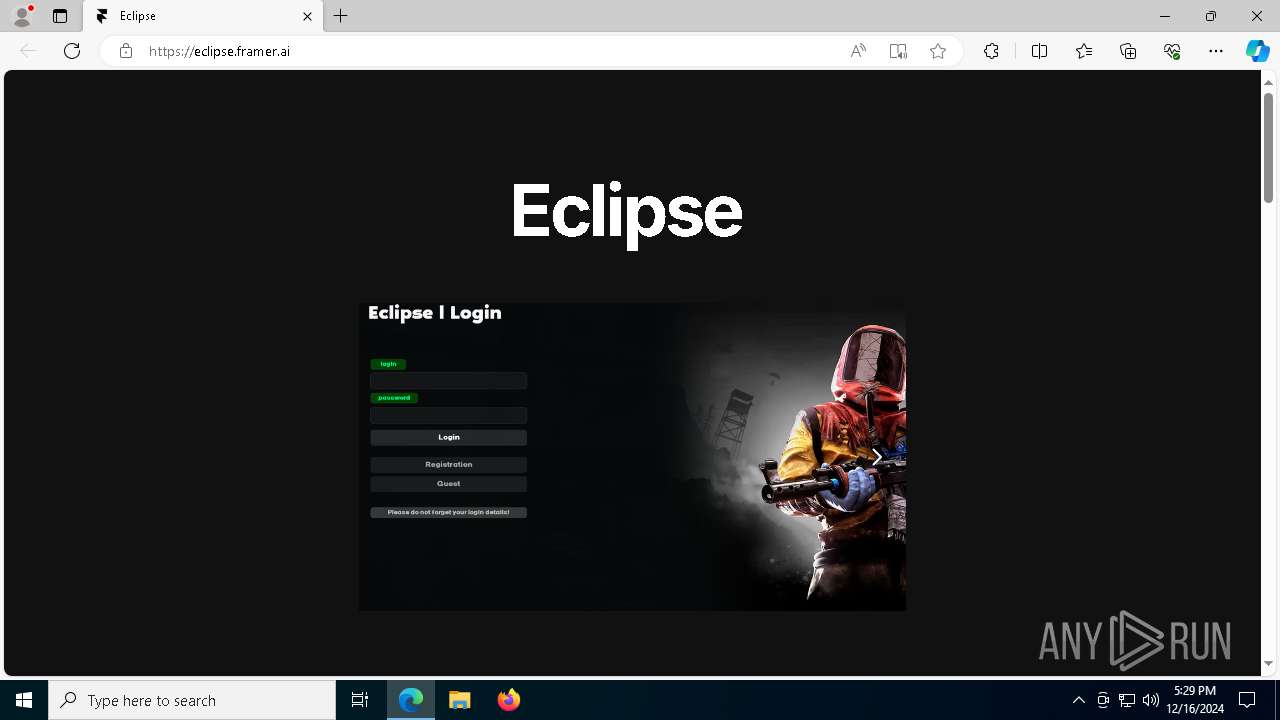
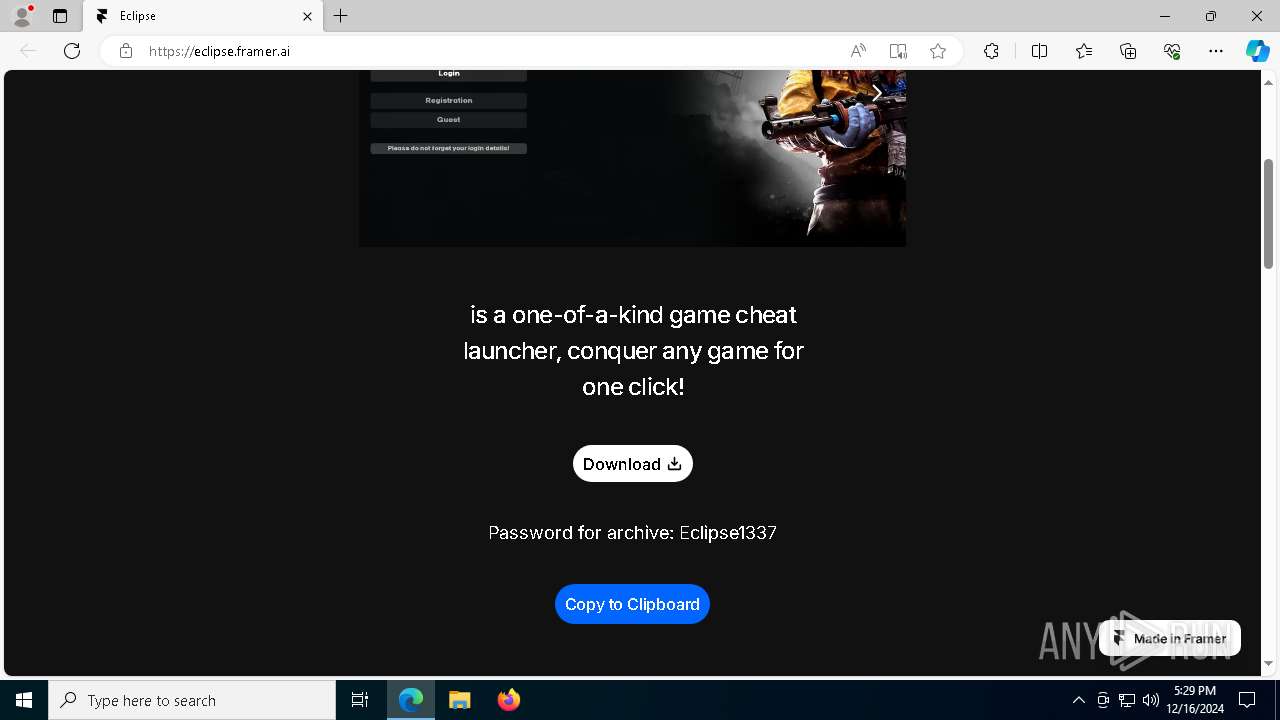
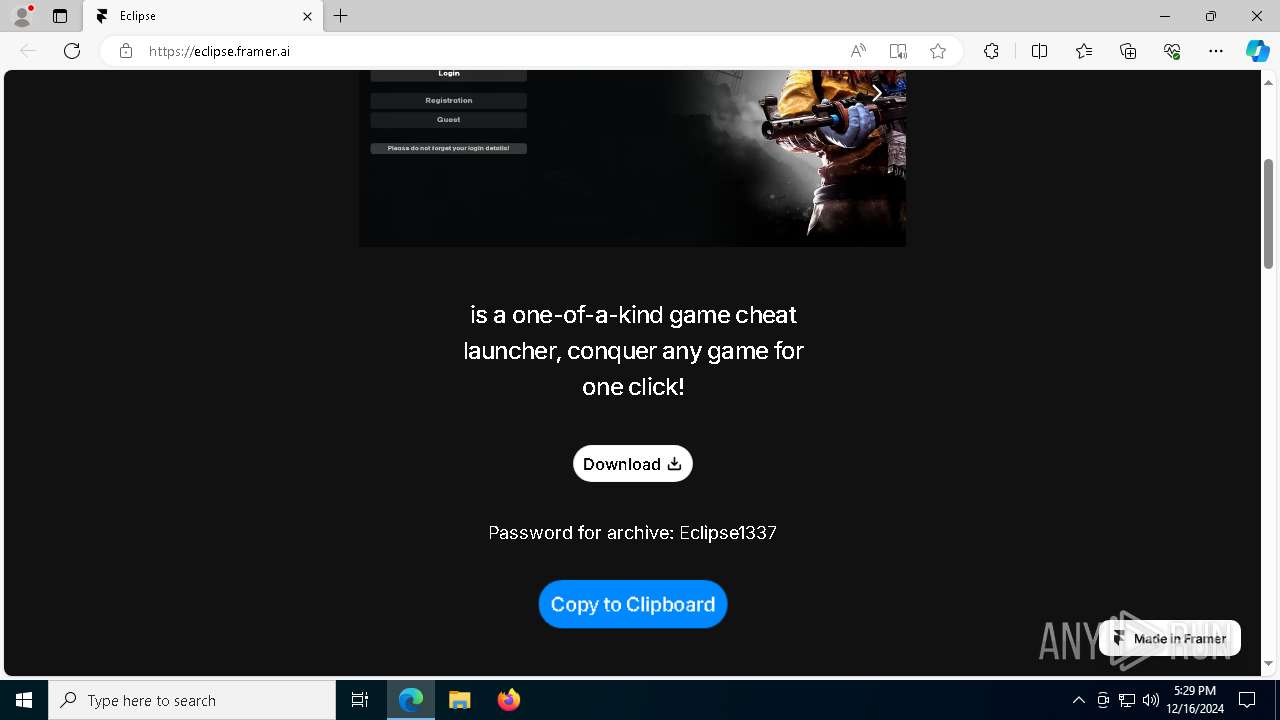
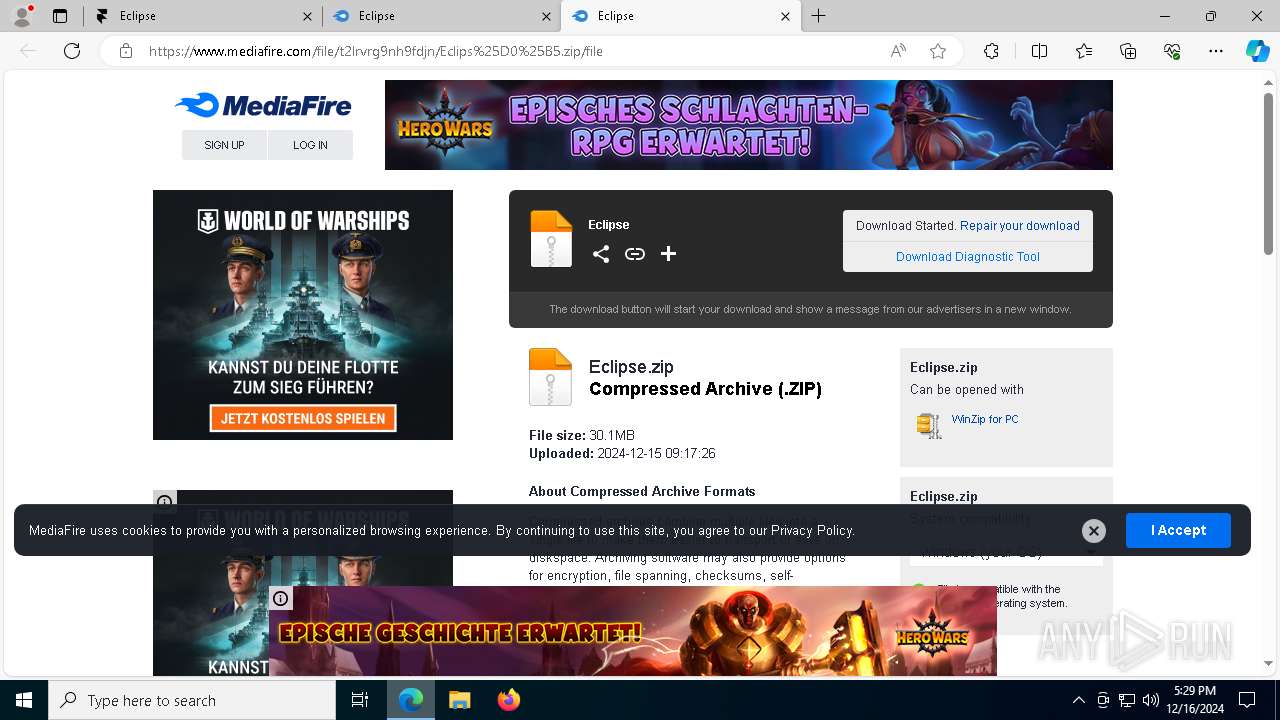
| URL: | https://eclipse.framer.ai/ |
| Full analysis: | https://app.any.run/tasks/04847806-6689-4b7a-8561-cb801347d68a |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | December 16, 2024, 17:29:05 |
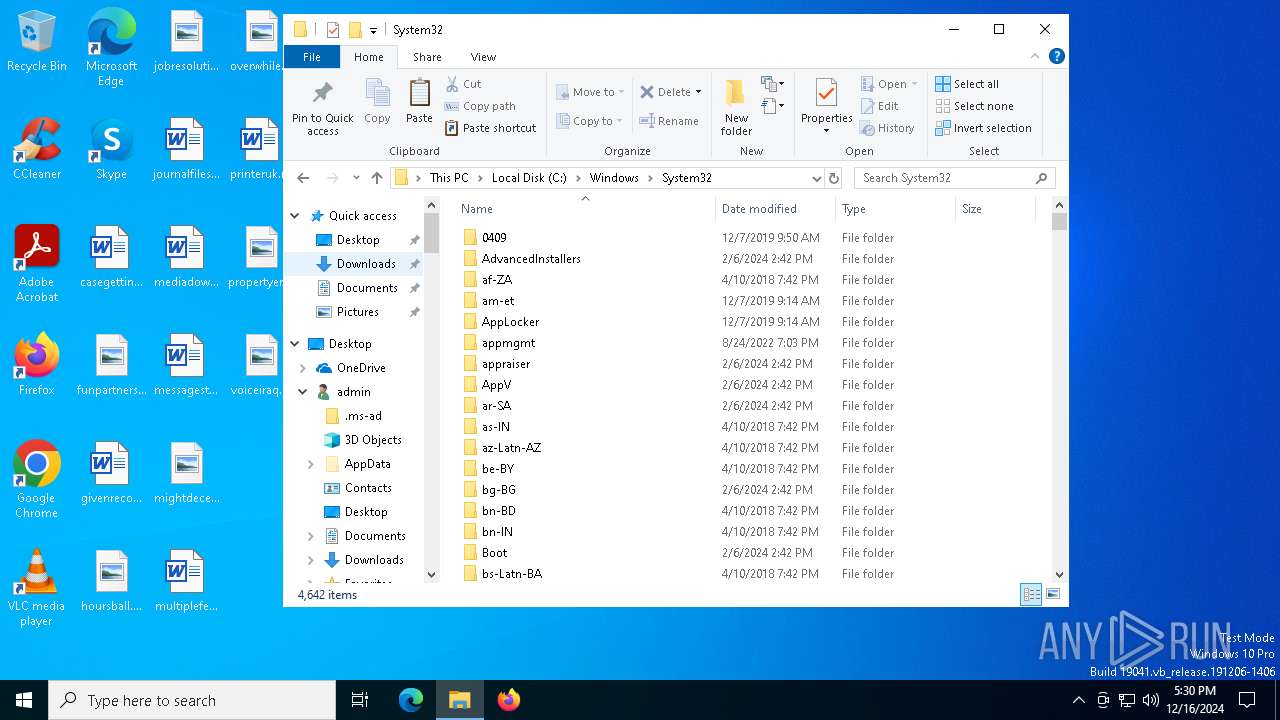
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 530EFEF8B71E2B2FFC731EA36CAE5F2C |
| SHA1: | 5F554E27DE434734CFB8322C8C44CB90FABAB644 |
| SHA256: | 9119B649563DDBD3224CD9456D8EB734E6C17F162FECA28C8D060B482A81A713 |
| SSDEEP: | 3:N8vuLEIYQ:2mLhYQ |
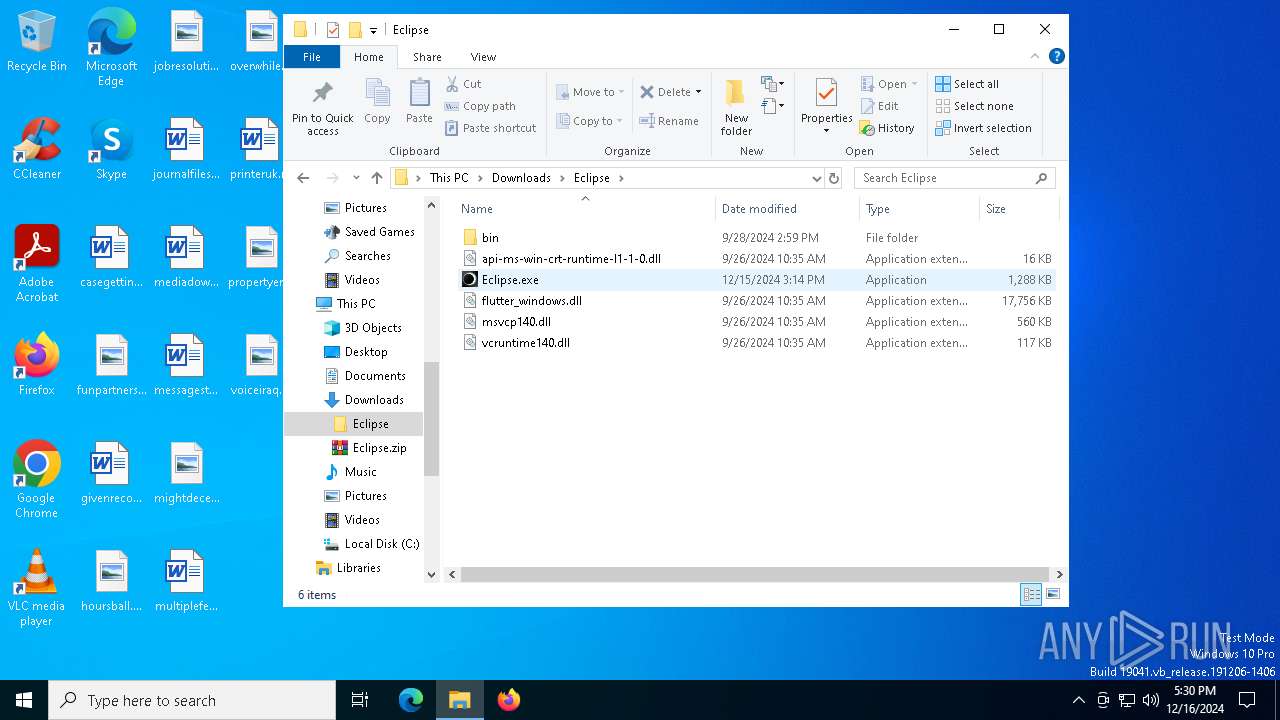
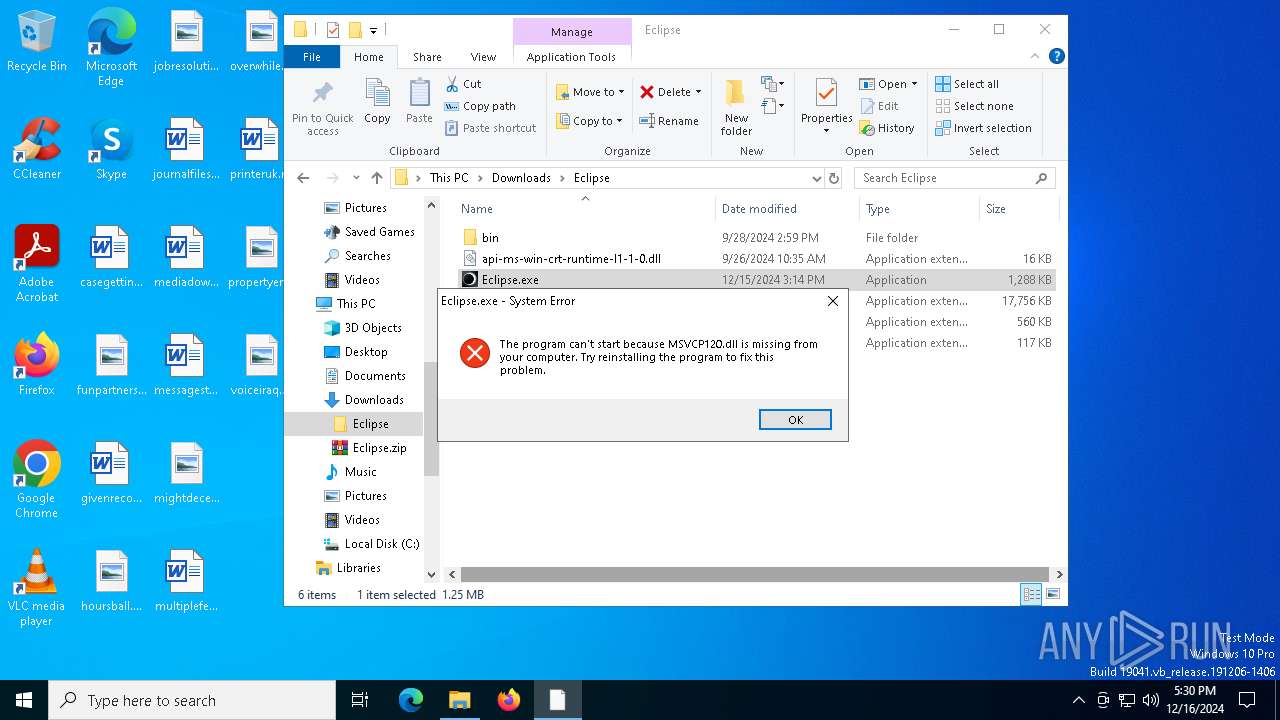
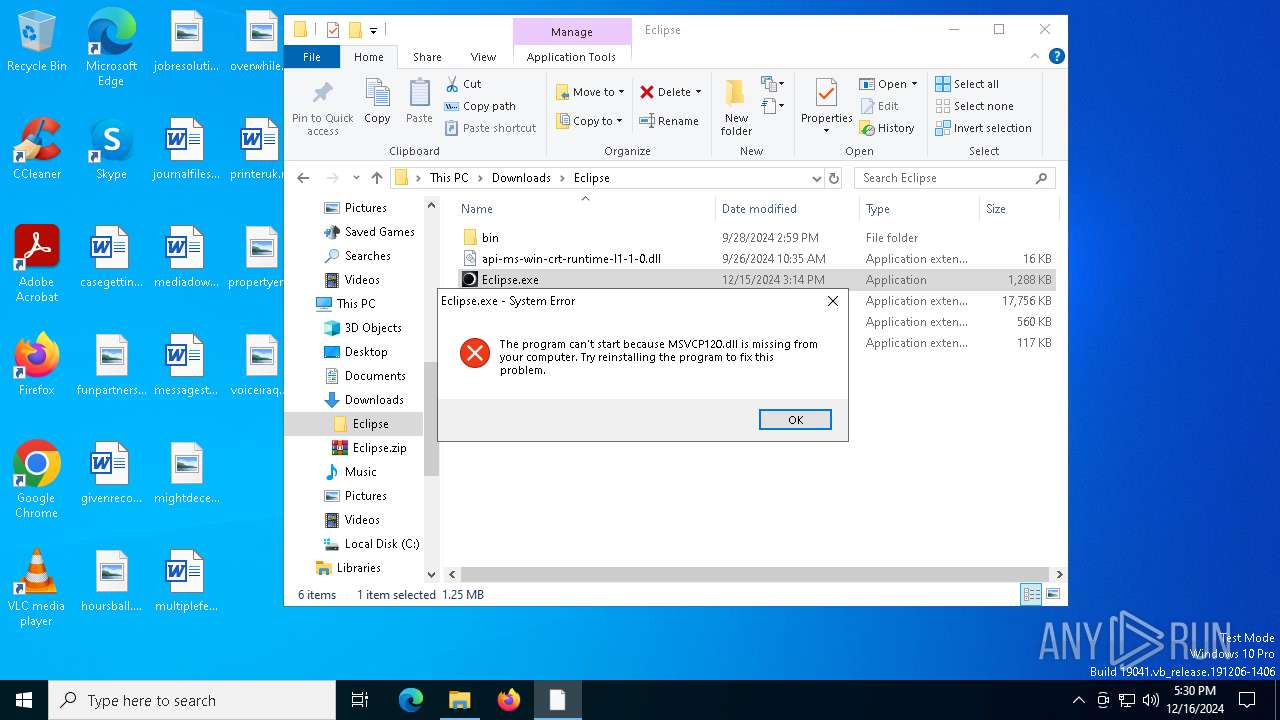
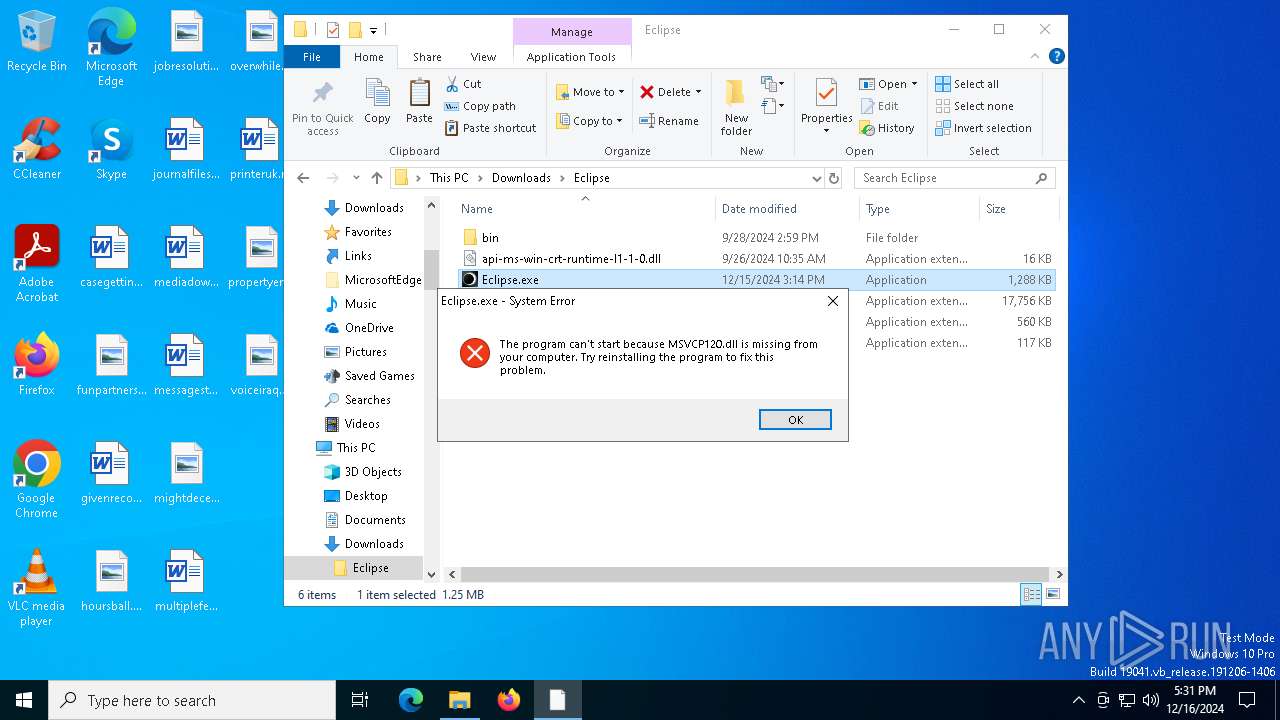
MALICIOUS
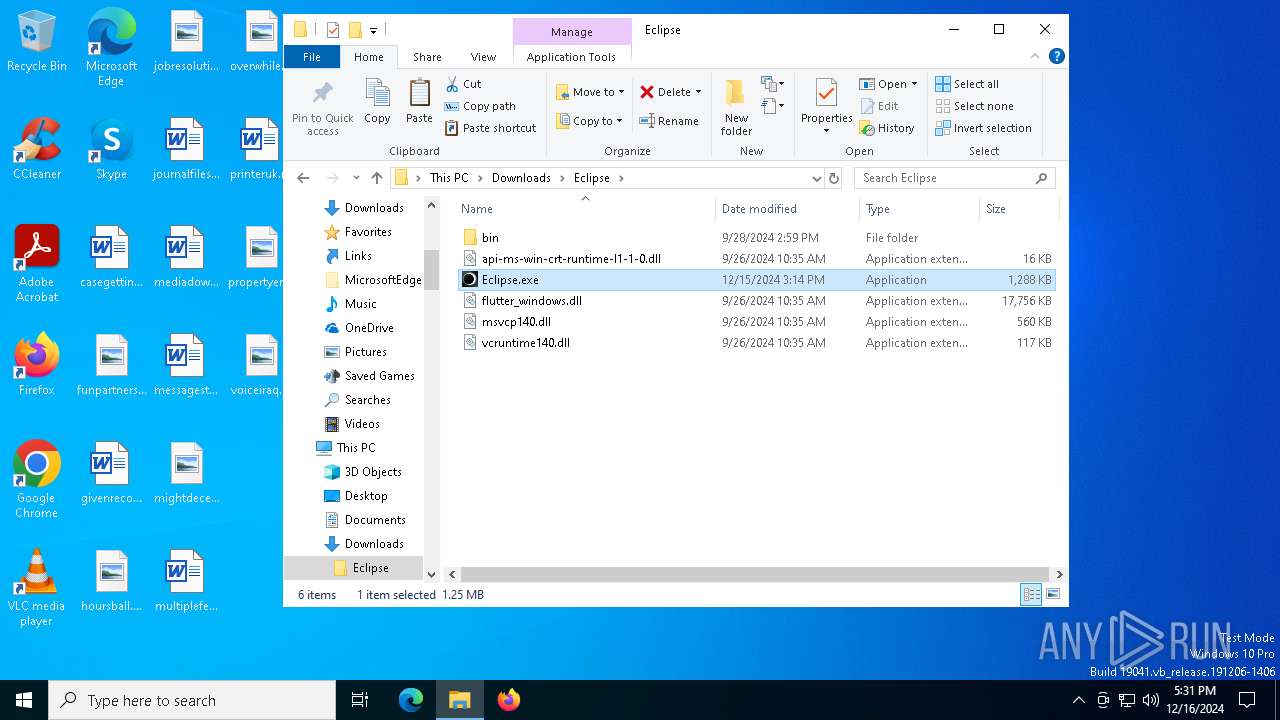
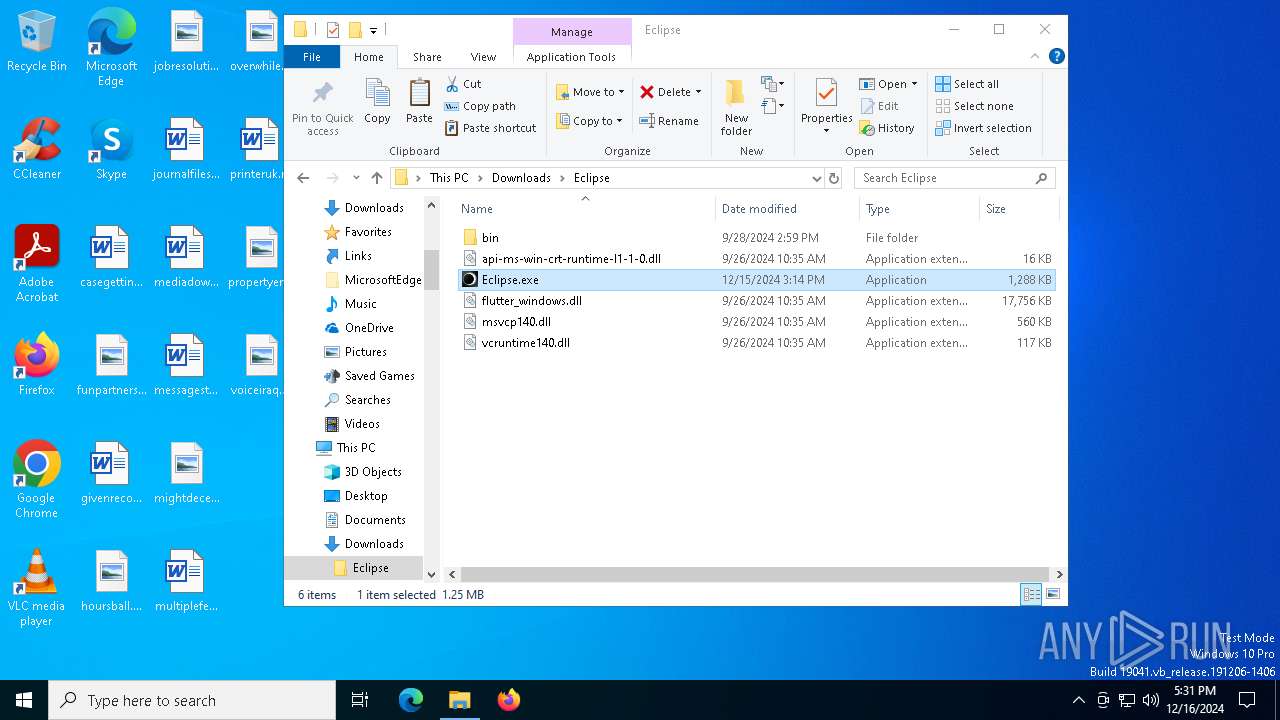
Executing a file with an untrusted certificate
- Eclipsе.exe (PID: 6164)
- Eclipsе.exe (PID: 6832)
- Eclipsе.exe (PID: 6096)
LUMMA mutex has been found
- Achieved.com (PID: 7268)
- Achieved.com (PID: 8044)
- Achieved.com (PID: 1172)
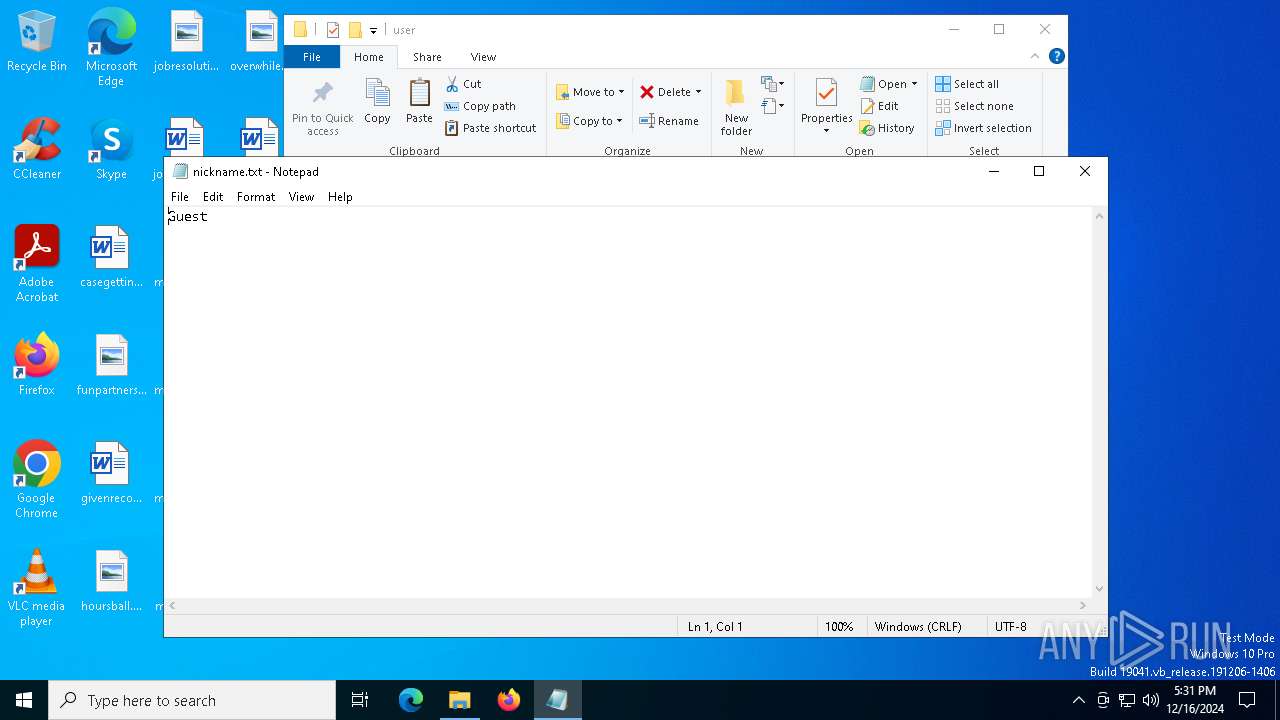
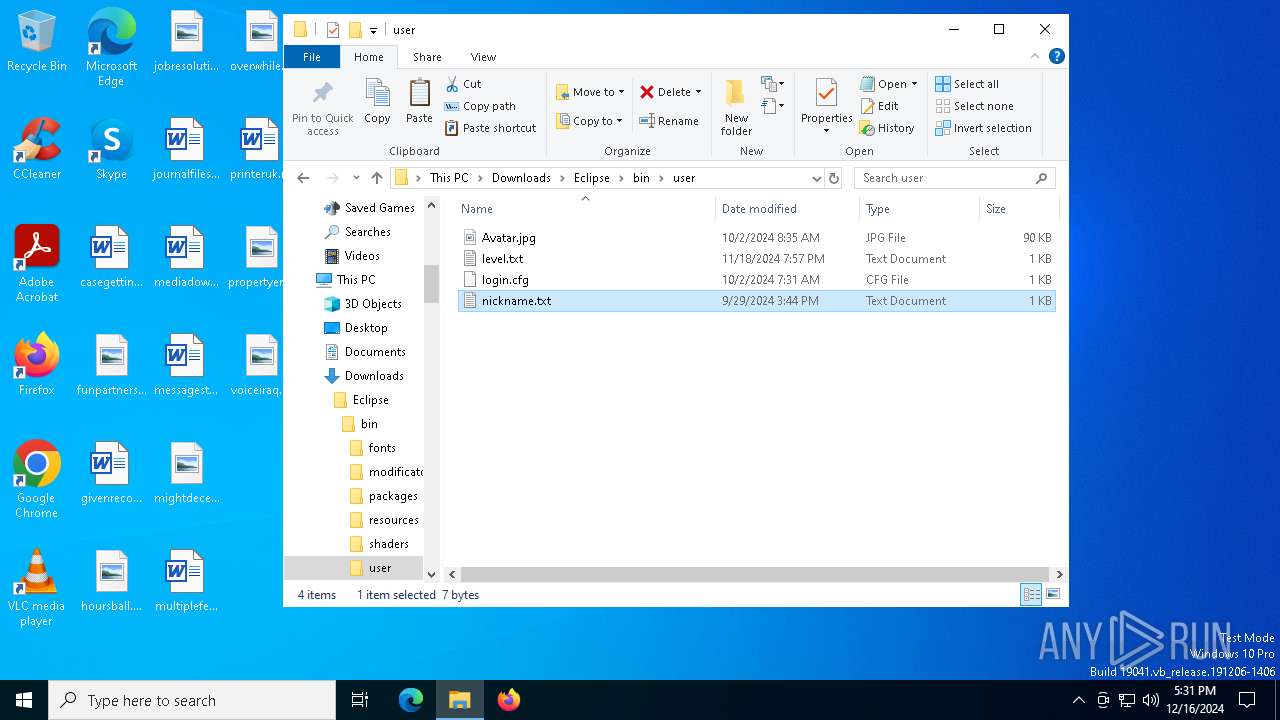
Actions looks like stealing of personal data
- Achieved.com (PID: 7268)
- Achieved.com (PID: 8044)
- Achieved.com (PID: 1172)
SUSPICIOUS
Reads security settings of Internet Explorer
- Eclipsе.exe (PID: 6164)
- Eclipsе.exe (PID: 6096)
Starts CMD.EXE for commands execution
- Eclipsе.exe (PID: 6164)
- cmd.exe (PID: 7016)
- Eclipsе.exe (PID: 6832)
- cmd.exe (PID: 6464)
- Eclipsе.exe (PID: 6096)
- cmd.exe (PID: 5872)
Executing commands from ".cmd" file
- Eclipsе.exe (PID: 6164)
- Eclipsе.exe (PID: 6832)
- Eclipsе.exe (PID: 6096)
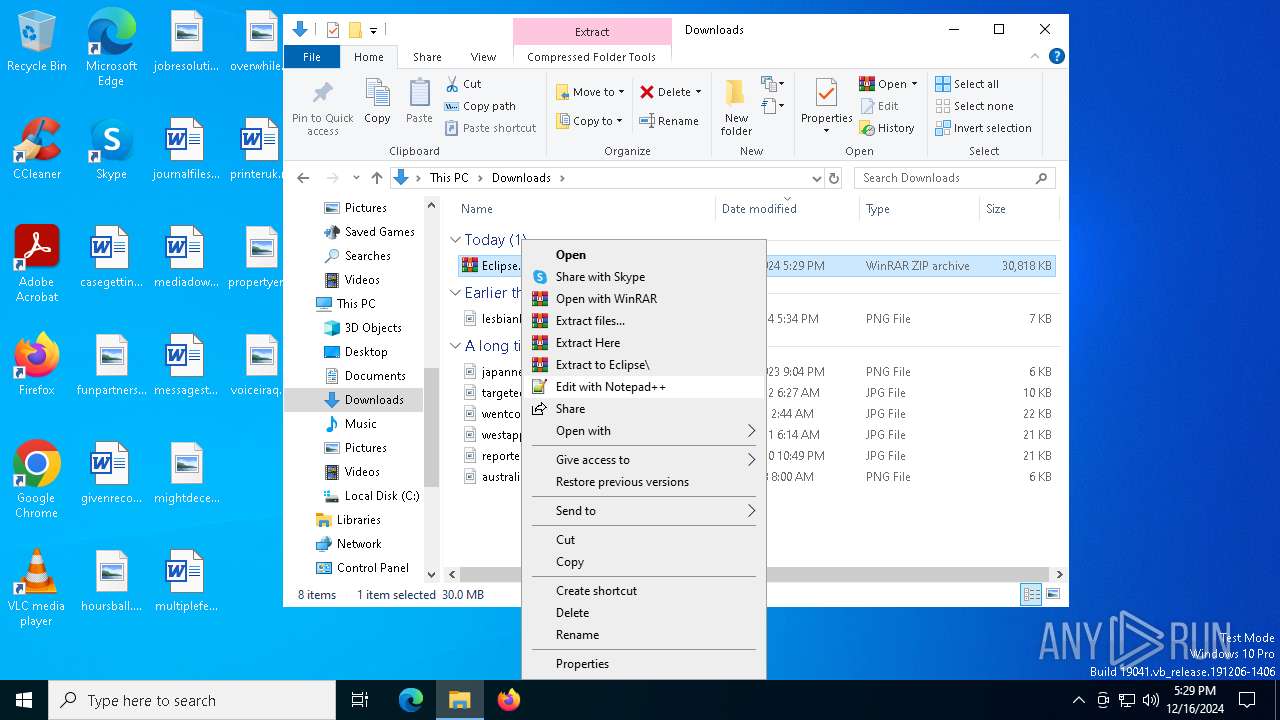
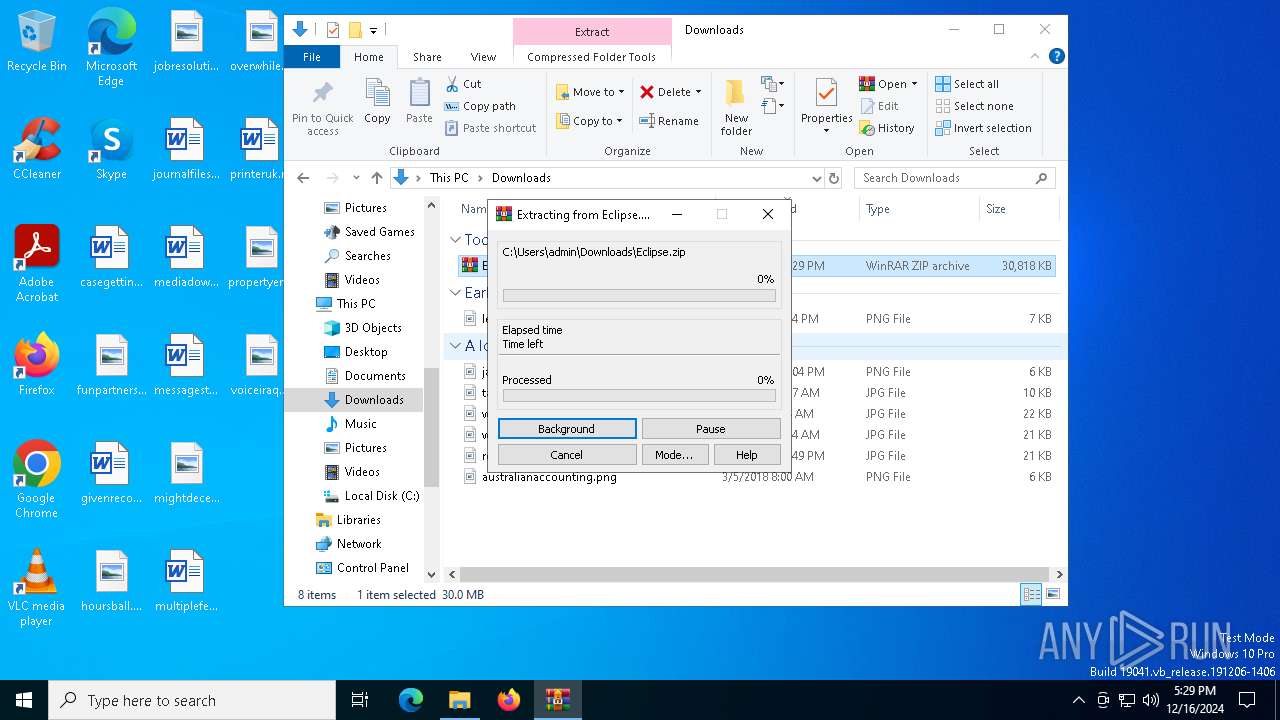
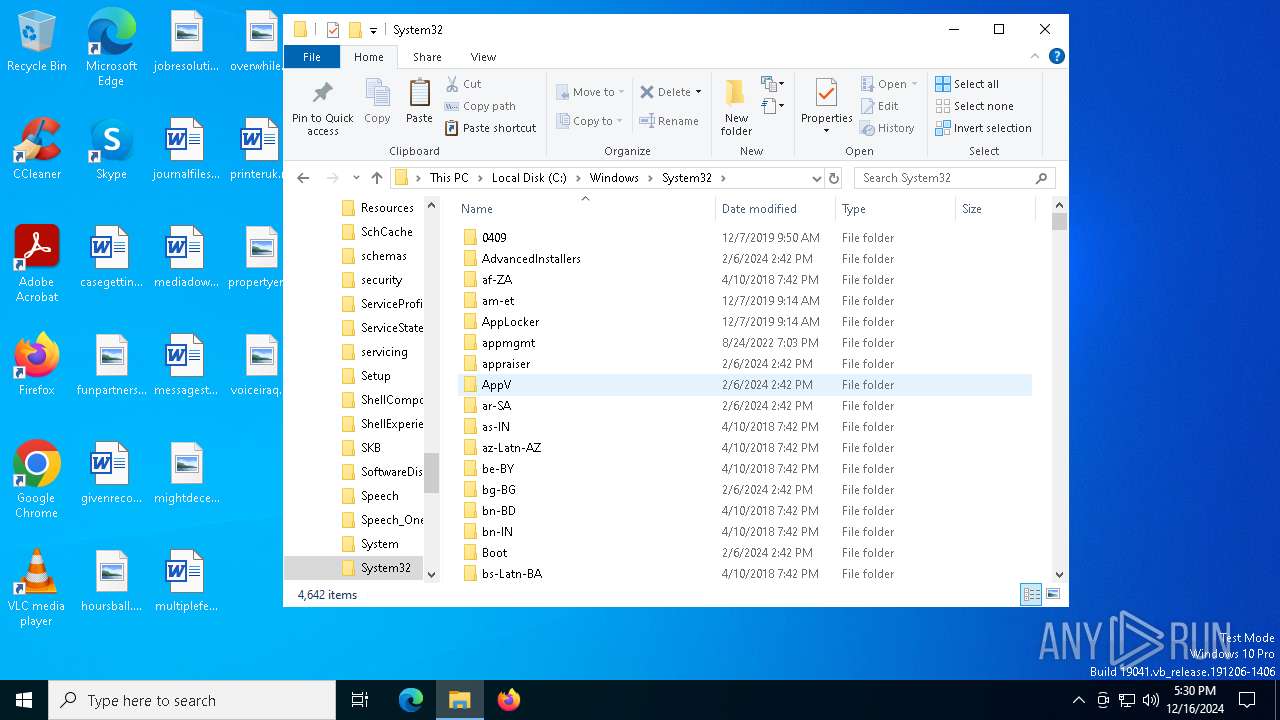
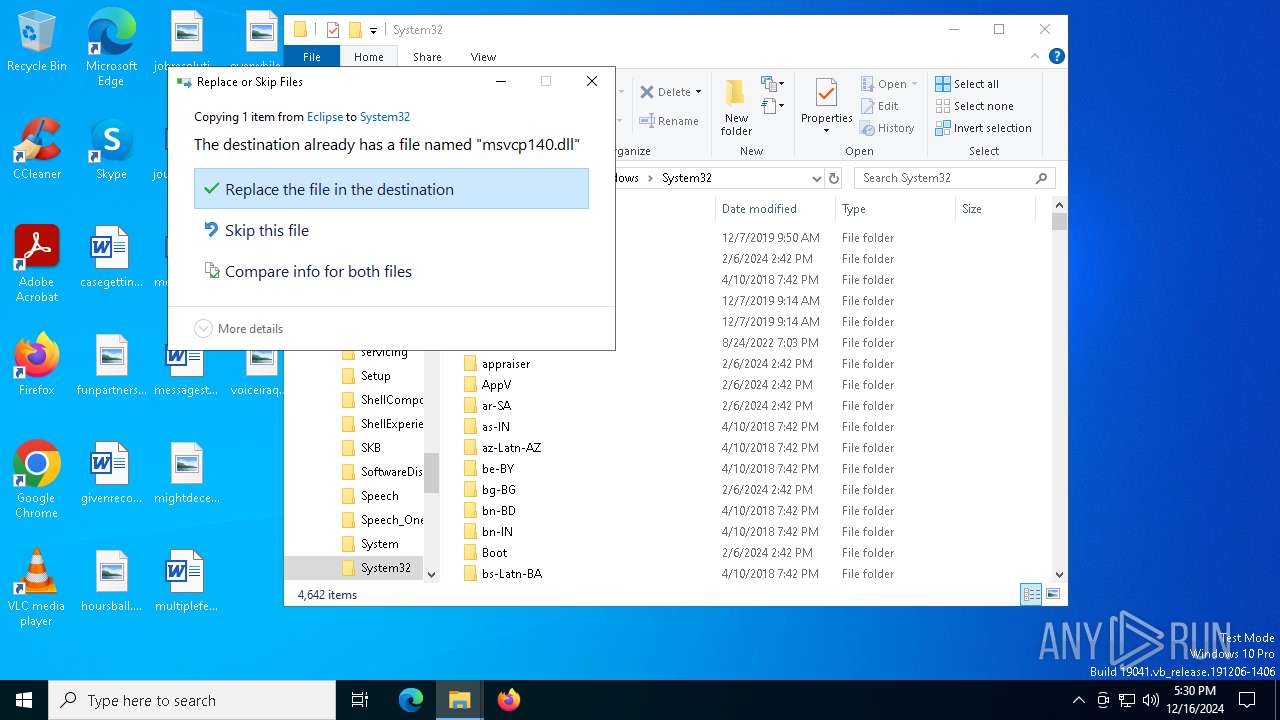
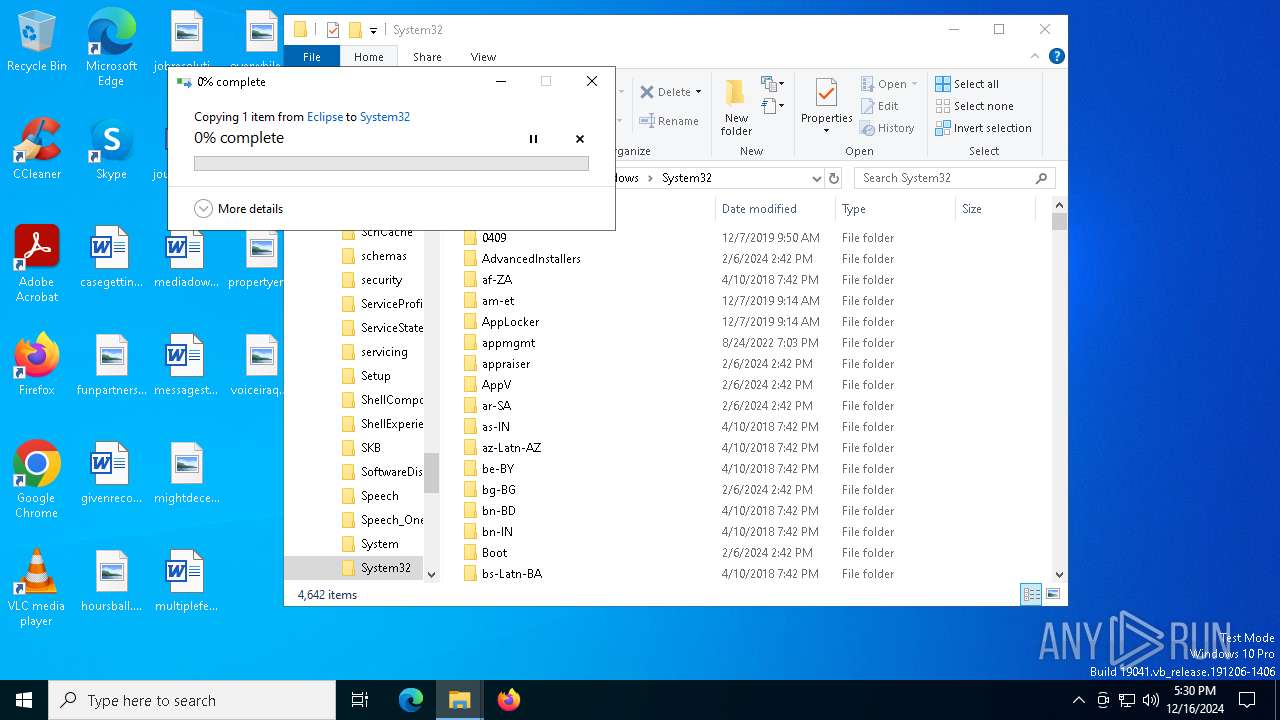
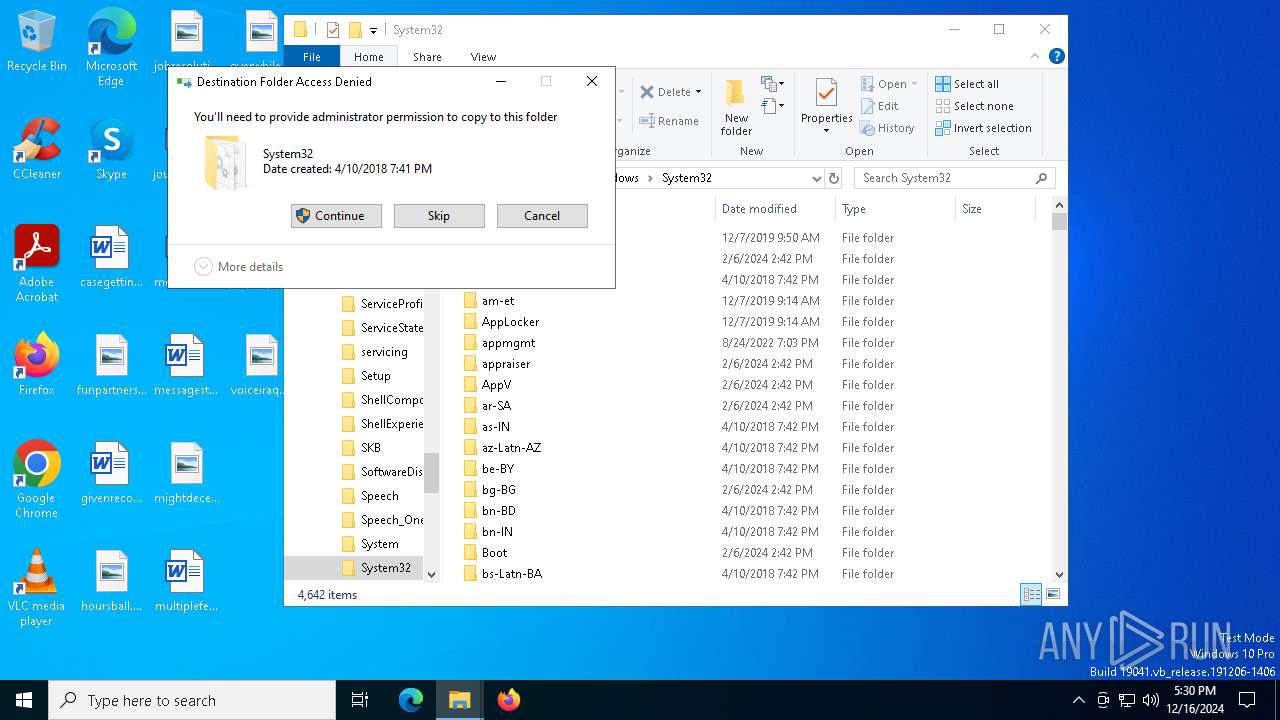
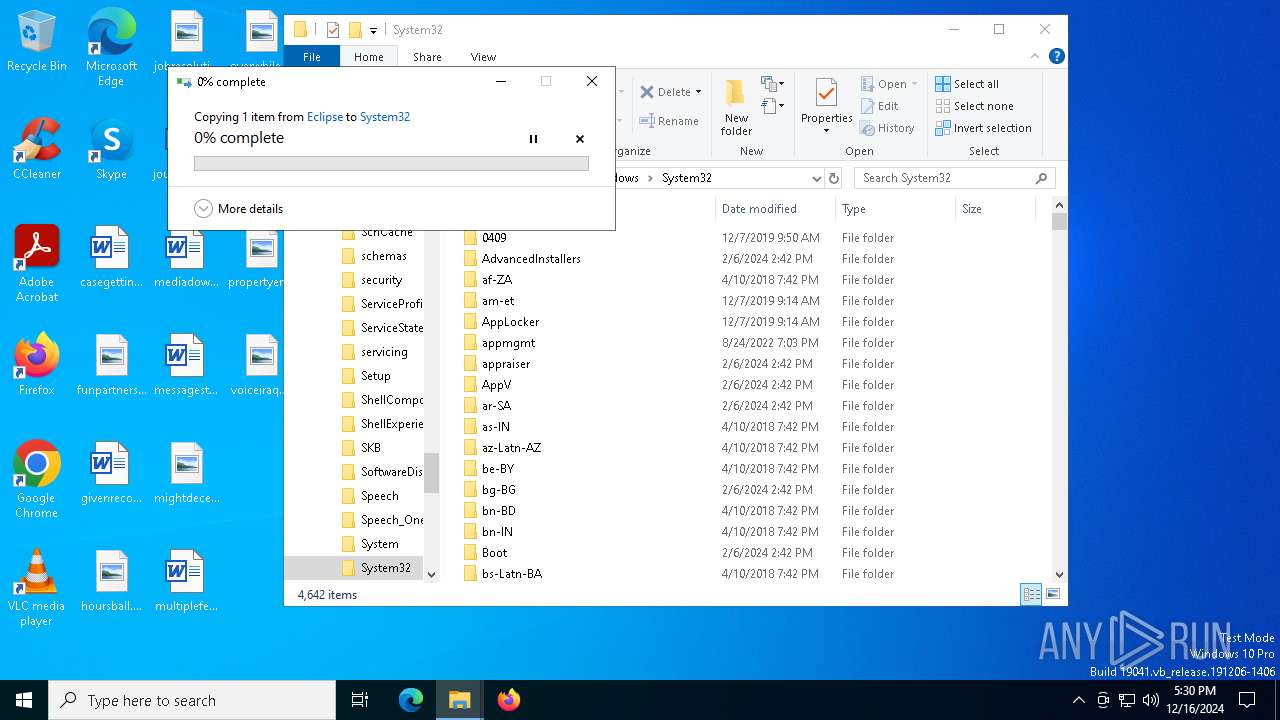
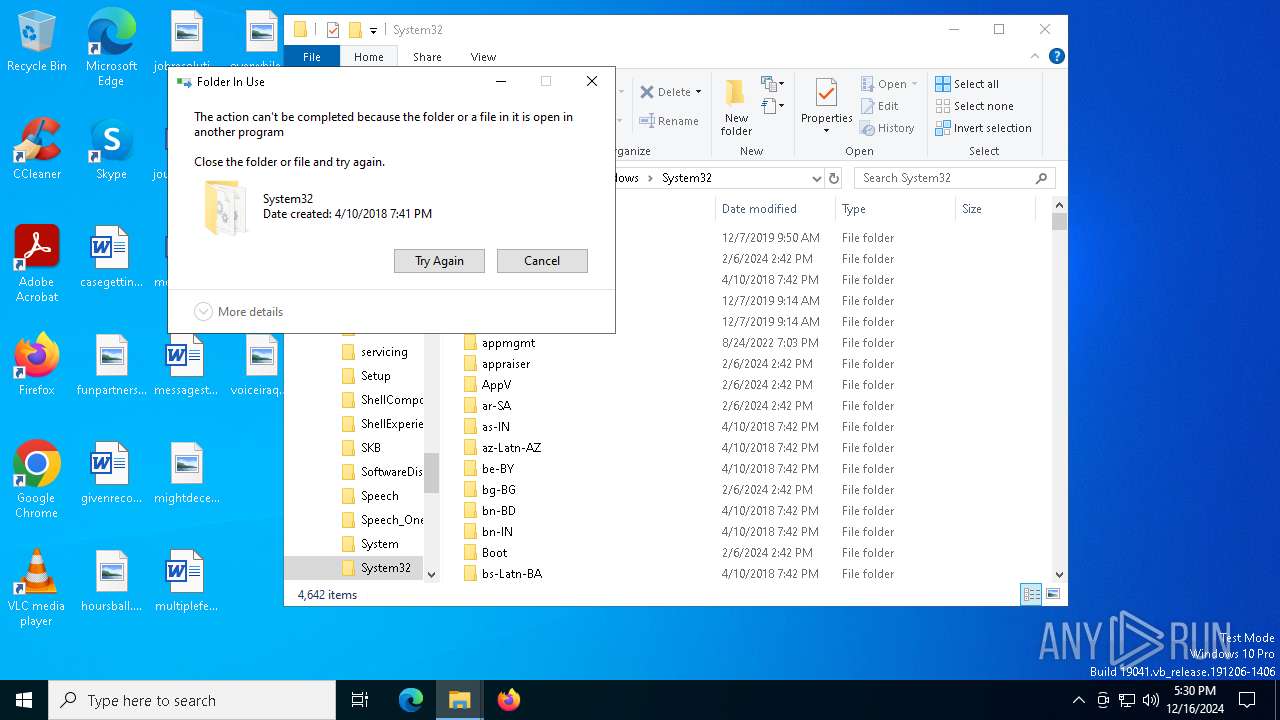
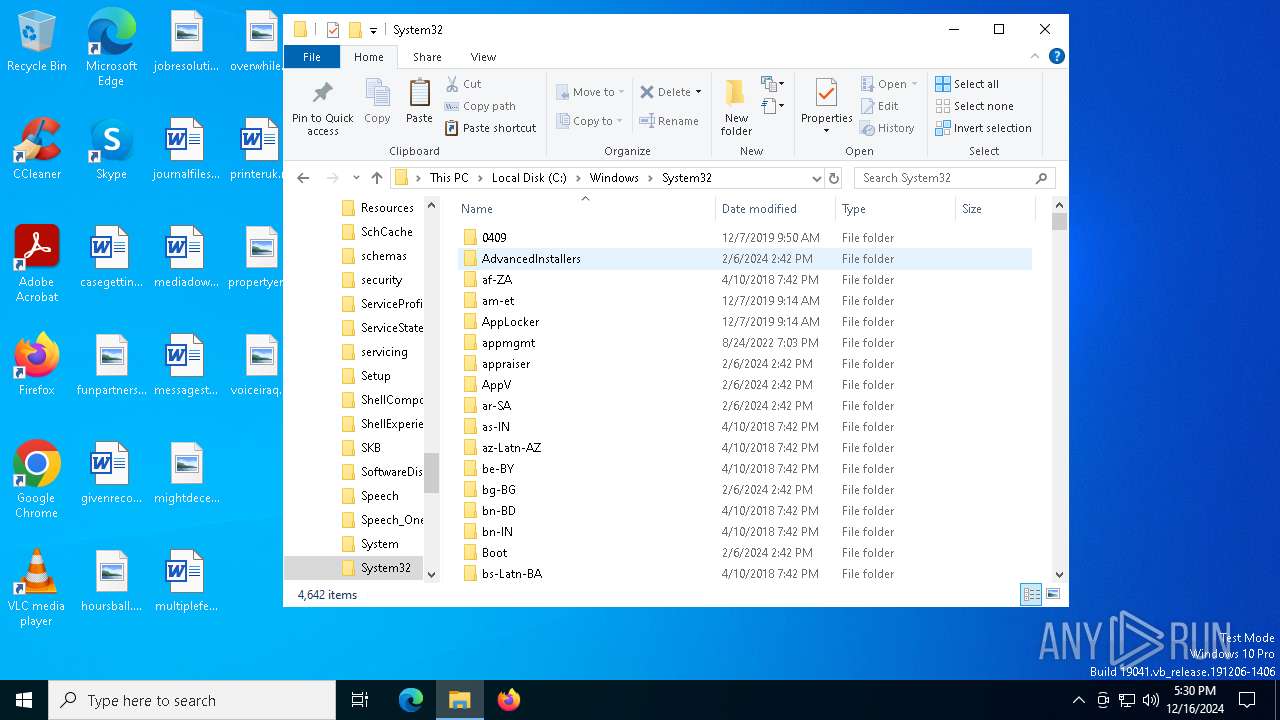
Process drops legitimate windows executable
- WinRAR.exe (PID: 7488)
Get information on the list of running processes
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 5872)
The executable file from the user directory is run by the CMD process
- Achieved.com (PID: 7268)
- Achieved.com (PID: 8044)
- Achieved.com (PID: 1172)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 5872)
Application launched itself
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 5872)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 5872)
Starts application with an unusual extension
- cmd.exe (PID: 7016)
- cmd.exe (PID: 6464)
- cmd.exe (PID: 5872)
INFO
Checks supported languages
- identity_helper.exe (PID: 7952)
- Eclipsе.exe (PID: 6164)
- Achieved.com (PID: 7268)
- Eclipsе.exe (PID: 6096)
- Achieved.com (PID: 1172)
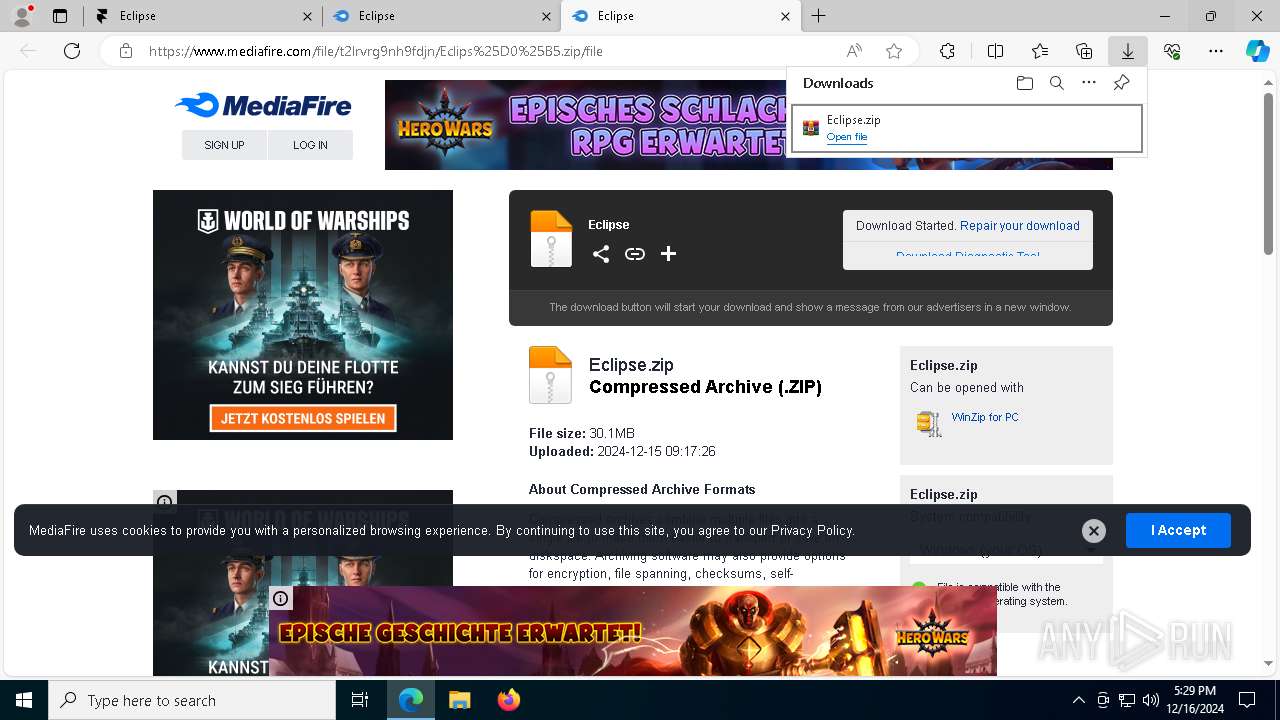
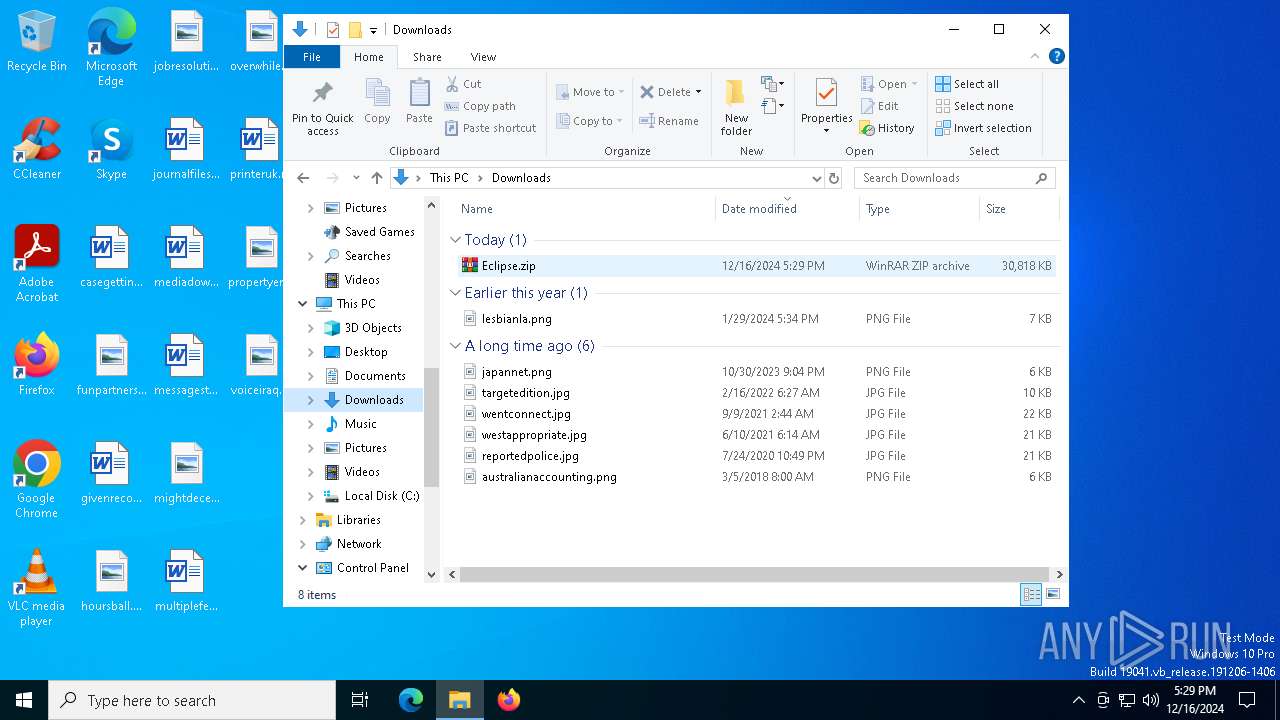
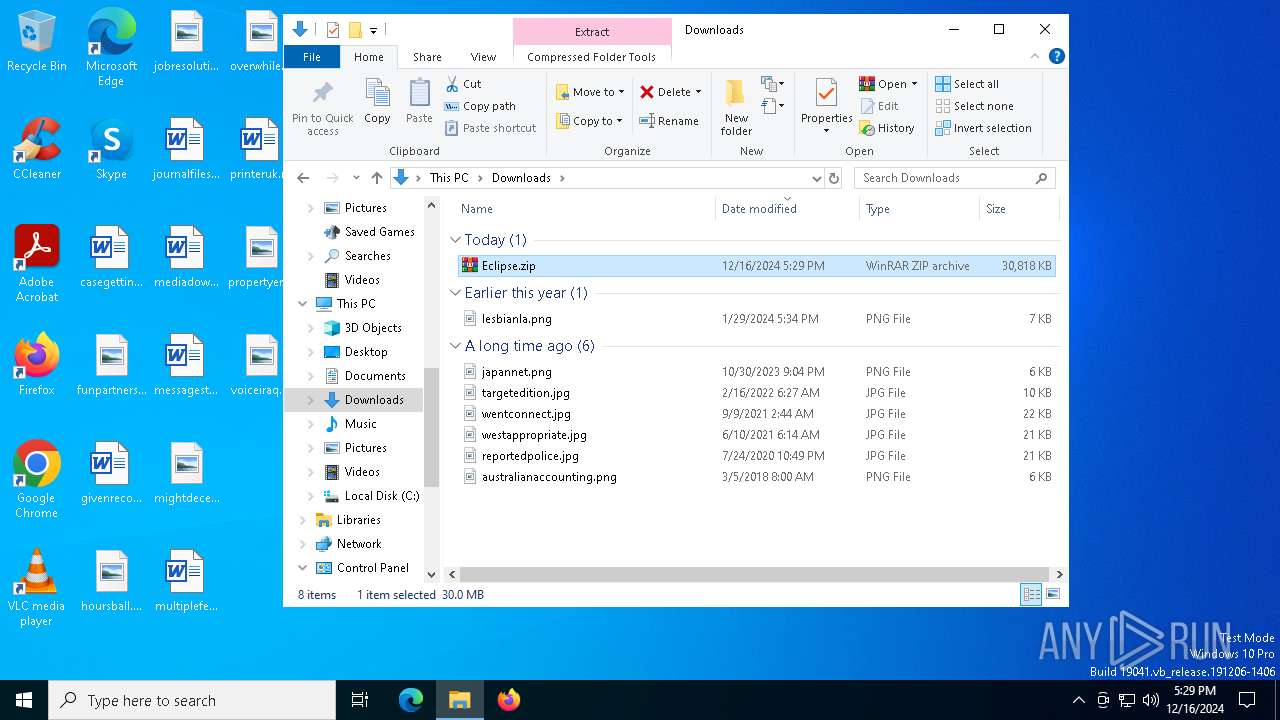
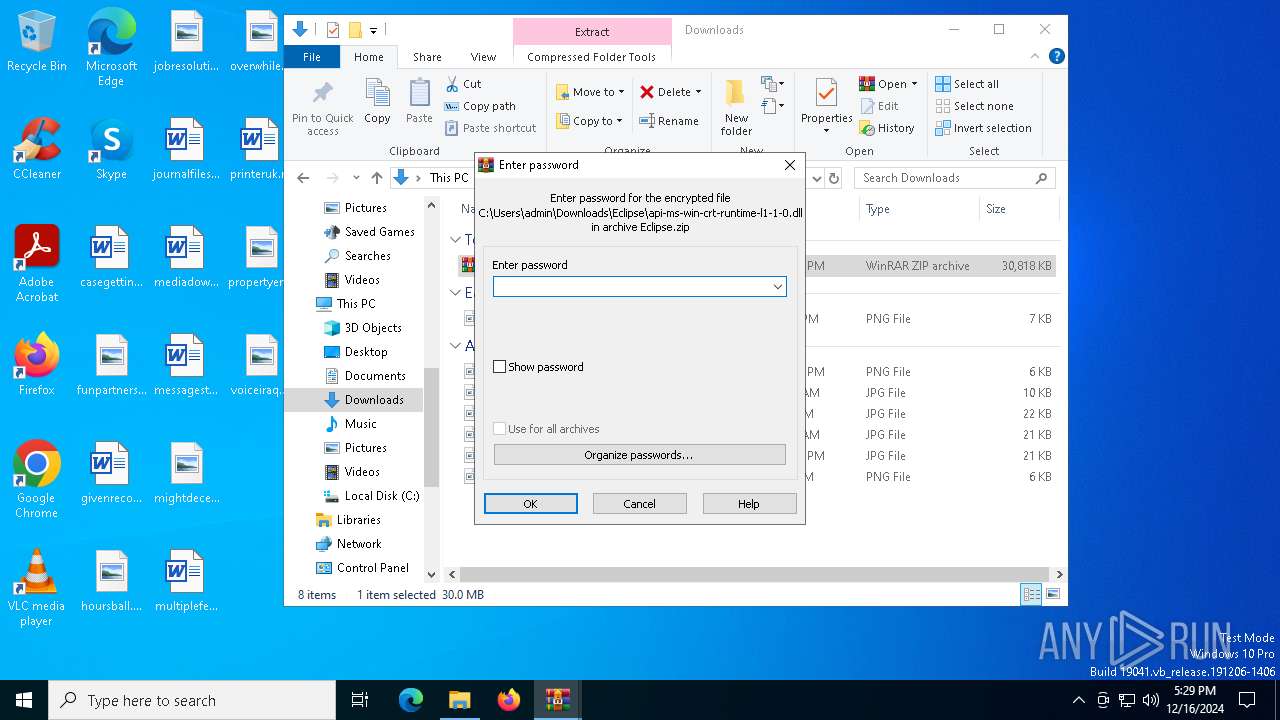
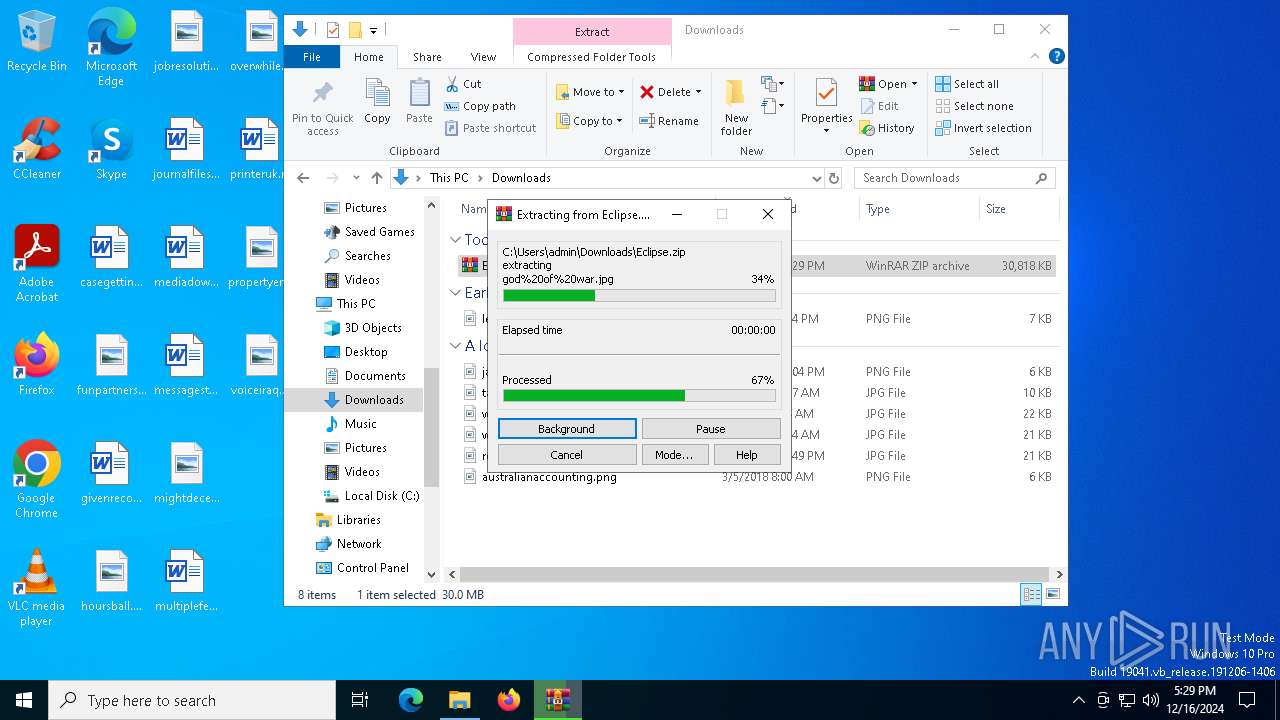
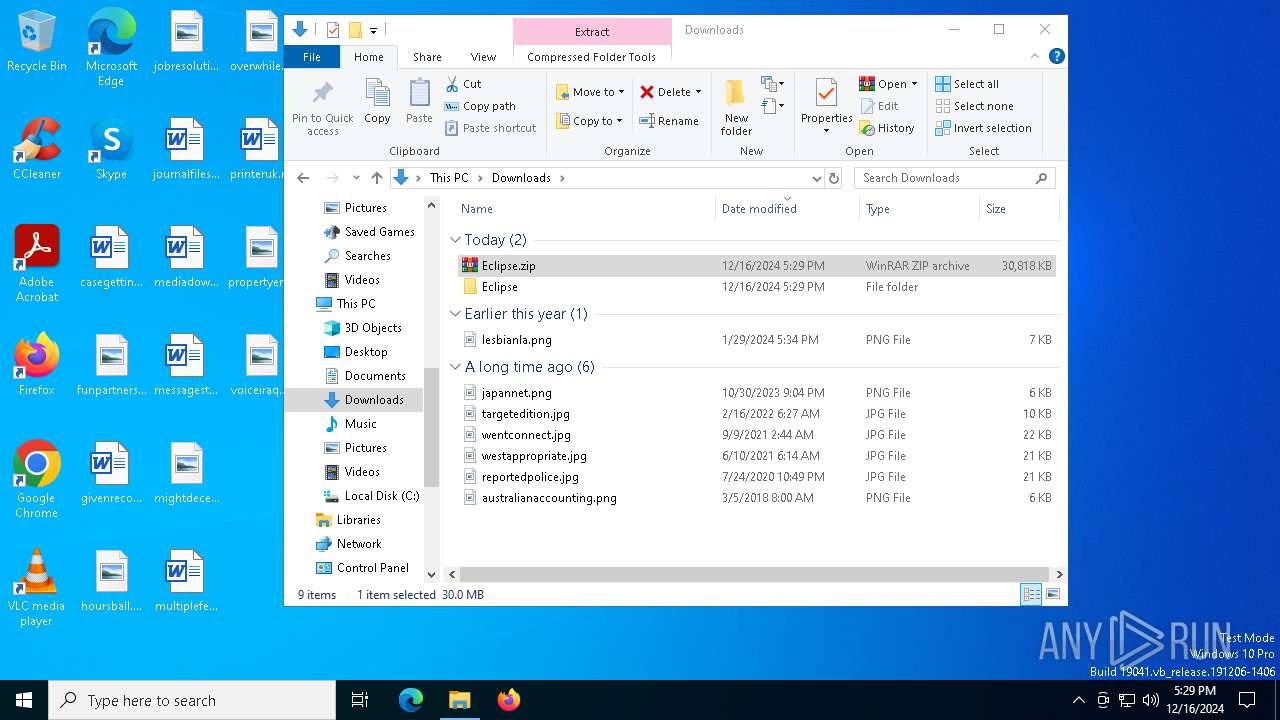
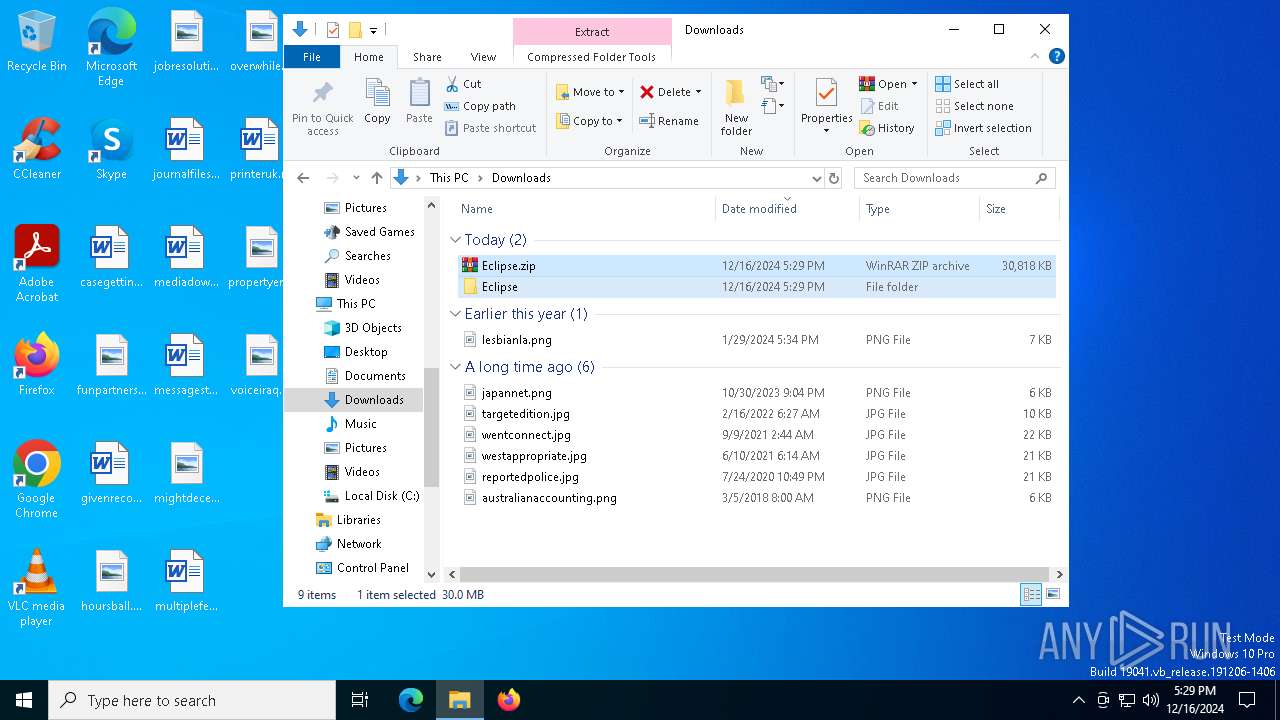
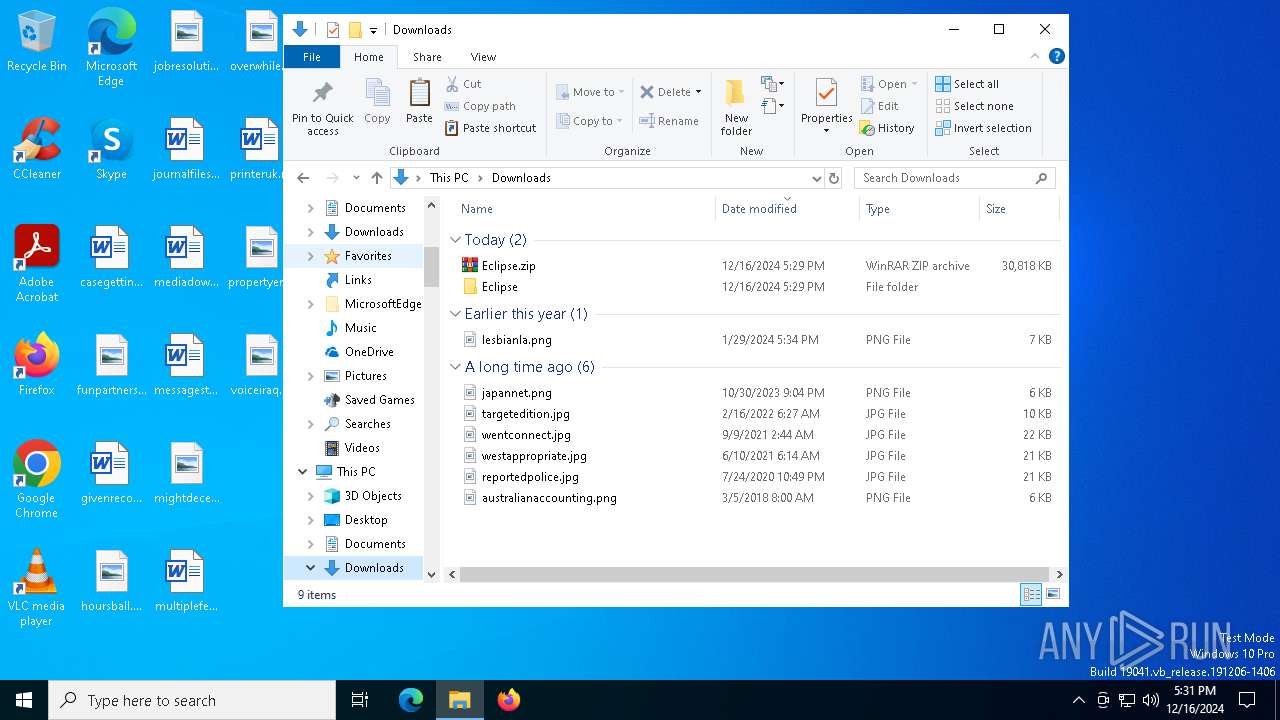
The process uses the downloaded file
- msedge.exe (PID: 5792)
- Eclipsе.exe (PID: 6164)
- WinRAR.exe (PID: 7488)
- Eclipsе.exe (PID: 6096)
Application launched itself
- msedge.exe (PID: 6348)
- msedge.exe (PID: 4392)
Create files in a temporary directory
- Eclipsе.exe (PID: 6164)
- Eclipsе.exe (PID: 6832)
- Eclipsе.exe (PID: 6096)
Reads the computer name
- identity_helper.exe (PID: 7952)
- Eclipsе.exe (PID: 6164)
- Achieved.com (PID: 8044)
Reads Environment values
- identity_helper.exe (PID: 7952)
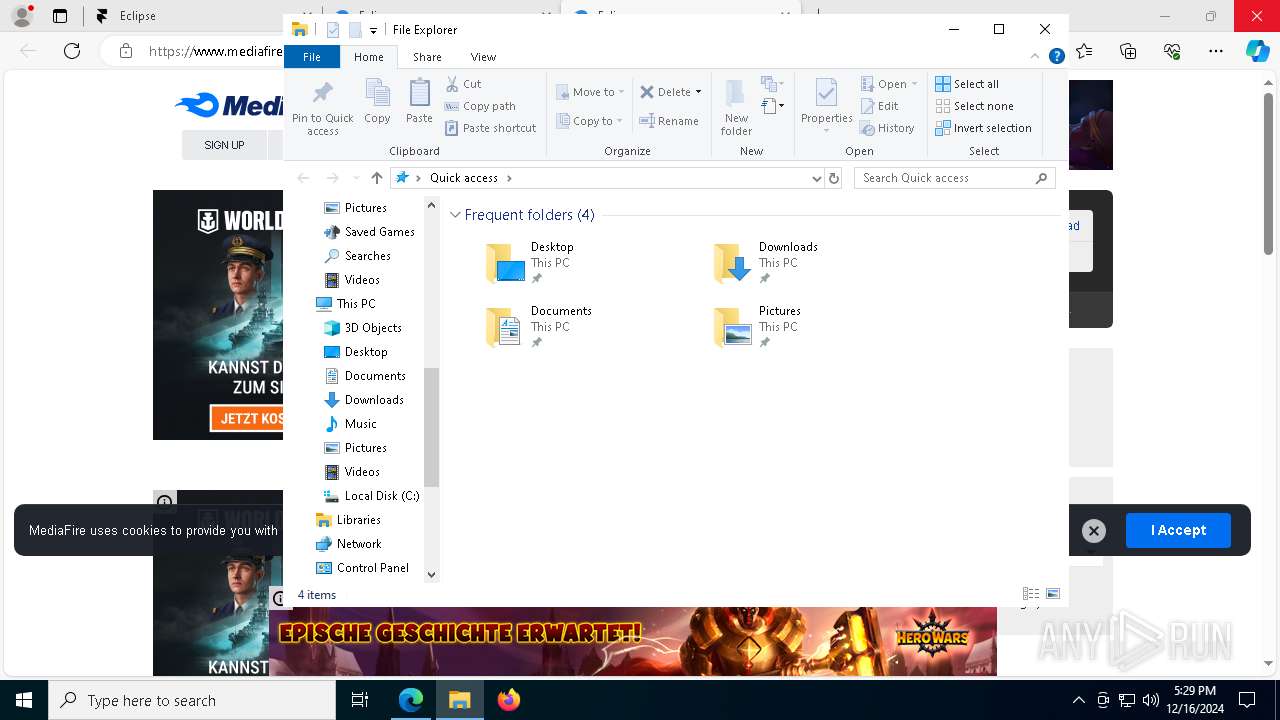
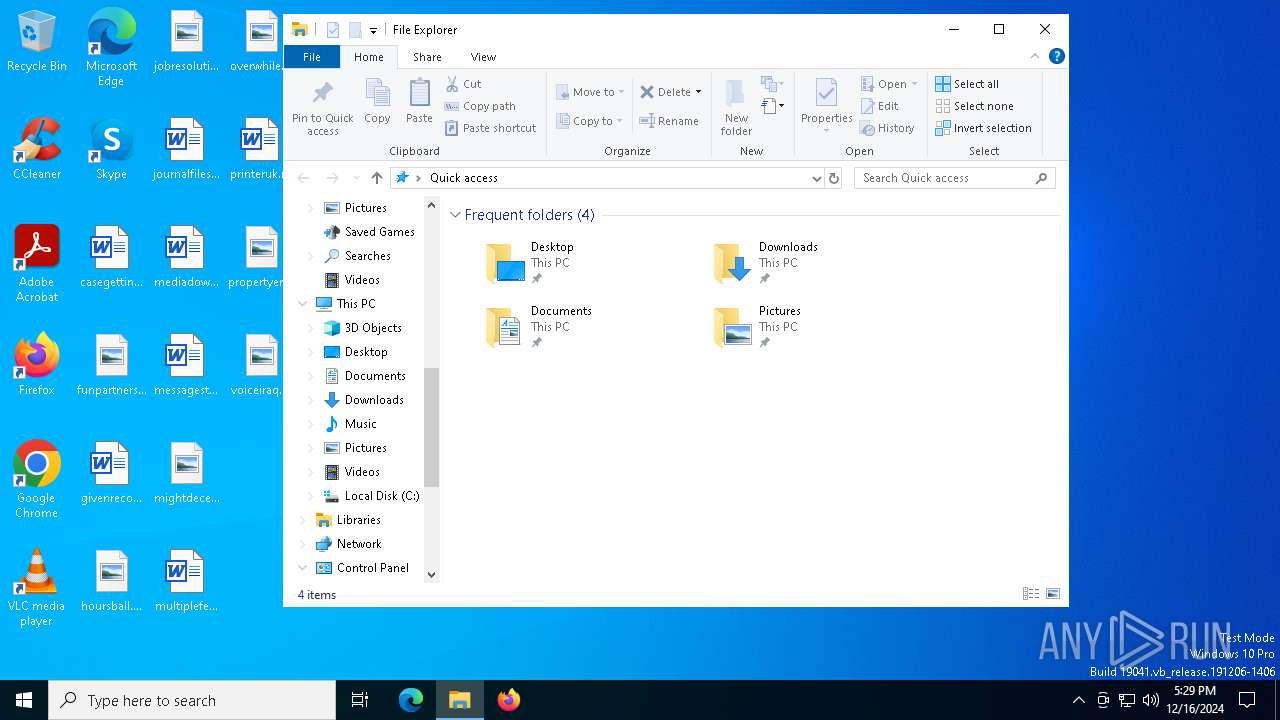
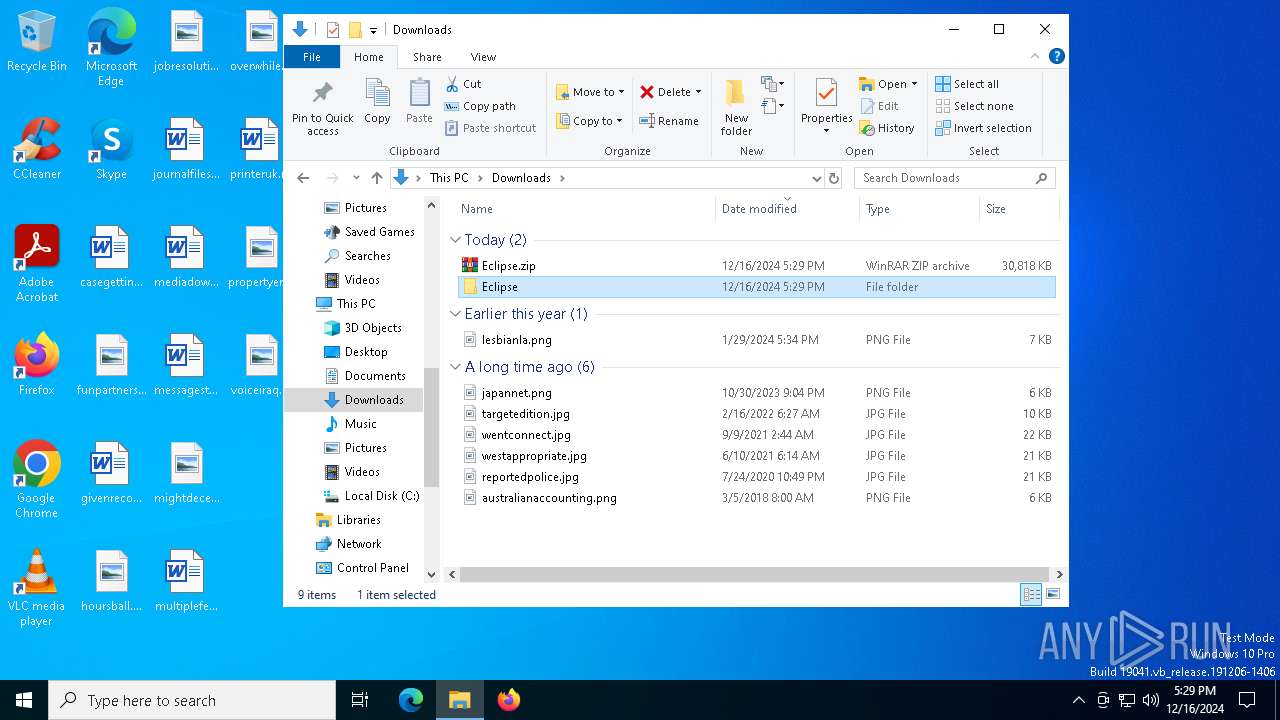
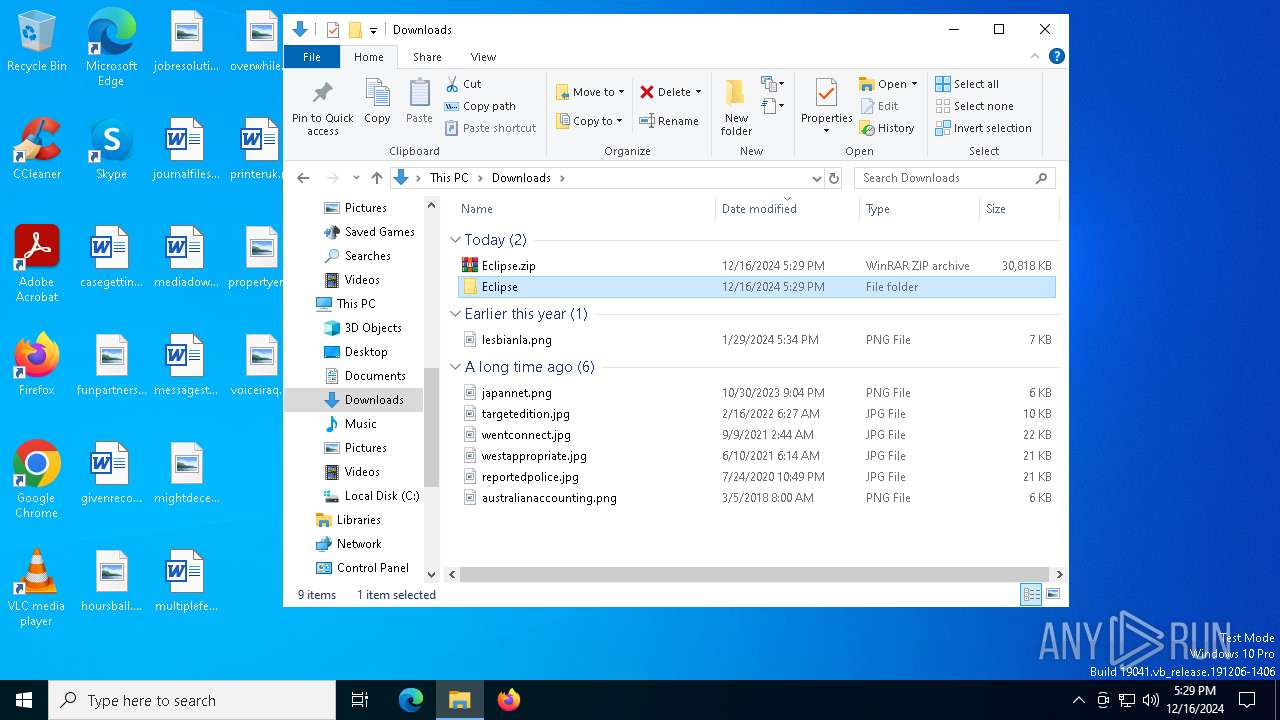
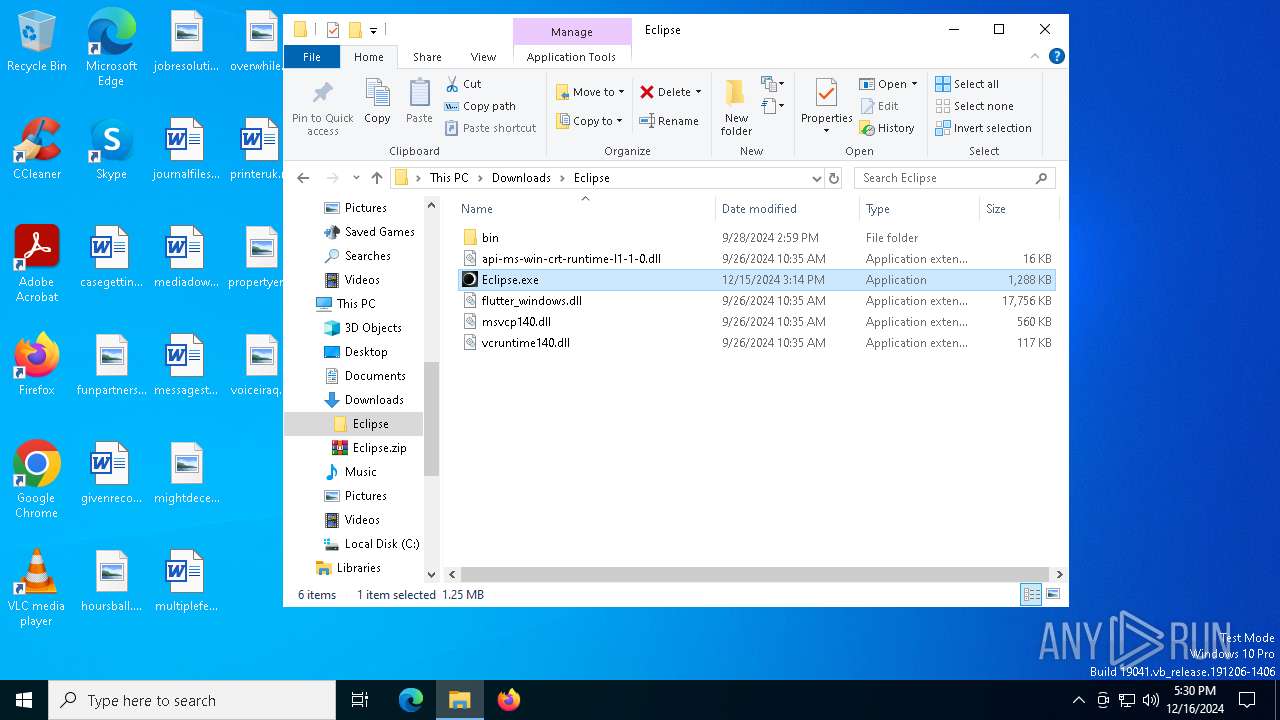
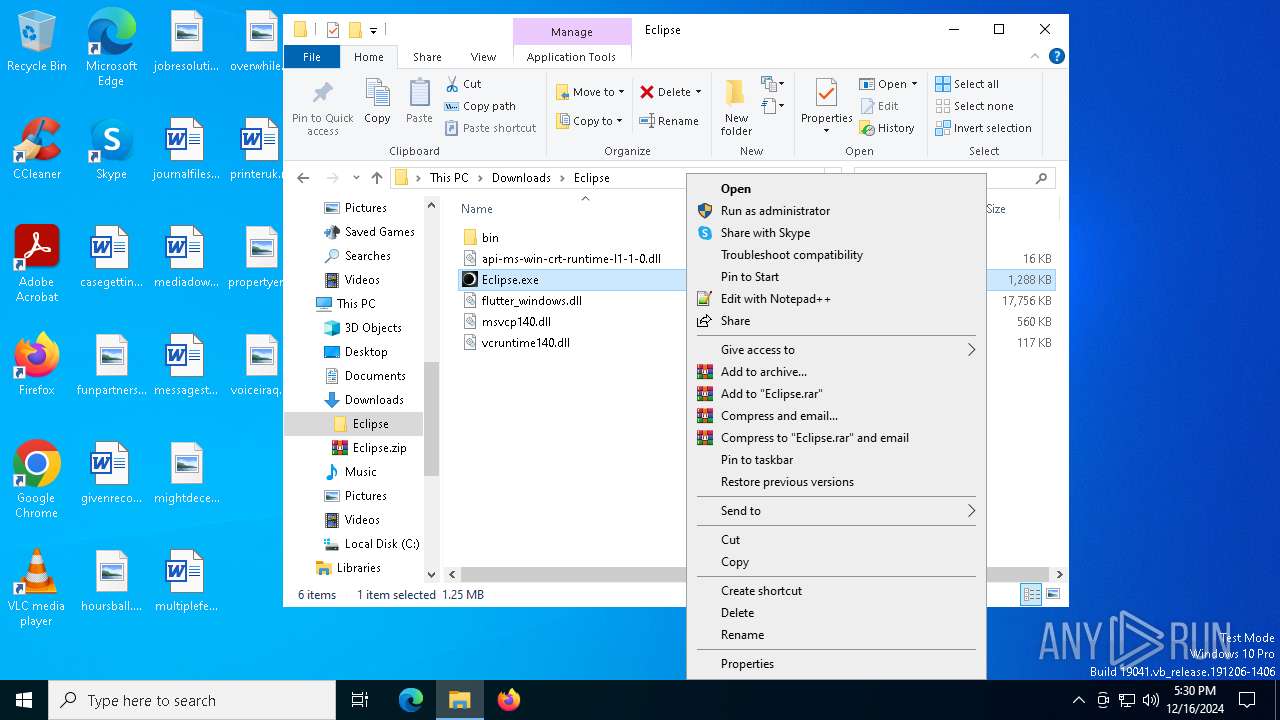
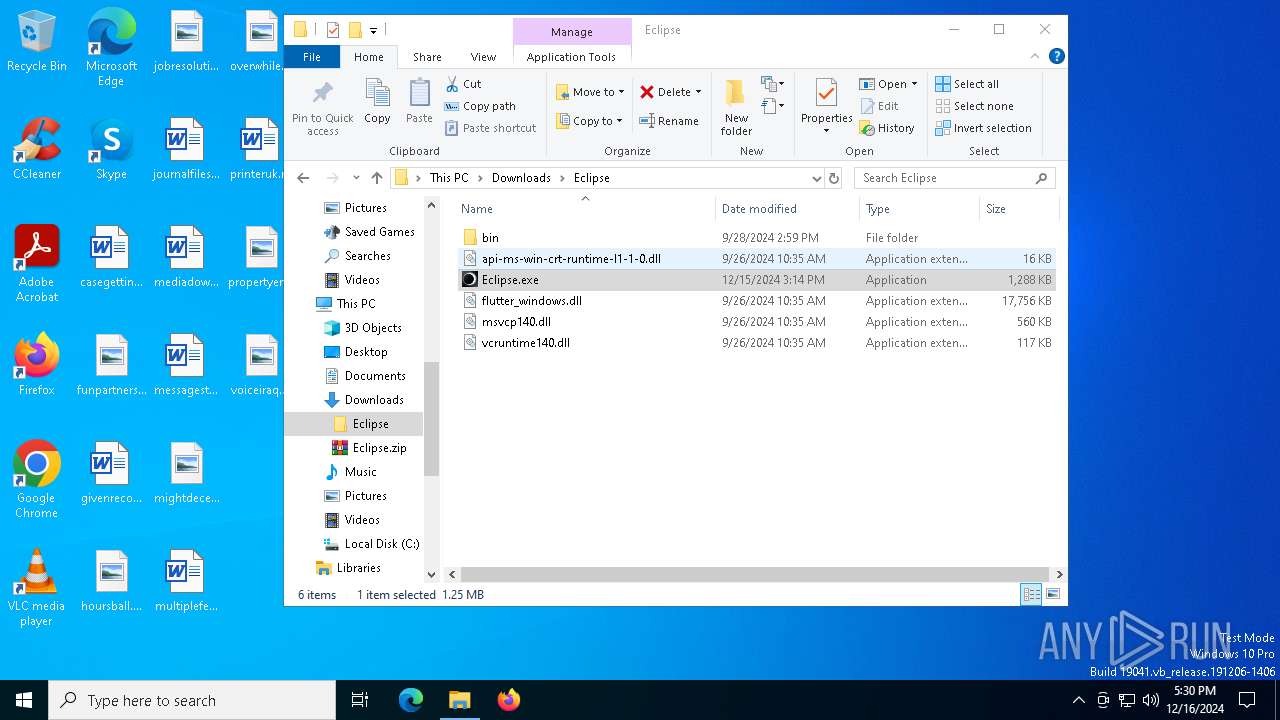
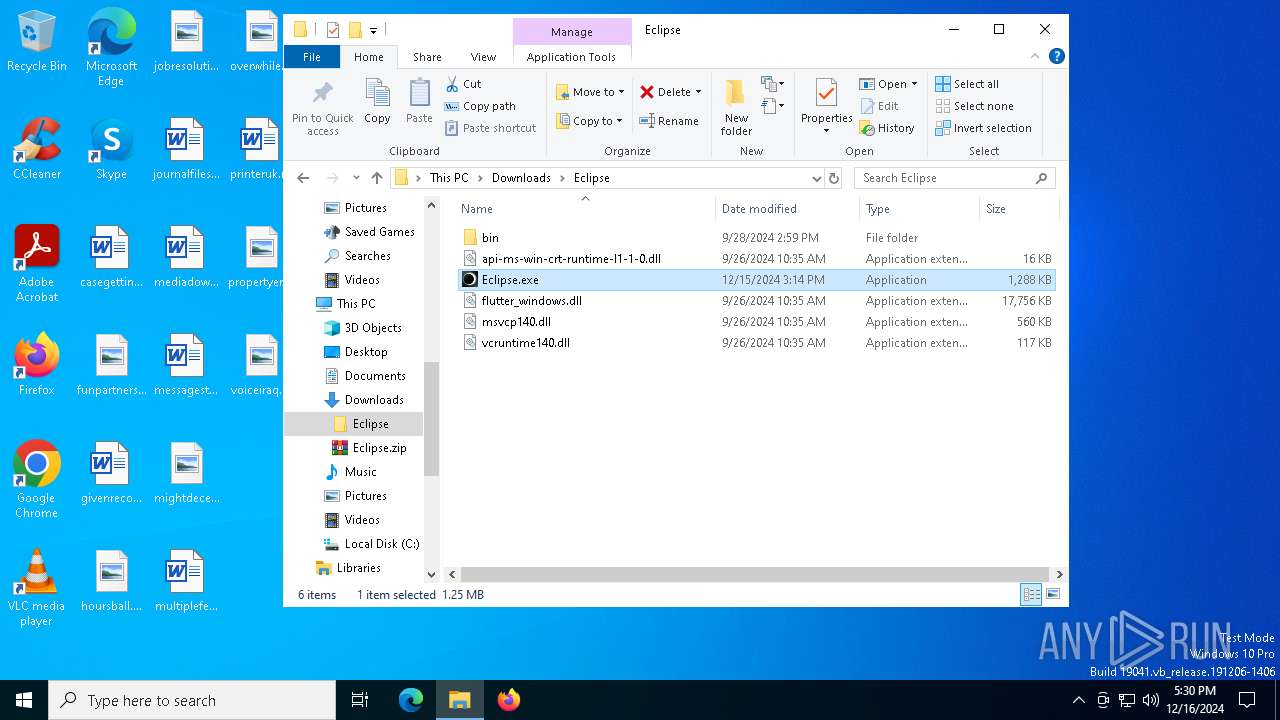
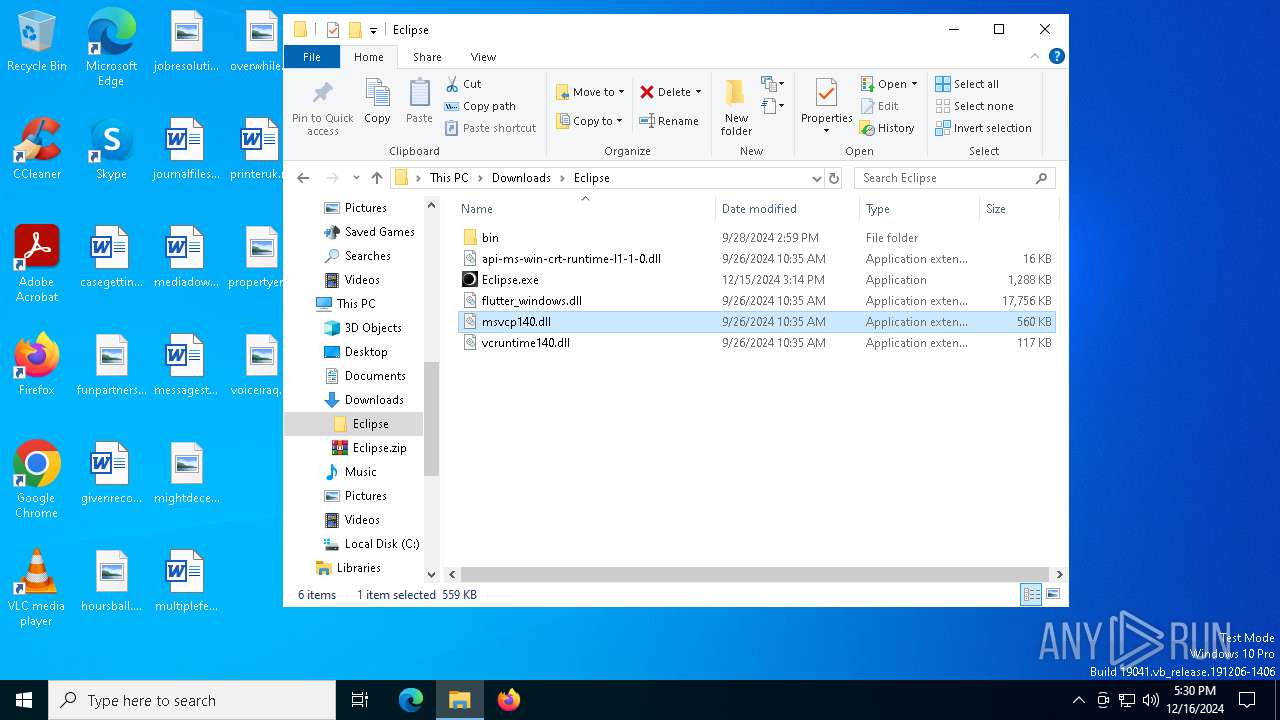
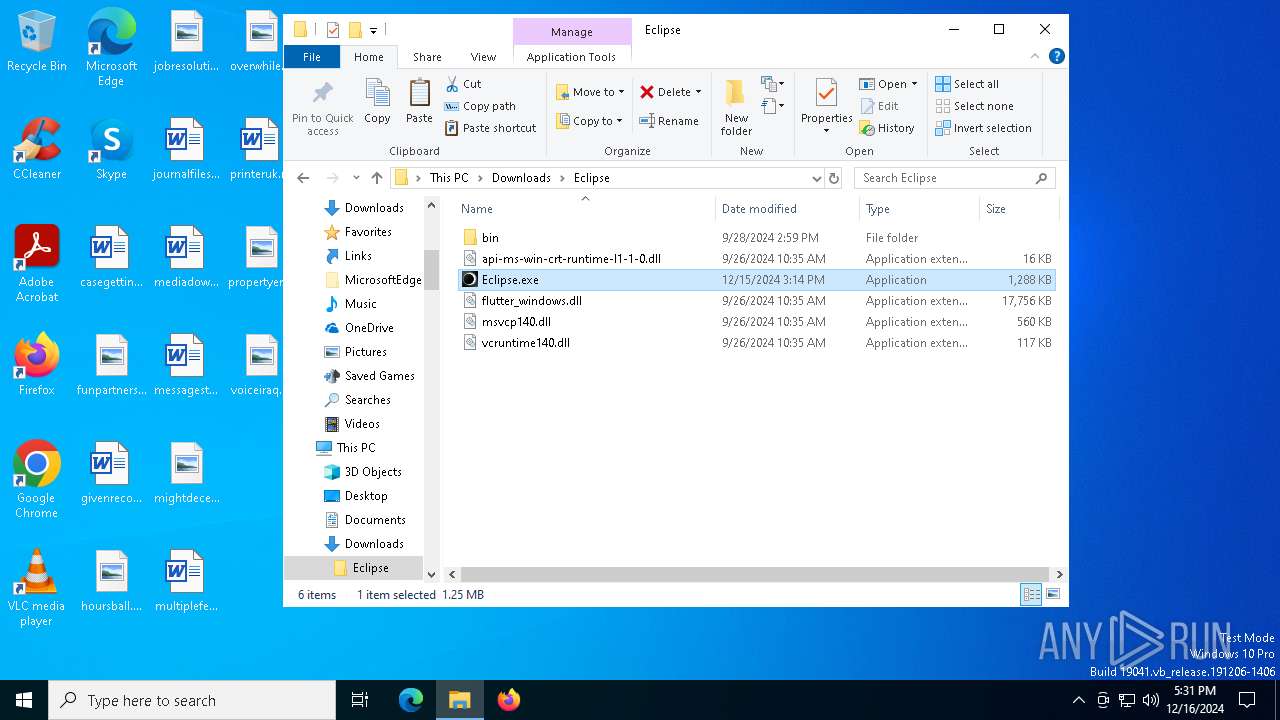
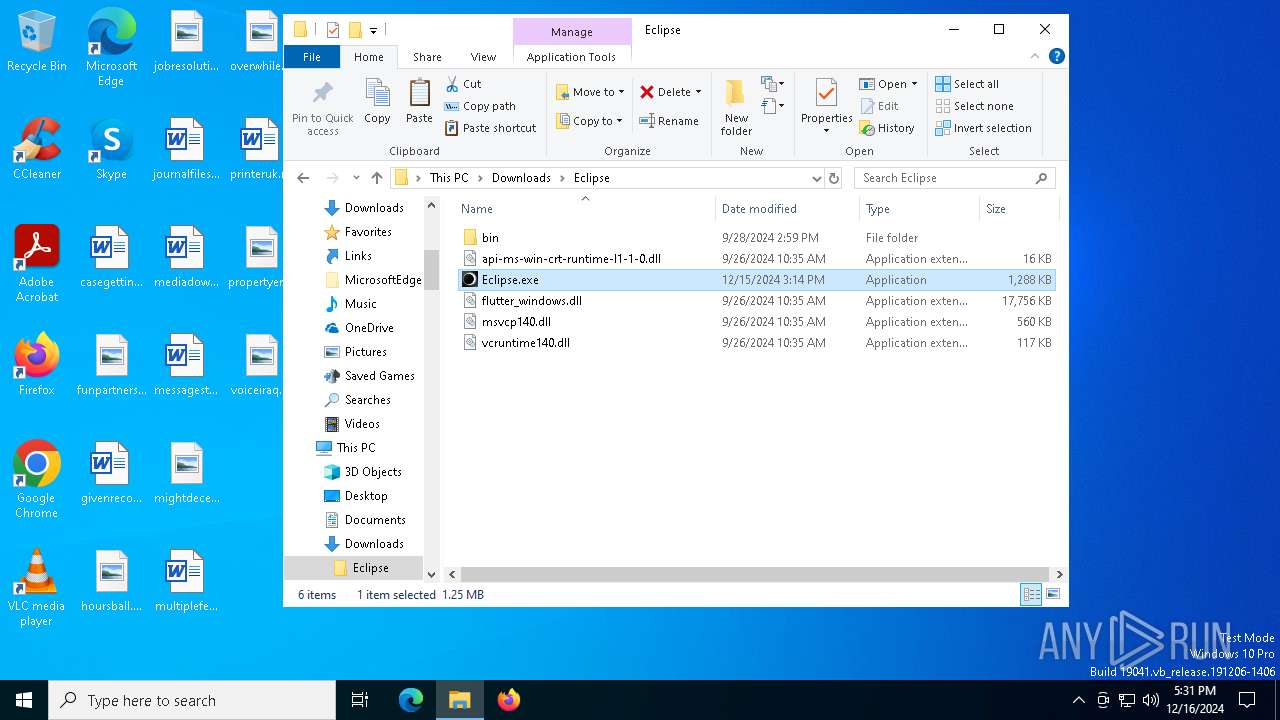
Manual execution by a user
- WinRAR.exe (PID: 7488)
- Eclipsе.exe (PID: 6164)
- Eclipsе.exe (PID: 6832)
- Eclipsе.exe (PID: 6096)
- notepad.exe (PID: 7340)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7488)
The sample compiled with english language support
- WinRAR.exe (PID: 7488)
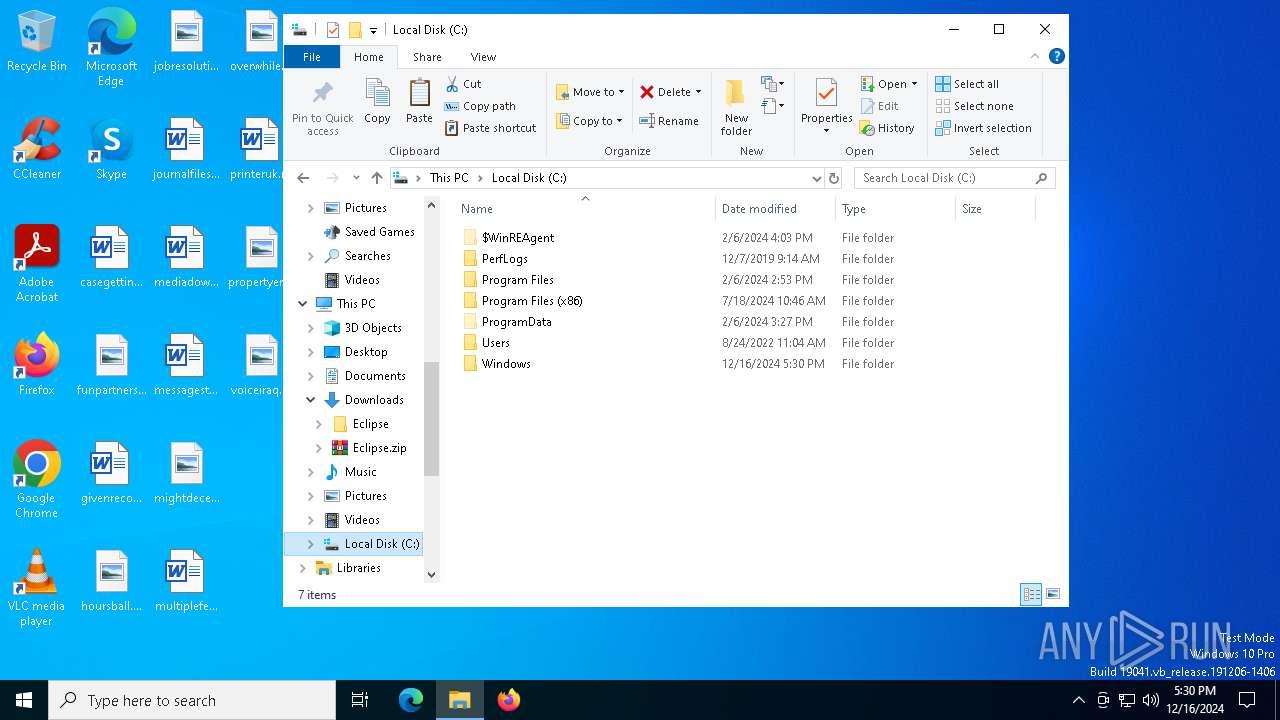
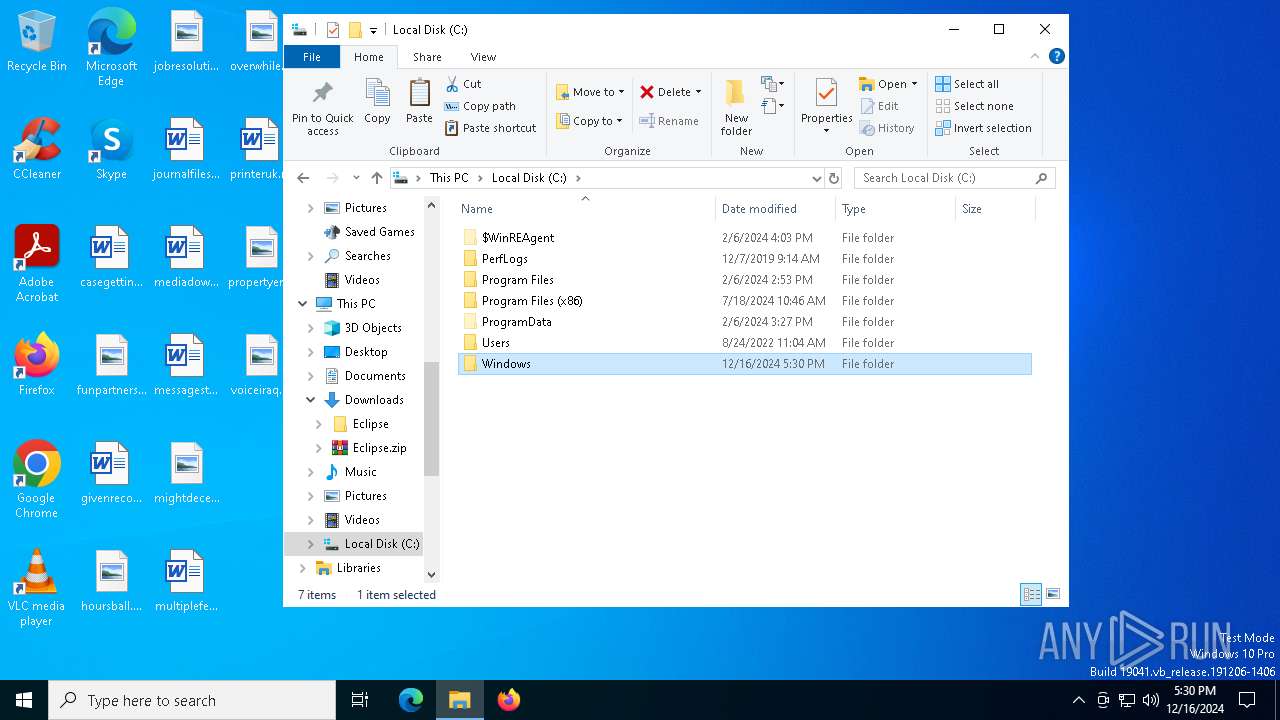
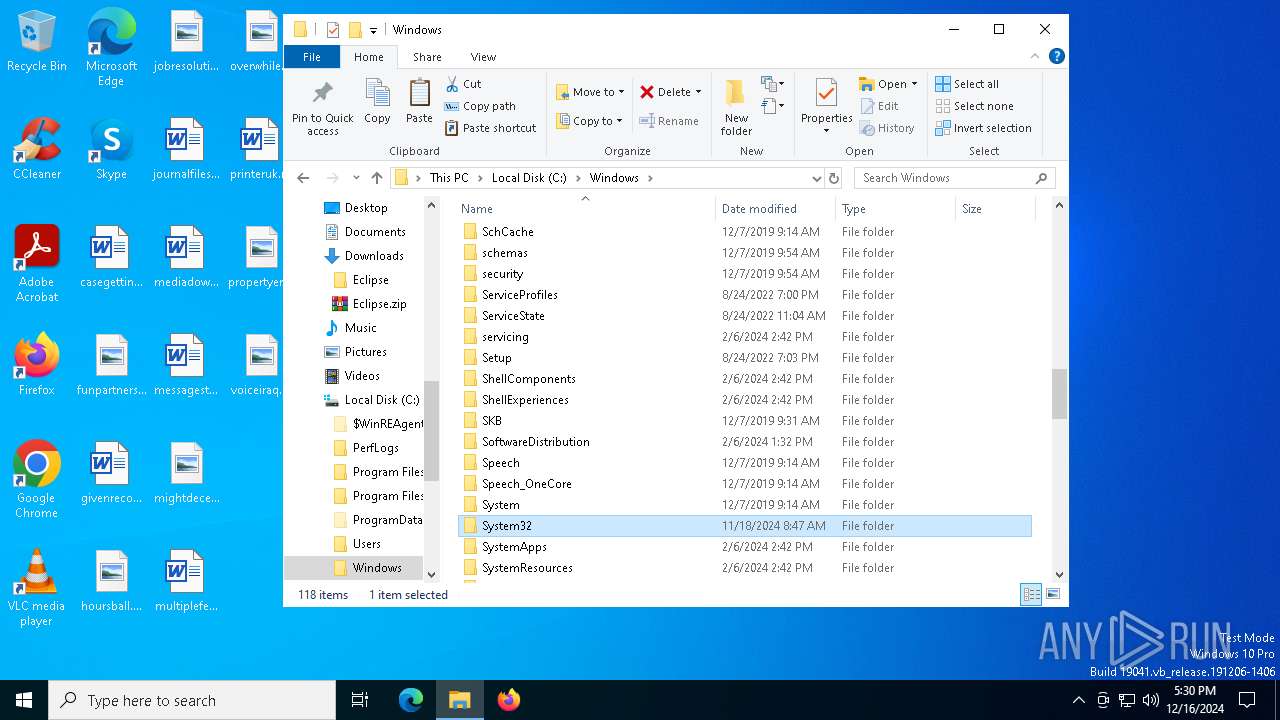
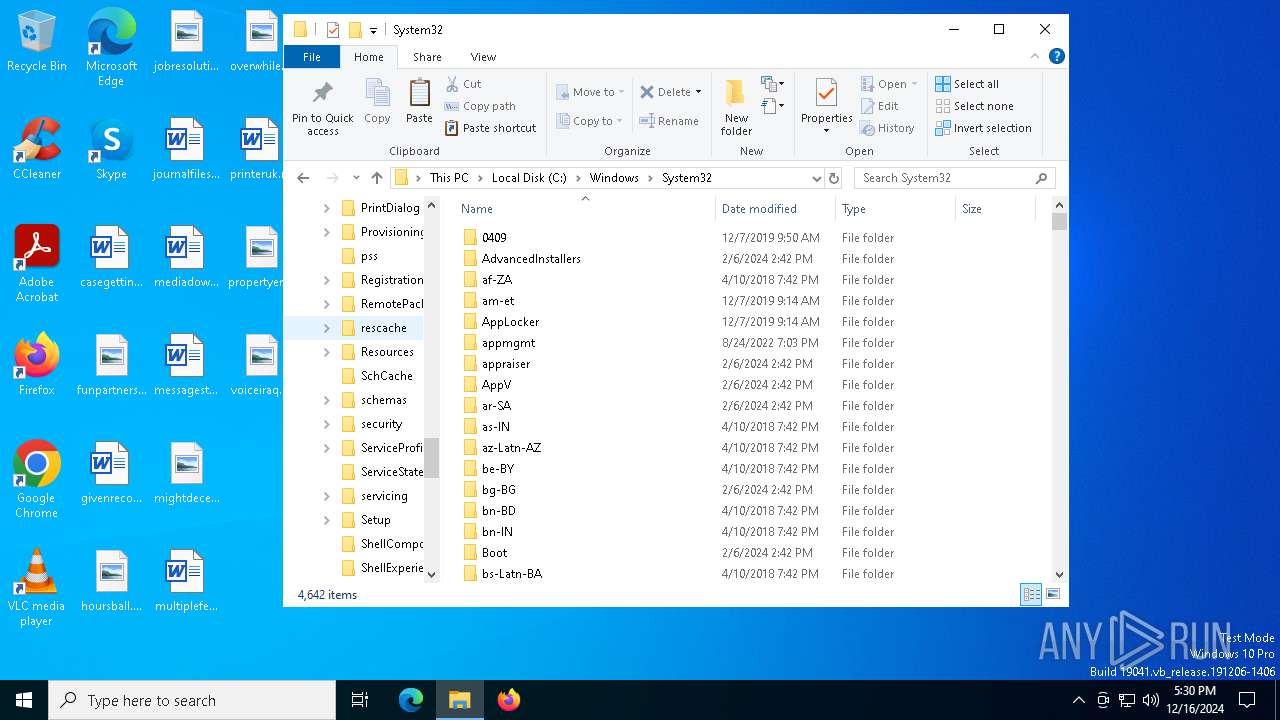
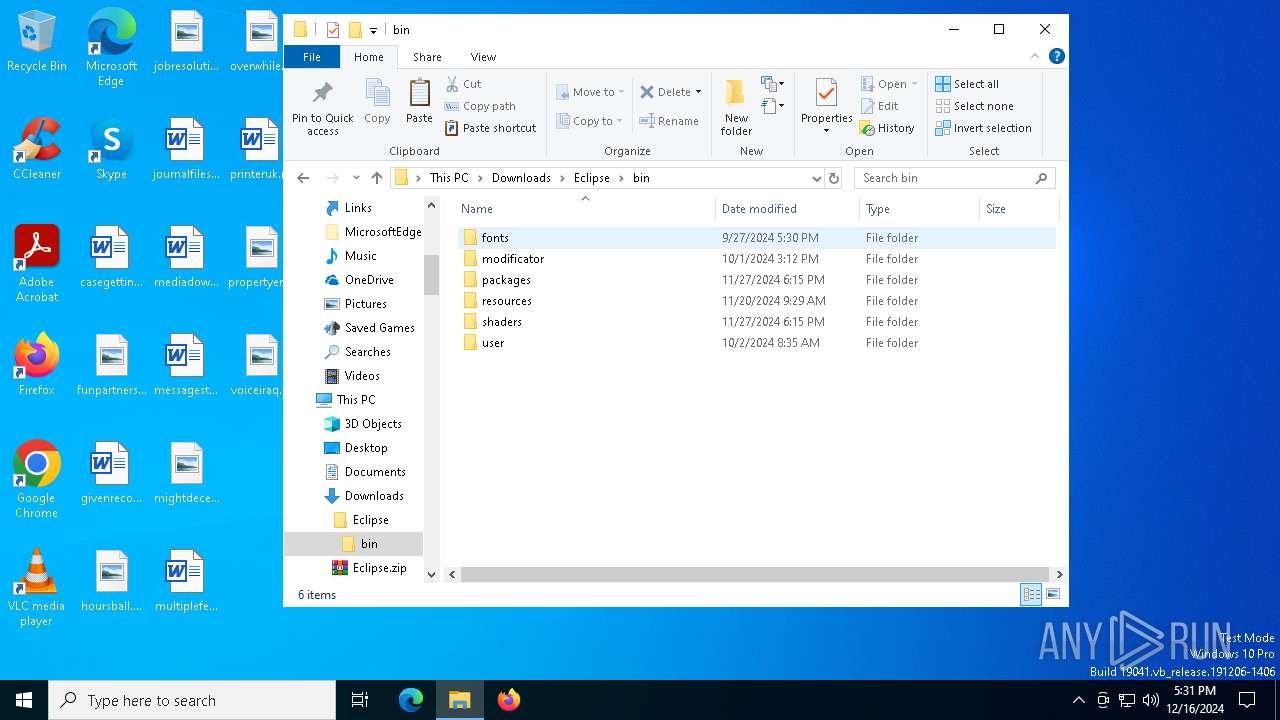
Creates a new folder
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7108)
- cmd.exe (PID: 2736)
Reads the software policy settings
- Achieved.com (PID: 7268)
- Achieved.com (PID: 8044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
232
Monitored processes
100
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --mojo-platform-channel-handle=6284 --field-trial-handle=2304,i,8155456712052296158,17923287116307315254,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1172 | Achieved.com t | C:\Users\admin\AppData\Local\Temp\256910\Achieved.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 1228 | cmd /c copy /b ..\Bracelets + ..\Application + ..\Saint + ..\Burden + ..\Gentleman + ..\Mission + ..\Gossip t | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1856 | findstr "AvastUI AVGUI bdservicehost nsWscSvc ekrn SophosHealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2120 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5276 --field-trial-handle=2324,i,17830174413582069806,7558622976362054623,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6112 --field-trial-handle=2304,i,8155456712052296158,17923287116307315254,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2212 | findstr "AvastUI AVGUI bdservicehost nsWscSvc ekrn SophosHealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2260 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2628 --field-trial-handle=2324,i,17830174413582069806,7558622976362054623,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
11 957
Read events
11 919
Write events
38
Delete events
0
Modification events
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 60002ACDFC872F00 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328540 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {37E9799F-EEC4-4487-9117-ACF32B681CF7} | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B02F35CDFC872F00 | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328540 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {256DDDEA-2D14-41C2-BB05-6DEFC9BCB7EF} | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328540 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F297F45E-3702-4094-AEBB-DF017FB90D4D} | |||
| (PID) Process: | (6348) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328540 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BB0A1A2F-EB3D-406C-B655-438989C0BACB} | |||
Executable files
22
Suspicious files
336
Text files
287
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135353.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135353.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135353.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135363.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135363.TMP | — | |
MD5:— | SHA256:— | |||
| 6348 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
235
DNS requests
218
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7076 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.24:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7400 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7400 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7076 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8112 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a439b687-6b63-46da-8116-1fe1bf7ca8a6?P1=1734568700&P2=404&P3=2&P4=Z3dcUxPgQ5OT9NLphzBo7JHJQ0wJAFzsTLtPp7c9EXYx0ynWxUmiv%2f%2fj0D1AHFBVk1IfJq0W9pPUm9HJogo5%2bA%3d%3d | unknown | — | — | whitelisted |
8112 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a439b687-6b63-46da-8116-1fe1bf7ca8a6?P1=1734568700&P2=404&P3=2&P4=Z3dcUxPgQ5OT9NLphzBo7JHJQ0wJAFzsTLtPp7c9EXYx0ynWxUmiv%2f%2fj0D1AHFBVk1IfJq0W9pPUm9HJogo5%2bA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2548 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.24:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.135:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6348 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
eclipse.framer.ai |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
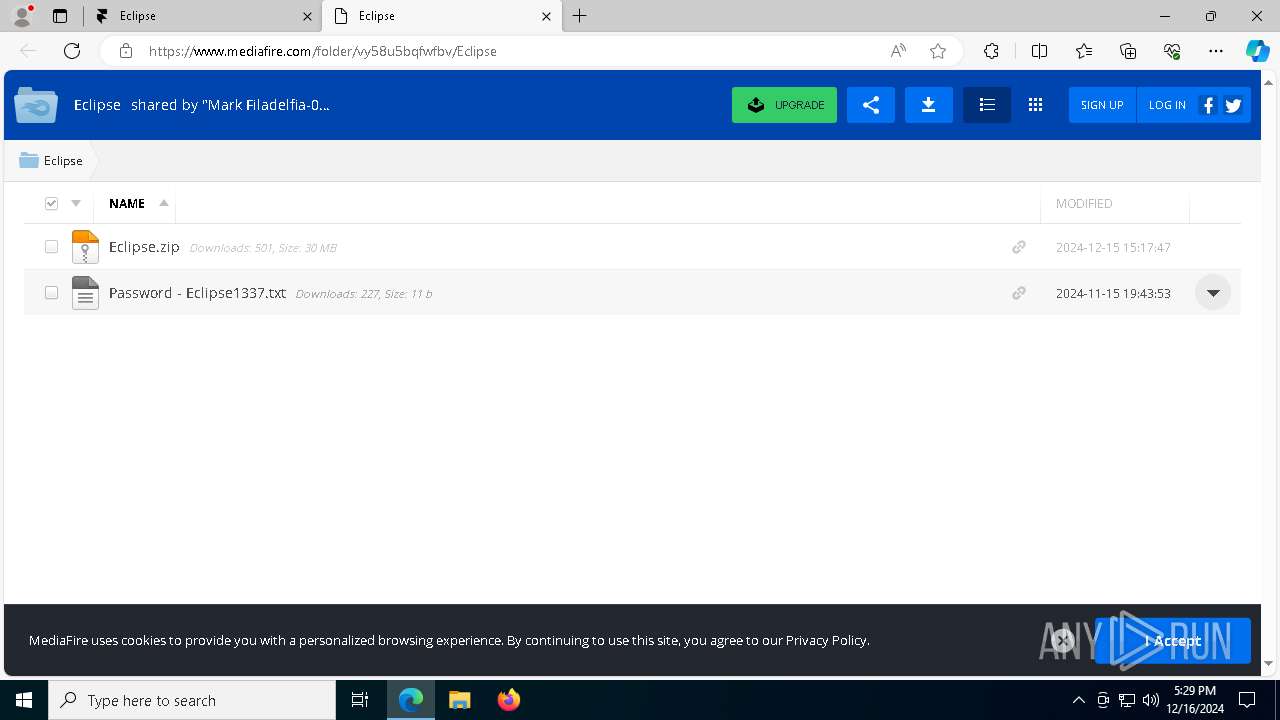
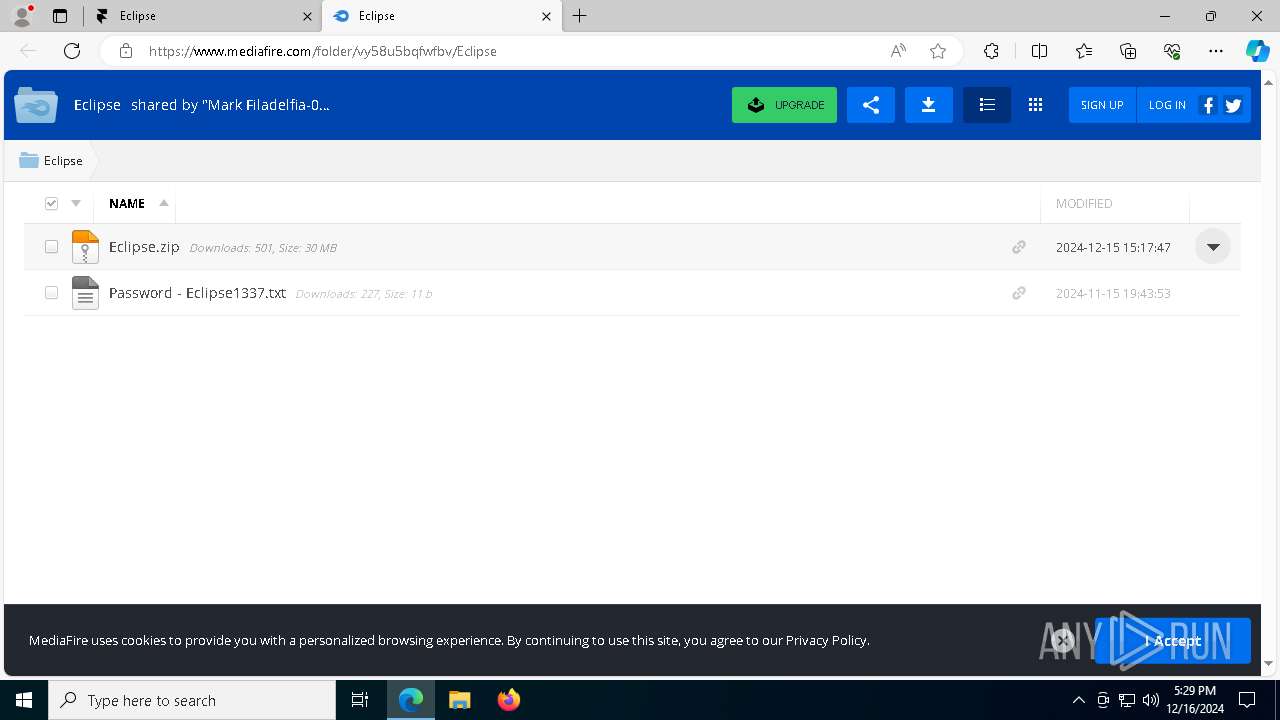
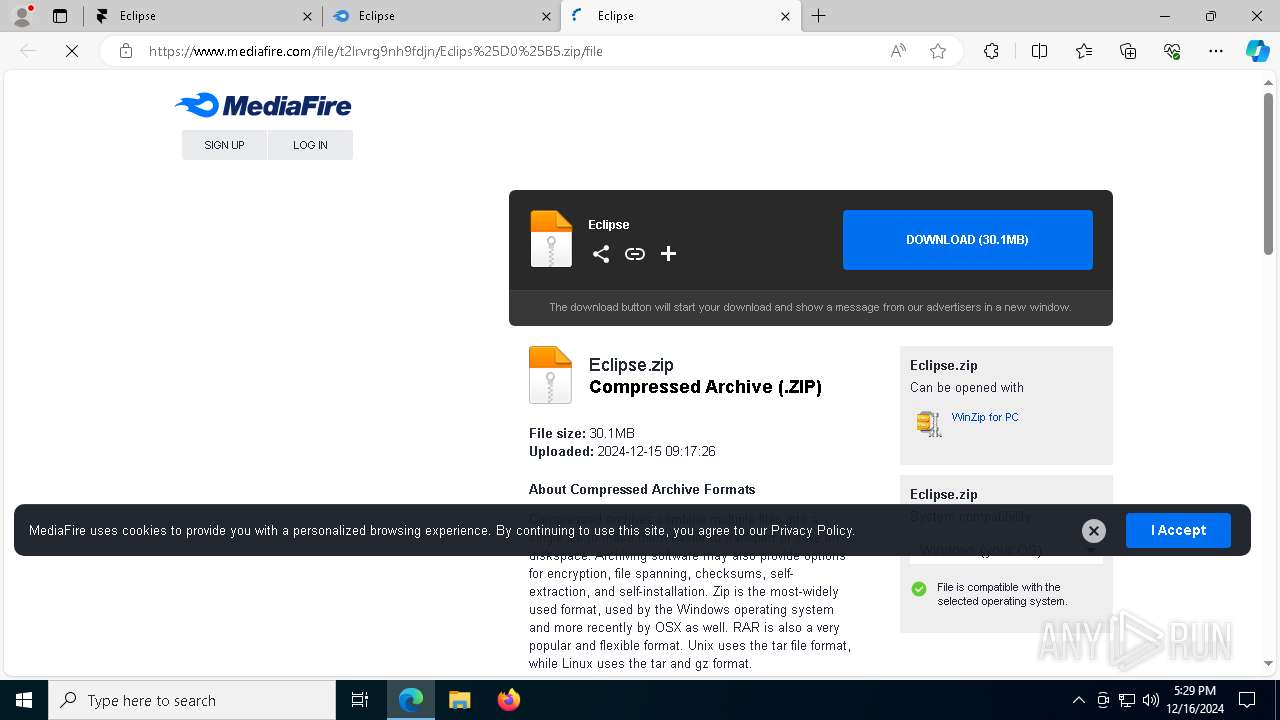
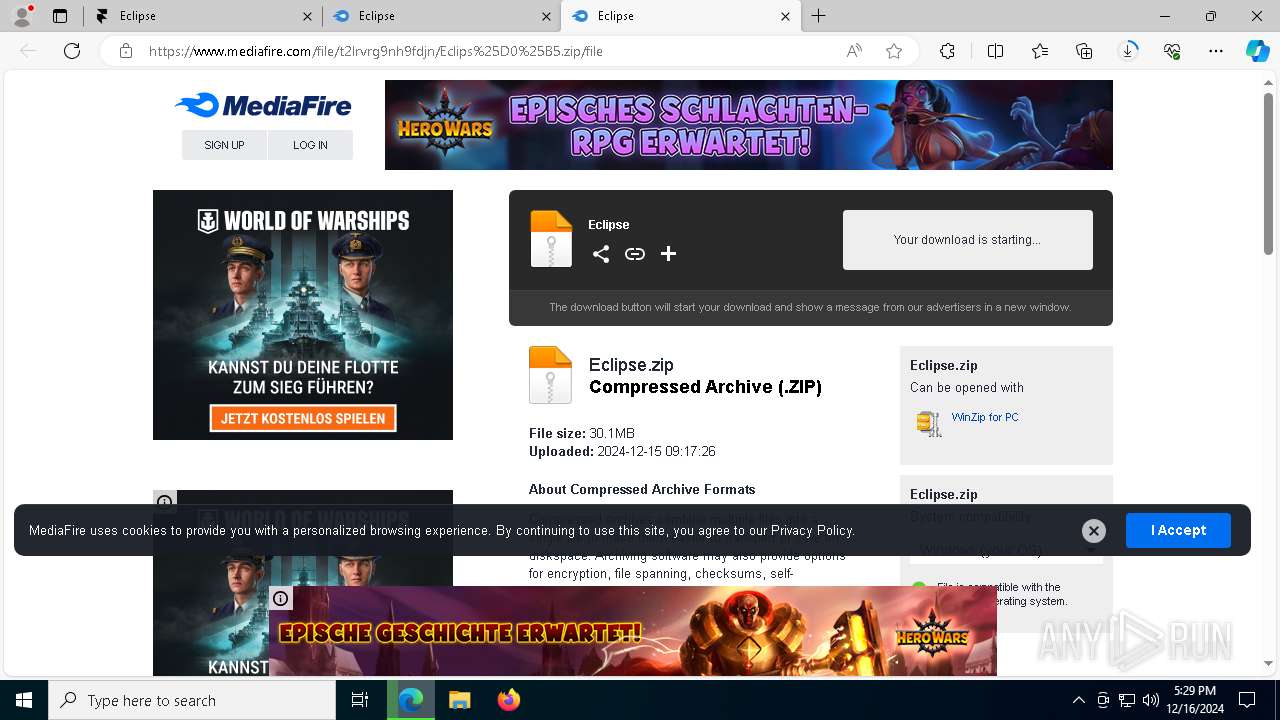
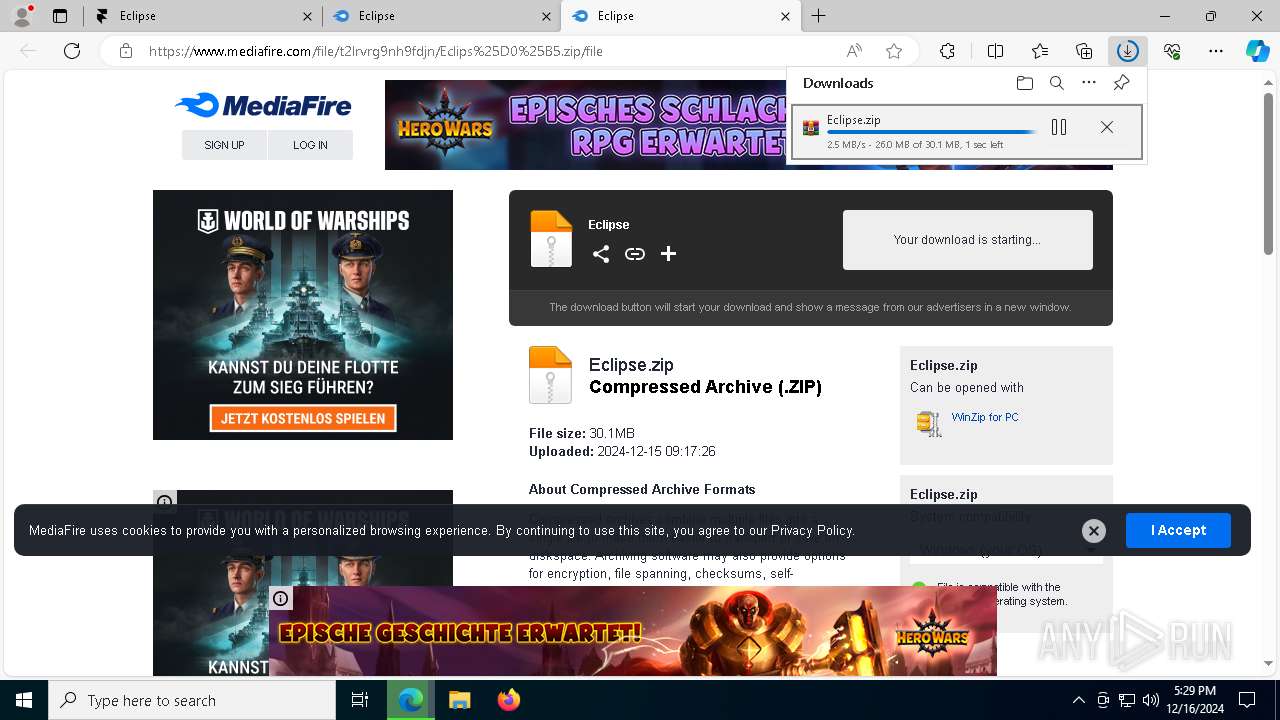
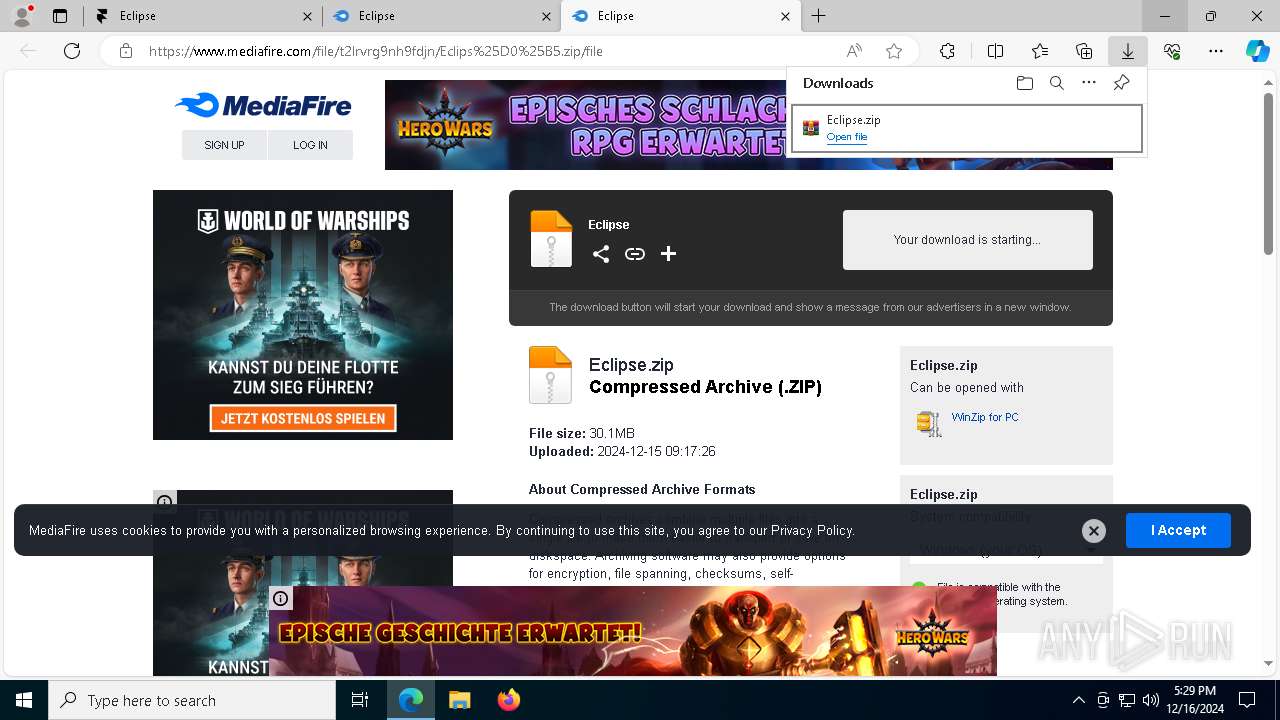
6684 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6684 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6684 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6684 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6684 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6684 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6684 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6684 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5 ETPRO signatures available at the full report