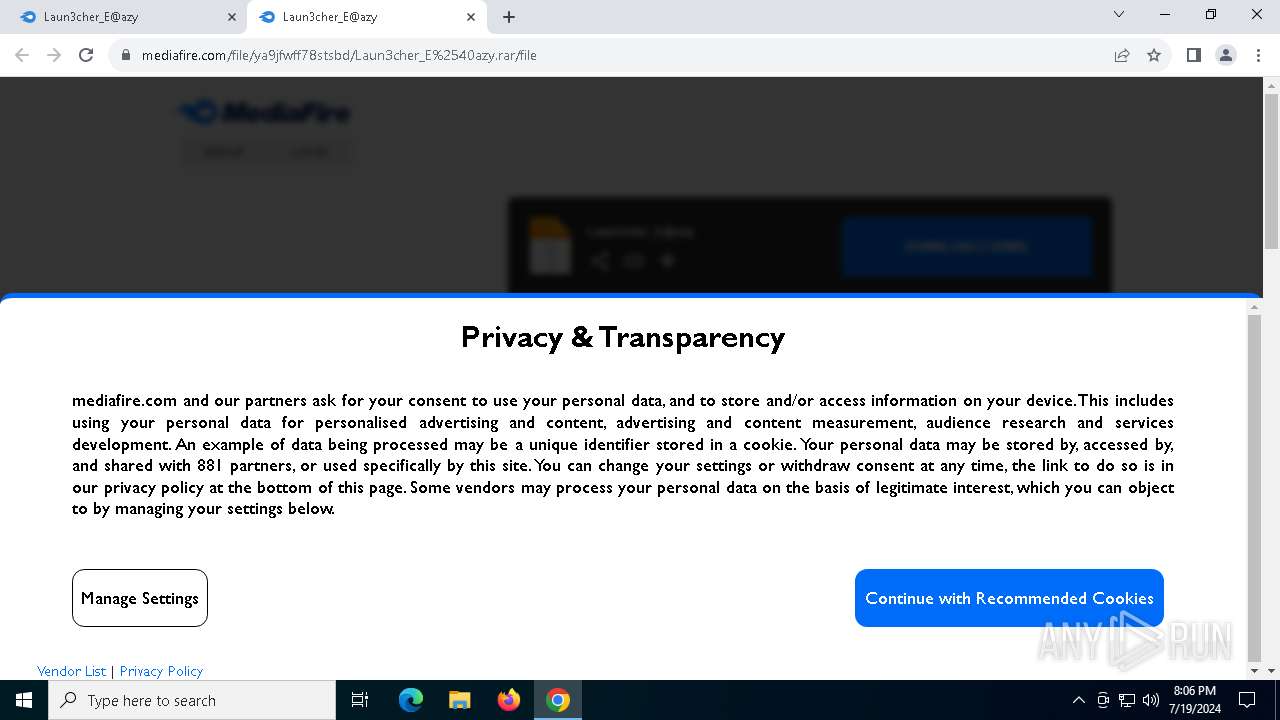
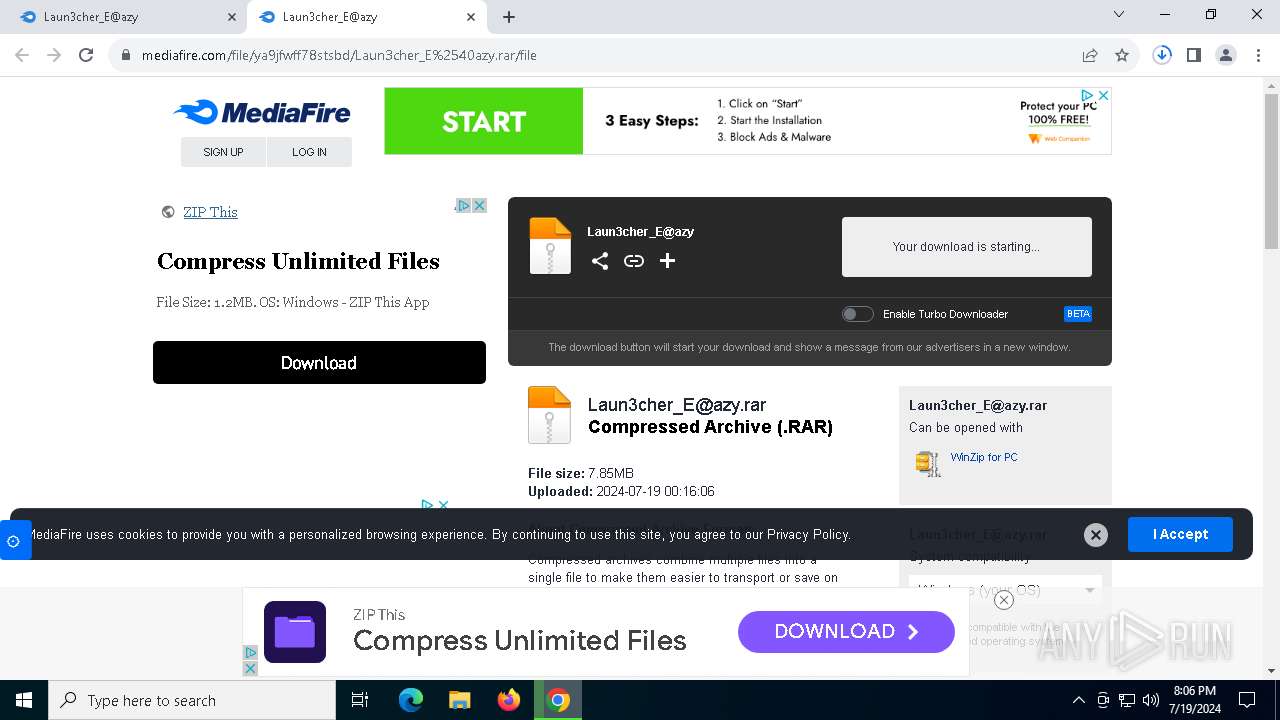
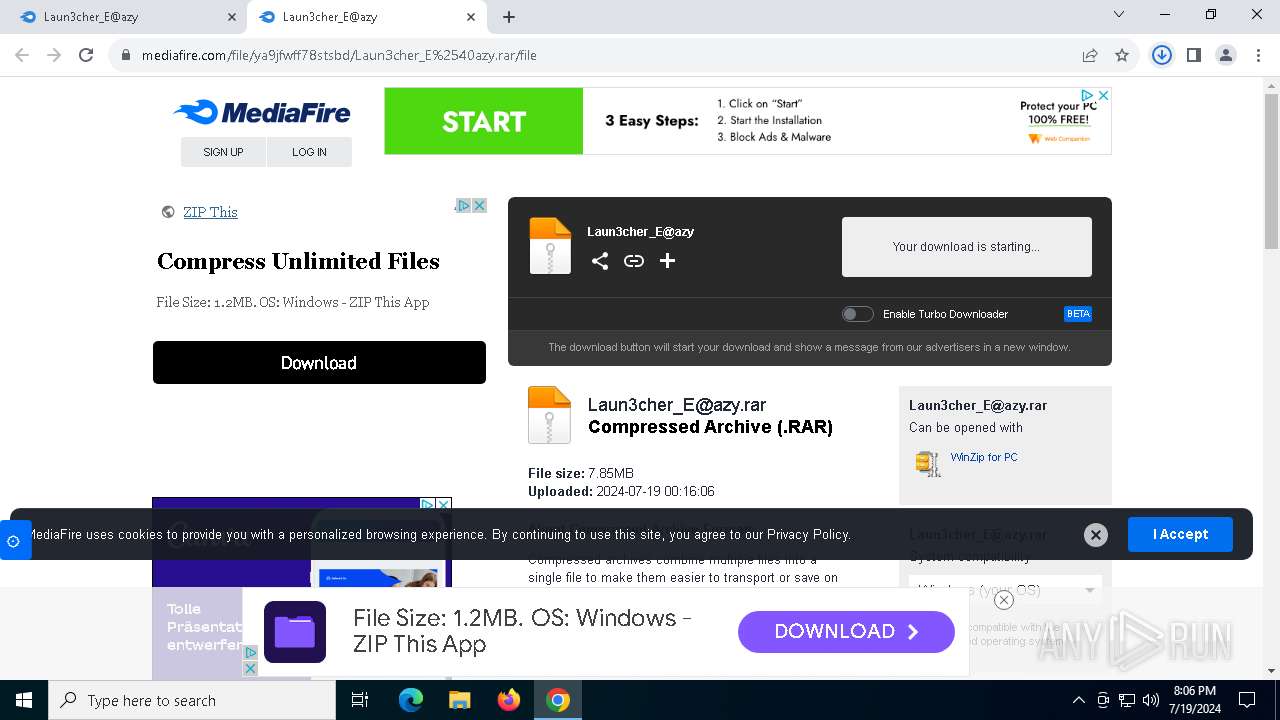
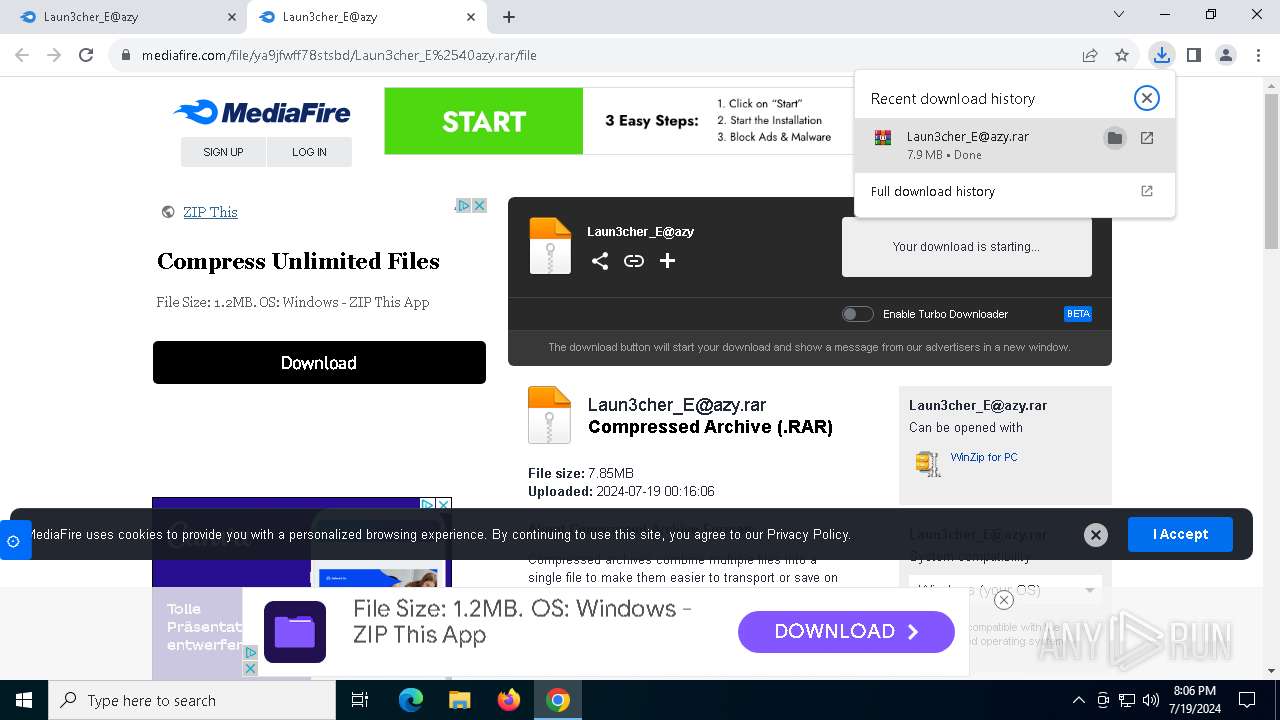
| URL: | tinyurl.com/hdzeeve8 |
| Full analysis: | https://app.any.run/tasks/27b18d82-21cd-4a75-adda-7c140ed3a65f |
| Verdict: | Malicious activity |
| Threats: | MetaStealer is an info-stealing malware primarily targeting sensitive data like login credentials, payment details, and browser history. It typically infects systems via phishing emails or malicious downloads and can exfiltrate data to a command and control (C2) server. MetaStealer is known for its stealthy techniques, including evasion and persistence mechanisms, which make it difficult to detect. This malware has been actively used in various cyberattacks, particularly for financial theft and credential harvesting from individuals and organizations. |
| Analysis date: | July 19, 2024, 20:06:08 |
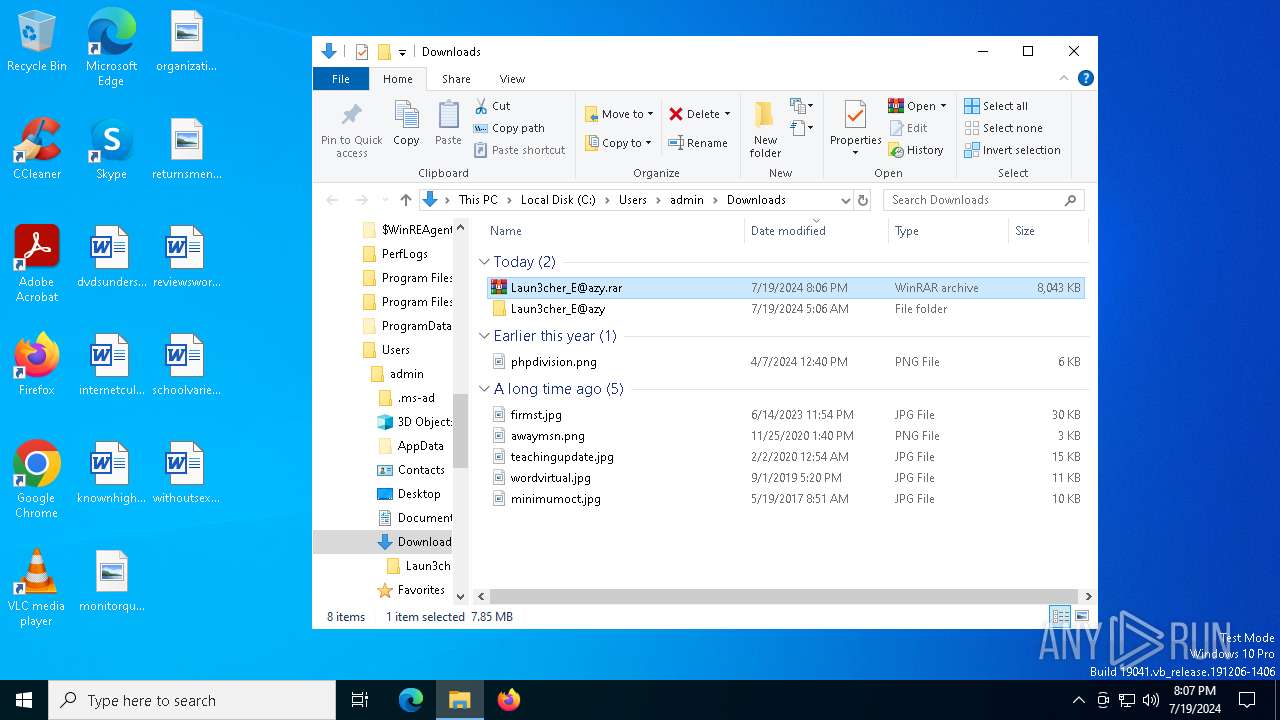
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1F49504827DEAECF76C405ED02504714 |
| SHA1: | 6F37E717671F99F734A64906805E8D12F4D563A1 |
| SHA256: | 911C6447AC2F8E5B7578B46509726B13A4BC210CB8ABD74C2915E70BD75AD878 |
| SSDEEP: | 3:ULdIWBmd:SdG |
MALICIOUS
Stealers network behavior
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
METASTEALER has been detected (SURICATA)
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
REDLINE has been detected (YARA)
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
REDLINE has been detected (SURICATA)
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Connects to the CnC server
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Steals credentials from Web Browsers
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Actions looks like stealing of personal data
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3024)
Reads the BIOS version
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Connects to unusual port
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Searches for installed software
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
INFO
The process uses the downloaded file
- chrome.exe (PID: 8108)
- WinRAR.exe (PID: 3024)
Reads Microsoft Office registry keys
- chrome.exe (PID: 5320)
Checks supported languages
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
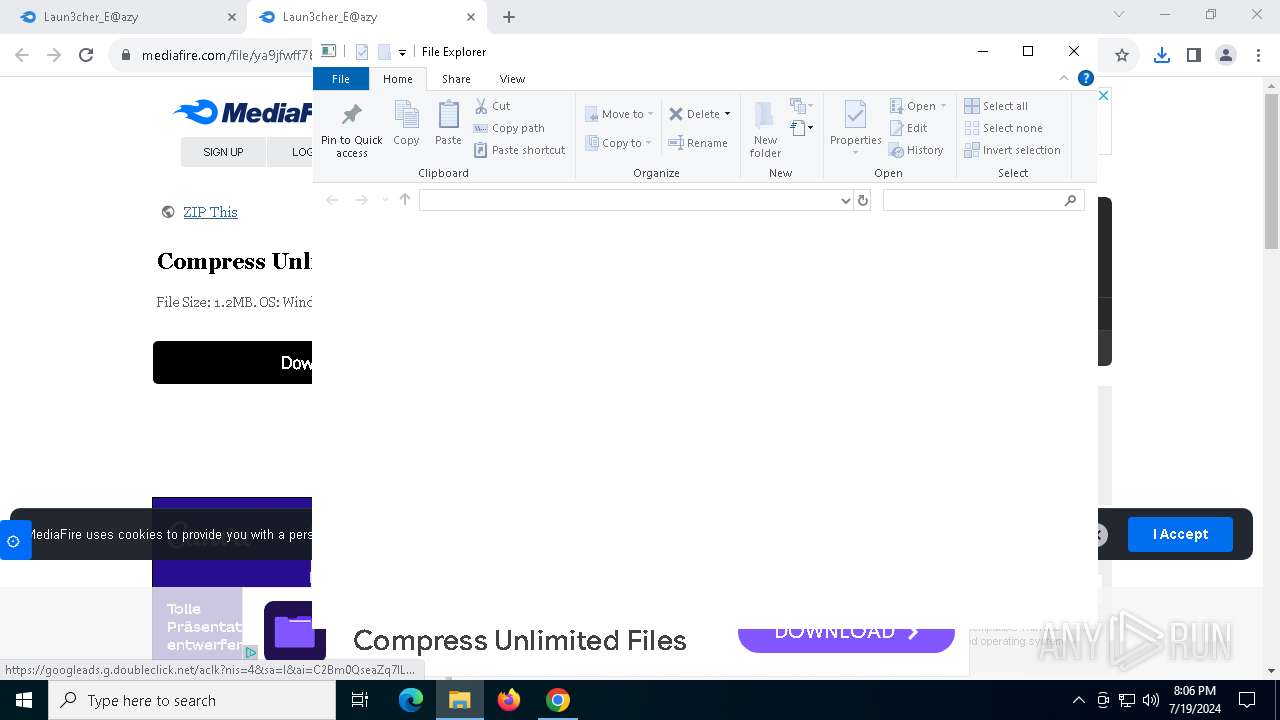
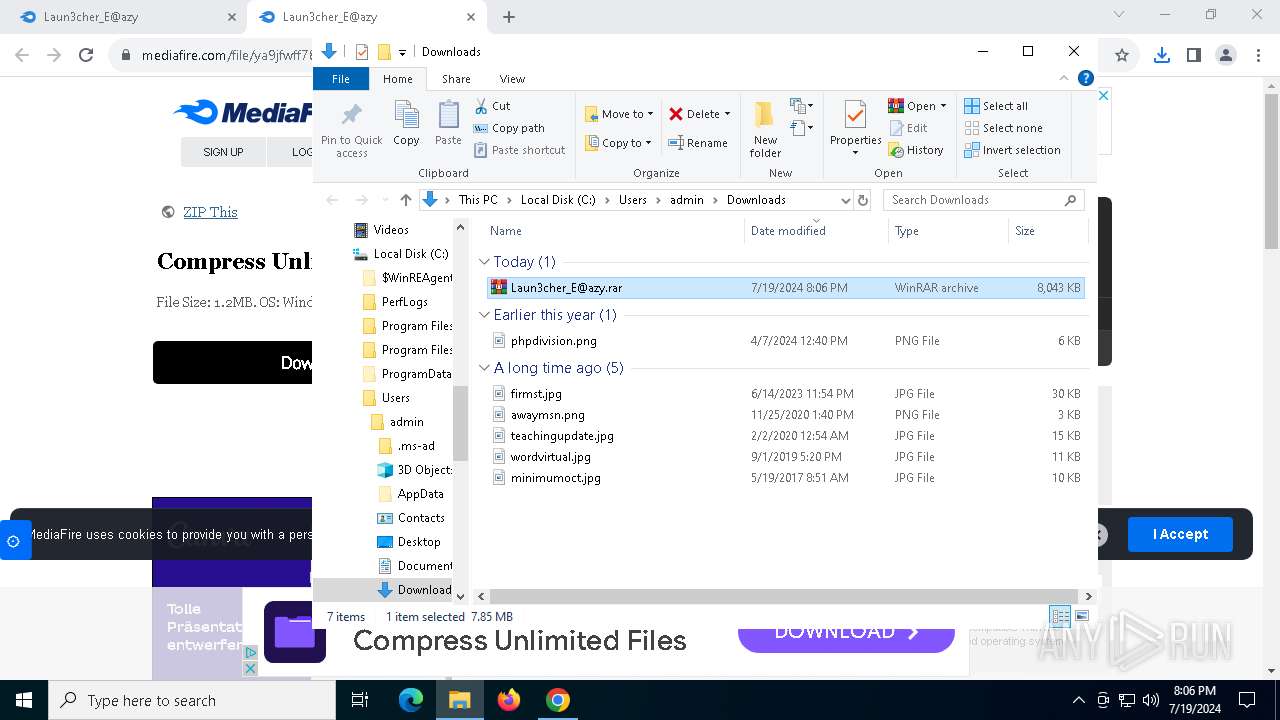
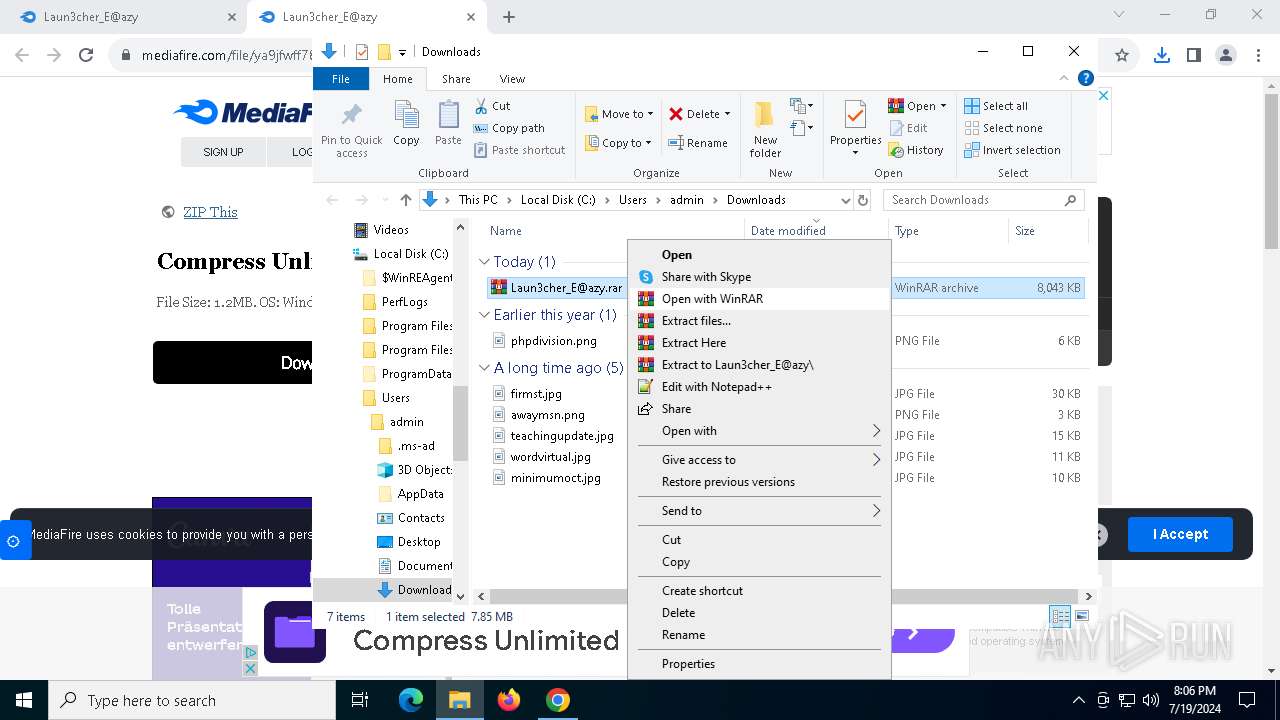
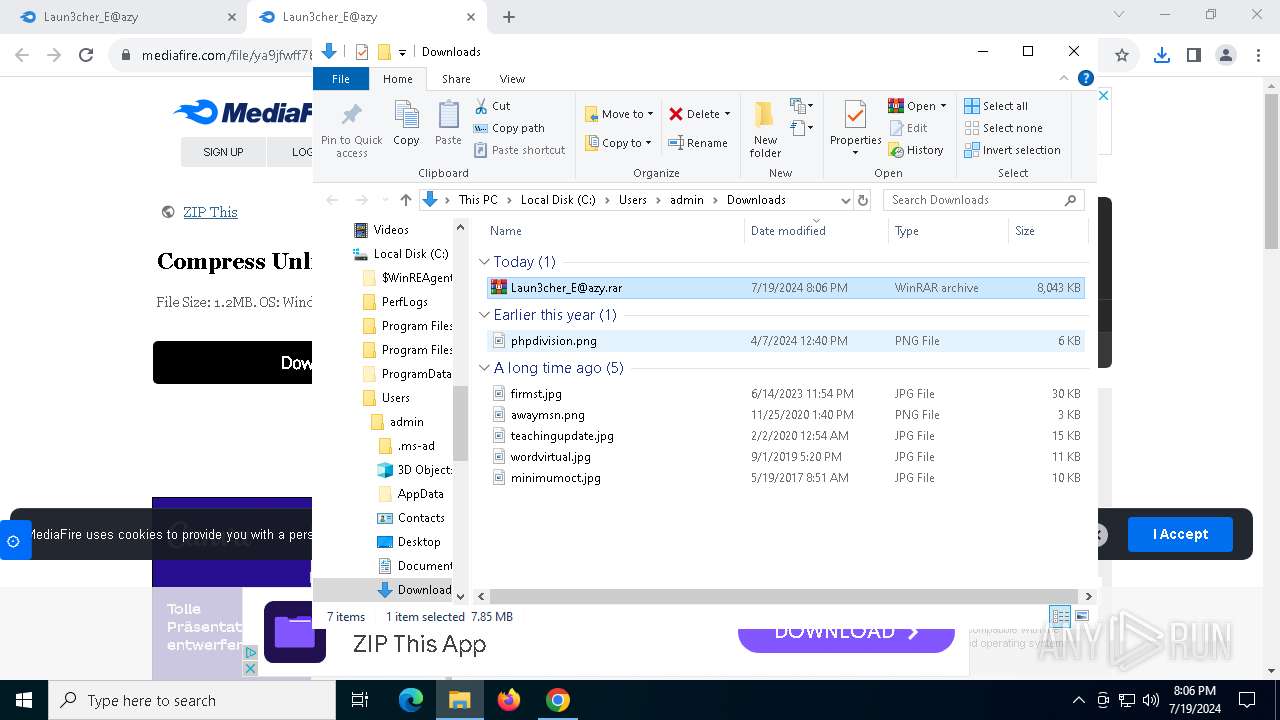
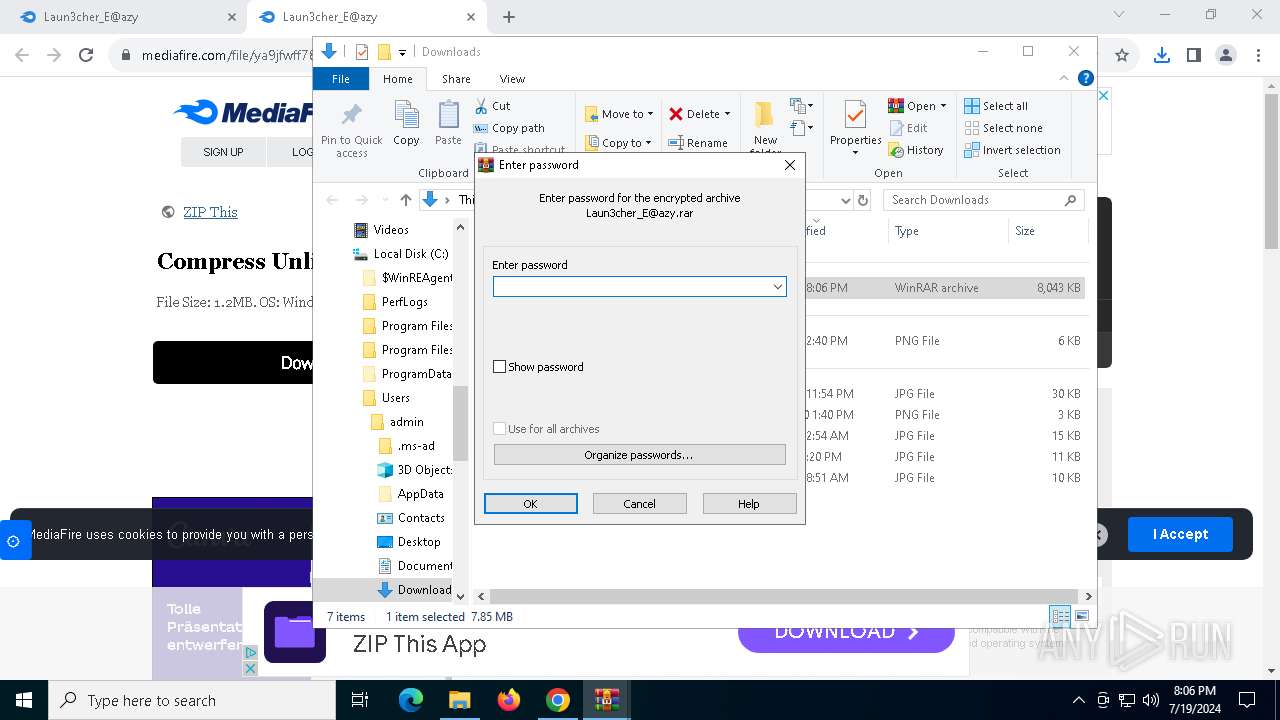
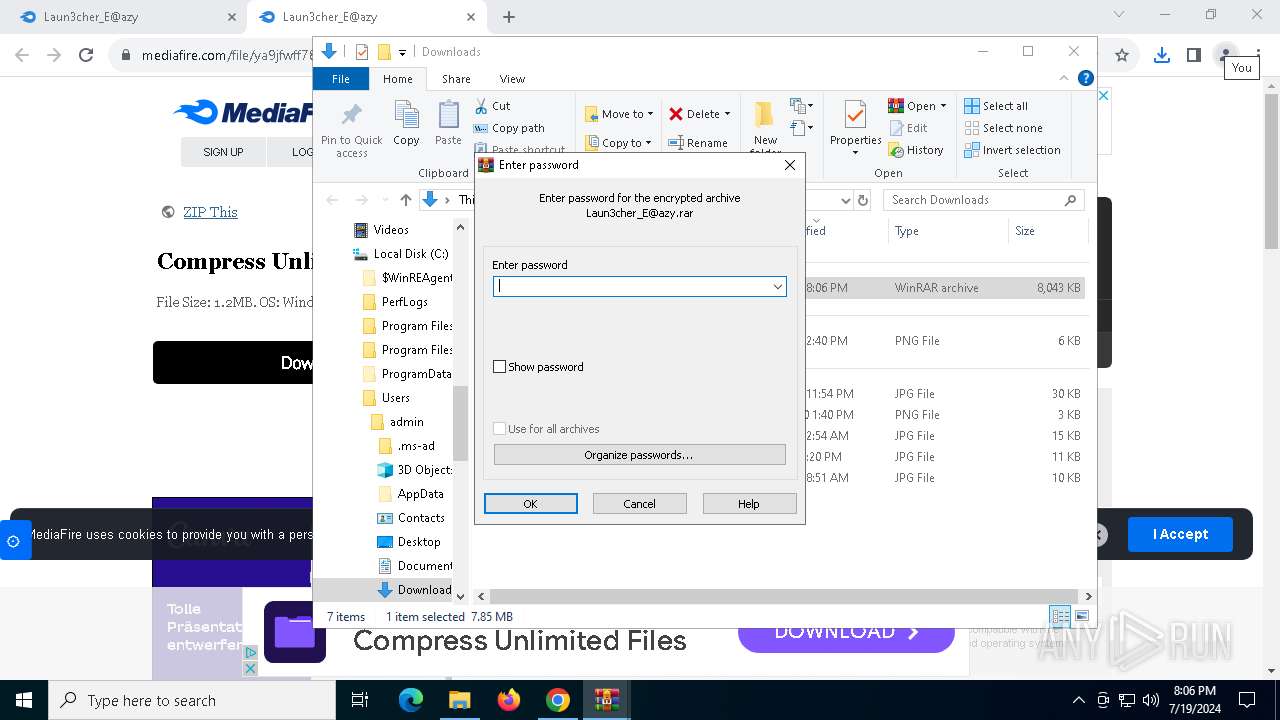
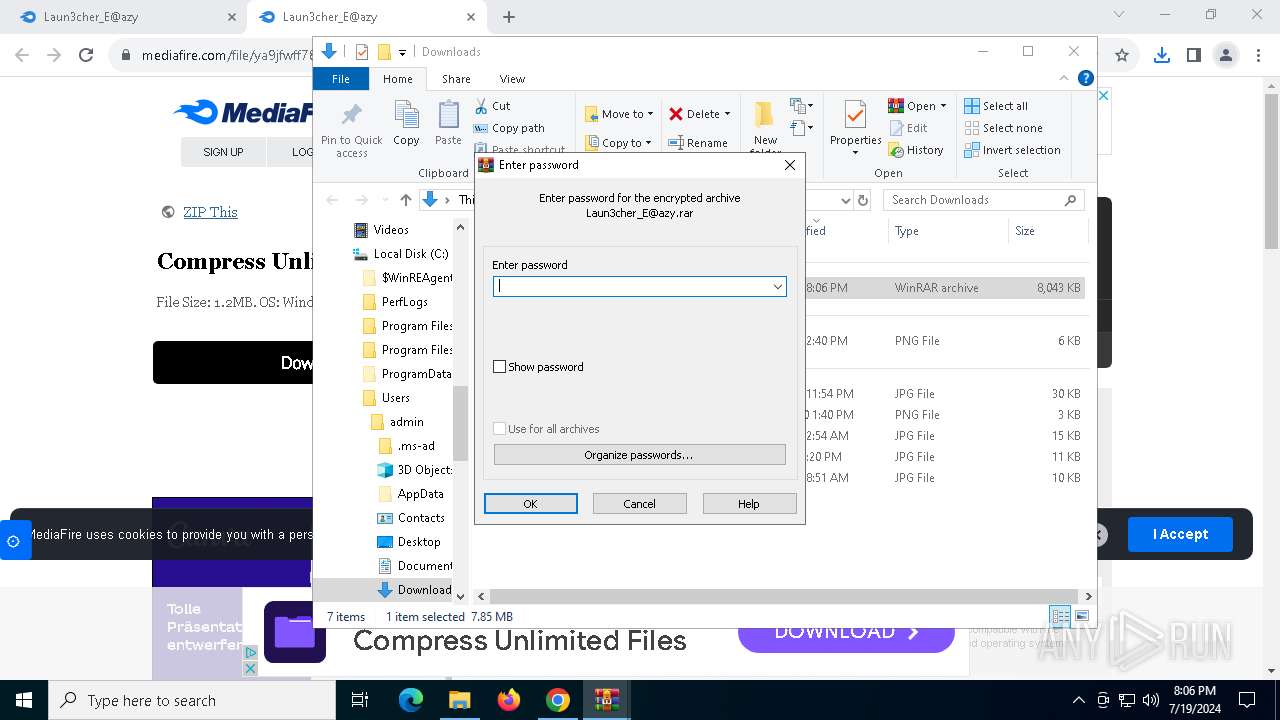
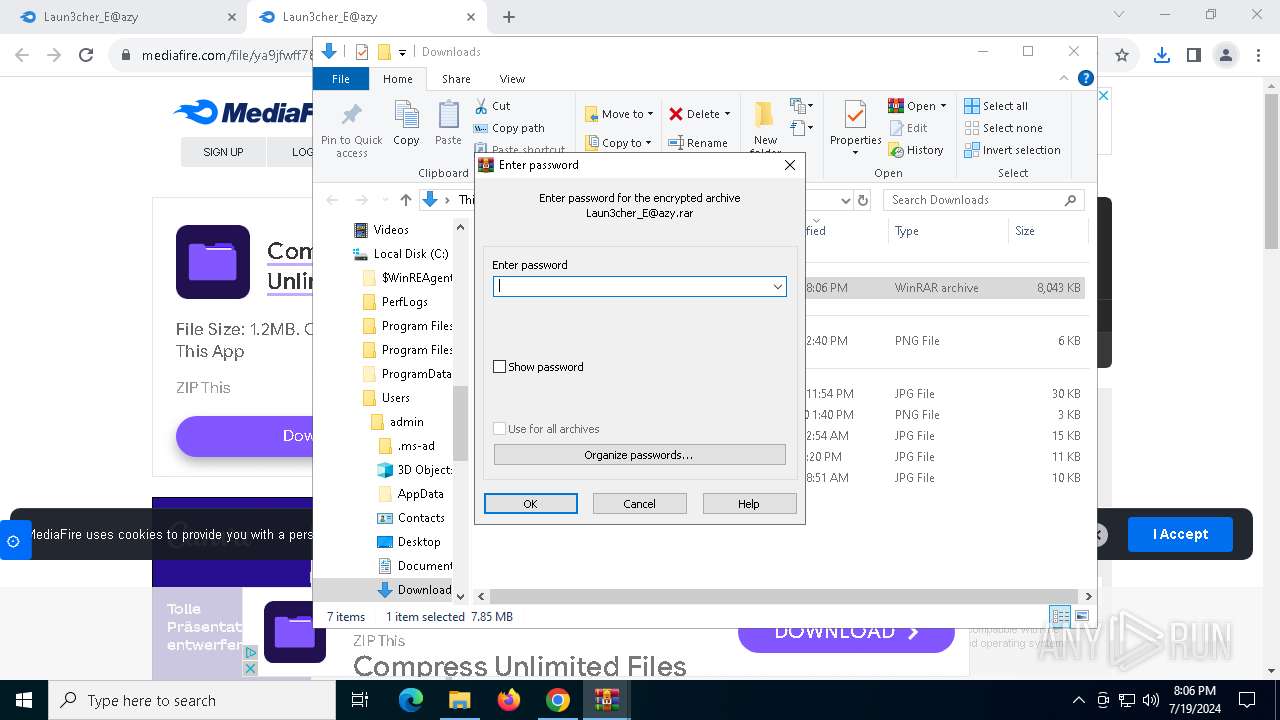
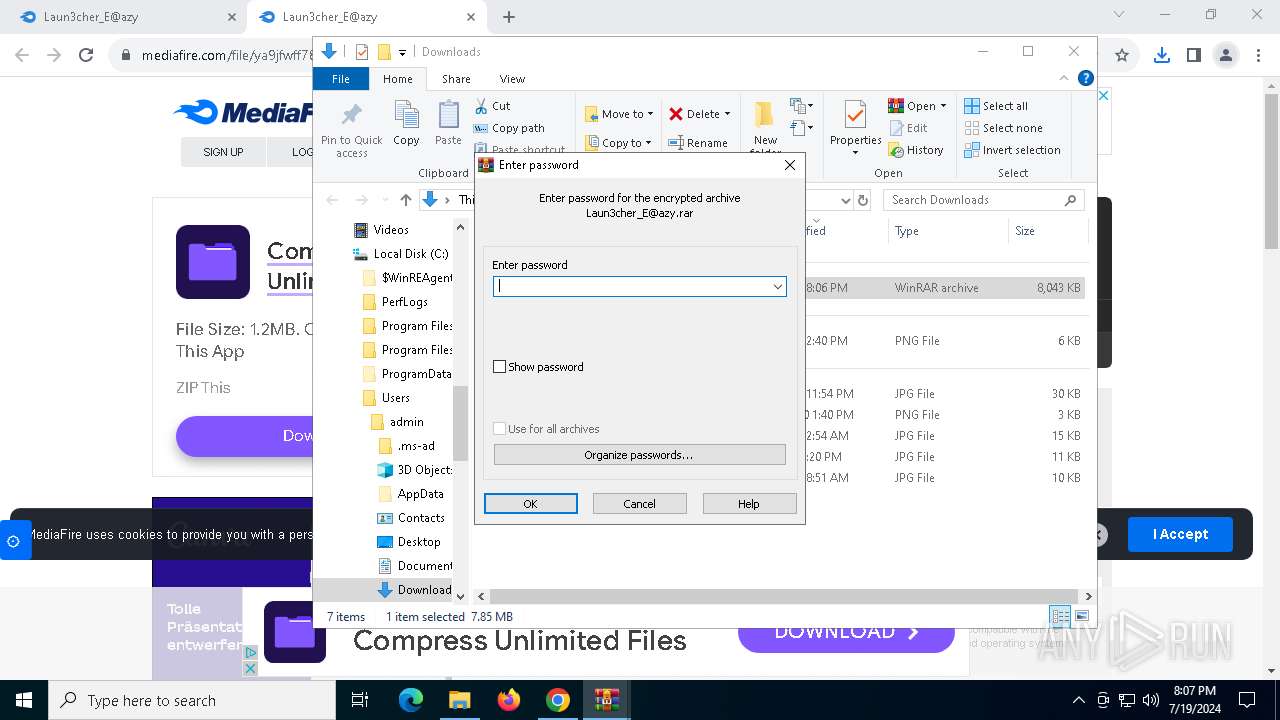
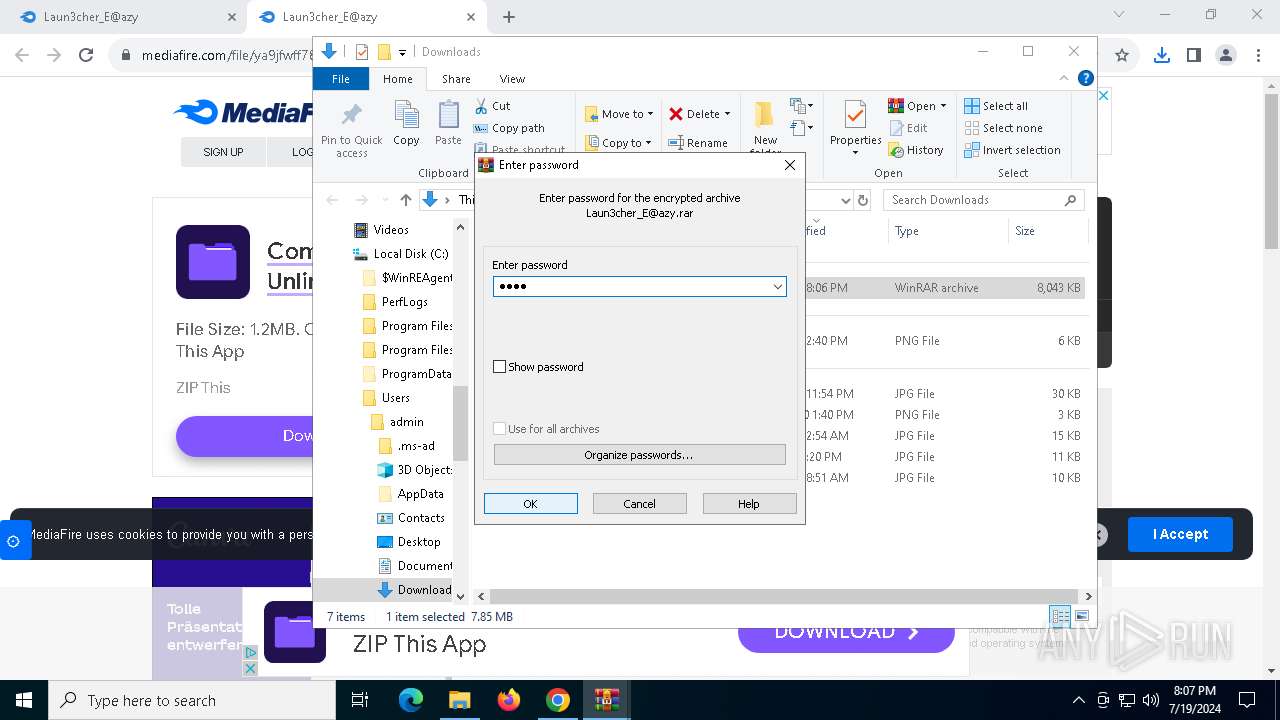
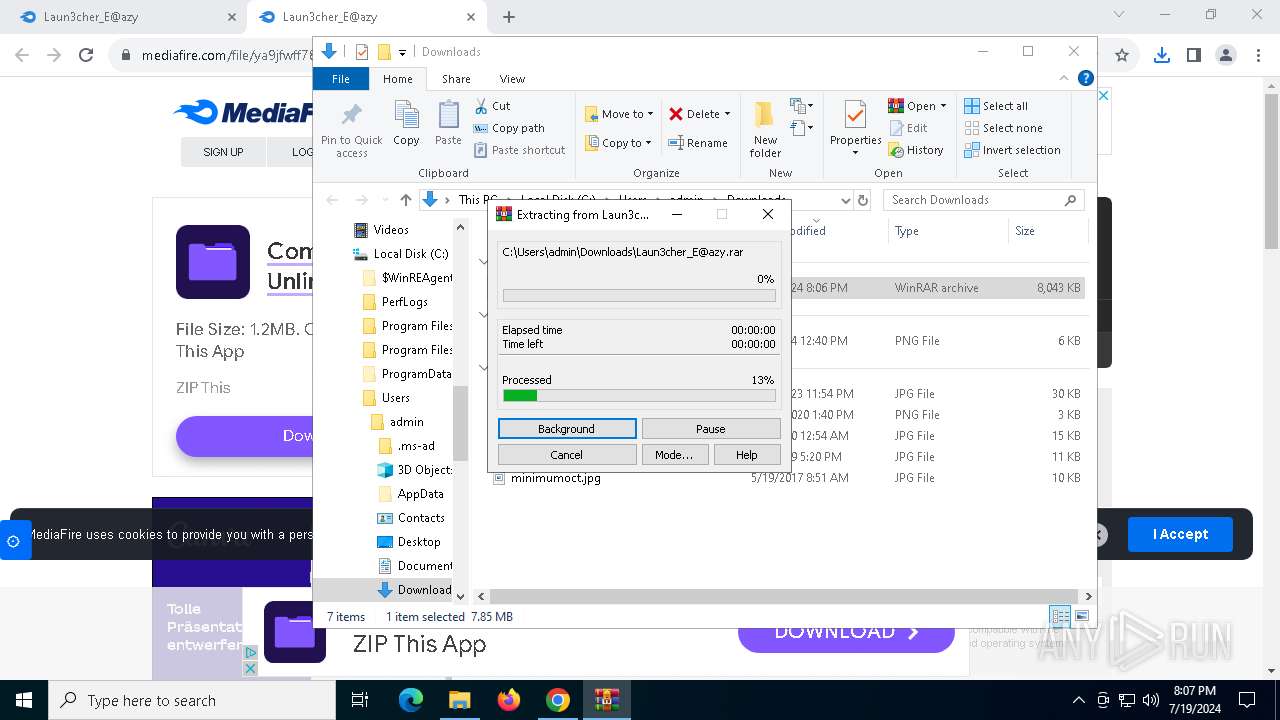
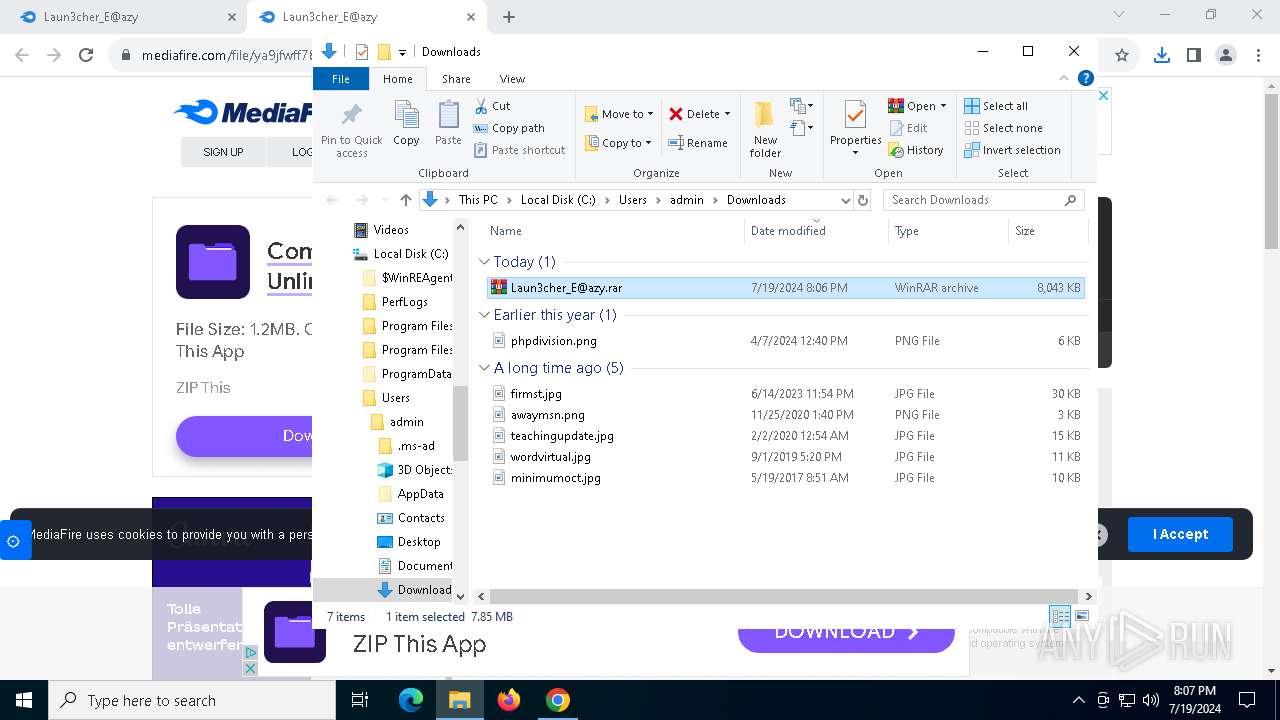
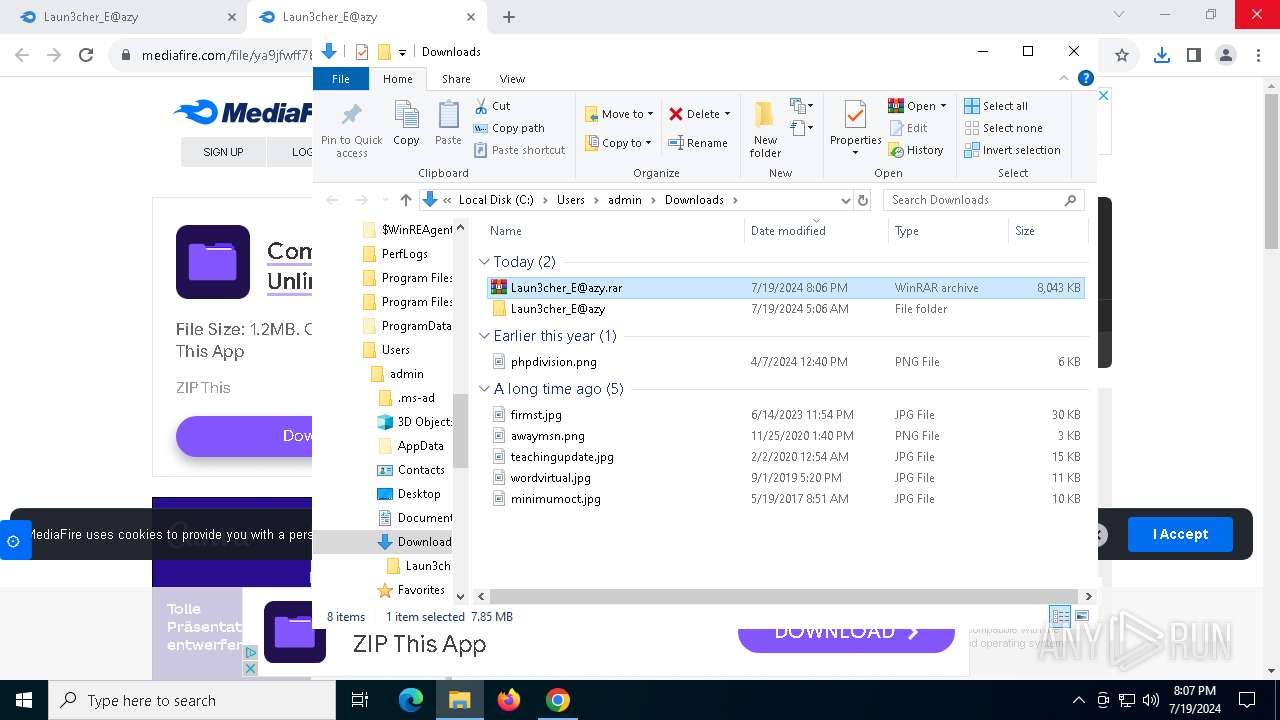
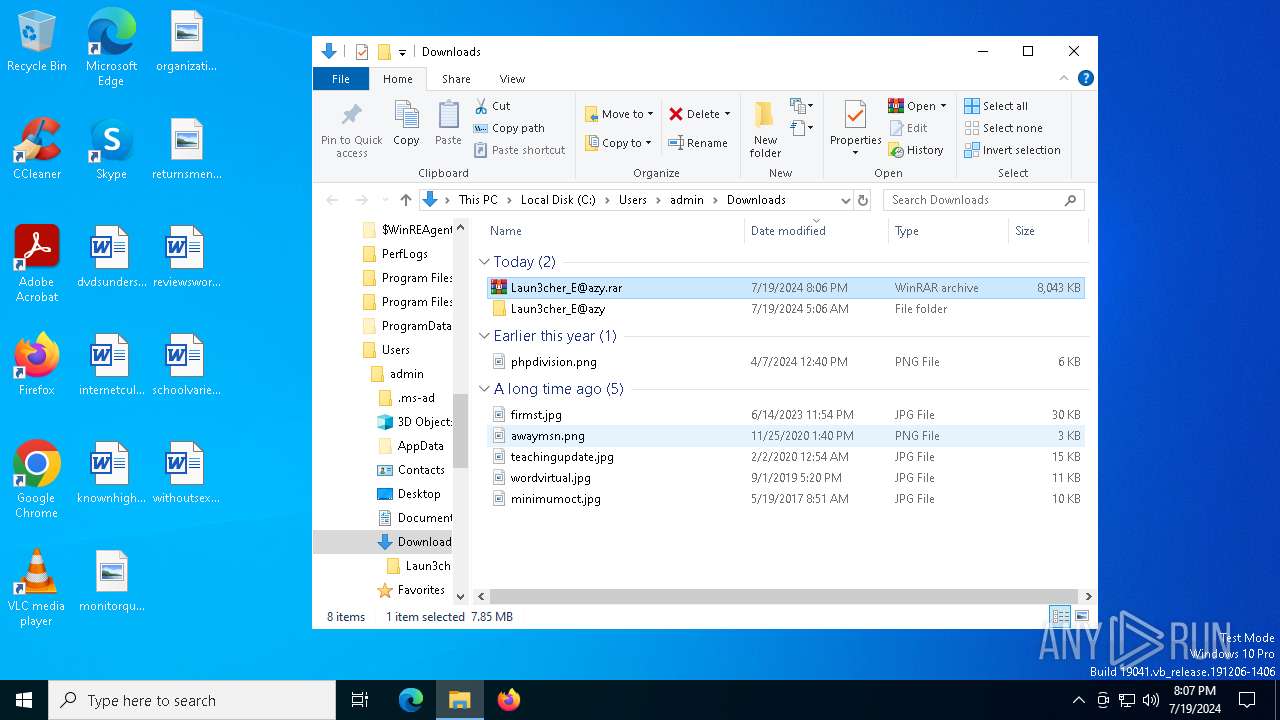
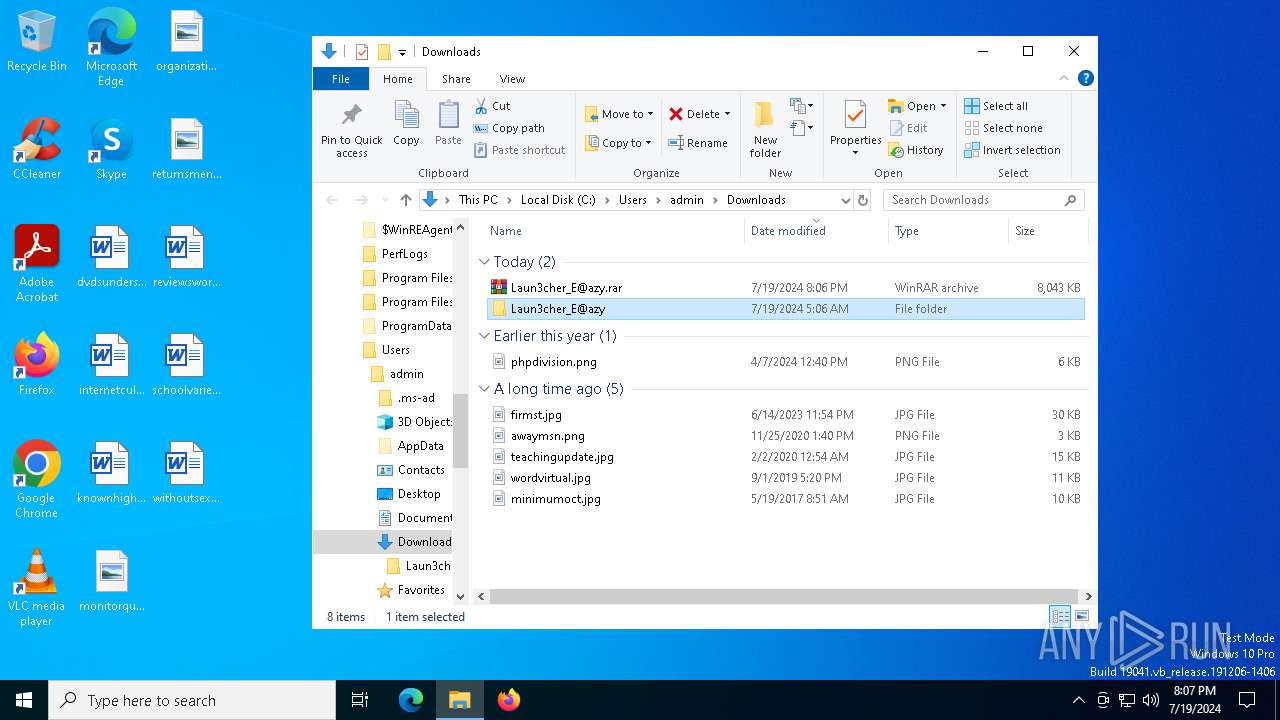
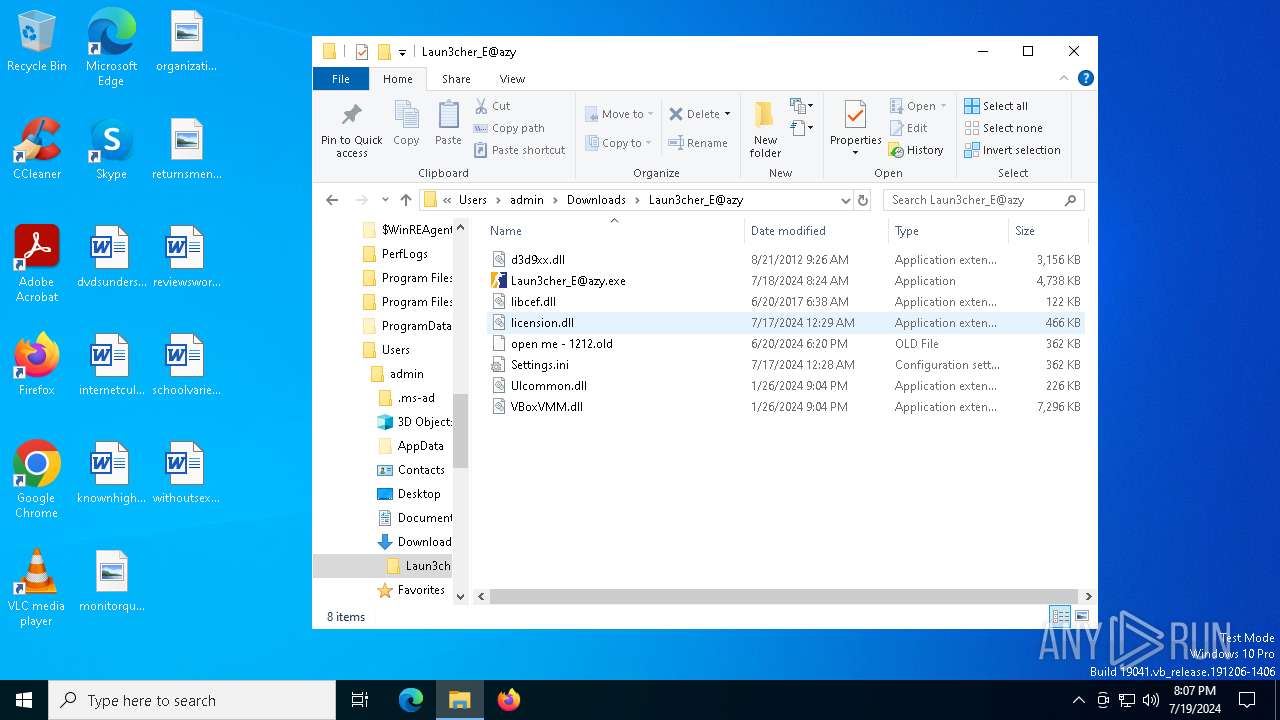
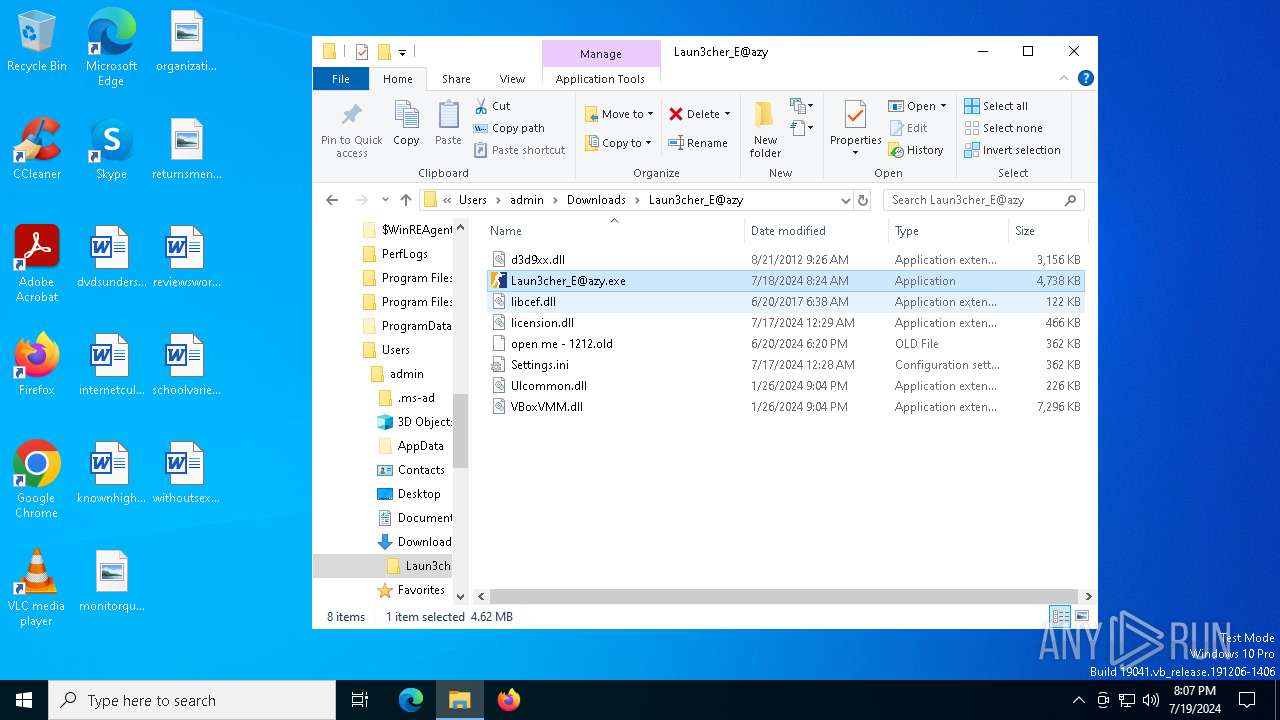
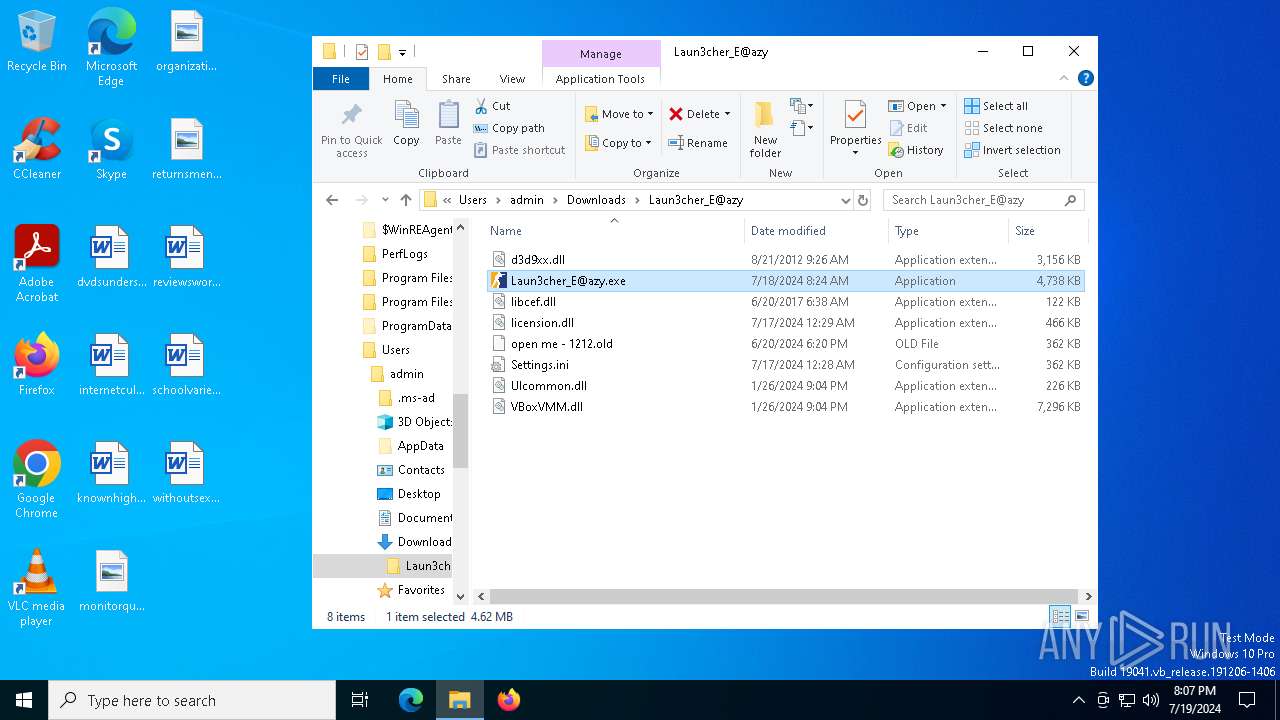
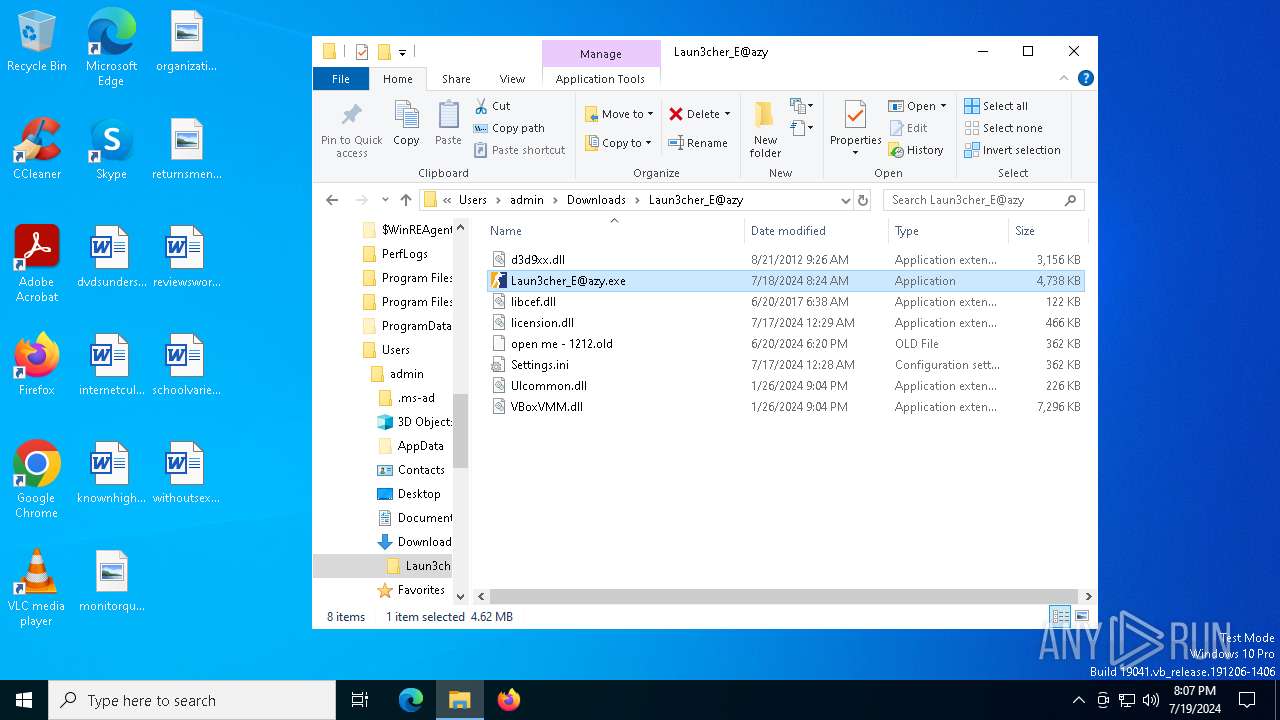
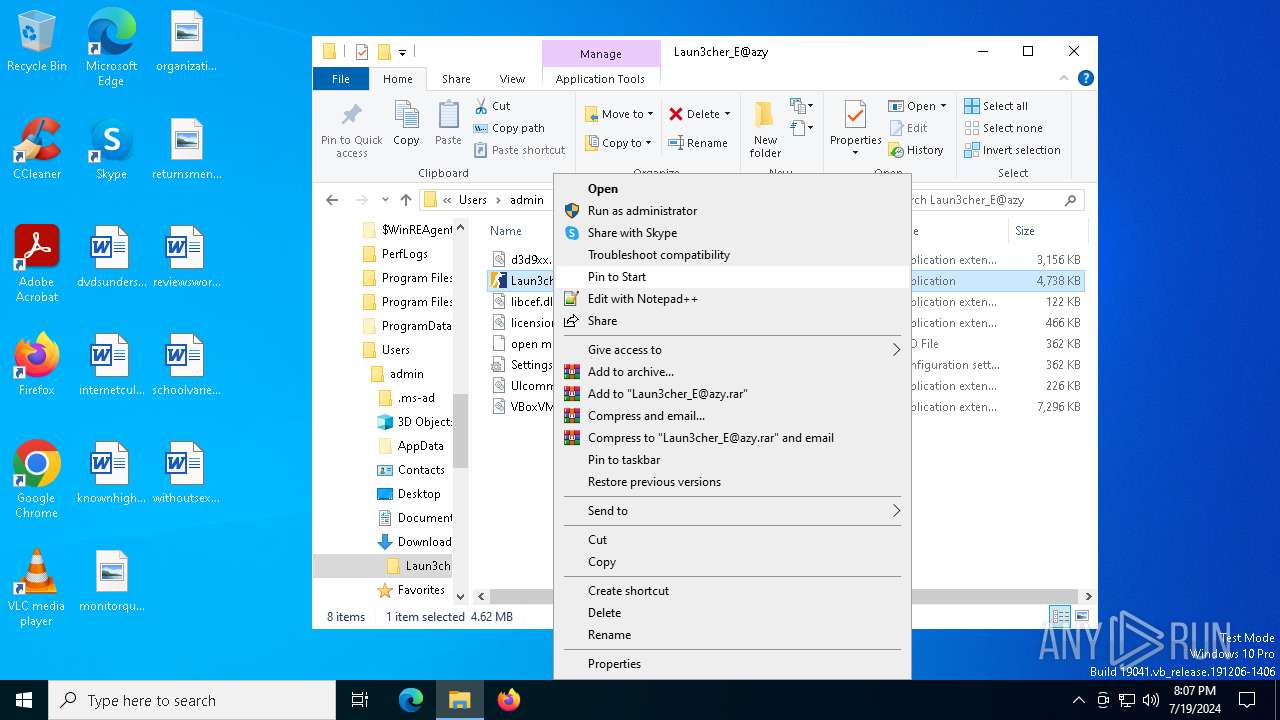
Manual execution by a user
- WinRAR.exe (PID: 3024)
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3024)
Reads the machine GUID from the registry
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3024)
Reads the computer name
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Application launched itself
- chrome.exe (PID: 5320)
Themida protector has been detected
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Reads Environment values
- Laun3cher_E@azy.exe (PID: 5272)
- Laun3cher_E@azy.exe (PID: 4364)
Process checks whether UAC notifications are on
- Laun3cher_E@azy.exe (PID: 4364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(5272) Laun3cher_E@azy.exe
C2 (1)77.105.164.59:20204
Botnetshabila
Options
ErrorMessage
Keys
XorGristly
(PID) Process(4364) Laun3cher_E@azy.exe
C2 (1)77.105.164.59:20204
Botnetshabila
Options
ErrorMessage
Keys
XorGristly
Total processes
165
Monitored processes
25
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --mojo-platform-channel-handle=5580 --field-trial-handle=2020,i,8402636119247424811,16323977782590140198,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4300 --field-trial-handle=2020,i,8402636119247424811,16323977782590140198,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=4812 --field-trial-handle=2020,i,8402636119247424811,16323977782590140198,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2980 --field-trial-handle=2020,i,8402636119247424811,16323977782590140198,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2968 --field-trial-handle=2020,i,8402636119247424811,16323977782590140198,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
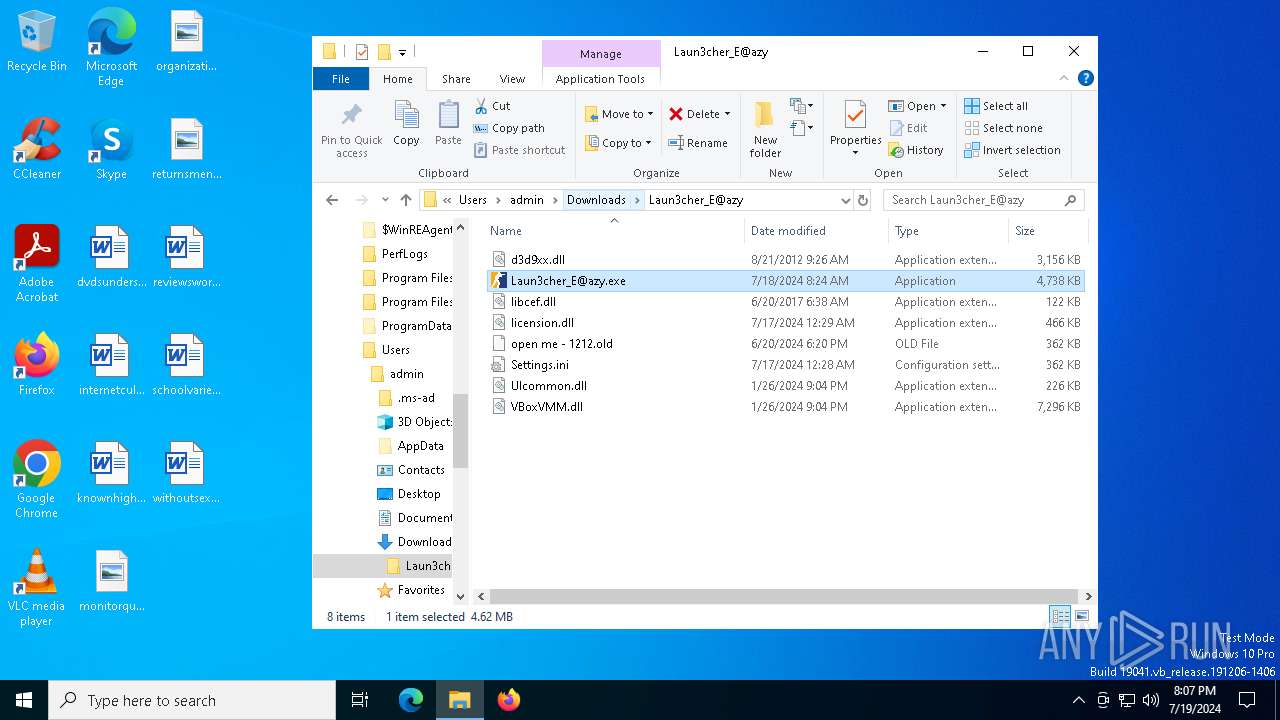
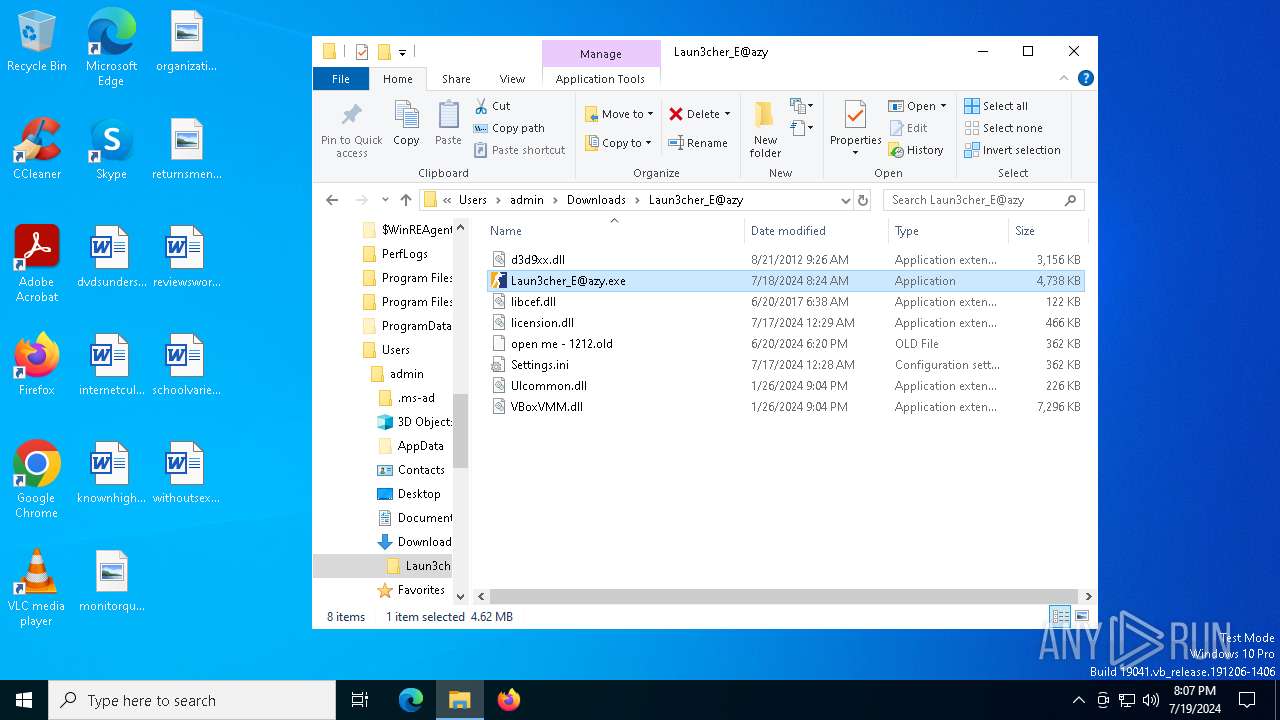
| 3024 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Laun3cher_E@azy.rar" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2372 --field-trial-handle=2020,i,8402636119247424811,16323977782590140198,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=5100 --field-trial-handle=2020,i,8402636119247424811,16323977782590140198,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4364 | "C:\Users\admin\Downloads\Laun3cher_E@azy\Laun3cher_E@azy.exe" | C:\Users\admin\Downloads\Laun3cher_E@azy\Laun3cher_E@azy.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: XHP Exit code: 0 Version: 12.9.1.22 Modules
RedLine(PID) Process(4364) Laun3cher_E@azy.exe C2 (1)77.105.164.59:20204 Botnetshabila Options ErrorMessage Keys XorGristly | |||||||||||||||
Total events
12 520
Read events
12 471
Write events
48
Delete events
1
Modification events
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5320) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
8
Suspicious files
57
Text files
29
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF42a835.TMP | — | |
MD5:— | SHA256:— | |||
| 5320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF42a835.TMP | — | |
MD5:— | SHA256:— | |||
| 5320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5320 | chrome.exe | C:\USERS\ADMIN\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\CRASHPAD\SETTINGS.DAT | binary | |
MD5:FC81892AC822DCBB09441D3B58B47125 | SHA256:FB077C966296D02D50CCBF7F761D2A3311A206A784A7496F331C2B0D6AD205C8 | |||
| 5320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:723783C35EAEEE1492EDB30847AE6750 | SHA256:C29323F784CF873BF34992E7A2B4630B19641BF42980109E31D5AF2D487DF6F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
170
DNS requests
227
Threats
66
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 4.209.32.198:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5320 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6940 | chrome.exe | 74.125.128.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6940 | chrome.exe | 104.17.112.233:443 | tinyurl.com | CLOUDFLARENET | — | unknown |
2760 | svchost.exe | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
tinyurl.com |
| shared |
accounts.google.com |
| whitelisted |
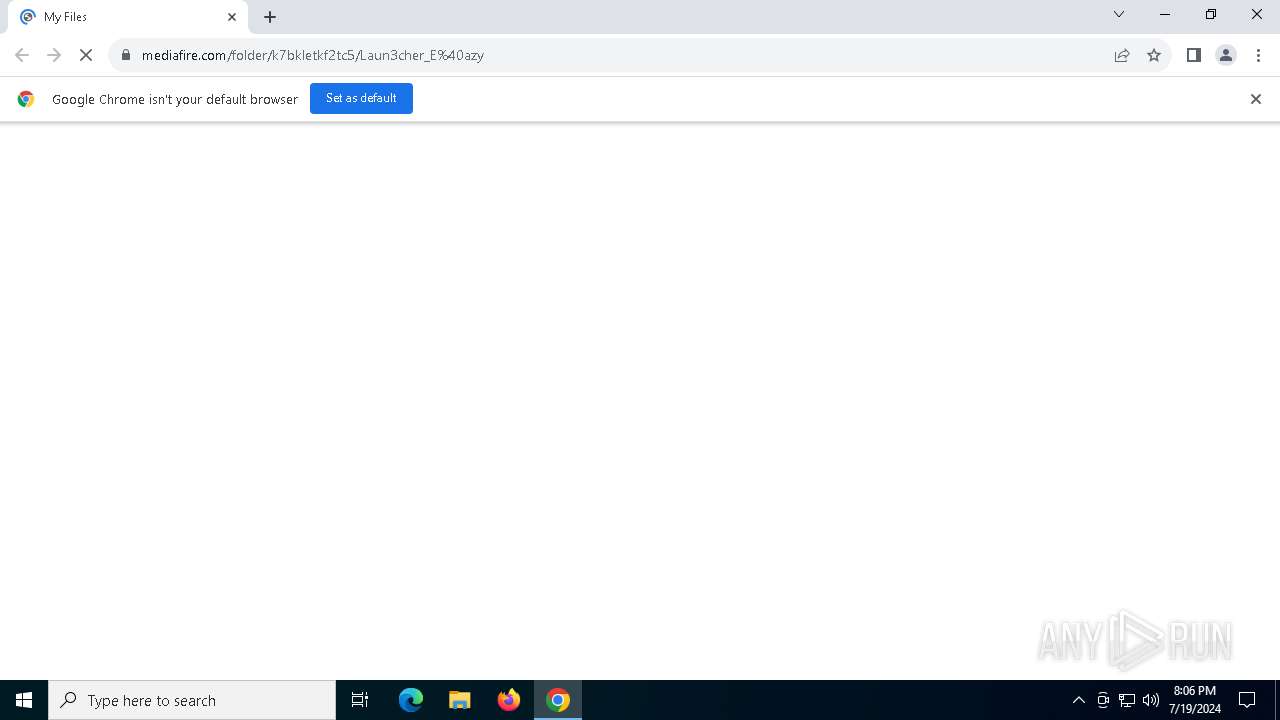
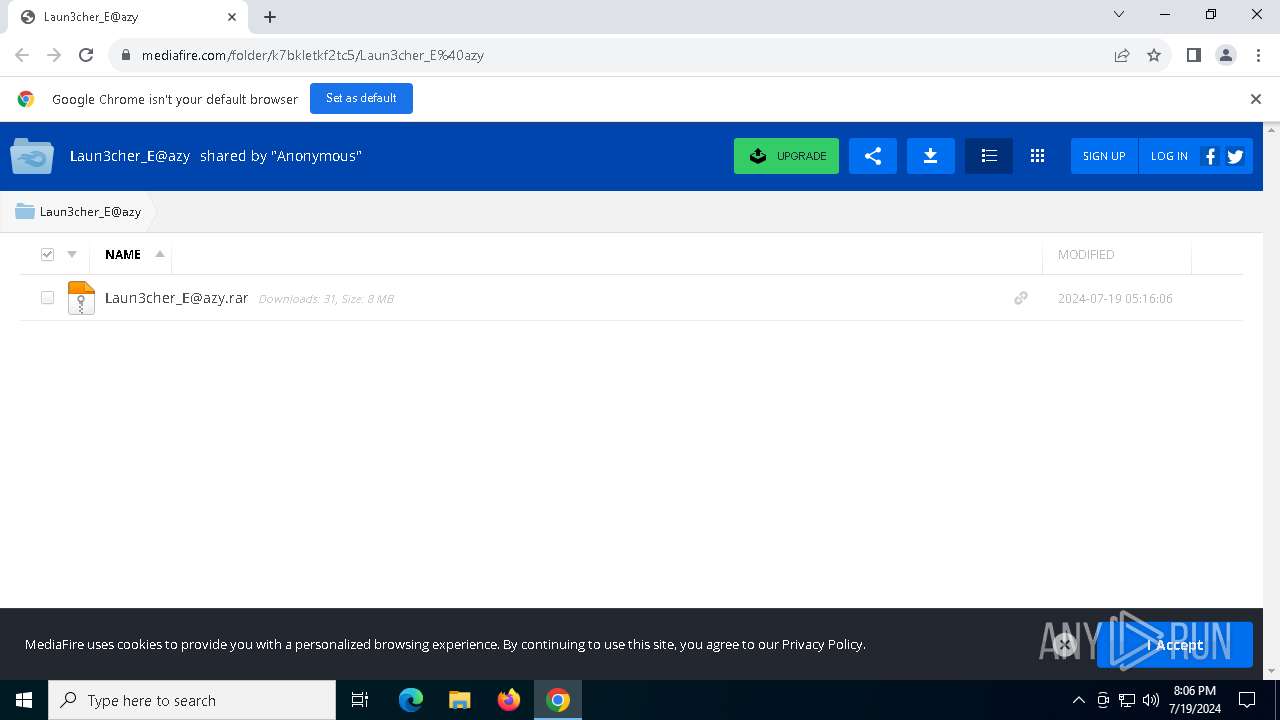
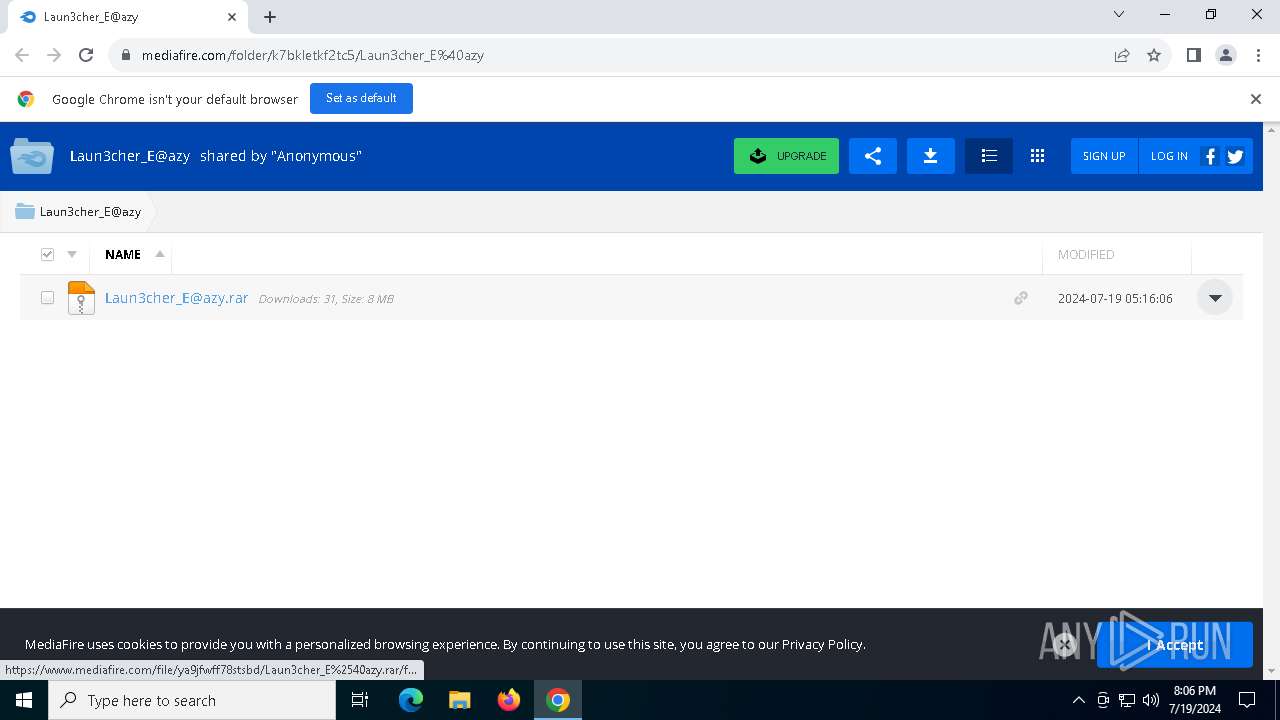
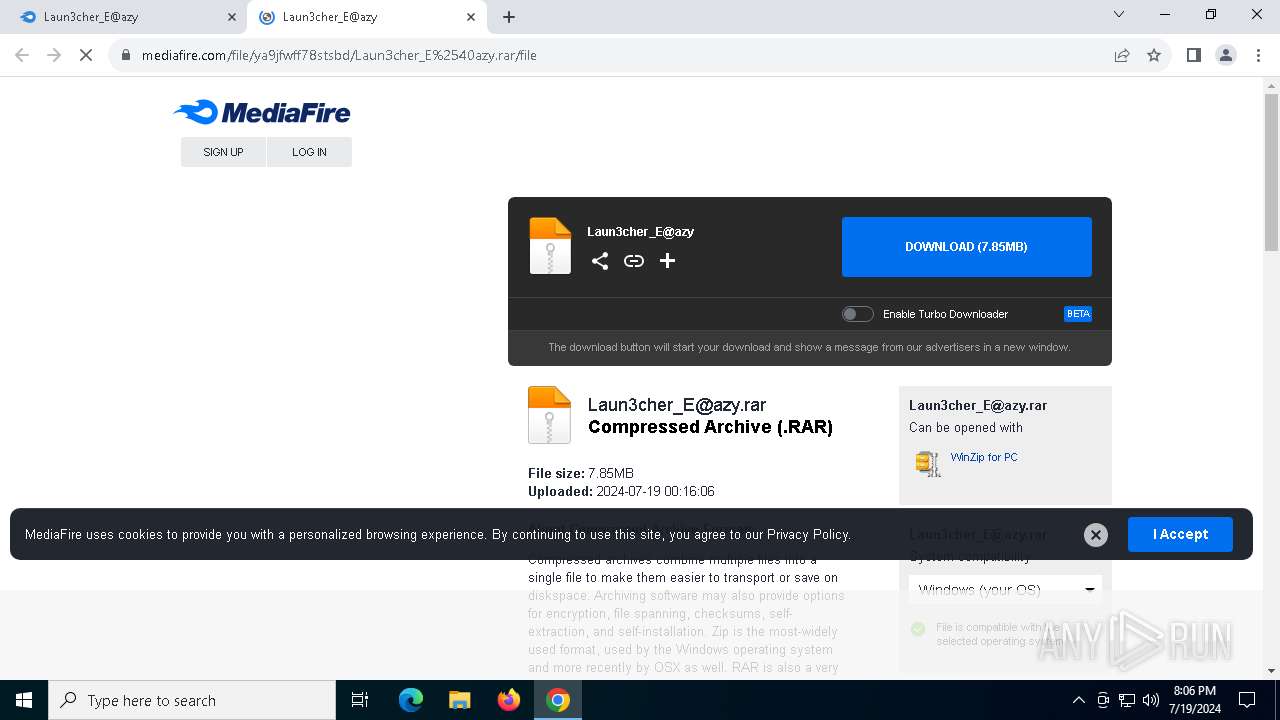
www.mediafire.com |
| shared |
static.mediafire.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6940 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6940 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6940 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6940 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6940 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
5272 | Laun3cher_E@azy.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
5272 | Laun3cher_E@azy.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
5272 | Laun3cher_E@azy.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer/MetaStealer Family Related (MC-NMF Authorization) |
5272 | Laun3cher_E@azy.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
5272 | Laun3cher_E@azy.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |