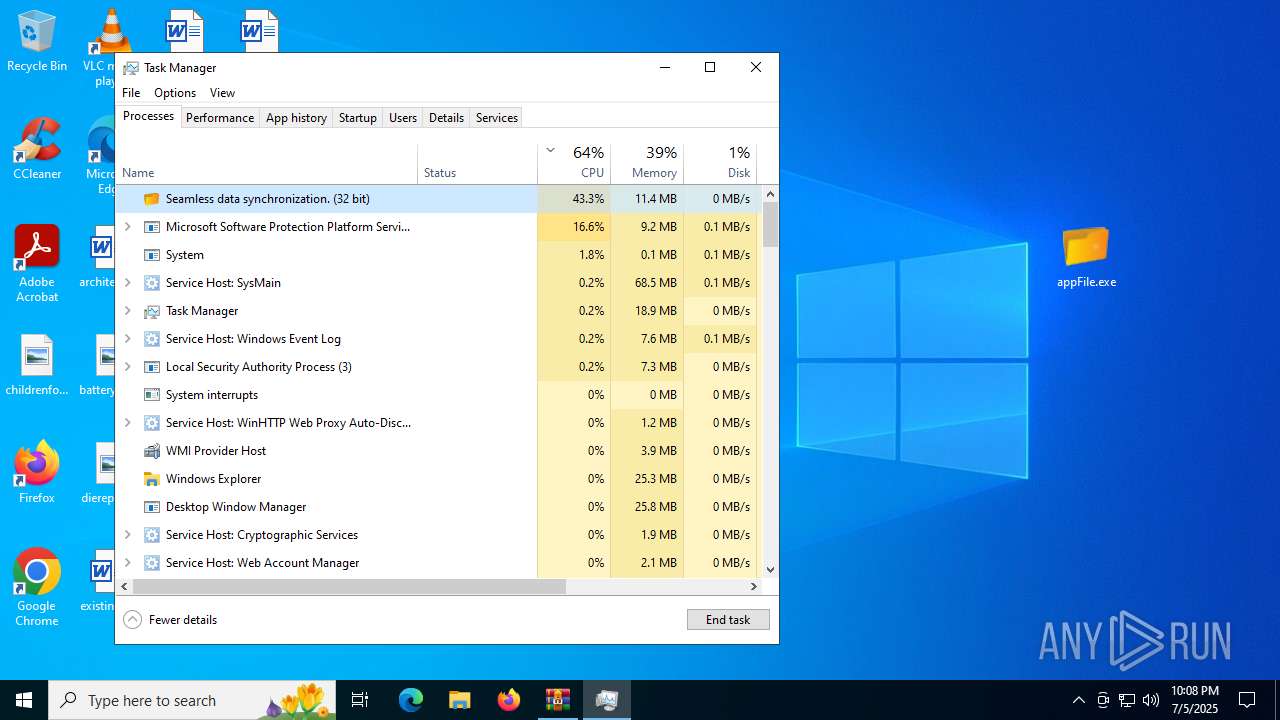
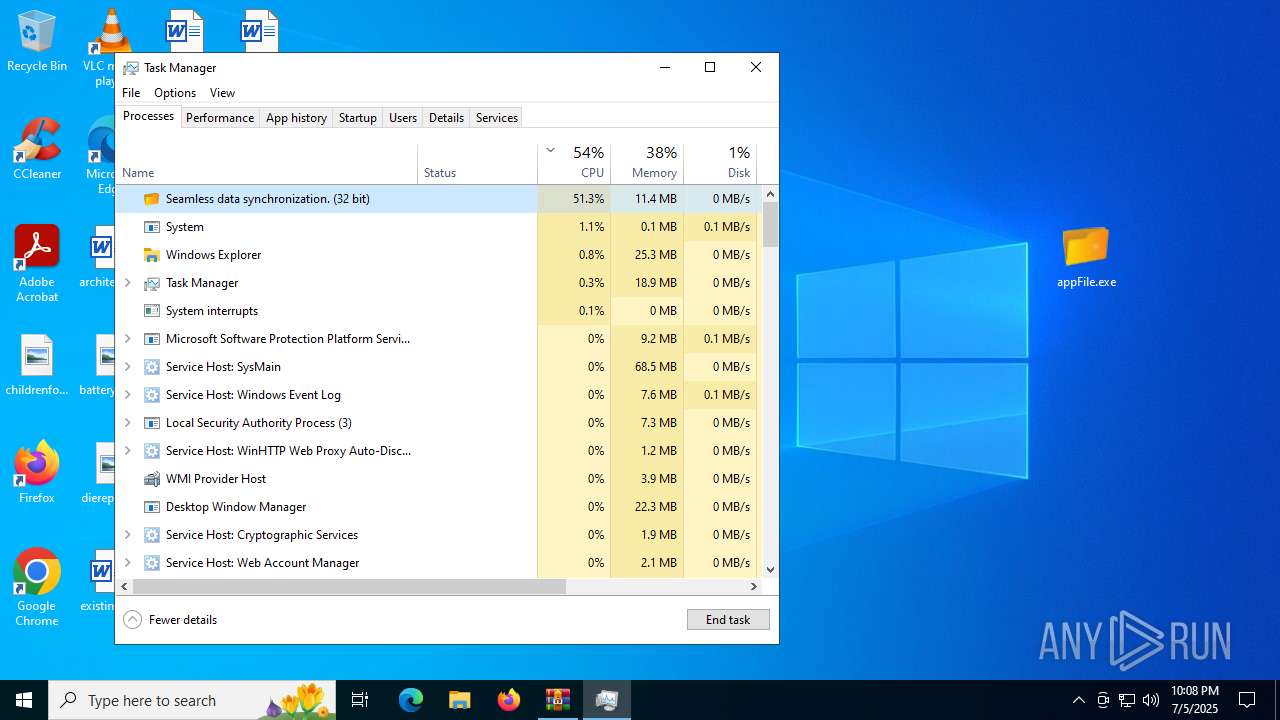
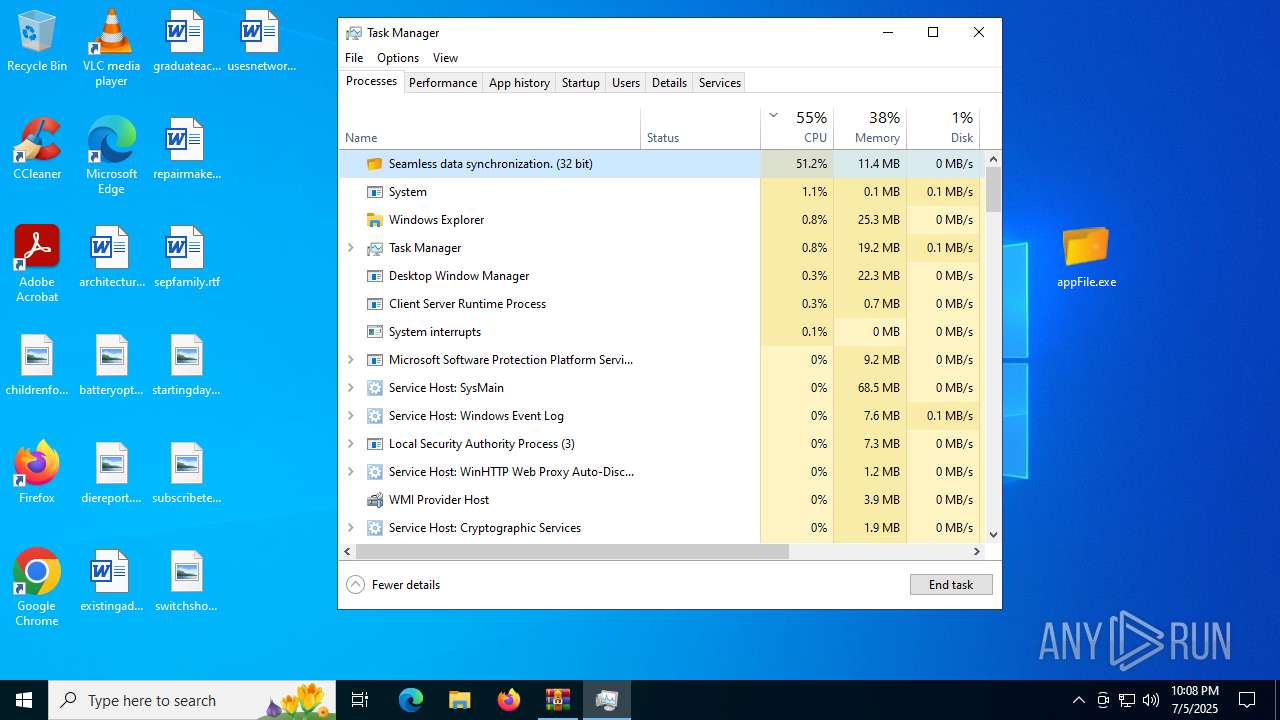
Total processes
264
Monitored processes
121
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2476,i,2194903268380860424,1689394948942852970,262144 --variations-seed-version --mojo-platform-channel-handle=2460 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Telephone.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2788,i,9708938781374473980,15844834227270598598,262144 --variations-seed-version --mojo-platform-channel-handle=2784 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1480 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4088,i,14722552308227093435,14003622130057580273,262144 --variations-seed-version --mojo-platform-channel-handle=4124 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4924,i,11483237793935759685,10589179664055462864,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4884 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2248,i,9708938781374473980,15844834227270598598,262144 --variations-seed-version --mojo-platform-channel-handle=2828 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1740 | findstr "nsWscSvc ekrn bdservicehost SophosHealth AvastUI AVGUI & if not errorlevel 1 Set rXPERneQsPoWqJTVAOXCZamD=AutoIt3.exe & Set GVmVuAERSAMNgPzesRmwUbJvhZZba=.a3x & Set WbuPJWqHgCtFcz=300 | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2404,i,12953881371493472149,3595661537096104590,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3596,i,13697024182472523247,1806285095537186518,262144 --variations-seed-version --mojo-platform-channel-handle=3532 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
31 054
Read events
30 957
Write events
96
Delete events
1
Modification events
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1C55CE1BCC972F00 | |||
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459496 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E4FCE6BD-B39C-4A55-8925-8EDF31BBCF27} | |||
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459496 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {88E18404-176E-46F2-8327-D9B5939AD1B1} | |||
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (2976) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7A87E41BCC972F00 | |||
Executable files
56
Suspicious files
608
Text files
381
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1757b5.TMP | — | |
MD5:— | SHA256:— | |||
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1757b5.TMP | — | |
MD5:— | SHA256:— | |||
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1757a5.TMP | — | |
MD5:— | SHA256:— | |||
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1757b5.TMP | — | |
MD5:— | SHA256:— | |||
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1757e4.TMP | — | |
MD5:— | SHA256:— | |||
| 2976 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
258
DNS requests
252
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6900 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:jTVguNR6mcB1f_EnbjcuMDy10XPcjOmtxoTfVC7Dxjg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2288 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8044 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8044 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4984 | chrome.exe | GET | 200 | 142.250.185.174:80 | http://clients2.google.com/time/1/current?cup2key=8:EDk4KxRAeJg65nZdNp9H-6pHOMrMtvJls1jOxjNJyeQ&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4676 | chrome.exe | GET | 200 | 142.250.185.174:80 | http://clients2.google.com/time/1/current?cup2key=8:NkAR3ABxt2V-rI1-1Ftcyo8wE6cnZSFnFYz277LyUAM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1232 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1752269267&P2=404&P3=2&P4=aSADpRgEsQbRczyG1wT7mVJBoKP%2bnbTwt8e%2fkvP7SwtoQByfiFrdD6z4lbn5iaeMygvZ2EE7MLazjRvc1RQP9A%3d%3d | unknown | — | — | whitelisted |
7564 | chrome.exe | GET | 200 | 142.250.185.174:80 | http://clients2.google.com/time/1/current?cup2key=8:BLVhPTu-tDDeG7SAdQCzN5viWBPQF8KYSpwyuuHfSKk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1352 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6900 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6900 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6900 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6900 | msedge.exe | 104.126.37.136:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
6900 | msedge.exe | 188.114.97.3:443 | arch2.cloud8323v2.sbs | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
arch2.cloud8323v2.sbs |
| unknown |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |