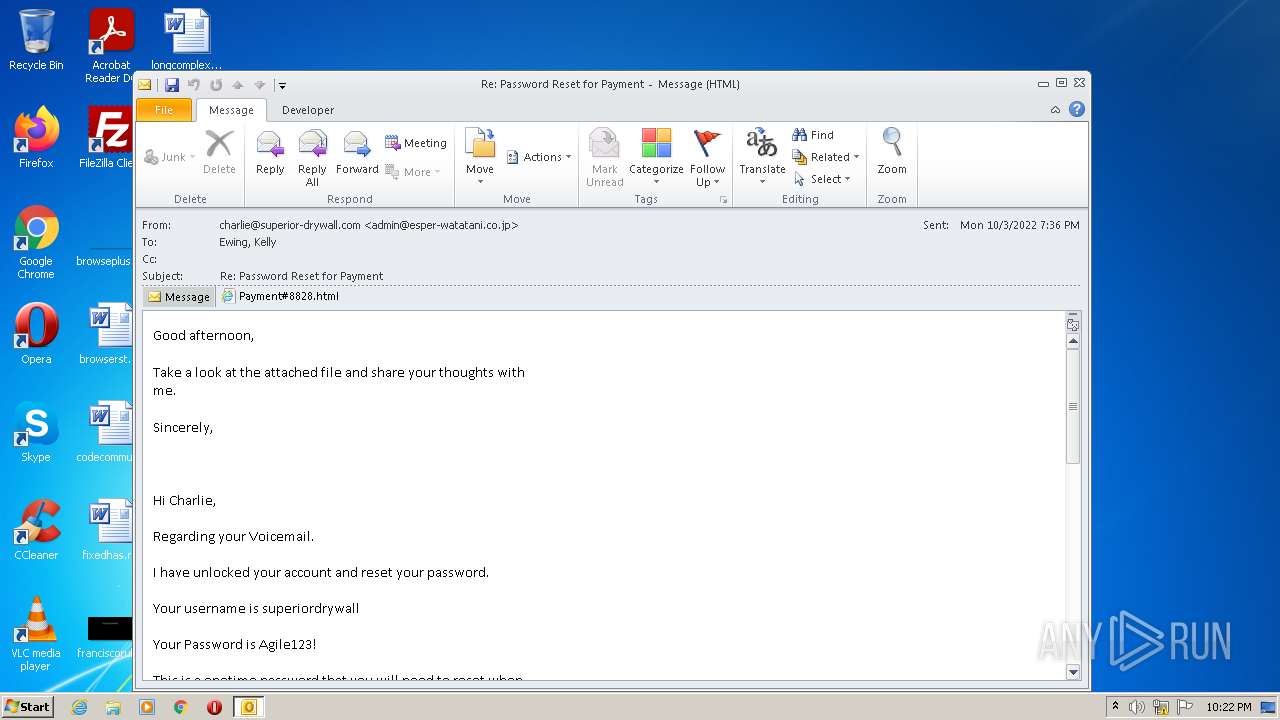
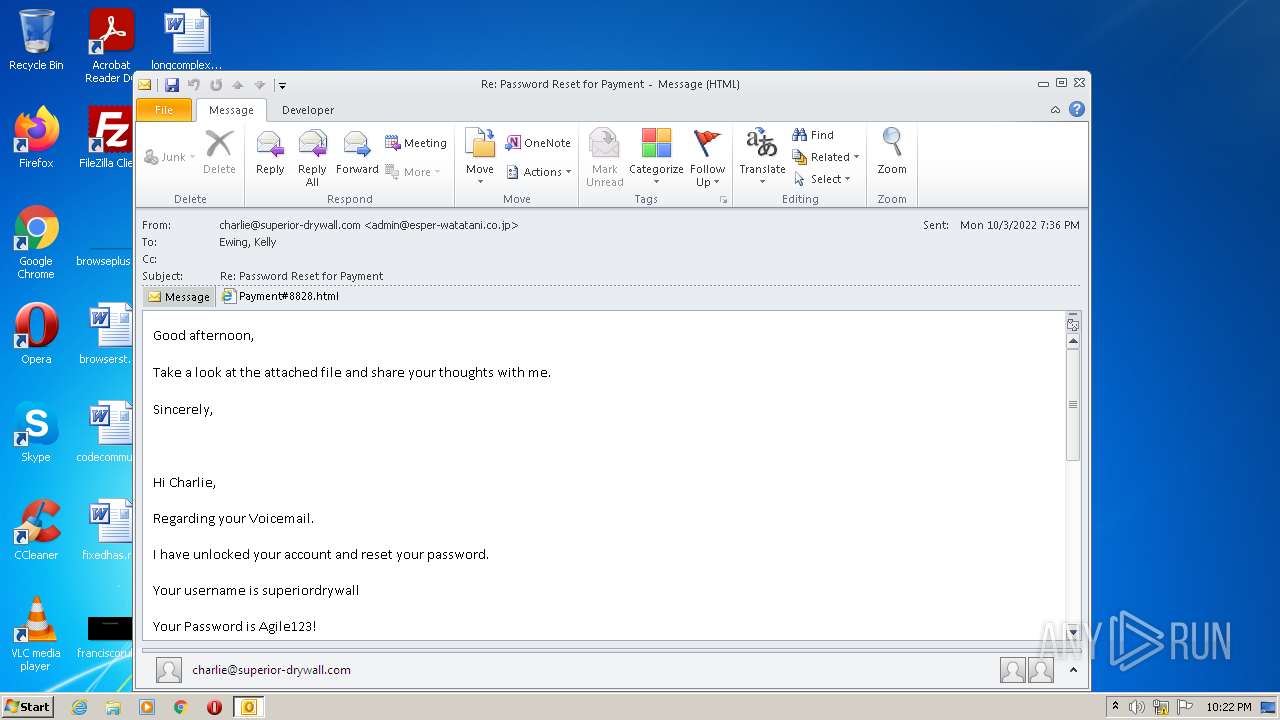
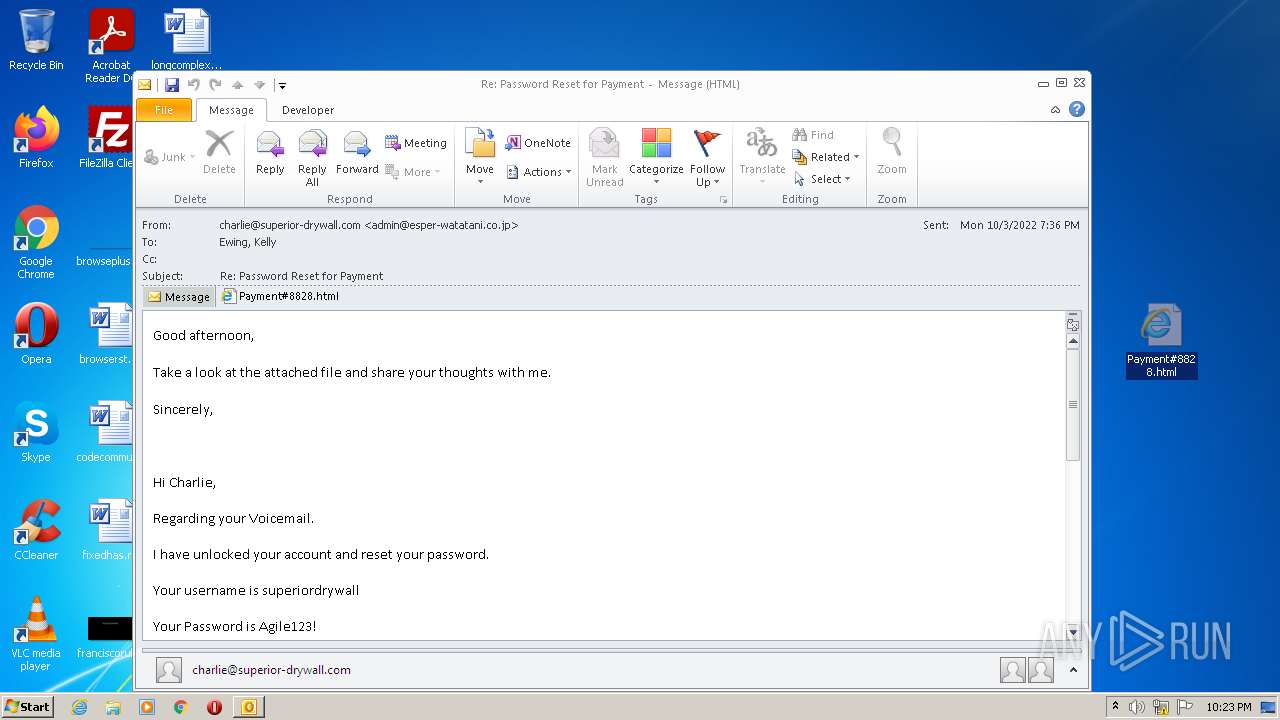
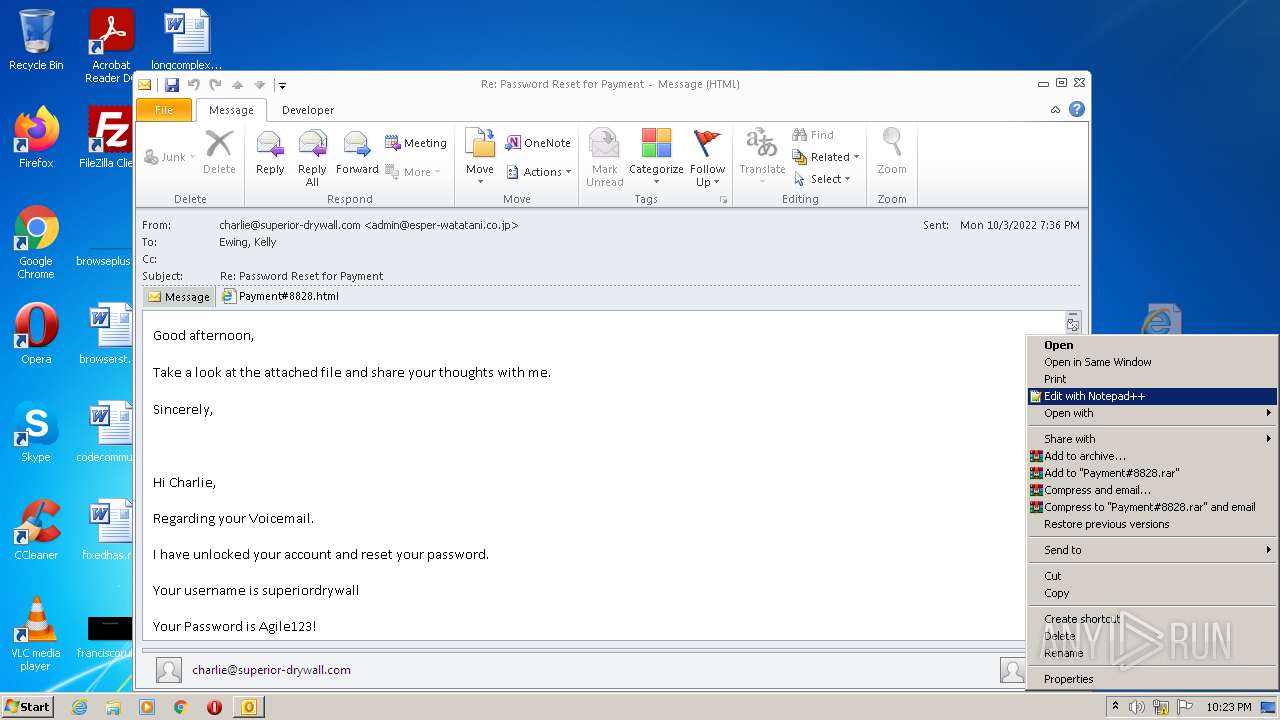
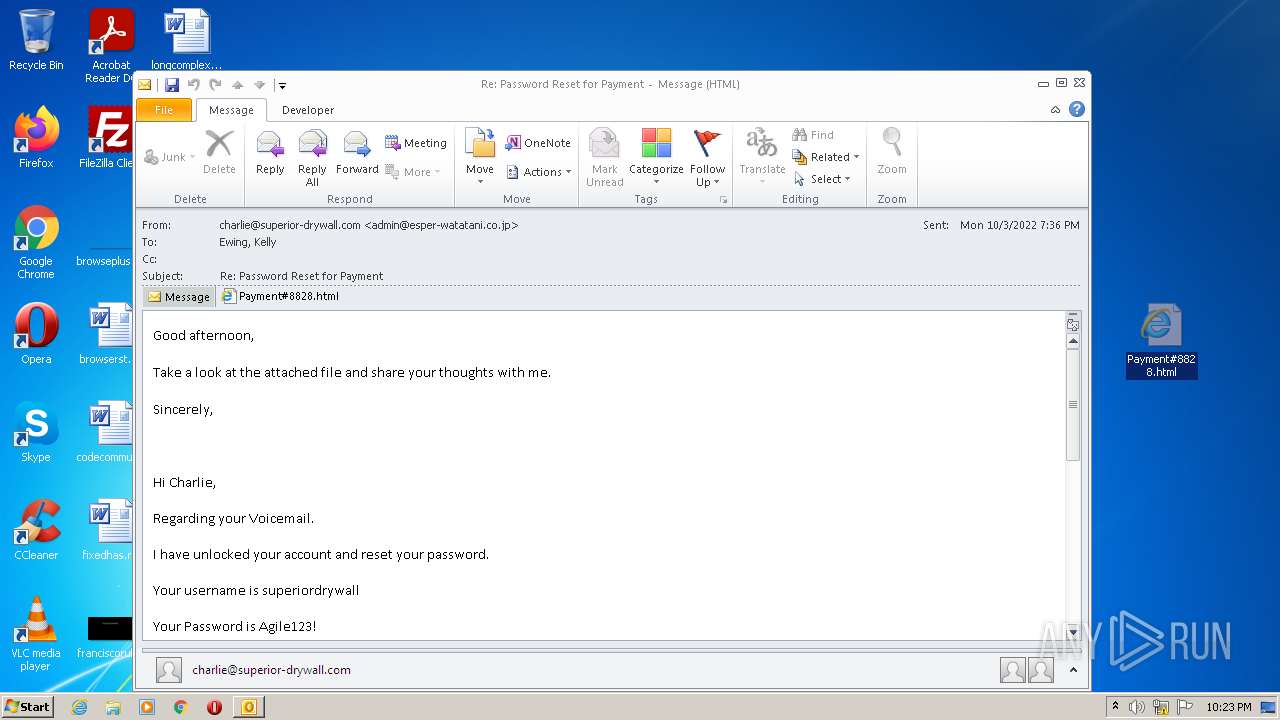
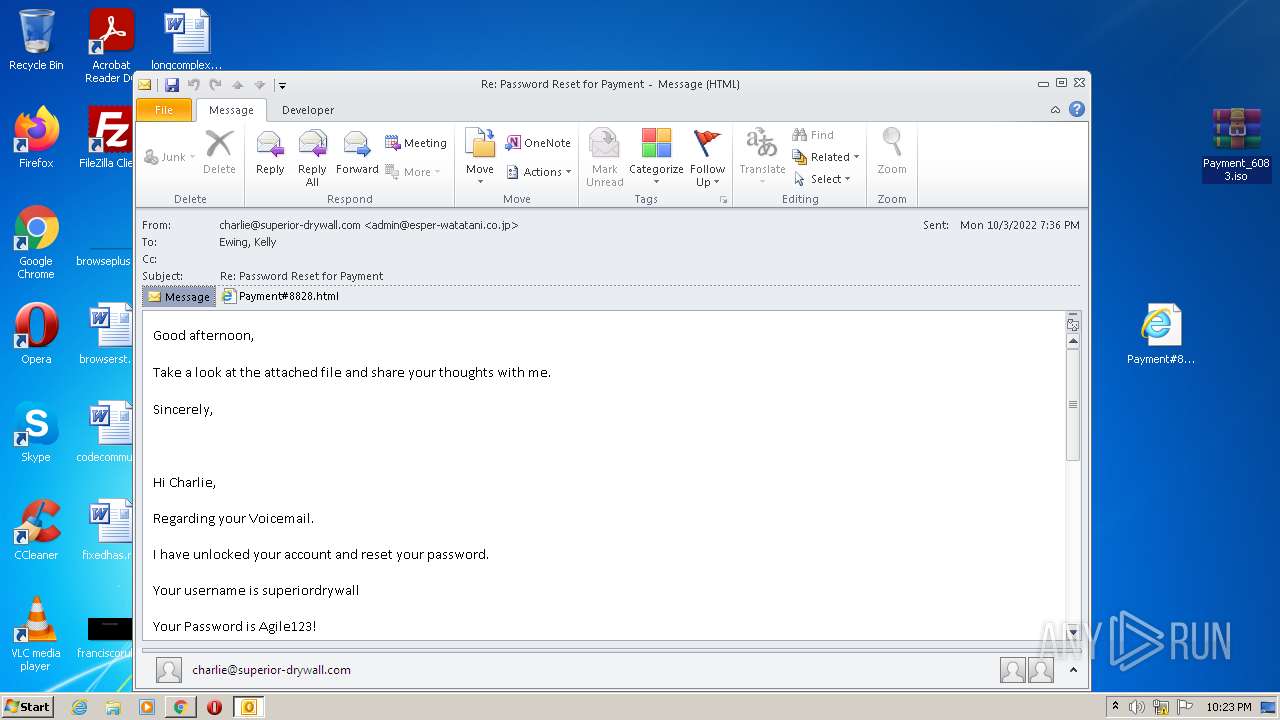
| File name: | Re Password Reset for Payment.msg |
| Full analysis: | https://app.any.run/tasks/5da55fcd-bf67-4373-a2ca-0217e4e6e694 |
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | October 04, 2022, 21:22:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | C29362B3983432EB7714DE54D9774B97 |
| SHA1: | 1E56715CB6147AE6A3788B83A592219B96AC7697 |
| SHA256: | 9144E2E6CFDFA1EE4B5598ADBCEC241F8265D022DE5EA9B6B55836B2818BFE4F |
| SSDEEP: | 24576:PyI3PPkDcjBR8+aCHfPGCRnJPfVUWCuTwwCsqOYKed3StreM+DF5LbIMiZnJgS:noubHPTpsKI3NpLLb/i |
MALICIOUS
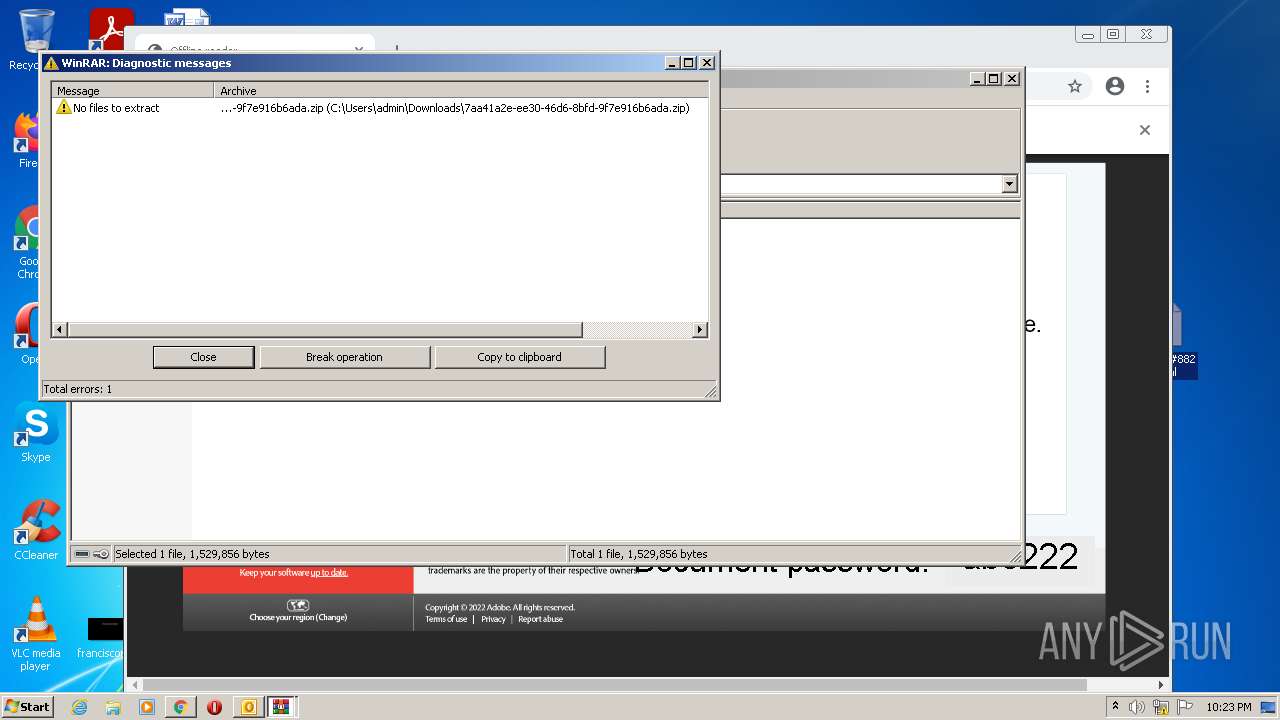
Drops executable file immediately after starts
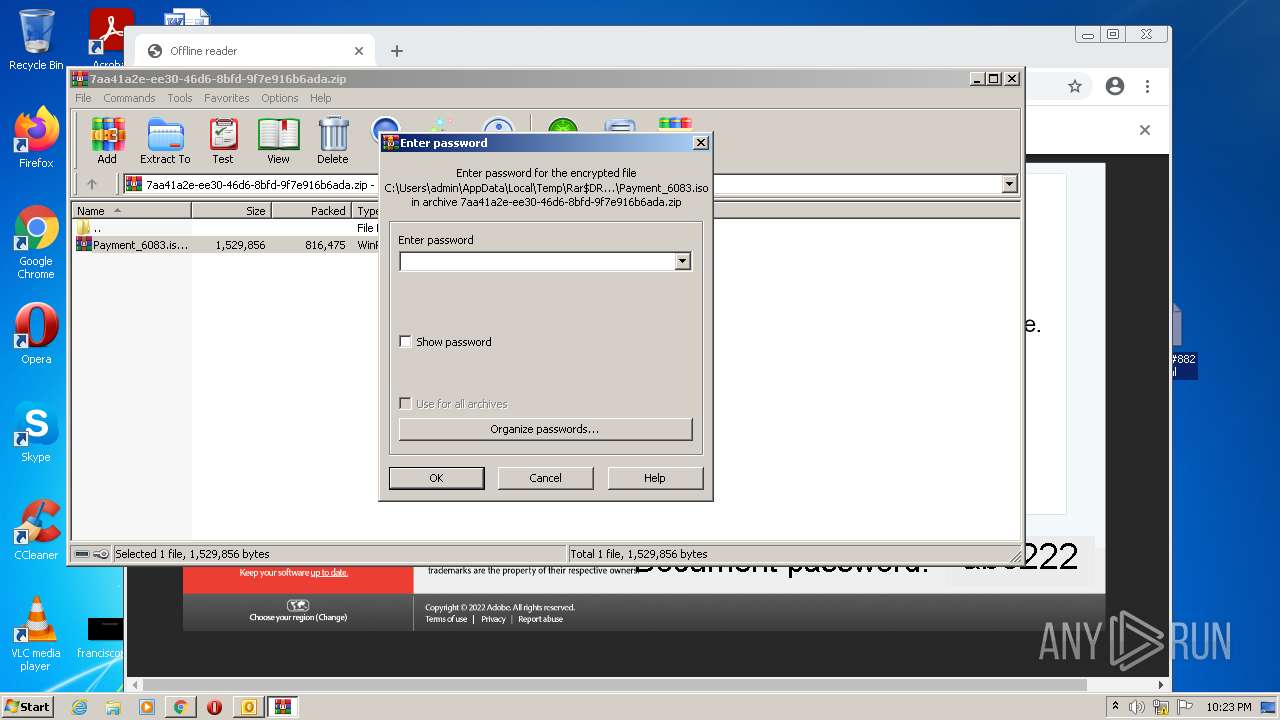
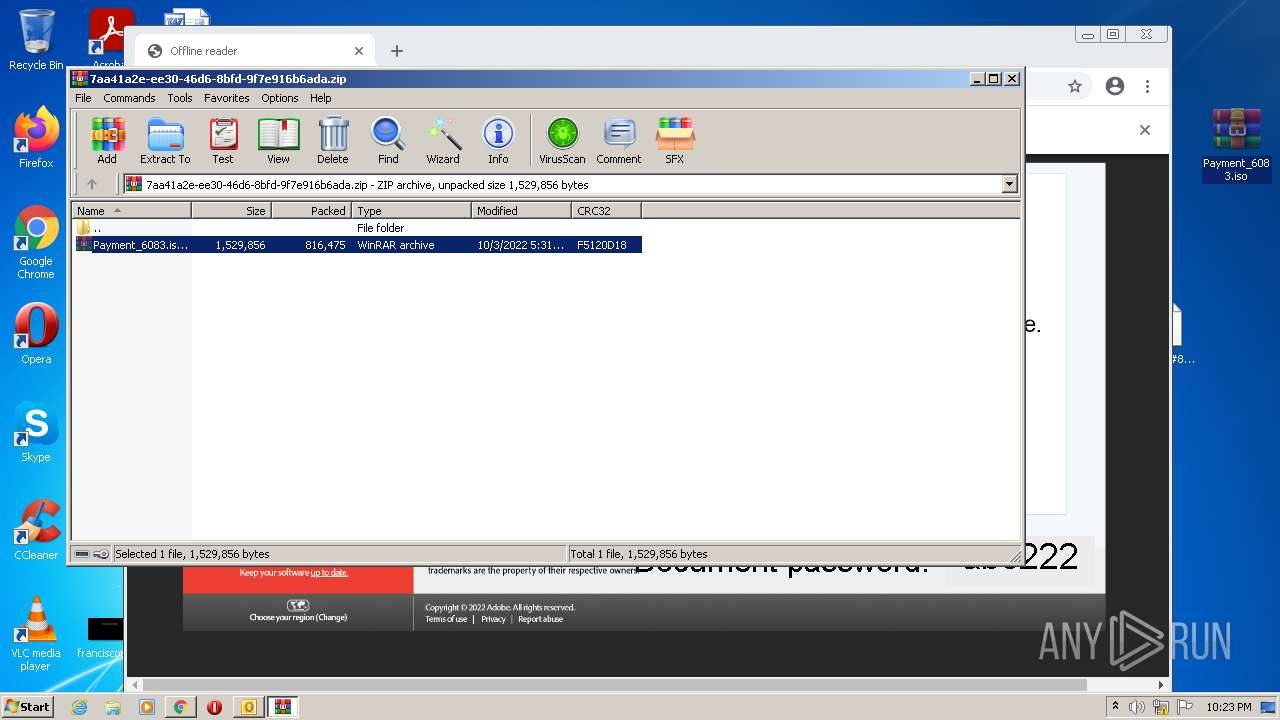
- WinRAR.exe (PID: 2948)
- chrome.exe (PID: 3776)
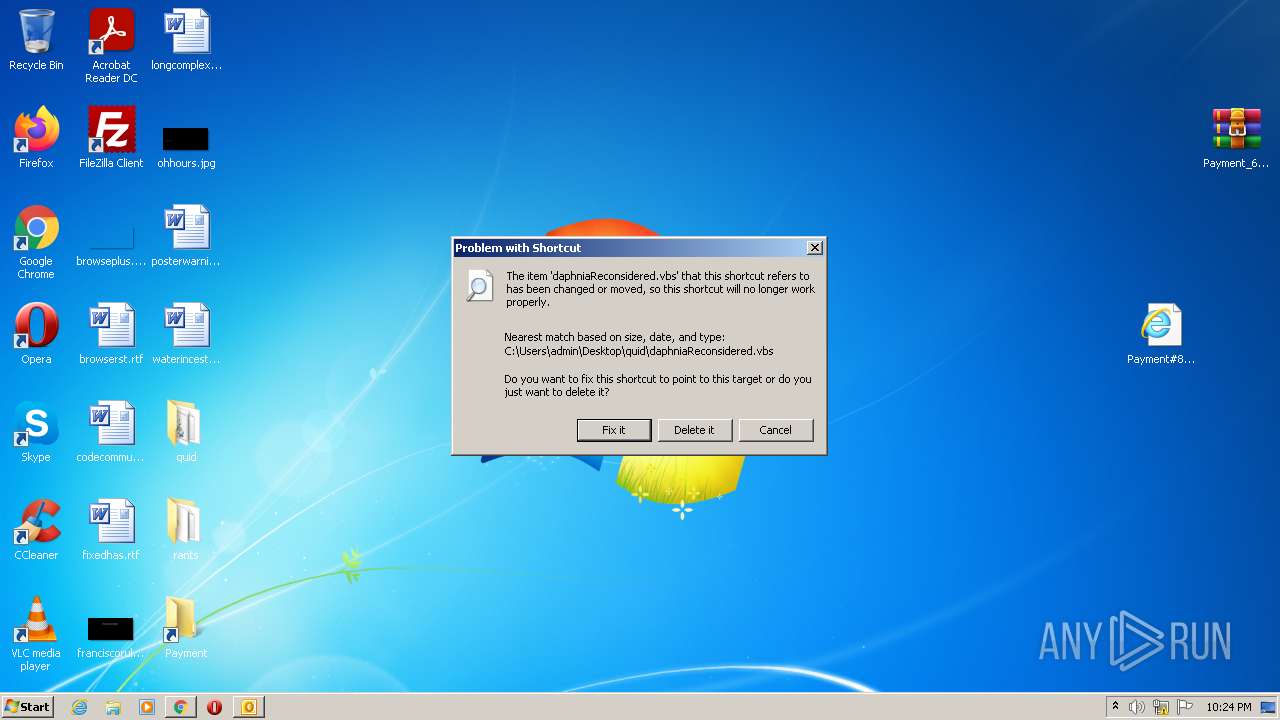
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 984)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2984)
QBOT detected by memory dumps
- wermgr.exe (PID: 2220)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3532)
Executed as Windows Service
- SearchIndexer.exe (PID: 3392)
Creates files in the program directory
- SearchIndexer.exe (PID: 3392)
Reads default file associations for system extensions
- SearchIndexer.exe (PID: 3392)
Checks supported languages
- WinRAR.exe (PID: 2192)
- WinRAR.exe (PID: 2480)
- WinRAR.exe (PID: 2948)
- WScript.exe (PID: 2932)
- cmd.exe (PID: 984)
Reads Microsoft Outlook installation path
- chrome.exe (PID: 2996)
Reads the computer name
- WinRAR.exe (PID: 2192)
- WinRAR.exe (PID: 2480)
- WScript.exe (PID: 2932)
- WinRAR.exe (PID: 2948)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2948)
- chrome.exe (PID: 3776)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2948)
- chrome.exe (PID: 3776)
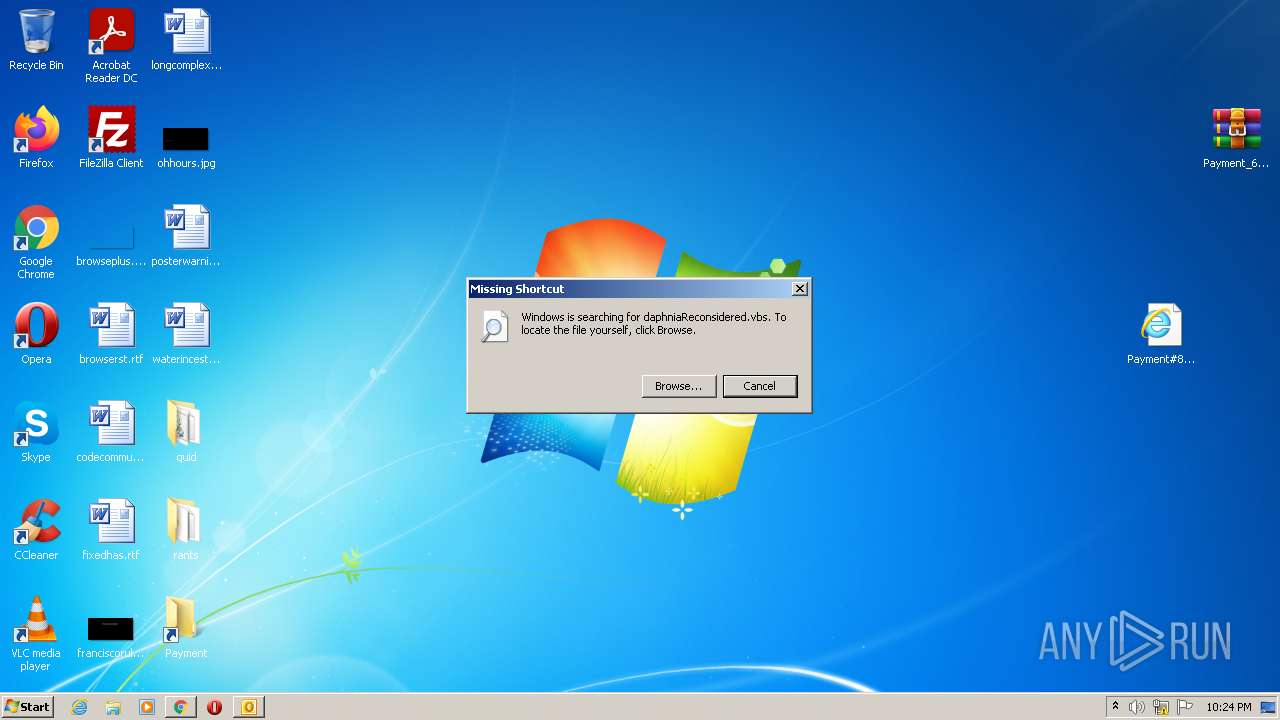
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2932)
INFO
Reads the computer name
- OUTLOOK.EXE (PID: 2964)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 760)
- SearchProtocolHost.exe (PID: 3092)
- SearchIndexer.exe (PID: 3392)
- SearchProtocolHost.exe (PID: 2464)
- SearchFilterHost.exe (PID: 2808)
- chrome.exe (PID: 1100)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 2476)
- regsvr32.exe (PID: 2984)
- wermgr.exe (PID: 2220)
Checks supported languages
- OUTLOOK.EXE (PID: 2964)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 2768)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 760)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 2952)
- SearchIndexer.exe (PID: 3392)
- SearchFilterHost.exe (PID: 2808)
- SearchProtocolHost.exe (PID: 2464)
- SearchProtocolHost.exe (PID: 3092)
- chrome.exe (PID: 1100)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2476)
- chrome.exe (PID: 2908)
- regsvr32.exe (PID: 2984)
- wermgr.exe (PID: 2220)
- chrome.exe (PID: 1272)
- chrome.exe (PID: 3204)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 3868)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 984)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 3776)
Searches for installed software
- OUTLOOK.EXE (PID: 2964)
Application launched itself
- chrome.exe (PID: 3532)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2964)
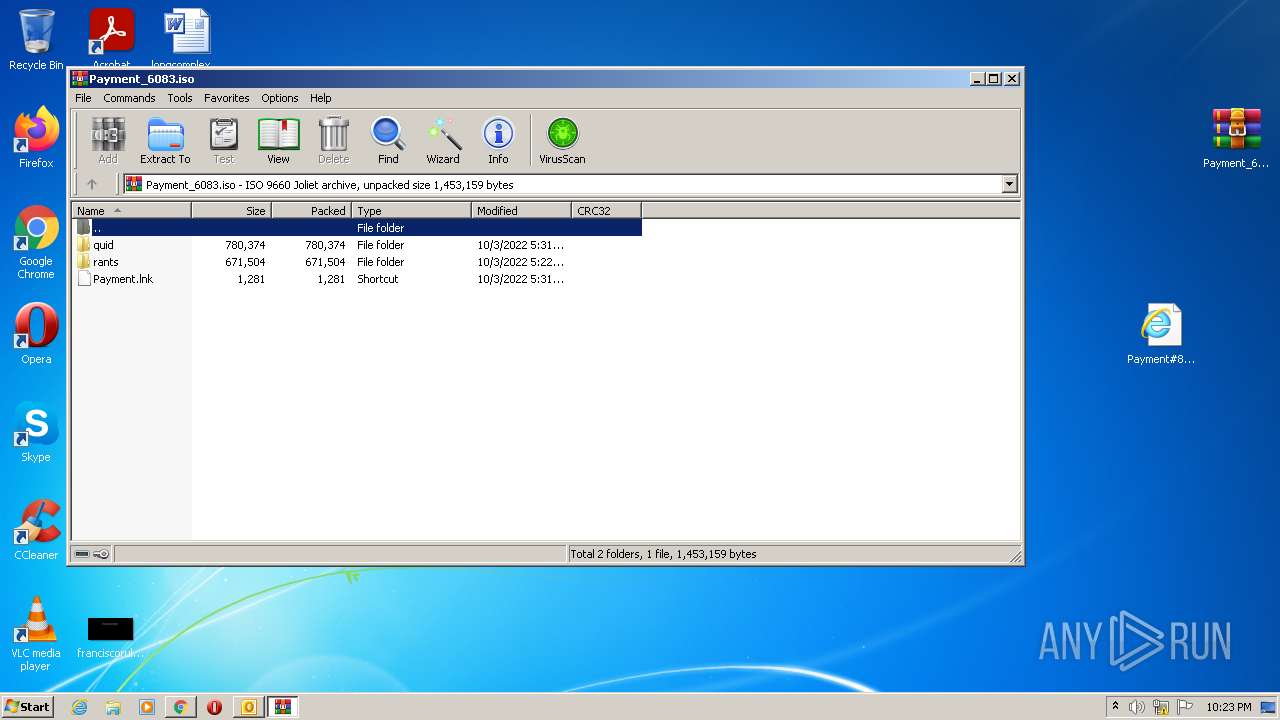
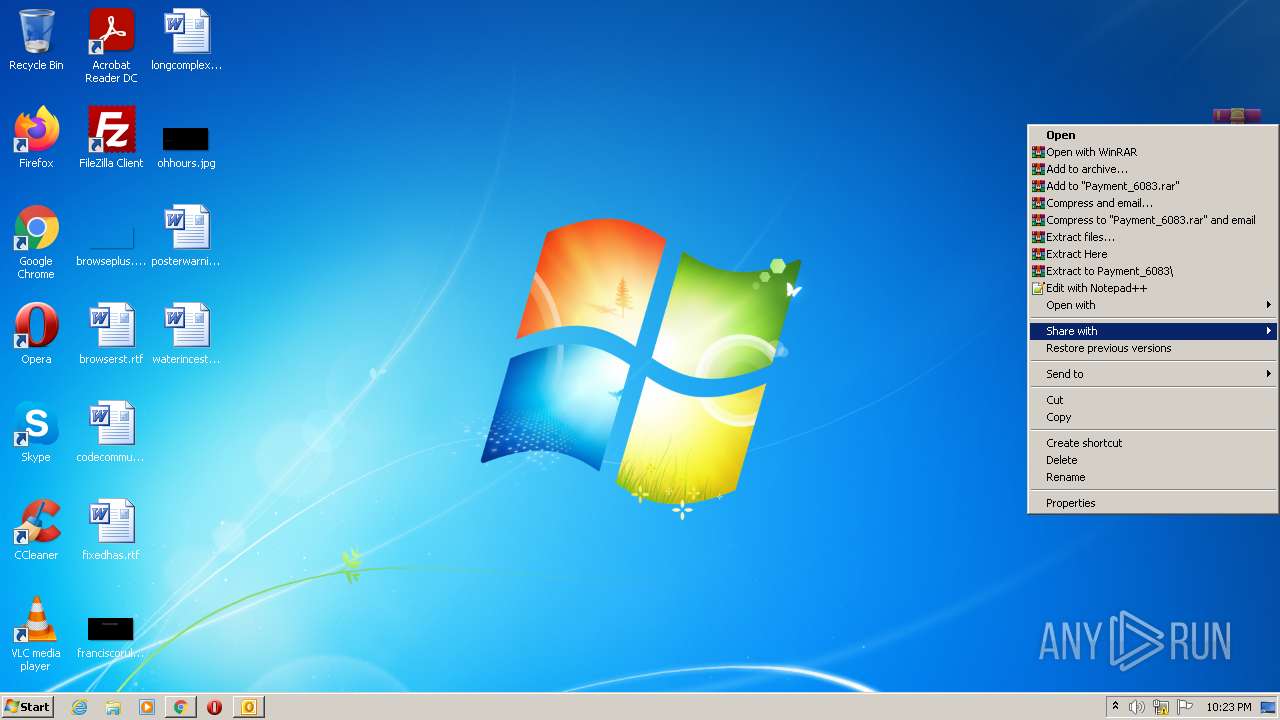
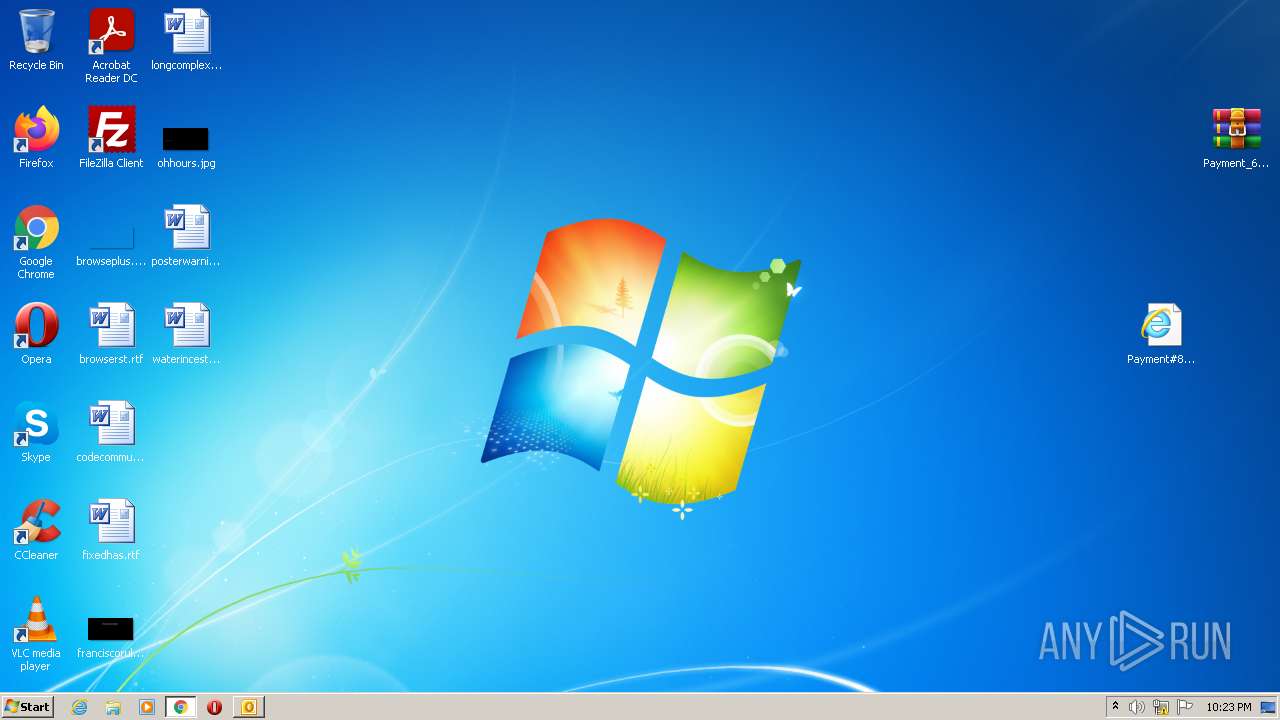
Manual execution by user
- chrome.exe (PID: 3532)
- WinRAR.exe (PID: 2480)
- WinRAR.exe (PID: 2948)
- WScript.exe (PID: 2932)
Reads the hosts file
- chrome.exe (PID: 3532)
- chrome.exe (PID: 3596)
Reads settings of System Certificates
- chrome.exe (PID: 3596)
Reads Microsoft Office registry keys
- SearchProtocolHost.exe (PID: 2464)
- OUTLOOK.EXE (PID: 2964)
Reads the date of Windows installation
- chrome.exe (PID: 2984)
Checks Windows Trust Settings
- WScript.exe (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
84
Monitored processes
42
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,146566666187487035,5798700481995718427,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2848 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 984 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\quid\conciliatorExactly.cmd" regs" | C:\Windows\system32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,146566666187487035,5798700481995718427,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=836 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1028,146566666187487035,5798700481995718427,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3256 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,146566666187487035,5798700481995718427,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3440 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,146566666187487035,5798700481995718427,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,146566666187487035,5798700481995718427,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3436 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
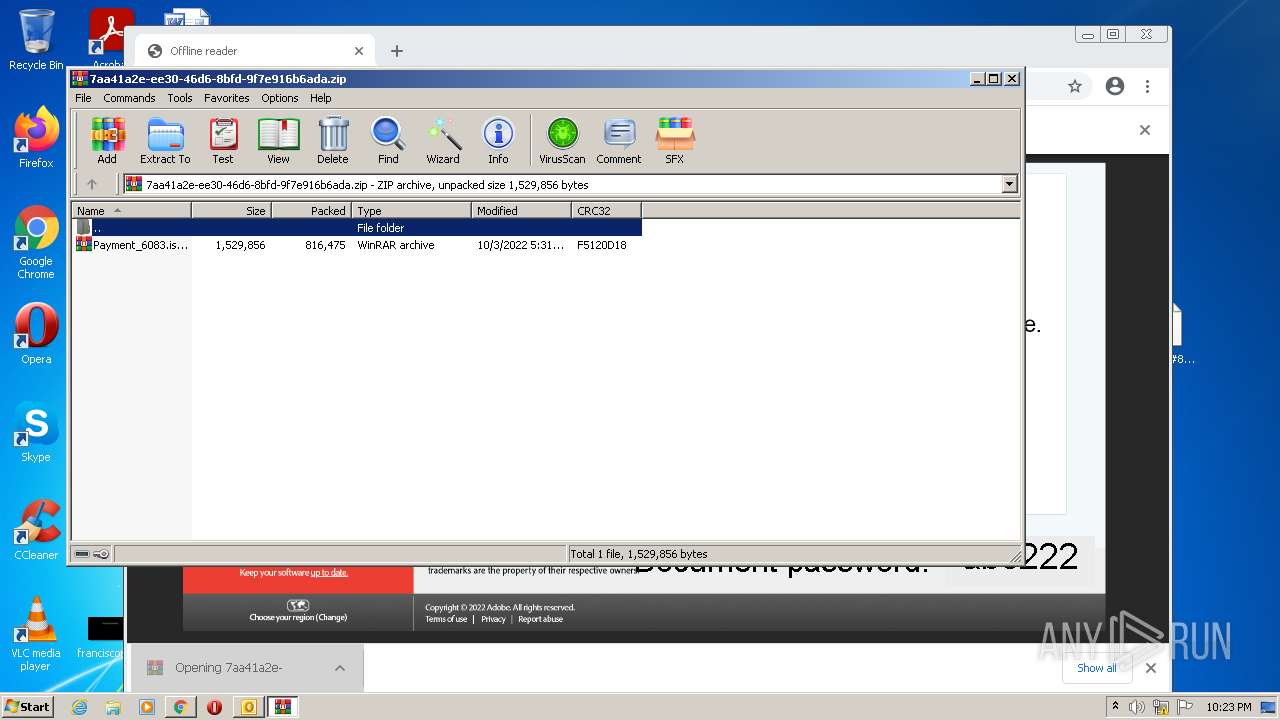
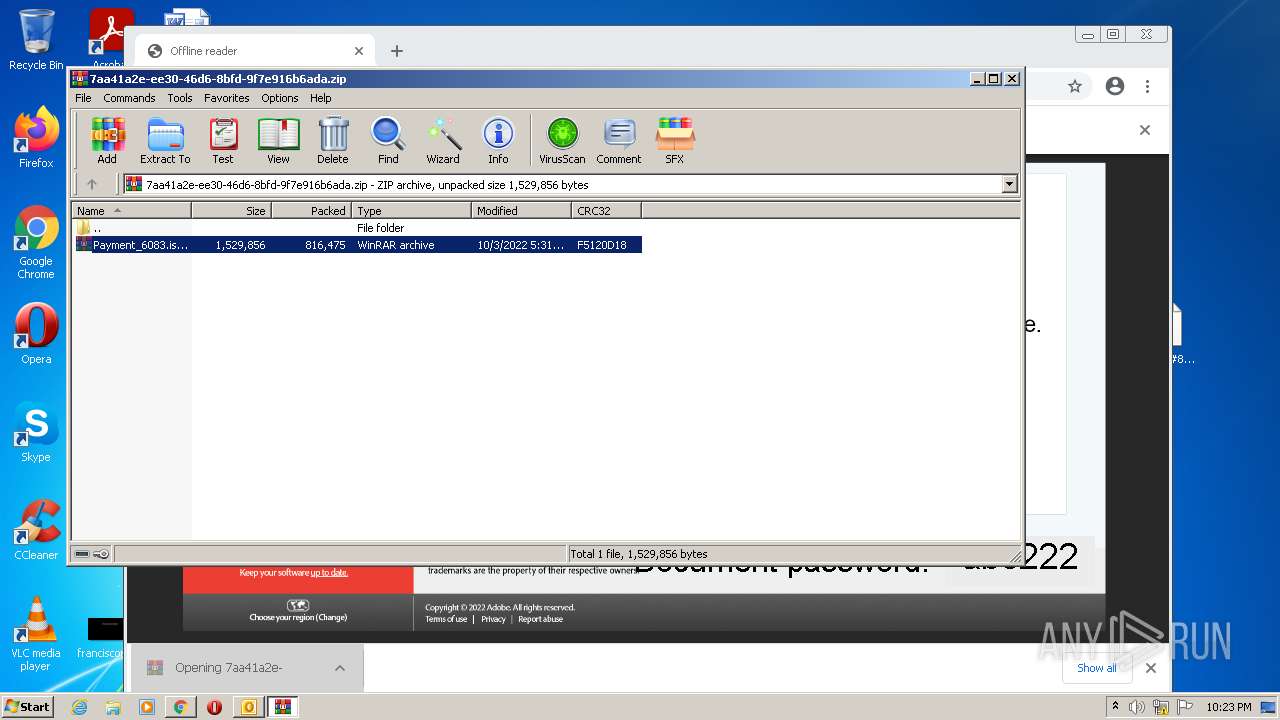
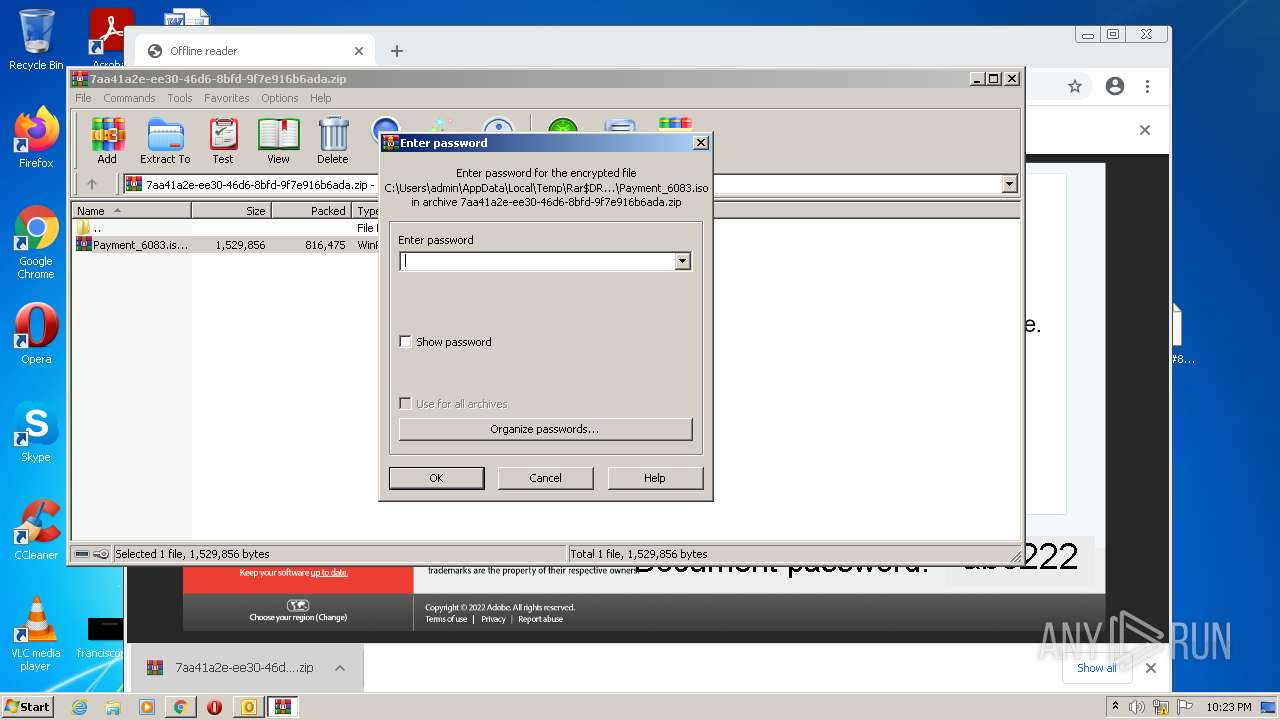
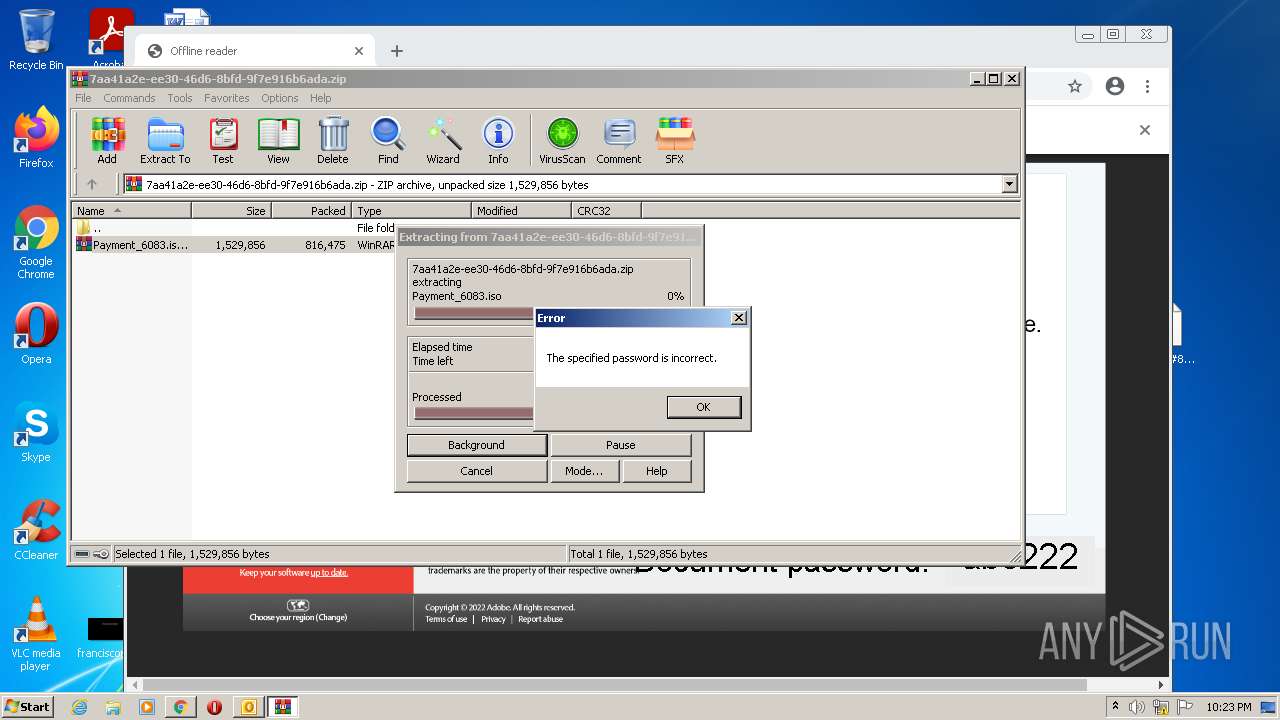
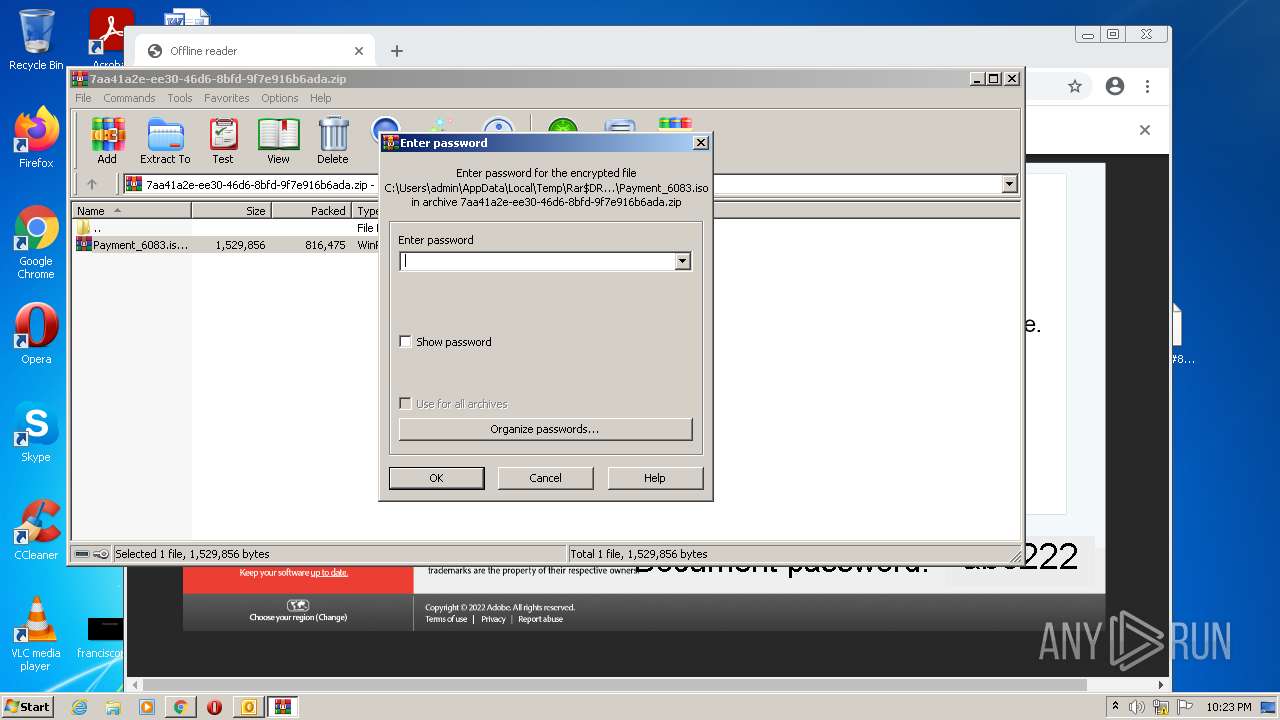
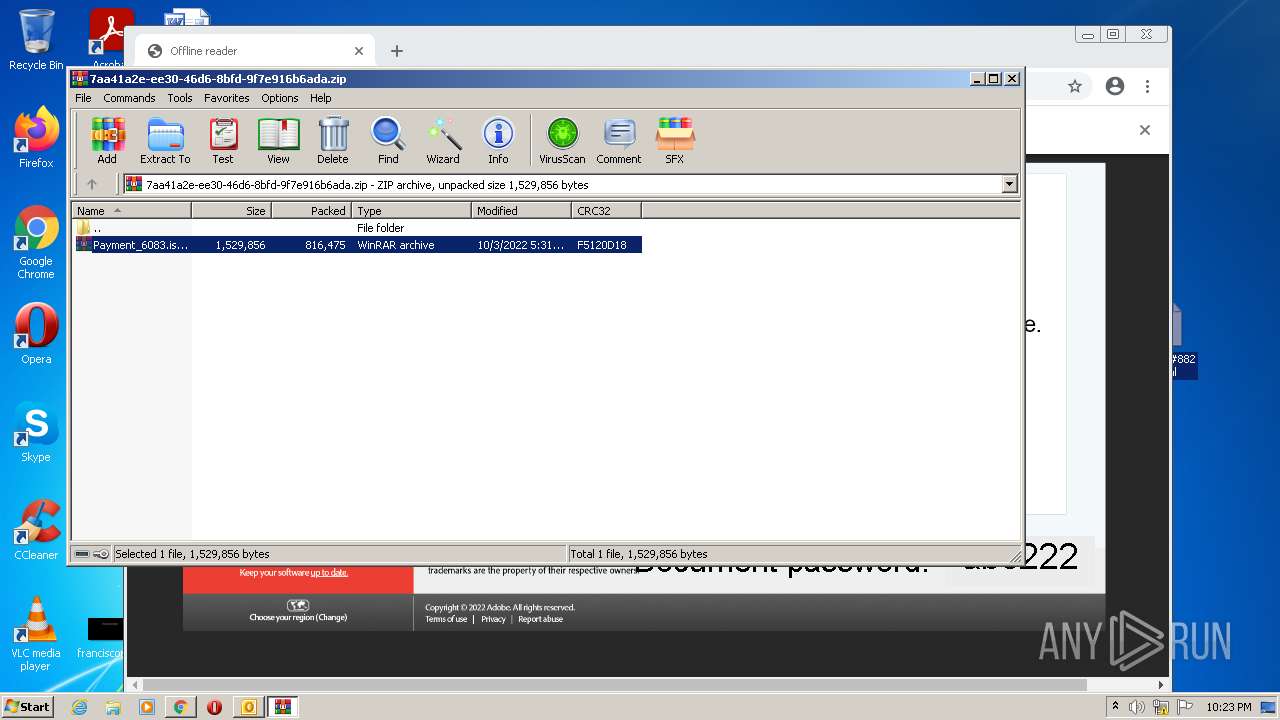
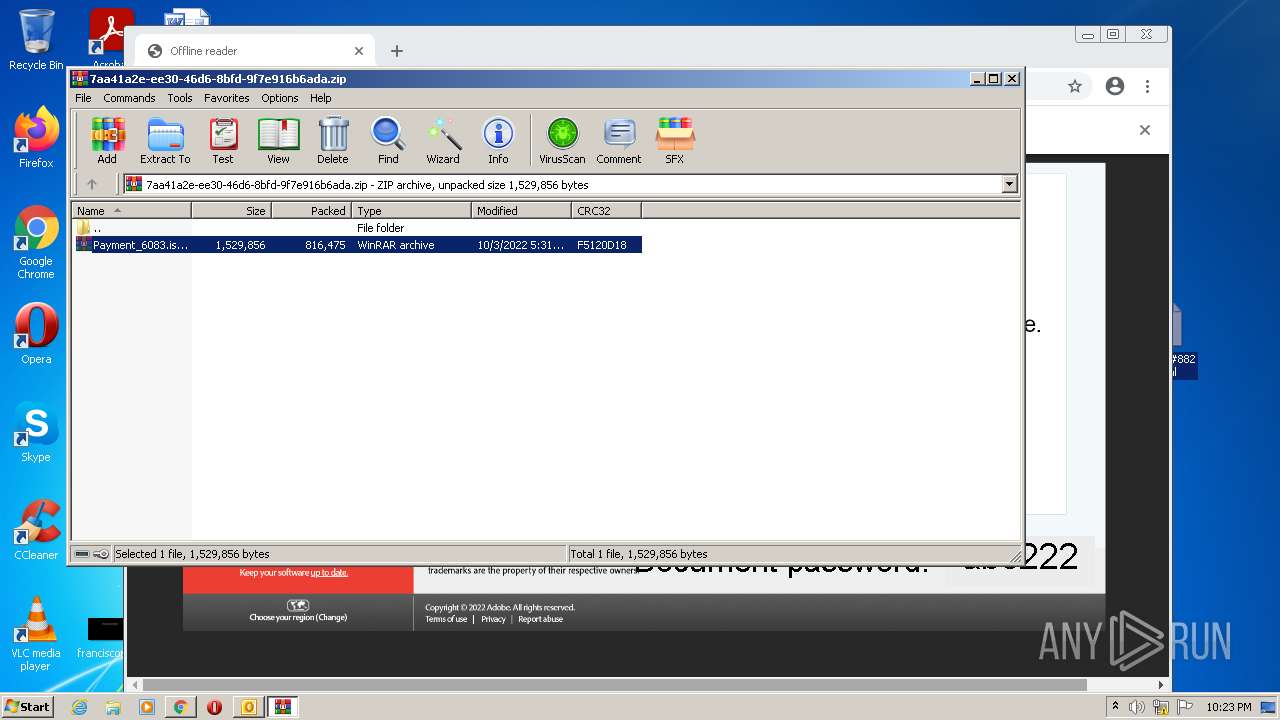
| 2192 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\7aa41a2e-ee30-46d6-8bfd-9f7e916b6ada.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2220 | C:\Windows\System32\wermgr.exe | C:\Windows\System32\wermgr.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7601.24521 (win7sp1_ldr_escrow.190909-1704) Modules
| |||||||||||||||
| 2464 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10001_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10001 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
Total events
25 390
Read events
24 413
Write events
947
Delete events
30
Modification events
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2964) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
3
Suspicious files
185
Text files
182
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA4EB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2964 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633CA43A-DCC.pma | — | |
MD5:— | SHA256:— | |||
| 2964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2964 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
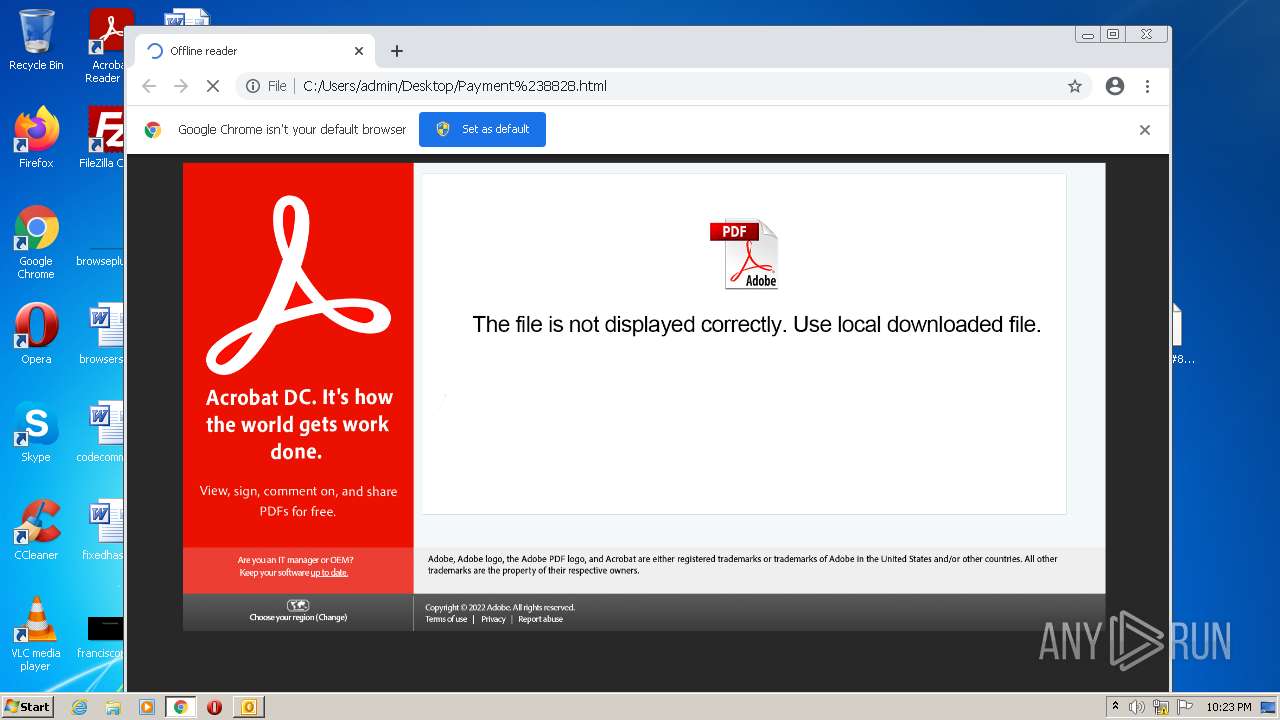
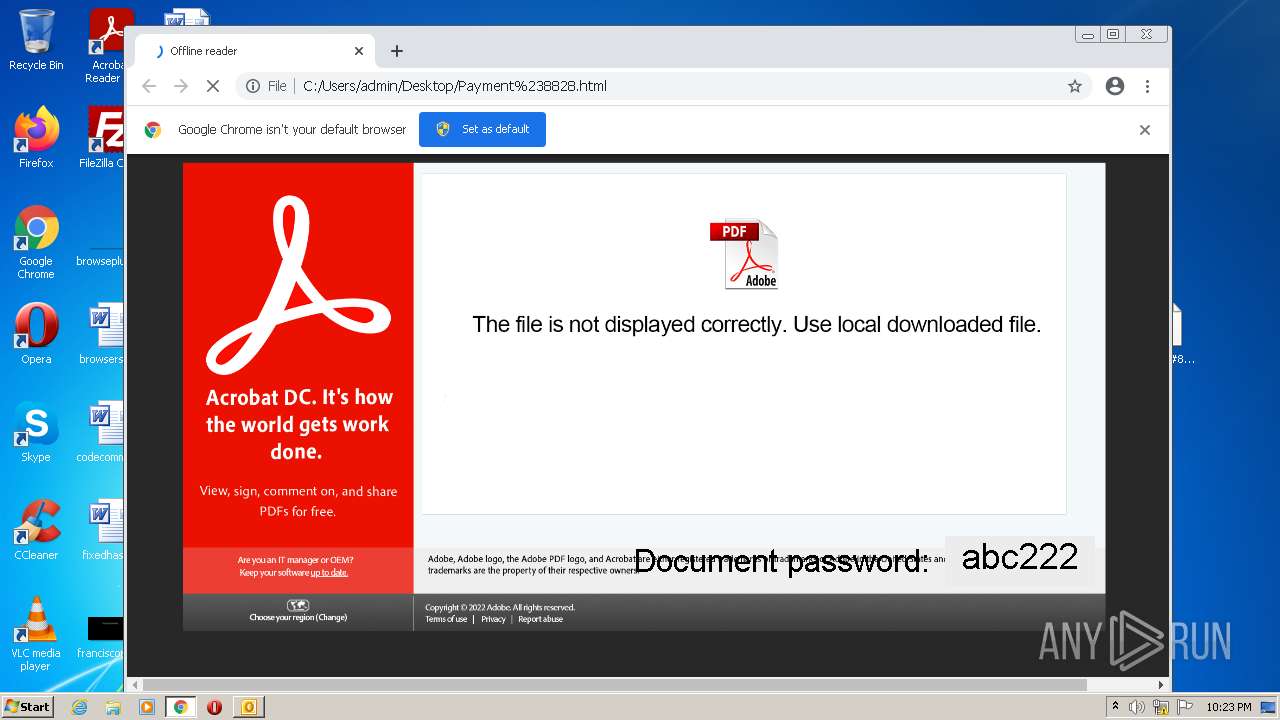
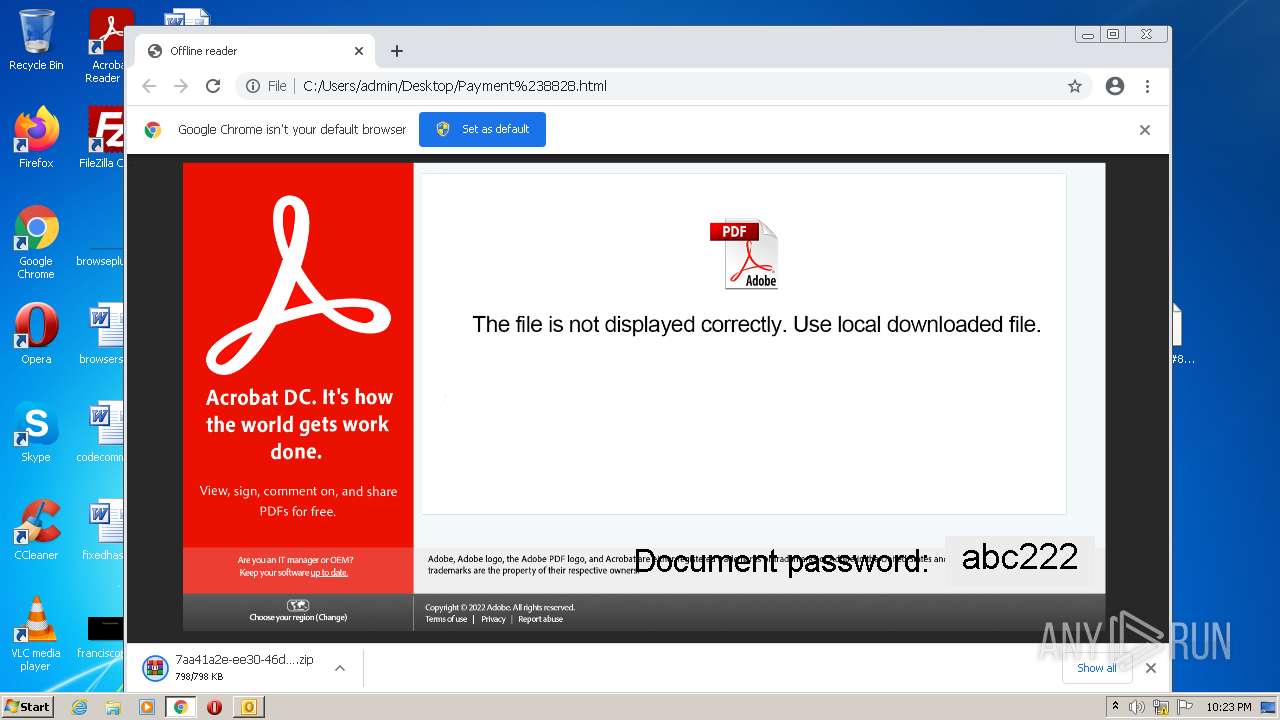
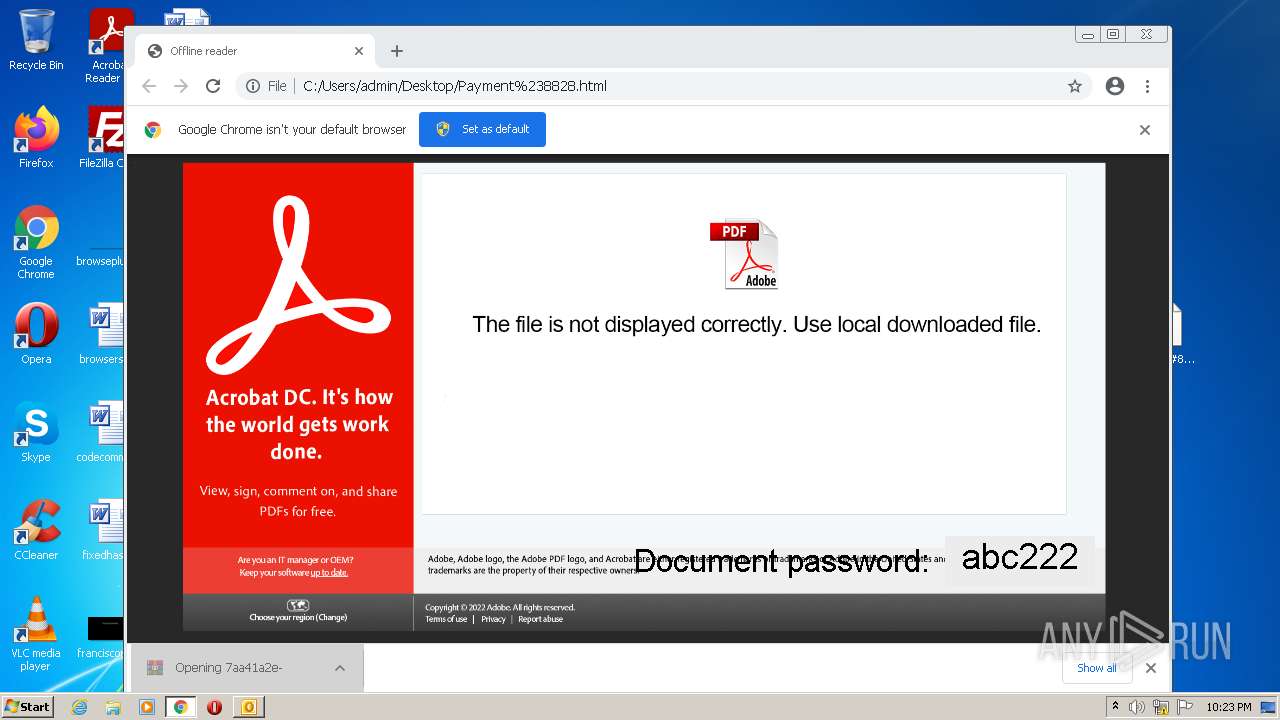
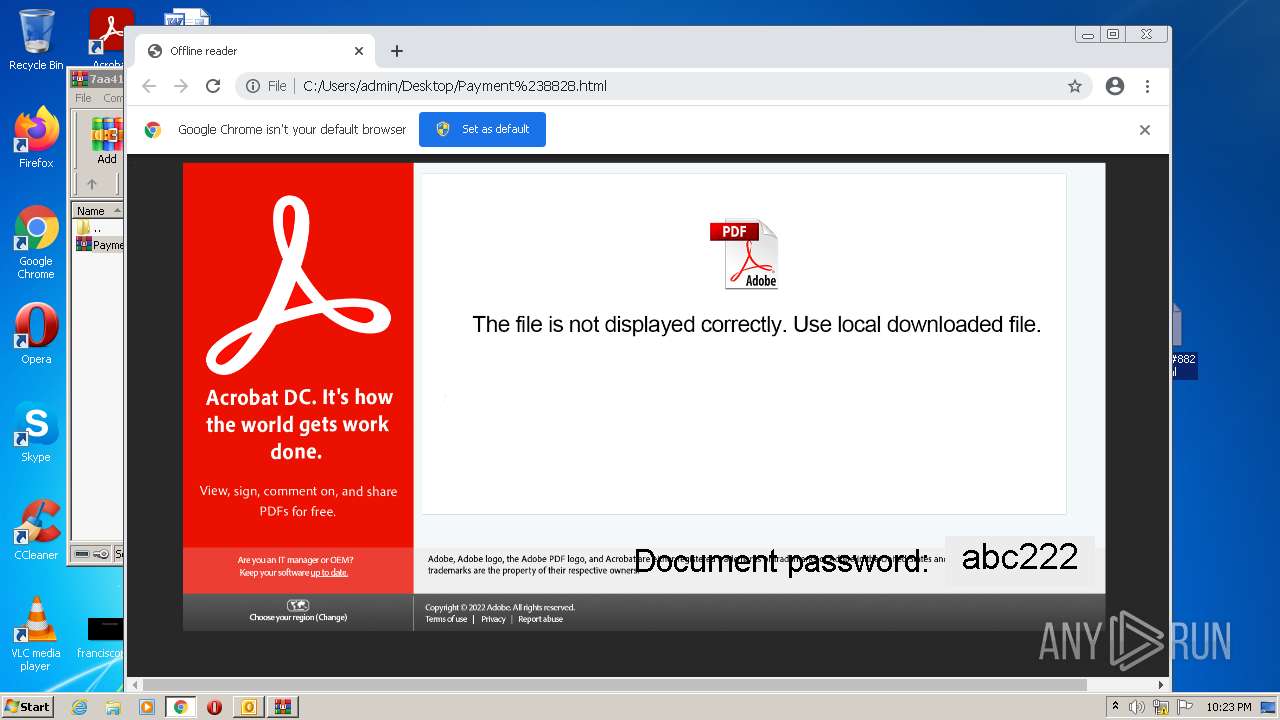
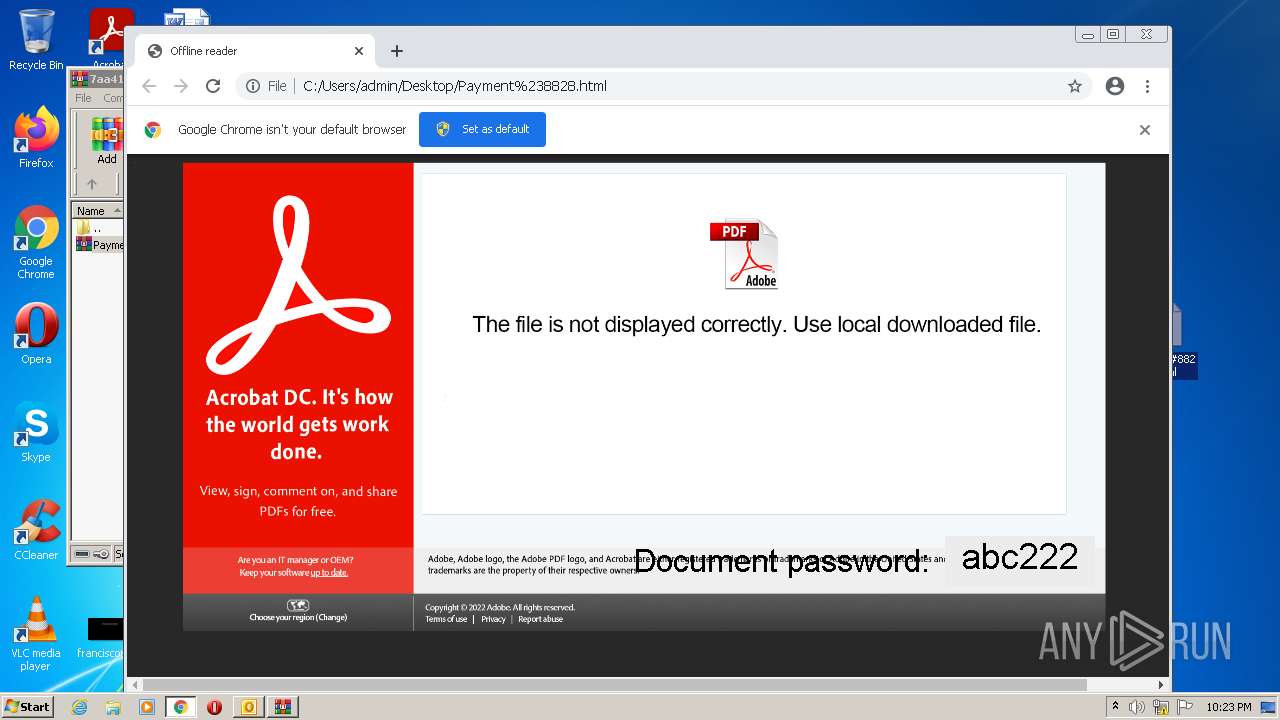
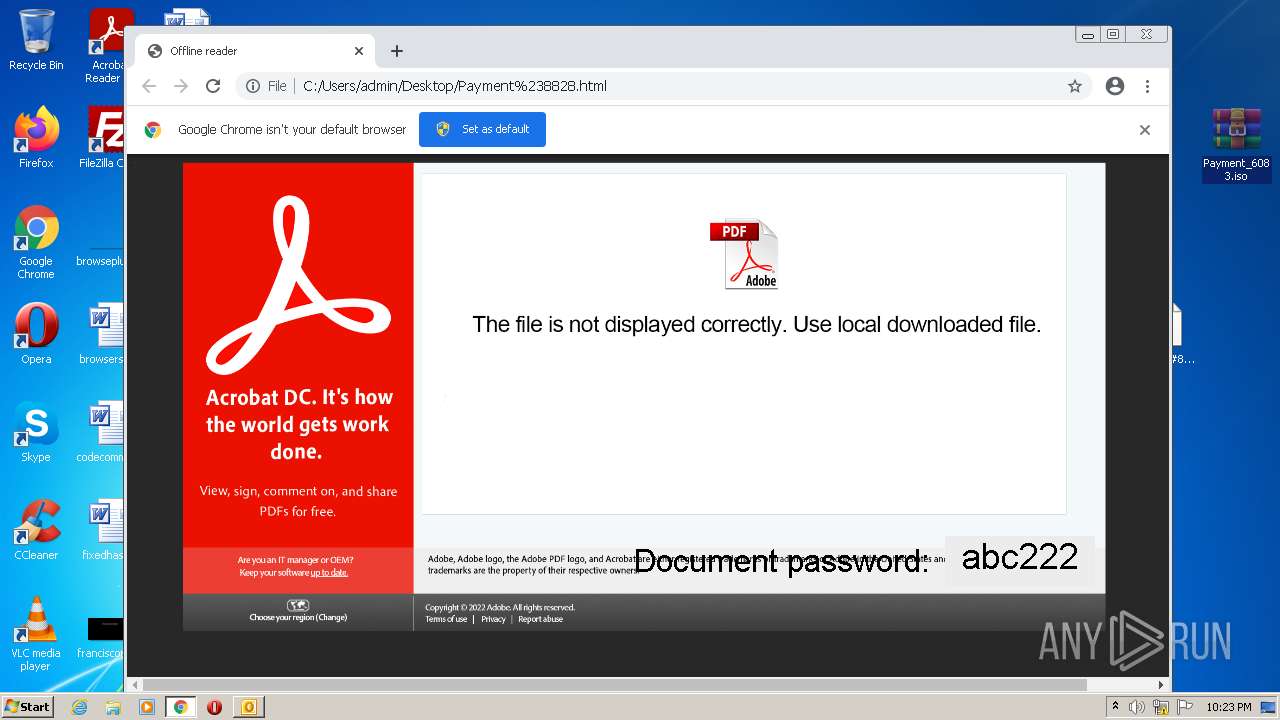
| 2964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\Z8V2299M\Payment#8828.html | html | |
MD5:— | SHA256:— | |||
| 2964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_09C4C2F1C1C2A14E9CAD5214A70F753D.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 2964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_C6A3C2A5FD3EFB43A3174D1D63A53F7D.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 2964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TCPrefs_2_120FBE90C829F74FB425FD6A4AB9490B.dat | xml | |
MD5:F194B1FA12F9B6F46A47391FAE8BEEC2 | SHA256:FCD8D7E030BE6EA7588E5C6CB568E3F1BDFC263942074B693942A27DF9521A74 | |||
| 2964 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\Z8V2299M\Payment#8828.html:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
14
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2964 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 21.1 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 5.78 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 43.6 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.90 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 7.05 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | fli | 88.6 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.90 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 178 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3596 | chrome.exe | 142.250.186.99:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3596 | chrome.exe | 142.250.186.129:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
3596 | chrome.exe | 172.217.16.206:443 | clients2.google.com | GOOGLE | US | whitelisted |
3596 | chrome.exe | 142.250.185.110:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
3596 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
3596 | chrome.exe | 142.250.186.35:443 | www.gstatic.com | GOOGLE | US | whitelisted |
3596 | chrome.exe | 142.250.186.131:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
856 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
3596 | chrome.exe | 142.250.185.202:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |