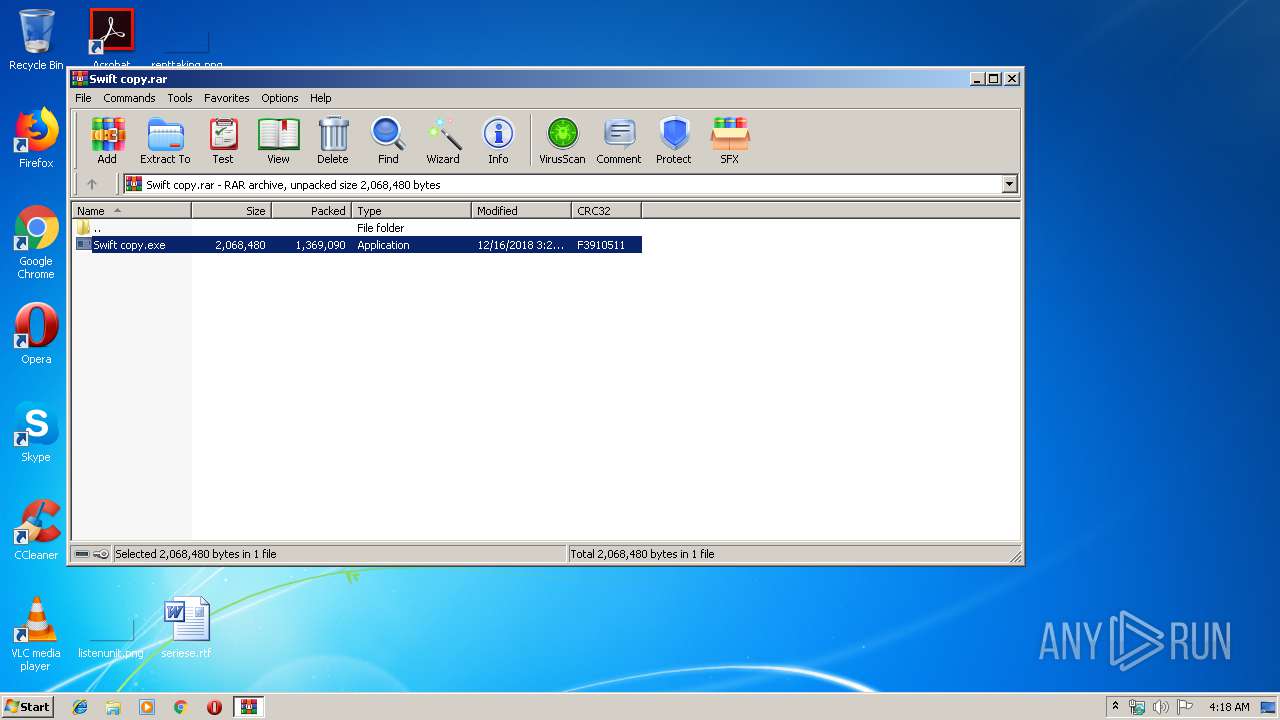
| File name: | Swift copy.rar |
| Full analysis: | https://app.any.run/tasks/75d7ea9e-54b5-447a-a905-688e48b7d7ad |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | August 26, 2019, 03:17:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | EE4981187F43EDD4339A3ACD2EB7D6A0 |
| SHA1: | BC75179EB0B5F9B0FDB585695F5F7C4CF96FEE62 |
| SHA256: | 90812C62FBF6DF192AC222FC07CD61F14B208B584E83CF02B343036687CBDDAC |
| SSDEEP: | 24576:Fbct6Y6zPg9khZQ+IdKtQ8sx/OpkmxNzUotrBLkbDOc4GYv2P9B8CG:o96cefIdKu8BkmxhU+rtkbDOc4GYv2PU |
MALICIOUS
Application was dropped or rewritten from another process
- Swift copy.exe (PID: 2868)
- Swift copy.exe (PID: 4016)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 2884)
AGENTTESLA was detected
- RegSvcs.exe (PID: 2884)
SUSPICIOUS
Application launched itself
- Swift copy.exe (PID: 4016)
Executable content was dropped or overwritten
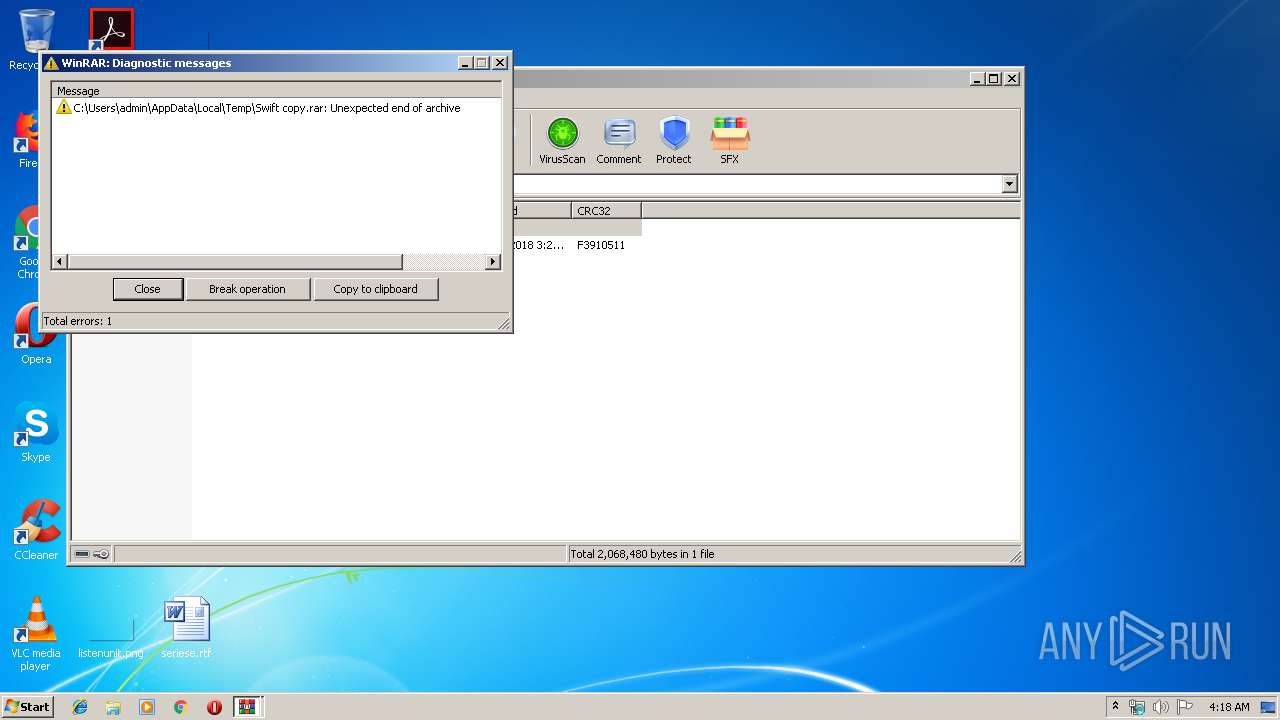
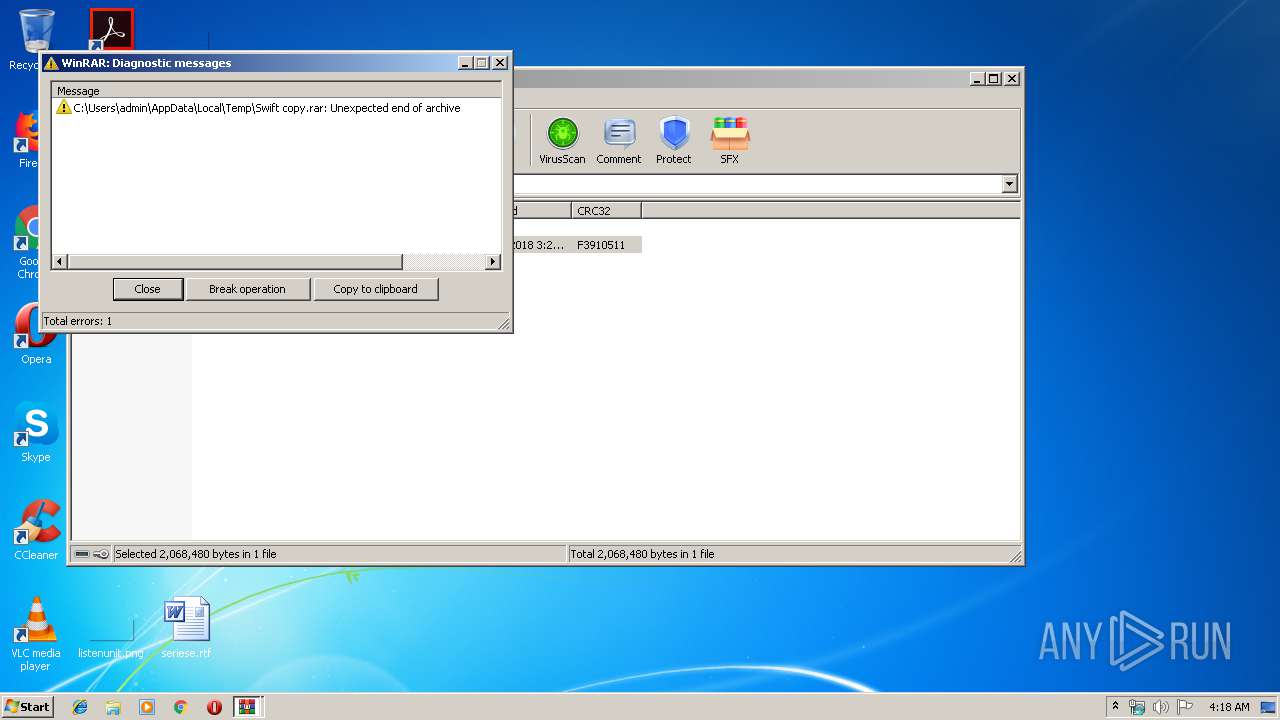
- WinRAR.exe (PID: 3512)
Checks for external IP
- RegSvcs.exe (PID: 2884)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
36
Monitored processes
4
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2868 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.49743\Swift copy.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.49743\Swift copy.exe | — | Swift copy.exe | |||||||||||
User: admin Company: CassiopeazodiacoFILIGRANED0 Integrity Level: MEDIUM Exit code: 0 Version: 9.08.0002 Modules
| |||||||||||||||
| 2884 | "C:\\Windows\Microsoft.NET\Framework\v2.0.50727\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegSvcs.exe | Swift copy.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
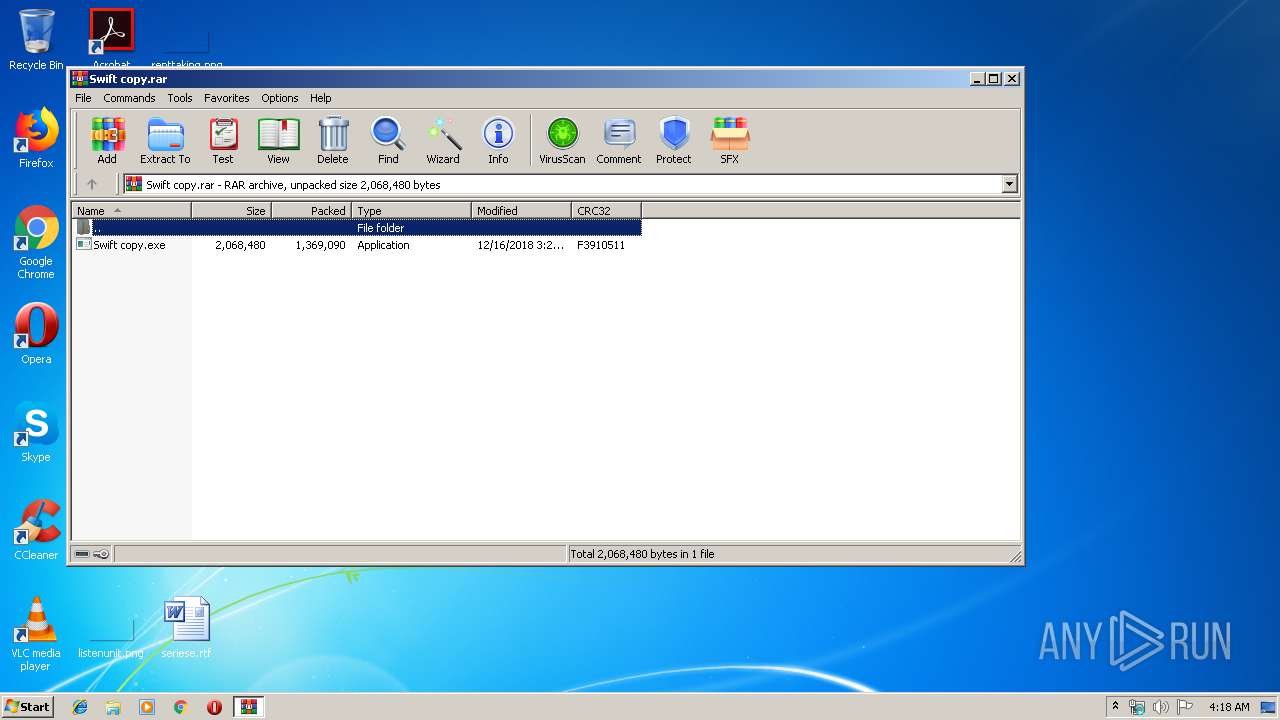
| 3512 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Swift copy.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 4016 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.49743\Swift copy.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.49743\Swift copy.exe | — | WinRAR.exe | |||||||||||
User: admin Company: CassiopeazodiacoFILIGRANED0 Integrity Level: MEDIUM Exit code: 0 Version: 9.08.0002 Modules
| |||||||||||||||
Total events
531
Read events
491
Write events
40
Delete events
0
Modification events
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Swift copy.rar | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3512) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | RegSvcs.exe | C:\Users\admin\AppData\Local\Temp\637023899325277500_6c2bbef4-3822-49b5-bc5b-98fa6281fbab.db | sqlite | |
MD5:— | SHA256:— | |||
| 3512 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3512.49743\Swift copy.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2884 | RegSvcs.exe | GET | 200 | 52.55.255.113:80 | http://checkip.amazonaws.com/ | US | text | 13 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2884 | RegSvcs.exe | 52.55.255.113:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
2884 | RegSvcs.exe | 208.91.198.143:587 | smtp.china-inze.com | PDR | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| malicious |
smtp.china-inze.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2884 | RegSvcs.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2884 | RegSvcs.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2884 | RegSvcs.exe | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla variant outbound SMTP connection |
2884 | RegSvcs.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan-Spy.Keylogger.AgentTesla Exfiltration by SMTP |
3 ETPRO signatures available at the full report