| File name: | 6cbbc0f1be8e61da11cec2e930d8e0a9.exe |
| Full analysis: | https://app.any.run/tasks/0cdbc055-ab7b-4795-8cef-da96fdc8cbb6 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 29, 2025, 05:54:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 6CBBC0F1BE8E61DA11CEC2E930D8E0A9 |
| SHA1: | 89A6ABF9D1CFAB1FA39FB8C65A124E39A24DB1AE |
| SHA256: | 90EDEE3419127E0724CB8B9EA5FEF8466FAC1D29AF4D32B182E0068E2570EAAA |
| SSDEEP: | 98304:U0IvQc2IEi0OcoTxtN2IRYN3WqJMTAFuEGLrXNTR0K2uQTkClpH7ESsJGgWQc/fR:22c |
MALICIOUS
LUMMA mutex has been found
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- MSBuild.exe (PID: 5352)
- MSBuild.exe (PID: 4528)
- MSBuild.exe (PID: 872)
Actions looks like stealing of personal data
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- MSBuild.exe (PID: 5352)
- MSBuild.exe (PID: 4528)
- MSBuild.exe (PID: 872)
LUMMA has been detected (YARA)
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 5352)
- MSBuild.exe (PID: 6760)
- MSBuild.exe (PID: 496)
- zb7jDew.exe (PID: 9124)
Connects to the CnC server
- svchost.exe (PID: 2196)
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
AMADEY has been found (auto)
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- VOWFGO964SM4LIK16O5FG.exe (PID: 6424)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 3156)
AMADEY has been detected (SURICATA)
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
AMADEY mutex has been found
- amnew.exe (PID: 4120)
- laren.exe (PID: 6068)
AMADEY has been detected (YARA)
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
Changes the autorun value in the registry
- saved.exe (PID: 2148)
Changes the login/logoff helper path in the registry
- reg.exe (PID: 4120)
Possible tool for stealing has been detected
- firefox.exe (PID: 3396)
- de2bc57ed4.exe (PID: 2088)
- de2bc57ed4.exe (PID: 6708)
- firefox.exe (PID: 3968)
- firefox.exe (PID: 7688)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6816)
- cmd.exe (PID: 616)
Run PowerShell with an invisible window
- powershell.exe (PID: 3156)
- powershell.exe (PID: 2416)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 7896)
- powershell.exe (PID: 6488)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 8300)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 7504)
Executing a file with an untrusted certificate
- WireGuard.exe (PID: 7396)
- WireGuard.exe (PID: 7840)
- WireGuard.exe (PID: 5044)
- core.exe (PID: 7144)
Bypass execution policy to execute commands
- powershell.exe (PID: 6488)
- powershell.exe (PID: 7684)
- powershell.exe (PID: 4980)
- powershell.exe (PID: 8300)
- powershell.exe (PID: 4560)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2152)
- powershell.exe (PID: 4980)
- core.exe (PID: 7144)
Stealers network behavior
- svchost.exe (PID: 2196)
GENERIC has been found (auto)
- 595031cb1c.exe (PID: 8096)
UPATRE has been detected (SURICATA)
- svchost.exe (PID: 3828)
- svchost.exe (PID: 8624)
GCLEANER has been detected (SURICATA)
- svchost015.exe (PID: 8488)
- svchost015.exe (PID: 8808)
STEALER has been found (auto)
- saved.exe (PID: 2148)
SUSPICIOUS
Reads the BIOS version
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
Potential Corporate Privacy Violation
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- saved.exe (PID: 2148)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- powershell.exe (PID: 7504)
- laren.exe (PID: 6068)
- svchost015.exe (PID: 8488)
Searches for installed software
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- MSBuild.exe (PID: 5352)
- MSBuild.exe (PID: 4528)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
- MSBuild.exe (PID: 5352)
- MSBuild.exe (PID: 6760)
- MSBuild.exe (PID: 496)
- zb7jDew.exe (PID: 9124)
Executable content was dropped or overwritten
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- VOWFGO964SM4LIK16O5FG.exe (PID: 6424)
- amnew.exe (PID: 4120)
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- cmd.exe (PID: 5384)
- powershell.exe (PID: 3156)
- powershell.exe (PID: 7504)
- WireGuard.exe (PID: 8180)
- 62ece15dc5.exe (PID: 7760)
- 62ece15dc5.tmp (PID: 2268)
- 595031cb1c.exe (PID: 8096)
- FskyITkMbcq.exe (PID: 8580)
- svchost015.exe (PID: 8488)
- FskyITkMbcq.tmp (PID: 5204)
- svchost015.exe (PID: 8808)
- filelistcreatorassist15.exe (PID: 9276)
Reads security settings of Internet Explorer
- VOWFGO964SM4LIK16O5FG.exe (PID: 6424)
- saved.exe (PID: 2148)
- amnew.exe (PID: 4120)
- laren.exe (PID: 6068)
Connects to the server without a host name
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 3156)
- svchost015.exe (PID: 8488)
- svchost015.exe (PID: 8808)
Process requests binary or script from the Internet
- saved.exe (PID: 2148)
- 5511ade474.exe (PID: 3304)
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- 5511ade474.exe (PID: 2092)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 3156)
- laren.exe (PID: 6068)
Starts itself from another location
- VOWFGO964SM4LIK16O5FG.exe (PID: 6424)
- amnew.exe (PID: 4120)
Starts CMD.EXE for commands execution
- JSEVGJV.exe (PID: 536)
- b938f7a239.exe (PID: 2236)
- b938f7a239.exe (PID: 3024)
- WireGuard.exe (PID: 8180)
- WireGuard.exe (PID: 7396)
- WireGuard.exe (PID: 5044)
- WireGuard.exe (PID: 7840)
- saved.exe (PID: 2148)
- JSEVGJV.exe (PID: 8240)
Hides command output
- cmd.exe (PID: 6724)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 8888)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 6724)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 8888)
There is functionality for taking screenshot (YARA)
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
There is functionality for enable RDP (YARA)
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
Process drops legitimate windows executable
- laren.exe (PID: 6068)
- saved.exe (PID: 2148)
- FskyITkMbcq.tmp (PID: 5204)
Starts a Microsoft application from unusual location
- Alex1234.exe (PID: 4300)
- Cron1.exe (PID: 1388)
- Cron2.exe (PID: 3024)
- 45c51f175f.exe (PID: 7632)
- 47Q6wZM.exe (PID: 2268)
- VisualCode.exe (PID: 8756)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6724)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 5352)
- MSBuild.exe (PID: 6760)
- powershell.exe (PID: 6488)
- MSBuild.exe (PID: 8880)
Uses TASKKILL.EXE to kill Browsers
- de2bc57ed4.exe (PID: 2088)
- de2bc57ed4.exe (PID: 6708)
Uses TASKKILL.EXE to kill process
- de2bc57ed4.exe (PID: 2088)
- de2bc57ed4.exe (PID: 6708)
Starts process via Powershell
- powershell.exe (PID: 3156)
- powershell.exe (PID: 2416)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 7896)
- powershell.exe (PID: 4980)
Found IP address in command line
- powershell.exe (PID: 3156)
- powershell.exe (PID: 2416)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 7896)
Probably download files using WebClient
- mshta.exe (PID: 680)
- mshta.exe (PID: 6760)
- mshta.exe (PID: 6676)
- mshta.exe (PID: 7788)
Manipulates environment variables
- powershell.exe (PID: 2416)
- powershell.exe (PID: 3156)
- powershell.exe (PID: 7504)
- powershell.exe (PID: 7896)
- powershell.exe (PID: 6488)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 6760)
- mshta.exe (PID: 680)
- mshta.exe (PID: 6676)
- mshta.exe (PID: 7788)
- cmd.exe (PID: 2152)
- powershell.exe (PID: 4980)
- filelistcreatorassist15.exe (PID: 9276)
- core.exe (PID: 7144)
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 732)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 7284)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 7456)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 720)
- cmd.exe (PID: 4812)
Uses WMIC.EXE to obtain CPU information
- cmd.exe (PID: 4528)
- cmd.exe (PID: 7852)
- cmd.exe (PID: 4756)
- cmd.exe (PID: 4728)
Application launched itself
- WireGuard.exe (PID: 8180)
- powershell.exe (PID: 4980)
The process executes via Task Scheduler
- laren.exe (PID: 5164)
- saved.exe (PID: 7476)
- laren.exe (PID: 5172)
- saved.exe (PID: 9784)
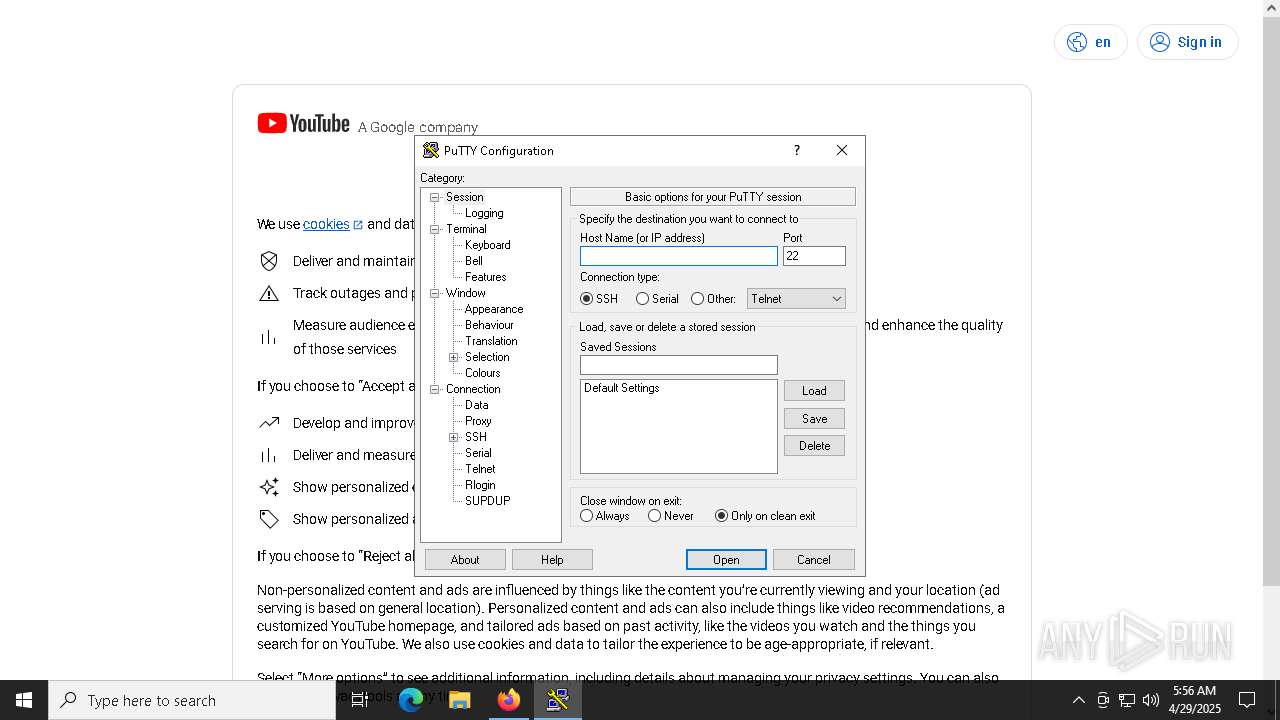
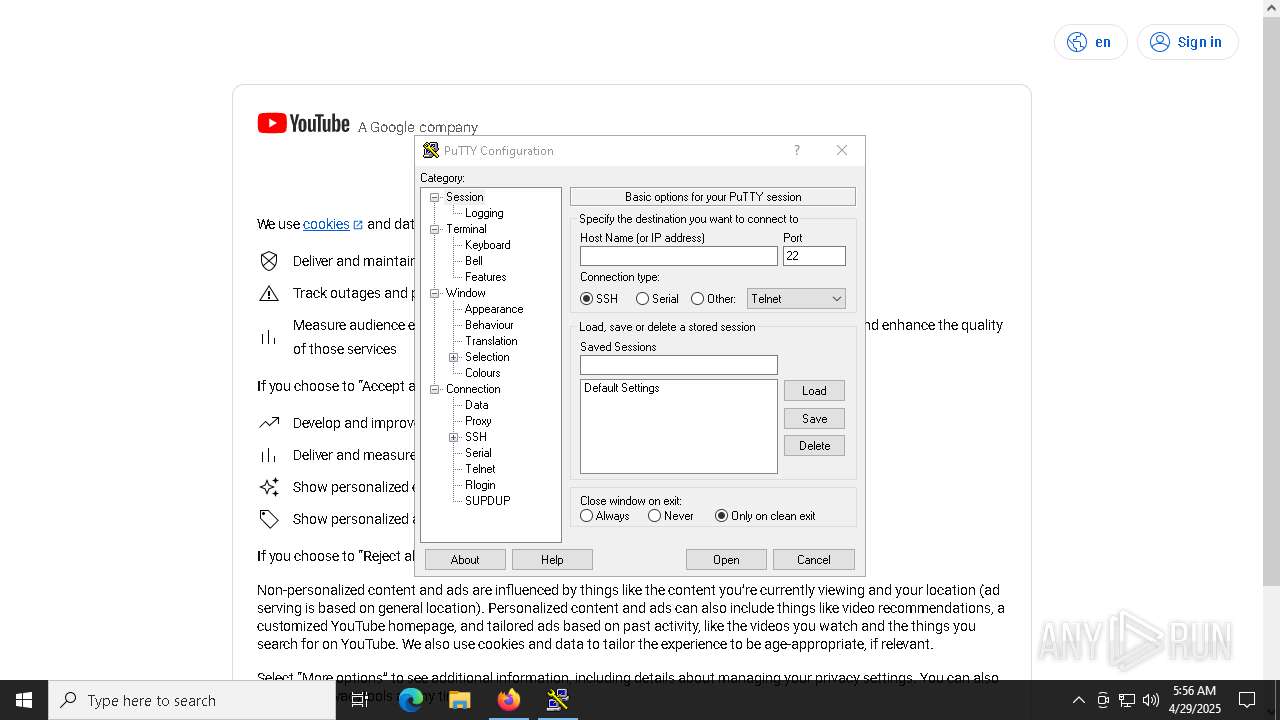
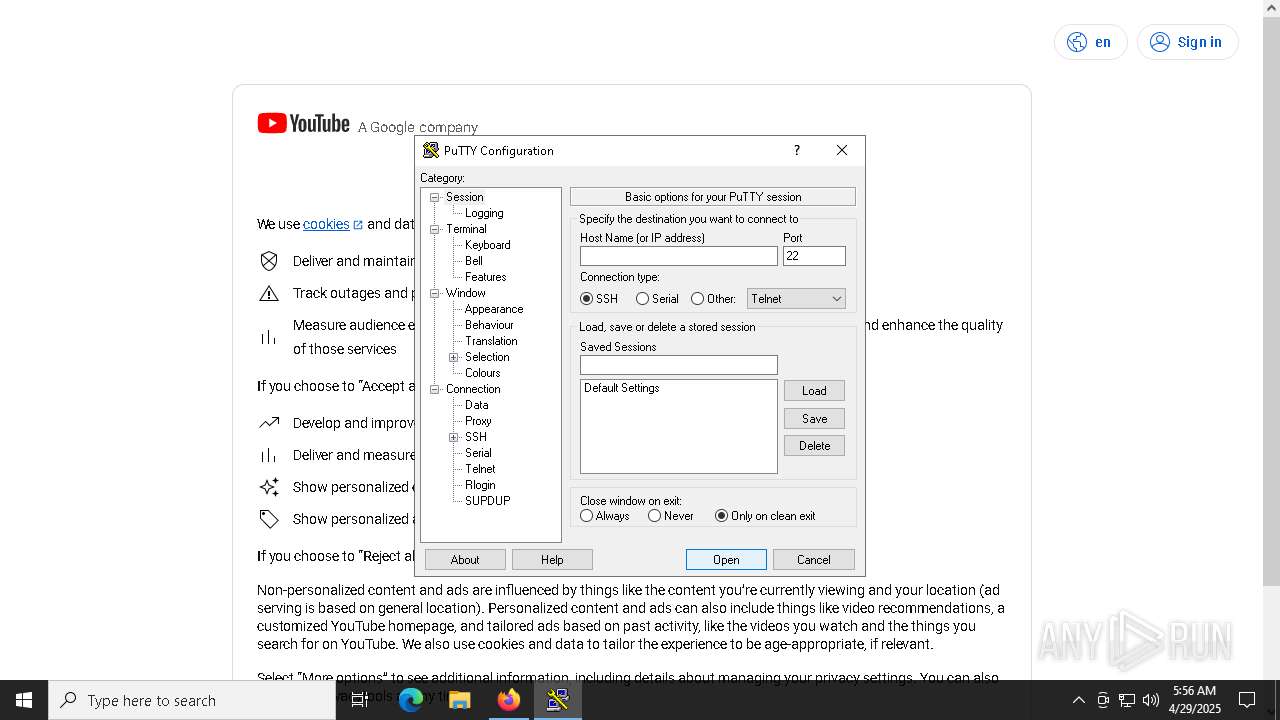
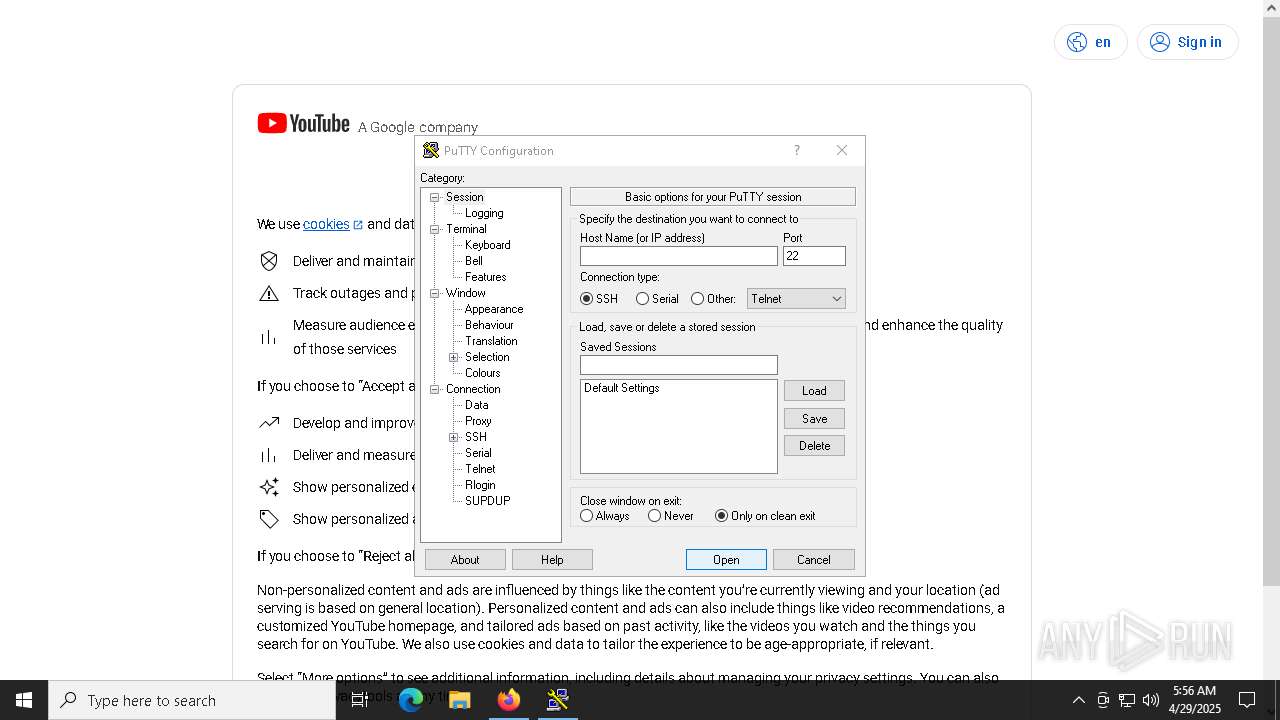
PUTTY has been detected
- putty.exe (PID: 3020)
Executing commands from ".cmd" file
- saved.exe (PID: 2148)
The process checks if current user has admin rights
- cmd.exe (PID: 2152)
The process executes Powershell scripts
- cmd.exe (PID: 2152)
- powershell.exe (PID: 4980)
Executes application which crashes
- 5bf43363e1.exe (PID: 236)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2152)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2152)
Checks for external IP
- svchost.exe (PID: 2196)
- powershell.exe (PID: 8300)
Connects to unusual port
- svchost.exe (PID: 3828)
- svchost.exe (PID: 8624)
The process drops C-runtime libraries
- FskyITkMbcq.tmp (PID: 5204)
INFO
Checks supported languages
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- VOWFGO964SM4LIK16O5FG.exe (PID: 6424)
- saved.exe (PID: 2148)
- JSEVGJV.exe (PID: 536)
- amnew.exe (PID: 4120)
- laren.exe (PID: 6068)
- 5511ade474.exe (PID: 3304)
- Alex1234.exe (PID: 4300)
- 5511ade474.exe (PID: 2092)
- de2bc57ed4.exe (PID: 2088)
- Cron1.exe (PID: 1388)
- MSBuild.exe (PID: 5352)
- T6ZW7OQL5SIDMPNRPM.exe (PID: 2152)
- MSBuild.exe (PID: 4528)
- HZU3NS1S9ZFTPR5M8ODZBVPMGIYB1K.exe (PID: 6752)
- Cron2.exe (PID: 3024)
- de2bc57ed4.exe (PID: 6708)
- b938f7a239.exe (PID: 2236)
- MSBuild.exe (PID: 872)
- b938f7a239.exe (PID: 3024)
- WireGuard.exe (PID: 8180)
- 45c51f175f.exe (PID: 7632)
Reads the computer name
- VOWFGO964SM4LIK16O5FG.exe (PID: 6424)
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
- JSEVGJV.exe (PID: 536)
- amnew.exe (PID: 4120)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- MSBuild.exe (PID: 5352)
- de2bc57ed4.exe (PID: 2088)
- MSBuild.exe (PID: 4528)
- de2bc57ed4.exe (PID: 6708)
- b938f7a239.exe (PID: 2236)
- MSBuild.exe (PID: 872)
- b938f7a239.exe (PID: 3024)
Reads the software policy settings
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- laren.exe (PID: 6068)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- MSBuild.exe (PID: 5352)
- MSBuild.exe (PID: 4528)
- MSBuild.exe (PID: 872)
Themida protector has been detected
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
Create files in a temporary directory
- 6cbbc0f1be8e61da11cec2e930d8e0a9.exe (PID: 6048)
- VOWFGO964SM4LIK16O5FG.exe (PID: 6424)
- saved.exe (PID: 2148)
- amnew.exe (PID: 4120)
- laren.exe (PID: 6068)
- 5511ade474.exe (PID: 3304)
- 5511ade474.exe (PID: 2092)
- b938f7a239.exe (PID: 3024)
- b938f7a239.exe (PID: 2236)
Process checks computer location settings
- VOWFGO964SM4LIK16O5FG.exe (PID: 6424)
- saved.exe (PID: 2148)
- amnew.exe (PID: 4120)
- laren.exe (PID: 6068)
Checks proxy server information
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
Creates files or folders in the user directory
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
The sample compiled with english language support
- saved.exe (PID: 2148)
- laren.exe (PID: 6068)
- cmd.exe (PID: 5384)
- WireGuard.exe (PID: 8180)
- 62ece15dc5.tmp (PID: 2268)
- 595031cb1c.exe (PID: 8096)
- FskyITkMbcq.tmp (PID: 5204)
NirSoft software is detected
- JSEVGJV.exe (PID: 536)
- DNS.exe (PID: 6852)
- JSEVGJV.exe (PID: 8240)
Reads the machine GUID from the registry
- JSEVGJV.exe (PID: 536)
- laren.exe (PID: 6068)
Auto-launch of the file from Registry key
- saved.exe (PID: 2148)
Manual execution by a user
- 5511ade474.exe (PID: 2092)
- de2bc57ed4.exe (PID: 6708)
- mshta.exe (PID: 6760)
- b938f7a239.exe (PID: 3024)
- mshta.exe (PID: 7788)
- svchost.exe (PID: 3828)
- svchost.exe (PID: 8624)
Reads mouse settings
- de2bc57ed4.exe (PID: 2088)
- de2bc57ed4.exe (PID: 6708)
- b938f7a239.exe (PID: 2236)
- b938f7a239.exe (PID: 3024)
Application launched itself
- firefox.exe (PID: 3396)
- firefox.exe (PID: 3968)
- firefox.exe (PID: 6436)
- firefox.exe (PID: 7688)
- firefox.exe (PID: 6252)
- chrome.exe (PID: 9864)
- chrome.exe (PID: 8272)
- msedge.exe (PID: 8248)
Auto-launch of the file from Task Scheduler
- cmd.exe (PID: 6816)
- cmd.exe (PID: 616)
Reads Internet Explorer settings
- mshta.exe (PID: 680)
- mshta.exe (PID: 6760)
- mshta.exe (PID: 6676)
- mshta.exe (PID: 7788)
Creates files in the program directory
- cmd.exe (PID: 5384)
Drops encrypted JS script (Microsoft Script Encoder)
- WireGuard.exe (PID: 8180)
The executable file from the user directory is run by the Powershell process
- Temp6HMNGSQO8MHWKL6XCKKYW8EHVPFMIAEC.EXE (PID: 5156)
- TempZAMMOGFF0ACQCO1GTJELYXLOXXH6KVZM.EXE (PID: 2908)
- Temp6HMNGSQO8MHWKL6XCKKYW8EHVPFMIAEC.EXE (PID: 7704)
- TempZAMMOGFF0ACQCO1GTJELYXLOXXH6KVZM.EXE (PID: 4740)
Attempting to use instant messaging service
- MSBuild.exe (PID: 6760)
- powershell.exe (PID: 6488)
Changes the registry key values via Powershell
- filelistcreatorassist15.exe (PID: 9276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(6048) 6cbbc0f1be8e61da11cec2e930d8e0a9.exe
C2 (9)parakehjet.run/kewk
buzzarddf.live/ktnt
zenithcorde.top/auid
bearjk.live/benj
techguidet.digital/apdo
techsyncq.run/riid
btcgeared.live/lbak
clarmodq.top/qoxo
fishgh.digital/tequ
Amadey
(PID) Process(2148) saved.exe
C2185.39.17.163
URLhttp://185.39.17.163/Su8kud7i/index.php
Version5.34
Options
Drop directoryc13dbdc4fa
Drop namesaved.exe
Strings (125)S-%lu-
og:
clip.dll
ProgramData\
shell32.dll
<c>
vs:
Programs
&&
VideoID
ESET
av:
\App
0000043f
Doctor Web
:::
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
------
rundll32.exe
00000422
185.39.17.163
0123456789
st=s
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
msi
ar:
GetNativeSystemInfo
Norton
-%lu
Sophos
zip
SOFTWARE\Microsoft\Windows NT\CurrentVersion
"
Content-Type: application/octet-stream
|
+++
" && ren
pc:
#
d1
cmd /C RMDIR /s/q
Bitdefender
Comodo
<d>
Kaspersky Lab
DefaultSettings.YResolution
Main
c13dbdc4fa
-executionpolicy remotesigned -File "
&& Exit"
ProductName
&unit=
2022
Panda Security
=
Rem
cmd
\0000
id:
sd:
--
/quiet
rundll32
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
%-lu
random
GET
"taskkill /f /im "
Content-Disposition: form-data; name="data"; filename="
00000423
5.34
2016
?scr=1
ComputerName
Keyboard Layout\Preload
Powershell.exe
POST
http://
AVAST Software
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
ps1
DefaultSettings.XResolution
Startup
CurrentBuild
e3
cred.dll|clip.dll|
------
WinDefender
wb
https://
Avira
2025
" && timeout 1 && del
cred.dll
un:
SYSTEM\ControlSet001\Services\BasicDisplay\Video
rb
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
360TotalSecurity
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
saved.exe
e1
lv:
/Su8kud7i/index.php
shutdown -s -t 0
/k
e2
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
exe
%USERPROFILE%
-unicode-
r=
.jpg
dll
Content-Type: multipart/form-data; boundary=----
2019
bi:
\
"
kernel32.dll
os:
abcdefghijklmnopqrstuvwxyz0123456789-_
dm:
AVG
(PID) Process(6068) laren.exe
C2185.39.17.122
URLhttp://185.39.17.122/som9unr/index.php
Version5.34
Options
Drop directory6f7406a7fa
Drop namelaren.exe
Strings (125)S-%lu-
og:
clip.dll
ProgramData\
shell32.dll
<c>
vs:
Programs
&&
VideoID
ESET
av:
\App
0000043f
Doctor Web
:::
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
------
rundll32.exe
00000422
0123456789
st=s
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
msi
ar:
GetNativeSystemInfo
Norton
-%lu
Sophos
zip
SOFTWARE\Microsoft\Windows NT\CurrentVersion
185.39.17.122
"
Content-Type: application/octet-stream
|
+++
" && ren
pc:
#
d1
cmd /C RMDIR /s/q
Bitdefender
Comodo
<d>
Kaspersky Lab
DefaultSettings.YResolution
Main
-executionpolicy remotesigned -File "
&& Exit"
ProductName
&unit=
2022
Panda Security
=
Rem
cmd
\0000
id:
sd:
--
/quiet
rundll32
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
6f7406a7fa
%-lu
random
GET
"taskkill /f /im "
Content-Disposition: form-data; name="data"; filename="
00000423
5.34
/som9unr/index.php
2016
?scr=1
ComputerName
Keyboard Layout\Preload
Powershell.exe
POST
http://
AVAST Software
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
ps1
DefaultSettings.XResolution
Startup
CurrentBuild
e3
cred.dll|clip.dll|
------
WinDefender
wb
https://
Avira
2025
" && timeout 1 && del
cred.dll
un:
SYSTEM\ControlSet001\Services\BasicDisplay\Video
rb
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
360TotalSecurity
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
laren.exe
e1
lv:
shutdown -s -t 0
/k
e2
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
exe
%USERPROFILE%
-unicode-
r=
.jpg
dll
Content-Type: multipart/form-data; boundary=----
2019
bi:
\
"
kernel32.dll
os:
abcdefghijklmnopqrstuvwxyz0123456789-_
dm:
AVG
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:26 14:47:23+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 312320 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x49e000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
373
Monitored processes
233
Malicious processes
43
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Users\admin\AppData\Local\Temp\10053380101\5bf43363e1.exe" | C:\Users\admin\AppData\Local\Temp\10053380101\5bf43363e1.exe | saved.exe | ||||||||||||
User: admin Company: FlashDevelop.org Integrity Level: MEDIUM Description: FlashDevelop Exit code: 3221225477 Version: 5.0.0.0 Modules
| |||||||||||||||
| 496 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | 47Q6wZM.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 536 | "C:\Users\admin\AppData\Local\Temp\10051580101\JSEVGJV.exe" | C:\Users\admin\AppData\Local\Temp\10051580101\JSEVGJV.exe | — | saved.exe | |||||||||||
User: admin Company: NirSoft Integrity Level: MEDIUM Description: AppNetworkCounter Exit code: 0 Version: 1.48 Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /c schtasks /create /tn pUYYdmahCOa /tr "mshta C:\Users\admin\AppData\Local\Temp\BFrHcoYpx.hta" /sc minute /mo 25 /ru "admin" /f | C:\Windows\SysWOW64\cmd.exe | — | b938f7a239.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | taskkill /F /IM msedge.exe /T | C:\Windows\SysWOW64\taskkill.exe | — | de2bc57ed4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | mshta C:\Users\admin\AppData\Local\Temp\X37gwFbmO.hta | C:\Windows\SysWOW64\mshta.exe | — | b938f7a239.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | CMD /C "WMIC DISKDRIVE GET SERIALNUMBER" | C:\Windows\System32\cmd.exe | — | WireGuard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=3736 --field-trial-handle=1996,i,12436279718547048677,15457973242183410040,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=4536 --field-trial-handle=2176,i,5351142364422254196,4447234071334576365,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
105 295
Read events
105 183
Write events
111
Delete events
1
Modification events
| (PID) Process: | (2148) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2148) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2148) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6068) laren.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6068) laren.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6068) laren.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2148) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 5511ade474.exe |
Value: C:\Users\admin\AppData\Local\Temp\10053290101\5511ade474.exe | |||
| (PID) Process: | (4120) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: explorer.exe,C:\ProgramData\DNS.exe, | |||
| (PID) Process: | (2148) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | de2bc57ed4.exe |
Value: C:\Users\admin\AppData\Local\Temp\10053310101\de2bc57ed4.exe | |||
| (PID) Process: | (680) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
95
Suspicious files
372
Text files
153
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6424 | VOWFGO964SM4LIK16O5FG.exe | C:\Windows\Tasks\saved.job | binary | |
MD5:D7871DC132657CDD7AB3174B1F6D8ED0 | SHA256:DA144543B61ACC753A8D5C07C12AB78F9757B6320576C5B186AC192F0403BB49 | |||
| 2148 | saved.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\JSEVGJV[1].exe | executable | |
MD5:0A083775390677239BFB7172689A2E75 | SHA256:B290AA87A5D4749E8BA7253B1D7735E5A322C7D6A9E317AD1DC8F5D5CFD8E75C | |||
| 2148 | saved.exe | C:\Users\admin\AppData\Local\Temp\10051660101\amnew.exe | executable | |
MD5:9B4ED35663DE10326D771433E97F2B26 | SHA256:187F74E40E00886C3062E39DC93D33609F87AA6287C5B1BD0E247D80C5BFCEC2 | |||
| 2148 | saved.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\random[1].exe | executable | |
MD5:1BAE0DAB5C42DFE20D6A315C0490B513 | SHA256:BB760E8484ADB256EB5EE807AD3585283E3454971AEDDBAFD02FAF816346F22C | |||
| 6068 | laren.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:D169E0D7D1B5A3820C1B44E20D92B2D2 | SHA256:0BF9DF173AB568450A2166F14352C122ECCAD86807FCA7F1BB174F1E68308376 | |||
| 6048 | 6cbbc0f1be8e61da11cec2e930d8e0a9.exe | C:\Users\admin\AppData\Local\Temp\VOWFGO964SM4LIK16O5FG.exe | executable | |
MD5:F6C20A18AFEAC04964A6CCAD6BE59731 | SHA256:CE75F9DEDE6D4E93549D35B816898113B6BEFAB9EF0AADF8949D4887C2C34BEA | |||
| 6424 | VOWFGO964SM4LIK16O5FG.exe | C:\Users\admin\AppData\Local\Temp\c13dbdc4fa\saved.exe | executable | |
MD5:F6C20A18AFEAC04964A6CCAD6BE59731 | SHA256:CE75F9DEDE6D4E93549D35B816898113B6BEFAB9EF0AADF8949D4887C2C34BEA | |||
| 2148 | saved.exe | C:\Users\admin\AppData\Local\Temp\10051580101\JSEVGJV.exe | executable | |
MD5:0A083775390677239BFB7172689A2E75 | SHA256:B290AA87A5D4749E8BA7253B1D7735E5A322C7D6A9E317AD1DC8F5D5CFD8E75C | |||
| 4120 | amnew.exe | C:\Users\admin\AppData\Local\Temp\6f7406a7fa\laren.exe | executable | |
MD5:9B4ED35663DE10326D771433E97F2B26 | SHA256:187F74E40E00886C3062E39DC93D33609F87AA6287C5B1BD0E247D80C5BFCEC2 | |||
| 4120 | amnew.exe | C:\Windows\Tasks\laren.job | binary | |
MD5:58B8034B13C3EFE457B31845D26A3E2D | SHA256:4F69307A7F54E1C2D59A5279249283FAA674FDD964944AB3ACE5B35B458CE7CA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
109
TCP/UDP connections
253
DNS requests
206
Threats
150
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2148 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | RU | text | 8 b | malicious |
2148 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | RU | text | 1.58 Kb | malicious |
2148 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/files/7677226784/JSEVGJV.exe | RU | executable | 6.16 Mb | malicious |
680 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
680 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | QA | binary | 407 b | whitelisted |
2148 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | RU | text | 4 b | malicious |
2148 | saved.exe | GET | 200 | 185.39.17.122:80 | http://185.39.17.122/test/amnew.exe | RU | executable | 415 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
— | — | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
6048 | 6cbbc0f1be8e61da11cec2e930d8e0a9.exe | 172.67.190.162:443 | zenithcorde.top | CLOUDFLARENET | US | unknown |
— | — | 172.67.190.162:443 | zenithcorde.top | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clarmodq.top |
| malicious |
zenithcorde.top |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (clarmodq .top) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (clarmodq .top) |
6048 | 6cbbc0f1be8e61da11cec2e930d8e0a9.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6048 | 6cbbc0f1be8e61da11cec2e930d8e0a9.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
6048 | 6cbbc0f1be8e61da11cec2e930d8e0a9.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6048 | 6cbbc0f1be8e61da11cec2e930d8e0a9.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6048 | 6cbbc0f1be8e61da11cec2e930d8e0a9.exe | Misc activity | ET INFO Packed Executable Download |
6048 | 6cbbc0f1be8e61da11cec2e930d8e0a9.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
2148 | saved.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |