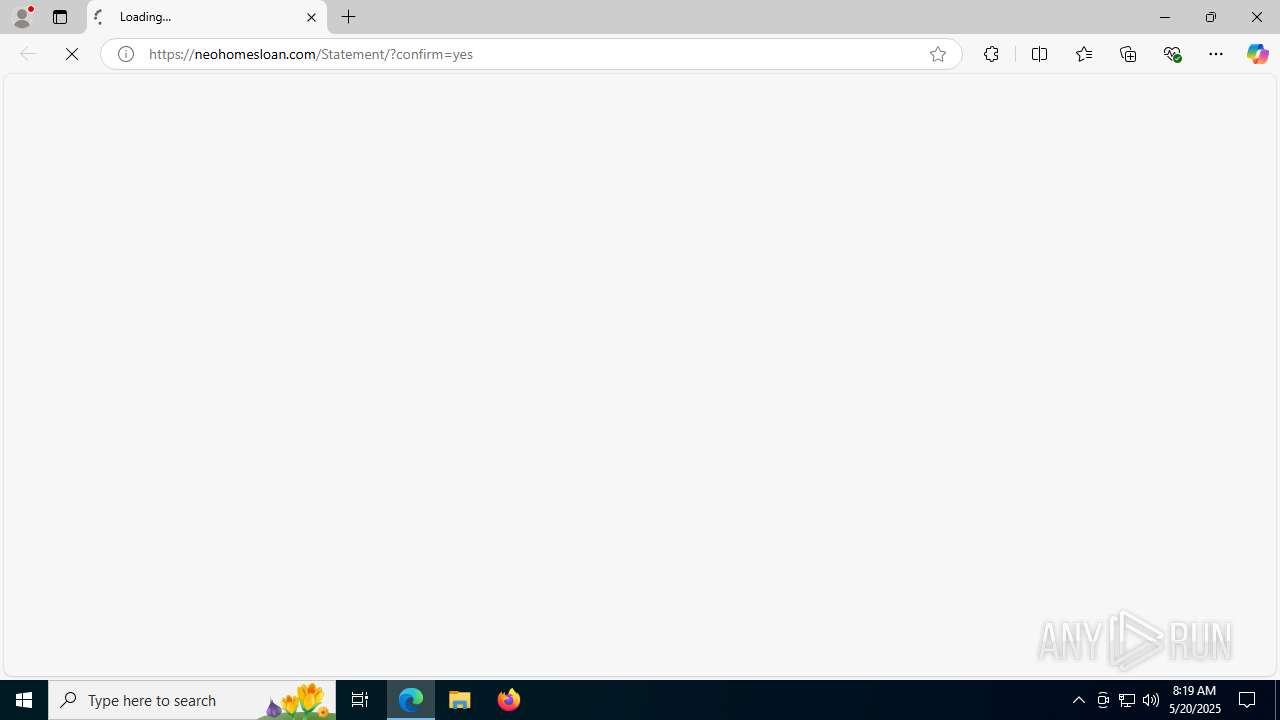
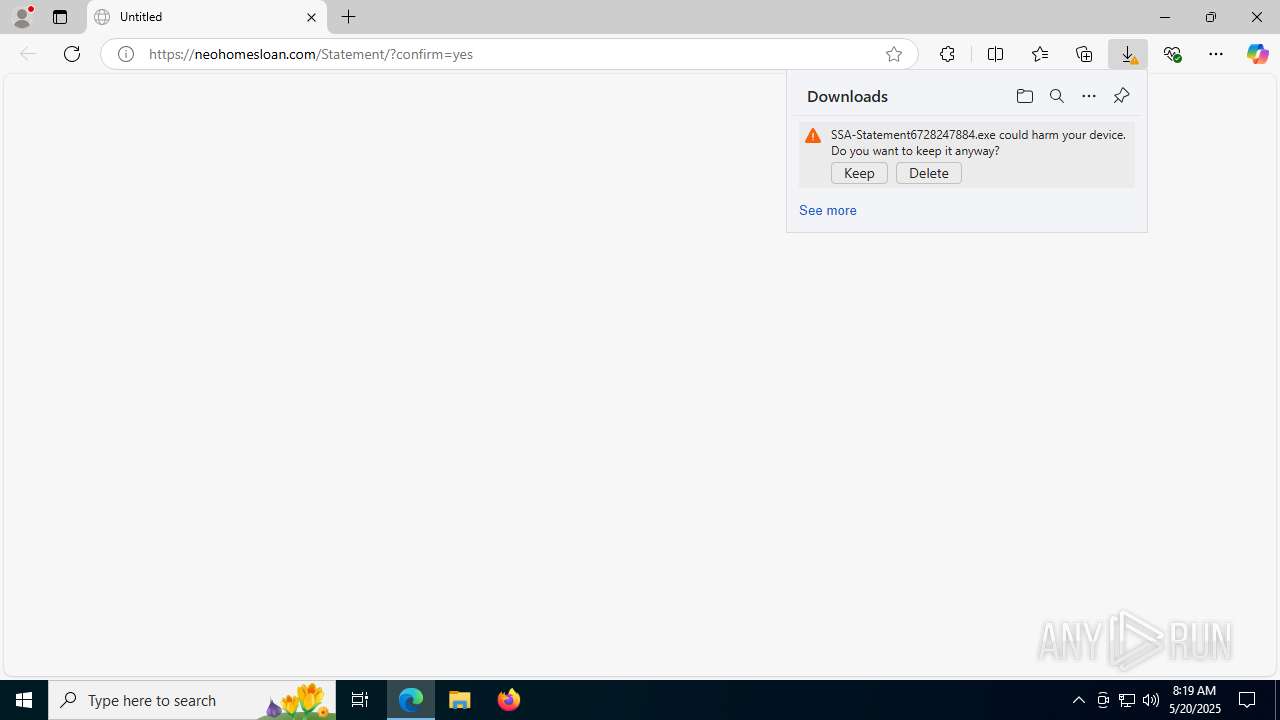
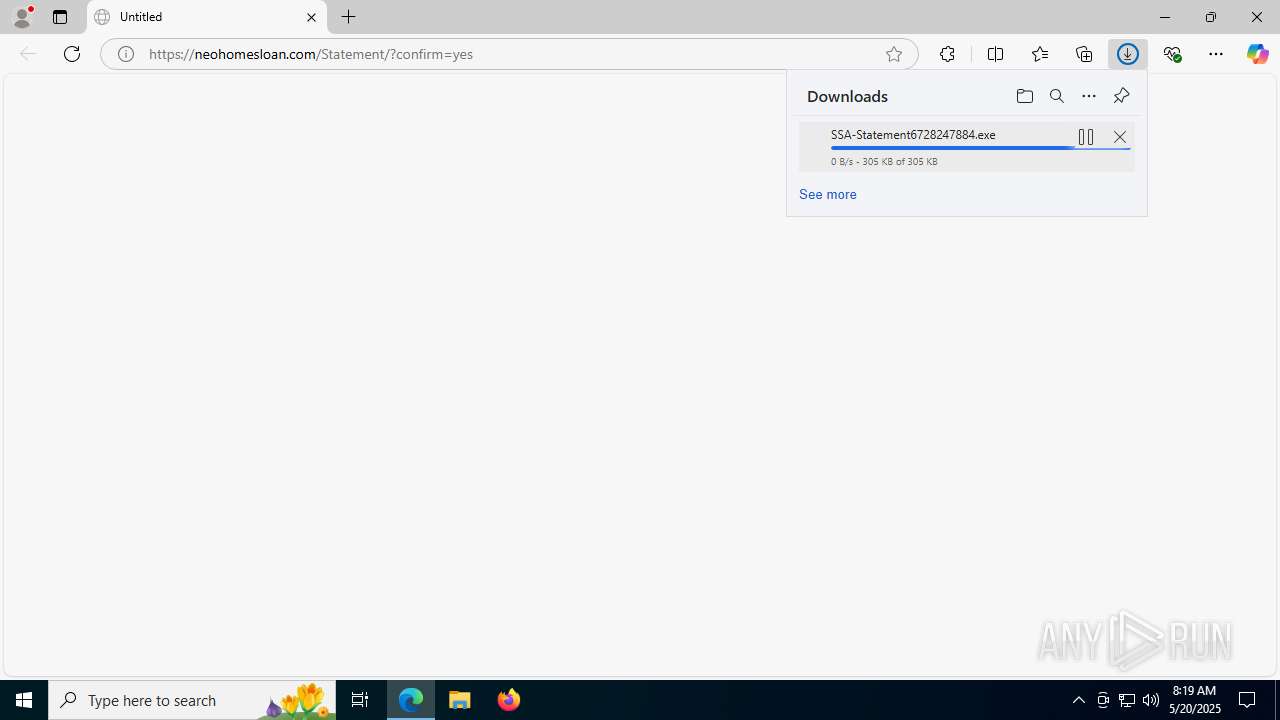
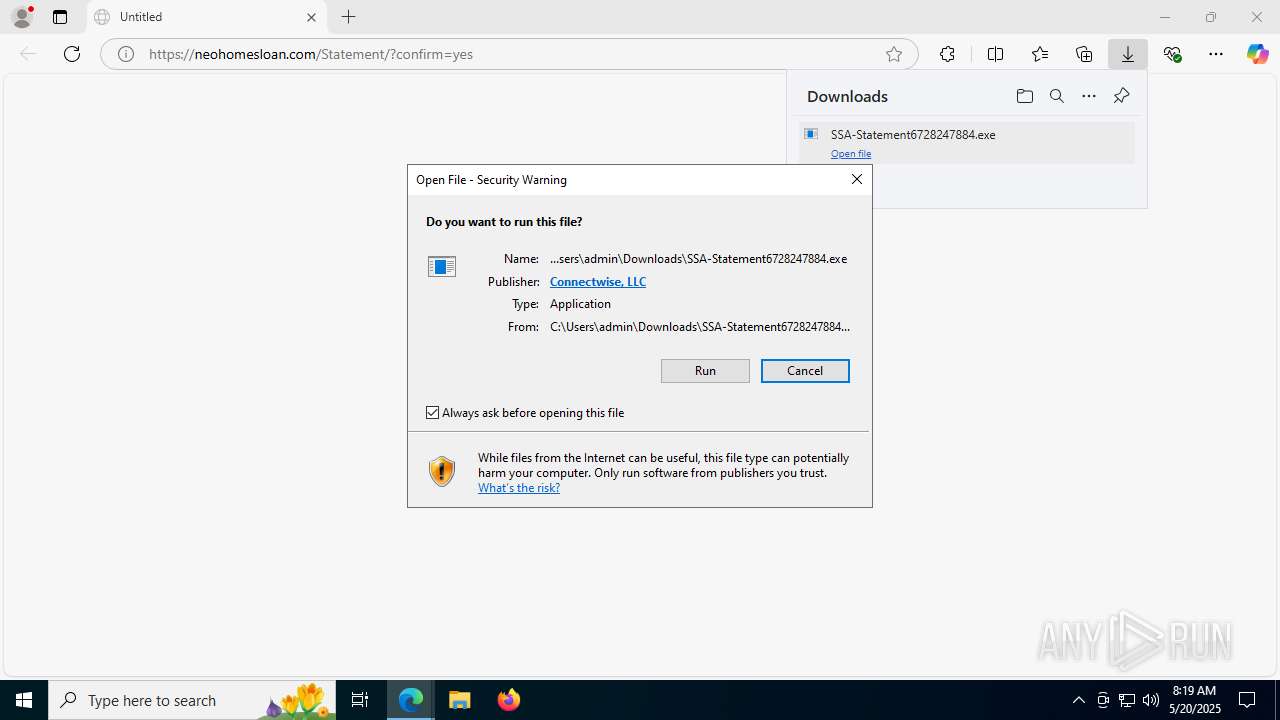
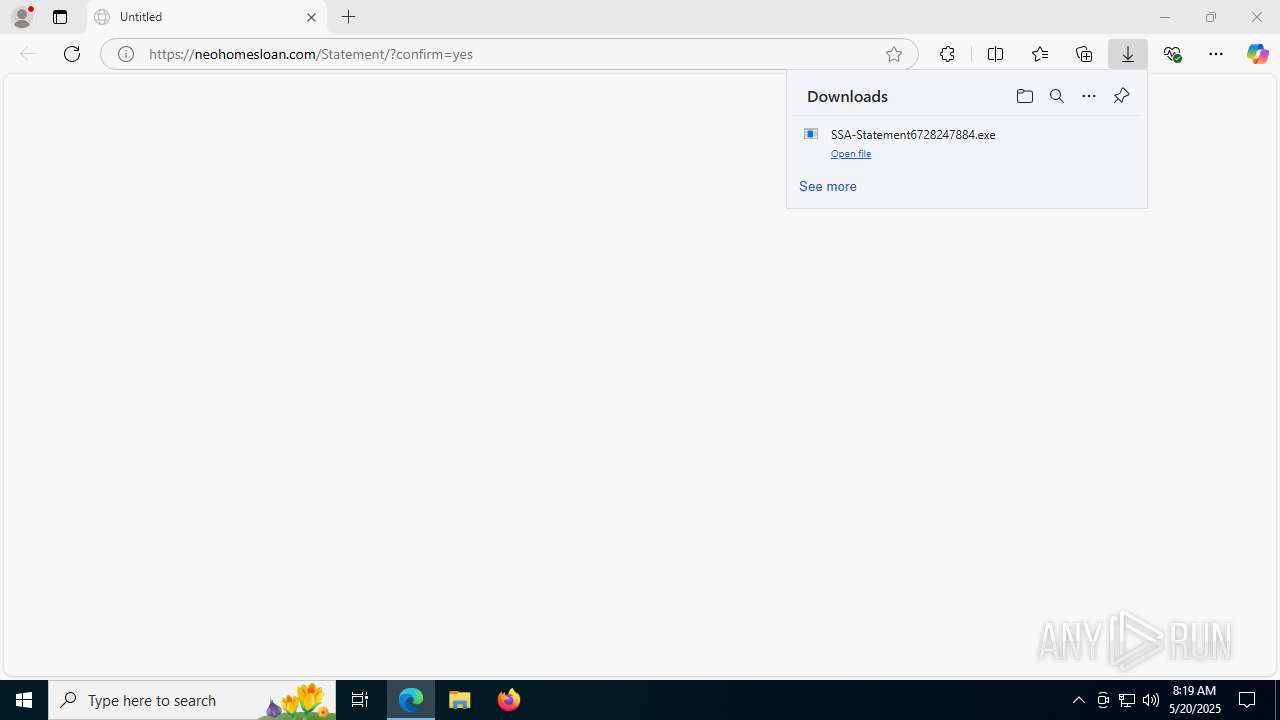
| URL: | https://neohomesloan.com/Statement/?confirm=yes |
| Full analysis: | https://app.any.run/tasks/fbb0730e-fbee-47b3-84bd-aa4440403575 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 20, 2025, 08:18:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 15B38F2C22FDA42E8AE56D5997295254 |
| SHA1: | 227E3CC7BD4B2672A77AA22995748784F4633C48 |
| SHA256: | 90C1817AB58318F0FE32435DA497B6B497D4402B30FD1744B693E9EFA3F71D38 |
| SSDEEP: | 3:N87X5yK3jmpRDDp:2n3j2RR |
MALICIOUS
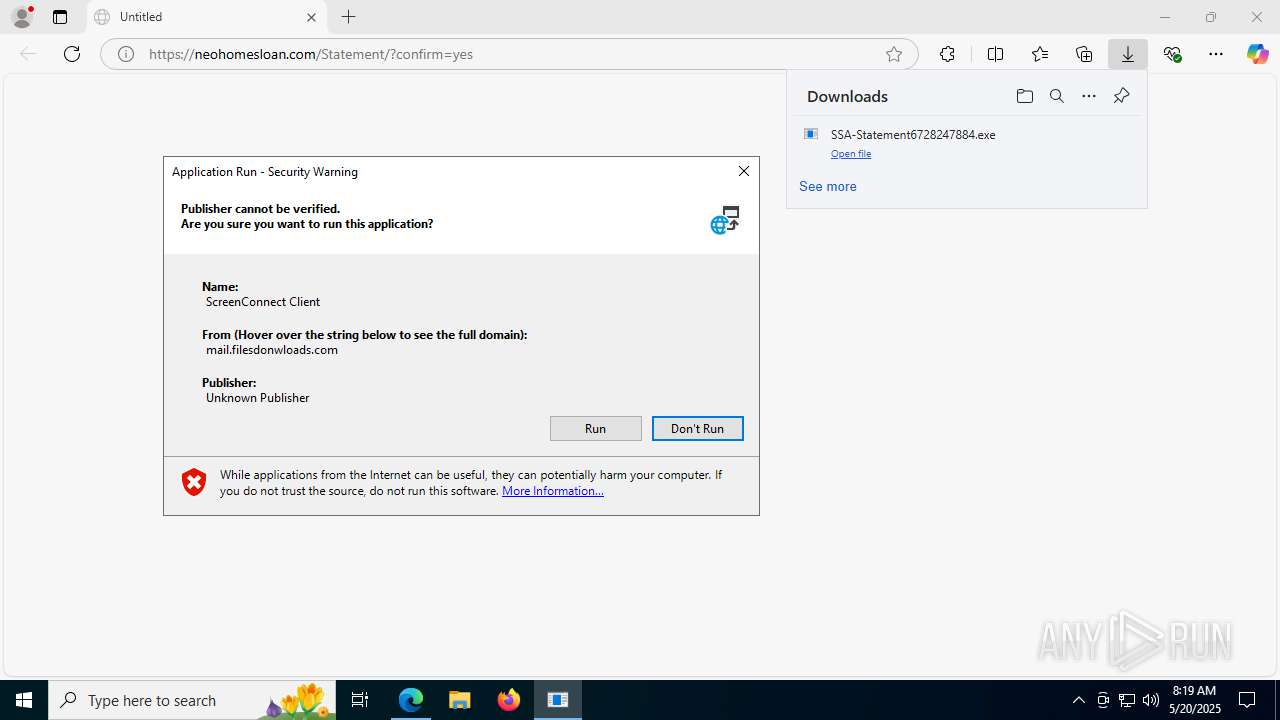
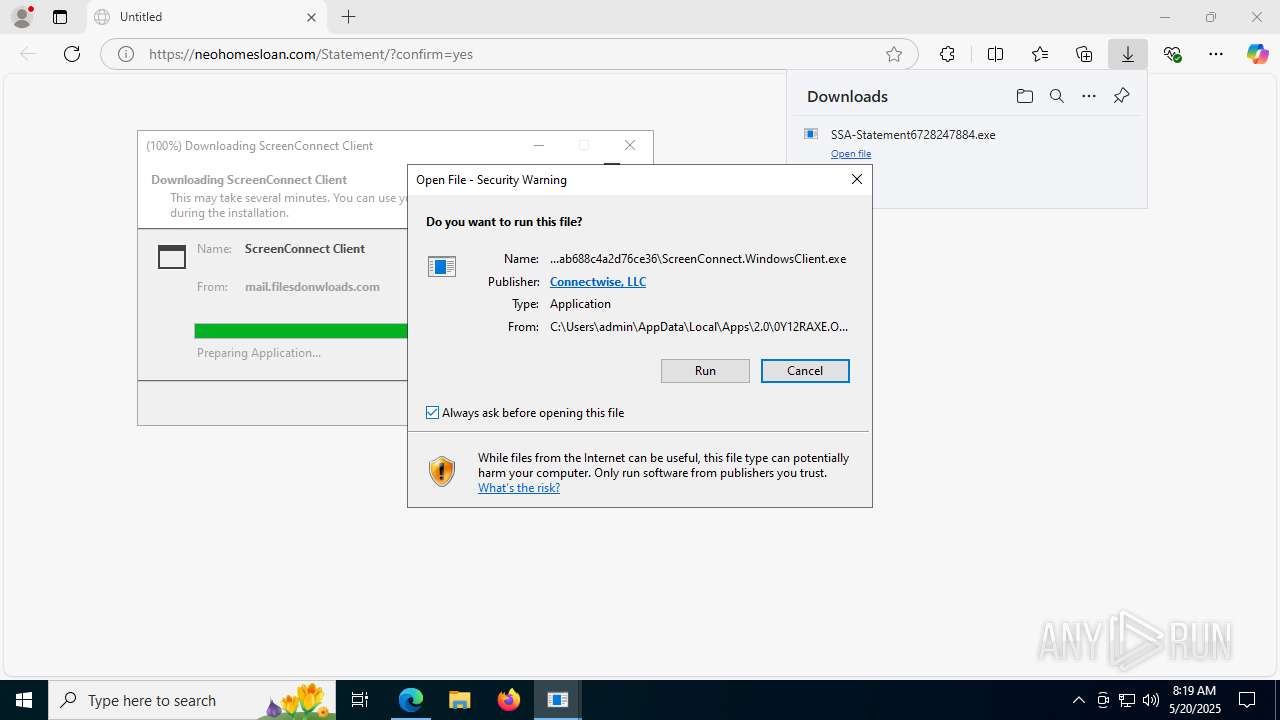
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 7524)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 7172)
- wscript.exe (PID: 5600)
Run PowerShell with an invisible window
- powershell.exe (PID: 7564)
- powershell.exe (PID: 7936)
Bypass execution policy to execute commands
- powershell.exe (PID: 7564)
- powershell.exe (PID: 7936)
Uses Task Scheduler to run other applications
- wscript.exe (PID: 7304)
- wscript.exe (PID: 2732)
- wscript.exe (PID: 4048)
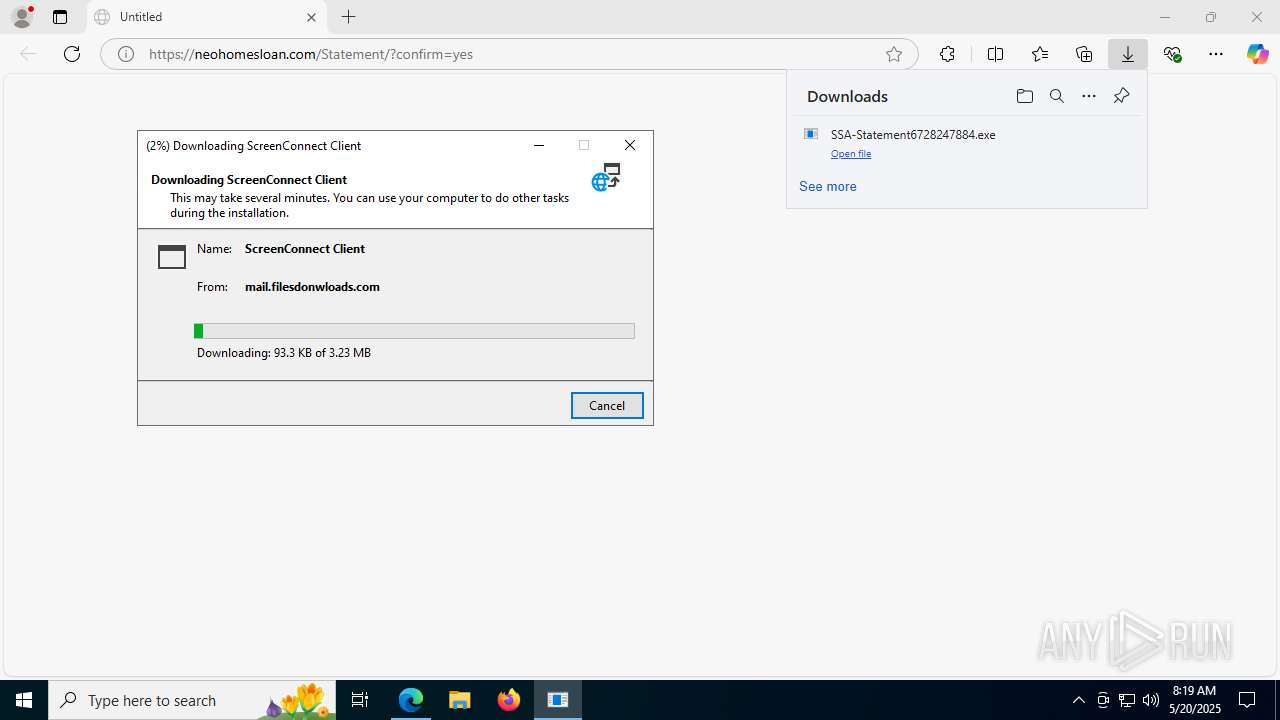
ASYNCRAT has been detected (SURICATA)
- jsc.exe (PID: 7104)
ASYNCRAT has been detected (YARA)
- jsc.exe (PID: 7104)
SUSPICIOUS
Adds/modifies Windows certificates
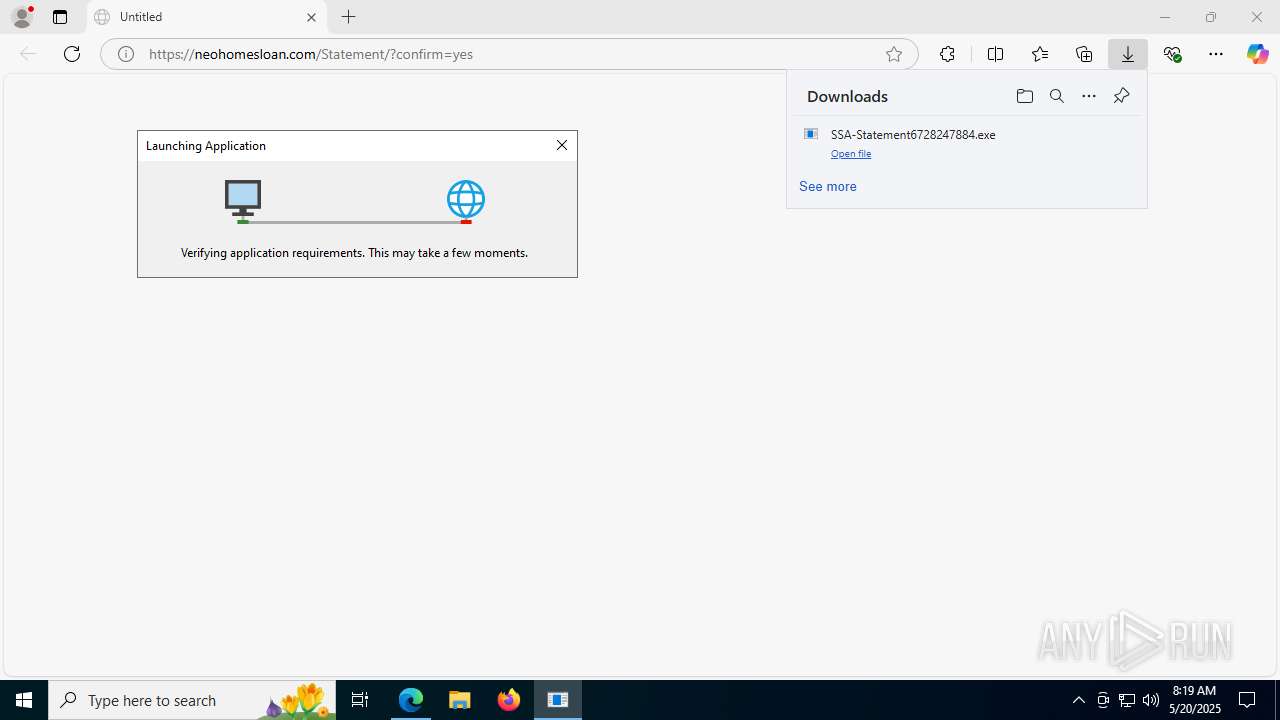
- SSA-Statement6728247884.exe (PID: 7856)
- dfsvc.exe (PID: 7928)
- SSA-Statement6728247884.exe (PID: 432)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 7928)
- ScreenConnect.WindowsClient.exe (PID: 7224)
- ScreenConnect.ClientService.exe (PID: 7584)
- ScreenConnect.ClientService.exe (PID: 7524)
- ScreenConnect.WindowsClient.exe (PID: 7792)
- ScreenConnect.WindowsClient.exe (PID: 2288)
Reads Internet Explorer settings
- dfsvc.exe (PID: 7928)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 7928)
- powershell.exe (PID: 7564)
- Guard.exe (PID: 4948)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 7928)
Reads the date of Windows installation
- dfsvc.exe (PID: 7928)
- ScreenConnect.WindowsClient.exe (PID: 7224)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 7524)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 7524)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 7524)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 7524)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 7524)
- jsc.exe (PID: 7104)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 7524)
Application launched itself
- ScreenConnect.WindowsClient.exe (PID: 7792)
The process hide an interactive prompt from the user
- wscript.exe (PID: 7172)
- wscript.exe (PID: 5600)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7172)
- wscript.exe (PID: 5600)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7172)
- wscript.exe (PID: 5600)
Connects to the server without a host name
- powershell.exe (PID: 7564)
- wscript.exe (PID: 7172)
- powershell.exe (PID: 7936)
Found IP address in command line
- powershell.exe (PID: 7564)
- powershell.exe (PID: 7936)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 7172)
- wscript.exe (PID: 5600)
There is functionality for taking screenshot (YARA)
- ScreenConnect.ClientService.exe (PID: 7524)
- ScreenConnect.WindowsClient.exe (PID: 7792)
Detects ScreenConnect RAT (YARA)
- ScreenConnect.ClientService.exe (PID: 7524)
- ScreenConnect.WindowsClient.exe (PID: 7792)
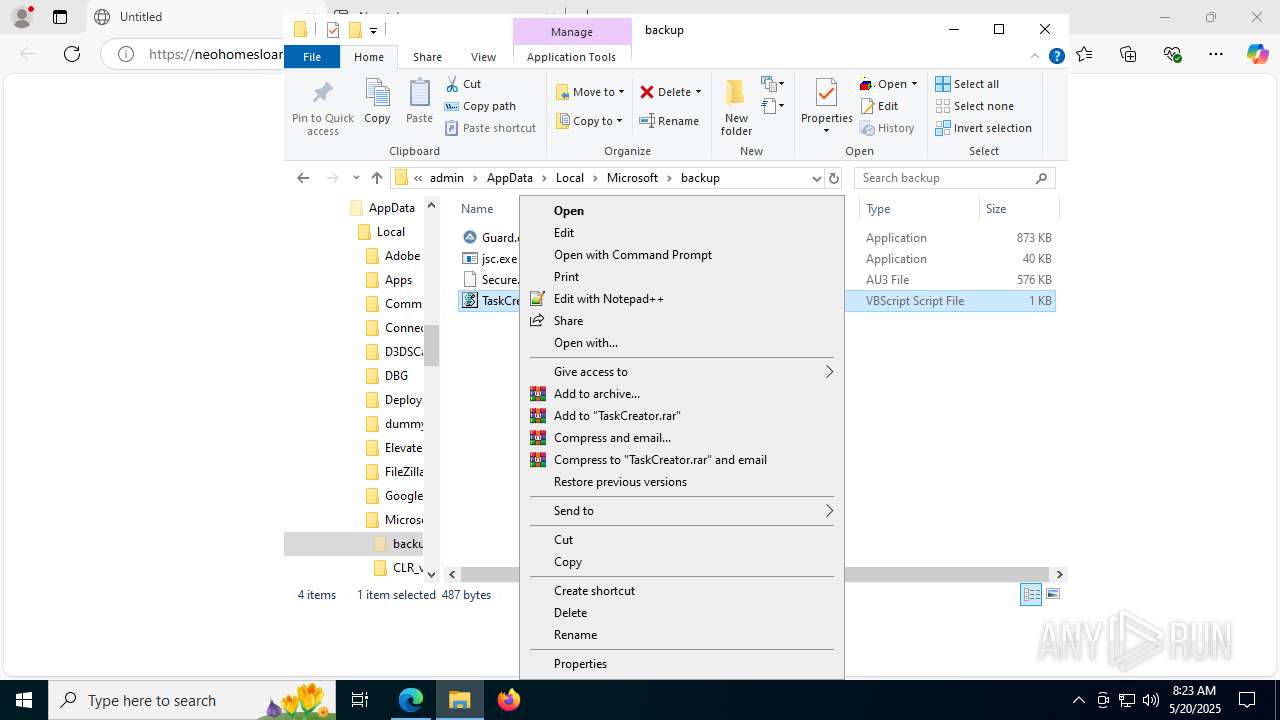
The process executes VB scripts
- powershell.exe (PID: 7564)
- powershell.exe (PID: 7936)
Starts the AutoIt3 executable file
- wscript.exe (PID: 7304)
- wscript.exe (PID: 2732)
- wscript.exe (PID: 4048)
Process drops legitimate windows executable
- Guard.exe (PID: 4948)
Contacting a server suspected of hosting an CnC
- jsc.exe (PID: 7104)
Executing commands from ".cmd" file
- ScreenConnect.ClientService.exe (PID: 7524)
Starts CMD.EXE for commands execution
- ScreenConnect.ClientService.exe (PID: 7524)
Checks for external IP
- svchost.exe (PID: 2200)
- curl.exe (PID: 7720)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 3572)
- msedge.exe (PID: 3780)
Application launched itself
- msedge.exe (PID: 3572)
Checks supported languages
- identity_helper.exe (PID: 7400)
- SSA-Statement6728247884.exe (PID: 7856)
- dfsvc.exe (PID: 7928)
- ScreenConnect.WindowsClient.exe (PID: 7224)
- ScreenConnect.ClientService.exe (PID: 7584)
- ScreenConnect.ClientService.exe (PID: 7524)
- ScreenConnect.WindowsClient.exe (PID: 7792)
- ScreenConnect.WindowsClient.exe (PID: 2288)
- SSA-Statement6728247884.exe (PID: 432)
Reads the computer name
- identity_helper.exe (PID: 7400)
- SSA-Statement6728247884.exe (PID: 7856)
- dfsvc.exe (PID: 7928)
- ScreenConnect.ClientService.exe (PID: 7584)
- ScreenConnect.ClientService.exe (PID: 7524)
- ScreenConnect.WindowsClient.exe (PID: 7792)
- ScreenConnect.WindowsClient.exe (PID: 7224)
- ScreenConnect.WindowsClient.exe (PID: 2288)
Disables trace logs
- dfsvc.exe (PID: 7928)
Checks proxy server information
- dfsvc.exe (PID: 7928)
Reads Environment values
- identity_helper.exe (PID: 7400)
- dfsvc.exe (PID: 7928)
Reads the software policy settings
- dfsvc.exe (PID: 7928)
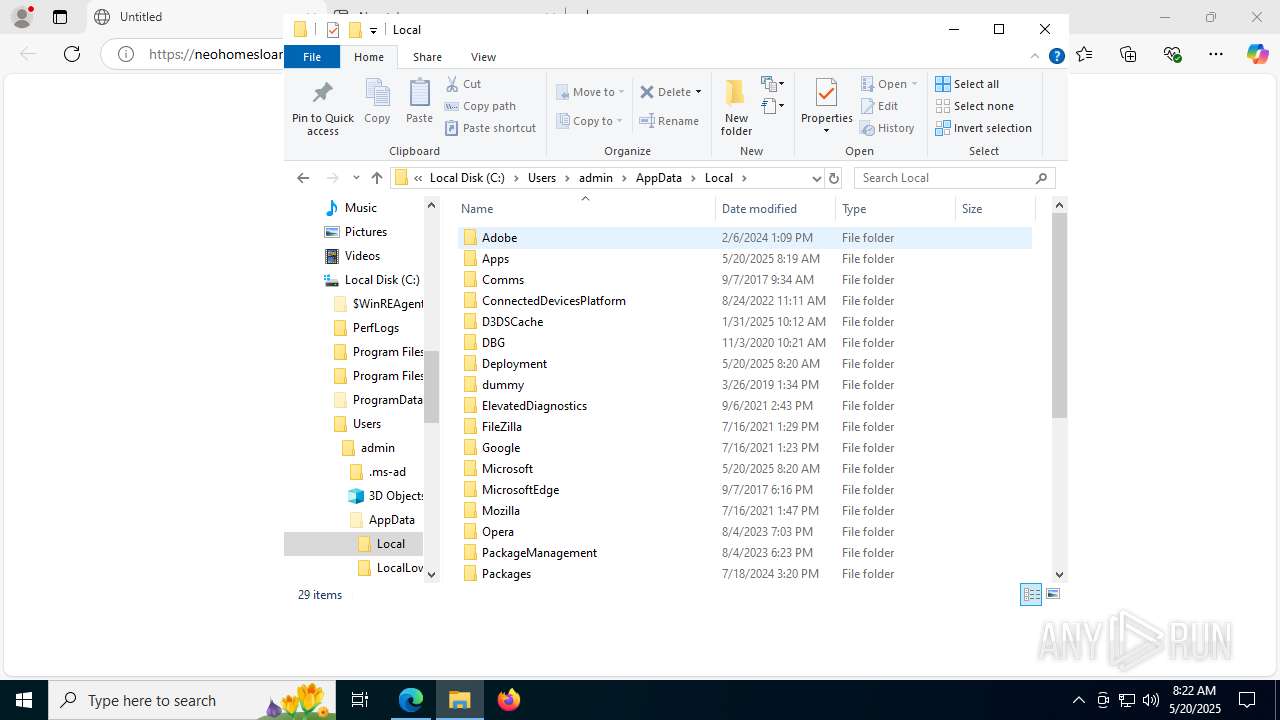
Create files in a temporary directory
- dfsvc.exe (PID: 7928)
Process checks whether UAC notifications are on
- dfsvc.exe (PID: 7928)
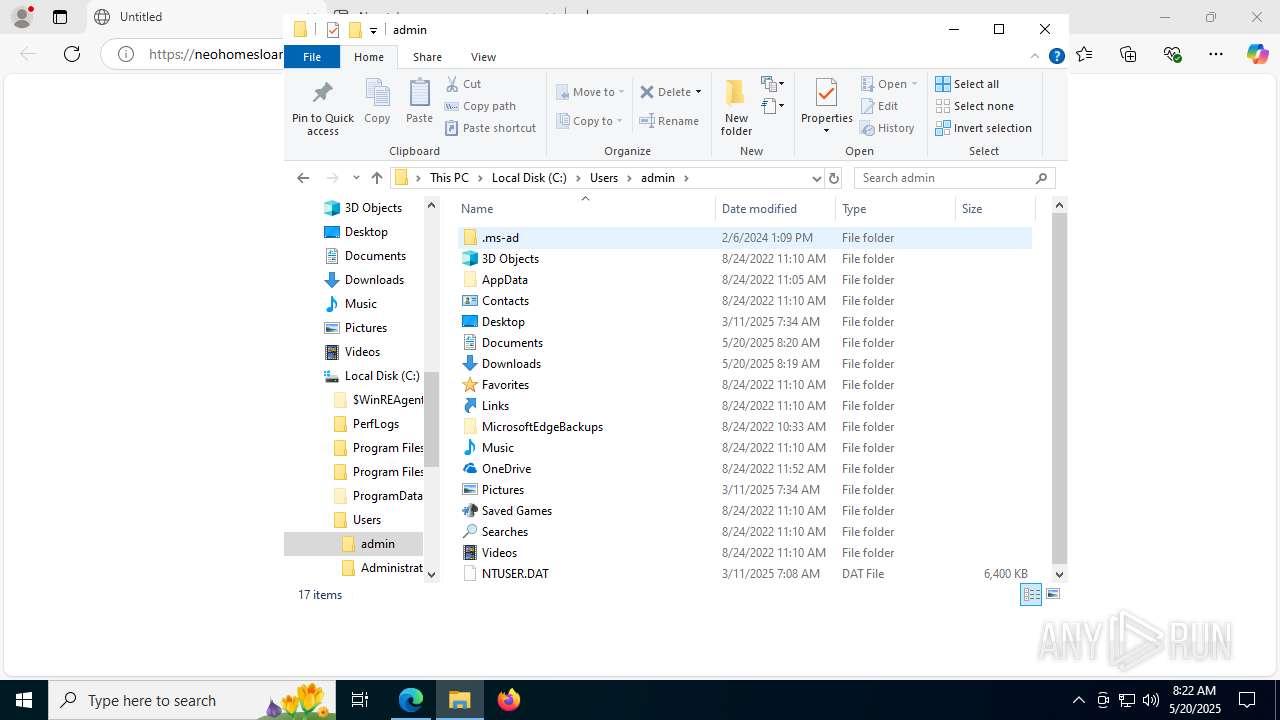
Creates files or folders in the user directory
- dfsvc.exe (PID: 7928)
- ScreenConnect.WindowsClient.exe (PID: 7224)
- ScreenConnect.ClientService.exe (PID: 7524)
Process checks computer location settings
- dfsvc.exe (PID: 7928)
- ScreenConnect.WindowsClient.exe (PID: 7224)
Reads the machine GUID from the registry
- ScreenConnect.WindowsClient.exe (PID: 7224)
- ScreenConnect.ClientService.exe (PID: 7584)
- SSA-Statement6728247884.exe (PID: 7856)
- dfsvc.exe (PID: 7928)
- ScreenConnect.ClientService.exe (PID: 7524)
- ScreenConnect.WindowsClient.exe (PID: 7792)
- ScreenConnect.WindowsClient.exe (PID: 2288)
- SSA-Statement6728247884.exe (PID: 432)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 2288)
The sample compiled with english language support
- powershell.exe (PID: 7564)
- Guard.exe (PID: 4948)
Manual execution by a user
- cmd.exe (PID: 7984)
- jsc.exe (PID: 7104)
- jsc.exe (PID: 1612)
- wscript.exe (PID: 4048)
- jsc.exe (PID: 8124)
SCREENCONNECT has been detected
- ScreenConnect.ClientService.exe (PID: 7524)
Execution of CURL command
- cmd.exe (PID: 1576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
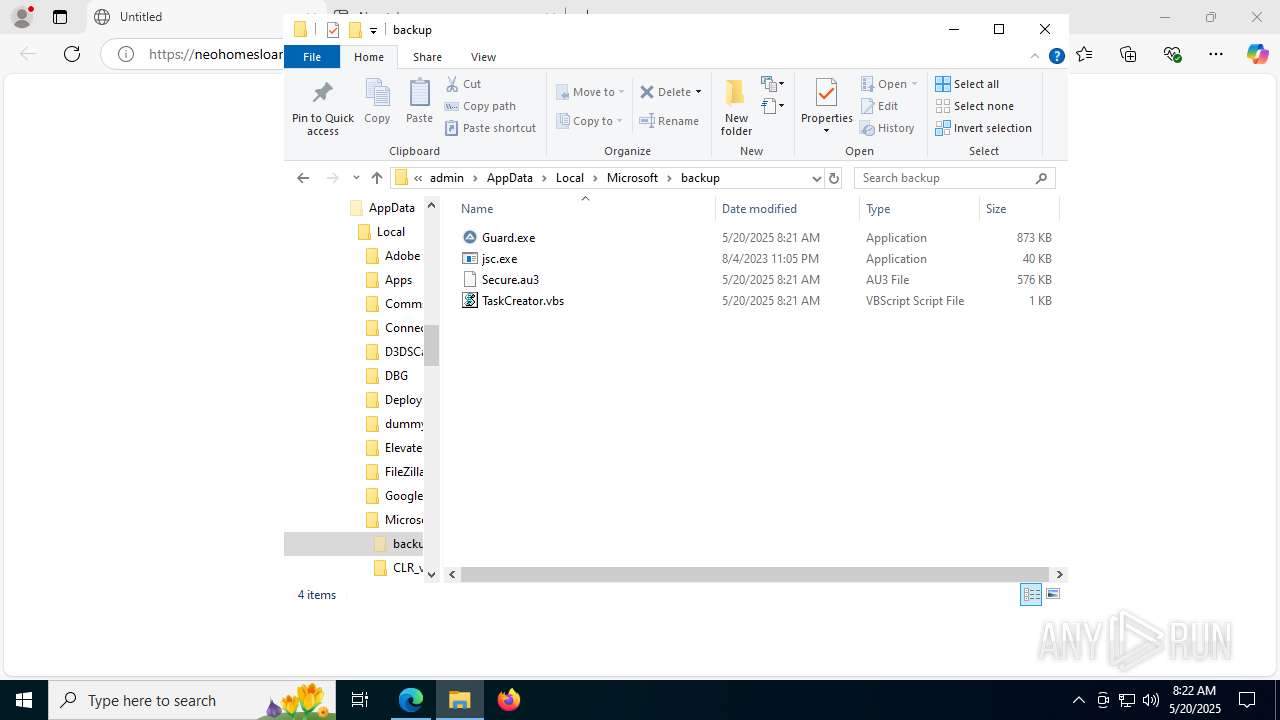
AsyncRat
(PID) Process(7104) jsc.exe
C2 (1)null
Ports (1)null
VersionAWS | 3Losh
Options
AutoRunfalse
Mutex00_001
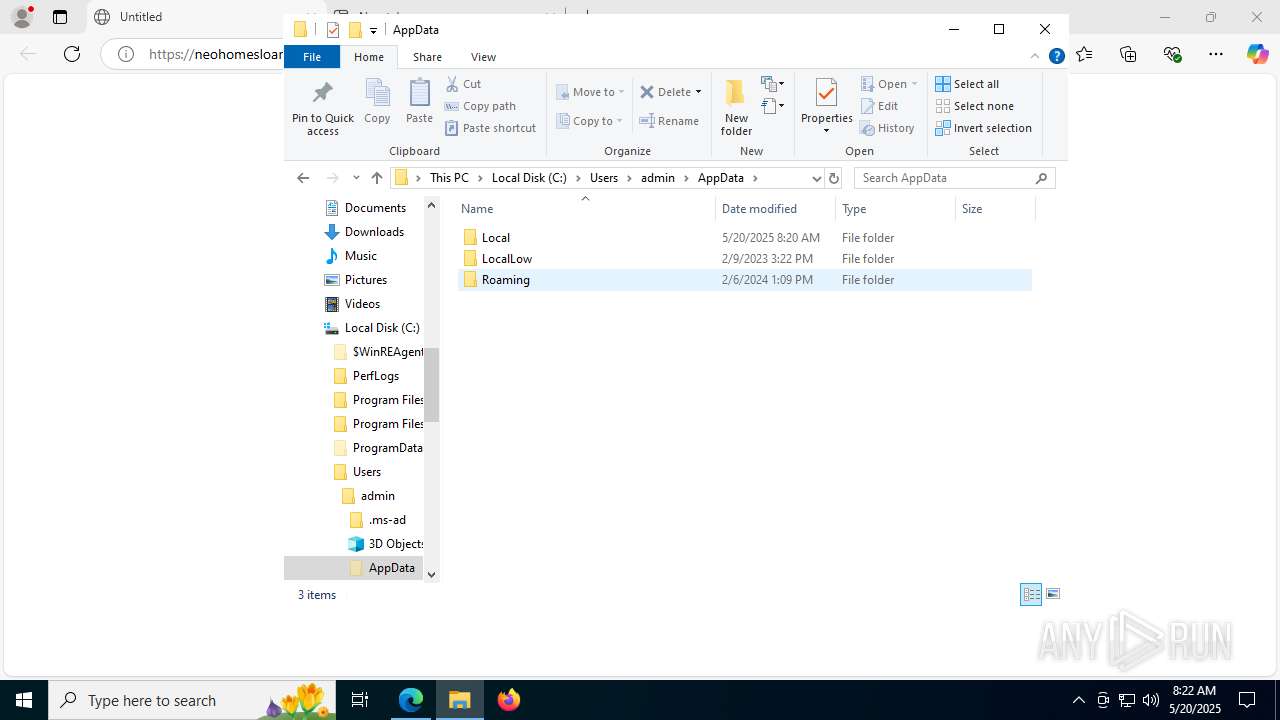
InstallFolder%AppData%
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAPeWQ4YJ3MvReCGwLzn7rTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjIwNDI1MDA0MTA5WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKT9nYYTjYTZhY+g1tekZ8/F29gsEIDgf/8odvCbCmYKGGZZi2yND9NjtBXEMANM9PAXCyMapGva...
Server_SignaturenoqFMM/gGGRM1T0v4ld7fxLV9WxWJ8hdbp1JyutZuFAJCqEPjxw/34f3DZR2UXqhO0xMQvA0i+h3M8yS/SCcQjyy0VyTBkNQcBzBDyjea5dQILecMfnGJMiVzyT1JifxguM73QB8n4qEXYDzA7Qg+Lp31Eb/ctMVVh176xjBMy63aj/UZhgBy+jIh+z0Y5cikqU55x+QF6UwyDXuhCUa5lLcFwQawxmkI2LRRwl4oYaiYOLVWTM+49MX6fCD581Q7IjV+YgBiKlmZgrnaQUYOidY64NSj/cRsUFG9eybs6qb...
Keys
AESa34a19adf716c14503666c58980b36e4dc0b081bbae08c7110b4d946b0a5b116
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
Total processes
221
Monitored processes
76
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
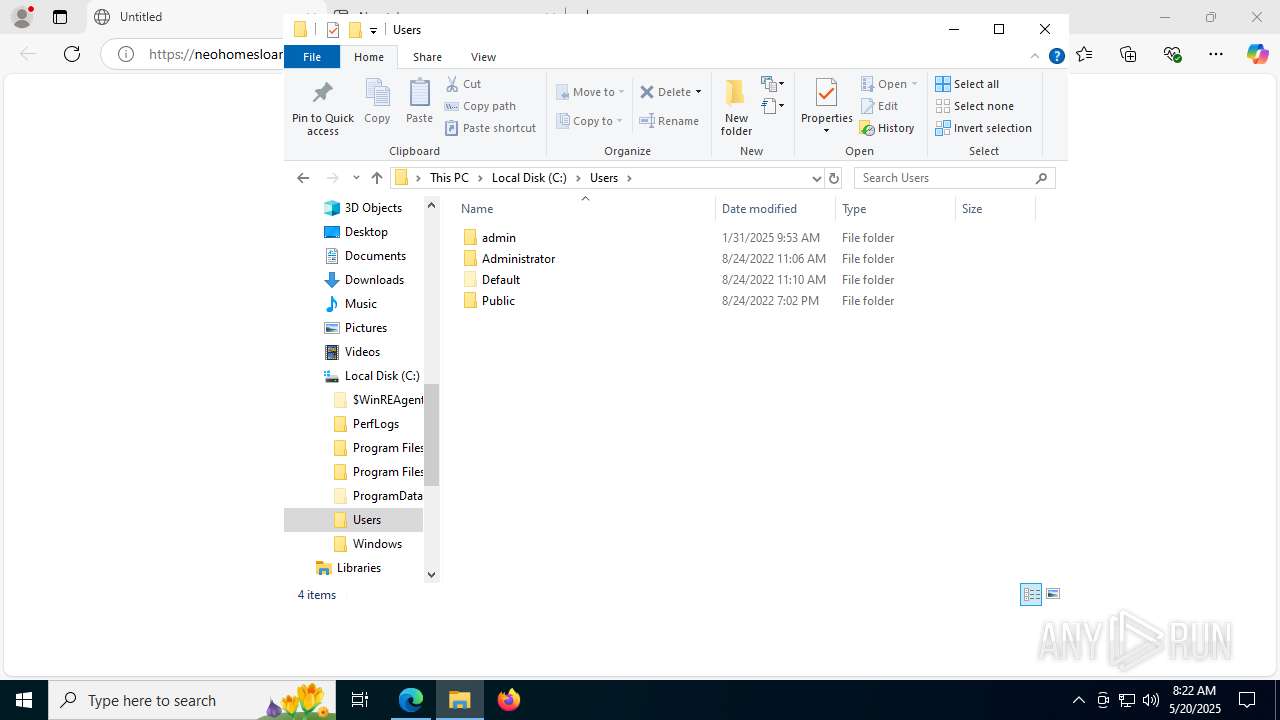
| 432 | "C:\Users\admin\Downloads\SSA-Statement6728247884.exe" | C:\Users\admin\Downloads\SSA-Statement6728247884.exe | — | msedge.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=8132,i,2752300099576751465,7874188804813833849,262144 --variations-seed-version --mojo-platform-channel-handle=7872 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3624,i,2752300099576751465,7874188804813833849,262144 --variations-seed-version --mojo-platform-channel-handle=3708 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\AppData\Local\Apps\2.0\0Y12RAXE.OY7\Q8ZCAQBP.ADH\scre..tion_25b0fbb6ef7eb094_0019.0001_ab688c4a2d76ce36\ScreenConnect.WindowsClient.exe" "RunFile" "C:\Users\admin\Documents\ScreenConnect\Temp\Recently_S_S_A_Statement#648216486.wsf" | C:\Users\admin\AppData\Local\Apps\2.0\0Y12RAXE.OY7\Q8ZCAQBP.ADH\scre..tion_25b0fbb6ef7eb094_0019.0001_ab688c4a2d76ce36\ScreenConnect.WindowsClient.exe | — | ScreenConnect.WindowsClient.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Exit code: 0 Version: 25.1.10.9197 Modules
| |||||||||||||||
| 1392 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7864,i,2752300099576751465,7874188804813833849,262144 --variations-seed-version --mojo-platform-channel-handle=7748 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7548,i,2752300099576751465,7874188804813833849,262144 --variations-seed-version --mojo-platform-channel-handle=7500 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1576 | "cmd.exe" /c "C:\WINDOWS\SystemTemp\ScreenConnect\25.1.10.9197\1m9YS8GxQkegrun.cmd" | C:\Windows\System32\cmd.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1592 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5812,i,2752300099576751465,7874188804813833849,262144 --variations-seed-version --mojo-platform-channel-handle=5816 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
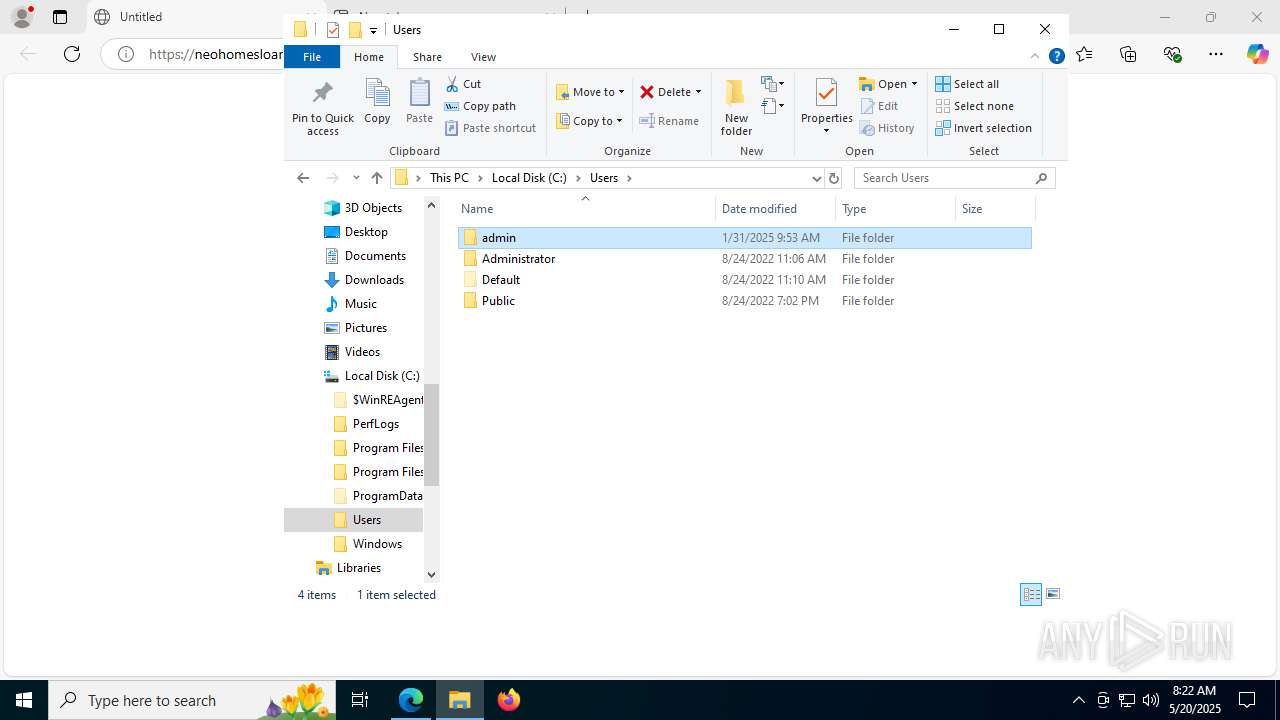
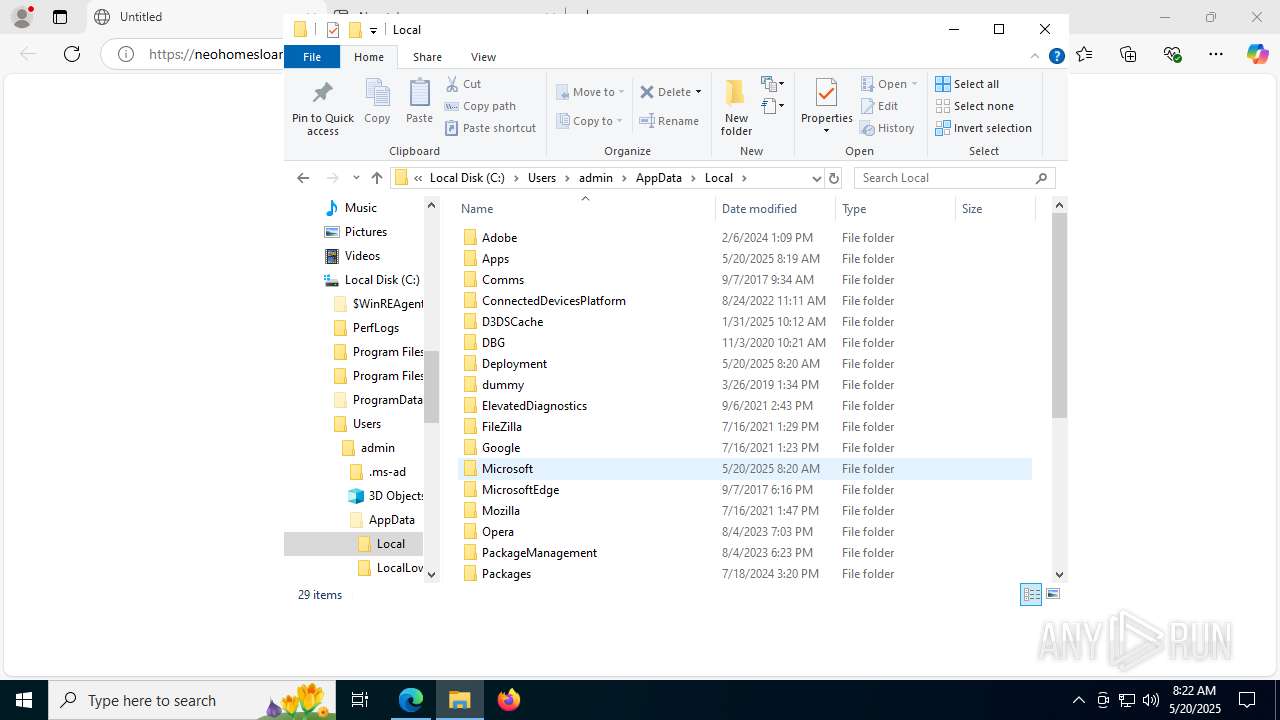
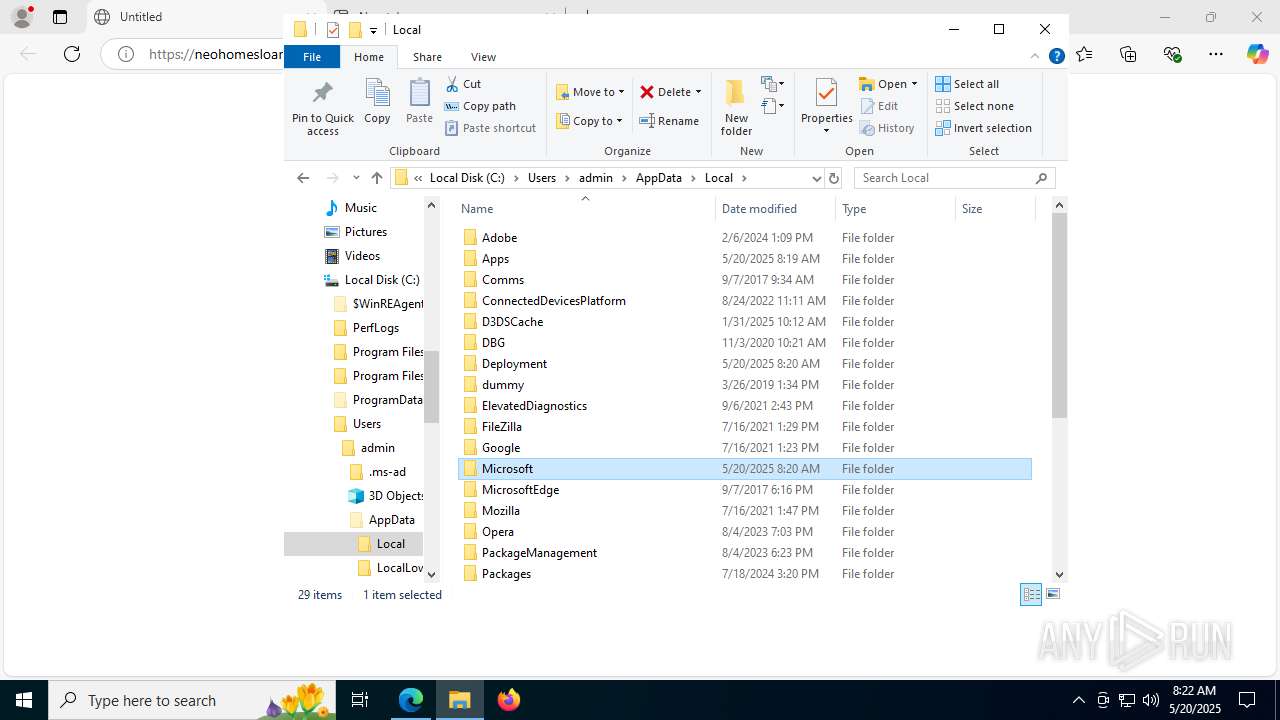
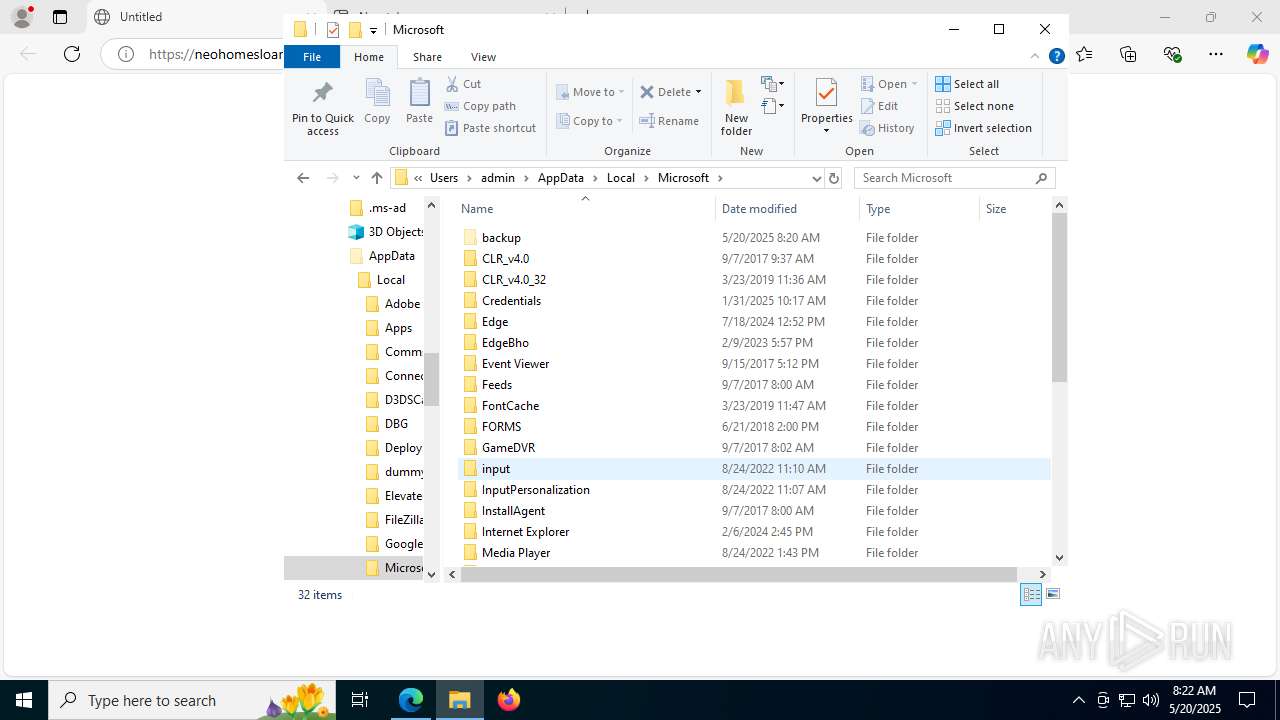
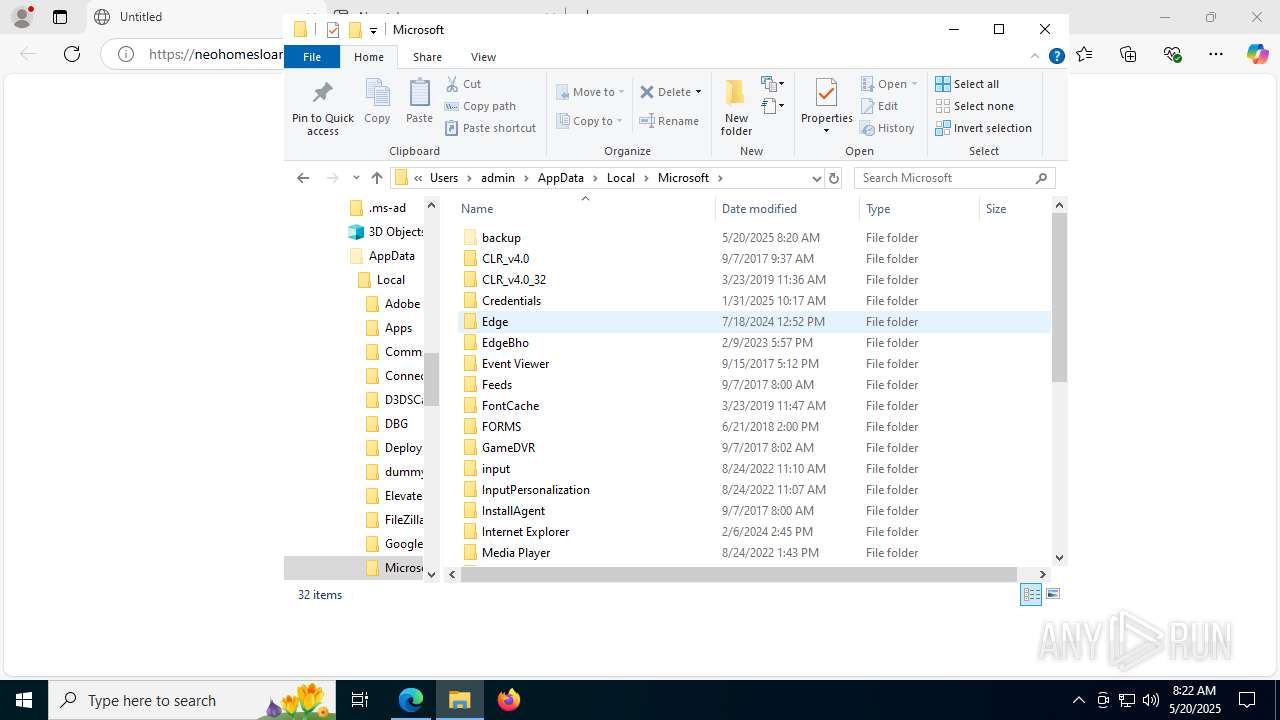
| 1612 | C:\Users\admin\AppData\Local\Microsoft\backup\jsc.exe | C:\Users\admin\AppData\Local\Microsoft\backup\jsc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: jsc.exe Exit code: 0 Version: 14.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 074
Read events
41 775
Write events
240
Delete events
59
Modification events
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7205CF2F23942F00 | |||
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262940 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FAC4815E-CE40-42AF-AF91-4AEB9703AA20} | |||
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262940 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E7C0D73B-9C93-4205-805D-65E8CB8D7871} | |||
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 82ABF42F23942F00 | |||
| (PID) Process: | (3572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
59
Suspicious files
500
Text files
132
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF177ce0.TMP | — | |
MD5:— | SHA256:— | |||
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF177ce0.TMP | — | |
MD5:— | SHA256:— | |||
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF177cf0.TMP | — | |
MD5:— | SHA256:— | |||
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF177cf0.TMP | — | |
MD5:— | SHA256:— | |||
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF177cf0.TMP | — | |
MD5:— | SHA256:— | |||
| 3572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
89
DNS requests
102
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3780 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:i-3ga_W8x1FVTLUxgVnK8w4rtR1MZgtRcoOl8BK_hRw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
3572 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
236 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3572 | msedge.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1984 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1748302731&P2=404&P3=2&P4=dLd6PDzQy01JUBUknFKhZr25tB4yKDOXcv4QR2BAe6BXC6DNI5pYjYdoHMsTUBi9bFpPry2V6Auh%2bmdZ4KzCDQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4708 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
236 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
236 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
neohomesloan.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7524 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |
7564 | powershell.exe | Misc activity | ET INFO Powershell Base64 Decode Command Inbound |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
7104 | jsc.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
7104 | jsc.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
7104 | jsc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
7104 | jsc.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
7172 | wscript.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Obfuscate VBS with replace |
7936 | powershell.exe | Misc activity | ET INFO Powershell Base64 Decode Command Inbound |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ipinfo .io) |
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741772
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\win32\isoreg_direct.cpp, line 1127
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741772
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\win32\isoreg_direct.cpp, line 1127
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741772
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\win32\isoreg_direct.cpp, line 1127
|